Documente Academic
Documente Profesional
Documente Cultură
Microsoft - Lead2pass.70 412.v2013!06!24.by - Anontester
Încărcat de
Anxo Alonso Da RosaDescriere originală:
Titlu original
Drepturi de autor
Formate disponibile
Partajați acest document
Partajați sau inserați document
Vi se pare util acest document?
Este necorespunzător acest conținut?
Raportați acest documentDrepturi de autor:
Formate disponibile
Microsoft - Lead2pass.70 412.v2013!06!24.by - Anontester
Încărcat de
Anxo Alonso Da RosaDrepturi de autor:
Formate disponibile
Lead2pass.
70-412
Number: 70-412 Passing Score: 700 Time Limit: 120 min File Version: 12.49
Vendor: Microsoft Exam Code: 70-412 Exam Name: Configuring Advanced Windows Server 2012 Services Version: 12.49
100% Pass Guaranteed or Full Refund Lead2Pass 70-412 braindumps can ensure you a passing score in the test. However, if you fail the 70-412 exam at the first attempt after using our products, we will arrange a Full Refund to you. You just need to send your 70-412 score report and some relevant forms to us. After confirming your information, we will proceed for the guarantee claim to eliminate your worries. Prompt Updates on 70-412 Once there is some changes on 70-412 exam, we will update the study materials timely to make them be consistent with the current exam. We devote to giving our customers the best and latest Microsoft 70-412 dumps. Besides, the product you buy will be updated in time within 150 Days for free.
http://www.lead2pass.com/70-412.html
Sections 1. Reworded Questions
Exam A QUESTION 1 Your network contains an Active Directory forest named contoso.com. The forest contains a single domain. The forest functional level is Windows Server 2012. You have a domain controller named DC1. On DC1, you create a new Group Policy object (GPO) named GPO1. You need to verify that GPO1 was replicated to all of the domain controllers. Which tool should you use? A. B. C. D. Group Policy Management Active Directory Sites and Services DFS Management Active Directory Administrative Center
Correct Answer: A Section: (none) Explanation Explanation/Reference: Explanation: http://social.technet.microsoft.com/Forums/en-US/winserverTS/thread/3e580e00-d619-4d25-b22d18f0170279c4 QUESTION 2 Your network contains two DNS servers named DN51 and DNS2 that run Windows Server 2012. DNS1 has a primary zone named contoso.com. DNS2 has a secondary copy of the contoso.com zone. You need to log the zone transfer packets sent between DNS1 and DNS2. What should you configure? A. B. C. D. Monitoring from DNS Manager Logging from Windows Firewall with Advanced Security A Data Collector Set (DCS) from Performance Monitor Debug logging from DNS Manager
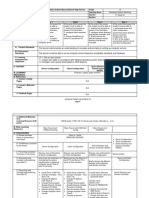
Correct Answer: D Section: (none) Explanation Explanation/Reference: Explanation: http://technet.microsoft.com/en-us/library/cc776361(v=ws.10).aspx http://technet.microsoft.com/en-us/library/cc749337.aspx QUESTION 3 Your network contains an Active Directory forest. The forest contains one domain named contoso.com. The domain contains three domain controllers. The domain controllers are configured as shown in the following table.
DC1 has all of the operations master roles installed. You transfer all of the operations master roles to DC2, and then you uninstall Active Directory from DC1. You need to ensure that you can use Password Settings objects (PSOs) in the domain. What should you do? A. B. C. D. Change the domain functional level. Upgrade DC2. Run the dcgpofix.exe command. Transfer the schema master role.
Correct Answer: A Section: (none) Explanation Explanation/Reference: Explanation: http://technet.microsoft.com/en-us/library/cc753104.aspx QUESTION 4 Your network contains an Active Directory domain named contoso.com. The domain contains a server named Server3 that runs Windows Server 2012 and has the DHCP Server server role installed. DHCP is configured as shown in the exhibit. (Click the Exhibit button.)
http://www.lead2pass.com/70-412.html You need to ensure that only Scope1, Scope3, and Scope5 assign the same DNS servers to DHCP clients. The solution must minimize administrative effort. What should you do? A. Create a superscope and scope-level policies. B. Configure the Scope Options. C. Create a superscope and a filter.
D. Configure the Server Options. Correct Answer: B Section: (none) Explanation Explanation/Reference: Explanation: http://technet.microsoft.com/en-us/library/cc757682(v=WS.10).aspx QUESTION 5 You have a server named Server1 that runs Windows Server 2012. When you install a custom application on Server1 and restart the server, you receive the following error message: "The Boot Configuration Data file is missing some required information. File: \Boot\BCD Error code: 0x0000034." You start Server1 by using Windows PE. You need to ensure that you can start Windows Server 2012 on Server1. Which tool should you use? A. B. C. D. Bootsect Bootim Bootrec Bootcfg
Correct Answer: C Section: (none) Explanation Explanation/Reference: Explanation: http://answers.microsoft.com/en-us/windows/forum/windows_7-system/error-code-0x0000034-in-windows7/4dcb8d38-a206-40ed-bced-55e4a4de9bf2 QUESTION 6 You have a server named Server1 that runs Windows Server 2012. Server1 fails. You identify that the master boot record (MBR) is corrupt. You need to repair the MBR. Which tool should you use? A. B. C. D. Bcdedit Bcdboot Bootrec Fixmbr
Correct Answer: C Section: (none) Explanation Explanation/Reference: Explanation: http://www.youtube.com/watch?v=kFU8kngy6O0
http://social.technet.microsoft.com/Forums/en-US/winservergen/thread/bbf4f440-50ce-4ea2-a3eaa96dc2500352 QUESTION 7 Your network contains an Active Directory domain named contoso.com. All domain controllers run Windows Server 2012. The domain contains two domain controllers. The domain controllers are configured as shown in the following table.
You configure a user named User1 as a delegated administrator of DC10. You need to ensure that User1 can log on to DC10 if the network link between the Main site and the Branch site fails. What should you do? A. B. C. D. Add User1 to the Domain Admins group. On DC10, run ntdsutil and configure the settings in the Roles context. Run repadmin and specify the /prp parameter. On DC1, modify the User Rights Assignment in Default Domain Controllers Group Policy object (GPO).
Correct Answer: D Section: (none) Explanation Explanation/Reference: Explanation: Modify the following policy: Computer Configuration\Windows Settings\Security Settings\Local Policies\User Rights Assignment\Allow log on locally Note: * User Rights Assignment policies determines which users or groups have logon rights or privileges on the computer. * Delegated administrator accounts gain local administrative permissions to the RODC. These users can operate with privileges equivalent to the local computer's Administrators group. They are not members of the Domain Admins or the domain built-in Administrators groups. This option is useful for delegating branch office administration without giving out domain administrative permissions. Configuring delegation of administration is not required. QUESTION 8 You perform a full installation of Windows Server 2012 on a virtual machine named Server1. You plan to use Server1 as a reference image. You need to minimize the amount of storage space used by the Windows Server 2012 installation. Which cmdlet should you use? A. B. C. D. Remove-Module Optimize-VHD Optimize-Volume Uninstall-WindowsFeaturehttp://www.lead2pass.com/70-412.html
Correct Answer: B Section: (none)
Explanation Explanation/Reference: Explanation:
http://technet.microsoft.com/en-us/library/hh848458(v=wps.620).aspx QUESTION 9 Your network contains an Active Directory domain named contoso.com. The domain contains a server named Server1 that runs Windows Server 2012 and has the DHCP Server server role installed. Server1 has a scope named Scope1. A policy named Policy1 is configured for Scope1. Policy1 is configured to provide Hyper-V virtual machines a one-day lease. All other computers receive an eight-day lease. You implement an additional DHCP server named Server2 that runs Windows Server 2012. On Server1, you configure Scopel for DHCP failover. You discover that virtual machines that receive IP addresses from Server2 have a lease duration of eight days. You need to ensure that when Server2 assigns IP addresses to the Hyper-V virtual machines, the lease duration is one day. The solution must ensure that other computers that receive IP addresses from Server2 have a lease duration of eight days. What should you do? A. B. C. D. On Server2, right-click Scope1, and then click Reconcile. On Server1, right-click Scope1, and then click Replicate Scope. On Server2, create a new DHCP policy. On Server1, delete Policy1, and then recreate the policy.
Correct Answer: B Section: (none) Explanation Explanation/Reference: Explanation: Scope 1 has been set up for DHCP failover. Now we need to replicate it from Server1 to Server2. QUESTION 10 You deploy an Active Directory Federation Services (AD FS) 2.1 infrastructure. The infrastructure uses Active Directory as the attribute store. Some users report that they fail to authenticate to the AD FS infrastructure. You discover that only users who run third-party web browsers experience issues. You need to ensure that all of the users can authenticate to the AD FS infrastructure successfully. Which Windows PowerShell command should you run? A. B. C. D. Set-ADFSProperties -ProxyTrustTokenLifetime 1:00:00 Set-ADFSProperties -AddProxyAuthenticationRules None Set-ADFSProperties -SSOLifetime 1:00:00 Set-ADFSProperties -ExtendedProtectionTokenCheck None
Correct Answer: A Section: (none) Explanation Explanation/Reference: Explanation: http://technet.microsoft.com/zh-cn/library/ee892317.aspx QUESTION 11 Your network contains an Active Directory domain named contoso.com. All servers run Windows Server 2012. The domain contains a file server named Server1. The domain contains a domain controller named DC1. Server1 contains three shared folders. The folders are configured as shown in the following table.
Folder2 has a conditional expression of User.Department= = MMarketing". You discover that a user named User1 cannot access \\Server1\folder2. User1 can access \\Server1\folderl and \\Server1\folder3. You verify the group membership of User1 as shown in the Member Of exhibit. (Click the Exhibit button.)
You verify the organization information of User1 as shown in the Organization exhibit. (Click the Exhibit button.)
You verify the general properties of User1 as shown in the General exhibit. (Click the Exhibit button.)
You need to ensure that User1 can access the contents of \\Server1\folder2. What should you do? A. From a Group Policy object (GPO), set the Support for Dynamic Access Control and Kerberos armoring setting to Always provide claims. B. Change the department attribute of User1. C. Grant the Full Control NTFS permissions on Folder2 to User1. D. Remove Userl1from the Accounting global group. Correct Answer: B Section: (none) Explanation Explanation/Reference: Explanation: QUESTION 12 You have a server named Server1 that runs Windows Server 2012. You install the File and Storage Services server role on Server1. From Windows Explorer, you view the properties of a folder named Folder1 and you discover that the
Classification tab is missing. You need to ensure that you can assign classifications to Folder1 from Windows Explorer manually. What should you do? A. B. C. D. From Folder Options, clear Hide protected operating system files (Recommended). Install the File Server Resource Manager role service. From Folder Options, select the Always show menus. Install the Share and Storage Management Tools.
Correct Answer: B Section: (none) Explanation Explanation/Reference: Explanation: http://technet.microsoft.com/en-us/library/dd758759(v=WS.10).aspx QUESTION 13 Your network contains an Active Directory domain named contoso.com. All domain controllers run Windows Server 2012. The domain contains two domain controllers. The domain controllers are configured as shown in the following table.
The Branch site contains a perimeter network. For security reasons, client computers in the perimeter network can communicate with client computers in the Branch site only. You plan to deploy a new RODC to the perimeter network in the Branch site. You need to ensure that the new RODC will be able to replicate from DC10. What should you do first on DC10? A. B. C. D. Enable the Bridge all site links setting. Run the Active Directory Domain Services Configuration Wizard. Create an Active Directory site link bridge. Create an Active Directory site.
Correct Answer: C Section: (none) Explanation Explanation/Reference: Explanation: The right answer is C http://technet.microsoft.com/en-us/library/cc738789(v=ws.10).aspx http://technet.microsoft.com/en-us/library/cc778718(v=WS.10).aspx QUESTION 14 Your network contains an Active Directory domain named contoso.com. The domain contains two member servers named Server1 and Server2 that run Windows Server 2012. Server1 has Microsoft SQL Server 2012 installed.
You install the Active Directory Federation Services server role on Server2. You need to configure Server2 as the first Active Directory Federation Services (AD FS) server in the domain. The solution must ensure that the AD FS database is stored in a SQL Server database on Server1. What should you do on Server2? A. B. C. D. From a command prompt, run fsutil.exe. From Windows PowerShell, run Install-ADFSFarm. From Server Manager, install the Federation Service Proxy. From Server Manager, install the AD FS Web Agents.
Correct Answer: B Section: (none) Explanation Explanation/Reference: Explanation: Install-AdfsFarm Creates the first node of a new federation server farm. Parameter: -SQLConnectionString<String> Specifies the SQL Server database that will store the AD FS configuration settings. If not specified, the AD FS installer uses the Windows Internal Database to store configuration settings. http://technet.microsoft.com/en-us/library/jj553792.aspx QUESTION 15 Your network contains an Active Directory forest named contoso.com. The forest contains a single domain. The domain contains three domain controllers. The domain controllers are configured as shown in the following table.
You plan to test an application on a server named Server1. Server1 is currently located in Site1. After the test, Server1 will be moved to Site2. You need to ensure that Server1 attempts to authenticate to DC3 first, while you test the application. What should you do? A. B. C. D. Create a new site and associate the site to an existing site link object. Modify the priority of site-specific service location (SRV) DNS records for Site2. Create a new subnet object and associate the subnet object to an existing site. Modify the weight of site-specific service location (SRV) DNS records Site1.
Correct Answer: B Section: (none) Explanation Explanation/Reference: Explanation: Service Location (SRV) Resource Record Priority A number between 0 and 65535 that indicates the priority or level of preference given for this record to the host that is specified in Host offering this service. Priority indicates this host's priority with respect to the other hosts in this domain that offer the same service and are specified by different service location (SRV) resource records.
Incorrect: Not D: Weight: A number between 1 and 65535 to be used as a load-balancing mechanism. When you select among more than one target SRV host for the type of service (specified in Service) that use the same Priority number, you can use this field to weight preference toward specific hosts. Where several hosts share equal priority, SRV-specified hosts with higher weight values that are entered here should be returned first to resolver clients in SRV query results. Reference: Service Location (SRV) Resource Record Dialog Box QUESTION 16 Your network contains an Active Directory domain named contoso.com. The domain contains a file server named Server1. The File Server Resource Manager role service is installed on Server1. All servers run Windows Server 2012. A Group Policy object (GPO) named GPO1 is linked to the organizational unit (OU) that contains Server1. The following graphic shows the configured settings in GPO1.
Server1 contains a folder named Folder1. Folder1 is shared as Share1. You attempt to configure access-denied assistance on Server1, but the Enable access-denied assistance option cannot be selected from File Server Resource Manager. You need to ensure that you can configure access-denied assistance on Server1 manually by using File Server Resource Manager. Which two actions should you perform? A. B. C. D. Set the Enable access-denied assistance on client for all file types policy setting to Disabled for GPO1. Set the Customize message for Access Denied errors policy setting to Not Configured for GPO1. Set the Enable access-denied assistance on client for all file types policy setting to Enabled for GPO1. Set the Customize message for Access Denied errors policy setting to Enabled for GPO1.
Correct Answer: B Section: (none) Explanation Explanation/Reference: Explanation: The right answer is D. http://technet.microsoft.com/en-us/library/hh831402.aspx#BKMK_1 QUESTION 17 Your company has a main office and a remote office. The remote office is used for disaster recovery. The network contains an Active Directory domain named contoso.com. The domain contains member servers named Server1, Server2, Server3, and Server4. All servers run Windows Server 2012.
Server1 and Server2 are located in the main office. Server3 and Server4 are located in the remote office. All servers have the Failover Clustering feature installed. The servers are configured as nodes in a failover cluster named Cluster1. Storage is replicated between the main office and the remote site. You need to ensure that Cluster1 is available if two nodes in the same office fail. What are two possible quorum configurations that achieve the goal? (Each correct answer presents a complete solution. Choose two.) A. B. C. D. Node Majority No Majority: Disk Only Node and File Share Majority Node and Disk Majority
Correct Answer: AB Section: (none) Explanation Explanation/Reference: Explanation: Depending on the quorum configuration option that you choose and your specific settings, the cluster will be configured in one of the following quorum modes: * (A) Node majority (no witness) Only nodes have votes. No quorum witness is configured. The cluster quorum is the majority of voting nodes in the active cluster membership. * (B) No majority (disk witness only) No nodes have votes. Only a disk witness has a vote. The cluster quorum is determined by the state of the disk witness. The cluster has quorum if one node is available and communicating with a specific disk in the cluster storage. Generally, this mode is not recommended, and it should not be selected because it creates a single point of failure for the cluster. * Node majority with witness (disk or file share) Nodes have votes. In addition, a quorum witness has a vote. The cluster quorum is the majority of voting nodes in the active cluster membership plus a witness vote. A quorum witness can be a designated disk witness or a designated file share witness. Note: * Quorum in Windows 2008 R2 referred to a consensus , that is, a majority of votes is required in order to reach quorum and maintain stability of the cluster. A new option created in Windows Server 2012 which was also back ported to Windows Server 2008 R2 SP1 was the ability to stop a node being able to participate in the voting process. * Dynamic quorum is the ability of the cluster to recalculate quorum on the fly and still maintain a working cluster. This is a huge improvement as we are now able to continue to run a cluster even if the number of nodes remaining in the cluster is less than 50%. This was not possible before but the dynamic quorum concept now allows us to do this. In fact we can reduce the cluster down to the last node (known as last man standing) and still maintain quorum. Reference: Configure and Manage the Quorum in a Windows Server 2012 Failover Cluster QUESTION 18 Your network contains an Active Directory domain named contoso.com. The domain contains four servers named Server1, Server2, Server3, and Server4 that run Windows Server 2012. All servers have the HyperV server role and the Failover Clustering feature installed. The servers are configured as shown in the following table.
Which three actions should you perform? (Each correct answer presents part of the solution. Choose three.) A. B. C. D. E. From Hyper-V Manager on a node in Cluster2, create three virtual machines. From Hyper-V Manager on a node in Cluster2, modify the Hyper-V settings. From Failover Cluster Manager on Cluster1, configure each virtual machine for replication. From Cluster1, add and configure the Hyper-V Replica Broker role. From Cluster2, add and configure the Hyper-V Replica Broker role.
Correct Answer: ACE Section: (none) Explanation Explanation/Reference: Explanation: A: Need to have same number of replicated VMs in the replicated site. C: Once the hosting server is configured for Replica, you can enable replication for each virtual machine that you want to be replicated. E: The Hyper-V Replica Broker is placed in the replicated cluster Note: * Each node of the failover cluster that is involved in Replica must have the Hyper-V server role installed. * Windows Server 2012 Hyper-V Replica is a built-in mechanism for replicating Virtual Machines (VMs). It can replicate selected VMs in real-time or asynchronously from a primary site to a designated replica site across LAN/WAN. Here a replica site hosts a replicated VM while an associated primary site is where the source VM runs. And either a replica site or a primary site can be a Windows Server 2012 Hyper-V host or a Windows Server 2012 Failover Cluster. QUESTION 19 Your network contains an Active Directory forest named contoso.com. The forest contains two domains named contoso.com and childl.contoso.com. The domains contain three domain controllers. The domain controllers are configured as shown in the following table.
You need to ensure that the KDC support for claims, compound authentication, and kerberos armoring setting is enforced in the child1.contoso.com domain. Which two actions should you perform? (Each correct answer presents part of the solution. Choose two.)
A. B. C. D. E.
Upgrade DC1 to Windows Server 2012. Upgrade DC11 to Windows Server 2012. Raise the domain functional level ofchildl.contoso.com, Raise the domain functional level of contoso.com. Raise the forest functional level of contoso.com.
Correct Answer: BD Section: (none) Explanation Explanation/Reference: Explanation: QUESTION 20 You have a server named Server1 that runs Windows Server 2012. The storage on Server1 is configured as shown in the following table.
You plan to implement Data Deduplication on Server1. You need to identify on which drives you can enable Data Deduplication. Which three drives should you identify? (Each correct answer presents part of the solution. Choose two.) A. B. C. D. E. C D E F G
Correct Answer: BDE Section: (none) Explanation Explanation/Reference: Explanation: Volumes that are candidates for deduplication must conform to the following requirements: * (not A) Must not be a system or boot volume. Deduplication is not supported on operating system volumes. * Can be partitioned as a master boot record (MBR) or a GUID Partition Table (GPT), and must be formatted using the NTFS file system. * Can reside on shared storage, such as storage that uses a Fibre Channel or an SAS array, or when an iSCSI SAN and Windows Failover Clustering is fully supported. * Do not rely on Cluster Shared Volumes (CSVs). You can access data if a deduplication-enabled volume is converted to a CSV, but you cannot continue to process files for deduplication. * (not C) Do not rely on the Microsoft Resilient File System (ReFS).
* Must be exposed to the operating system as non-removable drives. Remotely-mapped drives are not supported. QUESTION 21 You have 20 servers that run Windows Server 2012. You need to create a Windows PowerShell script that registers each server in Windows Azure Online Backup and sets an encryption passphrase. Which two PowerShell cmdlets should you run in the script? (Each correct answer presents part of the solution. Choose two.) A. B. C. D. E. New-OBPolicy New-OBRetentionPolicy Add-OBFileSpec Start-OBRegistration Set OBMachineSetting
Correct Answer: DE Section: (none) Explanation Explanation/Reference: Explanation: D: Start-OBRegistration Registers the current computer with Windows Azure Online Backup using the credentials (username and password) created during enrollment. E: The Set-OBMachineSetting cmdlet sets a OBMachineSetting object for the server that includes proxy server settings for accessing the internet, network bandwidth throttling settings, and the encryption passphrase that is required to decrypt the files during recovery to another server. Incorrect: Not C: The Add-OBFileSpec cmdlet adds the OBFileSpec object, which specifies the items to include or exclude from a backup, to the backup policy (OBPolicy object). The OBFileSpec object can include or exclude multiple files, folders, or volumes. T QUESTION 22 Your network contains an Active Directory domain named contoso.com. The domain contains a server named Server1 that runs Windows Server 2012. You need to ensure that a WIM file that is located on a network share is used as the installation source when installing server roles and features on Server1. Which two actions should you perform? (Each correct answer presents part of the solution. Choose two.) A. Run the dism.exe command and specify the /remove-package parameter. B. Run the Remove-WindowsFeature cmdlet. C. Enable and configure the Specify settings for optional component installation and component repair policy setting by using a Group Policy object (GPO). D. Enable the Enforce upgrade component rules policy setting by using a Group Policy object (GPO). E. Run the Remove-WindowsPackage cmdlet. Correct Answer: AC Section: (none) Explanation Explanation/Reference: Explanation: A: To remove packages from an offline image by using DISM Example: At a command prompt, specify the package identity to remove it from the image. You can remove multiple packages on one command line. DISM /Image:C:\test\offline /Remove-Package /PackageName:Microsoft.Windows.Calc.Demo~6595b6144ccf1df~x86~en~1.0.0.0 /PackageName: Microsoft-Windows-MediaPlayer-Package~31bf3856ad364e35~x86~~6.1.6801.0
C: * You can use Group Policy to specify a Windows image repair source to use within your network. The repair source can be used to restore Windows features or to repair a corrupted Windows image. * Set Group Policy You can use Group Policy to specify when to use Windows Update, or a network location as a repair source for features on demand and automatic corruption repair. To configure Group Policy for Feature on Demand Note: * The Windows Imaging Format (WIM) is a file-based disk image format. It was developed by Microsoft to help deploy Windows Vista and subsequent versions of Windows operating system family, as well as Windows Fundamentals for Legacy PCs. QUESTION 23 Your network contains an Active Directory forest. The forest contains two domains named contoso.com and fabrikam.com. The functional level of the forest is Windows Server 2003. You have a domain outside the forest named litwareinc.com. You need to configure an access solution to meet the following requirements: - Users in litwareinc.com must be able to access resources on a server named Server1 in contoso.com. - Users in the contoso.com forest must be prevented from accessing any resources in litwareinc.com. - Users in litwareinc.com must be prevented from accessing any other resources in the contoso.com forest. Which three actions should you perform? (Each correct answer presents part of the solution. Choose three.) A. B. C. D. E. F. Configure SID filtering on the trust. Configure forest-wide authentication on the trust. Create a one-way forest trust. Create a one-way external trust Modify the permission on the Server1 object. Configure selective authentication on the trust.
Correct Answer: DEF Section: (none) Explanation Explanation/Reference: Explanation: D (not C): litwareinc.com is outside the forest so we need an external trust (not a forest trust). E: Must grant the required permissions on Server1. F(not B): For external trust we must either select Domain-Wide or Selective Authentication (forst- wide authentication is not an option) BCE Note: * You can create an external trust to form a one-way or two-way, nontransitive trust with domains that are outside your forest. External trusts are sometimes necessary when users need access to resources in a Windows NT 4.0 domain or in a domain that is located in a separate forest that is not joined by a forest trust. / To select the scope of authentication for users that are authenticating through a forest trust, click the forest trust that you want to administer, and then click Properties . On the Authentication tab, click either Forest-wide authentication or Selective authentication . / To select the scope of authentication for users that are authenticating through an external trust, click the external trust that you want to administer, and then click Properties . On the Authentication tab, click either Domain-wide authentication or Selective authentication . * The forest-wide authentication setting permits unrestricted access by any users in the trusted forest to all available shared resources in any of the domains in the trusting forest. * Forest-wide authentication is generally recommended for users within the same organization. Reference: Select the Scope of Authentication for Users QUESTION 24 Your network contains an Active Directory domain named contoso.com. The domain contains a file server
named Server1 and a domain controller named DC1. All servers run Windows Server 2012. A Group Policy object (GPO) named GPO1 is linked to the domain. Server1 contains a folder named Folder1. Folder1 is shared as Share1. You need to ensure that authenticated users can request assistance when they are denied access to the resources on Server1. Which two actions should you perform? (Each correct answer presents part of the solution. Choose two.) A. B. C. D. E. Assign the Read Attributes NTFS permission on Folder1 to the Authenticated Users group. Install the File Server Resource Manager role service on Server1. Configure the Customize message for Access Denied errors policy setting of GPO1. Enable the Enable access-denied assistance on client for all file types policy setting for GPO1. Install the File Server Resource Manager role service on DC1.
Correct Answer: BD Section: (none) Explanation Explanation/Reference: http://technet.microsoft.com/en-us/library/hh831402.aspx#BKMK_1 QUESTION 25 Your network contains an Active Directory domain named adatum.com. All domain controllers run Windows Server 2008 R2. The domain contains a file server named Server6 that runs Windows Server 2012. Server6 contains a folder named Folder1. Folder1 is shared as Share1. The NTFS permissions on Folder1 are shown in the exhibit. (Click the Exhibit button.) The domain contains two global groups named Group1 and Group2. You need to ensure that only users who are members of both Group1 and Group2 are denied access to Folder1. Which two actions should you perform? (Each correct answer presents part of the solution. Choose two.) Exhibit:
A. B. C. D. E. F.
Remove the Deny permission for Group1 from Folder1. Deny Group2 permission to Folder1. Install a domain controller that runs Windows Server 2012. Create a conditional expression. Deny Group2 permission to Share1. Deny Group1 permission to Share1.
Correct Answer: CD Section: (none) Explanation Explanation/Reference: http://social.technet.microsoft.com/wiki/contents/articles/14269.introducing-dynamic-access-control-en-us. aspx QUESTION 26 You have a server named Server1 that runs Windows Server 2012. Server1 has a single volume that is encrypted by using BitLocker Drive Encryption (BitLocker). BitLocker is configured to save encryption keys to a Trusted Platform Module (TPM). Server1 is configured to perform a daily system image backup. The motherboard on Server1 is upgraded. After the upgrade, Windows Server 2012 on Server1 fails to start. You need to start the operating system on Server1 as soon as possible. What should you do?
A. Start Server1 from the installation media. Run startrec.exe. B. Move the disk to a server that has a model of the old motherboard. Start the server from the installation media. Run bcdboot.exe. C. Move the disk to a server that has a model of the old motherboard. Start the server. Run tpm.msc. D. Start Server1 from the installation media. Perform a system image recovery. Correct Answer: D Section: (none) Explanation Explanation/Reference: Encryption keys are lost. Nothing mentioned about password/keys recovery. My point is that the only way is to restore the server from a backup. QUESTION 27 You have 3 server named LON-DC1 that runs Windows Server 2012. An iSCSI virtual disk named VirtualiSCSIl.vhd exists on LON-DC1 as shown in the exhibit. (Click the Exhibit button.) You create a new iSCSI virtual disk named VirtualiSCSI2.vhd by using the existing itgt iSCSI target. VirtualiSCSIl.vhd is removed from LON-DC1. You need to assign VirtualiSCSI2.vhd a logical unit value of 0. What should you do? Exhibit:
A. Modify the properties of the VirtualiSCSI2.vhd iSCSI virtual disk. B. Run the Add-IscsiVirtualDiskTargetMapping cmdlet and specify the -Lun parameter.
C. Run the iscsicli command and specify the reportluns parameter. D. Run the iscsicpl command and specify the virtualdisklun parameter. Correct Answer: B Section: (none) Explanation Explanation/Reference: http://technet.microsoft.com/en-us/library/jj612800(v=wps.620).aspx
QUESTION 28 Your network contains an Active Directory forest named contoso.com. The forest contains a single domain. The forest contains three Active Directory sites named SiteA, SiteB, and SiteC. The sites contain four domain controllers. The domain controllers are configured as shown in the following table.
An IP site link exits between each site. You discover that the users in SiteC are authenticated by the domain controllers in SiteA and SiteB. You need to ensure that the SiteC users are authenticated by the domain controllers in SiteB, unless all of the domain controllers in SiteB are unavailable. What should you do? A. Create a site link bridge. B. Create additional connection objects for DC3 and DC4.
C. Create additional connection objects for DC1 and DC2. D. Increase the cost of the site link between SiteA and SiteC. Correct Answer: D Section: (none) Explanation Explanation/Reference: http://technet.microsoft.com/en-us/library/dd277430.aspx#XSLTsection126121120120
QUESTION 29 Your network contains an Active Directory domain named contoso.com. A previous administrator implemented a Proof of Concept installation of Active Directory Rights Management Services (AD RMS). After the proof of concept was complete, the Active Directory Rights Management Services server role was removed. You attempt to deploy AD RMS. During the configuration of AD RMS, you receive an error message indicating that an existing AD RMS Service Connection Point (SCP) was found. You need to remove the existing AD RMS SCP. Which tool should you use? A. B. C. D. Authorization Manager TPM Management Active Directory Sites and Services Services
Correct Answer: C Section: (none) Explanation Explanation/Reference:
QUESTION 30 You have a server named Server1 that runs Windows Server 2012. Windows Server 2012 is installed on volume C. You need to ensure that Safe Mode with Networking loads the next time Server1 restarts. Which tool should you use? A. B. C. D. The Msconfig command The Restart-Server cmdlet The Restart-Computer cmdlet The Bootcfg command
Correct Answer: A Section: (none) Explanation Explanation/Reference:
QUESTION 31 Your network contains an Active Directory domain named contoso.com. The domain contains a domain controller named DC1 that runs Windows Server 2012. DC1 has the DNS Server server role installed. The network contains client computers that run either Linux, Windows 7, or Windows 8. You have a standard primary zone named adatum.com as shown in the exhibit. (Click the Exhibit button.) You plan to configure Name Protection on all of the DHCP servers. You need to configure the adatum.com zone to support Name Protection. Which two configurations should you perform from DNS Manager? (Each correct answer presents part of the solution. Choose two.) Exhibit:
A. B. C. D.
Sign the zone. Store the zone in Active Directory. Modify the Security settings of the zone. Configure Dynamic updates.
Correct Answer: BD Section: (none) Explanation Explanation/Reference: http://technet.microsoft.com/en-us/library/ee941152(v=ws.10).aspx
QUESTION 32 You have a DNS server named Server1 that runs Windows Server 2012. Server1 has a signed zone for contoso.com.
You need to configure DNS clients to perform DNSSEC validation for the contoso.com DNS domain. What should you configure?
A. B. C. D.
The Network Connection settings A Name Resolution Policy The Network Location settings The DNS Client settings
Correct Answer: B Section: (none) Explanation Explanation/Reference: Explanation:
QUESTION 33 Your network contains an Active Directory domain named contoso.com. The domain contains a domain controller named DC1 that runs Windows Server 2012. On Dc1, you open DNS Manager as shown in the exhibit. (Click the Exhibit button.)
You need to change the replication scope of the contoso.com zone.
What should you do before you change the replication scope? A. B. C. D. Modify the Zone Transfers settings. Add DC1 to the Name Servers list. Add your user account to the Security settings of the zone. Unsign the zone.
Correct Answer: D Section: (none) Explanation Explanation/Reference: Explanation: http://www.microsoft.com/en-us/download/dlx/ThankYou.aspx?id=29018
QUESTION 34 Your network contains an Active Directory domain named contoso.com. The domain contains a domain controller named DC1 and a member server named Server1. Server1 has the IP Address Management (IPAM) Server feature installed. On Dc1, you configure Windows Firewall to allow all of the necessary inbound ports for IPAM. On Server1, you open Server Manager as shown in the exhibit. (Click the Exhibit button.)
You need to ensure that you can use IPAM on Server1 to manage DNS on DC1. What should you do? A. B. C. D. Modify the outbound firewall rules on Server1. Modify the inbound firewall rules on Server1. Add Server1 to the Remote Management Users group. Add Server1 to the Event Log Readers group.
Correct Answer: D Section: (none) Explanation Explanation/Reference: Explanation:http://social.technet.microsoft.com/Forums/en-US/winserver8gen/thread/c882c077-61bd-45f6ab47-735bd728d3bc/
QUESTION 35 Your network contains an Active Directory domain named contoso.com. The domain contains a domain controller named Dc1. DC1 has the DNS Server server role installed. The network has two sites named Site1 and Site2. Site1 uses 10.10.0.0/16 IP addresses and Site2 uses 10.11.0.0/16 IP addresses. All computers use DC1 as their DNS server. The domain contains four servers named Server1, Server2, Server3, and Server4. All of the servers run a service named Service1. DNS host records are configured as shown in the exhibit. (Click the Exhibit button.)
You discover that computers from the 10.10.1.0/24 network always resolve Service1 to the IP address of Server1. You need to configure DNS on DC1 to distribute computers in Site1 between Server1 and Server2 when the computers attempt to resolve Service1. What should run on DC1? A. B. C. D. dnscmd /config /bindsecondaries 1 dnscmd /config /localnetpriority 0 dnscmd /config /localnetprioritynetmask 0x0000ffff dnscmd /config /roundrobin 0
Correct Answer: C Section: (none) Explanation Explanation/Reference: Explanation: QUESTION 36 You have a DHCP server named Server1. Server1 has an IP address 192.168.1.2 is located on a subnet
that has a network ID of 192.168.1.0/24. On Server1, you create the scopes shown in the following table.
You need to ensure that Server1 can assign IP addresses from both scopes to the DHCP clients on the local subnet. What should you create on Server1? A. B. C. D. A scope A superscope A split-scope A multicast scope
Correct Answer: B Section: (none) Explanation Explanation/Reference: Explanation:
QUESTION 37 Your network contains an Active Directory domain named contoso.com. The domain contains two member servers named Server1 and Server2. All servers run Windows Server 2012. Server1 and Server2 have the Network Load Balancing (NLB) feature installed. The servers are configured as nodes in an NLB cluster named Cluster1. Cluster1 hosts a secure web application named WebApp1. WebApp1 saves user state information locally on each node. You need to ensure that when users connect to WebApp1, their session state is maintained. What should you configure? A. Affinity - None B. Affinity - Single C. The cluster quorum settings
D. E. F. G. H. I. J. K. L.
The failover settings A file server for general use The Handling priority The host priority Live migration The possible owner The preferred owner Quick migration The Scale-Out File Server
Correct Answer: B Section: (none) Explanation Explanation/Reference: http://technet.microsoft.com/en-us/library/bb687542.aspx
QUESTION 38 Your network contains an Active Directory domain named contoso.com. Domain controllers run either Windows Server 2008, Windows Server 2008 R2, or Windows Server 2012. You have a Password Settings object (PSOs) named PSO1. You need to view the settings of PSO1. Which tool should you use? A. B. C. D. Get-ADDomainControllerPasswordReplicationPolicy Get-ADDefaultDomainPasswordPolicy Server Manager Get-ADFineGrainedPasswordPolicy
Correct Answer: D Section: (none) Explanation Explanation/Reference: http://technet.microsoft.com/en-us/library/ee617231.aspx QUESTION 39 Your network contains an Active Directory domain named contoso.com. The domain contains two servers named Server1 and Server2 that run Windows Server 2012. Server1 has the IP Address Management (IPAM) Server feature installed. Server2 has the DHCP Server server role installed. A user named User1 is a member of the IPAM Users group on Server1. You need to ensure that User1 can use IPAM to modify the DHCP scopes on Server2. The solution must minimize the number of permissions assigned to User1. To which group should you add User1? A. B. C. D. IPAM ASM Administrators on Server1 IPAMUG in Active Directory DHCP Administrators on Server2 IPAM MSM Administrators on Server1
Correct Answer: C Section: (none) Explanation Explanation/Reference: QUESTION 40 Your network contains an Active Directory domain named contoso.com. The domain contains a main office and a branch office. An Active Directory site exists for each office. The domain contains two servers named Server1 and Server2 that run Windows Server 2012. Both servers have the DHCP Server server role installed. Server1 is located in the main office site. Server2 is located in the branch office site. Server1 provides IPv4 addresses to the client computers in the main office site. Server2 provides IPv4 addresses to the client computers in the branch office site. You need to ensure that if either Server1 or Server2 are offline, the client computers can still obtain IPv4 addresses. The solution must meet the following requirements: The storage location of the DHCP databases must not be a single point of failure. Server1 must provide IPv4 addresses to the client computers in the branch office site only if Server2 is offline. Server2 must provide IPv4 addresses to the client computers in the main office site only if Server1 is offline. Which configuration should you use? A. B. C. D. Load sharing mode failover partners Hot standby mode failover partners A Network Load Balancing (NLB) cluster A failover cluster
Correct Answer: B Section: (none) Explanation Explanation/Reference: http://blogs.technet.com/b/teamdhcp/archive/2012/09/03/dhcp-failover-hot-standby-mode.aspx
QUESTION 41 Your network contains an Active Directory domain named contoso.com. The domain contains two servers named Server1 and Server2 Both servers have the IP Address Management (IPAM) Server feature installed. You have a support technician named Tech1. Tech1 is a member of the IPAM Administrators group on Server1 and Server2. You need to ensure that Tech1 can use Server Manager on Server1 to manage IPAM on Server2. To which group on Server2 should you add Tech1. A. B. C. D. IPAM MSM Administrators IPAM Administrators winRMRemoteWMIUsers_ Remote Management Users
Correct Answer: C Section: (none) Explanation
Explanation/Reference: QUESTION 42 Your network contains an Active Directory domain named contoso.com. The domain contains a server named Server1 that runs Windows Server 2012. Server1 has the Active Directory Certificate Services server role installed and is configured as an enterprise certification authority (CA). You need to ensure that all of the users in the domain are issued a certificate that can be used for the following purposes: Email security Client authentication Encrypting File System (EFS) Which two actions should you perform? (Each correct answer presents part of the solution. Choose two.) A. B. C. D. E. Modify the properties of the User certificate template, and then publish the template. From a Group Policy, configure the Certificate Services Client - Certificate Enrollment Policy settings. From a Group Policy, configure the Automatic Certificate Request Settings settings. Duplicate the User certificate template, and then publish the template. From a Group Policy, configure the Certificate Services Client - Auto-Enrollment settings.
Correct Answer: DE Section: (none) Explanation Explanation/Reference:
http://technet.microsoft.com/en-us/library/dd851772.aspx
QUESTION 43 You manage an environment that has many servers. The servers run Windows Server 2012 and use iSCSI storage. Administrators report that it is difficult to locate available iSCSI resources on the network. You need to ensure that the administrators can locate iSCSI resources on the network by using a central repository. Which feature should you deploy? A. B. C. D. The iSNS Server service feature The iSCSI Target Storage Provider feature The Windows Standards-Based Storage Management feature The iSCSI Target Server role service
Correct Answer: A Section: (none) Explanation Explanation/Reference: http://technet.microsoft.com/en-us/library/cc772568.aspx QUESTION 44 Your network contains an Active Directory domain named contoso.com. The domain contains domain controllers that run either Windows Server 2003, Windows Server 2008 R2, or Windows Server 2012. You plan to implement a new Active Directory forest. The new forest will be used for testing and will be isolated from the production network. In the test network, you deploy a server named Server1 that runs Windows Server 2012. You need to configure Server1 as a new domain controller in a new forest named contoso.test that also does name resolution. The solution must meet the following.
Select two options below. A. B. C. D. E. F. G. H. I. J. K. There is no need to set the Forest Functional Level. Set Forest Functional Level to Windows 2003. Set Forest Functional Level to Windows 2008 Set Forest Functional Level to Windows 2008 R2. Set Forest Functional Level to Windows 2012. Set Domain name system(DNS) server There is no need to set the Domain Functional Level. Set Domain Functional Level to Windows 2003. Set Domain Functional Level to Windows 2008 Set Domain Functional Level to Windows 2008 R2. Set Domain Functional Level to Windows 2012.
Correct Answer: BFH Section: Reworded Questions Explanation Explanation/Reference: Very smartly reworded that you need to configure server 1 as new DC in a new forest named contoso.test and "also do name resolution". In the answer you will have to select Windows 2003 as domain and forest functional level and you should also check "Domain name system(DNS) server.... This is not in any dumps Explanation: * When you deploy AD DS, set the domain and forest functional levels to the highest value that your environment can support. This way, you can use as many AD DS features as possible. For example, if you are sure that you will never add domain controllers that run Windows Server 2003 to the domain or forest, select the Windows Server 2008 functional level during the deployment process. However, if you might retain or add domain controllers that run Windows Server 2003, select the Windows Server 2003 functional level. When you deploy a new forest, you are prompted to set the forest functional level and then set the domain functional level. You cannot set the domain functional level to a value that is lower than the forest functional level.
Reference: Understanding Active Directory Domain Services (AD DS) Functional Levels QUESTION 45 Your network contains two Active Directory forests named contoso.com and fabrikam.com. The contoso. com forest contains two domains named corp.contoso.com and contoso.com. You establish a two-way forest trust between contoso.com and fabrikam.com. Users from the corp.contoso.com domain report that they cannot log on to client computers in the fabrikam. com domain by using their corp.contoso.com user account. When they try to log on, they receive following error message: "The computer you are signing into is protected by an authentication firewall. The specified account is not allowed to authenticate to the computer." Corp.contoso.com users can log on successfully to client computers in the contoso.com domain by using their corp.contoso.com user account credentials. You need to allow users from the corp.contoso.com domain to log on to the client computers in the fabrikam.com forest. What should you do?
A. B. C. D.
Configure Windows Firewall with Advanced Security. Enable SID history. Configure forest-wide authentication. Instruct the users to log on by using a user principal name (UPN).
Correct Answer: C Section: (none) Explanation Explanation/Reference: Explanation: http://technet.microsoft.com/en-us/library/cc785875(v=ws.10).aspx
QUESTION 46 You have a server named Server1 that runs Windows Server 2012 and is used for testing. A developer at your company creates and installs an unsigned kernel-mode driver on Server1. The developer reports that Server1 will no longer start.
You need to ensure that the developer can test the new driver. The solution must minimize the amount of data loss. Which Advanced Boot Option should you select? A. B. C. D. Disable Driver Signature Enforcement Disable automatic restart on system failure Last Know Good Configuration (advanced) Repair Your Computer
Correct Answer: A Section: (none) Explanation Explanation/Reference: Explanation:
QUESTION 47 You have a server named Server 1 that runs Windows Server 2012. Server1 has five network adapters. Three of the network adapters are connected to a network named LAN1. The two other network adapters are connected to a network named LAN2. You create a network adapter team named Team1 from two of the adapters connected to LAN1. You create a network adapter team named Team2 from the two adapters connected to LAN2. A company policy states that all server IP addresses must be assigned by using a reserved address in DHCP. You need to identify how many DHCP reservations you must create for Server1. How many reservations should you identify? A. B. C. D. 2 3 5 7
Correct Answer: B
Section: (none) Explanation Explanation/Reference: 3 adapter on LAN 1 2 adapters on LAN 2 2 adapters on LAN 1 used in a team, so that's 3 - 2 leaving 1. 2 adapaters on LAN 2 used in a team, so that's 2 - 2 leaving 0. 1 team on LAN 1 + 1 team on LAN 2 + remaining adapter on LAN 1 = 3. QUESTION 48 Your network contains an Active Directory domain named contoso.com. The domain contains servers named Server1 and Server2 that run Windows Server 2012. Server1 has the IP Address Management (IPAM) Server feature installed. You install the IPAM client on Server2. You open Server Manager on Server2 as shown in the exhibit. (Click the Exhibit button.)
You need to manage IPAM from Server2. What should you do first? A. B. C. D. On Server2, open Computer Management and connect to Server1. On Server1, add the Server2 computer account to the IPAM ASM Administrators group. On Server2, add Server1 to Server Manager. On Server1, add the Server2 computer account to the IPAM MSM Administrators group.
Correct Answer: C Section: (none)
Explanation Explanation/Reference:
QUESTION 49 Your network contains an Active Directory domain named contoso.com. The domain contains a domain controller named DC1 and a member server named Server1. Server1 has the IP Address Management (IPAM) Server feature installed. On DC1, you configure Windows Firewall to allow all of the necessary inbound ports for IPAM. On Server1, you open Server Manager as shown in the exhibit. (Click the Exhibit button.) You need to ensure that you can use IPAM on Server1 to manage DNS on DC1. What should you do?
A. B. C. D.
Modify the outbound firewall rules on Server1. Add Server1 to the Remote Management Users group. Add Server1 to the Event Log Readers group. Modify the inbound firewall rules on Server1.
Correct Answer: C Section: (none) Explanation Explanation/Reference: http://technet.microsoft.com/en-us/library/jj878313.aspx
QUESTION 50 Your network contains an Active Directory domain named contoso.com. The domain contains a server named Server1 that runs Windows Server 2012. Server1 has the IP Address Management (IPAM) Server feature installed. IPAM is configured currently for Group Policy-based provisioning. You need to change the IPAM provisioning method on Server1. What should you do? A. B. C. D. Run the ipamgc.exe command. Run the Set-IPAMConfiguration cmdlet. Reinstall the IP Address Management (IPAM) Server feature. Delete IPAM Group Policy objects (GPOs) from the domain.
Correct Answer: C Section: (none) Explanation Explanation/Reference: You cannot change the provisioning method after completing the initial setup.
QUESTION 51 Your network contains an Active Directory domain named contoso.com. The domain contains four servers. The servers are configured as shown in the following table.
You plan to deploy an enterprise certification authority (CA) on a server named Server5. Server5 will be used to issue certificates to domain-joined computers and workgroup computers. You need to identify which server you must use as the certificate revocation list (CRL) distribution point for Server5. Which server should you identify? A. B. C. D. Server1 Server3 Server4 Server2
Correct Answer: B Section: (none) Explanation Explanation/Reference:
We cannot use AD DS because workgroup computers must access CRL distribution point QUESTION 52 Your network contains three Active Directory forests. Each forest contains an Active Directory Rights Management Services (AD RMS) root cluster. All of the users in all of the forests must be able to access protected content from any of the forests. You need to identify the minimum number of AD RMS trusts required. How many trusts should you identify? A. B. C. D. 2 3 4 6
Correct Answer: D Section: (none) Explanation Explanation/Reference: http://technet.microsoft.com/en-us/library/ee221071(v=ws.10).aspx
Exam B QUESTION 1 Your network contains two servers named Server1 and Server2 that run Windows Server 2012. Server1 and Server2 have the Hyper-V server role installed. Server1 and Server2 are configured as Hyper-V replicas of each other. Server1 hosts a virtual machine named VM1. VM1 is replicated to Server2. You need to verify whether the replica of VM1 on Server2 is functional. The solution must ensure that VM1 remains accessible to clients. What should you do from Hyper-V Manager?
A. B. C. D.
On Server1, execute a Planned Failover. On Server1, execute a Test Failover. On Server2, execute a Planned Failover. On Server2, execute a Test Failover.
Correct Answer: D Section: (none) Explanation Explanation/Reference: http://blogs.technet.com/b/virtualization/archive/2012/07/26/types-of-failover-operations-in-hyper-v-replica. aspx
QUESTION 2 You have a failover cluster named Cluster1 that contains four nodes. All of the nodes run Windows Server 2012. You need to force every node in Cluster1 to contact immediately the Windows Server Update Services (WSUS) server on your network for updates. Which tool should you use?
A. B. C. D.
The Add-CauClusterRole cmdlet The Wuauclt command The Wusa command The Invoke-CauScan cmdlet
Correct Answer: D Section: (none) Explanation
Explanation/Reference: http://technet.microsoft.com/en-us/library/hh831694.aspx QUESTION 3 Your network contains an Active Directory domain named contoso.com. The network contains a file server named Server1 that runs Windows Server 2012. You are configuring a central access policy for temporary employees. You enable the Department resource property and assign the property a suggested value of Temp. You need to configure a target resource condition for the central access rule that is scoped to resources assigned to Temp only. Which condition should you use?
A. B. C. D.
(Temp.Resource Equals "Department") (Resource.Temp Equals "Department") (Resource.Department Equals "Temp") (Department.Value Equals "Temp")
Correct Answer: C Section: (none) Explanation Explanation/Reference: http://technet.microsoft.com/fr-fr/library/hh846167.aspx
QUESTION 4 Your network contains a server named Server1 that runs Windows Server 2012. Server1 has the Active Directory Certificate Services server role installed and is configured as a standalone certification authority (CA).
You install a second server named Server2. You install the Online Responder role service on Server2. You need to ensure that Server1 can issue an Online Certificate Status Protocol (OCSP) Response Signing certificate to Server2. What should you do?
A. B. C. D.
On Server1, run the certutil.exe command and specify the -setreg parameter. On Server2, run the certutil.exe command and specify the -policy parameter. On Server1, configure Security for the OCSP Response Signing certificate template. On Server2, configure Issuance Requirements for the OCSP Response Signing certificate template.
Correct Answer: C Section: (none) Explanation Explanation/Reference: http://technet.microsoft.com/en-us/library/cc732526.aspx
QUESTION 5 Your network contains an Active Directory domain named adatum.com. The domain contains a server named CA1 that runs Windows Server 2012. CA1 has the Active Directory Certificate Services server role installed and is configured to support key archival and recovery. You need to ensure that a user named User1 can decrypt private keys archived in the Active Directory Certificate Services (AD CS) database. The solution must prevent User1 from retrieving the private keys from the AD CS database. What should you do?
A. B. C. D.
Assign User1 the Issue and Manage Certificates permission to Server1. Assign User1 the Read permission and the Write permission to all certificate templates. Provide User1 with access to a Key Recovery Agent certificate and a private key. Assign User1 the Manage CA permission to Server1.
Correct Answer: C Section: (none) Explanation Explanation/Reference: http://social.technet.microsoft.com/wiki/contents/articles/7573.active-directory-certificate-services-pki-keyarchival-and-management.aspx#Protecting_Key_Recovery_Agent_Keys
QUESTION 6 Your network contains an Active Directory domain named contoso.com. The domain contains two sites named Site1 and Site2 and two domain controllers named DC1 and DC2. Both domain controllers are located in Site1. You install an additional domain controller named DC3 in Site1 and you ship DC3 to Site2. A technician connects DC3 to Site2. You discover that users in Site2 are authenticated by all three domain controllers. You need to ensure that the users in Site2 are authenticated by DC1 or DC2 only if DC3 is unavailable. What should you do?
A. B. C. D.
From Network Connections, modify the IP address of DC3. In Active Directory Sites and Services, modify the Query Policy of DC3. From Active Directory Sites and Services, move DC3. In Active Directory Users and Computers, configure the insDS-PrimaryComputer attribute for the users in Site2.
Correct Answer: C Section: (none) Explanation Explanation/Reference: QUESTION 7 Your network contains two Active Directory forests named contoso.com and adatum.com. Contoso.com contains one domain. Adatum.com contains a child domain named child.adatum.com. Contoso.com has a one-way forest trust to adatum.com. Selective authentication is enabled on the forest trust. Several user accounts are migrated from child.adatum.com to adatum.com. Users report that after the migration, they fail to access resources in contoso.com. The users successfully accessed the resources in contoso.com before the accounts were migrated. You need to ensure that the migrated users can access the resources in contoso.com. What should you do?
A. B. C. D.
Replace the existing forest trust with an external trust. Run netdom and specify the /quarantine attribute. Disable SID filtering on the existing forest trust. Disable selective authentication on the existing forest trust.
Correct Answer: C Section: (none) Explanation Explanation/Reference: http://technet.microsoft.com/en-us/library/cc755321(v=ws.10).aspx
QUESTION 8 You have four servers that run Windows Server 2012. The servers have the Failover Clustering feature installed. You deploy a new cluster named Cluster1. Cluster1 is configured as shown in the following table.
Site2 is a disaster recovery site. Server1, Server2, and Server3 are configured as the preferred owners of the cluster roles. Dynamic quorum management is disabled. You plan to perform hardware maintenance on Server3. You need to ensure that if the WAN link between Site1 and Site2 fails while you are performing maintenance on Server3, the cluster resource will remain available in Site1. What should you do?
A. B. C. D.
Enable dynamic quorum management. Remove the node vote for Server3. Add a file share witness in Site1. Remove the node vote for Server4 and Server5.
Correct Answer: D Section: (none) Explanation
Explanation/Reference: http://msdn.microsoft.com/en-us/library/hh270280.aspx#VotingandNonVotingNodes
QUESTION 9 You have a test server named Server1 that is configured to dual-boot between Windows Server 2008 R2 and Windows Server 2012. You start Server1 and you discover that the boot entry for Windows Server 2008 R2 no longer appears on the boot menu. You start Windows Server 2012 on Server1 and you discover the disk configurations shown in the following table.
You need to restore the Windows Server 2008 R2 boot entry on Server1. What should you do?
A. B. C. D.
Run bcdedit.exe and specify the /createstore parameter. Run bootrec.exe and specify the /scanos parameter. Run bcdboot.exe d:\windows. Run bootrec.exe and specify the /rebuildbcd parameter.
Correct Answer: D Section: (none) Explanation Explanation/Reference: http://support.microsoft.com/kb/927392/en-us
QUESTION 10 You have a file server named FS1 that runs Windows Server 8. Data Deduplication is enabled on FS1. You need to configure Data Deduplication to run at a normal priority from 20:00 to 06:00 daily. What should you configure? A. B. C. D. File and Storage Services in Server Manager The Data Deduplication process in Task Manager Disk Management in Computer Management The properties of drive C
Correct Answer: A Section: (none) Explanation Explanation/Reference:
QUESTION 11 Your network contains two Active Directory forests named contoso.com and fabrikam.com. A two- way forest trust exists between the forests. The contoso.com forest contains an enterprise certification authority (CA) named CAl. You implement cross-forest certificate enrollment between the contoso.com forest and the fabrikam.com forest. On CA1, you create a new certificate template named Template1. You need to ensure that users in the fabrikam.com forest can request certificates that are based on Template1. Which tool should you use?
A. B. C. D. E.
Sync-ADObject Pkiview.msc CertificateServices.ps1 Certutil PKISync.ps1
Correct Answer: E Section: (none) Explanation Explanation/Reference: Explanation: http://technet.microsoft.com/en-us/library/ff955845(v=ws.10).aspx
QUESTION 12 Your network contains an Active Directory domain named contoso.com. A previous administrator implemented a Proof of Concept installation of Active Directory Rights Management Services (AD RMS). After the proof of concept was complete, the Active Directory Rights Management Services server role was removed. You attempt to deploy AD RMS. During the configuration of AD RMS, you receive an error message indicating that an existing AD RMS Service Connection Point (SCP) was found. You need to remove the existing AD RMS SCP. A. B. C. D. Certification Authority Authorization Manager ADSI Edit Active Directory Domains and Trusts
Correct Answer: C Section: (none) Explanation Explanation/Reference: Explanation: http://social.technet.microsoft.com/wiki/contents/articles/710.the-ad-rms-service-connection-point-en-us.
aspx
QUESTION 13 Your network contains an Active Directory domain named contoso.com. The domain contains a main office and a branch office. An Active Directory site exists for each office. All domain controllers run Windows Server 2012. The domain contains two domain controllers. The domain controllers are configured as shown in the following table.
DC1 hosts an Active Directory-integrated zone for contoso.com. You add the DNS Server server role to DC2. You discover that the contoso.com DNS zone fails to replicate to DC2. You verify that the domain, schema, and configuration naming contexts replicate from DC1 to DC2. You need to ensure that DC2 replicates the contoso.com zone by using Active Directory replication. Which tool should you use? A. B. C. D. Dnslint A DNS Manager Active Directory Users and Computers Dnscmd
Correct Answer: A Section: Reworded Questions Explanation Explanation/Reference: http://support.microsoft.com/kb/321045/ If you see question about AD Replication, First preference is AD sites and services, then Repadmin and then DNSLINT. QUESTION 14 Your network contains an Active Directory forest named adatum.com. The forest contains a single domain. The domain contains four servers. The servers are configured as shown in the following table.
You need to update the schema to support a domain controller that will run Windows Server 2012. On which server should you run adprep.exe? A. B. C. D. DC1 DC2 DC3 Server1
Correct Answer: C Section: (none) Explanation Explanation/Reference: http://technet.microsoft.com/en-us/library/dd464018(v=ws.10).aspx#BKMK_WS2012
QUESTION 15 Your network contains an Active Directory domain named contoso.com. The domain contains domain controllers that run either Windows Server 2003, Windows Server 2008 R2, or Windows Server 2012. You plan to implement a new Active Directory forest. The new forest will be used for testing and will be isolated from the production network. In the test network, you deploy a server named Server1 that runs Windows Server 2012.
You need to configure Server1 as a new domain controller in a new forest named contoso.test. The solution must meet the following.
Select two options below. A. B. C. D. E. F. G. H. I. J. There is no need to set the Forest Functional Level. Set Forest Functional Level to Windows 2003. Set Forest Functional Level to Windows 2008 Set Forest Functional Level to Windows 2008 R2. Set Forest Functional Level to Windows 2012. There is no need to set the Domain Functional Level. Set Domain Functional Level to Windows 2003. Set Domain Functional Level to Windows 2008 Set Domain Functional Level to Windows 2008 R2. Set Domain Functional Level to Windows 2012.
Correct Answer: BG Section: Reworded Questions Explanation Explanation/Reference: Very smartly reworded that you need to configure server 1 as new DC in a new forest named contoso.test and "also do name resolution". In the answer you will have to select Windows 2003 as domain and forest functional level and you should also check "Domain name system(DNS) server.... This is not in any dumps Explanation: * When you deploy AD DS, set the domain and forest functional levels to the highest value that your environment can support. This way, you can use as many AD DS features as possible. For example, if you are sure that you will never add domain controllers that run Windows Server 2003 to the domain or forest, select the Windows Server 2008 functional level during the deployment process. However, if you might retain or add domain controllers that run Windows Server 2003, select the Windows Server 2003 functional level. When you deploy a new forest, you are prompted to set the forest functional level and then set the domain functional level. You cannot set the domain functional level to a value that is lower than the forest functional level. Reference: Understanding Active Directory Domain Services (AD DS) Functional Levels
QUESTION 16 Your network contains two servers named Server1 and Server2 that run Windows Server 2012. Both servers have the Hyper-V server role installed. Server1 and Server2 are located in different offices. The offices connect to each other by using a high-latency WAN link. Server2 hosts a virtual machine named VM1. You need to ensure that you can start VM1 on Server1 if Server2 fails. The solution must minimize hardware costs. What should you do? A. On Server2, install the Multipath I/O (MPIO) feature. Modify the storage location of the VHDs for VM1. B. From the Hyper-V Settings of Server1, modify the Replication Configuration settings. Enable replication for VM1. C. On Server1, install the Multipath I/O (MPIO) feature. Modify the storage location of the VHDs for VM1. D. From the Hyper-V Settings of Server2, modify the Replication Configuration settings. Enable replication for VM1. Correct Answer: B Section: (none) Explanation Explanation/Reference: You first have to enable replication on the Replica server--Server1--by going to the server and modifying the "Replication Configuration" settings under Hyper-V settings. You then. go to VM1--which presides on Server2--and run the "Enable Replication" wizard on VM1.
QUESTION 17 You have a server named File1 that runs Windows Server 2012. File1 has the File Server role service installed. You plan to back up all shared folders by using Microsoft Online Backup. You download and install the Microsoft Online Backup Service Agent on File1. You need to ensure that you use Windows Server Backup to back up data to Microsoft Online Backup. What should you do? A. B. C. D. From Computer Management, add the File1 computer account to the Backup Operators group. From the Services console, modify the Log On settings of the Microsoft Online Backup Service Agent. From Windows Server Backup, run the Register Server Wizard. From a command prompt, run wbadmin.exe enable backup.
Correct Answer: C Section: (none) Explanation Explanation/Reference: http://blogs.technet.com/b/windowsserver/archive/2012/03/28/microsoft-online-backup-service.aspx
QUESTION 18 Your network contains an Active Directory domain named contoso.com. The domain contains three servers named Server1, Server2, and Server3 that run Windows Server 2012. All three servers have the Hyper-V server role installed and the Failover Clustering feature installed. Server1 and Server2 are nodes in a failover cluster named Cluster1. Several highly available virtual machines run on Cluster1. Cluster1 has the Hyper-V Replica Broker role installed. The Hyper-V Replica Broker currently runs on Server1. Server3 currently has no virtual machines. You need to configure Cluster1 to be a replica server for Server3 and Server3 to be a replica server for Cluster1. Which two tools should you use? (Each correct answer presents part of the solution. Choose two.) A. B. C. D. E. The Hyper-V Manager console connected to Server3 The Hyper-V Manager console connected to Server2 The Failover Cluster Manager console connected to Cluster1 The Failover Cluster Manager console connected to Server3 The Hyper-V Manager console connected to Server1
Correct Answer: AC Section: (none) Explanation Explanation/Reference: http://technet.microsoft.com/en-us/library/jj134240.aspx
QUESTION 19 You have a server named Server1 that runs Windows Server 2012. You modify the properties of a system driver and you restart Server1. You discover that Server1 continuously restarts without starting Windows Server 2012. You need to start Windows Server 2012 on Server1 in the least amount of time. The solution must minimize the amount of data loss. Which Advanced Boot Option should you select? A. Repair Your Computer B. Disable Driver Signature Enforcement C. Last Know Good Configuration (advanced)
D. Disable automatic restart on system failure Correct Answer: C Section: (none) Explanation Explanation/Reference: http://windows.microsoft.com/en-ph/windows-vista/using-last-known-good-configuration
QUESTION 20 You have a file server named Server1 that runs a Server Core Installation of Windows Server 2012. You need to ensure that users can access previous versions of files that are shared on Server1 by using the Previous Versions tab. Which tool should you use? A. B. C. D. wbadmin Diskpart Storrept Vssadmin
Correct Answer: D Section: (none) Explanation Explanation/Reference:
QUESTION 21 Your network contains a server named Server1 that runs Windows Server 2012. Server1 has the Hyper-V server role installed. Server1 hosts 10 virtual machines that run Windows Server 2012. You add a new server named Server2. Server2 has faster hard disk drives, more RAM, and a different processor manufacturer than Server1. You need to move all of the virtual machines from Server1 to Server2. The solution must minimize downtime. What should you do for each virtual machine? A. B. C. D. Perform a quick migration. Perform a storage migration. Export the virtual machines from Server1 and import the virtual machines to Server2. Perform a live migration.
Correct Answer: C Section: (none) Explanation Explanation/Reference: The different processor manufacturer is the key here. Storage, Live, and Quick all require same manufacturer.
QUESTION 22 Your network contains an Active Directory domain named contoso.com. The domain contains two member servers named Server1 and Server2. All servers run Windows Server 2012. Server1 and Server2 have the Failover Clustering feature installed. The servers are configured as nodes in a failover cluster named Cluster1. You add two additional nodes to Cluster1. You have a folder named Folder1 on Server1 that contains application data. You plan to provide continuously available access to Folder1. You need to ensure that all of the nodes in Cluster1 can actively respond to the client requests for Folder1. What should you configure? A. B. C. D. E. F. G. H. I. J. K. L. Affinity - None Affinity - Single The cluster quorum settings The failover settings A file server for general use The Handling priority The host priority Live migration The possible owner The preferred owner Quick migration The Scale-Out File Server
Correct Answer: L Section: (none) Explanation Explanation/Reference: http://technet.microsoft.com/en-us/library/hh831349.aspx Scale-Out File Server for application data (Scale-Out File Server) This clustered file server is introduced in Windows Server 2012 and lets you store server application data, such as Hyper-V virtual machine files, on file shares, and obtain a similar level of reliability, availability, manageability, and high performance that you would expect from a storage area network. All file shares are online on all nodes simultaneously. File shares associated with this type of clustered file server are called scale-out file shares. This is sometimes referred to as active-active.
QUESTION 23 Your network contains an Active Directory domain named contoso.com. The domain contains two member servers named Server1 and Server2. All servers run Windows Server 2012. Server1 and Server2 have the Failover Clustering feature installed. The servers are configured as nodes in a failover cluster named Cluster1. Cluster1 hosts an application named Appl. You need to ensure that Server2 handles all of the client requests to the cluster for Appl. The solution must ensure that if Server2 fails, Server1 becomes the active node for Appl. What should you configure? A. B. C. D. E. F. G. H. I. J. K. L. Affinity - None Affinity - Single The cluster quorum settings The failover settings A file server for general use The Handling priority The host priority Live migration The possible owner The preferred owner Quick migration The Scale-Out File Server
Correct Answer: J Section: (none) Explanation Explanation/Reference: http://blogs.msdn.com/b/clustering/archive/2008/10/14/9000092.aspx The preferred owner in a 2 server cluster will always be the active node unless it is down. QUESTION 24 You have a DHCP server named Server1. Server1 has one network adapter. Server1 is located on a subnet named Subnet1. Server1 has scope named Scope1. Scope1 contains IP addresses for the 192.168.1.0/24 network. Your company is migrating the IP addresses on Subnet1 to use a network ID of 10.10.0.0/16. On Server11 you create a scope named Scope2. Scope2 contains IP addresses for the 10.10.0.0/16 network. You need to ensure that clients on Subnet1 can receive IP addresses from either scope. What should you create on Server1? A. A multicast scope B. A scope C. A superscope
D. A split-scope Correct Answer: C Section: (none) Explanation Explanation/Reference: http://technet.microsoft.com/en-us/library/dd759168.aspx
QUESTION 25 Your network contains an Active Directory domain named adatum.com. The domain contains a domain controller named DC1 that runs Windows Server 2012. On Dc1, you open DNS Manager as shown in the exhibit. (Click the Exhibit button.)
You need to change the zone type of the contoso.com zone from an Active Directory-integrated zone to a standard primary zone. What should you do before you change the zone type? A. B. C. D. Unsign the zone. Modify the Zone Signing Key (ZSK). Modify the Key Signing Key (KSK). Change the Key Master.
Correct Answer: A
Section: (none) Explanation Explanation/Reference:
QUESTION 26 You have a server named Server1 that runs Windows Server 2012. Server1 has the DNS Server server role installed. You need to configure Server1 to resolve queries for single-label DNS names. Which two actions should you perform? (Each correct answer presents part of the solution. Choose two.) A. B. C. D. E. F. Run the Set-DNSServerGlobalNameZone cmdlet. Modify the DNS suffix search list setting. Modify the Primary DNS Suffix Devolution setting. Create a zone named ".". Create a zone named GlobalNames. Run the Set-DNSServerRootHint cmdlet.
Correct Answer: AE Section: (none) Explanation Explanation/Reference: Explanation: http://technet.microsoft.com/en-us/library/cc731744.aspx http://technet.microsoft.com/en-us/library/jj649907(v=wps.620).aspx
QUESTION 27 You have a server named DC2 that runs Windows Server 2012. DC2 contains a DNS zone named adatum. com. The adatum.com zone is shown in the exhibit. (Click the Exhibit button.)
You need to configure DNS clients to perform DNSSEC validation for the adatum.com DNS domain. What should you configure? A. B. C. D. The Network Location settings A Name Resolution Policy The DNS Client settings The Network Connection settings
Correct Answer: B Section: (none) Explanation Explanation/Reference: http://technet.microsoft.com/en-us/library/hh831411.aspx#config_client1
QUESTION 28 Your network contains an Active Directory domain named contoso.com. The domain contains two servers named Server1 and Server2 that run Windows Server 2012. Server1 has the DHCP Server server role installed. Server2 has the Hyper-V server role installed. Server2 has an IP address of 192.168.10.50. Server1 has a scope named Scope1 for the 192.168.10.0/24 network. You plan to deploy 20 virtual machines on Server2 that will be connected to the external network. The MAC addresses for the virtual machines will begin with 00-15-SD-83-03. You need to configure Server1 to offer the virtual machines IP addresses from 192.168.10.200 to 192.168.10.219. Physical computers on the network must be offered IP addresses outside this range. You want to achieve this goal by using the minimum amount of administrative effort. What should you do from the DHCP console? A. Create reservations.
B. Create a policy. C. Delete Scope1 and create two new scopes. D. Configure Allow filters and Deny filters. Correct Answer: B Section: (none) Explanation Explanation/Reference: Explanation: http://blogs.technet.com/b/teamdhcp/archive/2012/08/22/granular-dhcp-server-administration-using-dhcppolicies-in-windows-server-2012.aspx
QUESTION 29 Your network contains two Active Directory forests named contoso.com and adatum.com. All of the domain
controllers in both of the forests run Windows Server 2012. The adatum.com domain contains a file server named Servers. Adatum.com has a one-way forest trust to contoso.com. A contoso.com user name User10 attempts to access a shared folder on Servers and receives the error message shown in the exhibit. (Click the Exhibit button.)
You verify that the Authenticated Users group has Read permissions to the Data folder. You need to ensure that User10 can read the contents of the Data folder on Server5 in the adatum.com domain. What should you do? A. B. C. D. Grant the Other Organization group Read permissions to the Data folder. Modify the list of logon workstations of the contoso\User10 user account. Enable the Netlogon Service (NP-In) firewall rule on Servers. Modify the permissions on the Servers computer object in Active Directory.
Correct Answer: D Section: (none) Explanation Explanation/Reference: http://technet.microsoft.com/en-us/library/cc738653(v=ws.10).aspx
QUESTION 30 Your network contains an Active Directory forest. The forest contains two domains named contoso.com and fabrikam.com. The functional level of the forest is Windows Server 2003. You have a domain outside the forest named adatum.com. You need to configure an access solution to meet the following requirements: - Users in adatum.com must be able to access resources in contoso.com. - Users in adatum.com must be prevented from accessing resources in fabrikam.com. - Users in both contoso.com and fabrikam.com must be prevented from accessing resources in adatum. com. What should you create? A. B. C. D. A one-way external trust from contoso.com to adatum.com A one-way realm trust from adatum.com to contoso.com A one-way realm trust from contoso.com to adatum.com A one-way external trust from adatum.com to contoso.com
Correct Answer: A Section: Reworded Questions Explanation Explanation/Reference: domain names were changed, so understand the question well Explanation: You need to make trust relationship where domain contoso.com trusts adatum.com. http://technet.microsoft.com/en-us/library/cc728024(v=ws.10).aspx
QUESTION 31 Your network contains an Active Directory domain named contoso.com. The domain contains a main office and a branch office. An Active Directory site exists for each office. All domain controllers run Windows Server 2012. The domain contains two domain controllers. The domain controllers are configured as shown in the following table.
DC1 hosts an Active Directory-integrated zone for contoso.com. You add the DNS Server server role to DC2. You discover that the contoso.com DNS zone fails to replicate to DC2. You verify that the domain, schema, and configuration naming contexts replicate from DC1 to DC2. You need to ensure that DC2 replicates the contoso.com zone by using Active Directory replication. Which tool should you use? A. B. C. D. Active Directory Sites and Services Ntdsutil DNS Manager Active Directory Domains and Trusts
Correct Answer: A Section: Reworded Questions Explanation Explanation/Reference: Explanation: If you see question about AD Replication, First preference is AD sites and services, then Repadmin and then DNSLINT. QUESTION 32 Your network contains an Active Directory forest. The forest contains two domains named contoso.com and fabrikam.com. The functional level of the forest is Windows Server 2003. The contoso.com domain contains domain controllers that run either Windows Server 2008 or Windows Server 2008 R2. The functional level of the domain is Windows Server 2008. The fabrikam.com domain contains domain controllers that run either Windows Server 2003 or Windows Server 2008. The functional level of the domain is Windows Server 2003. The contoso.com domain contains a member server named Server1 that runs Windows Server 2012. You install the Active Directory Domain Services server role on Server1. You need to add Server1 as a new domain controller in the contoso.com domain. What should you do? A. B. C. D. Run the Active Directory Domain Services Configuration Wizard. Run adprep.exe /domainprep, and then run dcpromo.exe. Raise the functional level of the forest, and then run dcprorno.exe. Modify the Computer Name/Domain Changes properties.
Correct Answer: A Section: (none) Explanation
Explanation/Reference: Windows Server 2012 requires a Windows Server 2003 forest functional level. That is, before you can add a domain controller that runs Windows Server 2012 to an existing Active Directory forest, the forest functional level must be Windows Server 2003 or higher.
http://blogs.technet.com/b/askpfeplat/archive/2012/09/03/introducing-the-first-windows-server-2012domain-controller.aspx
QUESTION 33 Your network contains an Active Directory forest. The forest contains two domains named contoso.com and fabrikam.com. The forest functional level is Windows 2000. The contoso.com domain contains domain controllers that run either Windows Server 2008 or Windows Server 2008 R2. The domain functional level is Windows Server 2008. The fabrikam.com domain contains domain controllers that run either Windows 2000 Server or Windows Server 2003. The domain functional level is Windows 2000 native. The contoso.com domain contains a member server named Server1 that runs Windows Server 2012. You need to add Server1 as a new domain controller in the contoso.com domain. What should you do first? A. B. C. D. E. Raise the functional level of the contoso.com domain to Windows Server 2008 R2. Upgrade the domain controllers that run Windows Server 2008 to Windows Server 2008 R2. Raise the functional level of the fabrikam.com domain to Windows Server 2003. Decommission the domain controllers that run Windows 2000. Raise the forest functional level to Windows Server 2003.
Correct Answer: D Section: (none) Explanation Explanation/Reference: Explanation:Windows Server 2012 requires a Windows Server 2003 forest functional level. That is, before you can add a domain controller that runs Windows Server 2012 to an existing Active Directory forest, the forest functional level must be Windows Server 2003 or higher.
QUESTION 34 Your network contains an Active Directory domain named adatum.com. The domain contains two domain controllers that run Windows Server 2012. The domain controllers are configured as shown in the following table.
You log on to DC1 by using a user account that is a member of the Domain Admins group, and then you create a new user account named User1. You need to prepopulate the password for User1 on DC2. What should you do first? What should you do first? A. B. C. D. Connect to DC2 from Active Directory Users and Computers. Add DC2 to the Allowed RODC Password Replication Policy group. Add the User1 account to the Allowed RODC Password Replication Policy group. Run Active Directory Users and Computers as a member of the Enterprise Admins group.
Correct Answer: C Section: (none) Explanation Explanation/Reference: http://technet.microsoft.com/en-us/library/cc730883(v=ws.10).aspx http://technet.microsoft.com/en-us/library/cc753470(v=ws.10).aspx#BKMK_pre
QUESTION 35 Your company has offices in Montreal, New York, and Amsterdam. The network contains an Active Directory forest named contoso.com. An Active Directory site exists for each office. All of the sites connect to each other by using the DEFAULTIPSITELINK site link. You need to ensure that only between 20:00 and 08:00, the domain controllers in the Montreal office replicate the Active Directory changes to the domain controllers in the Amsterdam office. The solution must ensure that the domain controllers in the Montreal and the New York offices can replicate the Active Directory changes any time of day. What should you do? A. Create a new site link that contains Montreal and Amsterdam. Remove Amsterdam from DEFAULTIPSITELINK. Modify the schedule of DEFAULTIPSITELINK. B. Create a new site link that contains Montreal and Amsterdam. Create a new site link bridge. Modify the schedule of DEFAU LTIPSITELINK. C. Create a new site link that contains Montreal and Amsterdam. Remove Amsterdam from DEFAULTIPSITELINK. Modify the schedule of the new site link. D. Create a new site link that contains Montreal and Amsterdam. Create a new site link bridge. Modify the schedule of the new site link. Correct Answer: C Section: Reworded Questions Explanation Explanation/Reference: Explanation: Very Smartly reworded with same 3 offices. In the exam correct answer is "Create a new site link that contains Newyork to Montreal. Remove Montreal from DEFAULTIPSITELINK.Modify the schedule of the new site link". QUESTION 36 Your network contains two Active Directory forests named contoso.com and adatum.com. A two- way forest trust exists between the forests. The contoso.com forest contains an enterprise certification authority (CA) named Server1. You implement cross-forest certificate enrollment between the contoso.com forest and the adatum.com forest. On Server1, you create a new certificate template named Template1.
You need to ensure that users in the adatum.com forest can request certificates that are based on Template1. Which tool should you use? A. B. C. D. E. DumpADO.ps1 Repadmin Add-CATemplate Certutil PKISync.ps1
Correct Answer: E Section: (none) Explanation Explanation/Reference: http://technet.microsoft.com/en-us/library/ff955845(v=ws.10).aspx#BKMK_Consolidating
QUESTION 37 You have a server named Server1 that has the Active Directory Certificate Services server role installed. Server1 uses a hardware security module (HSM) to protect the private key of Server1. You need to ensure that the Active Directory Certificate Services (AD CS) database, log files, and private key are backed up. You perform regular backups of the HSM module by using a backup utility provided by the HSM manufacturer. What else should you do?
A. Run the certutil.exe command and specify the -backupkey parameter. B. Run the certutil.exe command and specify the -backupdb parameter.
C. Run the certutil.exe command and specify the -backup parameter. D. Run the certutil.exe command and specify the -dump parameter. Correct Answer: B Section: (none) Explanation Explanation/Reference: http://technet.microsoft.com/en-us/library/cc732443(v=ws.10).aspx#BKMK_backupDB
QUESTION 38 Your network contains an Active Directory domain named contoso.com. All servers run Windows Server 2012. The domain contains a domain controller named DC1 that is configured as an enterprise root certification authority (CA). All users in the domain are issued a smart card and are required to log on to their domain-joined client computer by using their smart card. A user named User1 resigned and started to work for a competing company. You need to prevent User1 immediately from logging on to any computer in the domain. The solution must not prevent other users from logging on to the domain. Which tool should you use? A. B. C. D. Active Directory Sites and Services Active Directory Administrative Center Server Manager Certificate Templates
Correct Answer: B Section: (none) Explanation Explanation/Reference: Explanation: QUESTION 39 Your company has a main office and a branch office. The main office contains a file server named Server1. Server1 has the BranchCache for Network Files role service installed. The branch office contains a server named Server2. Server2 is configured as a BranchCache hosted cache server. You need to preload the data from the file shares on Server1 to the cache on Server2. You generate hashes for the file shares on Server1. Which cmdlet should you run next? A. B. C. D. Add-BCDataCacheExtension Set-BCCache Publish-BCFileContent Export-BCCachePackage
Correct Answer: D
Section: (none) Explanation Explanation/Reference: http://technet.microsoft.com/fr-fr/library/jj572970.aspx
QUESTION 40 You have a file server named Server1 that runs Windows Server 2012. Data Deduplication is enabled on drive D of Server1. You need to exclude D:\Folder1 from Data Deduplication. What should you configure? A. B. C. D. Disk Management in Computer Management File and Storage Services in Server Manager the classification rules in File Server Resource Manager (FSRM) the properties of D:\Folder1
Correct Answer: B Section: (none) Explanation Explanation/Reference: http://technet.microsoft.com/en-us/library/hh831434.aspx
QUESTION 41 Your network contains an Active Directory domain named contoso.com. The network contains a file server named Server1 that runs Windows Server 2012. You create a folder named Folder1. You share Folder1 as Share1. The NTFS permissions on Folder1 are shown in the Folder1 exhibit. (Click the Exhibit button.)
The Everyone group has the Full control Share permission to Folder1. You configure a central access policy as shown in the Central Access Policy exhibit. (Click the Exhibit button.)
Members of the IT group report that they cannot modify the files in Folder1. You need to ensure that the IT group members can modify the files in Folder1. The solution must use central access policies to control the permissions. Which two actions should you perform? (Each correct answer presents part of the solution. Choose two.) A. On the Classification tab of Folder1, set the classification to Information Technology. B. On the Security tab of Folder1, add a conditional expression to the existing permission entry for the IT group. C. On Share 1, assign the Change Share permission to the IT group. D. On the Security tab of Folder1, remove the permission entry for the IT group. E. On the Security tab of Folder1, assign the Modify permission to the Authenticated Users group.
Correct Answer: AE Section: (none) Explanation Explanation/Reference: Explanation: Central access policies for files enable organizations to centrally deploy and manage authorization policies that include conditional expressions that use user groups, user claims, device claims, and resource properties. (Claims are assertions about the attributes of the object with which they are associated). For example, to access high-business-impact (HBI) data, a user must be a full-time employee, obtain access from a managed device, and log on with a smart card. These policies are defined and hosted in Active Directory Domain Services (AD DS). http://technet.microsoft.com/en-us/library/hh846167.aspx
QUESTION 42 Your network contains an Active Directory domain named contoso.com. You are creating a custom Windows Recovery Environment (Windows RE) image. You need to ensure that when a server starts from the custom Windows RE image, a drive is mapped automatically to a network share. What should you modify in the image? A. B. C. D. startnet.cmd Xsl-mApp1ngs.xml Win.ini smb.types.ps1xml
Correct Answer: A Section: (none) Explanation Explanation/Reference: Explanation: The best way to define what to start is using starnet.cmd http://technet.microsoft.com/en-us/library/cc766521(v=ws.10).aspx
QUESTION 43 You have a server named Server1 that runs Windows Server 2012. Server1 has the Windows Deployment Services server role installed. You back up Server1 each day by using Windows Server Backup. The disk array on Server1 fails. You replace the disk array. You need to restore Server1 as quickly as possible. What should you do? A. B. C. D. Start Server1 from the Windows Server 2012 installation media. Start Server1and press F8. Start Server1 and press Shift+F8. Start Server1 by using the PXE.
Correct Answer: A Section: (none) Explanation Explanation/Reference: Explanation: http://www.windowsnetworking.com/articles_tutorials/Restoring-Windows-Server-Bare-Metal. html QUESTION 44 You have a server named Server1 that runs Windows Server 2012. You download and install the Microsoft Online Backup Service Agent on Server1. You need to ensure that you can configure an online backup from Windows Server Backup. What should you do first? A. B. C. D. From a command prompt, run wbadmin.exe enable backup. From Windows Server Backup, run the Register Server Wizard. From the Services console, modify the Log On settings of the Microsoft Online Backup Service Agent. From Computer Management, add the Server1 computer account to the Backup Operators group.
Correct Answer: B Section: (none) Explanation Explanation/Reference: QUESTION 45
Your network contains an Active Directory domain named contoso.com. The domain contains two servers named Server1 and Server2. Both servers have the Hyper-V server role installed. You plan to replicate virtual machines between Server1 and Server2. The replication will be encrypted by using Secure Sockets Layer (SSL). You need to request a certificate on Server1 to ensure that the virtual machine replication is encrypted. Which two intended purposes should the certificate for Server1 contain? (Each correct answer presents part of the solution. Choose two.) A. B. C. D. E. Server Authentication KDC Authentication Kernel Mode Code Signing IP Security end system Client Authentication
Correct Answer: AE Section: (none) Explanation Explanation/Reference: http://blogs.technet.com/b/virtualization/archive/2012/03/13/hyper-v-replica-certificate-requirements.aspx
QUESTION 46 Your network contains an Active Directory domain named contoso.com. The domain contains two member servers named Server1 and Server2 that run Windows Server 2012. Both servers have the Hyper-V server role installed. The network contains an enterprise certification authority (CA). All servers are enrolled automatically for a certificate-based on the Computer certificate template. On Server1, you have a virtual machine named VM1. VM1 is replicated to Server2. You need to encrypt the replication of VM1. Which two actions should you perform? (Each correct answer presents part of the solution. Choose two.) A. B. C. D. E. F. On Server1, modify the settings of VM1. On Server2, modify the settings of the virtual switch to which VM1 is connected. On Server1, modify the Hyper-V Settings. On Server1, modify the settings of the virtual switch to which VM1 is connected, On Server2, modify the settings of VM1. On Server2, modify the Hyper-V Settings.
Correct Answer: AF Section: (none) Explanation Explanation/Reference: Once you change the Hyper-V Settings of Server 2 to encrypt replications with a certificate, you then need to change the replication information of VM1 to use the secure connection.
QUESTION 47 Your network contains an Active Directory domain named contoso.com. The domain contains a file server named Server1 that runs Windows Server 2012. You create a user account named User1 in the domain. You need to ensure that User1 can use Windows Server Backup to back up Server1. The solution must minimize the number of administrative rights assigned to User1. What should you do? A. B. C. D. Assign User1 the Back up files and directories user right. Add User1 to the Backup Operators group. Add User1 to the Power Users group. Assign User1 the Back up files and directories user right and the Restore files and directories user right.
Correct Answer: A Section: (none) Explanation Explanation/Reference: Backup Operators have these permissions by default:
However the question explicitly says we need to minimize administrative rights. Since the requirement is for backing up the data only--no requirement to restore or shutdown--then assigning the "Back up files and directories user right" would be the correct. answer.
QUESTION 48 You have a datacenter that contains six servers. Each server has the Hyper-V server role installed and runs Windows Server 2012. The servers are configured as shown in the following table.
Host4 and Hosts5 are part of a cluster named Cluster1. Cluster1 hosts a virtual machine named VM1. You
need to move VM1 to another Hyper-V host. The solution must minimize the downtime of VM1. To which server and by which method should you move VM1 A. B. C. D. To Host3 by using a storage migration To Host6 by using a storage migration To Host2 by using a live migration To Host1 by using a quick migration
Correct Answer: A Section: Reworded Questions Explanation Explanation/Reference: slightly changed with more answer options but correct answer is still "Intel iSCSI disk" http://technet.microsoft.com/en-us/library/hh831656.aspx QUESTION 49 Your network contains an Active Directory domain named contoso.com. The domain contains two member servers named Server1 and Server2. All servers run Windows Server 2012. Server1 and Server2 have the Failover Clustering feature installed. The servers are configured as nodes in a failover cluster named Cluster1. You add two additional nodes to Cluster1. You need to ensure that Cluster1 stops running if three nodes fail. What should you configure? A. B. C. D. E. F. G. H. I. J. K. L. Affinity - None Affinity - Single The cluster quorum settings The failover settings A file server for general use The Handling priority The host priority Live migration The possible owner The preferred owner Quick migration The Scale-Out File Server
Correct Answer: C Section: (none) Explanation Explanation/Reference: http://technet.microsoft.com/en-us/library/cc731739.aspx
QUESTION 50 Your network contains an Active Directory domain named contoso.com. The domain contains two member servers named Server1 and Server2. All servers run Windows Server 2012. Server1 and Server2 have the Failover Clustering feature installed. The servers are configured as nodes in a failover cluster named Cluster1. You add two additional nodes in Cluster1. You have a folder named Folder1 on Server1 that hosts application data. Folder1 is a folder target in a Distributed File System (DFS) namespace. You need to provide highly available access to Folder1. The solution must support DFS Replication to Folder1. What should you configure? A. Affinity - None
B. C. D. E. F. G. H. I. J. K. L.
Affinity - Single The cluster quorum settings The failover settings A file server for general use The Handling priority The host priority Live migration The possible owner The preferred owner Quick migration The Scale-Out File Server
Correct Answer: E Section: (none) Explanation Explanation/Reference: http://technet.microsoft.com/en-us/library/hh831349.aspx
Exam C QUESTION 1 Your network contains an Active Directory domain named contoso.com. The domain contains two member servers named Server1 and Server2. All servers run Windows Server 2012. Server1 and Server2 have the Failover Clustering feature installed. The servers are configured as nodes in a failover cluster named Cluster1. You configure File Services and DHCP as clustered resources for Cluster1. Server1 is the active node for both clustered resources. You need to ensure that if two consecutive heartbeat messages are missed between Server1 and Server2, Server2 will begin responding to DHCP requests. The solution must ensure that Server1 remains the active node for the File Services clustered resource for up to five missed heartbeat messages. What should you configure? A. B. C. D. E. F. G. H. I. J. K. L. Affinity - None Affinity - Single The cluster quorum settings The failover settings A file server for general use The Handling priority The host priority Live migration The possible owner The preferred owner Quick migration The Scale-Out File Server
Correct Answer: D Section: (none) Explanation Explanation/Reference: http://technet.microsoft.com/en-us/library/dd197562(v=ws.10).aspx http://blogs.msdn.com/b/clustering/archive/2012/11/21/10370765.aspx QUESTION 2 you are employee as a network administrator at abc.com. ABC.com has an active directory domain named ABC.com All servers on the abc.com network have windows server 2012 installed and all workstations have windows 8 enterprise installed. abc.com has established a remote Active directory site that only host workstations.The Computer accounts for these workstations have been placed in an organizational unit (OU),named ABCADRemote,which has a group policy object(GPO) associated with it. You are in the process of configuration Branchcahce for the remote Active directory site. You have Already turned Branchcache on. Which of the following actions should you take next_? A. B. C. D. You Should consider having the set Branchcache HostedServer Cache mode setting configured You Should consider having the set Branchcache Hostedclient Cache mode settting configured You Should consider having the set Branchcache distributed cache mode setting configured You should consider having the set BranchCache disabled cache mode settings configured
Correct Answer: C Section: (none) Explanation Explanation/Reference: QUESTION 3 You are employed as a network administrator at ABC.com ABC.com has an active directory domain named ABC.com ALL servers on the ABC.com network have windows server 2012.
ABC.com has a server,named server 1,which runs the windows deployment services server role.You make use of windows server backup to back up server 1. Subsequent to a disk array on server 1 becoming corrupt,you swap the disk array with new hardware. You now need to recover server1 in the shortest time conceivable. which of the following actions should you take? A. B. C. D. you should consider making use of the windows server 2012 installation media to start server1 you should consider restoring server1 from a snapshot backup you should consider restoring server 1 from an incremental backup you should consider restoring server 1 from a differential backup
Correct Answer: A Section: (none) Explanation Explanation/Reference: QUESTION 4 You are employed as a senior network administrator at ABC.com. ABC.com has an active directory domain named ABC.com. all servers on the abc.com network windows server2012 installed. You are currently running a training exercise for junior network administrators.You are discussing the PKISync.ps1 tool. which of the following is true with regards to The PKISync.ps1? A. it adds a certificate template to the CA B. it asssists administrators in diagnosing replication problems between windows domain controllers C. it is used to display information about the digital certificates that are installed on a directAccess client, DirectAcces server,or intranet resource D. it copies objects in the source forest to the target forest. Correct Answer: D Section: (none) Explanation Explanation/Reference:
QUESTION 5 You are employed as a network administrator ABC.com ABC.com has an active directory domain named ABC.com.all servers on the ABC.com network have windows server 2012 installed. ABC.com has a server named server1 which is configured as a DHCP server You have created a superscope on server1 . which of the following describes reason for creating a superscope?(choose all that apply.)
A. To support DHCP clients on a single physical network segment where multiple logical ip networks are used. B. To allow for the sending of network traffic to a group of endpoints destination hosts. C. To support remote DHCP clients located on the far side of DHCP and BOOTP relay agents. D. To provide fault tolerance Correct Answer: AC Section: (none) Explanation Explanation/Reference: http://technet.microsoft.com/en-us/library/cc757614(v=ws.10).aspx
QUESTION 6 You are employed as a network administrator at ABC.com ABC.com has an active directory domain named ABC.com all servers including domain controllers on the ABC.com network have windows server 2012 installed. ABC.com has its headquarters in London and an office in paris. The London Office has a domain controller named server1,which is configured as a writeable domain controller that servers as a Global catalog server and a DNS server. Server1 is configured to host an Active Directory-integrated zone for ABC.com The Paris office has a Read-Only domain controller (RODC) named server2 which servers as a Global catalog server. After installing the DNS server role on server2,you want to make sure that the ABC.com zone is replicated to server2 via active directory replication. Which of the following actions should you take? A. B. C. D. You should consider making use of Active Directory Sites and Services to Configured replication You should consider making use of replmon.exe to configure replication. You should consider making use of repadmin.exe to configure replication You should consider making use of Active Directory Schema To configure replication
Correct Answer: A Section: Reworded Questions Explanation Explanation/Reference: If you see question about AD Replication, First preference is AD sites and services, then Repadmin and then DNSLINT. QUESTION 7 You are employed as a network administrator at ABC.com. ABC.com has an Active Directory domain named. Abc.com all servers on the ABC.com network have windows server 2012. You are running a training exercise for junior network administrators.You are currently discussing DHCP failover architecture.You have informed the trainees that DHCP servers can be deployed as fail over partners in either hot standby mode or load sharing mode. Which of the following is TRUE with regards to hot standby mode? (Choose all that apply) A. It is when two servers function in a fail over relationship where an active server is responsible for leasing IP address and configuration data to all clients in a scope or subnet B. It when two servers in a fail over relationship server IP addresses and options to clients on a given
subnet at the same time C. It is best suited to deployments where a data center server acts as a standby backup server to a server at a remote site D. It is best suited deployments where both servers in a fail over relationship are located at the same physical site Correct Answer: AC Section: (none) Explanation Explanation/Reference: http://blogs.technet.com/b/teamdhcp/archive/2012/09/03/dhcp-failover-hot-standby-mode.aspx
QUESTION 8 You are emloyed as a network administrator at ABC.com Abc.com has an Active directory domain named ABC.com all servers on the ABC.com network have windows server 2012. The ABC.com domain has two Active Directory sites configured. You want to make use of change notification configure replication between these Active Directory Sites.You have opened DEFAULTIPSITELINK Properties to configure the necessary attribute. Which of the following is the attribute that needs to be configured? A. B. C. D. The revisiobn attribute The Options attribute The schedule attribute The proxyAddresses attribute
Correct Answer: B Section: (none) Explanation Explanation/Reference: QUESTION 9 You are employed as a network administrator at ABC.com ABC.com has an Active Directory domain named ABC.com all servers on the ABC.com network have Windows server 2012 installed. ABC.com has a server named SERVER1 which has been configured to run the HYPER-V server role Server1 is configures to host multiple vitrual mahines.When ABC.com acquires a server with a better hardware configuration to SERVER1 you are instructed to relocate the vitrual machines to the new server with as little interruptions as possible. Which of the following actions should you take ? (Choose all that apply.) A. You should consider exporting the vitrual machines from Server1. B. You should consider running a snapshot backup of the SERVER1.
C. You should consider importing the vitrual machine from Server1 to the new server. D. You shoul consider restoring the snapshot backup on the hard drives of the new server. Correct Answer: AC Section: (none) Explanation Explanation/Reference: QUESTION 10 You are employed as a network administrator at consoto.com. Contoso.com has in an Active Directory domain named contoso.com. All Servers on the contoso.com network have windows server 2012 installed. A contoso.com server ,named Server1,hosts the Active Directory Certificate Services Server role and utilizes a hardware security module(HSM) to safeguard its private key. You have beed instructed to backup the Active Directory Certificate Services (ADCS) database,log files,and private key regularly.You should not use a utility supplied by the hardware security module (HSM) creator. Which of the following actions should you take? A. B. C. D. You should consider scheduling an incremental backup You Should consider making use of the certutil.exe command. You should consider schedulling a differential backup You should consider schedulling a copy backup
Correct Answer: B Section: (none) Explanation Explanation/Reference: http://blogs.technet.com/b/pki/archive/2010/04/20/disaster-recovery-procedures-for-the-active-directorycertificate-services-adcs.aspx
QUESTION 11 You are employed as a senior network administrator at contoso.com contoso.com has an active directory domain named contoso.com. All servers on the contoso.com network have windows server 2012 installed. You are currently running at training exercise for junior network administrators.You are discussing the DNSSEC NRPT rule properly. Which of the following describes the purpose of this rule property?
A. It is used to indicate the namespace to which the policy applies. B. It is used to indicate whether the DNS client should check for DNSSEC validation in the response. C. It is used to indicate DNSSEC must be used to protect DNS traffic for queries belonging to the namespace. D. It is used to whether DNS connections over DNSSEC will use encryption Correct Answer: B Section: (none) Explanation Explanation/Reference: http://technet.microsoft.com/fr-fr/library/ee649182(v=ws.10).aspx In a DNSSEC deployment, validation of DNS queries by client computers is enabled through configuration of the following: IP security (IPsec). IPsec connection security rules are used to authenticate communications between DNS servers and client computers. For more information about configuring connection security rules, see Deploy IPsec Policy to DNS Servers and Deploy IPsec Policy to Client Computers. Name Resolution Policy Table (NRPT). The NRPT is a new feature available in Windows Server 2008 R2 and Windows 7 that contains policies and settings used by DNS clients when issuing DNS queries and receiving DNS responses. The NRPT enables a client to issue queries indicating the knowledge of DNSSEC and to check for validation in the response. QUESTION 12 You are employed as a network administrator at contoso.com . Contoso.com has an active directory domain named contoso.com All servers on the contoso.com network have windows server 2012 installed. Contoso.com has a server named server1,which is configured as a file server. You have been instructed to enabled a feature that discovers and eradicates duplication within data without compromising its reliability or accuracy. Which of the following actions should you take? A. B. C. D. You should consider having the Data Deduplication feature enabled. You should consider having the Storage Spaces feature enabled. You should consider having the Storage Management feature enabled. You should consider having the folder redirection feature enabled.
Correct Answer: A Section: (none) Explanation Explanation/Reference: http://blogs.technet.com/b/filecab/archive/2012/05/21/introduction-to-data-deduplication-in-windows-server2012.aspx
QUESTION 13 You are employed as a network administrator at contoso.com. contoso.com has a single Active Directory domain named contoso.com.All servers on the Contoso.com network have Windows server 2012 installed. Contoso.com has two servers,named server1 and server2 which are configured in a two-node fail over cluster. You are currently configuration the quorum settings for the cluster. You want to make use of a quorum mode that allows each node to vote if it is available and in communication. Which of the following is the mode you should use? A. B. C. D. Node Majority Node and Disk Majority Node and File Share Majority No Majority:Disk Only
Correct Answer: A Section: (none) Explanation Explanation/Reference: http://technet.microsoft.com/en-us/library/cc770620(v=ws.10).aspx
QUESTION 14 You are employed as a network administrator at contoso.com. Contoso.com has a single Active Directory domain named contoso.com. All servers on the contoso.com network have windows server 2012 installed. You are preparing to install a third-party application on a contoso.com server,named SERVER1. You find that the application is unable to install completely due to its driver not being digitally signed. You want to make sure that the application can be installed succesfully. Which of the following actions should you take_? A. You should consider downloading a signed driver B. You should consider having SERVER1 is restored to an earlier date C. You should consider making use of the Disable Driver Signature Enforcement option from the Advanced Boot Option.
D. You should consider restarting SERVER1 in safe Mode Correct Answer: C Section: (none) Explanation Explanation/Reference: QUESTION 15 You are employed as a senior network administrator at contoso.com.Contoso.com has a single Active Directory Domain named contoso.com.All servers on the contoso.com network have windows server 2012 installed. You are running a training exercise for junior network administrator.You are currently discussing the Dnslint. exe tool. Which of the following should this tool be used for ? (Choose all that apply)
A. B. C. D. E. F.
To help diagnose common DNS name resolution issues For developing scripts for configuring a DNS server To administer the DNS server Service. To look for specific DNS record set and sure that they are consistent across multiple DNS servers. To verify that DNS records used specifially for Active Directory replication are correct To Create and delete zones and resource records.
Correct Answer: ADE Section: (none) Explanation Explanation/Reference: http://support.microsoft.com/kb/321045
QUESTION 16 You work as an administrator at contoso.com. Contoso.com network consists of a single domain named contoso.com. All servers on the contoso.com network have Windows server 2012 installed. Contoso.com has a server,named SERVER1,which has the AD DS,DHCP and DNS server roles installed. Contoso.com also has a server named SERVER2,which has the DHCP and Remote Access Server Role installed.You have configured a server,which has the File and Storage Services Server role installed.to automatically acquire an IP address.The server is named Server3 You then create a filter on SERVER1 Which of the following is a reason for this configuration? A. B. C. D. To make sure that SERVER1 issues Server3 an IP address. To make sure that SERVER1 does not issue SERVER3 an IP address To make sure that SERVER3 acquires a constant IP address from SERVER2 only. To make sure that SERVER3 is configured with a static IP address
Correct Answer: B Section: (none) Explanation Explanation/Reference: QUESTION 17 You are employed as a network administrator at ABC.com. ABC.com has an Active Directory domain named ABC.com. All servers on the ABC.com network have Windows server 2012 installed.
You have been instructed to configure a custom Windows Recovery Environmen(Windows RE) image that should allow for a drive is mapped automatically to a network share in the event that a server is started using the image Which of the following actions should you take? A. B. C. D. You should consider configuring the startnet.cmd in the image You should consider configuring the startup.exe command included in the image. You should consider configuring the ntdsutil command included in the image You should consider configuring the certutil.exe command included in the image
Correct Answer: A Section: (none) Explanation Explanation/Reference: QUESTION 18 You are employed as a senior network administrator at ABC.com . ABC.com has an Active Directory domain named ABC.com. All servers on the ABC.com network have windows server 2012 installed You are currently running a training exercise for junior network administrators.You are discussing the endpoint types supported by Active Directory Federation Services(AD FS) Which of the following are supported types?(Choose three) A. B. C. D. E. SAML WebSSO Anonymous WS-Federation Passive Client Certicate WS-Trust
Correct Answer: ACE Section: (none) Explanation Explanation/Reference: http://technet.microsoft.com/en-us/library/adfs2-help-endpoints(v=ws.10).aspx
QUESTION 19 You are employed as a senior network administrator at ABC.com . ABC.com has an Active Directory domain named ABC.com. All servers on the ABC.com network have windows server 2012 installed The ABC.com domain has an Active Directory site configured in London,and an Active Directory site in New york. You have been instructed to make sure that the synchronization of account lockout data happens quicker. A. B. C. D. You should consider editing the options attribute from WANLINK properties You should consider editing the options attribute from LANLIK properties You should consider editing the options attribute from the DEFAULTSITELINK properties You should consider editing the proxyAddressess attribute from the DEFAULTIPSITELINK properties.
Correct Answer: C Section: (none) Explanation Explanation/Reference:
QUESTION 20 You are employed as a senior network administrator at ABC.com . ABC.com has an Active Directory domain named ABC.com. All servers on the ABC.com network have windows server 2012 installed.
ABC.com has two servers,named SERVER1 and SERVER2 which are configured in a two-node failover cluster.Server1 includes a folder,named ABCAppData,which is configured as a Distributed File System (DFS) name space folder target. After configuring another two nodes in the failover cluster, you are instructed to make sure that access to ABCAppData is highly available. You also have to make sure that application data is replicated to ABCAppData via DFS replication. Which following actions should you take ? A. B. C. D. You should consider configuring a scale-out File Server You should consider configuring the replication settings for the cluster You should consider configuring a file server for general use You should consider configuring the Quorum settings
Correct Answer: C Section: (none) Explanation Explanation/Reference: http://technet.microsoft.com/en-us/library/hh831349.aspx
QUESTION 21 Your network contains an Active Directory domain named contoso.com. The domain contains two member servers named Server1 and Server2. All servers run Windows Server 2012. Server1 and Server2 have the Network Load Balancing (NLB) feature installed. The servers are configured as nodes in an NLB cluster named Cluster1. Port rules are configured for all clustered applications. You need to ensure that Server2 handles all client requests to the cluster that are NOT covered by a port rule. What should you configure?
A. B. C. D. E. F. G. H. I. J. K. L.
Affinity-None Affinity-Single The cluster quorum settings The failover settings A file server for general use The Handling priority The host priority Live migration The possible owner The preferred owner Quick migration The Scale-Out File Server
Correct Answer: G Section: (none)
Explanation Explanation/Reference:
QUESTION 22 Your network contains an Active Directory domain named contoso.com. A previous administrator implemented a Proof of Concept installation of Active Directory Rights Management Services (AD RMS). After the proof of concept was complete, the Active Directory Rights Management Services server role was removed. You attempt to deploy AD RMS. During the configuration of AD RMS, you receive an error message indicating that an existing AD RMS Service Connection Point (SCP) was found. You need to remove the existing AD RMS SCP. Which two tools should you use? A. B. C. D. E. F. G. H. ADSI Edit Active Directory Users and Computers Active Directory Domains and Trusts Active Directory Sites and Services Services Authorization Manager TPM Management Certification Authority
Correct Answer: AD Section: (none) Explanation Explanation/Reference:
QUESTION 23 Your network contains an Active Directory domain named contoso.com. The domain contains a main office and a branch office. An Active Directory site exists for each office. All domain controllers run Windows Server 2012. The domain contains two domain controllers. DC1 hosts an Active Directory- integrated zone for contoso.com. You add the DNS Server server role to DC2. You discover that the contoso.com DNS zone fails to replicate to DC2. You verify that the domain, schema, and configuration naming contexts replicate from DC1 to DC2. You need to ensure that DC2 replicates the contoso.com zone by using Active Directory replication. Which tool should you use? A. B. C. D. E. Dnscmd Dnslint Repadmin Ntdsutil DNS Manager
F. Active Directory Sites and Services G. Active Directory Domains and Trusts H. Active Directory Users and Computers Correct Answer: C Section: Reworded Questions Explanation Explanation/Reference: If you see question about AD Replication, First preference is AD sites and services, then Repadmin and then DNSLINT. http://technet.microsoft.com/en-us/library/cc739941(v=ws.10).aspx
QUESTION 24 Your network contains an Active Directory domain named contoso.com. All servers run Windows Server 2012. The domain contains a domain controller named DC1 that is configured as an enterprise root certification authority (CA). All users in the domain are issued a smart card and are required to log on to their domain-joined client computer by using their smart card. A user named User1 resigned and started to work for a competing company. You need to prevent User1 immediately from logging on to any computer in the domain. The solution must not prevent other users from logging on to the domain. Which two tools should you use? A. B. C. D. E. F. G. H. Active Directory Administrative Center Active Directory Sites and Services Active Directory Users and Computers the Certification Authority console the Certificates snap-in Certificate Templates Server Manager the Security Configuration Wizard
Correct Answer: AC Section: (none) Explanation
Explanation/Reference: QUESTION 25 Your network contains two Active Directory forests named contoso.com and adatum.com. Both forests contain multiple domains. All domain controllers run Windows Server 2012. Contoso.com has a one-way forest trust to adatum.com. A domain named paris.eu.contoso.com hosts several legacy applications that use NTLM authentication. Users in a domain named london.europe.adatum.com report that it takes a long time to be authenticated when they attempt to access the legacy applications hosted in paris.eu.contoso. com. You need to reduce how long it takes for the london.europe.adatum.com users to be authenticated in paris. eu.contoso.com. What should you do? A. B. C. D. Create a shortcut trust. Create an external trust between the forest root domains. Disable SID filtering on the existing trust. Create an external trust.
Correct Answer: A Section: (none) Explanation Explanation/Reference: http://technet.microsoft.com/en-us/library/cc737939(v=ws.10).aspx
QUESTION 26 Your network contains an Active Directory domain named contoso.com. All servers run Windows Server
2012. You are creating a central access rule named TestFinance that will be used to audit members of the Authenticated Users group for access failure to shared folders in the finance department. You need to ensure that access requests are unaffected when the rule is published. What should you do? A. B. C. D. Add a User condition to the current permissions entry for the Authenticated Users principal. Set the Permissions to Use the following permissions as proposed permissions. Add a Resource condition to the current permissions entry for the Authenticated Users principal. Set the Permissions to Use following permissions as current permissions.
Correct Answer: B Section: (none) Explanation Explanation/Reference: http://technet.microsoft.com/en-us/library/jj134043.aspx
QUESTION 27 You have a server named Server1 that runs Windows Server 2012. Windows Server 2012 is installed on volume C. You need to ensure that Safe Mode with Command Prompt loads the next time Server1 restarts. Which tool should you use? A. B. C. D. The Restart-Server cmdlet The Bootcfg command The Restart-Computer cmdlet The Bcdedit command
Correct Answer: D Section: (none) Explanation Explanation/Reference:
You can see with msconfig tool that boot options have changed as follows :
After reboot you should remove the safeboot option using bcdedit: - bcdedit /deletevalue safeboot
QUESTION 28 You have a server named Server1 that runs a Server Core Installation of Windows Server 2012. Shadows copies are enabled on all volumes. You need to delete a specific shadow copy. The solution must minimize server downtime. Which tool should you use? A. B. C. D. Vssadmin Diskpart Wbadmin Shadow
Correct Answer: A Section: (none) Explanation Explanation/Reference: http://technet.microsoft.com/en-us/library/cc788026(v=ws.10).aspx
QUESTION 29 Your network contains two Web servers named Server1 and Server2. Server1 and Server2 are nodes in a Network Load Balancing (NLB) cluster. You configure the nodes to use the port rule shown in the exhibit. (Click the Exhibit button.) You need to configure the NLB cluster to meet the following requirements: HTTPS connections must be directed to Server1 if Server1 is available.HTTP connections must be load balanced between the two nodes. Which three actions should you perform? (Each correct answer presents part of the solution. Choose three.) Exhibit:
A. B. C. D. E. F.
From the host properties of Server1, set the Handling priority of the existing port rule to 2. From the host properties of Server1, set the Handling priority of the existing port rule to 1. From the host properties of Server2, set the Priority (Unique host ID) value to 1. Create a port rule for TCP port 80. Set the Filtering mode to Multiple host and set the Affinity to None. From the host properties of Server2, set the Handling priority of the existing port rule to 2. Create an additional port rule for TCP port 443. Set the Filtering mode to Multiple host and set the Affinity to Single.
Correct Answer: BDE Section: (none) Explanation Explanation/Reference: http://technet.microsoft.com/en-us/library/cc778263(v=ws.10).aspx
QUESTION 30 Your network contains two Active Directory forests named contoso.com and litwareinc.com. A two- way forest trusts exists between the forest. Selective authentication is enabled on the trust. The contoso.com forest contains a server named Server1. You need to ensure that users in litwareinc.com can access resources on Server1. What should you do? A. B. C. D. Install Active Directory Rights Management Services on a domain controller in contoso.com. Modify the permission on the Server1 computer account. Install Active Directory Rights Management Services on a domain controller in litwareinc.com. Configure SID filtering on the trust.
Correct Answer: B Section: (none) Explanation Explanation/Reference: http://technet.microsoft.com/en-us/library/cc772808(v=ws.10).aspx
QUESTION 31
Your network contains an Active Directory domain named contoso.com. The domain contains a domain controller named DC1 that runs Windows Server 2012. DC1 has the DHCP Server server role installed. DHCP is configured as shown in the exhibit. (Click the Exhibit button.) You discover that client computers cannot obtain IPv4 addresses from DC1. You need to ensure that the client computers can obtain IPv4 addresses from DC1. What should you do? Exhibit:
A. B. C. D.
Activate the scope. Authorize DC1. Disable the Allow filters. Disable the Deny filters.
Correct Answer: C Section: (none) Explanation Explanation/Reference: There is no items in the deny List. So it means that client computers MAC addresses is not listed in the allow list. So we have to disable the "Allow Filters"
QUESTION 32
Your network contains an Active Directory domain named contoso.com. The domain contains a server named Server1 that runs Windows Server 2012 and has the DHCP Server server role installed. You need to create an IPv6 scope on Server1. The scope must use an address space that is reserved for private networks. The addresses must be routable. Which IPV6 scope prefix should you use? A. B. C. D. FF00:: 2001:: FD00:123:4567:: FE80::
Correct Answer: C Section: (none) Explanation Explanation/Reference: Explanation: http://www.ipuptime.net/Multicast.aspx http://technet.microsoft.com/en-us/library/gg144561(v=exchg.141).aspx http://en.wikipedia.org/wiki/Unique_local_address QUESTION 33 Your network contains an Active Directory forest named contoso.com. The forest contains a single domain. The domain contains three domain controllers. The domain controllers are configured as shown in the following table.
You discover that when you run Group Policy Results from Group Policy Management, the settings from site-linked Group Policy objects (GPOs) fail to appear in the results. You need to ensure that the settings from site-linked GPOs appear in the results. What should you do first? A. B. C. D. Run adprep on DC3 by using Windows Server 2012 installation media. Transfer the infrastructure master role to DC3. Upgrade DC2 to Windows Server 2012. Run adprep on DC1 by using Windows Server 2003 installation media.
Correct Answer: A Section: (none) Explanation Explanation/Reference: Explanation: In this scenario a Windows 2012 server has been added to a Windows 2003 network. Note: * Before adding your new Windows 2012 Domain Controller, or attempting to perform an in-place upgrade of an existing Windows 2008 or 2008 R2 DC, you must make sure that the Schema is upgraded to support your new Windows 2012 DC, and that you prepare each domain where you plan to install Windows 2012 DCs. To do this we can use the ADPREP.exe tool found in the support\adprep folder on your installation media.
* Starting with Windows 2012 there is only one version of ADPREP available, and that is a 64-bit version. * Adprep is the utility--included in the OS installation media--that performs several crucial functions to upgrade AD to support that OS. The utility has three major options: /forestprep, /domainprep, and / rodcprep. The /forestprep option runs first, extending the AD schema with new object and attribute classes that the new AD version needs. The /domainprep option creates new well-known objects in AD, applies security changes, and miscellaneous other bits. Finally, /rodcprep makes forest-wide security changes to allow read-only domain controller (RODC) functionality. The Windows Server 2012 version of adprep.exe can run on any server that runs a 64-bit version of Windows Server 2008 or later. Reference: How to add a Windows Server 2012 domain controller to an existing Windows 2008 domain QUESTION 34 Your network contains an Active Directory domain named contoso.com. The domain contains a server named Server1 that runs Windows Server 2012 and has the DNS Server server role installed. Server1 is configured to use a DNS server from an Internet Service Provider (ISP) as a forwarder. Corporate management requires that client computers only resolve names of contoso.com computers. You need to configure Server1 to resolve names in the contoso.com zone only. What should you do on Server1? A. B. C. D. From DNS Manager, modify the root hints of Server1. From Windows PowerShell, run the Remove-DnsServerForwarder cmdlet. From Windows PowerShell, run the Set-NetDnsTransitionConfiguration cmdlet. From DNS Manager, modify the Advanced properties of Server1.
Correct Answer: A Section: (none) Explanation Explanation/Reference: Explanation: If the DNS server does not know the address of the requested site, then it will forward the request to another DNS server. In order to do so, the DNS server must know of the IP address of another DNS server that it can forward the request to. This is the job of root hints. Root hints provides a list of IP addresses of DNS servers that are considered to be authoritative at the root level of the DNS hierarchy(also known as root name server). QUESTION 35 You have a server named Server1 that runs Windows Server 2012. Each day, Server1 is backed up fully to an external disk. On Server1, the disk that contains the operating system fails. You replace the failed disk. You need to perform a bare-metal recovery of Server1 by using the Windows Recovery Environment (Windows RE). What should you use? A. B. C. D. The Wbadmin.exe command The Repair-bde.exe command The Get-WBBareMetalRecovery cmdlet The Start-WBVolumeRecovery cmdlet
Correct Answer: A Section: (none) Explanation Explanation/Reference:
Explanation:
http://technet.microsoft.com/en-us/library/cc754015(v=WS.10).aspx http://technet.microsoft.com/en-us/library/cc770593(v=WS.10). aspx#BKMK_Windows_Recovery_Environment_overview http://technet.microsoft.com/en-us/library/ff829851(v=WS.10).aspx http://technet.microsoft.com/en-us/library/ee706651.aspx http://technet.microsoft.com/en-us/library/jj902470(v=wps.620).aspx QUESTION 36 You have a file server named Server1 that runs a Server Core Installation of Windows Server 2012. Server1 has a volume named D that contains user data. Server1 has a volume named E that is empty. Server1 is configured to create a shadow copy of volume D every hour. You need to configure the shadow copies of volume D to be stored on volume E. What should you run? A. B. C. D. The Set-Volume cmdlet with the -driveletter parameter The Set-Volume cmdlet with the -path parameter The vssadmin.exe add shadowstorage command The vssadmin.exe create shadow command
Correct Answer: C Section: (none) Explanation Explanation/Reference: Explanation: http://technet.microsoft.com/en-us/library/cc754968(v=ws.10).aspx http://technet.microsoft.com/en-us/library/hh848673(v=wps.620).aspx QUESTION 37 You have a server named Server1 that runs Windows Server 2012. Server1 is backed up by using Windows Server Backup. The backup configuration is shown in the exhibit. (Click the Exhibit button.)
You discover that only the last copy of the backup is maintained. You need to ensure that multiple backup copies are maintained. What should you do? A. B. C. D. Modify the backup destination. Configure the Optimize Backup Performance settings. Modify the Volume Shadow Copy Service (VSS) settings. Modify the backup times.
Correct Answer: A Section: (none) Explanation Explanation/Reference: Explanation:
QUESTION 38 Your network contains an Active Directory forest named contoso.com. All servers run Windows Server 2012. The domain contains four servers. The servers are configured as shown in the following table.
You need to deploy IP Address Management (IPAM) to manage DNS and DHCP. On which server should you install IPAM? A. B. C. D. DC1 DC2 DC3 Server1
Correct Answer: D Section: (none) Explanation Explanation/Reference: Explanation:
http://technet.microsoft.com/en-us/library/hh831353.aspx QUESTION 39 You have a server named Server1 that runs Windows Server 2012. Server1 is located in the perimeter network and has the DNS Server server role installed. Server1 has a zone named contoso.com. You apply a security template to Server1. After you apply the template, users report that they can no longer resolve names from contoso.com. On Server1, you open DNS Manager as shown in the DNS exhibit. (Click the Exhibit button.)
On Server1, you open Windows Firewall with Advanced Security as shown in the Firewall exhibit. (Click the Exhibit button.)
You need to ensure that users can resolve contoso.com names. What should you do? A. From Windows Firewall with Advanced Security, disable the DNS (TCP, Incoming) rule and the DNS (UDP, Incoming) rule. B. From DNS Manager, modify the Zone Transfers settings of the contoso.com zone. C. From DNS Manager, unsign the contoso.com zone. D. From DNS Manager, modify the Start of Authority (SOA) of the contoso.com zone. E. From Windows Firewall with Advanced Security, modify the profiles of the DNS (TCP, Incoming) rule and the DNS (UDP, Incoming) rule. Correct Answer: E Section: (none) Explanation Explanation/Reference: Explanation: QUESTION 40 Your network contains an Active Directory domain named corp.contoso.com. You deploy Active Directory Rights Management Services (AD RMS). You have a rights policy template named Template1. Revocation is disabled for the template. A user named User1 can open content that is protected by Template1 while the user is connected to the corporate network. When User1 is disconnected from the corporate network, the user cannot open the protected content even if the user previously opened the content. You need to ensure that the content protected by Template1 can be opened by users who are disconnected from the corporate network. What should you modify? A. The User Rights settings of Template1 B. The templates file location of the AD RMS cluster
C. The Extended Policy settings of Template1 D. The exclusion policies of the AD RMS cluster Correct Answer: C Section: (none) Explanation Explanation/Reference: Explanation: QUESTION 41 Your company recently deployed a new Active Directory forest named contoso.com. The forest contains two Active Directory sites named Site1 and Site2. The first domain controller in the forest runs Windows Server 2012. You need to force the replication of the SYSVOL folder from Site1 to Site2. Which tool should you use? A. B. C. D. Active Directory Sites and Services DFS Management Repadmin Dfsrdiag
Correct Answer: D Section: (none) Explanation Explanation/Reference: Explanation: http://social.technet.microsoft.com/Forums/en-US/winserverfiles/thread/7e85c7bc-fec2-49bb-896b0635cb9a6e1d http://social.technet.microsoft.com/Forums/en-US/winserverDS/thread/a291bd0f-8cc9-47e1-aca8ce6767979bef QUESTION 42 You have 30 servers that run Windows Server 2012. All of the servers are backed up daily by using Windows Azure Online Backup. You need to perform an immediate backup of all the servers to Windows Azure Online Backup. Which Windows PowerShell cmdlets should you run on each server? A. B. C. D. Get-OBPolicy | StartOBBackup Start-OBRegistration | StartOBBackup Get-WBPolicy | Start-WBBackup Get-WBBackupTarget | Start-WBBackup
Correct Answer: A Section: (none) Explanation Explanation/Reference: Explanation: http://technet.microsoft.com/en-us/library/hh770406(v=wps.620).aspx QUESTION 43 Your network contains an Active Directory domain named contoso.com. All domain controllers run Windows Server 2012. The domain contains two domain controllers. The domain controllers are configured as shown in the following table.
The Branch site contains a member server named Server1 that runs Windows Server 2012. You need to identify which domain controller authenticated the computer account of Server1. What should you do? A. B. C. D. Verify the value of the %LOGONSERVER% environment variable. Run nltest /sc_query. Verify the value of the %SESSIONNAME% environment variable. Run nltest /dsgetsite.
Correct Answer: A Section: (none) Explanation Explanation/Reference: Explanation:The right answer is A
http://support.microsoft.com/kb/141714/en-us QUESTION 44 Your network contains an Active Directory domain named contoso.com. The domain contains two servers named Server1 and Server2 that run Windows Server 2012. Server1 is a file server that has the Hyper-V server role installed. Server1 hosts several virtual machines. The virtual machine configuration files are stored on drive D and the VHD files are stored on drive E. You plan to replace drive E with a larger volume. You need to ensure that the virtual machines on Server1 remain available while drive E is being replaced. What should you do? A. B. C. D. Perform a quick migration. Add Server1 and Server2 as nodes in a failover cluster. Perform a live migration. Perform a storage migration.
Correct Answer: D Section: (none) Explanation Explanation/Reference: Explanation:
http://technet.microsoft.com/en-us/library/hh831656.aspx QUESTION 45 Your network contains an Active Directory domain named contoso.com. The domain contains a file server named File1 that runs a Server Core Installation of Windows Server 2012. File1 has a volume named D that contains home folders. File1 creates a shadow copy of volume D twice a day. You discover that volume D is almost full. You add a new volume named H to File1. You need to ensure that the shadow copies of volume D are stored on volume H. Which command should you run? A. B. C. D. The Set-Volume cmdlet with the -driveletter parameter The vssadmin.exe create shadow command The Set-Volume cmdlet with the -path parameter The vssadmin.exe add shadowstorage command
Correct Answer: D Section: (none) Explanation Explanation/Reference: Explanation: The right answer is D http://technet.microsoft.com/en-us/library/cc754968(v=ws.10).aspx http://technet.microsoft.com/en-us/library/hh848673(v=wps.620).aspx QUESTION 46 Your network contains a perimeter network and an internal network. The internal network contains an Active Directory Federation Services (AD FS) 2.1 infrastructure. The infrastructure uses Active Directory as the attribute store. You plan to deploy a federation server proxy to a server named Server2 in the perimeter network. You need to identify which value must be included in the certificate that is deployed to Server2. What should you identify? A. B. C. D. The FQDN of the AD FS server The name of the Federation Service The name of the Active Directory domain The public IP address of Server2
Correct Answer: A Section: (none) Explanation Explanation/Reference: Explanation: The right answer is A
http://technet.microsoft.com/en-us/library/cc776786(v=ws.10).aspx http://technet.microsoft.com/en-us/library/cc782620(v=ws.10).aspx http://technet.microsoft.com/en-us/library/cc759635(v=ws.10).aspx QUESTION 47 You have a server named Server1 that runs Windows Server 2012. Server1 has the File Server Resource Manager role service installed. You are creating a file management task as shown in the exhibit. (Click the Exhibit button.)
You need to ensure that the Include all folders that store the following kinds of data list displays an entry named Corporate Data. What should you do? A. B. C. D. Modify the properties of the System Files file group. Create a new classification property. Create a new file group. Modify the Folder Usage classification property.
Correct Answer: B Section: (none) Explanation Explanation/Reference: Explanation: http://technet.microsoft.com/en-us/library/dd758765(v=WS.10).aspx QUESTION 48 Your network contains an Active Directory forest named adatum.com. The forest contains an Active Directory Rights Management Services (AD RMS) cluster.
A partner company has an Active Directory forest named litwareinc.com. The partner company does not have AD RMS deployed. You need to ensure that users in litwareinc.com can consume rights-protected content from adatum.com. Which type of trust policy should you create? A. B. C. D. At federated trust A trusted user domain A trusted publishing domain Windows Live ID
Correct Answer: A Section: (none) Explanation Explanation/Reference: Explanation:
http://technet.microsoft.com/en-us/library/dd772651(v=WS.10).aspx http://technet.microsoft.com/en-us/library/cc738707(v=WS.10).aspx http://technet.microsoft.com/en-us/library/cc757344(v=ws.10).aspx QUESTION 49 Your network contains an Active Directory domain named contoso.com. All domain controllers run Windows Server 2012. The domain contains two domain controllers. The domain controllers are configured as shown in the following table.
The Branch site contains a perimeter network. For security reasons, client computers in the perimeter network can communicate with client computers in the Branch site only. You plan to deploy a new RODC to the perimeter network in the Branch site. You need to ensure that the new RODC will be able to replicate from DC10. What should you do first on DC10? A. B. C. D. Run the Add-ADDSReadOnlyDomainControllerAccount cmdlet. Create an Active Directory site. Run the Active Directory Domain Services Configuration Wizard. Create an Active Directory subnet.
Correct Answer: A Section: (none) Explanation Explanation/Reference: Explanation: Add-ADDSReadOnlyDomainControllerAccount Creates a read-only domain controller (RODC) account that can be used to install an RODC in Active Directory. Note: * Notes Once you have added the RODC account, you can add an RODC to a server computer by using the InstallADDSDomainController cmdlet with the -ReadOnlyReplica switch parameter. * Example Adds a new read-only domain controller (RODC) account to the corp.contoso.com domain using the North America site as the source site for the replication source domain controller. C:\PS>Add-ADDSReadOnlyDomainControllerAccount -DomainControllerAccountName RODC1 DomainName corp.contoso.com -SiteName NorthAmerica Incorrect: Not B: There already is a branch site. Reference: Add-ADDSReadOnlyDomainControllerAccount http://technet.microsoft.com/en-us/library/hh974718(v=wps.620).aspx QUESTION 50 Your network contains an Active Directory domain named contoso.com. All domain controllers run Windows Server 2012. The domain contains two domain controllers. The domain controllers are configured as shown in the following table.
You configure a user named User1 as a delegated administrator of DC10. You need to ensure that User1 can log on to DC10 if the network link between the Main site and the Branch site fails. What should you do? A. B. C. D. Add User1 to the Domain Admins group. Modify the properties of the DC10 computer account. Run repadmin and specify /replsingleobject parameter. On DC10, modify the User Rights Assignment in Local Policies.
Correct Answer: D Section: (none) Explanation Explanation/Reference: Explanation: Modify the following policy: Computer Configuration\Windows Settings\Security Settings\Local Policies\User Rights Assignment\Allow log on locally Note: * User Rights Assignment policies determines which users or groups have logon rights or privileges on the computer.
* Delegated administrator accounts gain local administrative permissions to the RODC. These users can operate with privileges equivalent to the local computer's Administrators group. They are not members of the Domain Admins or the domain built-in Administrators groups. This option is useful for delegating branch office administration without giving out domain administrative permissions. Configuring delegation of administration is not required.
Exam D QUESTION 1 Your network contains servers that run Windows Server 2012. The network contains a large number of iSCSI storage locations and iSCSI clients. You need to deploy a central repository that can discover and list SCSI resources on the network automatically. Which feature should you deploy? A. B. C. D. the Windows Standards-Based Storage Management feature the iSCSI Target Server role service the iSCSI Target Storage Provider feature the iSNS Server service feature
Correct Answer: D Section: (none) Explanation Explanation/Reference: Explanation:
QUESTION 2 Your network contains an Active Directory forest named contoso.com that contains a single domain. The forest contains three sites named Site1, Site2, and Site3. Domain controllers run either Windows Server 2008 R2 or Windows Server 2012. Each site contains two domain controllers. Site1 and Site2 contain a global catalog server. You need to create a new site link between Site1 and Site2. The solution must ensure that the site link supports the replication of all the naming contexts. From which node should you create the site link? To answer, select the appropriate node in the answer area. Hot Area:
Correct Answer:
Section: (none) Explanation Explanation/Reference:
QUESTION 3 Your network contains an Active Directory domain named adatum.com. All servers run Windows Server 2012. All domain controllers have the DNS Server server role installed. You have a domain controller named DC1. On DC1, you create an Active Directory-integrated zone named adatum.com and you sign the zone by using DNSSEC. You deploy a new read-only domain controller (RODC) named R0DC1. You need to ensure that the contoso.com zone replicates to R0DC1. What should you configure on DC1? To answer, select the appropriate tab in the answer area. Hot Area:
Correct Answer:
Section: (none) Explanation Explanation/Reference:
QUESTION 4 Your network contains an Active Directory domain named contoso.com. The domain contains a server named Server2 that runs Windows Server 2012. You are a member of the local Administrators group on Server2. You install an Active Directory Rights Management Services (AD RMS) root cluster on Server2. You need to ensure that the AD RMS cluster is discoverable automatically by the AD RMS client computers and the users in contoso.com. Which additional configuration settings should you configure? To answer, select the appropriate tab in the answer area. Hot Area:
Correct Answer:
Section: (none) Explanation Explanation/Reference:
QUESTION 5 Your network contains an Active Directory domain named contoso.com. The domain contains two Active Directory sites named Site1 and Site2. You discover that when the account of a user in Site1 is locked out, the user can still log on to the servers in Site2 for up to 15 minutes by using Remote Desktop Services (RDS). You need to reduce the amount of time it takes to synchronize account lockout information across the domain. Which attribute should you modify? To answer, select the appropriate attribute in the answer area.
Hot Area:
Correct Answer:
Section: (none) Explanation Explanation/Reference: http://technet.microsoft.com/en-us/library/cc961787.aspx QUESTION 6 Your network contains an Active Directory domain named contoso.com. All client computers run Windows 8 Enterprise. You have a remote site that only contains client computers. All of the client computer accounts are located in an organizational unit (OU) named Remotel. A Group Policy object (GPO) named GPO1 is linked to the Remote1 OU. You need to configure BranchCache for the remote site. Which two settings should you configure in GPO1? To answer, select the two appropriate settings in the answer area. Hot Area:
Correct Answer:
Section: (none) Explanation Explanation/Reference: QUESTION 7 Your network contains an Active Directory domain named contoso.com. The domain contains two Active Directory sites named Site1 and Site2. You need to configure the replication between the sites to occur by using change notification. Which attribute should you modify? Hot Area:
Correct Answer:
Section: (none) Explanation Explanation/Reference: http://blogs.technet.com/b/qzaidi/archive/2010/09/23/enable-change-notifications-between-sites-how-andwhy.aspx http://blogs.msdn.com/b/canberrapfe/archive/2012/03/26/active-directory-replication-change-notificationamp-you.aspx
QUESTION 8 Your company has a main office and a branch office. An Active Directory site exists for each office. The network contains an Active Directory forest named contoso.com. The contoso.com domain contains three member servers named Server1, Server2, and Server3. All servers run Windows Server 2012. In the main office, you configure Server1 as a file server that uses BranchCache. In the branch office, you configure Server2 and Server3 as BranchCache hosted cache servers. You are creating a Group Policy for the branch office site. In the branch office, you need to configure the client computers that run Windows 8 to use Server2 and Server3 as BranchCache. Hot Area:
Correct Answer:
Section: (none) Explanation Explanation/Reference: http://technet.microsoft.com/en-us/library/ee649153(v=ws.10).aspx http://blogs.technet.com/b/wsnetdoc/archive/2012/06/01/highlighting-branchcache-hosted-cache-mode-inwindows-server-2012.aspx
QUESTION 9 Your company has a main office and a branch office. The main office is located in Detroit. The branch office is located in Seattle. The network contains an Active Directory domain named adatum.com. Client computers run either The main office contains 1,000 client computers and 50 servers. The branch office contains 20 client computers. All computer accounts for the branch office are located in an organizational unit (OU) named SeattleComputers. A Group Policy object (GPO) named GPO1 is linked to the SeattleComputers OU. You need to configure BranchCache for the branch office. Hot Area:
Correct Answer:
Section: (none) Explanation Explanation/Reference: http://technet.microsoft.com/en-us/library/dd637820(v=ws.10).aspx
Distributed Cache mode If client computers are configured to use Distributed Cache mode, the cached content is distributed among client computers on the branch office network. No infrastructure or services are required in the branch office beyond client computers running Windows 7. Hosted Cache mode In hosted cache mode, cached content is maintained on a computer running Windows Server 2008 R2 on the branch office network.
QUESTION 10 Your network contains an Active Directory domain named contoso.com. The domain contains two servers named Server1 and Server2. Both servers have the IP Address Management (IPAM) Server feature installed. You have a support technician named Tech1. Tech1 is a member of the IPAM Administrators group on Server1 and Server2. You need to ensure that Tech1 can use Server Manager on Server1 to manage IPAM on Server2. To which group on Server2 should you add Tech1? To answer, select the appropriate group in the answer area. Hot Area:
Correct Answer:
Section: (none) Explanation Explanation/Reference: http://www.microsoft.com/en-us/download/dlx/ThankYou.aspx?id=29012
Both WinRMRemoteWMIUsers_ and Remote Management Users have the exact same description. As such, I tested connecting with server manager remotely with a non-administrative account. I tried before adding to either group and got this error:
I then added to Remote Management Users and got this error:
--Note that this is due to access to the event log only. Next I removed from Remote Management Users and added to WinRMRemoteWMIUsers_ and got this error:
The error is exactly the same and the explanation is due to event log. In summary, Either one of these answers is correct, however since the document explicitly says use the "WinRMRemoteWMIUsers_" group, then that's what we gotta do. QUESTION 11 Your network contains an Active Directory domain named contoso.com. The domain contains a server named Server1 that runs Windows Server 2012. Server1 has the Active Directory Federation Services (AD FS) server role installed. Adatum.com is a partner organization. You are helping the administrator of adatum.com set up a federated trust between adatum.com and contoso.com. The administrator of adatum. com asks you to provide a file containing the federation metadata of contoso.com. You need to identify the location of the federation metadata file. Which node in the AD FS console should you select? To answer, select the appropriate node in the answer area Hot Area:
Correct Answer:
Section: (none) Explanation Explanation/Reference: http://blogs.msdn.com/b/card/archive/2010/06/25/using-federation-metadata-to-establish-a-relying-partytrust-in-ad-fs-2-0.aspx
QUESTION 12 Your network contains an Active Directory domain named contoso.com. The domain contains an enterprise certification authority (CA). The domain contains a server named Server1 that runs Windows Server 2012. You install the Active Directory Federation Services server role on Server1. You plan to configure Server1 as an Active Directory Federation Services (AD FS) server. The Federation Service name will be set to adfsl.contoso.com. You need to identify which type of certificate template you must use to request a certificate for AD FS. Which certificate template should you identify? To answer, select the appropriate template in the answer area. Hot Area:
Correct Answer:
Section: (none) Explanation Explanation/Reference: http://blogs.msdn.com/b/alextch/archive/2011/06/27/installing-a-stand-along-adfs-service.aspx QUESTION 13 HOTSPOT Your company has a primary data center and a disaster recovery data center. The network contains an Active Directory domain named contoso.com. The domain contains a server named Server1 runs Windows Server 2012. Server1 is located in the primary data center. Server1 has an enterprise root certification authority (CA) for contoso.com. You deploy another server named Server2 to the disaster recovery data center. You plan to configure Server2 as a secondary certificate revocation list (CRL) distribution point. You need to configure Server2 as a CRL distribution point (CDP). Which tab should you use to configure the required CDP entry? To answer, select the appropriate tab in the answer area.
Hot Area:
Correct Answer:
Section: (none) Explanation Explanation/Reference:
http://technet.microsoft.com/zh-cn/library/jj125369.aspx QUESTION 14 HOTSPOT Your network contains an Active Directory domain named contoso.com. The domain contains two member servers named Server1 and Server2. All servers run Windows Server 2012. Server1 and Server2 have the Network Load Balancing (NLB) feature installed. The servers are configured as nodes in an NLB cluster named Cluster1. Both servers connect to the same switch. Cluster1 hosts a secure web application named WebApp1. WebApp1 saves user state information in a central database. You need to ensure that the connections to WebApp1 are distributed evenly between the nodes. The solution must minimize port flooding. What should you configure? To answer, configure the appropriate affinity and the appropriate mode for Cluster1 in the answer area.
Hot Area:
Correct Answer:
Section: (none) Explanation Explanation/Reference: QUESTION 15 HOTSPOT Your network contains an Active Directory domain named contoso.com. The domain contains a server named Server1 that runs Windows Server 2012. Server1 has the Active Directory Federation Services server role installed. You need to make configuration changes to the Windows Token-based Agent role service. Which tool should you use? To answer, select the appropriate tool in the answer area.
Hot Area:
Correct Answer:
Section: (none) Explanation Explanation/Reference: QUESTION 16 HOTSPOT Your network contains an Active Directory domain named contoso.com. The domain contains two member servers named Server1 and Server2. All servers run Windows Server 2012. Server1 and Server2 have the Hyper-V server role installed. The servers are configured as shown in the following table.
You add a third server named Server3 to the network. Server3 has Intel processors. You need to move VM3 and VM6 to Server3. The solution must minimize downtime on the virtual machines. Which method should you use to move each virtual machine? To answer, select the appropriate method for each virtual machine in the answer area.
Hot Area:
Correct Answer:
Section: (none) Explanation Explanation/Reference: QUESTION 17 HOTSPOT Your network contains an Active Directory domain named contoso.com. The domain contains two member servers named Server1 and Server2. All servers run Windows Server 2012. Server1 and Server2 have the Hyper-V server role and the Failover Clustering feature installed. Server1 and Server2 are members of a cluster named Cluster1. Cluster1 hosts 10 virtual machines. When you try to migrate a running virtual machine from one server to another, you receive the following error message: "There was an error checking for virtual machine compatibility on the target node." You need to ensure that the virtual machines can be migrated from one node to another.
From which node should you perform the configuration? To answer, select the appropriate node in the answer area.
Hot Area:
Correct Answer:
Section: (none) Explanation Explanation/Reference:
http://www.shogan.co.uk/tag/esxi/ .shogan.co.uk/tag/esxi/ QUESTION 18 HOTSPOT Your network contains two servers named Server1 and Server2 that run Windows Server 2012. Server1 and Server2 have the Hyper-V server role installed. Server1 and Server2 have different processor models from the same manufacturer. On Server1, you plan to create a virtual machine named VM1. Eventually, VM1 will be exported to Server2. You need to ensure that when you import VM1 to Server2, you can start VM1 from saved snapshots. What should you configure on VM1? To answer, select the appropriate node in the answer area.
Hot Area:
Correct Answer:
Section: (none) Explanation Explanation/Reference: http://technet.microsoft.com/en-us/magazine/gg299590.aspx QUESTION 19 HOTSPOT Your network contains an Active Directory domain named contoso.com. The domain contains a file server named Server1. Server1 is a BranchCache hosted cache server that is located in a branch office. The network contains client computers that run either Windows 7 or Windows 8.
For the branch office, all of the user accounts and the client computer accounts are located in an organizational unit (OU) named Branch1. A Group Policy object (GPO) named GPO1 is linked to Branch 1. GPO1 contains the BranchCache settings. You discover that users in the branch office who have client computers that run Windows 7 do not access cached content from Server1. Users in the branch office who have Windows 8 computers access cached content from Server1. You need to configure the Windows 7 computers to use BranchCache on Server1. Which setting should you configure in GPO1? To answer, select the appropriate setting in the answer area.
Hot Area:
Correct Answer:
Section: (none) Explanation Explanation/Reference: QUESTION 20 HOTSPOT Your network contains two DHCP servers named Server1 and Server2. Server1 fails. You discover that DHCP clients can no longer receive IP address leases. You need to ensure that the DHCP clients receive IP addresses immediately.
What should you configure from the View/Edit Failover Relationship settings? To answer, select the appropriate setting in the answer area.
Hot Area:
Correct Answer:
Section: (none) Explanation Explanation/Reference: QUESTION 21 Your network contains an Active Directory domain named contoso.com. The domain contains a server named Server1 that runs Windows Server 2012. Server1 has the Active Directory Certificate Services server role installed and configured. For all users, you are deploying smart cards for logon. You are using an enrollment agent to enroll the smart card certificates for the users. You need to configure the Contoso Smartcard Logon certificate template to support the use of the enrollment agent.
Which setting should you modify? To answer, select the appropriate setting in the answer area. Hot Area:
Correct Answer:
Section: (none) Explanation Explanation/Reference: http://social.technet.microsoft.com/Forums/en-US/winserversecurity/thread/162e1108-bd46-4b2b-9ea04fff8949a810 http://technet.microsoft.com/en-us/library/cc725621(v=WS.10).aspx QUESTION 22 HOTSPOT Your network contains an Active Directory domain named contoso.com. The domain contains the two servers. The servers are configured as shown in the following table.
You investigate a report about the potential compromise of a private key for a certificate issued to Server2. You need to revoke the certificate issued to Server2. The solution must ensure that the revocation can be reverted. Which reason code should you select? To answer, select the appropriate reason code in the answer area.
Hot Area:
Correct Answer:
Section: (none) Explanation Explanation/Reference:
http://technet.microsoft.com/en-us/library/cc753724(v=WS.10).aspx QUESTION 23 HOTSPOT
You have a server named Server1 that runs Windows Server 2012. The volumes on Server1 are configured as shown in the following table.
A new corporate policy states that backups must use Windows Azure Online Backup whenever possible. You need to identify which backup methods you must use to back up Server1. The solution must use Windows Azure Online Backup whenever possible. Which backup type should you identify for each volume? To answer, select the appropriate backup type for each volume in the answer area.
Hot Area:
Correct Answer:
Section: (none) Explanation Explanation/Reference:
http://technet.microsoft.com/en-us/library/jj614621.aspx http://technet.microsoft.com/zh-cn/library/hh831419.aspx
Exam E QUESTION 1 Your network contains an Active Directory forest. The forest contains a single domain named contoso.com. The forest contains two Active Directory sites named Main and Branch1. The sites connect to each other by using a site link named Main-Branch1. There are no other site links. Each site contains several domain controllers. All domain controllers run Windows Server 2012. Your company plans to open a new branch site named Branch2. The new site will have a WAN link that connects to the Main site only. The site will contain two domain controllers that run Windows Server 2012. You need to create a new site and a new site link for Branch2. The solution must ensure that the domain controllers in Branch2 only replicate to the domain controllers in Branch1 if all of the domain controllers in Main are unavailable. Which three actions should you perform? To answer, move the three appropriate actions from the list of actions to the answer area and arrange them in the correct order. Select and Place:
Correct Answer:
Section: (none)
Explanation Explanation/Reference: QUESTION 2 Your network contains an Active Directory domain named contoso.com. The domain contains two member servers named Server1 and Server2 that run Windows Server 2012. You configure a new failover cluster named Cluster1. Server1 and Server2 are nodes in Cluster1. You need to configure the disk that will be used as a witness disk for Cluster1. How should you configure the witness disk? To answer, drag the appropriate configurations to the correct location or locations. Each configuration may be used once, more than once, or not at all. You may need to drag the split bar between panes or scroll to view content. Select and Place:
Correct Answer:
Section: (none) Explanation
Explanation/Reference: http://technet.microsoft.com/en-us/library/jj612870.aspx#BKMK_witness
QUESTION 3 Your network contains an Active Directory domain named contoso.com. All file servers in the domain run Windows Server 2012. The computer accounts of the file servers are in an organizational unit (OU) named OU1. A Group Policy object (GPO) named GP01 is linked to OU1. You plan to modify the NTFS permissions for many folders on the file servers by using central access policies. You need to identify any users who will be denied access to resources that they can currently access once the new permissions are implemented. In which order should you perform the five actions? To answer, move all actions from the list of actions to the answer area and arrange them in the correct order. Select and Place:
Correct Answer:
Section: (none) Explanation Explanation/Reference: http://technet.microsoft.com/en-us/library/hh846167.aspx QUESTION 4 You have a server named Server2 that runs Windows Server 2012. You have storage provisioned on Server2 as shown in the exhibit. (Click the Exhibit button.) You need to configure the storage so that it appears in Windows Explorer as a drive letter on Server1. Which three actions should you perform in sequence? To answer, move the three appropriate actions from the list of actions to the answer area and arrange them in the correct order.
Select and Place:
Correct Answer:
Section: (none) Explanation
Explanation/Reference: http://blogs.technet.com/b/filecab/archive/2012/05/21/introduction-of-iscsi-target-in-windows-server-2012. aspx QUESTION 5 Your network contains an Active Directory domain named contoso.com. The domain contains a file server named Server1. All servers run Windows Server 2012. All domain user accounts have the Division attribute automatically populated as part of the user provisioning process. The Support for Dynamic Access Control and Kerberos armoring policy is enabled for the domain. You need to control access to the file shares on Server1 based on the values in the Division attribute and the Division resource property. Which three actions should you perform in sequence? To answer, move the three appropriate actions from the list of actions to the answer area and arrange them in the correct order. Select and Place:
Correct Answer:
Section: (none) Explanation Explanation/Reference: http://technet.microsoft.com/de-de/library/hh846167.aspx First create a claim type for the property, then create a reference resource property that points back to the claim. Finally set the classification value on the folder. QUESTION 6 You have a file server named Server1 that runs Windows Server 2012. The folders on Server1 are configured as shown in the following table.
A new corporate policy states that backups must use Microsoft Online Backup whenever possible. You need to identify which technology you must use to back up Server1. The solution must use Microsoft Online Backup whenever possible. What should you identify? To answer, drag the appropriate backup type to the correct location or locations. Each backup type may be used once, more than once, or not at all. You may need to drag the split bar between panes or scroll to view content. Select and Place:
Correct Answer:
Section: (none) Explanation Explanation/Reference: http://technet.microsoft.com/en-us/library/hh831761.aspx
QUESTION 7 DRAG DROP You have 3 server named Server1 that runs Windows Server 2012. You are asked to test Windows Azure Online Backup to back up Server1. You need to back up Server1 by using Windows Azure Online Backup. Which four actions should you perform in sequence? To answer, move the appropriate four actions from the list of actions to the answer area and arrange them in the correct order.
Select and Place:
Correct Answer:
Section: (none) Explanation Explanation/Reference:
http://technet.microsoft.com/en-us/library/jj884318.aspx http://technet.microsoft.com/en-us/library/hh831761.aspx#BKMK_installagent So,
QUESTION 8 DRAG DROP Your network contains an Active Directory domain named contoso.com. The domain contains two DHCP servers named DHCP1 and DHCP2 that run Windows Server 2012. You install the IP Address Management (IPAM) Server feature on a member server named Server1 and you run the Run Invoke-IpamGpoProvisioning cmdlet. You need to manage the DHCP servers by using IPAM on Server1. Which three actions should you perform? To answer, move the three appropriate actions from the list of actions to the answer area and arrange them in the correct order.
Select and Place:
Correct Answer:
Section: (none) Explanation Explanation/Reference:
http://technet.microsoft.com/zh-cn/library/jj878325.aspx QUESTION 9 DRAG DROP Your network contains two Active Directory forests named contoso.com and adatum.com. All domain controllers run Windows Server 2012. A federated trust exists between adatum.com and contoso.com. The trust provides adatum.com users with access to contoso.com resources. You need to configure Active Directory Federation Services (AD FS) claim rules for the federated trust. The solution must meet the following requirements: - In contoso.com, replace an incoming claim type named Group with an outgoing claim type named Role. - In adatum.com, allow users to receive their tokens for the relying party by using their Active Directory group membership as the claim type. The AD FS claim rules must use predefined templates. Which rule types should you configure on each side of the federated trust? To answer, drag the appropriate rule types to the correct location or locations. Each rule type may be used once, more than once, or not at all. You may need to drag the split bar between panes or scroll to view content.
Select and Place:
Correct Answer:
Section: (none) Explanation Explanation/Reference:
http://technet.microsoft.com/zh-cn/library/ee913586(v=WS.10).aspx QUESTION 10 DRAG DROP Your network contains four servers that run Windows Server 2012. Each server has the Failover Clustering feature installed. Each server has three network adapters installed. An iSCSI SAN is available on the network. You create a failover cluster named Cluster1. You add the servers to the cluster. You plan to configure the network settings of each server node as shown in the following table.
You need to configure the network settings for Cluster1. What should you do? To answer, drag the appropriate network communication setting to the correct cluster network. Each network communication setting may be used once, more than once, or not at all. You may need to drag the split bar between panes or scroll to view content.
Select and Place:
Correct Answer:
Section: (none) Explanation Explanation/Reference:
http://technet.microsoft.com/en-us/library/cc787135(v=WS.10).aspx QUESTION 11
DRAG DROP Your network contains an Active Directory domain named contoso.com. The domain contains four member servers named Server1, Server2, Servers, and Server4. All servers run Windows Server 2012. Server1 and Server2 are located in a site named Site1. Server3 and Server4 are located in a site named Site2. The servers are configured as nodes in a failover cluster named Cluster1. Cluster1 is configured to use the Node Majority quorum configuration. You need to ensure that Server1 is the only server in Site1 that can vote to maintain quorum. What should you run from Windows PowerShell? To answer, drag the appropriate commands to the correct location. Each command may be used once, more than once, or not at all. You may need to drag the split bar between panes or scroll to view content.
Select and Place:
Correct Answer:
Section: (none) Explanation Explanation/Reference:
S-ar putea să vă placă și
- CEH v10 Module 14 - Hacking Web ApplicationsDocument11 paginiCEH v10 Module 14 - Hacking Web ApplicationsAnxo Alonso Da RosaÎncă nu există evaluări
- 2A ENU CompanionDocument80 pagini2A ENU CompanionAnxo Alonso Da RosaÎncă nu există evaluări
- 1A ENU CompanionDocument204 pagini1A ENU CompanionAnxo Alonso Da RosaÎncă nu există evaluări
- 20410ADocument390 pagini20410AAnxo Alonso Da RosaÎncă nu există evaluări
- Cisco ActualTests 640-864 v2012-07-05 by Meh123Document161 paginiCisco ActualTests 640-864 v2012-07-05 by Meh123Anxo Alonso Da RosaÎncă nu există evaluări
- Course Introduction: Vmware Vsphere: Install, Configure, ManageDocument9 paginiCourse Introduction: Vmware Vsphere: Install, Configure, ManageAnxo Alonso Da RosaÎncă nu există evaluări
- Shoe Dog: A Memoir by the Creator of NikeDe la EverandShoe Dog: A Memoir by the Creator of NikeEvaluare: 4.5 din 5 stele4.5/5 (537)
- The Yellow House: A Memoir (2019 National Book Award Winner)De la EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Evaluare: 4 din 5 stele4/5 (98)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeDe la EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeEvaluare: 4 din 5 stele4/5 (5794)
- The Little Book of Hygge: Danish Secrets to Happy LivingDe la EverandThe Little Book of Hygge: Danish Secrets to Happy LivingEvaluare: 3.5 din 5 stele3.5/5 (400)
- Grit: The Power of Passion and PerseveranceDe la EverandGrit: The Power of Passion and PerseveranceEvaluare: 4 din 5 stele4/5 (588)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureDe la EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureEvaluare: 4.5 din 5 stele4.5/5 (474)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryDe la EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryEvaluare: 3.5 din 5 stele3.5/5 (231)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceDe la EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceEvaluare: 4 din 5 stele4/5 (895)
- Team of Rivals: The Political Genius of Abraham LincolnDe la EverandTeam of Rivals: The Political Genius of Abraham LincolnEvaluare: 4.5 din 5 stele4.5/5 (234)
- Never Split the Difference: Negotiating As If Your Life Depended On ItDe la EverandNever Split the Difference: Negotiating As If Your Life Depended On ItEvaluare: 4.5 din 5 stele4.5/5 (838)
- The Emperor of All Maladies: A Biography of CancerDe la EverandThe Emperor of All Maladies: A Biography of CancerEvaluare: 4.5 din 5 stele4.5/5 (271)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaDe la EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaEvaluare: 4.5 din 5 stele4.5/5 (266)
- On Fire: The (Burning) Case for a Green New DealDe la EverandOn Fire: The (Burning) Case for a Green New DealEvaluare: 4 din 5 stele4/5 (74)
- The Unwinding: An Inner History of the New AmericaDe la EverandThe Unwinding: An Inner History of the New AmericaEvaluare: 4 din 5 stele4/5 (45)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersDe la EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersEvaluare: 4.5 din 5 stele4.5/5 (345)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyDe la EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyEvaluare: 3.5 din 5 stele3.5/5 (2259)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreDe la EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreEvaluare: 4 din 5 stele4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)De la EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Evaluare: 4.5 din 5 stele4.5/5 (121)
- Her Body and Other Parties: StoriesDe la EverandHer Body and Other Parties: StoriesEvaluare: 4 din 5 stele4/5 (821)
- PacketShaper Release Notes v921Document30 paginiPacketShaper Release Notes v921Noah HeaserÎncă nu există evaluări
- Exam SC 900 Microsoft Security Compliance and Identity Fundamentals Skills MeasuredDocument9 paginiExam SC 900 Microsoft Security Compliance and Identity Fundamentals Skills Measuredzawzaw htetÎncă nu există evaluări
- The Role of Azure Active Directory in Windows 10 Cloud SubscriptionsDocument9 paginiThe Role of Azure Active Directory in Windows 10 Cloud SubscriptionsAli OfiiÎncă nu există evaluări
- DLL CSS12 Week2Document4 paginiDLL CSS12 Week2Christian MarzoÎncă nu există evaluări
- ExamClubs Microsoft AZ-104 Dumps-1Document155 paginiExamClubs Microsoft AZ-104 Dumps-1gurunge100% (10)
- Active Directory in Server 2003 InstallmentDocument5 paginiActive Directory in Server 2003 Installmentarnold_najeraÎncă nu există evaluări
- Log Insight Administration GuideDocument133 paginiLog Insight Administration GuideRickzÎncă nu există evaluări
- Monthly Report ICT SimpleDocument30 paginiMonthly Report ICT SimpleAbdighaniMOGoudÎncă nu există evaluări
- Az 900Document160 paginiAz 900gurungeÎncă nu există evaluări
- FsffasaDocument2 paginiFsffasaHamid SaifÎncă nu există evaluări
- OpsCenter v10 9 3 Installation and Configuration Guide MK-99OPS001-19Document161 paginiOpsCenter v10 9 3 Installation and Configuration Guide MK-99OPS001-19smowaishyderÎncă nu există evaluări
- Pro-Watch 55 AE Document Nov 21 2021 800-07601V26 PDFDocument26 paginiPro-Watch 55 AE Document Nov 21 2021 800-07601V26 PDFthamer al-salekÎncă nu există evaluări
- IdM Quick ReferenceDocument14 paginiIdM Quick ReferencebelgaumÎncă nu există evaluări
- CurriculumVirtueDocument3 paginiCurriculumVirtueChristopher AiyapiÎncă nu există evaluări
- 00 - September - 2016 Senior Microsoft Windows System Engineer and Cloud InfrastructureDocument13 pagini00 - September - 2016 Senior Microsoft Windows System Engineer and Cloud InfrastructureRajesh ExperisÎncă nu există evaluări
- BPOS Standard Deployment Guide February2010 PDFDocument100 paginiBPOS Standard Deployment Guide February2010 PDFRuben Dario Pinzón ErasoÎncă nu există evaluări
- SQLServer 2005 FOCDocument108 paginiSQLServer 2005 FOCNasir Boakye-BoatengÎncă nu există evaluări
- AZ-104-microsoft Azure Administrator SyllabusDocument9 paginiAZ-104-microsoft Azure Administrator SyllabusamreshÎncă nu există evaluări
- Altos EasyStore Manual 021907Document169 paginiAltos EasyStore Manual 021907posetsÎncă nu există evaluări
- Pages From Microsoft - 70-410Document98 paginiPages From Microsoft - 70-410pankaj_subhedarÎncă nu există evaluări
- En US PDFDocument2 paginiEn US PDFAnonymous 7LJCiQo2rnÎncă nu există evaluări
- Full Form Acronyms.Document178 paginiFull Form Acronyms.Arpit SharmaÎncă nu există evaluări
- AZ First 6 Mod 3Document22 paginiAZ First 6 Mod 3jharajnish30Încă nu există evaluări
- 20742A ENU TrainerHandbook PDFDocument688 pagini20742A ENU TrainerHandbook PDFFernando CorderoÎncă nu există evaluări
- TrueNAS 9.2.1.8 Administrator GuideDocument201 paginiTrueNAS 9.2.1.8 Administrator GuideMohamad Reza NazariÎncă nu există evaluări
- Super Hybrid BI - PowerBI GatewayDocument26 paginiSuper Hybrid BI - PowerBI GatewaybrusselarÎncă nu există evaluări
- En - Security Center Administrator Guide 5.2Document901 paginiEn - Security Center Administrator Guide 5.2RebornteamAbdelkaderSariÎncă nu există evaluări
- Az 104 PDFDocument10 paginiAz 104 PDFwilfred maswaya100% (2)
- Design Hybrid IdentityDocument869 paginiDesign Hybrid IdentityRavinder SinghÎncă nu există evaluări