Documente Academic
Documente Profesional
Documente Cultură
Initial Steps - Pre - Mock Recall
Încărcat de
Floreid0 evaluări0% au considerat acest document util (0 voturi)
8 vizualizări1 paginăguidelines for mock recall
Titlu original
Initial Steps - Pre- Mock Recall
Drepturi de autor
© © All Rights Reserved
Formate disponibile
DOCX, PDF, TXT sau citiți online pe Scribd
Partajați acest document
Partajați sau inserați document
Vi se pare util acest document?
Este necorespunzător acest conținut?
Raportați acest documentguidelines for mock recall
Drepturi de autor:
© All Rights Reserved
Formate disponibile
Descărcați ca DOCX, PDF, TXT sau citiți online pe Scribd
0 evaluări0% au considerat acest document util (0 voturi)
8 vizualizări1 paginăInitial Steps - Pre - Mock Recall
Încărcat de
Floreidguidelines for mock recall
Drepturi de autor:
© All Rights Reserved
Formate disponibile
Descărcați ca DOCX, PDF, TXT sau citiți online pe Scribd
Sunteți pe pagina 1din 1
Initial Step: Conduct a Vulnerability Audit
Before a simulated food recall is conducted, you should complete a vulnerability
audit.
Start by creating a list of crises that could occur at or affect your company.
A good list can be developed by interviewing senior management officials, other supervisory personnel,
employees, distributors and sales reps, key customers, news and trade media that routinely cover your
business, trade association officials, suppliers and vendors, retail investors, stock analysts and
institutional investors, emergency responders like police, fire, hospital and HAZMAT personnel,
information systems experts and Internet consultants.
Make sure to focus on the right issues when conducting your vulnerability audit by analyzing your list
according to the following:
Likelihood of occurrence: Is the scenario very likely, possible but not likely in the near term or not likely
to occur at all?
Potential damage to the company: Does the scenario have the potential for serious damage,
manageable damage or easily managed damage? (Note: Damage refers not only to safety issues and
physical damage to facilities, but also to the potential for public outrage and harm to the companys
reputation.)
Next, combine these lists and rank them according to the following:
The scenario is very likely to occur and cause serious damage.
The scenario is likely to occur and damage is manageable. Here are a few questions you need to ask
yourself:
Where in your receiving area can
food be compromised?
Moving into your processing plant,
where might contamination enter the
process?
What is the nature of packaging
and/or shipping containers?
How do you track your products distribution?
If you use private labeling, what kind
of scrutiny do you have of your suppliers?
What do FDA inspection reports tell
you? CDC reports?
What types of problems have your
product or a competitive product
had in the marketplace?
What is the most serious problem
that could realistically occur?
What do your risk managers, lawyers
and insurance company indicate as
being major exposures for you?
This simple but critical vulnerability
auditas complete as possiblewill become
the basis for your simulation.
S-ar putea să vă placă și
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeDe la EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeEvaluare: 4 din 5 stele4/5 (5794)
- BCP Exercise Planner Instructions - FINAL - v6 - APR 25Document11 paginiBCP Exercise Planner Instructions - FINAL - v6 - APR 25FloreidÎncă nu există evaluări
- The Yellow House: A Memoir (2019 National Book Award Winner)De la EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Evaluare: 4 din 5 stele4/5 (98)
- Egg Safety: Consumer AdvisoryDocument2 paginiEgg Safety: Consumer AdvisoryFloreidÎncă nu există evaluări
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryDe la EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryEvaluare: 3.5 din 5 stele3.5/5 (231)
- g7s Spanish SyllabusDocument6 paginig7s Spanish SyllabusFloreidÎncă nu există evaluări
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceDe la EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceEvaluare: 4 din 5 stele4/5 (895)
- Traffic Door Brochure - EnglishDocument32 paginiTraffic Door Brochure - EnglishFloreidÎncă nu există evaluări
- The Little Book of Hygge: Danish Secrets to Happy LivingDe la EverandThe Little Book of Hygge: Danish Secrets to Happy LivingEvaluare: 3.5 din 5 stele3.5/5 (400)
- BCP Participant Feedback Form - FINALDocument2 paginiBCP Participant Feedback Form - FINALFloreidÎncă nu există evaluări
- Shoe Dog: A Memoir by the Creator of NikeDe la EverandShoe Dog: A Memoir by the Creator of NikeEvaluare: 4.5 din 5 stele4.5/5 (537)
- DMAIICDocument5 paginiDMAIICFloreidÎncă nu există evaluări
- Never Split the Difference: Negotiating As If Your Life Depended On ItDe la EverandNever Split the Difference: Negotiating As If Your Life Depended On ItEvaluare: 4.5 din 5 stele4.5/5 (838)
- BCP Situation Manual FINAL v7 APR 25Document30 paginiBCP Situation Manual FINAL v7 APR 25FloreidÎncă nu există evaluări
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureDe la EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureEvaluare: 4.5 din 5 stele4.5/5 (474)
- Switching RulesDocument2 paginiSwitching RulesFloreidÎncă nu există evaluări
- Grit: The Power of Passion and PerseveranceDe la EverandGrit: The Power of Passion and PerseveranceEvaluare: 4 din 5 stele4/5 (588)
- Blind Taste Test ReportDocument63 paginiBlind Taste Test ReportFloreid50% (2)
- Factory Assessment Questionaire - BlankDocument6 paginiFactory Assessment Questionaire - BlankFloreidÎncă nu există evaluări
- The Emperor of All Maladies: A Biography of CancerDe la EverandThe Emperor of All Maladies: A Biography of CancerEvaluare: 4.5 din 5 stele4.5/5 (271)
- Laboratory Quality Manual UCM216952Document82 paginiLaboratory Quality Manual UCM216952scottishpiper51100% (1)
- On Fire: The (Burning) Case for a Green New DealDe la EverandOn Fire: The (Burning) Case for a Green New DealEvaluare: 4 din 5 stele4/5 (74)
- Positive Release FormDocument2 paginiPositive Release FormFloreid100% (3)
- Team of Rivals: The Political Genius of Abraham LincolnDe la EverandTeam of Rivals: The Political Genius of Abraham LincolnEvaluare: 4.5 din 5 stele4.5/5 (234)
- Caricom LabellingDocument15 paginiCaricom LabellingFloreidÎncă nu există evaluări
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaDe la EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaEvaluare: 4.5 din 5 stele4.5/5 (266)
- Fire Safety Fill Out FormDocument3 paginiFire Safety Fill Out FormFloreidÎncă nu există evaluări
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersDe la EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersEvaluare: 4.5 din 5 stele4.5/5 (344)
- Eating OutDocument1 paginăEating OutFloreidÎncă nu există evaluări
- Regional QUality STandard For PinesDocument19 paginiRegional QUality STandard For PinesFloreidÎncă nu există evaluări
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyDe la EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyEvaluare: 3.5 din 5 stele3.5/5 (2259)
- Factors Affecting Pineapple Quality KPIs 2014Document116 paginiFactors Affecting Pineapple Quality KPIs 2014Floreid100% (1)
- PostHarvest Technology - Topic 1 IntroductionDocument1 paginăPostHarvest Technology - Topic 1 IntroductionFloreidÎncă nu există evaluări
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreDe la EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreEvaluare: 4 din 5 stele4/5 (1090)
- Pineapple Sub SectionsDocument1 paginăPineapple Sub SectionsFloreidÎncă nu există evaluări
- Management Review TrainingDocument1 paginăManagement Review TrainingFloreidÎncă nu există evaluări
- AnnuallyDocument70 paginiAnnuallyFloreidÎncă nu există evaluări
- The Unwinding: An Inner History of the New AmericaDe la EverandThe Unwinding: An Inner History of the New AmericaEvaluare: 4 din 5 stele4/5 (45)
- PostHarvest Technology - Module ObjectivesDocument1 paginăPostHarvest Technology - Module ObjectivesFloreidÎncă nu există evaluări
- MA871Document16 paginiMA871Robert SchiemannÎncă nu există evaluări
- Packaging Approval ChecklistDocument2 paginiPackaging Approval ChecklistFloreid100% (2)
- Sampling Procedure - CoffeeDocument4 paginiSampling Procedure - CoffeeFloreid100% (1)
- Coffee Working Group - Aug 27 2014Document51 paginiCoffee Working Group - Aug 27 2014FloreidÎncă nu există evaluări
- Interview Evaluation Form - S. GrahamDocument3 paginiInterview Evaluation Form - S. GrahamFloreidÎncă nu există evaluări
- Acc Activity1 HandsonexperimentsDocument11 paginiAcc Activity1 HandsonexperimentsFloreidÎncă nu există evaluări
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)De la EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Evaluare: 4.5 din 5 stele4.5/5 (121)
- Document Issue Sheet ExampleDocument1 paginăDocument Issue Sheet Examplealleagles2025Încă nu există evaluări
- Whitepaper - Automated Audit ManagementDocument6 paginiWhitepaper - Automated Audit ManagementFloreidÎncă nu există evaluări
- CBEU Service ConditionsDocument623 paginiCBEU Service ConditionsAtul ModiÎncă nu există evaluări
- Mycotoxin in Food Supply Chain (Peanuts)Document2 paginiMycotoxin in Food Supply Chain (Peanuts)Ghanthimathi GvsÎncă nu există evaluări
- Medical Records in Family PracticeDocument22 paginiMedical Records in Family PracticenurfadillahÎncă nu există evaluări
- Kyocera Fleet Services White Paper: SecurityDocument20 paginiKyocera Fleet Services White Paper: SecurityHoratiu OanaÎncă nu există evaluări
- Basics of Fire SprinklerDocument21 paginiBasics of Fire SprinklerLeo_1982Încă nu există evaluări
- BQ - Electrical Calibration Relay Bld803, NPBDocument2 paginiBQ - Electrical Calibration Relay Bld803, NPBKazuya KasumiÎncă nu există evaluări
- Lichens - Naturally Scottish (Gilbert 2004) PDFDocument46 paginiLichens - Naturally Scottish (Gilbert 2004) PDF18Delta100% (1)
- Solar Refrigeration: Prepared by M.DevakumarDocument21 paginiSolar Refrigeration: Prepared by M.DevakumarEasy StudyÎncă nu există evaluări
- Syllabus For Bachelor of Physiotherapy (BPT) Academic ProgrammeDocument36 paginiSyllabus For Bachelor of Physiotherapy (BPT) Academic ProgrammevikasmaeÎncă nu există evaluări
- Her Body and Other Parties: StoriesDe la EverandHer Body and Other Parties: StoriesEvaluare: 4 din 5 stele4/5 (821)
- 2133 Rla RlvaDocument2 pagini2133 Rla RlvaAgung SubangunÎncă nu există evaluări
- Ds0h Ufaa68 ProposalDocument11 paginiDs0h Ufaa68 Proposaledward baskaraÎncă nu există evaluări
- Transfer and Business Taxation SyllabusDocument5 paginiTransfer and Business Taxation SyllabusamqqndeahdgeÎncă nu există evaluări
- Mid Day Meal Scheme-Case Study of BiharDocument4 paginiMid Day Meal Scheme-Case Study of BiharKaran singh RautelaÎncă nu există evaluări
- Finite Element Analysis Project ReportDocument22 paginiFinite Element Analysis Project ReportsaurabhÎncă nu există evaluări
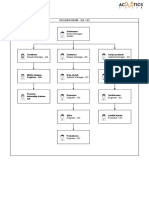
- Organogram - Qa / QC: Srinivasan SrinivasanDocument4 paginiOrganogram - Qa / QC: Srinivasan SrinivasanGowtham VenkatÎncă nu există evaluări
- Q1. (A) The Diagram Shows A Microphone Being Used To Detect The Output From ADocument10 paginiQ1. (A) The Diagram Shows A Microphone Being Used To Detect The Output From ASivmi MalishaÎncă nu există evaluări
- Unit-3.1.2-Sleeve and Cotter JointDocument18 paginiUnit-3.1.2-Sleeve and Cotter JointAsvath Guru100% (2)
- Heart Sounds: Presented by Group 2A & 3ADocument13 paginiHeart Sounds: Presented by Group 2A & 3AMeow Catto100% (1)
- Comparison and Contrast Essay FormatDocument5 paginiComparison and Contrast Essay Formattxmvblaeg100% (2)
- Crime Data Analysis 1Document2 paginiCrime Data Analysis 1kenny laroseÎncă nu există evaluări
- Benzil PDFDocument5 paginiBenzil PDFAijaz NawazÎncă nu există evaluări
- PEOPLE V JAURIGUE - Art 14 Aggravating CircumstancesDocument2 paginiPEOPLE V JAURIGUE - Art 14 Aggravating CircumstancesLady Diana TiangcoÎncă nu există evaluări
- Entitlement Cure SampleDocument34 paginiEntitlement Cure SampleZondervan100% (1)
- EIL Document On Motor, PanelDocument62 paginiEIL Document On Motor, PanelArindam Samanta100% (1)
- Goals in LifeDocument4 paginiGoals in LifeNessa Layos MorilloÎncă nu există evaluări
- Project Management A Technicians Guide Staples TOCDocument5 paginiProject Management A Technicians Guide Staples TOCAnonymous NwnJNO0% (3)
- Women and ViolenceDocument8 paginiWomen and ViolenceStyrich Nyl AbayonÎncă nu există evaluări
- Village Survey Form For Project Gaon-Setu (Village Questionnaire)Document4 paginiVillage Survey Form For Project Gaon-Setu (Village Questionnaire)Yash Kotadiya100% (2)
- Join Our Telegram Channel: @AJITLULLA: To Get Daily Question Papers & SolutionsDocument24 paginiJoin Our Telegram Channel: @AJITLULLA: To Get Daily Question Papers & SolutionsNaveen KumarÎncă nu există evaluări
- Education in America: The Dumbing Down of The U.S. Education SystemDocument4 paginiEducation in America: The Dumbing Down of The U.S. Education SystemmiichaanÎncă nu există evaluări
- The Layman's Guide GDPR Compliance for Small Medium BusinessDe la EverandThe Layman's Guide GDPR Compliance for Small Medium BusinessEvaluare: 5 din 5 stele5/5 (1)
- (ISC)2 CISSP Certified Information Systems Security Professional Official Study GuideDe la Everand(ISC)2 CISSP Certified Information Systems Security Professional Official Study GuideEvaluare: 2.5 din 5 stele2.5/5 (2)
- Internal Audit Checklists: Guide to Effective AuditingDe la EverandInternal Audit Checklists: Guide to Effective AuditingÎncă nu există evaluări
- Building a World-Class Compliance Program: Best Practices and Strategies for SuccessDe la EverandBuilding a World-Class Compliance Program: Best Practices and Strategies for SuccessÎncă nu există evaluări
- A Step By Step Guide: How to Perform Risk Based Internal Auditing for Internal Audit BeginnersDe la EverandA Step By Step Guide: How to Perform Risk Based Internal Auditing for Internal Audit BeginnersEvaluare: 4.5 din 5 stele4.5/5 (11)