Documente Academic
Documente Profesional
Documente Cultură
Assignment 1
Încărcat de
khushi_3290 evaluări0% au considerat acest document util (0 voturi)
61 vizualizări1 paginăDepartment of Computer Engineering Data Compression (CE 705)
Assignment No: 1 Information Theory Concepts
Last Date of Submission: 11/09/2010 Questions: 1. Compare & Differentiate Data Compression & Encryption process .(5) 2. Compare Fix length coding & Variable length coding. (4) 3. If Data completely fits into a model then do we require coding?(Y/N) justify your answer with example. (4) 4. How to choose modelling & coding algorithms? Does if depend on nature of data? (5) 5. A Code that is not
Drepturi de autor
© Attribution Non-Commercial (BY-NC)
Formate disponibile
DOC, PDF, TXT sau citiți online pe Scribd
Partajați acest document
Partajați sau inserați document
Vi se pare util acest document?
Este necorespunzător acest conținut?
Raportați acest documentDepartment of Computer Engineering Data Compression (CE 705)
Assignment No: 1 Information Theory Concepts
Last Date of Submission: 11/09/2010 Questions: 1. Compare & Differentiate Data Compression & Encryption process .(5) 2. Compare Fix length coding & Variable length coding. (4) 3. If Data completely fits into a model then do we require coding?(Y/N) justify your answer with example. (4) 4. How to choose modelling & coding algorithms? Does if depend on nature of data? (5) 5. A Code that is not
Drepturi de autor:
Attribution Non-Commercial (BY-NC)
Formate disponibile
Descărcați ca DOC, PDF, TXT sau citiți online pe Scribd
0 evaluări0% au considerat acest document util (0 voturi)
61 vizualizări1 paginăAssignment 1
Încărcat de
khushi_329Department of Computer Engineering Data Compression (CE 705)
Assignment No: 1 Information Theory Concepts
Last Date of Submission: 11/09/2010 Questions: 1. Compare & Differentiate Data Compression & Encryption process .(5) 2. Compare Fix length coding & Variable length coding. (4) 3. If Data completely fits into a model then do we require coding?(Y/N) justify your answer with example. (4) 4. How to choose modelling & coding algorithms? Does if depend on nature of data? (5) 5. A Code that is not
Drepturi de autor:
Attribution Non-Commercial (BY-NC)
Formate disponibile
Descărcați ca DOC, PDF, TXT sau citiți online pe Scribd
Sunteți pe pagina 1din 1
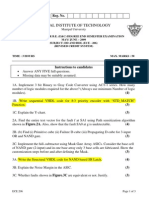
Department of Computer Engineering
Data Compression (CE 705)
Assignment No: 1 Information Theory Concepts
Date: 28/08/2010 Last Date of Submission: 11/09/2010
Questions:
1. Compare & Differentiate Data Compression & Encryption process .(5)
2. Compare Fix length coding & Variable length coding. (4)
3. If Data completely fits into a model then do we require coding?(Y/N) justify your answer with
example. (4)
4. How to choose modelling & coding algorithms? Does if depend on nature of data? (5)
5. A Code that is not prefix but is can be UDC Code. (T/F)Justify your answer with example. (5)
6. What is an instantaneous code? Answer with example. (4)
7. Write a algorithm for checking whether the code is UDC or not.(5)
8. Write a algorithm for checking whether the code is PREFIX or not.(5)
9. A source contains 2n symbols with equal probability. Prove that if error rate is more than (1/n)%,
then no data can be recovered with accuracy. (5)
10. Check whether the code are PREFIX & UDC or not: (5)
a. {00,010,001,0001}
b. {0,100, 1001}
c. {10,010,0110}
d. {111,1110,10111}
e. {0,10,110,1110,11110}
11. Derive equations for Compression Ratio, Redundancy Removed & Redundancy still there after
compression.(3)
12. Classify Data compression Algorithms. (4)
13. Is it possible that a code for a symbol remains same all the times or it can change also? Justify.
(4)
14. If there are 2n symbols with equal probability and initially n bit is assigned then Huffman does
not compress the data. (T/F) Justify the answer. (5)
15. Define terms: (5)
a. Variable Length Code (VLC)
b. Fixed Length Code (FLC)
c. Variable Code (VC).
d. Prefix Code
e. UDC Code
16. Find 1st Order Entropy , Average Length, Compression Ratio, Redundancy ( Removed)
,Redundancy (Still There) for following set of Data:
a. A(0.9), B(0.1)
b. A(0.7), B(0.3)
c. A (0.2), B (0.2), C (0.2), D (0.2), E (0.2).
d. A (0.4), B (0.3), C (0.15), D (0.1), E (0.05).
e. A (0.5), B (0.25), C (0.125), D (0.0625), E (0.0625).
f. A(0.45), B (0.45), C(0.1)
Comment on the results in each case. Numbers in brackets denotes probabilities. Assume 8 Bit ASCII
code initially.(2-3 for each)
S-ar putea să vă placă și
- Department of Information Technology Even Semester Dec 2015-Apr 2016 Model ExaminationDocument4 paginiDepartment of Information Technology Even Semester Dec 2015-Apr 2016 Model ExaminationVicter PaulÎncă nu există evaluări
- 2013 AL ICT Model Paper English at Apepanthiya - LKDocument24 pagini2013 AL ICT Model Paper English at Apepanthiya - LKprasannaÎncă nu există evaluări
- Gate Book - CseDocument291 paginiGate Book - Cseadityabaid4100% (3)
- PgtrbcomputerscienceDocument99 paginiPgtrbcomputerscienceDesperado Manogaran MÎncă nu există evaluări
- Department of Information Technology Information Theory and Coding Question Bank Unit-I Part - ADocument6 paginiDepartment of Information Technology Information Theory and Coding Question Bank Unit-I Part - ABalaji MuthukrishnanÎncă nu există evaluări
- General Certificate of Education (Advanced Level) Support Seminar-2013Document24 paginiGeneral Certificate of Education (Advanced Level) Support Seminar-2013hemacrcÎncă nu există evaluări
- Final Exam DataCommDocument7 paginiFinal Exam DataCommSandeep KumarÎncă nu există evaluări
- Not Expected From RohitDocument358 paginiNot Expected From RohitSachin GuptaÎncă nu există evaluări
- SAS Base DumpsDocument31 paginiSAS Base DumpsMahesh Kumar Joshi100% (5)
- Channel Coding ExerciseDocument13 paginiChannel Coding ExerciseSalman ShahÎncă nu există evaluări
- CryptoGraphy Exam PaperDocument8 paginiCryptoGraphy Exam PaperMesincahaya Masa KagebunshinÎncă nu există evaluări
- Advanced Embedded Systems (10EC118)Document2 paginiAdvanced Embedded Systems (10EC118)Shashank HollaÎncă nu există evaluări
- Matrix Codes: Multiple Bit Upsets Tolerant Method For SRAM MemoriesDocument9 paginiMatrix Codes: Multiple Bit Upsets Tolerant Method For SRAM Memoriessri deviÎncă nu există evaluări
- DS 432 Assignment I 2020Document7 paginiDS 432 Assignment I 2020sristi agrawalÎncă nu există evaluări
- 2 - Programming and Data Structures PDFDocument224 pagini2 - Programming and Data Structures PDFRishendra saiÎncă nu există evaluări
- CN Lab Manual-MinDocument37 paginiCN Lab Manual-Minabcx76605Încă nu există evaluări
- Automata Theory Questions and Answers - Finite Automata-IntroductionDocument278 paginiAutomata Theory Questions and Answers - Finite Automata-IntroductionSachin GuptaÎncă nu există evaluări
- MCQ EdugripDocument109 paginiMCQ EdugripArasanfiveStevenÎncă nu există evaluări
- 計概Q1Document11 pagini計概Q1楊喻妃Încă nu există evaluări
- Test Bank to Accompany Computers Data and ProcessingDe la EverandTest Bank to Accompany Computers Data and ProcessingÎncă nu există evaluări
- NSC 2007Document5 paginiNSC 2007andhracollegesÎncă nu există evaluări
- Semester - Iv PDFDocument12 paginiSemester - Iv PDFGeetaÎncă nu există evaluări
- Dea-1tt5 V12.35Document36 paginiDea-1tt5 V12.35Elie El Masry100% (1)
- AES MidSem 2011-12Q&ADocument2 paginiAES MidSem 2011-12Q&Aprashantgemini1973Încă nu există evaluări
- Institute of Engineering Studies (IES Bangalore) Cse Mock Test-IDocument12 paginiInstitute of Engineering Studies (IES Bangalore) Cse Mock Test-IInstitute of Engineering Studies (IES)100% (1)
- Computing QuestionsDocument33 paginiComputing QuestionsbabaisandipÎncă nu există evaluări
- Reed Solomon Code ThesisDocument5 paginiReed Solomon Code ThesisBuyALiteratureReviewPaperLittleRock100% (2)
- IT2302-Information Theory and CodingDocument9 paginiIT2302-Information Theory and CodingRakesh InaniÎncă nu există evaluări
- Class 9 Syllabus & Sample QuestionsDocument3 paginiClass 9 Syllabus & Sample QuestionsscribdsahilÎncă nu există evaluări
- Computer Science MQP II Pu 2023-24 Version.Document4 paginiComputer Science MQP II Pu 2023-24 Version.Pavan Kumarv100% (1)
- Cbse QP Sol 2011Document8 paginiCbse QP Sol 2011thiripura sundariÎncă nu există evaluări
- It 2004Document20 paginiIt 2004Navya SriniÎncă nu există evaluări
- End Term Examination: DEC.2014 - JAN.2015 ToDocument1 paginăEnd Term Examination: DEC.2014 - JAN.2015 ToYashika MadanÎncă nu există evaluări
- Neb Grade XiiDocument20 paginiNeb Grade XiiSamjhana LamaÎncă nu există evaluări
- JUNE 2011: Amiete - Cs/It (Old Scheme)Document3 paginiJUNE 2011: Amiete - Cs/It (Old Scheme)Justin TiataniaÎncă nu există evaluări
- Hamming Code PDFDocument4 paginiHamming Code PDFFind ProgrammerÎncă nu există evaluări
- MCS 012Document118 paginiMCS 012SongYak YamÎncă nu există evaluări
- Data CompressionDocument2 paginiData CompressionayaanÎncă nu există evaluări
- DD and HDL (ECE - 206) RCSDocument3 paginiDD and HDL (ECE - 206) RCSShailendra Kumar TiwariÎncă nu există evaluări
- 計概Q3Document43 pagini計概Q3楊喻妃Încă nu există evaluări
- Jan10 RTSDocument1 paginăJan10 RTSSrikanth SridharÎncă nu există evaluări
- CU-2021 B.Sc. (Honours) Computer Science Semester-IV Paper-CC-10 QPDocument2 paginiCU-2021 B.Sc. (Honours) Computer Science Semester-IV Paper-CC-10 QPKuntalMukherjeeÎncă nu există evaluări
- Computer Science 2013Document3 paginiComputer Science 2013Mansoor Ali KhanÎncă nu există evaluări
- MCS 042 Previous Year Question Papers by IgnouassignmentguruDocument58 paginiMCS 042 Previous Year Question Papers by IgnouassignmentguruAbhi kumarÎncă nu există evaluări
- (COMP5214) (2021) (S) Midterm Cmu63l 15021Document9 pagini(COMP5214) (2021) (S) Midterm Cmu63l 15021ferdyÎncă nu există evaluări
- Design for Testability, Debug and Reliability: Next Generation Measures Using Formal TechniquesDe la EverandDesign for Testability, Debug and Reliability: Next Generation Measures Using Formal TechniquesÎncă nu există evaluări
- CS-504D Wbut QuestionsDocument7 paginiCS-504D Wbut QuestionsBikram BanickÎncă nu există evaluări
- Smart Test Series: 1-Circle The Correct One. (15x1 15)Document3 paginiSmart Test Series: 1-Circle The Correct One. (15x1 15)Zaheer AhmedÎncă nu există evaluări
- Nso Science Olympiad Sample Question Paper 1 Class 10Document22 paginiNso Science Olympiad Sample Question Paper 1 Class 10Technical AyushÎncă nu există evaluări
- Thapar Institute of Engineering & Technology, Patiala: End Semester Examination (May 2019)Document4 paginiThapar Institute of Engineering & Technology, Patiala: End Semester Examination (May 2019)Forza HorizonÎncă nu există evaluări
- Computing and Informatics - An203/Ad303: Postal Test Paper - 2 MARKS:100 DURATION:3 HoursDocument1 paginăComputing and Informatics - An203/Ad303: Postal Test Paper - 2 MARKS:100 DURATION:3 HourskaviatchennaiÎncă nu există evaluări
- Part One-40 Part Two - 60Document12 paginiPart One-40 Part Two - 60api-3782519Încă nu există evaluări
- CISSP Exam Prep Questions, Answers & Explanations: 1500+ CISSP Practice Questions with SolutionsDe la EverandCISSP Exam Prep Questions, Answers & Explanations: 1500+ CISSP Practice Questions with SolutionsEvaluare: 3 din 5 stele3/5 (7)
- CCNA Interview Questions You'll Most Likely Be AskedDe la EverandCCNA Interview Questions You'll Most Likely Be AskedÎncă nu există evaluări
- Outline The Main Business Applications of Mobile Computing and Describe The Importance of These Applications in The Wireless Business Domain. Answer Mobile ComputingDocument3 paginiOutline The Main Business Applications of Mobile Computing and Describe The Importance of These Applications in The Wireless Business Domain. Answer Mobile ComputingVikram KumarÎncă nu există evaluări
- VedHymns p2 PDFDocument529 paginiVedHymns p2 PDFKamakshi Kripa KendraÎncă nu există evaluări
- New Text DocumentDocument30 paginiNew Text DocumentKumarSonuÎncă nu există evaluări
- HP LaserJet Enterprise M607, M608, M609, M610, M611, M612, HP LaserJet Managed E60055, E60065Document72 paginiHP LaserJet Enterprise M607, M608, M609, M610, M611, M612, HP LaserJet Managed E60055, E60065Alves Carvalho100% (1)
- New PPT Nursing InfromaticsDocument35 paginiNew PPT Nursing InfromaticsSusi SeptianiÎncă nu există evaluări
- The Linux Command Line Cheat SheetDocument4 paginiThe Linux Command Line Cheat SheetFernÎncă nu există evaluări
- Electrical Engineering 4-Year Plan 2022Document1 paginăElectrical Engineering 4-Year Plan 2022Diana Paola Molina RodríguezÎncă nu există evaluări
- Using The WAGO 750-340 PROFINET Coupler As Remote I/O With A Siemens S7 PLCDocument30 paginiUsing The WAGO 750-340 PROFINET Coupler As Remote I/O With A Siemens S7 PLCMeryem asouabÎncă nu există evaluări
- Digital Library System ProjectDocument2 paginiDigital Library System ProjectChala GetaÎncă nu există evaluări
- XTran R4.7.2 TXCare Quick Installation GuideDocument10 paginiXTran R4.7.2 TXCare Quick Installation GuideRiky FitriadiÎncă nu există evaluări
- Computer Operating SystemDocument9 paginiComputer Operating SystemamshahidÎncă nu există evaluări
- Phishing Email Detection AbstractDocument8 paginiPhishing Email Detection AbstractTunnu SunnyÎncă nu există evaluări
- Backend Assignment - Dream11Document2 paginiBackend Assignment - Dream11Priyanka mestryÎncă nu există evaluări
- Integration of Cellular and WiFi Networks 9.25.13 - 4G AmericasDocument65 paginiIntegration of Cellular and WiFi Networks 9.25.13 - 4G Americaslouie mabiniÎncă nu există evaluări
- Text Mining in Cybersecurity A SystematicDocument36 paginiText Mining in Cybersecurity A SystematicRafael PaimÎncă nu există evaluări
- Lab Report 2 - Wireless Communication Systems Using BluetoothDocument4 paginiLab Report 2 - Wireless Communication Systems Using BluetoothDANIELA INZUNZAÎncă nu există evaluări
- Session 1 M.I.S Class KoDocument27 paginiSession 1 M.I.S Class KoRoland John MarzanÎncă nu există evaluări
- Red Hat Enterprise Linux-6-Identity Management Guide-En-USDocument446 paginiRed Hat Enterprise Linux-6-Identity Management Guide-En-USSushant KhandelwalÎncă nu există evaluări
- SRDF Replication: SRDF Synchronous (SRDF/S) SRDF Asynchronous (SRDF/A)Document6 paginiSRDF Replication: SRDF Synchronous (SRDF/S) SRDF Asynchronous (SRDF/A)Phani KumarÎncă nu există evaluări
- AZ-900 StudyGuide ENU FY23Q1 10.07Document2 paginiAZ-900 StudyGuide ENU FY23Q1 10.07jeppoo1Încă nu există evaluări
- Author: Udeh Cornelius MATRIC NO: 11/0179Document10 paginiAuthor: Udeh Cornelius MATRIC NO: 11/0179Nkindi Fiston100% (1)
- Cyber SecurityDocument117 paginiCyber Securitybeautyofnature142Încă nu există evaluări
- Network Security TutorialDocument76 paginiNetwork Security Tutorial20IF131NaikSiddheshÎncă nu există evaluări
- 81819-ISE Posture Configuration ExerciseDocument81 pagini81819-ISE Posture Configuration ExerciseNguyen LeÎncă nu există evaluări
- Splunk - Data - Assessment 2022 11 15Document24 paginiSplunk - Data - Assessment 2022 11 15Vijay JoshiÎncă nu există evaluări
- Empowerment Technology ReviewerDocument4 paginiEmpowerment Technology ReviewereukiÎncă nu există evaluări
- Sample Acceptable Email Use PolicyDocument2 paginiSample Acceptable Email Use PolicyAshokÎncă nu există evaluări
- Data Act ImplicationsDocument5 paginiData Act ImplicationsoshashÎncă nu există evaluări
- Types of Computer LanguagesDocument9 paginiTypes of Computer LanguagesArushi SinghÎncă nu există evaluări
- E Learning PPT Chapter1Document24 paginiE Learning PPT Chapter1Burhanuddin MohammadÎncă nu există evaluări