Documente Academic
Documente Profesional
Documente Cultură
2007 11 08 Larry Clinton ISA Overview For International Businesses
Încărcat de
isallianceDescriere originală:
Titlu original
Drepturi de autor
Formate disponibile
Partajați acest document
Partajați sau inserați document
Vi se pare util acest document?
Este necorespunzător acest conținut?
Raportați acest documentDrepturi de autor:
Formate disponibile
2007 11 08 Larry Clinton ISA Overview For International Businesses
Încărcat de
isallianceDrepturi de autor:
Formate disponibile
The Evolving Cyber Threat
and what businesses can do about it
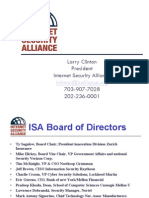
Larry Clinton, President
Direct 703/907-7028
lclinton@isalliance.org
Founders
Our Partners
The Old Web
The Web Today
Source: http://cm.bell-labs.com/who/ches/map/gallery/index.html
The Earlier Threat:
Growth in vulnerabilities (CERT/cc)
4,500 4,000 3,500 3,000 2,500 2,000 1,500 1,000 500 171 0
345 311 262 417 1,090 2,437 4,129
1995
2002
The Earlier Threat:
Cyber incidents
120000
110,000
100000 80000
55,100
60000 40000
21,756
20000
6 132 252 406 773 1,334 2,340 2,412 2,573 2,134 3,734 9,859
0 1988 1989 1990 1991 1992 1993 1994 1995 1996 1997 1998 1999 2000 2001 2002
The Changing Threat
A fast-moving virus or worm pandemic is not the threat it was...
2002-2004 almost 100 medium-to-high risk attacks (Slammer; SoBig). 2005, there were only 6 2006 and 2007.. Zero
The Threat Landscape is Changing
Early Attacks
Who: Kids, researchers, hackers, isolated criminals Why: Seeking fame & glory, use widespread attacks for maximum publicity Risk Exposure: Downtime, business disruption, information loss, defacement
New Era Attacks
Organized criminals, corporate spies, disgruntled employees, terrorists Seeking profits, revenge, use targeted stealth attacks to avoid detection Direct financial loss via theft and/or embezzlement, breach disclosure, IP compromised, business disruption, infrastructure failure
The Threat Landscape is Changing
Early Attacks
Defense: Reactive AV signatures Recovery: Scan & remove Type: Virus, worm, spyware
New Era Attacks
Multilayer pre-emptive and behavioral systems System wide, sometimes impossible without re-image of system Targeted malware, root kits, spear phishing, ransomware, denial of service, back door taps, trojans, IW
Digital Defense? Maybe Not
29% of Senior Executives acknowledged that they did not know how many negative security events they had in the past year 50% of Senior Executives said they did not know how much money was lost due to attacks
Source: PricewaterhouseCoopers survey of 7,000 companies 9/06
Digital Defense Not So Much
23% of CTOs did not know if cyber losses were covered by insurance. 34% of CTOs thought cyber losses would be covered by insurance----and were wrong. The biggest network vulnerability in American corporations are extra connections added for senior executives without proper security.
---Source: DHS Chief Economist Scott Borg
Percentage of Participants Who Experienced an Insider Incident
100 80 60 40 20 0 41 39 55
2004
2005
2006
Insider Incidents - 2006
Total (%) Theft of IP Theft of Proprietary Info. Sabotage 30 36 33 Insider (%) 63 56 49 Outsider (%) 45 49 41
Most common insider incidents in 2006 survey: rogue wireless access points (72%), theft of IP (64%), exposure of sensitive or confidential information (56%) In 2006 insiders committed more theft of IP & proprietary information and sabotage than outsiders!
Economic Effects of Attacks
25% of our wealth---$3 trillion---is transmitted over the Internet daily FBI: Cyber crime cost business $26 billion (probably LOW estimate) Financial Institutions are generally considered the safest---their losses were up 450% in the last year There are more electronic financial transfers than paper checks now: Only 1% of cyber crooks are caught.
Cyber Attacks Effect Stock Price
Investigations into the stock price impact of cyber attacks show that identified target firms suffer losses of one to five percent in the days after an attack. For the average NYSE corporation, price drops of these magnitudes translate into shareholder losses between $50 and $200 million.
Source: US Congressional Research Service 2004
Indirect Economic Effects
While the tangible effects of a security incident can be measured in terms of lost productivity and staff time to recover and restore systems, the intangible effects can be of an order of magnitude larger. Intangible effects include the impact on an organizations trust relationships, harm to its reputation, and loss of economical and society confidence
Source Carnegie Mellon CyLab 2007
S-ar putea să vă placă și
- Dark Web Market Price Index Hacking Tools July 2018 Top10VPN2Document7 paginiDark Web Market Price Index Hacking Tools July 2018 Top10VPN2AppTest PI88% (8)
- Apple Platform Security GuideDocument196 paginiApple Platform Security Guideazm9sÎncă nu există evaluări
- White Paper - Protecting SAP Systems From Cyber Attack PDFDocument42 paginiWhite Paper - Protecting SAP Systems From Cyber Attack PDFDan ArgynovÎncă nu există evaluări
- Cyber Security 3Document11 paginiCyber Security 3Saeed FaÎncă nu există evaluări
- ASTRIDE BasedThreatModelforTelehealthSystemsDocument16 paginiASTRIDE BasedThreatModelforTelehealthSystemsfernando PalloÎncă nu există evaluări
- A Study of Current Scenario of Cyber Security Practices and Measures: Literature ReviewDocument8 paginiA Study of Current Scenario of Cyber Security Practices and Measures: Literature ReviewattaullahÎncă nu există evaluări
- Pentestreport RomioDocument72 paginiPentestreport Romioapi-508435779Încă nu există evaluări
- Cisco Next-Generation Security Solutions PDFDocument371 paginiCisco Next-Generation Security Solutions PDFYrving Blanco100% (1)
- Social Engineering Techniques PDFDocument4 paginiSocial Engineering Techniques PDFiuliannitescu4817Încă nu există evaluări
- TR EB Cybersec Career2Document10 paginiTR EB Cybersec Career2RothÎncă nu există evaluări
- Unit-5 Cybersecurity: Organizational Implications: IV-II SEM CSE, Cyber Security Unit - VDocument13 paginiUnit-5 Cybersecurity: Organizational Implications: IV-II SEM CSE, Cyber Security Unit - VLakshmi Narayana ReddyÎncă nu există evaluări
- Cyber SecurityDocument55 paginiCyber SecurityRishi Shakya100% (1)
- Ebook - A Complete Guide To CybersecurityDocument29 paginiEbook - A Complete Guide To CybersecuritydsaÎncă nu există evaluări
- Exam SC 900 Microsoft Security Compliance and Identity Fundamentals Skills MeasuredDocument9 paginiExam SC 900 Microsoft Security Compliance and Identity Fundamentals Skills Measuredzawzaw htetÎncă nu există evaluări
- PenTest Magazine Mobile PentestingDocument34 paginiPenTest Magazine Mobile PentestingsonyÎncă nu există evaluări
- Blockchain and Digital Identity: The Path To Self Sovereign IdentityDocument22 paginiBlockchain and Digital Identity: The Path To Self Sovereign IdentitySanada4realÎncă nu există evaluări
- Threat IdentificationDocument4 paginiThreat IdentificationSyifa HusnaÎncă nu există evaluări
- 2008 05 25 Larry Clinton Financial Risk Management Presentation For Unnamed NYC EventDocument11 pagini2008 05 25 Larry Clinton Financial Risk Management Presentation For Unnamed NYC EventisallianceÎncă nu există evaluări
- 2008 11 19 Larry Clinton ISA Overview and International Outreach To PortugalDocument34 pagini2008 11 19 Larry Clinton ISA Overview and International Outreach To PortugalisallianceÎncă nu există evaluări
- 2008 06 07 Larry Clinton Rochester Presentation About Evolving Threat and Best PracticesDocument38 pagini2008 06 07 Larry Clinton Rochester Presentation About Evolving Threat and Best PracticesisallianceÎncă nu există evaluări
- Cyber Security - Organizational ImplicationsDocument40 paginiCyber Security - Organizational Implications245120737162Încă nu există evaluări
- Deloitte - Cyber Crime - 2010Document16 paginiDeloitte - Cyber Crime - 2010lacengearÎncă nu există evaluări
- 2011 11 09 Larry Clinton BrightTalk Webinars Evolution of Cyber Threats and Pub PolicyDocument45 pagini2011 11 09 Larry Clinton BrightTalk Webinars Evolution of Cyber Threats and Pub PolicyisallianceÎncă nu există evaluări
- The Changing Threat: PlenaDocument52 paginiThe Changing Threat: Plenajo1327Încă nu există evaluări
- Banking Cyber Security TechniquesDocument42 paginiBanking Cyber Security Techniques89kdsbzdtmÎncă nu există evaluări
- 2010 01 15 Larry Clinton CSC Presentation On The Social ContractDocument33 pagini2010 01 15 Larry Clinton CSC Presentation On The Social ContractisallianceÎncă nu există evaluări
- Unit 5Document15 paginiUnit 5Gangisetti SrihariÎncă nu există evaluări
- Cyber Security - OrganisationDocument21 paginiCyber Security - OrganisationShambhu Kumar singhÎncă nu există evaluări
- Identificarea AmenintarilorDocument3 paginiIdentificarea AmenintarilorCretu CalinÎncă nu există evaluări
- 2011 12 02 Larry Clinton Cyber Risk and Data Breach Management Summit Presentation in NYC About PWC Study APTDocument31 pagini2011 12 02 Larry Clinton Cyber Risk and Data Breach Management Summit Presentation in NYC About PWC Study APTisallianceÎncă nu există evaluări
- Research ProjectDocument11 paginiResearch Projectapi-727439988Încă nu există evaluări
- Cyberattacks Against State and Local Governments SurgeDocument2 paginiCyberattacks Against State and Local Governments SurgeAzka IhsanÎncă nu există evaluări
- Cyber - Security 19mca05Document35 paginiCyber - Security 19mca05Aliva PatelÎncă nu există evaluări
- CLSR ArticleDocument7 paginiCLSR ArticleAegis GoodÎncă nu există evaluări
- 2009 01 08 Barry Foer and Larry Clinton ISA Comprehensive Overview For Critical Infrastructure Partnership Advisory Council CIPAC PresentationDocument43 pagini2009 01 08 Barry Foer and Larry Clinton ISA Comprehensive Overview For Critical Infrastructure Partnership Advisory Council CIPAC PresentationisallianceÎncă nu există evaluări
- Powered by The: Infoblox Cyber Intelligence UnitDocument30 paginiPowered by The: Infoblox Cyber Intelligence UnitAhmed TantawyÎncă nu există evaluări
- Cyber Law Compliance AuditDocument13 paginiCyber Law Compliance AuditTwinkleÎncă nu există evaluări
- 2011 06 00 Larry Clinton Financial Risk Management Presentation at BeconDocument25 pagini2011 06 00 Larry Clinton Financial Risk Management Presentation at BeconisallianceÎncă nu există evaluări
- 2011 10 05 Larry Clinton Presentation To FERC Staff About Utility Cybersecurity Regulation and APTDocument19 pagini2011 10 05 Larry Clinton Presentation To FERC Staff About Utility Cybersecurity Regulation and APTisallianceÎncă nu există evaluări
- 2010 04 02 Larry Clinton Aviation Week PresentationDocument13 pagini2010 04 02 Larry Clinton Aviation Week PresentationisallianceÎncă nu există evaluări
- 2004 01 30 Larry Clinton Hill Briefing On ISA and Insurance Industry Certification ProgramDocument15 pagini2004 01 30 Larry Clinton Hill Briefing On ISA and Insurance Industry Certification ProgramisallianceÎncă nu există evaluări
- The SolarWinds HackDocument3 paginiThe SolarWinds HackAtthulaiÎncă nu există evaluări
- Why Do I Need Cyber Liability InsuranceDocument15 paginiWhy Do I Need Cyber Liability InsuranceFanniÎncă nu există evaluări
- Cyber Security Organizational ImplicationsDocument5 paginiCyber Security Organizational ImplicationsaslamÎncă nu există evaluări
- Network Security EssentialsDocument20 paginiNetwork Security Essentialsturbon2009Încă nu există evaluări
- Social Engineering Case StudyDocument21 paginiSocial Engineering Case StudyazylenbÎncă nu există evaluări
- Cybercrime: Issues, Problems & PreventionDocument87 paginiCybercrime: Issues, Problems & PreventionHimanshu YadavÎncă nu există evaluări
- Information Technology Database System SecurityDocument10 paginiInformation Technology Database System Securitypeter otienoÎncă nu există evaluări
- Green (2015) Cyber Security An Introduction To Non-Technical ManagersDocument264 paginiGreen (2015) Cyber Security An Introduction To Non-Technical ManagersFinneganÎncă nu există evaluări
- Cyber Situational AwarenessDocument10 paginiCyber Situational AwarenessBob KoblovskyÎncă nu există evaluări
- CYB401Document14 paginiCYB401yormie2019Încă nu există evaluări
- 2011 10 13 Larry Clinton CIO Global Forum On APT in DCDocument30 pagini2011 10 13 Larry Clinton CIO Global Forum On APT in DCisallianceÎncă nu există evaluări
- 2004 02 00 Larry Clinton ISA Overview and Philosophy Presentation at Homeland Security Event in FLDocument34 pagini2004 02 00 Larry Clinton ISA Overview and Philosophy Presentation at Homeland Security Event in FLisallianceÎncă nu există evaluări
- Leveraging Agile Project Management for Robust Cybersecurity: A Guide for Leaders & ManagersDe la EverandLeveraging Agile Project Management for Robust Cybersecurity: A Guide for Leaders & ManagersÎncă nu există evaluări
- Webroot FirewallDocument13 paginiWebroot FirewallsinesacurÎncă nu există evaluări
- Cloud Computing Security TutorialDocument68 paginiCloud Computing Security TutorialvarmasalvaÎncă nu există evaluări
- Cyber Security: Threats, Reasons, Challenges, Methodologies and State of The Art Solutions For Industrial ApplicationsDocument6 paginiCyber Security: Threats, Reasons, Challenges, Methodologies and State of The Art Solutions For Industrial ApplicationsnadjamÎncă nu există evaluări
- Cybercrime and The Internet of ThreatsDocument7 paginiCybercrime and The Internet of Threatsmus1402Încă nu există evaluări
- 1.3.1.6 Lab Threat IdentificationDocument2 pagini1.3.1.6 Lab Threat IdentificationTamara Mardari100% (1)
- Cyber Risk Nature of RiskDocument10 paginiCyber Risk Nature of RiskRebeca JiménezÎncă nu există evaluări
- Cybercrime: - Cybercrimes Reach Everywhere and Hurt EveryoneDocument23 paginiCybercrime: - Cybercrimes Reach Everywhere and Hurt EveryonePiyusha SurveÎncă nu există evaluări
- How Hackker Change The World by HackingDocument7 paginiHow Hackker Change The World by HackingSagar KumarÎncă nu există evaluări
- Digital RobberyDocument16 paginiDigital RobberyAakrisht GoelÎncă nu există evaluări
- Ransomware Attack Against Critical InfrastructureDocument3 paginiRansomware Attack Against Critical InfrastructureAtthulaiÎncă nu există evaluări
- Information On Cyber Threats and Risks 20160331Document33 paginiInformation On Cyber Threats and Risks 20160331vdimeskaÎncă nu există evaluări
- 2009 04 26 Larry Clinton ISA Overview Presentation For Ed StullDocument13 pagini2009 04 26 Larry Clinton ISA Overview Presentation For Ed StullisallianceÎncă nu există evaluări
- INSECURE Mag 37 PDFDocument62 paginiINSECURE Mag 37 PDFDimitarÎncă nu există evaluări
- 2010 09 15 Larry Clinton InfraGuard Seminar Providing Leg Update On Effective Collaboration To Protect Critical InfrastructuresDocument25 pagini2010 09 15 Larry Clinton InfraGuard Seminar Providing Leg Update On Effective Collaboration To Protect Critical InfrastructuresisallianceÎncă nu există evaluări
- EU ISA CSCG Position PaperDocument12 paginiEU ISA CSCG Position PaperisallianceÎncă nu există evaluări
- 2009 09 30 Larry Clinton Carnegie Cadet Academy Presentation For EstoniaDocument42 pagini2009 09 30 Larry Clinton Carnegie Cadet Academy Presentation For EstoniaisallianceÎncă nu există evaluări
- Larry Clinton President Internet Security Alliance 703-907-7028Document9 paginiLarry Clinton President Internet Security Alliance 703-907-7028isallianceÎncă nu există evaluări
- The "Phi Project" - The Financial Impact of Breached Protected Health InformationDocument29 paginiThe "Phi Project" - The Financial Impact of Breached Protected Health InformationisallianceÎncă nu există evaluări
- 2011 06 29 Larry Clinton Supply Chain Presentation For The Software Assurance SwA Working GroupDocument14 pagini2011 06 29 Larry Clinton Supply Chain Presentation For The Software Assurance SwA Working GroupisallianceÎncă nu există evaluări
- 2009 00 00 Larry Clinton Brussels Belgium PresentationDocument20 pagini2009 00 00 Larry Clinton Brussels Belgium PresentationisallianceÎncă nu există evaluări
- 2009 10 01 Larry Clinton ISA Overview For Estonian BusinessmenDocument31 pagini2009 10 01 Larry Clinton ISA Overview For Estonian BusinessmenisallianceÎncă nu există evaluări
- 2009 10 02 Larry Clinton ISA Overview Geared To Estonian Foreign Affairs PeopleDocument47 pagini2009 10 02 Larry Clinton ISA Overview Geared To Estonian Foreign Affairs PeopleisallianceÎncă nu există evaluări
- 2009 10 23 Larry Clinton ISA Overview Presentation To NATO Personnel in EstoniaDocument49 pagini2009 10 23 Larry Clinton ISA Overview Presentation To NATO Personnel in EstoniaisallianceÎncă nu există evaluări
- 2004 01 07 Larry Clinton Risk Management and Insurance Presentation For The Institute of Internal of Auditors IIADocument38 pagini2004 01 07 Larry Clinton Risk Management and Insurance Presentation For The Institute of Internal of Auditors IIAisallianceÎncă nu există evaluări
- Larry Clinton President 703-907-7028Document20 paginiLarry Clinton President 703-907-7028isallianceÎncă nu există evaluări
- Internet Security Alliance: Larry Clinton PresidentDocument19 paginiInternet Security Alliance: Larry Clinton PresidentisallianceÎncă nu există evaluări
- 2003 07 24 Larry Clinton Presentation For Org of American States OAS About ISA and Information SharingDocument21 pagini2003 07 24 Larry Clinton Presentation For Org of American States OAS About ISA and Information SharingisallianceÎncă nu există evaluări
- 2003 07 30 Larry Clinton ISA Overview and International Outreach To JapanDocument25 pagini2003 07 30 Larry Clinton ISA Overview and International Outreach To JapanisallianceÎncă nu există evaluări
- 2003 11 13 Larry Clinton India Security Anchor ProposalDocument17 pagini2003 11 13 Larry Clinton India Security Anchor ProposalisallianceÎncă nu există evaluări
- 2004 02 02 Dave McCurdy India PresentationDocument48 pagini2004 02 02 Dave McCurdy India PresentationisallianceÎncă nu există evaluări
- 2003 10 00 Dave McCurdy Risk Management and Insurance Presentation To ManufacturersDocument35 pagini2003 10 00 Dave McCurdy Risk Management and Insurance Presentation To ManufacturersisallianceÎncă nu există evaluări
- 2004 01 30 Larry Clinton Hill Briefing On ISA and Insurance Industry Certification ProgramDocument15 pagini2004 01 30 Larry Clinton Hill Briefing On ISA and Insurance Industry Certification ProgramisallianceÎncă nu există evaluări
- 2010 10 08 Ty Sagalow Public Private Partnership and Risk Tolerance and InsuranceDocument5 pagini2010 10 08 Ty Sagalow Public Private Partnership and Risk Tolerance and InsuranceisallianceÎncă nu există evaluări
- 2009 06 05 Waters Edge Navigating Compliance and Security For Unified Communications PresentationDocument10 pagini2009 06 05 Waters Edge Navigating Compliance and Security For Unified Communications PresentationisallianceÎncă nu există evaluări
- 2009 04 02 Larry Clinton Supply Chain Presentation at The NDIAs DIB CIP ConferenceDocument15 pagini2009 04 02 Larry Clinton Supply Chain Presentation at The NDIAs DIB CIP ConferenceisallianceÎncă nu există evaluări
- 2010 11 30 Larry Clinton Supply Chain Presentation For Critical Infrastructure Protection CIP CongressDocument7 pagini2010 11 30 Larry Clinton Supply Chain Presentation For Critical Infrastructure Protection CIP CongressisallianceÎncă nu există evaluări
- 2007 11 28 Vishant Shah DHS National Cyber Security Divisions NCSDs Control System Security Program PresentationDocument5 pagini2007 11 28 Vishant Shah DHS National Cyber Security Divisions NCSDs Control System Security Program PresentationisallianceÎncă nu există evaluări
- 2009 08 07 Larry Clinton Supply Chain Presentation For GSA in DCDocument18 pagini2009 08 07 Larry Clinton Supply Chain Presentation For GSA in DCisallianceÎncă nu există evaluări
- 2007 11 28 Larry Clinton ISA Overview For Secure Manufacturing in The Age of Globalization WorkshopDocument22 pagini2007 11 28 Larry Clinton ISA Overview For Secure Manufacturing in The Age of Globalization WorkshopisallianceÎncă nu există evaluări
- 2010 00 00 Brent Pressentin Supply Chain Presentation To AIADocument21 pagini2010 00 00 Brent Pressentin Supply Chain Presentation To AIAisallianceÎncă nu există evaluări
- Creating Value From VulnerabilityDocument11 paginiCreating Value From VulnerabilityisallianceÎncă nu există evaluări
- The FBI's Transformation : 1. Counterterrorism 2. Counterintelligence 3. Cyber SecurityDocument4 paginiThe FBI's Transformation : 1. Counterterrorism 2. Counterintelligence 3. Cyber SecurityisallianceÎncă nu există evaluări
- Chapter 1. Introduction To IASDocument32 paginiChapter 1. Introduction To IASSilento GunoÎncă nu există evaluări
- Chapter 3Document8 paginiChapter 3منذر النيهومÎncă nu există evaluări
- (Network Security 2017-Jan Vol. 2017 Iss. 1) Wood, Michael - How To Make SD-WAN Secure (2017) (10.1016 - S1353-4858 (17) 30006-5) - Libgen - LiDocument3 pagini(Network Security 2017-Jan Vol. 2017 Iss. 1) Wood, Michael - How To Make SD-WAN Secure (2017) (10.1016 - S1353-4858 (17) 30006-5) - Libgen - LiElias DendirÎncă nu există evaluări
- Data Dictionary Wedding ManagementDocument18 paginiData Dictionary Wedding ManagementChirag KherÎncă nu există evaluări
- Introduction To CryptographyDocument30 paginiIntroduction To CryptographyHarsh GuptaÎncă nu există evaluări
- How AAA Action WorksDocument1 paginăHow AAA Action WorksJagadeeh ValasapalliÎncă nu există evaluări
- PII, PHI, PCI Data HandlingDocument2 paginiPII, PHI, PCI Data HandlingKhaled SaifÎncă nu există evaluări
- Presentation 1Document3 paginiPresentation 1abishekvsÎncă nu există evaluări
- CEH Exam Blueprint v4.0: EC-CouncilDocument5 paginiCEH Exam Blueprint v4.0: EC-CouncilGustavoBuschÎncă nu există evaluări
- BCC 301 AssignmentDocument2 paginiBCC 301 Assignmentitsm8011Încă nu există evaluări
- A Survey On Various Encryption Techniques: John Justin M, Manimurugan SDocument4 paginiA Survey On Various Encryption Techniques: John Justin M, Manimurugan SUmmama khanÎncă nu există evaluări
- Secure Your PBXDocument23 paginiSecure Your PBXinnovativekaluÎncă nu există evaluări
- The Xtea Cryprology AlgorithmDocument5 paginiThe Xtea Cryprology Algorithmmiki_dudaulÎncă nu există evaluări
- 8 2 Data EncodingDocument17 pagini8 2 Data EncodingJayesh ShindeÎncă nu există evaluări
- Reverse Shell Lockheed Martin Khalil ResearchDocument19 paginiReverse Shell Lockheed Martin Khalil Researchapi-704658175Încă nu există evaluări
- Chapter 6 ModuleDocument11 paginiChapter 6 ModuleJane GonzagaÎncă nu există evaluări
- SecurityFund PPT 1.1Document13 paginiSecurityFund PPT 1.1Fmunoz MunozÎncă nu există evaluări
- Cyber SecurityDocument11 paginiCyber SecurityYogesh PatilÎncă nu există evaluări
- SSH Secure ShellDocument6 paginiSSH Secure ShellfabiobonadiaÎncă nu există evaluări
- 1 Introduction NetworksecurityCryptography 1 2Document22 pagini1 Introduction NetworksecurityCryptography 1 2sumayya shaikÎncă nu există evaluări
- 1 NetiquetteDocument4 pagini1 NetiquetteGlenn M. GonzalesÎncă nu există evaluări