Documente Academic
Documente Profesional
Documente Cultură
MP 75-1996 Strategies For The Implementation of A Public Key Authentication Framework (PKAF) in Australia
Încărcat de
SAI Global - APACTitlu original
Drepturi de autor
Formate disponibile
Partajați acest document
Partajați sau inserați document
Vi se pare util acest document?
Este necorespunzător acest conținut?
Raportați acest documentDrepturi de autor:
Formate disponibile
MP 75-1996 Strategies For The Implementation of A Public Key Authentication Framework (PKAF) in Australia
Încărcat de
SAI Global - APACDrepturi de autor:
Formate disponibile
Miscellaneous Publication
This is a free 14 page sample. Access the full version at http://infostore.saiglobal.com.
Strategies for the implementation of a Public Key Authentication Framework (PKAF) in Australia
SAA MP751996
This is a free 14 page sample. Access the full version at http://infostore.saiglobal.com.
STRATEGIES FOR THE
IMPLEMENTATION OF A PUBLIC KEY AUTHENTICATION FRAMEWORK (PKAF) IN AUSTRALIA
SAA MP751996
PUBLISHED BY STANDARDS AUSTRALIA (STANDARDS ASSOCIATION OF AUSTRALIA) 1 THE CRESCENT, HOMEBUSH, NSW 2140
ISBN 0 7337 0802 1
SAA MP75 1996
Standards Australia
ABSTRACT
As electronic commerce becomes commonplace, there is a growing need for users to ensure that electronic transactions can be validated. Compatible national and international systems of digital signatures are necessary for the introduction of secure electronic commerce. Standards Australia formed the Public Key Authentication Framework (PKAF) Task Group to examine all options for operating a national system for the creation and management of digital signatures as well as being compatible with systems in other
This is a free 14 page sample. Access the full version at http://infostore.saiglobal.com.
countries. This strategy report describes issues and recommendations relevant to Australias businesses and government operations, and also addresses compatibility issues between organizations and private citizens (both locally and internationally). Policy and legal issues are also canvassed.
Copyright
STANDARDS AUSTRALIA
Users of Standards are reminded that copyright subsists in all Standards Australia publications and software. Except where the Copyright Act allows and except where provided for below no publications or software produced by Standards Australia may be reproduced, stored in a retrieval system in any form or transmitted by any means without prior permission in writing from Standards Australia. Permission may be conditional on an appropriate royalty payment. Requests for permission and information on commercial software royalties should be directed to the head office of Standards Australia. Standards Australia will permit up to 10 percent of the technical content pages of a Standard to be copied for use exclusively in-house by purchasers of the Standard without payment of a royalty or advice to Standards Australia. Standards Australia will also permit the inclusion of its copyright material in computer software programs for no royalty payment provided such programs are used exclusively in-house by the creators of the programs. Care should be taken to ensure that material used is from the current edition of the Standard and that it is updated whenever the Standard is amended or revised. The number and date of the Standard should therefore be clearly identified. The use of material in print form or in computer software programs to be used commercially, with or without payment, or in commercial contracts is subject to the payment of a royalty. This policy may be varied by Standards Australia at any time.
Standards Australia
SAA MP75 1996
TABLE OF CONTENTS
1 INTRODUCTION . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 12 1.1 1.2 1.3 1.4
This is a free 14 page sample. Access the full version at http://infostore.saiglobal.com.
Background . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 12 Purpose of a Public Key Authentication Framework . . . . . . . . . . . 12 Scope of the Public Key Authentication Framework (PKAF) . . . . . 13 Standards . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 13
2 TERMINOLOGY . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 15 2.1 2.2 2.3 2.4 2.5 2.6 2.7 2.8 2.9 Certicate . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 15 Certication Authority (CA) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 15 Certication Block . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 15 Digital Signature . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 16 Digitized Signature . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 16 Distinguished Name . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 16 Intermediate Certication Authority (ICA) . . . . . . . . . . . . . . . . . . . 16 Organizational Registration Authority (ORA) . . . . . . . . . . . . . . . . . 16 Policy and Root Registration Authority (PARRA) . . . . . . . . . . . . . . . 16
2.10 Public Key Authentication Framework (PKAF) . . . . . . . . . . . . . . . . 17 2.11 PKAF Infrastructure . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 17 2.12 Revocation of Certicate . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 17 2.13 Trusted . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 17 2.14 Trustedness . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 17 2.15 Valid Certicate . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 18 3 PKAF REQUIREMENTS . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 19 3.1 Summary of Key PKAF Requirements . . . . . . . . . . . . . . . . . . . . . . . 19 3.1.1 User Authentication . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 19 3.1.2 Certication Policies . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 19
SAA MP75 1996
Standards Australia
3.1.3 Certication Practice Statements . . . . . . . . . . . . . . . . . . . . 19 3.1.4 Trusted Certication Authority . . . . . . . . . . . . . . . . . . . . . . . 19 3.1.5 Multiple Certicates . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 20 3.1.6 Certicate Revocation Lists . . . . . . . . . . . . . . . . . . . . . . . . . 20 3.1.7 Services of CA . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 21 3.2 General Infrastructure Requirements . . . . . . . . . . . . . . . . . . . . . . . 21 3.2.1 Trust . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 21
This is a free 14 page sample. Access the full version at http://infostore.saiglobal.com.
3.2.2 Interoperability . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 22 3.2.3 Naming Convention . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 22 3.2.4 Scalability . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 22 3.2.5 Flexibility . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 23 3.2.6 Archiving . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 23 3.3 Key Generation and Management . . . . . . . . . . . . . . . . . . . . . . . . 23 3.3.1 Certied Key Generation . . . . . . . . . . . . . . . . . . . . . . . . . . . 24 3.3.2 Secure Key Generation and Key Management . . . . . . . . . . 25 3.3.3 Key Backup . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 25 3.3.4 Initiating Revocation . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 25 3.3.5 Notice of Revocation . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 25 3.3.6 Presumptions in Adjudications . . . . . . . . . . . . . . . . . . . . . . . 25 3.4 Certication Authority (CA) Requirements (applicable to PARRA, ICA, ORA) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 26 3.4.1 Level of Trust . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 26 3.4.2 Availability . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 26 3.4.3 Services and Functions . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 26 3.4.3.1 User Authentication . . . . . . . . . . . . . . . . . . . . . . . . . 27 3.4.3.2 Certicate Generation . . . . . . . . . . . . . . . . . . . . . . . 27 3.4.3.3 Certicate Distribution . . . . . . . . . . . . . . . . . . . . . . . 27 3.4.3.4 Certicate Storage and Retrieval . . . . . . . . . . . . . . 28
Standards Australia
SAA MP75 1996
3.4.3.5 Certicate Revocation Request . . . . . . . . . . . . . . . . 28 3.4.3.6 CRL Generation and Maintenance . . . . . . . . . . . . . 28 3.4.3.7 CRL Distribution . . . . . . . . . . . . . . . . . . . . . . . . . . . . 29 3.4.3.8 CRL Storage and Retrieval . . . . . . . . . . . . . . . . . . . . 29 3.4.4 Auditing . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 29 3.4.5 Archiving . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 29 3.5
This is a free 14 page sample. Access the full version at http://infostore.saiglobal.com.
Organizational Registration Authority (ORA) Requirements . . . . . . 30 3.5.1 Level of Trust . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 30 3.5.2 Availability . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 30 3.5.3 Services and Functions . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 30 3.5.3.1 User Verication and Authentication . . . . . . . . . . . . 30 3.5.3.2 Certication Request . . . . . . . . . . . . . . . . . . . . . . . . 31 3.5.3.3 Certicate Receipt . . . . . . . . . . . . . . . . . . . . . . . . . . 31 3.5.3.4 Delivery of New Certicate . . . . . . . . . . . . . . . . . . . 31 3.5.3.5 Certicate Revocation Request . . . . . . . . . . . . . . . . 31 3.5.3.6 Auditing . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 32 3.5.3.7 Archiving . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 32
3.6
Information Services . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 32 3.6.1 Information . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 32 3.6.2 Revoked Certicates . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 32 3.6.3 Current Certicates . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 32
3.7
Certicates . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 33 3.7.1 Personal Certicates . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 33 3.7.2 Multiple Certicates . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 33 3.7.3 Role-based Certicates . . . . . . . . . . . . . . . . . . . . . . . . . . . . 33 3.7.4 Anonymous Certicates . . . . . . . . . . . . . . . . . . . . . . . . . . . . 33 3.7.5 CA Certicates . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 34 3.7.6 Certicate Format . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 34
SAA MP75 1996
Standards Australia
3.8 3.9
Certicate Revocation List . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 34 Users . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 35 3.9.1 Applications as Users . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 35 3.9.2 Unlisted Entities . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 35
4 POLICIES . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 36 4.1 4.2
This is a free 14 page sample. Access the full version at http://infostore.saiglobal.com.
Public Key Authentication Framework (PKAF) . . . . . . . . . . . . . . . . 36 Presumptions in Adjudications . . . . . . . . . . . . . . . . . . . . . . . . . . . . 36 Availability of the Certicate . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 36 Certicate . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 37 Valid Certicate . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 37 Certicate Effective and Expiration Dates . . . . . . . . . . . . . . . . . . . 38 Certicate Revocation . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 38 Initiating Revocation . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 38 Notice of Revocation . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 38
4.3 4.4 4.5 4.6 4.7 4.8 4.9
4.10 Revocation of Certicate . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 39 4.11 Certication Authoritys Representations in Certicate . . . . . . . . . 39 4.12 Certication Authoritys Responsibilities . . . . . . . . . . . . . . . . . . . . . 39 4.13 Employees and Contractors . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 40 4.14 Generating the Key Pair . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 40 4.15 Security . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 40 4.16 User Representations . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 40 4.17 Records . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 41 4.18 Safeguarding Private Keys . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 41 4.19 User Responsibilities . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 41 4.20 Integrity and Retention . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 42 4.21 Liability . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 42 4.22 Liability Policy . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 44
Standards Australia
SAA MP75 1996
5 CONSIDERED STRUCTURES FOR PKAF ELEMENTS . . . . . . . . . . . . . . . . . . . 45 5.1 Architectural Options . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 45 5.1.1 Architectural Option (a) . . . . . . . . . . . . . . . . . . . . . . . . . . . . 45 5.1.2 Architectural Option (b) . . . . . . . . . . . . . . . . . . . . . . . . . . . . 46 5.1.3 Architectural Option (c) . . . . . . . . . . . . . . . . . . . . . . . . . . . . 47 5.1.4 Comparison of Architectural Options . . . . . . . . . . . . . . . . . 47 5.2
This is a free 14 page sample. Access the full version at http://infostore.saiglobal.com.
Preferred Option . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 48 Objective of the Preferred Option . . . . . . . . . . . . . . . . . . . . . . . . . 49
5.3
6 COMPOSITION, ROLES AND FUNCTIONS OF THE PREFERRED STRUCTURE . 51 6.1 Policy and Root Registration Authority (PARRA) . . . . . . . . . . . . . . . 54 6.1.1 PARRA Composition . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 54 6.1.2 PARRA Role . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 54 6.1.3 PARRA Functions . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 55 6.1.4 PARRA Process . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 56 6.2 Intermediate Certication Authorities (ICA) . . . . . . . . . . . . . . . . . . 56 6.2.1 ICA Composition . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 56 6.2.2 ICA Examples . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 58 6.2.3 ICA Role . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 61 6.2.4 ICA Functions . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 62 6.2.5 ICA Process . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 63 6.3 Organizational Certication Authorities (OCA) . . . . . . . . . . . . . . . 64 6.3.1 OCA Composition . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 64 6.3.2 OCA Examples . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 65 6.3.3 OCA Role . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 67 6.3.4 OCA Functions . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 67 6.3.5 OCA Process . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 67 6.4 Organizational Registration Authorities (ORA) . . . . . . . . . . . . . . . . 67 6.4.1 ORA Composition . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 68
SAA MP75 1996
Standards Australia
6.4.2 ORA Examples . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 69 6.4.3 ORA Role . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 70 6.4.4 ORA Functions . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 70 6.4.5 ORA Process . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 70 6.5 Consolidated Proposed PKAF Structure . . . . . . . . . . . . . . . . . . . . . 71
APPENDIX A: RECOMMENDED STANDARDS . . . . . . . . . . . . . . . . . . . . . . . . 73 A.1 Primary PKAF Standard . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 73
This is a free 14 page sample. Access the full version at http://infostore.saiglobal.com.
A.2 Practices and Procedures . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 73 A.2.1 Procedures for the Operation of a Policy and Root Registration Authority . . . . . . . . . . . . . . . . . . . . . . . . . . 73 A.2.2 Procedures for the Operation of a Certication Author . . . 74 A.3 Additional PKAF Standards . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 74 A.3.1 Guidelines for Key Management . . . . . . . . . . . . . . . . . . . . . 74 A.3.2 Guidelines for Identication of People and Entities . . . . . . . 74 APPENDIX B: GUIDELINES FOR STANDARDS . . . . . . . . . . . . . . . . . . . . . . . . 75 B.1 Procedures for the Operation of a Certication Authority . . . . . . . 75 B.1.1 Functions . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 75 B.1.2 Operational Requirements . . . . . . . . . . . . . . . . . . . . . . . . . . 75 B.1.3 Technical Requirements . . . . . . . . . . . . . . . . . . . . . . . . . . . . 76 B.1.3.1 Certicate Management Services . . . . . . . . . . . . . . 76 B.1.3.2 Alert Management Services . . . . . . . . . . . . . . . . . . . 76 B.1.3.3 Protection of Private Digital Signature Keys . . . . . . . 76 B.2 Guidelines for Certication Authorities . . . . . . . . . . . . . . . . . . . . . . 77
APPENDIX C: LEGAL ISSUES 70 . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 78 C.1 Introduction . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 78 C.2 Giving Legal Effect . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 78 C.3 The PKAF Framework . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 79 C.4 Overseas Reciprocal Arrangements . . . . . . . . . . . . . . . . . . . . . . . 80
Standards Australia
SAA MP75 1996
C.5 Legal Material . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 81 C.6 Fullment of Signature Requirements . . . . . . . . . . . . . . . . . . . . . . . 81
APPENDIX D: APPENDIX E: APPENDIX F: F.1 F.2
This is a free 14 page sample. Access the full version at http://infostore.saiglobal.com.
RELEVANT STANDARDS . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 82 TUTORIAL ON DIGITAL SIGNATURES . . . . . . . . . . . . . . . . . . . 85 THREATS AND REQUIREMENTS . . . . . . . . . . . . . . . . . . . . . . . 86
Theft . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 86 Contract Negotiation and Signing . . . . . . . . . . . . . . . . . . . . . . . . . 86 MEMBERSHIP OF THE PUBLIC KEY AUTHENTICATION FRAMEWORK TASK GROUP . . . . . . . . . . . . . . . . . . . . . . . . . 87
APPENDIX G:
First published as SAA MP75 1996.
SAA MP75 1996
10
Standards Australia
EXECUTIVE SUMMARY
Todays corporate and government communications environment is rapidly changing. Solutions to problems must cover: the explosion of inter-corporate and inter-government networking; the tremendous growth of applications such as electronic messaging and electronic commerce; efforts under the banner of business process re-engineering to
This is a free 14 page sample. Access the full version at http://infostore.saiglobal.com.
automate workow and eliminate expensive paper transactions in an expanding and increasingly competitive global market place; and remote access for mobile employees, clients and those working at home. This report recommends a single purpose national framework for a national infrastructure that will enable strong authentication of users involved in electronic transactions. The system will provide for the unequivocal identication of an individual or entity (authentication). It does not provide specic assistance for a user who wishes to use encryption to reduce or prevent unauthorized access to data or information. This is in line with activities, both in Australia and overseas, to separate authentication techniques from encryption techniques. The problem faced by corporations and governments is providing an infrastructure that will provide the necessary service and enable benets to be gained. Public/private key cryptography is widely recognized as the enabling technology for authentication within a globally dispersed environment. This technology exists today. There is also a need to provide for supporting legislation, the establishment of trusted infrastructure services and the education of users and potential users. The recommendations for this strategy are: 1 that a single national root authority be established in Australia, empowered to establish the framework for interoperation and cross-certication with other recognized national root authorities, in accordance with Section 6; 2 that the root authority accredit certication authorities which comply with the established framework of common policies, procedures and technologies;
Standards Australia
11
SAA MP75 1996
3 that the PKAF requirements described in Section 3 be incorporated in the establishment brief of the root authority; and 4 that the necessary technical standards to support the PKAF structure be identied or developed and adopted, using internationally agreed standards where available.
This is a free 14 page sample. Access the full version at http://infostore.saiglobal.com.
SAA MP75 1996
12
Standards Australia
1
1.1
INTRODUCTION
Background
Standards Australia formed a Task Group (see Appendix G for the Task Groups membership) to study the technical, policy and legal issues associated with establishing an infrastructure for the creation, management and distribution of signature key material and associated electronic signature certicates using public key techniques.
This is a free 14 page sample. Access the full version at http://infostore.saiglobal.com.
The Task Group examined infrastructure requirements and provided recommendations to establish a Public Key Authentication Framework (PKAF) for use within Australia. The group is representative of industry and government elements. As anticipated, the group has encountered aspects which may require government intervention. This report offers these recommendations as input to legislative, infrastructure and technical standards considerations. This document was available for public comment during April and May 1996 and the comments received have been considered in accordance with Standards Australias processes. This report proposes a scheme for Australia but recognises that it must support international interoperability. The PKAF would need to be supported by appropriate legislation to confer legal status on digital signatures created and used under the scheme. There is also a need to dene the liability of users when using the scheme.
1.2
Purpose of a Public Key Authentication Framework
The framework for producing, managing and distributing signature key material and public certicates is called the PKAF. The PKAF proposes the use of public/private key cryptography as a mechanism to ensure validation of and non-repudiation of users. The purpose of the PKAF is to: provide a framework for the distribution and management of public certicates both directly or indirectly;
COPYRIGHT
Standards Australia
13
SAA MP75 1996
facilitate the generation and management of public key certicates that bind the identity of users to their public key material in a trusted and legally based manner; and provide users, directly or indirectly, with timely announcements of certicate revocations or key compromise. It is a framework for providing a credible national digital signature system which is essential for the conduct of trade and business transactions over electronic communications paths.
This is a free 14 page sample. Access the full version at http://infostore.saiglobal.com.
1.3
Scope of the Public Key Authentication Framework (PKAF)
This framework will provide a scheme where a digital signature (represented by a public/private key pair) will be linked to a particular distinguished name by chain of electronic certicates from the national root registration authority (PARRA) to the user. The ownership of, and right to use, the distinguished name will have been previously established to the PARRA or one of its Certifying Agencies (CAs). The right to use the distinguished name will need to be established with the CA by a physical identication system such as the one used for the issue of passports. The key pair which constitutes the signature will be generated in such a way that the private key is available only to its owner and the certifying authority can be satised that the public key does correspond to the owners private key. The framework will endeavour to ensure that these two requirements are met.
1.4
Standards
Standards are required for the Australian Public Key Authentication Framework to ensure interoperability. With such standards in place, it will be possible to implement the PKAF in a manner that provides trusted services available to all PKAF users. This report recommends a number of standards. These standards will, as a group, provide a statement of requirements for the implementation of the various components of the PKAF. The set of standards will be identied over a period of time, and it is expected
COPYRIGHT
This is a free preview. Purchase the entire publication at the link below:
This is a free 14 page sample. Access the full version at http://infostore.saiglobal.com.
MP 75-1996, Strategies for the implementation of a Public Key Authentication Framework (PKAF) in Australia
Looking for additional Standards? Visit SAI Global Infostore Subscribe to our Free Newsletters about Australian Standards in Legislation; ISO, IEC, BSI and more Do you need to Manage Standards Collections Online? Learn about LexConnect, All Jurisdictions, Standards referenced in Australian legislation Do you want to know when a Standard has changed? Want to become an SAI Global Standards Sales Affiliate? Learn about other SAI Global Services: LOGICOM Military Parts and Supplier Database Metals Infobase Database of Metal Grades, Standards and Manufacturers Materials Infobase Database of Materials, Standards and Suppliers Database of European Law, CELEX and Court Decisions
Need to speak with a Customer Service Representative - Contact Us
S-ar putea să vă placă și
- MP 88-2000 Evolution of Australian Standard For Pressure Vessel Steel PlateDocument6 paginiMP 88-2000 Evolution of Australian Standard For Pressure Vessel Steel PlateSAI Global - APAC0% (1)
- MP 96-2008 Standards For Enterprise-Wide Patient Administration SystemsDocument7 paginiMP 96-2008 Standards For Enterprise-Wide Patient Administration SystemsSAI Global - APAC0% (1)
- SAI Global Expands Standards On-LineDocument2 paginiSAI Global Expands Standards On-LineSAI Global - APAC0% (1)
- MP 78-1999 Manual For The Assessment of Risks of Plumbing ProductsDocument5 paginiMP 78-1999 Manual For The Assessment of Risks of Plumbing ProductsSAI Global - APACÎncă nu există evaluări
- MP 84-2000 Evolution of Australian Standards For Structural SteelDocument4 paginiMP 84-2000 Evolution of Australian Standards For Structural SteelSAI Global - APACÎncă nu există evaluări
- MP 87.2-2007 Australian New Zealand Certification Scheme For Explosion-Protected Electrical Equipment (ANZExDocument7 paginiMP 87.2-2007 Australian New Zealand Certification Scheme For Explosion-Protected Electrical Equipment (ANZExSAI Global - APAC0% (1)
- MP 87.1-2008 Australian New Zealand Certification Scheme For Explosion-Protected Electrical Equipment (ANZExDocument6 paginiMP 87.1-2008 Australian New Zealand Certification Scheme For Explosion-Protected Electrical Equipment (ANZExSAI Global - APACÎncă nu există evaluări
- MP 55-1988 Vehicle Identification Number (VIN) CodesDocument6 paginiMP 55-1988 Vehicle Identification Number (VIN) CodesSAI Global - APACÎncă nu există evaluări
- MP 76-1997 Pressure Equipment - Inspection Bodies and PersonnelDocument8 paginiMP 76-1997 Pressure Equipment - Inspection Bodies and PersonnelSAI Global - APACÎncă nu există evaluări
- MP 58-1991 Workplace Injury and Disease Recording Standard - Resource KitDocument6 paginiMP 58-1991 Workplace Injury and Disease Recording Standard - Resource KitSAI Global - APAC100% (1)
- MP 52-2005 Manual of Authorization Procedures For Plumbing and Drainage ProductsDocument8 paginiMP 52-2005 Manual of Authorization Procedures For Plumbing and Drainage ProductsSAI Global - APACÎncă nu există evaluări
- As 1562.1-1992 Design and Installation of Sheet Roof and Wall Cladding MetalDocument5 paginiAs 1562.1-1992 Design and Installation of Sheet Roof and Wall Cladding MetalSAI Global - APAC17% (6)
- MP 63-1992 The Australian GarmentMark - Specifications and ProceduresDocument5 paginiMP 63-1992 The Australian GarmentMark - Specifications and ProceduresSAI Global - APAC0% (1)
- MP 48-2008 Certified Gas Cylinder Test StationsDocument6 paginiMP 48-2008 Certified Gas Cylinder Test StationsSAI Global - APACÎncă nu există evaluări
- HB 9-1994 Occupational Personal ProtectionDocument8 paginiHB 9-1994 Occupational Personal ProtectionSAI Global - APACÎncă nu există evaluări
- MP 100-2009 Procedures For Certification of Organic and Biodynamic ProductsDocument8 paginiMP 100-2009 Procedures For Certification of Organic and Biodynamic ProductsSAI Global - APACÎncă nu există evaluări
- MP 15.2-1990 Standards Australia Style Manual Drafting of Australian StandardsDocument8 paginiMP 15.2-1990 Standards Australia Style Manual Drafting of Australian StandardsSAI Global - APACÎncă nu există evaluări
- MP 15.6-1990 Standards Australia Style Manual Drafting and Interpretation of Standards From A Legal PerspectiDocument7 paginiMP 15.6-1990 Standards Australia Style Manual Drafting and Interpretation of Standards From A Legal PerspectiSAI Global - APACÎncă nu există evaluări
- HB 90.1-2000 The Small Business Handbook - Guide To ISO 9001-2000 The Small Business Handbook - Guide To ISODocument36 paginiHB 90.1-2000 The Small Business Handbook - Guide To ISO 9001-2000 The Small Business Handbook - Guide To ISOSAI Global - APACÎncă nu există evaluări
- HB 90.6-2000 The Legal Profession - Guide To ISO 9001-2000 The Legal Profession - Guide To ISO 9001-2000Document19 paginiHB 90.6-2000 The Legal Profession - Guide To ISO 9001-2000 The Legal Profession - Guide To ISO 9001-2000SAI Global - APACÎncă nu există evaluări
- HB 87-1997 (CJC 1) Joint Use of Poles - The Placement On Poles of Power Lines and Paired Cable TelecommunicatiDocument7 paginiHB 87-1997 (CJC 1) Joint Use of Poles - The Placement On Poles of Power Lines and Paired Cable TelecommunicatiSAI Global - APACÎncă nu există evaluări
- HB 90.3-2000 The Construction Industry - Guide To ISO 9001-2000 The Construction Industry - Guide To ISO 9001Document17 paginiHB 90.3-2000 The Construction Industry - Guide To ISO 9001-2000 The Construction Industry - Guide To ISO 9001SAI Global - APACÎncă nu există evaluări
- HB 90.0-2000 The ISO 9001 Comparison - 2000 Vs 1994 The ISO 9001 Comparison - 2000 Vs 1994Document18 paginiHB 90.0-2000 The ISO 9001 Comparison - 2000 Vs 1994 The ISO 9001 Comparison - 2000 Vs 1994SAI Global - APACÎncă nu există evaluări
- Shoe Dog: A Memoir by the Creator of NikeDe la EverandShoe Dog: A Memoir by the Creator of NikeEvaluare: 4.5 din 5 stele4.5/5 (537)
- The Yellow House: A Memoir (2019 National Book Award Winner)De la EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Evaluare: 4 din 5 stele4/5 (98)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeDe la EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeEvaluare: 4 din 5 stele4/5 (5794)
- The Little Book of Hygge: Danish Secrets to Happy LivingDe la EverandThe Little Book of Hygge: Danish Secrets to Happy LivingEvaluare: 3.5 din 5 stele3.5/5 (400)
- Grit: The Power of Passion and PerseveranceDe la EverandGrit: The Power of Passion and PerseveranceEvaluare: 4 din 5 stele4/5 (588)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureDe la EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureEvaluare: 4.5 din 5 stele4.5/5 (474)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryDe la EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryEvaluare: 3.5 din 5 stele3.5/5 (231)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceDe la EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceEvaluare: 4 din 5 stele4/5 (895)
- Team of Rivals: The Political Genius of Abraham LincolnDe la EverandTeam of Rivals: The Political Genius of Abraham LincolnEvaluare: 4.5 din 5 stele4.5/5 (234)
- Never Split the Difference: Negotiating As If Your Life Depended On ItDe la EverandNever Split the Difference: Negotiating As If Your Life Depended On ItEvaluare: 4.5 din 5 stele4.5/5 (838)
- The Emperor of All Maladies: A Biography of CancerDe la EverandThe Emperor of All Maladies: A Biography of CancerEvaluare: 4.5 din 5 stele4.5/5 (271)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaDe la EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaEvaluare: 4.5 din 5 stele4.5/5 (266)
- On Fire: The (Burning) Case for a Green New DealDe la EverandOn Fire: The (Burning) Case for a Green New DealEvaluare: 4 din 5 stele4/5 (74)
- The Unwinding: An Inner History of the New AmericaDe la EverandThe Unwinding: An Inner History of the New AmericaEvaluare: 4 din 5 stele4/5 (45)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersDe la EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersEvaluare: 4.5 din 5 stele4.5/5 (345)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyDe la EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyEvaluare: 3.5 din 5 stele3.5/5 (2259)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreDe la EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreEvaluare: 4 din 5 stele4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)De la EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Evaluare: 4.5 din 5 stele4.5/5 (121)
- Her Body and Other Parties: StoriesDe la EverandHer Body and Other Parties: StoriesEvaluare: 4 din 5 stele4/5 (821)
- Gaurav SirDocument29 paginiGaurav SirMandira PrakashÎncă nu există evaluări
- Quizzer in Corpo Set ADocument10 paginiQuizzer in Corpo Set ACJBÎncă nu există evaluări
- CutoffDocument4 paginiCutofffercyagnesÎncă nu există evaluări
- Cima Edition 15 Worksheet CASH FLOWDocument3 paginiCima Edition 15 Worksheet CASH FLOWananditaÎncă nu există evaluări
- 860600-Identifying Modes of CirculationDocument7 pagini860600-Identifying Modes of CirculationericÎncă nu există evaluări
- Extending Civic Values in Architectures of Listening: Arendt, Mouffe and The Pluralistic Imperative For Organizational ListeningDocument23 paginiExtending Civic Values in Architectures of Listening: Arendt, Mouffe and The Pluralistic Imperative For Organizational ListeningOwenÎncă nu există evaluări
- Thoery of IR June Exam NotesDocument36 paginiThoery of IR June Exam NotesRalitsa HristovaÎncă nu există evaluări
- This Content Downloaded From 103.232.241.147 On Mon, 19 Sep 2022 16:51:43 UTCDocument15 paginiThis Content Downloaded From 103.232.241.147 On Mon, 19 Sep 2022 16:51:43 UTCsayondeepÎncă nu există evaluări
- Latest Circular For Payment of Interest Free Festival Advance To StaffDocument1 paginăLatest Circular For Payment of Interest Free Festival Advance To Staffhimadri_bhattacharjeÎncă nu există evaluări
- Impact of Consumer Protection Act, 2019 On E-CommerceDocument3 paginiImpact of Consumer Protection Act, 2019 On E-CommerceVidhatri DeoliÎncă nu există evaluări
- A Case Applying Revenue Recognition StandardsDocument17 paginiA Case Applying Revenue Recognition StandardsMajdouline FarazdagÎncă nu există evaluări
- Historical BackgroundDocument66 paginiHistorical BackgroundBunbun 221Încă nu există evaluări
- Sargasso Vs Philippine PortsDocument28 paginiSargasso Vs Philippine PortsAtty. R. PerezÎncă nu există evaluări
- WEEK 7A - Philippines Under American TutelageDocument28 paginiWEEK 7A - Philippines Under American TutelageJULIANA NICOLE TUIBUENÎncă nu există evaluări
- Employment Contract - DraftDocument6 paginiEmployment Contract - DraftMarvin LimÎncă nu există evaluări
- Task Syariah Compliance House Matrix: International Islamic University MalaysiaDocument5 paginiTask Syariah Compliance House Matrix: International Islamic University MalaysiaAlya syaahindahÎncă nu există evaluări
- Apple Academy Exams Trainers: Monday 19th July, 2021 Principles of Accounts Summer ClassesDocument10 paginiApple Academy Exams Trainers: Monday 19th July, 2021 Principles of Accounts Summer ClassesAnthony JulesÎncă nu există evaluări
- WWW - tnpsCGURU.in TNPSC Group 4 2014 General Studies Question Paper With Answer KeyDocument18 paginiWWW - tnpsCGURU.in TNPSC Group 4 2014 General Studies Question Paper With Answer KeySrini VasaÎncă nu există evaluări
- C11 Strategy DevelopmentDocument30 paginiC11 Strategy DevelopmentPARTI KEADILAN RAKYAT NIBONG TEBALÎncă nu există evaluări
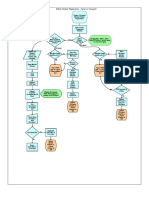
- Mobile Number Reg FlowchartDocument1 paginăMobile Number Reg FlowchartKarthikayani PalaniÎncă nu există evaluări
- Kenya's Physical and Land Use Planning Act 2019Document67 paginiKenya's Physical and Land Use Planning Act 2019Sahil KhadkaÎncă nu există evaluări
- Sales Flow Chart 2019Document2 paginiSales Flow Chart 2019grace hutallaÎncă nu există evaluări
- Session Twelve: Harambee and Development 12.1 ObjectivesDocument4 paginiSession Twelve: Harambee and Development 12.1 ObjectivesJpricarioÎncă nu există evaluări
- Case Study 1 2Document1 paginăCase Study 1 2Ashok RoyÎncă nu există evaluări
- Criminal Law I Program Module No. 4 AteneoDocument4 paginiCriminal Law I Program Module No. 4 AteneoBABY LOVE UMPAÎncă nu există evaluări
- Justice Prevail in Law Research Papaer 4Document5 paginiJustice Prevail in Law Research Papaer 4saumilÎncă nu există evaluări
- Affidavit Cum Undertaking TechDocument2 paginiAffidavit Cum Undertaking TechAshish KumarÎncă nu există evaluări
- Aguirre V SOJDocument2 paginiAguirre V SOJJaz Sumalinog0% (1)
- Comparative Police SystemDocument52 paginiComparative Police SystemBong MisalangÎncă nu există evaluări
- Canopy CountersuitDocument12 paginiCanopy CountersuitJohn ArchibaldÎncă nu există evaluări