Documente Academic
Documente Profesional
Documente Cultură
Question 1
Încărcat de
Harun Raaj GuptaDescriere originală:
Drepturi de autor
Formate disponibile
Partajați acest document
Partajați sau inserați document
Vi se pare util acest document?
Este necorespunzător acest conținut?
Raportați acest documentDrepturi de autor:
Formate disponibile
Question 1
Încărcat de
Harun Raaj GuptaDrepturi de autor:
Formate disponibile
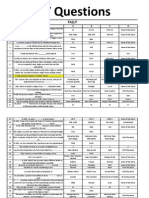
Q. No.
AC64
Question Body In an accounting information system, which of the following types of computer files most likely would be a master file? Which of the following is an advantage of a computer-based system for transaction processing over a manual system? A computer-based system: What general term describes the physical equipment of a computer system, such as its video screen, keyboard, and storage devices? Where would you find the letters QUERTY? What are you most likely to use when playing a computer game? A digitising tablet can be used for? Which of the following is a pointing device used for computer input? What input device could tell you the price of a product Where would you find a magnetic strip? Hard copy is a term used to describe...?
Choice A Inventory subsidiary.
Choice B Cash disbursements.
Choice C Cash receipts.
Choice D Payroll transactions.
An s A
AC65
Does not require as stringent a set of internal controls.
Will produce a more accurate set of financial statements.
BC 01
hardware
software
Will be more efficient at producin g financial stateme nts. output
Eliminates the need to reconcile control accounts and subsidiary ledgers.
input
BC 02 BC 03 BC 04 BC 05 BC 06 BC 07 BC 08
Mouse Touch screen Printing letters Touch screen Mouse Credit card Writing on a hard board
Keyboard Light pen Tracing Diagrams Hard disk Bar code reader Mouse Printed output
Numeric Keypad Joystick Reading Bar Codes Keyboar d Optical mark reader Speaker s Storing informat ion on the hard
Printer Scanner Digital Signatures CD ROM Drive Keyboard Printer Back-up on a Cartridge
B C B A B A B
BC 09
BC 10 BC 100 BC 100 BC 101 BC 101 BC 102 BC 102 BC 103
What are the individual dots which make up a picture on the monitor screen Called A daisy wheel is a type of...? What input device can be used for marking a multiple-choice test? Laptop computers use QWERTY is used with reference to What input device could tell you the price of a bar of chocolate? A GUI is Where would you find a magnetic strip? Multiprogramming refers to
Coloured spots Printer Mouse CRT displays screen layout Mouse hardware Credit card having several programs in RAM at the same time having several programs in RAM at the same time multitasking
Pixels
disk Pixies
Pickers
Storage device Bar code reader LCD displays mouse button layout Bar code reader language interpreter Speakers multitasking
Pointing device Optical mark reader SSGA displays keyboar d layout Optical mark reader software interface Smart card writing program s in multiple languag es writing program s in multiple languag es to run more than one program at the same time Third generati
CD-ROM None of the above none of the previous word processing software None of the above an operating system None of the above none of the previous
B C B C A A
BC 104
Multitasking refers to
the ability to run 2 or more programs concurrently an operating system
none of the previous
BC 105
Multiprogramming is a prerequisite for
none of the above
BC 105
UNIVAC Computer belongs to the
First generation
Second generation
Fifth - generation computers.
computers. BC 106 BC 106 BC 107 BC 107 Timesharing is the same as Name the first Indian Super Computer? Disk fragmentation The technology which is used to check answer sheets of multiple-choice questions in civil services or similar examinations is: A compiler is multitasking Vishwajeet is caused by wear Bar code Reader Technology
computers. multiprogrammi ng Deep Blue caused by overuse Optical Mark Reader Technology
on compute rs. Multiuser Param is due to bad disk blocks Magneti c Ink Charact er Recognit ion Technol ogy converts a program to machine code Desk jet Printer compres sing it Virtual informat ion reader & user system An ink pen WAN technolo gy 10-12 sec
none of the previous Arjun none of the previous Image Scanning Technology
A C C B
BC 108
a fast interpreter
slower than an interpreter
none of the previous
BC 108 BC 109 BC 109
Which printer among the following is fastest Zipping a file means What does acronym VIRUS stands for
Drum Printer encrypting it Very important reader user sequence Electrically charged ink mainframe technology 10-6 sec
Dot - Matrix Printer decrypting it Vital information resource under siege
Thermal Printer transmitting it None of above
A C B
BC 11 BC 110 BC 111
An impact printer creates characters by using...? A client-server system is based on A nanosecond is
Thermal Paper LAN technology 10-3 sec
An inked ribbon and print head Unix operating system 10-9 sec
D B D
BC 112
The memory address register is used to store
data to be transferred to memory Contingency Planning NIC Card Record Count
data that has been transferred from memory System feasibility report VSAT Identification Number
BC 113 BC 113 BC 114
BC 114
Inefficient usage of excess computer equipment can be controlled by Which of the following is not the component of a CPU A trailer label is used on a magnetic tape file, it is the last record and summarises the file. The following is an information not found in the trailer label Hard copy is a term used to describe...?
the address of a memory location Capacity Planning RAM Control totals for one or more fields Storing informat ion on the hard disk Visual audio board File protecti on ring Pixies
an instruction that has been transferred from memory Exception reporting AGP Card End-of-file and end-of-reel code
B B
Writing on a hard board
Printed output
None of above
BC 115 BC 116
What do the abbreviations VAB stand for What control would prevent the accidental erasure of customer information from a magnetic tape What are the individual dots which make up a picture on the monitor screen called? Header label normally include all the following except the A daisy wheel is a type of...? Which approach or technique is a control
Voice activated broadcastin g Validity check
Voice answer back Boundary protection
None of above
Limited access files
BC 116 BC 117 BC 117 BC 118
Coloured spots File Name Printer
Pixels
None of above
Identification number Storage device
Reel Number Pointing device Console Log
Batch Total None of above Data Dictionary
D A B
System Logs Physical Security
BC 118
usually associated with microcomputers An impact printer creates characters by using...? The best security control in a microcomputer environment is to What would you NOT use with a flatbed plotter? What do you need for an ink jet printer? The greatest control exposure in a microcomputer environment is the lack of What do you need for an ink jet printer? A laser printer does NOT use? The amount of data that a disk may contain is known as the disks...? You can ________ protect a floppy disk. Information on a hard disk is usually backed-up using a...? Magnetic tape is a...?
Electrically charged ink
An ink pen
BC 119 BC 119 BC 12 BC 120
Restrict physical access A pen A cartridge Separation of duties
Use only unremovable media Paper A drum Centralised function for PC acquisition
An inked ribbon and print head Require user passwor ds Eraser A ribbon
None of above
Make duplicate copies of files None of above A cassette
C A A
BC 120 BC 121 BC 122 BC 123 BC 124 BC 125 BC 126 BC 128
A cartridge A print head Volume Read Magnetic tape Serial access medium 1.44MB A CD-ROM
A drum A laser beam Size Write PAN drive Random access medium 20 GB A floppy disk
Centralis Distributed ed policies or function procedures for PC Dispositi on A ribbon None of above An INK RIBBON Storage capacity Read and Write Floppy disk A parallel access medium 700MB Magneti c tape storage None of above None of above None of above None of above None of above
A C C B A A
Hard disks can have a storage capacity in the region of...? Which storage device has the largest capacity in Mb?
None of above None of above
B C
BC 129 BC 13 BC 130 BC 133 BC 134 BC 135 BC 136 BC 137 BC 138 BC 14
Which storage device cannot be erased? You can ________ protect a floppy disk Where should floppy disks be stored? The contents of these chips are lost when the computer is switched off? What are responsible for storing permanent data and instructions? Which parts of the computer perform arithmetic calculations? What are small high speed memory units used for storing temporary results? How many bits of information can each memory cell in a computer chip hold? What type of computer chips are said to be volatile? Magnetic tape is a...?
A CD-ROM Read By a sunny window ROM chips
A floppy disk Write By magnet objects RAM chips
Magneti c tape storage Read and Write In a drawer CDROM chips DRAM chips Logic bus Control unit 8 bits
None of above Not None of above None of above
A B C B
RAM chips ALU CPUs
ROM chips Registers Registers
None of above None of above None of above
B A B
0 bits
1 bit
None of above
RAM chips Serial access medium Network software and security software Supercomp uter Notebook
ROM chips Random access medium
CACHE A parallel access medium Business software and games software Mainfra me compute r Jon Von
None of above A selective access medium
A A
BC 14
Software can be divided into two areas:
Systems software and application software Personal computer Supercomputers
None of the above
BC 140 BC
Travel agents use this computer system when reserving flights Which computers are
None of above
None of above
141
used in the weather forecasting industry? Vacuum tube based electronic computers are...? Which generation of computer was developed from microchips? Which generation of computer uses more than one microprocessor? Which generation of computer developed using integrated circuits? Which generation of computer developed using solid state components? Name three steps involved in developing an information system
computers
BC 142 BC 143 BC 144 BC 145 BC 146 BC 147
First generation Second generation Second generation Second generation Second generation Specificatio n, Design, and Testing
Second generation First generation Third generation
Neuman n compute rs Hoover generati on Fourth generati on Fifth generati on Fifth generati on Fifth generati on Analysis, System Design, and Impleme ntation This involves looking at a system and finding out how informat ion is being handled Mainten ance, reliabilit y, and
None of above None of above None of above
A C C
Third generation
None of above
Third generation
None of above
Programming, Design, and Testing
None of above
BC 148
How do you define analysis of an information system?
Analysis translates program code of a high level language to machine code
Analysis is the loading of programs that perform routines to control peripheral devices
None of above
BC 149
What areas need to be considered in the SOFTWARE design process?
Only hardware and software
Inputs, outputs, file design hardware, and software
None of above
BC 15 BC 15 BC 151
What is the function of systems software? Formatting a disk results in all the data being...? What is Direct Implementation?
To collect data Deleted from the disk Users operate the manual system and computer system at the same time The new system is introduced alongside the existing system Instructions and technical documentat ion For technical support
To execute any programs Copied from the disk Users operate the computer system from a given date
upgrade ability To maintain security Saved to the disk Users operate the manual system
None of the above Transferred from the disk None of above
D A B
BC 152
What is parallel running?
The new system is introduced and users start operating it Log files and temporary files
Users continue operatin g the old system User Guide and technica l docume ntation User guides cover how to run the system, enter data, save, print, etc. Databas e systems and
None of above
BC 153
What documents are produced during the development of a system?
None of above
BC 154
What are User Guides are used for?
To enable any printer to be connected to the network
None of above
BC 16
Systems software can be categorised into:
Operating systems and system services
Network systems and communication services
None of the above
BC 16 BC 17
Which storage device cannot be erased? Application software are programs that are written
Magnetic CD-ROM tape storage To maintain To do a a backup particular task. copy of all the information Data bus Auto bus
BC 17
BC 170 BC 18 BC 183
Which bus carries information between processors and peripherals? Convert the decimal number 2989 to Hexadecimal Which bus controls the sequencing of read/write operations? What are utilities?
backup services floppy disk To help someon e who is applying for employ ment Address bus TED Address bus Data structur es that are part of the kernel of an operatin g system. decimal form represen ted 256 characte rs 16 bits 230 bytes 32 Mb of
Hard disk None of the above
B B
Control Bus
FDDI Data bus Peripherals that are connected to a computer.
BAD Auto bus Operating system routines that execute in supervisor mode.
MAD Control Bus Shells, compilers and other useful system programs.
B D D
BC 184 BC 185 BC 186 BC 187 BC
Numbers are stored and transmitted inside a computer in The original ASCII codes
binary form were 7 bits
ASCII code form 8 bits
alphanumeric form represented 127 characters 32 bits 1024 bytes a 32-bit bus or 32-
A A
A Nibble corresponds to A gigabyte represents A 32-bit processor has
4 bits More than 1000 mega bytes 32 registers
8 bits 1000 kilobytes 32 I/O devices
A A D
188 BC 189 BC 19
A parity bit is
BC 190 BC 191 BC 192 BC 20 BC 200
he contents of these chips are lost when the computer is switched off? Clock speed is measured in Cache memory enhances CISC machines
used to indicate uppercase letters ROM
used to detect errors RAM
RAM is the first bit in a byte DRAM
bit registers is the last bit in a byte CROM
bits per second memory capacity have fewer instructions than RISC machines ALU Power is switched off
baud memory access time use more RAM than RISC machines Registers Computer is improperly shut down
bytes seconda ry storage capacity have medium clock speeds Variable s Data is not saved before compute r is shut down printer interface ink-jet printer stores more informat ion than RAM provides backup power in the event of
Hertz secondary storage access time use variable size instructions Logic Bus All of the above
D B
Which parts of the computer perform arithmetic calculations? Every data from the primary memory will be erased if
A D
BC 201 BC 202 BC 203
An RS-232 interface is For print quality you would expect best results from ROM
a parallel interface line printer is faster to access than RAM increased the storage capacity of a computer system
a serial interface dot matrix printer is non-volatile
a modem interface laser printer. is used for cache memory
B D B
BC 204
A UPS
increases the process speed
none of the previous
BC 206
smart card
is a form of ATM card
has more storage capacity than an ATM card LCD displays multitasking
BC 207 BC 208
Laptop computers use Multiprogramming refers to
CRT displays having several programs in RAM at the same time having several softwares running at the same time ALU
BC 209
Multitasking refers to
the ability to run 2 or more programs concurrently Registers
BC 21
BC 21
BC 210
What are small high speed memory units used for storing temporary results? A good way to exchange information that changes rapidly is through Multiprogramming is a prerequisite for
a power cut is an access card for a security system SSGA displays writing program s in multiple languag es writing program s in multiple languag es Variable s CD-ROM
contains a microprocessor
none of the previous none of the previous
B A
none of the previous
Logic Bus
brochures
magazines
multitaskin g
an operating system
BC 211 BC 212 BC 213
Timesharing is the same as Virtual memory is Multiprocessing is
multitaskin g related to virtual reality same as multitasking
multiprogrammi ng a form of ROM same as multiprogrammi
to run more than one program at the same time multius er a form of VRAM multiuse r
none of the above
none of the previous none of the previous involves using more than one
C D D
ng BC 22 To help keep sensitive computer-based information confidential, the user should What is the function of a disk drive? A 4GL is A nanosecond is What small, hand-held device is used to move the cursor to a specific location on the screen? The memory address register is used to store save the file set up a password to read from or write information to a floppy disk uses Java 103 sec a mouse make a backup copy to print sheets of paper
processor at the same time use a virus protection program
BC 22
to calculate numbers Uses Cobol 106 sec a keypad
BC 228 BC 229 BC 23
to display information or pictures on a screen uses C+ none of the + previous. 1012 109 sec sec a frog a message pad
D D B
BC 230
data to be transferred to memory data to be transferred to or from memory an instruction that has been decoded a cursor
data that has been transferred from memory data to be transferred to the stack an instruction that has been fetched from memory
BC 231
The memory data register is used to store
BC 232
The instruction register stores
BC 24
BC 25
Which of the following is used to indicate the location on the computer monitor? A mathematical procedure that can be explicitly coded in a set of computer language instructions that
a scroll bar
the address of a memory location the address of a memory location an instructi on that has been execute d a light pen Program
an instruction that has been transferred from memory. an instruction that has been transferred from memory
the address of the D next instruction to be executed
a magic marker
Formula
Algorithm
Data
BC 26
BC 27 BC 28 BC 28
manipulate data. Which of the following translates a program written in high-level language into machine language for execution? Detecting errors in real memory is a function of To find where a file has been saved on disk, the user should A series of instructions telling the computer how to process data or files is defined as a To ensure that data is not lost if a computer system fails, the user should Having a single CPU alternatively process tasks entered from multiple terminals is called The place in the CPU where the data and programs are temporarily stored during processing is called the All are examples of computer software except Computer manufactures are now installing software programs permanently inside the computer. It is known as Which of the following file organisation forms most efficiently allows
Assembler
Compiler
Artificial Intellige nce Range checkin g use the backup facility System
Parity Checker
Memory protection use the directory search tools Network
Parity Checking search each file in turn Program
Validation use find and replace Modem
B A B
BC 29
BC 29
save copies use different of the file filenames on the with the system same name on the system Multiprocess Time sharing ing
keep a record of compute r failures Multipro grammi ng Floppy Disk
backup to a secure medium
Multiplexing
BC 30
ROM
RAM
Magnetic Disk
BC 31 BC 32
Firmware Firmware
Word Processor Word Processor
Telepho ne modem Telepho ne modem Indexed
Shareware Shareware
C A
BC 32
Sequential
Hashed
Random
BC 33
BC 34 BC 35 BC 36
BC 37
BC 37
BC 38
BC 38
access to a record The part of the computer system controlling data manipulation is called the For direct access storage devices the recording area is divided into The data hierarchy from the largest to the smallest is Which of the following hardware or software system controls provides a detailed record of all activities performed by a computer system Which one of the following parts of a computer is necessary to enable it to play music? An educational CD-ROM on Indian Poets contains 1000 pages of text, 500 colour pictures, 15 minutes of sound and 1 minute of video. Which of the four different media listed takes up most space on the CDROM? Which one of the following printers is suitable for printing sprocket fed carbon copies? Multimedia software can be most productively used for
Operating System Tracks and Sectors Character, field, database Valid character check
ALU
CPU
Primary Storage
Blocks and Sectors Database, character, record Maintenance diagnostic program
Files and Schema and Tracks subschema File, record, field Systems logs Element, field, file Parity check
A C C
Sound card.
CD-ROM
MIDI interface
Serial interface
Text
Pictures
Sound
Video
Laser
Dot matrix
Ink-jet
Drum
viewing an encyclopae dia CDROM.
creating the plans for a building design.
presenti ng an order for stock to a warehou se.
recording current stock in a supermarket and answering customer queries.
BC 39 BC 40
BC 41
To be effective a virus checker should be Which one of the following software applications would be the MOST appropriate for performing numerical and statistical calculations? Passwords enable users to 12. How many bytes do 4 Kilobytes represent? Back up of the data files will help to prevent Which one of the following is the MOST common internet protocol? The advantage of a PC network is that
replaced regularly Database
never updated Document processor
updated updated once a regularly year Graphics Spreadsheet package
C D
get into the system quickly 512 loss of confidentiali ty TCP/IP
make efficient use of time 1024 duplication of data HTML
BC 42 BC 43 BC 44
retain confiden tiality of files 4096 virus infection IPX/SPX
simplify file structures 8192 loss of data NetBEUI
C D A
BC 45
access to the internet is quicker a file name universal port serial orphan files can be left on the system
files can be shared
BC 46 BC 47
The term A:\ refers to UPS stands for
BC 48
The main problem associated with uninstalling software is that
BC 48
You are conducting
data.
printer can do 1000s of pages a day a subdirectory the root director y up-line provider uninterr service uptable power supply the program the executable may system not allow it to be requires uninstalled a network administ rator to uninstall it documents. informat
the operating system is easy to use the hard drive uniform page source the system always requires a re-boot and defrag afterwards
D C
text.
BC 484
research for a Income Tax assignment. The raw facts you collect are called A flow chart is the
ion.
Graphical representati on of logic Purchase, sales, receipt, payments etc. assist in maintenanc e senior executive support for IT. input.
Rules writte in procedural language To fill the log register
BC 485
A voucher entry in Tally is done for
Logical Steps in any languag e It is mandat ory in tally prevent unautho rised access IT understa nds the business processi ng.
None of the above
None of the bove
BC 49
Passwords are applied to files in order to Each of the following is an enabler of IT-business alignment except: The basic systems model is used to describe virtually all information systems and it consists of the following elements: What is a computeraided design system?
speed up access
allow encryption
BC 491 BC 492
IT management lacks leadership. output.
None of the above
All of the above
BC 494
The use of computers to design state-of-theart, highquality products.
Using computers to do architecture.
BC 499 BC 50
A(n) __________ offers a solution package for an entire industry. File extensions are used in order to
specialist or functional name the file
Application Service Provider ensure the filename is not
Software that generat es innovate d designs and artistic patterns . enterpri se identify the file
None of the above
local identify the file type
B D
BC 506 BC 51 BC 52
BC 53 BC 53
BC 54
BC 54
Information systems controls include all of the following EXCEPT: Hashing for disk files is called Components of expert systems include: a) inference engine; b) user interface; c) knowledge base; d) fuzzy logic Black box testing and white box testing are part of: What is the term used to describe the point of interaction between a computer and any other entity, such as a printer or human operator? The advantages of CASE tools are: a) reusability; b) maintainability; c) portability; d) flexibility Which of the following is an acceptable way to shut down the computer?
preventive controls. external hashing A: (a) , (b), (d)
lost detective controls. static hashing B: (a) to (d)
correctiv e controls. dynamic hashing C: (a), (b), (c)
All of the above D are parts of IS controls. extensible hashing A D: (b), (c), (d) C
corrective controls Component
preventive controls Interface
detectiv e controls Settings
general controls Control
C B
(a), (c), (d)
(b), (c), (d)
(a) to (d)
(a), (b), (c)
Press the reset button.
Turn the computer off at the power point.
BC 55
BC 555
Yesterday, in your music class you saved your compositions as MP3 files. Today, you cannot remember where you saved them. Which is the best way to locate the files? Components of an information system model are: a) applications architecture; b)
Create the files again.
Ask the person next to you.
Select the Shut Down option from a menu. Use the Find or Search feature.
Pull the power cord from the back of the computer.
Put your hand up and ask the teacher
(a), (c), (d)
(a), (b), (c)
(a) to (d)
(b), (c), (d)
BC 56 BC 57
functional architecture; c) technology architecture; d) information architecture Benchmarks form part of: Continuity controls include: a) record counts; b) date checks; c) label checks; d) runto-run totals Which is not part of help desk documentation: Testing of individual modules is known as: Design phase of CASE tools includes: a) data architecture; b) decision architecture; c) interface architecture; d) presentation architecture Which is part of installation testing: The computer operating system performs scheduling, resource allocation, and data retrieval functions based on a set of instructions provided by the: Which of the following falls under multimedia data: a) text; b) images; c) video; d) audio Which of the following procedures should be included in the disaster recovery plan for an Information Technology department?
detective controls (a), (c), (d)
organisational controls (a), (b), (c)
preventi ve controls (a) to (d)
corrective controls (b), (c), (d)
C C
BC 58 BC 59 BC 60
problem logging unit testing (b), (c), (d)
call lights data testing (a), (b), (d)
program change requests thread testing (a), (b), (c)
resolution procedures loop testing (a) to (d)
C A D
BC 60 BC 60
benchmark testing Multiplexer.
specifications matching Peripheral processors.
parallel operatio ns Concent rator.
system walkthroughs Job control language.
B D
BC 61
(a) to (d)
(b), (c), (d)
(a), (b), (c) Physical security of warehou se facilities
(a), (c), (d)
BC 61
Replacemen t personal computers for user department s.
Identification of critical applications.
Cross-training of operating personnel.
BC 62 BC 63 BC 64 BC 65 BC 66
Designing relationships among components is part of: Several Computers connected together is called: Which network topology uses a Hub? Which of the following topologies is used for Ethernet? Application software are programs
architectural design Clientserver Star Star To maintain a backup copy of are written all the information Direct
interface design Client Bus Bus To do a particular job such as editing, storing information Sequential
. procedu ral design Comput er network Mesh Ring To help someon e who is applying for employ ment Binary
data design Hub Ring All of the above To Store data in an organised manner
A C A D B
BC 67
BC 67
BC 68
BC 69
BC 70
Which type of file search method requires a computer first read all locations preceding the desired one Which of the following areas of responsibility are normally assigned to a systems programmer in a computer system environment? Which of the following is recommended when many searches for data are required It is unlikely that a magnetic tape containing several thousand blocked records can be used on two machines of different architecture directly because Which component of the CPU has the most
Indexed
Systems analysis and applications programmin g. A sequential file on a disk Tapes can only be read by the machine on which they are written Data path part
Data communications hardware and software. A sequential file on a tape Parity errors will result
Control Unit
Operatin Computer g operations. systems and compiler s. A direct A direct access file access on a tape file on a disk Informat Data record can ion never be blocked formats together common ly vary between architect ures Address Input output calculati channel
BC 71
BC 72
influence on its cost versus performance Which of the following terms applies to network used to connect computers with other computers, peripherals and workstations that are in fairly close proximity Intelligent terminals differ from dumb terminals in that they
on part Distributed systems Local Area network Wide area network Protocol B
Can send data to a computer and receive data from a computer
Use the computer to which they are connected to perform all processing operations
BC 73
BC 74
A computer is to be linked to 8 terminals using a single communication link. To permit simultaneous terminal operations, communication path will require which of the following A modem is a device that
Mixer
Modem
Generall y require a keyboar d for data entry and a CRT for display Multiple xor
Are required with a microprocessor which permits some data processing such as input validation
Time sharing computer
BC 75
BC 76
A LAN includes 20 PCs, each directly connected to the central shared pool of disk drives and printers. This type of network is called a A computer based system for sending,
Allows Aids in back-up computer procedures signals to be send over a telephone line Planetary Ring Network network
Packs data in a disk file
Speeds up online printing
Loop Network
Star Network
Office Automation
Executor systems
Electroni c
Instant post-office
BC 77
BC 78 BC 79 BC 79
forwarding, receiving and storing messages is called an If a workstation contains a processor, monitor, screen manipulation device, printer, storage and communication capabilities, it is said to be Terminal hardware controls include RS-232 is a What is a compiler?
mailing A dumb workstation An intelligent workstation A personal compute r A mainframe PC B
Time of day control locks Type of cable A compiler does a conversion line by line as the program is run
Encryption algorithms Terminal Standard A compiler converts the whole of a higher level program code into machine code in one step
BC 80
What are the stages in the compilation process?
Feasibility study, system design, and testing
Implementation and documentation
BC 80 BC 81
Which of the following is not a data transmission coding scheme What is the definition of an interpreter?
CRC An interpreter does the conversion line by line as the
Baudot An interpreter is a representation of the system being designed
Parity checks Commu nication protocol A compiler is a general purpose languag e providin g very efficient executio n Lexical analysis, CONVER SION, and code generati on ASCII An interpret er is a general purpose languag
All of them Device interconnect standard None of the above
C D B
None of the above
EBCDIC None of the above
A A
program is run
BC 81
BC 82
BC 82
A device used in data communications to divide a transmission signal into several subbands is known as a Third generation languages such as COBOL, C, and FORTRAN are referred to as Serial Communication is used over long distance because it In what areas is the COBOL programming language used?
Modem
Demodulator
High-level languages
Middle-level languages
BC 83
It is faster It is less error than parallel prone communicat ion Financial Graphic design sector and and education engineering
BC 83
The primary function of a front-end processor is to
Communicat e with the console operator
Manage the paging function in a virtual environment
BC 84 BC 84
What is the first stage in program development? Which of the following is not used for data transmission within a local area network What is System Analysis?
Specificatio n and design Fiber Optics
System Analysis Coaxial Cable
e providin g very efficient executio n Frequen Time Division cy Multiplexor division multiple xor LowNone of the above level languag es It is less Uses only one prone to path attenuat ion Accounti None of the above ng systems, commer cial sector Relieve Reduce the main competition CPU of between the repetitiv input/output e devices commun ication tasks Testing None of the above Commo n carrier System Analysis involves creating Telephone Lines
B C
BC 85
The design of the screen the user will see
System Analysis defines the format and type of data the
None of the above
and use to enter or display data
program will use
BC 85
BC 86
A device to device hardware communication link is called What will a good software provider consider?
A cache
An interface
a formal model of the problem to be solved A buffer
An online protocol
The different types of network to be used Star 10101010 Parity
Testing to check for errors before the system is introduced
BC 86 BC 87 BC 87
BC 88 BC 88
BC 89 BC 89
BC 9
The topology of a network can be each of the following except What is the 8-bit binary value of the decimal number 85? Which is the most common data transmission error checking method What is the decimal value of the binary number 1111? Which of the following devices merges communication signals onto a single line What is the decimal value of the octal number 215? Which tool is used to help an organization build and use business intelligence? Cache memory enhances
Packet 01100101 Retransmission
Hardwar e, Software and size of program . Ring 0101010 1
None of the above
Bus None of the above
B C A
Cyclic Hash Count Redunda ncy 64 Multiple xor 97 Data manage ment systems seconda ry storage None of the above Acoustic coupler
15 Port
4 Modem
A C
327 Data warehouse memory capacity
141 Data Mining tools memory access time
None of the above All of them
B B
secondary storage access time
BC 90 BC 90
What is the decimal value of the hexadecimal number FF? Numbers are stored and transmitted inside a computer in What is the hexadecimal value of the decimal number 1476? A byte corresponds to What does EBCDIC coding of numbers mean? A Kb corresponds to
30 binary form
255 ASCII code form
capacity 256 decimal form 5C4 16 bits Bit Code Design 210 bits 01110 decimal form Numeric Keypad is the first bit in a byte It has ears bytes Joystick MHz Reading bar codes
None of the above alphanumeric form None of the above 32 bits None of the above 210 bytes None of the above alphanumeric form None of the above is the last bit in a byte None of the above
B A
BC 91 BC 91 BC 92 BC 92 BC 93 BC 93 BC 94 BC 94
4C5 4 bits Basic Coding Description 1024 bits
1B7 8 bits Binary Coded Decimal 1000 bytes 01112 ASCII code form Keyboard used to detect errors Its moves like a mouse baud Light pen MIPS Tracing diagrams
A B D A A A A B
BC 95
BC 95 BC 96 BC 96 BC 97
What is the binary sum 10000 of 01011 and 00101? Information is stored and binary form transmitted inside a computer in Where would you find Mouse the letters QWERTY? A parity bit is used to indicate uppercase letters How did the computer Because it mouse get its name? squeaks when moved Clock speed is measured bits per in second What are you most likely to use when playing a computer game? CPU performance may be measured in A digitising tablet can be used for? Touch screen BPS Printing letters
Hertz None of the above VLSI None of the above
D C B B
BC 97
BC 98 BC 98
In processing cheques which of the following I/O techniques have banks traditionally used Which of the following is a pointing device used for computer input? A UPS
OCR
MICR
barcode scannin g CD-ROM drive provides backup power in the event of a power cut Light sensitive element s 5 Mb External file labels
voice recognition
Touch screen increased the storage capacity of a computer system Refillable ink 100K Limit checks
Hard disk increases the process speed
None of the above none of the previous
A C
BC 99
What does a light pen contain? The capacity of a 3.5 floppy is around A procedural control used to minimize the possibility of data or program file destruction through operator error is the use of A predefined computational task is referred to as a(n): Which of the following is not the feature of GAPs
Pencil lead
None of the above
BC 99 BC11 5
1.44 Mb Control figures
1 Gb Cross footing tests
B C
BS 319 CA 486
array. Wide access to various data base ACL A sample of transactions
constant. Can extract and analyse data
function.
formula. Can define the audit objectives
C D
CA 487 CA 488
Which is the example of CAATs In audit procedures, test data is
CA
Which of the following is
Tests of
Can aid in simple selectio n IDEA High End CAATs A utility software A programme special purpose written program Analytical review Complia
All of the above None of the above
D A
All of the above
489
not the use of CAATs
details of transactions
procedures
CA 490 DB 01 DB 02
DB 03
Which of the following are called explicitly by another procedure? What term applies to a collection of related records in a database? All of the following terms are related to computerized databases except which one? What is a database?
Macros clipboard search
Action Procedures file sort
nce tests of general EDP controls Event General Procedur Procedures es field layout field names An organise d way of storing informat ion about a set of similar things A docume nt which contains text Relation al DBMS is related to data mining Comput er matchin g An organise d way of storing record grab
D B D
A way to analyse and manipulate numerical information
A tool to produce high quality documents
A way of maintaining a log
DB 04
What does a record contain?
Information about certain programs remote DBMS storing data offline at a separate site Key verification A way to analyse and manipulate numerical
It contains all the data about one specific item relative DBMS backing up data regularly Computer sequence checks A tool to produce high qualitydocument s
A collection of files
DB 05 DB 06
An RDBMS is a Data Warehousing refers to Unauthorised alteration of on-line records can be prevented by employing What is a database?
Reliable DBMS uses tape as opposed to disk Database access controls None of the above
C C
DB 07
DB 10
information
DB 11
What does a record contain?
Information about certain programs Reports allow users to extract information as hard copy (printed output) Extracting and analysing data Compilers, interpreters, editors
It contains all the data about one specific item Reports provide a very flexible way of creating and editing documents
DB 12
What is a report?
DB 13
What is the best way to analyse and change data What are some popular office orientated software applications?
Spreadsheets make data easy to analyse Network software, backup systems
informat ion about a set of similar things A docume nt which contains text A tool which allows text and graphics to be placed in docume nts Using queries Word process ors, spreads heets, databas es, DTP PRIMARY KEY and UNIQUE constrai nts ALTER TABLE Relation al DBMS is
None of the above
None of the above
None of the above
DB 18
None of the above
DB 19
DB 20
DB 226 DB
Which of the following constraints can be used to enforce the uniqueness of rows in a table? Which of the following commands is used to change the structure of table? An RDBMS is a Data Warehousing refers
DEFAULT and NOT NULL constraints CHANGE TABLE remote DBMS storing
FOREIGN KEY constraints
IDENTITY columns
MODIFY TABLE
UPDATE TABLE
relative DBMS backing up data
Reliable DBMS uses tape as
C C
227
to
DB 235
DB 24
You are creating a client application that calls ActiveX DLLs. Which of the following properties of the Err object provides the name of a component that sends an error back to the client application? This database holds personal information. The user can help to keep it confidential by If the database holds customer names and addresses, personalised letters can be created automatically using Application software suited to storing the survey information obtained in the table would be The characters * and ? are sometimes used in search criteria as Which of the following field types will generate the primary key automatically? Referential integrity ensures that the:
data offline at a separate site Number
regularly
related to data mining Compon ent
opposed to disk
Description
Source
using a password
keeping a backup copy
DB 26
the product code
the primary key
keeping the original paper copy mail merge
saving the file with different filenames e-mail
DB 27
A database
Graphics
browser
DB 30 DB 365 DB 366
bookmarks Auto Primary records in a dynaset are consistent with the underlying tables.
operators Auto ID
wildcard s AutoNu mber forms in a databas e are consiste nt with the underlyi ng
engines Auto Key
C C
related tables in a database are consistent with one another.
reports are consistent with the underlying tables or queries.
DB 367
Tables are related to one another through a:
foreign key.
main form and a subform.
DB 368 DB 369
A foreign key is:
DB 370
DB 371
DB 372
You are creating a banking database to track customer loans. The bank will, of course, have many customers, each of whom may take out one or more loans, while each loan may be associated with only one customer (there are no joint accounts). What is the relationship between the Customers and Loans tables? In a one-to-many relationship between Companies and Employees, which field is found in both tables? Which of the following ensures that records in related tables are consistent with one another? For example, it ensures that you cannot add a record with an invalid foreign key. How would you delete a relationship between tables in the Relationships window?
the primary key of both related tables. One-to-one
the primary key of the related table. One-to-many
tables or queries. query and its associat ed dynaset. a field from an unrelate d table. Many-tomany
report and its related query.
not a primary key of either related table. Many-to-one
EmployeeID
CompanyID
Employe eLastNa me The join line
CompanyAddress
The Tools menu, Relationship window
Referential integrity
The one-to-many relationship
Double click the Relationship line
Right-click the Relationship line, then select Delete from the shortcut menu
Select Undo in the Relation ships pull-
Click the Delete Relationships button on the toolbar
DB 373
In a Customers tables, what does a plus sign next to the CustomerID field mean?
That there are several customers associated with that ID They must both be numbers
That some of the data is not viewable
DB 374
What is required of the fields that join two tables?
They cannot be text fields
DB 375
Assume a one-to-many relationship between the Customers table and the Loans table, with referential integrity in effect. What happens when you attempt to delete a customer ID from the Customer table that still has entries in the Loans table?
Nothing, Access ignores the attempted command.
The customers ID is deleted from the Customers table.
DB 376
Which of the following is true when viewing a main form and its associated subform in the Form Design view? Which of the following relationships does not belong in a database based on a professional sports league such as
The subform is not visible.
The subform is displayed in Datasheet view.
DB 377
A one-tomany relationship between teams and
A one-to-many relationship between teams and coaches
down menu That there are records in a related table They cannot be AutoNu mber data types The custome rs ID is deleted from the Custome rs table, and all the related loans are deleted from the Loans table. The subform is displaye d in Form view. A oneto-many relations hip between
That records can be added by clicking on the plus sign
They must be the same data type
An error message is displayed.
The subform is an object on the form and can be moved or sized like any other object. A many-to-many relationship between players and teams
football or basketball? DB 378 Which symbol is used at the end of the join line in a related table to signify the many side of a one-to-many relationship? You have created a oneto-many relationship with referential integrity between a Customers table and a Loans table. From which table can you delete a record? The correct order of the arguments for the MsgBox statement is: The first statement in a procedure named CreateList is: Which of the following is TRUE related to form fields?
players # M
coaches and teams
DB 379
Either table at any time
The Customers table only when there are Loan records associated with that customer prompt, icon, title bar text. Sub CreateList. A text field enables the form user to choose from one of several existing entries.
The Loans table at any time
Neither table
DB 380 DB 381 DB 393
prompt, title bar text, icon. Dim CreateList. A check box enables the form user to choose from one of several existing entries.
title bar text, prompt, icon. CreateLi st. A dropdown list enables the user to choose from one of several existing entries. does not have to be set. create tables of rows and columns .
title bar text, icon, prompt. Sub. A drop-down list enables the user to enter text.
B C
DB 394 DB 401
A text field: The purpose of a database is to:
must be set for one word. help people keep track of things.
must be set for multiple words. store data in tables.
must be set for two words. maintain data on different things in different tables.
C A
DB 402 DB 403 DB 404
A database stores: A database records: A sales contact manager used by a salesperson is an example of _______________
data. facts. single-user database application
relationships. figures. multiuser database application
DB 405
A Customer Resource Management (CRM) system is an example of_________
single-user database application
multiuser database application
DB 407
DB 408 DB 409 DB 410
The industry standard supported by all major DBMSs that allows tables to be joined together is called __________. A program whose job is to create, process and administer databases is called the _____ Microsoft Access may use which of the following DBMS engines? Which of the following are basic components of an enterprise-class database system?
Sequential Query Language (SQL) Database Modeling System Jet The user
Structured Question Language (SQL) Database Management System SQL Server The database application
metadat a. informat ion. ecommer ce databas e applicati on ecommer ce databas e applicati on Structur ed Query Languag e (SQL) Data Business Model System Oracle The databas e manage ment system (DBMS) None of above
all of the above a and b a or b
D D A
None of above
Relational Question Language (RQL) Relational Model Manager a and b All of the above.
D D
DB 411
In an enterprise-class database system ________ .
the database application( s) interact(s) with the DBMS
the DBMS accesses the database data
All of above
DB 412 DB 413
In an enterprise-class database system, the database application ___ . In an enterprise-class database system, reports are created by ____________________ .
creates queries the user
creates form
creates reports the databas e manage ment system (DBMS) it contains a descripti on of its own structur e holds indexes stored procedu res as a redesign of an existing databas e as a redesign of an existing databas e as a redesign of an existing databas
b and c
the database application
the database
DB 414
A database is considered "self-describing" because _______ .
all the users' data is in one place
it reduces data duplication
All of the above.
DB 415 DB 416 DB 417
DB 418
DB 419
In an enterprise-class database system, the database _________ . A database may contain _________________________ . A database designed using spreadsheets from the Sales department is a database being designed _________________________ . A database designed to implement requirements for a reporting application needed by the Sales department is a database being designed _______ . A database designed to combine two databases used by the Sales department is a database being designed
holds user data tables from existing data
holds metadata metadata as a new systems development project
All of the above. All of the above. a and b
D D A
from existing nondatabase data from existing data
as a new systems development project
a and b
as a new systems development project
a and b
DB 420 DB 421
DB 422
DB 423
DB 424 DB 425
_________________________ . Database professionals use ________________ as specific data sources for studies and analyses. Database professionals use a set of principles called ________________ to guide and assess database design. A very popular development technique used by database professionals for database design is known as _______________________ . A very popular development technique used by database professionals to adopt a database design to new or changing requirement is known as _____ . The predecessor(s) of database processing was (were) __________ . In a relation _________________________ _.
e data marts normalization data models data models entity-relationship data modeling entity-relationship data modeling A
data marts
normalization
data marts
normalization
data models
entity-relationship data modeling
data marts
normalization
entityrelations hip data modelin g network models the order of the rows is unimpor tant row key
data migration
file managers entities in a column vary as to kind
hierarchical models the order of the columns is important
relational data model more than one column can use the same name
A C
DB 426 DB 427 DB 428
An attribute is also known as a(n) . A combination of one or more columns used to identify particular rows in a is___ . A combination of two or more columns used to identify particular rows
table record
relation field
field tuple
D C
record
field
composi te key
foreign key
DB 429 DB 430
DB 431
DB 432
DB 433
in a relation is________ . A determinant that determines all the other columns in a relation is______ . When designing a database, one of the candidate keys in a relation is selected as the _________ . Normalization is a process used to deal with which of the following modification anomalies? When you are given a set of tables and asked to create a database to store their data, the first step is to ____ . Modern microcomputer personal DBMS products______.
record
field
foreign key foreign key
candidate key
composite key
primary key
surrogate key
Insertion anomaly
Update anomaly
Deletion anomaly
All of above
DB 434
Which of the following are true about data mining applications?
DB 435
We have obtained access to the company's operational data. We examine 50 records for customers with phone numbers that should use the current area code of 345. Of these 50 records, we find 10 that still use an older area code of 567. This is an example of________
assess the existing tables' structure and content are supplied by several wellestablished manufactur ers They use sophisticate d mathematic al techniques. dirty data
design the database structure were essentially killed off by MS Access
create one or more new tables have poor respons e time Noninte grated data
move the data into the new database are not true DBMS products
Their report delivery is more difficult than report delivery for reporting systems. inconsistent data
None of the above
noninteg rated data
a "wrong format" problem
DB 436
DB 437
We have obtained access to the company's operational data. We have been asked to produce a report with an item by item analysis of sales, but the only sales figure available is the total sale value for each order. This is example of_____ A data warehouse database differs from an operational database because:
dirty data
inconsistent data
noninteg rated data
a "wrong format" problem
data warehouse data are not stored in tables. Form Forms and reports It will be easier for the user to upgrade it if the objects and tables are in one database.
data warehouse databases do not have metadata.
DB 463 DB 464 DB 465
Which of the following objects is used to display a menu? Which of the following objects are NOT found in an Access application? You are developing an Access application that you expect to upgrade periodically. Which of the following statements is TRUE?
Table Queries and tables It will be easier for the user to upgrade it if the objects are in one database and the tables in another.
data warehou se data are often denorm alized. Report Macros It is advisabl e to put each object and table into a separate databas e. All objects in an applicati on, includin g the tables, must
b and c
Query Spreadsheets Regardless of how the objects and tables are stored, the user will have to reenter the data in the tables when the application is upgraded. An application can be created in such a way that it objects such as forms and reports can be changed without disturbing the existing data.
A D B
DB 466
Which of the following statements regarding Access applications is NOT true?
The Link Tables command can be used to associate the tables in one database with the
An application may consist of multiple databases, each with multiple objects, linked to yet another database containing only
objects in another database.
tables.
DB 467
DB 469
Which of the following brings a copy of the table into the current database and does not maintain a tie to the original table? What makes a database an application?
Import
Link
reside within the same databas e. Merge
Join
It contains more than one table
It contains tables, reports, queries, and forms
DB 470 DB 503
What is the Access tool that is used to create the user interface? The purpose of a data warehouse is to:
Menu Wizard create backups for mission critical corporate data.
Build Menu centralize the manageability of data collection.
DS 279 DS 59
____________ is the art of protecting information by transforming it into an unreadable format. Which of the following activities would most likely detect computerrelated fraud? A digital signature is used primarily to determine that a
Decryption
Cipher
It contains a user interface , or switchbo ard Interfac e Design Wizard put key business informat ion into the hands or more decision makers. Encrypti on Conducti ng fraudawarene ss training. Receive d by the intended
It contains macros
Switchboard Manager store all corporate transaction data in one single location.
D C
Cryptography
Using data encryption.
Performing validity checks.
Reviewing the systems-access log.
DS 62
Unaltered in transmissio n.
Not intercepted en route.
Sent to the correct address.
message is: DS 63 What is a major disadvantage to using a private key to encrypt data? Both sender and receiver must have the private key before this encryption method will work. The private key cannot be broken into fragments and distributed to the receiver.
DS 66
EC 103 EC 301
Which of the following Collision. risks can be minimized by requiring all employees accessing the information system to use passwords? The most beneficial Error advantage of ERP checking system is What is the term that describes spying on ones business rivals to gain a competitive advantage? What would you NOT be looking for when spying on a competitor? An online drugstore such as Drugstore.com is an example of_______ Competitive espionage
Data entry errors.
recipient . The private key is used by the sender for encrypti on but not by the receiver for decrypti on. Failure of server duplicati ng function. Low cost of operatio n Industria l espiona ge Researc h data ecommer ce databas e applicati on Includin
The private key is used by the receiver for decryption but not by the sender for encryption.
Firewall vulnerability.
Data Integration
Quality management Economic espionage
Corporate espionage
EC 302 EC 406
A list of competitor s clients single-user database application
Contact numbers of the management group multi-user database application
A competitors new project None of above
EC 51
Which of the following is
Replying
Keeping
Using all capital
EC 58
an example of unacceptable online netiquette? Which of the following statements is correct concerning the security of messages in an electronic data interchange (EDI) system?
promptly Removable drives that can be locked up at night provide adequate security when the confidentiali ty of data is the primary risk.
messages short Message authentication in EDI systems performs the same function as segregation of duties in other information systems.
g the Subject Encrypti on perform ed by a physicall y secure hardwar e device is more secure than encrypti on perform ed by software . No border 2,2,2
letters Security at the transaction phase in EDI systems is not necessary because problems at that level will be identified by the service provider. C
EX 1 EX 10
EX 11
On an Excel sheet the active cell is indicated by Cell A4 =2 and A5 = 4. You select both cells and drag the fill handle down to A8. The contents of cells A6, A7, and A8 are _____. If a cell shows ####### , it means that _____.
A dark wide border 8,16,32
A dotted border 2,4,2
A blinking border 6,8,10
A D
your formula has a syntax error
the row is too short to show the number at the current font size
EX 12
EX 13
Which is not an advantage of using computerized spreadsheets? The gym teacher has a new program to
ability to generate tables word processing
speed of calculation graphical
the column is too narrow to show all the digits of the number flexibilit y of moving entries databas e
either b or c
cost of initial setup spreadsheet
EX 14 EX 15 EX 2
calculate physical fitness in terms of weight and exercise. The use inputs different weights or amounts of exercise to determine the related physical fitness. This "What if" program is most likely which of the following types of software? The difference between the highest and the lowest values. Spreadsheets can be used for... To select a column the easiest method is to
Range Producing graphs double-click any cell in the column ENTER array.
Address Writing letters drag from the top cell in the column to the last cell in the column CTRL + ENTER function.
Gap Drawing pictures click the column heading TAB constant . =C5+D5 . Numeric constant s *
Rows Document filing click the column label
A A C
EX 3 EX 320 EX 321 EX 322 EX 323 EX 324 EX
If you press _____, the cell accepts your typing as its contents. The contents of cell C15 is =AVERAGE(C3:C14). AVERAGE(C3:C14) is known as All of the following are considered constants EXCEPT: Which of the following may NOT be included in a formula? Which of the following is NOT a valid mathematical operator in Excel? Given the formula =B5*B6+C3/D4^2, which expression would be evaluated first? Which part of the
INSERT formula.
A B
100. Cell references ^
(201)555-1212. Functions /
Tom McKenzie. Text constants \
C D D
B5*B6
C3/D4
D4^2
It is impossible to determine. G7*SUM(H9:H11)
E12
SUM(H9:
325 EX 326
formula +E12/6+ (G7*SUM(H9:H11) is considered a constant? How can you tell which cell in a worksheet is the active cell? How can you change the active cell?
H11) It is surrounded by a heavy border. By clicking in a different cell It is blinking. It is displaye d in reverse video. By either clicking in a different cell or using the arrow keys to move to a different cell The Cell Format comman d on the Edit menu the Save As comman d on the File menu. View The phrase active cell appears in the Status bar. By typing the reference of the cell you want to move to in the formula bar A
EX 327
By using the arrow keys to move to a different cell
EX 328
Which of the following would you use to change the font size of a cell in Excel? The command that will save the current workbook with a different file type is: The command that will print an Excel workbook is found on the ____________ menu. In the Save As and Open dialog boxes, the ___________ view shows the file size as well as the date and time a file was last modified.
The Standard toolbar
The Formatting toolbar
The Font Size command on the Tools menu.
EX 330
the New command on the File menu. File
the Save command on the File menu.
the File Type command on the File menu.
EX 331 EX 332
Edit
Window
Preview
Details
List
Properties
EX 333 EX 334 EX 335 EX 336 EX 337 EX 338 EX 339 EX 340 EX 341 EX 342 EX 343 EX 344
Which of the following commands will automatically adjust cell references in formulas? Which of the following commands will remove cells, rows, or columns from a worksheet? Which of the following options is NOT controlled through the Page Setup command? Which command enables you to change the margins for a printed worksheet? All commands are carried out on a rectangular groups of cells known as a: Which of the following is a valid cell range? In a copy operation, the cell(s) you are copying from is called the: In a copy operation, the cell(s) you are copying to is called the: Which of the following commands is needed to duplicate the contents of a cell in another? A cell reference that does not change during a copy operation is known as Which of the following is considered an absolute cell reference? Cell E3 contains the function =AVERAGE(A3:D3). If the contents of cell E3 are copied to cell E4,
Insert
Delete
Clear
Delete
Orientation (portrait or landscape) Options
Headers and footers Page Setup
Both Insert and Delete Both Clear and Delete Fonts
Clear
Remove
Margins
View
Edit
worksheet.
range.
group.
cell group.
6 copy range. paste range. The Duplicate command absolute
D12, G25 destination range. destination range. The Copy command relative
D12:G25 clipboar d. clipboar d. The Paste comman d mixed
D source range. source range. Both the Copy and Paste commands constant
C D B D
B4 =AVERAGE( A3:D3)
$B4 =AVERAGE(A4:D 4)
B$4 =AVERA GE($A$3 :$D$3)
$B$4 =AVERAGE($A$4: $D$4)
D B
EX 345
EX 346
EX 347
what will be the contents of cell E4? Cell E3 contains the function =AVERAGE($A$3:$D$3). If the contents of cell E3 are copied to cell E4, what will be the contents of cell E4? Which of the following commands is needed to transfer the contents of one cell range to another? The F4 key is used to:
=AVERAGE( A3:D3)
=AVERAGE(A4:D 4)
=AVERA GE($A$3 :$D$3)
=AVERAGE($A$4: $D$4)
The Move command
The Cut command
The Paste comman d cycle through absolute , relative, and mixed cell referenc es. the Formatti ng toolbar Rightclick a cell and click the Edit Hyperlin k comman d. whether the cell has an absolute or a relative cell
Both the Cut and Paste commands
copy and paste cells.
edit cells.
cycle through open applications.
EX 352 EX 353
Which of the following quickly copies the formatting of a selected cell to other cells? Which of the following will insert a hyperlink into an Excel worksheet?
the Fill Handle Select the Insert Hyperlink command from the File menu.
the Format Painter Click the Insert Hyperlink button on the Standard toolbar.
Conditional formatting Double-click a cell and click the Insert Hyperlink command.
EX 354
Conditional formatting applies formatting to a cell based on:
whether the cell has a formula or a value in it.
the cell address.
the value in the cell
EX 358
If you enter a date into a cell, Excel stores the date as: You created a worksheet on July 30 and entered the =Today() function in cell E17. You opened that worksheet again on August 31. What will be displayed in cell E17 on August 31? The number of days between two cells containing dates can be calculated by:
text with a two-digit year. July 30
text with a fourdigit year.
referenc e. an integer.
EX 361
August 31
=Today( )
text with either a two-digit or fourdigit year, depending on the format. It is impossible to determine from the information given.
EX 362
subtracting the earlier date from the later one. the F4 key. 3/4
adding the earlier date to the later one.
EX 363 EX 364 EX 384 EX 4
The function key that is used to quickly edit the contents of a cell is: What will be stored in a cell if 3/4 is entered in it?
the F2 key. .75
subtracti ng the later date from the earlier one. the Esc key. March 4 of the current year a constant . B1;G10
adding the later date to the earlier one.
the F1 key. Either 3/4 or .75, depending on the cell formatting either a cell on a worksheet or a variable. B1:G10
B C
EX 42
A users response to the a cell on a InputBox function can be worksheet. stored in: The cell reference for a B1-G10 range of cells that starts in cell B1 and goes over to column G and down to row 10 is _____. The teacher has a AVERAGE spreadsheet showing all Year 10 students and their marks in one Mathematics test. To find the student with the highest mark, which of
a variable. B1.G10
D D
COUNT
MAX
SUM
EX 43 EX 462
the following functions should be used? Which chart type best shows proportions of a whole? Which of the following is TRUE regarding chart types?
Combinatio n Once a bar chart is chosen it cannot be changed to a column chart.
Line Once a column chart is chosen it cannot be changed to a bar chart.
Pie Once a pie chart has been chosen it cannot be changed to line chart. hold down the ALT key Transfer informat ion to a databas e
Scatter Once a line chart has been chosen it can be changed to a pie chart.
C D
EX 5
EX 52
EX 57
EX 6
EX 6
To select several cells or ranges that are not touching each other, you would _____ while selecting. Your Institute teachers have set an assignment on Studies. You are required to use a spreadsheet to record all that you study on each day for four weeks. You decide to show each weeks data with an accompanying graph. What is the best way of doing this? What would be the best method to quickly copy the formula from the active cell to each cell below it? To arrange rows in alphabetical order based on column A, you need to use the command _____. What can you NOT do with a spreadsheet?
hold down the CTRL key Use tables
hold down the SHIFT key
hold down CTRL + SHIFT
Create four separate files
Use multiple sheets
Paste
Fill Down
Fill Right
Paste Special
Tools | Sort
Data | Sort
Edit | Data | Sort Create forms
none of the choices
Analyse data
Calculate data
None of the above
EX 7
To print just part of a sheet, you would select what you want to print and _____ .
click the Print button
press the PRINT SCREEN key
EX 7 EX 8
EX 8 EX 9
Spreadsheets can be used for... The formula that will add the value of cell D4 to the value of C2 and then multiply by the value in B2 is _____. Which of the functions is not valid for performing addition The default orientation for the printed page is _____. Which is not a valid cell address? Which of the following best describes uploading information? A characteristic of a communication channel that is the amount of information that can be passed through it in a given amount of time, expressed in bits per second. The act of searching through storage to locate information without necessarily knowing of the existence of the information being
producing graphs (D4+C2)*B2
writing letters D4+C2*B2
select Print selectio n on Page Setup | Sheet and then print drawing pictures =(D4+C 2)*B2
select Print selection in the Print dialog and then print
None of the above =(B2*(D4+C2)
A C
=SUM(A3:C 3) portrait
=A3SUM:B3SUM :C3SUM landscape
=A3+B3 +C3 whateve r was last used A0 storing data on the hard drive Size
None of the above vertical
B A
EX9. IN 01
AD213 storing data on a disk drive Bandwidth
ZA1 sending information to a host computer Speed
None of the above receiving information from a host computer Channel
C B
IN 02
IN 03
Find
Save
Browse
Retrieve
IN 04
IN 05
IN 06
IN 07
IN 08
IN 09 IN 10 IN 104
IN 11 IN
sought. The principles, means Photography Digital Signature and methods for rendering information unintelligible and for restoring encrypted information to intelligible form. A long string of Key Lock seemingly random bits used with cryptographic algorithms to create or verify digital signatures and encrypt an decrypt messages and conversations. Protected/private User-id Password character string used to authenticate an identity or to authorize access to data. The successful act of Penetration Retrieval bypassing security mechanisms of the system. A set of rules and Acts Regulations formats, semantic and syntactic, that permits entities to exchange information. An attempt to get access Spoofing Imposting to a system by posing to be an authorised person. An action or event that Loss Threat might prejudice security. According to information Sales - tax Income - tax Technology Act, 2000, authorities authorities To investigate contraventions the controller of certifying authority shall exercise the like powers to that of Malicious software. Utility Pirated software None the person who is Tim Berner Hoffman
Cryptogr aphy
Message Digest
Hash Function
Formula
Name
Address
Cryptogr aphy Address
Password Cracker
Protocols
Unautho rising Exposur e Judge of a civil court
Approving Hacking Police officer of IPS rank.
A B B
Virus Charles
Cracker Howard Aiken
C A
110 IN 111 IN 112
known as father of Internet This website is the biggest bookstore on the earth. When we talk of Data Transmission modes, then ATM stands for A sequence of bits or characters that identifies the destination and the source of a transmission. The means of communicating between networks A group of computers and other devices dispersed over a relatively limited area and connected by communication links that enable a device to interact with any other on the network. The term HTTP stands for A NIC is considered as A hub is a device that can connect Which of the following is true concerning the function of a switch?
Lee Etrade.com Automated Tailor Machine Acts Amazon .com Any Time Money
Bubbage Dell .com Asynchr onous Transmi ssion mode Address Msn .com None of above B C
IN 12
Regulations
Protocols
IN 13 IN 14
Router LAN
Gateway WAN
Port CAN
Pin PAN
B A
IN 15
IN 155 IN 156 IN 157
hyper terminal tracing program National Informatics Center Only Computers Concentrate s connectivity
hypertext tracing program Network Interface card Can not computers Combines connectivity of a hub with the traffic regulation of a bridge
IN
What do routers
Bridges and
Two or more
hyperte xt transfer protocol New Informat ion Card Only printers Switches data from incomin g ports to outgoing ports. Bridges
hypertext tracing protocol None of the above None of the above All of Above
B D B
Hubs and nodes
158 IN 159 IN 16
connect? What does a router route? Software which prevents external access to a system is termed If four computers are connected to a hub and then to the internet, how many IP addresses are required for these 5 devices? Which of the following in an OSI layer When creating a network from just two PCs, what kind of cable would be used to connect them? An IP address is a To construct a simple LAN of 4 computers, you would connect them with ______connect them What happens to data that is ruined before reaching to receiver
Repeaters. bits firewall
networks frames gateway
and Hubs Packets router
None of the above virus checker
C A
IN 160
One
Two
Four
None of the above
IN 161 IN 162 IN 163 IN 164 IN 165
Physical Layer RG7U
Data-Link Layer Coaxial cable
Network Layer Fiber
All of the above Twisted pair
D B
Physical address A cable
Logical address Hub
A memory address Router
None of the above None of the above
B B
Data return to the sender
It gets destroyed bit by bit.
IN 166 IN 167 IN 168
Bluetooth is
Wireless technology Physical Layer Binary
Wired Technology Data Link Layer ASCII
Which is not one of the recognized IEEE sub layers? The most preferred number system to
It continue on to target device with corrupt data Ultra violet technolo gy Network Layer Octal
None of the above
None of the above
All of the above None of the above
D A
IN 169 IN 17
represent a IP address is A MAC address is of Protocol is
48 Bits software that facilitates connection to the internet Novell PC
48 Bytes a list of rules for transferring data over a network Client
48 KB software that allows file copying Server
48 MB a gateway calling program for internet bridging
A B
IN 172
IN 173
A ............... is a LANbased computer with software that acts as a controlling device for controlling access to at least part, if not all, of a local area network and its available resources. What is the biggest disadvantage of the Ring topology?
Network PC
There isn't one
If one node goes down, it brings down the entire ring
IN 174
IN 175 IN 176 IN 177 IN 178
The .............. of the network concerns how network devices are physically (or optically) interconnected. The principal topologies used with LANs are: What are the various types of bus architecture? What are the various types of ring architecture? In a ................., each workstation attaches to a common backplane via its own physical cable
Physiology
Topology
If the hub goes down, it brings down all of the nodes on that section Both A and B
If the hub goes down, it brings down all of the nodes on all of the rings
None of the above
Bus Linear Parallel Ring
Star Parallel Circular Bus
Ring Both A and B Linear Star
All of above None Both A and B Mesh
D A B C
IN 179 IN 18 IN 180
IN 181 IN 182 IN 194 IN 195 IN 196
that terminates at the hub In a ............... , each work station is directly connected to a common communications channel Which one of the following is NOT a network topology? In a .............. , the cable system forms a loop with workstations attached at various intervals around the loop The Media Access Control (MAC) is a sub layer of the: What are the most common LAN technologies used in networking today? Modem speeds are measured in LAN speeds are measured in WAN speeds are
Ring
Bus
Star
Mesh
Star Ring
Bus Bus
Linear Star
Ring Mesh
C A
Network Layer Ethernet, token ring, DecNET bps bps usually higher than LAN speeds CD-ROM drive must use the World Wide Web key gateway interface a Novell Interface Controller
Transport Layer Ethernet, token ring, FDDI kbps Kbps measured in bytes per second a modem must use electronic mail uniform resource locator used to control a printer
Physical Layer Ethernet , DecNET, FDDI mbps Mbps depend on the transmis sion medium Window s 95
Data Link Layer Ethernet, token ring, ARCnet mips Mips limited by modem speeds
D B
B C C
IN 197 IN 198 IN 20
Accessing the Internet from a typical home PC requires the use of To use the Internet, you
Netscape
B A
IN 205
The worldwide web server uses the following standard interface to act as the middleware: An NIC
must All of the above have a LAN account common application gateway protocol interface interface interfac es a modem connects a computer to a network
IN 21
Accessing the Internet from a typical home PC requires the use of The most widely used network operating system on PC LANs is JPEG and MPEG
CD-ROM drive Linux have to do with compressio n of graphics and video must use the World Wide Web Printer provides access to the Internet used to send email used to send email used to protect a computer room from fires and floods a backup server hardware
a modem
to a compute r Window s package Window s NT the Internet
Netscape
IN 214 IN 218
Novell Netware have to do with Web pages
None of the above none of the previous
C A
IN 22
To use the Internet you
must use electronic mail modem is a CPU register used to browse the Web uses wireless communication medium a form of virus
IN 220 IN 221 IN 222 IN 223 IN 224
A multiplexer is a form of An ISP FTP is
must have a LAN account bridge is a CPU function al unit is part of Netscap e is part of Netscap e a screen saver program a poor file server browser
use appropriate communications software none of the previous make of processor is a protocol for the transfer of files between computers None of the above none of the previous
D A D
Telnet
A firewall is
IN 225 IN 23
A proxy server is A search engine is
an email server IR system for the Internet
none none of the previous
D C
IN 23
IN 24 IN 25
To look for information about interest areas on the internet, the user should use a An ISP FTP is
scanner
CD-ROM
clip-art file is a CPU function al unit is part of Netscap e
search engine
provides access to the Internet used to send email used to send email The layers cannot communicat e with one another.
is a CPU register used to browse the Web uses telephone lines Any layer can communicate directly with any other layer.
make of processor
A D
IN 26 IN 267
Telnet Which of the following is a true statement about the OSI model layers?
IN 268
Which of the following is NOT true about the Internet?
It is one large network.
IN 269
IN 27
The traditional intent and impact of this common type of attack is to prevent or impair the legitimate use of network resources. A firewall is
Password cracking
It is made up of many networks connected into transmission lines called backbones. System intrusion
is a protocol for the transfer of files between computers is part of is a protocol that Netscap allows for remote e login Any Any layer can layer communicate only can with the layer commun above it. icate only with the layer directly above or below it. It works Individual the computers can same connect to it using way as a an ISP. local network. Denial of Port sniffing Service
D C
IN
Which of the following is
used to protect a computer room from fires and floods IP flood
a form of virus
a screen saver program
none of the previous
Flood a Web
Virus
UDP flood
270
NOT an example of a DoS attack that is popular among hackers? A ____________ attack is when a hacker sends a continuous flow of packets to a system. One defense option on a large network is to configure a ____________ to disallow any external traffic. A proxy server is Which of the following would be performed on a network server and not normally on individual workstations? What can be said about the safety of the Internet? hack
server with requests packet
IN 272 IN 273
that initiates a ping flood flood
traffic
firewall
router
switch
hub
IN 28 IN 285
a backup server Apply security patches All sites are safe and reliable.
an email server Update virus definitions
a poor file server Backup data on a daily basis Only large namerecogniz able sites are safe. Use of logical access methods by attachin g itself to a docume nt. Web traffic
none of the above Limit logging on access
D C
IN 288
There are safe and unsafe sites.
ActiveX-enabled sites are safe.
IN 29
IN 290
To secure communication network against wire-tapping the most effective control is One way that a virus CANNOT spread throughout a network is:
Use of identifiers
Use of passwords
Use of encryption methods by scanning the computer for a connection.
by attaching through an FTP to an eport. mail.
IN 297
IN
Which of the following is NOT a means of monitoring employee use of company technology? ____________ would be
Phone
Application updates
A Trojan
Adware
A worm
Spyware
298 IN 30
IN 304 IN 306 IN 307 IN 308
used by parents to monitor their children on their home system. The formal rules and parameters which are established to permit a microcomputer to communicate with the mainframe computer as though it was a terminal of the mainframe are called The two most common tools used to help with extracting information are: Which of the following would NOT be considered an example of cyber terrorism? Which of the following would be a form of cyber terrorism? Which of the following is a likely target of a cyber terrorist that would cause considerable loss of life? An organisation is upgrading its telecommunication lines. Which is the least important objective while upgradation A company posts a price list of its products on its website. The advantage to the customer is that the company can Which of the following is an easy-to-use service to get information on
horse Modems Protocols Multiple xors LAN B
cookies and Trojan horses. An attack on a system for personal gain Economic damage Crashing the stock market, as in the 1930s To carry more network capacity set its prices very high
Trojan horses and key loggers. An attack with the purpose of gaining publicity Disruption in communication Shutdown of military security systems To improve network services
cookies and key loggers. Giving out disinfor mation Disrupti on in supply lines Contami nating water systems To improve system respons e time stop its competit ors seeing their prices USA People Search
key loggers and worms. Changing the content of a Web page All of the above are correct. Shutdown of nuclear plant safety systems
IN 31
IN 31
limit access to computer owners only
To obtain an D accurate inventory of network related equipment and parts and network nodes update its prices D as soon as they are changed
IN 310
People Search
Yahoo People Search
Lycos Search
IN 312 IN 313 IN 314
someone? Which of the following pieces of information would NOT be found online? Which of the following is the most common danger on the Internet? The famous Nigerian Fraud scam offered victims the opportunity to: The fraud type that sends e-mails that claim to be from legitimate sites in order to obtain sensitive information is called _________________. Using the Internet to pursue, harass, or contact another in an unsolicited fashion is called: Setting your privacy settings in Internet Explorer to medium is one way to block: What is the best means of protection from cyber stalking? Which of the following is not an appropriate control over telecommunications software Encryption techniques can be implemented in Hardware-Software Which protocol would be used to download a free anti-virus program from the Internet?
Name of your bank Virus buy stocks.
Date of birth
Personal assets Adware purchas e offshore property . Siphonin g
Criminal records
Fraud invest without risk.
Spyware make large amounts of money by parking funds in their bank account. Hoaxing
B D
IN 315
Shill bidding
Phishing
IN 316
Internet stalking.
cyber stalking.
virtual stalking.
Web stalking.
IN 317 IN 318 IN 32
pop-ups.
cookies.
spam.
viruses.
Use a fake e-mail address. Encryption
Never use your real identity.
IN 33 IN 33
I only irc
Use a proxy server. Physical Message Security controls sequenc e number checkin g II only Both I & II www
Use anti-spyware software. Logical access controls
B B
Neither I or II telnet
C C
ftp
IN 34 IN 348 IN 349
The major advantage of the checksum program is when it Which of the following is a Web browser? A Web page is another name for -----------
Adds more bytes to programs HTML Web query.
Verifies integrity of files Internet Explorer HTML document.
IN 35
IN 350 IN 351 IN 359
Domain names must contain a description of the type of organisation that the domain represents. A very common abbreviation used include: A standard language for creating and formatting Web documents is: The Web page format in which all elements of a Web page are saved as one file is called: Which of the following requires an Internet connection?
.com is used for company
.co in used for company
Increase s boot up time Microsof t Excel round trip HTML docume nt. .con is used for compani es
Misleads a program recompilation both HTML and Internet Explorer Web browser.
B B B
None of the above
round trip HTML. XML.
the World Wide Web Consortium HTML.
HTML. DHTML.
one way HTML. MHTML
C D
using Internet Explorer to view a Web page that is stored on the hard drive on your computer
updating the values that are obtained through a Web query
IN 36
Mr Rao wants to find a website that he briefly browsed over yesterday. After turning on his computer how would he
Click on the Back arrow until the desired site is found
Click on Go to or Search in the browser
clicking a hyperlin k that referenc es a docume nt that is stored in the floppy drive on your compute r Go to the History page and look
viewing an Excel worksheet that you have saved as a Web page.
Go to the Bookmarks or Favorites page
do this? IN 360 IN 45 Which of the following is used to update a Web query? You download from the internet, a screensaver, a ten-second sound file and a ten-second music video clip. You also add a hyperlink. Which of the media elements has the greatest effect on the file size? When saving a photograph for use on a website, which format should you choose? While researching the Direct taxes assignment, you find a useful website. What is the most efficient way to access the site at a later time? A system that uses the Internet for business-tobusiness interaction is called a(n): A block of text automatically added to the end of an outgoing email is called _________ refers to the use of Internet technologies for placing telephone calls. Most client/server applications operate on a three-tiered architecture consisting of which of the following layers? the Refresh command Hyperlink the Insert Hyperlink command Screensaver
for the site the Update comman d Sound
the External Data command Video
IN 47
BMP
GIF
JPEG
TIFF
IN 49
Save it to a floppy disk.
Write it down on a piece of paper.
Add it to Favourit es or Bookma rks. privilege d network. a footer.
Cut and paste it to a word processor document.
IN 493 IN 50
extranet.
intranet.
network topology
an attachment. VoIP
a signature.
an encryption.
IN 501 IN 68
IPT
IPP
PoIP
Desktop client, application, and database.
Desktop client, software, and hardware.
Desktop server, applicati on, and databas e.
Desktop server, software, and hardware.
IN 69 IN 70 IN 71
Which do you NOT need to connect to the Internet? What does FTP stand for? What is the purpose of DNS?
Modem File Transfer Program So computers can be referenced by a name 193.1.2.3 paul .trigg @ domain. org. uk The US government Internet Relay Chat It will be deleted
CD-ROM File Transmission Protocol So IP addresses can be shorter
Telepho ne line File Transfer Protocol So email is delivere d faster 143.215. 12.19 paul.do main.uk No-one Internet Remote Convers ations A letter will be sent to you in the post Hyper Text Mark-up Languag e High volumes of email
None of the above None of the above None of the above
B B A
IN 72. IN 73. IN 74. IN 75.
Which of the following is NOT a properly formatted IP address? Which of the following is a properly formatted email address? The Internet is controlled by whom? What does IRC stand for? If you do not pick up your email for a week...?
45.1.1.1 paul.trigg@dom ain.org.uk Scientists in Switzerland International Relay of Characters It will be waiting for you to collect it Hyperlink Text Marking Language People discussing a topic of interest globally Utility Programs
None of the above None of the above None of the above None of the above
D B C A
IN 76
None of the above
IN 77
What does HTML stand for?
Hyper Textual Mark-up Lingo Receiving messages automaticall y from anyone in the group Application Software
None of the above
IN 78
What is a disadvantage of joining a mailing list?
None of the above
OS 01
Which of the following computer software is designed to direct and assist the execution of application programs
Operatin g system
Database management system
OS 127 OS 131 OS 132 OS 139 OS 193 OS 199 OS 215 OS 216
Formatting a disk results in all the data being...? Which bus carries information between processors and peripherals? Which bus controls the sequencing of read/write operations? Which computers use single chip processors? CPU performance may be measured in In processing cheques which of the following I/O techniques have banks traditionally used Disk fragmentation
Deleted from the disk Data bus
Copied from the disk Auto bus
Saved to the disk Address bus Control bus Super compute rs MHz barcode scannin g is due to bad disk blocks convert sa program to assembl y code convert sa program to machine code compre ssing it an interpret er the power cord The
None of above None of above
A A
Data bus Personal computers BPS OCR
Address bus Parallel computers MIPS MICR
None of above None of above VLSI voice recognition
C A B B
is caused by wear a fast interpreter
caused by overuse slower than an interpreter
none of the previous none of the previous
A compiler is
OS 217
An interpreter is
faster than a compiler
translates and executes programs statement by statement decrypting it a compiler the CU A compile time
none of the previous
OS 219 OS 233 OS 234 OS
Zipping a file means An assembly language program is translated to machine code by Which of the following is not part of the processor If the Cancel Error
encrypting it an assembler the ALU A runtime
transmitting it a linker None of the above You need to carry
C A C A
236
Property of the CommonDialog Box is set to true then which of the following statement is true: __________ control defaults to displaying the files in the current directory: A ____________ occurs any time a program writes more information into the temporary space it has allocated in the memory. Assessing a system requires certain common tools. Which of the following is NOT a tool used to assess a system? The ____________________ Web site has a utility that will tell you what software and operating system a Web server is running. When software vendors discover flaws in their software, they usually will write corrections to their code, known as: All ____________ have the option of blocking ports. Which of the following is NOT a characteristic of a firewall?
error can result if the user clicks the cancel button File List Box
error occurs
OS 238 OS 271
Dir List Box
program execute s without any error Drive List Box RAM overflow
out conditional compilation
Combo Box
memory overflow
systems overload
buffer overflow
OS 274
Netcop
NetBrute
Netcraft
NetBIOS
OS 275
www.nettoo ls.com
www.WhoIs.com
www.net craft.co m
www.netstat.com
OS 276
code correct.
patches.
updates.
upgrades.
OS 277 OS 278
firewalls It can consist of hardware, software, or both. That any open applications
switches It hides your network.
hubs One of its techniqu es is packet filtering. That you are not on the
scanners It is a barrier between your network and the rest of the Internet. That you also shut down associated services
A B
OS 280
Before shutting a service on an individual machine, which of the
Dependencies on other services
OS 281 OS 282
following would you always check? At a minimum, which of the following should be implemented under the protection phase? Attacks on your system may be prevented or trapped through the use of: Setting restrictions as to the number of unique passwords to use before a user can recycle them is called a password: Which of the following is NOT a step to take in securing a workstation?
be exited Antivirus software an intrusiondetection system. cycle. Intrusiondetection software antivirus software.
Internet Firewall Router C
OS 283
renewal.
a network preventi on system. age.
a proxy filtering system.
history.
OS 284
Make sure all update and security patches are applied. Delete it from the system and use the guest account.
Install and keep current antivirus and antispyware programs. Delete it and change the builtin guest account to a power user account.
OS 286
To prevent a hacker from unauthorized access, what should you do with the administrator account?
OS 287
What should be done with old backup tapes and CDs?
OS 289 OS
Which of the following is NOT an example of malware? One step you can take to
Tapes can be used over and over, and CDs should be kept forever. Trojan horse place a
Tapes and CDs can be thrown away in the trash.
Limit users ability to configur e the workstat ion. Disable it and create a nondesc ript user account with administ rator rights. Tapes should be melted and CDs broken. IP spoofing downloa
Block all incoming traffic on a network.
Create another administrator account to confuse the hacker.
Give them to a recycle shop.
Virus add spyware to
Spyware hone your
C C
291
reduce the risk of being infected by a virus is to:
OS 292 OS 293
Which of the following is NOT a sign that a virus has infected your system? Which of the following is the safest way to protect yourself from e-mail viruses?
router between your ISP and your system. System acts abnormal Update antivirus software.
your system.
Files are missing
d files from reliable Web sites. Printing problem s Turn off the autolaunch in your e-mail client. spyware
programming skills.
Problems with your wireless mouse Never open an email attachment unless you know what it is and who sent it. buffer overflow
Do not propagate hoax viruses.
OS 294
OS 295 OS 296 OS 299 OS 300
A ____________ attack causes too much information to be placed into temporary memory space. ____________ gathers user information with the users knowledge. Which of the following is the most common function of spyware? Which of the following is NOT a virus-scanning technique? Which of the following would NOT be a way to protect your system from spyware?
virus
Trojan horse
A virus Obtain system IP addresses E-mail and attachment scanning Use your browsers security settings
A Trojan horse Obtain cookies Download scanning Do not open attachments in unknown e-mails
Spyware Check for open ports File scannin g Avoid skins and toolbar s downloa d Junior account ant The Open
A buffer overflow Obtain usernames and passwords Backup file scanning Use encryption software
C D D D
OS 309
OS 329
For which of the following positions would it be advisable to conduct an extensive background check? Which of the following would you use to open
Administrati ve assistant to the president The Standard
Cook
Network administrator
The Formatting toolbar
The Save command on the
an existing file?
toolbar
OS 355 OS 356
The ability to have multiple applications open at the same time is known as: Which of the following can be changed using the Options command?
multitasking . the default file location of new files
tiling.
comman d on the Edit menu cascadin g. the number of windows you have open minimizi ng
File menu
minimizing.
whether the worksheet prints in landscape or portrait orientation multitasking
the margins on the printed DOCUMENT
OS 357
OS 396 OS 397
Which of the following leaves an application open but shrinks the window to a button on the Windows taskbar? Which of the following actions would move a floating toolbar to dock it in a different place? To display a missing or needed toolbar, click the:
shrinking
cascading
Click on any border and drag. right mouse button anywhere on the Word window, choose the Customize command from the contextsensitive menu, and check the box for the missing toolbar from the Toolbars tab dialog box. All
Click on any corner and drag. right mouse button on any visible toolbar, and click on the missing toolbar.
Click on the title bar and drag. left mouse button on any visible toolbar, and click on the missing toolbar.
You cannot move a floating toolbar. left mouse button anywhere on the Word window, choose the Customize command from the contextsensitive menu, and check the box for the missing toolbar from the Toolbars tab dialog box.
OS
Which of the following is
The password is
Once a
Passwords can be
399
NOT a true statement regarding password protection?
documents are automaticall y saved with a default password.
case-sensitive.
OS 495
The Linux operating systems is an example of: The Windows operating systems is:
public domain software. public domain software. on-demand computing. best-cost provider Operational systems power outages. hot
nonprotective open source software. nonprotective open source software. on-demand software. software provider Informational systems hardware failures. cold
OS 496
OS 497 OS 498 OS 502 OS 504 OS 505
Application service providers offer: A(n) _________ offers ondemand software on an as-needed basis to its clients over the web. _________ are systems used to interact with customers and run a business in real time. The most common cause(s) of disaster is (are): A _______ backup site is backup facility consisting of an empty warehouse with all necessary connections for power and communication, but
docume nt is protecte d by a passwor d, it cannot be opened without that passwor d. protecti ve open source software . protecti ve open source software . utility computi ng. Web service provider Structur ed query systems floods. empty
up to only seven characters long.
proprietary software
proprietary software.
utility software. application service provider Office automation
B D
All of the above. dormant
D B
OS23 9 PP 44
nothing else. To destroy an object and free the memory space occupied by it, the keyword used is: An example of the components of a multimedia presentation could include Which of the following formatting elements can be applied to a PowerPoint diagram using the AutoFormat tool? Which of the following formatting elements can be applied to a PowerPoint diagram using the Format AutoShape command? What happens when you double click a blank graph placeholder in a PowerPoint presentation?
Delete
Kill
Nothing
New
text, graphics and email address. the Line style
text, hypertext and Power Point.
PP 442
the Line color
CDROM, digital camera and sound. the Font and the text alignme nt Line thicknes s
text, hypertext, Power Point, video and sound.
Line style, Line color, text font, and text alignment Fill color, Line color, and Line thickness
PP 443
Fill color
Line color
PP 444
Excel is started so that you can create a chart.
A popup box prompts you for an existing Excel chart to insert.
PP 445
The legend in a Microsoft Graph chart is:
always taken from the first row of data in the datasheet.
always taken from the first column of data in the datasheet.
Microsof t Graph is started so that you can create a graph. taken from the first column or row of data in the datashe et, dependi ng on whether the data
The graph placeholder is deleted.
entered by the user.
PP 446
PP 447
Suppose you are creating a Microsoft Graph of quarterly sales by region. Which would be the best chart type if you want to emphasize the total sales of each region? Which of the following actions will enable you to insert a graph into a PowerPoint presentation?
Side-by-side column
Stacked column
series are in rows or columns . Pie chart
Line chart
Pull down the Insert menu and select Chart.
Click the Insert Chart button on the Standard toolbar.
PP 448
If you are editing a slide containing a Microsoft Graph, how do you display the underlying datasheet? How do you deselect a chart that has been placed onto a PowerPoint slide after you have finished creating the chart? What happens when you click the Datasheet button on the Microsoft Graph toolbar?
It automaticall y displays in Slide view.
PP 449
Single click the chart.
Click the chart object, then click the View Datasheet button on the Standard toolbar. Double click the chart.
Pull down the Insert menu and select the appropri ate Object. Pull down the Edit menu, then select Object. Click outside the chart. The datashe et is saved as a separate file.
Pull down the Insert menu and select Chart, click the Insert Chart button on the Standard toolbar, or pull down the Insert menu and select the appropriate Object. You cannot display the underlying datasheet once the slide is finished. Change to Slide Sorter view.
PP 450
A dialog box is displayed allowing you to enter the name of the Excel worksheet
A dialog box is displayed allowing you to enter the name of the Excel worksheet that should be
The datasheet window is toggled from closed to open (or from open to closed).
PP 451 PP 452 PP 453
What happens if you single click a chart that is not currently active? What happens if you double click a chart that is not currently active? Using custom animation effects, you can build:
that should be linked to the PowerPoint presentatio n. The chart is selected. The chart is selected. a slide one bullet item at a time.
embedded in the PowerPoint presentation.
The chart is deleted. The chart is deleted. bullet items one letter at a time.
The chart is doubled in size. The chart is doubled in size. bullet items one word at a time. Exciting Both enter and exit, and fly in from top or bottom Alt the way objects exit a slide.
The application that created the chart is started. Microsoft Graph will restart. a slide one bullet item at a time, build bullet items a letter at a time, and build bullet items a word at a time. Subtle, Moderate, or Exciting Neither enter nor exit; neither fly in from top nor bottom
PP 454 PP 455
Which of the following animation effects can be added to a slide? Which of the following animations effects can be added to a slide?
Subtle Enter and exit
Moderate Fly in from top or bottom
D C
PP 456 PP 457
Which keyboard key is used to select more than one picture on a slide? Custom animation can be used to affect ONLY:
Enter the way objects appear on a slide.
Shift what objects do after they appear on a slide.
Ctrl Custom animation can be used to affect the way objects appear on a slide, to what objects do after they appear on a slide, and to the way objects exit a slide.
B D
PP 458
Which of the following best describes the information that appears on the advanced timeline?
The advanced timeline shows the sequence in which objects will appear on the slide.
The advanced timeline shows the duration of the effect applied to each object.
PP 459 PP 46
PP 460 PP 461
Which of the following objects can contain custom animation effects? What type of program allows an object within an image to be edited without affecting other objects? Which of the following animation effects can be added to a slide? Which of the following is TRUE regarding the Datasheet?
Clips
Organization charts Draw program
The advance d timeline shows the sequenc e in which objects will appear on the slide and the duration of the effect applied to each object. Text
The advanced timeline shows neither the sequence in which objects will appear on the slide, nor the duration of the effect applied to each object.
Clips, organization charts, and text Animation program
Paint program
Filtering program
Fly in
From top
Dissolve in Data cannot be entered into Datashe et. OLST.
Fly in, From top, and Dissolve in There is no such thing as a Datasheet.
D B
Once data is Once data is entered it entered it can cannot be be changed. changed.
PP 500
Graphical software tools that provide complex analysis of stored data are:
OLTP.
OLAP.
OLIP.
PP43 8
Which of the following statements is TRUE regarding PowerPoint diagrams?
You can change the appearance of a whole diagram, but not individual shapes of a diagram. [Enter+A]
You can change both the appearance of a whole diagram and the individual shapes of a diagram.
PP43 9 VB 237 VB 240 VB 241 VB 242
VB 243
VB
Which keyboard key combination is used to undo the previous command(s)? What is the extension of the Visual Basic project file that stores the design of a user control. Which event of a text box would you use for validating the data entered by the user? Which of the following statements forces inline error handling? The _______ method resets the contents of bound controls to their original values when the user clicks on the cancel button. To deactivate the Form UnLoad event, you make the following change in the function definiton: Private Sub Query_Unload(Cancel as Integer,UnloadMode as Integer) To prevent the Form from closing, you will set the: How many root nodes
[Shift+Z]
You cannot change the style of the connecti ng lines in an Organiz ation chart. [Alt+Z]
You cannot change the color of the boxes in an Organization chart.
[Ctrl+Z]
.ctx
.ctl
.ctr
.ocx
Validate
Validation
Check
Audit
On Error GoTo linelabel UpdateCont rols
On Error GoTo Inline PaintPicture
On Error Stop Refresh
On Error Resume Next Resize
D A
Cancel parameter to a nonzero value
Cancel parameter to 0
UnloadM ode paramet er to a non-zero value
UnloadMode parameter to a zero value
None of the above
244 VB 245
can a TreeView control have? A project group is a Project which:
Consists of several Programs
Consists of several Applications
VB 246
VB 247
Procedures declared in a _____ are local whereas procedures declared in a ______ are available to the whole application. How can you keep the user from exiting a form by clicking the Close button? The _______ property enables Visual Basic to draw complete images in memory before displaying them on the Screen. You want to display the code and the description of an error. What would be the correct syntax? What is the purpose of the Image List Control? Which method would you use to get a free or unused File identifier while opening any file: Which property procedure is used to retrieve the value of a property? Which of the following can be shown to the
Form window, standard or code module Place code in the Terminate event AutoRedraw = True
Project window, view code window Place code in the Unload event AutoRedraw = False
Consists of Various Forms And Code Modules Class module, code module Place code in the Deactiva te event Refresh
Consists of several Projects
None of the above
None of the above
VB 248
PaintPicture
VB 249
Msgbox err.no & err.text To display images to the user FreeFile
Msgbox err.number & err.text To help in creating a ToolBar GetFileNum
VB 250 VB 251 VB 252 VB 253
Msgbox error.nu mber & error.tex t To allow the editing of icons GetFile
Msgbox error.number & error.description To provide a repository for images used by other controls GetBytes
Retrieve
Get
GetProp erty Window s
Value
Common messages
Open dialog box
Input box
VB 255 VB 256 VB 257 VB 258
VB 259
VB 260
VB 261 VB 262 VB 263
user using the Common Dialog control in VB? Which of the following are not properties of Command Button: Which events enable you to determine which key was pressed by the user? In order to access a file in Non-textual format, you have to open file in: Visual Basic displays information depending upon the current value of two properties of the form, called: Which of the following procedure types will execute when you assign a value to a property of an object? In order to overlap the controls (say a command button) during design time, we use the Send To Back or Bring To Front option from the Edit menu. To change it dynamically (i.e.during program execution) we need to change: Which property of the ProgressBar determines how much of the bar is filled? The ______ function can be used to run any .com, .exe, .bat or .pif file from a Visual Basic program. The caption and the name properties of the command button:
passed to Windows Caption Click and KeyPress Ascii Format CurrentX and CurrentY Property Get
explorer Visible Click, KeyUp and KeyDown Binary Format ScaleLeft and ScaleTop MultiLine KeyUp and KeyDow n Input Mode ScaleHei ght and ScaleTo p Property Let Font KeyPress, KeyUp and KeyDown Output mode x and y C D
B A
Property Assign
Property Set
Background color property
Caption property
ZOrder property
AutoRedraw property
Min
Max
Value
CurrentVal
Shell
Substr
SetAttr
CStr
Are one and the same
Can be different at times
Are actually not properti
None of the above
VB 264
VB 265 VB 266 VB 382 VB 383
You try to initialize a new Object variable with the following line but receive an error. What could be the possible cause? Set MyVar = New Classname Which of the following will perform a direct execution of a Command object? The vb Critical symbol displays: vbYesNo is an example of a(n): The primary difference between the MsgBox statement and the InputBox function is the:
You do not need to use the Set command here
You do not have the permission to access the class
es MyVar has not been declared
None of the above
The Open method A warning query icon statement. MsgBox statement returns a value, while the InputBox function does not.
The Exec method A critical message icon variable. InputBox function returns a value, while the MsgBox statement does not.
VB 395
VB25 4
Which of the following is TRUE about a protected form (i.e., a form where the Protect Form button on the Forms toolbar is toggled on and is assumed to remain in that position)? Which event is triggered when the user moves to another open form?
Data cannot be entered into the form.
The form can be modified.
The ExecPro cedure method An exclama tion icon intrinsic constant . InputBo x function can be created with the macro recorder , while the MsgBox stateme nt cannot. Data can be entered.
None of the above
None of the above built-in procedure. MsgBox statement can be created with the macro recorder, while the InputBox function cannot.
B C B
A new check box can be added.
Unload
QueryUnload
Deactiva te
Terminate
WO 01
WO 02 WO 03 WO 04
Veena is entering a paragraph in a word processing program. When the cursor gets to the end of a line, what is the best way to get the cursor to the next line? How are data organized in a spreadsheet? Which key moves the cursor to the beginning of the next line of text? Veena typed the following sentence: "The girl was very beautiful." In which word processing utility could she find a synonym for "beautiful"? Using an electronic bulletin board, Seema can do all of the following except which one? Aryan has created a tenpage story, but only wants to print the first two pages. What printer command should he select? What process should be used to recall a document saved previously? Which is used to indent text within a document? Desktop publishing is a more sophisticated form of which of the following types of software? What is a Word
press the return key
press the tab key
press the escape key
just keep typing
layers and planes tab
lines and spaces enter/return
height and width backspa ce/ delete thesauru s
rows and columns shift
D B
grammar checker
spell checker
outliner
WO 05
WO 06
send a public message to friends interested in one topic Print all
send pictures to a friend
send private messag es to a friend Page setup
send a package to a friend
From ___ To ____
Print preview
WO 07 WO 08 WO 09 WO 1
Enter
Copy
Retrieve
Save
closing database
tabbing graphing
spacing word processi ng Storing
sorting spreadsheet
B C
To analyse
Creating and
None of the above B
Processor used for? WO 10 WO 11 WO 12 What is a picture that is saved on a diskette and can be pasted into a document? What is a Word Processor used for? What basic tools would you find in the Edit menu of a word processor What is a header in a document?
figures subscript
editing documents annotation
informat ion clip art
clipboard
To analyse figures Clear, replace and select Text at the bottom of every page
Creating and editing documents Spelling, grammar and autocorrect Numbers which appear on every page
WO 13
WO 2
What hardware is essential for a word?
WO 25 WO 3
The user could take a picture from a magazine and insert it into the document by using a What basic tools would you find in the Edit
Mouse, printer and processing system keyboard? Browser
Keyboard, Mouse, monitor and printer clip-art file
Storing informat ion Cut, copy, paste and clear Text which appear at the top of every page Monitor, keyboar d and mouse microph one Cut, copy, paste and clear Select all
Making Calculations Font, Paragraph, Bullet and Numbering Designated area on the document
B C
None of the above
digital scanner
Clear, replace and Toolbars Paste
Spelling, grammar and autocorrect Replace
None of the above
WO 32
What command in a word-processing program can be used to change the word him to her, and also the word he to she in the given phrase? On a cold and still night, the only sound that could be
AutoCorrect
WO 34
WO 385
heard was the owl that had ade its home in the nest outside the bedroom window. It was eerie and the babysitter was consistently checking the children. He was new at the job, and had never been to this familys house before now. He was wishing he had visited during the day, just to get a layout of the house. What edit commands would you use to insert a paragraph from one document into another document, while still keeping the paragraph in the first document? Which of the following statements would NOT be a reason for showing suggested revisions in a Word document without changing the original document?
Copy, then paste
Cut, then paste
Delete, then paste
Insert, then paste
To give the original author a chance to accept suggested changes from the person who entered the revisions
To give the original author a chance to reject suggested changes from the person who entered the revisions
WO 386
Which statement is NOT true regarding revisions made in a Word document?
A line appears through text that is to be deleted.
A red underline appears beneath text that is to be added.
To complic ate the revision process and to force the author to spend more time making correctio ns A vertical line outside the left margin signifies
To allow multiple people to work on one document in collaboration with one another
Comments are enclosed in a text box at the right of the document.
WO 387
How are suggested changes entered for review on an initial Word document? Which of the following is TRUE about saving a document using the Versions command?
WO 388
Through the Edit menu by choosing Track Changes command The Versions command will allow you to save multiple versions of a document, including any changes that may have been made to that document.
Through the Tools menu by choosing Track Changes command The Versions command will allow you to save only one version of a document, including any changes that may have been made to that document.
WO 389
What happens when you open a document that has been saved using the Versions command?
All versions are opened automaticall y.
The latest version is opened automatically.
a change has been made at that point in the docume nt. Through tools on the Reviewi ng toolbar The Versions comman d will allow you to save only one version of a docume nt without any changes that were just made to the docume nt. The first and second versions are opened
Both through the Tools menu and the Reviewing toolbar The Versions command will allow you to save only two versions of a document: one version of the original and one version of any changes made to the document.
The previous version is opened automatically.
WO 39
WO 390
You have used the word discover four times in an English essay you have created using a word processing program. You would like to find another word of similar meaning to use instead of discover. Which of the following would you use to do this? When opening and working with multiple versions of a document, how can you tell which is the most recent version?
Dictionary
Grammar check
automat ically. Spell check
Thesaurus
Word displays a list of the dates and times each file was saved.
The most recent version will appear at the bottom of the list.
WO 391
WO 392 WO 398
Various fields are added to a regular document to create a special document called a form through the ____________ toolbar. Which of the following types of fields CANNOT be inserted into a form? Which of the following is TRUE related to editing comments in a Word document?
Fields
Tools
Word will show the name of the person who saved each version. Forms
Word is not able to tell the most recent version of a document.
Insert
Check boxes Comments cannot be edited.
Toggle button Comments cannot be deleted.
Text fields Comme nts can be edited or deleted by right clicking the highlight
A drop-down list Comments can be edited or deleted by left clicking the highlighted text.
B C
WO 4
What is a header in a document?
Text at the bottom of every page
Numbers which appear on every page
WO 40
WO 400 WO 41 WO 440 WO 468 WO 471 WO 472
In your English essay you notice that the paragraph at the bottom of page 1 continues on to page 2. You would like to make this paragraph start on page 2.What would be the best way to do this? Tables in a document help you to easily arrange all of the following EXCEPT: To identify a document, it is helpful to include the file name on each page as a Which of the following tools will copy the formatting of selected text to other places? What is the name of the process of determining the cause of errors in a macro? Drop caps are added to a Word document using the ___________ menu. A reverse in a newsletter is:
Press tab.
Press Return.
ed text. Text which appear at the top of every page Copy and paste.
None of the above
Insert page break.
text.
graphics.
forms.
numbers.
header/foot er. Copy button
bibliography.
find/sear ch. Format Painter button Error Injecting Format the guidelin es used to establis h where different element
macro.
Paste button
This action is not possible. Debugging
Fault Finding Insert a section of white text on a black background.
Bug Squashing
Tools a section of text where the first letter of each sentence is lowercase and the rest are uppercase.
Edit an enlarged capital letter at the beginning of a paragraph.
C A
WO 473
A pull quote is best emphasized by:
setting it in larger type or font size. The reverse technique means to add dark text on a light background.
typing it all in capital letters.
WO 474
Which of the following definitions is CORRECT?
A pull quote is a quotation taken from (pulled) from another document.
WO 475
WO 476 WO 477
WO 478
Pertaining to newsletters, which of the following cannot be changed using the Columns command dialog box? As related to type size, how many points are there to the inch? Assume you are working on a newsletter in which the masthead extends across the top of the entire first page. The rest of the newsletter has two columns. What is the minimum number of sections in the newsletter? Which of the following is NOT correct with respect
The width of each column
The height of each column
s of the newslett er will go. underlini ng the text of the pull quote. A dropped cap is a word that starts with a lowercas e letter when it should have a capital letter. The number of columns 12 Three
changing the color.
A grid is a set of horizontal and vertical lines that determine the placement of elements in a newsletter or other document.
The tab spacing within each column
6 One
10 Two
72 Four
D B
Press Ctrl+Enter
Press Ctrl+Shift+Enter
Press Enter to
Press Shift+Enter to force a line
to page, column, and section breaks? WO 479 WO 480 Which of the following would be the most appropriate font for a newsletter headline? Which of the following is the default Word column width? Assume you are creating a two-column newsletter. Which type size is the most reasonable for the text in the columns? Given the default left and right margins, and -inch spacing between columns, the width of each column in a twocolumn document will be: Assume you have made all appropriate selections in the Columns dialog box in Word, but cannot see any columns on the screen. What is the most likely cause? While word processing, in which of the following situations would Tom use the "Copy" command?
to create a page break. A serif font at 10 points 2 inches
to create a column break. A sans serif font at 10 points 3 inches
create a section break. A serif font at 20 points 4 inches
break. A sans serif font at 45 points It depends on the left and right margins, and how many columns are specified. 25 point D
WO 481
6 point
10 point
15 point
WO 482
2 inches.
2 inches.
3 inches.
impossible to determine.
WO 483
You are not in Print Layout view.
You have not inserted a column section break..
WO 484
to store a file on the hard drive
to store a file on a diskette
WO 5
What does a document
Data about
Mainly text
You have not specifie d continuo us section breaks. to move a section of text from the original location to another location A set of
Word cannot display columns during editing; you will see them only when you print the document. to leave an original section of text in place while pasting a copy elsewhere
None of the above
contain? WO 56 Before submitting your work you want to find any words spelt incorrectly. Which of the following would you use?
a set of similar things Thesaurus
different graphics Spell Checker Gramma r Checker Find and Replace B
S-ar putea să vă placă și
- QuestionsDocument172 paginiQuestionsHarun Raaj GuptaÎncă nu există evaluări
- Foundation Course for Advanced Computer StudiesDe la EverandFoundation Course for Advanced Computer StudiesÎncă nu există evaluări
- Prepking ICDL-IT Exam QuestionsDocument11 paginiPrepking ICDL-IT Exam QuestionsdashwanÎncă nu există evaluări
- C Programming for the Pc the Mac and the Arduino Microcontroller SystemDe la EverandC Programming for the Pc the Mac and the Arduino Microcontroller SystemÎncă nu există evaluări
- NOS-110 Chapter 6 QuizDocument10 paginiNOS-110 Chapter 6 Quiznikkie704Încă nu există evaluări
- Question Excerpt From A+Document55 paginiQuestion Excerpt From A+ramanaidu007Încă nu există evaluări
- CompTIA A+ Certification All-in-One Exam Questions Prep (220-701 & 220-702)De la EverandCompTIA A+ Certification All-in-One Exam Questions Prep (220-701 & 220-702)Evaluare: 2.5 din 5 stele2.5/5 (6)
- IT Essentials Chapter 1 Quiz W - AnswersDocument9 paginiIT Essentials Chapter 1 Quiz W - AnswersAckevia100% (3)
- Computer for Kids: Input, Output and Storage DevicesDe la EverandComputer for Kids: Input, Output and Storage DevicesÎncă nu există evaluări
- QPDEC2010 Sem 1Document16 paginiQPDEC2010 Sem 1Vishal KanojiyaÎncă nu există evaluări
- Embedded C Programming: Techniques and Applications of C and PIC MCUSDe la EverandEmbedded C Programming: Techniques and Applications of C and PIC MCUSEvaluare: 3 din 5 stele3/5 (3)
- COA Netacad FullDocument284 paginiCOA Netacad Full69th guyÎncă nu există evaluări
- Computer Knowledge Bit Bank for All Competitive ExamsDe la EverandComputer Knowledge Bit Bank for All Competitive ExamsEvaluare: 4 din 5 stele4/5 (4)
- I.T. Chapter 6: A Docking Station May Have PCI Slots For Expansion Cards and SpeakersDocument8 paginiI.T. Chapter 6: A Docking Station May Have PCI Slots For Expansion Cards and SpeakersAnita RahmawatiÎncă nu există evaluări
- F1 198 Revision QuestionsDocument6 paginiF1 198 Revision QuestionsCharles GhatiÎncă nu există evaluări
- How to Build a Computer: The Best Beginner's Guide to Building Your Own PC from Scratch!De la EverandHow to Build a Computer: The Best Beginner's Guide to Building Your Own PC from Scratch!Încă nu există evaluări
- Computer Basics and NetworksDocument40 paginiComputer Basics and Networksapi-249547905Încă nu există evaluări
- Perform Calculations Using Electronics and Implemented Separate Computation and Memory For The First Time?Document10 paginiPerform Calculations Using Electronics and Implemented Separate Computation and Memory For The First Time?Sayandip MondalÎncă nu există evaluări
- Boodocs of Lovek2Document11 paginiBoodocs of Lovek2Matthew FleckÎncă nu există evaluări
- Institute of Engineering & Technology: InstructionsDocument12 paginiInstitute of Engineering & Technology: InstructionsAshutosh RainaÎncă nu există evaluări
- Computer Book For PPSC Lecturer Computer ScienceDocument107 paginiComputer Book For PPSC Lecturer Computer ScienceFaique MemonÎncă nu există evaluări
- Tech Test Concentrix - 122443Document30 paginiTech Test Concentrix - 122443Esmeralda CuadraÎncă nu există evaluări
- Important Multiple Choice Questions: Computer SystemDocument14 paginiImportant Multiple Choice Questions: Computer SystemSureshÎncă nu există evaluări
- Maxim Nyansa I.T Solution (Nigeria) : Note On Computer RepairsDocument16 paginiMaxim Nyansa I.T Solution (Nigeria) : Note On Computer RepairsOlúwaṣẹ́gunÎncă nu există evaluări
- Ôn tập Anh chuyên ngànhDocument21 paginiÔn tập Anh chuyên ngànhMy MyÎncă nu există evaluări
- Basic Mcqs of Computer Science (It) For Nts and PPSC Test: Posted by Asif Ramay FB Page: Dte Punjab DSD OnDocument39 paginiBasic Mcqs of Computer Science (It) For Nts and PPSC Test: Posted by Asif Ramay FB Page: Dte Punjab DSD OnTayyab AliÎncă nu există evaluări
- MCQ TestDocument5 paginiMCQ Testknowledge-depotÎncă nu există evaluări
- Icdl/Ecdl Information Technology: Lesson 1Document13 paginiIcdl/Ecdl Information Technology: Lesson 1wao2008Încă nu există evaluări
- ICT - Question Bank (Basic Computer)Document3 paginiICT - Question Bank (Basic Computer)Shafeek Ghreeb84% (19)
- Basic Hardware Introduction of DesktopDocument36 paginiBasic Hardware Introduction of DesktopLeander PaulÎncă nu există evaluări
- To Move The Heat Away From The CPU: Bottom of FormDocument5 paginiTo Move The Heat Away From The CPU: Bottom of Formdj_eqc7227Încă nu există evaluări
- Assignment 1: Assignment 1: Chapter 1, 2 &4 Q1) Choose The Correct AnswerDocument5 paginiAssignment 1: Assignment 1: Chapter 1, 2 &4 Q1) Choose The Correct AnswerSerena AlQudah•Încă nu există evaluări
- Version 6.0Document14 paginiVersion 6.0socialboy002Încă nu există evaluări
- What Does A Yellow Exclamation Point Next To A Device in The Device Manager IndicateDocument16 paginiWhat Does A Yellow Exclamation Point Next To A Device in The Device Manager Indicatek3lvyn100% (1)
- Satish's CCC Question BankDocument263 paginiSatish's CCC Question Bankmasim_shaikhÎncă nu există evaluări
- ITE v6 Final Exam 2016Document18 paginiITE v6 Final Exam 2016anon_788551900Încă nu există evaluări
- Computer QuizDocument11 paginiComputer QuiznivlalrakobmasÎncă nu există evaluări
- Examinations For 2005 - 2006 / Semester 1: Module: Computer Fundamentals Module Code: Duration: 2 HoursDocument8 paginiExaminations For 2005 - 2006 / Semester 1: Module: Computer Fundamentals Module Code: Duration: 2 HoursAmani UrassaÎncă nu există evaluări
- Tutorial Sheet 3Document8 paginiTutorial Sheet 3mulambyalovemoreÎncă nu există evaluări
- Stet by Step Guide To Building Own Computer by Cuthbert Chinji JNR Vaal University of TechnologyDocument12 paginiStet by Step Guide To Building Own Computer by Cuthbert Chinji JNR Vaal University of TechnologyCuthbert Chinji JnrÎncă nu există evaluări
- Mid-Term Exam ICTDocument5 paginiMid-Term Exam ICTchandy RendajeÎncă nu există evaluări
- Computer SkillsDocument5 paginiComputer SkillsMustafa RadaidehÎncă nu există evaluări
- Computer QuestionDocument22 paginiComputer QuestionTareqÎncă nu există evaluări
- Multiple Choice QuestionsDocument6 paginiMultiple Choice QuestionsSravanthi Gelley0% (1)
- It Chapter 1Document7 paginiIt Chapter 1Wolverine100% (5)
- Answers Key 6Document2 paginiAnswers Key 6palopejoel1991Încă nu există evaluări
- COC1 CBLM Install and Configure Computer SystemsDocument173 paginiCOC1 CBLM Install and Configure Computer Systemssydneyduma639Încă nu există evaluări
- Tech Question For FresherDocument9 paginiTech Question For FresherSnehaÎncă nu există evaluări
- IT Questions: 1.1.1 Which One of The Following Terms Describes The Physical Components of A Computer System?Document26 paginiIT Questions: 1.1.1 Which One of The Following Terms Describes The Physical Components of A Computer System?Mohammed DahkemÎncă nu există evaluări
- Computer Question Bank: Objective QuestionsDocument8 paginiComputer Question Bank: Objective QuestionsrashmiameÎncă nu există evaluări
- Latest Basic Computer Hardware Interview QuestionsDocument3 paginiLatest Basic Computer Hardware Interview QuestionsSahil ThakurÎncă nu există evaluări
- ComputerScience Xi-IDocument5 paginiComputerScience Xi-IediealiÎncă nu există evaluări
- Objective Computer Fundamental Bca FirstDocument11 paginiObjective Computer Fundamental Bca FirstSanjeev Kumar YadavÎncă nu există evaluări
- ICT-Unit 1-Test 1Document5 paginiICT-Unit 1-Test 1Shahriar Hossain EmonÎncă nu există evaluări
- Computer Acronyms and AbbreviationsDocument5 paginiComputer Acronyms and AbbreviationsJeian Ashley A. MaasinÎncă nu există evaluări
- Question 2Document80 paginiQuestion 2Harun Raaj GuptaÎncă nu există evaluări
- Que 1Document33 paginiQue 1Harun Raaj GuptaÎncă nu există evaluări
- Type of Project: Sname College Assignment Title Platform Date of SubmissionDocument1 paginăType of Project: Sname College Assignment Title Platform Date of SubmissionHarun Raaj GuptaÎncă nu există evaluări
- Module - 1: S.No Name Option 1 Option 2 Option 3 Option 4 AnswerDocument3 paginiModule - 1: S.No Name Option 1 Option 2 Option 3 Option 4 AnswerHarun Raaj GuptaÎncă nu există evaluări
- ITT QuestionsDocument27 paginiITT QuestionsHarun Raaj GuptaÎncă nu există evaluări
- Itt QuesDocument72 paginiItt QuesHarun Raaj GuptaÎncă nu există evaluări
- CAATs For Auditing in Real WorldDocument8 paginiCAATs For Auditing in Real WorldHarun Raaj GuptaÎncă nu există evaluări
- Icai 4Document55 paginiIcai 4Harun Raaj GuptaÎncă nu există evaluări
- Practical Case Studies of CaatsDocument7 paginiPractical Case Studies of CaatsHarun Raaj GuptaÎncă nu există evaluări
- Percy JacksonDocument13 paginiPercy JacksonDawn Marco0% (2)
- Singular & Plural Nouns: Regular PluralsDocument4 paginiSingular & Plural Nouns: Regular PluralsМарина ВетерÎncă nu există evaluări
- Fruitful Outreaches Intercessory Prayer GuidelinesDocument5 paginiFruitful Outreaches Intercessory Prayer GuidelinesPaul Moiloa100% (1)
- Sample File: A of TheDocument6 paginiSample File: A of TheMegan KennedyÎncă nu există evaluări
- Risk AssessmentDocument38 paginiRisk AssessmentYasar arafat SHÎncă nu există evaluări
- Occupant Response To Vehicular VibrationDocument16 paginiOccupant Response To Vehicular VibrationAishhwarya Priya100% (1)
- WatsuDocument5 paginiWatsuTIME-TREVELER100% (1)
- DLL Template MathDocument3 paginiDLL Template MathVash Mc GregorÎncă nu există evaluări
- Types of CostsDocument9 paginiTypes of CostsPrathna AminÎncă nu există evaluări
- Abstraction and Empathy - ReviewDocument7 paginiAbstraction and Empathy - ReviewXXXXÎncă nu există evaluări
- Does Moore Succeed in Refuting IdealismDocument5 paginiDoes Moore Succeed in Refuting IdealismharryÎncă nu există evaluări
- Activity 2Document2 paginiActivity 2cesar jimenezÎncă nu există evaluări
- Foreign Laguage Teaching - Nzjournal - 15.1wiechertDocument4 paginiForeign Laguage Teaching - Nzjournal - 15.1wiechertNicole MichelÎncă nu există evaluări
- Consumer Trend Canvas (CTC) Template 2022Document1 paginăConsumer Trend Canvas (CTC) Template 2022Patricia DominguezÎncă nu există evaluări
- Improving Hands-On Experimentation Through Model Making and Rapid Prototyping: The Case of The University of Botswana's Industrial Design StudentsDocument6 paginiImproving Hands-On Experimentation Through Model Making and Rapid Prototyping: The Case of The University of Botswana's Industrial Design StudentsnaimshaikhÎncă nu există evaluări
- Sample ProposalDocument2 paginiSample ProposaltoupieÎncă nu există evaluări
- Unsworth - Re-Branding The City - Changing The Images of PlacesDocument45 paginiUnsworth - Re-Branding The City - Changing The Images of PlacesNatalia Ney100% (2)
- FA2Document6 paginiFA2yuktiÎncă nu există evaluări
- Introduction To Computational Fluid DynamicsDocument3 paginiIntroduction To Computational Fluid DynamicsJonyzhitop TenorioÎncă nu există evaluări
- Calculation For Service Platform & Pump Shelter StructureDocument36 paginiCalculation For Service Platform & Pump Shelter Structuretrian33100% (1)
- Read Chapter 4 Minicase: Fondren Publishing, Inc. From The Sales Force Management Textbook by Mark W. Johnston & Greg W. MarshallDocument1 paginăRead Chapter 4 Minicase: Fondren Publishing, Inc. From The Sales Force Management Textbook by Mark W. Johnston & Greg W. MarshallKJRÎncă nu există evaluări
- Appraising The Secretaries of Sweet Water UniversityDocument4 paginiAppraising The Secretaries of Sweet Water UniversityZain4uÎncă nu există evaluări
- Extraction of Non-Timber Forest Products in The PDFDocument18 paginiExtraction of Non-Timber Forest Products in The PDFRohit Kumar YadavÎncă nu există evaluări
- 2018 UPlink NMAT Review Social Science LectureDocument133 pagini2018 UPlink NMAT Review Social Science LectureFranchesca LugoÎncă nu există evaluări
- The Peppers, Cracklings, and Knots of Wool Cookbook The Global Migration of African CuisineDocument486 paginiThe Peppers, Cracklings, and Knots of Wool Cookbook The Global Migration of African Cuisinemikefcebu100% (1)
- Thursday 08 October 2020: MathematicsDocument32 paginiThursday 08 October 2020: MathematicsAmjad AshaÎncă nu există evaluări
- MATH 7S eIIaDocument8 paginiMATH 7S eIIaELLA MAE DUBLASÎncă nu există evaluări
- Criteria 5 Points 4 Points 3 Points 2 Points 1 Point Total PointsDocument2 paginiCriteria 5 Points 4 Points 3 Points 2 Points 1 Point Total PointsReyno D. Paca-anasÎncă nu există evaluări
- Disciplines, Intersections and The Future of Communication Research. Journal of Communication 58 603-614iplineDocument12 paginiDisciplines, Intersections and The Future of Communication Research. Journal of Communication 58 603-614iplineErez CohenÎncă nu există evaluări
- Material Concerning Ukrainian-Jewish Relations (1917-1921)Document106 paginiMaterial Concerning Ukrainian-Jewish Relations (1917-1921)lastivka978Încă nu există evaluări