Documente Academic
Documente Profesional
Documente Cultură
Srs 2
Încărcat de
Naveen KumarDrepturi de autor
Formate disponibile
Partajați acest document
Partajați sau inserați document
Vi se pare util acest document?
Este necorespunzător acest conținut?
Raportați acest documentDrepturi de autor:
Formate disponibile
Srs 2
Încărcat de
Naveen KumarDrepturi de autor:
Formate disponibile
Software Requirements Specification for Continuous Authentication in smart Phones using Behavioural Biometrics.
Page |1
1 Introduction
1.1 Purpose
This document describes the requirements specification (SRS) for the product that enables continuous authentication in smart phones using behavioural biometrics and provides an overall description of it. The purpose of the document is to describe the necessity and functionality of the software product. The SRS will include the details of the project's requirements, interface, design issues, and components.
1.2 Scope
The scope of the product is that it provides a means for a secure authentication technique by eliminating entry point based authentication and enabling a continuous authentication technique. This product makes use of behavioural biometrics, thus making it less complex for authentication.
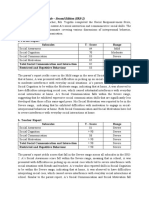
1.3 Definitions, Acronyms and Abbreviations Term
PIN EER FRR FAR SMS API SVM kNN GPS
Definition
Personal Identification Number Equal Error Rate False Rejection Rate False Acceptance Rate Short message Service
Application Programming Interface
Support Vector Machine K Nearest Neighbour Global Positioning System
Software Requirements Specification for Continuous Authentication in smart Phones using Behavioural Biometrics. Page |2
1.4 References
1) Jain, A. Ross, and S. Pankanti, Biometrics: A tool for information security, IEEE Trans. Inf. Forensics Security, vol. 1, no. 2, pp.125143, Jun. 2006. 2) Derawi, C. Nickel, P. Bours, and C. Busch, Unobtrusive userAuthentication on mobile phones using biometric gait recognition, in Proc. 6th Int. Conf. Intelligent Information Hiding and Multimedia Signal Processing, Oct. 2010, pp. 306311. 3) L. Lee, T. Berger, and E. Aviczer, Reliable on-line human signature verification systems, IEEE Trans. Pattern Anal.Mach. Intell., vol. 18,no. 6, pp. 643647, Jun. 1996..
2 Overall Description
2.1 Product Perspective
Text password or patterns has been adopted as the primary form of user authentication for smart phones. In order to log into the device successfully, users must enter their selected passwords correctly. Generally, password-based user authentication can resist brute force and dictionary attacks if users select strong passwords to provide sufficient entropy. However, password-based user authentication has a major problem that humans are not experts in memorizing text strings nor do have the patience to re-enter the passwords repetitively for smaller tasks. Thus, most users would choose easy-to-remember passwords or no passwords at all.
2.2 Product Functionality
A continuous authentication technique is used which makes use of behavioural biometrics to authenticate the user continuously whether the user is an authorized or unauthorized user. The product consists of three major functions Enrolment phase: Initially, the system must be trained in an enrollment phase like sliding horizontally over the screen. Usually, one does this to browse through images or to navigate to the next page of icons in the main screen and sliding
Software Requirements Specification for Continuous Authentication in smart Phones using Behavioural Biometrics. Page |3
vertically over the screen to move screen content up or down. This is typically done for reading e-mail, documents or web-pages, or for browsing menus. Authentication Phase: Once the classifiers are trained, the device begins the authentication phase. During this phase, the system continuously tracks all strokes and the classifier estimates if they were made by the legitimate user. Security Phase: During this phase, since the user is unauthorized the mobile device has been locked and the GPS fetches the location of the smart phone and sends the tracked information to the registered email/SMS.
2.3 Users and Characteristics
Every individual smart phone user with basic knowledge of touch screen usage.
2.4 Operating Environment
2.4.1 SOFTWARE REQUIREMENTS:
Android
2.4.2 HARDWARE REQUIREMENTS:
Android Phone with : Touch screen Accelerometer GPS
2.5 Design and Implementation Constraints
Network coverage should be available for the sending and receiving SMS. Minimum Android version 2.3 required.
Software Requirements Specification for Continuous Authentication in smart Phones using Behavioural Biometrics. Page |4
2.6 Assumptions and Dependencies
The Android operating system has to provide access to the secure behavioural features of the user.
3 Specific Requirements
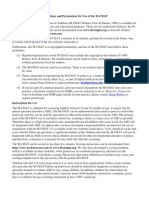
3.1 External Interface Requirements 3.1.1 User Interfaces 3.1.2 Hardware Interfaces 3.1.3 Software Interfaces 3.1.4 Communications Interfaces 3.2 Functional Requirements
Enrolment Phase: The system must be trained in an enrollment phase. We define two particular user actions and call them trigger actions. These actions should be frequent for any usage and primitive, i.e., they should be part of all more complex navigational gestures. Whenever the user performs a trigger action, the system logs the fingertip data. Authentication Phase: Once the device is trained, the device begins the authentication phase. During this phase, the system continuously tracks all strokes and the classifier estimates if they were made by the legitimate user. Security Phase: If the phone detects an unauthorized user, our proposed mechanism could just support the standard authentication mechanisms and serve as a theft detection mechanism that responds to theft by activating GPS, sending SMS, or locking the device.
Software Requirements Specification for Continuous Authentication in smart Phones using Behavioural Biometrics. Page |5
3.3 Behaviour Requirements 3.3.1 Use Case View
4 Other Non-functional Requirements
4.1 Performance Requirements 4.2 Safety and Security requirements:
Users should safeguard mobile phone from antivirus. Our authentication application should not be closed or disabled by the android system or third party application or manually.
4.2 Software Quality Attributes
Functionality: The required function is that user should be able to use the device securely without the need for password protection mechanism. Reliability: As user makes use of personal mobile, it is highly reliable that the mobile is secure even though the primary password is hacked. Usability: No technical knowledge is required for use of application and product highly supports ease of use.
Appendix A Data Dictionary
S-ar putea să vă placă și
- ASD Screening and Diagnostic Tools and TechniquesDocument4 paginiASD Screening and Diagnostic Tools and Techniquestracycw100% (4)
- Social Responsiveness Scale SRSDocument1 paginăSocial Responsiveness Scale SRSstandard2138% (8)
- Autism Diagnostic Interview RevisedDocument12 paginiAutism Diagnostic Interview RevisedRon Ladlow0% (1)
- ABAS-3: Adaptive Behavior Assessment System Third EditionDocument14 paginiABAS-3: Adaptive Behavior Assessment System Third EditionMonica Pires Lake87% (31)
- Behaviour and Personality Questionnaire For ChildrenDocument3 paginiBehaviour and Personality Questionnaire For ChildrenSimiÎncă nu există evaluări
- Table 2 ASD Specific ScreeningDocument7 paginiTable 2 ASD Specific ScreeningJovanka SolmosanÎncă nu există evaluări
- VOLUNTARY ADOS Checklist Version 8Document5 paginiVOLUNTARY ADOS Checklist Version 8Kaah Kah0% (1)
- Asd-parent-Interview Formatted 2012 0325Document7 paginiAsd-parent-Interview Formatted 2012 0325Vivek SagarÎncă nu există evaluări
- C.A.R.S - Childhood Autism Rating ScaleDocument9 paginiC.A.R.S - Childhood Autism Rating Scaleabhishekaslp1708Încă nu există evaluări
- CARS - 2 هاد النسخة الجديدة PDFDocument9 paginiCARS - 2 هاد النسخة الجديدة PDFKhadidja Boutouil100% (1)
- Interpretive ReportDocument7 paginiInterpretive ReportKelly Montilla50% (2)
- AQ Child Scoring KeyDocument3 paginiAQ Child Scoring Keydanielaica21100% (1)
- Appendix - E.17 Study Start Social Responsiveness Scale-Preschool PDFDocument4 paginiAppendix - E.17 Study Start Social Responsiveness Scale-Preschool PDFMa Cyril Dawn Muncada50% (2)
- ABAS-3: Adaptive Behavior Assessment System, Third EditionDocument1 paginăABAS-3: Adaptive Behavior Assessment System, Third Editionmlopes_880761100% (1)
- GarsDocument2 paginiGarsAnonymous uWlv9rllaÎncă nu există evaluări
- Social Communication Questionnaire (SCQ) - Lifetime PC Answer SheetDocument2 paginiSocial Communication Questionnaire (SCQ) - Lifetime PC Answer SheetRi Ri75% (4)
- ADOS 2 - Revised AlgorithmDocument2 paginiADOS 2 - Revised AlgorithmGoropad50% (2)
- Vineland Adaptive Behavior ScalesDocument2 paginiVineland Adaptive Behavior ScalesAlice BulkaÎncă nu există evaluări
- S3 CARS 2 SampleWriteUp 1Document1 paginăS3 CARS 2 SampleWriteUp 1Janet FernandezÎncă nu există evaluări
- ADOS - Toddler ModuleDocument28 paginiADOS - Toddler ModuleGoropad100% (1)
- ABAS Parent521Document4 paginiABAS Parent521Gratiela PgÎncă nu există evaluări
- BRIEF2 Parent Form Interpretive Report SampleDocument27 paginiBRIEF2 Parent Form Interpretive Report SampleMageeÎncă nu există evaluări
- SRS 2 TemplateDocument2 paginiSRS 2 TemplateMelanie Greenway33% (3)
- ABAS3 Score Report ExamplesDocument16 paginiABAS3 Score Report ExamplesAllana LimaÎncă nu există evaluări
- Adir SampleDocument4 paginiAdir SampleTerapie Aba50% (2)
- Vineland 3Document2 paginiVineland 3Teguh Lesmana71% (7)
- SRS AdultsDocument5 paginiSRS AdultsPeggy Kein100% (9)
- Repetitive Beha Repetitive Behavior Sca Vior Scal Le - Revised E - Revised Parent ParentDocument3 paginiRepetitive Beha Repetitive Behavior Sca Vior Scal Le - Revised E - Revised Parent ParentAinna AldayÎncă nu există evaluări
- SRS Scoring & InterpretationsDocument16 paginiSRS Scoring & InterpretationsPeggy Kein100% (6)
- SRS Adult Other Profile SheetDocument5 paginiSRS Adult Other Profile SheetPeggy Kein80% (5)
- ABASII Sample Report F Hr2Document60 paginiABASII Sample Report F Hr2kdmspoon100% (1)
- Cat Q PDFDocument15 paginiCat Q PDFKrol Amafo100% (2)
- Developmental Profile 3: Gerald Alpern, PHDDocument15 paginiDevelopmental Profile 3: Gerald Alpern, PHDtruly fine Art100% (1)
- Social Responsiveness Scale Sample ReportDocument2 paginiSocial Responsiveness Scale Sample ReportHong Chun Yeoh100% (1)
- FINAL Vineland June-2012Document6 paginiFINAL Vineland June-2012Uswatul KhairaÎncă nu există evaluări
- The Child Autism Rating ScaleDocument22 paginiThe Child Autism Rating ScaleGoropad100% (1)
- Gilliam Autism Rating Scale PaperDocument8 paginiGilliam Autism Rating Scale Paperapi-3155179620% (1)
- I. Stereotyped Behavior Subscale: Repetitive Behavior Scale - Revised (RBS-R) InstructionsDocument6 paginiI. Stereotyped Behavior Subscale: Repetitive Behavior Scale - Revised (RBS-R) InstructionsPatras Vladut100% (1)
- Abas 3Document2 paginiAbas 3Peeve Kaye Balbuena11% (9)
- Quantar RSS Manual PDFDocument362 paginiQuantar RSS Manual PDFFrancisco NarvaezÎncă nu există evaluări
- Vineland-Ii Review - VelenoDocument14 paginiVineland-Ii Review - Velenoapi-163017967100% (1)
- The Gilliam Autism Rating Scale GARS - 2 A Pilot SDocument2 paginiThe Gilliam Autism Rating Scale GARS - 2 A Pilot SAnish VeettiyankalÎncă nu există evaluări
- CARS: Childhood Autism Rating Scale (Sample) : Relating To PeopleDocument4 paginiCARS: Childhood Autism Rating Scale (Sample) : Relating To PeopleTareas UCRISHÎncă nu există evaluări
- The Social Responsiveness Scale SRS-2 in School-AgDocument12 paginiThe Social Responsiveness Scale SRS-2 in School-AgGemaAspergerAsturias100% (1)
- Essentials of School Neuropsychological AssessmentDe la EverandEssentials of School Neuropsychological AssessmentÎncă nu există evaluări
- Claim Digger Baseline Schedule VDocument28 paginiClaim Digger Baseline Schedule VDilip KumarÎncă nu există evaluări
- Child Behavior ChecklistDocument2 paginiChild Behavior ChecklistPricope MadalinaÎncă nu există evaluări
- ESDM Acquisition and Bar Graph 03 SampleFilledDocument3 paginiESDM Acquisition and Bar Graph 03 SampleFilledGökçe Gökçümen KocaÎncă nu există evaluări
- Abas 3 Chapter 5Document62 paginiAbas 3 Chapter 5GF David SalasÎncă nu există evaluări
- M ChatDocument2 paginiM Chatballad3100% (2)
- 2.TAFJ Tools Day1Sn2Document7 pagini2.TAFJ Tools Day1Sn2Krishna100% (1)
- Childhood Autism Rating Scale™ - Second Edition (CARS-2) : August 2015Document5 paginiChildhood Autism Rating Scale™ - Second Edition (CARS-2) : August 2015Alejandro Espinoza50% (2)
- PS 571 Asperger Syndrome Diagnostic Scale PowerPointDocument38 paginiPS 571 Asperger Syndrome Diagnostic Scale PowerPointAna Leonor BorgesÎncă nu există evaluări
- Assessment Review - Cars2Document11 paginiAssessment Review - Cars2api-3151104170% (1)
- Lista de AvaliaçõesDocument4 paginiLista de AvaliaçõesVitor AugustoÎncă nu există evaluări
- Childhood Autism Rating ScaleDocument2 paginiChildhood Autism Rating ScaleAsmaa ElarabyÎncă nu există evaluări
- Autism Spectrum Disorder Final HandoutDocument2 paginiAutism Spectrum Disorder Final Handoutapi-264629576Încă nu există evaluări
- Abas II Jan 2012Document5 paginiAbas II Jan 2012Luísa TeixeiraÎncă nu există evaluări
- Sample: Multidimensional Anxiety Scale For Children 2nd Edition-Self-ReportDocument11 paginiSample: Multidimensional Anxiety Scale For Children 2nd Edition-Self-ReportirinatomaÎncă nu există evaluări
- Aba Formulário de Avaliação Do Programa - Avaliação RápidaDocument2 paginiAba Formulário de Avaliação Do Programa - Avaliação RápidaLeana Bernardes100% (2)
- Diafix Troubleshooting NovoDocument242 paginiDiafix Troubleshooting NovoInfo e TecÎncă nu există evaluări
- Software Defined RadioDocument6 paginiSoftware Defined RadioUjjwal DhusiaÎncă nu există evaluări
- Example M3 Report 2019Document7 paginiExample M3 Report 2019EverestÎncă nu există evaluări
- ADR-3000 System Introduction En122 PDFDocument28 paginiADR-3000 System Introduction En122 PDFJoseph BoshehÎncă nu există evaluări
- Uxpin The 5 Building Blocks of Interaction DesignDocument31 paginiUxpin The 5 Building Blocks of Interaction DesignD.j. Pop UpÎncă nu există evaluări
- IAB - Proj Dimas: Integrated Architecture BuilderDocument114 paginiIAB - Proj Dimas: Integrated Architecture BuilderDimas CaceresÎncă nu există evaluări
- ADOS 2 Module 4 Revised Algorithm Hus and Lord 2014 April 2022Document2 paginiADOS 2 Module 4 Revised Algorithm Hus and Lord 2014 April 2022DanielÎncă nu există evaluări
- Program 1: Mvi A, 52h Sta 4000h HLT Program 2Document9 paginiProgram 1: Mvi A, 52h Sta 4000h HLT Program 2mdchandmca100% (2)
- Cenopdf User'S Manual: Lystech ComputingDocument112 paginiCenopdf User'S Manual: Lystech ComputingTheetaÎncă nu există evaluări
- ICT Lecture 08 Computer SoftwareDocument32 paginiICT Lecture 08 Computer SoftwareNasir Faraz KalmatiÎncă nu există evaluări
- Materials Requirements PlanningDocument34 paginiMaterials Requirements PlanningRahul KhannaÎncă nu există evaluări
- Yealink SIP-T2 Series T19 (P) E2 T4 Series IP Phones Administrator Guide V81 20Document1.042 paginiYealink SIP-T2 Series T19 (P) E2 T4 Series IP Phones Administrator Guide V81 20groovyonlineÎncă nu există evaluări
- DC v2016.12-SP3 Lab Setup Checks: 1. UNIX% CP - R Lab5 Test - Lab5 CD Test - Lab5 DC - Shell - TopoDocument3 paginiDC v2016.12-SP3 Lab Setup Checks: 1. UNIX% CP - R Lab5 Test - Lab5 CD Test - Lab5 DC - Shell - TopomanojkumarÎncă nu există evaluări
- CPU Scheduling: CPU - I/O Burst CycleDocument4 paginiCPU Scheduling: CPU - I/O Burst Cyclearj0701Încă nu există evaluări
- Evermotion Archmodels Vol. 151Document27 paginiEvermotion Archmodels Vol. 151AKASH SINGHÎncă nu există evaluări
- CPQ-FOM IntegrationDocument16 paginiCPQ-FOM IntegrationAnkush FayeÎncă nu există evaluări
- Mbed Pin IO Tutorial PDFDocument5 paginiMbed Pin IO Tutorial PDFIanÎncă nu există evaluări
- DEVISER S7200 - ManualDocument326 paginiDEVISER S7200 - ManualNicolas Maldonado BenitezÎncă nu există evaluări
- Imanager NetEco 1000S User Manual (V100R001C01 - Draft B) (PDF) - ENDocument86 paginiImanager NetEco 1000S User Manual (V100R001C01 - Draft B) (PDF) - ENJean Constantin Eko MedjoÎncă nu există evaluări
- Introduction To Embedded Systems: Melaku MDocument150 paginiIntroduction To Embedded Systems: Melaku MTalemaÎncă nu există evaluări
- Unit 1 Cs 191cse046jDocument21 paginiUnit 1 Cs 191cse046jTRB hubÎncă nu există evaluări
- Action Multimedia Feb Price ListDocument21 paginiAction Multimedia Feb Price ListRafeeq AhmadÎncă nu există evaluări
- Oracle JDeveloper 10g Build Applications With ADF Instructor Guide - Volume 2 PDFDocument256 paginiOracle JDeveloper 10g Build Applications With ADF Instructor Guide - Volume 2 PDFjurgen1871Încă nu există evaluări
- PowerExchange - SAP Functionality OverviewDocument13 paginiPowerExchange - SAP Functionality OverviewMahesh SharmaÎncă nu există evaluări
- Big Data Mining, and AnalyticsDocument22 paginiBig Data Mining, and AnalyticsAriadna Setentaytres100% (1)
- Nortel CMDDocument1.054 paginiNortel CMDbarone_28Încă nu există evaluări
- Spring Security WhitepaperDocument7 paginiSpring Security WhitepaperMamat LepakÎncă nu există evaluări
- Sap AuditDocument12 paginiSap AuditVino BrilloÎncă nu există evaluări
- AIS Chapter 1-3Document24 paginiAIS Chapter 1-3Crissa SamsamanÎncă nu există evaluări