Documente Academic
Documente Profesional
Documente Cultură
Cyber Risk and Cyber Insurance
Încărcat de
sresearcher7Drepturi de autor
Formate disponibile
Partajați acest document
Partajați sau inserați document
Vi se pare util acest document?
Este necorespunzător acest conținut?
Raportați acest documentDrepturi de autor:
Formate disponibile
Cyber Risk and Cyber Insurance
Încărcat de
sresearcher7Drepturi de autor:
Formate disponibile
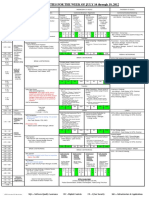
CYBER RISK & CYBER INSURANCE An MAIA Member Information White Paper MAIA F.A.C.T.S.
COMMITTEE 10-14-11
1 MAIA F.A.C.T.S. Committee Information White Paper 10-14-11
Part 1 Cyber Risk
o Cyber Risk & Cyber Exposures o Cyber Laws & Law Suits o Cyber Risk Terms o Why Cyber Risk Is Not Likely Insured Elsewhere o Cyber Claims Examples
Part 2 Cyber Insurance
o Cyber Insurance Policies o 1st Party Insurance: Business Interruption, Crisis Management, Expense Coverage for Notification, Extortion, Threat & Reward
2 MAIA F.A.C.T.S. Committee Information White Paper 10-14-11
o 3rd Party Insurance: Privacy (Data Breach), Security, Intellectual Property, Media Content o Loss Control (Cyber Security) o 16. Questions You Need to Ask
Part 1 - Cyber Risk
What is Cyber Risk ?
"Financial Damages resulting from Any E-Business (electronic transmissions) o Internet o Internal Business Network o Any Electronic Data! & o We cant forget the paper exposure! (server or "cloud" storage, email attachments, faxes, mail, etc.)
1st Party Cyber Risk:
Your financial loss because of injury to your electronic data or systems resulting from acts of others Examples o Costs of fixing your problem
3 MAIA F.A.C.T.S. Committee Information White Paper 10-14-11
o Expenses to protect clients (including notification costs) o Other expenses to mitigate loss (including publicity costs) o Theft of data & intangible property o Loss of your future income o Cyber extortion
3rd Party Cyber Risk:
Your liability for financial losses or costs sustained by others [Financial damages resulting from client law suits and law suits from others for their personal/content injury, intellectual property claims, professional services, and injury from a security or privacy breach]
Cyber Risk Claim Examples
Privacy An online retailer attempted to sell its customers' personal information to pay creditors as part of the retailer's bankruptcy! But the retailer's privacy policy had stated that personally identifiable information (PII) would not be sold. Several parties threatened to sue. Privacy & Security A hacker infiltrated an online shopping website and stole 300,000 customer credit card numbers. The website faced claims from
4 MAIA F.A.C.T.S. Committee Information White Paper 10-14-11
the customers for unauthorized charges made on their credit cards. Security Businesses that unknowingly spread a worm, virus, or other corrupting files via email to 3rd parties could face liability from those 3rd parties for revenues lost as a result of the virus overloading the 3rd parties' computer network (denial of service).
Media/Content A university pathologist
posted a message on a bulletin board accusing another doctor with receiving kickbacks from a company trying to obtain a contract to provide pathology services to the university. The university doctor sued, and a jury awarded him $675,000.
Intellectual Property A business that used
a competitor's trademarked name on its website was sued by the competitor for trademark infringement and unfair competition.
Federal Cyber Laws
The protection and disclosure of confidential consumer information, both personally identifiable information (PII) and protected health information (PHI), is currently governed by a patchwork of federal and state laws that target different exposures. Some of these federal statutes include:
Family Educational Rights Privacy Act (FERPA) HIPAA Gramm Leach Bliley Act
5
MAIA F.A.C.T.S. Committee Information White Paper 10-14-11
Fair Credit Reporting Act Sarbanes-Oxley (SOX) Federal Privacy Act.
Two of the newest additions HITECH Act
It beefed-up HIPAA by requiring notification of potential private health information (PHI) breaches. It went into effect 2/17/09, but as of 9/23/09 HITECH now includes all "business associates Business associates are persons or entities who perform services on behalf of a HIPAA-covered entity and in so doing access the PHI of the covered entity. Businesses have 60 days to report a breach once discovered. Breaches over 500 persons requires notice to the media! HITECH will be enforced by the Department of Health and Human Services (DHHS). DHHS will do annual audits and levy fines for non-compliance.
"Red Flags" Rule (FTC)
Was supposed to go into effect 11/1/2009, but was postponed for the 5th time to June 2010. is now part of 2009 Omnibus Healthcare Law and now in effect! requires any business that has any creditor relationships to have a written Identity Theft Prevention Program. broadly defines "creditor" to include essentially any business that defers payments for services, including healthcare providers.
6 MAIA F.A.C.T.S. Committee Information White Paper 10-14-11
requires doctors offices, hospitals and other providers (including business associates) to establish a written procedure to identify warning signs ("red flags) of identity theft .
State Cyber Laws
Consumer Notification o Is now required in 46 states, PR & DC o Is based on the location of the consumer, not the business location o Example: In New York - NY Business Law Section 899-aa requires notice of breach of security of all computerized personal information held by both public and private entities (Consumers Union 8/21/2007)
Credit monitoring & restoration is not typically required by state law, but may soon be imposed by judicial or regulatory decision, based on precedents being set by current settlements
TJX class action for damages to ID theft victims as well as credit monitoring services: $40,800,000 settlement with VISA, $24,000,000 settlement with MasterCard
(Source: Media/Professional Insurance)
Cyber Negligence
Plaintiffs are now challenging the standard of care on their Personal Identifiable Information (Pll) and Personal Health Information (PHI). Example
7 MAIA F.A.C.T.S. Committee Information White Paper 10-14-11
o One publicly-disclosed case involved San Diego-based Ligand Pharmaceuticals Inc... o A lab assistant found a box with 38 former employees' personnel records o The assistant then used the information to acquire 75 credit cards, $100,000 in merchandise, opened 20 cellular telephone accounts and rented three apartments! o The assistant was subsequently convicted and imprisoned, but then 14 of the former employees filed suit, charging Ligand with negligence. o A confidential "significant six-figure" settlement was approved by the court.
Cyber Risk Terms
Personally Identifiable Information (PII) o Any Credit Card Information o Any Personal Financial Information o All Social Security Numbers o All Drivers License Numbers o Any Banking Information o Any Employment Information o Any Insurance Information
Personal Health Information (PHI)
8 MAIA F.A.C.T.S. Committee Information White Paper 10-14-11
Any Business Information of Others (including their Trade Secrets)
Cyber Risk Includes
o Network Data o Non-Network Data o Corporate Servers o Third Party Data Storage (Cloud Computing) o Spam o Virus o Hackers o Storage Media o PCs
Servers Electronic Tape Backup Laptops USBs (flash drives) Handheld Devices (iPads) CDs/DVDs/floppy disks Paper!
9 MAIA F.A.C.T.S. Committee Information White Paper 10-14-11
Cyber Risk Why Its Likely Not Covered Elsewhere
1. General Liability covers Bodily Injury and Property Damage, not stolen identities. Personal Injury coverage may be limited to "invasion of privacy" arising from the publication of material. 2. Property Insurance does not consider data as tangible property. 3. Media Liability policies only cover libel, slander and copyright. 4. E&O policies cover services for others for a fee. Some may cover invasion of privacy, but will only respond to actual damages But, many businesses hold PII but are not a service industry thats eligible to buy E&O (example: gas stations!) 5. Intellectual Property (Patent/Copyright). These policies are designed to protect the insured from claims brought by competitors and other third parties. This coverage responds to theft of ideas, products or content, not identities or money. 6. Crime Insurance covers theft of money, securities and property. In the absence of a cyber insurance policy, there wouldn't be coverage for notification and credit monitoring .
Part 2 - Cyber Insurance
o An Evolving Coverage
10 MAIA F.A.C.T.S. Committee Information White Paper 10-14-11
o Insurers vary widely on:
Coverage Policy wording Policy structure Terminology
o No standard policies yet Cyber
Insurance
Who sells it? 1. 2. 3. 4. 5. 6. 7. 8. 9. Chartis (AIG) (netAdvantage) CNA (netProtect) Beazley Chubb Evanston Hiscox (affirmative Contractual Liability included) Markel American Philadelphia + 9 other insurers to date
Cyber Insurance Insuring Agreements
1st Party (The Insured):
11 MAIA F.A.C.T.S. Committee Information White Paper 10-14-11
1. Business Interruption 2. Crisis Management Expense 3. Extortion/Threat Expenses 4. Privacy (Notification Expense of Data Breach) [if 3rd Party (Other-Than-The-Insured)] 5. Privacy Liability (Data Breach) 6. Security 7. Administrative & Regulatory Actions 8. Intellectual Property 9. Media/Content 3rd Party - Privacy Coverage Regulatory Defense & Expenses many new regulations exist related to the protection of confidential data. Insurance will provide defense cost coverage for regulatory proceeding and even penalties where insurable. Credit Monitoring policies may cover up to 1 year of credit monitoring services for those exposed. In some cases 2 years of monitoring may be available. Credit Repair Services policies may cover 1 year of services to repair credit of an actual identity theft. Privacy: Data Breach Example Hackers broke into a Virginia web site used by pharmacists to track prescription drug abuse The hackers made a copy of the records, deleted the original, then encrypted their copy A ransom demand was then made for $10,000,000 in exchange for the password to the encrypted records 8 million records were stolen and encrypted !
12 MAIA F.A.C.T.S. Committee Information White Paper 10-14-11
Privacy: Claims Examples
An online business processer inadvertently provided access to a non-authorized user. Confidential customer contact information was exposed to unauthorized users. A regulatory investigation for the data privacy incident lead to a fine. Loss: Private suit for loss of/damage to data settled for $875,000. Defense expenses incurred were in excess of $275,000.
A bank employee had a laptop with sensitive client data missing. Regulatory investigation is ongoing. Multiple lawsuits are pending by individuals whose data has been compromised. Loss: Total defense costs now exceed $700,000.
A pharmacy sold to an individual a computer that still contained prescription records including the names, addresses, social security numbers and medication lists of pharmacy customers. State law required certified notification to all of the affected parties. Two lawsuits were filed: 1) Employee plaintiff alleged damages due to job loss as a result of the disclosure; 2) Client plaintiff alleged her identity was stolen and sued to recover the costs of correction and emotional distress. A HIPAA investigation was triggered. Loss in excess of $410,000
Security Coverage
Covers:
Third party economic loss resulting from a network and information security failure (security breach) Unauthorized access & unauthorized use
13 MAIA F.A.C.T.S. Committee Information White Paper 10-14-11
Denial of service (eg: WikiLeaks jamming)
Security: Statistics for 2008 o At least 43% of businesses have experienced some kind of cyber security incident. o Annual reported losses from cyber security in 2008 were $288,618 per business. incidents
o Financial fraud was the most expensive type of incident with an average reported cost of $463,100. [Source: Computer Security Institute, CSI Computer Crime and Security Survey 2008. ] Security: Losses Breakdown The percentage of incidents for each category has remained consistent from 2007 to 2008. Insider abuse, laptop & virus incidents are still the more common occurrence.
Cyber Loss Control
All businesses need to establish
Corporate Cyber Policies/Plans:
Privacy Policy Information Security Policy Computer Usage Policy Incident Response Plan
Employee Cyber Risk Awareness Training
14
MAIA F.A.C.T.S. Committee Information White Paper 10-14-11
Cyber Software Security Controls
Firewalls, passwords, encryption, antivirus
Physical (Hardware) Security Controls Locks, portable equipment restrictions, theft controls
16 Questions You Need to Ask
1. Do you hold any private data of clients, vendors, employees or others? 2. Are you aware of the notice requirements in each state if you lose control of that data? 3. What steps would you take/who would you call if you lost those private records? 4. Do you have a corporate-wide privacy policy? 5. Do you have a disaster plan specific to data breaches? 6. Are your records stored electronically? Paper? Are the records secure? Do you shred? 7. Do any employees have access to private client records? 8. Do you allow use of USB drives on computers that can access private data? 9. .Are your records ever handled by a 3rd party? 10. Are all of your laptops and wireless connections encrypted? Email encrypted? 11. Are you confident your antivirus and firewall systems are 100% effective?
15 MAIA F.A.C.T.S. Committee Information White Paper 10-14-11
12. Have any of your systems been programmed by nonemployees? 13.How would your clients respond if you lost their private records? 14.If your network was damaged or disabled by a virus or hacker attack, would it affect your income? 15.Do you have a backup system? 16.How long would it take you to recover?
Summary Basically
Every business has an exposure to Cyber Risk! Every business needs Cyber Insurance!
Credits o June Wysocki, AmWins, Grand Rapids, MI o Jim Whetstone, Hiscox US, Chicago, IL o Dark Reading (IWKBTnewsletters@techweb.com) o National Underwriter o Rough Notes o American Agent & Broker o IRMI o Business Insurance
16 MAIA F.A.C.T.S. Committee Information White Paper 10-14-11
S-ar putea să vă placă și
- Defense Acquisition Guidebook (DAG), ForewordDocument2 paginiDefense Acquisition Guidebook (DAG), Forewordsresearcher7Încă nu există evaluări
- Donald BaconDocument5 paginiDonald Baconsresearcher7Încă nu există evaluări
- CFP Cyber v3Document2 paginiCFP Cyber v3sresearcher7Încă nu există evaluări
- Sec Patt IntroDocument19 paginiSec Patt Introkrishnaveni_muruganÎncă nu există evaluări
- Gradschooltalk PDFDocument22 paginiGradschooltalk PDFsresearcher7Încă nu există evaluări
- CricDocument1 paginăCricsresearcher7Încă nu există evaluări
- KYPO Cyber Range Developer: PositionDocument1 paginăKYPO Cyber Range Developer: Positionsresearcher7Încă nu există evaluări
- How To Become A Cyber Warrior - 2012 - 016 - 102 - 67947Document4 paginiHow To Become A Cyber Warrior - 2012 - 016 - 102 - 67947sresearcher7Încă nu există evaluări
- Module 1 Chapter 1 Exercises SummaryDocument2 paginiModule 1 Chapter 1 Exercises Summarysresearcher750% (2)
- DHS HOST Project Open Source Cybersecurity Software CatalogDocument3 paginiDHS HOST Project Open Source Cybersecurity Software Catalogsresearcher7Încă nu există evaluări
- NITSL Activities for the Week of July 16-19, 2012Document1 paginăNITSL Activities for the Week of July 16-19, 2012sresearcher7Încă nu există evaluări
- Analysis of The Implementation of An Interactive Kinetic Cyber Range ComponentDocument1 paginăAnalysis of The Implementation of An Interactive Kinetic Cyber Range Componentsresearcher7Încă nu există evaluări
- CricDocument1 paginăCricsresearcher7Încă nu există evaluări
- Ideai2 Att1 Draft SowDocument7 paginiIdeai2 Att1 Draft SowPoer JavaÎncă nu există evaluări
- CricDocument1 paginăCricsresearcher7Încă nu există evaluări
- CricDocument1 paginăCricsresearcher7Încă nu există evaluări
- CricDocument1 paginăCricsresearcher7Încă nu există evaluări
- 0verview-Crisc Part 1 The Big Picture 2011Document66 pagini0verview-Crisc Part 1 The Big Picture 2011saryus2012100% (3)
- CricDocument1 paginăCricsresearcher7Încă nu există evaluări
- CricDocument1 paginăCricsresearcher7Încă nu există evaluări
- CricDocument1 paginăCricsresearcher7Încă nu există evaluări
- CricDocument1 paginăCricsresearcher7Încă nu există evaluări
- CricDocument1 paginăCricsresearcher7Încă nu există evaluări
- CricDocument1 paginăCricsresearcher7Încă nu există evaluări
- CricDocument1 paginăCricsresearcher7Încă nu există evaluări
- CricDocument1 paginăCricsresearcher7Încă nu există evaluări
- CricDocument1 paginăCricsresearcher7Încă nu există evaluări
- CricDocument1 paginăCricsresearcher7Încă nu există evaluări
- CricDocument1 paginăCricsresearcher7Încă nu există evaluări
- CricDocument1 paginăCricsresearcher7Încă nu există evaluări
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeDe la EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeEvaluare: 4 din 5 stele4/5 (5794)
- The Little Book of Hygge: Danish Secrets to Happy LivingDe la EverandThe Little Book of Hygge: Danish Secrets to Happy LivingEvaluare: 3.5 din 5 stele3.5/5 (399)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryDe la EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryEvaluare: 3.5 din 5 stele3.5/5 (231)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceDe la EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceEvaluare: 4 din 5 stele4/5 (894)
- The Yellow House: A Memoir (2019 National Book Award Winner)De la EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Evaluare: 4 din 5 stele4/5 (98)
- Shoe Dog: A Memoir by the Creator of NikeDe la EverandShoe Dog: A Memoir by the Creator of NikeEvaluare: 4.5 din 5 stele4.5/5 (537)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureDe la EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureEvaluare: 4.5 din 5 stele4.5/5 (474)
- Never Split the Difference: Negotiating As If Your Life Depended On ItDe la EverandNever Split the Difference: Negotiating As If Your Life Depended On ItEvaluare: 4.5 din 5 stele4.5/5 (838)
- Grit: The Power of Passion and PerseveranceDe la EverandGrit: The Power of Passion and PerseveranceEvaluare: 4 din 5 stele4/5 (587)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaDe la EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaEvaluare: 4.5 din 5 stele4.5/5 (265)
- The Emperor of All Maladies: A Biography of CancerDe la EverandThe Emperor of All Maladies: A Biography of CancerEvaluare: 4.5 din 5 stele4.5/5 (271)
- On Fire: The (Burning) Case for a Green New DealDe la EverandOn Fire: The (Burning) Case for a Green New DealEvaluare: 4 din 5 stele4/5 (73)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersDe la EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersEvaluare: 4.5 din 5 stele4.5/5 (344)
- Team of Rivals: The Political Genius of Abraham LincolnDe la EverandTeam of Rivals: The Political Genius of Abraham LincolnEvaluare: 4.5 din 5 stele4.5/5 (234)
- The Unwinding: An Inner History of the New AmericaDe la EverandThe Unwinding: An Inner History of the New AmericaEvaluare: 4 din 5 stele4/5 (45)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyDe la EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyEvaluare: 3.5 din 5 stele3.5/5 (2219)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreDe la EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreEvaluare: 4 din 5 stele4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)De la EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Evaluare: 4.5 din 5 stele4.5/5 (119)
- Her Body and Other Parties: StoriesDe la EverandHer Body and Other Parties: StoriesEvaluare: 4 din 5 stele4/5 (821)
- Summer Internship Project at ICICI BankDocument81 paginiSummer Internship Project at ICICI BankNeha Vora100% (3)
- HW On Cash BDocument6 paginiHW On Cash BAngelo123Încă nu există evaluări
- University of Santo Tomas Alfredo M. Velayo College of AccountancyDocument4 paginiUniversity of Santo Tomas Alfredo M. Velayo College of AccountancyChni Gals0% (1)
- Answer Key Section 1 To 5 Nov2022batchDocument15 paginiAnswer Key Section 1 To 5 Nov2022batchICS Davao2 (Epyong)100% (1)
- RG-AP810-I Wi-Fi 6 Dual-Radio Access Point Datasheet - For Preview - 09270949Document18 paginiRG-AP810-I Wi-Fi 6 Dual-Radio Access Point Datasheet - For Preview - 09270949takeshiyamato11Încă nu există evaluări
- Unit 7: Account Current: Learning OutcomesDocument14 paginiUnit 7: Account Current: Learning OutcomesamirÎncă nu există evaluări
- Vmware Customer Case Study Surrey and Sussex PoliceDocument3 paginiVmware Customer Case Study Surrey and Sussex PoliceNobby NobbsÎncă nu există evaluări
- Job Order Costing: Prepared By: C. Douglas Cloud Professor Emeritus of Accounting Pepperdine UniversityDocument78 paginiJob Order Costing: Prepared By: C. Douglas Cloud Professor Emeritus of Accounting Pepperdine UniversityDiola QuilingÎncă nu există evaluări
- Handout AP 2306 FDocument14 paginiHandout AP 2306 FDyosa MeÎncă nu există evaluări
- Travel Demand Forecasting I. Trip GenerationDocument5 paginiTravel Demand Forecasting I. Trip GenerationJaper WeakÎncă nu există evaluări
- Bsspar1 Rg30 Chapter 12 (E) GprsDocument63 paginiBsspar1 Rg30 Chapter 12 (E) GprsNokiaML LogfilesÎncă nu există evaluări
- Cip 2.0Document1 paginăCip 2.0JitendraBhartiÎncă nu există evaluări
- None 7ae25c51Document10 paginiNone 7ae25c51Nirmala OyÎncă nu există evaluări
- Banking Enquiry: Payment Cards and Interchange Fee HearingsDocument18 paginiBanking Enquiry: Payment Cards and Interchange Fee HearingssanjayjogsÎncă nu există evaluări
- Electronic Commerce SystemsDocument48 paginiElectronic Commerce SystemsYasir HasnainÎncă nu există evaluări
- Big BazaarDocument19 paginiBig BazaarAlok RanjanÎncă nu există evaluări
- Policy No 3001 - 138098143 - 00 - 000Document3 paginiPolicy No 3001 - 138098143 - 00 - 000sanatana yogÎncă nu există evaluări
- L1-History of RadioDocument11 paginiL1-History of RadioTai SankioÎncă nu există evaluări
- Original Copy UniversityDocument1 paginăOriginal Copy UniversityUmesh MuliÎncă nu există evaluări
- Statement of Account: Date Narration Chq./Ref - No. Value DT Withdrawal Amt. Deposit Amt. Closing BalanceDocument2 paginiStatement of Account: Date Narration Chq./Ref - No. Value DT Withdrawal Amt. Deposit Amt. Closing BalanceDeb DasÎncă nu există evaluări
- Handout On The Pawnshop Regulation ActDocument3 paginiHandout On The Pawnshop Regulation Actamazing_pinoyÎncă nu există evaluări
- Reliance JioDocument12 paginiReliance JioShamsheer ShahulÎncă nu există evaluări
- Lichfield Sutton Coldfield Birmingham Long Bridge RedditchDocument4 paginiLichfield Sutton Coldfield Birmingham Long Bridge RedditchLouisMichaelÎncă nu există evaluări
- Retail Multichannel Unit 2Document26 paginiRetail Multichannel Unit 2Nikita ShekhawatÎncă nu există evaluări
- Accountant: Joshua M. ToldingDocument2 paginiAccountant: Joshua M. ToldingEllenare RacionÎncă nu există evaluări
- Boost your business with quality reports and expert consultancyDocument129 paginiBoost your business with quality reports and expert consultancyShabnam NazÎncă nu există evaluări
- FORM 4 Penilaian Kredensial UlangDocument3 paginiFORM 4 Penilaian Kredensial UlangHeru FirmanÎncă nu există evaluări
- ITS323Y09S1E01 Midterm Exam AnswersDocument19 paginiITS323Y09S1E01 Midterm Exam AnswersRachel PacisÎncă nu există evaluări
- HVLTL T510 JqchiweDocument5 paginiHVLTL T510 Jqchiwema.shehlaintÎncă nu există evaluări
- Contact Details Modification Form Federal BankDocument16 paginiContact Details Modification Form Federal BankSidhi KodurÎncă nu există evaluări