Documente Academic
Documente Profesional
Documente Cultură
Ijret - A Combined Approach Using Triple Des and Blowfish
Drepturi de autor
Formate disponibile
Partajați acest document
Partajați sau inserați document
Vi se pare util acest document?
Este necorespunzător acest conținut?
Raportați acest documentDrepturi de autor:
Formate disponibile
Ijret - A Combined Approach Using Triple Des and Blowfish
Drepturi de autor:
Formate disponibile
IJRET: International Journal of Research in Engineering and Technology
eISSN: 2319-1163 | pISSN: 2321-7308
A COMBINED APPROACH USING TRIPLE DES AND BLOWFISH RESEARCH AREA: COMPUTER SCIENCE (CRYPTOGRAPHY)
Shreya Singh singh_shreya@yahoo.com
Abstract
In this paper we study about the triple DES algorithm along with the blowfish algorithm. This is a combined approach and is aimed at improving their individual performances. Then this is briefly compared to the advanced encryption standard;
Keywords:-DES, Blowfish, TDES, AES. --------------------------------------------------------------------***-------------------------------------------------------------------------1. INTRODUCTION
There are two ways of communication possible cryptographically. One is by the use of the public key system. Here two different keys are used for encryption and decryption. The three main forms of public key systems are public key distribution systems, digital signature systems, and public key cryptosystems, which can perform both public key distribution and digital signature services. In a Public-key cryptographic system, two keys are required. One is a secret key and the other one is a public key. The second method is the use of symmetric key cryptography. Here the same key is used for both the encryption and the decryption. These are a class of algorithms which are used for cryptography. In the case of public key cryptosystem two different keys were being used for the process of encryption and decryption. In symmetric key cryptosystem we use the same cryptographic keys for both encryption of the plaintext and decryption of the cipher text. Symmetric encryption is a faster procedure. DES is one algorithm which have been widely used for the encryption of data. It was developed in 1975 by IBM. It is now considered insecure. Another variant of the DES was developed later known as the triple DES which is considered to be more secure in nature. Though nowadays the AES is in use instead of DES. AES is a symmetric block cipher with a block size of 128 bits. Key lengths can be 128 bits, 192 bits, or 256 bits; 8 called AES-128, AES-192, and AES-256, respectively. AES-128 uses 10 rounds, AES-192 uses 12 rounds, and AES-256 uses 14 rounds. Blowfish has a 64-bit block size and a key length of anywhere from 32 bits to 448 bits. It is a 16-round Feistel cipher and uses large keydependent S-boxes. It is similar in structure to CAST-128, which uses fixed S-boxes. Blowfish is not subject to any patents and is therefore freely available for anyone to use. This has contributed to its popularity in cryptographic software. Blowfish is one of the fastest block ciphers in widespread use, except when changing keys. Each new key requires preprocessing equivalent to encrypting about 4 kilobytes of text, which is very slow compared to other block ciphers.
2. DES
In DES the block cipher was used 64 bits at a time. The initial permutation rearranges 64 bits. The encoding was done in 16 rounds.
The 64 bits were divided into left, right halves. The right half goes through function f, mixed with the key. The right half was added to the left half. Then these halves were swapped. The right side was then expanded from 32 to 48 bits and the 48 bits of key were added. In the S-boxes, the set of 6 was reduced to 4. The P-box then permutes 32 bits.
__________________________________________________________________________________________
Volume: 02 Issue: 07 | Jul-2013, Available @ http://www.ijret.org 63
IJRET: International Journal of Research in Engineering and Technology
eISSN: 2319-1163 | pISSN: 2321-7308
Eight bits are used only for checking parity. These are later discarded. Thus the effective key length is 56 bits. Three modes of operations are present. They are: ECB CBC OFB
In the electronic CodeBook mode each 64-bit block is encrypted independently. This is prone to attacks as the attacker can easily build the CodeBook. In the Cipher Block Chaining mode the encryption and decryption as carried as follows: Encryption: Ci = EK(Pi Ci-1) Decryption: Pi = Ci-1 DK(Ci) The OFB mode allows byte-wise encryption.
3. TRIPLE DES
Triple DES is also known as the Triple Data Encryption Algorithm block cipher. Here the DES cipher algorithm is applied thrice. This is done to each data block. Triples DES increases the key size of DES and thus provides improved protection against attacks. The algorithm is described as follows: Triple DES uses a "key bundle" which comprises three DES keys. These are K1, K2 and K3. Each comprise of 56 bits. The encryption algorithm is: ciphertext = EK3(DK2(EK1(plaintext))), DES encrypt with K1, DES decrypt with K2, then DES encrypt with K3. Decryption is the reverse: plaintext = DK1(EK2(DK3(ciphertext)))that is , decrypt with K3, encrypt with K2, then decrypt with K1. Each triple encryption encrypts one block of 64 bits of data. In each case the middle operation is the reverse of the first and last. This improves the strength of the algorithm when using keying option 2, and provides backward compatibility with DES with keying option 3. The three keying options are : Keying option 1: All three keys are independent. Keying option 2: K1 and K2 are independent, and K3 = K1. Keying option 3: All three keys are identical, i.e. K1 = K2 = K3. Keying option 1 has a key length of 168 bits consisting of three 56-bit DES keys. One of the known attack is the meet in the middle attack due to which option 1 can only provide 112 bits security. Keying option 2 reduces the key size to 112 bits. Again this option is prone to certain chosen-plaintext or known-plaintext attacks. It thus provides us with only 80 bits of security.
4. BLOWFISH
Blowfish is a symmetric block cipher that can be used for encryption and protection of data. It takes a variable-length key, from 32 bits to 448 bits. Blowfish was designed in 1993 by Bruce Schneier. It is suitable for applications where the key does not change often. . The block size is 64 bits, and the key
__________________________________________________________________________________________
Volume: 02 Issue: 07 | Jul-2013, Available @ http://www.ijret.org 64
IJRET: International Journal of Research in Engineering and Technology
eISSN: 2319-1163 | pISSN: 2321-7308
can be any length up to 448 bits. Data encryption occurs via a 16-round Feistel network. Each round consists of a key dependent permutation, and a key- and data-dependent substitution. All operations are XORs and additions on 32-bit words. The only additional operations are four indexed array data lookups per round. Blowfish has 16 rounds. There are four 32-bit S-boxes with 256 entries each: S1,0, S2,0, S3,0, S4,0, S1,1,..., S1,255; S2,1,..,, S2,255; S3,1,..., S3,255; S4,1,..,, S4,255.
Divide x into two 32-bit halves: xL, xR. Then, for i = 1 to 16: xL = xL XOR Pi xR = F(xL) XOR xR Swap xL and xR After the sixteenth round, swap xL and xR again to undo the last swap. Then, xR = xR XOR P17 and xL = xL XOR P18. Finally, recombine xL and xR to get the ciphertext.
The subkeys are generated in the following manner: 1. Initialize first the P-array and then the four S-boxes, in order, with a fixed string. This string consists of the hexadecimal digits of pi. 2. XOR P1 with the first 32 bits of the key, XOR P2 with the second 32-bits of the key, and so on for all bits of the key (possibly up to P14). Repeatedly cycle through the key bits until the entire P-array has been XORed with key bits. 3. Encrypt the all-zero string with the Blowfish algorithm, using the subkeys described in steps (1) and (2). 4. Replace P1 and P2 with the output of step (3). 5. Encrypt the output of step (3) using the Blowfish algorithm with the modified subkeys. 6. Replace P3 and P4 with the output of step (5). 7. Continue the process, replacing all entries of the P array, and then all four S-boxes in order, with the output of the continuously changing Blowfish algorithm. Encryption is done in this way: The input is a 64-bit data element, x.
__________________________________________________________________________________________
Volume: 02 Issue: 07 | Jul-2013, Available @ http://www.ijret.org 65
IJRET: International Journal of Research in Engineering and Technology
eISSN: 2319-1163 | pISSN: 2321-7308
boxes. These S-boxes were based on modular arithmetic with polynomials. Each version uses a different cipher key size (128, 192, or 256), but the round keys are always 128 bits. AES, like DES, uses substitution. AES uses two invertible transformations. The first transformation, SubBytes, is used at the encryption site. To substitute a byte, we interpret the byte as two hexadecimal digits. Step 1: ByteSub Transformation Step 2: ShiftRow Transformation Step 3: MixColumn Transformation Step 4: Round Key Addition
Final round is a little different because it removes the MixColumns step.
5. COMPARISON WITH AES
The Advanced Encryption Standard (AES) is a symmetric-key block cipher published by the National Institute of Standards and Technology (NIST) in December 2001. AES has defined three versions, with 10, 12, and 14 rounds. It was similar to DES: block cipher (with different modes), but 128-bit blocks 128-bit, 192-bit, or 256-bit key, Mix of permutations, S-
__________________________________________________________________________________________
Volume: 02 Issue: 07 | Jul-2013, Available @ http://www.ijret.org 66
IJRET: International Journal of Research in Engineering and Technology
eISSN: 2319-1163 | pISSN: 2321-7308
Each byte of the block is replaced by its substitute in an Sbox. Each byte is treated independently and single S-box is used for the entire state. Each row of the state is shifted cyclically a certain number of steps. State columns are treated as polynomials over GF(28). Each column is multiplied by modulo x4 + 1 by a fixed polynomial c(x) = `03` x3 + `01` x2 + `01`x + `02`. It has been shown Rijndael can be written as an over defined system of multivariate quadratic equations. Assuming that one could build a machine that could recover a DES key in a second (i.e., try 255 keys per second), then it would take that machine approximately 149 trillion years to crack a 128-bit AES key.
CONCLUSIONS
DES was prone to attacks and the triple DES standard was considered slow. The blowfish algorithm when combined with the triple DES algorithm would provide a better algorithm. It would be less prone to attacks. Triple DES would provide it with security and the blowfish algorithm will add to the speed of the algorithm.
REFERENCES
[1] [2] William Stallings Cryptography and Network Security,3rd Edition, Prentice-Hall Inc., 2005. A study of DES and Blowfish encryption algorithm, Tingyuan Nie ; Commun. & Electron. Eng. Inst., Qingdao Technol. Univ., Qingdao, China ; Teng Zhang. Performance Evaluation of DES and Blowfish Algorithms, Tingyuan Nie ; Commun. & Electron. Eng. Inst., Qingdao Technol. Univ., Qingdao, China ; Chuanwang Song ; Xulong Zhi. A proposed mode for triple-DES encryption, Coppersmith, D. ; IBM Research Division, Thomas J. Watson Research Center, P.O. Box 218, Yorktown Heights, New York 10598, USA ; Johnson, D.B. ; Matyas, S.M. Integrated design of AES (Advanced Encryption Standard) encrypter and decrypter, Chih-Chung Lu ; Internet Platform Application Dept., Ind. Technol. Res. Inst., Hsinchu, Taiwan ; Shau-Yin Tseng.
[3]
[4]
[5]
__________________________________________________________________________________________
Volume: 02 Issue: 07 | Jul-2013, Available @ http://www.ijret.org 67
S-ar putea să vă placă și
- Enhancing Post Disaster Recovery by Optimal Infrastructure Capacity BuildingDocument8 paginiEnhancing Post Disaster Recovery by Optimal Infrastructure Capacity BuildingInternational Journal of Research in Engineering and TechnologyÎncă nu există evaluări
- Wind Damage To Trees in The Gitam University Campus at Visakhapatnam by Cyclone HudhudDocument11 paginiWind Damage To Trees in The Gitam University Campus at Visakhapatnam by Cyclone HudhudInternational Journal of Research in Engineering and TechnologyÎncă nu există evaluări
- Impact of Flood Disaster in A Drought Prone Area - Case Study of Alampur Village of Mahabub Nagar DistrictDocument5 paginiImpact of Flood Disaster in A Drought Prone Area - Case Study of Alampur Village of Mahabub Nagar DistrictInternational Journal of Research in Engineering and TechnologyÎncă nu există evaluări
- Flood Related Disasters Concerned To Urban Flooding in Bangalore, IndiaDocument8 paginiFlood Related Disasters Concerned To Urban Flooding in Bangalore, IndiaInternational Journal of Research in Engineering and TechnologyÎncă nu există evaluări
- Groundwater Investigation Using Geophysical Methods - A Case Study of Pydibhimavaram Industrial AreaDocument5 paginiGroundwater Investigation Using Geophysical Methods - A Case Study of Pydibhimavaram Industrial AreaInternational Journal of Research in Engineering and TechnologyÎncă nu există evaluări
- Likely Impacts of Hudhud On The Environment of VisakhapatnamDocument3 paginiLikely Impacts of Hudhud On The Environment of VisakhapatnamInternational Journal of Research in Engineering and TechnologyÎncă nu există evaluări
- Wind Damage To Buildings, Infrastrucuture and Landscape Elements Along The Beach Road at VisakhapatnamDocument10 paginiWind Damage To Buildings, Infrastrucuture and Landscape Elements Along The Beach Road at VisakhapatnamInternational Journal of Research in Engineering and TechnologyÎncă nu există evaluări
- Shear Strength of RC Deep Beam Panels - A ReviewDocument15 paginiShear Strength of RC Deep Beam Panels - A ReviewInternational Journal of Research in Engineering and TechnologyÎncă nu există evaluări
- Monitoring and Assessment of Air Quality With Reference To Dust Particles (Pm10 and Pm2.5) in Urban EnvironmentDocument3 paginiMonitoring and Assessment of Air Quality With Reference To Dust Particles (Pm10 and Pm2.5) in Urban EnvironmentInternational Journal of Research in Engineering and TechnologyÎncă nu există evaluări
- Effect of Lintel and Lintel Band On The Global Performance of Reinforced Concrete Masonry In-Filled FramesDocument9 paginiEffect of Lintel and Lintel Band On The Global Performance of Reinforced Concrete Masonry In-Filled FramesInternational Journal of Research in Engineering and TechnologyÎncă nu există evaluări
- Low Cost Wireless Sensor Networks and Smartphone Applications For Disaster Management and Improving Quality of LifeDocument5 paginiLow Cost Wireless Sensor Networks and Smartphone Applications For Disaster Management and Improving Quality of LifeInternational Journal of Research in Engineering and TechnologyÎncă nu există evaluări
- Role of Voluntary Teams of Professional Engineers in Dissater Management - Experiences From Gujarat EarthquakeDocument6 paginiRole of Voluntary Teams of Professional Engineers in Dissater Management - Experiences From Gujarat EarthquakeInternational Journal of Research in Engineering and TechnologyÎncă nu există evaluări
- Cyclone Disaster On Housing and Coastal AreaDocument7 paginiCyclone Disaster On Housing and Coastal AreaInternational Journal of Research in Engineering and TechnologyÎncă nu există evaluări
- Hudhud Cyclone - A Severe Disaster in VisakhapatnamDocument8 paginiHudhud Cyclone - A Severe Disaster in VisakhapatnamInternational Journal of Research in Engineering and TechnologyÎncă nu există evaluări
- A Geophysical Insight of Earthquake Occurred On 21st May 2014 Off Paradip, Bay of BengalDocument5 paginiA Geophysical Insight of Earthquake Occurred On 21st May 2014 Off Paradip, Bay of BengalInternational Journal of Research in Engineering and TechnologyÎncă nu există evaluări
- Cpw-Fed Uwb Antenna With Wimax Band-Notched CharacteristicsDocument5 paginiCpw-Fed Uwb Antenna With Wimax Band-Notched CharacteristicsInternational Journal of Research in Engineering and TechnologyÎncă nu există evaluări
- Review Study On Performance of Seismically Tested Repaired Shear WallsDocument7 paginiReview Study On Performance of Seismically Tested Repaired Shear WallsInternational Journal of Research in Engineering and TechnologyÎncă nu există evaluări
- Comparative Study of The Forces in G+5 and G+10 Multi Storied Buildings Subjected To Different Wind SpeedsDocument10 paginiComparative Study of The Forces in G+5 and G+10 Multi Storied Buildings Subjected To Different Wind SpeedsInternational Journal of Research in Engineering and TechnologyÎncă nu există evaluări
- Assessment of Seismic Susceptibility of RC BuildingsDocument4 paginiAssessment of Seismic Susceptibility of RC BuildingsInternational Journal of Research in Engineering and TechnologyÎncă nu există evaluări
- Detection of Hazard Prone Areas in The Upper Himalayan Region in Gis EnvironmentDocument9 paginiDetection of Hazard Prone Areas in The Upper Himalayan Region in Gis EnvironmentInternational Journal of Research in Engineering and TechnologyÎncă nu există evaluări
- Challenges in Oil and Gas Industry For Major Fire and Gas Leaks - Risk Reduction MethodsDocument4 paginiChallenges in Oil and Gas Industry For Major Fire and Gas Leaks - Risk Reduction MethodsInternational Journal of Research in Engineering and TechnologyÎncă nu există evaluări
- Developing of Decision Support System For Budget Allocation of An R&D OrganizationDocument6 paginiDeveloping of Decision Support System For Budget Allocation of An R&D OrganizationInternational Journal of Research in Engineering and TechnologyÎncă nu există evaluări
- Can Fracture Mechanics Predict Damage Due Disaster of StructuresDocument6 paginiCan Fracture Mechanics Predict Damage Due Disaster of StructuresInternational Journal of Research in Engineering and TechnologyÎncă nu există evaluări
- Effect of Hudhud Cyclone On The Development of Visakhapatnam As Smart and Green City - A Case StudyDocument4 paginiEffect of Hudhud Cyclone On The Development of Visakhapatnam As Smart and Green City - A Case StudyInternational Journal of Research in Engineering and TechnologyÎncă nu există evaluări
- Coastal Zones - Seismic Vulnerability An Analysis From East Coast of IndiaDocument4 paginiCoastal Zones - Seismic Vulnerability An Analysis From East Coast of IndiaInternational Journal of Research in Engineering and TechnologyÎncă nu există evaluări
- Disaster Recovery Sustainable HousingDocument4 paginiDisaster Recovery Sustainable HousingInternational Journal of Research in Engineering and TechnologyÎncă nu există evaluări
- Brain Tumor Segmentation Using Asymmetry Based Histogram Thresholding and K-Means ClusteringDocument4 paginiBrain Tumor Segmentation Using Asymmetry Based Histogram Thresholding and K-Means ClusteringInternational Journal of Research in Engineering and TechnologyÎncă nu există evaluări
- Analytical Solutions For Square Shape PressureDocument4 paginiAnalytical Solutions For Square Shape PressureInternational Journal of Research in Engineering and TechnologyÎncă nu există evaluări
- Rate Adaptive Resource Allocation in Ofdma Using Bees AlgorithmDocument5 paginiRate Adaptive Resource Allocation in Ofdma Using Bees AlgorithmInternational Journal of Research in Engineering and TechnologyÎncă nu există evaluări
- Shoe Dog: A Memoir by the Creator of NikeDe la EverandShoe Dog: A Memoir by the Creator of NikeEvaluare: 4.5 din 5 stele4.5/5 (537)
- The Yellow House: A Memoir (2019 National Book Award Winner)De la EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Evaluare: 4 din 5 stele4/5 (98)
- Never Split the Difference: Negotiating As If Your Life Depended On ItDe la EverandNever Split the Difference: Negotiating As If Your Life Depended On ItEvaluare: 4.5 din 5 stele4.5/5 (838)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceDe la EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceEvaluare: 4 din 5 stele4/5 (890)
- Grit: The Power of Passion and PerseveranceDe la EverandGrit: The Power of Passion and PerseveranceEvaluare: 4 din 5 stele4/5 (587)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeDe la EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeEvaluare: 4 din 5 stele4/5 (5794)
- The Little Book of Hygge: Danish Secrets to Happy LivingDe la EverandThe Little Book of Hygge: Danish Secrets to Happy LivingEvaluare: 3.5 din 5 stele3.5/5 (399)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureDe la EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureEvaluare: 4.5 din 5 stele4.5/5 (474)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryDe la EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryEvaluare: 3.5 din 5 stele3.5/5 (231)
- The Emperor of All Maladies: A Biography of CancerDe la EverandThe Emperor of All Maladies: A Biography of CancerEvaluare: 4.5 din 5 stele4.5/5 (271)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersDe la EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersEvaluare: 4.5 din 5 stele4.5/5 (344)
- On Fire: The (Burning) Case for a Green New DealDe la EverandOn Fire: The (Burning) Case for a Green New DealEvaluare: 4 din 5 stele4/5 (73)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaDe la EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaEvaluare: 4.5 din 5 stele4.5/5 (265)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyDe la EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyEvaluare: 3.5 din 5 stele3.5/5 (2219)
- Team of Rivals: The Political Genius of Abraham LincolnDe la EverandTeam of Rivals: The Political Genius of Abraham LincolnEvaluare: 4.5 din 5 stele4.5/5 (234)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreDe la EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreEvaluare: 4 din 5 stele4/5 (1090)
- The Unwinding: An Inner History of the New AmericaDe la EverandThe Unwinding: An Inner History of the New AmericaEvaluare: 4 din 5 stele4/5 (45)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)De la EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Evaluare: 4.5 din 5 stele4.5/5 (119)
- Her Body and Other Parties: StoriesDe la EverandHer Body and Other Parties: StoriesEvaluare: 4 din 5 stele4/5 (821)
- What Do Good Hackers DoDocument3 paginiWhat Do Good Hackers Dofilipczar230% (1)
- Information Security Two Marks With AnswerDocument18 paginiInformation Security Two Marks With AnswerThumilvannan SambandamÎncă nu există evaluări
- One and The Same Certificate: Government of KeralaDocument1 paginăOne and The Same Certificate: Government of KeralaJostin PunnasseryÎncă nu există evaluări
- Crypto Anal Is IsDocument102 paginiCrypto Anal Is IsHugo LinaresÎncă nu există evaluări
- Message Integrity and AuthenticationDocument31 paginiMessage Integrity and Authenticationrahulthebest15Încă nu există evaluări
- Computer Security Book 27-08-2022 - Proof Reading Unit 1 - 4Document396 paginiComputer Security Book 27-08-2022 - Proof Reading Unit 1 - 4Dr. Ramesh Singh GautamÎncă nu există evaluări
- Guide To Internet Cryptography: Jörg SchwenkDocument535 paginiGuide To Internet Cryptography: Jörg SchwenkWilliam Danilo Saboya BautistaÎncă nu există evaluări
- Iclass Bioclass Readers rklb57 rwklb575 Ds enDocument2 paginiIclass Bioclass Readers rklb57 rwklb575 Ds enharish sawsundarÎncă nu există evaluări
- Key For NOD32Document8 paginiKey For NOD32Alin HînceştiÎncă nu există evaluări
- Active Directory Security Best PracticesDocument10 paginiActive Directory Security Best PracticesSEEMA SEEMAÎncă nu există evaluări
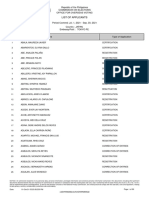
- List of Applicants 20210701 0930Document107 paginiList of Applicants 20210701 0930Rovern Keith Oro CuencaÎncă nu există evaluări
- Intro to Cyber SecurityDocument11 paginiIntro to Cyber SecurityAsh KetchumÎncă nu există evaluări
- Info Assurance PDFDocument13 paginiInfo Assurance PDFRoger AndalÎncă nu există evaluări
- Squirrel 2014 PA DSS Implementation Guide v3!03!01!20!2014Document203 paginiSquirrel 2014 PA DSS Implementation Guide v3!03!01!20!2014Mazen Al-Refaei100% (1)
- Magic Quadrant For Web Application FirewallsDocument13 paginiMagic Quadrant For Web Application Firewallsnao2001Încă nu există evaluări
- Cryptography Network Security PDFDocument43 paginiCryptography Network Security PDFprasadÎncă nu există evaluări
- Finalsol f05Document6 paginiFinalsol f05sparkyboy1Încă nu există evaluări
- Host HardeningDocument28 paginiHost HardeningYonGodeÎncă nu există evaluări
- A Security Analysis Comparison Between Signal, Whatsapp and TelegramDocument15 paginiA Security Analysis Comparison Between Signal, Whatsapp and TelegramjdhffszlagsxyvÎncă nu există evaluări
- Quorum-Guide (The Top 4 Security Threats of 2021)Document8 paginiQuorum-Guide (The Top 4 Security Threats of 2021)EditorÎncă nu există evaluări
- Fortiweb v6.1.0 Admin Guide PDFDocument862 paginiFortiweb v6.1.0 Admin Guide PDFdonna.nixÎncă nu există evaluări
- TCS Class - II IndividualDocument3 paginiTCS Class - II Individualdigital SignatureÎncă nu există evaluări
- Partner Playbook: Data Protection PortfolioDocument34 paginiPartner Playbook: Data Protection Portfoliokarlosm84Încă nu există evaluări
- What Is Cybercrime?Document3 paginiWhat Is Cybercrime?JoshuaFrom YTÎncă nu există evaluări
- HSM Key Change Flow Using ThalesDocument9 paginiHSM Key Change Flow Using ThalesSURYA DHARMA PUTRAÎncă nu există evaluări
- Introduction To Security and Network ForensicsDocument495 paginiIntroduction To Security and Network ForensicsAriel CupertinoÎncă nu există evaluări
- Active Exploitation: Con Uence Server CVE-2021-26084: Learn MoreDocument2 paginiActive Exploitation: Con Uence Server CVE-2021-26084: Learn Morefateh tiribarkÎncă nu există evaluări
- Ch09+-+Public Key Cryptography and RSADocument49 paginiCh09+-+Public Key Cryptography and RSASawsan TawfiqÎncă nu există evaluări
- Samara University Computer Security Group PKI ReportDocument16 paginiSamara University Computer Security Group PKI Reporthamza iliyas100% (1)
- Preseented By: LUCKY BEHERA (BS21-149)Document20 paginiPreseented By: LUCKY BEHERA (BS21-149)vaxepo6367Încă nu există evaluări