Documente Academic
Documente Profesional
Documente Cultură
FI - 13-284 - Feb 1 2014
Încărcat de
newton1980 evaluări0% au considerat acest document util (0 voturi)
734 vizualizări83 paginiFringe Intelligence Open Source
Drepturi de autor
© © All Rights Reserved
Formate disponibile
PDF, TXT sau citiți online pe Scribd
Partajați acest document
Partajați sau inserați document
Vi se pare util acest document?
Este necorespunzător acest conținut?
Raportați acest documentFringe Intelligence Open Source
Drepturi de autor:
© All Rights Reserved
Formate disponibile
Descărcați ca PDF, TXT sau citiți online pe Scribd
0 evaluări0% au considerat acest document util (0 voturi)
734 vizualizări83 paginiFI - 13-284 - Feb 1 2014
Încărcat de
newton198Fringe Intelligence Open Source
Drepturi de autor:
© All Rights Reserved
Formate disponibile
Descărcați ca PDF, TXT sau citiți online pe Scribd
Sunteți pe pagina 1din 83
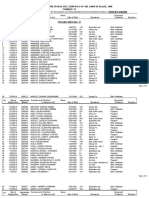
FRINGE INTELLIGENCE - year 13 - no.
284 February 1 2014 - page 1
FRINGE INTELLIGENCE
* A biweekly journal focusing on not yet established & next to mainstream intel news *
* Editor: Roger Vleugels - roger.vleugels@planet.nl *
* Donations are very welcome, see colophon *
* Year 13- No. 284 February 1 2014 *
General content
02 Reporting in the Post-Snowden Era
03 Al Qaeda: A NSA Surveillance Target
05 Snow Job
07 Failures of Intelligence
08 British Spies Snooped on Facebook
10 Angry Birds, NSA and GCHQ
13 Turkish Intel Trucks Reveal Secrets
14 UK Loses its Liberties
15 Assad Accused of Boosting al-Qaeda
16 Google Calls for new NSA Reforms
18 Germany Eyes SIGINT Airframes
18 Out of Blackwater and Into China
20 The Facts about the Metadata 'Menace'
21 The CIAs Black Prison in Poland
23 Russia's Surveillance State
28 Intel Can't Deal with Nuclear Tasks
29 The US Surrounded Iran with Drones
30 The Escalating Obama Drone Campaign
32 NSAs Spying on Phone Calls Illegal
33 Claims Obama Made on NSA Surveillance
35 Israel Busts Jihad Terror Cell
36 US withholding Fisa Court Orders ... NSA
37 FBI Emphasizes Law Enforcement's Role
37 Israel, Urenco and Stuxnet
41 A 'lost Decade' since 9/11
42 NSA Provided 1,000 Terror Tips to FBI
43 Karegeya Murder Case at sensitive Stage
43 Die Ermordung von Karegeya
45 UK Deports Taiwanese Intel Agent
46 Beyond Snowden: A NSA Reality Check
50 Canadian Eavesdropping Review
51 Top Secret NSA Slides and SMS
52 Social Network Analysis in Intelligence
58 NSA Reforms Are PR Only
59 NSA Spying Fallout Hits French ... Deal
60 NSA Collects Millions of Text Messages
62 Some Restraints on US Surveillance
64 Surveillance Threatens US Business
65 Philippines: ISAFP to Be Expanded
66 Report on Benghazi Terrorist Attacks
66 German Double Agent Killed in Pakistan
67 US Anti-Drug Center in Bahrain
68 Drone Control: CIA or Pentagon
70 Breaking the India-US diplomatic Ice
70 Obama from Spy Critic to Overseer
Content on NARINT: Natural Resources Intel
72 US Spied on 2009 Climate Summit
74 Enhanced Geothermal Energy Systems
Content on Intelligence 2.0: The IT Wild West
75 Mark Zuckerberg Runs a ... Spy Machine
Content on The Netherlands
77 Philips werkte samen met NSA - 2
77 Philips werkte samen met NSA - 1
78 Steden runnen eigen inlichtingendienst
79 AIVD informeert burgemeesters over AFA
Content in the Fringe
81 The Remote Stopping of Cars
82 Fringe Colophon
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 2
REPORTING IN THE POST-SNOWDEN ERA
A panel at Columbia discussed challenges and triumphs
http://www.cjr.org/behind_the_news/snowden_abramson_bell_columbia.php?page=all
Columbia journalism Review / by Lauren Kirchner
Jan 31 2014 Jan 31. In an auditorium so large that Columbia's Journalism School typically only
uses it for its graduation ceremonies, hundreds attended the panel discussion Journalism After Snow-
den on Thursday evening. The topic was as vast as it is timely encompassing the rising tensions
between media organizations and their governments, the practical process of protecting sensitive
information (digitally) and oneself (legally), and the delicate dance between privacy and power.
Emily Bell, director of the Tow Center at the journalism school, moderated the panel, and she started it
off by asking Guardian US Editor in Chief Janine Gibson to give a behind-the-scenes account of the
very beginning of the Summer of Snowden. Gibson described how Glenn Greenwald called her in New
York shortly after making contact with his then-nameless source, saying something like I think I have
the biggest intelligence leak in a generation, if not ever.
Gibson was skeptical, but listening; however, she also knew that Greenwald was calling her from Rio
over a Skype line. She knew from her previous work on the paper's WikiLeaks coverage that Skype
was relatively untrustworthy technology, and she all but hung up on him. But Greenwald soon flew to
New York to meet with her and a few trusted staff members. There, he showed them the tiny sample
of stuff he had gotten from his source starting with the PRISM PowerPoint slides on a new, air-gapped
laptop hastily bought from Best Buy for the occasion.
You very quickly realize that this is an incredibly huge, sensitive, difficult story or it's the Hitler Diaries,
it's a great big hoax, said Gibson. Then came the story of the now-familiar trip to Hong Kong, and their
meeting with an oddly young contractor and his Rubik's Cube, and the cache of documents of a size
that no one has yet been able to quantify.
Verifying that Snowden's account was legit was one challenge reporting the story out was an entirely
different one. They started with the Foreign Intelligence Surveillance Court order for Verizon metadata.
We were trying to edit, write, report, understand, and verify a document that no one has ever seen,
said Gibson. You can't Google secret FISA Court order to see if it looks like one that's in front of you.
The audience laughed at this. No, that's not funny, that's a genuine problem, she countered, drily.
The conversation shifted to the Guardian's collaboration with The New York Times as the documents
from Snowden kept coming over the following months. Jill Abramson's first response to Bell's question
about the Times getting involved was an honest memory of her disappointment that her paper hadn't
been first with the scoop. We did not break the story the Guardian and The Washington Post did and
that caused me, you know, severe indigestion, said Abramson.
But both Gibson and Abramson agreed that the partnership between the two papers during this
process was invaluable. Tech-savvy reporters and editors at the Guardian educated their peers at the
Times about best digital-security practices for communicating, searching, viewing, and storing the
classified documents. Then, the Times was able to protect the files when the British government
aggressively pursued (and forced editors to destroy) the Guardian's hard drives in the UK.
The Guardian's outside counsel, David Schulz, was on the panel as well. He had previously worked
with the Times during their WikiLeaks coverage. When asked about the legal challenges to news or-
ganizations dealing with such sensitive material, he started with the word conundrum. A news organi-
zation possessing and then publishing classified documents is still a legal gray area, said Schulz.
Later in the evening, Barton Gellman, who leads NSA coverage at The Washington Post, spoke to this
same issue. Speaking from the audience, Gellman asked the panelists to try to parse the Director of
National Intelligence's statement this week that Edward Snowden and his accomplices should return
the documents he stole in order to protect US security from being further compromised. Are we to
understand that James Clapper was referring to the press with that term, accomplices, Gellman asked,
or was this just a rhetorical flourish of his agency's frustration? Either way, he said, it is getting harder
to report on national security issues.
Almost everything you want to write about, if you are writing about diplomacy or intelligence or defen-
se, is classified; everything but the press release and the news conference is classified, Gellman said.
That's just the way the US government works. There may be more classified information now than
there is open-source information on the planet.
In a larger sense, though, what information is or is not classified, and what legal protections reporters
may or may not have, are beside the point as these NSA stories have revealed. Schulz responded to
Gellman's concerns with this frightening truth: The technology that we have today, you don't need to
subpoena a reporter anymore. There's an ability to find out who gave out any information, said Schulz.
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 3
And we should all be very concerned about that, because we all need whistleblowers. If we don't have
a mechanism that allows for whistleblowers, our whole society is going to suffer.
That was a persistent and important theme that the panel kept returning to that, besides journalists
legal protections, equivalent protections should be extended to the people who risk their livelihoods,
and lives, to bring this information to light in the first place. Gibson said Snowden had an eerie
prescience, and described his sense of urgency in getting as many NSA stories published before the
government, and his critics, tried to make the story about him and his traitorous intentions.
Bell agreed: Where oversight has failed, a whistleblower and journalism has succeeded, she said. And
yet the system is still wanting to punish, if you like, the one thing which has led to transparency and
clarity.
But that should be completely unsurprising, Abramson jumped in, citing the fact that the current ad-
ministration has investigated seven criminal leaks, more than twice the number of such investigations,
based on a law passed in 1917, pursued before President Obama took office. That such legal battles
were still being fought by James Rosen, of Fox News, and James Risen, of the Times, were mention-
ed several times throughout the evening.
Gibson also highlighted the new and alarming ways in which the Snowden story has caused certain
threats from the establishment to escalate.
Instead of the position that journalists find themselves in where they're being threatened with prosecu-
tion over identifying their sources, we are now being put in the position of something even more
chilling of being co-conspirators, said Gibson. The accusation is now You're part of a conspiracy,
possibly involving the KGB, or maybe China. Because the ordinary way of chilling journalism won't
work in this case. And I think this should be profoundly worrying, because that's not going to stop. That
is a Journalism After Snowden problem.
At one point, Bell asked the panel, I think we can all agree that Edward Snowden has done us a favor.
Do we have general agreement on that?
I have no comment on that, answered Cass Sunstein, the fourth panelist, who participated in the Pre-
sident's outside review group that recently released a report proposing changes to the NSA surveillan-
ce program. We have a 300-page report, and the word Snowden doesn't appear. Later, Sunstein also
said that he did not think that the members of the review group would refer to Snowden as a whistle-
blower at all. (So what is he, then?)
After a substantial question-and-answer period from the audience, Bell ended the night by asking the
panelists for their magic-wand wish for what journalism would ideally look like in this post-Snowden
age. Sunstein named internet freedom, and Schultz imagined an internationally agreed-upon standard
for individual privacy rights.
The two editors had more profession-specific requests.
More great stories, said Abramson.
No prosecution for journalists, said Gibson. This was met by spontaneous applause.
AL QAEDA: A NSA SURVEILLANCE TARGET
More Snowden leaks - and this time Al Qaeda is the surveillance target
Unredacted NSA power point slides, leaked by Snowden, reveal a program to track terrorists
via their mobile phones.
www.csmonitor.com/World/Security-Watch/Backchannels/2014/0130/More-Snowden-leaks-and-this-time-Al-Qaeda-is-the-surveillance-target
Christian Science Monitor / by Dan Murphy
Stringer: Martin Rudner [ret.] / Carleton University / Ottawa / www.carleton.ca/cciss
Jan 31 2014 Jan 31. Earlier this week The New York Times and other newspapers, relying on
power point slides stolen from the National Security Agency by Edward Snowden, reported that the US
and Britain have been trying to develop better means to spy on the massive amounts of data filtering
through smart phones and into the world's telecommunications networks.
A particular target has been smartphone apps everything from the popular game Angry Birds to
photo uploading tools. As the Times wrote:
According to dozens of previously undisclosed classified documents, among the most valuable of
those unintended intelligence tools are so-called leaky apps that spew everything from the
smartphone identification codes of users to where they have been that day.
The NSA. and Britains Government Communications Headquarters were working together on how to
collect and store data from dozens of smartphone apps by 2007, according to the documents,
provided by Edward J. Snowden, the former NSA. contractor. Since then, the agencies have traded
recipes for grabbing location and planning data when a target uses Google Maps, and for vacuuming
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 4
up address books, buddy lists, telephone logs and the geographic data embedded in photographs
when someone sends a post to the mobile versions of Facebook, Flickr, LinkedIn, Twitter and other
Internet services.
The paper also uploaded some of the slides, but with one problem: Amateurish redaction of some
details, designed to hide the identity of an NSA employee and make it harder for terrorist groups to
make good use of the information, that was no redaction at all. The paper quickly rectified the error but
not before the original uploads were snatched by the anti-secrecy website Cryptome, at least accord-
ing to a Twitter account linked to the website. (The person who controls the account has since deleted
this claim, as well as an assertion that he'd do any redactions himself when "hell freezes over.")
This error highlights the risks of the tens of thousands of Snowden documents that are now floating
around among at least a dozen journalists: Promises that all documents will be handled carefully and
be fully vetted by responsible reporters are just that. The more documents and different organizations
involved, the greater chances for error and there is little point in closing the barn door after the
horses have bolted.
But what caught my eye in one of the unredacted slides was the mention of Al Qaeda in Iraq being a
particular target of the NSA's efforts. The slide reads: "Visual Communicator Free application that
combines Instant Messaging, Photo-Messaging, and Push2Talk capabilities on a mobile platform. VC
used on GPRS or 3G networks." The next five words were what the Times tried and failed to redact:
"heavily used in AQI Mosul Network."
The aim as described in the documents is to target mobile phone apps that can give away a target's
physical location. The utility of this in tracking terrorists hardly needs to be stated. The document
describes a program focusing on clear security interests Al Qaeda in Iraq, now calling itself Al Qaeda
in Iraq and the Levant (ISIS) killed thousands in Iraq during the US-led war there and continues to
carry out suicide bombings and attacks on civilians there on a weekly basis. ISIS is also deeply
involved in the civil war in Syria, and the groups ties to Al Qaeda make it an obvious security concern
for the US.
Snowden has often insisted that he isn't interested in exposing intelligence programs that have
legitimate security concerns behind them and has gone so far as to say that almost none of the NSA's
efforts have anything to do with terrorism. Glenn Greenwald, who's worked with Snowden on releasing
NSA documents since at least February of last year, has also made that second claim.
In December Snowden wrote an open letter to "the people of Brazil" (he's been hoping to get asylum
there) and in it he claimed:
There is a huge difference between legal programs, legitimate spying, legitimate law enforcement
where individuals are targeted based on a reasonable, individualized suspicion and these programs
of dragnet mass surveillance that put entire populations under an all-seeing eye and save copies
forever.
These programs were never about terrorism: theyre about economic spying, social control, and
diplomatic manipulation. Theyre about power.
Mr. Greenwald said the following in an interview with CNN's Christian Amanpour last October, after
being asked if leaders like British Prime Minister David Cameron were correct in saying the world has
become a more dangerous place because "bad guys know how we're listening to them and we're not
able to do as much intercepting and stopping of these potentially damaging plots as we could in the
past":
Let's just use our common sense analyzing the claims of political officials when they say that. Ever
since 9/11 British and American officials have screamed terrorism over and over and over every time
they get caught doing bad doing things they shouldn't do -- from lying to the public about invading Iraq
to setting up a worldwide torture regime to kidnapping people and taking them around the world to be
tortured. They just want to put the population in fear by saying that terrorists will get you if you don't
want to submit to whatever authority it is that we want to do and that's all they're doing here. It's the
same tactic they always use. Let's just use common sense. Every terrorist who's capable of tying their
own shoes has long known that the US government and the UK government are trying to monitor their
communications in every way that they can. That isn't new. We didn't reveal anything to the terrorists
that they didn't already know. What we revealed is that the spying system is largely devoted not to
terrorists but is directed at innocent people around the world. That is what was not previously known
and that is why American and British officials are so angry because they wanted to hide what the true
purpose of the spying system is from the people at whom it's directed. And that is the only thing that's
new in what we reported.
Amanpour then plays a short clip of Rep. Mike Rogers saying that if French people understood the
uses and intent of NSA telecommunications in that country, which he says is focused on terrorism and
security, they'd "be popping champagne corks." Greenwald responds:
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 5
Well first of all a lot of people like to ask why is there so much anti-American sentiment around the
world all you have to do is listen to that tape of Mike Rogers to understand it he's basically going
around telling the world that they ought to be grateful that without their knowledge we're stealing all of
their communications data and invading their privacy. None of this has anything to do with terrorism. Is
Angela Merkel a terrorist? Are 60 or 70 million French citizens terrorists?... This is is clearly about
political power and economic espionage and the claim that this is all about terrorism is seen around
the world as what it is. Which is -- pure deceit.
The above two quotes contain a lot of hogwash, not to mention Greenwald's extremely binary thinking
on this issue.
Is all American spying about terrorism? No. And no one in the government ever claimed that. The US
Congress has directed the NSA and other intelligence agencies to collect intelligence on foreign
governments, just as they collect intelligence on the US.
Is it reasonable to claim that the US and other governments have overplayed the threat of terrorism as
justification for acts that erode civil liberties? In my view, absolutely.
But his claim that "none of this has anything to do with terrorism" is not reasonable. That's pure
nonsense -- as is his attempt to suggest that any revelations of eavesdropping techniques can't do any
harm because terrorists already know all about it. Terrorists may know that the US is trying to spy on
them as best it can (just as Germany and France know that). But knowing the precise methods is
another thing altogether.
That fact is that while intelligence tools created to spy on terrorists could end up being used and
misused for other purposes, it's an enormous logical leap to then claim that "this is is clearly about
political power and economic espionage and the claim that this is all about terrorism is seen around
the world as what it is. Which is -- pure deceit."
That's a claim refuted by a careful reading of the documents Greenwald say help prove his position.
SNOW JOB
It's time to blow the whistle on Edward Snowden.
www.politico.com/magazine/story/2014/01/edward-snowden-nsa-snow-job-102740.html#ixzz2rtIjvsby
Politico / by Edward Lucas [Senior editor at the Economist. His newest book: Tthe Snowden Operation]
Stringer: Martin Rudner [ret.] / Carleton University / Ottawa / www.carleton.ca/cciss
Jan 30 2014 Jan 28. Anyone who has seen the Bourne Identity, or scores of similar Hollywood
films, finds Edward Snowden a familiar character. The fugitive insider is the star. The rogue agency is
the villain in pursuit. By the closing credits, the hero will be vindicated, thanks to media coverage and
belated congressional scrutiny. He gets the girl. Generals James Clapper and Keith Alexanderor
their screen counterpartstake a perp walk.
It is easy to go along with that narrative, particularly if you are a journalist. Our trade instinctively sides
with David, not Goliath. We thrill to the idea of disclosing secrets. We flinch at any constraint on press
freedom. The thought of British spooks attacking a Guardian computer with an angle-grinder in the
name of safeguarding secrets that have already been copied and stashed elsewhere seems as
grotesque as it is pointless.
But I disagree. The theft and publication of secret documents, as my new book, The Snowden
Operation, argues, is not a heroic campaign but reckless self-indulgence, with disastrous
consequences. Snowden and his accomplices deserve censure, not applause.
Snowden claims the moral high ground. In a recent softball interview with German television, he
claimed that the National Security Agency was involved in scandalous industrial espionage. In a live
Q&A on his supporters website, he decried unaccountable senior officials authorizing these
unconstitutional programs. His revelations continue, most recently via NBC and the Guardian,
claiming among other things that the NSA uses the Angry Birds video game to track its targets
(though closer scrutiny of the material suggested a different story).
The furor is misleading, though. In judging the action of whistle-blowers, three criteria apply. They
must have clear and convincing evidence of abuse. Publishing the information must not pose a
disproportionate threat to public safety. And the leak must be as limited in scope and scale as
possible. Snowden failed all three of these tests.
The documents published thus far do not depict a rogue agency. They indicatewith partial, out-of-
date and ambiguous evidence, mostly consisting of out-of-context presentation slidesthat the NSA
has plenty of flaws. How could it not? Like other government agencies and bureaucracies, it pushes
the limits of its regulatory, political and judicial constraints. That is not surprising. Like people
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 6
everywhere, NSA officials brag. They make mistakes (and get disciplined for them). Again, not too
surprising.
To justify even a limited breach of secrecy, Snowden would need to prove something far more:
evidence of systematic, gross wrongdoing, based on wilful contempt for judicial, legislative and
political oversight. In such circumstances, the actions of a Daniel Ellsberg can be justified.
But nothing published by Snowden shows that. The NSA revealed in these documents looks nothing
like J. Edgar Hoovers FBI. And Barack Obama, for all his faults, is not Richard Nixon, using the power
of the state to go after his domestic enemies. On the contrary: The United States has put the most
elusive and lawless part of governmentintelligenceinto the strongest system of legislative and
judicial control anywhere in the world. Some want it still stronger (I think its too cumbersome and
intrusive). But such questions are for the political process to settle. They do not justify catastrophic and
destructive leaking.
The Snowdenistas second line of defense is that they have at least sparked a debate. But a public
discussion, and limited reforms, on issues such as the use of National Security Letters (secret FBI
orders to force people and businesses to cooperate with law enforcement), the privacy risks of
warehousing metadata and whether zero-day exploits (vulnerabilities in computer hardware and
software) should be instantly patched or exploited for espionageare limited benefits, not
overwhelming ones. They do not justify catastrophic damage either. The question of whether we
house telephone metadata at the NSA or house it at tech companies is not exactly the difference
between tyranny and freedom.
Nor does impact alone justify the actions of the Snowdenistas media accomplices. Journalism
operates in a moral framework. Every potential story has a source and an effect. A responsible editor
considers bothand not just the sizzle of the material itself. Simply arguing that a story will interest the
public betrays the medias claim to be taken seriously. The defense that there is no point turning down
a scoop because another outlet will publish it is even more unconvincing.
The Snowdenistas have not only failed to prove that the NSA is out of control, or that it intrudes on
Americans personal privacy. They have also published material that has nothing to do with these
issues. Why is it in the public interest to reveal how honest, law-governed countries spy on corrupt,
authoritarian ones? The Snowden revelations about Norwegian and Swedish intelligence cooperation
with the NSA against Russia, published by the Dagbladet newspaper in Oslo and Swedish television,
respectively, are the most glaring example of the thoughtlessness of the Snowden approach. These
countries have every reason to be worried about Russia. Their agencies operate under democratic
control and with strong public support. But for the Snowdenistas, the only thing that matters is that
they cooperate with the NSA, the Great Satan of the intelligence world. It is worth noting that America
is at the heart of the worlds only successful no-spy agreements, with its close allies notably Britain,
Canada, Australia and New Zealand. A list of countries that would trust Germany or France not to spy
on them would be rather shorter.
Other disclosures are similarly hard to justify. Why is it in the public interest to reveal how the NSA
intercepts e-mails, phone calls and radio transmissions of Taliban fighters in Pakistan, as
the Washington Post did, or to show that the agency is intensifying scrutiny on the security of that
countrys nuclear weapons? Snowden even revealed details of how the NSA hacks into computers
and mobile phones in China and Hong Konghardly whistleblowing stuff.
It is fatuous for Snowdens allies to say that they are keeping the stolen material safe from hostile
intelligence agencies. Few outsiders would suggest they have the skills or knowledge necessary to do
so. With equal fatuity, they assert that they redact the published material so as not to breach security.
How can they possibly know what will be damaging and what may be harmless? In any case, their
technical ability seems not to extend even to deleting an agents name from an Adobe Acrobat file.
Snowdens leaks have weakened Western security relationships, corroded public trust, undermined
the Wests standing in the eyes of the rest of the world and paralyzed our intelligence agencies. The
Snowdenistas seem oblivious to this. Like the anti-nuclear campaigners of the 1980s, or the anti-
capitalist protestors of more recent years, they see Western faults with blinding clarity, but forget that
we have enemies and competitors. When we stumbleor are trippedthey advance.
All this neatly and suspiciously fits the interests of one country, Russiawhich just happens to be
where Snowden arrived in such curious circumstances, and now lives in such strange secrecy. Based
on 30 years of experience dealing with friendly and hostile intelligence in the Cold War and afterwards,
I am stunned that colleagues who are so extraordinarily paranoid about the actions of their own
governments are so trusting when it comes to the aims and capabilities of the Russian authorities.
(Scanty clues, which I detail in the book, suggest that Snowden lives either in or near the Russian
foreign intelligence headquarters in Yasenevo in southern Moscow.)
The political agendas of the most ardent Snowdenistaspeople such as the bombastic Brazil-based
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 7
blogger Glenn Greenwald, the hysterical hacktivist Jacob Appelbaum and the WikiLeaks founder
Julian Assangecloak extreme and muddled beliefs in the language of privacy rights, civil liberties
and digital freedomsa naive and one-sided attitude exemplified by the Norwegian Socialist Left
Party's nomination of Snowden for the Nobel Peace prize. To expose and attack the security and
intelligence services of democracies, while sheltering in the capital of a country that habitually
menaces its neighbours, is an odd way of promoting world peace. A political party based on these
quasi-anarchist, nihilist ideas would get nowhere. Yet they are bringing about the greatest peacetime
defeat in the history of the West.
My argument does not rest on whispers from the shadows: It is based on publicly available facts, plain
for everyone to see. Snowden and the Snowdenistas are not on a noble crusade; they are at best
useful idiots, at worst engaged in sabotage and treason. Someone should make a Hollywood film
about it.
FAILURES OF INTELLIGENCE
http://krepon.armscontrolwonk.com/archive/4028/failures-of-intelligence
Arms Control Wonk / by Michael Krepon
Stringer: Kees Kalkman / VDAmok / Utrecht NL / kees@amok.antenna.nl
Jan 29 2014 Jan 26. US intelligence agencies have been guilty of four general types of error or
more, depending on counting rules. The most costly type of error is a failure to recognize and pull
together actionable intelligence in time to foil bad surprises. Type I errors are typically abetted by
compartmentalization within the intelligence community. The failure to connect the dots prior to 9/11
wasnt new; it used to be characterized as failing to detect signals in noise, as particularized in
Roberta Wohlstetters masterful book, Pearl Harbor: Warning and Decision. A subset of this type of
error is being unable to detect well-established, covert nuclear weapon programs, like Saddam
Husseins prior to the first Gulf war.
Type II errors are the reluctance or inability to predict the possibility of pleasant surprises, which
become possible when leaders change, when they realize dead-end policies, or when they mess up.
Its hard to predict good news. Leaders open to changing course remain surrounded by those who
have survived by not taking risks or by engaging in bad behavior. Besides, strategic culture doesnt
change on a dime, so risk-takers have to send mixed messages, signaling new possibilities while
protecting their flanks.
A subset of this type of error is assessing the existence of a well-established covert nuclear weapon
program when it may have been halted by decision, incompetence, or dysfunction. Examples include
Saddam Husseins Iraq prior to the second Gulf War and Muammar Qaddafis Libya.
Predicting more of the same is always a safer course than predicting the possibility of diplomatic
breakthroughs especially since the latter can brand the intelligence analyst as being hopelessly
nave. Did the US intelligence community see the course-correction in Burma coming, or was it as
wrong as the Kremlinologists who misread Gorbachev? As noted earlier in this space, US Iran
watchers and proliferation cynics may have gotten Rouhani wrong, as well well see.
Type III errors occur with the zealous collection of data that does far more harm to US diplomacy and
international standing than might be gained from preventing bad surprises. This error is now a daily
occurrence, enabled by new information-retrieval technologies and the lingering effects of suffering
massive attacks on the US homeland over a decade ago. One measure of how much 9/11 remains
with us is the reluctance of a President steeped in Constitutional Law to pare back the National
Security Agencys appetite for collecting and storing metadata on American citizens.
Type IV errors relate to discounting the possibility of paranoid behavior by bunkered adversaries. The
presumption at work here, sometimes tested by those seeking to burnish their hardline credentials, is
that bad actors wont over-act, even when the US jerks their chains. This type of error was most
egregiously on display in 1983, when some in the Reagan Administration were oblivious to the
possible consequences of pursuing initiatives to keep the Kremlin off-balance. The US intelligence
community, which found it difficult to distinguish between paranoid and aggressive Soviet behavior,
failed to raise cautionary flags. For those interested in the particulars of this Year of Living
Dangerously, check out the National Security Archives treasure trove of files about Able Archer.
The Obama Administration, chastened by ill-conceived, costly, and poorly executed wars in
Afghanistan and Iraq the surge in Iraq being successful only on a timescale irrelevant to larger
consequences is unlikely to engage in Type IV errors anytime soon, whether or not the intelligence
community speaks up.
The commingling of Type IV and Type II errors makes it hard to explore whether the potential for
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 8
positive developments exists below layers of paranoia and pathology. Making overtures to reduce
nuclear dangers in such cases requires heroic efforts to establish footholds for those not locked into
enemy images, to relax the grip of those who are, and to assure allies and friends dubious of risky
diplomacy. This would be as hard to do for North Korea in the future as it is now for Iran. Leaders who
accept this challenge can expect very little help from intelligence agencies.
BRITISH SPIES SNOOPED ON YOUTUBE AND FACEBOOK
http://investigations.nbcnews.com/_news/2014/01/27/22469304-snowden-docs-reveal-british-spies-
snooped-on-youtube-and-facebook?lite
NBC News / by Richard Esposito, Matthew Cole, Mark Schone and Glenn Greenwald
Stringer: Kees Kalkman / VDAmok / Utrecht NL / kees@amok.antenna.nl
Jan 28 2014 Jan 27. The British government can tap into the cables carrying the worlds web traffic
at will and spy on what people are doing on some of the worlds most popular social media sites,
including YouTube, all without the knowledge or consent of the companies.
Documents taken from the National Security Agency by Edward Snowden and obtained by NBC News
detail how British cyber spies demonstrated a pilot program to their U.S. partners in 2012 in which they
were able to monitor YouTube in real time and collect addresses from the billions of videos watched
daily, as well as some user information, for analysis. At the time the documents were printed, they
were also able to spy on Facebook and Twitter.
Called Psychology A New Kind of SIGDEV" (Signals Development), the presentation includes a
section that spells out Broad real-time monitoring of online activity of YouTube videos, URLs liked
on Facebook, and Blogspot/Blogger visits. The monitoring program is called Squeaky Dolphin.
Experts told NBC News the documents show the British had to have been either physically able to tap
the cables carrying the worlds web traffic or able to use a third party to gain physical access to the
massive stream of data, and would be able to extract some key data about specific users as well.
Representatives of Facebook and Google, which owns YouTube, said they hadnt given the British
government permission to access data and were unaware the collection had occurred. A source close
to Google who asked not to be identified when discussing company policy said the company was
shocked to learn the U.K. could have been grabbing its data.
In connection with this report, NBC is publishing documents that Edward Snowden took from the NSA
before fleeing the U.S., which can be viewed by clicking here. The documents are being published
with minimal redactions.
One of the people who helped prepare the demonstration was an official from the British signals
intelligence agency Government Communications Headquarters (GCHQ) who worked for a division of
the agency called GTE, or Global Telecoms Exploitation. GTE has already been shown in other
documents released by Snowden to be tapping fiber optic cables around the world.
In 2013, the Guardian reported that Snowden documents showed GCHQ was able to tap fiber optic
cables and store huge amounts of data for 30 days, and that the government was placing intercept
probes on transatlantic cables when they landed on British territory. Germanys Sueddeutsche Zeitung
reported that another Snowden document indicated major telecom firms, including BT, Verizon and
Vodafone, were cooperating.
The British cyber spies sometimes share their intercepted raw data and their analyses with their
American counterparts. In October, the Washington Post revealed that a Snowden document dated
Jan. 9, 2013, described a joint NSA/GCHQ program called MUSCULAR, in which the U.S. and British
agencies shared intercepted data from fiber optic cables and copied entire data flows from Yahoo
and Google.
According to a source knowledgeable about the agencys operations, the NSA does analysis of social
media similar to that in the GCHQ demonstration.
National security experts say that both the U.S. and British operations are within the scope of their
respective national laws. When the Washington Post reported on the MUSCULAR program, the NSA
said in a statement that it is focused on discovering and developing intelligence about valid foreign
intelligence targets only and that it uses Attorney General-approved processes to protect the privacy
of U.S. persons.
But privacy experts and former government officials say the lack of disclosure by the intelligence
agencies inspires public fear that rights of privacy, free speech and dissent have been infringed.
Governments have no business knowing which YouTube videos everyone in the world is watching,
said Chris Soghoian, chief technologist for the ACLU. Its one thing to spy on a particular person who
has done something to warrant a government investigation but governments have no business
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 9
monitoring the Facebook likes or YouTube views of hundreds of millions of people.
It might also have a chilling effect on companies like Google. Jason Healey, former White House cyber
czar under George W. Bush, says U.S. and British intelligence encroachment on the internet is a
threat to everyone, including social media companies.
We want our security services to be out there and keeping us safe," said Healey, "but we can also
look for balance, we can look for limits, especially if were putting at risk this most transformative
technology since Gutenberg.
According to the documents obtained by NBC News, intelligence officers from GCHQ gave a
demonstration in August 2012 that spelled out to their U.S. colleagues how the agencys Squeaky
Dolphin program could collect, analyze and utilize YouTube, Facebook and Blogger data in specific
situations in real time.
The demonstration showed that by using tools including a version of commercially available analytic
software called Splunk, GCHQ could extract information from the torrent of electronic data that moves
across fiber optic cable and display it graphically on a computer dashboard. The presentation showed
that analysts could determine which videos were popular among residents of specific cities, but did not
provide information on individual social media users.
The presenters gave an example of their real-time monitoring capability, showing the Americans how
they pulled trend information from YouTube, Facebook and blog posts on Feb. 13, 2012, in advance of
an anti-government protest in Bahrain the following day.
More than a year prior to the demonstration, in a 2012 annual report, members of Parliament had
complained that the U.K.s intelligence agencies had missed the warning signs of the uprisings that
became the Arab Spring of 2011, and had expressed the wish to improve global intelligence
collection.
During the presentation, according to a note on the documents, the presenters noted for their
audience that Squeaky Dolphin was not intended for spying on specific people and their internet
behavior. The note reads, Not interested in individuals just broad trends!
But cyber-security experts told NBC News that once the information has been collected, intelligence
agencies have the ability to extract some user information as well. In 2010, according to other
Snowden documents obtained by NBC News, GCHQ exploited unencrypted data from Twitter to
identify specific users around the world and target them with propaganda.
The experts also said that the only way that GCHQ would be able to do real-time analysis of trends
would be to tap the cables directly and store the data or use a third party, like a private company, to
extract and collect the raw data. As much as 11 percent of global internet bandwidth travels through
U.K. internet exchanges, according to Bill Woodcock, president of PCH, a non-profit internet
organization that tracks and measures and documents fiber infrastructure around the world.
In the case of the YouTube video information, the surveillance of the unencrypted material was done
not only without the knowledge of the public but without the knowledge or permission of Google, the
U.S. company that owns the video sharing service.
"We have long been concerned about the possibility of this kind of snooping, which is why we have
continued to extend encryption across more and more Google services and links, said a Google
spokesperson. We do not provide any government, including the UK government, with access to our
systems. These allegations underscore the urgent need for reform of government surveillance
practices."
A source close to Google added that Google was shocked because the company had pushed back
against British legislation that would have required Google to store its metadata and other information
for U.K. government use. The legislation, introduced by Home Secretary Theresa May in 2012, was
publicly repudiated by Deputy Prime Minister Nick Clegg in 2013 and has never become law. May
hopes to reintroduce a modified version this spring.
Its extremely surprising, said the source, that while they were pushing for the data via the law, they
might have simultaneously been using their capability to grab it anyway.
Encryption would prevent simple collection of the data by an outside entity like the government.
Google has not yet encrypted YouTube or Blogger. Facebook and Twitter have now fully encrypted all
their data.
Facebook confirmed to NBC News that while its like data was unencrypted, the company never gave
it to the U.K. government and was unaware that GCHQ might have been siphoning the data. The
company assumes the data was taken somewhere outside its networks and data centers.
Network security is an important part of the way we protect user information, said Facebook
spokesman Jay Nancarrow, which is why we finished moving our site traffic to HTTPS by default last
year, implemented Perfect Forward Secrecy, and continue to strengthen all aspects of our network.
GCHQ would not confirm or deny the existence of the Squeaky Dolphin program or anything else
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 10
connected with this report. The agency declined to answer questions about the scope of its data
collection or how it accessed the datastream.
In a statement, a GCHQ spokesperson emphasized that that the agency operated within the law.
All of GCHQ's work is carried out in accordance with a strict legal and policy framework, said the
statement, which ensure[s] that our activities are authorized, necessary and proportionate, and that
there is rigorous oversight, including from the Secretary of State, the Interception and Intelligence
Services Commissioners and the Parliamentary Intelligence and Security Committee. All of our
operational processes rigorously support this position.
A spokesperson for the NSA said in a statement that the U.S. agency is not interested in the
communications of people who are not valid foreign intelligence targets.
Any implication that NSA's foreign intelligence collection is focused on the social media
communications of everyday Americans is not true, said the statement. We collect only those
communications that we are authorized by law to collect for valid foreign intelligence and
counterintelligence purposes regardless of the technical means used by the targets. Because some
data of U.S. persons may at times be incidentally collected in NSAs lawful foreign intelligence
mission, privacy protections for U.S. persons exist across the entire process concerning the use,
handling, retention, and dissemination of data.
The spokesperson also said that working with foreign intelligence services strengthens the national
security of both nations, but that NSA cant use those relationships to circumvent U.S. legal
restrictions.
Both U.S. and British officials assert that while their passive collection of electronic communications
might have great breadth, the actual use of the data collected is very targeted, and is dictated by
specific missions. Sources familiar with GCHQ operations state firmly that this is the case in each of
the agencys operations.
Journalist Glenn Greenwald was formerly a columnist at Salon and the Guardian. In late 2012 he was
contacted by NSA contractor Edward Snowden, who later provided him with thousands of sensitive
documents, and he was the first to report on Snowdens documents in June 2013 while on the staff of
the Guardian. Greenwald has since reported on the documents with multiple media outlets around the
world, and has won several journalism awards for his NSA reporting both in the U.S. and abroad. He is
now helping launch, and will write for, a new, non-profit media outlet known as First Look Media that
will encourage, support and empower independent, adversarial journalists.
ANGRY BIRDS, NSA AND GCHQ
Angry Birds and 'leaky' phone apps targeted by NSA and GCHQ for user data
US and UK spy agencies piggyback on commercial data
Details can include age, location and sexual orientation
Documents also reveal targeted tools against individual phones
www.theguardian.com/world/2014/jan/27/nsa-gchq-smartphone-app-angry-birds-personal-data?CMP=twt_gu
The Guardian / by James Ball
Stringer: Kees Kalkman / VDAmok / Utrecht NL / kees@amok.antenna.nl
Jan 28 2014 Jan 28. GCHQ documents use Angry Birds reportedly downloaded more than 1.7bn
times as a case study for app data collection.
The National Security Agency and its UK counterpart GCHQ have been developing capabilities to take
advantage of "leaky" smartphone apps, such as the wildly popular Angry Birds game, that transmit
users' private information across the internet, according to top secret documents.
The data pouring onto communication networks from the new generation of iPhone and Android apps
ranges from phone model and screen size to personal details such as age, gender and location. Some
apps, the documents state, can share users' most sensitive information such as sexual orientation
and one app recorded in the material even sends specific sexual preferences such as whether or not
the user may be a swinger.
Many smartphone owners will be unaware of the full extent this information is being shared across the
internet, and even the most sophisticated would be unlikely to realise that all of it is available for the
spy agencies to collect.
Dozens of classified documents, provided to the Guardian by whistleblower Edward Snowden and
reported in partnership with the New York Times and ProPublica, detail the NSA and GCHQ efforts to
piggyback on this commercial data collection for their own purposes.
Scooping up information the apps are sending about their users allows the agencies to collect large
quantities of mobile phone data from their existing mass surveillance tools such as cable taps, or
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 11
from international mobile networks rather than solely from hacking into individual mobile handsets.
Exploiting phone information and location is a high-priority effort for the intelligence agencies, as
terrorists and other intelligence targets make substantial use of phones in planning and carrying out
their activities, for example by using phones as triggering devices in conflict zones. The NSA has
cumulatively spent more than $1bn in its phone targeting efforts.
The disclosures also reveal how much the shift towards smartphone browsing could benefit spy
agencies' collection efforts.
One slide from a May 2010 NSA presentation on getting data from smartphones breathlessly titled
"Golden Nugget!" sets out the agency's "perfect scenario": "Target uploading photo to a social media
site taken with a mobile device. What can we get?"
The question is answered in the notes to the slide: from that event alone, the agency said it could
obtain a "possible image", email selector, phone, buddy lists, and "a host of other social working data
as well as location".
In practice, most major social media sites, such as Facebook and Twitter, strip photos of identifying
location metadata (known as EXIF data) before publication. However, depending on when this is done
during upload, such data may still, briefly, be available for collection by the agencies as it travels
across the networks.
Depending on what profile information a user had supplied, the documents suggested, the agency
would be able to collect almost every key detail of a user's life: including home country, current
location (through geolocation), age, gender, zip code, marital status options included "single",
"married", "divorced", "swinger" and more income, ethnicity, sexual orientation, education level, and
number of children.
The agencies also made use of their mobile interception capabilities to collect location information in
bulk, from Google and other mapping apps. One basic effort by GCHQ and the NSA was to build a
database geolocating every mobile phone mast in the world meaning that just by taking tower ID
from a handset, location information could be gleaned.
A more sophisticated effort, though, relied on intercepting Google Maps queries made on smartpho-
nes, and using them to collect large volumes of location information.
So successful was this effort that one 2008 document noted that "[i]t effectively means that anyone
using Google Maps on a smartphone is working in support of a GCHQ system."
The information generated by each app is chosen by its developers, or by the company that delivers
an app's adverts. The documents do not detail whether the agencies actually collect the potentially
sensitive details some apps are capable of storing or transmitting, but any such information would
likely qualify as content, rather than metadata.
Data collected from smartphone apps is subject to the same laws and minimisation procedures as all
other NSA activity procedures that the US president, Barack Obama, suggested may be subject to
reform in a speech 10 days ago. But the president focused largely on the NSA's collection of the
metadata from US phone calls and made no mention in his address of the large amounts of data the
agency collects from smartphone apps.
The latest disclosures could also add to mounting public concern about how the technology sector
collects and uses information, especially for those outside the US, who enjoy fewer privacy protections
than Americans. A January poll for the Washington Post showed 69% of US adults were already
concerned about how tech companies such as Google used and stored their information.
The documents do not make it clear how much of the information that can be taken from apps is
routinely collected, stored or searched, nor how many users may be affected. The NSA says it does
not target Americans and its capabilities are deployed only against "valid foreign intelligence targets".
The documents do set out in great detail exactly how much information can be collected from widely
popular apps. One document held on GCHQ's internal Wikipedia-style guide for staff details what can
be collected from different apps. Though it uses Android apps for most of its examples, it suggests
much of the same data could be taken from equivalent apps on iPhone or other platforms.
The GCHQ documents set out examples of what information can be extracted from different ad
platforms, using perhaps the most popular mobile phone game of all time, Angry Birds which has
reportedly been downloaded more than 1.7bn times as a case study.
From some app platforms, relatively limited, but identifying, information such as exact handset model,
the unique ID of the handset, software version, and similar details are all that are transmitted.
Other apps choose to transmit much more data, meaning the agency could potentially net far more.
One mobile ad platform, Millennial Media, appeared to offer particularly rich information. Millennial
Media's website states it has partnered with Rovio on a special edition of Angry Birds; with Farmville
maker Zynga; with Call of Duty developer Activision, and many other major franchises.
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 12
Rovio, the maker of Angry Birds, said it had no knowledge of any NSA or GCHQ programs looking to
extract data from its apps users.
"Rovio doesn't have any previous knowledge of this matter, and have not been aware of such activity
in 3rd party advertising networks," said Saara Bergstrm, Rovio's VP of marketing and
communications. "Nor do we have any involvement with the organizations you mentioned [NSA and
GCHQ]."
Millennial Media did not respond to a request for comment.
In December, the Washington Post reported on how the NSA could make use of advertising tracking
files generated through normal internet browsing known as cookies from Google and others to get
information on potential targets.
However, the richer personal data available to many apps, coupled with real-time geolocation, and the
uniquely identifying handset information many apps transmit give the agencies a far richer data source
than conventional web-tracking cookies.
Almost every major website uses cookies to serve targeted advertising and content, as well as
streamline the experience for the user, for example by managing logins. One GCHQ document from
2010 notes that cookie data which generally qualifies as metadata has become just as important to
the spies. In fact, the agencies were sweeping it up in such high volumes that their were struggling to
store it.
"They are gathered in bulk, and are currently our single largest type of events," the document stated.
The ability to obtain targeted intelligence by hacking individual handsets has been well documented,
both through several years of hacker conferences and previous NSA disclosures in Der Spiegel, and
both the NSA and GCHQ have extensive tools ready to deploy against iPhone, Android and other
phone platforms.
GCHQ's targeted tools against individual smartphones are named after characters in the TV series
The Smurfs. An ability to make the phone's microphone 'hot', to listen in to conversations, is named
"Nosey Smurf". High-precision geolocation is called "Tracker Smurf", power management an ability
to stealthily activate an a phone that is apparently turned off is "Dreamy Smurf", while the spyware's
self-hiding capabilities are codenamed "Paranoid Smurf".
Those capability names are set out in a much broader 2010 presentation that sheds light on spy
agencies' aspirations for mobile phone interception, and that less-documented mass-collection
abilities.
The cover sheet of the document sets out the team's aspirations:
mobile theme 1
The cover slide for a May 2010 GCHQ presentation on mobile phone data interception.
Another slide details weak spots in where data flows from mobile phone network providers to the wider
internet, where the agency attempts to intercept communications. These are locations either within a
particular network, or international roaming exchanges (known as GRXs), where data from travellers
roaming outside their home country is routed.
mobile briefing 2
While GCHQ uses Android apps for most of its examples, it suggests much of the same data could be
taken from iPhone apps.
mobile briefing 3
GCHQ's targeted tools against individual smartphones are named after characters in the TV series
The Smurfs.
These are particularly useful to the agency as data is often only weakly encrypted on such networks,
and includes extra information such as handset ID or mobile number much stronger target identifiers
than usual IP addresses or similar information left behind when PCs and laptops browse the internet.
The NSA said its phone interception techniques are only used against valid targets, and are subject to
stringent legal safeguards.
"The communications of people who are not valid foreign intelligence targets are not of interest to the
National Security Agency," said a spokeswoman in a statement.
"Any implication that NSA's foreign intelligence collection is focused on the smartphone or social
media communications of everyday Americans is not true. Moreover, NSA does not profile everyday
Americans as it carries out its foreign intelligence mission. We collect only those communications that
we are authorized by law to collect for valid foreign intelligence and counterintelligence purposes
regardless of the technical means used by the targets.
"Because some data of US persons may at times be incidentally collected in NSA's lawful foreign
intelligence mission, privacy protections for US persons exist across the entire process concerning the
use, handling, retention, and dissemination of data. In addition, NSA actively works to remove
extraneous data, to include that of innocent foreign citizens, as early as possible in the process.
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 13
"Continuous and selective publication of specific techniques and tools lawfully used by NSA to pursue
legitimate foreign intelligence targets is detrimental to the security of the United States and our allies
and places at risk those we are sworn to protect."
The NSA declined to respond to a series of queries on how routinely capabilities against apps were
deployed, or on the specific minimisation procedures used to prevent US citizens' information being
stored through such measures.
GCHQ declined to comment on any of its specific programs, but stressed all of its activities were
proportional and complied with UK law.
"It is a longstanding policy that we do not comment on intelligence matters," said a spokesman.
"Furthermore, all of GCHQ's work is carried out in accordance with a strict legal and policy framework
that ensures that our activities are authorised, necessary and proportionate, and that there is rigorous
oversight, including from the Secretary of State, the Interception and Intelligence Services
Commissioners and the Parliamentary Intelligence and Security Committee. All our operational
processes rigorously support this position."
A separate disclosure on Wednesday, published by Glenn Greenwald and NBC News, gave examples
of how GCHQ was making use of its cable-tapping capabilities to monitor YouTube and social media
traffic in real-time.
GCHQs cable-tapping and internet buffering capabilities , codenamed Tempora, were disclosed by
the Guardian in June, but the new documents published by NBC from a GCHQ presentation titled
Psychology: A New Kind of SIGDEV" set out a program codenamed Squeaky Dolphin which gave the
British spies broad real-time monitoring of YouTube Video Views, URLs Liked on Facebook and
Blogspot/Blogger Visits.
A further slide noted that passive a term for large-scale surveillance through cable intercepts give
the agency scalability.
The means of interception mean GCHQ and NSA could obtain data without any knowledge or co-
operation from the technology companies. Spokespeople for the NSA and GCHQ told NBC all
programs were carried out in accordance with US and UK law.
TURKISH INTELLIGENCE SERVICE TRUCKS REVEAL SECRETS
www.al-monitor.com/pulse/originals/2014/01/turkish-intelligence-trucks-smuggle-syria.html?ut-
m_source=Al-Monitor+Newsletter+%5BEnglish%5D&utm_campaign=eeea8d1097-January_27_20-
141_26_2014&utm_medium=email&utm_term=0_28264b27a0-eeea8d1097-93067721
Al-Monitor / by Fehim Tatekin
Stringer: Kees Kalkman / VDAmok / Utrecht NL / kees@amok.antenna.nl
Jan 28 2014 Jan 20. Turkeys National Intelligence Organization (MIT), which has bloomed as a
parallel Foreign Ministry under Justice and Development Party (AKP) rule after years of keeping a low
public profile, was again caught transporting weapons to Syrian opposition forces. After saving a
suspicious truck from the prosecutors and gendarmerie on Jan. 1, when the government called it a
state secret, MIT this time hit the headlines with seven semis reported to be laden with weapons.
Security forces were able to search some of the trucks in an operation on Jan. 19 that was launched
after a tip was received and the government was slow in intervening. Nevertheless, the local governor
did not allow a detailed search on state secret grounds and the trucks were released.
According to information Al-Monitor obtained from security sources, on Jan. 19 at 7:15 a.m., the
prosecutor of Adana Anti-Terror Court instructed the Adana Provincial Gendarmerie Command to stop
and search three semis.
Around noon, a security detail of 200 personnel stopped the semis with plates 06 DY 0393, 06 EY
2115 and 06 FC 9193 and an Audi A3 car accompanying them at Adana Sirkeli Motorway entry point.
Eight drivers and other personnel in the trucks were detained. It was also discovered that there were
two MIT officials in the Audi escort vehicle.
After explosives-detecting dogs gave appropriate signals, the prosecutor allowed steel containers in
the trucks to be opened. In six metal crates, concealed among medical supplies, were mortar shells,
rockets and various other ammunition. While the trucks were being moved to nearby Seyhan Town
Gendarmerie Command for a detailed search, the trucks were blocked by MIT personnel from their
Adana regional office. At that point, the governor, Adana Huseyin Avni Cos, the provincial police chief
and the MIT regional director arrived at the scene accompanied by 200 policemen. Cos tried for one
hour to persuade the prosecutor not to go ahead with the search but couldnt. Then Cos wrote to the
Ceyhan district governor and the Adana Provincial Gendarmerie Command, warning that the MIT was
attached directly to the prime minister and searching MIT vehicles without the permission of the prime
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 14
ministers office would be an offense. The vehicles then were released under the governors
instructions and continued on their way toward Syria.
Routine duty
According to information provided to Al-Monitor when the first three suspicious trucks were stopped,
MIT personnel tried to save the other four trucks from searches but they, too, were stopped by the
gendarmerie.
While the trucks once again were disappearing, the head prosecutor of the Anti-Terror Court said they
could not give a list of items found because the investigation was confidential.
At the end of the day, the governors office of Adana issued the following statement: It was
understood that in the three vehicles moving in the Adana-Ceyhan direction, there were MIT personnel
doing their routine duties. After appropriate checks, these personnel left the location to continue with
their routine duties. The term routine duties used by the governors office only added to accusations
that the MIT has been involved in field operations since the beginning of the Syrian crisis.
Immunity for MIT
The new truck incident rekindled the debate on immunity of the MIT. Huseyin Celik, the deputy
chairman of Erdogan's AKP, issued a public reprimand, saying, This is a truck of the MIT. What is
inside it doesnt concern anyone. Who are these prosecutors working for? Stopping MIT trucks means
not knowing your limits. The prosecutors who make such mistakes will be held accountable. Celik,
like Cos, said no MIT activity can be questioned without the prime ministers permission.
According to legal experts, the rule that the prime ministers approval is needed to investigate the MIT
doesnt accord the organization a blanket immunity. Experts say that a suspicious vehicle can be
searched if there is likelihood of a crime, to collect the evidence and then a request for permission to
investigate the MIT personnel is made. If this is not done, then the MIT is given liberty to commit
crimes.
On Nov. 7, also in Adana, a truck owned by a private company was found to contain 933 rocket
warheads after a tip was received about narcotics smuggling.
UK LOSES ITS LIBERTIES
The police get the tools they want, Britain loses the liberties it holds dear
Crime rates are down, yet the police create a fantasy world of chaos demanding ever greater
control over a free people
http://www.theguardian.com/commentisfree/2014/jan/24/police-tools-liberties-britain-crime-rates
The Guardian / by Henry Porter
Stringer: Kees Kalkman / VDAmok / Utrecht NL / kees@amok.antenna.nl
Jan 28 2914 Jan 24. There are two striking images of modern Britain in this week's news. The first
is the story that crime in Britain is at a 32-year low, which confirms evidence in statistical trends that,
like most western countries, we are becoming a more orderly and law-abiding society.
The second is provided by the police, which, while suffering a thoroughly deserved collapse in their
own reputation, seeks to draw a picture of chaos and misrule that demands ever harsher and more
invasive policing techniques. Five years after the financial crash, the police are making the case for
deploying water cannon to deal with expected "austerity riots", when it is blindingly obvious that Britain
has passed through a very difficult period without widespread disorder (the riots that began in
Tottenham two years ago were mostly a failure of policing, not a response to economic conditions)
and, moreover, the economy and employment have both picked up.
But the far more worrying development is the unscrutinised rollout of the police automated
numberplate recognition system (ANPR) for tracking vehicles, which, according to Nick Hopkins'
report, currently stores 17bn images in its archive and is set to increase its capacity by 2018 to read
and store 50-75 million separate vehicle sightings a day.
This is a very powerful surveillance system and the important thing to remember is that the decision to
cover Britain's motorways and town centres with cameras that track the movements of innocent
citizens is that it was never debated by parliament.
The system was cooked up between "twinned" committees from the Home Office and the Association
of Chief Police Officers, which, incidentally, was a private company and immune from FOI requests,
then deployed with constabularies footing the maintenance bill. Not one minute of parliamentary
debate preceded the installation of the system; politicians of all parties went along with the police
assertion that this was a necessary and proportionate tool of modern policing.
And like all new tools given to the police, it has been abused, with officers using the system to track
partners, to conduct minute-by-minute surveillance on the movement of legitimate protestors and to
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 15
meet targets and raise revenue from minor motoring offences. There are urgent questions about links
to other databases and which bodies have access to this enormous store of information, but a much
greater worry exists about the state's vast surveillance dragnet, which we know now has access to the
movement, communications and personal details of everyone in Britain.
Julian Blazeby, the assistant chief constable for Staffordshire and lead on ANPR for the Association of
Chief Police Officers (Acpo), attempts to soothe worries about abuse and transparency by saying: "It is
always a challenge for us, balancing the rights of individuals with preventing and detecting crime,
however we want to be as transparent as possible, and perhaps in the past we have not been as open
as we could have been." But it doesn't appear that neither Blazeby, nor any other member of Acpo,
gives the slightest consideration to the liberty of innocent citizens in an increasingly law-abiding
country.
The actual trends evident in British society of course have no influence on the sponsors of the great
surveillance project, for this is simply a matter of the state and its agencies gaining greater degrees of
unfettered control over a free people. It is possible to exaggerate the threat, but we can now
legitimately claim that through our communications and movements each one of us has been virtually
tagged by the state. A handful of politicians have raised concerns over the years, but the truth is that
while taxpayers continue to fork out tens of millions for systems that are utterly out of proportion to the
problems the police and intelligence agencies face, the issues about liberty and oversight find no
mainstream political expression. The police get what they want, whether it's water cannon, Taser guns
or the extended ANPR system, and that is because we do not remind them that they are our servants,
not our masters.
We can be sure of one thing this system will be abused and, in times of political upheaval, we can
expect it to be used to defend the state against legitimate political dissent. Imagine its use during the
miners' strike; consider how it is currently used to track climate-change protesters.
But the main point is surely the contrast between the increasing orderliness of society and the
examples of endemic corruption, destruction of evidence, misuse of firearms, punitive attitudes to
innocent members of the public, racism, excessive force, the misuse of undercover policing operations
and deaths in custody that litter the record of British police. While we become more law-abiding, police
standards decline. Instead of addressing their own problems they create a fantasy world of chaos and
lawlessness that requires more and more control and surveillance.
Where are the politicians who will guard our liberties and ensure the police meet our standards of
lawfulness?
ASSAD ACCUSED OF BOOSTING AL-QAEDA WITH SECRET OIL DEALS
Western intelligence suggests Bashar al-Assad collaborating with jihadists to persuade West
the uprising is terrorist-led
www.telegraph.co.uk/news/worldnews/middleeast/syria/10585391/Syrias-Assad-accused-of-boosting-al-Qaeda-with-secret-oil-deals.html
The Telegraph / by Ruth Sherlock and Richard Spencer
Stringer: Kees Kalkman / VDAmok / Utrecht NL / kees@amok.antenna.nl
Jan 28 2014 Jan 20. The Syrian regime of President Bashar al-Assad has funded and co-operated
with al-Qaeda in a complex double game even as the terrorists fight Damascus, according to new
allegations by Western intelligence agencies, rebels and al-Qaeda defectors.
Jabhat al-Nusra, and the even more extreme Islamic State of Iraq and al-Shams (ISIS), the two al-
Qaeda affiliates operating in Syria, have both been financed by selling oil and gas from wells under
their control to and through the regime, intelligence sources have told The Daily Telegraph.
Rebels and defectors say the regime also deliberately released militant prisoners to strengthen jihadist
ranks at the expense of moderate rebel forces. The aim was to persuade the West that the uprising
was sponsored by Islamist militants including al-Qaeda as a way of stopping Western support for it.
The allegations by Western intelligence sources, who spoke on condition of anonymity, are in part a
public response to demands by Assad that the focus of peace talks due to begin in Switzerland
tomorrow be switched from replacing his government to co-operating against al-Qaeda in the war on
terrorism.
Assads vow to strike terrorism with an iron fist is nothing more than bare-faced hypocrisy, an
intelligence source said. At the same time as peddling a triumphant narrative about the fight against
terrorism, his regime has made deals to serve its own interests and ensure its survival.
Intelligence gathered by Western secret services suggested the regime began collaborating actively
with these groups again in the spring of 2013. When Jabhat al-Nusra seized control of Syrias most
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 16
lucrative oil fields in the eastern province of Deir al-Zour, it began funding its operations in Syria by
selling crude oil, with sums raised in the millions of dollars.
The regime is paying al-Nusra to protect oil and gas pipelines under al-Nusras control in the north
and east of the country, and is also allowing the transport of oil to regime-held areas, the source said.
We are also now starting to see evidence of oil and gas facilities under ISIS control.
The source accepted that the regime and the al-Qaeda affiliates were still hostile to each other and the
relationship was opportunistic, but added that the deals confirmed that despite Assads finger-
pointing his regime was to blame for the rise of al-Qaeda in Syria.
Western diplomats were furious at recent claims that delegations of officials led by a retired MI6 officer
had visited Damascus to re-open contact with the Assad regime. There is no doubt that the West is
alarmed at the rise of al-Qaeda within the rebel ranks, which played a major role in decisions by
Washington and London to back off from sending arms to the opposition.
But the fury is also an indication that they suspect they have been outmanoeuvred by Assad, who has
during his rule alternated between waging war on Islamist militants and working with them.
After September 11, he co-operated with the United States rendition programme for militant suspects;
after the invasion of Iraq, he helped al-Qaeda to establish itself in Western Iraq as part of an axis of
resistance to the West; then when the group turned violently against the Iraqi Shias who were backed
by Assads key ally, Iran, he began to arrest them again.
As the uprising against his rule began, Assad switched again, releasing al-Qaeda prisoners. It
happened as part of an amnesty, said one Syrian activist who was released from Sednaya prison near
Damascus at the same time.
There was no explanation for the release of the jihadis, the activist, called Mazen, said. I saw some
of them being paraded on Syrian state television, accused of being Jabhat al-Nusra and planting car
bombs. This was impossible, as they had been in prison with me at the time the regime said the
bombs were planted. He was using them to promote his argument that the revolution was made of
extremists.
Other activists and former Sednaya inmates corroborated his account, and analysts have identified a
number of former prisoners now at the head of militant groups, including Jabhat al-Nusra, ISIS and a
third group, Ahrar al-Sham, which fought alongside Jabhat al-Nusra but has now turned against ISIS.
One former inmate said he had been in prison with Abu Ali who is now the head of the ISIS Sharia
court in the north-eastern al-Qaeda-run city of Raqqa. Another said he knew leaders in Raqqa and
Aleppo who were prisoners in Sednaya until early 2012.
These men then spearheaded the gradual takeover of the revolution from secular activists, defected
army officers and more moderate Islamist rebels.
Syrian intelligence has historically had close connections with extremist groups. In an interview with
The Daily Telegraph after he defected, Nawaf al-Fares, a Syrian security chief, told how he was part of
an operation to smuggle jihadist volunteers into Iraq from Syria after the 2003 invasion.
Aron Lund, editor of a website, Syria in Crisis, used by the Carnegie Endowment to monitor the war,
said: The regime has done a good job in trying to turn the revolution Islamist. The releases from
Sednaya prison are a good example of this. The regime claims that it released the prisoners because
Assad had shortened their sentences as part of a general amnesty. But it seems to have gone beyond
that. There are no random acts of kindness from this regime.
Rebels both inside and outside ISIS also say they believe the regime targeted its attacks on non-
militant groups, leaving ISIS alone. We were confident that the regime would not bomb us, an ISIS
defector, who called himself Murad, said. We always slept soundly in our bases.
GOOGLE CALLS FOR NEW NSA REFORMS
http://www.bbc.co.uk/news/technology-25910694?print=true
BBC News / by Adam Blenford
Source: Infowarrior / https://attrition.org/mailman/listinfo/infowarrior
Jan 27 2014 Jan 27. Moves by US President Barack Obama to rein in spies at the National Security
Agency do not go far enough, a senior figure at Google has told the BBC.
David Drummond, the tech giant's chief legal officer, said the US needed to change its approach to
intelligence to restore trust in the internet.
His comments are some of the first by a senior tech figure since a speech by the US president earlier
this month.
They come as ex-NSA contractor Edward Snowden gave his first TV interview.
Mr Snowden, who has been in exile in Russia since leaking the information that lifted the lid on the
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 17
scale of US and UK intelligence programmes, told Germany's public broadcaster ARD that the NSA
practised "industrial espionage".
He said the agency would spy on big German companies that competed with US firms.
Mr Snowden, 30, also said he believed that US officials wanted to kill him.
Innovation concern
Google's Mr Drummond described Mr Obama's high-profile speech on intelligence, delivered on 17
January at the Department of Justice in Washington, as a "positive step".
But he said the president's proposals - which mainly focused on limiting the mass collection of phone
call information, or metadata - were not enough.
"Let me be clear about it, in general they fall short of where any of the speech and the proposal and
the speech fell short of where we'd like to see this go," Mr Drummond said.
"But I think it was a first step for the administration, it's not the final word on where this will go,
hopefully, we intend to be very engaged in that debate."
Almost eight months of leaks by Mr Snowden have focused attention on the large-scale collection of
phone call, SMS and internet data by the NSA and by GCHQ in the UK.
The leaks have worried tech companies such as Google, Facebook and Microsoft, who are concerned
that public trust in their services has been undermined by the US government.
"People really need to trust the internet and to trust internet companies and that really underpins a lot
of the innovation," Mr Drummond said.
"We've been concerned about the long-term user trust in the internet and what that means for
acceptance for new innovations," he added.
"If you build something great but people are worried or won't try it because they're afraid, then it's not
going to work."
Separately, the politician responsible for piloting a new European data protection law described Mr
Snowden's leaks as a "wake-up call" to the world that had undermined trust between Europe and the
US.
But EU Justice Commissioner Viviane Reding told the BBC that after two years of negotiations with
the US over European efforts to update legal safeguards for EU citizens and companies exchanging
data with the US, politicians in Washington were now starting to hear her message.
"I have been speaking with the Attorney General, Eric Holder, and we are working to see what
regulations in the United States can be changed so there is reciprocity and we can finalise this much-
needed regulation on both sides of the Atlantic for exchanging data," Ms Reding said.
She said Mr Obama would meet European Commission head Jose Manuel Barroso on 26 March,
adding that she expected concrete achievements by then.
"Our American partners always told us that data protection was something dear to the heart of the
Europeans but nobody cares in the United States. I think that recently people in the US also care -
members of Congress, senators as well."
Snowden: 'I sleep well'
Mr Snowden's interview with German broadcaster ARD was his first on-camera interview since
revealing himself last June as the source of the NSA leaks.
Since being offered temporary asylum in Russia, Mr Snowden has given just one major interview, to
the Washington Post shortly before Christmas. He has also answered email questions submitted to
him by some journalists.
Last week he answered questions on a website called Free Snowden.
ARD said they had carried out a six-hour interview that was filmed in a Moscow hotel suite, airing 40
minutes of the footage.
He suggested the NSA spied on companies of interest to US national interests, as well as its stated
core mission of national security.
"If there's information at Siemens that's beneficial to US national interests - even if it doesn't have
anything to do with national security - then they'll take that information nevertheless," Mr Snowden
said.
He also discussed reports of threats to his life, describing them as "significant" but saying: "I sleep
very well."
"These people, and they are government officials, have said they would love to put a bullet in my head
or poison me when I come out of the supermarket and then watch me die in the shower," he said,
referring to anonymous quotes on US website BuzzFeed.
"I'm still alive and don't lose sleep for what I did because it was the right thing to do."
Mr Snowden's leaks caused outrage in Germany when it came to light that Chancellor Angela Merkel's
phone had been bugged.
After the news broke last year, Mrs Merkel accused the US of an unacceptable breach of trust.
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 18
Last week President Obama indicated to Germany's ZDF TV that US bugging of Mrs Merkel's mobile
phone had been a mistake and would not happen again.
The US has charged Mr Snowden with theft of government property, unauthorised communication of
national defence information and wilful communication of classified communications intelligence.
Each of the charges carries a maximum 10-year prison sentence. Earlier this week he said he had "no
chance" of a fair trial in the US and had no plans to return there.
GERMANY EYES SIGINT AIRFRAMES
http://defensenews.va.newsmemory.com
Defense News
Stringer: Martin Broek / Investigative Journalism / Amsterdam / http://broekstukken.blogspot.com
Jan 27 2014 Jan 27. The German military is considering four variants for a new signals intelligence
(SIGINT) aircraft to replace the scrapped Eurohawk UAV project. The Federal Office of Bundeswehr
Equipment, Information Technology and In-Service Support has come up with manned and unmanned
solutions.
These options include an unmanned version in the MALE [medium- altitude, long-endurance] UAV
class; a carrier the size of a business jet; a short-range passenger aircraft to carry the ISIS [Integrated
Signal Intelligence System]; and an existing complete solution without the ISIS system, a Defense
Ministry spokesman said. The chief of staff will decide by the end of the quarter which option comes
into question.
The new ISIS SIGINT system had been developed by Airbus, formerly EADS, for the Eurohawk UAV.
OUT OF BLACKWATER AND INTO CHINA
Erik Prince: The former CIA asset on his latest venture: After being 'blowtorched' by U.S.
politics, he says, this time he's working for Beijing.
http://online.wsj.com/news/articles/SB10001424052702303465004579324650302912522
Wall Street Journal / by David Feith
Stringer: Frank Slijper / Campaign Against Arms Trade / Groningen NL / frank.slijper@hetnet.nl
Jan 26 2014 Jan 24. Erik Prince ex-Navy SEAL, ex-CIA spy, ex-CEO of private-security firm
Blackwater calls himself an "accidental tourist" whose modest business boomed after 9/11,
expanded into Iraq and Afghanistan, and then was "blowtorched by politics." To critics and conspiracy
theorists, he is a mercenary war-profiteer. To admirers, he's a patriot who has repeatedly answered
America's call with bravery and creativity.
Now, sitting in a boardroom above Hong Kong's Victoria Harbour, he explains his newest title,
acquired this month: chairman of Frontier Services Group, an Africa-focused security and logistics
company with intimate ties to China's largest state-owned conglomerate, Citic Group. Beijing has
titanic ambitions to tap Africa's resourcesincluding $1 trillion in planned spending on roads, railways
and airports by 2025and Mr. Prince wants in.
With a public listing in Hong Kong, and with Citic as its second-largest shareholder (a 15% stake) and
Citic executives sitting on its board, Frontier Services Group is a long way from Blackwater's CIA ties
and $2 billion in U.S. government contracts. For that, Mr. Prince is relieved.
"I would rather deal with the vagaries of investing in Africa than in figuring out what the hell else
Washington is going to do to the entrepreneur next," says the crew-cut 44-year-old.
Having launched Blackwater in 1997 as a rural North Carolina training facility for U.S. soldiers and
police, Mr. Prince says he "kept saying 'yes' as the demand curve calledColumbine, the USS Cole
and then 9/11." In 100,000 missions in Iraq and Afghanistan, he says, Blackwater contractors never
lost a U.S. official under their protection. But the company gained a trigger-happy reputation,
especially after a September 2007 shootout that left 17 civilians dead in Baghdad's Nisour Square.
At that point, charges Mr. Prince, Blackwater was "completely thrown under the bus by a fickle
customer"the U.S. government, and especially the State Department. He says Washington opted to
"churn up the entire federal bureaucracy" and sic it on Blackwater "like a bunch of rabid dogs."
According to Mr. Prince, IRS auditors told his colleagues that they had "never been under so much
pressure to get someone as to get Erik Prince," and congressional staffers promised, "We're going to
ride you till you're out of business."
Amid several federal prosecutions involving Blackwater employees, most of which fizzled, Mr. Prince
resigned as CEO in 2009 and now feels "absolutely total regret in every way, shape and form for ever
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 19
saying 'yes' " to a State Department contract.
Which brings him to Hong Kong and his new firm. "This is not a patriotic endeavor of ourswe're here
to build a great business and make some money doing it," he says. Asia, and especially China, "has
the appetite to take frontier risk, that expeditionary risk of going to those less-certain, less-normal
markets and figuring out how to make it happen." Mr. Prince says "critics can throw stones all they
want" but he is quick to point out that he has "a lot of experience in dealing in uncertainties in difficult
places," and says "this is a very rational decisionmade, I guess, emotionless."
Mr. Prince aims to provide "end-to-end" services to companies in the "big extractive, big infrastructure
and big energy" industries. Initially focused on building a Pan-African fleet of aircraft, his firm will
expand into barging, trucking and shipping, along with "remote-area construction" as needed for
reliable transport. A companyChinese, Russian, American or otherwisemay have "an extremely
rich hydrocarbon or mining asset," he explains, "but it's worth nothing unless you can get it to where
someone will pay you for it." His investor prospectus notes that with today's transportation
infrastructure, "it costs more to ship a ton of wheat from Mombasa, Kenya to Kampala, Uganda than
from Chicago to Mombasa."
Such high costs also reflect the dangers of piracy and civil conflict, but Mr. Prince plays down his firm's
plans in the security realm. "We are not there to provide military training. We are not there to provide
security per se. Most of that security"say, if an oil pipeline or mining camp needs protection"would
be done by whatever local services are there," including police and private firms. "We don't envision
setting up a whole bunch of local guard services around the continent."
So the former Blackwater chief won't employ guys with guns? Well, he says, "that would be the
exception, certainly not the rule."
He says his attention is on "expeditionary logistics" and "asset management." If a company needs to
build a dam, he muses by way of example, "how do you deliver an extremely high-dollar turbine into a
very remote part of the world? . . . Do you sling it with a helicopter? There's all sorts of interesting
challenges like that that we'll be endeavoring to face."
Mr. Prince won't share any revenue projections, but his prospectus notes that "China is Africa's largest
trading partner," with annual flows of $125 billion. Most estimates put that figure closer to $200 billion,
a meteoric increase from $10 billion in 2000 and $1 billion in 1980. The U.S., which was Africa's top
trade partner until 2009, registered $100 billion in annual African exchange at last count. China-Africa
trade could reach $385 billion by 2015, according to Standard Chartered Bank.
"The U.S. has been fixated on terrorism the last 10 or 15 years," says Mr. Prince, "and American
companies by and large haven't had the appetite for Africa." In 2010 the African Development Bank
found that Chinese firms signed 20 contracts in Africa for every one signed by an American firm. But
does post-9/11 distraction really explain this discrepancy?
A better explanation would begin with China's state-directed investment strategy, which funds opaque
state-owned firms to operate across Africa with little regard for trifles such as financial transparency,
environmental degradation or human rights. When a tyrant like Sudan's Omar al- Bashir can't get
Western financing for a mega-dam across the Nile River, China arrives with an easy loan, some state-
owned firms to build the dam and some others to claim oil or mineral concessions elsewhere in the
country. Beijing's approach has helped boost African economic growthprojected at 6% this year by
the International Monetary Fundbut it has also helped entrench some of the world's most oppressive
governments.
Mr. Prince prefers to look on the bright side. "Developing good investments in Africa is by and large
the best for the people of Africa that have a job, that have electricity, that might have clean water, that
might have those things that we in the West take horribly for granted."
It's Capitalism 101, he argues. "When someone needs copper, or wood or an ag product, and they
invest capital somewhere to make that happen, and people get jobs from that, and that good gets
introduced to the world stage and it gets traded and moved, the whole world benefits."
As for Chinese patronage of presidents-for-life like Sudan's Bashir, Mr. Prince's CEO, Gregg Smith
a former U.S. Marine and Deloitte executiveoffers this observation: "There's thousands of tribal
conflicts in Africa every decade that have nothing to do with anyone from the outside. It has everything
to do with tribal conflicts that have been going on for centuries, and the fact that the economies cause
folks not to have jobs," says Mr. Smith. "It's not about who backs Omar al-Bashir."
Nor, adds Mr. Prince, does China's expanding commercial empire come at the expense of American
interests. "The United States and China are among each other's largest trading partners," he notes,
"and I think countries that trade goods together tend not to trade lead," meaning to shoot at each
other.
This historically questionable reassurance notwithstanding, Mr. Prince certainly isn't complacent about
America's global standing. U.S. policy in Africa, he says, "is just nonexistent. It's about as coherent as
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 20
U.S. Middle East policyincoherent."
Americans, he says, "are at a competitive disadvantage because of their government. . . . It's amazing
how many countries run their embassies as commercial outposts to promote businessmen from their
country. I think the U.S. has forgotten about that one."
At this point in the interview, Mr. Prince begins speaking more sharply, even bitterly, not simply as a
critic of Washington policy but as a man betrayed. Which he was, in 2009, when he was outed publicly
as a CIA asset.
For years while running Blackwater, it turns out, Mr. Prince was also using his personal wealth and
expertise to recruit and deploy a world-wide network of spies tracking al Qaeda operatives in "hard
target" locations where even the CIA couldn't reliably operate. This work remained secret until June
2009, when then-CIA Director Leon Panetta mentioned it in classified testimony to Congress. Within
weeks, leaks hit the front pages.
"The one job I loved more than any other was ripped away from me thanks to gross acts of
professional negligence at the CIA," Mr. Prince wrote in his memoir, "Civilian Warriors," published in
November.
This background comes to mind as Mr. Prince makes the surprising claim that "there's very little
advantage to being an American citizen anymore. They tax you anywhere in the world you are, they
regulate you, and they certainly don't help you, at all."
His advice for Washington: "Stop committing suicide." Lawmakers should "get out of their heads this
idea that they can recklessly spend money that they don't have," he says. "The United States
government is too big in all areas. . . . It's time to make the entire thing a lot smaller." That would
include doing everything from allowing Americans to buy incandescent light bulbs to reining in
domestic surveillance by the National Security Agency.
At no point does Mr. Prince address the irony of making these arguments days after going into
business with a state-owned firm founded as part of Communist China's Ministry of State Security.
"Look," he says, grasping to end our talk on an optimistic note, "America can pull its head out at any
time. That happens at the ballot box. Ballot boxes have consequences still in America." He continues:
"But the American electorate has to actually pay attention, has to turn off the Xbox long enough to pay
attention. Otherwise they're going to continue to elect the government they deserve."
THE FACTS ABOUT THE METADATA 'MENACE'
The NSA program sounds ominous, until you understand what's being collected and how.
www.latimes.com/opinion/commentary/la-oe-riley-nsa-metadata-20140126,0,5561469.story#axzz2rPqniKXe
Los Angeles Times / by Jack Riley [Vice president of the nonpartisan, nonprofit Rand Corp. and
director of the Rand National Security Research Division]
Stringer: Martin Rudner [ret.] / Carleton University / Ottawa / www.carleton.ca/cciss
Jan 25 2014 Jan 26 [!]. President Obama has announced several significant changes to U.S.
counter-terrorism intelligence-collection programs, including an overhaul of the way the National
Security Agency stores and accesses telephone metadata. But what has sometimes been overlooked
in the firestorm created by Edward Snowden's leaks about the program is a clear definition of what
metadata is, and what it is not.
On the eve of the president's announcement, I took part in a daylong session of briefings, discussion
and debate at the NSA. The session, arranged by Carnegie Mellon University professor Kiron Skinner
and Emily Goldman of the Pentagon's Cyber Command, involved a small group of computer scientists
and other researchers and the top leadership of the NSA. The meetings were spectacular for their
clarity and candor.
Much of what Snowden leaked has proved controversial, but probably nothing more so than the
metadata program authorized by the Patriot Act. This program permits the collection and under
limited circumstances analysis of metadata on American phone numbers and thus American
citizens for counter-terrorism purposes.
Metadata from a phone call include information such as the direction (who called whom), length, date
and time. The program does not record the location or the name associated with a call. No one is
listening to the call and no content is recorded. And the metadata are segregated and stored
separately from all the other signals data the NSA collects.
Here's a typical way the metadata are used: An intelligence community client, say the FBI, will send
the NSA an official request for investigation of a certain phone number that it believes might be
associated with suspected terrorists. In order to examine the metadata associated with a phone
number, the NSA has to "make RAS" that is, to show "reasonably articulable suspicion."
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 21
For a phone number that meets the RAS standard, the NSA can examine metadata two hops, or two
call generations, away from the original number. Think of a phone bill that displays calls made and
received. It can look at metadata for every phone number on the original bill, plus the phone numbers
on the bills for the numbers that show up on the bill of the original number. That's two hops. Among
the reforms unveiled by Obama was the reduction in the number of permitted hops from three to two.
What prevents the NSA from relentlessly hopping from one "interesting" number to the next? There
are a number of checks: Subsequent generations of metadata and phone numbers cannot be
investigated without making RAS on them, which means new review and new approvals; only 22 NSA
managers are authorized to approve examination of metadata; the Justice Department audits the
program every 90 days; and the program has to undergo reauthorization with the Foreign Intelligence
Surveillance Court every quarter. That means at least 15 different federal judges have looked at
and approved the program since its inception.
What is not happening with the metadata? There's no freewheeling data-mining, no Facebook-style
graphing of social networks and no unrestricted exploratory data analysis.
The president has proposed a number of reforms, including requiring judicial approval before the NSA
can access metadata. He also proposed a transition that would shift storage of the metadata from
NSA to a third party, possibly the telephone companies.
Judicial review of metadata use is already occurring, albeit after the fact in quarterly court reviews.
Integrating judicial review into each explicit accessing of the metadata is a prudent and reasonable
step, though it has the potential to slow investigations.
At first glance, shifting data-retention responsibilities to a third party might appear to keep Americans'
metadata one additional step removed from prying NSA eyes. But there are potential risks associated
with this move. Private retention could be technically complex and could slow investigations. Even with
the NSA providing storage standards and guidance, the data may be less secure simply because they
are spread across more organizations and locations.
The reforms sought by the administration may or may not ease the privacy concerns many Americans
have about the metadata collection program. Understanding what metadata is, and isn't, might.
THE CIAS BLACK PRISON IN POLAND
Washington Post / by Adam Goldman
http://www.matthewaid.com/post/74318970270/the-secret-history-of-the-cias-black-prison-in
Matthew Aid
Jan 24 2014 Jan 24. On a cold day in early 2003, two senior CIA officers arrived at the US Embas-
sy in Warsaw to pick up a pair of large cardboard boxes. Inside were bundles of cash totaling $15
million that had been flown from Germany via diplomatic pouch.
The men put the boxes in a van and weaved through the Polish capital until coming to the head-
quarters of Polish intelligence. They were met by Col. Andrzej Derlatka, deputy chief of the intelligence
service, and two of his associates.
A villa in the lake district was arguably one of the most important of the black sites created in the wake
of Sept. 11.
The Americans and Poles formalized an agreement that over the previous weeks had allowed the CIA
the use of a secret prison a remote villa in the Polish lake district to interrogate al-Qaeda
suspects. The Polish intelligence service had some more funds, and the agency had a solid location
for its newest covert operation, according to former CIA officials who spoke on the condition of
anonymity to discuss the interrogation program, including previously unreported details about the
creation of the agencys black sites.
The CIA prison in Poland was arguably the most important of all the black sites created by the agency
in the wake of the Sept. 11, 2001, attacks. It was the first of a trio in Europe that housed the initial
wave of accused Sept. 11 conspirators, and it was where Khalid Sheik Mohammed, the self-declared
mastermind of the attacks, was waterboarded 183 times after his capture.
Much about the creation and operation of the CIAs prison at a base in one of the young democracies
of Central Europe remains cloaked in mystery, matters that are classified as state secrets by the U.S.
government. But what happened in Poland more than a decade ago continues to reverberate, and the
bitter debate about the CIAs interrogation program is about to be revisited.
The U.S. Senate Select Committee on Intelligence is preparing to release at least portions of an
exhaustive 6,00o-page report on the CIA interrogation program, its value in eliciting critical
intelligence, and whether Congress was misled about aspects of what the agency was doing.
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 22
The treatment of detainees also continues to be a legal issue in the military trials of Mohammed and
others at Guantanamo Bay in Cuba.
And in December, the European Court of Human Rights heard arguments that Poland violated
international law and participated in torture by accommodating its American ally; a decision is
expected this year.
In the face of Polish and United States efforts to draw a veil over these abuses, the European Court
of Human Rights now has an opportunity to break this conspiracy of silence and uphold the rule of
law, said Amrit Singh, a lawyer with the Open Society Justice Initiative that petitioned the court on
behalf of a detainee who was held there.
Wanted: A better location
The story of a Polish villa that became the site one of the most infamous prisons in American history
began in the Pakistani city of Faisalabad with the capture of Zayn al-Abidin Muhammed Hussein,
better known as Abu Zubaida, in March 2002. The CIA needed a place to stash its first high-value
detainee, a man who was thought to be closely tied to the al-Qaeda leadership and might know of
follow-on plots.
Cambodia and Thailand offered to help the CIA. Cambodia turned out to be the less desirable of the
two. Agency officers told superiors that a proposed site was infested with snakes. So the agency flew
Abu Zubaida to Thailand, housing him at a remote location at least an hours drive from Bangkok.
The CIA declined to comment, as did Polish authorities through Polands embassy in Washington.
Derlatka, the Polish intelligence officer, did not return messages seeking comment.
Several months after the detention of Abu Zubaida, the CIA caught Abd al-Rahim al-Nashiri, another
wanted operative who had been tied to an al-Qaeda attack on a U.S. warship in Yemen. He, too, was
taken to the Thai site.
With the prospect of holding more and more captives, the CIA required a better location. It was just a
chicken coop we remodeled, a former senior CIA official said of the facility in Thailand.
The agency reached out to its liaison partners. The CIA station chief in Warsaw reported back with
good news. The Polish intelligence service, known as Agencja Wywiadu, had a training base with a
villa that the CIA could use in Stare Kiejkuty, a three-hour drive north of Warsaw.
Polish officials asked whether the CIA could make some improvements to the facility. The CIA obliged,
paying nearly $300,000 to outfit it with security cameras.
The accommodations were not spacious. The two-story villa could hold only up to a handful of
detainees. A large shed behind the house was also converted into a cell.
It was pretty spartan, the agency official recalled.
There was also a room where detainees, if they cooperated, could ride a stationary bike or use a
treadmill.
On Dec. 5, 2002, Nashiri and Abu Zubaida were flown to Poland and taken to the site, which was
code-named Quartz.
Five days later, an e-mail went out to agency employees that the interrogation program was up and
running, and under the supervision of the Special Missions Department of the Counterterrorism Center
(CTC).
Officials then began shutting down the prison in Thailand, eliminating all traces that the CIA had been
there.
Harsh interrogations
Agency executives tapped Mike Sealy, a senior intelligence officer, to run the Polish black site,
according to former CIA officials. He was called a program manager and was briefed on an
escalating series of enhanced interrogation techniques that were formulated at the CIA and
approved by Justice Department lawyers. These included slapping, sleep deprivation and
waterboarding, a technique that involved pouring water over the shrouded face of the detainee and
creating the sensation of drowning.
I do believe that it is torture, President Obama said of waterboarding in 2009.
In Poland, Sealy oversaw about a half-dozen or so special protective officers the CIA had sent to
provide security. The number of analysts and officers varied. Polish officials could visit a common area
where lunch was served, but they didnt have access to the detainees.
There would soon be problems in implementation of the interrogation protocols.
Agency officers clashed over the importance of Nashiris role in the bombing of the USS Cole in
Yemen in 2000; the attack killed 17 U.S. servicemen.
He was an idiot, said the former CIA official, who supported the program. He couldnt read or
comprehend a comic book.
Other Counterterrorism Center officials believed that Nashiri was a key al-Qaeda figure and was
withholding information. After a tense meeting in December 2002, top CIA officials decided they
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 23
needed to get tougher with him, two former U.S. intelligence officials recounted.
A decision was also made to dispatch a CIA linguist who had once worked for the FBI in New York.
Albert El Gamil was of Egyptian descent and spoke Arabic fluently, but he was not a trained
interrogator.
El Gamil flew to Poland, where he subjected Nashiri to a mock execution and put a drill to the head of
the blindfolded man, according to several former CIA officials. The CIA inspector general also reported
on those events.
Top CIA officials learned about the incidents in January 2003 after a security guard at the facility
sounded the alarm. Sealy and El Gamil were pulled out of Poland and dismissed from the program,
according to several former agency officials. They left the CIA a short time later.
Both Sealy and El Gamil declined to comment.
Dramatic positive results
In March 2003, Khalid Sheik Mohammed was captured in the Pakistani city of Rawalpindi and brought
to Poland. He proved difficult to break, even when waterboarded, according to several former CIA
officials. Mohammed would count off the seconds, between 20 and 40, knowing the simulated
drowning always ended within a certain period.
An agency official said that one time, Mohammed fell asleep on the waterboard between sessions. But
agency officials have said he finally crumbled after extended sleep deprivation.
CIA officials assert that while in Poland, Mohammed, who had a sizable ego, began talking. He liked to
lecture the CIA officers, who would then steer the conversations in ways that benefited them. He also
liked to joust with his inquisitors. Once a female officer, who was later killed in Afghanistan, questioned
Mohammed in Poland. She told him that she knew everything about him and that he shouldnt lie to
her, two CIA former officials said.
Mohammed leaned back in his chair and said, Then why are you here?
Abu Zubaida also provided important information to his interrogators, officials said. He identified
people in photographs and provided what one official called hundreds of data points.
Officials said Abu Zubaida was even willing to help get new detainees to talk. Allah knows I am only
human and knows that I will be forgiven, a former official recalled him saying.
Former agency officials directly involved in the program, such as the CIAs former deputy director of
operations, Jose Rodriguez, have said the harsh techniques produced dramatic positive results.
The Senate Select Committee on Intelligence intends to challenge such assertions when its report is
made public. Sen. Dianne Feinstein (D-Calif.), the committee chairman, said her investigation will
provide a detailed, factual description of how interrogation techniques were used, the conditions under
which detainees were held, and the intelligence that was, or wasnt, gained from the program.
Eventually, the CIA had to leave Poland, fearing that maintaining one location for too long risked
exposure.
In September 2003, the Polish site was emptied. The CIA scattered detainees to Romania, Morocco
and, later, Lithuania. Looking for a long-term solution, the CIA paid the Moroccans $20 million to build
a prison it never used that was code-named Bombay.
In 2005, The Washington Post reported that the CIA had operated secret prisons in Eastern Europe.
Locations in Poland and Romania were soon identified by Human Rights Watch, and their presence
has since been confirmed by multiple European officials and news accounts.
Before Porter J. Goss stepped down as CIA director in May 2006, the facilities in Romania and Lithua-
nia were closed. Some of the detainees were sent to a Moroccan jail that been previously used and
others to a new CIA prison in Kabul called Fernando, which had replaced one known as the Salt Pit
From those locations, 14 high-value detainees were shipped to the Guantanamo Bay military detention
center in September 2006. Obama ended the interrogation program in 2009.
The previous year, Polish prosecutors opened a criminal investigation into what happened at the
training base. They also quietly issued arrest warrants for CIA officials who had visited the black site.
It is not clear whether the warrants are still in effect.
RUSSIA'S SURVEILLANCE STATE
http://www.worldpolicy.org/journal/fall2013/Russia-surveillance
World Policy Journal 'Secrecy & Security / by Andrei Soldatov and Irina Borogan [Both are Russian
investigative journalists who cover the operations of Russian security services. They are co-founders of the website
Agentura, which chronicles the services activities. They also co-authored The New Nobility: The Restoration of
Russias Security State and the Enduring Legacy of the KGB (Public Affairs, 2011).]
Jan 24 2014 Fall 2013. In March 2013, the Bureau of Diplomatic Security at the U.S. State Depart-
ment issued a warning for Americans wanting to come to the Winter Olympics in Sochi, Russia next
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 24
February: Beware of SORM. The System of Operative-Investigative Measures, or SORM, is Russias
national system of lawful interception of all electronic utterancesan Orwellian network that jeopardi-
zes privacy and the ability to use telecommunications to oppose the government. The U.S. warning
ends with a list of Travel Cyber Security Best Practices, which, apart from the new technology, re-
sembles the briefing instructions for a Cold War-era spy:
Consider traveling with clean electronic devicesif you do not need the device, do not take it. Other-
wise, essential devices should have all personal identifying information and sensitive files removed or
sanitized. Devices with wireless connection capabilities should have the Wi-Fi turned off at all times.
Do not check business or personal electronic devices with your luggage at the airport. Do not
connect to local ISPs at cafes, coffee shops, hotels, airports, or other local venues. Change all your
passwords before and after your trip. Be sure to remove the battery from your Smartphone when
not in use. Technology is commercially available that can geo-track your location and activate the
microphone on your phone. Assume any electronic device you take can be exploited. If you must
utilize a phone during travel consider using a burn phone that uses a SIM card purchased locally with
cash. Sanitize sensitive conversations as necessary.
The list of recommendations ends with the advice to discard the users phone and SIM card before
returning. The instruction might seem like overreaction, but far from it. Anyone who wants to attend the
Olympics needs a Spectator pass, which requires registering on the official Sochi 2014 site, a
procedure that includes taking a photo. What is curious is that when clicking to take a photo, a
MacBook immediately warns the user that the site is requesting access to your camera and
microphone. If you click Allow, you may be recorded.
But the Russian surveillance effort is not limited to the Sochi area, nor confined to foreigners. For
years, Russian secret services have been busy tightening their hold over Internet users in their
country, and now theyre helping their counterparts in the rest of the former Soviet Union do the same.
In the future, Russia may even succeed in splintering the web, breaking off from the global Internet a
Russian intranet thats easier for it to control.
INTERCEPT TELECOM
Over the last two years, the Kremlin has transformed Russia into a surveillance stateat a level that
would have made the Soviet KGB (Committe for State Security) envious. Seven Russian investigative
and security agencies have been granted the legal right to intercept phone calls and emails. But its
the Federal Security Service (FSB), the successor to the KGB, that defines interception procedures,
and theyve done that in a very peculiar way.
In most Western nations, law enforcement or intelligence agencies must receive a court order before
wiretapping. That warrant is sent to phone operators and Internet providers, which are then required
by law to intercept the requested information and forward it to the respective government agencies. In
Russia, FSB officers are also required to obtain a court order to eavesdrop, but once they have it, they
are not required to present it to anybody except their superiors in the FSB. Telecom providers have no
right to demand that the FSB show them the warrant. The providers are required to pay for the SORM
equipment and its installation, but they are denied access to the surveillance boxes.
The FSB has control centers connected directly to operators computer servers. To monitor particular
phone conversations or Internet communications, an FSB agent only has to enter a command into the
control center located in the local FSB headquarters. This system is replicated across the country. In
every Russian town, there are protected underground cables, which connect the local FSB bureau
with all Internet Service Providers (ISPs) and telecom providers in the region. That system, or SORM,
is a holdover from the countrys Soviet past and was developed by a KGB research institute in the
mid-1980s. Recent technological advances have only updated the system. Now, the SORM-1 system
captures telephone and mobile phone communications, SORM-2 intercepts Internet traffic, and
SORM-3 collects information from all forms of communication, providing long-term storage of all
information and data on subscribers, including actual recordings and locations.
Over the last six years, Russias use of SORM has skyrocketed. According to Russias Supreme
Court, the number of intercepted telephone conversations and email messages has doubled in six
years, from 265,937 in 2007 to 539,864 in 2012. These statistics do not include counterintelligence
eavesdropping on Russian citizens and foreigners.
At the same time, Moscow is cracking down on ISPs that dont adhere to their SORM obligations. We
discovered Roskomnadzor (the Agency for the Supervision of Information Technology,
Communications, and Mass Media) statistics covering the number of warnings issued to ISPs and
telecoms providers. In 2010, there were 16 such warnings, and there were another 13 in 2011. The
next year, that number jumped to 30 warnings. In most cases, when the local FSB or prosecutors
office identified shortcomings, they sent the information to Roskomnadzor, which warned the ISP.
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 25
Penalties for failure to meet their obligations are swift and sure. First, the ISP is fined, then if violations
persist, its license may be revoked.
TARGETING WHOM?
In 2011-2012, while protesters flooded Moscows streets, the phones of a number of Russian opposi-
tion leaders and members of the State Duma were hacked. Recordings of their private telephone
conversations were even published online. On December 19, 2011, audio-files of nine tapped phone
calls of Boris Nemtsov, a former deputy prime minister and now a prominent opposition leader, were
posted on the pro-government site lifenews.ru. Nemtsov requested an official investigation. As yet,
none of the leakers have been found or prosecuted, and the official investigation has not identified a
single culprit.
Such victims have no doubt they were bugged and filmed by security services, but only in the fall of
2012 did the first clear indication emerge that SORM was used to wiretap opponents of President
Vladimir Putin. On November 12, 2012, Russias Supreme Court upheld the right of authorities to
eavesdrop on the opposition. The court ruled that spying on Maxim Petlin, a regional opposition leader
in Yekaterinburg, was lawful since he had taken part in rallies that included calls against extending the
powers of Russias security services. The court decided that these were demands for extremist
actions and approved surveillance and telephone interception.
FACEBOOK THREAT
After securing the legal ability to snoop on mobile phones and emails, the Russian secret services
targeted social networks next. Immediately after the Arab Spring, they were tasked with finding a
response to the threat of political stability ostensibly posed by social networks. In August 2011, at an
informal summit of the Collective Security Treaty Organization (CSTO), a regional military alliance led
by Moscow, in Astana, Kazakhstan, the main topics of discussion were the revolutions in the Middle
East and the role played by social networks. The summit, which was attended by then Russian
president Dmitry Medvedev, adopted a confidential document recognizing the potential danger of
social media in the organization of protests in Russia.
But nobody in the Kremlin and security services seemed to have any strategies in place in December
2011, when mass protests broke out in Moscow prompted by Putins campaign to return to the
presidency. All the FSB could muster was a fax, signed by the chief of the St. Petersburg FSB
department, to Pavel Durov, a founder of the Russian social network VKontakte, requiring him to
neutralize the websites of protest groups. Durov refused.
On March 27, 2012, this failure to find the means to deal with protesters activities on social networks
was admitted by the first deputy director of the FSB, Sergei Smirnov. At a meeting of the regional anti-
terrorist group operating within the Shanghai Cooperation Organizationa broad group of nations that
includes most CSTO states as well as ChinaSmirnov referred directly to the challenge posed by the
Arab Spring. New technologies [are being] used by Western special services to create and maintain a
level of continual tension in society with serious intentions extending even to regime change. Our
elections, especially the presidential election and the situation in the preceding period, revealed the
potential of the blogosphere. Smirnov stated that it was essential to develop ways to react to such
technologies and confessed that this has not yet happened.
The Kremlins goal was to use any available type of regional security alliance to build a system of
regional cybersecuritya plausible pretext to help Central Asian states protect themselves and Russia
from the fallout of Arab Spring movements. The Russian secret services launched several programs to
control whats published on the Internet. The FSB, the Interior Ministry, the Foreign Intelligence SVR,
and the Investigative Committee (the Russian analog of the FBI) have new software systems to
monitor social networks and identify participants in online debates. But apparently its the FSBs
Center for Information Security that has taken the lead in policing what Russians are allowed to read
and write.
A gloomy, monumental building on the corner of Lubyanka Square and Myasnitskaya Street houses
the FSBs counterintelligence department. This looming fortress, built in the 1980s as the KGBs IT
Center, forms a part of a row of buildings, known as the Lubyanka, where thousands of dissidents
were imprisoned and interrogated back in the days of the feared Lavrentiy Beria, Stalins hated
spymaster. Initially the Center was responsible for protecting computer networks and tracking down
hackers, but in the late 2000s, it was tasked with monitoring social networks and the Internet as a
whole.
The Commonwealth of Independent States (CIS), a regional organization made up of nine former
Soviet states, uses special analytical search systems developed by Russian programmers. Called
Semantic Archive, the system is produced by the Russian firm Analytic Business Solutions. On the
first floor of the Stalin-era yellow brick building, more than 20 programmers headed by 37-year old
Denis Shatrov are busy updating Semantic Archive. Not long after the release of the first version in
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 26
2004, it was installed in the Russian Security Council and Ministry of Defense headquarters, as well as
the FSB and the Interior Ministry. From the beginning we aimed our systems at the security services,
says Denis Shatrov, a trained programmer who founded the company in 2004. We thought that if we
worked with them, then we would also attract business from our intelligence services and those of our
competitors too. Shatrov told us that he began developing analytic systems in the mid-90s with his
father, the director of a factory that produced automated steering systems for spacecraft. Then they
began to produce simulation systemsfor electoral and economic applications. Their success came in
1999 when they sold their product to the Ukrainian President Kuchmas situation room for use in his
successful campaign for a second term. In the mid-2000s father and son separated, the elder Shatrov
specializing in economic modeling, Denis in media analysis.
The idea of its most popular product, Semantic Archive, is to monitor any sorts of open datamedia
archives, online sources, blogs, and social networksfor key words and then to produce analyses,
most famously, by building charts of connections. As it boasts on the companys own website, the
system uses this raw information to extract objects of interest (certain persons, organizations,
corporate brands, regions, etc.), their actions and relationships.
Semantic Archive is not the only product used by the Russian security services to monitor social
networks, but all of them seem to share the same fundamental flaw. These systems were developed
for searching structured computer files, or databases, and only afterwards adapted, some more
successfully than others, for semantic analysis of the Internet. Most of these systems were designed
to work with open sources and are incapable of monitoring closed accounts such as Facebook.
The FSB discovered early on that the only way to deal with the problem was to turn to SORM. The
licenses require businesses that rent out site space on servers to give the security services access to
these servers via SORM, without informing site owners. With this provision, the FSB has had few
problems monitoring closed groups and accounts on Russian social networks Vkontakte and
Odnoklassniki. But Facebook and Twitter are not hosted in Russia and that has posed a real
challenge for surveillance.
FILTERING
In November 2012, Russia acquired a nationwide system of Internet-filtering. The principle of Internet
censorship wasnt new to Russian authorities. Since 2007, regional prosecutors have implemented
court decisions requiring Internet providers to block access to banned sites accused of extremism. But
this had not been done systematically. Sites blocked in one region remained accessible in others. The
Single Register, officially introduced on November 1, 2012, aimed to solve this problem. Three
government agenciesthe Roskomnadzor, the Federal Anti-Drug Agency, and the Federal Service for
the Supervision of Consumer Rights and Public Welfaresubmit data for the governments black list
of sites. Service providers are then required to block access to each such site within 24 hours.
Since last November, hundreds of websites have been banned from the Russian Internet. The list
ranges from the lighthearted Australian viral YouTube hit Dumb Ways to Die to Absurdopedia (the
Russian version of Uncyclopedia). Even the parody web site Gospoisk (gossearch.ru) was blocked.
The site was a fake search engine, ostensibly created with government support, structured so that
when a visitor types a query in the search box, he is asked to enter his first and last name, patronymic,
passport details, address, and the reason for the request. Since it was a parody, this data evaporated
into the ether.
The new Internet monitoring law has had some substantial offline consequences as well. Institutions
providing public access to the Internetschools, libraries, Internet cafs, and even post officeshave
been targeted for law enforcement inspections to check for computers containing software that might
allow access to banned websites. This problem took on a new urgency, especially in the Muslim-
dominated region of the North Caucasus after the appearance of a YouTube video in September 2012
called The Real Life of Muhammad that was viewed as a direct insult to the Prophet Muhammad.
Russian authorities promptly blocked the entire website in some regions. That made global Internet
service providers much more cooperative with Russian requests. Google removed the video from
YouTube on December 26. Then Twitter blocked an account that promoted drugs on March 15 and on
March 29. Facebook took down a page called Club Suicide rather than see the entire network
blacklisted by the Russians.
The apparent readiness of global services to cooperate with the Russian government seems to
provoke the authorities to push increasingly in the Chinese direction, especially in dealing with social
networks. Moscow is attempting to force international social networking companies into Russias
national jurisdiction.
Then, right on time, Edward Snowden appeared on the world stage. The NSA scandal made a perfect
excuse for the Russian authorities to launch a campaign to bring global web platforms such as Gmail
and Facebook under Russian laweither requiring them to be accessible in Russia by the domain
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 27
extension .ru, or obliging them to be hosted on Russian territory. Under Russian control, these
companies and their Russian users could protect their data from U.S. government surveillance and,
most importantly, be completely transparent for Russian secret services.
Russia wants to shift supervision and control of the Internet from global companies to local or national
authorities, allowing the FSB more authority and latitude to thwart penetration from outside. At
Decembers International Telecommunications Union (ITU) conference in Dubai, Moscow tried to win
over other countries to its plan for a new system of control. The key to the project is to hand off the
functions of managing distribution of domain names/IP-addresses from the U.S.-based organization
ICANN to an international organization such as the ITU, where Russia can play a central role. Russia
also proposed limiting the right of access to the Internet in such cases where telecommunication
services are used for the purpose of interfering in the internal affairs or undermining the sovereignty,
national security, territorial integrity, and public safety of other states, or to divulge information of a
sensitive nature. Some 89 countries voted for the Russian proposals, but not the United States,
United Kingdom, Western Europe, Australia, or Canada. The result is a stalemate.
Web services would be required to build backdoors for the Russian secret services to access whats
stored there. Prominent Russian MP Sergei Zheleznyak, a member of the ruling United Russia party,
has called on Russia to reclaim its digital sovereignty and wean its citizens off foreign websites. He
said he would introduce legislation this fall to create a national server, which analysts say would
require foreign websites to register on Russian territory, thus giving the Kremlins own security
services the access they have long been seeking. Of course, building such a national system would
defeat the global value of the Internet.
BEYOND RUSSIAN BORDERS
Fearing Arab Spring-style uprisings, former Soviet republics have looked to Moscow for guidance on
dealing with free speech in cyberspace. On June 15, 2011 Nursultan Nazarbayev, president of
Kazakhstan, proposed the idea of an alliance-wide cyber police force at the opening of the Shanghai
Cooperation Organization summit in Astana. He added that it was time to include the concept of
electronic borders and e-sovereignty in international law.
Ten months later, at a second SCO summit, member states agreed on joint measures to be taken by
their secret services to prevent and disrupt the usage of the Internet for terrorist, separatist, and
extremist purposes. In turn, the Collective Security Treaty Organization of the CIS countries
established a working group on information security and launched a series of joint operations by secret
services of member-states. The operation was called PROKSI, and Nikolai Bordyuzha, secretary
general of the CSTO, reported that it has led to the shutdown of 216 websites in Russia alone.
But the leaders of these countries clearly understand that censorship and Internet-filtering should be
combined with surveillance. After all, they share the same Soviet legacy. When the Soviet Union
collapsed, the KGBs regional branches became the security services of the newly independent states.
But they retained the KGBs operational DNA, which is apparent in the CIS states continued use of
Soviet and Russian terminology for surveillance operations. The term ORM, or Operative-Investigative
Measures, was kept by all CIS countries. At the same time, the Russian approach to lawful
interception has been adopted in Belarus, Ukraine, Uzbekistan, Kyrgyzstan, and Kazakhstan. And
over the last three years Belarus, Ukraine, and Kyrgyzstan have all updated their national interception
systems, modeled after the Russian SORM.
In March 2010, Belarusian president Alexander Lukashenko introduced SORM into his country. Two
years later, the national telecom operator Beltelecom installed SORM on its data network. In late 2010,
Ukraine updated its national requirements for SORM equipment. And in August 2012, Kyrgyzstan
updated its network to make it virtually identical to the Russian interception systemin all, bringing
tens of millions of new individuals under potential surveillance by security services.
Meanwhile, the export of Russian surveillance procedures and equipment in many cases also means
exporting Russian technology, giving homegrown manufacturers natural advantages over their
Western counterparts. This, in turn, has led to the growing presence of Russian advisers. SORM is
also not the only surveillance technology imported from Russia to the other CIS countries. The
Semantic Archive, the favorite technology of monitoring social networks, was installed in Ukraine,
Belarus, and Kazakhstanmuch to the delight, and profit, of Denis Shatrov.
The further localization of the Internet is likely. Soon, we will end up with a Balkanization of what was
once a global internet, replaced by a collection of national or regional internets. Local security services
will sell their various surveillance technologies and strategies. Governments will be delighted to extract
more controls, with the global Internet services themselves being driven in the same direction of
increased fragmentation by the very logic of the advertising business which requires ever finer
targeting and accountability of their audience. Russian customers are led to google.ru, not because its
established by the Kremlin or the FSB, but because Google can target ads with more precision. In the
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 28
future, however, it could be the FSB directing your Internet travels.
Today, global Internet platforms are rightly considered public services, and for the benefit of the public
or its institutions. To keep web services and products, not to mention the information they carry, both
transparent and global, companies and countries need to resist pressure to fragment the Internet.
The World Wide Web must keep its first W. It is in the interest of all those trying to spread the ideas of
democracy around the world.
INTEL CAN'T DEAL WITH NUCLEAR TASKS
Pentagon Study Finds Agencies Ill Equipped to Detect Foreign Nuclear Efforts
www.nytimes.com/2014/01/24/us/politics/us-efforts-to-detect-nuclear-programs-are-inadequate-
pentagon-study-finds.html?nl=todaysheadlines&emc=edit_th_20140124&_r=0
NY Times / David E Sanger and William J Broad
Stringer: Frank Slijper / Campaign Against Arms Trade / Groningen NL / frank.slijper@hetnet.nl
Jan 24 2014 Jan 23. A three-year study by the Pentagon has concluded that American intelligence
agencies are not yet organized or fully equipped to detect when foreign powers are developing nu-
clear weapons or ramping up their existing arsenals, and calls for using some of the same techniques
that the National Security Agency has developed against terrorists.
The study, a 100-page report by the Defense Science Board, contends that the detection abilities
needed in cases like Iran including finding undeclared facilities and/or covert operations are either
inadequate, or more often, do not exist.
The report is circulating just two months before President Obama will attend his third nuclear security
summit meeting, set for March in The Hague, an effort he began in order to lock down loose nuclear
materials and, eventually, reduce the number of countries that could build nuclear weapons. Mr.
Obamas efforts to sweep up the materials have largely been considered a success. But the report
concluded that potential new nuclear states are emerging in numbers not seen since the early days of
the Cold War, and that monitoring for proliferation should be a top national security objective but one
for which the nation is not yet organized or fully equipped to address.
The report confirmed what many outside experts have learned anecdotally: While the most famous
intelligence failure in the past decade involving nuclear weapons occurred in Iraq, where the C.I.A.
and others saw a program that did not exist, the bigger concern may be that major nuclear programs
were entirely missed.
American officials first learned of a reactor in Syria, built with North Korean assistance, when the
Israelis alerted them. (Israel destroyed the facility in 2007.) North Korea, early during the Obama
administration, built a uranium enrichment facility that went undetected until the North showed it off to
a visiting professor from Stanford.
The lesson from this history is that we found these at the last moment, if we found them at all, said
Bruce Riedel, a former C.I.A. expert on terrorism and nuclear proliferation who is now at the Brookings
Institution.
The Defense Science Board came to a similar conclusion. It said that in the future, satellite photo-
graphs and other reconnaissance will most likely be of limited use. Instead, it suggested that many of
the cyber and big-data programs developed by the N.S.A. should be used to detect proliferation, a bet
that the United States would be more likely to pick up evidence of scientists and engineers talking,
emailing, or searching for nuclear-related technologies than it would be to see a weapons facility being
built.
In fact, the growing need to detect proliferation was one of the arguments Mr. Obama made last Friday
in his speech explaining why many of the programs started by the N.S.A. in recent years must be
preserved.
A former senior intelligence official familiar with the report, which was commissioned by Ashton B.
Carter, the former deputy secretary of defense who resigned late last year, said the effort was to focus
the governments efforts on the global dimensions of the atomic threat.
One of the highest priorities of successive administrations is countering proliferation, the official said.
But theres little coherence on what agencies do to move that interest forward.
The range of government departments that were interviewed by the Defense Science Board
underscores how spread out the effort has become: Officials of several of the nations 16 intelligence
agencies participated, along with four of the Energy Departments National Laboratories and its
National Nuclear Security Administration, the Department of Homeland Security, the Defense Threat
Reduction Agency and the White Houses National Security Council.
The former senior official said that many signs of a nuclear program could be found by monitoring
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 29
open sources, and that clues there are frequently overlooked.
Theres always evidence of it, he said of clandestine nuclear activity, speaking on the condition of
anonymity. For instance, he said, how much of a countrys gross domestic product is devoted to
certain industries could be a significant clue.
From open sources you can put that together, he said. But no entity in the government brings
coherence to all these things.
The report did not name any specific countries that are under American surveillance because of their
current or suspected weapons programs. But it is no secret that the United States spends enormous
resources tracking Pakistans arsenal, along with those of Russia, China, India, North Korea and
Israel.
The report implicitly called into question whether administration officials should be so confident that
they would detect if Iran ever violated the nuclear accord that began this week.
THE US SURROUNDED IRAN WITH STEALTH DRONES
RQ-170 Sentinels secretly staged to the UAE
https://medium.com/war-is-boring/404024f84fc0
War is Boring / by David Axe & Joe Trevithick
Stringer: Frank Slijper / Campaign Against Arms Trade / Groningen NL / frank.slijper@hetnet.nl
Jan 24 2014 Starting at least four years ago, the U.S. Air Force and the Central Intelligence Agency
secretly and systematically surrounded Iran with Americas most high-tech, radar-evading spy drones.
In December 2011, one of the 60-foot-wingspan RQ-170 Sentinel drones, probably flying from Kanda-
har in southern Afghanistan, crashed on the Iran-Pakistan border and was seized by Iranian forces.
The Sentinel presumably had been surveilling Iranspecifically, Tehrans suspected nuclear weapons
program.
The crash revealed one arc of the stealth drone cordon around Iran. The other arc, apparently an-
chored south of Iran in the United Arab Emirates, has never been revealed before now.
Sometime in 2010, it appears that the 30th Reconnaissance Squadrona combined Air Force and
CIA unit normally based in remote Tonopah, Nevadadeployed some of its estimated 20 Sentinels to
Al Dhafra, a sprawling air base in the UAE where the Pentagon stages many of its most sophisticated
spy planes for patrols near Iran.
According to heavily-redacted official documents obtained by War is Boring through the Freedom of
Information Act, on Sept. 14, 2010, the Air Forces Air Combat Commandthe headquarters that
oversees the 30th Reconnaissance Squadroncirculated an internal memo discussing the pre-
deployment site survey for placing some of the satellite-controlled RQ-170s in the Emirates.
The RQ-170s were built by Lockheed Martin in the early 2000s and helped spy on Iraq during the
2003 invasion. One of the distinctive, bat-shaped bots was photographed by a journalist at Kandahar
airfield in 2007. In 2009, the Air Force copped to the Sentinels existence, but released no details. An
RQ-170 reportedly orbited overhead as Navy SEALs raided Osama Bin Ladens compound in
Pakistan in May 2011, killing the Al Qaeda leader.
Another version of Air Combat Commands Sentinel survey memo circulated on Sept. 27, 2010this
one specifying Al Dhafra air base as the stealth drones destination. Sentinels, like the non-stealthy
Predator and Reaper spy drones also used by the Air Force and CIA, apparently deploy in groups of at
least three, allowing one to be airborne over the target area around the clock, while the others are in
transit or under repair.
Having surveyed Al Dhafra for Sentinel basing and apparently cleared the massive facility for hosting
the secretive robot planes, on Oct. 7, 2010, a U.S. Air Force delegation met with a counterpart group
from the UAE Air Force, a strong ally of the American flying branch that operates U.S.-made Predators
and F-16s.
Based on the documents we obtained via FOIA, the topic of the meeting seemed to have been the
RQ-170although its unclear exactly what the officers said about the drone.
In any event, the surveys and meeting paved the way for Sentinels to fly from Al Dhafra. Lacking
additional documentary evidence, we can only assume that the elusive bots actually did deploy to the
desert airfield shortly thereafter. Its hard to imagine that the Air Force would go to the trouble of
clearing Al Dhafra for the stealth drones unless the flying branch truly intended to send them there.
While the Emirates air base is convenient to the entire Persian Gulf, the American aircraft at the
facility, including high-flying U-2 photo-recon birds and four-engine E-3 radar planes, traditionally focus
their attention on Iran.
The Air Force and Navy also both base RQ-4 Global Hawk spy drones at Al Dhafra. In late 2013, the
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 30
Navy contracted with RQ-4-builder Northrop Grumman to nearly double the frequency of its robotic
missions near Iran to 15 a month.
The stealthy Sentinel solved a worsening problem for U.S. forces around Iran. In recent years,
Tehrans ramshackle but increasingly aggressive air force has begun intercepting American drones
near Iranian air space.
In November 2012, an Iranian Su-25 attack jet fired its gun at an MQ-1 Predator but missed. In March
2013, an Iranian F-4 fighter intercepted another Predator but was chased off by a U.S. F-22 stealth
fighter that slipped in underneath the 1960s-vintage F-4.
The Predators and other spy planes are unable to avoid detection and sometimes need rescuing. But
the Sentinels can fly independently, using their hard-to-detect shape and, presumably, radar-
absorbing coating to dodge Iranian sensors.
Until an RQ-170 crashed on the Afghan-Iranian border, its possible Tehran had no idea the drones
were even probing its air spaceand indeed had the country surrounded.
THE ESCALATING OBAMA DRONE CAMPAIGN
More than 2,400 dead as Obamas drone campaign marks five years
www.thebureauinvestigates.com
The Bureau of Invastigative Journalism
Jan 23 2014 Five years ago, on January 23 2009, a CIA drone flattened a house in Pakistans tribal
regions. It was the third day of Barack Obamas presidency, and this was the new commander-in-
chiefs first covert drone strike.
Initial reports said up to ten militants were killed, including foreign fighters and possibly a high-value
target a successful first hit for the fledgling administration.
But reports of civilian casualties began to emerge. As later reports revealed, the strike was far from a
success. At least nine civilians died, most of them from one family. There was one survivor, 14-year-
old Fahim Qureshi, but with horrific injuries including shrapnel wounds in his stomach, a fractured skull
and a lost eye, he was as much a victim as his dead relatives.
Later that day, the CIA attacked again and levelled another house. It proved another mistake, this
time one that killed between five and ten people, all civilians.
Obama was briefed on the civilian casualties almost immediately and was understandably disturbed,
Newsweek reporter Daniel Klaidman later wrote. Three days earlier, in his inauguration
address, Obama had told the world that America is a friend of each nation, and every man, woman
and child who seeks a future of peace and dignity.
The Pakistani government also knew civilians had been killed in the strikes. A record of the strikes
made by the local political administration and published by the Bureau last year listed nine civilians
among the dead. But the government said nothing about this loss of life.
Yet despite this disastrous start the Obama administration markedly stepped up the use of drones.
Since Obamas inauguration in 2009, the CIA has launched 330 strikes on Pakistan his predecessor,
President George Bush, conducted 51 strikes in four years. And in Yemen, Obama has opened a new
front in the secret drone war.
Lethal strikes
Across Pakistan, Yemen and Somalia, the Obama administration has launched more than 390 drone
strikes in the five years since the first attack that injured Qureshi eight times as many as were
launched in the entire Bush presidency. These strikes have killed more than 2,400 people, at least 273
of them reportedly civilians.
Although drone strikes under Obamas presidency have killed nearly six times as many people as
were killed under Bush, the casualty rate the number of people killed on average in each strike has
dropped from eight to six under Obama. The civilian casualty rate has fallen too. Strikes during the
Bush years killed nearly more than three civilians in each strike on average. This has halved under
Obama (1.43 civilians per strike on average). In fact reported civilian casualties in Pakistan have fallen
sharply since 2010, with no confirmed reports of civilian casualties in 2013.
The decline in civilian casualties could be because of reported improvements in drone and missile
technology, rising tensions between Pakistan and the US over the drone campaign, and greater
scrutiny of the covert drone campaign both at home and abroad.
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 31
Obama has sharply escalated the drone campaign in Pakistan.
The apparent change in targeting is well demonstrated by comparing a strike carried out by the Bush
administration in 2006 and one seven years later under Obama. On October 30 2006 at least 68
children were killed when CIA drones destroyed a madrassa a religious school in the Bajaur area
of Pakistans tribal belt. The attack was reportedly targeting then-al Qaeda second-in-command
Ayman al Zawahiri. He escaped. On November 21 last year, drones again targeted a madrassa, this
time in Hangu, outside the tribal regions. As many as 80 students were sleeping in the building. But
the strike destroyed a specific portion of the building just one or two rooms and killed between six
and nine people.
In Yemen, however, civilians continue to die in US drone strikes. Last year saw the highest civilian
casualty rate since Obama first hit the country in 2009.
Drones were not the first weapon the administration turned to when it started to attack the country. On
December 17 2009 a US Navy submarine launched a cluster bomb-laden cruise missile at a
suspected militant camp in al Majala, southern Yemen.
The missile slammed into a hamlet hitting one of the poorest tribes in Yemen. Shrapnel and fire left at
least 41 civilians dead, including at least 21 children and 12 women five of them were pregnant. A
week earlier President Obama had been awarded the Nobel Peace Prize. He used his acceptance
speech to defend the use of force at times as not only necessary but morally justified. He warned that
negotiations cannot convince al Qaedas leaders to lay down their arms.
Strikes in Pakistan are carried out by the CIA. But in Yemen the CIA and the US militarys special
forces unit, Joint Special Operations Command, have used various weapons including drones and
conventional jets as well as cruise missiles to target al Qaeda militants.
However in recent years drones have come to dominate Obamas war in Yemen as much as in
Pakistan. President Bush ordered a single drone strike in Yemen, killing six people in 2002. Under
Obama, the CIA and the Pentagon have launched at least 58 drone strikes on the country killing more
than 281 people, including at least 24 reported civilians.
Opaque operations
The escalation in the drone war has happened with almost no official transparency from the White
House. It took Obama three years to publicly mention his use of drones. In January 2012 he said
actually drones have not caused a huge number of civilian casualties. He added: For the most part
they have been very precise, precision strikes against al Qaeda and affiliates.
In this period Bureau records show drones reportedly killed at least 236 civilians including 61
children. And according to a leaked CIA record of drone strikes, seen by the McClatchy news agency,
the US often did not know who it was killing. In the year after September 2010 at least 265 of up to
482 people were recorded as the documents as killed by drones were assessed as Afghan,
Pakistani and unknown extremists.
A letter written by Attorney General Eric Holder and leaked to NBC confirmed drones had killed four
US citizens living abroad. US citizen Anwar al Awlaki died in a missile strike in Yemen on September
30 2011. His 16-year-old son Abdulrahman, who was born in Detroit, was killed in a separate strike
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 32
two weeks later.
In April 2013 a leaked Department of Justice memo outlined the administrations legal justification for
such killings: the US has the right to kill US citizens if they pose an imminent threat, it said. It added
that determining a citizen poses an imminent threat does not require the United States to have clear
evidence that a specific attack on US persons and interests will take place in the immediate future.
Jameel Jaffer of the American Civil Liberties Union described the memo as a chilling document.
The following month President Obama made a major policy speech in which he codified the rules his
administration must follow as it selects targets for drone strikes and special forces teams.
The rules are meant to constrain the use of drones. Obama said the US only carries out such attacks
against individuals who pose a continuing and imminent threat to US citizens, not to punish indivi-
duals. Obama acknowledged drone strikes had killed civilians, saying: For me, and those in my chain
of command, those deaths will haunt us as long as we live. And he added: Before any strike is taken,
there must be near-certainty that no civilians will be killed or injured the highest standard we can
set.
However Bureau analysis shows more people were killed in Pakistan and Yemen in the six months
after the speech than the six months before. And the casualty rate also rose over the same period.
In 2013, there were no confirmed civilian casualties in Pakistan the first year of the drone campaign
that this was the case. But in Yemen, the year ended with mass civilian casualties. On December 12,
JSOC drones attacked a convoy taking a bride to her wedding. The attack destroyed several vehicles
and flying shrapnel killed up to 15 civilians. It was the biggest single loss of civilian life from a US strike
for more than a year. The Yemeni government initially claimed al Qaeda militants were killed. But the
Yemeni government quickly negotiated reparations with the families of the victims, sending them
$140,000 and 100 rifles. The US has not commented on the strike, but in an unprecedented move
Washington is carrying out an investigation.
NSAS SPYING ON PHONE CALLS ILLEGAL: US PRIVACY BOARD
www.bloomberg.com/news/2014-01-23/nsa-s-spying-on-phone-calls-illegal-u-s-privacy-board.html
Bloomberg News / by Margaret Talev & Chris Strohm
Stringer: Martin Rudner [ret.] / Carleton University / Ottawa / www.carleton.ca/cciss
Jan 23 2014 Jan 23. The U.S. National Security Agency is illegally collecting phone call records
from millions of Americans and the program should be stopped, a federal privacy board recommends
in a report issued today.
The five-member Privacy and Civil Liberties Oversight Board, created by Congress to protect privacy
under post-Sept. 11 anti-terrorism laws, said in a 238-page report that the program has provided only
minimal help to the U.S. in thwarting other terrorist attacks, according to the report.
This panel has no authority to change the programs and President Barack Obama last week went
ahead, without waiting for todays report, and presented his own plan that doesnt end the use of bulk
phone records. Its conclusion presents a public relations challenge for a White House under pressure
from phone and Internet companies, foreign governments and civil libertarians after disclosures by
former government contractor Edward Snowden of electronic spying by the NSA.
By questioning the programs legality, the panel may give ammunition to critics in Congress and fuel
legal challenges. At the same time, the boards 3-2 split on the question of legality of collecting phone
data from such carriers as Verizon Communications Inc. (VZ) and AT&T Inc. may diminish the impact
of the report and highlights the complexities of balancing security and democratic freedoms.
Constitutional Concerns
The U.S. justification for the phone records collection under Section 215 of the Patriot Act implicates
constitutional concerns under the First and Fourth Amendments, raises serious threats to privacy and
civil liberties as a policy matter, and has shown only limited value, the report said. As a result, the
board recommends that the government end the program.
The panels two dissenters served in President George W. Bushs administration. All the members
were appointed by Obama and confirmed by the Democratic-controlled Senate.
The bombshell nature of the reports central conclusion may explain why Obama, after meeting with
the board on its planned recommendations weeks ago, decided to announce his proposals on Jan. 17.
Obama defended U.S. electronic spying as a bulwark against terrorism. He proposed changing
aspects of the phone metadata program, which may require Congress to sort out details such as
whether the government, the phone companies or an unidentified third party should retain the data.
Split Cited
Three of the five privacy board members agreed with the legal analysis that the NSAs phone records
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 33
collection is illegal, while two other panelists said the board should limit its review to whether the
program violates privacy and civil liberties.
Representative Mike Rogers, a Michigan Republican and chairman of the House intelligence
committee, who has been supportive of the surveillance tools, seized on that disagreement in an e-
mailed statement today.
In 38 times over the past seven years, 17 federal judges have examined this issue and found the
telephone metadata program to be legal, concluding this program complies with both the statutory text
and with the U.S. Constitution, Rogers said. I dont believe the Board should go outside its expertise
to opine on the effectiveness of counterterrorism programs.
The panels findings were reported earlier by the New York Times.
Internet Data
Internet companies such as Google Inc. (GOOG), Yahoo! Inc., and Facebook Inc., which have pushed
for more transparency about government court requests for e-mail and other content from their
customers, should be able to voluntarily disclose certain statistical information, the report said. In
addition, the government should publicly disclose more detailed statistics to provide a more complete
picture of government surveillance operations.
Obama had deferred decisions regarding the NSAs Internet data collection to Congress and a new
panel expected to be appointed.
Members of the privacy board briefed Obama on their planned recommendations ahead of his Jan. 17
announcement. The recommendations from the bipartisan, independent agency housed in the
executive branch also follows a December report by a separate, independent review panel appointed
by the president.
The privacy panel, created by Congress in 2007 but only operational last year, is led by David Medine,
a former Federal Trade Commission official in former President Bill Clintons administration. Medine
agreed with the findings along with retired appeals court Judge Patricia M. Wald, and James X.
Dempsey, a civil liberties advocate who specializes in technology issues.
Judicial Review
The two members who disagreed with the legal analysis are Washington attorneys Rachel Brand and
Elisebeth Collins Cook.
Obama said he would require judicial review of requests to query phone call databases and ordered
the Justice Department and intelligence officials to devise a way to take storage of that data out of the
governments hands.
He left other steps to limit surveillance up to a divided Congress, meaning that other changes may be
months away if they are adopted at all.
Obama gave Attorney General Eric Holder and intelligence officials 60 days to develop a plan for
storing bulk telephone records outside of government custody, one of the most contentious issues
arising from Snowdens disclosures.
New Panel
Phone companies, such as Verizon and AT&T, have resisted being required to retain telephone
metadata for the government because of the potential cost and legal exposure. An entity to take on
that role doesnt yet exist. The administration plans to deliver a proposal on data storage to Congress
by the end of March.
Obama called for the creation of an outside panel of advocates to weigh in on new and major privacy
issues before the Foreign Intelligence Surveillance Court.
The most concrete and immediate changes announced by Obama will require judicial review for
queries of the metadata records. In addition, the government can no longer access records that go
beyond two persons removed from the query the government makes.
Under the presidents plan, the U.S. wont monitor the communications of leaders of close allies unless
there is a compelling national security interest while that leaves loopholes for the U.S. government to
continue its spying abroad.
CLAIMS OBAMA MADE ON NSA SURVEILLANCE
In preparation for President Obama's speech on surveillance policy today, here are four of the
misleading statements he has made about the NSA.
http://www.propublica.org/article/four-questionable-claims-obama-has-made-on-nsa-surveillance
ProPublica / by Kara Brandeisky
Stringer: Kees Kalkman / VDAmok / Utrecht NL / kees@amok.antenna.nl
Jan 23 2014 Jan 17. Today President Obama plans to announce some reportedly limited reforms to
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 34
National Security Agency surveillance programs.
Since the first disclosures based on documents provided by former NSA contractor Edward Snowden,
Obama has offered his own defenses of the programs. But not all of the presidents claims have stood
up to scrutiny. Here are some of the misleading assertions he has made.
1. There have been no abuses.
"And I think it's important to note that in all the reviews of this program [Section 215] that have been
done, in fact, there have not been actual instances where it's been alleged that the NSA in some ways
acted inappropriately in the use of this data There had not been evidence and there continues not
to be evidence that the particular program had been abused in how it was used." -- Dec. 20, 2013
At press conferences in June, August and December, Obama made assurances that two types of bulk
surveillance had not been misused. In fact, the Foreign Intelligence Surveillance Court has
reprimanded the NSA for abuses both in warrantless surveillance targeting people abroad, and in bulk
domestic phone records collection.
In 2011, the FISA Court found that for three years, the NSA had been collecting tens of thousands of
domestic emails and other communications in violation of the Fourth Amendment. The court ordered
the NSA to do more to filter out those communications. In a footnote, Judge John D. Bates also
chastised the NSA for repeatedly misleading the court about the extent of its surveillance. In 2009
weeks after Obama took office the court concluded the procedures designed to protect the privacy of
American phone records had been so frequently and systemically violated that it can fairly be said
that this critical element of the overall regime has never functioned effectively.
The NSA told the court those violations were unintentional and a result of technological limitations. But
the NSAs own inspector general has also documented some willful abuses: About a dozen NSA
employees have used government surveillance to spy on their lovers and exes, a practice reportedly
called LOVEINT.
2. At least 50 terrorist threats have been averted.
"We know of at least 50 threats that have been averted because of this information not just in the
United States, but, in some cases, threats here in Germany. So lives have been saved." -- June 19,
2013
The record is far less clear. Obamas own review group concluded that the sweeping phone records
collection program has not prevented any terrorist attacks. At this point, the only suspect the NSA says
it identified using the phone records collection program is a San Diego cab driver later convicted of
sending $8,500 to a terrorist group in his homeland of Somalia.
The NSAs targeting of people abroad appears to have been more effective around counter-terrorism,
as even surveillance skeptics in Congress acknowledge. But its impossible to assess the role the NSA
played in each case because the list of thwarted attacks is classified. And what we do know about the
few cases that have become public raises even more questions:
Contrary to what Obama suggested on the Charlie Rose Show in June, the AP has reported that the
FBI did not need either program to identify Najibullah Zazi, later convicted of plotting to attack the New
York subway system.
ProPublica has reported that one case began with a tip from British intelligence, not NSA surveillance.
In another case, no one has been charged related to the alleged plot.
3. The NSA does not do any domestic spying.
"We put in some additional safeguards to make sure that there is federal court oversight as well as
Congressional oversight that there is no spying on Americans. We don't have a domestic spying
program. What we do have are some mechanisms where we can track a phone number or an e-mail
address that we know is connected to some sort of terrorist threat, and that information is useful." --
Aug. 7, 2013
In fact, plenty of Americans communications get swept up. The government, of course, has the phone
records of most Americans. And, as the FISA Court learned in 2011, the NSA was gathering tens of
thousands of domestic emails and other communications.
Additionally, the NSA's minimization procedures, which are supposed to protect American privacy,
allow the agency to keep and use purely domestic communications in some circumstances. If the NSA
inadvertently vacuums up American communications that are encrypted, contain evidence of a crime,
or relate to cybersecurity, the NSA can retain those communications.
The privacy standards suggest there is a backdoor loophole that allows the NSA to search for
American communications. NSA critic Sen. Ron Wyden, D-Ore., has said, Once Americans'
communications are collected, a gap in the law that I call the 'back-door searches loophole' allows the
government to potentially go through these communications and conduct warrantless searches for the
phone calls or emails of law-abiding Americans.Its not clear whether the NSA has actually used this
backdoor.
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 35
And while the NSA acknowledges that it intercepts communications between Americans and
surveillance targets abroad, the agency also intercepts some domestic communications that mention
information about foreigners who have been targeted. As a result, the NSA has sometimes searched
communications from Americans who have not been suspected of wrongdoing though an NSA
official says the agency uses very precise searches to avoid those intercepts as much as possible.
4. Snowden failed to take advantage of whistleblower protections.
"I signed an executive order well before Mr. Snowden leaked this information that provided
whistleblower protection to the intelligence community for the first time. So there were other avenues
available for somebody whose conscience was stirred and thought that they needed to question
government actions." -- Aug. 9, 2013
Obamas presidential policy directive forbids agencies from retaliating against intelligence personnel
who report waste, fraud and abuse. But the measure mentions only employees, not contractors.
Whistleblower advocates say that means the order does not cover intelligence contractors.
I often have contractors coming to me with whistleblower-type concerns and they are the least
protected of them all, attorney Mark Zaid told the Washington Post.
Whats more, the directive was not yet in effect at the time Snowden came forward.Since the leaks,
the Office of the Director of National Intelligence has said the Executive Branch is evaluating the
scope of the protections.
Former NSA employee Thomas Drake argues that even if Snowden were a government employee
who went through the proper legal channels, he still wouldnt have been safe from retaliation. Drake
says while he reported his concerns about a 2001 surveillance program to his NSA superiors,
Congress, and the Department of Defense, he was told the program was legal. Drake was later
indicted for providing information to the Baltimore Sun. After years of legal wrangling, Drake pleaded
guilty to a lesser charge and got no prison time.
ISRAEL BUSTS JIHAD TERROR CELL
Israel busts 'global jihad' terror cell planning attacks, including against US Embassy
http://www.longwarjournal.org/archives/2014/01/israel_busts_global.php
The Long War Journal / by David Barnett
Stringer: Martin Rudner [ret.] / Carleton University / Ottawa / www.carleton.ca/cciss
Jan 23 2014 Jan 22. Israeli authorities today announced the arrest of three global jihadists who
were allegedly preparing to carry out terror attacks after being recruited by an al-Qaeda-linked opera-
tive in the Gaza Strip. The three terrorists were identified as Iyad Mahmoud Khalil Abu Sara, Rubin
Abu Nagma, and Ala Yasin Mohammed Anam.
The arrested Palestinians from the West Bank and Jerusalem area were recruited online and planned
to carry out kidnappings and bombings at the International Convention Centre in Jerusalem as well as
the US Embassy in Tel Aviv, among other attacks. Israeli authorities kept their counterparts in the "US
and elsewhere" updated on their investigation, Israeli security sources said.
According to the Shin Bet, the three had been recruited separately by a Gaza-based operative called
Oreib al Sham. "Senior Shin Bet sources said they believed Al-Sham received his orders directly from
the head of al-Qaeda's central structure, Ayman Al-Zawahri," the Jerusalem Post reported. The
unconfirmed claim "is based on statements made by the suspects during questioning," Haaretz noted.
According to Haaretz, al Sham told the recruits that he worked for Zawahiri.
Abu Sara admitted to planning a shooting attack on a bus traveling between Jerusalem and Ma'ale
Adumim. According to the Shin Bet, the plot would have seen terrorists fire at the wheels of a bus,
causing it to overturn, and then opening fire on the passengers and emergency responders. Abu Sara
also reportedly agreed to assist in a double suicide bombing operation against the US Embassy in Tel
Aviv and the International Convention Centre in Jerusalem.
Using fake Russian passports and traveling under the guise of tourists, foreign jihadists were
supposed to enter Israel, where they would have been assisted by Abu Sara in carrying out the
bombings, the security agency said. According to the Shin Bet, Abu Sara had agreed to go to Syria for
military training, but had not yet done so. He had already received files from Gaza detailing how to
manufacture explosives, however.
Rubin Abu Nagma had been planning to kidnap a soldier from a Jerusalem bus stop in addition to
detonating explosives at a housing complex in the area of Abu Tor, the Shin Bet statement said. Ala
Yasin Mohammed Anam purportedly sought to establish a Salafi jihadist terror cell in the West Bank.
News of the recent arrests comes about two months after Israel security forces killed three Salafi
jihadists near Hebron. The jihadists were "only a small part" of the Salafi jihadist structure in the West
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 36
Bank, and "what was hidden was greater," the Gaza-based Mujahideen Shura Council in the Environs
of Jerusalem said in a statement praising the three jihadists. A Shin Bet official said those recently
arrested were not linked to those killed in November, Ynet News reported.
Shin Bet officials believe that the spread of al Qaeda-linked activity in the West Bank is in its infancy
and can be stopped, Reuters reported.
US WITHHOLDING FISA COURT ORDERS ON NSA BULK COLLECTION
OF AMERICANS' DATA
http://www.theguardian.com/world/2014/jan/21/us-withholding-fisa-court-orders-nsa-bulk-collection
The Guardian by Specer Ackerman
Jan 22 2014 Jan 21. The Justice Department is withholding documents related to the bulk collection
of Americans data from a transparency lawsuit launched by the American Civil Liberties Union.
US attorney Preet Bharara of the southern district of New York informed the ACLU in a Friday letter
that the government would not turn over certain other records from a secret surveillance court, which
are being withheld in full from a Freedom of Information Act suit the civil liberties group filed to shed
light on bulk surveillance activities performed under the Patriot Act.
The decision to keep some of the records secret, in the thick of Edward Snowden's revelations, has
raised suspicions within the ACLU that the government continues to hide bulk surveillance activities
from the public, despite US president Barack Obama's Friday concession that controversial National
Security Agency programs have never been subject to vigorous public debate.
The ACLU lawsuit, like others filed by civil liberties groups, has resulted in a trove of documents from
the so-called Fisa court detailing the scope, authorizations and, in some cases, violations surrounding
NSA surveillance ostensibly occurring under Section 215 of the Patriot Act. The director of national
intelligence now posts the released documents to a Tumblr page, usually without revealing that the
disclosures were spurred by lawsuits.
The latest such disclosure happened Friday with the release of 24 documents, mostly detailing Fisa
court reauthorizations of the bulk phone records collection first reported by the Guardian thanks to
leaks from whistleblower Snowden.
Among the information disclosed in the documents, which date back to 2006 the first year in which the
program received authorization from the Fisa court at all is the footnoted stipulation that the court
understands that NSA expects it will continue to provide, on average, approximately 3 telephone
numbers per day to the FBI.
If true the footnote only appears in pre-2009 court reauthorizations the estimate suggests the NSA has
given the FBI approximately 13,203 phone numbers based on the 12-year-old domestic bulk phone
data program.
In his letter, written on the day Obama gave a long-awaited speech on surveillance that pledged
additional transparency, Bhahara said that Friday's release will be the last disclosure under the terms
of the ACLU's lawsuit.
As discussed by telephone this morning, the government in fact has processed all of the remaining
FISC Orders responsive to the FOIA request in this case that relate to bulk collection, regardless of
whether the order contains any additions and/or adjustments to the implementation procedures,
minimization procedures, and/or reporting requirements set out in other FISC orders,? the US attorney
wrote.
The government cannot specify the total number of documents withheld in full from this final set of
responsive documents because the number itself is classified."
Alexander Abdo, an ACLU attorney, noted that the government's bulk surveillance disclosures have
yet to include, among other efforts, a reported CIA program to collect international money transfers in
bulk, revealed in November by the Wall Street Journal and the New York Times.
It appears that the government is concealing the existence of other bulk collection programs under the
Patriot Act, such as the CIA's reported collection of our financial records, Abdo said.
In other words, on the same day that President Obama recognized the need for a vigorous debate
about bulk collection, the government appears to be hiding the ball. We can't have the public debate
that President Obama wants without the facts that his agencies are hiding.
Abdo said that the scope of the ACLU's disclosure lawsuit only concerned surveillance efforts under
Section 215 of the Patriot Act and that surveillance authorizations containing individualized suspicion
were already excluded.
The NSA conducts other bulk data collection under the Foreign Intelligence Surveillance Act of 1978,
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 37
an update to that law in 2008, and under a three-decade-old executive order known as 12333, all of
which are outside the terms of the ACLU's lawsuit.
Bharara's office routed a request for comment back through the Justice Department, which has yet to
respond.
FBI EMPHASIZES LAW ENFORCEMENT'S ROLE
In Reversal, FBI Now Emphasizes Role in Law Enforcement
http://thecable.foreignpolicy.com/posts/2014/01/17/in_reversal_fbi_now_emphasizes_role_in_law_enforcement
Foreign Policy / by John Hudson
Source: Infowarrior / https://attrition.org/mailman/listinfo/infowarrior
Jan 21 2014 Jan 19. The Federal Bureau of Investigation has decided to revise a controversial fact
sheet that declared its primary mission to be "national security," following criticism that the agency
seemed to be moving away from its longstanding role as the nation's preeminent law enforcement
agency.
The change emphasizes that stopping terrorism and battling more conventional domestic criminal
activity are both "primary functions" of the FBI. The lightning-fast revision should dispel any notion that
large bureaucratic organizations can only operate at a snail's pace: The fact sheet was updated less
than 48 hours after a report on it in Foreign Policy went viral last week. An FBI official confirmed that
the change was a direct result of the article.
"It's most accurate to say our primary functions are law enforcement and national security and that's
probably what it should've said all along," FBI spokesman Paul Bresson told FP. "We've always been
both."
The changes come after FP reported Jan. 5 that that FBI fact sheets declared "the primary function of
the FBI is national security."
Two days later, on Jan. 7, the language changed to "the primary functions of the FBI are national
security and law enforcement.
"That has to be some kind of a record," said Kel McClanahan, a Washington-based attorney who
alerted FP to the original fact sheet revisions. "Doing this so quickly and so obviously cover your ass-y
seems beneath them." For some critics of the U.S. national security state, the FBI's creeping advance
into counterterrorism since the 9/11 attacks has come at the cost of investigating other illegal activities
such as mortgage fraud, financial fraud, violent crime, and bank robberies. Those critics seized on last
week's report as evidence of the FBI's further drift toward counterterrorism.
"If the FBI's primary mission is national security,' what's the Department of Homeland Security's
mission?" asked the Government Accountability Project's Jesselyn Radack.
Others accused the agency of rebranding itself in order to extract more funding from Congress. "How
many terror plots are there in this country? Not that many, but that's where the big bucks are," said
Cenk Uygur, host of The Young Turks webcast. The article was also picked up by the Drudge Report
and the massive link-sharing site Reddit.
Bresson said critics were wrongly confusing a small change on a fact sheet with a substantive change
in priorities.
"You're talking about a fact sheet, not a change in policy," he said. "The FBI's mission today, and
throughout the course of our history, has been law enforcement and national security.
This may not be the final word on the issue. The fact sheets accompany every response the agency
gives to Freedom of Information Act requests. The latest change was discovered by FOIA expert
Shawn Musgrave who has already filed a public records request for the internal memos related to the
fact sheet revisions. We'll keep you posted.
ISRAEL, URENCO AND STUXNET
The truth about Israel's secret nuclear arsenal
Israel has been stealing nuclear secrets and covertly making bombs since the 1950s. And
western governments, including Britain and the US, turn a blind eye. But how can we expect
Iran to curb its nuclear ambitions if the Israelis won't come clean?
www.theguardian.com/world/2014/jan/15/truth-israels-secret-nuclear-arsenal
The Guardian / by Julian Borger
Stringer: Kees Kalkman / VDAmok / Utrecht NL / kees@amok.antenna.nl
Jan 21 2014 Jan 15. Deep beneath desert sands, an embattled Middle Eastern state has built a
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 38
covert nuclear bomb, using technology and materials provided by friendly powers or stolen by a
clandestine network of agents. It is the stuff of pulp thrillers and the sort of narrative often used to
characterise the worst fears about the Iranian nuclear programme. In reality, though, neither US nor
British intelligence believe Tehran has decided to build a bomb, and Iran's atomic projects are under
constant international monitoring.
The exotic tale of the bomb hidden in the desert is a true story, though. It's just one that applies to
another country. In an extraordinary feat of subterfuge, Israel managed to assemble an entire
underground nuclear arsenal now estimated at 80 warheads, on a par with India and Pakistan and
even tested a bomb nearly half a century ago, with a minimum of international outcry or even much
public awareness of what it was doing.
Despite the fact that the Israel's nuclear programme has been an open secret since a disgruntled
technician, Mordechai Vanunu, blew the whistle on it in 1986, the official Israeli position is still never to
confirm or deny its existence.
When the former speaker of the Knesset, Avraham Burg, broke the taboo last month, declaring Israeli
possession of both nuclear and chemical weapons and describing the official non-disclosure policy as
"outdated and childish" a rightwing group formally called for a police investigation for treason.
Meanwhile, western governments have played along with the policy of "opacity" by avoiding all
mention of the issue. In 2009, when a veteran Washington reporter, Helen Thomas, asked Barack
Obama in the first month of his presidency if he knew of any country in the Middle East with nuclear
weapons, he dodged the trapdoor by saying only that he did not wish to "speculate".
UK governments have generally followed suit. Asked in the House of Lords in November about Israeli
nuclear weapons, Baroness Warsi answered tangentially. "Israel has not declared a nuclear weapons
programme. We have regular discussions with the government of Israel on a range of nuclear-related
issues," the minister said. "The government of Israel is in no doubt as to our views. We encourage
Israel to become a state party to the nuclear Non-Proliferation Treaty [NPT]."
But through the cracks in this stone wall, more and more details continue to emerge of how Israel built
its nuclear weapons from smuggled parts and pilfered technology.
The tale serves as a historical counterpoint to today's drawn-out struggle over Iran's nuclear
ambitions. The parallels are not exact Israel, unlike Iran, never signed up to the 1968 NPT so could
not violate it. But it almost certainly broke a treaty banning nuclear tests, as well as countless national
and international laws restricting the traffic in nuclear materials and technology.
The list of nations that secretly sold Israel the material and expertise to make nuclear warheads, or
who turned a blind eye to its theft, include today's staunchest campaigners against proliferation: the
US, France, Germany, Britain and even Norway.
Meanwhile, Israeli agents charged with buying fissile material and state-of-the-art technology found
their way into some of the most sensitive industrial establishments in the world. This daring and
remarkably successful spy ring, known as Lakam, the Hebrew acronym for the innocuous-sounding
Science Liaison Bureau, included such colourful figures as Arnon Milchan, a billionaire Hollywood
producer behind such hits as Pretty Woman, LA Confidential and 12 Years a Slave, who finally
admitted his role last month.
"Do you know what it's like to be a twentysomething-year-old kid [and] his country lets him be James
Bond? Wow! The action! That was exciting," he said in an Israeli documentary.
Milchan's life story is colourful, and unlikely enough to be the subject of one of the blockbusters he
bankrolls. In the documentary, Robert de Niro recalls discussing Milchan's role in the illicit purchase of
nuclear-warhead triggers. "At some point I was asking something about that, being friends, but not in
an accusatory way. I just wanted to know," De Niro says. "And he said: yeah I did that. Israel's my
country."
Milchan was not shy about using Hollywood connections to help his shadowy second career. At one
point, he admits in the documentary, he used the lure of a visit to actor Richard Dreyfuss's home to get
a top US nuclear scientist, Arthur Biehl, to join the board of one of his companies.
According to Milchan's biography, by Israeli journalists Meir Doron and Joseph Gelman, he was
recruited in 1965 by Israel's current president, Shimon Peres, who he met in a Tel Aviv nightclub
(called Mandy's, named after the hostess and owner's wife Mandy Rice-Davies, freshly notorious for
her role in the Profumo sex scandal). Milchan, who then ran the family fertiliser company, never looked
back, playing a central role in Israel's clandestine acquisition programme.
He was responsible for securing vital uranium-enrichment technology, photographing centrifuge
blueprints that a German executive had been bribed into temporarily "mislaying" in his kitchen. The
same blueprints, belonging to the European uranium enrichment consortium, Urenco, were stolen a
second time by a Pakistani employee, Abdul Qadeer Khan, who used them to found his country's
enrichment programme and to set up a global nuclear smuggling business, selling the design to Libya,
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 39
North Korea and Iran.
For that reason, Israel's centrifuges are near-identical to Iran's, a convergence that allowed Israeli to
try out a computer worm, codenamed Stuxnet, on its own centrifuges before unleashing it on Iran in
2010.
Arguably, Lakam's exploits were even more daring than Khan's. In 1968, it organised the disappea-
rance of an entire freighter full of uranium ore in the middle of the Mediterranean. In what became
known as the Plumbat affair, the Israelis used a web of front companies to buy a consignment of
uranium oxide, known as yellowcake, in Antwerp. The yellowcake was concealed in drums labelled
"plumbat", a lead derivative, and loaded onto a freighter leased by a phony Liberian company. The
sale was camouflaged as a transaction between German and Italian companies with help from Ger-
man officials, reportedly in return for an Israeli offer to help the Germans with centrifuge technology.
When the ship, the Scheersberg A, docked in Rotterdam, the entire crew was dismissed on the pretext
that the vessel had been sold and an Israeli crew took their place. The ship sailed into the
Mediterranean where, under Israeli naval guard, the cargo was transferred to another vessel.
US and British documents declassified last year also revealed a previously unknown Israeli purchase
of about 100 tons of yellowcake from Argentina in 1963 or 1964, without the safeguards typically used
in nuclear transactions to prevent the material being used in weapons.
Israel had few qualms about proliferating nuclear weapons knowhow and materials, giving South
Africa's apartheid regime help in developing its own bomb in the 1970s in return for 600 tons of
yellowcake.
Israel's nuclear reactor also required deuterium oxide, also known as heavy water, to moderate the
fissile reaction. For that, Israel turned to Norway and Britain. In 1959, Israel managed to buy 20 tons of
heavy water that Norway had sold to the UK but was surplus to requirements for the British nuclear
programme. Both governments were suspicious that the material would be used to make weapons,
but decided to look the other way. In documents seen by the BBC in 2005 British officials argued it
would be "over-zealous" to impose safeguards. For its part, Norway carried out only one inspection
visit, in 1961.
Israel's nuclear-weapons project could never have got off the ground, though, without an enormous
contribution from France. The country that took the toughest line on counter-proliferation when it came
to Iran helped lay the foundations of Israel's nuclear weapons programme, driven by by a sense of
guilt over letting Israel down in the 1956 Suez conflict, sympathy from French-Jewish scientists,
intelligence-sharing over Algeria and a drive to sell French expertise and abroad.
"There was a tendency to try to export and there was a general feeling of support for Israel," Andre
Finkelstein, a former deputy commissioner at France's Atomic Energy Commissariat and deputy
director general at the International Atomic Energy Agency, told Avner Cohen, an Israeli-American
nuclear historian.
France's first reactor went critical as early as 1948 but the decision to build nuclear weapons seems to
have been taken in 1954, after Pierre Mends France made his first trip to Washington as president of
the council of ministers of the chaotic Fourth Republic. On the way back he told an aide: "It's exactly
like a meeting of gangsters. Everyone is putting his gun on the table, if you have no gun you are
nobody. So we must have a nuclear programme."
Mends France gave the order to start building bombs in December 1954. And as it built its arsenal,
Paris solds material assistance to other aspiring weapons states, not just Israel.
"[T]his went on for many, many years until we did some stupid exports, including Iraq and the
reprocessing plant in Pakistan, which was crazy," Finkelstein recalled in an interview that can now be
read in a collection of Cohen's papers at the Wilson Centre thinktank in Washington. "We have been
the most irresponsible country on nonproliferation."
In Dimona, French engineers poured in to help build Israel a nuclear reactor and a far more secret
reprocessing plant capable of separating plutonium from spent reactor fuel. This was the real
giveaway that Israel's nuclear programme was aimed at producing weapons.
By the end of the 50s, there were 2,500 French citizens living in Dimona, transforming it from a village
to a cosmopolitan town, complete with French lyces and streets full of Renaults, and yet the whole
endeavour was conducted under a thick veil of secrecy. The American investigative journalist
Seymour Hersh wrote in his book The Samson Option: "French workers at Dimona were forbidden to
write directly to relatives and friends in France and elsewhere, but sent mail to a phony post-office box
in Latin America."
The British were kept out of the loop, being told at different times that the huge construction site was a
desert grasslands research institute and a manganese processing plant. The Americans, also kept in
the dark by both Israel and France, flew U2 spy planes over Dimona in an attempt to find out what
they were up to.
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 40
The Israelis admitted to having a reactor but insisted it was for entirely peaceful purposes. The spent
fuel was sent to France for reprocessing, they claimed, even providing film footage of it being
supposedly being loaded onto French freighters. Throughout the 60s it flatly denied the existence of
the underground reprocessing plant in Dimona that was churning out plutonium for bombs.
Israel refused to countenance visits by the International Atomic Energy Agency (IAEA), so in the early
1960s President Kennedy demanded they accept American inspectors. US physicists were dispatched
to Dimona but were given the run-around from the start. Visits were never twice-yearly as had been
agreed with Kennedy and were subject to repeated postponements. The US physicists sent to Dimona
were not allowed to bring their own equipment or collect samples. The lead American inspector, Floyd
Culler, an expert on plutonium extraction, noted in his reports that there were newly plastered and
painted walls in one of the buildings. It turned out that before each American visit, the Israelis had built
false walls around the row of lifts that descended six levels to the subterranean reprocessing plant.
As more and more evidence of Israel's weapons programme emerged, the US role progressed from
unwitting dupe to reluctant accomplice. In 1968 the CIA director Richard Helms told President Johnson
that Israel had indeed managed to build nuclear weapons and that its air force had conducted sorties
to practise dropping them.
The timing could not have been worse. The NPT, intended to prevent too many nuclear genies from
escaping from their bottles, had just been drawn up and if news broke that one of the supposedly non-
nuclear-weapons states had secretly made its own bomb, it would have become a dead letter that
many countries, especially Arab states, would refuse to sign.
The Johnson White House decided to say nothing, and the decision was formalised at a 1969 meeting
between Richard Nixon and Golda Meir, at which the US president agreed to not to pressure Israel in-
to signing the NPT, while the Israeli prime minister agreed her country would not be the first to "intro-
duce" nuclear weapons into the Middle East and not do anything to make their existence public.
In fact, US involvement went deeper than mere silence. At a meeting in 1976 that has only recently
become public knowledge, the CIA deputy director Carl Duckett informed a dozen officials from the US
Nuclear Regulatory Commission that the agency suspected some of the fissile fuel in Israel's bombs
was weapons-grade uranium stolen under America's nose from a processing plant in Pennsylvania.
Not only was an alarming amount of fissile material going missing at the company, Nuclear Materials
and Equipment Corporation (Numec), but it had been visited by a veritable who's-who of Israeli
intelligence, including Rafael Eitan, described by the firm as an Israeli defence ministry "chemist", but,
in fact, a top Mossad operative who went on to head Lakam.
"It was a shock. Everyody was open-mouthed," recalls Victor Gilinsky, who was one of the American
nuclear officials briefed by Duckett. "It was one of the most glaring cases of diverted nuclear material
but the consequences appeared so awful for the people involved and for the US than nobody really
wanted to find out what was going on."
The investigation was shelved and no charges were made.
A few years later, on 22 September 1979, a US satellite, Vela 6911, detected the double-flash typical
of a nuclear weapon test off the coast of South Africa. Leonard Weiss, a mathematician and an expert
on nuclear proliferation, was working as a Senate advisor at the time and after being briefed on the
incident by US intelligence agencies and the country's nuclear weapons laboratories, he became
convinced a nuclear test, in contravention to the Limited Test Ban Treaty, had taken place.
It was only after both the Carter and then the Reagan administrations attempted to gag him on the
incident and tried to whitewash it with an unconvincing panel of enquiry, that it dawned on Weiss that it
was the Israelis, rather than the South Africans, who had carried out the detonation.
"I was told it would create a very serious foreign policy issue for the US, if I said it was a test.
Someone had let something off that US didn't want anyone to know about," says Weiss.
Israeli sources told Hersh the flash picked up by the Vela satellite was actually the third of a series of
Indian Ocean nuclear tests that Israel conducted in cooperation with South Africa.
"It was a fuck-up," one source told him. "There was a storm and we figured it would block Vela, but
there was a gap in the weather a window and Vela got blinded by the flash."
The US policy of silence continues to this day, even though Israel appears to be continuing to trade on
the nuclear black market, albeit at much reduced volumes. In a paper on the illegal trade in nuclear
material and technology published in October, the Washington-based Institute for Science and
International Security (ISIS) noted: "Under US pressure in the 1980s and early 1990s, Israel
decided to largely stop its illicit procurement for its nuclear weapons programme. Today, there is
evidence that Israel may still make occasional illicit procurements US sting operations and legal
cases show this."
Avner Cohen, the author of two books on Israel's bomb, said that policy of opacity in both Israel and in
Washington is kept in place now largely by inertia. "At the political level, no one wants to deal with it
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 41
for fear of opening a Pandora's box. It has in many ways become a burden for the US, but people in
Washington, all the way up to Obama will not touch it, because of the fear it could compromise the
very basis of the Israeli-US understanding."
In the Arab world and beyond, there is growing impatience with the skewed nuclear status quo. Egypt
in particular has threatened to walk out of the NPT unless there is progress towards creating a
nuclear-free zone in the Middle East. The western powers promised to stage a conference on the
proposal in 2012 but it was called off, largely at America's behest, to reduce the pressure on Israel to
attend and declare its nuclear arsenal.
"Somehow the kabuki goes on," Weiss says. "If it is admitted Israel has nuclear weapons at least you
can have an honest discussion. It seems to me it's very difficult to get a resolution of the Iran issue
without being honest about that."
A 'LOST DECADE' SINCE 9/11
Cyberexperts: a 'lost decade' since 9/11 to address infrastructure threats
Top critical infrastructure cybersecurity experts, who met in Miami this week, cite a surprising
number of control systems that are still exposed to hackers.
http://m.csmonitor.com/USA/2014/0117/Cyberexperts-a-lost-decade-since-9-11-to-address-infrastructure-threats
Christian Science Monitor / by Mark Clayton
Stringer: Martin Rudner [ret.] / Carleton University / Ottawa / www.carleton.ca/cciss
Jan 20 2014 Jan 17. Cyberexperts now are calling the years since 9/11 a lost decade in which
little was done to protect the vulnerable computer-controlled machines that operate critical US
infrastructure like the power grid and transportation and financial sectors against malicious
software, hackers, and nation-states.
Its now become a serious game of catch-up. Threats to the vital digital networks that run substations
and transmission lines, chemical plant processes, and air traffic control are growing dramatically,
leaving the United States at greater risk than at any time since 9/11, these industrial control system
experts say.
Yet the vulnerabilities in these industrial cybersystems have never been more widely acknowledged or
as well understood in their intricacy, say top critical infrastructure cybersecurity experts, who met in
Miami this week. Despite some gains, however, a surprising number of control systems for critical
infrastructure are still visible on the Internet and exposed to hackers, lacking even rudimentary digital
security.
Whats amazing is that, 13 years after 9/11, theres been almost no progress on the devices and
equipment that send commands or do the monitoring on these networks, says Dale Peterson, founder
of Digital Bond and organizer of the S4 conference.
While there's been some limited progress in shoring up security on servers and workstations that store
information for these industrial networks, the same can't be said of the huge mass of industrial
computerized controllers, switches, valves, instruments, and older legacy gear that were created
insecure by design, he adds. "Theyre terribly insecure at a time when threats against them are
increasing rapidly."
Other top experts point to the rapid development of cyberweapons by more than 30 nation-states, as
well as a profusion of new software exploits that make it far easier for nonexperts to hack control
systems.
For example, Jason Larsen, a researcher at Idaho National Laboratory in Idaho Falls, Idaho,
demonstrated a futuristic technique in which attackers could take over control of vital sensors in a
power plant without being detected.
Such demonstrations show that the development of offensive capabilities is moving ahead rapidly,
says Ralph Langner, the German industrial control system expert who was first to identify Stuxnet as a
cyberweapon targeting Irans nuclear fuel facilities in 2010. "But we don't see nearly as much
investment in defensive systems."
The idea of a lost decade is not fiction. Its a fact, he adds. "The worst thing is that this lost decade is
expanding."
Researchers at the Miami meeting also revealed new means that hackers would probably use in the
future to try to wrest control from legitimate operators. Major vulnerabilities continue to be found in
areas ranging from critical communications protocols used by the industrial control systems that
monitor and regulate digital switches across the power grid to the valves and motors across the water
purification sector.
Chris Sistrunk, a cybersecurity expert with Entergy, the big New Orleans-based electric utility, teamed
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 42
up with Adam Crain, an industrial control system security expert at the company Automatak, to explain
how specialized detection fuzzer software that they had created enabled them to spot previously
invisible vulnerabilities in a key communications protocol. That protocol, called DNP3, is widely used
by utilities to manage the power grid and water sectors in the US and Australia.
Rather than being robust, as previously thought, DNP3 was shown to be rife with vulnerabilities. Any
one of those weaknesses could be used by an attacker to gain control of a utilitys master controller,
which might oversee hundreds or thousands of devices, and wreak havoc across a utilitys industrial
network and the section of the grid it controlled, the researchers said.
But the utility industry and control-system and equipment vendors are at least starting to take such
vulnerabilities seriously, Mr. Sistrunk says. In fact, the majority of industrial control system companies,
when confronted with evidence that the protocol being used in their systems was like Swiss cheese,
moved swiftly to patch the vulnerabilities an unusual level of responsiveness from an industry that
has sometimes stonily resisted fixing its products, he and other experts say.
A lot of similar things were done as far back as 10 years ago, but there was no traction within the
industry, Sistrunk says. But we are starting to see, just now in the last few years since Stuxnet
some companies have started to decide, hey, we need to make changes.
Other glimmers of a shift can also be seen in the increasing number of large control system vendors
creating equipment that, for the first time, has serious security features.
Moreover, several big industrial control system manufacturers like Siemens and General Electric have
created cyber-emergency response teams to fix vulnerabilities.
Were serious about developing products that have good cybersecurity in them, says an official with
a company that makes digital controllers, who asked to remain anonymous because he was not
permitted to speak to the press. Were seeing demand for these devices increase.
But one researcher, who also asked for anonymity for the same reason, says that careful analysis of
the software code produced by industrial control system vendors shows any perceived gains so far to
be tenuous.
You would think that the vendor equipment would keep getting better after doing several rounds of
testing, but the new software code inside them isnt significantly better than the old code in terms of
vulnerabilities, the researcher says. The bug rate has fallen, but quite a number of the vendors are
producing bad code like it was 10 years ago.
For these and other reasons, Mr. Peterson, Mr. Langner and other thought leaders in the industry are
leery of touting the recent evidence of progress. While he rails against government inaction on
mandating that companies secure their critical infrastructure, Langner concedes that Obama
administration directives have had some limited positive impact, even though he considers them to be
far too weak for example, a presidential directive to have the National Institute of Standards and
Technology define critical infrastructures standards that could be followed voluntarily by industry.
Theres been some movement, but its small compared to the offensive capabilities now being
developed, he says.
Government-mandated standards developed in recent years by the North American Electric Reliability
Corp., an electric utility industry watchdog, have also convinced utilities that they must make some
progress in cybersecurity, if reluctantly because of the added cost.
Yet the Department of Homeland Security has yet to require that older insecure-by-design systems
must be replaced in a time frame of a few years, Peterson says. Instead, government, as well as
cybersecurity industry expert apologists, continue to predict that it will take decades to make the
transition.
You read the articles from industry organizations talking about it, he says. Obama talks about how
important it is. Yet no one says we actually have to fix these things.
"Its either critical infrastructure or its not. You cant have it both ways.
NSA PHONE PROGRAM PROVIDED 1,000 TERROR TIPS A YEAR TO FBI
Newly Declassified Documents Were Released Late Friday
http://online.wsj.com/news/articles/SB10001424052702304757004579330971503849030
Wall Street Journal / by Devlin Barrett
Stringer: Martin Rudner [ret.] / Carleton University / Ottawa / www.carleton.ca/cciss
Jan 20 2014 Jan 20. The National Security Agency's phone-surveillance program generated more
than 1,000 tips a year to the Federal Bureau of Investigation, according to newly declassified
documents.
The court documents, released late Friday by the Office of the Director of National Intelligence, are
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 43
frequently repetitive and contain a significant number of redacted sections, but also contain intriguing
footnotes suggesting how frequently the NSA's phone program leads to or supplements domestic
terrorism probes.
U.S. President Barack Obama speaks about the NSA and intelligence agencies surveillance techni-
ques in Washington, DC, on Jan. 17. Agence France-Presse/Getty Images
In 2006, the phone records program generated an average of two such tips a day, according to a
document from November of that year. That would mean more than 700 a year.
"With respect to any information the FBI receives as a result of this order (information that is passed or
"tipped" to it by NSA), the FBI shall follow minimization procedures,'' the November 2006 document
states. A footnote to that statement adds the NSA "expects that it will continue to provide on average
approximately two telephone numbers a day to the FBI."
The documents show that the following year the estimate jumped to three a day, which would mean
more than 1,100 such tips a year.
The document were released was part of a pre-existing effort by the Obama administration to reveal
where possible more details about how the once-secret phone program works, one part of its defense
of the NSA's activities. They were made public just hours after a Friday speech by President Barack
Obama that outlined a host of changes to intelligence programs in the wake of revelations from former
NSA contractor Edward Snowden.
The biggest change the president has called for would be to move the possession of Americans'
phone records out of the government to some still-undecided entity. These kinds of details about how
the program worksin particular, those that point to its usefulness or otherwise-will be central to the
coming debate in Congress about how or whether to implement Mr. Obama's ideas.
The documents don't describe the quality of tips provided by the NSA, or how often the FBI launched
domestic criminal investigations because of the NSA's information. They do suggest the agency has
been active in forwarding investigative suggestions to the FBI. A recent presidentially appointed review
of the program found the NSA phone surveillance program had not been essential to preventing
attacks. The program's defenders argue it has been an important counterterrorism tool.
On Sunday, congressional leaders said they were skeptical of Mr. Obama's proposal to take
possession of Americans' phone records out of the government's hands. That is an early indication of
how difficult it may be for Mr. Obama to make the changes he has described.
Sen. Dianne Feinstein (D., Calif.) told NBC's "Meet the Press" on Sunday that she wasn't sold on the
idea of making changes to where the phone data is warehoused.
"I think that is a very difficult thing," she said. "The whole purpose of this program is to provide
instantaneous information to be able to disrupt any plot that may be taking place."
Ms. Feinstein chairs the Senate intelligence committee, and her concerns were shared by her
counterpart in the House, Rep. Mike Rogers, who called moving the phone record data out of
government hands "a huge problem."
Mr. Rogers (R., Mich.) said the president's speech left key issues unresolved. "We really did need a
decision on this but what we got was lots of uncertainty,'' he said.
The NSA's program is designed to find connections between terror suspects. The program doesn't
track the names linked to numbers, but the FBI can find out that information when it is given a number
to investigate.
The "three a day'' average continued until March 2009, the last time it is referenced in the unredacted
portions of the documents. The documents don't offer any clues as to why officials stopped including
that estimate. The same year, a secret surveillance court ordered a major review of the program after
learning there were significant differences between what it was doing and what government lawyers
had previously told the court.
In 2010, the court authorizations change again, dropping the previous language about the NSA tipping
the FBI, and instead refer to it only as "information.''
An FBI spokesman didn't immediately comment on the documents.
Currently, the NSA gathers U.S. phone records from the major phone companies and assembles it in
a giant database. The president said that data should no longer be held by the government, and
ordered Attorney General Eric Holder to propose a new arrangement.
Like many of the ideas contained in his speech, moving the phone data could require passage of new
legislation by Congress. What happens there in coming weeks will more than any executive actions
determine how far-reaching the NSA revamp will be. The early reaction shows how much remains
subject to the political process.
The phone companies are opposed to taking responsibility for such a database, and doing so could
create new technical challenges, according to intelligence officials.
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 44
KAREGEYA MURDER CASE AT SENSITIVE STAGE
www.sabc.co.za/news/a/7ffae80042970796a636fe56d5ffbd92/Karegeya-murder-case-at-sensitive-stage:-Hawks
SABC
Stringer: Kees Kalkman / VDAmok / Utrecht NL / kees@amok.antenna.nl
Jan 20 2014 Jan 17. South Africas elite crime fighting unit, Hawks, says their investigation into the
murder of Rwandan ex-spy chief, Colonel Patrick Karegeya, is at a sensitive stage. Karegeyas body
was found at an upmarket hotel in Sandton on New Years Day.
Hawks spokesperson, Paul Ramoloko has denied reports that quoted the Mozambican police's
spokesperson, Joao Machava, as saying four people suspected of involvement in the murder had
been arrested.
Mozambican authorities could not be reached for comment.
Ramoloko says the South African police are following up all leads. Our investigation into the death of
Karegeya has reached a more sensitive stage. The arrests which are being spoken about in
Mozambique do not exist. We are in direct contact with our Mozambican counterparts and we have not
made any arrests yet, says Ramoloko.
Meanwhile, Karegeya will be laid to rest in Johannesburg on Saturday.
Family spokesperson, David Batenga says they would have liked to bury Karegeya in his country of
birth, however, there have been issues related to his dual citizenship.
He was born in Uganda and grew up there. He later moved to Rwanda, where he was a spy chief. He
has been living in South Africa as a refugee since 2008. Ideally, he wouldn't go back to Rwanda for
the burial, but we had expected to bury him in Uganda. This never happened because of political
issues that are connected between Uganda and Rwanda, says Batenga.
DIE ERMORDUNG VON KAREGEYA
Erwrgt im Hotelzimmer
Die rtselhafte Ermordung des Ruandischen Exilpolitikers Patrick Karegeya in Sdafrika
schlgt Wellen. Der Verdacht richtet sich gegen Ruandas Regierung.
http://www.taz.de/!131069/
Die Tageszeitung / by Francois Misser
Stringer: Kees Kalkman / VDAmok / Utrecht NL / kees@amok.antenna.nl
Jan 20 2014 Jan 15. Die Leiche lag erwrgt auf dem Hotelbett, das dazugehrige blutverschmierte
Handtuch und ein Strick lagen im Safe. Patrick Karegeya hatte offensichtlich nicht Selbstmord
begangen, bevor er in der Nacht zum 2. Januar im Hotel Michelangelo Towers im sdafrikanischen
Johannesburg tot aufgefunden wurde.
Der gewaltsame Tod des 53-jhrigen Ruanders, ehemals ein enger Vertrauter von Ruandas Prsident
Paul Kagame und zuletzt einer seiner grten Feinde, schlgt hohe Wellen.
Ruandas Botschafter in Sdafrika, Vicent Karega, dementiert zwar, dass seine Regierung irgendetwas
damit zu tun htte; aber in Ruandas Hauptstadt Kigali sagte Prsident Kagame am vergangenen
Wochenende auf einem US-amerikanischen Prayer Breakfast, ohne Namen zu nennen: Man kann
nicht Ruanda verraten und damit durchkommen. Es hat Konsequenzen, wenn man sein Land verrt.
Ruandas Regierung benutzt Karegeyas Tod als Warnung an Dissidenten. Der ruandische Botschafter
in London, William Nkurunziza, bezeichnete Karegeya als Staatsfeind.
Er kannte alle Geheimnisse der RPF
Karegeya ist in Ruandas Geschichte eine Schlsselfigur. Niemand, auer Prsident Paul Kagame
selbst, kannte so viele Geheimnisse der regierenden ehemaligen Tutsi-Guerilla RPF (Ruandische
Patriotische Front), die Ruanda seit Beendigung des Vlkermords an den Tutsi 1994 regiert. Mit RPF-
Fhrer Kagame lebte er einst im ugandischen Exil; von 1994 bis 2004 leitete er Ruandas Auslands-
geheimdienst bis zu seiner Verhaftung wegen Ungehorsam und dem Entzug seines Rangs als
Oberst.
Karegeya fand zunchst Zuflucht in Uganda, bevor er 2007 Asyl in Sdafrika erhielt. Zu ihm stie drei
Jahre spter ein anderes in Ungnade gefallenes ehemaliges Mitglied des engsten ruandischen
Machtzirkels: Exgeneralstabschef Faustin Kayumba Nyamwasa. General Kayumba fiel im Juni 2010,
whrend der Fuball-WM, beinahe einem Anschlag zum Opfer und machte anschlieend Ruandas
Regierung dafr verantwortlich.
Ein sdafrikanischer Ermittler sagte spter aus, ein ruandischer Geschftsmann habe ihn bestechen
wollen, nachdem ruchbar geworden war, dass er die sechs mutmalichen Tter bezahlt habe. Kein
Wunder, dass der Mord an Karegeya nun einen hnlichen Verdacht erregt.
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 45
Nach seinem Tod das Handy benutzt
Nach Angaben seines Neffen David war Patrick Karegeya am Silvesterabend mit einem alten Freund
verabredet: mit Appolo Kiririsi Gafaranga, einem Geschftsmann, den er noch aus Ruanda kannte. Als
Karegeya am nchsten Tag nicht ans Telefon ging, holten Freunde seinen Neffen, und der fand die
Leiche, aber nicht Karegeyas drei Handys und auch nicht das von Kiririsi.
Nach einem Bericht des franzsischen RFI-Rundfunks hat jemand Karegeyas Mailbox zwei Tage nach
seinem Tod geffnet. Kiririsi ist verschwunden und wird in Sdafrika als Zeuge gesucht. Ruandas
Exilopposition ist nun davon berzeugt, dass Kiririsi auf Karegeya angesetzt wurde.
Seit Jahren verdchtigt Ruandas Regierung Karegeya und Kayumba, aus dem sdafrikanischen Exil
heraus Verbindungen zu den ruandischen Hutu-Milizionren der FDLR (Demokratische Krfte zur Be-
freiung Ruandas) im Kongo zu unterhalten, um einen bewaffneten Kampf in Ruanda zu beginnen.
Ihre Organisation RNC (Ruandischer Nationalkongress) ist nach eigenen Angaben mit der nicht zuge-
lassenen ruandischen Oppositionspartei FDU (Vereinigte Demokratische Krfte) verbndet, deren
Fhrerin Victoire Ingabire vor Kurzem in Kigali wegen Verschwrung zu 20 Jahren Haft verurteilt wur-
de; mehrere Mitangeklagte hatten vor Gericht bekannt, zur FDLR zu gehren.
Untergrundarmee mit UN-Geldern?
Geld fr den Aufbau einer Untergrundarmee knnte Karegeya, wie vor Jahren ugandische Medien
berichteten, ber einen UN-Beratervertrag im Umfang von 4 Millionen Dollar zur Anwerbung privater
Sicherheitskrfte zum Schutz der bergangsregierung von Somalia erworben haben ein Auftrag,
den der Ruander gemeinsam mit seinem ugandischen Geschftspartner Salim Saleh, Halbbruder des
ugandischen Prsidenten, ergattert haben soll.
Man kann angesichts dessen nachvollziehen, warum Ruandas Regierung weder Sdafrika noch der
UNO traut und schon gar nicht der sdafrikanisch dominierten neuen UN-Eingreifbrigade im Ostkon-
go, die letztes Jahr die mutmalich von Ruanda untersttzten M23-Rebellen besiegte.
Alles deutet darauf hin, dass Kigali vom Mord an Karegeya zumindest profitiert. Dennoch gibt es kei-
nen eindeutigen Beweis seiner Tterschaft. Es ist wahr, dass ruandische Oppositionelle im Exil hufig
zu Tode kommen. Aber von Ruandas ehemaligem Oberspion wrde man erwarten, dass er alle Tricks
kennt. Am Samstag wird Karegeya in Sdafrika beerdigt.
UK DEPORTS TAIWANESE INTELLIGENCE AGENT
AFP
www.sinodaily.com/reports/UK_deports_Taiwanese_intelligence_agent_government_999.html
Sino Daily
Stringer: Frank Slijper / Campaign Against Arms Trade / Groningen NL / frank.slijper@hetnet.nl
Jan 20 2014 Jen 19. A young Taiwanese military intelligence officer who had been on the country's
'wanted' list after failing to return from an overseas trip has been deported by the British authorities,
the government said.
Yeh Mei, a lieutenant with Taiwan's Military Intelligence Agency was deported on Saturday for
overstaying her visa and escorted to Taiwan by British personnel, the Taiwanese foreign ministry said
in a statement.
"Upon arrival, Yeh was taken to Taichung by officials from the prosecutors' office there," it said in a
statement, referring to the city in central Taiwan where she had served her duty before taking an
overseas sightseeing trip and going AWOL in June 2012.
The ministry did not provide further details, but an investigation bureau officer familiar with the legal
process told AFP that she expected Yeh to be placed in custody for questioning.
Local TVBS news network showed Yeh, reported to be 33, being escorted by security officials upon
her arrival at the airport. She covered her head with a jacket as she was handcuffed and taken away.
Yeh had been put on a wanted list by a local court after she failed to return for duty after an overseas
trip.
She told the Taipei-based Apple Daily that her colleagues had been hostile to her and her repeated
attempts to drop out had been rejected by her boss.
She had claimed that she could be sentenced to death and sought political asylum with the British
authorities, but the bid was rejected, foreign ministry officials said.
When Yeh first disappeared, there was speculation in Taiwan's media that she may have joined
China's spy network.
But the country's Military Intelligence Agency has attributed Yeh's disappearance to 'personal factors'.
China still claims Taiwan as part of its territory awaiting reunification, by force if necessary, even
though the two sides have been governed separately since the end of a civil war in 1949.
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 46
Ties have improved markedly since Ma Ying-jeou of Taiwan's China-friendly Kuomintang party came
to power in 2008.
But the former arch-rivals still spy on each other. In 2012 Taiwan's top court rejected an appeal by
former army general Lo Hsien-che, who was jailed for life in the toughest punishment meted out in an
espionage case in decades.
He was suspected of handing over to China information relating to a project that gave the Taiwanese
military some access to US intelligence systems
BEYOND SNOWDEN: A NSA REALITY CHECK
http://www.worldaffairsjournal.org/article/beyond-snowden-nsa-reality-check
World Affairs Journal / by Michael V. Hayden [Director of the CIA from 2006 to 2009]
Stringer: Martin Rudner [ret.] / Carleton University / Ottawa / www.carleton.ca/cciss
Jan 19 2014 Jan-Feb. The October 10, 2013, edition of many American papers featured a photo of
fugitive NSA contractor Edward Snowden in Russia, surrounded by former NSA executive Thomas
Drake, former FBI agent Coleen Rowley, and former CIA analyst Ray McGovern.
The three former government officials were in Russia to present Snowden with something called the
Sam Adams Award for Integrity in Intelligence. All three had previously won the award themselves,
along with WikiLeaks founder Julian Assange and Katharine Gun, a translator for the British
intelligence agency GCHQ who alleged NSA plans to tap the communications of UN members in the
run-up to the Iraq War.
A week earlier, I had been a panelist at a Washington symposium on Snowden. At that session,
moderator David Ignatius pointed out that Snowden was on the short list for the European
Parliaments Sakharov Prize for Freedom of Thought. I couldnt help but say, I must admit, in my
darker moments over the past several months, Id also thought of nominating Mr. Snowden, but it was
for a different list.
While many Americans applaud Edward Snowdens leaks, many have also unwisely discounted the
essential role that intelligence plays in the nations security, as well as the perils of such leaks.
That comment lit up the blogosphere as supporters of Snowden accused me of wanting to put him on
a kill list. That thought was far from my mind. But it showedas did the awards he has been
nominated for and receivedthat Snowdens revelations have struck a very deep chord in global
thought. While the new head of Britains MI-5 warns that Snowdens revelations are a gift to
terrorists, for instance, ACLU Executive Director Anthony Romero believes that Edward Snowden has
done this country [the US] a service.
The depth of feeling was shown in a House of Representatives vote in July where nearly sixty percent
of Democrats and forty percent of Republicans voted to defund the NSA metadata program that
Snowden had revealed. The program survived by a mere twelve votes.
Despite continuing debates over debt limits and government shutdowns, the reach of NSA surveillance
has become a hot and enduring topic. And foreign leaders are weighing in on the scope of alleged
NSA activities against them.
Snowdens disclosures no doubt accelerated and intensified this discussion, but it had long been
coming. By the late 1990s, the NSA was well aware that legitimately targetable foreign
communications (like Soviet high command transmissions to ICBM units) were no longer confined to
isolated adversary networks. It knew, too, that modern targets (like al-Qaedas e-mails) coexisted with
innocent and even constitutionally protected messages on integrated global communication networks.
The NSA knew that it would never get the power, legally or technically, to acquire the one unless it
could show it had the discipline to respect and protect the other.
The dilemma only got more acute with the events of 9/11, when the enemy demonstrated that he was
already inside the gates, and even when not physically in the country, terrorists made use of e-mail
accounts whose servers were here.
The changes in technology and the appearance of new adversaries to go along with old ones, who
continued to pose problems, was accompanied by cultural shifts on matters of transparency and
espionage, particularly where they touched on the digital privacy of a new generation of Americans.
At one point while at the CIA, I asked members of our civilian advisory board to examine whether or
not they believed America would be able to conduct espionage in the future inside a broader political
culture that every day seemed to demand more transparency and more public accountability from
every aspect of national life. When they reported back to me a few months later, they said that they
werent sure.
The coming debate Edward Snowden accelerated will no doubt be consumed with talk about whether
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 47
or not the NSA should keep metadata (the call records but not the content) of American phone calls for
five years or fewer or not at all. And there will be heated discussion about when and how and by whom
this data should be accessed.
There will be passionate calls for an ombudsman of some type for the FISA court, and there will be
demands that the proceedings and decisions of that tribunal be made more public.
Foreign leaders will continue to insist on explanations of American activities, and even on guarantees
that they will not be repeated.
All of these matters are important in their own right, and decisions on each could carry weighty
consequences for both freedom and security. But it is also true that these questions are just symptoms
of a much larger issue: the future of espionage and, specifically, the future of American espionage.
What will US spies be expected to do? What will they be allowed to do? How will the governed give
their consent in these weighty issues?
In short, the stakes are even higher than some people imagine. So this debate should proceed
carefully. Sweeping charges, bumper sticker explanations, score settling, demagoguery, and outright
ignorance have characterized this discussion so far. The consequences of such irresponsibility,
intended and otherwise, will be far-reaching.
With that in mind, let me offer some thoughts about things we would be wise to keep in mind as we go
forward. There is no pretense here to provide answers to the debate but it is my hope that all the
stakeholders here, including the broad American public, will make sure that they are aware of all the
factors bearing on the problem as the conversation we are now fated to have takes place.
Context matters.
Mike Rogers, chairman of the House Intelligence Committee, points out that this debate could not be
coming at a worse time, given that we are in the middle of a perfect storm of public concern over
government overreach.
Hes right. Questions about NSA data gathering are coming fast on the heels of accusations of the IRS
scandal and FBI overreach in gathering the call records of the Associated Press and labeling a Fox
News reporter as a co-conspirator in a case brought under the Espionage Act.
The respected editor Len Downie recently filed a scathing report for the Committee to Protect
Journalists labeling the current administration as the most intrusive and controlling since the Nixon
years, with a significant uptick in reporters sources fearing they will be tracked by government
surveillance.
President Obama has also been aggressive in using his executive authority to enact regulations
rejected by Congress, to make recess appointments when Congress does not consider itself to be in
recess, and to override the views of the Department of Defense in defining US war making in Libya so
that it will not be considered a war under the War Powers Act.
Defenders of NSA surveillance, which is now seen as just one more element in this perfect storm, will
be battling uphill in this environment, especially if the public is not able to dissociate this activity from
other offenses, real or imagined.
Put another way, a balanced discussion is going to be hard and extraordinary effort will be required if
metadata collection and programs like PRISM, XKeyscore, Boundless Informant, and others revealed
by Snowden are to be judged on their merits and not merely swept away by the broader politics of the
day.
And for a fact-based discussion to have any chance of taking place, the administration and the intelli-
gence community are going to have to be very forthcoming with facts, far more than they traditionally
have been.
Director of National Intelligence James Clapper and NSA Director Keith Alexander seem to know this.
Data is being posted on a new website, redacted FISA court opinions are being made public, and
General Alexander (in particular) has been effectively speaking to public audiences.
But the intelligence community has enormous distance to make up in this effort. The Guardian of
London and several American newspapers have rolled out charge after charge, catching the
administration flatfooted because it chooses to respond through a cumbersome interagency vetting
process that often produces answers that are tepid, tardy, or stripped bare of content.
Meanwhile, media coverage of the scandal is ever escalating and always reaching for more
sensational revelations. A Guardian headline in July ominously and hyperbolically described NSAs
XKeyscore program as collecting nearly everything a user does on the Internet. The Los Angeles
Times, USA Today, and the Washington Post all enthusiastically followed up on a September
screecher by Glenn Greenwald, Laura Poitras, and Ewen MacAskill, also in the Guardian: NSA
Shares Raw Intelligence Including Americans Data with Israel.
Another page-one headline in the August 15th edition of the Washington Post screamed that the NSA
was breaking privacy rules thousands of times per year. I parsed the data for that one in a short
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 48
piece for USA Today and pointed out that:
All of the incidents were inadvertent; no one claims that any rules were intentionally violated. All of the
incidents were discovered, reported, and corrected by NSA itself.
Fully two-thirds of the incidents were comprised of roamers legitimately targeted foreigners who
were temporarily in the US (and thus temporarily protected by the Fourth Amendment).
Picture a cellphone call, not collected in the air in the US, but made by such an individual that is routed
back to its home network before heading to its intended recipient. It looks every inch like a foreign call
and is collected as such, until something in the calls content or the physics of the intercept suggests
that its origins are herethen collection is stopped and the inadvertent collection (the privacy
violation) reported.
Other violations included database queries, searches of data already collected. The document the
Post relied on reveals that in one quarter, there were one hundred and fifteen incidents of queries
being incorrectly entered, mistakes like mistyping or using too-broad search criteria. Thats one
hundred and fifteen out of sixty-one million inquiries.
The backstory on the USA Today op-ed is instructive. The Post broke its story on Thursday. USA
Today wanted to run its point-counterpoint editorial the following Monday. They invited the NSA to
write the contrary view, an opportunity that the agency eagerly accepted. By late Saturday night,
though, the agency despaired of getting interagency clearance for its response and the newspaper
then turned to me.
I wrote the piece on Sunday morning and had it cleared for classification that afternoon. That the NSA
was prevented from doing the same thing, especially given the destructive paranoia about intelligence
gathering abroad today, is beyond explanation.
There are reasons to keep some things secret but, in the current climate, the sum of individually
defensible classification decisions is creating a lack of public confidence in the intelligence
communitys lawfulness. The community will have to show more transparency, in effect trading a
measure of operational impact in return for building a national consensus in support of its activities.
Another surprising aspect of the NSA debate is who is and who is not participating in it.
The most vocal supporters of the NSA program are in Congress (as are, admittedly, its most vocal
critics). The chairs and ranking members of the two intelligence oversight committees have been
steadfast in their public explanation and defense of the agencys efforts.
House Chairman Mike Rogers has been particularly active in describing and defending both the NSAs
activity and his committees oversight of it.
Rogers, along with his senior Democrat, Dutch Ruppersberger, and their colleagues on the committee,
have come in for their own share of criticism. Justin Amash, a Republican from Michigan (like Rogers),
recently bashed the committee as the enemies of Congress...covering up for the administration.
The same syndrome can be seen on the Senate side, where Dianne Feinstein and Saxby Chambliss
(chair and vice chair of the Senate Intelligence Committee) have been equally supportive of the NSA
and equally criticized for this support. They were likely among the targets of Senator Ron Wydens
recent condemnation of defenders of the status quo and the business as usual brigade, the Oregon
Democrats description for intelligence officials and their supporters. That Wyden is a member of the
Senate Intelligence Committee and has received secret briefings made the remark even more
stinging.
There are members of the executive branch who are (or should be) even more knowledgeable than
Congress, and their silence has been puzzling. If Vice President Biden has made any public defense
of the NSA, I must have missed it. The secretary of defense, for whom the NSA director works, has
said little, and officials like the national security adviser and the secretary of state, who actually help
set intelligence requirements and receive reports based on that tasking, have been silent. Where do
they think this stuff comes from?
The president has actually defended the NSA...to a point. Shortly after the Snowden debacle began
in June, he took a single question right before meeting Chinese President Xi Jinping in California. His
extemporaneous response about NSA activity was carefully crafted, technically accurate (not an easy
matter), and constituted a calm but forcefully given defense of the agency and its programs.
The president continued his response to query defense in interviews with CNN and with Charlie
Rose, supporting NSA efforts along lines similar to those he laid out in California, although he was
now admitting that the capabilities of the NSA are scary to people.
By September, when he was asked a question before a foreign audience in Sweden, the presidents
response was a bit more apologetic and defensive. He appeared to be willing to walk back some of the
support he had given and took pains to point out repeatedly that ...what Ive said domestically and
what I say to international audiences is...just because we can do something doesnt mean we should
do it.
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 49
On matters such as these, intelligence professionals believe that they have a social contract with their
government, that when they do these lawful but politically edgy things, someone will have their back. I
suspect, for instance, that when President Bush launched the metadata program in 2006, and the
PRISM effort in 2008, he told General Alexander to take these authorities and defend America. Im
sure he added that if they ever became politically contentious, it would be his job, not Alexanders, to
defend the agency. (Im sure, because this is exactly how President Bush dealt with the programs for
which I was responsible.)
When President Obama embraced these efforts in 2009, he embraced that social contract as well,
even though it might be more difficult for him to fulfill it because it would cut against his base more
than it would have for President Bush. More difficult because such seemingly intrusive surveillance
also cuts against the narrative of al-Qaeda is on the run and the tide of war is receding.
Its also made more difficult by the presidents 2008 campaign, which sought to put distance between
himself and the actions of the Bush administration. There is no doubt he intended to be judgmental in
his first inaugural when he said, As for our common defense, we reject as false the choice between
our safety and our ideals.
Compare that to his June explanation of NSA activities: But I think its important for everybody to
understand...that there are some trade-offs involved. ...you cant have a hundred percent security
and also then have a hundred percent privacy and zero inconvenience. You know, were going to have
to make some choices as a society.
The later statement is certainly true and it doesnt necessarily contradict the earlier one, but overall
there has been a disappointing silence from the administration, leaving General Alexander and
Director Clapperwhen they are permitted to speakstrangely alone.
Some of the most irritated (and irritating) responses to the Snowden revelations have come from
abroad, from national leaders complaining about real or imagined intrusions by NSA collection
programs. So many foreign leaders, or intelligence heads acting on behalf of foreign leaders, have
come to Washington to seek explanations that there were scheduling challenges for a while.
Lets be clear. Espionage is an accepted international practice and the US Constitutions Fourth
Amendment protection against unreasonable search is not an international treaty.
Actually, President Obama nailed it when he noted in Sweden that some of the folks who have been
most greatly offended publicly we know privately engage in the same activities directed at us.... And
he got to the heart of the matter when he pointed out that even though we may have the same goals,
our means are significantly greater.
But it is also clear that the administration is rethinking how the NSA targets global communications. In
addition to the just because we can doesnt mean we should meme, the president admitted that there
were questions in terms of whether were tipping over into being too intrusive with respect to theyou
know, the interactions of other governments.
In response to specific allegations of spying against Brazil and Mexico, President Obama was
conciliatory. In a statement made from St. Petersburg during his Russia visit, he said: I understand
the concerns of the Mexican and Brazilian people, and that we will work with their teams to resolve
what is a source of tension.
Clearly, there is necessarily at least a little theater involved here. Public allegations of specific
espionage require victims to be outraged. They also require perpetrators to look into the matter.
More troubling was Mexican President Pea Nietos report, based on a personal conversation, that
President Obama promised to apply corresponding sanctions (apparently to the intelligence
community) if the allegations proved true.
Let me put this in the starkest possible terms. American signals intelligence is limited by the demands
of the Fourth Amendment and defined by the demands of American security. Absent political guidance
to the contrary, if you are not protected by the US Constitution, and your communications contain
information that would help keep America free and safe, information that would not otherwise be made
available to the US government, then game on. Your privacy is simply not the concern of the NSA
director.
When I was at the NSA, I received my fair share of political guidance to stand down on certain efforts,
but all the parties seemed to agree that we should be careful not to overachieve here. American
intelligence suffered mightily in the 1990s when human intelligence collectors were told to stand down
and not talk to bad people. We would create the same effect again if we now tell signals intelligence
collectors they cannot listen to good people.
The president has launched a review group to assess whether American technical collection
appropriately accounts for other policy considerations, such as the risk of unauthorized disclosure and
our need to maintain the public trust. The group has strong leadership, but there are lingering fears
within the intelligence community that its report will be used to walk back current protocols for data
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 50
collection.
It may be tough for us to stand our ground. The president has undoubtedly been embarrassed by
some of these revelations, and his administration at times even seems surprised by the extent of NSA
activities.
Publicly, both the president and his administration have taken a beating, especially in Europe. Coming
on top of drones and targeted killings, the NSA story may have ended the European love affair with
President Obama. An embittered contributor to Der Spiegel put it this way: If this happened during the
administration of George W. Bush, we could at least think, Its just Bush....There is a better Ameri-
ca. Now we know: There is only one America.
I hope hes right.
In the most iconic scene in one of Americas most iconic movies, High Noon, Marshal Will Kane,
played by Gary Cooper, throws his badge into the dust as he prepares to abandon the ungrateful town
he has defended for years.
Kane had sought the support of the townsfolk as murderous Frank Miller and his gang descended on
them. He got no such support; they even objected to his standing up against the gang on his own, as it
might endanger them. Still Kane went into harms way, refusing to flee, finally killing Miller and his
henchmen.
In the last scene, the townsfolk are almost tripping over themselves to congratulate and praise Kane
for his heroism. He stares them down, removes his badge, and climbs aboard a buckboard driven by
his new wife (Grace Kelly) and heads out of town.
The folks at Fort Meade today have to feel a little bit like Will Kane. They dont seem to be getting
much help against the current threats to them.
House Intelligence Chairman Mike Rogers summed it up pretty well at a recent panel, noting that the
United States had the only intelligence services on the planet that are under siege from its
adversaries and from its internal support system, the citizens of the United States.
It should trouble all Americans when the NSA director and his deputy feel it necessary to send a letter
to the families of all NSA officers to assure them that their loved ones are heroes, not criminals.
There is no doubt that these are difficult issues, and the fundamental questions brought on by new
technologies and new enemies remain to be resolved. But the NSA played by the rules. Its actions
were anchored in statute (the 2006 renewal of the Patriot Act and the 2008 FISA Amendment Act),
briefed to all members of the congressional committees, and overseen by an unprecedented level of
court supervision. And yet a New York Times op-ed casually leads with the headline The Criminal
NSA.
Even President Obamas efforts to defend the agency have had a pointed edge at times. At an August
press conference, the president praised the men and women of the intelligence community as patriots
and then, understandably and correctly, characterized those who have raised their voices against
various NSA programs as patriots, too.
Fair enough, in some general rhetorical sense. But to the people at Fort Meade, the presidents words
just equated his own workforce with those who routinely accuse that same workforce of felonies. That
doesnt go down easily.
Perhaps what is missing here is a personal touch. When President Obama released CIA interrogation
memos in 2009, an event that David Ignatius equated to a car bomb going off in the driveway, the
president visited Langley. A visit to Fort Meade today, to thank and support an embattled and routinely
traduced workforce, would be almost sacramental in its character, delivering both sign and substance
of the presidents commitment.
It would also set a precedent. In the sixty-one-year history of the NSA, no Democratic president has
ever visited the agency.
There are a lot of risks involved in the controversy that Edward Snowden started. The greatest of all,
perhaps, is the impact of an uninformed blizzard of accusations on the morale of our intelligence
workers. The last thing the nation needs is for this community to ride out of town with the Frank Millers
of today still standing.
CANADIAN EAVESDROPPING REVIEW
NSA leaks prompted major Canadian eavesdropping review
www.vancouversun.com/news/leaks+prompted+major+Canadian+eavesdropping+review/9400685/story.html#ixzz2s6uYPHut
Vancouver Sun / by Jim Bronskill
Jan 18 2014 Jan 17. The massive intelligence leak by former U.S. spy contractor Edward Snowden
prompted Canada's secret eavesdropping agency to review its policies on sharing information with the
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 51
Americans and other key partners, a newly declassified memo reveals.
The three-page note from Communications Security Establishment Canada chief John Forster says
the unprecedented breach also sparked a CSEC examination of its practices for protecting the privacy
of Canadians.
The undated memo to national security adviser Stephen Rigby obtained by The Canadian Press
under the Access to Information Act was prepared some time in mid-2013, after Snowden's leaks
began making global headlines.
The memo, originally classified top secret, says CSEC set about assessing the potential damage to
Canadian signals intelligence collection capabilities, as well as asking its partners for confirmation on
what data Snowden took from the U.S. National Security Agency.
The highly sensitive material showed the NSA had quietly obtained access to a broad spectrum of
emails, chat logs and other information from major Internet companies, as well as data about a huge
volume of telephone calls.
CSEC, the NSA's Canadian counterpart, monitors foreign computer, satellite, radio and telephone
traffic for information of intelligence interest.
With a staff of more than 2,000 including skilled mathematicians, linguists and computer specialists
CSEC is a key player in the so-called Five Eyes community comprising Canada, the United States,
Britain, Australia and New Zealand.
"In collaboration with domestic and international partners, CSEC is undertaking an organization-wide
operation to assess the impacts of these unlawful disclosures of classified information," says the
memo, portions of which remain secret.
"Due to the unauthorized disclosures CSEC has developed an ongoing damage assessment, initiated
external and internal communications strategies and introduced preventative measures to mitigate the
potential of future damage."
A section on Forster's initial assessment of the damage is blacked out.
In addition to liaising with its Five Eyes partners, the spy agency briefed a committee of deputy
ministers on the fallout and arranged a series of bilateral meetings with the Privy Council Office (where
Rigby works), Foreign Affairs, the Canadian Security Intelligence Service and the RCMP.
The Ottawa-based CSEC held two briefings for staff members, along with specialized sessions, and
took steps to "remind them of security protocols and provide guidance and support where
appropriate," the memo says.
"CSEC is also reviewing internal policies related to information sharing with the Five Eyes as well as
the protection of the privacy of Canadians to ensure that they are appropriate and clear."
CSEC spokeswoman Lauri Sullivan said Friday the agency "continues to review its policies, processes
and procedures to ensure they are effective, and to ensure that CSE is taking the appropriate steps to
protect information and the privacy of Canadians."
The CSEC memo's release came as U.S. President Barack Obama announced changes Friday to
NSA practices with the aim of reassuring Americans their civil liberties will not be trampled.
At the time of the Forster memo, there had been no direct mention of CSEC in any of the stories
spawned by Snowden's cache of documents.
However, material later disclosed by the whistleblower indicated that Canada helped the United States
and Britain spy on participants at the London G20 summit in 2009. Other documents suggested CSEC
once monitored Brazil's department of mines and energy.
Articles based on Snowden's material continue to appear in the media.
Forster told Rigby the electronic spy agency so low-profile it is still unknown to many Canadians
was exploring ways to better inform the public about what it does, including its efforts to prevent
terrorism and cyber-attacks.
CSEC has since posted new information on its website about how the agency functions.
"CSEC will also keep employees informed as its damage assessment and forensic work unfold," the
memo says.
TOP SECRET NSA SLIDES AND SMS
http://cryptome.org/2014/01/nsa-sms-exploit.pdf
Cryptome
Jan 18 2014 Fringe: Use the URL
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 52
SOCIAL NETWORK ANALYSIS IN INTELLIGENCE
http://www.e-ir.info/2014/01/09/the-potential-of-social-network-analysis-in-intelligence/
E-International Relations / by Kristan J. Wheaton and Melonie K. Richey [Kristan J. Wheaton is an
Associate Professor at Mercyhurst University whose research focuses on the intersection of games-based learning
and intelligence analysis; he teaches the use of social network analysis and its application to traditional intelligence
problems.
Melonie K. Richey is a graduate student at Mercyhurst University who is currently participating in IARPAs Sirius
Project. Her current research focuses on exploring the viability of tabletop games in the intelligence classroom and on
modeling and simulating the Syrian refugee crisis by combining principles of social network analysis, geospatial
analysis and military techniques designed to understand how terrain impacts the movements of enemy forces.]
Jan 18 2014 Jan 9. The legality of the National Security Agencys (NSAs) use of US citizens
metadata to identify and track foreign intelligence organizations and their operatives is currently a
subject of much debate. Less well understood (and consequently routinely misreported) are the
capabilities and limitations of social network analysis, the methodology often used to evaluate this
metadata.
One of the first causes of confusion is definitional. Social network analysis is often linked to an in-
appropriate degree with social media. True, social media such as Facebook and Twitter are frequently
used as rich data sources for social network analysis, but understanding the importance of networks in
the affairs of states has been around at least since Machiavelli.[1]
In addition, the first modern version of what would come to be called social network analysis was de-
veloped not by an intelligence agency or computer scientist but by Columbia professor and psycho-
sociologist, Jacob Moreno, in 1934. These sociograms, as Moreno called them were used to graph
individual preferences or relations within a small group.
Little did Moreno suspect that his method for understanding the relationships between people, when
combined with graph theory and the processing power of computers, would allow for the detailed ana-
lysis of thousands of people or organizations with hundreds of thousands of connections between
them (See Fig. 2). [2]
Figure 2 Modern social network analysis uses powerful computers and graph theory to
map out the relationships between thousands of nodes and hundreds of thousands of links.
Shown here is the network of the over 6000 Twitter users who follow the Twitter handle of
the American Nuclear Society along with their over 200,000 connections. (Image Source:
Melonie Richey)
Along with the undeniable power of this type of analysis comes the inevitable (and justified) concerns
for privacy and constitutionality. But just how powerful is social network analysis? What can
intelligence agencies actually glean from the exabytes of data they are purportedly collecting?
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 53
Social Network Analysis, as an analytic method, has inarguable applicability to the field of intelligence
and is progressively reshaping the analytic landscape in terms of how analysts understand networks.
For example, analysts currently use SNA to identify key people in an organization or social network,
develop a strategic agent network, identify new agents and simulate information flows through a
network. Beyond this, SNA can be easily combined with other analytic practices such as Geographic
Information Systems (GIS), gravity model analysis or Intelligence Preparation of the Battlefield (IPB) to
create robust, predictive analyses.
Identifying Key People/Organizations in a Network
The most obvious use of SNA is its ability to identify key actors and entities within a network. Centrality
measures within a network are means for measuring a nodes relative importance within the network.
[3] It is well-accepted that the ability to measure centrality in social networks has been a particularly
useful development in social network analysis. What is more interesting, however, is the number of
centrality measures that social network analysts use to reveal different things about how key actors
interact within a network. [4] For example, a node with a high degree centrality is connected to many
other nodes. In Figure 3 below, it is unsurprising that the American Nuclear Society (ANS) has the
highest degree centrality in its own Twitter network. However, a node with a high betweenness centra-
lity is one that connects the cliques in the network. Figure 4 shows the same ANS network, reconfi-
gured and revisualized with an emphasis on betweenness, with a new node, Nuclear.com, emerging
as the most important.
Figure 3 (Image Source: Melonie Richey)
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 54
Figure 4 (Image Source: Melonie Richey)
For example, by analyzing the network in accordance with different centrality measures and establish-
ing filtering criteria (and using Carnegie Mellons ORA software), [5] we were able to reduce a network
representing the entire nuclear energy and non-proliferation communities on Twitter (6000+ nodes and
200,000+ links) to the 19 most influential individuals within that network (See Figure 5). These indivi-
duals are the nodes that would be able to disseminate information to the majority of the network within
a matter of hours.
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 55
Figure 5 (Image Source: Melonie Richey)
Identifying New Agents
Another traditional intelligence activity that could benefit from SNA is identifying potential new agents
people or organizations who might be willing or able to provide information to an intelligence agency.
For example, by using Twitters list feature, which allows users to establish lists of people to follow for
particular purposes and some simple cross-referencing techniques, we were able to identify 50 highly
reputable individuals and organizations talking about strategic mining and minerals on Twitter [6].
Figure 6 (Image Source: Melonie Richey)
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 56
While such a use by intelligence agencies may seem Orwellian, it is similar to techniques currently
used in business to identify potential customers. Likewise, a similar algorithm likely supports various
friend/colleague recommendation engines such as LinkedIns People You May Know feature.
Simulating Information Flows
Of all the capabilities of SNA, simulations are likely one of the most useful. Carnegie Mellons ORA, for
example, provides four main kinds of simulations in order to demonstrate how money, information,
disease or technology would move through a network. Pathway simulations locate the most direct or
indirect routes from one node to another. Still other simulations also indicate how a network would
react to the removal of any particular node or set of nodes (for example, how a decentralized terrorist
network such as the Taliban would function if the leaders from two key cells were killed).
Figure 7 (Image Source: Melonie Richey)
As an example of this feature, Figure 7, shows the effect of providing a highly relevant piece of infor-
mation to the 19 individuals identified in the Twitter network of nuclear specialists discussed above.
The dots, representing individuals and organizations on Twitter, get larger and change color as the
information flows throughout the system. Variables within the simulation allow researchers to alter the
level of interest the network likely has to a particular piece of information (the informations virality).
Combining SNA with Other Methods
These simulations and other features of SNA provide idealized analyses that can then be combined
with other techniques, such as GIS. Networks within ORA and many other SNA tools can be visualized
geospatially if coordinates are provided for each node. Running simulations through these networks
can then be represented on a map much like the simulation of Syrian refugee population movement
throughout Turkey shown in Figure 8. This, in turn, allows for powerful predictive analytics. Figure 9
reflects the outcome of the simulation in Figure 8; not only does the image represent reality (the known
locations of Syrian refugees according to the UN), [7] it also predicts where refugees are likely to move
within the next 12 to 24 months. This analysis employed SNA as the cornerstone analytic technique in
conjunction with GIS and even includes ideas from the more traditional intelligence methodology of
Intelligence Preparation of the Battlefield.
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 57
Figure 8 (Image Source: Melonie Richey)
Figure 9 (Image Source: Melonie Richey)
Caveat Emptor
Like all analytic techniques, SNA is imperfect and comes with a number of caveats for researchers
new to the method. SNA, while widely applicable, is by no means universally applicable.
For example, in early 2013, one of the authors sought to use SNA to locate terrorists using social
media. SNA and social media seemed like a good place to start, even though it seemed unlikely that
many such individuals would self identify as a radical extremist or Al-Qaeda affiliate. Ultimately
though, the effort failed because there was just too much of what social network analysts like to call
white noise, or extraneous information picked up through a comprehensive scraping of the Internet.
Our search for radical extremists returned journalists, university students of international relations and
politics, and a slew of ordinary people just keeping up with current events and Tweeting about it.
Another issue with SNA has to do with the nature of relationships. In the real world, they are often
messy and convoluted. Just because two people work together and do so often, does not necessarily
mean that they like each other. Similarly, the best way to describe the relationship between two busi-
nesses might not be the number of contracts the two have signed together. SNA works best, however,
with clearly definable relationships and where one factor in the relationship correlates well with other
factors important in a relationship. Modern intelligence problems, which often contain, political,
economic, military, tribal, geographic, personal, and historical relationship data require the application
of advanced SNA techniques and, even then, may yield little of real use to decisionmakers.
Finally, SNA is fundamentally a mathematical tool but is most useful in the decisionmaking process
when the networks are visualized. It is, without doubt, the visualization of these networks that tends to
capture the most attention from the policymakers that intelligence units typically support. This is both a
blessing and a curse. While it is easy to capture attention, explaining why the charts and graphs look
the way they do is an art. All too often, the initial excited reaction to these diagrams turns to boredom
and confusion as analysts bog the decisionmakers down with the arcana of SNA. In addition, creating
these complex visualizations often stresses even the most powerful personal computers (the images
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 58
of the simulation in Figure 8 above took approximately 2 hours to produce using a powerful desktop
PC with two high end graphics cards).
Like every analytic technique, SNA has great utility for the right question. Within its limits, SNA is
unmatched and can be usefully applied to identify key individuals or organizations within a network,
generate new leads and simulate the flows of information or money throughout a network. SNA,
however, remains just an answer, not the answer. Used inappropriately or without a full understanding
of the limits of the method and analysts will only be finding new and more technically sophisticated
ways to fail. That, then, is the primary job of the modern day analyst: making the judgment call of
which techniques to use and when. Equally as important as knowing when to use SNA is knowing
when not to use it.
Notes
[1] Machiavelli, N. (1515). Why the kingdom of darius, conquered by alexander, did not rebel against the successors of
alexander at his death. In The Prince Retrieved from http://www.constitution.org/mac/prince00.htm
[2] Rieder, B. (2012, March 19). Retrieved from http://thepoliticsofsystems.net/2012/03/
[3] Newman, M. (2009). Networks: an introduction. Oxford University Press, chap. 3.
[4] Costenbader, E., & Valente, T. W. (2003). The stability of centrality measures when networks are sampled. Social networks,
25(4), 283-307.
[5] ORA: Software. (2013). Available from Carnegie Mellon. Retrieved from www.casos.cs.cmu.edu/projects/ora/software.php
[6] For more information on how we did this analysis (and both the strengths and weaknesses of SNA as a tool for finding
agents), see The New HUMINT?
[7] UNHCR Turkey Syrian refugee daily sitrep. UNHCR: The UN refugee agency, November 25, 2013.
[8] UNHCR: UN refugee agency, Syrian refugee camps in Turkey. Last modified: Oct. 243, 2013. Accessed: Nov. 25, 2013.
[9] Syria needs analysis project (SNAP), Regional analysis Syria Part II: Host Countries. Last modified September 26, 2013.
Accessed November 25, 2013.
NSA REFORMS ARE PR ONLY
Obama's NSA 'reforms' are little more than a PR attempt to mollify the public
www.theguardian.com/commentisfree/2014/jan/17/obama-nsa-reforms-bulk-surveillance-remains
The Guardian / by Glenn Greenwald
Source: Infowarrior / https://attrition.org/mailman/listinfo/infowarrior
Jan 18 2014 Jan 17. In response to political scandal and public outrage, official Washington repeat-
edly uses the same well-worn tactic. It is the one that has been hauled out over decades in response
to many of America's most significant political scandals. Predictably, it is the same one that shaped
President Obama's much-heralded Friday speech to announce his proposals for "reforming" the Na-
tional Security Agency in the wake of seven months of intense worldwide controversy.
The crux of this tactic is that US political leaders pretend to validate and even channel public anger by
acknowledging that there are "serious questions that have been raised". They vow changes to fix the
system and ensure these problems never happen again. And they then set out, with their actions, to
do exactly the opposite: to make the system prettier and more politically palatable with empty, cosme-
tic "reforms" so as to placate public anger while leaving the system fundamentally unchanged, even
more immune than before to serious challenge.
This scam has been so frequently used that it is now easily recognizable. In the mid-1970s, the
Senate uncovered surveillance abuses that had been ongoing for decades, generating widespread
public fury. In response, the US Congress enacted a new law (Fisa) which featured two primary
"safeguards": a requirement of judicial review for any domestic surveillance, and newly created
committees to ensure legal compliance by the intelligence community.
But the new court was designed to ensure that all of the government's requests were approved: it met
in secret, only the government's lawyers could attend, it was staffed with the most pro-government
judges, and it was even housed in the executive branch. As planned, the court over the next 30 years
virtually never said no to the government.
Identically, the most devoted and slavish loyalists of the National Security State were repeatedly
installed as the committee's heads, currently in the form of NSA cheerleaders Democrat Dianne
Feinstein in the Senate and Republican Mike Rogers in the House. As the New Yorker's Ryan Lizza
put it in a December 2013 article on the joke of Congressional oversight, the committees "more often
treat senior intelligence officials like matinee idols".
As a result, the committees, ostensibly intended to serve an overseer function, have far more often
acted as the NSA's in-house PR firm. The heralded mid-1970s reforms did more to make Americans
believe there was reform than actually providing any, thus shielding it from real reforms.
The same thing happened after the New York Times, in 2005, revealed that the NSA under Bush had
been eavesdropping on Americans for years without the warrants required by criminal law. The US
political class loudly claimed that they would resolve the problems that led to that scandal. Instead,
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 59
they did the opposite: in 2008, a bipartisan Congress, with the support of then-Senator Barack
Obama, enacted a new Fisa law that legalized the bulk of the once-illegal Bush program, including
allowing warrantless eavesdropping on hundreds of millions of foreign nationals and large numbers of
Americans as well.
This was also the same tactic used in the wake of the 2008 financial crises. Politicians dutifully read
from the script that blamed unregulated Wall Street excesses and angrily vowed to rein them in. They
then enacted legislation that left the bankers almost entirely unscathed, and which made the "too-big-
to-fail" problem that spawned the crises worse than ever.
And now we have the spectacle of President Obama reciting paeans to the values of individual privacy
and the pressing need for NSA safeguards. "Individual freedom is the wellspring of human progress,"
he gushed with an impressively straight face. "One thing I'm certain of, this debate will make us
stronger," he pronounced, while still seeking to imprison for decades the whistleblower who enabled
that debate. The bottom line, he said, is this: "I believe we need a new approach."
But those pretty rhetorical flourishes were accompanied by a series of plainly cosmetic "reforms". By
design, those proposals will do little more than maintain rigidly in place the very bulk surveillance
systems that have sparked such controversy and anger.
To be sure, there were several proposals from Obama that are positive steps. A public advocate in the
Fisa court, a loosening of "gag orders" for national security letters, removing metadata control from the
NSA, stricter standards for accessing metadata, and narrower authorizations for spying on friendly
foreign leaders (but not, of course, their populations) can all have some marginal benefits. But even
there, Obama's speech was so bereft of specifics ? what will the new standards be who will now
control Americans' metadata that they are more like slogans than serious proposals.
Ultimately, the radical essence of the NSA ? a system of suspicion-less spying aimed at hundreds of
millions of people in the US and around the world ? will fully endure even if all of Obama's proposals
are adopted. That's because Obama never hid the real purpose of this process. It is, he and his
officials repeatedly acknowledged, "to restore public confidence" in the NSA. In other words, the goal
isn't to truly reform the agency; it is deceive people into believing it has been so that they no longer
fear it or are angry about it.
As the ACLU's executive director Anthony Romero said after the speech: "The president should end
not mend the government's collection and retention of all law-abiding Americans' data. When the
government collects and stores every American's phone call data, it is engaging in a textbook example
of an 'unreasonable search' that violates the constitution."
That, in general, has long been Obama's primary role in our political system and his premiere, defining
value to the permanent power factions that run Washington. He prettifies the ugly; he drapes the
banner of change over systematic status quo perpetuation; he makes Americans feel better about
policies they find repellent without the need to change any of them in meaningful ways. He's not an
agent of change but the soothing branding packaging for it.
As is always the case, those who want genuine changes should not look to politicians, and certainly
not to Barack Obama, to wait for it to be gifted. Obama was forced to give this speech by rising public
pressure, increasingly scared US tech giants, and surprisingly strong resistance from the international
community to the out-of-control American surveillance state.
Today's speech should be seen as the first step, not the last, on the road to restoring privacy. The
causes that drove Obama to give this speech need to be, and will be, stoked and nurtured further until
it becomes clear to official Washington that, this time around, cosmetic gestures are plainly
inadequate.
NSA SPYING FALLOUT HITS FRENCH SATELLITE DEAL
www.techdirt.com/articles/20140114/04272125862/nsa-spying-fallout-hits-french-satellite-deal.shtml
Techdirt / by Glyn Moody
Stringer: Kees Kalkman / VDAmok / Utrecht NL / kees@amok.antenna.nl
Jan 17 2014 Jan 16. Techdirt has already noted how the NSA's massive spying programs around
the world are costing US companies money through lost business -- and are likely to cost them even
more in the future. But it seems that the fallout is even wider, as this story from The Voice of Russia
makes clear: The sale of two intelligence satellites by France to the UAE [United Arab Emirates] for
nearly $1bln could go bust after the satellites were found to contain US technology designed to
intercept data transmitted to the ground station.
A top UAE defence source said that the satellites contain specific US-made components designed to
intercept the satellites' communication with their accompanying ground station.
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 60
As a result, the UAE might do a deal with the Russians instead: An unnamed UAE defence source
said that it is not clear if the US equipment can be taken off the French satellites, so the incident has
resulted in an increase of talks with Moscow, which, along with Beijing, has also been a frequent
defence technology supplier to the Emirates.
So it seems likely that not only will US companies find it hard to sell their wares directly to nations that
are worried about possible surveillance, but foreign manufacturers will also be reluctant to include
certain types of US technology in their own products, since that might cost them contracts. The price
being paid by US businesses for the NSA's "collect it all" approach continues to rise.
NSA COLLECTS MILLIONS OF TEXT MESSAGES DAILY IN 'UNTARGETED'
GLOBAL SWEEP
NSA extracts location, contacts and financial transactions
'Dishfire' program sweeps up 'pretty much everything it can'
GCHQ using database to search metadata from UK numbers
Dishfire presentation on text message collection key extracts
www.theguardian.com/world/2014/jan/16/nsa-collects-millions-text-messages-daily-untargeted-global-sweep
The Guardian / by James Ball
Stringer: Kees Kalkman / VDAmok / Utrecht NL / kees@amok.antenna.nl
Jan 17 2014 Jan 16. The National Security Agency has collected almost 200 million text messages
a day from across the globe, using them to extract data including location, contact networks and credit
card details, according to top-secret documents.
The untargeted collection and storage of SMS messages including their contacts is revealed in a
joint investigation between the Guardian and the UKs Channel 4 News based on material provided by
NSA whistleblower Edward Snowden.
The documents also reveal the UK spy agency GCHQ has made use of the NSA database to search
the metadata of untargeted and unwarranted communications belonging to people in the UK.
The NSA program, codenamed Dishfire, collects pretty much everything it can, according to GCHQ
documents, rather than merely storing the communications of existing surveillance targets.
The NSA has made extensive use of its vast text message database to extract information on peoples
travel plans, contact books, financial transactions and more including of individuals under no
suspicion of illegal activity.
An agency presentation from 2011 subtitled SMS Text Messages: A Goldmine to Exploit reveals
the program collected an average of 194 million text messages a day in April of that year. In addition
to storing the messages themselves, a further program known as Prefer conducted automated
analysis on the untargeted communications.
The Prefer program uses automated text messages such as missed call alerts or texts sent with
international roaming charges to extract information, which the agency describes as content-derived
metadata, and explains that such gems are not in current metadata stores and would enhance
current analytics.
On average, each day the NSA was able to extract:
More than 5 million missed-call alerts, for use in contact-chaining analysis (working out someones
social network from who they contact and when)
Details of 1.6 million border crossings a day, from network roaming alerts
More than 110,000 names, from electronic business cards, which also included the ability to extract
and save images.
Over 800,000 financial transactions, either through text-to-text payments or linking credit cards to
phone users
The agency was also able to extract geolocation data from more than 76,000 text messages a day,
including from requests by people for route info and setting up meetings. Other travel information
was obtained from itinerary texts sent by travel companies, even including cancellations and delays to
travel plans.
Communications from US phone numbers, the documents suggest, were removed (or minimized)
from the database but those of other countries, including the UK, were retained.
The revelation the NSA is collecting and extracting personal information from hundreds of millions of
global text messages a day is likely to intensify international pressure on US president Barack Obama,
who on Friday is set to give his response to the report of his NSA review panel.
While US attention has focused on whether the NSAs controversial phone metadata program will be
discontinued, the panel also suggested US spy agencies should pay more consideration to the privacy
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 61
rights of foreigners, and reconsider spying efforts against allied heads of state and diplomats.
In a statement to the Guardian, a spokeswoman for the NSA said any implication that the agencys
collection was arbitrary and unconstrained is false. The agencys capabilities were directed only
against valid foreign intelligence targets and were subject to stringent legal safeguards, she said.
The ways in which the UK spy agency GCHQ has made use of the NSA Dishfire database also seems
likely to raise questions on the scope of its powers.
While GCHQ is not allowed to search through the content of messages without a warrant though the
contents are stored rather than deleted or minimized from the database the agencys lawyers
decided analysts were able to see who UK phone numbers had been texting, and search for them in
the database.
The GCHQ memo sets out in clear terms what the agencys access to Dishfire allows it to do, before
handling how UK communications should be treated. The unique property of Dishfire, it states, is how
much untargeted or unselected information it stores.
In contrast to [most] GCHQ equivalents, DISHFIRE contains a large volume of unselected SMS
traffic, it states (emphasis original). This makes it particularly useful for the development of new
targets, since it is possible to examine the content of messages sent months or even years before the
target was known to be of interest.
It later explains in plain terms how useful this capability can be. Comparing Dishfire favourably to a
GCHQ counterpart which only collects against phone numbers that have specifically been targeted, it
states Dishfire collects pretty much everything it can, so you can see SMS from a selector which is
not targeted.
The document also states the database allows for broad, bulk searches of keywords which could
result in a high number of hits, rather than just narrow searches against particular phone numbers: It
is also possible to search against the content in bulk (e.g. for a name or home telephone number) if
the targets mobile phone number is not known.
Analysts are warned to be careful when searching content for terms relating to UK citizens or people
currently residing in the UK, as these searches could be successful but would not be legal without a
warrant or similar targeting authority.
However, a note from GCHQs operational legalities team, dated May 2008, states agents can search
Dishfire for events data relating to UK numbers who is contacting who, and when.
You may run a search of UK numbers in DISHFIRE in order to retrieve only events data, the note
states, before setting out how an analyst can prevent himself seeing the content of messages when he
searches by toggling a single setting on the search tool.
Once this is done, the document continues, this will now enable you to run a search without
displaying the content of the SMS, especially useful for untargeted and unwarranted UK numbers.
A separate document gives a sense of how large-scale each Dishfire search can be, asking analysts
to restrain their searches to no more than 1,800 phone numbers at a time.
The note warns analysts they must be careful to make sure they use the forms toggle before
searching, as otherwise the database will return the content of the UK messages which would,
without a warrant, cause the analyst to unlawfully be seeing the content of the SMS.
The note also adds that the NSA automatically removes all US-related SMS from the database, so it
is not available for searching.
A GCHQ spokesman refused to comment on any particular matters, but said all its intelligence
activities were in compliance with UK law and oversight.
But Vodafone, one of the worlds largest mobile phone companies with operations in 25 countries
including Britain, greeted the latest revelations with shock.
Its the first weve heard about it and naturally were shocked and surprised, the groups privacy
officer and head of legal for privacy, security and content standards told Channel 4 News.
What youre describing sounds concerning to us because the regime that we are required to comply
with is very clear and we will only disclose information to governments where we are legally compelled
to do so, wont go beyond the law and comply with due process.
But what youre describing is something that sounds as if thats been circumvented. And for us as a
business this is anathema because our whole business is founded on protecting privacy as a
fundamental imperative.
He said the company would be challenging the UK government over this. From our perspective, the
law is there to protect our customers and it doesnt sound as if that is what is necessarily happening.
The NSAs access to, and storage of, the content of communications of UK citizens may also be
contentious in the light of earlier Guardian revelations that the agency was drafting policies to facilitate
spying on the citizens of its allies, including the UK and Australia, which would if enacted enable
the agency to search its databases for UK citizens without informing GCHQ or UK politicians.
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 62
The documents seen by the Guardian were from an internal Wikipedia-style guide to the NSA program
provided for GCHQ analysts, and noted the Dishfire program was operational at the time the site was
accessed, in 2012.
The documents do not, however, state whether any rules were subsequently changed, or give
estimates of how many UK text messages are collected or stored in the Dishfire system, or from where
they are being intercepted.
In the statement, the NSA spokeswoman said: As we have previously stated, the implication that
NSA's collection is arbitrary and unconstrained is false.
NSA's activities are focused and specifically deployed against and only against valid foreign
intelligence targets in response to intelligence requirements.
Dishfire is a system that processes and stores lawfully collected SMS data. Because some SMS data
of US persons may at times be incidentally collected in NSAs lawful foreign intelligence mission,
privacy protections for US persons exist across the entire process concerning the use, handling,
retention, and dissemination of SMS data in Dishfire.
In addition, NSA actively works to remove extraneous data, to include that of innocent foreign
citizens, as early as possible in the process.
The agency draws a distinction between the bulk collection of communications and the use of that
data to monitor or find specific targets.
A spokesman for GCHQ refused to respond to any specific queries regarding Dishfire, but said the
agency complied with UK law and regulators.
It is a longstanding policy that we do not comment on intelligence matters, he said. Furthermore, all
of GCHQ's work is carried out in accordance with a strict legal and policy framework which ensures
that our activities are authorised, necessary and proportionate, and that there is rigorous oversight,
including from the Secretary of State, the Interception and Intelligence Services Commissioners and
the Parliamentary Intelligence and Security Committee.
GCHQ also directed the Guardian towards a statement made to the House of Commons in June 2013
by foreign secretary William Hague, in response to revelations of the agencys use of the Prism
program.
Any data obtained by us from the US involving UK nationals is subject to proper UK statutory controls
and safeguards, including the relevant sections of the Intelligence Services Act, the Human Rights Act
and the Regulation of Investigatory Powers Act, Hague told MPs.
SOME RESTRAINTS ON US SURVEILLANCE
www.nytimes.com/2014/01/15/us/politics/judge-warns-proposed-safeguards-could-hamper-surveillance-court.html
NY Times / by Peter Baker and Charlie Savage
Jan 16 2014 Jan 14. President Obama will issue new guidelines on Friday to curtail government
surveillance, but will not embrace the most far-reaching proposals of his own advisers and will ask
Congress to help decide some of the toughest issues, according to people briefed on his thinking.
Mr. Obama plans to increase limits on access to bulk telephone data, call for privacy safeguards for
foreigners and propose the creation of a public advocate to represent privacy concerns at a secret
intelligence court. But he will not endorse leaving bulk data in the custody of telecommunications firms,
nor will he require court permission for all so-called national security letters seeking business records.
The emerging approach, described by current and former government officials who insisted on
anonymity in advance of Mr. Obama?s widely anticipated speech, suggested a president trying to
straddle a difficult line in hopes of placating foreign leaders and advocates of civil liberties without a
backlash from national security agencies. The result seems to be a speech that leaves in place many
current programs, but embraces the spirit of reform and keeps the door open to changes later.
The decision to provide additional privacy protections for non-American citizens or residents, for
instance, largely codifies existing practices but will be followed by a 180-day study by the director of
national intelligence about whether to go further. Likewise, instead of taking the storage of bulk data
out of government hands, as recommended by a review panel he appointed, Mr. Obama will leave it in
place for now and ask lawmakers to weigh in.
The blend of decisions, to be outlined in a speech at the Justice Department and in a presidential
guidelines memorandum, will be Mr. Obama's highest-profile response to the disclosures about the
National Security Agency made in recent months by Edward J. Snowden, a former N.S.A. contractor
who has fled to Russia.
But as intelligence officials have sorted through Mr. Obama's evolving position, they have been
divided about how significant his adjustments will be.
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 63
Some officials complained that the changes will add layers of cumbersome procedure that will hinder
the hunt for potential terrorists, while others expressed relief that Mr. Obama is not going further and
confidence that they could still work within the new guidelines without sacrificing much.
Is it cosmetic or is there a real thumb on the scale in a different direction asked one former govern-
ment official who worked on intelligence issues. That's the question.
The White House said the president's review is incomplete and would not comment further Tuesday.
The developments came as the nation's judiciary waded into the highly charged debate. In a letter
made public on Tuesday, a judge designated by Chief Justice John G. Roberts Jr. to express the
views of the judicial branch warned that some changes under consideration would have a negative
operational impact on a secret foreign intelligence court.
Judge John D. Bates, a former chief judge of the Foreign Intelligence Surveillance Court, urged Mr.
Obama and Congress not to alter the way the court is appointed or to create an independent public
advocate to argue against the Justice Department in secret proceedings. Any such advocate, he
wrote, should instead be appointed only when the court decided one was needed.
Judge Bates objected to the workload of requiring that courts approve all national security letters,
which are administrative subpoenas allowing the F.B.I. to obtain records about communications and
financial transactions without court approval.
And he raised concerns about greater public disclosure of court rulings, arguing that unclassified
summaries would be likely to promote confusion and misunderstanding.
The judge's letter, versions of which he sent to the leaders of several congressional committees, was
released as all five members of Mr. Obama's surveillance review group testified Tuesday before the
Senate Judiciary Committee, seeking support for their recommendations.
Illustrating the cross-pressures on the president, the advisers argued for the appointment of the
independent version of a public advocate, a recommendation the president is expected to follow,
though it is not clear how he will structure the position.
We admire Judge Bates and respect his views, said Cass R. Sunstein, of Harvard Law School and a
former Obama White House official who served on the review panel. We respectfully disagree with
that one, on the ground that the judge sometimes is not in the ideal position to know whether a
particular view needs representation and that in our tradition, standardly, the judge doesn't decide
whether one or another view gets a lawyer.
The judge's objection to the proposal on national security letters dovetailed with that of the F.B.I.
director, James B. Comey, who argued it would be inefficient to have to go to a judge each time
records were sought. Mr. Obama has decided not to require court approval in every case, but might
still require it in some circumstances, according to one administration official.
Mr. Obama will cut back on the number of people whose phone records can be examined by the
N.S.A. through its bulk data program. Currently the agency can scrutinize call records of people as far
as three steps, or hops, removed from a suspect. Mr. Obama's review panel proposed limiting
searches to people just two steps removed. He is also likely to cut down the number of years such
data can be retained; currently it is deleted after five years.
But the president will not, at least for now, back the panel's suggestion that telecommunications firms
keep such data and that the government be allowed to tap into those databases only when necessary.
Intelligence officials complained it would be inefficient to have to go to multiple companies, so some
officials proposed creating an independent consortium to store the data instead.
Mr. Obama has decided against keeping the data at the private providers because they do not want
that responsibility, officials said, and no independent consortium currently exists. As a result, he will
ask Congress to work with him to determine the best way to store the data.
He also appears likely to reject the idea of separating code breakers and code makers. Some critics of
the N.S.A. were disturbed that the agency's encryption team charged with bolstering online security
systems against hackers was working with the team that tries to penetrate computer systems used by
terrorists.
The letter by Judge Bates was accompanied by 15 pages of often specific comments about possible
surveillance reforms.
It is highly unusual for judges to weigh in on public policy debates involving the other two branches of
government, but Judge Bates, the director of the Administrative Office of the United States Court, said
that Chief Justice Roberts had designated him to act as a liaison and that he had consulted other
judges.
The judge emphasized that his comments were meant to address smooth operation of the court and
were not intended as expressions of support or opposition to particular introduced bills.
Still, his comments went beyond workload issues. He objected to a proposal by Mr. Obama's review
group to take away Chief Justice Roberts's sole power to appoint the 11 judges of the surveillance
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 64
court and have them picked instead by the chief judges of the appeals courts.
Ten of the 11 current judges were appointed by Republican presidents, and critics have called for
more diversity. The chief justice is uniquely positioned to select qualified judges, Judge Bates argued.
SURVEILLANCE THREATENS US BUSINESS CLIMATE, DEMOCRACY
Stanford scholars say blanket mass surveillance undermines the U.S. economy by creating the
global perception of an unsafe American business climate. Meanwhile, the technology behind
surveillance is evolving well ahead of the law. As a result, privacy and civil liberty concerns are
mounting.
http://news.stanford.edu/news/2014/january/business-spying-dangers-011614.html
Stanford Report / by Clifton B. Parker
Source: Infowarrior / https://attrition.org/mailman/listinfo/infowarrior
Jan 16 2014 Jan 16. Mass surveillance by U.S. intelligence agencies is jeopardizing America's
reputation as a safe place to do business, according to a Stanford scholar.
"We are no longer seen as a safe business climate," said Aleecia M. McDonald, director of privacy at
Stanford's Center for Internet and Society. "It is difficult to convey the intensity of international outrage
over the U.S.'s conduct," as revealed by document leaker Edward Snowden.
Snowden, a former National Security Agency (NSA) contractor, released voluminous documents
describing a massive U.S. surveillance effort, both domestically and abroad.
As McDonald points out, the NSA tapped into German Chancellor Angela Merkel's cell phone and
news reports indicate that the agency eavesdropped on more than 35 international politicians,
including heads of state and senior officials in the European Union. This has economic repercussions,
she said.
"U.S. companies are frustrated that the NSA is also collecting the user data they collect themselves,"
she said. "There is no longer a clear-cut distinction between government and corporate tracking within
the U.S."
McDonald, whose research focuses on Internet privacy, behavioral economics and online privacy, said
that the NSA's actions have hurt American interests worldwide.
In particular, the Snowden affair revealed that the "breadth and depth of surveillance is far more
intense than imagined," McDonald said. The NSA every day is monitoring millions of phone calls,
email messages, instant messages and address books.
"This puts U.S. businesses in a difficult bind," said McDonald. Despite knowing their Internet browser
cookies may be used for NSA tracking, companies are not planning to make changes to their lucrative
advertising networks.
"The difficulty businesses face is that massive data collection about their users is the underlying
business model for most Internet companies," she said.
McDonald recently joined hundreds of other higher education scholars from around the world to sign a
petition calling for an end to the surveillance. "This has to stop. Without privacy, people cannot freely
express their opinions or seek and receive information," the petition states.
Surveillance law still evolving
In the courts, the issue is uncharted territory no government has ever before had the technological
power or the economic ability to eavesdrop on such a massive scale. Then the question arises: How is
mass surveillance threatening the rule of law and democracy?
Bruce M. Owen, director of Stanford's Public Policy Program and a senior fellow at the Stanford
Institute for Economic Policy Research, says that the Founding Fathers like Thomas Jefferson
believed that "we, the people" were the only legitimate source of political power.
"Protecting liberty required constraints on potentially tyrannical central government," Owen said.
Of course, government has legitimate functions, he noted, and as a result, a tradeoff exists between
the ability of the government to protect the people from crime or foreign threats while maintaining
individual liberty. However, technology often evolves well ahead of the justice system.
"Current laws reflect this tradeoff, but may not take account of new technologies that make it easier for
the government to invade the private domain," said Owen, whose research focuses on the economic
analysis of law, especially in the areas of telecommunications and mass media.
It will take new civil protections to simply maintain the degree of privacy that Americans have
experienced in the past, he said. International treaties can help protect the fundamental rights of
people against mass surveillance by governments.
"To the extent that current technology permits U.S. citizens' liberty to be invaded by foreign govern-
ments, and vice versa, countervailing treaties are an appropriate remedy," he said.
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 65
The U.S. government is not great at policing itself, he said. "We, the people, have to put some effort
into preserving our liberties. One can see Snowden as a martyr in this cause. Of course, martyrs by
definition must pay a price for their words or actions."
As for Snowden's role in the release of NSA documents, Owen said, "Just because you can do some-
thing doesn't automatically make the doing of it right or just."
Legal process: 'slow'
Jonathan Mayer, a doctoral student in computer science and Cybersecurity Fellow at the Center for
International Security and Cooperation, said that the law is still evolving in our highly digital world ?
and right now, it does not go far enough in safeguarding privacy.
"The NSA's mass surveillance programs are not unlimited. They are bound by legal rules. But our
computer science research suggests that those legal rules fail to protect Americans' privacy," Mayer
said in an email during a trip to Cambodia.
Mayer noted that the NSA can legally compel an American company to divulge records about
foreigners, with no individualized judicial review and little transparency.
"The legal process is slower and more cumbersome than technical surveillance, to be sure, but still
leaves much of the globe at risk," Mayer co-wrote in a 2013 article with Edward Felten of Princeton
University. "As long as companies collect and retain tracking data, there will be a risk of disclosure
through legal process, and users, especially those overseas, will be wary."
As for the NSA's claim last year that it was only collecting nameless phone numbers on Americans in
its mass surveillance efforts, Mayer and another colleague, Patrick Mutchler, conducted an experiment
of their own last year. They randomly sampled 5,000 phone numbers from a data set known as
MetaPhone and attempted to match those with entries in Yelp, Google Places and Facebook. They
matched 1,356 (27 percent) of the numbers.
"If a few academic researchers can get this far this quickly, it's difficult to believe the NSA would have
any trouble identifying the overwhelming majority of American phone numbers," Mayer wrote in a blog
post.
Chilling effect on speech, behavior
Richard Forno, a junior affiliate scholar with the Center for Internet and Society, warns that mass
surveillance can create conformity in social thought and interactions.
"If a person believes they are constantly being watched, they will, over time, conform to what they
think those watching them will deem as 'expected' norms of conduct and communication," he said.
In a liberal Western society like the United States, that can lead to self-censorship of thought, word
and behavior, he suggested. Such an effect is not conducive to democratic ideals.
Even more unsettling to Forno is the fact that the NSA surveillance illustrates how "government
actions are concealed by secret interpretations of otherwise public law," such as the Patriot Act
legislation, he said, that was rushed through Congress without a solid understanding or vetting.
Forno urged more independent-minded legislative and executive oversight of U.S. intelligence
agencies: "We need critical and objectively informed overseers who do not simply take the carefully
prepared statements and testimony of the intelligence community as absolute, unassailable facts
when deliberating their conduct or need for certain activities."
However, some in Congress are too concerned about appearing to be soft on security or lacking in
patriotism, he said. And so, there is no true public accountability of the intelligence community when
the hard questions cannot be asked because of all the secrets.
"It's hard to watch the watcher," Forno said, "and foster meaningful transparency or accountability in a
democratic system when the watchers themselves control what you see, along with how, when and
where you can see it."
PHILIPPINES: ISAFP TO BE EXPANDED
ISAFP to be expanded, not abolished, says chief
http://www.philstar.com/headlines/2014/01/12/1277822/isafp-be-expanded-not-abolished-says-chief
The Philippine Star / by Jaime Laude
Stringer: Kees Kalkman / VDAmok / Utrecht NL / kees@amok.antenna.nl
Jan 16 2014 Jan 12. The Intelligence Service of the Armed Forces of the Philippines (ISAFP) is not
up for deactivation but due for expansion, the commander of the militarys top intelligence unit said
yesterday.
Its not true. The defense planning guidance is to create one big intelligence organization in the future
with ISAFP under a different name, serving as its backbone, ISAFP chief Brig. Gen. Eduardo Ao
said.
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 66
Ao made the clarification to douse talks that the fire that broke out in the ISAFPs well-guarded
compound late Friday could be related to plans to abolish the military intelligence unit.
Ao pointed out last Fridays fire also damaged the message center of the AFP Deputy for Intelligence
(J2), whose office is located inside the ISAFP compound.
He added a representative from an insurance firm would be arriving on Monday to determine the
actual damage caused by the fire, which he described as very minimal.
According to Ao, the ISAFP expansion plan would be patterned after the defense intelligence
services of other countries.
He stressed the ISAFP will remain as the intelligence unit of the AFP but this time, once the study is
completed, it will be under the Department of National Defense (DND).
Ao stressed that everything surrounding the upsizing of ISAFP is still on the drawing board and is not
expected to happen this year.
REPORT ON BENGHAZI TERRORIST ATTACKS
Senate Intelligence Committee Releases Declassified Bipartisan Report on Benghazi Attacks
Full report: http://www.intelligence.senate.gov/benghazi2014/benghazi.pdf
US Senate
Source: Sabrina Pacifici / BeSpacific / Silver Spring US / www.bespacific.com
Jan 16 2014 Jan 15. The Senate Intelligence Committee today issued a declassified report on the
September 11-12, 2012, terrorist attacks against U.S. personnel at the Temporary Mission Facility and
CIA Annex in Benghazi, Libya. The committee found the attacks were preventable, based on extensi-
ve intelligence reporting on the terrorist activity in Libyato include prior threats and attacks against
Western targetsand given the known security shortfalls at the U.S. Mission. The reportannounced
by Senate Intelligence Committee Chairman Dianne Feinstein (D-Calif.) and Vice Chairman Saxby
Chambliss (R-Ga.)was approved by the committee in December 2013 by voice vote. The report
includes 18 recommendations designed to improve security of American diplomatic and intelligence
facilities abroad. In some cases, the State Department and the intelligence community (IC) have
begun taking action to adopt the recommendations identified in the report.
GERMAN DOUBLE AGENT KILLED IN PAKISTAN
How Did a German Man End Up Dead in a US Drone Strike?
http://blog.foreignpolicy.com/posts/2014/01/15/how_did_a_german_man_end_up_dead_in_an_american_drone_strike
Foreign Policy / by Elias Groll
Stringer: Kees Kalkman / VDAmok / Utrecht NL / kees@amok.antenna.nl
Jan 16 2014 Jan 15. On Feb. 16, 2012 a missile launched from an American drone struck a pickup
truck outside the city of Mir Ali in Pakistan's rugged tribal region. As many as 15 men died in the
attack, which many reports claimed killed mostly "Uzbek Islamists."
Now, nearly two years after the fact, it turns out a German man was among the dead that day.
According to a report in the German newspaper Suddeutsche Zeitung, a man known as Patrick was
killed in the attack. A convert to Islam, Patrick had at one point allegedly served as an informant for the
German security services, reporting on the Islamist scene around Bonn.
It's an irony that surrounds much of the initial reporting on American drone strikes in Pakistan and
elsewhere. Initial reports cite the deaths of various "suspected insurgents." Only later do the actual
identities of those killed in the strike emerge -- be they civilian or combatant.
In the case of Patrick, the death of a former informant for the German security services raises as many
questions as it answers. According to the Suddueutsche Zeitung, Patrick had been converted at the
age of 16 during the winter of 2001 and had been briefly arrested in Bonn ahead of a gathering of
Social Democrats there that was subject to various terror threats. Those threats turned out be empty,
and Patrick disappeared shortly thereafter. His family reported him missing.
It was only this week that he turned up once more -- in a jihadist propaganda video announcing his
death. Patrick appears to have joined up with a group known as the Islamic Movement of Uzbekistan,
a group with strong ties to the Taliban and al Qaeda. Two German brothers -- Mounir and Yassin
Chouka -- run the group's propaganda outfit and produce high-quality German-language propaganda
videos for consumption back home.
While Patrick's alleged work for the German security services remains unconfirmed, that line on his
resume raises two tantalizing questions. First, could Patrick have been sent back to Pakistan as a
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 67
German agent? Second, if Patrick wasn't a double agent, what was a fluent German speaker doing
still in Pakistan? Shouldn't such a man be given a haircut, a suit, a ticket to Karachi, and an order to
await further instructions? Few better candidates exist for terror missions in Western Europe.
The answers to these questions -- to the extent they're answerable, anyway -- offer something of a
snapshot of the current jihadist movement and the threat it poses to European countries.
Guido Steinberg is an expert on jihadist groups, including the Islamic Movement of Uzbekistan, and,
according to him, the likelihood that Patrick was sent to Pakistan as a double agent is extremely
unlikely. "The German services have never managed to infiltrate these networks," Steinberg, who is a
senior associate at the German Institute for International and Security Affairs, told Foreign Policy. "At
one point they did here in Berlin for a very, very short time. I'd be surprised -- it doesn't really fit their
normal activities." The idea that Germany spies would be able to launch such an operation is, in fact,
somewhat laughable. "Our services are virtually helpless without the help of the Americans," Steinberg
added.
European security services are currently consumed with the fear that members of their growing
Muslim minority will travel abroad to participate in jihadist movements only to return later and apply
what they have learned on the battlefields of Syria and Pakistan in terrorist attacks at home. The
intensifying conflict in Syria has only exacerbated that fear, and that country has now surpassed
Afghanistan and Pakistan as the prime destination for European jihadists. "The global jihad has
prioritized the Syrian conflict as its principal front," a Spanish intelligence official told Newsweek in
October.
So far, the fear among European security officials toward returning jihadists appears to have paid off.
There have been no major attacks in recent years, and European security services have proven fairly
competent at foiling such attacks. The result, Steinberg says, is that foreign terrorist groups are loath
to send their fighters back to Europe when in all likelihood they'll get caught or killed anyway.
Instead, Steinberg says, groups like IMU have turned toward utilizing savvy propaganda strategies to
inspire attacks inside Germany, including a failed attempt to kill a right-wing politician. That's a familiar
reality for American security officials. For example, Maj. Nidal Hassan, the man responsible for killing
13 people at the American military base at Ft. Hood, became radicalized in part by watching sermons
online.
In the digital era, old notions of double agents and moles aren't as relevant as they used to be. It's
fanciful to imagine that a rogue German be sent back from the wilds of Pakistan to carry out an attack
in Berlin. What's more likely is that some anonymous-looking kid carries out the deed after getting
radicalized online.
That's a target America's drones can't hit.
US ANTI-DRUG CENTER IN BAHRAIN
With Afghan drawdown ongoing, U.S. to set up center in Bahrain to continue anti-drug efforts
www.washingtonpost.com/world/national-security/with-afghan-drawdown-ongoing-us-to-set-up-center-in-
bahrain-to-continue-anti-drug-efforts/2014/01/15/25dc771e-7e2d-11e3-9556-4a4bf7bcbd84_story.html
The Washington Post / by Ernesto Londoo
Stringer: Kees Kalkman / VDAmok / Utrecht NL / kees@amok.antenna.nl
Jan 16 2014 Jan 16. As the United States shrinks its civilian presence in Afghanistan, limiting its
ability to combat the countrys booming drug industry, U.S. officials intend to establish an intelligence
center in Bahrain to continue fighting the trade.
The center in the tiny Persian Gulf nation, home to the U.S. Navys 5th Fleet, will be an integral part
of the Defense Departments post-2014 strategy in Afghanistan, Erin Logan, who oversees the
Pentagons counternarcotics efforts, said Wednesday afternoon.
The center will help fill the gap where space for personnel on the ground in Afghanistan is no longer
available, she told a Senate panel on narcotics control.
Lawmakers and the inspector general overseeing reconstruction efforts in Afghanistan said they were
alarmed that a problem that Washington has spent billions of dollars trying to combat is likely to
worsen and further destabilize Afghanistan at a critical time.
John F. Sopko, the special inspector general for Afghanistan reconstruction, said that during a recent
visit to the country, Afghan and U.S. officials conveyed to him that Afghanistans drug problem is dire,
with little prospect for improvement in 2014 or beyond, after the end of the U.S. combat mission.
The narcotics trade is poisoning the Afghan financial sector and fueling a growing illicit economy,
said Sopko, who has launched an audit of U.S. counternarcotics efforts. This, in turn, is undermining
the Afghan states legitimacy by stoking corruption, nourishing criminal networks and providing
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 68
significant financial support to the Taliban and other insurgent groups.
Cultivation of opium poppies, which are processed to make heroin, reached a record high of 516,450
acres last year, according to the United Nations. The statistic raised questions about the return on
Washingtons $7 billion investment in efforts to root out poppy cultivation and break the link between
the trade and the insurgency. Administration officials conceded that those efforts are going to become
more challenging.
The U.S. Drug Enforcement Administration's mission in Kabul, which included nearly 100 personnel as
of the end of last year, is in the midst of its own drawdown. Although staffing plans have not been
finalized, the agency intends to trim its personnel to 45 permanent slots by October and 25 to 30 by
the end of the year, according to a document outlining the plans that was obtained by The Washington
Post.
James L. Capra, the agencys chief of operations, testified that DEA agents will soon lose the ability to
travel easily across the country, particularly to provinces in the south that form the backbone of the
poppy industry.
Currently, the government of Afghanistan is not capable of absorbing or replicating the scale of
assistance provided by the international community, he said.
DEA agents hope to continue working with and supporting elite Afghan police units that have carried
out drug investigations in recent years, Capra said.
Sen. Dianne Feinstein (D-Calif.), chairman of the counter-narcotics panel, called Afghanistans drug
trade a problem with no easy solution, adding that new approaches must be found. We ignore it at
our peril, she said.
Feinstein said Washington should attempt to collaborate on counternarcotics efforts with Iran, which
shares a border with Afghanistan and is a leading destination and crossing point of the heroin trade.
There may be many areas of disagreement, but this is one where we should agree, she said.
DRONE CONTROL: CIA OR PENTAGON
Lawmakers seek to stymie plan to shift control of drone campaign from CIA to Pentagon
www.washingtonpost.com/world/national-security/lawmakers-seek-to-stymie-plan-to-shift-control-of-drone-
campaign-from-cia-to-pentagon/2014/01/15/c0096b18-7e0e-11e3-9556-4a4bf7bcbd84_story.html
The Washington Post / by Greg Miller
Stringer: Kees Kalkman / VDAmok / Utrecht NL / kees@amok.antenna.nl
Jan 16 2014 Jan 16. Congress has moved to block President Obamas plan to shift control of the
U.S. drone campaign from the CIA to the Defense Department, inserting a secret provision in the
massive government spending bill introduced this week that would preserve the spy agencys role in
lethal counterterrorism operations, U.S. officials said.
The measure, included in a classified annex to the $1.1 trillion federal budget plan, would restrict the
use of any funding to transfer unmanned aircraft or the authority to carry out drone strikes from the
CIA to the Pentagon, officials said.
The provision represents an unusually direct intervention by lawmakers into the way covert operations
are run, impeding an administration plan aimed at returning the CIAs focus to traditional intelligence
gathering and possibly bringing more transparency to drone strikes.
The move also reflects some lawmakers lingering doubts about the U.S. militarys ability to conduct
strikes against al-Qaeda and its regional affiliates without hitting the wrong targets and killing civilians.
Those apprehensions were amplified after a U.S. military strike in Yemen last month killed a dozen
people, including as many as six civilians, in an 11-vehicle convoy that tribal leaders said was part of a
wedding procession. U.S. officials said that the strike was aimed at a senior al-Qaeda operative but
that reviews of the operation have raised concern that it failed to comply with White House guidelines
requiring near certainty that no civilians would be harmed.
On Wednesday, there were reports that another U.S. strike had killed a farmer in Yemen.
The extent of the restrictions contained in the drone provision remained unclear. The measure was
included by members of the House and Senate appropriations committees, said officials who spoke on
the condition of anonymity because they were not authorized to comment publicly on the legislation.
Other senior lawmakers and congressional officials declined to comment on the contents of the
classified annex, which details funding for U.S. spy agencies.
Still, senior lawmakers have been vocal in expressing concern about the prospect of the CIA ceding
responsibility for drone strikes to the military. Sen. Dianne Feinstein (D-Calif.), the chairman of the
Senate Intelligence Committee and a member of the Appropriations Committee, said last year that she
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 69
had seen the CIA exercise patience and discretion specifically to prevent collateral damage and that
she would really have to be convinced that the military would carry it out that well.
Feinstein declined to comment on the budget measure this week. But a senior aide said that the
senator stands by her earlier statements and that the Intelligence Committee has recently reviewed
this issue, and Senator Feinstein believes her views are widely shared on the committee.
Asked about the scope of that review, the aide said the panel took stock of the program and came to
a conclusion but would not elaborate.
Among Feinsteins colleagues on the Intelligence Committee is Sen. Barbara A. Mikulski (D-Md.), who
is chairman of the appropriations panel responsible for the budget bill. A spokesman for that
committee declined to comment.
There is no mention of the drone provision in the hundreds of pages of the budget blueprint released
to the public. A section outlining $572 billion in Pentagon spending notes that adjustments to
classified programs are addressed in the accompanying classified annex.
A person familiar with the omnibus bill confirmed that the annex includes language on the drone
program but would say only that the provision is more complicated than merely withholding money to
prevent drone operations from being transferred to the Pentagon.
Former U.S. officials familiar with the intelligence appropriations process said that aside from placing
restrictions on funding, Congress could create other obstacles for example, requiring the Pentagon
to certify that it has matched the CIAs capabilities and targeting methodology before it is allowed to
proceed.
Spokespeople for the White House, the CIA and the Pentagon declined to comment.
The spending bill sets budgets for agencies across the federal government for the fiscal year that ends
Sept. 30. The measure cleared the House late Wednesday. It is expected to be approved by the
Senate this week and delivered to President Obama for his signature as soon as Saturday.
The move by Congress carries implications for the course of the U.S. efforts against al-Qaeda at a
time when its affiliates in Yemen, Somalia, Iraq and Syria have become more worrisome to American
counterterrorism officials than the terrorist organizations traditional core.
Also at issue is the fundamental mission of the CIA, which during the past decade has morphed into a
paramilitary force. Senior officials, including CIA Director John O. Brennan, have warned that the
agencys emphasis on lethal operations deviates from its traditional mission and could impair its ability
to focus on gathering intelligence.
The administration first signaled its intent to shift control of drone operations to the Pentagon last year,
when Obama announced new guidelines for counterterrorism missions including a pledge of
greater transparency during a speech at the National Defense University. At the time,
administration officials briefing reporters said there would be a preference for the Department of
Defense to engage in the use of force outside war zones.
The remark was a reference to Pakistan, Yemen and Somalia countries beyond the war zones of
Iraq and Afghanistan, where the United States has carried out drone strikes against al-Qaeda targets.
Obamas policy shift was expected to mainly affect Yemen, where the CIA and the elite U.S. Joint
Special Operations Command conduct overlapping drone campaigns.
The overall pace of strikes has diminished significantly in Pakistan and Yemen, and Brennan has held
secret meetings with Pentagon officials in recent months to work out logistical challenges and other
impediments to shifting control of drone operations.
But the CIA still carries out the majority of strikes, and the collateral damage that has accompanied
some JSOC strikes has generated growing opposition to removing the agency from such operations
anytime soon.
The Pentagon has refused to release any details on the Dec. 12 strike carried out by JSOC in Radaa,
a district that has become a stronghold for al-Qaeda in the Arabian Peninsula, or AQAP. Yemen
initially insisted that only militants had been killed, but it later acknowledged civilian casualties.
The government then delivered rifles and other compensation to victims families payments that a
Yemeni official described as a deposit to encourage clan leaders to take part in tribal mediation and
accept further compensation rather than seek retaliation against the Sanaa government.
There was a [legitimate] target, and then something happened, a misfire, the Yemeni official said,
speaking on the condition of anonymity because of the secrecy surrounding U.S. strikes. Ive never
been aware of any incident before where a strike targeted such a large convoy of vehicles.
AQAP is responsible for near-miss attacks on the United States, including the attempted bombing of a
Detroit-bound airliner on Christmas Day in 2009. The terrorist group has been driven out of territory it
had gained over the past two years but is still considered by U.S. officials to pose a serious threat to
the United States.
In a meeting with U.S., European and Middle Eastern diplomats last week, Yemeni President Abed
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 70
Rabbo Mansour Hadi described the security situation as unstable and warned specifically of
indications that potential al-Qaeda recruits from European and other Western nations were seeking to
enter the country, according to U.S. and Yemeni officials.
BREAKING THE INDIA-US DIPLOMATIC ICE
Joint Intelligence Council chief meets delegation from U.S. Director of National Intelligences
office for talks focussed on Afghanistan
www.thehindu.com/todays-paper/tp-national/intelligence-meet-breaks-indiaus-diplomatic-ice/article5575598.ece
The Hindu / by Praveen Swami
Stringer: Kees Kalkman / VDAmok / Utrecht NL / kees@amok.antenna.nl
Jan 16 2014 Jan 14. Indian and United States intelligence services began a three-day meeting on
Monday, the first high-level dialogue between the two countries since the crisis sparked off by the
arrest of Indian diplomat Devyani Khobragade in December. Led by Joint Intelligence Council chief Ajit
Lal, an Indian delegation met officials from the office of the Director of National Intelligence for the
latest in a series of discussions on regional security and strategic issues.
The latest round of the dialogue is focussed on events in Afghanistan leading up to the United States
drawdown in 2014, a highly-placed Indian government source told The Hindu . The United States is
extremely concerned at Afghan President Hamid Karzais delay on signing a security agreement, and
hopes India will be willing to use its influence to persuade him to do so.
Peter Lavoy, Assistant Secretary of Defence for Asian and Pacific Security Affairs, had visited New
Delhi last month for scheduled discussions on the situation in Afghanistan, following President Karzais
visit to New Delhi. However, key defence, intelligence and diplomatic officials declined to meet Dr.
Lavoy following Ms. Khobragades controversial arrest in New York.
Last week, two senior U.S. officials, Energy Secretary Ernest Moniz and Assistant Secretary of State
Nisha Desai Biswal postponed their visits to New Delhi.
External Affairs Ministry sources in New Delhi declined to comment on the JIC-DNI meeting, saying
they could not comment on intelligence issues.
Eleven rounds of dialogue have been held between the DNI and the JIC, with the two organisations
meeting each June in Washington, D.C., and in New Delhi in January. No details were immediately
available on the composition of the United States delegation.
It is important for India that the intelligence dialogues continue, irrespective of problems that will from
time to time crop up in the relationship with the United States, former Intelligence Bureau chief Ajit
Doval told The Hindu . Both countries have vital interests which need to be discussed at the highest
level.
Founded in 1998, the JIC is mandated to provide the government with big-picture assessments of
strategic issues. Its secretariat, which reports to the Cabinet Secretariat, produces papers and strategy
documents based on analysis of information from the Research and Analysis Wing, the Intelligence
Bureau, and the directorates of military, naval and air intelligence.
OBAMA FROM SPY CRITIC TO OVERSEER
www.nytimes.com/2014/01/16/us/obamas-path-from-critic-to-defender-of-spying.html?nl=todaysheadlines&emc=edit_th_20140116&_r=0
NY Times / by Peter Baker
Stringer: Frank Slijper / Campaign Against Arms Trade / Groningen NL / frank.slijper@hetnet.nl
Jan 16 2014 Jan 15. As a young lawmaker defining himself as a presidential candidate, Barack
Obama visited a center for scholars in August 2007 to give a speech on terrorism. He described a
surveillance state run amok and vowed to rein it in. That means no more illegal wiretapping of
American citizens, he declared. No more national security letters to spy on citizens who are not
suspected of a crime.
More than six years later, the onetime constitutional lawyer is now the commander in chief presiding
over a surveillance state that some of his own advisers think has once again gotten out of control. On
Friday, he will give another speech, this time at the Justice Department defending government spying
even as he adjusts it to address a wave of public concern over civil liberties.
The journey between those two speeches reflects the transition from the backbench of the United
States Senate to the chair behind the Resolute Desk in the Oval Office. Like other presidents before
him, the idealistic candidate skeptical of government power found that the tricky trade-offs of national
security issues look different to the person charged with using that power to ensure public safety.
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 71
Aides said that even as a senator, Mr. Obama supported robust surveillance as long as it was legal
and appropriate, and that as president he still shares the concerns about overreach he expressed
years ago. But they said his views have been shaped to a striking degree by the reality of waking up
every day in the White House responsible for heading off the myriad threats he finds in his daily
intelligence briefings.
When you get the package every morning, it puts steel in your spine, said David Plouffe, the
presidents longtime adviser. There are people out there every day who are plotting. The notion that
we would put down a tool that would protect people here in America is hard to fathom.
At the same time, aides said Mr. Obama was surprised to learn after leaks by Edward J. Snowden, the
former National Security Agency contractor, just how far the surveillance had gone. Things seem to
have grown at the N.S.A., Mr. Plouffe said, citing specifically the tapping of foreign leaders
telephones. I think it was disturbing to most people, and I think he found it disturbing.
Yet it is hard to express indignation at actions of the government after five years of running it, and
some involved in surveillance note that it was Mr. Obama who pushed national security agencies to be
aggressive in hunting terrorists. For some, his outrage does ring a little bit hollow, said a former
counterterrorism official.
All of which leads to worries by critics of government surveillance that he will not go far enough on
Friday. If the speech is anything like what is being reported, the president will go down in history for
having retained and defended George W. Bushs surveillance programs rather than reformed them,
said Anthony D. Romero, executive director of the American Civil Liberties Union.
Mr. Obama first confronted the questions of national security and privacy during his 2004 campaign for
Senate, taking aim at the Patriot Act for violating our fundamental notions of privacy and declaring
that we dont like federal agents poking around our libraries.
Once elected, Mr. Obama took an interest in curbing surveillance. He would ask me about various
issues that relate to the topic of the day how do you come up with policies that make sure that
security and liberty are not mutually exclusive? recalled Senator Ron Wyden, Democrat of Oregon
and a leading critic of surveillance policies then and now.
Mr. Obama was a sponsor of a bill in 2005 to raise the standard required for federal agents using
administrative subpoenas known as national security letters to obtain business records without court
order. He joined other Democrats fighting the renewal of the Patriot Act until it was amended to
address civil liberties concerns, then voted for its extension in 2006 after a compromise, breaking with
Mr. Wyden who voted no.
Mr. Obamas 2007 speech at the Woodrow Wilson International Center for Scholars came after the
revelation that President George W. Bush had authorized warrantless surveillance in terrorism cases
without permission from the Foreign Intelligence Surveillance Court. A presidential candidate, Mr.
Obama criticized Mr. Bushs false choice between the liberties we cherish and the security we
provide.
But as a former Obama aide put it recently, The rhetoric was probably sharper than his votes. By
summer 2008, with the Democratic nomination secured and the White House now a real possibility,
Mr. Obama voted for legislation essentially ratifying Mr. Bushs surveillance programs. Mr. Obama
realized he would take my lumps from the left and said it was not an easy call for me, but he argued
that putting the programs under the jurisdiction of the intelligence court restored accountability.
As a result, after he won the election, surveillance issues were off his agenda; instead, he focused on
banning interrogation techniques he deemed torture and trying, futilely, to close the prison at
Guantnamo Bay, Cuba. There wasnt really any serious discussion of what N.S.A. was up to, said a
former intelligence official, who like others did not want to be named describing internal conversations.
Mr. Obama was told before his inauguration of a supposed plot by Somali extremists to attack the
ceremony, what David Axelrod, his adviser, called a welcome-to-the-N.B.A. moment before the first
game. Although the report proved unfounded, it reinforced to Mr. Obama the need to detect threats
before they materialized. The whole Somali threat injected their team into the realities of national
security in a tangible and complicated way, recalled Juan C. Zarate, the departing counterterrorism
adviser to Mr. Bush who worked with the Obama team on the threat.
So while instituting additional procedural changes, Mr. Obama undertook no major overhaul of the
surveillance programs he inherited. Hes sitting on the other end of the pen now, said the former
Obama aide. He has more information than he did then. And he trusts himself to use these powers
more than he did the Bush administration.
Just weeks after the inauguration, Judge Reggie B. Walton issued a secret ruling reprimanding the
N.S.A. for violating its own procedures. But when Mr. Obama was briefed, the case did not stir
consternation. The presidents team instructed the Justice Department to fix the problem, but this was
not a central concern and he was very quick in knowing how to deal with it, said a former
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 72
administration official.
The calculus had shifted enough that Mr. Obama began presiding over a record number of leak
prosecutions. When civil liberties advocates visited to press him to do more to reverse Mr. Bushs
policies, Mr. Obama pushed back. He reminded me that he had a different role to play, that he was
commander in chief and that he needed to protect the American people, recalled Mr. Romero of the
A.C.L.U.
That was brought home even more starkly at Christmas in 2009 when a Nigerian man tried to detonate
explosives in his underwear aboard an airliner. At a meeting at the White House afterward, an agitated
Mr. Obama was extremely firm with intelligence officials, saying that he expected us to do better,
recalled one who was in the room.
We hadnt had a major attack in a number of years and the fact that this guy came as close as he did
basically the detonator didnt work and the fact that we hadnt detected it in advance really came
as a shock to them, said John E. McLaughlin, a former deputy C.I.A. director who participated in a
review of the incident for the administration.
Feeling little pressure to curb the security agencies, Mr. Obama largely left them alone until Mr.
Snowden began disclosing secret programs last year. Mr. Obama was angry at the revelations,
privately excoriating Mr. Snowden as a self-important narcissist who had not thought through the
consequences of his actions.
He was surprised at the uproar that ensued, advisers said, particularly that so many Americans did not
trust him, much less trust the oversight provided by the intelligence court and Congress. As more
secrets spilled out, though, aides said even Mr. Obama was chagrined. They said he was exercised to
learn that the mobile phone of Chancellor Angela Merkel of Germany was being tapped.
Mr. Obama appointed a panel to review the programs. The point we made to him was, Were not
really concerned about you, Barack, but God forbid some other guys in the office five years from now
and theres another 9/11, said Richard A. Clarke, a former White House counterterrorism adviser
who served on the panel. He had to lay down some roadblocks in addition to what we have now so
that once youre gone itll be harder to abuse spying abilities.
On the other hand, Mr. Obama was acutely aware of the risks of being seen as handcuffing the
security agencies. Whatever reforms he makes, you can be sure if theres another incident and the
odds are there will be in our history therell be someone on CNN within seconds saying if the
president hadnt hamstrung the intelligence community, this wouldnt have happened, Mr. Axelrod
said.
Benjamin J. Rhodes, a deputy national security adviser working on Fridays speech, said Mr. Obama
saw the issue as two separate questions abuse of government power and extent of government
power. With the 2008 legislation setting a new structure, the president had focused on avoiding abuse
until the latest revelations. At this point, were looking more systematically at these programs to
ensure that were taking into account both technological advances and also the need to inspire greater
public confidence, Mr. Rhodes said. We have an ability to do essentially anything technologically. So
do we have the appropriate legal and policy overlay to ensure thats focused?
That will be the question Mr. Obama tries to answer in the speech.
FRINGE NARINT
Interested in this topic, in debate, in contacts? Consider joining the Linked In group; NARINT
US SPIED ON 2009 CLIMATE SUMMIT
Snowden Docs: U.S. Spied On Negotiators At 2009 Climate Summit
www.huffingtonpost.com/2014/01/29/snowden-nsa-surveillance-_n_4681362.html?1391048276
The Huffington Post
Stringer: Kees Kalkman / VDAmok / Utrecht NL / kees@amok.antenna.nl
Jan 31 2014 Jan 29 The National Security Agency monitored the communications of other govern-
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 73
ments ahead of and during the 2009 United Nations climate negotiations in Copenhagen, Denmark,
according to the latest document from whistleblower Edward Snowden.
The document, with portions marked "top secret," indicates that the NSA was monitoring the commu-
nications of other countries ahead of the conference, and intended to continue doing so throughout the
meeting. Posted on an internal NSA website on Dec. 7, 2009, the first day of the Copenhagen summit,
it states that "analysts here at NSA, as well as our Second Party partners, will continue to provide
policymakers with unique, timely, and valuable insights into key countries' preparations and goals for
the conference, as well as the deliberations within countries on climate change policies and nego-
tiation strategies."
"Second Party partners" refers to the intelligence agencies of the United Kingdom, Canada, Australia,
and New Zealand, with which the U.S. has an intelligence-sharing relationship. "While the outcome of
the Copenhagen Climate Change Conference remains uncertain, signals intelligence will undoubtedly
play a significant role in keeping our negotiators as well informed as possible throughout the 2-week
event," the document says.
The Huffington Post published the documents Wednesday night in coordination with the Danish daily
newspaper Information, which worked with American journalist Laura Poitras.
The December 2009 meeting in Copenhagen was the 15th Conference of the Parties to the United
Nations Framework Convention on Climate Change, which brings together 195 countries to negotiate
measures to address rising greenhouse gas emissions and their impact. The Copenhagen summit
was the first big climate meeting after the election of President Barack Obama, and was widely
expected to yield a significant breakthrough. Other major developed nations were already part of the
1997 Kyoto Protocol, which set emissions limits, while the United States -- the world's biggest emitter
of greenhouse gases when the protocol went into effect in 2004 -- had famously declined to join. The
two-week meeting was supposed to produce a successor agreement that would include the U.S., as
well as China, India and other countries with rapidly increasing emissions.
The document indicates that the NSA planned to gather information as the leaders and negotiating
teams of other countries held private discussions throughout the Copenhagen meeting. "[L]eaders and
negotiating teams from around the world will undoubtedly be engaging in intense last-minute policy
formulating; at the same time, they will be holding sidebar discussions with their counterparts -- details
of which are of great interest to our policymakers," the document states. The information likely would
be used to brief U.S. officials, such as Secretary of State Hillary Clinton and Obama, among others,
according to the document.
The document does not detail how the agency planned to continue gathering information during the
summit, other than noting that it would be capturing signals intelligence such as calls and emails.
Previous disclosures have indicated that the NSA has the ability to monitor the mobile phones of
heads of state. Other documents that Snowden has released indicate that the U.K.'s intelligence
service tapped into delegates' email and telephone communications at the 2009 G-20 meetings in
London. Other previous Snowden disclosures documented the surveillance of the G-8 and G-20
summits in Canada in 2010, and the U.N. climate change conference in Bali in 2007.
The document also refers to some intelligence gathered ahead of the meeting, including a report that
"detailed China's efforts to coordinate its position with India and ensure that the two leaders of the
developing world are working towards the same outcome." It refers to another report that "provided
advance details of the Danish proposal and their efforts to launch a 'rescue plan' to save COP-15."
The Danish proposal was a draft agreement that the country's negotiators had drawn up in the months
ahead of the summit in consultation with a small number key of countries. The text was leaked to The
Guardian early in the conference, causing some disarray as countries that were not consulted balked
that it promoted the interests of developed nations and undermined principles laid out in previous
climate negotiations. As Information reports, Danish officials wanted to keep U.S. negotiators from
seeing the text in the weeks ahead of the conference, worried that it may dim their ambitions in the
negotiations for proposed cuts to greenhouse gas emissions.
The Danes did share the text with the U.S. and other key nations ahead of the meeting. But the NSA
document noting this as "advance details" indicates that the U.S. may have already intercepted it. The
paragraph referring to the Danish text is marked "SI" in the Snowden document -- which most likely
means "signals intelligence," indicating that it came from electronic information intercepted by the
NSA, rather than being provided to the U.S. negotiators.
That could be why U.S. negotiators took the positions they did going into the conference, a Danish
official told Information. "They simply sat back, just as we had feared they would if they knew about
our document," the official said. "They made no constructive statements. Obviously, if they had known
about our plans since the fall of 2009, it was in their interest to simply wait for our draft proposal to be
brought to the table at the summit."
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 74
Members of the Danish delegation indicated in interviews with Information that they thought the
American and Chinese negotiators seemed "peculiarly well-informed" about discussions that had
taken place behind closed doors. "Particularly the Americans," said one official. "I was often
completely taken aback by what they knew."
Despite high hopes for an agreement at Copenhagen, the negotiations started slowly and there were
few signs of progress. Obama and heads of state from more than 100 nations arrived late in the
second week in hopes of achieving a breakthrough, but the final day wore on without an outcome.
There were few promising signals until late Friday night, when Obama made a surprise announcement
that he -- along with leaders from China, India, Brazil and South Africa -- had come up with the
"Copenhagen Accord."
The three-page document set a goal of keeping the average rise in global temperature to less than 2
degrees Celsius, but allowed countries to write their own plans for cutting emissions -- leaving out any
legally binding targets or even a path to a formal treaty. Obama called the accord "an unprecedented
breakthrough" in a press conference, then took off for home on Air Force One. But other countries
balked, pointing out that the accord was merely a political agreement, drafted outside the U.N. process
and of uncertain influence for future negotiations.
The climate summits since then have advanced at a glacial pace; a legally binding treaty isn't currently
expected until 2015. And the U.S. Congress, despite assurances made in Copenhagen, never passed
new laws cutting planet-warming emissions. (The Environmental Protection Agency is, however,
moving forward with regulations on emissions from power plants, but a new law to addressing the
issue had been widely considered as preferable.)
The revelation that the NSA was surveilling the communications of leaders during the Copenhagen
talks is unlikely to help build the trust of negotiators from other nations in the future.
"It can't help in the sense that if people think you're trying to get an unfair advantage or manipulate the
process, they're not going to have much trust in you," said Alden Meyer, director of strategy and policy
for the Union of Concerned Scientists and a seasoned veteran of the U.N. climate negotiations. Meyer
said he worried that the disclosure might cause the parties to "start becoming more cautious, more
secretive, and less forthcoming" in the negotiations. "That's not a good dynamic in a process where
you're trying to encourage collaboration, compromise, and working together, as opposed to trying to
get a comparative advantage," he said.
Obama has defended the NSA's work as important in fighting terrorism at home and abroad. But the
latest Snowden document indicates that the agency plays a broader role in protecting U.S. interests
internationally.
National Security Council spokeswoman Caitlin Hayden declined to comment directly on the Snowden
document in an email to The Huffington Post, but did say that "the U.S. Government has made clear
that the United States gathers foreign intelligence of the type gathered by all nations." She noted that
Obama's Jan. 17 speech on the NSA "laid out a series of concrete and substantial reforms the
Administration will adopt or seek to codify with Congress" regarding surveillance.
"In particular, he issued a new Presidential Directive that lays out new principles that govern how we
conduct signals intelligence collection, and strengthen how we provide executive branch oversight of
our signals intelligence activities," Hayden said. "It will ensure that we take into account our security
requirements, but also our alliances; our trade and investment relationships, including the concerns of
our companies; and our commitment to privacy and basic liberties. And we will review decisions about
intelligence priorities and sensitive targets on an annual basis, so that our actions are regularly
scrutinized by the Presidents senior national security team."
Read the full document here:
http://big.assets.huffingtonpost.com/unclimatechangeconference.pdf
ENHANCED GEOTHERMAL ENERGY SYSTEMS
Source: Steven Aftergood / Secrecy News / FAS / Washington / www.fas.org
Jan 30 2014 Jan 30. The potential for new technologies to harvest energy from the Earth's crust
was considered in a new report from the elite JASON science advisory board on "Enhanced Geo-
thermal Systems" (EGS).
"EGS offers important opportunities for increasing the contribution of geothermal energy to U.S. power
production: by a few-fold over the next few years, according to our estimation, and much more so if
this initial success is appropriately leveraged over subsequent years," the report concluded.
As described in the report, EGS entails drilling deep into the Earth's crust -- 1 to 5 kilometers or more -
- and forcing a fluid (water or brine) through hot, permeable rock. Energy from the heated fluid can
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 75
then be extracted.
Of course, the technology is not without hazards. One is the potential for pollution of potable water
acquifers. Another more ominous concern is "induced seismicity" -- or artificially-generated
earthquakes.
"Induced seismicity is a relatively well-documented phenomenon associated with changing fluid
pressures at depth," the report notes. The JASONs assert that "there is a basis for controlling the
induced seismicity and therefore for minimizing this potential hazard attributable to EGS."
The new JASON report is elegantly written and can be at least partially understood by non-specialist
readers who may have forgotten their heat and mass transfer equations. A copy was obtained by
Secrecy News.
Over the past year, the JASONs completed eight classified studies containing sensitive compart-
mented information (SCI) that have not been disclosed. Several other unclassified reports were also
performed and their release is pending.
In 2012, the Central Intelligence Agency refused to release a JASON report entitled "Metamaterials."
FRINGE INTEL 2.0
Interested in this topic, debate, contacts? Consider joining the Linked In group: Intelligence 2.0
MARK ZUCKERBERG RUNS A GIANT SPY MACHINE IN PALO ALTO
http://www.businessinsider.com/deep-state-on-social-networking-privacy-2013-7#ixzz2qh2qGmgM
Business Insider
Source: Beowulf / Grendel Report / US / beowulf@westerndefense.net
Jan 19 2014 Mark Zuckerberg runs a giant spy machine in Palo Alto, California. He wasnt the first
to build one, but his was the best, and every day hundreds of thousands of people upload the most
intimate details of their lives to the Internet. The real coup wasnt hoodwinking the public into revealing
their thoughts, closest associates, and exact geographic coordinates at any given time. Rather, it was
getting the public to volunteer that information.
Then he turned off the privacy settings. [Editor's note: Facebook disputes the notion that it has "turned
off" its privacy settings. We have provided a statement from the company, and a response from one of
the authors, at the bottom of this post.]
People have really gotten comfortable not only sharing more information and different kinds, but more
openly and with more people, said Zuckerberg after moving 350 million people into a glass privacy
ghetto. That social norm is just something that has evolved over time.
If the state had organized such an information drive, protestors would have burned down the White
House. But the state is the natural beneficiary of this new social norm. Today, that information is
regularly used in court proceedings and law enforcement. There is no need for warrants or subpoenas.
Judges need not be consulted. The Fourth Amendment does not come into play.
Intelligence agencies don't have to worry about violating laws protecting citizenry from wiretapping and
information gathering. Sharing information more openly and with more people is a step backward in
civil liberties.
And spies, whether foreign or domestic, are more people, too.
Julian Assange, founder of WikiLeaks, knows better than anyone how to exploit holes in the secrecy
apparatus to the detriment of American security. His raison d'tre is to blast down the walls protecting
state secrets and annihilate the implicit bargain, yet even he is frightened by the brazenness of
Facebook and other such social networking sites:
Here we have the worlds most comprehensive database about people, their relationships, their
names, their addresses, their locations and their communications with each other, their relatives, all
sitting within the United States, all accessible to the U.S. intelligence. Facebook, Google, Yahoo all
these major U.S. organizations have built-in interfaces for U.S.
intelligence. Its not a matter of serving a subpoena. They have an interface that they have developed
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 76
for U.S. intelligence to use.
Its all there, and the Internet never forgets. But even if the impossible happened and the Internet did
somehow develop selective amnesia, in the case of microblogging service Twitter, the Library of
Congress has acquired every message ever posted by its two hundred million members. As Jeffrey
Rosen wrote in the New York Times:
Weve known for years that the Web allows for unprecedented voyeurism, exhibitionism and
inadvertent indiscretion, but we are only beginning to understand the costs of an age in which so much
of what we say, and of what others say about us, goes into our permanent and public digital files.
The fact that the Internet never seems to forget is threatening, at an almost existential level, our ability
to control our identities; to preserve the option of reinventing ourselves and starting anew to overcome
our checkered pasts.
The U.S. government isn't the only institution to notice. Early in the military campaigns in Afghanistan
and Iraq, soldiers of the social networking generation uploaded to their MySpace profiles pictures of
camp life in the war zones. Innocuous photos of troops horsing around in front of tent cities, bunkers,
outposts, motor pools, and operations centers circulated freely on what was then described as a
place for friends.
The U.S. military soon realized that foreign intelligence services, sympathetic to Americas enemies
and savvy to the social revolution, could collect these photographs by the thousands and build
detailed, full-color maps of American military bases. During the Cold War, this would have required the
insertion of first-rate spies, briefcases filled with cash, and elaborate blackmail schemes. In the age of
radical transparency, all it would take is a MySpace account to know exactly where to fire the mortar
round to inflict maximum damage on the United States.
The Marine Corps confirmed this in a 2009 directive. These Internet sites in general are a proven
haven for malicious actors and content are a particularly high risk due to information exposure, user
generated content and targeting by adversaries. The directive continued, The very nature of [social
networking sites] creates a larger attack and exploitation window, exposes unnecessary information to
adversaries and provides an easy conduit for information leakage, putting operational security,
communications security, and U.S. military personnel at an elevated risk of compromise.
This type of clever thinking on the part of Americas enemies is not unique to this conflict. During the
run-up to the Gulf War, foreign intelligence services had a pretty good idea that the U.S. war machine
was preparing for its most substantial engagement since Vietnam. The U.S. military recognized a new
kind of threat one that didnt require foreign intelligence to insert an agent onto every base in the
Republic. Open source information could be just as dangerous. Spikes in late-night orders from
pizzerias near key military bases and an exceptionally busy parking lot at the Pentagon could tell
hostile powers everything they needed to know.
In determining what should remain secret and what should not, the military like each component of
the American secrecy apparatus is good at overreaction. The default answer: more secrets. To
counter the MySpace problem, they banned blogs and social networks. This benefitted base security
but killed morale at home. No longer could parents see their young sons and daughters safe and
even happy in the war zone. All that remained were breathless reports of intense combat on the
cable news networks. And while the average supply clerk is probably safer in Baghdad than in Detroit,
every parent and spouse saw the same thing: a son or daughter in a flag-draped casket.
In 2010, the Department of Defense revised and consolidated its ad hoc policy on social media. On its
official website it declared, Service members and [Department of Defense] employees are welcome
and encouraged to use new media to communicate with family and friends at home stations or
deployed, but warned, its important to do it safely.)
From "Deep State: Inside the Government Secrecy Industry" by journalists Marc Ambinder and D.B.
Grady. Reprinted with permission from D.B. Grady.
*"When the book was actually written, they were still in Palo Alto." - D.B. Grady
In a statement to Business Insider, Facebook notes: "In reality we spend a lot of time building privacy
controls, and working to make them powerful, easy to use, and also educating our users on them. For
example:
- Announcing new tools in December:
http://newsroom.fb.com/News/547/Better-Controls-for-Managing-Your-Content
- (in the same post) In-product education about privacy that we did in December:
http://newsroom.fb.com/News/547/Better-Controls-for-Managing-Your-Content
- Recent flyout in the News Feed ahead of Graph Search that pointed to the new tools and highlighted
how people could check their stuff:
http://newsroom.fb.com/News/660/Expanding-Graph-Search-Beta"
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 77
FRINGE NETHERLANDS
Interested in this topic, in debate and in contacts? Consider joining the Linked In group:
Dutch Intelligence Watch specialists
PHILIPS WERKTE SAMEN MET NSA - 2
www.trouw.nl/tr/nl/14468/Buitenland/article/detail/3585933/2014/01/29/Philips-werkte-samen-met-NSA.dhtml
Volkskrant
Jan 29 2014 Jan 29. Philips leverde jarenlang telefoons aan het ministerie van buitenlandse zaken
telefoons die zijn ontwikkeld door de Amerikaanse veiligheidsdienst NSA. Dat blijkt uit archiefonder-
zoek van de Groene Amsterdammer. Of de samenwerking tussen Philips en NSA betekent dat de
veiligheidsdienst decennialang informatie heeft kunnen aftappen, is onduidelijk.
De samenwerking tussen Philips en NSA startte al in 1977. Toen haalde het elektronicabedrijf zijn
eigen versleutelingsprogramma voor de NAVO van de markt haalde. In plaats daarvan stapte Philips,
of eigenlijk het dochterbedrijf USFA, over op een programma dat was ontwikkeld door veiligheids-
dienst NSA. KG-81, zoals het versleutelingsprogramma heet, was 2,5 keer sneller dan het systeem
dat uit de koker kwam van Philips.
Als dank voor de overstap mocht Philips de KG-81 gaan produceren voor de Europese markt. Vanaf
1980 bouwde dochterbedrijf USFA honderden codeermachines en digitaal beveiligde telefoons met
NSA-programmatuur voor de Europese markt. De opdrachten bleven toenemen en de omzet schoot
omhoog.
Ook het Nederlandse leger en dus ook het ministerie van buitenlandse zaken voorzag Philips onder-
meer van telefoons waarbij woorden meteen werden vervormd. Pas aan het andere uiteinde werden
deze woorden weer verstaanbaar gemaakt. Of de NSA misbruik kon maken van haar positie als ont-
wikkelaar van het besturingsprogramma van de telefoons en codeermachines, is onduidelijk.
De Groene Amsterdammer schrijft dat het nu wachten is op meer onthullingen. Maar volgens NRC
Handelsblad is de kans zeer klein dat NSA Nederlandse telefoons aftapte. Om de telefoons in gebruik
te nemen, moest een speciale sleutel geladen worden, zegt NRC-verslaggever Steven Derrix. Alleen
door die sleutels met anderen te delen, was aftappen mogelijk. Derrix: "Nederland had eigen beveilig-
de sleutels die niet zijn gedeeld. De NAVO gebruikte wel sleutels van de NSA, maar dat is niet zo
vreemd als je bedenkt dat de apparatuur daar gebruikt wordt voor militaire communicatie."
PHILIPS WERKTE SAMEN MET NSA - 1
Philips werkte jarenlang intensief samen met NSA-spionnen
http://www.volkskrant.nl/vk/nl/2680/Economie/article/detail/3585464/2014/01/29/Philips-werkte-
jarenlang-intensief-samen-met-NSA-spionnen.dhtml
Volkskrant / byMichael Persson
Jan 29 2014 Jan 29. Elektronicaconcern Philips heeft jarenlang intensief samengewerkt met de
Amerikaanse inlichtingendienst NSA. Philips verkocht beveiligde telefoons aan de Nederlandse
overheid, waarvan de versleuteling afkomstig was van de Amerikaanse spionnen en hun Britse
collega's (de GCHQ, Government Communications Headquarters).
De telefoons zijn tot een paar jaar geleden door het Nederlandse leger en op ambassades gebruikt.
De NSA bevond zich in het hart van het Nederlandse militaire en diplomatieke verkeer. Philips liep in
zekere zin aan de leiband van de NSA, zo beschrijft onderzoeksjournalist en Philips-biograaf Marcel
Metze in een artikel dat vandaag in De Groene Amsterdammer verschijnt.
Uit archiefonderzoek en gesprekken met voormalige medewerkers van Philips-dochter Ultra Sonore
Fabricage Afdeling (USFA), de cryptografische afdeling van het concern, blijkt dat het bedrijf wel met
de Amerikanen moest samenwerken. Zonder de NSA-input maakten de Nederlanders geen kans op
opdrachten van NAVO-landen.
Encryptiemachines
Dus nam Philips de NSA aan boord, toen het begin jaren tachtig encryptiemachines ging bouwen voor
de NAVO en meedong naar een grote order (200 miljoen gulden) voor een nieuw
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 78
communicatienetwerk voor het Nederlandse leger. Philips leverde in de jaren daarna onder de
codenaam Zodiac mobiele verbindingen, telefooncentrales en duizenden digitaal beveiligde telefoons
aan het leger. De telefoons waren zeer vernieuwend: ze verhaspelden de woorden meteen tijdens het
spreken. Ook het ministerie van Buitenlandse Zaken nam de telefoons af.
De NSA leverde een met de GCHQ ontwikkeld versleutelingsprogramma voor de telefoons, Saville,
dat ingebakken in drie chips in de apparaten werd ingebouwd. Er waren slechts enkele medewerkers
bij Philips die het algoritme kenden.
Overigens zat de NSA-code in alle apparatuur van de NAVO-landen. 'De NSA had die order
gewonnen, zij waren gewoon de beste', zegt hoogleraar computerbeveiliging Bart Jacobs van de
Radboud Universiteit Nijmegen.
Of de Amerikanen hun kennis misbruikt hebben is niet duidelijk. Betrokken Philips-medewerkers
zeggen daarvan niet op de hoogte te zijn. Als de Amerikanen opzettelijk een zwakke plek (een
'achterdeur') in de software zouden hebben ingebouwd, zou dat henzelf ook kwetsbaar hebben
gemaakt zegt Jacobs. 'Want zij gebruikten de apparaten zelf ook binnen de NAVO.'
Achterdeurtjes
Uit documenten van Snowden is vorig jaar gebleken dat de NSA graag dergelijke achterdeurtjes
inbouwt in commercile encryptiesoftware. Zo bleek vorig jaar dat de NSA ook een zwakke plek had
laten maken in een algoritme van het bedrijf RSA. De commissie die president Obama adviseerde
over de NSA pleitte er in december voor dat de dienst zich niet meer bemoeit met encryptiesoftware
bij bedrijven. Of de NSA nog steeds apparatuur levert aan NAVO-landen is niet bekend. Jacobs: 'Ik
kan me niet voorstellen van niet.'
Philips wil hierop niet inhoudelijk reageren, omdat het archief van de betrokken dochter USFA in 1989
via de verkoop van Holland Signaal is beland bij het Franse Thomson. Ook noemt een woordvoerder
delen van het verhaal speculatief. 'Wij zien op grond hiervan geen aanleiding om eigen onderzoek te
beginnen.'
Een woordvoerder van het ministerie van Defensie zegt dat het 'niet meer dan logisch is' dat
bondgenoten met elkaar kunnen praten. 'Dan is het ook niet raar dat diensten voor encryptie van
communicatieapparatuur met bedrijven samenwerken.'
STEDEN RUNNEN HUN EIGEN INLICHTINGENDIENST
www.trouw.nl/tr/nl/4500/Politiek/article/detail/3585734/2014/01/29/Steden-runnen-hun-eigen-inlichtingendienst.dhtml
Trouw / by Marten van de Wier and Perdiep Ramesar
Jan 29 2014 Jan 29. Eindhoven en Tilburg gaan met eigen inlichtingenmedewerkers de strijd aan
met criminelen. De gemeenten analyseren zelf politiegegevens, omdat politie en justitie daar niet altijd
aan toekomen. "De opsporingscapaciteit van het OM is beperkt", zegt burgemeester Rob van Gijzel.
Hij wil dat minister Opstelten het mogelijk maakt dat meer politiedata naar de gemeenten gaan.
In Tilburg en Eindhoven zijn medewerkers vrijgemaakt om data over criminaliteit te analyseren. Deze
intelligence-medewerkers trekken aan de bel bij opvallende ontwikkelingen, zoals een inbraakgolf.
Volgens hoogleraar Algemene Rechtwetenschappen Jan Brouwer past het in de ontwikkeling dat
gemeenten het werk doen dat vroeger de gemeentepolitie deed. Naast de intelligence-medewerkers
achter hun bureau heb je ook de bijzonder opsporingsambtenaren (boa's) op straat. "Gemeenten zien
met lede ogen dat de nationale politie weinig oog heeft voor kleine criminaliteit. De bevolking vraagt
om veiligheid, en gemeenten nemen hun verantwoordelijkheid."
Oppassen
Brouwer, die werkt aan de Rijksuniversiteit Groningen, heeft 'gemengde gevoelens' bij die trend. De
politie is aan strenge regels gebonden, maar voor gemeenteambtenaren ontbreekt dat wettelijk kader
vaak. "We moeten oppassen voor een overheid die almachtig wordt."
Politiegegevens zijn beschermd, en mogen niet zomaar aan een gemeente worden verstrekt vanwege
de privacy van verdachten. Eindhoven krijgt nu op incidentele basis of via convenanten informatie van
de politie, maar de gemeente wil structureel beschikken over bepaalde informatie. Sinds de Wet Poli-
tiegegevens uit 2007 kan dat, als er een 'zwaarwegend belang' is. Opstelten zou positief tegenover
het voorstel staan.
Preventief
Eindhoven wil de informatie onder meer gebruiken voor het jeugdbeleid. "Als wij weten dat van een
gezin de oudste broer is opgepakt, kunnen we voorkomen dat in dat gezin ook jongere kinderen in de
problemen komen", zegt Van Gijzel. "De politie zit op het strafrecht. Wij zijn meer preventief bezig."
Andere grotere gemeenten hebben geen intelligence units. Woordvoerders van de grote steden zeg-
gen dat die niet nodig zijn, omdat er al verschillende organen zijn waar informatie wordt geanalyseerd
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 79
en gedeeld. Zo is er het vaste overleg van burgemeester, korpschef en officier van justitie. Ook heeft
de politie eigen informatie- en inlichtingenafdelingen, en er is het Regionaal Inlichtingen en Expertise
Centrum (RIEC) waar regionaal informatie wordt gedeeld.
AIVD INFORMEERT BURGEMEESTERS OVER AFA
https://www.aivd.nl/algemene-onderdelen/uitgebreid-zoeken/@2449/aivd-informeert/
AIVD
Jan 19 2014 De AIVD heeft alle burgemeesters van Nederland vandaag in een brief genformeerd
over de werkwijze van de Anti Fascistische Actie (AFA). De linkse AFA zoekt de confrontatie met in
hun ogen rechtse partijen tijdens partijbijeenkomsten en demonstraties en probeert dit soort bijeen-
komsten te voorkomen door het lokale bestuur op oneigenlijke wijze of onder valse voorwendselen te
benaderen. AFA past deze werkwijze ook toe in de aanloop naar de gemeenteraadsverkiezingen. De
AIVD licht de AFA-werkwijze toe zodat bestuurders in staat zijn hierop adequaat te reageren.
AFA benadert regelmatig vaak onder het mom van een antidiscriminatiebureau gemeentebesturen
om te voorkomen dat in hun ogen rechtse groeperingen de mogelijkheid krijgen bijeenkomsten te
houden of te demonstreren. Wanneer AFA kennis heeft van een geplande demonstratie door rechts,
worden gemeenten en bijvoorbeeld zaaleigenaren benaderd en gewaarschuwd voor materile schade
die het gevolg kan zijn van dergelijke demonstraties. Schade is in de regel echter juist het gevolg van
AFAs tegendemonstraties.
Elke gemeente die op enigerlei wijze ruimte biedt aan activiteiten van deze rechtse bewegingen kan
te maken krijgen met AFA. De AIVD brengt waar mogelijk altijd de lokale autoriteiten via de regionale
inlichtingendiensten (RIDen) vroegtijdig op de hoogte van te verwachten ontwikkelingen
Fringe De brief van de AIVD
Activiteiten Antifascistische Actie in relatie tot lokaal bestuur
Inleiding
De AIVD constateert dat de antifascistische actie (AFA) in het verwezenlijken van haar doelstellingen
gebruik maakt van valse voorwendselen en oneigenlijke middelen. AFA benadert regelmatig dikwijls
in de meer neutrale hoedanigheid van een antidiscriminatiebureau het lokaal bestuur, met als doel
te voorkomen dat in hun ogen fascistische groeperingen de mogelijkheid krijgen om hun doelstellin-
gen en activiteiten lokaal en nationaal te verwezenlijken.
De werkwijze van AFA kan zich richten op iedere gemeente die op enigerlei wijze ruimte biedt aan
activiteiten van, naar inzicht van AFA, rechtse bewegingen. AFA past deze werkwijze ook toe in de
aanloop naar de gemeenteraadsverkiezingen, hetgeen aanleiding is u nader te informeren over de
door de AIVD geconstateerde ontwikkelingen met betrekking tot de werkwijze van AFA.
Geschiedenis en ontwikkeling AFA
AFA is opgericht in 1992 en heeft verschillende lokale afdelingen. De meeste van deze afdelingen
worden via een landelijk secretariaat aangestuurd, sommige acteren autonoom. In de bij haar
oprichting uitgebrachte persverklaring stelde AFA zich nadrukkelijk ten doel om manifestaties van
fascisten te voorkomen. Hiertoe wilde zij de confrontatie aangaan en zonodig verhinderen dat
dergelijke manifestaties plaatsvonden.
Waar de antifascistische beweging begon als een groep puur gewelddadige actievoerders, van wie
een zekere dreiging uitging (zoals grootschalige verstoring van de openbare orde), groeide zij de
laatste twee decennia uit tot een meer politieke lobbygroep.
Gebruik van geweld, in eerste instantie tegen de rechtse tegenstander maar daarnaast zeker ook
tegen de politie, bleef echter volgens AFA geoorloofd.
AFA verrichtte de laatste jaren steeds meer lobbywerk naar, onder meer, het lokaal bestuur. Daarbij
wordt bijvoorbeeld gewaarschuwd voor grote schade die kan ontstaan bij manifestaties van
extreemrechts. Ook slaagt AFA er frequent in te infiltreren in extreemrechtse groeperingen.
Sinds 2000 tracht AFA in toenemende mate elke rechtse activiteit in willekeurig welke gemeente te
verhinderen. Daarbij wordt geen onderscheid gemaakt tussen rechtsextremistische groeperingen die
het gebruik van geweld niet schuwen en (extreem)rechtse partijen die zich beperken tot het gebruik
van politieke middelen.
Werkwijze AFA
Benvloeding
AFA gebruikt verschillende methoden om haar doel te realiseren. Zij doet zich in haar contacten met
gemeenteambtenaren en (lokale) politici vaak voor als n van de vele antidiscriminatiebureaus. In die
hoedanigheid biedt zij haar expertise aan. Met name wanneer (extreem)rechtse partijen en
groeperingen een demonstratie aanmelden, komt AFA in actie en benadert zij het betreffende lokaal
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 80
bestuur, alsmede de zaaleigenaren in de (buurt)gemeenten. De AIVD constateert dat de AFA bij haar
activiteiten gebruik maakt van oneigenlijke middelen.
Woordvoerders van AFA treden hun gesprekspartners niet onder eigen naam tegemoet. AFA richt
zich tot zaaleigenaren om hen te bewegen, onder verwijzing naar te verwachten schade, geen
contract af te sluiten met (extreem)rechtse groeperingen. Ook tracht zij op oneigenlijke wijze invloed
uit te oefenen op lokaal beleid; eveneens onder alias. Zo worden gemeenten aangeschreven met
verwijzingen naar eventuele grote materile schade door toedoen van extreemrechts, wanneer de
gemeente een demonstratie van extreemrechts toestaat. In sommige gevallen heeft dit geleid tot
annulering van een demonstratie, die vervolgens met succes bij de rechter werd aangevochten door
bijvoorbeeld de Nederlandse Volksunie (NVU). Wanneer de manifestaties wel doorgang vinden, wordt
de materile schade doorgaans veroorzaakt door antifascisten en hun sympathisanten zelf, en niet
door rechtse demonstranten.
De AIVD heeft in diverse gevallen geconstateerd dat lokale bestuurders door AFA zijn benaderd om
aan AFA bruikbare informatie te leveren over activiteiten van rechtse groepen en partijen. Dit
gebeurde met de waarschuwing voor mogelijke ernstige verstoringen van de openbare orde door
rechtse groeperingen. In n geval verschafte een door AFA benaderde, gentimideerde, persoon
diverse data waaronder persoonsgegevens aan AFA. Deze, gedeeltelijk dus ook vertrouwelijke,
informatie werd vervolgens door AFA breed verspreid. Dit heeft in het verleden geleid tot fysiek
geweld tegen personen die volgens AFA extreemrechts zijn.
Daarnaast tracht AFA in relatie tot verkiezingen zeer vroegtijdig in het bezit te komen van
kandidatenlijsten en persoonsgegevens van kandidaten. Zij doen dit via contactpersonen binnen
partijen. Deze data worden in sommige gevallen gebruikt in eigen onderzoek van AFA naar, deels
vermeende, rechtsextremisten. Daarbij is het gebeurd dat individuen ten onrechte werden neergezet
als rechtsextremist en als zodanig werden geschaad.
Tegendemonstraties van AFA
Acties van AFA kunnen ook een meer gewelddadige vorm aannemen. Dit is bijvoorbeeld het geval bij
demonstraties tegen de in hun ogen rechtse tegenstander, zoals de extreemrechtse NVU, of de ter
plaatse optredende Mobiele Eenheid.
De werkwijze van AFA volgt hierbij meestal een vast patroon. Tot 2009 meldde AFA in dezelfde
gemeente een eigen tegendemonstratie aan, met als doel een demonstratie van de NVU te verstoren.
Sinds 2009 worden deze acties georganiseerd door een AFAwerkgroep met de naam Laat Ze Niet
Lopen (LZNL). Deze tegendemonstraties worden doorgaans geaccepteerd. De NVU demonstreert en
AFA roept elke linkse demonstrant op om het politiekordon te doorbreken, om zo te trachten een
(gewelddadige) confrontatie met de NVU aan te gaan. Dit mislukt in de meeste gevallen, waarna het
vaak tot een harde confrontatie komt tussen antifascisten en de Mobiele Eenheid. Voorbeelden waren
in 2009 Maastricht (anti-Voorpost manifestatie) en in Venlo (anti-NVU betoging).
In de loop van 2009 heeft AFA haar werkwijze met betrekking tot tegendemonstraties verder ontwik-
keld. AFA meldt niet langer al haar tegendemonstraties aan. Bovendien speelt de AFA-activist tijdens
acties nu meer een aansturende rol dan een deelnemende. Leden van de AFA werkgroep LZNL zijn
door infiltratie vaak vroegtijdig op de hoogte van plaats en datum van demonstraties. LZNL zoekt
vervolgens lokaal hulp en benadert groepen die te mobiliseren zijn om tegen rechts te demonstreren.
Dit kunnen bijvoorbeeld de plaatselijke moskee, Marokkaanse verenigingen of voetbalhooligans met
linkse sympathien zijn. Ook de werkwijze op straat is veranderd: deelnemers verschijnen nu in kleine
groepjes en in nette kleding. Deze groepen trachten door middel van hit-en-run acties bij de tegen-
standers te komen of door het blokkeren van de route hun demonstratie te verhinderen. Deze nieuwe
werkwijze is vorig jaar uitgeprobeerd in Den Bosch, Maastricht en Venlo.
WOB
Via de Wet Openbaarheid van Bestuur (WOB) vragen AFA-vertegenwoordigers allerlei voor hen
nuttige informatie op. Recent zijn nieuwe WOB-voorschriften opgesteld waarbij bijvoorbeeld een
overschrijding van de beantwoordingstermijn financile consequenties heeft voor de aangeschrevene.
Niet uitgesloten kan worden dat deze regelgeving, bijvoorbeeld als extra inkomstenbron, door AFA
wordt aangegrepen om nog meer verzoeken in te dienen.
Gemeenteraadsverkiezingen 2010
In 2009 is binnen AFA een werkgroep opgericht, die het doel heeft om de plannen van de PVV in
kaart te brengen met het oog op de gemeenteraadsverkiezingen. Inmiddels hebben diverse manifes-
taties van antifascisten en geestverwanten plaatsgevonden. De eerste hiervan was een lawaaidemon-
stratie in Waddinxveen (februari 2009) waar PVV-leider Wilders zijn opwachting maakte. Begin no-
vember 2009 trok een fakkeloptocht in Arnhem ongeveer tweehonderd deelnemers. Naast (veelal
jonge) antifascisten namen daaraan ook oudere verontruste burgers en allochtone Nederlanders deel.
De manifestatie werd door de organisatoren (AFA) als een groot succes beoordeeld en gaf aanleiding
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 81
om de samenwerking met lokale groeperingen en individuen vaker te zoeken in relatie tot de gemeen-
teraadsverkiezingen. De AIVD heeft aanwijzingen dat AFA in de aanloop naar de verkiezingen meer
van dit soort acties voorbereidt, waarbij zij zich naast de PVV ook richt op partijen als NVU, Trots op
Nederland en de Partij Vrij Utrecht van Wim Vreeswijk.
Op zich is een en ander geoorloofd. AFA beschikt echter over een harde kern die geweld niet schuwt,
en het valt niet uit te sluiten dat n of meer van de bijeenkomsten van deze partijen zal ontaarden in
verstoringen van de openbare orde. De intensiteit van de acties zal mogelijk toenemen met het
naderbij komen van de verkiezingen. Een onberekenbare factor is de deelname van allerlei lokale
actievoerders aan de AFA-manifestaties. In het verleden heeft dit escalerend gewerkt.
Conclusie
AFA is volgens de AIVD geen antidiscriminatie- of onderzoeksbureau, maar veeleer een actiegroep
die in het realiseren van haar doelstellingen soms op oneigenlijke wijze lokale bestuurders benadert.
Daarnaast wordt geweld tegen in hun ogen extreemrechts en/of ordebewaarders niet geschuwd. De
AIVD zal, zoals altijd, waar mogelijk de lokale autoriteiten middels de RID vroegtijdig op de hoogte
brengen van de te verwachten ontwikkelingen.
in the Fringe
THE REMOTE STOPPING OF CARS
EU has secret plan for police to 'remote stop' cars
The EU is developing a secret plan to give the police the power to control cars by switching the
engine off remotely
www.telegraph.co.uk/news/worldnews/europe/eu/10605328/EU-has-secret-plan-for-police-to-remote-stop-cars.html
Telegraph
Source: Steven Aftergood / Secrecy News / FAS / Washington / www.fas.org
Jan 30 2014 Jan 29. The European Union is secretly developing a "remote stopping" device to be
fitted to all cars that would allow the police to disable vehicles at the flick of a switch from a control
room.
Confidential documents from a committee of senior EU police officers, who hold their meetings in
secret, have set out a plan entitled "remote stopping vehicles" as part of wider law enforcement
surveillance and tracking measures.
"The project will work on a technological solution that can be a 'build in standard' for all cars that enter
the European market," said a restricted document.
The devices, which could be in all new cars by the end of the decade, would be activated by a police
officer working from a computer screen in a central headquarters.
Once enabled the engine of a car used by a fugitive or other suspect would stop, the supply of fuel
would be cut and the ignition switched off.
The technology, scheduled for a six-year development timetable, is aimed at bringing dangerous high-
speed car chases to an end and to make redundant current stopping techniques such as spiking a
vehicle's tyres.
The proposal was outlined as part of the "key objectives" for the "European Network of Law
Enforcement Technologies", or Enlets, a secretive off-shoot of a European "working party" aimed at
enhancing police cooperation across the EU.
Statewatch, a watchdog monitoring police powers, state surveillance and civil liberties in the EU, have
leaked the documents amid concerns the technology poses a serious threat to civil liberties
"We all know about the problems surrounding police stop and searches, so why will be these cars
stopped in the first place," said Tony Bunyan, director of Statewatch.
"We also need to know if there is any evidence that this is a widespread problem. Let's have some
evidence that this is a problem, and then let's have some guidelines on how this would be used."
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 82
The remote stopping and other surveillance plans have been signed off by the EU's Standing
Committee on Operational Cooperation on Internal Security, known as Cosi, meaning that the project
has the support of senior British Home Office civil servants and police officers.
Cosi, which also meets in secret, was set up by the Lisbon EU Treaty in 2010 to develop and
implement what has emerged as a European internal security policy without the oversight of MPs in
the House of Commons.
Douglas Carswell, the Conservative MP for Clacton, attacked the plan for threatening civil liberties and
for bypassing the parliament.
"The price we pay for surrendering our democratic sovereignty is that we are governed by an
unaccountable secretive clique," he said.
Nigel Farage, the leader of Ukip, described the measure as "incredible" and a "draconian imposition".
"It is appalling they are even thinking of it," he said. "People must protest against this attack on their
liberty and vote against an EU big Brother state during the Euro election in May."
In 2012, Enlets received a ?484,000 grant from the European Commission for its declared mission to
"support front line policing and the fight against serious and organised crime by gathering user
requirements, scanning and raising awareness of new technology and best practices, benchmarking
and giving advice".
The six-year work programme for Enlets also includes improving automatic number plate recognition
technology and intelligence sharing. Although the technology for police to stop a vehicle by remote
control has still to be developed, Enlets argues the merits of developing such a system.
"Cars on the run can be dangerous for citizens," said a document. "Criminal offenders will take risks to
escape after a crime. In most cases the police are unable to chase the criminal due to a lack of
efficient means to stop the vehicle safely."
The introduction of stopping devices has raised questions of road safety. David Davis, the
Conservative MP for Haltemprice and Howden, warned that the technology could pose a danger to all
road users.
"I would be fascinated to know what the state's liability will be if they put these devices in all vehicles
and one went off by accident whilst a car was doing 70mph on a motorway with a truck behind it
resulting in loss of life," he said.
"It is time legislators stopped believing technology is a form of magic and realised that is fallible, and
those failures do real harm."
Fringe Colophon
About the editor/publisher: Roger Vleugels
In 1986, I started my own office and began working as a legal advisor / acting lawyer and lecturer specialized in freedom of
information and intelligence. In 2001, I added the publishing of the Fringe journals to my activities.
I lecture on freedom of information at journalism schools, universities and corporations. I have taught students in or from
Argentina, Aruba, Belgium, Bulgaria, Denmark, Estonia, Finland, Germany, Hungary, Indonesia, Italy, Iran, Ireland, Macedonia,
Mexico, Moldova, the Netherlands, Norway, Slovakia, South Africa, Sweden, Turkey and the United Kingdom.
Since 1988, I have as a legal advisor / acting lawyer filed for or with my clients more than 4,500 FOIA requests. Most of these
clients are journalists in the Netherlands but also special interest groups, NGOs, researchers and private persons.
As an intelligence specialist, I research and lecture on this topic, with a focus on forensic and operational aspects. I comment in
the press, brief members of parliament and advise journalists and lawyers.
The format of the Fringe journals
The main goal of the Fringe journals is: not being a regular magazine. The journals are purely a research tool. Articles are not
selected for their content but for the facts or trends within them. One of the consequences is that Fringe does not dis-
criminate between information and disinformation.
Other goals are trying to publish news in early stages, before the news is established with an overall focus on next to main-
stream. After doing so Fringe will not cover such a topic further, unless there is again something special, and above all: Fringe
hopes to be a bit wayward.
Surfing, searching, stringers and sources
Articles are gathered for Fringe by a small group of Dutch and foreign stringers, some of whom work covertly. Without the work
of these stringers Fringe would not be possible. Additionally I do some gathering on my own, mainly by netsurfing and maintain-
ing a range of subscriptions, feeds and alerts. Some of the more specialized sources are: Access Info Europe, Article 19, Be-
Spacific, Bits of Freedom, Centre for Law & Democracy, Cryptogram, CFOI, Cryptome, EDRi-gram, EFF, EPIC, FOIANet, Free-
FRINGE INTELLIGENCE - year 13 - no.284 February 1 2014 - page 83
domInfo, Geheim, Infowarrior, Intelforum, Intelligence Online, Memory Hole, Mother Jones, National Security Archive, Nato-
Watch, NISA, Privacy International, RCFP, Secrecy News, StateWatch, Terrorism Monitor and Wired.
Two Fringe journals
Fringe Intelligence gathers intelligence news from established media and outlets beyond the mainstream. The journal offers ar-
ticles covering classical intelligence and counterintelligence, criminal and private espionage and more. The main focus is on
forensic and operational information, and not on bureaucracy, politics and the formal/legal aspects of intelligence. Fringe Intel-
ligence does not concentrate on terrorism. Special sections highlight NARINT, or Natural Resources Intelligence [dealing with
energy, rare earth, water and climate intelligence], and Intelligence 2.0 [IT sector-generated private intelligence]. These sections
look beyond jihad, cyber and other previous or present threats.
Fringe Spitting publishes for freedom of information [FOI] specialists, investigative journalists and other researchers, with a spe-
cial focus on FOI practitioners and requesters, news on caseload, jurisprudence, litigation, tools and trends. Space is also devo-
ted to recently disclosed old news on intelligence, revealed by FOI requests.
Taken together, the two biweekly journals contain about 100 articles per month selected from a variety of media sources. Almost
all articles are internet downloads. Over 90% are in English. Less than 10% are focused on the Netherlands.
3,100 subscribers
In terms of circulation, both Fringe journals enjoy a top ranking in their sector, respectively OSINT and FOI, among the world-
wide communities of independent email journals and mailing lists.
Fifty-five percent of the subscribers are intelligence specialists, 30% journalists and 15% FOIA specialists. They live in 118
countries: 35% in NL, 25% in US, 5% in the UK and 35% in the rest of the world.
Pose questions directly or by LinkedIn or Twitter
Please feel free to mail me directly. You can also contact me by the networks I belong to. More than 2,000 subscribers have
joined one or more groups managed by me on LinkedIn: FOIA Specialists; Wob Specialists; NARINT; Dutch Intelligence
Watch Specialists or Intelligence 2.0.
I am also active on Twitter. Most of my tweets are in Dutch. Breaking news I tweet in English: @RogerVleugels. For privacy
and usability reasons, I do not like Facebook. Therefore I am only passively present on that network.
Fringe is solely a research tool
All articles [re]published in Fringe are solely meant for research by the subscribers themselves. It is forbidden to [re]publish or
[re]circulate articles either in part or in their entirety. This is not a Fringe policy but a consequence of the Fair Use Notice.
Because Fringe is a free-of-charge research tool, it is permitted to recirculate copyrighted material according to the Fair Use
Notice. One of the conditions is: in a closed circuit; that is why there is no site.
More information on this rule is available at the end of this colophon.
The meaning of the symbol
At the start of an article you will find several . They identify the source and the date of the article.
The source: after one or more you will find the source [the first source mentioned is the original one, the latter source is the
publication or stringer from which/whom Fringe received the article].
The date: before you will see the date on which Fringe received the article; after the original publication date [if known].
Subscriptions are free of charge and include both journals
Subscribers receive both journals free of charge. A voluntary contribution is very welcome, however. Producing Fringe is a time-
consuming project. Each year in January I ask subscribers for a voluntary contribution.
Copyright law [see the Fair Use Restriction at the bottom of this colophon] forbids to charge for journals like Fringe. Therefore,
the only way to collect enough money to keep this service going is by voluntary contributions or donations.
To guarantee the service in the long run 400-500 paying subscribers on a yearly basis are needed. This number is now about
150 and rising. so please consider paying the voluntary contribution every your or once in every 2, 3 or 4 years.
To start a subscription e-mail 'Start Fringe' and to unsubscribe 'Stop Fringe' in the subject line, to roger.vleugels@planet.nl
Voluntary contributions or donations are very welcome
My suggestion:
48.00 Euros per year for individual subscribers [this equals one Euro per issue]
24.00 Euros per year for students and others with modest means
200.00 Euros per year for news media or other organizations with multiple users/subscribers or subscribers who are well to do
Payments via the bank
ING Bank: IBAN: NL79 INGB 0003 4320 10 / BIC: INGBNL2A, account holder: Roger Vleugels, Utrecht, The Netherlands
Reference: Fringe contribution of Fringe donation
Payments by post or check (for larger sums, please use registered mail)
Roger Vleugels / Korfoedreef 213 / 3562 SL Utrecht / The Netherlands
Reference: Fringe contribution of Fringe donation
Fair Use Notice
The Fringe journals contain copyrighted material the use of which has not always been specifically authorized by the copyright
owner. The material is being made available for purposes of education and research of the subscribers themselves. This
constitutes a "fair use" of such copyrighted material as provided for in section 107 of the US Copyright Law.
In accordance with Title 17 U.S.C. Section 107, the material on these journals are distributed without profit to those who have
expressed an interest in receiving the included information for research and educational purposes only. If a subscriber wishes to
use copyrighted material from these journals for purposes that go beyond "fair use," you must obtain permission from the
copyright owner. For more information: www.law.cornell.edu/uscode/17/107.html
S-ar putea să vă placă și
- No Place to Hide: Edward Snowden, the NSA, and the U.S. Surveillance StateDe la EverandNo Place to Hide: Edward Snowden, the NSA, and the U.S. Surveillance StateEvaluare: 4 din 5 stele4/5 (250)
- Dead Wrong: Straight Facts on the Country's Most Controversial Cover-UpsDe la EverandDead Wrong: Straight Facts on the Country's Most Controversial Cover-UpsEvaluare: 3.5 din 5 stele3.5/5 (13)
- Ethics For The Information Age: Chapter 5 - Privacy IIDocument51 paginiEthics For The Information Age: Chapter 5 - Privacy IISaimaTahirÎncă nu există evaluări
- Nsa PDFDocument13 paginiNsa PDFapi-252964796Încă nu există evaluări
- Conspiracy X 20 - Introductory Game KitDocument34 paginiConspiracy X 20 - Introductory Game KitRodrigo Trajano100% (1)
- Inside Rumsfeld's Orwellian PentagonDocument5 paginiInside Rumsfeld's Orwellian PentagonLiam CowdenÎncă nu există evaluări
- Bravehearts: Whistle-Blowing in the Age of SnowdenDe la EverandBravehearts: Whistle-Blowing in the Age of SnowdenEvaluare: 4 din 5 stele4/5 (5)
- NSA Secrets: Government Spying in the Internet AgeDe la EverandNSA Secrets: Government Spying in the Internet AgeEvaluare: 4 din 5 stele4/5 (3)
- No Place To Hide - Glenn GreenwaldDocument3 paginiNo Place To Hide - Glenn Greenwaldtony alvaÎncă nu există evaluări
- The Panama Papers: Breaking the Story of How the Rich and Powerful Hide Their MoneyDe la EverandThe Panama Papers: Breaking the Story of How the Rich and Powerful Hide Their MoneyEvaluare: 4 din 5 stele4/5 (52)
- NSA Snooping Act of TreasonDocument3 paginiNSA Snooping Act of Treasonglue2Încă nu există evaluări
- Acta de Nacimiento TraduccionDocument1 paginăActa de Nacimiento TraduccionGuadalupeÎncă nu există evaluări
- Edward SnowdenDocument2 paginiEdward SnowdenBanPengTanÎncă nu există evaluări
- Jon Rappoport On Disclosure Jan 2018Document4 paginiJon Rappoport On Disclosure Jan 2018Beyond Being Human100% (1)
- Advanced Certificate in Crowd Management & Riot Control For Security ProfessionalsDocument3 paginiAdvanced Certificate in Crowd Management & Riot Control For Security Professionals360 BSIÎncă nu există evaluări
- Contents Black 53Document18 paginiContents Black 53EyemanProphetÎncă nu există evaluări
- EC-Council CEH v10 Complete Training Guide With Practice Labs Exam 312Document701 paginiEC-Council CEH v10 Complete Training Guide With Practice Labs Exam 312Nitish KumarÎncă nu există evaluări
- Summary and Analysis of No Place to Hide: Edward Snowden, the NSA, and the U.S. Surveillance State: Based on the Book by Glenn GreenwaldDe la EverandSummary and Analysis of No Place to Hide: Edward Snowden, the NSA, and the U.S. Surveillance State: Based on the Book by Glenn GreenwaldÎncă nu există evaluări
- Trevor Loudon AssangeDocument36 paginiTrevor Loudon AssangeAlena KlÎncă nu există evaluări
- 12-04-13 Wikileaks Releases Kissinger Cables and Two Decisions in Manning TrialDocument12 pagini12-04-13 Wikileaks Releases Kissinger Cables and Two Decisions in Manning TrialWilliam J GreenbergÎncă nu există evaluări
- No Place to Hide: Edward Snowden, the NSA, and the U.S. Surveillance State by Glenn Greenwald.... SummarizedDe la EverandNo Place to Hide: Edward Snowden, the NSA, and the U.S. Surveillance State by Glenn Greenwald.... SummarizedEvaluare: 4 din 5 stele4/5 (1)
- Russian Spy Ring Obama-Hillary-Bill or How Putin Rules USA.M.KryzhanovskyDocument160 paginiRussian Spy Ring Obama-Hillary-Bill or How Putin Rules USA.M.KryzhanovskyMikhail KryzhanovskyÎncă nu există evaluări
- Round TableDocument25 paginiRound TableLiz Matarong BayanoÎncă nu există evaluări
- Queen's SquareDocument45 paginiQueen's SquareGarifuna NationÎncă nu există evaluări
- Harnessing IoT Global DevelopmentDocument61 paginiHarnessing IoT Global Developmentcjwang50% (2)
- Summary of No Place to Hide: by Glenn Greenwald | Includes AnalysisDe la EverandSummary of No Place to Hide: by Glenn Greenwald | Includes AnalysisÎncă nu există evaluări
- PRISM Exposed - US SPYING Through Worldwide Data SurveillanceDocument5 paginiPRISM Exposed - US SPYING Through Worldwide Data SurveillanceFlorence TanÎncă nu există evaluări
- Final Research PaperDocument12 paginiFinal Research Paperapi-302274400Încă nu există evaluări
- Breaking News: The Remaking of Journalism and Why It Matters NowDe la EverandBreaking News: The Remaking of Journalism and Why It Matters NowEvaluare: 4.5 din 5 stele4.5/5 (17)
- Greenwald - US, British Media Are Servants of Security Apparatus - RT NewsDocument25 paginiGreenwald - US, British Media Are Servants of Security Apparatus - RT NewsGordon LoganÎncă nu există evaluări
- Nsa Leaked Why WhatDocument2 paginiNsa Leaked Why Whatapi-324745122Încă nu există evaluări
- Mail On Sunday June 1, 2003Document4 paginiMail On Sunday June 1, 2003Bren-RÎncă nu există evaluări
- Cab 1 0150to0153Document4 paginiCab 1 0150to0153Bren-RÎncă nu există evaluări
- Merkel Compared NSA To Stasi in Heated Encounter With Obama - World News - The GuardianDocument4 paginiMerkel Compared NSA To Stasi in Heated Encounter With Obama - World News - The GuardianGordon LoganÎncă nu există evaluări
- BBC 5 0042to0055Document14 paginiBBC 5 0042to0055Bren-RÎncă nu există evaluări
- Edward Snowden Is Completely WrongDocument5 paginiEdward Snowden Is Completely WrongLong JunÎncă nu există evaluări
- BBC Radio 4 Today Programme 315' MAY 2003 Andrew Giligan EssayDocument2 paginiBBC Radio 4 Today Programme 315' MAY 2003 Andrew Giligan EssayBren-RÎncă nu există evaluări
- Edward Snowden - Whistleblower or TraitorDocument3 paginiEdward Snowden - Whistleblower or TraitorluithehardcarryÎncă nu există evaluări
- Edward Snowden Spy Leaks - Liam Fox in Push For Guardian Newspaper To Be ProsecutedDocument6 paginiEdward Snowden Spy Leaks - Liam Fox in Push For Guardian Newspaper To Be ProsecutedDemonIgÎncă nu există evaluări
- A Demand For Russian Hacking ProofDocument7 paginiA Demand For Russian Hacking ProofbenkokoscribedÎncă nu există evaluări
- BBC 1 0025to0026Document2 paginiBBC 1 0025to0026Bren-RÎncă nu există evaluări
- US ScrutinizesLeaks 100728Document3 paginiUS ScrutinizesLeaks 100728steveÎncă nu există evaluări
- Read An Excerpt From "The Snowden Files" by Luke HardingDocument6 paginiRead An Excerpt From "The Snowden Files" by Luke HardingOnPointRadioÎncă nu există evaluări
- International Diplomacy and WIKILEAKSA: Before and An After?Document3 paginiInternational Diplomacy and WIKILEAKSA: Before and An After?MELISSA DAVILA CHAVEZÎncă nu există evaluări
- The Death of Truth: This Interview Is A Joint Project of Truthdig and MagazineDocument12 paginiThe Death of Truth: This Interview Is A Joint Project of Truthdig and MagazineWilliam J GreenbergÎncă nu există evaluări
- Why Obama Should Pardon Snowden - LAtimesDocument2 paginiWhy Obama Should Pardon Snowden - LAtimesAnsh JhatakiaÎncă nu există evaluări
- 02-04-08 HP-Sibel Edmonds Must Be Heard Philip GiraldiDocument2 pagini02-04-08 HP-Sibel Edmonds Must Be Heard Philip GiraldiMark WelkieÎncă nu există evaluări
- Havasi Gabriella - RP1Document3 paginiHavasi Gabriella - RP1Máté Gergely BaloghÎncă nu există evaluări
- Flight Path: The Fifth Plane and the Threat to Air Force OneDe la EverandFlight Path: The Fifth Plane and the Threat to Air Force OneÎncă nu există evaluări
- #ManhuntDocument4 pagini#Manhuntpimiento24Încă nu există evaluări
- Orwellian Misdemeanours PDFDocument9 paginiOrwellian Misdemeanours PDFjeroe12Încă nu există evaluări
- 03-22-08 Der Spiegel-German Intelligence Was Dishonest, UnpDocument3 pagini03-22-08 Der Spiegel-German Intelligence Was Dishonest, UnpMark WelkieÎncă nu există evaluări
- Insights from Declassified NSA Article on Soviet ShootdownsDocument32 paginiInsights from Declassified NSA Article on Soviet Shootdownsnewton198Încă nu există evaluări
- Julian Assange, The Man Behind WikileaksDocument9 paginiJulian Assange, The Man Behind WikileaksMaito UslenghiÎncă nu există evaluări
- BBC 13 0040to0041Document2 paginiBBC 13 0040to0041Bren-RÎncă nu există evaluări
- Poole-Snowden 042814-FinalDocument13 paginiPoole-Snowden 042814-Finalapi-247281933Încă nu există evaluări
- Stephen Fry Attacks 'Squalid' Coalition For Inaction On Snowden Revelations - World News - The ObserverDocument4 paginiStephen Fry Attacks 'Squalid' Coalition For Inaction On Snowden Revelations - World News - The ObserverfiliplatinovicÎncă nu există evaluări
- Dreamworks, Guardian, and Channel4 WikiLeaks ProfiteersDocument15 paginiDreamworks, Guardian, and Channel4 WikiLeaks Profiteersmary engÎncă nu există evaluări
- Topic Outline of Edward Snowden de MesaDocument5 paginiTopic Outline of Edward Snowden de MesaGelyn Malabanan De MesaÎncă nu există evaluări
- BBC 7 0076to0078Document3 paginiBBC 7 0076to0078Bren-RÎncă nu există evaluări
- Top Secret America - A Washington Post Investigation - A Hidden World, Growing Beyond ControlDocument51 paginiTop Secret America - A Washington Post Investigation - A Hidden World, Growing Beyond ControlMark CottellÎncă nu există evaluări
- Wikileaks Defies The "War On Hi-Tech Terror": John PilgerDocument7 paginiWikileaks Defies The "War On Hi-Tech Terror": John PilgerSwanson TudorÎncă nu există evaluări
- Wikileaks: Good or Bad?: The IssueDocument6 paginiWikileaks: Good or Bad?: The IssueIshan PadgotraÎncă nu există evaluări
- BBC 12 0024to0025Document2 paginiBBC 12 0024to0025Bren-RÎncă nu există evaluări
- Edward Snowden USDocument5 paginiEdward Snowden USAnonymous GKPCQIcmXSÎncă nu există evaluări
- Authorization LetterDocument1 paginăAuthorization Letterwael radiÎncă nu există evaluări
- ARREST OF TOP WANTED PERSONS IN CAGAYANDocument13 paginiARREST OF TOP WANTED PERSONS IN CAGAYANVince Prince100% (1)
- CSE IndexDocument13 paginiCSE IndexVenkatesh ThirugnanasambandamÎncă nu există evaluări
- BASIC CONTRACT ADMINISTRATION TEXTDocument445 paginiBASIC CONTRACT ADMINISTRATION TEXTitaleÎncă nu există evaluări
- Chapter 33 UpdateDocument5 paginiChapter 33 UpdateArs TechnicaÎncă nu există evaluări
- AFF Islamophobia GDIDocument336 paginiAFF Islamophobia GDILincoln TeamÎncă nu există evaluări
- Fidler CV August 2021Document9 paginiFidler CV August 2021Gabe KaminskyÎncă nu există evaluări
- GTC Company Profile 2.2Document6 paginiGTC Company Profile 2.2Muhammad RamadhanÎncă nu există evaluări
- Entrepreneurial Resources 2016Document134 paginiEntrepreneurial Resources 2016Nacho Alonso LÎncă nu există evaluări
- Why You Should Use Alertpay!: 10 Great Reasons To Use Our Up-And-Coming Payment SolutionDocument7 paginiWhy You Should Use Alertpay!: 10 Great Reasons To Use Our Up-And-Coming Payment SolutionLazar SimićÎncă nu există evaluări
- Certificate As GraduateDocument22 paginiCertificate As GraduateLovely CamposanoÎncă nu există evaluări
- Objective 14: Compare Various Security MechanismsDocument16 paginiObjective 14: Compare Various Security MechanismsTyrick MinottÎncă nu există evaluări
- Defending Digital Globalization - Foreign AffairsDocument10 paginiDefending Digital Globalization - Foreign AffairsveroÎncă nu există evaluări
- Exam Candidate Guide Continuous TestingDocument22 paginiExam Candidate Guide Continuous TestingPawanKumar100% (1)
- QweqwezxzxcDocument109 paginiQweqwezxzxcMarvin SinuesÎncă nu există evaluări
- Boost Your ASIS Certification ScoreDocument12 paginiBoost Your ASIS Certification ScoreN Chandra SekharÎncă nu există evaluări
- Ametek Surface Vision Metals Brochure v5 12142018Document8 paginiAmetek Surface Vision Metals Brochure v5 12142018VladimirAgeevÎncă nu există evaluări
- Finals Gen ElectiveDocument16 paginiFinals Gen ElectiveGaydee MaduroÎncă nu există evaluări
- DJI Remote Identification Whitepaper 3-22-17Document10 paginiDJI Remote Identification Whitepaper 3-22-17Александр ШинÎncă nu există evaluări
- Conveyor Group: JAPAN 2020Document24 paginiConveyor Group: JAPAN 2020Asm Saiduzzaman SayeedÎncă nu există evaluări
- PA-GAN: A Patch-Attention Based Aggregation Network For Face Recognition in SurveillanceDocument10 paginiPA-GAN: A Patch-Attention Based Aggregation Network For Face Recognition in SurveillanceGOURISREE MÎncă nu există evaluări
- Top Links July 2018Document79 paginiTop Links July 2018Andrew Richard ThompsonÎncă nu există evaluări
- StrongWatch FOTM PPT 07082013Document14 paginiStrongWatch FOTM PPT 07082013CheckLBPD.orgÎncă nu există evaluări