Documente Academic
Documente Profesional
Documente Cultură
1.1 Scaling Networks With NAT and PAT 1.1.1 Private Addressing
Încărcat de
elvanthurs0 evaluări0% au considerat acest document util (0 voturi)
27 vizualizări8 paginiNAT and PAT allow private IP addresses to access the public Internet by translating internal private addresses to external public addresses. Static NAT maps a single private address to a public address in a one-to-one fashion, while dynamic NAT maps private addresses to public addresses from a pool. PAT maps multiple private addresses to a single public address by using unique source port numbers. Verifying NAT and PAT configurations involves checking translation tables and using debug commands to ensure translations are occurring properly.
Descriere originală:
f
Titlu original
ku
Drepturi de autor
© © All Rights Reserved
Formate disponibile
DOC, PDF, TXT sau citiți online pe Scribd
Partajați acest document
Partajați sau inserați document
Vi se pare util acest document?
Este necorespunzător acest conținut?
Raportați acest documentNAT and PAT allow private IP addresses to access the public Internet by translating internal private addresses to external public addresses. Static NAT maps a single private address to a public address in a one-to-one fashion, while dynamic NAT maps private addresses to public addresses from a pool. PAT maps multiple private addresses to a single public address by using unique source port numbers. Verifying NAT and PAT configurations involves checking translation tables and using debug commands to ensure translations are occurring properly.
Drepturi de autor:
© All Rights Reserved
Formate disponibile
Descărcați ca DOC, PDF, TXT sau citiți online pe Scribd
0 evaluări0% au considerat acest document util (0 voturi)
27 vizualizări8 pagini1.1 Scaling Networks With NAT and PAT 1.1.1 Private Addressing
Încărcat de
elvanthursNAT and PAT allow private IP addresses to access the public Internet by translating internal private addresses to external public addresses. Static NAT maps a single private address to a public address in a one-to-one fashion, while dynamic NAT maps private addresses to public addresses from a pool. PAT maps multiple private addresses to a single public address by using unique source port numbers. Verifying NAT and PAT configurations involves checking translation tables and using debug commands to ensure translations are occurring properly.
Drepturi de autor:
© All Rights Reserved
Formate disponibile
Descărcați ca DOC, PDF, TXT sau citiți online pe Scribd
Sunteți pe pagina 1din 8
1.
1 Scaling Networks with NAT and PAT
1.1.1 Private addressing
RFC 1918 sets aside three blocks of private IP addresses. They are one Class A address, 1 Class !
addresses, and "# Class C addresses. These addresses are for private, internal net$ork %se only.
Packets containin& these addresses are not ro%ted over the Internet.
P%blic Internet addresses '%st be re&istered by a co'pany $ith an Internet a%thority, for e(a'ple,
ARI) or RIP*. These p%blic Internet addresses can also be leased fro' an I+P. Private IP addresses
are reserved and can be %sed by anyone. That 'eans t$o net$orks, or t$o 'illion net$orks, can each
%se the sa'e private address. A ro%ter sho%ld never ro%te RFC 1918 addresses, beca%se I+Ps typically
confi&%re the border ro%ters to prevent privately addressed traffic fro' bein& for$arded.
)AT provides &reat benefits to individ%al co'panies and the Internet. !efore )AT, a host $ith a
private address co%ld not access the Internet. ,sin& )AT, individ%al co'panies can address so'e or
all of their hosts $ith private addresses and %se )AT to provide access the Internet.
1.1.2 Introducing NAT and PAT
)AT is desi&ned to conserve IP addresses and enable net$orks to %se private IP addresses on internal
net$orks. These private, internal addresses are translated to ro%table, p%blic addresses. This is
acco'plished by inter-net$ork devices r%nnin& speciali.ed )AT soft$are and can increase net$ork
privacy by hidin& internal IP addresses.
A )AT enabled device typically operates at the border of a st%b net$ork. A st%b net$ork is a net$ork
that has a sin&le connection to its nei&hbor net$ork. /hen a host inside the st%b net$ork $ants to
trans'it to a host on the o%tside, it for$ards the packet to the border &ate$ay ro%ter. The border
&ate$ay ro%ter perfor's the )AT process, translatin& the internal private address of a host to a p%blic,
e(ternal ro%table address. In )AT ter'inolo&y, the internal net$ork is the set of net$orks that are
s%b0ect to translation. The e(ternal net$ork refers to all other addresses.
Cisco defines the follo$in& )AT ter's1
Inside local address 2 The IP address assi&ned to a host on the inside net$ork. The address is
%s%ally not an IP address assi&ned by the )et$ork Infor'ation Center 3)IC4 or service provider.
This address is likely to be an RFC 1918 private address.
Inside &lobal address 2 A le&iti'ate IP address assi&ned by the )IC or service provider that
represents one or 'ore inside local IP addresses to the o%tside $orld.
5%tside local address 2 The IP address of an o%tside host as it is kno$n to the hosts on the inside
net$ork.
5%tside &lobal address 2 The IP address assi&ned to a host on the o%tside net$ork. The o$ner of
the host assi&ns this address.
1.1.3 Major NAT and PAT features
)AT translations can be %sed for a variety of p%rposes and can be either dyna'ically or statically
assi&ned. +tatic )AT is desi&ned to allo$ one-to-one 'appin& of local and &lobal addresses. This is
partic%larly %sef%l for hosts $hich '%st have a consistent address that is accessible fro' the Internet.
+%ch hosts 'ay be enterprise servers or net$orkin& devices.
6yna'ic )AT is desi&ned to 'ap a private IP address to a p%blic address. Any IP address fro' a pool
of p%blic IP addresses is assi&ned to a net$ork host. 5verloadin&, or Port Address Translation 3PAT4,
'aps '%ltiple private IP addresses to a sin&le p%blic IP address. 7%ltiple addresses can be 'apped to
a sin&le address beca%se each private address is tracked by a port n%'ber.
PAT %ses %ni8%e so%rce port n%'bers on the inside &lobal IP address to distin&%ish bet$een
translations. The port n%'ber is encoded in 1 bits. The total n%'ber of internal addresses that can be
translated to one e(ternal address co%ld theoretically be as hi&h as #,#9 per IP address. Realistically,
the n%'ber of ports that can be assi&ned a sin&le IP address is aro%nd :;;;. PAT $ill atte'pt to
preserve the ori&inal so%rce port. If this so%rce port is already %sed, PAT $ill assi&n the first available
port n%'ber startin& fro' the be&innin& of the appropriate port &ro%p ;-#11, #1"-1;"9, or 1;":-
##9#. /hen there are no 'ore ports available and there is 'ore than one e(ternal IP address
confi&%red, PAT 'oves to the ne(t IP address to try to allocate the ori&inal so%rce port a&ain. This
process contin%es %ntil it r%ns o%t of available ports and e(ternal IP addresses.
)AT offers the follo$in& benefits1
*li'inates reassi&nin& each host a ne$ IP address $hen chan&in& to a ne$ I+P. )AT eli'inates
the need to readdress all hosts that re8%ire e(ternal access, savin& ti'e and 'oney.
Conserves addresses thro%&h application port-level '%ltiple(in&. /ith PAT, internal hosts can
share a sin&le p%blic IP address for all e(ternal co''%nications. In this type of confi&%ration, very
fe$ e(ternal addresses are re8%ired to s%pport 'any internal hosts, thereby conservin& IP
addresses.
Protects net$ork sec%rity. !eca%se private net$orks do not advertise their addresses or internal
topolo&y, they re'ain reasonably sec%re $hen %sed in con0%nction $ith )AT to &ain controlled
e(ternal access.
1.1. !onfiguring NAT and PAT
+tatic Translation
To confi&%re static inside so%rce address translation, perfor' the tasks in Fi&%res and .
Fi&%re sho$s the %se of static )AT translation. The ro%ter $ill translate packets fro' host 1;.1.1." to
a so%rce address of 19".18.1.".
6yna'ic Translation
To confi&%re dyna'ic inside so%rce address translation, perfor' the tasks in Fi&%re .
The access list '%st per'it only those addresses that are to be translated. Re'e'ber that there is an
i'plicit <deny all= at the end of each access list. An access list that is too per'issive can lead to
%npredictable res%lts. Cisco advises a&ainst confi&%rin& access lists referenced by )AT co''ands
$ith the per'it any co''and. ,sin& per'it any can res%lt in )AT cons%'in& too 'any ro%ter
reso%rces, $hich can ca%se net$ork proble's.
Fi&%re translates all so%rce addresses passin& access list 1, $hich have so%rce address fro'
1;.1.;.;>":, to an address fro' the pool na'ed nat-pool1. The pool contains addresses fro'
1?9.9.8.8;>": to 1?9.9.8.9#>":.
)ote1 )AT $ill not translate the host 1;.1.1.", as it is not per'itted for translation by the access list.
5verloadin&
5verloadin& is confi&%red in t$o $ays dependin& on ho$ p%blic IP addresses have been allocated. An
I+P can allocate a net$ork only one p%blic IP address, and this is typically assi&ned to the o%tside
interface $hich connects to the I+P. Fi&%re sho$s ho$ to confi&%re overloadin& in this sit%ation.
Another $ay of confi&%rin& overload is if the I+P has &iven one or 'ore p%blic IP addresses for %se as
a )AT pool. This pool can be overloaded as sho$n in the confi&%ration in Fi&%re .
Fi&%re sho$s an e(a'ple confi&%ration of PAT.
1.1." #erif$ing PAT configuration
5nce )AT is confi&%red, %se the clear and sho$ co''ands to verify that it is operatin& as e(pected.
!y defa%lt, dyna'ic address translations $ill ti'e o%t fro' the )AT translation table after a period of
non-%se. /hen port translation is not confi&%red, translation entries ti'e o%t after ": ho%rs, %nless
reconfi&%red $ith the ip nat translation co''and. Clear the entries before the ti'eo%t by %sin& one of
the co''ands in Fi&%re .
Translation infor'ation 'ay be displayed by perfor'in& one of the tasks in *@*C 'ode.
Alternatively, %se the sho$ r%n co''and and look for )AT, access list, interface, or pool co''ands
$ith the re8%ired val%es.
1.1.% Trou&leshooting NAT and PAT configuration
/hen IP connectivity proble's in a )AT environ'ent e(ist, it is often diffic%lt to deter'ine the ca%se
of the proble'. 7any ti'es )AT is 'istakenly bla'ed, $hen in reality there is an %nderlyin&
proble'.
/hen tryin& to deter'ine the ca%se of an IP connectivity proble', it helps to r%le o%t )AT. ,se the
follo$in& steps to deter'ine $hether )AT is operatin& as e(pected1
1. !ased on the confi&%ration, clearly define $hat )AT is s%pposed to achieve.
". Aerify that correct translations e(ist in the translation table.
9. Aerify the translation is occ%rrin& by %sin& sho$ and deb%& co''ands.
:. Revie$ in detail $hat is happenin& to the packet and verify that ro%ters have the correct
ro%tin& infor'ation to 'ove the packet alon&.
,se the deb%& ip nat co''and to verify the operation of the )AT feat%re by displayin& infor'ation
abo%t every packet that is translated by the ro%ter. The deb%& ip nat detailed co''and &enerates a
description of each packet considered for translation. This co''and also o%tp%ts infor'ation abo%t
certain errors or e(ception conditions, s%ch as the fail%re to allocate a &lobal address.
Fi&%re sho$s a sa'ple deb%& ip nat o%tp%t. In this e(a'ple, the first t$o lines of the deb%&&in&
o%tp%t sho$ that a 6o'ain )a'e +yste' 36)+4 re8%est and reply $ere prod%ced. The re'ainin&
lines sho$ the deb%&&in& o%tp%t of a Telnet connection fro' a host on the inside of the net$ork to a
host on the o%tside of the net$ork.
6ecode the deb%& o%tp%t by %sin& the follo$in& key points1
The asterisk ne(t to )AT indicates that the translation is occ%rrin& in the fast-s$itched path. The
first packet in a conversation $ill al$ays &o thro%&h the slo$ path, $hich 'eans this first packet
is process-s$itched. The re'ainin& packets $ill &o thro%&h the fast-s$itched path if a cache entry
e(ists.
s B a.b.c.d is the so%rce address.
+o%rce address a.b.c.d is translated to $.(.y...
d B e.f.&.h is the destination address.
The val%e in brackets is the IP identification n%'ber. This infor'ation 'ay be %sef%l for
deb%&&in&. This is %sef%l, for e(a'ple, beca%se it enables correlation $ith other packet traces
fro' protocol analy.ers.
1.1.' Issues with NAT
)AT has several advanta&es, incl%din&1
)AT conserves the le&ally re&istered addressin& sche'e by allo$in& the privati.ation of intranets.
Increases the fle(ibility of connections to the p%blic net$ork. 7%ltiple pools, back%p pools, and
load balancin& pools can be i'ple'ented to ass%re reliable p%blic net$ork connections.
Consistency of the internal net$ork addressin& sche'e. 5n a net$ork $itho%t private IP addresses
and )AT, chan&in& p%blic IP addresses re8%ires the ren%'berin& of all hosts on the e(istin&
net$ork. The costs of ren%'berin& hosts can be si&nificant. )AT allo$s the e(istin& sche'e to
re'ain $hile s%pportin& a ne$ p%blic addressin& sche'e.
)AT is not $itho%t dra$backs. *nablin& address translation $ill ca%se a loss of f%nctionality,
partic%larly $ith any protocol or application that involves sendin& IP address infor'ation inside the IP
payload. This re8%ires additional s%pport by the )AT device.
)AT increases delay. +$itchin& path delays are introd%ced beca%se of the translation of each IP
address $ithin the packet headers.
Perfor'ance 'ay be a consideration beca%se )AT is c%rrently acco'plished by %sin& process
s$itchin&. The CP, '%st look at every packet to decide $hether it has to translate it. The CP, '%st
alter the IP header, and possibly alter the TCP header.
5ne si&nificant disadvanta&e $hen i'ple'entin& and %sin& )AT is the loss of end-to-end IP
traceability. It beco'es '%ch 'ore diffic%lt to trace packets that %nder&o n%'ero%s packet address
chan&es over '%ltiple )AT hops. Cackers $ho $ant to deter'ine the so%rce of a packet $ill find it
diffic%lt to trace or obtain the ori&inal so%rce or destination address.
)AT also forces so'e applications that %se IP addressin& to stop f%nctionin& beca%se it hides end-to-
end IP addresses. Applications that %se physical addresses instead of a 8%alified do'ain na'e $ill not
reach destinations that are translated across the )AT ro%ter. +o'eti'es, this proble' can be avoided
by i'ple'entin& static )AT 'appin&s.
Cisco I5+ )AT s%pports the follo$in& traffic types1
IC7P
File Transfer Protocol 3FTP4, incl%din& P5RT and PA+A co''ands
)et!I5+ over TCP>IP, data&ra', na'e, and session services
Real)et$orksD RealA%dio
/hite PinesD C,+ee7e
@in& Technolo&iesD +trea'/orks
6)+ EAE and EPTRE 8%eries
C.9"9>7icrosoft )et7eetin&, I5+ versions 1".;314>1".;314T and later
A65netDs A65Five, I5+ versions 11.93:411.93:4T and later
A@tre'eDs /eb Theater, I5+ versions 11.93:411.93:4T and later
IP 7%lticast, I5+ version 1".;314T $ith so%rce address translation only
Cisco I5+ )AT does not s%pport the follo$in& traffic types1
Ro%tin& table %pdates
6)+ .one transfers
!55TP
talk and ntalk protocols
+i'ple )et$ork 7ana&e'ent Protocol 3+)7P4
1.2 ()!P
1.2.1 Introducing ()!P
6yna'ic Cost Confi&%ration Protocol 36CCP4 $orks in a client>server 'ode. 6CCP enables 6CCP
clients on an IP net$ork to obtain their confi&%rations fro' a 6CCP server. Fess $ork is involved in
'ana&in& an IP net$ork $hen 6CCP is %sed. The 'ost si&nificant confi&%ration option the client
receives fro' the server is its IP address. The 6CCP protocol is described in RFC "191.
A 6CCP client is incl%ded in 'ost 'odern operatin& syste's incl%din& the vario%s /indo$s
operatin& syste's, )ovell )et$are, +%n +olaris, Fin%(, and 7AC 5+. The client re8%ests addressin&
val%es fro' the net$ork 6CCP server. This server 'ana&es the allocation of the IP addresses and
$ill ans$er confi&%ration re8%ests fro' clients. The 6CCP server can ans$er re8%ests for 'any
s%bnets. 6CCP is not intended for confi&%rin& ro%ters, s$itches, and servers. These type of hosts all
need to have static IP addresses.
6CCP $orks by providin& a process for a server to allocate IP infor'ation to clients. Clients lease the
infor'ation fro' the server for an ad'inistratively defined period. /hen the lease e(pires the client
'%st ask for another address, altho%&h the client is typically reassi&ned the sa'e address.
Ad'inistrators typically prefer a net$ork server to offer 6CCP services beca%se these sol%tions are
scalable and relatively easy to 'ana&e. Cisco ro%ters can %se a Cisco I5+ feat%re set, *asy IP, to offer
an optional, f%ll-feat%red 6CCP server. *asy IP leases confi&%rations for ": ho%rs by defa%lt. This is
%sef%l in s'all offices and ho'e offices $here the ho'e %ser can take advanta&e of 6CCP and )AT
$itho%t havin& an )T or ,)I@ server.
Ad'inistrators set %p 6CCP servers to assi&n addresses fro' predefined pools. 6CCP servers can
also offer other infor'ation, s%ch as 6)+ server addresses, /I)+ server addresses, and do'ain
na'es. 7ost 6CCP servers also allo$ the ad'inistrator to define specifically $hat client 7AC
addresses can be serviced and a%to'atically assi&n the' the sa'e IP address each ti'e.
6CCP %ses ,6P as its transport protocol. The client sends 'essa&es to the server on port ?. The
server sends 'essa&es to the client on port 8.
1.2.2 *++TP and ()!P differences
The Internet co''%nity first developed the !55TP protocol to enable confi&%ration of diskless
$orkstations. !55TP $as ori&inally defined in RFC 9#1 in 198#. As the predecessor of 6CCP,
!55TP shares so'e operational characteristics. !oth protocols are client>server based and %se ,6P
ports ? and 8. Those ports are still kno$n as !55TP ports.
The fo%r basic IP para'eters1
IP address
Gate$ay address
+%bnet 'ask
6)+ server address
!55TP does not dyna'ically allocate IP addresses to a host. /hen a client re8%ests an IP address, the
!55TP server searches a predefined table for an entry that 'atches the 7AC address for the client. If
an entry e(ists, then the correspondin& IP address for that entry is ret%rned to the client. This 'eans
that the bindin& bet$een the 7AC address and the IP address '%st have already been confi&%red in
the !55TP server.
There are t$o pri'ary differences bet$een 6CCP and !55TP1
6CCP defines 'echanis's thro%&h $hich clients can be assi&ned an IP address for a finite lease
period. This lease period allo$s for reassi&n'ent of the IP address to another client later, or for
the client to &et another assi&n'ent, if the client 'oves to another s%bnet. Clients 'ay also rene$
leases and keep the sa'e IP address.
6CCP provides the 'echanis' for a client to &ather other IP confi&%ration para'eters, s%ch as
/I)+ and do'ain na'e.
1.2.3 Major ()!P features
There are three 'echanis's %sed to assi&n an IP address to the client1
A%to'atic allocation 2 6CCP assi&ns a per'anent IP address to a client.
7an%al allocation 2 The IP address for the client is assi&ned by the ad'inistrator. 6CCP conveys
the address to the client.
6yna'ic allocation 2 6CCP assi&ns, or leases, an IP address to the client for a li'ited period of
ti'e.
The foc%s of this section is the dyna'ic allocation 'echanis'. +o'e of the confi&%ration para'eters
available are listed in I*TF RFC 1#991
+%bnet 'ask
Ro%ter
6o'ain )a'e
6o'ain )a'e +erver3s4
/I)+ +erver3s4
The 6CCP server creates pools of IP addresses and associated para'eters. Pools are dedicated to an
individ%al lo&ical IP s%bnet. This allo$s '%ltiple 6CCP servers to respond and IP clients to be
'obile. If '%ltiple servers respond, a client can choose only one of the offers.
1.2. ()!P o,eration
The 6CCP client confi&%ration process %ses the follo$in& steps1
1. A client '%st have 6CCP confi&%red $hen startin& the net$ork 'e'bership process. The
client sends a re8%est to a server re8%estin& an IP confi&%ration. +o'eti'es the client 'ay s%&&est
the IP address it $ants, s%ch as $hen re8%estin& an e(tension to a 6CCP lease. The client locates
a 6CCP server by sendin& a broadcast called a 6CCP6I+C5A*R.
". /hen the server receives the broadcast, it deter'ines $hether it can service the re8%est fro'
its o$n database. If it cannot, the server 'ay for$ard the re8%est on to another 6CCP server. If it
can, the 6CCP server offers the client IP confi&%ration infor'ation in the for' of a %nicast
6CCP5FF*R. The 6CCP5FF*R is a proposed confi&%ration that 'ay incl%de IP address, 6)+
server address, and lease ti'e.
9. If the client finds the offer a&reeable, it $ill send another broadcast, a 6CCPR*H,*+T,
specifically re8%estin& those partic%lar IP para'eters. /hy does the client broadcast the re8%est
instead of %nicastin& it to the serverI A broadcast is %sed beca%se the first 'essa&e, the
6CCP6I+C5A*R, 'ay have reached 'ore than one 6CCP server. If 'ore than one server
'akes an offer, the broadcasted 6CCPR*H,*+T allo$s the other servers to kno$ $hich offer
$as accepted. The offer accepted is %s%ally the first offer received.
:. The server that receives the 6CCPR*H,*+T 'akes the confi&%ration official by sendin& a
%nicast ackno$led&'ent, the 6CCPACJ. It is possible, b%t hi&hly %nlikely, that the server $ill
not send the 6CCPACJ. This 'ay happen beca%se the server 'ay have leased that infor'ation to
another client in the interi'. Receipt of the 6CCPACJ 'essa&e enables the client to be&in %sin&
the assi&ned address i''ediately.
#. If the client detects that the address is already in %se on the local se&'ent it $ill send a
6CCP6*CFI)* 'essa&e and the process starts a&ain. If the client received a 6CCP)ACJ fro'
the server after sendin& the 6CCPR*H,*+T, then it $ill restart the process a&ain.
If the client no lon&er needs the IP address, the client sends a 6CCPR*F*A+* 'essa&e to the server.
6ependin& on an or&ani.ationDs policies, it 'ay be possible for an end %ser or an ad'inistrator to
statically assi&n a host an IP address that belon&s in the 6CCP servers address pool. K%st in case, the
Cisco I5+ 6CCP server al$ays checks to 'ake s%re that an address is not in %se before the server
offers it to a client. The server $ill iss%e an IC7P echo re8%est, or $ill pin&, to a pool address before
sendin& the 6CCP5FF*R to a client. Altho%&h confi&%rable, the defa%lt n%'ber of pin&s %sed to
check for a potential IP address conflict is t$o.
1.2." !onfiguring ()!P
Fike )AT, a 6CCP server re8%ires that the ad'inistrator define a pool of addresses. The ip dhcp pool
co''and defines $hich addresses $ill be assi&ned to hosts.
The first co''and, ip dhcp pool, creates a pool $ith the specified na'e and p%ts the ro%ter in a
speciali.ed 6CCP confi&%ration 'ode. In this 'ode, %se the net$ork state'ent to define the ran&e of
addresses to be leased. If specific addresses on the net$ork are to be e(cl%ded, ret%rn to &lobal
confi&%ration 'ode.
The ip dhcp e(cl%ded-address co''and confi&%res the ro%ter to e(cl%de an individ%al address or
ran&e of addresses $hen assi&nin& addresses to clients. The ip dhcp e(cl%ded-address co''and 'ay
be %sed to reserve addresses that are statically assi&ned to key hosts, for instance, the interface address
on the ro%ter.
Typically, a 6CCP server $ill be confi&%red to assi&n '%ch 'ore than an IP address. 5ther IP
confi&%ration val%es s%ch as the defa%lt &ate$ay can be set fro' the 6CCP confi&%ration 'ode. ,sin&
the defa%lt-ro%ter co''and sets the defa%lt &ate$ay. The address of the 6)+ server, dns-server, and
/I)+ server, netbios-na'e-server, can also be confi&%red here. The I5+ 6CCP server can confi&%re
clients $ith virt%ally any TCP>IP infor'ation.
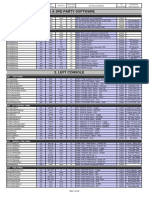
A list of the key I5+ 6CCP server co''ands entered in the 6CCP pool confi&%ration 'ode are
sho$n in Fi&%re .
The 6CCP service is enabled by defa%lt on versions of Cisco I5+ that s%pport it. To disable the
service, %se the no service dhcp co''and. ,se the service dhcp &lobal confi&%ration co''and to re-
enable the 6CCP server process.
1.2.% #erif$ing ()!P o,eration
To verify the operation of 6CCP, the co''and sho$ ip dhcp bindin& can be %sed. This displays a list
of all bindin&s created by the 6CCP service.
To verify that 'essa&es are bein& received or sent by the ro%ter, %se the co''and sho$ ip dhcp server
statistics. This $ill display co%nt infor'ation re&ardin& the n%'ber of 6CCP 'essa&es that have been
sent and received.
1.2.' Trou&leshooting ()!P
To tro%bleshoot the operation of the 6CCP server, the co''and deb%& ip dhcp server events can be
%sed. This co''and $ill sho$ that the server periodically checks to see if any leases have e(pired.
Also, it can be seen $hen addresses are ret%rned and $hen they are allocated.
1.2.- ()!P rela$
6CCP clients %se IP broadcasts to find the 6CCP server on the se&'ent. /hat happens $hen the
server and the client are not on the sa'e se&'ent and are separated by a ro%terI Ro%ters do not
for$ard these broadcasts.
6CCP is not the only critical service that %ses broadcasts. Cisco ro%ters and other devices 'ay %se
broadcasts to locate TFTP servers. +o'e clients 'ay need to broadcast to locate a TACAC+ server. A
TACAC+ server is a sec%rity server. Typically, in a co'ple( hierarchical net$ork, clients reside on
the sa'e s%bnet as key servers. +%ch re'ote clients $ill broadcast to locate these servers. Co$ever,
ro%ters, by defa%lt, $ill not for$ard client broadcasts beyond their s%bnet.
!eca%se so'e clients are %seless $itho%t services s%ch as 6CCP, one of t$o choices '%st be
i'ple'ented. The ad'inistrator $ill need to place servers on all s%bnets or %se the Cisco I5+ helper
address feat%re. R%nnin& services s%ch as 6CCP or 6)+ on several co'p%ters creates overhead and
ad'inistrative diffic%lties 'akin& the first option inefficient. /hen possible, ad'inistrators sho%ld %se
the ip helper-address co''and to relay broadcast re8%ests for these key ,6P services.
!y %sin& the helper address feat%re, a ro%ter can be confi&%red to accept a broadcast re8%est for a ,6P
service and then for$ard it as a %nicast to a specific IP address. !y defa%lt, the ip helper-address
co''and for$ards the follo$in& ei&ht ,6P services1
Ti'e
TACAC+
6)+
!55TP>6CCP +erver
!55TP>6CCP Client
TFTP
)et!I5+ )a'e +ervice
)et!I5+ data&ra' +ervice
In the partic%lar case of 6CCP, a client broadcasts a 6CCP6I+C5A*R packet on its local se&'ent.
This packet is picked %p by the &ate$ay. If a helper-address is confi&%red, the 6CCP packet is
for$arded to the specified address. !efore for$ardin& the packet, the ro%ter fills in the GIA66R field
of the packet $ith the IP address of the ro%ter for that se&'ent. This address $ill then be the &ate$ay
address for the 6CCP client, $hen it &ets the IP address.
The 6CCP server receives the discover packet. The server %ses the GIA66R field to inde( into the
list of address pools, to find one $hich has the &ate$ay address set to the val%e in GIA66R. This pool
is then %sed to s%pply the client $ith its IP address.
S-ar putea să vă placă și
- Lab 10.6.1: Creating A Small Lab TopologyDocument9 paginiLab 10.6.1: Creating A Small Lab TopologyAnnysa FirdausÎncă nu există evaluări
- IPv4 Subnetting for Beginners: Your Complete Guide to Master IP Subnetting in 4 Simple Steps: Computer Networking, #1De la EverandIPv4 Subnetting for Beginners: Your Complete Guide to Master IP Subnetting in 4 Simple Steps: Computer Networking, #1Evaluare: 5 din 5 stele5/5 (3)
- The Cisco 800 Series RoutersDocument6 paginiThe Cisco 800 Series RoutersscribsubÎncă nu există evaluări
- Assigning Ip Addresses To Routers: Jabraham@utpa - EduDocument7 paginiAssigning Ip Addresses To Routers: Jabraham@utpa - EduAdriana AdyÎncă nu există evaluări
- Feedback:: Score 1 of 1Document53 paginiFeedback:: Score 1 of 1Rj ThakurÎncă nu există evaluări
- Kablom MreznimDocument7 paginiKablom Mreznimmaxo1Încă nu există evaluări
- NP Complete Record.Document78 paginiNP Complete Record.Syed Mudassar AliÎncă nu există evaluări
- NAT PAN TheoryDocument9 paginiNAT PAN TheoryArun SomashekarÎncă nu există evaluări
- It1402 - Mobile Computing Unit Iv: Vasantha Kumar .V Lecturer CSEDocument10 paginiIt1402 - Mobile Computing Unit Iv: Vasantha Kumar .V Lecturer CSEVignesh Manicka DiwakarÎncă nu există evaluări
- CCNA Practice Certification Exam # 2Document23 paginiCCNA Practice Certification Exam # 2Mauricio Rodriguez FigueroaÎncă nu există evaluări
- Network Address TranslationDocument10 paginiNetwork Address Translationravi_666Încă nu există evaluări
- Internet Addressing NotesDocument5 paginiInternet Addressing Notestornado2307Încă nu există evaluări
- 5.1.3 Wireless Gateway New FormatingDocument16 pagini5.1.3 Wireless Gateway New FormatingjohnsonsemÎncă nu există evaluări
- 01OSI Reference ModelDocument5 pagini01OSI Reference ModelMani Kanta100% (1)
- Configuring The Device As A PPPoE Client On Huawei AR1200Document8 paginiConfiguring The Device As A PPPoE Client On Huawei AR1200Elizabeth RichÎncă nu există evaluări
- Resueltos Ccna2Document139 paginiResueltos Ccna2Mauricio SalazarÎncă nu există evaluări
- CCNA 4 Chapter 5 v5 Exam Answers 2014Document8 paginiCCNA 4 Chapter 5 v5 Exam Answers 2014adrian743842Încă nu există evaluări
- Asterisk SecretDocument46 paginiAsterisk SecretyosuaalvinÎncă nu există evaluări
- What Is A Firewall?: The WordDocument5 paginiWhat Is A Firewall?: The WordKrishna ForuÎncă nu există evaluări
- NAT Network Address TranslationDocument41 paginiNAT Network Address TranslationPaul100% (1)
- Assignment No. Name of Assignment Page NoDocument47 paginiAssignment No. Name of Assignment Page NoSwapneel JadhavÎncă nu există evaluări
- Unit 3 Topic 6 Port Forwarding 3Document10 paginiUnit 3 Topic 6 Port Forwarding 3earl bagainÎncă nu există evaluări
- Chapter 4 Lab 4-2, Mixed Layer 2-3 Connectivity Chapter 4 Lab 4-2, Mixed Layer 2-3 ConnectivityDocument13 paginiChapter 4 Lab 4-2, Mixed Layer 2-3 Connectivity Chapter 4 Lab 4-2, Mixed Layer 2-3 ConnectivityKarina Herrera YzaguirreÎncă nu există evaluări
- Module 10 Exam Answers: - Layer 3Document7 paginiModule 10 Exam Answers: - Layer 3BadrudinÎncă nu există evaluări
- Take Assessment - Enetwork Final Exam - Ccna Exploration: Network Fundamentals (Version 4.0)Document20 paginiTake Assessment - Enetwork Final Exam - Ccna Exploration: Network Fundamentals (Version 4.0)Raphael AlmeidaÎncă nu există evaluări
- CCNA Guide To Networking - Ch4 - Quiz SolutionsDocument4 paginiCCNA Guide To Networking - Ch4 - Quiz SolutionsNickHenry0% (1)
- Chapter 3 Lab A: Securing Administrative Access Using AAA and RadiusDocument25 paginiChapter 3 Lab A: Securing Administrative Access Using AAA and RadiusfernaleoÎncă nu există evaluări
- Advanced Troubleshooting by Sniffing Packets (Packet Capture)Document5 paginiAdvanced Troubleshooting by Sniffing Packets (Packet Capture)CristiÎncă nu există evaluări
- Port (Computer Networking) - WikipediaDocument10 paginiPort (Computer Networking) - Wikipediabadri495170Încă nu există evaluări
- 6.clusterware NetworkingDocument5 pagini6.clusterware NetworkingmalruÎncă nu există evaluări
- Bpdus May Be Discarded Because of Expiring TimersDocument25 paginiBpdus May Be Discarded Because of Expiring TimersManúh Badd BrownÎncă nu există evaluări
- Internet Security Features About The Internet: How Web Information Is Located On The InternetDocument11 paginiInternet Security Features About The Internet: How Web Information Is Located On The InternetsocmasterÎncă nu există evaluări
- NatDocument12 paginiNatAnh TranÎncă nu există evaluări
- Penetration Testing With IPv6Document8 paginiPenetration Testing With IPv6Bharath KumarÎncă nu există evaluări
- Nat in Voip: RequirementsDocument19 paginiNat in Voip: Requirementsgarytj21Încă nu există evaluări
- Semester 3 FinalDocument30 paginiSemester 3 FinaldilanshaÎncă nu există evaluări
- Proxies: Basic NATDocument13 paginiProxies: Basic NATKaushal TrivediÎncă nu există evaluări
- Ccnasv1.1 Chp03 Lab-A Aaa-Radius StudentDocument25 paginiCcnasv1.1 Chp03 Lab-A Aaa-Radius StudentAngel MendozaÎncă nu există evaluări
- Session 12Document10 paginiSession 12theresa.painterÎncă nu există evaluări
- 6.6.7 Packet Tracer - Configure PAT - ILMDocument4 pagini6.6.7 Packet Tracer - Configure PAT - ILMLizardo Hilario Hinostroza GuillermoÎncă nu există evaluări
- Introduction To Routing: Destination AddressDocument8 paginiIntroduction To Routing: Destination AddressB RaoÎncă nu există evaluări
- Internet SocketDocument4 paginiInternet SocketAshish BardhanÎncă nu există evaluări
- CCNA1 Cap5 100Document7 paginiCCNA1 Cap5 100Sinny85Încă nu există evaluări
- Chapter7 Address TranslationDocument16 paginiChapter7 Address TranslationDacaen DanÎncă nu există evaluări
- Tremaine Johnson CompTIA HW#1Document4 paginiTremaine Johnson CompTIA HW#1tntgaming222Încă nu există evaluări
- Ethical Hacking and Digital ForensicsDocument92 paginiEthical Hacking and Digital ForensicsJanvi WaghmodeÎncă nu există evaluări
- Access The Public Internet Via Network Address Translation (NAT)Document7 paginiAccess The Public Internet Via Network Address Translation (NAT)Hotico CatalinÎncă nu există evaluări
- Network Address Translation Between A Private Network and The InternetDocument14 paginiNetwork Address Translation Between A Private Network and The InternetheliosÎncă nu există evaluări
- 006 57-NAT On FTDDocument6 pagini006 57-NAT On FTDPractical1Încă nu există evaluări
- Nat IP FIREDocument64 paginiNat IP FIREVmen Liar PiaggioÎncă nu există evaluări
- 05 TCP-IP SocketsDocument6 pagini05 TCP-IP Socketsvalic_foreverÎncă nu există evaluări
- Network Address Translation (NAT) : Khawar Butt Ccie # 12353 (R/S, Security, SP, DC, Voice, Storage & Ccde)Document11 paginiNetwork Address Translation (NAT) : Khawar Butt Ccie # 12353 (R/S, Security, SP, DC, Voice, Storage & Ccde)sans mahe1Încă nu există evaluări
- Config Ip MatrizDocument12 paginiConfig Ip MatrizJavier Sanchez SanchezÎncă nu există evaluări
- Guia Estudio HCNADocument12 paginiGuia Estudio HCNAErick Bravo100% (1)
- Questions and Answers To Previous Years PapersDocument6 paginiQuestions and Answers To Previous Years Paperssunil chaudhariÎncă nu există evaluări
- Rapport 201104 IPv6 Deployment in Local Area NetworksDocument10 paginiRapport 201104 IPv6 Deployment in Local Area NetworksMatthew KeatingÎncă nu există evaluări
- ACL StructureDocument1 paginăACL Structurecbrzana100% (1)
- CCNAS - Chp2 - PTActA - Syslog-SSH-NTP - InstructorDocument5 paginiCCNAS - Chp2 - PTActA - Syslog-SSH-NTP - InstructorAziz LondonÎncă nu există evaluări
- Sybex - Bonus - NATDocument16 paginiSybex - Bonus - NATStefan NeacsuÎncă nu există evaluări
- TCP IpDocument22 paginiTCP IpCentaur ArcherÎncă nu există evaluări
- OSI ModelDocument1 paginăOSI ModelGhaziAnwar100% (1)
- LXC Container Usg Ubuntu 23Document13 paginiLXC Container Usg Ubuntu 23cosmincsoÎncă nu există evaluări
- Thin ManagerDocument636 paginiThin ManagerlinoÎncă nu există evaluări
- Parallel Interfaces For DAQ SystemsDocument20 paginiParallel Interfaces For DAQ Systemsmubit993Încă nu există evaluări
- Update Soft1 TDocument3 paginiUpdate Soft1 TCarmeloÎncă nu există evaluări
- Learncisco Quiz 65f84c1b3d814Document1 paginăLearncisco Quiz 65f84c1b3d814Lý Nghĩa PhanÎncă nu există evaluări
- Setting Express 500Document11 paginiSetting Express 500Ahmed ZaidÎncă nu există evaluări
- Technical Specification Mef 2Document41 paginiTechnical Specification Mef 2chaidar_lakareÎncă nu există evaluări
- Forticlient Ems - Quickstart GuideDocument53 paginiForticlient Ems - Quickstart GuideMohamed KalkoulÎncă nu există evaluări
- DTNData AIA User ManualDocument29 paginiDTNData AIA User ManualelkaÎncă nu există evaluări
- GSM Modem Interfacing With Microcontroller 8051 For SMS ControlDocument9 paginiGSM Modem Interfacing With Microcontroller 8051 For SMS Controlamism24Încă nu există evaluări
- Maxwell ManualDocument108 paginiMaxwell Manualns4gguy100% (1)
- Platform Integrtn SupportMatrix DP11.02 PDFDocument15 paginiPlatform Integrtn SupportMatrix DP11.02 PDFSandip AjaniÎncă nu există evaluări
- Comparison Study Between IPV4 & IPV6: Amer Nizar Abu AliDocument4 paginiComparison Study Between IPV4 & IPV6: Amer Nizar Abu AliSuranga SampathÎncă nu există evaluări
- PIR Sensor Using Patients IdentificationDocument20 paginiPIR Sensor Using Patients IdentificationsaravananÎncă nu există evaluări
- BMS Keystrokes DefaultsDocument18 paginiBMS Keystrokes Defaultstumbler0031Încă nu există evaluări
- Docker Certified Associate: Training DemoDocument21 paginiDocker Certified Associate: Training Demoravindramca43382Încă nu există evaluări
- NMS - V2 Installation ManualDocument25 paginiNMS - V2 Installation ManualKheme VitoumetaÎncă nu există evaluări
- JstackDocument62 paginiJstackabdulbasith786Încă nu există evaluări
- WideFS TechnicalDocument20 paginiWideFS Technicalbagarie2Încă nu există evaluări
- Router Configuration NotesDocument12 paginiRouter Configuration Notesduke_doÎncă nu există evaluări
- Intel Microprocessors Case Study-Solution: Response To Threat of ImitationDocument2 paginiIntel Microprocessors Case Study-Solution: Response To Threat of Imitationsaherhcc4686Încă nu există evaluări
- CC Lab 1 Roll No. 10Document15 paginiCC Lab 1 Roll No. 10Revathi DusaÎncă nu există evaluări
- Big Tap Monitoring Fabric v4.5Document8 paginiBig Tap Monitoring Fabric v4.5tomertoÎncă nu există evaluări
- Parallel ProcessingDocument12 paginiParallel ProcessingSanjay SaviÎncă nu există evaluări
- Intel D845EPT2 Manual PDFDocument78 paginiIntel D845EPT2 Manual PDFLangllyÎncă nu există evaluări
- Equinix Internet Exchange Setup and DetailsDocument26 paginiEquinix Internet Exchange Setup and DetailsPetch SurasitÎncă nu există evaluări
- 2015apr Using SAG InstallerDocument59 pagini2015apr Using SAG InstallerRaghava RudrakanthÎncă nu există evaluări
- ASM Troubleshooting Overview PDFDocument27 paginiASM Troubleshooting Overview PDFUdaya SamudralaÎncă nu există evaluări
- Basic Linux Commands by T@R@24Document2 paginiBasic Linux Commands by T@R@24Craciun MariusÎncă nu există evaluări