Documente Academic
Documente Profesional
Documente Cultură
18 Iss 1155 PDF
Încărcat de
abdel_lak0 evaluări0% au considerat acest document util (0 voturi)
48 vizualizări5 paginiIn this paper, we provide a selected list of tools that can be used for assessing web application security. Intention is to present available tools that can help in search of vulnerabilities in web applications and thus make them more secure. Paper is written for web application developers and testers, and of course, students who have interest in web development.
Descriere originală:
Titlu original
18_ISS_1155.pdf
Drepturi de autor
© © All Rights Reserved
Formate disponibile
PDF, TXT sau citiți online pe Scribd
Partajați acest document
Partajați sau inserați document
Vi se pare util acest document?
Este necorespunzător acest conținut?
Raportați acest documentIn this paper, we provide a selected list of tools that can be used for assessing web application security. Intention is to present available tools that can help in search of vulnerabilities in web applications and thus make them more secure. Paper is written for web application developers and testers, and of course, students who have interest in web development.
Drepturi de autor:
© All Rights Reserved
Formate disponibile
Descărcați ca PDF, TXT sau citiți online pe Scribd
0 evaluări0% au considerat acest document util (0 voturi)
48 vizualizări5 pagini18 Iss 1155 PDF
Încărcat de
abdel_lakIn this paper, we provide a selected list of tools that can be used for assessing web application security. Intention is to present available tools that can help in search of vulnerabilities in web applications and thus make them more secure. Paper is written for web application developers and testers, and of course, students who have interest in web development.
Drepturi de autor:
© All Rights Reserved
Formate disponibile
Descărcați ca PDF, TXT sau citiți online pe Scribd
Sunteți pe pagina 1din 5
Evaluation of tools for assessing Web applications
V. Suhina, M. Kozina and S. Gro
Department of Electronics, Microelectronics, Computer and Intelligent Systems
Faculty of Electrical Engineering and Computing
Unska 3, 10000 Zagreb, Croatia
Phone: (01) 612-99-35 Fax: (01) 617-00-07 E-mail: vanja.suhina@fer.hr
Summary In this paper, we provide a selected list of tools
that can be used for assessing Web application security.
Intention is to present available tools that can help in search
of vulnerabilities in Web applications and thus make them
more secure. The paper is written for Web application
developers and testers, and of course, students who have
interest in web development. So, it is concentrated on free
and/or open source tools, and thereby, commercial products
are not mentioned. First part of paper provides overview of
vulnerabilities that can be detected by using mentioned tools.
In the second part, the tools are described and it is shown for
which actions these tools can be used.
I. INTRODUCTION
Web applications have become common way for companies to
conduct business with the outside world. The static web pages are
gone and now, almost every company has its own dynamic,
interactive Web application that communicates with their clients.
Sometimes, these applications are written by programmers not
familiarized with security problems behind their Web application
front-end or their work is guided by hard to get deadlines so
application security is not very high on priority list. Thus these
Web applications become main threat to secrecy and integrity of
companys sensitive data.
Web applications security incidents have significantly
increased in past two years [1]. Most incidents were possible to
happen due to very well known design flaws in applications. As it
is shown in [2], some of the most common flaws are Cross Site
Scripting (XSS), Injection flaws, Malicious File Execution,
Insecure Direct Object Reference and Cross Site Request Forgery
(CSRF). Last year, top four types of vulnerabilities, XSS, SQL
Injection, Remote File Inclusion and Buffer Overflow, were
responsible for more than 50% of all Common Vulnerabilities
and Exposures (CVEs) [3].
There are various tools for Web application security
assessment, both open and closed source. In this paper are listed
and evaluated those that are found valuable and mature while in
the same time being freely available, i.e. open source. Description
of their features and architecture is also given.
The paper is structured as follows. In the second section
overview of the most common vulnerabilities is given. Then, in
section 3, description of each tool is given. The paper finishes
with conclusion in section 4, and list of references in section 5.
II. OVERVIEW OF VULNERABILITIES
To aid understanding of the description of tools given in the
following section, as well as to emphasize what should be taken
care of during design and development of Web applications, a
short description of most common techniques and vulnerabilities
used to compromise Web applications follows.
Session Prediction or Session Hijacking is a method of
impersonating a Web application user by deducting or guessing
the unique value used to identify a user session. As a
consequence of this vulnerability, attacker gains the ability to
issue web site request with hijacked users privileges [4]. This
method is directed to objects used to bind user actions into a
single stateful session by web applications. Most common objects
are cookies and URL parameters.
Cross Site Scripting (XSS) vulnerability occurs when an
attacker uses a Web application to send malicious executable
code to another Web application user. Web application simply
takes attacker supplied data and sends it to users web browser
without validating data. Executable code is often used to
compromise confidential information or even hijack user sessions
[4].
Directory indexing and information leakages are
vulnerabilities that reveal sensitive data, such as developer
comments, error messages, secret files and other contents. As a
result of this vulnerabilities, an attacker gains additional
information and guidance in exploitation of a Web application
[4].
Insufficient Process Validation vulnerability occurs when a
logical flow of a Web applicationis bypassed or circumventedby
user - attacker. If the user state through a session is not verified,
the Web application could be exploited [4].
SQL injection attacks are used to compromise Web
applications that construct SQL statements from user input.
Before a user supplied input is used in a Web application
processes, it must be adequately validated and checked for special
characters that can be used to construct a custom SQL statement.
This attack can lead to information leakage or taking full control
of a database by an attacker [4].
HTTP response splitting attack occur when the data enters a
Web application through an untrusted source, most frequently an
HTTP request, and then, it is included in an HTTP response
header sent to a web user without being validated for malicious
characters. It can lead to web cache poisoning, cross user
defacement, hijacking pages and Cross Site Scripting [5].
A Brute Force attack is an automated process of trial and error
used to guess user credentials[4].
III. TOOLS
In this section description and evaluation of several free Web
application assessment tools is given. These tools are:
WebScarab
Pantera
ATK
Gamja
Burp Suite
Wapiti
While examining tools, focus has been on their architecture,
functionality, analyzing and testing abilities. In the case when a
tool is modularized, most important modules and their
functionalities are described.
1. WebScarab
The aim of WebScarab is to provide a free tool for Web
application developers and reviewers that will help them in better
understanding of Web applications functionality and in
identification of the possible vulnerabilities that could
compromise or bring down those Web applications.
OWASP (Open Web Application Security Project) WebScarab
is an open-source framework written in J ava used for analyzing
and testing Web applications.
Common use of WebScarab is as an intercepting proxy. Proxy
allows operator to review and modify requests created by a user
using web browser before those requests are sent to a server. It
can also review and modify responses sent froma server, before
they are received by users browser. Intercepting proxy applies
both to HTTP and HTTPS communication. Every conversation
which passes through WebScarab is added to a communication
list, so it can be reviewed and additionally analyzed.
WebScarab is based on plugin architecture. There are two
types of plugins: (i) plugins that create conversation, and
(ii) plugins that analyze conversations. Plugins that create
conversations use specific methods to decide which resources to
request fromthe server, how to parameterize the request headers,
and then submits the request to the server. After receiving the
response froma server, they can perform some computation on
the responses, and based on computation result decide whether or
not to submit that conversation to the framework. When
conversation is submitted to the framework, it is distributed to
other plugins that can do further analysis. Current version of
WebScarab offers these plugins:
Proxy
Manual Request
Spider
SessionID Analysis
Scripted
Fragments
Compare
Fuzzer
Search
Proxy plugins observe traffic between the browser and the web
server. The WebScarab proxy is able to observe both HTTP, and
encrypted HTTPS traffic by negotiating an SSL connection
between WebScarab and the browser instead of simply
connecting the browser to the server and allowing an encrypted
streamto pass through it. Various additional proxy plugins have
been developed to allow the operator control over requests and
responses that pass through the proxy [6]. The Manual Intercept
is a special proxy plugin which allows the user to intercept
requests fromthe browser and responses fromthe server, inspect
them, and optionally make modifications before transmission.
This is particularly useful when one wants to submit a formto a
web server, but J avaScript validation rejects the values entered
into the form. The request can be altered after the validation has
been performed.
The Manual Request plugin allows the user to handcraft a
request to be sent to the server. It is also possible to replay a
previous request by selecting it fromthe drop down selection
box. Previous requests which are loaded into the editor can also
be edited before being sent to the server. When the "Fetch
Response" button is selected, WebScarab sends the request to the
appropriate server, and saves the conversation for analysis by the
other WebScarab plugins. It can also be used for getting cookies
relevant to the requested URL from the "Shared Cookies" list and
use them in future requests [7].
The Spider plugin analyses responses to identify any links in
the response body or the "Location" header. If the URL
represented has not been seen, the URL is added to a tree, and
can be automatically downloaded when desired. WebScarab has
two modes of fetching unseen links. "Fetch Tree" enumerates all
currently unknown links below the selected node, and queues
them for retrieval. "Fetch Selection" queues only the selected
nodes for retrieval [7].
SessionID Analysis plugin collects and analyses a number of
cookies or URL-based parameters to visually determine the
degree of randomness and unpredictability. WebScarab tags all
sessionids with the date and time when they were collected, and
then, after performing calculations on the string value of the
sessionid in order to convert it into a number, plots the value
against time on a graph. The human eye is a lot more efficient at
identifying patterns than a computer, so by plotting the values it
makes it easy for humans to visualize the sequence [7].
Scripted plugin is intended to give users the ability to create
test scripts by using special BSF (Bean Scripting Framework)
supported scripting language. BSF is J ava-like language used to
write test scripts. Scripts use WebScarab J ava objects in order to
create requests and send them to the server, and then to perform
analysis on the responses [7].
The Fragments plugin parses HTML responses, and looks for
scripts and comments. This plugin can be used for searching any
hidden links, other debugging code.
The Compare plugin allows the user to judge the degree of
difference between a number of responses. This is useful when
client issued a number of requests for a particular URL, possibly
via the Scripted plugin, and we would like to evaluate the results.
Obviously, if it is possible to eliminate groups of identical
responses at once, it can save some time.
The Fuzzer plugin allows users to use different combinations
of parameters. The idea is to configure the request method, the
basic URL, the request version, and list of parameters to expose
incomplete parameter validation, leading to vulnerabilities like
Cross Site Scripting (XSS) and SQL Injection.
The Search plugin uses BSF scripts to identify and filter
conversations that user would like to analyze.
Use case of WebScarab can be divided into two phases. In the
first phase analysis is performed, and we'll call it analysis phase.
In the analysis phase it is recommended to use Proxy, Fragments,
Scripted and Spider plugins. Proxy is very helpful in analyzing
communication, especially in inspecting structure of requests and
responses. Fragments plugin can be used to detect possible
information leakage caused by comments or scripts. Spider
plugin is used to crawl through application to gather all possible
links and even find links to hidden files.
Second phase is a testing phase. WebScarab is an excellent
tool for manual testing. Main plugins used in this phase are:
Manual Request, Session ID analyzer and Fuzzer plugin. Manual
Request plugin is used to make customized requests and for
cookie manipulations. It can be used to detect security
vulnerabilities like HTTP splitting. Session ID analyzer collects
and examines a reasonably large sample of session identifiers, to
determine if they could be vulnerable to prediction, or brute force
attacks. Fuzzer is very useful in detection of SQL or LDAP
injection, XSS vulnerabilities and insufficient process validation
vulnerability.
2. Pantera
OWASP Pantera is a web assessment project written in Python
[8] currently in beta development phase. Pantera itself is a Web
application that runs inside the browser and can be customized by
the user. Although Pantera is still under development it offers
tools like penetration testing proxy, an application scanner and an
intelligence analysis framework. Panteras analysis engine can
store each web page that Pantera sees and analyze it for
comments, scripts, vulnerabilities, hidden tags and more. All this
is done in background and transparent to the user while testing
the Web application manually. All the information gathered
during analysis is stored in the database [9]. Pantera has many
utilities like Data Miner, Interceptor, Session Trace, Fuzzer, Web
spider. All those utilities make Pantera powerful web assessment
studio in searching of all kinds of vulnerabilities.
In future, the primary goal of Pantera would be to combine
automated capabilities with complete manual testing to get the
best penetration testing results.
3. ATK
Attack Tool Kit (ATK) is tool developed in Visual Basic,
written for Windows operating system. It is licensed under the
GNU General Public License (GPL) and is free to use and
distribute. It can be used to perform fast checks for dedicated
vulnerabilities [10].
The tool is also based on plugin architecture, but plugins have
a little bit different meaning than usual. Each plugin is actually
one check, i.e. one specific test designed to detect or exploit
certain vulnerability or flaw. The tool is shipped with 340
preinstalled plugins (checks), but it is very simple to download
and add new one or even write custom ones. The plugins are
written in simple scripting language, and there exists detailed
documentation on how to use it. The biggest advantage of this
tool is possibility of easy modification of each plugin [10]. It can
even be done during run-time.
The plugins can be searched by several parameters: name, ID,
port number, family, severity or class (of vulnerability). All this
makes it very simple to find required plugin. On Visualizing
form, it can be monitored on dynamic sketch what's going on
between the attacker and the target. On Response form, the last
response fromthe server is shown. Everything is logged and can
be nicely combined into one report and statistics sheet.
This tool is great for verifying existence of a specific
vulnerability and exploitation of a specific weakness. This makes
it useful for scanning systems for vulnerable applications or
server flaws and it comes handy while doing penetration tests.
However, the tool is not designed for automatic testing of custom
made applications and finding new security flaws. For automatic
scanning, it relies on knowledge base of known server and
application flaws that it tries to find. To test custom made
applications, new tests need to be written.
4. Gamja
Gamja is another project written under GPL license. It is
command-line tool written in Perl [11], portable to most popular
platforms and at this moment it is in early beta phase. This tool is
able to find XSS vulnerabilities, SQL Injection flaws and does
URL perimeter validation check [11].
The scanning of web site is fixed process that cannot be
altered. Only parameters that can be configured for scanning are
port number and start page. As this project is in early phase of
development, it is assumed that new configuration options and
features will be added. The tool crawls through a web site for all
accessible links, finds entry points to the application and tries to
exploit them. As there is no available documentation for the tool,
the methods of how this tool works can only be deduced by
examining the source code.
5. Burp Suite
Burp Suite is a tool for attacking web applications. It consists
of several, so called, burp tools (Proxy, Spider, Intruder and
Repeater) and the robust framework that lies beneath them. The
framework is designed to handle HTTP requests, authentication,
downstream proxy, logging and alerting, and the tools are
designed to help in a process of assessing applications. All tools
are well matched and information gathered fromone tool can
easily be shared with all the other tools. Each tool can be used as
a single application, but the strength of Burp Suite comes when
combining all of them together.
Burp suite is written in J ava, so it is portable on all platforms
that have J ava Runtime Environment available. It is copyrighted
to PortSwigger.net [13]. The code is closed, but the tool can
freely be used for personal and commercial purposes.
Burp Repeater is tool for manually sending HTTP or HTTPS
requests to web application. The request sent can easily be altered
before sending new one. The Repeater remembers all sent
requests and responses and allows simple navigation through
them. It's search engine can be used for tracking values that
match regular expressions through given responses. It is well
connected with other Burp tools such as Burp Proxy.
Burp suite has its own proxy. It allows user to intercept,
inspect and modify the raw traffic passing in both directions. It
can also display traffic in three different ways: raw text, table of
parameters and values, and hexadecimal view. The incoming and
outgoing traffic can be filtered using very efficient filtering rules
that can be combined using simple filter statements. One more
addition to this tool is header manipulation area, which allows
configuring replacement for some strings (matched by regular
expressions) found in HTTP headers. All traffic is saved to
history where it can select some packet and send it to other tool
such as Burp Repeater, Intruder or Spider.
Burp Spider is tool for enumerating applications content and
functionality. It follows hyperlinks found within HTML,
J avaScript, and submitting forms, but it also uses other clues such
as directory listings, source code comments and configuration
files. The results can be displayed in tree view or table format and
requests can be again sent to burp intruder or repeater. When one
item is selected, the tool also displays information regarding
where this resource is linked from, and what other hyperlinks
does it have.
Burp Intruder is central tool for assessing web applications. It
is used to automate a wide range of attacks against applications,
including testing for common web application vulnerabilities.
Some of them are SQL injection, cross-site scripting, buffer
overflows, directory traversal, etc. Before using the Intruder, the
user must gain some knowledge of functionality and structure of
the target application. This information can be gathered with
other burp tools. First, places in HTTP requests where payloads
will be injected have to be defined. There are many types of
payloads that can be used: preset list of strings, character and
case substitutions, number and date iterators, bruteforcer
character sets, illegal Unicode and null values, etc. One example
where injecting payloads can be used is password guessing.
Besides performing the simple brute force attack, more complex
types can be achieved using character substitution (common
substitution of letters with numbers that look alike), case
substitutions, etc. All payloads can be URL-encoded or base-64
encoded and its hash can be calculated. All this makes Intruder
highly configurable and capable for all types of attacks.
Burp Suite is excellent tool for checking and attacking web
applications. It is not simple point-and-click tool as it requires
some knowledge of the target application. But, it can easily
automate further investigation and exploitation of vulnerabilities
and flaws.
At the time of this writing, it is announced that another tool
will soon be released, Burp Scanner. Burp Scanner will perform
automated vulnerability assessments of web-enabled applications
[13].
6. Wapiti
Wapiti is a web application security auditor written in Python.
It works as a black box vulnerability scanner and it can find
following vulnerabilities: Database injection, Cross Site
Scripting, Bad File Handling detection, Command Execution
detection, Lightweight Directory Access Protocol (LDAP) and
Carriage Return Line Feed (CRLF) injection. [14]
For optimal performance, it should be used with Tidy library
[15] whose purpose is to clean up the HTML and thus, helps
scanner to do the scan more efficiently. The code is broken in
several files. Wapiti.py acts as a fuzzer, lswww.py is webspider
and cookie.py and getcookie.py are tools for getting cookie from
server.
It is command line tool so all configuration is done through
parameters to the application. The configuration is very simple
and consists of configuring start URL, excluding some URLs
from checking, setting proxy, cookie or authentication
credentials.
The tool is released under GPL.
IV. CONCLUSION
Developing a secure web application has become an important,
but difficult task to many web developers. Difficulty lies in
growing number of vulnerabilities which cause web applications
to malfunction. While developing applications, focus is mostly on
functionality, scalability and user-friendly features which leaves
less time for development of security measures. Many Web
applications go through rapid development phases with extremely
short turnaround time, making it difficult to eliminate
vulnerabilities. Much vulnerabilities can be avoided by better
coding, secure strategies and education of developers, but these
solutions are very expensive.
Todays tendency of solving security issues and removing
vulnerabilities fromweb applications is to use web application
security assessment tools. Open source web application security
tools are free so they dont increase cost of developing web
application. Every tool analyzed in this paper has it own field of
usage where it shows the best results.
OWASP WebScarab is one of the most comprehensive tools in
the field used for analyzing request and responses fromboth
HTTP and HTTPS communication. It is also very powerful tool
in doing manual tests of web applications. Users of this tool
should know basics of HTTP and of todays web application
vulnerabilities to fully use every feature of WebScarab. On the
other hand, WebScarabs limitation is an absence of a database
with known prearranged list of vulnerabilities, so WebScarab
cant be used for automatic web application security tests. As a
result of this shortcoming, OWASP took one step further, and
started development of a new project Pantera. Idea of Pantera is
to provide a user with a full security assessment of a web
application. Pantera will have more features than WebScarab,
especially in the field of automatic test and data mining. Also,
knowledge needed to use Pantera would be minimal.
For those looking for a database-oriented tool that checks
server and application for known flaws, ATK is a suitable tool. It
is very simple to use, but it depends on a knowledge base, so if
not updated regularly, it may not find newly discovered
vulnerabilities. It can be used as first step in assessing the target:
defining on which server application run, finding some server
misconfigurations, gathering sensitive data, etc.
For more aggressive approach, there is Burp Suite. Beside
finding vulnerabilities, this tool can also be used for exploiting
them. One of the examples is automatization of password
guessing. However, to use this tool, the user should be
familiarized with concepts of why vulnerabilities exist and how
exploits work.
Gamja and Wapiti projects have not come so far in richness of
features, but if theres a need for command line tools that are
portable via all kind of platforms, they should be tried.
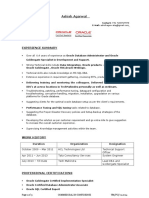
In Table 1., it is given overview of each tools features and
field of use.
TABLE I.
OVERVIEW OF TOOLS FEATURES
T
e
s
t
s
f
o
r
k
n
o
w
n
v
u
l
n
e
r
a
b
i
l
i
t
i
e
s
A
u
t
o
m
a
t
i
c
t
e
s
t
s
M
a
n
u
a
l
t
e
s
t
s
F
e
t
c
h
i
n
g
a
n
d
u
s
i
n
g
C
o
o
k
i
e
s
H
T
T
P
p
a
c
k
e
t
a
n
d
U
r
l
p
a
r
a
m
e
t
e
r
s
m
a
n
i
p
u
l
a
t
i
o
n
P
r
o
x
y
L
i
n
k
c
r
a
w
l
e
r
WebScarab x x x x x
Pantera x x x x
ATK x x x
Gamja x x
BurpSuite x x x x
Wapiti x x x
REFERENCES
[1] Web Application Security Consortium Web Hacking
Statistics (10.1.2007.)
http://www.webappsec.org/projects/whid/statistics.shtml
[2] The Open Web Application Security Project, The Ten
Most Critical Web Application Security Vulnerabilities:
2007 Update, Release Candidate 1
[3] Steven M. Christey, Vulnerability Type Distribution in
CVE
[4] Web Application Security Consortium Threat
classification (15.1.2007)
http://www.webappsec.org/projects/threat/
[5] A. Klein, Divide and Conquer HTTP Response
Splitting, Web Cache Poisoning Attacks, and Related
Topics, Sanctum Inc., March 2004
[6] OWASP OWASP WebScarab Project (20.1.2007)
http://www.owasp.org/index.php/OWASP_WebScarab_
Project
[7] WebScarab - User documentation (21.1.2007)
http://dawes.za.net/rogan/webscarab/docs/
[8] OWASP OWASP Pantera Project (28.1.2007)
http://www.owasp.org/index.php/OWASP_Pantera_project
[9] Python Programming Language
http://www.python.org/
[10] The Attack Tool Kit Web Site, Marc Ruef (27.1.2007)
http://www.computec.ch/projekte/atk/
[11] Perl.com: The Source for Perl
http://www.perl.com
[12] Gamja: Web vulnerability scanner (28.1.2007)
http://sourceforge.net/projects/gamja
[13] PortSwigger.net (25.1.2007)
http://portswigger.net/
[14] Wapiti (26.1.2007)
http://wapiti.sourceforge.net/
[15] Tidy library (26.1.2007)
http://tidy.sourceforge.net/
S-ar putea să vă placă și
- Barracuda Web Application Firewall WP AdvantageDocument4 paginiBarracuda Web Application Firewall WP Advantageabdel_lakÎncă nu există evaluări
- Nse4-5 4Document5 paginiNse4-5 4abdel_lakÎncă nu există evaluări
- 1385454776-19. An Efficient Structure - Full PDFDocument6 pagini1385454776-19. An Efficient Structure - Full PDFabdel_lakÎncă nu există evaluări
- Network Security: Compromises and Countermeasures: Key WordsDocument6 paginiNetwork Security: Compromises and Countermeasures: Key Wordsabdel_lakÎncă nu există evaluări
- 006Document15 pagini006abdel_lakÎncă nu există evaluări
- Open Source Intrusion Detection System Using Snort: Conference PaperDocument8 paginiOpen Source Intrusion Detection System Using Snort: Conference Paperabdel_lak100% (1)
- Isaca Selftestengine COBIT-5 v2018-03-17 by Mia 30qDocument14 paginiIsaca Selftestengine COBIT-5 v2018-03-17 by Mia 30qabdel_lakÎncă nu există evaluări
- 06320109Document9 pagini06320109abdel_lakÎncă nu există evaluări
- CookiesDocument3 paginiCookiesabdel_lakÎncă nu există evaluări
- V5i4 0287Document5 paginiV5i4 0287abdel_lakÎncă nu există evaluări
- Parno CVDocument7 paginiParno CVabdel_lakÎncă nu există evaluări
- ReadmeDocument1 paginăReadmeabdel_lakÎncă nu există evaluări
- Default LogDocument3 paginiDefault Logabdel_lakÎncă nu există evaluări
- 2016 PetsDocument16 pagini2016 Petsabdel_lakÎncă nu există evaluări
- Institutional FirewallDocument6 paginiInstitutional Firewallabdel_lakÎncă nu există evaluări
- WatchGuard Training CourseDocument1 paginăWatchGuard Training Courseabdel_lakÎncă nu există evaluări
- 05 LectureDocument58 pagini05 Lectureabdel_lakÎncă nu există evaluări
- Master UOCDocument19 paginiMaster UOCabdel_lakÎncă nu există evaluări
- Bluetooth 11 Specifications BookDocument1 paginăBluetooth 11 Specifications BookDuc DuyÎncă nu există evaluări
- VMware VSphere Enterprise DataSheet DS enDocument4 paginiVMware VSphere Enterprise DataSheet DS enabdel_lakÎncă nu există evaluări
- Journal of Environmental Science, Computer Science and Engineering & TechnologyDocument9 paginiJournal of Environmental Science, Computer Science and Engineering & Technologyabdel_lakÎncă nu există evaluări
- Computer Security and Machine Learning: Worst Enemies or Best Friends?Document4 paginiComputer Security and Machine Learning: Worst Enemies or Best Friends?abdel_lakÎncă nu există evaluări
- Justin Sherrill ResumeDocument3 paginiJustin Sherrill Resumeabdel_lakÎncă nu există evaluări
- 2010-15 IFMAP Stage 1 Inventory Progress Report - 2010Document6 pagini2010-15 IFMAP Stage 1 Inventory Progress Report - 2010abdel_lakÎncă nu există evaluări
- Us Aers Cyber Espionage 07292011Document16 paginiUs Aers Cyber Espionage 07292011abdel_lakÎncă nu există evaluări
- How To Conduct Security AuditDocument7 paginiHow To Conduct Security Auditronics123Încă nu există evaluări
- Abowd Lane Barcelona 2004Document10 paginiAbowd Lane Barcelona 2004abdel_lakÎncă nu există evaluări
- Code ObfuscationDocument15 paginiCode Obfuscationabdel_lakÎncă nu există evaluări
- Bronie STRDocument17 paginiBronie STRabdel_lakÎncă nu există evaluări
- Bronie STRDocument17 paginiBronie STRabdel_lakÎncă nu există evaluări
- The Yellow House: A Memoir (2019 National Book Award Winner)De la EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Evaluare: 4 din 5 stele4/5 (98)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceDe la EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceEvaluare: 4 din 5 stele4/5 (895)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeDe la EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeEvaluare: 4 din 5 stele4/5 (5794)
- The Little Book of Hygge: Danish Secrets to Happy LivingDe la EverandThe Little Book of Hygge: Danish Secrets to Happy LivingEvaluare: 3.5 din 5 stele3.5/5 (399)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaDe la EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaEvaluare: 4.5 din 5 stele4.5/5 (266)
- Shoe Dog: A Memoir by the Creator of NikeDe la EverandShoe Dog: A Memoir by the Creator of NikeEvaluare: 4.5 din 5 stele4.5/5 (537)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureDe la EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureEvaluare: 4.5 din 5 stele4.5/5 (474)
- Never Split the Difference: Negotiating As If Your Life Depended On ItDe la EverandNever Split the Difference: Negotiating As If Your Life Depended On ItEvaluare: 4.5 din 5 stele4.5/5 (838)
- Grit: The Power of Passion and PerseveranceDe la EverandGrit: The Power of Passion and PerseveranceEvaluare: 4 din 5 stele4/5 (588)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryDe la EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryEvaluare: 3.5 din 5 stele3.5/5 (231)
- The Emperor of All Maladies: A Biography of CancerDe la EverandThe Emperor of All Maladies: A Biography of CancerEvaluare: 4.5 din 5 stele4.5/5 (271)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyDe la EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyEvaluare: 3.5 din 5 stele3.5/5 (2259)
- On Fire: The (Burning) Case for a Green New DealDe la EverandOn Fire: The (Burning) Case for a Green New DealEvaluare: 4 din 5 stele4/5 (73)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersDe la EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersEvaluare: 4.5 din 5 stele4.5/5 (344)
- Team of Rivals: The Political Genius of Abraham LincolnDe la EverandTeam of Rivals: The Political Genius of Abraham LincolnEvaluare: 4.5 din 5 stele4.5/5 (234)
- The Unwinding: An Inner History of the New AmericaDe la EverandThe Unwinding: An Inner History of the New AmericaEvaluare: 4 din 5 stele4/5 (45)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreDe la EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreEvaluare: 4 din 5 stele4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)De la EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Evaluare: 4.5 din 5 stele4.5/5 (121)
- Her Body and Other Parties: StoriesDe la EverandHer Body and Other Parties: StoriesEvaluare: 4 din 5 stele4/5 (821)
- c220m6 SFF SpecsheetDocument102 paginic220m6 SFF SpecsheetVijay DanielÎncă nu există evaluări
- Top Database Interview Questions and Answers UpdatedDocument9 paginiTop Database Interview Questions and Answers Updatedsoumya moturiÎncă nu există evaluări
- Exercise Week 1Document5 paginiExercise Week 1Sivaram DasariÎncă nu există evaluări
- OFSAAI Installation Guide 8.0.1.2.0Document8 paginiOFSAAI Installation Guide 8.0.1.2.0Prasad BillahalliÎncă nu există evaluări
- Manual-de-Zimbra-parte-IV-Comandos-en-Consola-Migracion-de-Servidores-Correo-hacia-Zimbra-8-7 Parte 5Document7 paginiManual-de-Zimbra-parte-IV-Comandos-en-Consola-Migracion-de-Servidores-Correo-hacia-Zimbra-8-7 Parte 5juan carlos barriosÎncă nu există evaluări
- Question Bank-Part A (2 Marks) - Unit II Struts and HibernateDocument25 paginiQuestion Bank-Part A (2 Marks) - Unit II Struts and Hibernatearavindan476Încă nu există evaluări
- Project Instructions 2 PDFDocument5 paginiProject Instructions 2 PDFsonali PradhanÎncă nu există evaluări
- DB2 V11 Tech OverviewDocument49 paginiDB2 V11 Tech OverviewEzhilmaran SandirasegaraneÎncă nu există evaluări
- AWS Database Products InfographicDocument1 paginăAWS Database Products InfographicHomer SemmsÎncă nu există evaluări
- Slides 13 Nat TraversalDocument22 paginiSlides 13 Nat TraversalEdson LivongueÎncă nu există evaluări
- 4th - Business IntelligenceDocument30 pagini4th - Business IntelligenceJoyce Gutierrez JulianoÎncă nu există evaluări
- The Primaver P6 Users Guide To ExcelDocument44 paginiThe Primaver P6 Users Guide To Excelaliengineer95383% (6)
- How To Embed Bangla Font in Web Pages How To Embed Bangla Font in Web PagesDocument27 paginiHow To Embed Bangla Font in Web Pages How To Embed Bangla Font in Web PagesmdmonzurhÎncă nu există evaluări
- Cisco MDS 9000 Family Acceleration Services - Enhances Hitachi TrueCopy Synchronous Replication Performance Solution Overview - CiscoDocument3 paginiCisco MDS 9000 Family Acceleration Services - Enhances Hitachi TrueCopy Synchronous Replication Performance Solution Overview - CiscoChristopher JonesÎncă nu există evaluări
- Data Processing SS2Document29 paginiData Processing SS2Ideji EkemenaÎncă nu există evaluări
- DBMS Final CodeDocument60 paginiDBMS Final Codeetaitu7Încă nu există evaluări
- LAB03-Creating An ETL Solution With SSISDocument9 paginiLAB03-Creating An ETL Solution With SSIShiba_cherifÎncă nu există evaluări
- تحليل وتصميم النظم وبناء قواعد البياناتDocument18 paginiتحليل وتصميم النظم وبناء قواعد البياناتMohmmad AhmedÎncă nu există evaluări
- Veeam ExamDocument5 paginiVeeam Examcrisandy3150% (2)
- Ashish Agarwal TechM FormatDocument7 paginiAshish Agarwal TechM Formatravi ranjan guptaÎncă nu există evaluări
- D3648 Rev G Programing EZIII VisualcDocument46 paginiD3648 Rev G Programing EZIII VisualcPdro Javier Figueredo PerezÎncă nu există evaluări
- Overview SymcliDocument34 paginiOverview SymcliDhananjay GuptaÎncă nu există evaluări
- ITT Online Test Question Bank 1Document165 paginiITT Online Test Question Bank 1Manjith MothiramÎncă nu există evaluări
- Chapter 1 Library SystemDocument2 paginiChapter 1 Library SystemMatthieu ZabatÎncă nu există evaluări
- KT Questions V1.6-LatestDocument18 paginiKT Questions V1.6-Latestvenu_logicÎncă nu există evaluări
- Sample Sales Re Engineering in OBIEE 11g Part IDocument10 paginiSample Sales Re Engineering in OBIEE 11g Part IAmit SharmaÎncă nu există evaluări
- Lecture No. 02Document9 paginiLecture No. 02usmanÎncă nu există evaluări
- ACE Certification Study GuideDocument2 paginiACE Certification Study GuidedumkoliveiraÎncă nu există evaluări
- Customui Ribbon Tabs Tab: " " Onload Rxiribbonui - OnloadDocument99 paginiCustomui Ribbon Tabs Tab: " " Onload Rxiribbonui - OnloadpabloloayzaÎncă nu există evaluări
- Power Query-Transforming Work Processes Using Excel PDocument2 paginiPower Query-Transforming Work Processes Using Excel PJia Xin0% (3)