Documente Academic
Documente Profesional
Documente Cultură
IEEE 2014 JAVA PARALLEL DISTRIBUTION PROJECT Behavior Rule Specification-Based Intrusion Detection For Safety Critical Medical Cyber Physical Systems
Încărcat de
2014PARALLELSYSTEMS0 evaluări0% au considerat acest document util (0 voturi)
12 vizualizări5 paginiTo Get any Project for CSE, IT ECE, EEE Contact Me @ 09666155510, 09849539085 or mail us - ieeefinalsemprojects@gmail.com-Visit Our Website: www.finalyearprojects.org
Titlu original
IEEE 2014 JAVA PARALLEL DISTRIBUTION PROJECT Behavior Rule Specification-based Intrusion Detection for Safety Critical Medical Cyber Physical Systems
Drepturi de autor
© © All Rights Reserved
Formate disponibile
DOC, PDF, TXT sau citiți online pe Scribd
Partajați acest document
Partajați sau inserați document
Vi se pare util acest document?
Este necorespunzător acest conținut?
Raportați acest documentTo Get any Project for CSE, IT ECE, EEE Contact Me @ 09666155510, 09849539085 or mail us - ieeefinalsemprojects@gmail.com-Visit Our Website: www.finalyearprojects.org
Drepturi de autor:
© All Rights Reserved
Formate disponibile
Descărcați ca DOC, PDF, TXT sau citiți online pe Scribd
0 evaluări0% au considerat acest document util (0 voturi)
12 vizualizări5 paginiIEEE 2014 JAVA PARALLEL DISTRIBUTION PROJECT Behavior Rule Specification-Based Intrusion Detection For Safety Critical Medical Cyber Physical Systems
Încărcat de
2014PARALLELSYSTEMSTo Get any Project for CSE, IT ECE, EEE Contact Me @ 09666155510, 09849539085 or mail us - ieeefinalsemprojects@gmail.com-Visit Our Website: www.finalyearprojects.org
Drepturi de autor:
© All Rights Reserved
Formate disponibile
Descărcați ca DOC, PDF, TXT sau citiți online pe Scribd
Sunteți pe pagina 1din 5
Behavior Rule Specifcation-based Intrusion
Detection for Safety Critical Medical Cyber
Physical Systems
Abstract:
We propose and analyze a behavior-rule specification-based technique for
intrusion detection of medical devices embedded in a medical cyber physical system
(MCPS) in which the patients safety is of the utmost importance! We propose a
methodolo"y to transform behavior rules to a state machine# so that a device that is bein"
monitored for its behavior can easily be chec$ed a"ainst the transformed state machine
for deviation from its behavior specification! %sin" vital si"n monitor medical devices as
an e&le' we demonstrate that our intrusion detection technique can effectively trade
false positives off for a hi"h detection probability to cope with more sophisticated and
hidden attac$ers to support ultra safe and secure MCPS applications! Moreover# throu"h a
comparative analysis# we demonstrate that our behavior-rule specification based ()S
technique outperforms two e&istin" anomaly-based techniques for detectin" abnormal
patient behaviors in pervasive healthcare applications!
Algorithm:
IDS techniques:
We demonstrate that our behavior-rule specification based IDS
technique outperforms two existing anomaly-based techniques for detecting
abnormal patient behaviors in pervasive healthcare applications.
Anomaly-based techniques using statistical analysis one studies user
sessions !to detect live intruders"# and the other studies the runtime
behavior of programs !to detect malicious code". We propose semi-
supervised anomaly-based IDS targeted for assisted living environments.
GLOBALSOFT TECHNOLOGIES
IEEE PROJECTS & SOFTWARE DEVELOPMENTS
IEEE FINAL YEAR PROJECTS|IEEE ENGINEERING PROJECTS|IEEE STUDENTS
PROJECTS|IEEE
BULK PROJECTS|BE/BTECH/ME/MTECH/MS/MCA PROJECTS|CSE/IT/ECE/EEE
PROJECTS
CELL: +91 9!9" #9$"% +91 99&&' #"(% +91 9!9" "(9$% +91 9($1!
!$!$1
V)*)+: ,,,-.)/012304546738+*-649 M0)1 +6:)333.)/01*3:546738+*;9:0)1-86:
GLOBALSOFT TECHNOLOGIES
IEEE PROJECTS & SOFTWARE DEVELOPMENTS
IEEE FINAL YEAR PROJECTS|IEEE ENGINEERING PROJECTS|IEEE STUDENTS
PROJECTS|IEEE
BULK PROJECTS|BE/BTECH/ME/MTECH/MS/MCA PROJECTS|CSE/IT/ECE/EEE
PROJECTS
CELL: +91 9!9" #9$"% +91 99&&' #"(% +91 9!9" "(9$% +91 9($1!
!$!$1
V)*)+: ,,,-.)/012304546738+*-649 M0)1 +6:)333.)/01*3:546738+*;9:0)1-86:
$heir design is behavior-based and audits series of events which they call
episodes. $he authors% events are &-tuples comprising sensor ID# start time
and duration.
Key points:
*! live intruders
+! runtime behavior
,! livin" environments
Existing System:
-&istin" wor$ only considered specification-based state machines for intrusion
detection of communication protocol misbehavin" patterns! .efore that not usin" trust
based techniques to avoid delay due to trust a""re"ation and propa"ation to promptly
react to malicious behaviors in safety critical MCPSs!
Proposed System:
We propose a methodolo"y to transform behavior rules to a state machine# so that
a device that is bein" monitored for its behavior can easily be chec$ed a"ainst the
transformed state machine for deviation from its behavior specification! We also
investi"ate the impact of attac$er behaviors on the effectiveness of MCPS intrusion
detection! We demonstrate that our specification based ()S technique can effectively
trade hi"her false positives off for lower false ne"atives to cope with more sophisticated
and hidden attac$ers! We show results for a ran"e of confi"urations to illustrate this trade!
.ecause the $ey motivation in MCPS is safety# our solution is deployed in a
confi"uration yieldin" a hi"h detection rate without compromisin" the false positive
probability! /ur approach is monitorin"-based relyin" on the use of peer devices to
monitor and measure the compliance de"ree of a trustee device connected to the
monitorin" node by the CPS networ$! 0he rules comparin" monitor and trustee
physiolo"y (blood pressure# o&y"en saturation# pulse# respiration and temperature)
e&ceeds protection possible by considerin" devices in isolation!
System architecture
Modules:
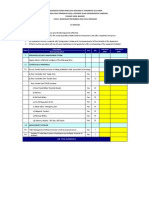
0he system is proposed to have the followin" modules alon" with functional
requirements!
'. $hreat (odel
). Attac*er Archetypes
&. +ehavior ,ules
-. Intrusion detection system
1 !hreat Model
We focus on defeatin" inside attac$ers that violate the inte"rity of the MCPS with the
ob1ective to disable the MCPS functionality! /ur desi"n is also effective a"ainst attac$s such as
subtle manipulations that chan"e medical doses sli"htly to cause lon" term harm to patients or
medical or billin" record e&filtrations which violate privacy! 0here are two distinct sta"es in an
attac$2 before a node is compromised and after a node is compromised! .efore a node is
compromised# the adversary focuses on the tactical "oal of achievin" a foothold on the tar"et
system!
" Attac#er Archetypes
We differentiate two attac$er archetypes2 rec$less# random and opportunistic! 3 rec$less
attac$er performs attac$s whenever it has a chance to impair the MCPS functionality as soon as
possible! 3 random attac$er# on the other hand# performs attac$s only randomly to avoid
detection! (t is thus insidious and hidden with the ob1ective to cripple the MCPS functionality!
We model the attac$er behavior by a random attac$ probability pa! When pa 4 * the attac$er is a
rec$less adversary! 5andom attac$s are typically implemented with on off attac$s in real-world
scenarios# so pa is not a random variable drawn from uniform distribution %(6# *) but rather a
probability that a malicious node is performin" attac$s at any time with this on-off attac$
behavior! 3n opportunistic attac$er is the third archetype! 3n opportunistic attac$er e&ploits
ambient noise modeled by perr (probability of mis-monitorin")to perform attac$s!
$ %eha&ior 'ules
.ehavior rules for a device are specified durin" the desi"n and testin" phase of an MCPS!
/ur intrusion detection protocol ta$es a set of behavior rules for a device as input and detects if a
devices behavior deviates from the e&pected behavior specified by the set of behavior rules!
Since the intrusion detection activity is performed in the bac$"round# it allows behavior rules to
be chan"ed if incomplete or imprecise specifications are discovered durin" the operational phase
Without disruptin" the MCPS operation! /ur ()S desi"n for the reference MCPS model relies on
0he use of li"htwei"ht specification-based behavior rules for each sensor or actuator medical
device!
( Intrusion detection system
(ntrusion detection system (()S) desi"n for cyber physical systems (CPSs) has attracted
considerable because of the dire consequence of CPS failure! (n this paper# we consider
specification rather than si"nature-based detection to deal with un$nown attac$er patterns! We
consider specification rather than anomaly based techniques to avoid usin" resource constrained
Sensors or actuators in an MCPS for profilin" anomaly patterns (e!"!# throu"h learnin") and to
avoid hi"h false positives! We consider specification rather than trust based techniques to avoid
delay due to trust a""re"ation and propa"ation to promptly react to malicious behaviors in Safety
critical MCPSs!
So)t*are 'equirements:
0echnolo"ies 2 3sp !7et and C8!7et
)atabase 2 MS-S9: Server +66;<+66=
()- 2 >isual Studio +66=
+ard*are 'equirements:
Processor 2 Pentium (>
53M 2 *?.
S-ar putea să vă placă și
- The Yellow House: A Memoir (2019 National Book Award Winner)De la EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Evaluare: 4 din 5 stele4/5 (98)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceDe la EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceEvaluare: 4 din 5 stele4/5 (895)
- IEEE 2014 JAVA/.NET IMAGE PROCESSING PROJECT Variational Exemplar-Based Image ColorizationDocument4 paginiIEEE 2014 JAVA/.NET IMAGE PROCESSING PROJECT Variational Exemplar-Based Image Colorization2014SECURECOMPUTINGÎncă nu există evaluări
- IEEE 2014 .NET IMAGE PROCESSING PROJECT Efficient Homomorphic Encryption On Integer Vectors and Its ApplicationsDocument4 paginiIEEE 2014 .NET IMAGE PROCESSING PROJECT Efficient Homomorphic Encryption On Integer Vectors and Its Applications2014PARALLELSYSTEMSÎncă nu există evaluări
- IEEE 2014 .NET IMAGE PROCESSING PROJECT A New Iterative Triclass Thresholding Technique in Image SegmentationDocument6 paginiIEEE 2014 .NET IMAGE PROCESSING PROJECT A New Iterative Triclass Thresholding Technique in Image Segmentation2014PARALLELSYSTEMSÎncă nu există evaluări
- IEEE 2014 .NET IMAGE PROCESSING PROJECT Photometric Stereo Using Sparse Bayesian Regression For General Diffuse SurfacesDocument6 paginiIEEE 2014 .NET IMAGE PROCESSING PROJECT Photometric Stereo Using Sparse Bayesian Regression For General Diffuse Surfaces2014PARALLELSYSTEMSÎncă nu există evaluări
- IEEE 2014 .NET PARALLEL DISTRIBUTION PROJECT A K-Main Routes Approach To Spatial Network Activity SummarizationDocument4 paginiIEEE 2014 .NET PARALLEL DISTRIBUTION PROJECT A K-Main Routes Approach To Spatial Network Activity Summarization2014PARALLELSYSTEMSÎncă nu există evaluări
- 2014 IEEE .NET CLOUD COMPUTING PROJECT Towards Differential Query Services in Cost-Efficient CloudsDocument5 pagini2014 IEEE .NET CLOUD COMPUTING PROJECT Towards Differential Query Services in Cost-Efficient CloudsIEEESTUDENTPROJECTSÎncă nu există evaluări
- IEEE 2014 .NET PARALLEL DISTRIBUTION PROJECT A Dynamic QoS-Aware Logistics Service Composition Algorithm Based On SocialDocument3 paginiIEEE 2014 .NET PARALLEL DISTRIBUTION PROJECT A Dynamic QoS-Aware Logistics Service Composition Algorithm Based On Social2014PARALLELSYSTEMSÎncă nu există evaluări
- IEEE 2014 JAVA/.NET NETWORK SECURITY PROJECT Shared Authority Based Privacy-Preserving Authentication Protocol in Cloud ComputingDocument10 paginiIEEE 2014 JAVA/.NET NETWORK SECURITY PROJECT Shared Authority Based Privacy-Preserving Authentication Protocol in Cloud Computing2014SECURECOMPUTINGÎncă nu există evaluări
- IEEE 2014 JAVA PARALLEL DISTRIBUTION PROJECT Distributed Throughput Maximization in Wireless Networks Via Random Power AllocationDocument4 paginiIEEE 2014 JAVA PARALLEL DISTRIBUTION PROJECT Distributed Throughput Maximization in Wireless Networks Via Random Power Allocation2014PARALLELSYSTEMSÎncă nu există evaluări
- IEEE 2014 JAVA PARALLEL DISTRIBUTION PROJECT Exploiting Service Similarity For Privacy in Location Based Search QueriesDocument8 paginiIEEE 2014 JAVA PARALLEL DISTRIBUTION PROJECT Exploiting Service Similarity For Privacy in Location Based Search Queries2014PARALLELSYSTEMSÎncă nu există evaluări
- IEEE 2014 JAVA/DOTNET NETWORK SECURITY PROJECT A Two-Stage Deanonymization Attack Against Anonymized Social NetworksDocument6 paginiIEEE 2014 JAVA/DOTNET NETWORK SECURITY PROJECT A Two-Stage Deanonymization Attack Against Anonymized Social Networks2014NETWORKINGÎncă nu există evaluări
- IEEE 2014 JAVA PARALLEL DISTRIBUTION PROJECT A System For Denial-Of-Service Attack Detection Based OnMultivariate Correlation AnalysisDocument6 paginiIEEE 2014 JAVA PARALLEL DISTRIBUTION PROJECT A System For Denial-Of-Service Attack Detection Based OnMultivariate Correlation Analysis2014PARALLELSYSTEMSÎncă nu există evaluări
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeDe la EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeEvaluare: 4 din 5 stele4/5 (5794)
- The Little Book of Hygge: Danish Secrets to Happy LivingDe la EverandThe Little Book of Hygge: Danish Secrets to Happy LivingEvaluare: 3.5 din 5 stele3.5/5 (399)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaDe la EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaEvaluare: 4.5 din 5 stele4.5/5 (266)
- Shoe Dog: A Memoir by the Creator of NikeDe la EverandShoe Dog: A Memoir by the Creator of NikeEvaluare: 4.5 din 5 stele4.5/5 (537)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureDe la EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureEvaluare: 4.5 din 5 stele4.5/5 (474)
- Never Split the Difference: Negotiating As If Your Life Depended On ItDe la EverandNever Split the Difference: Negotiating As If Your Life Depended On ItEvaluare: 4.5 din 5 stele4.5/5 (838)
- Grit: The Power of Passion and PerseveranceDe la EverandGrit: The Power of Passion and PerseveranceEvaluare: 4 din 5 stele4/5 (588)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryDe la EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryEvaluare: 3.5 din 5 stele3.5/5 (231)
- The Emperor of All Maladies: A Biography of CancerDe la EverandThe Emperor of All Maladies: A Biography of CancerEvaluare: 4.5 din 5 stele4.5/5 (271)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyDe la EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyEvaluare: 3.5 din 5 stele3.5/5 (2259)
- On Fire: The (Burning) Case for a Green New DealDe la EverandOn Fire: The (Burning) Case for a Green New DealEvaluare: 4 din 5 stele4/5 (73)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersDe la EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersEvaluare: 4.5 din 5 stele4.5/5 (344)
- Team of Rivals: The Political Genius of Abraham LincolnDe la EverandTeam of Rivals: The Political Genius of Abraham LincolnEvaluare: 4.5 din 5 stele4.5/5 (234)
- The Unwinding: An Inner History of the New AmericaDe la EverandThe Unwinding: An Inner History of the New AmericaEvaluare: 4 din 5 stele4/5 (45)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreDe la EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreEvaluare: 4 din 5 stele4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)De la EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Evaluare: 4.5 din 5 stele4.5/5 (121)
- Her Body and Other Parties: StoriesDe la EverandHer Body and Other Parties: StoriesEvaluare: 4 din 5 stele4/5 (821)
- Creating A Company Culture For Security Design Documentation Name Institution DateDocument5 paginiCreating A Company Culture For Security Design Documentation Name Institution DateChris Jackson'sÎncă nu există evaluări
- Exercise 1: Snort As An IDS: Kali Linux VM For This LabDocument18 paginiExercise 1: Snort As An IDS: Kali Linux VM For This LabMalluÎncă nu există evaluări
- National Security Council Secretariat: Cyber Security Audit Baseline RequirementsDocument19 paginiNational Security Council Secretariat: Cyber Security Audit Baseline Requirementsdhir.ankurÎncă nu există evaluări
- Cisco Certified Support Technician Cybersecurit Workbook D2Document18 paginiCisco Certified Support Technician Cybersecurit Workbook D2rotef90360Încă nu există evaluări
- 1 - Unit 5 - Assignment Brief 1Document3 pagini1 - Unit 5 - Assignment Brief 1Tran Quang Thang FGW DNÎncă nu există evaluări
- Deloitte - KPI and Measuring SecurityDocument28 paginiDeloitte - KPI and Measuring Securitythe syah89% (18)
- Question Bank PDFDocument10 paginiQuestion Bank PDFjayaprasanna123Încă nu există evaluări
- PrashantSahdevParab - Database Monitoring Analyst - Pune - MphasisDocument3 paginiPrashantSahdevParab - Database Monitoring Analyst - Pune - MphasisSoniya chaudharyÎncă nu există evaluări
- BOQDocument16 paginiBOQOsama M. DaraghmehÎncă nu există evaluări
- Smart Care Service Pre-Installation ChecklistDocument8 paginiSmart Care Service Pre-Installation ChecklistFabian Bottega MendozaÎncă nu există evaluări
- Quiz 5 - CS690 A1 Network ..Document7 paginiQuiz 5 - CS690 A1 Network ..Nishant KawaÎncă nu există evaluări
- ASA FirepowersDocument30 paginiASA FirepowersAndrea Celeste Gonzàlez FigueroaÎncă nu există evaluări
- Learner Resource ICTNWK509Document56 paginiLearner Resource ICTNWK509manpreet kaurÎncă nu există evaluări
- Authors BookDocument180 paginiAuthors BookMaria DialÎncă nu există evaluări
- Insident ResponseDocument8 paginiInsident Responseraghuram medapatiÎncă nu există evaluări
- Incident Response Plan (Template)Document17 paginiIncident Response Plan (Template)Gerardo RGLÎncă nu există evaluări
- Wireless Communication: V.Manikandan, R.RavichandranDocument16 paginiWireless Communication: V.Manikandan, R.Ravichandranmanis57Încă nu există evaluări
- Question Bank For (ICS) : Information and Cyber SecurityDocument29 paginiQuestion Bank For (ICS) : Information and Cyber Securitysagar kardileÎncă nu există evaluări
- Kaspersky CiberSecurityDocument14 paginiKaspersky CiberSecuritylegajiusÎncă nu există evaluări
- What Is Network SecurityDocument28 paginiWhat Is Network SecurityTamannaÎncă nu există evaluări
- Diamond PDFDocument61 paginiDiamond PDFsjmpakÎncă nu există evaluări
- Docs Securityonion Net en 2.3Document373 paginiDocs Securityonion Net en 2.3Abdul Rahaman GaffarÎncă nu există evaluări
- RSA BattleCardDocument6 paginiRSA BattleCardRKSÎncă nu există evaluări
- Research Proposal: Topic: Information Security in Banking SectorDocument42 paginiResearch Proposal: Topic: Information Security in Banking SectorGorav BhallaÎncă nu există evaluări
- Bluesocket Controller (BSC) Setup and Administration GuideDocument376 paginiBluesocket Controller (BSC) Setup and Administration GuideBeatriz RomanÎncă nu există evaluări
- 10 Coolest Jobs in CybersecurityDocument1 pagină10 Coolest Jobs in CybersecurityHajaÎncă nu există evaluări
- Comnputer and Network Security NEW 3350704Document8 paginiComnputer and Network Security NEW 3350704shyjuother9773Încă nu există evaluări
- A Study On NSL-KDD Dataset PDFDocument7 paginiA Study On NSL-KDD Dataset PDFAnonymous N22tyB6UNÎncă nu există evaluări
- CEH Definition Flashcards PDFDocument9 paginiCEH Definition Flashcards PDFmedtrachiÎncă nu există evaluări
- Detecting IoT Botnet Attacks Using Machine Learning MethodsDocument7 paginiDetecting IoT Botnet Attacks Using Machine Learning MethodscmgarciasilvaÎncă nu există evaluări