Documente Academic
Documente Profesional
Documente Cultură
Misfortune Cookie Tr069 Protection Whitepaper
Încărcat de
simul99Drepturi de autor
Formate disponibile
Partajați acest document
Partajați sau inserați document
Vi se pare util acest document?
Este necorespunzător acest conținut?
Raportați acest documentDrepturi de autor:
Formate disponibile
Misfortune Cookie Tr069 Protection Whitepaper
Încărcat de
simul99Drepturi de autor:
Formate disponibile
Check Point Protecting Against Misfortune Cookie and TR-069 ACS Vulnerabilities |
White Paper
CHECK POINT
PROTECTING AGAINST
MISFORTUNE COOKIE AND
TR-069 ACS VULNERABILITIES
SEVERITY OF RESIDENTIAL GATEWAY
(SOHO ROUTER) COMPROMISE
The security of residential gateways is notoriously weak. Between devices running
with default admin credentials, old versions of software and zero -to-little patch
management in place, the home router security landscape is woefully behind
the times.
When an attacker controls a home router, they can affect traffic in subtle ways .
Details for two separate gateway-based campaigns were brought to the public
eye this year with similar characteristics:
Massive amount of home routers compromised
Any user traffic destined for banking or financial sites was redirected to
malicious servers under the attackers control or redirected through SSL
proxies where the security of the traffic was compromised via an
SSL man-in-the-middle attack.
Collections of compromised home routers could be used for large-scale DoS attacks,
spam campaigns, attack launch pads and covert eavesdropping on traffic.
MISFORTUNE COOKIE VULNERABILITY
Researchers from Check Points Malware and Vulnerability Research Group have
uncovered a critical vulnerability present on millions of SOHO router and gateway
devices. The vulnerability is in an embedded web server installed on millions of
customer gateway devices. This web server happens to be used by ISPs to manage
Customer Premise Equipment (CPE) via CPE WAN Management Protocol (CWMP).
An attacker can use this vulnerability to remotely control CPE gateway devices such
as DSL/Cable/FiOS routers with administrative privileges.
The Misfortune Cookie vulnerability is exploitable due to an error within the HTTP
cookie management mechanism present in the affected software, allowing an attacker
to determine the fortune of a request by manipulating cookies. Attackers can send
specially crafted HTTP cookies that exploit the vulnerability to corrupt memory and
alter the application state. This, in effect, can trick the attacked web server to treat
the current session with administrative privileges.
2014 Check Point Software Technologies Ltd. All rights reserved. [Protected] Non -confidential content
December 17, 2014
Check Point Protecting Against Misfortune Cookie and TR-069 ACS Vulnerabilities |
White Paper
Research detected at least 12 million readily exploitable devices globally on the
Internet. There are no public exploits for Misfortune Cookie but it is possible certain
attackers have already discovered and exploited the vulnerability in private, remaining
undetected for extensive periods of time. Because of a unique combination of severity,
ease of exploitability, and the sheer amount of vulnerable devices, we believe this
is a very important issue for users and ISPs.
The affected software is the embedded web server RomPager from AllegroSoft.
Internet-wide scans suggest RomPager is likely the most popular web server
software in the world with respect to number of available endpoints. RomPager
is typically embedded in the firmware released with the device. This specific
vulnerability was introduced to the code base in 2002. Vulnerable versions
are susceptible to Misfortune Cookie on either port 80 or any CWMP port.
AllegroSoft released a fixed version to address the Misfortune Cookie vulnerability in
2005. However, the patch propagation process is complicated. Due to the way chip
manufacturers bundle applications in Software Development Kits for certain chipsets
and the way application updates are integrated in router firmware, many devices ship
with the vulnerable version in place. Additionally, in order to patch the 12 million
vulnerable devices in the wild, manufacturers will have to obtain an updated version
of RomPager, integrate it into their current firmware for all vulnerable lines and
models, release the firmware version, and then users and/or Internet Service
Providers will have to install the update on every vulnerable device in the world.
This update may be easier for ISPs by bulk installing via the TR-069 protocol.
Check Point actively contributes to the security community by making independent
research progress and working towards better public security awareness
and education.
WHAT IS TR-069/CWMP?
TR-069 is a document or specification created by The Broadband Forum that defines
the CPE WAN Management Protocol (CWMP). The Broadband Forum consists of
key players in the broadband market that define standards and work towards
common goals.
CWMP is designed to be a secure architecture in which Customer Premise Equipment
(CPE) devices initiate connections to an Auto-Configuration Server (ACS), and accept
RPC commands via the XML based Simple Object Access Protocol (SOAP). RPC
commands can consist of:
Set/Get Configuration Parameters
Receive updates
Upload/Download files
Reboot device
Perform a Factory Reset
2014 Check Point Software Technologies Ltd. All rights reserved. [Protected] Non -confidential content
December 17, 2014
Check Point Protecting Against Misfortune Cookie and TR-069 ACS Vulnerabilities |
White Paper
CWMP is proving useful, more ISPs are adopting it, and more devices are shipping
with it enabled, such as VOIP phones, webcams and set-top cable boxes/DVRs. The
default TCP port for CWMP is 7547; research shows this is currently the second most
active server port listening on the Internet next to TCP port 80.
ACS VULNERABILITIES
The ability to control one ACS, in-turn, allows an attacker to control many thousands
of home routers.
Earlier this year Check Points Malware and Vulnerability Research Group discovered
a number of vulnerabilities in several ACS implementations. The vu lnerability types
are quite severe consisting of Remote Code Execution, authentication bypass, SQL
injection, Denial of Service, and arbitrary file creation. This research highlighted the
severity of ACS compromise and alerted ISPs to implement defense -in-depth around
their TR-069 deployments.
PROTECTIONS AND MITIGATIONS
Check Points ThreatCloud Operations Center has released the following
IPS Signatures that can be used to prevent Misfortune Cookie and ACS attacks.
Internet Service Providers can set CPE devices to notify when configuration
parameters change via the ACS. Parameters that change are reported using the
TR-069 Inform RPC. Monitoring for unexpected configuration changes can help
providers detect compromised devices. Changes in devices administrator credentials,
DNS server, ACS server, and other important settings can indicate compromise.
ACS and CPE logs should be monitored for abnormal characteristics.
Network architecture can be examined and, if not already, security devices and
controls can be deployed to restrict and monitor TR-069/CWMP traffic. Firewall
policies should block this traffic from unexpected IP ranges. Preferably IPS would
also be deployed inline to prevent attacks. In the event that a providers network is
not architected to allow monitoring for TR-069/CWMP attacks real-time, traffic can
be passively monitored for added visibility and attack detection.
A surprising amount of providers use unencrypted communications for CPE
management. TR-069 provisioning and connection requests can implement strict
TLS (SSL) where the TR-069 client implementation properly validates server
certificates to improve overall security.
Disabling additional services on the ACS machine will reduce attack surface.
For example running DNS servers and web servers on the ACS increases risk
and provides additional points of compromise.
The version and patch level of ACS and CWMP software should be reviewed with
hardware vendors to determine if devices or servers are vulnerable. If so work
with vendors to deploy server patches and update customer device firmware where
appropriate. A patch update policy where patches are regularly applied and reviewed
will reduce exposure to vulnerabilities.
2014 Check Point Software Technologies Ltd. All rights reserved. [Protected] Non -confidential content
December 17, 2014
Check Point Protecting Against Misfortune Cookie and TR-069 ACS Vulnerabilities |
White Paper
A few additional steps can be taken by Internet Service Providers to mitigate risk:
If possible, use a custom URL path and port for the ACS URL, to avoid
automatic detection by opportunistic attackers.
Using a non-standard port for CWMP can reduce simple scans from
discovering CWMP devices automatically and disrupt opportunistic
attacker exploitation.
Reconfiguring CWMP networks to use private non-routable internet
addresses will prevent off-network attacks.
Blocking CWMP port access from outside the network will also prevent
off-network attacks.
Enable authentication for all requests, including connection requests.
If the ACS solution allows it, use a distinct username/password pair
for each provisioned device, assigned at the initial provisioning session.
Disable user tampering of TR-069 client connection settings.
Enable alarms for any ACS authentication failure.
Enable rate blocking for API calls if available.
IPS PROTECTION DETAILS
CONTACT US
Protection Name
CVE
Protection Description
Release Date
TR-069 Auto
Configuration Servers
Multiple Vulnerabilities
CVE-2014-2840
CVE-2014-4956
CVE-2014-4916
CVE-2014-4917
CVE-2014-4918
CVE-2014-4957
28 July 2014
RomPager Authorization
Buffer Overflow Denial
of Service
CVE-2014-9223
The TR-069 protocol allows remote
management of end-user broadband
devices. Several vulnerabilities have
been detected in certain TR-069
server implementations that could
allow a remote attacker to obtain
administrative access to the servers or
execute arbitrary code on them.
A buffer overflow vulnerability exist in
RomPager Web Server. A remote
attacker could exploit this vulnerability
by sending a crafted request to the
vulnerable server causing a denial of
service.
RomPager
Authentication Security
Bypass
MisfortuneCookie
CVE-2014-9222
An authentication bypass vulnerability
exists in RomPager Server. The
vulnerability is due to an insecure
design in the RomPager Server.
Remote attacker could exploit this
vulnerability to access the RomPager
web-server under administrator
privileges.
21 December
2014
21 December
2014
Worldwide Headquarters | 5 HaSolelim Street, Tel Aviv 67897, Israel | Tel: 972-3-753-4555 | Fax: 972-3-624-1100 | Email: info@checkpoint.com
U.S. Headquarters | 959 Skyway Road, Suite 300, San Carlos, CA 94070 | Tel: 800-429-4391; 650-628-2000 | Fax: 650-654-4233 | www.checkpoint.com
2014 Check Point Software Technologies Ltd. All rights reserved. [Protected] Non -confidential content
December 17, 2014
S-ar putea să vă placă și
- Network Defense 14gDocument36 paginiNetwork Defense 14gBolaji WilliamsÎncă nu există evaluări
- Requirement Gathering For IT Infrastructure - 1Document11 paginiRequirement Gathering For IT Infrastructure - 1ASN PrasadÎncă nu există evaluări
- Geothermal Project TimelinesDocument10 paginiGeothermal Project TimelinesAldwin EncarnacionÎncă nu există evaluări
- Pharma MarketingDocument55 paginiPharma MarketingArpan KoradiyaÎncă nu există evaluări
- 20 - Web Application Security Testing Using Burp Suite (Compatibility Mode) PDFDocument35 pagini20 - Web Application Security Testing Using Burp Suite (Compatibility Mode) PDFsamsÎncă nu există evaluări
- SPC & MSA PresentationDocument84 paginiSPC & MSA PresentationRaajha Munibathiran100% (3)
- 23 - Battery Sizing DischargeDocument19 pagini23 - Battery Sizing Dischargechanchai T100% (4)
- 09hakin9 09 2012 EN EbookDocument49 pagini09hakin9 09 2012 EN EbookcristianorpjÎncă nu există evaluări
- Chapter 5e ch05 HallDocument9 paginiChapter 5e ch05 HallGlorden Mae Ibañez SalandananÎncă nu există evaluări
- Seven Steps To Effectively Defend Industrial Control SystemsDocument7 paginiSeven Steps To Effectively Defend Industrial Control SystemsGerardo F. GonzalezÎncă nu există evaluări
- FIREWALLDocument26 paginiFIREWALLmanish 2003Încă nu există evaluări
- CSS Unit-5Document28 paginiCSS Unit-5Vivek TripathiÎncă nu există evaluări
- Module 10: LAN Security Concepts: Instructor MaterialsDocument41 paginiModule 10: LAN Security Concepts: Instructor MaterialsKim Andre MacaraegÎncă nu există evaluări
- Unit5 Part1Document21 paginiUnit5 Part1Deepak YaduvanshiÎncă nu există evaluări
- Role of VPN IN Network Security: Presented byDocument11 paginiRole of VPN IN Network Security: Presented byvenkateshmukharjiÎncă nu există evaluări
- Module 10: LAN Security Concepts: Instructor MaterialsDocument37 paginiModule 10: LAN Security Concepts: Instructor MaterialsShakir AmzarÎncă nu există evaluări
- SRWE Module 10Document26 paginiSRWE Module 10حمدان ناصر الغيثيÎncă nu există evaluări
- Endpoint Security (Ch10)Document15 paginiEndpoint Security (Ch10)Areej OmarÎncă nu există evaluări
- 2006032-VP0206 FirewallsDocument6 pagini2006032-VP0206 Firewallsladyjay3710Încă nu există evaluări
- Firewall Checklist - SampleDocument7 paginiFirewall Checklist - SampleAnil ChiplunkarÎncă nu există evaluări
- Task 1 - SecurityDocument25 paginiTask 1 - SecurityMuheet zahidÎncă nu există evaluări
- Dev ProcessDocument4 paginiDev ProcessAdrian OnuÎncă nu există evaluări
- Module 10: LAN Security Concepts: Switching, Routing and Wireless Essentials v7.0 (SRWE)Document38 paginiModule 10: LAN Security Concepts: Switching, Routing and Wireless Essentials v7.0 (SRWE)random studentÎncă nu există evaluări
- Telco Signalling Security AssessmentDocument12 paginiTelco Signalling Security AssessmentThái Duy HòaÎncă nu există evaluări
- AA21-131A Darkside Ransomware Best Practices For Preventing Business Dis..Document6 paginiAA21-131A Darkside Ransomware Best Practices For Preventing Business Dis..Eni TestÎncă nu există evaluări
- Module 10: LAN Security Concepts: Instructor MaterialsDocument32 paginiModule 10: LAN Security Concepts: Instructor MaterialsKhairul AzrinÎncă nu există evaluări
- ProSec CyberHardeningGuide USDocument6 paginiProSec CyberHardeningGuide USderickoti45Încă nu există evaluări
- Paper Wk6Document8 paginiPaper Wk6hmplaceÎncă nu există evaluări
- Banking System Have ApplicationsDocument6 paginiBanking System Have ApplicationsRahul SurapaneniÎncă nu există evaluări
- Hardening Network DevicesDocument3 paginiHardening Network DevicesJaime BlancoÎncă nu există evaluări
- Modern Malware For Dummies Chapter-5 & 6: Submitted byDocument20 paginiModern Malware For Dummies Chapter-5 & 6: Submitted byAnkita AgarwalÎncă nu există evaluări
- Mitigating Security Risks: at The Network'S EdgeDocument16 paginiMitigating Security Risks: at The Network'S EdgeHéctor AndradeÎncă nu există evaluări
- Network Automation DevilDocument15 paginiNetwork Automation Devilrkjadhav1453Încă nu există evaluări
- Vaprogram ExampleDocument37 paginiVaprogram ExampleayalewtesfawÎncă nu există evaluări
- CCNAv 7Document134 paginiCCNAv 7Jose ScottÎncă nu există evaluări
- Application, Data and Host SecurityDocument24 paginiApplication, Data and Host SecurityKari AlfaroÎncă nu există evaluări
- Firewalls Are Used To Protect Both Home and Corporate NetworksDocument4 paginiFirewalls Are Used To Protect Both Home and Corporate NetworksAnkita SoniÎncă nu există evaluări
- Data Security in Cloud ComputingDocument22 paginiData Security in Cloud ComputingPiyush MittalÎncă nu există evaluări
- ITSY 2401 - Firewalls and Network Security - Network Security Plan ProjectDocument7 paginiITSY 2401 - Firewalls and Network Security - Network Security Plan ProjectKyle LaPatoÎncă nu există evaluări
- Ics-Cert Advisory: Icsa-10-214-01 - Vxworks VulnerabilitiesDocument5 paginiIcs-Cert Advisory: Icsa-10-214-01 - Vxworks VulnerabilitiesosisynÎncă nu există evaluări
- AA21-131A DarkSide RansomwareDocument6 paginiAA21-131A DarkSide RansomwareNelson AbreuÎncă nu există evaluări
- Assingment Week 3Document8 paginiAssingment Week 3Ghulam Abbas AbbasÎncă nu există evaluări
- Web Application Vulnerability AreasDocument12 paginiWeb Application Vulnerability AreasMichael CorselloÎncă nu există evaluări
- Cloud Application and Network Security 5-4-2022Document7 paginiCloud Application and Network Security 5-4-2022hoangtruc.ptitÎncă nu există evaluări
- Cyber SecurityDocument14 paginiCyber Securitygodsonbenny123Încă nu există evaluări
- Welcome To International Journal of Engineering Research and Development (IJERD)Document5 paginiWelcome To International Journal of Engineering Research and Development (IJERD)IJERDÎncă nu există evaluări
- Conficker - Note To CustomersDocument3 paginiConficker - Note To CustomersPrakash VivekÎncă nu există evaluări
- "Firewall": A Seminar Report OnDocument15 pagini"Firewall": A Seminar Report OnkumarÎncă nu există evaluări
- "Firewall": A Seminar Report OnDocument15 pagini"Firewall": A Seminar Report OnkumarÎncă nu există evaluări
- 8thsem 3rd DefenceDocument7 pagini8thsem 3rd DefenceAyush SinghalÎncă nu există evaluări
- "Firewall": A Seminar Report OnDocument15 pagini"Firewall": A Seminar Report OnkumarÎncă nu există evaluări
- Secure Wireless Firewall Integration: Role of The FirewallDocument54 paginiSecure Wireless Firewall Integration: Role of The FirewallFlavio MirandaÎncă nu există evaluări
- Mikrotik - Tr069Document26 paginiMikrotik - Tr069TKJ StembaseÎncă nu există evaluări
- 3/25/2020 Muthukumar.A / ASP/ ECE / CNS / UNIT V / Firewall Design Principles 1Document9 pagini3/25/2020 Muthukumar.A / ASP/ ECE / CNS / UNIT V / Firewall Design Principles 1Harseerat SidhuÎncă nu există evaluări
- Resumen TR-069 y Diferencias SNMP PDFDocument26 paginiResumen TR-069 y Diferencias SNMP PDFManolo Ferreira HerreraÎncă nu există evaluări
- Best Practices For Wireless Network SecurityDocument7 paginiBest Practices For Wireless Network SecuritymatÎncă nu există evaluări
- Cloud Computing: Hottest Buzzword in Information TechnologyDocument19 paginiCloud Computing: Hottest Buzzword in Information TechnologySatish KumarÎncă nu există evaluări
- E-Business Systems UG2 Revision Topics 2012/13: 1. Quality of E-ServicesDocument7 paginiE-Business Systems UG2 Revision Topics 2012/13: 1. Quality of E-ServicesRob ChapmanÎncă nu există evaluări
- 2022 Network SecurityFinal AssessmentDocument6 pagini2022 Network SecurityFinal AssessmentMd. Ziaul Haque ShiponÎncă nu există evaluări
- SOPHOS NERC Response - May2015 (Total Tech) PDFDocument6 paginiSOPHOS NERC Response - May2015 (Total Tech) PDFLonnie RossÎncă nu există evaluări
- Protecting The OrganizationDocument16 paginiProtecting The OrganizationSalman ShahÎncă nu există evaluări
- Welcome To International Journal of Engineering Research and Development (IJERD)Document7 paginiWelcome To International Journal of Engineering Research and Development (IJERD)IJERDÎncă nu există evaluări
- Best Practices For WirelessDocument3 paginiBest Practices For WirelesskenyrÎncă nu există evaluări
- C) 256 Bits AESDocument4 paginiC) 256 Bits AESsyafiq rossleyÎncă nu există evaluări
- Best Practices Using The Master 35361Document12 paginiBest Practices Using The Master 35361simul99Încă nu există evaluări
- OpenScape VoiceDocument8 paginiOpenScape Voicesimul99Încă nu există evaluări
- UC Software Admin Guide v4 0 1Document616 paginiUC Software Admin Guide v4 0 1simul99Încă nu există evaluări
- OpenScape Voice V8Document12 paginiOpenScape Voice V8simul99Încă nu există evaluări
- Misfortune Cookie Suspected VulnerableDocument5 paginiMisfortune Cookie Suspected VulnerableRexhastaÎncă nu există evaluări
- Iperf ManualDocument13 paginiIperf ManualrtecnologiaÎncă nu există evaluări
- HUAWEI UMTS Datacard Modem at Command Interface Specification - V2.3Document107 paginiHUAWEI UMTS Datacard Modem at Command Interface Specification - V2.3simul99Încă nu există evaluări
- GSM UMTS 3GPP Numbering Cross Reference: Select by Specification Number View Full List (Almost 2000 Items)Document164 paginiGSM UMTS 3GPP Numbering Cross Reference: Select by Specification Number View Full List (Almost 2000 Items)simul99Încă nu există evaluări
- Modems3g ZTE USB Modem Config ProcedureDocument1 paginăModems3g ZTE USB Modem Config Proceduresimul99Încă nu există evaluări
- At Commands TCP-IP Stack P1DDocument17 paginiAt Commands TCP-IP Stack P1Dsimul99Încă nu există evaluări
- GT47 Technical DescriptionDocument43 paginiGT47 Technical Descriptionsimul99Încă nu există evaluări
- At CMD GPRSDocument38 paginiAt CMD GPRSusgraha100% (1)
- Unit - 1: (B) Difference Between Thermodynamcis and Heat TransferDocument66 paginiUnit - 1: (B) Difference Between Thermodynamcis and Heat TransferSayyadh Rahamath Baba100% (1)
- Advance Java Sem 5Document18 paginiAdvance Java Sem 5Gunjan Pratim JadhavÎncă nu există evaluări
- Scania TruckAndBus 2023Document403 paginiScania TruckAndBus 2023Piotr ZiąbkowskiÎncă nu există evaluări
- Digital Data, Digital SignalDocument8 paginiDigital Data, Digital SignalBastomi Adi NugrohoÎncă nu există evaluări
- Turnitin Originality ReportDocument47 paginiTurnitin Originality ReportStillward Laud Mark-MillsÎncă nu există evaluări
- 28L059 PDFDocument9 pagini28L059 PDFone_blanche6175Încă nu există evaluări
- Mohit Soni ReportDocument104 paginiMohit Soni ReportMohitÎncă nu există evaluări
- Improvements in Offshore Pipeline Cathodic ProtectionDocument6 paginiImprovements in Offshore Pipeline Cathodic ProtectionEddy Norman Benites DelgadoÎncă nu există evaluări
- AC 29 2cincorporatedDocument1.109 paginiAC 29 2cincorporatedzzudhirÎncă nu există evaluări
- Dbms Lab Manual-2013Document27 paginiDbms Lab Manual-2013Arham JainÎncă nu există evaluări
- PPG en-US P162.OutputDocument4 paginiPPG en-US P162.OutputChemical EngineerÎncă nu există evaluări
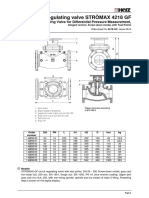
- Circuit Regulating Valve STRÖMAX 4218 GFDocument14 paginiCircuit Regulating Valve STRÖMAX 4218 GFMario Mô Ri AÎncă nu există evaluări
- Colphenebswh 1816Document2 paginiColphenebswh 1816vinoth kumar SanthanamÎncă nu există evaluări
- 020 - MDCC For Sluice GatesDocument1 pagină020 - MDCC For Sluice GatesYOGESH PHALKEÎncă nu există evaluări
- Course Add Drop Form For Ug Course 1718T2 PDFDocument1 paginăCourse Add Drop Form For Ug Course 1718T2 PDFArtyomÎncă nu există evaluări
- A Project Report On DMRCDocument22 paginiA Project Report On DMRCRahul Mehrotra100% (1)
- Ms500se PDFDocument5 paginiMs500se PDFEduardo NazarioÎncă nu există evaluări
- PAC4200 Product GuideDocument4 paginiPAC4200 Product GuideHugo Alberto Malespin SolisÎncă nu există evaluări
- Theta76PrinterUnit EL V1-0Document58 paginiTheta76PrinterUnit EL V1-0MarcelinoMorillasCecilia100% (1)
- Pelland Pumptrack2018Document60 paginiPelland Pumptrack2018ksnakaÎncă nu există evaluări
- Na Edifact Desadv SpecificationsDocument17 paginiNa Edifact Desadv Specificationsrajendra2505Încă nu există evaluări
- Schaeffler Kolloquium 2010 13 enDocument7 paginiSchaeffler Kolloquium 2010 13 enMehdi AlizadehÎncă nu există evaluări
- Syllabus New PDFDocument107 paginiSyllabus New PDFmassÎncă nu există evaluări
- Swot Analysis of PTCLDocument5 paginiSwot Analysis of PTCLM Aqeel Akhtar JajjaÎncă nu există evaluări
- Unit 9 Computer NetworksDocument8 paginiUnit 9 Computer NetworksDaniel BellÎncă nu există evaluări