Documente Academic
Documente Profesional
Documente Cultură
JMF (Java Media Framework) and VIC (Video Conferencing Tool)
Încărcat de
Gagan Deep SinghTitlu original
Drepturi de autor
Formate disponibile
Partajați acest document
Partajați sau inserați document
Vi se pare util acest document?
Este necorespunzător acest conținut?
Raportați acest documentDrepturi de autor:
Formate disponibile
JMF (Java Media Framework) and VIC (Video Conferencing Tool)
Încărcat de
Gagan Deep SinghDrepturi de autor:
Formate disponibile
Design and Testing of two secure Video Conferencing applications based on
JMF (Java Media Framework) and VIC (Video Conferencing Tool)
L. Mengual1, J. Bobadilla2, R. Caballero 1, G. Hernndez1
DLSIIS, Facultad de Informtica, U.P.M., Madrid, Spain
1
{lmengual, rcaballero ghernandez }@fi.upm.es
2
{jbobi}@eui.upm.es
Abstract
We present two secure real-time video conferencing
solutions with JPEG coding using a cipher engine based
on the Blowfish algorithm. One of these solutions is
developed from Java Media Framework (JMF) [1]. In
this case, our solution consists of encrypting frames
coded with JPEG that are later encapsulated in packets
of the RTP protocol [2] (Real Time Transport Protocol).
Our cipher system is based on the Blowfish algorithm [3]
of the Cryptix [4] open source cryptographic software
library.
Another solution is developed from VIC (Video
Conferencing Tool)[5]. In this case, our solution consists
of encrypting the UDP packets that contain the JPEG
coded frames incorporated in RTP packets. In this paper
we analyse the solutions proposed and test the
implementations developed in different data networks
(LAN/ WLAN, Frame Relay).
Key words: Secure video conferencing systems, JPEG
Codec, Blowfish algorithm, LAN/WLAN
1. Introduction
Usage of the Internet for on-line banking, shopping
and many others applications like Video Conferencing
systems is growing exponentially. Some of these
applications involve the transfer of sensitive information
such as credit card details. Hence to support these type of
networked transactions a number of security techniques
have been developed. [7,..11].
At the present, the problem of the security in the
communications over Internet has extended to real-time
communications. The necessity to protect multimedia data
distributed over Internet makes it necessary to encrypt the
audio/video flows transported on Internet. The aim is that
the resulting flow allows its later reproduction in real
time. It is therefore very important to choose a specific
place to incorporate the cipher engine in the code of our
multimedia application, as well as to choose an
encryption algorithm fast enough to allow real time
communications.
Real time packet transmission should resolve the
difficulties inherent in packet networks [12,.. ,16], among
which we have: the delay and loss of packets, the
unordered delivery, the appearance of duplicated packets,
etc. Real Time Protocol (RTP) [2] is a protocol based on
IP networks that provides end-to-end network delivery
services for the transmission of the real-time data. RTP is
network and transport-protocol independent, thought it is
often used over UDP. RTP enables you identify the type
of data being transmitted, determines what order the
packets of data should be presented in, and resolve the
problem of synchronize media streams from different
sources. While RTP does not provide any mechanism to
ensure timely delivery or provide other quality of services
guarantees, it is augmented by the protocol RTCP (RTP
Control Protocol) [2]. It provides control and
identification mechanisms for RTP transmissions and
enables you to monitor the quality of the data distribution.
Over the past few years, a collaborative effort in the
network research community has produced a suite of
tools and different systems for multimedia video
conferencing over the Internet like JMF [1], VIC [17],
Marratech [18], Isabel [19], GnomeMeeting[20], Access
Grid [21], MPEG-4IP[22] and others.
We have chosen some of the most well known tools,
such as JMF and VIC, and we have created real time
applications with symmetric-key encryption. In this paper
we present the conclusions reached in a comparative
study.
Java Media Framework (JMF) is a versatile
Application
Programming
Interface
(API)
for
incorporating time-based media into Java applications
and therefore portable and independent of the underlying
hardware. Any data that change meaningfully with
respect to time can be characterized as time-based media.
Such media data can be obtained from a variety of
sources, such as cameras, microphones etc. To send or
receive a live media broadcast or conduct a Video
This work is supported partially by Science and Technology Ministry of Spain under the projects: A Multi-Agent System Architecture for the
automatic and dynamic Implementation of security protocols (TIC2001-3376) and Open System of Multimedia Digital Presentation in Real Time
(TIC2000-1734-C03-02)
Conference over Internet or Intranet, you need to be able
to receive and transmit media streams in real time. JMF
uses RTP for receiving and transmitting media streams
across the network. This way, JMF can: play various
multimedia files in a Java applet or application (The
formats supported include
AVI, MIDI, MPEG,
QuickTime, and WAV); play streaming media from the
Internet; capture audio and video with your microphone
and video camera; process time-based media and change
the content-type format; transmit audio and video in realtime on the Internet; broadcast live radio or television
programs.
VIC (Video Conferencing Tool) is a real-time video
conferencing application over the Internet developed by
the Network Research Group at the Lawrence Berkeley
National Laboratory in collaboration with the University
of California, Berkeley. VIC was designed with a flexible
and extensible architecture to support heterogeneous
environments and configurations. For example, in high
bandwidth settings, multi-megabit full-motion JPEG
streams can be sourced using hardware assisted
compression, while in low bandwidth environments like
the Internet, aggressive low bit-rate coding can be carried
out in software.
VIC is based on the Draft Internet Standard Real-time
Transport Protocol (RTP) developed by the IETF
Audio/Video Transport working group. RTP is an
application-level protocol implemented entirely within
VIC. You need no special system enhancements to run
RTP. Although VIC can be run point-to-point using
standard unicast IP addresses, it is primarily intended as a
multiparty conferencing application. To make use of the
conferencing capabilities, your system must support IP
Multicast, and ideally, your network should be connected
to the IP Multicast Backbone (MBone).
2. Solutions Presented
In this paper we compare two solutions for real time
video transmission with symmetric-key encryption. The
Blowfish algorithm is used in both solutions. The two
evaluation contexts are: an owner application developed
using the API in Java of Java Media Framework, and the
VIC, a video conferencing application developed by the
Lawrence Berkeley National Laboratory.
In the video conferencing with JMF solution we opted
for the implementation of a secure JPEG Codec using the
Codec dynamic registration services provided by the JMF
API. This means that in this case (see Fig. 1) we designed
a JPEG Codec in which the RTP packets have a payload
that corresponds to the encrypted video frames using a
cipher engine based on Blowfish using the Cryptix library
[4].
RTP PACKET
IP Header
20 Oct.
UDP Header
8 Oct.
RTP Header
12 Oct.
RTP PAYLOAD
ENCRYPTED
Figure 1: Incorporation of encrypting in a video
conferencing application implemented with JMF
In the VIC solution we have incorporated the Blowfish
algorithm from [6] in the part of the code in charge of
constructing the RTP packets and incorporating them in
the UDP datagrams. The solution used in this case (see
Fig. 2) is therefore not related to the chosen Codec. The
most important implementation work involved here was
to locate the classes in charge of transporting the RTP
packets that contain the video frames, and within them, to
encrypt the UDP datagrams generated.
RTP PACKET
IP Header
20 O ct.
UDP Header
8 Oct.
RTP Header
12 O ct.
RTP PAYLOAD
ENCRYPTED
Figure 2: Incorporation of encrypting in the VIC
application
3. Video Conference Application Structure
based on JMF
The incorporation of security services to a video
conference application, that has been developed with
JMF, implies to encrypt the video/audio data that are
transported by the network. This circumstance outlines
several problems to solve: a first problem resides in the
election of an encryption algorithm fast enough to
guarantee the real time communications. Another
problem resides in choosing the proper location of the
cipher engine inside the JMF architecture of classes.
Finally, a last problem and, thats not trivial, is the
distribution of the session key among the system users.
Regarding the previous problems our alternative
consist in, firstly, selecting the Blowfish algorithm as the
responsible cipher engine. Blowfish is a symmetric block
cipher of 64 bit block and uses a variable-length key,
from 32 bits to 448 bits, fast enough to make the
communication in real time possible.
We decide to include the cipher engine in the classes
that implement the JPEG video Codec selected. In
particular, the location was the classes of the JMF
architecture denominated "...packetizer/...depacketizer.
The .packetizer class is an implementation of the
BasicCodec interface inside the architecture of classes
and interfaces of JMF. This class encapsulates the JPEG
data in RTP packets to be sent through the network. The
class "...depacketizer" is invoked in the receiver. This
class receives RTP packets in a buffer and depacketizes
them to obtain a complete frame in JPEG format. Our
solution consists on encrypt the video data before its
incorporation to the RTP packets (see Fig. 3).
JPEG FRAMES ENCRYPTED
IN RTP PACKETS
VIDEO
JPEG FRAMES
Native
Encoder
JPEG FRAMES
Packetizer
DePacketizer
BLOWFISH
CIPHER ENGINE
BLOWFISH
CIPHER ENGINE
VIDEO
Native
Decoder
SECURE JPEG CODEC
Figure 3. Secure JPEG CODEC in JMF
The basic structure of our application is composed of
the SecureCustomTrans class (see Fig. 4). This class,
from its method main, obtains the session key in a secure
way implementing a security protocol; next it carries out
the dynamic registration in the architecture JMF of the
secure video JPEG Codec that we have implemented
through registerCustomPayload method. Once
registered the new Codecs, the start method of the
SecureCustomTrans class invokes the methods and
functions of the JMF API to establish the RTP session.
public class SecureCustomTrans {
static Format myJPEGFormat
static Format myGSMFormat
private byte[] key;
--------------static boolean registerCustomPayload () {.....}
private String createProcessors() { ...}
private String createTransmitter() { ...}
..................................................................................................
public static void main(String [] args) {
java.security.Security.addProvider(new cryptix.provider.Cryptix());
security_protocol sp=new security_protocol ();
Key = sp. Get_Key ;
----------------registerCustomPayload();
SecureCustomTrans sct = new SecureCustomTrans (..);
String result =sct.start(); }//main
}//SecureCustomTrans
Figure 4. SecureCustomTrans class pseudocode
This way the SecureCustomTrans class creates two
new
classes:
CreateProcessor
and
CreateTransmiter. The first one creates what in JMF is
called proccesor that is the entity in charge of managing
the input signal, to choose the appropriate Codec and to
return the encoded data. The second class takes charge
basically of encapsulating the data that receives from the
processor in RTP packets.
The "...jpegencrypted.Packetizer" object (see Fig. 5)
was created from the SecureCustomTrans class by the
registerCustomPayload method by means of a
constructor that receives as parameter a session key
distributed by the security protocol. In this constructor the
CipherEngineCodec object is created. This will be in
charge of encrypting video data with Blowfish algorithm.
The kernel of the Codec jpegencrypted.Packetizer is
the process method that carries out the processing of
the input signal through the inbuf object and it returns
the encryption data through the outBuf object.
public class Packetizer extends BasicCodec {
static final JPEGFormat fJPEG = new JPEGFormat(); static String
JPEG_ENCRYPTED = "jpegencrypted/rtp"; private MotorEncriptacionCODEC
private byte[] mykey;
public Packetizer (byte[] key) {
inputFormats = new VideoFormat[] {new VideoFormat(VideoFormat.JPEG)};
outputFormats = new VideoFormat[] {new
VideoFormat(JPEG_ENCRYPTED)};
mykey=key;
MyCipherEngine =new CipherEngineCODEC(); } // Packetizer
public synchronized int process(Buffer inBuffer, Buffer outBuffer){
...
byte [] inData = (byte[]) inBuffer.getData();
System.arraycopy(inData,offset + inBuffer.getOffset(),sincif,0,copyLength);
byte[] cifin = MyCipherEngine.BlowfishCipher(sincif, mykey);
} // Packetizer
Figure 5. ...jpeg.packetizer class pseudocode
4. Video Conference Application based on
VIC
One of the problems that arose when including
security in our video conferencing application based on
VIC was the way to add the security. We considered
several solutions depending on where the cipher engine
was included. One possible solution would be to encrypt
at frame level, i.e. every time a frame is obtained from the
data source, the source should be encrypted by the
application. Another possible solution would be to design
a Codec in such a way that it automatically encrypts all
the information that goes through it. This Codec will be
used to encrypt and decrypt the information depending on
whether it is used by the transmitter or the receiver. The
last solution to this problem, which was the one that was
finally chosen, is to add the security at socket level, i.e. to
detect the socket that is being used for the transmission
and reception of the data of the corresponding session and
to encrypt the data just before it is sent by the transmitter
and decrypt it as soon as it is received by the receiver.
To achieve this objective we used a Blowfish cipher
engine using the source code [6] as the starting point,
which was fast enough to allow it to work in real time.
The code that implements and makes the data encryption
possible, using the Blowfish API functions, is
incorporated in the Network class methods. The
Network class (see Fig. 6) incorporates methods that
implement the transfer of information between entities
through the Windows Sockets interface and it is part of the
group of classes invoked from the TclObject class. We
have added the symmetrical cipher engine to these
methods so that before sending any data it is encrypted
with the session key, and as soon as any data is received it
is decrypted with the same key.
TclObject
TclObject
Transmiter
Network
SesionManager
IPNetwork
VideoSesionManager
Figure 6. Class Structure in VIC
5. Performance Study
A wide range of tests were carried out to prove the
features of the implementations made. The tests consisted
of evaluating the performance of real time video
transmission with JPEG code in the two implementations
developed, VIC and JMF. The analysis of the
transmission was carried out by evaluating the
incorporation of a Blowfish cipher engine and by using
different Network technologies (LAN 10 -100 Mbps,
Frame Relay 2 Mbps and WLAN 11 Mbps). Finally, the
possible influence of abrupt movements in front of the
camera was studied.
We must point out that in both evaluation
environments a fixed RTP packet size of 960 Bytes was
used in the VIC environment and 1024 Bytes in the JMF
environment. The relative comparison of features was
also carried out in the Windows 2000 operating system
with a Pentium II processor at 450 MHz with 512 Mbytes
on the transmitter and a Pentium II processor at 400 MHz
256 Mbytes on the video receiver.
5.1 Results in JMF
5.1.1 Cost of frame transmission protocol. Different
data networks have been evaluated: LAN (Local Area
Networks) 10 -100 Mbps, Frame Relay 2 Mbps and
WLAN (Wireless Local Area Networks) 11 Mbps. At
JPEG quality 0.2, 14 fps (frames per second) are reached
in LAN at 10/100 Mbps or FR at 2 Mbps, whilst only 12
fps are reached in WLAN (see Fig. 7.a). With a JPEG
quality of 0.7, 11 fps are reached in LAN at 10/100 Mbps
or FR at 2 Mbps, whilst only 8 are reached in WLAN (see
Fig. 7.a).
5.1.2 Relationship between the number of frames and
the quality without encryption. The set of tests carried
out covers a range of JPEG qualities from 0.2 to 0.7,
obtaining a clear conclusion from the reduction in the
number of frames from a range of 14-12 fps with quality
0.2 to a range of 11-8 fps when the quality is increased.
By increasing the quality the JPEG algorithm is
compressed to lesser extent and the JPEG frames are
larger.
5.1.3 Relationship between the number of frames, the
quality and Bits per second without encryption. In
direct association with the previous conclusion we can
point out the following: At low quality, we have
mentioned that more small frames are transmitted due to
the strong compression. Therefore, in this situation less
bandwidth is required, oscillating between approximately
450 Kbps (WLAN)-500 Kbps (LAN/FR) with quality 0.2
and almost 1250 (WLAN)-1450 Kbps (LAN/FR) with
quality 0.7.
5.1.4 Cost of real time encryption. With quality 0.2 we
can see that the average rate of fps reached is around 12
fps in LAN/FR whilst in WLAN only 11 fps are reached
(see Fig. 7.a). With quality 0.7 we can see that the
average rate of fps reached is around 7 fps in LAN/FR and
WLAN only 6 fps are reached (see Fig. 7.a).
From the analysis of the results we can deduce that the
cost of encryption at low quality (0.2) is approximately 12 fps: From 14 fps sent without encryption to 12 fps
encrypted in LAN/FR. And from 12 fps sent without
encryption to 11 fps encrypted in WLAN. By increasing
the quality to 0.7 the cost of using real time encryption is
also increased, reaching a difference of 4 fps in LAN/FR:
From 11 fps sent without encryption to 7 fps encrypted.
And of 2 fps in WLAN: From 8 fps sent without
encryption to 6 fps encrypted.
5.2 Comparison of Results JMF-VIC
In relation to the curves without encryption, the
behaviour of VIC and JMF is similar as regards the fps
sent. This way, this value increases to 12 fps at medium
quality (0,5) with LAN/FR and 10 fps in WLAN, for
example (see Fig. 7). The difference is in the bandwidth
used from 700 Kbps (WLAN)-750 Kbps (LAN/FR) in VIC
and 780 Kbps (WLAN)-900 Kbps (LAN/FR) in JMF.
The number of packets required also varies
proportionally: from 90 pps (WLAN)-100 pps (LAN/FR)
in VIC and 110 pps (WLAN)-130 pps (LAN/FR) in JMF.
The explanation could be found in the optimisation of the
JPEG Codec of VIC as opposed to JMF and the slight
difference in the size of the RTP packet used in VIC and
JMF.
Secure JMF (a)
13
0.2
fps
11
0.2
0.3
0.5
0.
0.3
9
0.6
0.5
0.7
0.6
500
750
with encryption
1000
1250
without encryption
Secure VIC (b)
13
0.2
fps
11
0.3
0.4
0.5
0.5
0.6
0.7
9
7
5
250
500
750
6. Conclusions
0.7
5
250
3,5 times faster in C/C++ tests than in Java tests (3,03
using a 400-Mhz. CPU and 3,98 using a 1-GHz. CPU).
Both solutions show a similar performance without the
use of the cipher engine; however, by using a JPEG
quality of more than 0.3, the secure JMF version produces
an average of 2 frames per second less than the VIC
version. This is the price we have to pay in order to use
JMF, a portable, flexible and reliable java-based
framework where the new codecs and digital drivers are
automatically maintained.
1000
1250
Mbps
Figure 7. JMF-VIC Comparative test results. WLAN,
400-MHz, CPU
Nevertheless, the most significant differences are
centred on the results obtained using Blowfish cipher
engine. Therefore, using VIC the average number of
frames sent with medium quality is 10 fps in LAN/FR and
9 fps in WLAN (see Fig. 7.b). In JMF on the other hand,
we obtain 8 fps in LAN/FR and 7 fps in WLAN (see Fig.
7.a). The relative difference is therefore 2 fps. Using
encryption the use of bandwidth oscillates between 650
Kbps (WLAN) and 700 Kbps (LAN/FR) in VIC and 550
Kbps (WLAN) and 650 Kbps (LAN/FR) in JMF. A clear
difference according to the lower number of frames sent
by JMF.
VIC and our JMF secure videoconferencing system
have been tested using a wireless network (WLAN
802.11b) and a 400-MHz CPU. Fig. 7 shows the test
results using different JPEG qualities (y-axis: fps
achieved, x-axis: necessary bandwidth). We can observe
that the encryption algorithm processing overload affects
JMF more than VIC. This is mainly because Java does
not run as fast as C/C++; the Blowfish cipher engine runs
In this work we have presented two practical real time
video conferencing solutions using the Blowfish cipher
engine. In the first solution, using JMF we obtain a
flexible solution, which, through the dynamic registration
of Codecs, allows users to choose the security services in
the JPEG Video transmission. In this solution we encrypt
the content of the RTP packets. The use of the Java
language allows versatility in the video broadcast
platform. In the second solution, we propose a cipher
engine that has no relation with the Codec in the VIC
video conferencing environment. In this solution, the
content of the UDP packets that contain the video
conferencing frames is encrypted. The cipher engine used
developed in C/C++ has been used from [6].
The comparison of results reveals that both solutions
present a similar rate of fps without the use of the cipher
engine, however there is a greater use of bandwidth in the
case of JMF. When using the Blowfish cipher engine the
differences are more significant as an average difference
of 3 fps is produced in the transmission of JPEG
encrypted video. These differences can attributed, firstly,
to the difference in the efficiency of the cipher engine in
Java as opposed to in C/C++, as we have already
mentioned, and, secondly, to the efficiency of the JPEG
Codec in one version or the other.
7. References
1. Java Media Framework (JMF):
http://java.sun.com/products/java-media/jmf/
2. Schulzrinne, H, Casner, S., Frederick, R., Jacobson, V.
(Audio-video Transport working group) RTP: A Transport
Protocol for Real-Time Applications, RFC 1889, January
1996.
3. Schneier B. Description of a New Variable-length Key, 64Bit Block Cipher (Blowfish)., Cambridge Security
Workshop Proceedings Springer-Verlag, 1994.
4. Cryptix: open-source cryptographic software libraries:
http://www.cryptix.org/
5. McCanne, S., and Jacobson, V. VIC: A Flexible
Framework for Packet Video. ACM Multimedia 95 Electronic Proceedings November 5-9, 1995 San Francisco.
6. Blowfish open source code:
http://www.counterpane.com/blowfish-download.html
7. Deswarte, Y.; Powell, D. "Internet security: an intrusiontolerance approach" Proceedings of the IEEE, Volume 94,
Issue 2, Feb. 2006 Page(s):432 - 441
8. Chang, S.S., Chiang, M.S. "An e-intelligence approach to ecommerce intrusion detection". IEEE International
Conference on Granular Computing, 2005. Volume 2, 25-27
July 2005. Page(s):401 - 404. Vol. 2.
9. Kemmerer, R.A. , Vigna, G. "Hi-DRA: intrusion detection
for Internet security". Proceedings of the IEEE, Volume 93,
Issue 10, Oct. 2005. Page(s):1848 1857.
10. Ylitalo, J., Salmela, P., Tschofenig, H."SPINAT: Integrating
IPsec into Overlay Routing"First International Conference
on Security and Privacy for Emerging Areas in
Communications Networks, 2005. SecureComm 2005. 0509 Sept. 2005 Page(s):315 - 326.
11. Schwab, S.; Wilson, B.; Thomas, R. "Methodologies and
Metrics for the Testing and Analysis of Distributed Denial
of Service Attacks and Defenses". IEEE Military
Communications Conference, 2005. MILCOM 2005. 17-20
Oct. 2005 Page(s):1 7.
12. Mehra, P., De Vleeschouwer, C., Zakhor, A. "Receiverdriven bandwidth sharing for TCP and its application to
video streaming". IEEE Transactions on Multimedia,
Volume 7, Issue 4, Aug. 2005 Page(s):740 752.
13. Qian Zhang, Quji Guo, Qiang Ni, Wenwu Zhu, Ya-Qin
Zhang "Sender-adaptive and receiver-driven layered
multicast for scalable video over the Internet". IEEE
Transactions on Circuits and Systems for Video
Technology, Volume 15, Issue 4, April 2005 Page(s):482 495.
14. Ahmed, T., Mehaoua, A., Boutaba, R., Iraqi, Y. "Adaptive
packet video streaming over IP networks: a cross-layer
approach". IEEE Journal on Selected Areas in
Communications Volume 23, Issue 2, Feb 2005 Page(s):385
- 401.
15 Yan, J., Katrinis, K., May, M.; Plattner, B. "Media- and
TCP-Friendly Congestion. Control for Scalable Video
Streams". IEEE Transactions on Multimedia, Volume 8,
Issue 2, April 2006 Page(s):196 - 206.
16. Chou, P.A., Miao, Z. "Rate-Distortion Optimized Streaming
of Packetized Media". IEEE Transactions on Multimedia,
Volume 8, Issue 2, April 2006 Page(s):390 404.
17. Video
Conference
Tool
(VIC):
mice.cs.ucl.ac.uk/multimedia/software/vic/
18 Marratech: http://www.marratech.com
19. ISABEL: http://isabel.dit.upm.es/
20. GnomeMeeting: http://www.gnomemeeting.org/
http://www-
21. Access Grid: http://www.accessgrid.org/
22. MPEG-4IP: http://www.mpeg4ip.net/
S-ar putea să vă placă și
- The UFO Book Encyclopedia of The Extraterrestrial (PDFDrive)Document756 paginiThe UFO Book Encyclopedia of The Extraterrestrial (PDFDrive)James Lee Fallin100% (2)
- Popular Mechanics 2010-06Document171 paginiPopular Mechanics 2010-06BookshebooksÎncă nu există evaluări
- MI 276 Rev B - Conversion of Turbochargers For Opposite Engine RotationDocument15 paginiMI 276 Rev B - Conversion of Turbochargers For Opposite Engine RotationJesse BarnettÎncă nu există evaluări
- Schematic Diagram of Ip Camera With EthernetDocument18 paginiSchematic Diagram of Ip Camera With EthernetnguyenminhtuanengineÎncă nu există evaluări
- IPTV (Internet Protocol Television) MAINDocument27 paginiIPTV (Internet Protocol Television) MAINSnehal Ingole100% (1)
- Language Culture and ThoughtDocument24 paginiLanguage Culture and ThoughtLý Hiển NhiênÎncă nu există evaluări
- Video Compression Using H.264Document27 paginiVideo Compression Using H.264Er Shreyas ShahÎncă nu există evaluări
- Simviki: A Tool For The Simulation of Secure Video Communication SystemsDocument6 paginiSimviki: A Tool For The Simulation of Secure Video Communication SystemsSujith KattappanaÎncă nu există evaluări
- Telecom Interactive 97Document22 paginiTelecom Interactive 97abhi_protocol123Încă nu există evaluări
- Scalable Internet Video Using MPEG-4: Hayder Radha, Yingwei Chen, Kavitha Parthasarathy, Robert CohenDocument32 paginiScalable Internet Video Using MPEG-4: Hayder Radha, Yingwei Chen, Kavitha Parthasarathy, Robert CohenVaqar HyderÎncă nu există evaluări
- Performance Evaluation of MPEG-4 Video Transmission Over IP-NetworksDocument12 paginiPerformance Evaluation of MPEG-4 Video Transmission Over IP-NetworksAlexander DeckerÎncă nu există evaluări
- Ip-Distributed Computer-Aided Video-Surveillance System: S Redureau'Document5 paginiIp-Distributed Computer-Aided Video-Surveillance System: S Redureau'Payal AnandÎncă nu există evaluări
- Video Transmission in 3G TelephonyDocument6 paginiVideo Transmission in 3G TelephonygattupallikÎncă nu există evaluări
- Altera Quality of Service in Home NetworkingDocument4 paginiAltera Quality of Service in Home Networkingkn65238859Încă nu există evaluări
- Video Streaming: What Is A Video?Document15 paginiVideo Streaming: What Is A Video?saurabh_singhalÎncă nu există evaluări
- Digital Video Transcoding: Jun Xin, Chia-Wen Lin, Ming-Ting SunDocument14 paginiDigital Video Transcoding: Jun Xin, Chia-Wen Lin, Ming-Ting SundarwinÎncă nu există evaluări
- Iccgi 2014 7 10 10092Document6 paginiIccgi 2014 7 10 10092Jahaan AhamadÎncă nu există evaluări
- MPEG-4 and H.264 Video Prediction MethodsDocument8 paginiMPEG-4 and H.264 Video Prediction MethodsThành PhạmÎncă nu există evaluări
- Qoe-Vs: A Cross-Layer Qoe-Aware Video Streaming Platform Using Software-Defined RadioDocument7 paginiQoe-Vs: A Cross-Layer Qoe-Aware Video Streaming Platform Using Software-Defined RadioFabian MolinengoÎncă nu există evaluări
- Literature Review: Keywords: Video Encryption, Distributed and ParallelDocument7 paginiLiterature Review: Keywords: Video Encryption, Distributed and ParallelijcsnÎncă nu există evaluări
- Video Coding and A Mobile Augmented Reality ApproachDocument10 paginiVideo Coding and A Mobile Augmented Reality Approachvfotop1Încă nu există evaluări
- A Position Paper For The W3C "Web and TV" WorkshopDocument5 paginiA Position Paper For The W3C "Web and TV" WorkshopDonÎncă nu există evaluări
- Mo Hinh Suy HaoDocument6 paginiMo Hinh Suy HaoDung Viet NgoÎncă nu există evaluări
- Evalvid ImageDocument23 paginiEvalvid ImageSamaWhiteÎncă nu există evaluări
- Research Article: Digital Video Encryption Algorithms Based On Correlation-Preserving PermutationsDocument15 paginiResearch Article: Digital Video Encryption Algorithms Based On Correlation-Preserving PermutationsChatradi HarikaÎncă nu există evaluări
- Digital Video Encryption Algorithms Based On Correlation-Preserving PermutationsDocument24 paginiDigital Video Encryption Algorithms Based On Correlation-Preserving PermutationsKrishnamoorthy KumarÎncă nu există evaluări
- Ee 549 Undergraduate Project Ii: "Voip To PSTN Converter"Document30 paginiEe 549 Undergraduate Project Ii: "Voip To PSTN Converter"Obaweya SeyiÎncă nu există evaluări
- Learning Guide - How Does VoIP WorkDocument18 paginiLearning Guide - How Does VoIP Workshubham_cool1996Încă nu există evaluări
- The Design and Implementation of A Networked Real-Time Video Surveillance System Based On FPGADocument5 paginiThe Design and Implementation of A Networked Real-Time Video Surveillance System Based On FPGAKamesh SelvamÎncă nu există evaluări
- Article 1Document5 paginiArticle 1hdnsÎncă nu există evaluări
- Multi-protocol Traffic Generation and Measurement Tool (D-ITGDocument2 paginiMulti-protocol Traffic Generation and Measurement Tool (D-ITGThành VõÎncă nu există evaluări
- Applications For IP Video Surveillance Over The ITRI MTWAL: Rui-Yen Chang, Hsin-Ta Chiao, Chin-Lung Lee, Yu-Cheng ChenDocument6 paginiApplications For IP Video Surveillance Over The ITRI MTWAL: Rui-Yen Chang, Hsin-Ta Chiao, Chin-Lung Lee, Yu-Cheng ChenWalter CañazacaÎncă nu există evaluări
- Mpeg4 Kod Iptv: "Kontekst Gdje Očekujem Mnogo Od Realnog Novca Će BitiDocument6 paginiMpeg4 Kod Iptv: "Kontekst Gdje Očekujem Mnogo Od Realnog Novca Će BitiemsadiÎncă nu există evaluări
- AIoT - Group ProjectDocument7 paginiAIoT - Group Projectlorel17157Încă nu există evaluări
- EEET1089 - Preliminary 1Document3 paginiEEET1089 - Preliminary 1Vivek ArvindÎncă nu există evaluări
- SSRN Id3701416Document6 paginiSSRN Id3701416Ishtiaque AhmedÎncă nu există evaluări
- LCS1113 PaperDocument4 paginiLCS1113 PaperHạ Thu Phạm NgọcÎncă nu există evaluări
- Real-Time and Rate-Distortion Optimized Video Streaming With TCPDocument15 paginiReal-Time and Rate-Distortion Optimized Video Streaming With TCPDiaa MustafaÎncă nu există evaluări
- Digital Video Transcoding: Proceedings of The IEEE February 2005Document15 paginiDigital Video Transcoding: Proceedings of The IEEE February 2005María Gabriela Danieri AndaraÎncă nu există evaluări
- Maximizing MPEG-4 Video Quality over the InternetDocument5 paginiMaximizing MPEG-4 Video Quality over the Internetavin29Încă nu există evaluări
- Synopsis WebRTCDocument6 paginiSynopsis WebRTCPratik KanthiÎncă nu există evaluări
- Embedded Real Time Video Monitoring System Using Arm: Kavitha Mamindla, Dr.V.Padmaja, CH - NagadeepaDocument5 paginiEmbedded Real Time Video Monitoring System Using Arm: Kavitha Mamindla, Dr.V.Padmaja, CH - Nagadeepabrao89Încă nu există evaluări
- Remote Media Immersion System Delivers Immersive Digital ExperiencesDocument17 paginiRemote Media Immersion System Delivers Immersive Digital ExperiencesswapnaaaaÎncă nu există evaluări
- Set-Top Box Software Architectures For Digital Video BroadcastDocument6 paginiSet-Top Box Software Architectures For Digital Video BroadcastDimitri PetrovÎncă nu există evaluări
- The Mobile Video Surveillance System Based On Wireless LAN: Chunhua Wang Zheng Mao Yu Zhang Hailong LuoDocument7 paginiThe Mobile Video Surveillance System Based On Wireless LAN: Chunhua Wang Zheng Mao Yu Zhang Hailong LuoWERMERMÎncă nu există evaluări
- Raptor Codes For Reliable Download Delivery in Wireless Broadcast SystemsDocument7 paginiRaptor Codes For Reliable Download Delivery in Wireless Broadcast SystemsgotabÎncă nu există evaluări
- Fast Encryption Algorithm For Streaming Video Over Wireless NetworksDocument4 paginiFast Encryption Algorithm For Streaming Video Over Wireless NetworksInternational Journal of computational Engineering research (IJCER)Încă nu există evaluări
- A Cloud-Assisted P2P Video Streaming Architecture For Scalable Video CodingDocument6 paginiA Cloud-Assisted P2P Video Streaming Architecture For Scalable Video CodingSDIWCÎncă nu există evaluări
- VOIP Introduction and Challenges by Shawky MenisyDocument5 paginiVOIP Introduction and Challenges by Shawky MenisyShawky MenesyÎncă nu există evaluări
- Video Transcoding: An Overview of Various Techniques and Research IssuesDocument12 paginiVideo Transcoding: An Overview of Various Techniques and Research Issuessilver starÎncă nu există evaluări
- Novel Video Steganography Algorithm Based On Secret Sharing and Error-Correcting Code For H.264/AVCDocument12 paginiNovel Video Steganography Algorithm Based On Secret Sharing and Error-Correcting Code For H.264/AVCmadhupavi_2007Încă nu există evaluări
- 20IO International Conference On Computer Application and System ModelingDocument19 pagini20IO International Conference On Computer Application and System ModelingAnand KumarÎncă nu există evaluări
- An Introduction To Multimedia Processors: Stephan SossauDocument11 paginiAn Introduction To Multimedia Processors: Stephan SossauHyder LutfyÎncă nu există evaluări
- A Technical Survey On Secure Video TransmissionDocument6 paginiA Technical Survey On Secure Video TransmissionIJSTEÎncă nu există evaluări
- Desmo Uliers 2012Document12 paginiDesmo Uliers 2012Anonymous UI7JawqÎncă nu există evaluări
- Improving Content Delivery in A Video-on-Demand Over IP EnvironmentDocument8 paginiImproving Content Delivery in A Video-on-Demand Over IP EnvironmentrabiniluÎncă nu există evaluări
- Moving Picture Experts Group (MPEG)Document8 paginiMoving Picture Experts Group (MPEG)Firdaus SikumbangÎncă nu există evaluări
- Java Multimedia StudioDocument14 paginiJava Multimedia StudioFranco MinucciÎncă nu există evaluări
- Technologies For Multimedia and Video Surveillance ConvergenceDocument13 paginiTechnologies For Multimedia and Video Surveillance ConvergenceSenapathi TejaÎncă nu există evaluări
- DTCPDocument11 paginiDTCPmkrasanÎncă nu există evaluări
- FEB-14-19-Implementation and Porting of Light Weight TCPIP For Embedded Web Server - EWSDocument6 paginiFEB-14-19-Implementation and Porting of Light Weight TCPIP For Embedded Web Server - EWSKumar Goud.KÎncă nu există evaluări
- Advanced Multimedia Service Provisioning Based On Efficient Interoperability of Adaptive Streaming Protocol and High Efficient Video CodingDocument12 paginiAdvanced Multimedia Service Provisioning Based On Efficient Interoperability of Adaptive Streaming Protocol and High Efficient Video CodingabdelatifÎncă nu există evaluări
- Dishivam9876mbimph, GOVINDASAMY512022AJOAIR1870Document8 paginiDishivam9876mbimph, GOVINDASAMY512022AJOAIR1870ahmed.haddadÎncă nu există evaluări
- Intermediate C Programming for the PIC Microcontroller: Simplifying Embedded ProgrammingDe la EverandIntermediate C Programming for the PIC Microcontroller: Simplifying Embedded ProgrammingÎncă nu există evaluări
- 857am7.dr. C Abdul Majeed & Haseena Jasmine C KDocument8 pagini857am7.dr. C Abdul Majeed & Haseena Jasmine C KGagan Deep SinghÎncă nu există evaluări
- Java ConferencingDocument9 paginiJava ConferencingSanjesh SinghÎncă nu există evaluări
- HRM-1Document9 paginiHRM-1Gagan Deep SinghÎncă nu există evaluări
- Research on FreemiumsDocument106 paginiResearch on FreemiumsGagan Deep SinghÎncă nu există evaluări
- I Jcs CN 2013030107Document9 paginiI Jcs CN 2013030107Gagan Deep SinghÎncă nu există evaluări
- BJMC 1st Sem Result SummaryDocument200 paginiBJMC 1st Sem Result SummaryGagan Deep SinghÎncă nu există evaluări
- Financial Management Toy World, Inc. Case Analysis Final ReportDocument9 paginiFinancial Management Toy World, Inc. Case Analysis Final ReportGagan Deep SinghÎncă nu există evaluări
- Thesis Final1 PDFDocument55 paginiThesis Final1 PDFGagan Deep SinghÎncă nu există evaluări
- Arbitration ActDocument9 paginiArbitration ActGagan Deep SinghÎncă nu există evaluări
- AdmissionAnnouncement2013 14Document2 paginiAdmissionAnnouncement2013 14Ajeet_1991Încă nu există evaluări
- Secure Video Conferencing For Web Based Security Surveillance SystemDocument55 paginiSecure Video Conferencing For Web Based Security Surveillance SystemGagan Deep SinghÎncă nu există evaluări
- 2 Portfolio Selection in Multipath RoutingDocument7 pagini2 Portfolio Selection in Multipath RoutingGagan Deep SinghÎncă nu există evaluări
- Final Syn1Document11 paginiFinal Syn1Gagan Deep SinghÎncă nu există evaluări
- CPDocument1 paginăCPGagan Deep SinghÎncă nu există evaluări
- Video Conferencing Research for EducationDocument9 paginiVideo Conferencing Research for EducationGagan Deep SinghÎncă nu există evaluări
- Virtual Classroom System SRSDocument22 paginiVirtual Classroom System SRSGagan Deep SinghÎncă nu există evaluări
- PrashadDocument1 paginăPrashadGagan Deep SinghÎncă nu există evaluări
- Time Series DecompositionDocument4 paginiTime Series DecompositionGagan Deep SinghÎncă nu există evaluări
- 8queensproblemusingbacktracking 120903114053 Phpapp01Document51 pagini8queensproblemusingbacktracking 120903114053 Phpapp01Seravana KumarÎncă nu există evaluări
- Mps SyllabusDocument1 paginăMps SyllabusGagan Deep SinghÎncă nu există evaluări
- Java Media Framework PresentationDocument28 paginiJava Media Framework PresentationGagan Deep SinghÎncă nu există evaluări
- Revised Date Sheet (MT-I)Document1 paginăRevised Date Sheet (MT-I)Gagan Deep SinghÎncă nu există evaluări
- Question For DWDM VivaDocument1 paginăQuestion For DWDM VivaGagan Deep SinghÎncă nu există evaluări
- New Microsoft Office Word DocumentDocument4 paginiNew Microsoft Office Word DocumentGagan Deep SinghÎncă nu există evaluări
- Size: - 4inch 6inch, 4 Inch Height 6 InchDocument1 paginăSize: - 4inch 6inch, 4 Inch Height 6 InchGagan Deep SinghÎncă nu există evaluări
- Semester I Max. Theory Internal Lecture Tutorial Practical Exam. Marks Exam. Asst. HoursDocument4 paginiSemester I Max. Theory Internal Lecture Tutorial Practical Exam. Marks Exam. Asst. HoursGagan Deep SinghÎncă nu există evaluări
- Ipconfig AllDocument1 paginăIpconfig AllGagan Deep SinghÎncă nu există evaluări
- Software Engineer Fresher ResumeDocument2 paginiSoftware Engineer Fresher ResumeGagan Deep SinghÎncă nu există evaluări
- Arts CommerceDocument8 paginiArts CommerceNDTVÎncă nu există evaluări
- Lux MeterDocument4 paginiLux MeterNmg KumarÎncă nu există evaluări
- SOP Questionnaire GREDocument4 paginiSOP Questionnaire GREYuvraj GuptaÎncă nu există evaluări
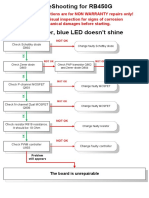
- RB450G Trouble ShootingDocument9 paginiRB450G Trouble Shootingjocimar1000Încă nu există evaluări
- Penomoran Bantex - K64&COMPDocument8 paginiPenomoran Bantex - K64&COMPVigour Rizko MurdyneÎncă nu există evaluări
- AR Adjustments: Details, Setup, Flow, Accounting and API: September 5th, 2008Document5 paginiAR Adjustments: Details, Setup, Flow, Accounting and API: September 5th, 2008John SmithÎncă nu există evaluări
- Manufacturing Processes (ME361) Lecture 13: Instructor: Shantanu BhattacharyaDocument28 paginiManufacturing Processes (ME361) Lecture 13: Instructor: Shantanu BhattacharyaSahil SundaÎncă nu există evaluări
- Develop Network Monitoring System IP Subnet CalculatorDocument23 paginiDevelop Network Monitoring System IP Subnet CalculatorabiramanÎncă nu există evaluări
- Math 101Document3 paginiMath 101Nitish ShahÎncă nu există evaluări
- TCBE - Conversation Skills TemplateDocument10 paginiTCBE - Conversation Skills TemplateAryoma GoswamiÎncă nu există evaluări
- Chemical Engineering Assignment SubmissionDocument10 paginiChemical Engineering Assignment SubmissionFahad KamranÎncă nu există evaluări
- REFLEKSI KASUS PLASENTADocument48 paginiREFLEKSI KASUS PLASENTAImelda AritonangÎncă nu există evaluări
- Comparison of Waste-Water Treatment Using Activated Carbon and Fullers Earth - A Case StudyDocument6 paginiComparison of Waste-Water Treatment Using Activated Carbon and Fullers Earth - A Case StudyDEVESH SINGH100% (1)
- Lolita An Intelligent and Charming Holstein Cow Consumes Only TwoDocument1 paginăLolita An Intelligent and Charming Holstein Cow Consumes Only Twotrilocksp SinghÎncă nu există evaluări
- Managerial Performance Evaluation ProceduresDocument3 paginiManagerial Performance Evaluation Procedures1robcortesÎncă nu există evaluări
- WORK ORDER TITLEDocument2 paginiWORK ORDER TITLEDesign V-Tork ControlsÎncă nu există evaluări
- Campbell Soup Case-StudyDocument3 paginiCampbell Soup Case-StudyraghudeepaÎncă nu există evaluări
- SO CF, Internal Fault Map Class 1A SO CF, Internal Fault Map Class 2A SO CF, External Condition Map Class 1BDocument15 paginiSO CF, Internal Fault Map Class 1A SO CF, Internal Fault Map Class 2A SO CF, External Condition Map Class 1BATMMOBILISÎncă nu există evaluări
- Holacracy FinalDocument24 paginiHolacracy FinalShakil Reddy BhimavarapuÎncă nu există evaluări
- Limits, Fits and Tolerances: Prof. S. S. PandeDocument31 paginiLimits, Fits and Tolerances: Prof. S. S. PandeM PankajÎncă nu există evaluări
- Kuliah 1 - Konservasi GeologiDocument5 paginiKuliah 1 - Konservasi GeologiFerdianÎncă nu există evaluări
- Lab 1 Handout Electrical MachinesDocument23 paginiLab 1 Handout Electrical Machinesvishalsharma08Încă nu există evaluări
- Lecture 6Document16 paginiLecture 6Dina Saad EskandereÎncă nu există evaluări
- Transformer Oil Testing: Dissolved Gas AnalysisDocument18 paginiTransformer Oil Testing: Dissolved Gas AnalysisIkhsan LyÎncă nu există evaluări
- PrEN 12271-10 - Factory Production ControlDocument17 paginiPrEN 12271-10 - Factory Production ControlPedjaÎncă nu există evaluări
- The Eukaryotic Replication Machine: D. Zhang, M. O'DonnellDocument39 paginiThe Eukaryotic Replication Machine: D. Zhang, M. O'DonnellÁgnes TóthÎncă nu există evaluări
- 713 Catalog PagesDocument2 pagini713 Catalog PagesJosé AcostaÎncă nu există evaluări