Documente Academic
Documente Profesional
Documente Cultură
Introduction To Network Security Threats
Încărcat de
iwc2008007Titlu original
Drepturi de autor
Formate disponibile
Partajați acest document
Partajați sau inserați document
Vi se pare util acest document?
Este necorespunzător acest conținut?
Raportați acest documentDrepturi de autor:
Formate disponibile
Introduction To Network Security Threats
Încărcat de
iwc2008007Drepturi de autor:
Formate disponibile
02 0789730235 ch02
9/30/03
3:21 PM
Page 9
2
Introduction to Network
Security Threats
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .
Terms youll need to understand:
Denial of service (DoS)
Distributed denial of service (DDoS)
Reconnaissance attacks
Access attacks
Internal threats
External threats
Unstructured threats
Structured threats
Cisco Secure Access Control Server (CSACS)
Cisco Secure Scanner
Techniques youll need to master:
Security policy
Types of attacks
Cisco security wheel
02 0789730235 ch02
10
9/30/03
3:21 PM
Page 10
Chapter
. . . . .2. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .
Introduction to security involves discussing the types of threats we face in
our secure environments. Policies and processes help us protect our secure
environments from threats in this ever-changing world of security. This
chapter introduces a basic understanding of the types of threats we face and
the policies and processes necessary for maintaining secure environments.
Network Security Threats
Data communications networks have served the academic, corporate, and
government sectors for many years; however, the concept of security within
these networks has only recently become a high priority. As data becomes
readily available by connecting networks to public media or even other internal networks, the vulnerability of data to attacks and threats becomes apparent. Several distinct types of threats have emerged, and the network security
community has developed new ways to protect us from these threats.
Types of Security Threats
Several types of threats exist in secure environments, but most of them can
be classified into the following four main categories:
Internal threats
External threats
Unstructured threats
Structured threats
Internal Threats
Internal threats are more widespread than most people realize. These threats
typically come from users who have legitimate access to the computers or
networks they want to harm. Disgruntled or former employees whose privileged access has not been promptly terminated can cause a considerable
amount of damage to a system. Lastly, these internal threats can be some of
the most difficult to monitor and defend against.
Results of surveys conducted by the Computer Security Institute (CSI) revealed that
70% of organizations polled admitted to security breaches, 60% of which came from
within the organizations themselves (internal threats).
02 0789730235 ch02
9/30/03
3:21 PM
Page 11
. . . . . . . . . . . . . . . . . . . . . . . . . . Introduction
. . . . . . . to
. .Network
. . . . Security
. . . . . Threats
. . . .
External Threats
External threats originate from individuals who are operating outside an
organizations network. The individuals typically do not have authorized
access to the network but use remote access channels such as dial-up or
Internet connections to attempt security breaches. This threat is difficult to
protect against and is always present when external access is provided by the
company. If no Internet access or dial-up capabilities exist, you are safe from
true external threats.
Unstructured Threats
Unstructured threats are caused by individuals commonly known as script kiddies who use prebuilt tools, programs, or scripts readily available on the
Internet to launch their attacks. Script kiddies can be compared to kids joy
riding in a car; their actions are motivated more by excitement than by any
calculated thought or knowledge. If their tools fail to give them access to the
networks they desire, they typically move on to another target, rapidly losing interest. Script kiddies might seem harmless, but the damage they can
cause makes them potentially very dangerous. In most cases, unstructured
threats are performed by individuals lacking an understanding of how their
actions can impact themselves or the target network.
Structured Threats
By contrast, structured threats are performed by individuals who are fully
aware of what they intend to do and who use programs and tools to attack
networks or computers. The attackers have the ability to modify their tools
as required and the skills to develop their own new methods of attack against
unknown vendor vulnerabilities. Structured attackers can be driven by certain goals, including credit card number theft, software code theft, or intentional damage to a competitors Web site and internal networks. In addition
to their tools, these attackers also have the patience needed to penetrate the
networks, using meticulously self-created programs or even social engineering tactics. Competitors, law enforcement, or other agencies might hire the
services of structured attackers to acquire information, test security, or cause
damage to specific networks.
Social engineering is a means of collecting information from people by fooling
them; its also known as people hacking. A typical example of this is calling or sending an email message to a corporate user, posing as a manager or an administrator, to extract information such as a users password.
11
02 0789730235 ch02
12
9/30/03
3:21 PM
Page 12
Chapter
. . . . .2. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .
Three Types of Attacks
There are several types of attacks on networks. Some aim to gain information or access to restricted locations, whereas others focus on bringing down
computers. These attacks are categorized into three main types:
Reconnaissance attacks
Access attacks
Denial-of-service attacks
Reconnaissance Attacks
A reconnaissance attack is a form of information gathering from a network or
computer system. Hackers might start mapping out a network using tools
such as ping sweepers to locate active computers. Additional information,
such as operating systems in use and available open ports, can be acquired
through port scanners and Simple Network Management Protocol (SNMP).
Reconnaissance attacks usually occur prior to a denial-of-service (DoS) or
access attack.
Access Attacks
The access attacks involve collecting or obtaining access to data or networks
that usually are not available to the individual. These attacks can come in several forms, including unauthorized data retrieval, unauthorized system
access, and unauthorized privilege escalation. This form of attack can be
accomplished in several ways; however, two common hacking tools used to
gain access are password hacking programs and Trojan horses. The types of
access attacks are described in the following list:
Unauthorized data retrievalThe process of reading, writing, and possi-
bly deleting normally inaccessible information
Unauthorized system accessThe process of gaining access to a system by
exploiting a weakness in the operating system
Unauthorized privilege escalationThe process in which a low-level user
tries to gain a higher level of access such as administrator-level privileges
02 0789730235 ch02
9/30/03
3:21 PM
Page 13
. . . . . . . . . . . . . . . . . . . . . . . . . . Introduction
. . . . . . . to
. .Network
. . . . Security
. . . . . Threats
. . . .
A Trojan horse is an impostor that hides inside an email message or another program. When the email is opened or the program launched, the Trojan horse is
released, causing unlimited possible problems. This type of attacking mechanism
(which Cisco might reference as a virus, on the exam) can delete files, steal passwords, give access to remote systems, or even download more Trojan horses and
viruses.
Denial-of-Service Attacks
Hackers use denial-of-service (DoS) attacks when trying to disable, slow down,
or corrupt a network, thus denying service to the networks intended users.
Even though the hacker might not actually have a valid user account on the
network computers, if network access is achieved, the hacker can launch an
attack. This attack typically floods the targeted computer or network with
traffic with the intention to disable it.
Distributed DoS (DDoS) attacks combine the power of multiple attacking
computers, which focus their attacks on a single receiving computer or network. Because DDoS attacks can come from so many computers in different
geographical areas, administrators have extreme difficulty repelling such
attacks. For example, if a single computer pings a Web server, little stress is
placed on the server. However, if 10,000 computers are pinging a Web server all at the same time, the server can be so busy responding to the ping
requests that users accessing a Web page time out and never receive the page.
These types of attacks are some of the most feared by network administrators because blocking all the attacking computers without blocking legitimate users is very difficult.
Denial-of-service and distributed DoS attacks send large amounts of useless traffic
into a network to disable or cripple a server or network.
The Secure Network
Obtaining a secure network is not a destination, but a never-ending quest to
provide the best protection while the environment is constantly changing. A
secure system today could be a very insecure system tomorrow, as hackers
discover new vulnerabilities and security holes. Security policies and processes help set rules and guidelines to assist in acquiring and maintaining the
most secure network environment possible.
13
02 0789730235 ch02
14
9/30/03
3:21 PM
Page 14
Chapter
. . . . .2. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .
The Security Policy
The security policy is the core document or set of procedures used to
describe how an organizations information, data, and services will be protected. The policy supports the organizations primary security objectives, as
defined by who will be allowed access, who will be denied access, and what
explicitly the policy aims to protect. Lastly, this document should define
roles, responsibilities, and managed expectations and provide guidelines in
the event of a security breach or noncompliance.
RFC 2196, Site Security Handbook, states, A security policy is a formal statement of the rules by which people who are given access to an organizations technology and information assets must abide.
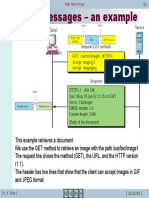
The Security Process
Security requires an ongoing process of evaluation and adaptation. What
works today might not be secure enough tomorrow. Cisco has created the
security wheel to represent graphically the continuously evolving process of
security. This process entails securing, monitoring, testing, and improving
the security policy and technical changes necessary to protect the environment. Figure 2.1 shows the Cisco security wheel.
Secure
Improve
Security
Policy
Monitor
Test
Figure 2.1 The Cisco security wheel.
The Cisco Security Wheel contains four basic steps to help visually display
the process needed to maintain a secure environment. These steps are listed
here:
02 0789730235 ch02
9/30/03
3:21 PM
Page 15
. . . . . . . . . . . . . . . . . . . . . . . . . . Introduction
. . . . . . . to
. .Network
. . . . Security
. . . . . Threats
. . . .
1. Securing the environment
2. Monitoring the environment for violations and attacks
3. Testing the security of the environment
4. Improving the security policy
Step 1: Securing the Environment
Securing the environment involves the implementation of various tools
addressing different points of vulnerability. Authentication systems, such as
One-Time-Passwords (OTP) support and Cisco Secure Access Control
Server (CSACS), aid protection by allowing only authenticated users into the
environment. Encryption techniques can be used to disguise data traveling
across insecure media; virtual private network (VPN) tunnels encrypted
using Internet Protocol Security (IPSec) are a good example of this.
Implementing firewalls, which filter incoming and outgoing traffic, can provide another layer of protection between a corporate inside network and outside intruders. Systems with known security holes should be kept up-to-date
through the use of vulnerability patching. Physical security, which is often
overlooked, involves keeping equipment secure behind locked doors. For
example, if an intruder can physically access Cisco equipment, he can employ
password-breaking procedures and have his way with your systems.
Step 2: Monitoring the Environment for Violations and
Attacks
Monitoring for violations plays a critical role in determining how effective
the secured environment is in supporting the security policy requirements.
Using intrusion detection systems, such as Cisco Secure Intrusion Detection
Systems (CSIDS), can provide an excellent solution for monitoring and
blocking unwanted traffic. In addition, logging information such as user
access and modifications to system settings can be recorded. Because the
recording of log files can accumulate large amounts of raw data, you should
store this data in a separate location, such as the Syslog server.
Step 3: Testing the Security of the Environment
After establishing your secure environment and security monitors, testing
your environment is the only way you can ensure that your security measures
are upholding your policy. Also, testing helps find new security holes in the
environment before hackers find them. Cisco Secure Scanner is a tool you
can use to test and identify such security holes.
15
02 0789730235 ch02
16
9/30/03
3:21 PM
Page 16
Chapter
. . . . .2. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .
Step 4: Improving the Security Policy
Improving the security policy within a varying and highly unpredictable
external environment is an ongoing job. Continuously monitoring, testing,
and identifying flaws and attacks against the network are imperative in refining and tuning the security policy. Vulnerability reports enable administrators
to maintain an awareness of new potential attacks and should be considered
during this step.
This chapter introduced the types of security threats that can be present
against your networks. The security policy can be used to help you document
what in your company needs protecting and how you will go about protecting that data. Ciscos security wheel demonstrates the ever-evolving
enhancements you need to make to your security policy to keep you on the
leading edge of protection and monitoring.
S-ar putea să vă placă și
- Security in NetworkingDocument8 paginiSecurity in NetworkingAdhithya KannanÎncă nu există evaluări
- Cyber Security - Network Intrusion Case StudyDocument9 paginiCyber Security - Network Intrusion Case Studysaby aroraÎncă nu există evaluări
- Malware Protection A Complete Guide - 2019 EditionDe la EverandMalware Protection A Complete Guide - 2019 EditionÎncă nu există evaluări
- Cyber Security Insurance Plan A Complete Guide - 2020 EditionDe la EverandCyber Security Insurance Plan A Complete Guide - 2020 EditionÎncă nu există evaluări
- Cyber Security Audit A Complete Guide - 2020 EditionDe la EverandCyber Security Audit A Complete Guide - 2020 EditionÎncă nu există evaluări
- Email Security Architecture A Clear and Concise ReferenceDe la EverandEmail Security Architecture A Clear and Concise ReferenceÎncă nu există evaluări
- Cyber security standards A Complete Guide - 2019 EditionDe la EverandCyber security standards A Complete Guide - 2019 EditionÎncă nu există evaluări
- Marking Scheme Computer NetworksDocument3 paginiMarking Scheme Computer NetworksWilberforce MurikahÎncă nu există evaluări
- Data Vs InformationDocument12 paginiData Vs InformationNickyStephensÎncă nu există evaluări
- Computer Security Quiz 1 AnswersDocument6 paginiComputer Security Quiz 1 AnswersBesho MarghalaniÎncă nu există evaluări
- Classification of Cyber CrimesDocument4 paginiClassification of Cyber CrimesFnatashaaÎncă nu există evaluări
- Cyber Crime and LawDocument47 paginiCyber Crime and LawMtÎncă nu există evaluări
- Cyber Security Term Paper 2018-Odd: Hardware Attacks Allow Greater AccessDocument13 paginiCyber Security Term Paper 2018-Odd: Hardware Attacks Allow Greater AccessVinay BharwaniÎncă nu există evaluări
- Computer and Network Security PrinciplesDocument26 paginiComputer and Network Security PrinciplesPutrimeliana HutasoitÎncă nu există evaluări
- Cyber SecurityDocument22 paginiCyber SecurityCarey HallÎncă nu există evaluări
- Stepwise Refinement ExplainedDocument8 paginiStepwise Refinement Explainedjuggle333Încă nu există evaluări
- Chapter OneDocument42 paginiChapter OneMagarsa BedasaÎncă nu există evaluări
- Cyber Crime NotesDocument12 paginiCyber Crime NotesDelhi University UpdatesÎncă nu există evaluări
- Information Security QuestionsDocument4 paginiInformation Security Questionssuresh.anandmÎncă nu există evaluări
- Chap 05 ClassfulDocument69 paginiChap 05 ClassfulAbhi RamÎncă nu există evaluări
- PPT ch01Document39 paginiPPT ch01jackjstickÎncă nu există evaluări
- Cyber Forensic ArticleDocument6 paginiCyber Forensic ArticleDeepika BansalÎncă nu există evaluări
- Cyber LawDocument35 paginiCyber LawSiva Sankari100% (1)
- Information SecurityDocument2 paginiInformation Security3qtrtymÎncă nu există evaluări
- Cyber WarfareDocument28 paginiCyber WarfareAritra BhattacharyyaÎncă nu există evaluări
- Cyber Crime in IndiaDocument4 paginiCyber Crime in IndiaShubhamÎncă nu există evaluări
- Computer Forensics Final GradeDocument15 paginiComputer Forensics Final GradeNicasio AquinoÎncă nu există evaluări
- Analysing an Infected Memory ImageDocument23 paginiAnalysing an Infected Memory ImageFREDDY ALLAN PALACIOS GONZÁLEZÎncă nu există evaluări
- C, C++ QuestionsDocument78 paginiC, C++ QuestionskhanjukhÎncă nu există evaluări
- Fundamentals of Computers and Information SystemDocument2 paginiFundamentals of Computers and Information SystemDreamtech PressÎncă nu există evaluări
- Legal Issues in Information Security-Chapter-5Document37 paginiLegal Issues in Information Security-Chapter-5nishit_beraÎncă nu există evaluări
- Scope, Objective and Outcome of EEDM (Unit 1)Document27 paginiScope, Objective and Outcome of EEDM (Unit 1)KUSHAL S YADAVÎncă nu există evaluări
- Introduction To Computer SecurityDocument22 paginiIntroduction To Computer SecurityJunaedi PratamaÎncă nu există evaluări
- Cyber Topics: Space, Squatting, Punk, Warfare & TerrorismDocument12 paginiCyber Topics: Space, Squatting, Punk, Warfare & TerrorismayushÎncă nu există evaluări
- Unit-5 Cybersecurity: Organizational Implications: IV-II SEM CSE, Cyber Security Unit - VDocument13 paginiUnit-5 Cybersecurity: Organizational Implications: IV-II SEM CSE, Cyber Security Unit - VLakshmi Narayana ReddyÎncă nu există evaluări
- Tutorial Basic of C++ Lesson 1 enDocument7 paginiTutorial Basic of C++ Lesson 1 enqrembiezsÎncă nu există evaluări
- Cyber Attacks Implications For UkDocument79 paginiCyber Attacks Implications For UkAlex Andra MurariuÎncă nu există evaluări
- Computer Security GoalsDocument72 paginiComputer Security GoalsAnkur Agrawal100% (2)
- Network Penetration Testing & Ethical Hacking Sample Exam (M3G421124Document3 paginiNetwork Penetration Testing & Ethical Hacking Sample Exam (M3G421124Daniel NeillÎncă nu există evaluări
- Effect of Cyber Crime in Legal PracticeDocument2 paginiEffect of Cyber Crime in Legal PracticeTwain JonesÎncă nu există evaluări
- Chapter 5Document111 paginiChapter 5Kaustubh ParthasarathyÎncă nu există evaluări
- Database Security LESSON1Document16 paginiDatabase Security LESSON1JonathanÎncă nu există evaluări
- Chapter Two (Network Thesis Book)Document16 paginiChapter Two (Network Thesis Book)Latest Tricks100% (1)
- Course Outline Is 830Document3 paginiCourse Outline Is 830lectureslidesÎncă nu există evaluări
- Ict - Important Keyword To RememberDocument8 paginiIct - Important Keyword To Remembermal887Încă nu există evaluări
- Biometric Systems Sample Exercises Chapter 1Document3 paginiBiometric Systems Sample Exercises Chapter 1YazanAlomariÎncă nu există evaluări
- ICT Form 4 Lesson PlansDocument9 paginiICT Form 4 Lesson PlansBro AhmadÎncă nu există evaluări
- PPT Ch03-Amr PDFDocument56 paginiPPT Ch03-Amr PDFCharlito MikolliÎncă nu există evaluări
- Writing Sample On Cyber Defense OrganizationDocument21 paginiWriting Sample On Cyber Defense Organizationgarret021Încă nu există evaluări
- Network SecurityDocument13 paginiNetwork SecurityNitish GuptaÎncă nu există evaluări
- Network Security Threats and Solutions 1234397207859233 2Document10 paginiNetwork Security Threats and Solutions 1234397207859233 2api-281608253Încă nu există evaluări
- CyberwarfareDocument37 paginiCyberwarfareJAIRÎncă nu există evaluări
- Syllabus IT 430-002 Ethical HackingDocument3 paginiSyllabus IT 430-002 Ethical HackingsafarneoÎncă nu există evaluări
- Cyber Awareness 2 0 2 1: BY Ayokunle OlaniyiDocument31 paginiCyber Awareness 2 0 2 1: BY Ayokunle OlaniyiOludare OgunkoyaÎncă nu există evaluări
- Risk Management: "Once We Know Our Weaknesses, They Cease To Do Us Any Harm"Document61 paginiRisk Management: "Once We Know Our Weaknesses, They Cease To Do Us Any Harm"Paolo LegaspiÎncă nu există evaluări
- Intrusion Detection Techniques in Mobile NetworksDocument8 paginiIntrusion Detection Techniques in Mobile NetworksInternational Organization of Scientific Research (IOSR)Încă nu există evaluări
- Phishing Email AnalysisDocument11 paginiPhishing Email AnalysisnagarjunaÎncă nu există evaluări
- Ethical Hacking: Cyber Vulnerabilities & ExploitsDocument10 paginiEthical Hacking: Cyber Vulnerabilities & ExploitsShaimaa AliÎncă nu există evaluări
- Unit 38 DatabaseManagementSystDocument27 paginiUnit 38 DatabaseManagementSystmomin nadeemÎncă nu există evaluări
- Web Technology 6-HyperText Transfer ProtocolDocument1 paginăWeb Technology 6-HyperText Transfer Protocoliwc2008007Încă nu există evaluări
- Web Technology 5-The Web: Some JargonDocument1 paginăWeb Technology 5-The Web: Some Jargoniwc2008007Încă nu există evaluări
- Web Technology 7-URLDocument1 paginăWeb Technology 7-URLiwc2008007Încă nu există evaluări
- Web Technology 4-World Wide Web-A Repository of InformationDocument1 paginăWeb Technology 4-World Wide Web-A Repository of Informationiwc2008007Încă nu există evaluări
- Web Technology 9-HTTP - ExampleDocument1 paginăWeb Technology 9-HTTP - Exampleiwc2008007Încă nu există evaluări
- Web Technology 15-HTTP - Message Format (Status Code)Document1 paginăWeb Technology 15-HTTP - Message Format (Status Code)iwc2008007Încă nu există evaluări
- Web Technology 11-HTTP Protocol - Message FormatDocument1 paginăWeb Technology 11-HTTP Protocol - Message Formatiwc2008007Încă nu există evaluări
- Web Technology 10-HTTP - Example (CNT'D)Document1 paginăWeb Technology 10-HTTP - Example (CNT'D)iwc2008007Încă nu există evaluări
- Web Technology 16-HTTP - Message Format (Status Code)Document1 paginăWeb Technology 16-HTTP - Message Format (Status Code)iwc2008007Încă nu există evaluări
- Web Technology 8-URL - ContinuedDocument1 paginăWeb Technology 8-URL - Continuediwc2008007Încă nu există evaluări
- Web Technology 14-HTTP - Message Format (Status Code)Document1 paginăWeb Technology 14-HTTP - Message Format (Status Code)iwc2008007Încă nu există evaluări
- Web Technology 13-HTTP - Message FormatDocument1 paginăWeb Technology 13-HTTP - Message Formatiwc2008007Încă nu există evaluări
- Web Technology 18-HTTP - Message FormatDocument1 paginăWeb Technology 18-HTTP - Message Formatiwc2008007Încă nu există evaluări
- Web Technology 22-HTTP - Message Format (Entity Header)Document1 paginăWeb Technology 22-HTTP - Message Format (Entity Header)iwc2008007Încă nu există evaluări
- Web Technology 20-HTTP - Message Format (Request Header)Document1 paginăWeb Technology 20-HTTP - Message Format (Request Header)iwc2008007Încă nu există evaluări
- Web Technology 21-HTTP - Message Format (Response Header)Document1 paginăWeb Technology 21-HTTP - Message Format (Response Header)iwc2008007Încă nu există evaluări
- Web-Technology 27 PDFDocument1 paginăWeb-Technology 27 PDFiwc2008007Încă nu există evaluări
- Web Technology 19-HTTP - Message FormatDocument1 paginăWeb Technology 19-HTTP - Message Formatiwc2008007Încă nu există evaluări
- Web Technology 26-Web Caches - ProxyDocument1 paginăWeb Technology 26-Web Caches - Proxyiwc2008007Încă nu există evaluări
- Web Technology 24-HTTP Messages - An ExampleDocument1 paginăWeb Technology 24-HTTP Messages - An Exampleiwc2008007Încă nu există evaluări
- Web-Technology 4 PDFDocument1 paginăWeb-Technology 4 PDFiwc2008007Încă nu există evaluări
- Web-Technology 26 PDFDocument1 paginăWeb-Technology 26 PDFiwc2008007Încă nu există evaluări
- Web Technology 25-Persistent and Nonpersistent ConnectionsDocument1 paginăWeb Technology 25-Persistent and Nonpersistent Connectionsiwc2008007Încă nu există evaluări
- Web Technology 27 Why Web Caching?Document1 paginăWeb Technology 27 Why Web Caching?iwc2008007Încă nu există evaluări
- Web Technology 28 Consistency of Web CachingDocument1 paginăWeb Technology 28 Consistency of Web Cachingiwc2008007Încă nu există evaluări
- Web Technology 27 Why Web Caching?Document1 paginăWeb Technology 27 Why Web Caching?iwc2008007Încă nu există evaluări
- Web-Technology 23 PDFDocument1 paginăWeb-Technology 23 PDFiwc2008007Încă nu există evaluări
- Web-Technology 22 PDFDocument1 paginăWeb-Technology 22 PDFiwc2008007Încă nu există evaluări
- Web-Technology 24 PDFDocument1 paginăWeb-Technology 24 PDFiwc2008007Încă nu există evaluări
- BMSIT (Techincal Seminar)Document16 paginiBMSIT (Techincal Seminar)Manish ManiÎncă nu există evaluări
- Basic Pentesting: 1 Walkthrough | Vulnhub ExploitedDocument6 paginiBasic Pentesting: 1 Walkthrough | Vulnhub ExploitedKevin MejiaÎncă nu există evaluări
- Visa Integrated Circuit Card SpecificationDocument370 paginiVisa Integrated Circuit Card Specificationlucianozx100% (3)
- HotStar IDDocument1 paginăHotStar IDsunilÎncă nu există evaluări
- High Authority Social Profile BacklinksDocument1 paginăHigh Authority Social Profile BacklinksGulam Robbani SrkshazuÎncă nu există evaluări
- CBSE Class 8 Computer Science - Introduction To Computer SecurityDocument4 paginiCBSE Class 8 Computer Science - Introduction To Computer SecurityRajeshji100% (1)
- On Chaos EncryptionDocument24 paginiOn Chaos EncryptionChaitra BaluÎncă nu există evaluări
- PCNSE DemoDocument11 paginiPCNSE DemodezaxxlÎncă nu există evaluări
- Mas NSEPDocument244 paginiMas NSEPRishit Sriwastava100% (1)
- Eset Smart Security, Nod32 usernames, passwords and serial keysDocument7 paginiEset Smart Security, Nod32 usernames, passwords and serial keysHedy KasperskyÎncă nu există evaluări
- H4ckingWorld Hack Suite v1Document6 paginiH4ckingWorld Hack Suite v1api-3834671100% (5)
- Information Security SOPDocument15 paginiInformation Security SOPHaemlet100% (1)
- Block Ciphers & Symmetric Key Cryptography: Simplified DESDocument32 paginiBlock Ciphers & Symmetric Key Cryptography: Simplified DESGeethanjali KotaruÎncă nu există evaluări
- Password CrackingDocument41 paginiPassword Crackingrahul123678Încă nu există evaluări
- Research On End-To End Encryption of TETRA: Zhang YangDocument4 paginiResearch On End-To End Encryption of TETRA: Zhang YangJosip StjepanovićÎncă nu există evaluări
- Penetration Testing Procedure Ambersail SampleDocument8 paginiPenetration Testing Procedure Ambersail SampleAbdulkadir YÜKSELÎncă nu există evaluări
- Crypsis - 2020 Incident Response and Data Breach Report - FINALDocument52 paginiCrypsis - 2020 Incident Response and Data Breach Report - FINALForkLogÎncă nu există evaluări
- Virtual Private Networking BasicsDocument14 paginiVirtual Private Networking BasicsManeeshaÎncă nu există evaluări
- SAP Logon ParametersDocument3 paginiSAP Logon Parametersjgb6275Încă nu există evaluări
- Cybersecurity Guide For Dummies Compressed PDFDocument34 paginiCybersecurity Guide For Dummies Compressed PDFAeenRi melonwaterÎncă nu există evaluări
- 000 139 PDFDocument17 pagini000 139 PDFtareqcccccÎncă nu există evaluări
- Security Protocols: Helping Alice and Bob To Share Secrets (COMP - SEC.220) Coursework IDocument6 paginiSecurity Protocols: Helping Alice and Bob To Share Secrets (COMP - SEC.220) Coursework Isoulfly_shahedÎncă nu există evaluări
- Allow IBM MQ Channels To Use ANY - TLS12Document3 paginiAllow IBM MQ Channels To Use ANY - TLS12Siropani BhattamishraÎncă nu există evaluări
- Nemty Dybhcdr - DecryptDocument2 paginiNemty Dybhcdr - DecryptWillian WijayaÎncă nu există evaluări
- Implementation of Substitution Technique: Experiment-1Document8 paginiImplementation of Substitution Technique: Experiment-1Sonam GuptaÎncă nu există evaluări
- Arba Minch University Institute of Technology Faculty of Computing & Software EngineeringDocument65 paginiArba Minch University Institute of Technology Faculty of Computing & Software Engineeringjemu mamedÎncă nu există evaluări
- PT08 18 PreviewDocument35 paginiPT08 18 PreviewFredd VargasÎncă nu există evaluări
- Empowerment TechnologiesDocument4 paginiEmpowerment TechnologiesMNO JapalÎncă nu există evaluări
- Setting Modem MobinilDocument1 paginăSetting Modem MobinilTjokop JpÎncă nu există evaluări
- Authentication and Authorization Mechanism For Internet of Things InfrastructureDocument31 paginiAuthentication and Authorization Mechanism For Internet of Things InfrastructureDhanushka DolapihillaÎncă nu există evaluări