Documente Academic
Documente Profesional
Documente Cultură
Base Paper
Încărcat de
Add KDrepturi de autor
Formate disponibile
Partajați acest document
Partajați sau inserați document
Vi se pare util acest document?
Este necorespunzător acest conținut?
Raportați acest documentDrepturi de autor:
Formate disponibile
Base Paper
Încărcat de
Add KDrepturi de autor:
Formate disponibile
364
IEEE TRANSACTIONS ON MOBILE COMPUTING, VOL. 13, NO. 2, FEBRUARY 2014
Autonomous Mobile Mesh Networks
Wei-Liang Shen, Chung-Shiuan Chen,
Kate Ching-Ju Lin, Member, IEEE, and Kien A. Hua, Fellow, IEEE
AbstractMobile ad hoc networks (MANETs) are ideal for situations where a fixed infrastructure is unavailable or infeasible. Todays
MANETs, however, may suffer from network partitioning. This limitation makes MANETs unsuitable for applications such as crisis
management and battlefield communications, in which team members might need to work in groups scattered in the application terrain.
In such applications, intergroup communication is crucial to the team collaboration. To address this weakness, we introduce in this
paper a new class of ad-hoc network called Autonomous Mobile Mesh Network (AMMNET). Unlike conventional mesh networks, the
mobile mesh nodes of an AMMNET are capable of following the mesh clients in the application terrain, and organizing themselves into
a suitable network topology to ensure good connectivity for both intra- and intergroup communications. We propose a distributed client
tracking solution to deal with the dynamic nature of client mobility, and present techniques for dynamic topology adaptation in
accordance with the mobility pattern of the clients. Our simulation results indicate that AMMNET is robust against network partitioning and
capable of providing high relay throughput for the mobile clients.
Index TermsMobile mesh networks, dynamic topology deployment, client tracking
INTRODUCTION
technology has been one of the most
transforming and empowering technologies in recent
IRELESS
years. In particular, mobile ad hoc networks (MANETs) are
among the most popularly studied network communication technologies. In such an environment, no communication infrastructure is required. The mobile nodes also
play the role of the routers, helping to forward data
packets to their destinations via multiple-hop relay. This
type of network is suitable for situations where a fixed
infrastructure is unavailable or infeasible. They are also a
cost effective solution because the same ad hoc network
can be relocated, and reused in different places at different
times for different applications.
One great challenge in designing robust MANETs is to
minimize network partitions. As autonomous mobile
users move about in a MANET, the network topology
may change rapidly and unpredictably over time; and
portions of the network may intermittently become
partitioned. This condition is undesirable, particularly for
mission-critical applications such as crisis management
and battlefield communications. We address this challenging problem in this paper by proposing a new class of
robust mobile ad hoc network called Autonomous Mobile
Mesh Networks (AMMNET).
In a standard wireless mesh network, stationary mesh
nodes provide routing and relay capabilities. They form a
mesh-like wireless network that allows mobile mesh clients
to communicate with each other through multihop communications. Such a network is scalable, flexible, and low in
. W.-L. Shen, C.-S. Chen, and K.C.-J. Lin are with the Research Center for IT
Innovation, Academia Sinica, No. 128, Academia Road, Sec. 2, Nankang,
Taipei 115, R.O.C. E-mail: katelin@citi.sinica.edu.tw.
. K.A. Hua is with the Division of Computer Science, University of Central
Florida, 2775 Marsh Wren Circle, Longwood, FL 32779.
Manuscript received 9 Feb. 2012; revised 30 July 2012; accepted 30 Nov. 2012;
published online 20 Dec. 2012.
For information on obtaining reprints of this article, please send e-mail to:
tmc@computer.org, and reference IEEECS Log Number TMC-2012-02-0067.
Digital Object Identifier no. 10.1109/TMC.2012.259.
1536-1233/14/$31.00
IEEE
maintenance cost. When a mesh node fails, it can simply be
replaced by a new one; and the mesh network will recognize
the new mesh node and automatically reconfigure itself. The
proposed AMMNET has the following additional advantage. The mobility of the mesh clients is confined to the fixed
area serviced by a standard wireless mesh network due to
the stationary mesh nodes. In contrast, an AMMNET is a
wireless mesh network with autonomous mobile mesh
nodes. In addition to the standard routing and relay
functionality, these mobile mesh nodes move with their
mesh clients, and have the intelligence to dynamically adapt
the network topology to provide optimal service. In
particular, an AMMNET tries to prevent network partitioning to ensure connectivity for all its users. This property
makes AMMNET a highly robust MANET.
The topology adaptation of an AMMNET is illustrated in
Fig. 1:
.
Fig. 1a: The mesh clients initially concentrate in one
group. All the mesh nodes position themselves
within the same proximity to support communications inside the group.
. Fig. 1b: The mesh clients move northwards and split
into two groups. The mobile mesh nodes, in this
case, reorganize themselves into a new topology not
only to facilitate intragroup communications, but
also to support intergroup communications effectively preventing a network partition.
. Fig. 1c: The same mesh clients now move southeast
and form three groups. The mobile mesh nodes
adapt their topology accordingly to archive full
connectivity for all the mesh clients.
We note that it is not always feasible to replace a mobile
mesh network with a standard stationary mesh network
that is large enough to provide coverage for the entire
application terrain as shown in Fig. 2. In this paper, we deal
with application terrains that are too large and too
expensive for such a deployment. Besides, predeployment
of such a fixed mesh network might not even be possible for
Published by the IEEE CS, CASS, ComSoc, IES, & SPS
SHEN ET AL.: AUTONOMOUS MOBILE MESH NETWORKS
365
Fig. 1. Topology adaptation of the autonomous mobile mesh network
under three scenarios.
Fig. 2. Fixed grid-based square topology under three scenarios
illustrated in Fig. 1.
many applications such as disaster recovery and battlefield
communications. Specifically, LTE [1] and WiMAX [2]
might be able to support broadband access for a given
application terrain. They, however, are not flexible enough
to adapt to topology changes for the dynamic applications
considered in this work, and hence might require a much
higher deployment cost, including the costs of equipments,
manpower, and rewiring. In other words, they are a costeffective technology only when there is a high density of
users in a fixed and known application terrain, like in urban
or suburban residential networks, to justify the expensive
deployment cost. However, when this condition is not
satisfied, such as a large temporary and uncertain application terrain in battlefield communication or disaster
management applications, AMMNET is a good candidate
because it can adapt to a very dynamic environment. Delay
tolerant network (DTN) [3] is another option to support
opportunistic communications for mobile networks. However, there is no guarantee of finding a routing path to
forward data. In contrast, the goal of our design is to
provide such mobile networks a robust infrastructure with
persistent connectivity. We note that if the number of mesh
nodes in AMMNET is not enough to support full connectivity for the entire terrain, DTN can be used to improve
the probability of data delivery. We leave the integration of
AMMNET and DTN as our future study.
We assume that each mobile mesh node is equipped with
a localization device such as GPS. In addition, a mobile
mesh node can detect mesh clients within its sensing range,
but does not know their exact locations. For instance, this
can be achieved by detecting beacon messages transmitted
from the clients. Alternatively, RFID has been proposed for
location-based applications [4]. Similarly, mesh clients can
be tagged with an inexpensive RFID and mobile mesh
nodes are equipped with an RFID reader to detect the
presence of mobile nodes within their sensing range.
Our challenges in designing the proposed AMMNET
are twofold. First, the mesh clients do not have knowledge
of their locations making it difficult for the mobile mesh
nodes to synthesize a global map of the user locations.
Second, the topology adaptation needs to be based on a
highly efficient distributed computing technique to keep
up with the dynamic movement of the mobile users. These
challenges are addressed in this paper.
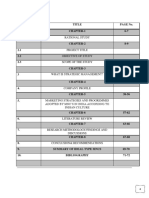
The remainder of this paper is organized as follows:
We introduce the framework of an AMMNET, and present
how to realize mobile client tracking in a distributed
manner in Section 2. In Section 3, a number of network
topology optimization methods are discussed. Our performance evaluation results are given in Section 4. We
summarize some related work in Section 5, and conclude
this paper in Section 6.
DISTRIBUTED CLIENT TRACKING IN AMMNET We
first give an overview of the AMMNET framework, and then
present how the mobile mesh nodes automatically adapt
their locations to tracking mobile clients.
2.1
AMMNET Overview
Similar to stationary wireless mesh networks, an AMMNET
is a mesh-based infrastructure that forwards data for mobile
clients as shown in Fig. 1. A client can connect to any nearby
mesh node, which helps relay data to the destination mesh
node via multihop forwarding. For ease of description, in
this paper we use the terms mesh node and router
interchangeably. Like stationary wireless mesh networks,
where routers are deployed in fixed locations, routers in an
AMMNET can forward data for mobile clients along the
routing paths built by any existing ad hoc routing protocols,
for example, AODV. Unlike stationary wireless mesh
networks, where routers are deployed at fixed locations,
routers in an AMMNET are mobile platforms with autonomous movement capability [5]. They are equipped with
positioning devices such as GPS, to provide navigational aid
while tracking mobile clients. Clients are not required to
know their locations, and only need to periodically probe
beacon messages. Once mesh nodes receive the beacon
messages, they can detect the clients within its transmission
range. With this capability, mesh nodes can continuously
monitor the mobility pattern of the clients, and move with
them to provide them seamless connectivity.
A few assumptions are made in our design. We consider
a two-dimensional airborne terrain, where there is no
obstacle in the target field. Mesh nodes can exchange
information, such as their locations and the list of detected
clients, with their neighboring mesh nodes. The radio range
of each node is not a perfect circle in an application domain
with obstacles. This factor may affect the accuracy of the
sensing mechanism and, to a minor degree, the coverage.
However, this does not affect the general applicability of
the proposed techniques for AMMNETs. For simplicity, we
assume that the radio range of both mesh nodes and clients
is a perfect sphere.
366
IEEE TRANSACTIONS ON MOBILE COMPUTING, VOL. 13, NO. 2, FEBRUARY 2014
Our design considers applications where clients follow
group mobility patterns [6] to move toward different
directions in smaller groups. That is, the clients belonging
to the same group have similar movement characteristics.
However, different groups of clients might move in
different directions, as illustrated in Fig. 1. The group
mobility model has been verified as a realistic mobility
model [7] and applied to many practical scenarios, such as
campus networks [8] and ad hoc networks [9], [10]. Our
goal is to dynamically allocate a finite number of mesh
nodes to cover as many mobile clients as possible, while
maintaining the connectivity between the groups of clients.
Even though we describe the operation of AMMNET using
the group mobility model, AMMNET can actually support
a more general mobility model, where clients might move
independently. In an extreme case, each client can be
thought of as a group that contains only one user, and the
design of AMMNET can still be applied to support
connectivity for those independent clients. To support
such a dynamically changing mesh topology, mobile mesh
nodes can be classified into the following types according
to their current roles in this network:
Intragroup routers. A mesh node is an intragroup
router if it detects at least one client within its radio
range and is in charge of monitoring the movement
of clients in its range. Intragroup routers that
monitor the same group of clients can communicate
with each other via multihop routing. For example,
routers r1 and r2 in Fig. 4 are intragroup routers that
monitor group G1.
. Intergroup routers. A mesh node is an intergroup
router, i.e., square nodes in Fig. 4, if it plays the role of
a relay node helping to interconnect different groups.
For each group, we designate at least one intergroup
router that can communicate with any intragroup
routers of that group via multihop forwarding as the
bridge router, for example, router b1 for group G1.
. Free routers. A mesh node is a free router if it is neither
an intragroup router nor an intergroup router.
We consider a scenario where clients originate in one
given location, and can be covered by the radio range of a
single mesh node. Thus, the initial configuration of the
AMMNET consists of only one intragroup router; and all
remaining routers are free. In tracking the mobile clients,
the mobile mesh nodes change their operation modes based
on Algorithm 1 as follows:
.
. Adapting to intragroup movement. As a group of
clients moves from place to place, the area they
occupy may change over time. The intragroup
routers must track these changes to move with the
clients and dynamically adjust their topology accordingly to sustain the communication coverage for
the clients.
. Reclaiming redundant routers. When the topology
changes due to client mobility, some intra- and
intergroup routers might become redundant and
should be reclaimed as free routers for future use.
. Interconnecting groups. Clients of a group may split
into smaller groups that move in different directions.
In this case, some free routers should change their
operation mode to become intergroup routers to
interconnect these partitioned groups.
We assume that each mesh node is fully charged in the initial
location and has enough power to update its location and
forward data for mobile clients. However, once an inter- or
intragroup router detects that its energy level is low, it can
request to be replaced by a free router. The replaced lowpower node is then reclaimed as a free router and can go back
to the initial location, for example, control center, to replace
the battery. The above strategy prevents the network from
partition due to energy-depleted mesh nodes. A sophisticate
scheme that optimizes energy efficiency of AMMNET is
still worth studying and is left as our future work.
Algorithm 1. Distributed Client Tracking for Router r.
1: for each Beacon message interval do
2:
switch mode of router r do
3:
case Intra-group
4:
if detect missing clients then
5:
Request the client list from neighboring
intra-group routers;
6:
if all its clients are covered by neighbors then
7:
Switch to the Intergroup mode;
8:
else
9:
Assign free routers to navigate its
coverage boundary;
10:
end if
11:
end if
12:
case Intergroup bridge
13:
Piggyback its location in the forwarded
packets;
14:
Retrieve the locations of other bridge routers
and the identity of the intergroup routers along
the bridge networks from the forwarded
packets;
15:
Initiate topology adaptation if necessary
(see Algorithm 3);
16:
case Free
17:
if receive the tracking request from intra-group
routers then
18:
Navigate the assigned segment to detect the
missing clients;
19:
if locate the missing clients then
20:
Switch to the intra-group mode;
21:
Request some of the free routers to follow
this new intra-group router;
22:
end if
23:
end if
24:
end switch
25: end for
26: return
In terms of security, techniques developed for standard
mesh networks are also applicable to the proposed
AMMNET; and we refer the interested reader to [11], [12],
[13], for examples, of these techniques. Another reasonable
concern is the protection of the mobile mesh nodes against
destruction. This issue depends on the physical design of the
mobile mesh node and the application domain. As an
example, autonomous quadrocopters [5] powered by solar
energy can be used as the mobile mesh nodes. Such mobile
mesh nodes are generally safe for applications such as crisis
management (Fig. 3). A battlefield environment, however,
SHEN ET AL.: AUTONOMOUS MOBILE MESH NETWORKS
367
Fig. 5. Tracking the clients. If the client moves from one router area to
another router area as in (a), no action is required. If a client moves out of
the current network coverage area as in (b), free routers are triggered to
track the missing clients.
Fig. 3. Autonomous airborne mesh networks for crisis management.
would be more hostile; where the enemy could attempt
to disable the flying mesh nodes. Such a topic is beyond
the scope of this paper although replacement mobile
mesh nodes could be launched as needed to maintain the
desired communication coverage; in which case, the airborne network would reorganize itself to integrate the new
mesh nodes.
2.2
Adapting to Intragroup Movement
We recall that each client continuously broadcasts beacon
message to notify its present within the ratio range of an
intragroup router. When this router no longer hears the
expected beacon messages, one of two possible scenarios
might have happened. The first scenario is illustrated in
Fig. 5a. It shows that client c moves out of the communication range of router r into the communication range of an
adjacent router r0 in the same group. The second scenario is
illustrated in Fig. 5b. It shows that the missing client c
moves from the communication range of router r to a space
not currently covered by any of the routers in the group.
The router r can distinguish the above two scenarios by
querying its neighboring routers for their lists of monitored
clients. If c is in any of these lists, r determines that the first
scenario has occurred. In this case, since some of the
neighboring routers provide the coverage for c, no further
action is required. On the other hand, if none of the client
lists includes c, which indicates the second scenario,
topology adaptation is required to extend the coverage to
include c at its new location.
Fig. 4. AMMNET Framework. Routers are partitioned into two groups.
Intragroup routers support intragroup communication; and intergroup
routers prevent a network partition.
To achieve this goal, once router r detects the missing
client, it broadcasts a message to trigger the neighboring
free routers to track the missing client c. Specifically, since
client c moves out from the radio range of router r, a free
router must be able to locate the client c by navigating the
boundary of rs coverage, which is the circle centered at r,
i.e., the red segment shown in Fig. 5b. Once a free router
detects the missing client, it then stops navigating and
switches its mode to become an intragroup router. We note
that this new intragroup router will have connectivity to the
rest of the intragroup routers because it is within the radio
range of the original monitoring router r.
The following optimization can be performed to further
reduce the disconnection time for a missing client. We
divide the boundary of each active router into k segments,
where k is the minimum of 12 and Nf =Na. Nf and Na are
the numbers of currently free and active routers, respectively. The benefit of this strategy is twofold. First, k free
routers are available to search a given missing client in
parallel by traversing different segments of the boundary
simultaneously; second, the free routers are evenly distributed among the active routers to ensure good performance at all client groups in the terrain.
2.3
Reclaiming Redundant Routers
When the intra- and intergroup routers are no longer
required due to client mobility, the AMMNET should
reclaim them for future use. We discuss the case of
intragroup routers. Reclamation of intergroup routers will
be treated in Section 3. Consider the example shown in the
right-hand side of Fig. 5b. All the clients in the radio range
of router r are also covered by the neighboring intragroup
routers. In this case, router r is no longer needed and can
be reclaimed as follows: Router r requests the clients list of
the neighboring intragroup routers. If r detects that all its
clients are covered by the neighboring routers, it sends a
message to inform these neighbors of its intent to switch
the operation mode. After receiving the acknowledgment
from all these neighbors, r can switch to become an
intergroup router. There are three points worth noting. First,
this switching protocol is to avoid the situation where
multiple neighboring intragroup routers simultaneously
switch their mode, rendering some clients without any
covering intragroup routers. Second, the redundant intragroup router can only declare itself as an intergroup
router, instead of a free router, because it might be a
bridge interconnecting two partitioned groups. Third,
this switching protocol might generate more redundant
intergroup routers, which can later be reclaimed to the
368
IEEE TRANSACTIONS ON MOBILE COMPUTING, VOL. 13, NO. 2, FEBRUARY 2014
Fig. 6. Group partition. When clients are partitioned into several groups and move toward different directions, as in (a) and (b), the intragroup routers,
which originally operate as intragroup routers to cover clients, are then switched to act as the intergroup routers that relay data among groups, as in
(c). By applying local adaptation, as in (d), we can eliminate detour paths between groups.
free-router pool during the topology adaptation phase
discussed in Section 3.
2.4
Interconnecting Groups
Given a set of intragroup routers that provide communication coverage for a group of mobile users, these mobile users
might move out of this coverage area in smaller groups. To
avoid network partitioning, each of the new groups must be
supported by their local intragroup routers; and intergroup
routers must organize themselves into a subnetwork of
bridges to support the intergroup communications.
Let us consider the example in Fig. 6a. We initially have
a single group of mobile users with a local network
consisting of intragroup routers r1 and r2. Sometime later,
some of these clients are moving away from this coverage
area in three different directions as shown in Fig. 6b. Let us
focus on group G2. As the two clients of this group move
out of the initial coverage area, a free router joins the
network as a new intragroup router to provide coverage for
these two departing clients. This is done as discussed in
Section 2.2. At this time, r2 can switch itself to become an
intergroup router, as discussed in Section 2.3, because it no
longer has any client within its radio range. r2 now serves
as a network bridge to interconnect the two groups G1 and
G2 as shown in Fig. 6b. If the group G2 continues to move
farther away from G1, the above process repeats and more
intragroup routers in G2 become intergroup routers. They
extend the network bridge, one intergroup router at a time
along the trajectory of the group G2, to maintain the
connectivity between G2 and G1. Fig. 6c illustrated three
bridging networks connected to interconnect groups G2, G3,
and G4 to their original group G1. These bridging networks
maintain the connectivity for all clients and prevent
network partition. After interconnecting all the groups,
free routers can be redistributed such that all the partitioned groups have a similar number of free routers to
improve tracking efficiency. After redeployment, each free
router sends its identification to the bridge routers in its
group, and hence, any bridge router can track the number
of free routers in its group.
3 TOPOLOGY ADAPTATION
The protocol discussed so far ensures that the mesh nodes
maintain the connectivity for all clients. The resulting
networks, however, might incur long end-to-end delay with
potentially many unnecessary intergroup routers because
the bridging networks are constructed independently. As the
example shown in Fig. 6c, if a client in group G2 wants to
communicate with another client in group G3, this must be
done through a long path over the router b1 at group G1
although groups G2 and G3 are near each other. Another
potential drawback is the excessive use of the intergroup
routers. To improve this condition, we propose two topology
adaptation schemes, namely local adaptation and global
adaptation, each with a different resolution of location
information to shorten the relay paths between groups.
3.1
Local Adaptation
Consider again the example in Fig. 6c. To save intergroup
routers, we can replace three independent bridging networks with a star network as shown in Fig. 6d. A star
topology generally provides shorter relay paths, and, as a
result, requires fewer intergroup routers. To construct a star
topology, we let the bridge routers exchange their location
information opportunistically, and perform local adaptation as
shown in Algorithm 2 when some bridge routers detect that
they are close to each other.
Algorithm 2. Topology Adaptation (initiated by router r).
input: (Collected in Algorithm 1) Rb: set of bridge routers
known by r opportunistically; Lb: location of router
b2Rb; Ri:set ofintergroup routers connecting all
known bridge routers b 2 Rb
1: if number of free routers in rs group < then
2:
Call Algorithm 3 to perform global adaptation;
3: else
4:
Compute the single star topology S for Rb;
5:
Build a bridge network B connecting to any bridge
router b0 2 Rb;
6: N0 i
number of intergroup routers needed for
S and B;
7:
if i
jRij then
8:
Trigger the assigned intergroup routers to adapt
their topology to S [ B after a three-way
handshaking;
9:
Reclaim the rest of intergroup routers to the
free-router poor;
10:
end if
11: end if
12: return
Specifically, when clients in different groups are communicating with each other, the corresponding bridge
routers can exchange their location information by piggybacking such information in the data packets. For instance,
when client c1 transmits a data packet to client c2 through
SHEN ET AL.: AUTONOMOUS MOBILE MESH NETWORKS
the bridge routers b2, b1, and b4 as shown in Fig. 6c, b2 and b1
attach their location information to the data before forwarding the packet. When this data packet arrives at the
bridge router b4, it can extract the location information of b2
and b1 before forwarding the data packet. Similarly, the
bridge router b1 can extract the location information of b2
from the data packet. This opportunistic strategy allows the
exchange of location information with minimum overhead.
Note that as the data packet traverses the route from
client c1 to c2 in the above example, the intergroup routers
append their ID to the data before forwarding the packet.
Thus, the bridge router b4 also knows about the intergroup
routers on the bridge networks between b2 and b1 and
between b1 and b4.
After a bridge router (say b4) has gathered the local
location information, it notices that bridge routers b2, b3, and
itself are located near each other. This indicates that the
corresponding groups G2, G3, and G4 are within proximity.
To more effectively interconnect them using a star topology,
the bridge router b4 can act as the coordinating bridge router
or coordinator to trigger local topology adaptation. Specifically, the bridge router b4 determines the minimumbounding rectangle for the locations of b2, b3, and itself;
and uses the center of this rectangle as the center of the star
topology as seen in Fig. 6d. The coordinator also needs to
ensure that the new constructed star topology will be
connected to the rest of the AMMNET. Hence, to guarantee
seamless network connectivity, the coordinator broadcasts a
message to find a bridge router not a part of the new star
network, for example, b1 in this example, and builds a
bridge network to this bridge router before the star network
can be constructed.
Construction of the star network in the above example is
done as follows: The bridging networks between b2 and b1
and between b3 and b1 can be dismantled, and their
intergroup routers used for the new star network. Since
the coordinating bridge router b4 knows about these
intergroup routers, it can create an assignment list to assign
them to distinct data forwarding positions in the star
network. This assignment list is multicast to all the
intergroup routers on the bridge networks about to be
dismantled. If these routers found them in the list, they
move to the designated location to take their position in the
new star network; otherwise, they change to the free mode
and return to the free pool. Thus, such local adaptation not
only improves the network performance, i.e., smaller endto-end delay, but also saves mobile routers. In the less
frequent situations in which the number of intergroup
routers is not enough for the construction of the new star
network, the coordinator cancels the construction process.
We note that multiple bridge networks in proximity
might attempt to initiate their own local topology adaptation at about the same time. This is addressed by time
stamping each adaptation request. When a bridge router
receives a request with a smaller time stamp than that of the
adaptation the router is currently involved with, it cancels
its current adaptation process and follows the new one with
a smaller time stamp. In terms of coordinating the
intergroup routers, a three-way handshake protocol is
employed. After a coordinating bridge router sends out its
assignment list, it waits for the intergroup routers to
confirm. If all agree to participate, the coordinator sends
them a notification to proceed with the topology adaptation;
otherwise, the coordinator cancels the adaptation.
369
3.2
Global Adaptation
Local topology adaptation provides local optimization. It is
desirable to also perform global topology adaptation to
achieve global optimality. The motivation is to achieve
better overall end-to-end delay and free up intergroup
routers for subsequent local adaptation. A simple option for
global optimization is to apply Algorithm 2 to construct a
star network for all the bridge routers in the AMMNET.
Such a star network, however, would be inefficient and
require more intergroup routers than necessary, particularly when there are a significant number of groups in the
network as in Fig. 7a.
Ideally, an AMMNET should use as few intergroup
routers as possible to minimize the number of mobile
routers required and deliver good end-to-end delay for the
application. This optimization problem can be formulated
as the connected set cover problem, which has been proved
to be NP-hard [14], [15]. In this paper, we propose a
hierarchical star topology, which is a near-optimal technique based on R-tree [16] as shown in Algorithm 3. The Rtree is a multidimensional tree structure that aggregates at
most M objects into a minimum-bounding rectangle. M of
such rectangles are further aggregated into a larger
bounding rectangle at the next higher level in the tree. This
clustering process is repeated recursively at the higher
levels until there is a single minimum-bounding rectangle
left at the root of the R-tree. To determine a suitable value of
M, we can apply k-means clustering [17] or affinity
propagation [18] to cluster the bridge routers in the
network. The latter does not require a specified number of
clusters k. After clustering, each bridge router is associated
with a distinct cluster based on its Euclidian distance with
k
size of all the clusters, i.e., M Pi1jCij=k, wherekvisrthe
number of clusters and jCij is the number of bridge routers in
the ith cluster Ci.
Algorithm 3. Hierarchical Star Topology Construction.
Input: M: size of a bounding box
1: Broadcast a message to all the bridge routers to collect
information and coordinate global adaptation;
2: Rb
set of bridge routers;
3: Lb
location of routerb 2 Rb;
4: Ri
set of nonbridge intergroup routers;
5: Classify all r 2 Rb into cluster Ci; i 1; 2; . . . ; k;
6: M
Ci jj
k
7: T
R-Tree(Rb; Lb; M);
8: for all vertex v in T do
9:
while v is a leave node and any ri; rj 2 v belong to the
same group do
10:
Remove rj from v;
11:
end while
12:
if not all elements r 2 v are interconnected then
13:
Deploy a subset of intergroup routers in Ri as a
star topology to connect all r 2 v and remove
those routers from Ri;
14:
end if
15: end for
16: Reclaim the remaining routers in Ri as free routers;
17: return
370
IEEE TRANSACTIONS ON MOBILE COMPUTING, VOL. 13, NO. 2, FEBRUARY 2014
Fig. 7. Hierarchical Topology Construction. Groups can be connected as a hierarchical star topology and communicate through shorter relay paths.
By applying the hierarchical clustering strategy to the
bridge routers in an AMMNET, we can deploy a star
network to interconnect the bridge routers in each rectangle
at the leaf level of the R-tree. At each of the subsequent
higher level in the R-tree, the star networks in each
bounding rectangle are further interconnected into a star
network in a hierarchical manner. This interconnection
strategy is repeated until it reaches the rectangle at the root
of the R-tree. Let us consider the example in Fig. 7a with
seven groups of clients. If the desired number of objects per
bounding rectangle M is 3, the R-tree is constructed as
shown in Fig. 7c with the corresponding hierarchical star
network illustrated in Fig. 7d. In this example, the star
network of rectangle a interconnects the bridge routers b1,
b2, and b3. The star networks for the rectangles b and c are
constructed similarly. At the next higher level, i.e., the root
of the R-tree, a star network is created for the rectangle d to
interconnect the three star networks of rectangles a, b, and c,
respectively. For each bounding rectangle, the star networks
from the lower level are interconnected through the bridge
routers closest to the center of their respective bounding
rectangle as illustrated in Fig. 7d. This scheme optimizes the
overall end-to-end delay for the network.
To further reduce the number of intergroup routers, we
consider two additional strategies. First, we do not need to
build a star router for the bridge routers at some leaf
rectangle in the R-tree if they are already interconnected.
For instance, the bridge routers b1, b2, and b3 of rectangle a
in Fig. 7d do not need a star network. Second, if a client
group has multiple bridge routers, only one needs to
participate in the star network. The other bridge routers can
be freed for future use. See the example in Fig. 7d. Since
both bridge routers b5 and b6 in rectangle b are associated
with client group G4, b6 is removed, i.e., freed, before
connecting b4 and b5 as a star topology. The result of local
adaptation, applied to Fig. 7a, is given in Fig. 7b.
Comparing Figs. 7b and 7d, we observe that global
adaptation achieves two goals, namely better end-to-end
delay and using less intergroup routers.
Global adaptation is triggered when network partitioning is about to occur at some client groups due to lack of
available free routers. We recall that each client group has a
bridge router that tracks the number of free routers for this
group. When this number drops below a predefined
threshold, i.e., in Algorithm 2, which is set to one free
router in our implementation, the corresponding bridge
router acts as a coordinate and broadcasts a message to all
the bridge routers in the network to initiate global
adaptation (optimization). Any bridge router receiving this
message replies its location and the number of locally
available free routers (if known) to the coordinating bridge
router. In addition, the coordinating bridge router also
needs to collect the information about all the intergroup
routers. To this end, we let each intergroup router piggybacks its identification and location in the reply message of
any bridge router. When the coordinator receives positive
replies from all the bridge routers, it proceeds to start the
adaptation process. It executes Algorithm 3 to construct the
hierarchical star network and generate the corresponding
assignment list. Each intergroup router is assigned to the
forwarding position in the hierarchical star tree that is
closest to its original location. This strategy reduces the
distances the intergroup routers must travel to their
positions in the new topology. For intergroup routers that
are not needed for the new topology, they can simply be
freed and divided among the client groups such that each
SHEN ET AL.: AUTONOMOUS MOBILE MESH NETWORKS
371
group has about a similar number of free routers. Once the
assignment list is ready, the coordinating bridge router
broadcasts this list to all the intergroup routers, which then
move to their designated positions in the hierarchical star
network. Those intergroup routers who do not find their
assignment change into the free mode and join the
designated group as free routers.
4 EVALUATION
We conduct extensive simulations, implemented via NS2
[19], to study the ability of AMMNET in adapting to the
dynamic movement of mobile clients and the data
forwarding efficiency of such networks. Our performance
evaluation compares the following network schemes:
Grid-mesh. This simple scheme employs a grid-based
square topology for the mobile mesh nodes. This
mobile mesh network follows the users by tracking
and following one randomly selected client. The
network maintains the same grid topology as it
moves over the application terrain.
AMMNET. This is our design of AMMNET, in which
routers adapt their locations using only locally
cached location information about some of the
bridge routers. Global adaptation is also performed
when the number of free routers at some user
groups drops below a predefined threshold.
Global-AMMNET. This is similar to the above
AMMNET, except that global adaptation is performed by a randomly selected bridge router
whenever any client moves out of the current
network coverage area.
Oracle. This is a centralized scheme that assumes
location information of all clients is available. The
routers can move to the assigned locations in the
network instantaneously without any moving delay.
This scheme is only used as a bound for the purpose
of performance comparison. Unlike AMMNET that
uses the locations of the bridge routers to approximate the distribution of the user groups in the
application terrain and constructs the R-tree
based on these routers accordingly, Oracle constructs
the R-tree using the exact locations of the mobile
users. When there are not enough available routers
to provide full connectivity for all the clients, this
scheme favors user groups (R-tree nodes) with a
higher density of clients.
Unless stated otherwise, we use the following default
values for the parameters. In each simulation, all clients
originate from a randomly selected initial region in the
terrain. These clients belong to several mobile groups. The
number of clients in each group follows a Zipf distribution.
Members of each user group demonstrate the following
group mobility pattern [6]: the group leader moves in
accordance to the random way-point mobility model with a
moving speed that is uniformly distributed with a mean of
2.5 m/s; and the group members follow the leader with
their own random local movements. There are 200 mesh
nodes; and we assume the AMMNETs are airborne, with
the flying wireless routers implemented using devices such
as quadrocopters [5]. Their flying speed, which is within the
Fig. 8. Impact of router speeds: 4
is sufficient to track mobile clients.
devices normal operating capability range is 10 m/s [5].
Their communication range is 150 m. However, since they
are flying at a height of 90 m, the coverage radius of each
router is reduced to 120 m on the ground. Each simulation
run continues for 120 time slots of 10 seconds each. In each
time slot, five pairs of clients are randomly selected to
transmit UDP traffic. Each router applies AODV to build its
routing table. The simulation results reported in this paper are
averaged over 20 simulation runs.
4.1
Performance of Network Coverage
We start by examining the performance of the network
coverage under different network scenarios as follows:
4.1.1 Impact of Router Moving Speed
We first determine how many clients can be covered by
mobile mesh nodes when the number of available mesh
nodes is not enough to cover all the clients in the simulation
terrain. To meet this constraint, we deploy only 100
available mesh nodes in this simulation. Each simulation
includes 100 clients classified into five mobile groups. We
vary the moving speed of routers from the mean speed of
clients to six times of the mean speed of clients. We note
that the number of routers might appear excessive for the
number of users in the network. However, the cost of the
network should be considered from the view point of
the area of the application terrain (not the number of users)
in the context of AMMNET. That is, substantially many
more routers would be required to provide the communication coverage for the entire application terrain, otherwise. Fig. 8 shows that the number of clients within the
coverage area decreases as the clients move away from their
initial locations over time. This is because AMMNET might
fail to track some missing clients if free routers cannot move
fast enough to navigate the assigned boundary segment.
Once AMMNET misses tracking some clients, it might not
be able to get back the control of those missing clients even
if there are still free routers. To keep tracking mobile clients,
the free routers need to move fast enough to navigate the
boundary before the missing clients move out of the radio
range of any point of the boundary. The figure shows that
AMMNET is able to efficiently utilize all free routers to
track mobile clients when the flying speed is four times of
the moving speed of clients.
4.1.2 Coverage Area Given a Finite Number of Routers
We next check how many clients can be served by different
comparison schemes under the same simulation setting, yet
372
IEEE TRANSACTIONS ON MOBILE COMPUTING, VOL. 13, NO. 2, FEBRUARY 2014
Fig. 9. Number of clients covered by mesh nodes. Routers in AMMNET
adapt their locations in accordance with client movement, and provide a
coverage comparable to the scheme that uses global location
information.
with the moving speed of routers fixed at 10 m/s, i.e., four
times of the client speed. Fig. 9 shows that AMMNET is able
to achieve coverage comparable to that of Oracle. The slight
increase in the performance gap for the last few time slots is
due to the failure in tracking some of the clients under
AMMNET, whereas Oracle always uses the up-to-date
location information of clients to recompute the topology
and, thereby, can best utilize all available routers. Oracle
sometimes performs worse because it selects the rectangle
with the most users as the initial covering point, which
might not guarantee the best coverage if all available
routers cannot provide a full coverage. The fixed grid-based
mesh, on the other hand, cannot optimally utilize available
routers and, hence, only covers a small subset of the clients.
4.1.3 Number of Routers Required to Provide Full
Coverage
In this study, we attempt to investigate how many routers
are required to achieve full coverage. To this end, we
assume an infinite number of mesh routers. We vary the
number of clients from 50 to 250, while still classifying all
clients into five groups. Fig. 10 shows the average number
of routers selected as the intra- or inter-routers to cover all
clients at the last 10 time slots. The figure shows that the
grid-based mesh requires 6.5 times as many routers as
AMMNET because it maintains a fixed topology and waste
many routers for the areas without any clients. AMMNET
does not perform global adaptation all the time to reclaim
all redundant intergroup routers, and therefore requires
more routers than Global-AMMNET does. On the other
hand, Oracle connects every client using an R-tree with
more layers, as compared to the R-tree only including
bridge routers in AMMNET, might require a few more
routers to cover the entire hierarchical topology.
The figure also shows that the number of required
mobile routers required to cover all the clients does not
increase with the increasing number of clients. This means
that AMMNET is scalable with increases in the number of
mesh clients if clients are partitioned into a limited number
of groups. Such results are expected because users belonging to the same group only require a few mobile mesh
routers to cover them and help forward their data. Instead,
scalability of AMMNET is limited only by the severity of
the network partition problem, i.e., not having enough
mobile mesh nodes to maintain intergroup connectivity
because the clients break into too many groups that move in
Fig. 10. Number of routers required to cover various numbers of clients.
AMMNET requires much fewer routers than a grid mesh. The number of
routers required to cover all clients is more related to the number of
groups, but less affected by the number of clients in the application
terrain.
different directions to occupy almost the entire application
terrain simultaneously. However, in practice, the number of
groups in the mobile applications considered in this paper is
typically small relative to the number of users, and hence, the
scalability is usually not a concern for this class of
applications. Therefore, it is possible that the dynamic
AMMNET framework could support even a larger number of
mobile users (say 1,000 users) if they are partitioned into only
a few number of groups.
4.1.4 Impact of Mobility Pattern on Network Coverage
We examine how well 200 routers can provide communication coverage for 200 clients when they are separated into
different numbers of groups. Figs. 11a and 11b plot the
number of clients located within the coverage area and the
number of routers used to provide the coverage, respectively, at the last 10 time slots. The figure indicates that a
fixed grid-mesh runs out of all available routers, but can only
cover less than 60 clients. By continuously tracking mobile
clients during the entire simulation period, AMMNET can
adapt the network topology to connect almost all the clients
all the time. The number of routers required to connect the
clients increases when clients are partitioned into more small
groups because more intergroup routers are organized as
network bridges to interconnect groups.
4.2
Performance of Data Forwarding
We next examine the throughput performance in a critical
environment, where the number of mesh nodes is not
sufficient to always provide full coverage. As a result, we
set the number of available routers to 125 because the result
in Fig. 10 shows that the number of routers required to
cover all clients is about 130 on average. In this simulation,
we also compare AMMNET with the traditional mobile ad
hoc network. Since MANET is not an infrastructure-based
network, we let each MANET user act as a mobile router,
which can transmit/receive its own data and also forward
data for other users. Each simulation includes 100 clients
partitioned into five mobility groups. Each router forwards
data at the transmission bit-rate of 11 Mb/s. From the 60th
to 90th time slots, we randomly select five pairs of nodes to
concurrently transmit UDP flows, each with a data rate of
800 Kb/s.
To isolate the impact of frequent route update on the
forwarding throughput, we measure the throughput of
SHEN ET AL.: AUTONOMOUS MOBILE MESH NETWORKS
373
Fig. 11. Impact of mobility patterns on network coverage. More routers
are required to cover all clients if they are partitioned into more small
groups.
Oracle only when the routing table in each router has been
reconfigured after each topology adaption. Nevertheless,
the throughputs of all the other schemes are measured for
the entire duration of the simulation to evaluate how they
are affected by dynamic topology and route reconfiguration. Fig. 12a shows the average throughput of all the
traffic given various numbers of mesh nodes. 1 The figure
shows that the average throughput obtained in AMMNET
is about 33 percent higher than that in the grid-based mesh.
This is due to the fact that some source-destination pairs in
the grid-based mesh are not served by any routers and data
could not be delivered. AMMNET can achieve a throughput about 70 percent of that of the Oracle scheme. The
performance gap comes from the slightly longer relay
paths, and, more deterministically, the packet loss due to
route reconfiguration. More specifically, when mesh nodes
adapt their locations to client movements, each router
cannot relay data along the previous relay paths and needs
to discover new routes. Some packets buffered in the
original routing paths might be dropped, resulting in
throughput degradation. Moreover, the throughput of
MANET is far lower than that of AMMNET. This is to be
expected because, when the network is partitioned into
multiple groups, a MANET source destination pair might
not be able to find a path to communicate with each other
when they belong to two partitioned groups, as a result
leading to a zero throughput. This situation is quite
common in a dynamic environment, where users are
1. We plot the throughput of MANET as a straight line because the
number of routers in MANET equals the number of users.
Fig. 12. Throughput Comparison. Throughput gap between schemes is
mainly caused by three factors: 1) coverage area, 2) relay path length,
and 3) update frequency of routing paths, which is closely related to
changes in network topology.
highly mobile in a large application terrain. These results
also confirm the need of designing a new mobile infrastructure that can cope with topology changes (network
partitions and merges) in highly dynamic applications such
as crisis management and battlefield communications.
The results with various client moving speeds in
Fig. 12b also support the same statement. In particular,
since we measure the throughput of Oracle, as a comparison bound, only when the routing paths are stabilized, the
throughput of Oracle is not affected much by the moving
speed. On the contrary, the throughput in AMMNET and
Global-AMMNET degrades gradually when the moving
speed increases. This is also why AMMNET outperforms
Global-AMMNET under lower speeds and the grid mesh
374
IEEE TRANSACTIONS ON MOBILE COMPUTING, VOL. 13, NO. 2, FEBRUARY 2014
Fig. 13. Average Relay Hop Count. The average relay path length in
AMMNET is only 0.6 hop more than that in the deployment scheme
using global location information.
Fig. 14. Message exchange overhead. AMMNET exploits data forwarding opportunities to collect location information of bridge routers, and
therefore requires a small message overhead.
tolerates higher moving speeds. Finally, Fig. 12c shows
that, in general, the throughput of each source-destination
pair decreases when there are more contending flows;
however, the performance of all schemes follows a similar
trend discussed above.
We further evaluate the forwarding latency in terms of
the number of relay hops required to forward a packet.
Fig. 13 shows the average hop count of traffic pairs. Since
the grid-based mesh might not be able to cover all clients,
for fair comparison, we remove it from this comparison.
The results reveal that even though AMMNET uses location
information of only some representative bridge routers to
adapt the topology, it provides an average path length only
0.6 hop longer than Oracle, which uses the global map of
user locations to build a near-optimized mesh.
4.3
System Overhead
To perform network adaptations, a node needs to collect
location information of the bridge routers, and multicast the
assigned locations to the selected intergroup routers. In this
study, we evaluate the number of exchanged messages
required for such an adaptation process. Here, each
message forwarding over a wireless link is counted as a
message exchange. We consider a network with 100 users
and 200 routers. The Grid-Mesh schemes are excluded in
this study because each mesh node only needs to notify its
updated location to it neighboring nodes. Namely, in GridMesh, the message overhead is independent of the number
of groups in a terrain.
Fig. 14 shows the average number of message exchanges
per time slot. This message overhead increases with the
number of groups, i.e., the number of intergroup routers
along the bridging networks. Oracle requires a high message
overhead to collect location information from all routers
designated to track mobile clients. In contrast, AMMNET
takes advantage of data forwarding opportunities to collect
partial location information. It incurs only a few message
overheads in collecting the location information for the
computation of the assignment list. Global-AMMNET
requires a few more messages than AMMNET because
Global-AMMNET needs to query all bridge routers for their
location information. Such a small overhead, as compared to
Oracle, however helps build a topology that provides a
coverage and throughput performance comparable to those
of Oracle.
RELATED WORK
We classify the works related to AMMNET into three
categories: 1) stationary wireless mesh networks: AMMNET
is a new type of mesh networks, but supports dynamic
topology adaptation, 2) sensor covering: the techniques
for sensor covering is related to the design of covering
mobile clients in AMMNET, and 3) location tracking:
tracking mobile clients in AMMNET is an application of
location tracking.
Stationary wireless mesh networks. In the last few years,
stationary wireless mesh networks have been developed to
enable last-mile wireless broadband access [20]. Past work
on stationary mesh networks focuses on routing traffic in a
mesh topology to best utilize the network capacity [21], [22].
Some literatures further study how to utilize nonoverlapping channels [23], [24], [25] and explicitly control the
network topology [26], [27] to improve the network capacity
of a stationary mesh. Our work builds on the concept of
such a stationary mesh-based infrastructure, and extends it
to enable communication among partitioned mobile clients.
We study dynamic deployment of an AMMNET in this
work, and leave utilizing nonoverlapping channels to
improve network capacity as our future study.
Sensor covering. Our work on router deployment is also
related to recent work on sensor covering in a stationary
sensor network [28], [29], [30]. These schemes ensure that
each point in a target field is in the interior of at least k
different sensors. Several work [31], [32], [33] further takes
energy efficiency into account, and assigns each sensor a
sleep-active schedule to guarantee sensor cover and, at the
same time, prolong the lifetime of a sensor network. More
recently, some work exploits sensor mobility to improve the
performance of sensor covering. A self-deployment protocol is proposed in [34] to enable randomly scattered sensors
to automatically move to the target planned positions.
Instead of deploying stationary sensor nodes to cover the
entire monitoring field, an alternative is proposed in [35],
[36] to use mobile mules to move around different monitoring areas and gather data along the traversed paths. All the
above studies focus on deploying sensor nodes to monitor a
given target area. Our work differs from the sensor
coverage schemes in that it builds a dynamic mesh
infrastructure for mobile clients that have unpredictable
moving patterns and move around a nonpredefined
application terrain.
SHEN ET AL.: AUTONOMOUS MOBILE MESH NETWORKS
Location tracking. On the other hand, there is much work
that has been done on the problem of tracking the geometric
location of a mobile node. Most of the localization
technologies [37], [38], [39], [40] measure the distance
between nodes and use this range information to estimate
the location of a client. Some other range-free schemes [41],
[42] only use node connectivity and hop-count information
to estimate node locations without explicitly measuring
every link distance. Compared to those localization schemes
designed to minimize the estimation error of node locations,
an AMMNET only needs to track mobile clients, and does
not require the exact location information of each client.
These localization technologies, however, can be integrated
with AMMNET to improve the accuracy of client tracking.
375
100-2221-E-001-005-MY2, Academia Sinica of R.O.C. under
project No. AS-101-TP2-A10, and the US National Science
Foundation under Grant Number 0917082. Any opinions,
findings, and conclusions or recommendations expressed in
this material are those of the authors and do not necessarily
reflect the views of the National Science Council of R.O.C.,
Academia Sinica of R.O.C., or the US National Science
Foundation.
REFERENCES
[1]
[2]
[3]
6 CONCLUSION
For applications such as crisis management and battlefield
communications, the mobile users need to work in
dynamically formed groups that occupy different parts of
a large and uncertain application terrain at different times.
There is currently no cost-effective solution for such
applications. Since the user groups occupy only a small
portion of the terrain at any one time, it is not justifiable to
deploy an expensive infrastructure to provide network
coverage for the entire application terrain at all time. Other
challenges are due to the potentially hostile environment
and the uncertainty in how the application terrain unfolding with time. In this paper, we introduced a mobile
infrastructure called AMMNET. Unlike conventional mobile ad hoc networks that suffer network partitions when
the user groups move apart, the mobile mesh routers of an
AMMNET track the users and dynamically adapt the
network topology to seamlessly support both their intragroup and intergroup communications. Since this mobile
infrastructure follows the users, full connectivity can be
achieved without the need and high cost of providing
network coverage for the entire application terrain at all
time as in traditional stationary infrastructure.
We conducted extensive simulation study to assess
the effectiveness of AMMNET. The results confirm that
the proposed distributed topology adaptation scheme
based on autonomous mobile mesh routers is almost as
effective as a hypothetical centralized technique with
complete knowledge of the locations of the mobile clients.
The simulation results also indicate that AMMNET is
scalable with the number of users. The required number of
mobile mesh nodes does not increase with increases in the
user population. Although an excessively large number of
user groups may affect the performance of AMMNET, the
number of user groups is typically very small relative to the
number of users for most applications and AMMNET is
effective for most practical scenarios. There are still many
interesting issues not yet examined in our study such as
searching for disappearing mobile clients, minimizing
routing paths, and utilizing nonoverlapping channels.
We leave these changes for future research.
ACKNOWLEDGMENTS
This material is based on work partially supported by the
National Science Council of R.O.C. under contract No. NSC
[4]
E. Dahlman, S. Parkvall, and J. Skold, 4G LTE/LTE-Advanced for
Mobile Broadband. Academic, 2011.
L. Nuaymi, WiMAX: Technology for Broadband Wireless Access. John
Wiley & Sons, 2007.
K. Fall, A Delay-Tolerant Network Architecture for Challenged
Internets, Proc. ACM Special Interest Group on Data Comm., 2003.
A. Petkova, K.A. Hua, and S. Koompairojn, Processing Approximate Rank Queries in a Wireless Mobile Sensor Environment,
Proc. 11th Intl Conf. Mobile Data Management (MDM), 2010.
[5] Quadrocopter LLC, http://quadrocopter.us/, 2013.
[6] R. Roy, Handbook of Mobility Models and Mobile Ad Hoc Networks.
Springer, 2010.
[7] Y.-C. Chen, E. Rosensweig, J. Kurose, and D. Towsley, Group
Detection in Mobility Traces, Proc. Sixth Intl Wireless Comm. and
Mobile Computing Conf. (IWCMC 10), 2010.
[8] T. Camp, J. Boleng, and V. Davies, A Survey of Mobility Models
for Ad Hoc Network Research, Wireless Comm. and Mobile
Computing, vol. 2, no. 5, pp. 483-502, 2002.
[9] X. Hong, M. Gerla, G. Pei, and C. Chiang, A Group Mobility
Model for Ad Hoc Wireless Networks, Proc. Second ACM Intl
Workshop Modeling, Analysis and Simulation of Wireless and Mobile
Systems (MSWiM 99), 1999.
[10] K. Blakely and B. Lowekamp, A Structured Group Mobility
Model for the Simulation of Mobile Ad Hoc Networks, Proc.
Second Intl Workshop Mobility Management & Wireless Access
Protocols (MobiWac), 2004.
[11] Y. Zhang and Y. Fang, ARSA: An Attack-Resilient Security
Architecture for Multihop Wireless Mesh Networks, IEEE
J. Selected Areas in Comm., vol. 24, no. 10, pp. 1916-1928, Oct. 2006.
[12]
J. Sun, C. Zhang, and Y. Fang, A Security Architecture Achieving
Anonymity and Traceability in Wireless Mesh Networks, Proc.
IEEE INFOCOM, 2008.
[13] B. Salem and J. Hubaux, Securing Wireless Mesh Networks,
IEEE Wireless Comm., vol. 13, no. 2, pp. 50-55, Apr. 2006.
[14]
T. Shuai and X. Hu, Connected Set Cover Problem and Its
Applications, Proc. Second Intl Conf. Algorithmic Aspects in
Information and Management, pp. 243-254, 2006.
[15] R. Gandhi, S. Khuller, and A. Srinivasan, Approximation
Algorithms for Partial Covering Problems, Proc. 28th Intl
Colloquium Automata, Languages and Programming, pp. 225-236,
2001.
[16] A. Guttman, R-Trees: A Dynamic Index Structure for Spatial
Searching, Proc. ACM SIGMOD Intl Conf. Management of Data
(SIGMOD), 1984.
[17] J. MacQuene, Some Methods for Classification and Analysis of
Multivariate Observations, Proc. Fifth Berkeley Symp. Math.
Statistics and Probability, 1967.
[18] B. Frey and D. Bueck, Clustering by Passing Messages between
Data Points, Science, vol. 315, no. 5814, pp. 972-976, 2007. [19] The
Network Simulator - ns-2, http://www.isi.edu/nsnam/ns,
2013.
[20] I.F. Akyildiz, X. Wang, and W. Wang, Wireless Mesh Networks:
A Survey, Computer Networks, vol. 47, no. 4, pp. 445-487, 2005.
[21]
R. Draves, J. Padhye, and B. Zill, Comparison of Routing Metrics
for Static Multi-Hop Wireless Networks, Proc. ACM SIGCOMM,
2004.
[22] R. Draves, J. Padhye, and B. Zill, Routing in Multi-Radio, MultiHop Wireless Mesh Networks, Proc. ACM MobiCom, 2004.
[23]
A. Raniwala and T.-C. Chiueh, Architecture and Algorithms for
an IEEE 802.11-Based Multi-Channel Wireless Mesh Network,
Proc. IEEE INFOCOM, 2005.
[24] M. Alicherry, R. Bhatia, and L.E. Li, Joint Channel Assignment
and Routing for Throughput Optimization in Multi-Radio Wireless Mesh Networks, Proc. ACM MobiCom, 2005.
376
IEEE TRANSACTIONS ON MOBILE COMPUTING, VOL. 13, NO. 2, FEBRUARY 2014
[25] K.N. Ramachandran, E.M. Belding, K.C. Almeroth, and M.M.
Buddhikot, Interference-Aware Channel Assignment in MultiRadio Wireless Mesh Networks, Proc. IEEE INFOCOM, 2006.
[26] J. Tang, G. Xue, and W. Zhang, Interference-Aware Topology
Control and QoS Routing in Multi-Channel Wireless Mesh
Networks, Proc. ACM MobiHoc, 2005.
[27] A. Naveed, S. Kanhere, and S. Jha,
Topology Control and
Channel Assignment in Multi-Radio Multi-Channel Wireless
Mesh Networks, Proc. IEEE Intl Conf. Mobile Adhoc and Sensor
Systems (MASS), 2007.
[28] S. Meguerdichian, F. Koushanfar, M. Potkonjak, and M. Srivastava, Coverage Problems in Wireless Ad-Hoc Sensor Networks,
Proc. IEEE INFOCOM, 2001.
[29] C.-F. Huang and Y.-C. Tseng,
The Coverage Problem in a
Wireless Sensor Network, Mobile Networks and Applications,
vol. 10, pp. 519-528, Aug. 2005.
[30] Y. Bejerano, Simple and Efficient k-Coverage Verification without Location Information, Proc. IEEE INFOCOM, 2008.
[31] X. Wang, G. Xing, Y. Zhang, C. Lu, R. Pless, and C. Gill,
Integrated Coverage and Connectivity Configuration in Wireless
Sensor Networks, Proc. ACM First Intl Conf. Embedded Networked
Sensor Systems (SenSys), 2003.
[32] S. Kumar, T.H. Lai, and J. Balogh, On k-Coverage in a Mostly
Sleeping Sensor Network, Proc. ACM MobiCom, 2004.
[33] G.S. Kasbekar, Y. Bejerano, and S. Sarkar, Lifetime and Coverage
Guarantees through Distributed Coordinate-Free Sensor Activation, Proc. ACM MobiCom, 2009.
[34] G. Wang, G. Cao, and T.F.L. Porta, Movement-Assisted Sensor
Deployment, IEEE Trans. Mobile Computing, vol. 5, no. 6, pp. 640652, June 2006.
[35] B. Liu, P. Brass, O. Dousse, P. Nain, and D. Towsley, Mobility
Improves Coverage of Sensor Networks, Proc. ACM MobiHoc,
2005.
[36] R. Sugihara and R.K. Gupta, Optimal Speed Control of Mobile
Node for Data Collection in Sensor Networks, IEEE Trans. Mobile
Computing, vol. 9, no. 1, pp. 127-139, Jan. 2010.
[37] A. Savvides, C.-C. Han, and M.B. Strivastava, Dynamic FineGrained Localization in Ad-Hoc Networks of Sensors, Proc. ACM
MobiCom, 2001.
[38] C. Savarese, J.M. Rabaey, and K. Langendoen, Robust Positioning
Algorithms for Distributed Ad-Hoc Wireless Sensor Networks,
Proc. USENIX Ann. Technical Conf., 2002.
[39] J. Liu, Y. Zhang, and F. Zhao,
Robust Distributed Node
Localization with Error Management, Proc. ACM MobiHoc, 2006.
[40] H.T. Kung, C.-K. Lin, T.-H. Lin, and D. Vlah, Localization with
Snap-Inducing Shaped Residuals (SISR): Coping with Errors in
Measurement, Proc. ACM MobiCom, 2009.
[41] T. He, C. Huang, B.M. Blum, J.A. Stankovic, and T. Abdelzaher,
Range-Free Localization Schemes for Large Scale Sensor Networks, Proc. ACM MobiCom, 2003.
[42] Y. Shang, W. Rumi, Y. Zhang, and M. Fromherz, Localization
from Connectivity in Sensor Networks, IEEE Trans. Parallel and
Distributed Systems, vol. 15, no. 11, pp. 961-974, Nov. 2004.
Wei-Liang Shen received the BS degree from
National Central University, Taiwan, in 2008 and
the MS degree from National Taiwan University,
Taiwan, in 2010. He is working toward the PhD
degree at National Taiwan University. He is
currently a research assistant at the Research
Center for IT Innovation at Academia Sinica,
Taiwan. His current research interests include
multiuser MIMO systems, multimedia networking, and wireless systems.
Chung-Shiuan Chen received the BS and MS
degrees from the Department of Computer and
Communication Engineering, National Kaohsiung First University of Science and Technology,
in June 2000 and June 2002, respectively. He
received the PhD degree from the Department of
Computer Science and Information Engineering,
National Central University, Taiwan. His research
interests include content adaptation, wireless
networks, and artificial intelligence.
Kate Ching-Ju Lin received the BS degree from
National Tsing Hua University, Taiwan, in 2003
and the PhD degree from National Taiwan
University in 2009. She was a visiting scholar
at CSAIL, MIT, in 2007. After her graduation,
she joined the Research Center for IT Innovation
at Academia Sinica, Taiwan. She is currently an
assistant research fellow. Her current research
interests include multiuser MIMO networks,
wireless systems, multimedia networking, and
mobile social networks.
Kien A. Hua received the BS degree in
computer science and the MS and PhD degrees
in electrical engineering all from the University of
Illinois at Urbana-Champaign. He is a professor
of computer science and the director of the Data
Systems Lab at the University of Central Florida
(UCF). He served as the associate dean for
Research of the College of Engineering and
Computer Science at UCF. Before joining the
university, he was a lead architect at IBM MidHudson Lab, where he helped develop a highly parallel computer
system, the precursor to the highly successful commercial parallel
computer known as SP2. His diverse expertise includes network and
wireless communications, image/video computing, sensor networks,
medical imaging, databases, mobile computing, and intelligent transportation systems. He has published widely, with more than 10 papers
recognized as best/top papers at conferences and a journal. Many of his
researches have had significant impact on society. His Chaining
technique started the peer-to-peer video streaming paradigm. His
Skyscraper Broadcasting, Patching, and Zigzag techniques have been
heavily cited in the literature and have inspired many commercial
systems in use today. He has served as a conference chair, an
associate chair, and a technical program committee member of
numerous international conferences, as well as on the editorial boards
of a number of professional journals. He is a fellow of the IEEE.
. For more information on this or any other computing topic,
please visit our Digital Library at www.computer.org/publications/dlib.
S-ar putea să vă placă și
- For Data AnalysisDocument3 paginiFor Data AnalysisAdd KÎncă nu există evaluări
- Docshare - Tips - Comparative Study of Hero Honda Vs Bajaj Bikes PDFDocument77 paginiDocshare - Tips - Comparative Study of Hero Honda Vs Bajaj Bikes PDFAdd KÎncă nu există evaluări
- Q1. Are You Smartphone User?Document5 paginiQ1. Are You Smartphone User?Add KÎncă nu există evaluări
- Job Analysis, Job Design and Quality of Work LifeDocument13 paginiJob Analysis, Job Design and Quality of Work LifeAdd KÎncă nu există evaluări
- Consumer PerceptionDocument19 paginiConsumer PerceptionAdd KÎncă nu există evaluări
- Civil Aviation Policy in India - A Critical AnalysisDocument15 paginiCivil Aviation Policy in India - A Critical AnalysisAdd KÎncă nu există evaluări
- Research Paper: Zero Defects'' Mentality), But To Keep Do More. Doing More'' Suggests TheDocument9 paginiResearch Paper: Zero Defects'' Mentality), But To Keep Do More. Doing More'' Suggests TheAdd KÎncă nu există evaluări
- Lva1 App6891 PDFDocument92 paginiLva1 App6891 PDFAdd KÎncă nu există evaluări
- Supplier Assessment QuestionnaireDocument3 paginiSupplier Assessment QuestionnaireAdd KÎncă nu există evaluări
- Serial No. Title Page No. Chapter-1 6-7 1 Chapter-2 8-9 2.1 2.2 2.3 Chapter-3 10-21 3 Chapter-4 22-37 4. Chapter-5 38-56 5Document69 paginiSerial No. Title Page No. Chapter-1 6-7 1 Chapter-2 8-9 2.1 2.2 2.3 Chapter-3 10-21 3 Chapter-4 22-37 4. Chapter-5 38-56 5Add KÎncă nu există evaluări
- Big Data Survey QuestionnaireDocument9 paginiBig Data Survey QuestionnaireAdd K100% (2)
- Grit: The Power of Passion and PerseveranceDe la EverandGrit: The Power of Passion and PerseveranceEvaluare: 4 din 5 stele4/5 (588)
- The Yellow House: A Memoir (2019 National Book Award Winner)De la EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Evaluare: 4 din 5 stele4/5 (98)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeDe la EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeEvaluare: 4 din 5 stele4/5 (5795)
- Never Split the Difference: Negotiating As If Your Life Depended On ItDe la EverandNever Split the Difference: Negotiating As If Your Life Depended On ItEvaluare: 4.5 din 5 stele4.5/5 (838)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceDe la EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceEvaluare: 4 din 5 stele4/5 (895)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersDe la EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersEvaluare: 4.5 din 5 stele4.5/5 (345)
- Shoe Dog: A Memoir by the Creator of NikeDe la EverandShoe Dog: A Memoir by the Creator of NikeEvaluare: 4.5 din 5 stele4.5/5 (537)
- The Little Book of Hygge: Danish Secrets to Happy LivingDe la EverandThe Little Book of Hygge: Danish Secrets to Happy LivingEvaluare: 3.5 din 5 stele3.5/5 (400)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureDe la EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureEvaluare: 4.5 din 5 stele4.5/5 (474)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryDe la EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryEvaluare: 3.5 din 5 stele3.5/5 (231)
- On Fire: The (Burning) Case for a Green New DealDe la EverandOn Fire: The (Burning) Case for a Green New DealEvaluare: 4 din 5 stele4/5 (74)
- The Emperor of All Maladies: A Biography of CancerDe la EverandThe Emperor of All Maladies: A Biography of CancerEvaluare: 4.5 din 5 stele4.5/5 (271)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaDe la EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaEvaluare: 4.5 din 5 stele4.5/5 (266)
- The Unwinding: An Inner History of the New AmericaDe la EverandThe Unwinding: An Inner History of the New AmericaEvaluare: 4 din 5 stele4/5 (45)
- Team of Rivals: The Political Genius of Abraham LincolnDe la EverandTeam of Rivals: The Political Genius of Abraham LincolnEvaluare: 4.5 din 5 stele4.5/5 (234)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyDe la EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyEvaluare: 3.5 din 5 stele3.5/5 (2259)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreDe la EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreEvaluare: 4 din 5 stele4/5 (1091)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)De la EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Evaluare: 4.5 din 5 stele4.5/5 (121)
- Her Body and Other Parties: StoriesDe la EverandHer Body and Other Parties: StoriesEvaluare: 4 din 5 stele4/5 (821)
- How To Install Owncloud 9 On Centos 7Document10 paginiHow To Install Owncloud 9 On Centos 7vqbhanuÎncă nu există evaluări
- Computer NetworkDocument49 paginiComputer NetworkP.s. Dhiman60% (5)
- Anycast: User ManualDocument6 paginiAnycast: User ManualMladen MilicevicÎncă nu există evaluări
- Wireless Datagram Protocol (WDP)Document3 paginiWireless Datagram Protocol (WDP)Gunasekaran PÎncă nu există evaluări
- Assignment 1Document4 paginiAssignment 1akttripathiÎncă nu există evaluări
- CCNAS Chp4 PTActC Zone Based Policy Firewall InstructorDocument5 paginiCCNAS Chp4 PTActC Zone Based Policy Firewall InstructorilhamdaniÎncă nu există evaluări
- NN48500 PDFDocument137 paginiNN48500 PDFvsaraÎncă nu există evaluări
- SPA Navi GetallDocument691 paginiSPA Navi Getallredhot321Încă nu există evaluări
- Configuring ASA Basic Settings and Firewall Using CLIDocument16 paginiConfiguring ASA Basic Settings and Firewall Using CLIGiovanny DíazÎncă nu există evaluări
- Akses Kontrol ContohDocument53 paginiAkses Kontrol ContohnyintÎncă nu există evaluări
- Data CentersDocument30 paginiData Centersapi-364049439Încă nu există evaluări
- BTS BSC Alarms and Troubleshuting - MotorolaDocument9 paginiBTS BSC Alarms and Troubleshuting - MotorolaArjun AslekarÎncă nu există evaluări
- WebFMC ManualDocument22 paginiWebFMC ManualJose Manuel VidalÎncă nu există evaluări
- Huawei B2368Document10 paginiHuawei B2368Anthony Fernandez MendezÎncă nu există evaluări
- Digital Communication in BusinessDocument69 paginiDigital Communication in BusinessNelzen GarayÎncă nu există evaluări
- DDOS 5 1 0 9 ReleaseNotes 765-0009-0018Document31 paginiDDOS 5 1 0 9 ReleaseNotes 765-0009-0018ParthiÎncă nu există evaluări
- Cube Notes For DNSDocument17 paginiCube Notes For DNSoli_via_roÎncă nu există evaluări
- Monitoring VMware With Nagios XIDocument2 paginiMonitoring VMware With Nagios XIalfonso-camachoÎncă nu există evaluări
- Aci Apic - Learn Work ItDocument12 paginiAci Apic - Learn Work Itravi kantÎncă nu există evaluări
- Solutions For Enterprise Communications: Nortel Networks Meridian 1 Option 61C, 81C Communication SystemsDocument2 paginiSolutions For Enterprise Communications: Nortel Networks Meridian 1 Option 61C, 81C Communication Systemssagar323Încă nu există evaluări
- 3GPP TS 21.101Document15 pagini3GPP TS 21.101mhanslÎncă nu există evaluări
- HCL Leap v9.2 Installation GuideDocument6 paginiHCL Leap v9.2 Installation GuideLuisÎncă nu există evaluări
- Subnetting: Historic Network ClassesDocument9 paginiSubnetting: Historic Network ClassesLicio LentimoÎncă nu există evaluări
- Pembelajaran SosialDocument604 paginiPembelajaran Sosialkokom GamingÎncă nu există evaluări
- Technical Note - Loading FortiGate Firmware Image Using TFTPDocument4 paginiTechnical Note - Loading FortiGate Firmware Image Using TFTPMohit SharmaÎncă nu există evaluări
- Junior NAT AtualizadoDocument591 paginiJunior NAT AtualizadoAwday RuanÎncă nu există evaluări
- ECEN 5823 IoT Embedded FirmwareDocument4 paginiECEN 5823 IoT Embedded FirmwareMehul PatelÎncă nu există evaluări
- SansDocument1.013 paginiSansSajjad AkramÎncă nu există evaluări
- Meghdoot ManualDocument5 paginiMeghdoot ManualJai SharmaÎncă nu există evaluări
- Cisco Learning Web LABS TrainingDocument17 paginiCisco Learning Web LABS Trainingnea317Încă nu există evaluări