Documente Academic
Documente Profesional
Documente Cultură
UGC NET Computer Science and Applications Paper II Dec 05
Încărcat de
adityaDrepturi de autor
Formate disponibile
Partajați acest document
Partajați sau inserați document
Vi se pare util acest document?
Este necorespunzător acest conținut?
Raportați acest documentDrepturi de autor:
Formate disponibile
UGC NET Computer Science and Applications Paper II Dec 05
Încărcat de
adityaDrepturi de autor:
Formate disponibile
Downloaded from: http://www.upscportal.
com
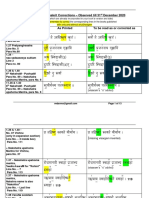
Signature and Name of Invigilator
Answer Sheet No. : ................................................
(To be filled by the Candidate)
1. (Signature)
Roll No.
(Name)
(In figures as per admission card)
Roll No.
2. (Signature)
(In words)
(Name)
Test Booklet No.
D8 7 0 5
PAPERII
COMPUTER APPLICATIONS
Time : 1 hours]
Number of Pages in this Booklet : 8
[Maximum Marks : 100
Number of Questions in this Booklet : 50
Instructions for the Candidates
1.
Write your roll number in the space provided on the top of this
page.
1. U DU U S U UU U
2.
This paper consists of fifty multiple-choice type of questions.
3. U U U, -S U U U
3.
At the commencement of examination, the question booklet
will be given to you. In the first 5 minutes, you are requested
to open the booklet and compulsorily examine it as below :
(i)
4.
2. -
-S
U
To have access to the Question Booklet, tear off the paper
seal on the edge of this cover page. Do not accept a
booklet without sticker-seal and do not accept an open
booklet.
-S U U
U U SUU-U S
SU U
(ii)
U DU U U U -S DU
U U U U U U S
DU / U UU
U U S SU U
UUU S U U -S
U U
-S U
UQ
(ii)
Tally the number of pages and number of questions in
the booklet with the information printed on the cover
page. Faulty booklets due to pages/questions missing
or duplicate or not in serial order or any other
discrepancy should be got replaced immediately by a
correct booklet from the invigilator within the period of
5 minutes. Afterwards, neither the question booklet
will be replaced nor any extra time will be given.
(iii)
After this verification is over, the Serial No. of the booklet
should be entered in the Answer-sheets and the Serial
No. of Answer Sheet should be entered on this Booklet.
(iii) -S R U- U
Each item has four alternative responses marked (A), (B), (C)
and (D). You have to darken the oval as indicated below on the
correct response against each item.
4. U U (A), (B), (C) (D)
Example :
U UU U- R -S U U
U UU U
where (C) is the correct response.
Your responses to the items are to be indicated in the Answer
Sheet given inside the Paper I booklet only. If you mark at
any place other than in the ovals in the Answer Sheet, it will
not be evaluated.
6.
Read instructions given inside carefully.
7.
Rough Work is to be done in the end of this booklet.
8.
If you write your name or put any mark on any part of the test
booklet, except for the space allotted for the relevant entries,
which may disclose your identity, you will render yourself
liable to disqualification.
5. U U I U U- U
U U U
S U U U , U
6. U U
7. (Rough Work) S DU U U
8. U-S U
, U U U
U
9. U # U U-S U UU
U U # U U
U
You have to return the test question booklet to the invigilators
at the end of the examination compulsorily and must not carry
it with you outside the Examination Hall.
/ U ZU S U
U (UU) U U
12. U U
10.
10. Use only Blue/Black Ball point pen.
11.
11. Use of any calculator or log table etc., is prohibited.
12. There is NO negative marking.
D8705
(C) U
5.
9.
(i)
www.upscportal.com
P.T.O.
Downloaded from: http://www.upscportal.com
Computer Science and Applications
PAPERII
Note :
1.
2.
3.
4.
This paper contains fifty (50) objective-type questions, each question carrying
two (2) marks. Attempt all of them.
T is a graph with n vertices. T is connected and has exactly n-1 edges, then :
(A)
T is a tree
(B)
T contains no cycles
(C)
Every pairs of vertices in T is connected by exactly one path
(D)
All of these
If the proposition 7 P Q is true, then the truth value of the proportion 7 PV (P Q)
is :
(A)
True
(B)
Multi - Valued
(C)
Flase
(D)
Can not determined
Let A and B be two arbitrary events, then :
(A)
P(A B) 5 P(A) P (B)
(B)
P(P B) 5 P(A) 1P (B)
(C)
P(A B) [ P(A) 1P (B)
(D)
P(A/B) 5 P(A B) 1P (B)
Which sentence can be generated by S d/bA, A d/ccA :
(A)
5.
7.
(B)
aabccd
(C)
ababccd
(D)
abbbd
{a, b}
(D)
None of these
Regular expression a1b denotes the set :
(A)
6.
bccddd
{a}
(B)
{e, a, b}
(C)
Which of the following is divisible by 4 ?
(A)
100101100
(B)
1110001110001
(C)
11110011
(D)
10101010101010
A half-adder is also known as :
(A)
AND Circuit
(B)
NAND Circuit
(C)
NOR Circuit
(D)
EX-OR Circuit
D8705
www.upscportal.com
Downloaded from: http://www.upscportal.com
8.
Consider the following sequence of instructions :
a5a b, b5a b, a5b a This Sequence
9.
(A)
retains the value of the a and b
(B)
complements the value of a and b
(C)
swap a and b
(D)
negates values of a and b
Consider the following circuit :
to make it a Tautology the
(A)
10.
11.
NAND gate
(B)
should be :
AND gate
(C)
OR gate
(D)
EX-OR gate
When an inventor is placed between both inputs of an S-R flip flop, the resulting flip
flop is :
(A)
JK flip-flop
(B)
D-flip-flop
(C)
T flip-flop
(D)
None of these
What is the output of the following C-program main () :
{print f(''%d%d%d'', size of (3.14f), size of (3.14), size of (3.141));}
(A)
12.
14.
(B)
4 8 10
(C)
848
(D)
888
(C)
42
(D)
39
The bitwise OR of 35 with 7 in C will be :
(A)
13.
444
35
(B)
Data members and member function of a class by default is repectively :
(A)
private and public
(B)
public
(C)
public and private
(D)
private
Function over loading done at :
(A)
Runtime
(B)
Compile time
(C)
Linking time
(D)
Switching from function to function
D8705
www.upscportal.com
P.T.O.
Downloaded from: http://www.upscportal.com
15.
What will be the value of i for the following expression :
int i511, i53 ;
i15(f >3) ? i & 2:5 ;
(A)
16.
17.
18.
20.
21.
22.
(B)
(C)
13
(D)
12
(D)
All the above
A schema describes :
(A)
data elements
(B)
records and files
(C)
record relationship
(D)
all of the above
One approach to standarolizing storing of data :
(A)
MIS
(B)
CODASYL
(C)
Structured Programing
(D)
None of the above
In a relational schema, each tuple is divided in fields called :
(A)
19.
Relations
(B)
Domains
(C)
Queries
An embedded printer provides :
(A)
Physical record key
(B)
An inserted Index
(C)
A secondary access path
(D)
All the above
A locked file can be :
(A)
accessed by only one user
(B)
modified by users with the correct possword
(C)
is used to hide sensitive imformation
(D)
both (B) and (C)
In what tree, for every node the height of its left subtree and right subtree differ at least
by one :
(A)
Binary search tree
(B)
AVL - tree
(C)
Threaded binary tree
(D)
Complete tree
A hash function f defined as f(key)5key mod 7, with linear probing it is used to insert
the key 37,38,72,48,98,11,56 into a table index from 0 to 6. What will be the locations
of 11 :
(A)
D8705
(B)
(C)
www.upscportal.com
(D)
Downloaded from: http://www.upscportal.com
23.
Consider the graph, which of the following is a valid topological sorting ?
(A)
24.
25.
26.
30.
BADC
(D)
(B)
3 deletions, 2 additions
(C)
3 deletions, 4 additions
(D)
3 deletions, 3 additions
ABDC
Which traversal techniques lists the nodes of a binary search tree in ascending order ?
(A)
post - order
(B)
in - order
(C)
pre - order
(D)
linear - order
The data unit in the TCP/IP application Layer is called a __________ .
message
(B)
segment
(C)
datagram
(D)
frame
(D)
HTTP
Which of following file retrieval methods use hypermedia ?
HTML
(B)
Veronica
(C)
WAIS
Which of following is an example of a client - server model :
DNS
(B)
FTP
(C)
TELNET
(D)
All the above
__________ provide a method to recover data that has been delivered but not get
used :
(A)
Segmentation
(B)
Concatenation
(C)
Transalation
(D)
Synchronization
Encryption and decryption are the functions of the __________ layer of OSI model :
(A)
31.
(C)
2 deletions, 3 additions
(A)
29.
BACD
(A)
(A)
28.
(B)
The initial configuration of quaue is a, b, c, d. a is at the front. To get the configuration
d, c, b, a how many deletions and additions required :
(A)
27.
ABCD
transport
(B)
session
(C)
router
(D)
presentation
The Register or main memory location which contains the effective address of the
operand is known as :
(A)
Pointer
(B)
Indexed register
(C)
Special Locations
(D)
Scratch Pad
D8705
www.upscportal.com
P.T.O.
Downloaded from: http://www.upscportal.com
32.
33.
A Top - down Parse generates :
(A) Left most derivation
(C) Right - most derivation in reverse
(B)
(D)
Right - most derivation
Left - most derivation in reverse
A general macroprocessor is an in built function of :
(A) Loader
(B) Linker
(C) Editor
(D)
Assembler
34.
Which of the following is not collision Resolution Technique :
(A) Hash addressing
(B) Chainning
(C) Indexing
(D) None of these
35.
Which activities is not included in the first pass of two pass assembler ?
(A) build the symbol table
(B) construct the Intermediate code
(C) separate memonic opcode and operand field.
(D) none of these
36.
Producer consumer problem can be solved using :
(A) semaphores
(B) event counters
(C) monitors
(D) all the above
37.
If you want to execute more than one program at a time, the systems software that are
used must be capable of :
(A) word processing
(B) virtual memory
(C) compiling
(D) multitasking
38.
Which of the following checks cannot be carried out on the input data to a system ?
(A) Consistency check
(B) Syntax check
(C) Range check
(D) All the above
39.
Nonmodifiable procedures are called :
(A) Serially usable procedure
(B)
(C) Reentrant procedure
(D)
Concurrent procedure
Topdown procedure
40.
Bankers algorithm is used for __________ purpose :
(A) Deadlock avoidance
(B) Deadlock removal
(C) Deadlock prevention
(D) Deadlock continuations
41.
The testing of software against SRS is called :
(A) Acceptance testing
(B) Integration testing
(C) Regression testing
(D) Series testing
D8705
www.upscportal.com
Downloaded from: http://www.upscportal.com
42.
43.
44.
45.
46.
47.
The lower degree of cohesion is :
(A)
logical cohesion
(B)
coincidential cohesion
(C)
procedural cohesion
(D)
communicational cohesion
The Reliability of the software is directly dependent upon :
(A)
Quality of the design
(B)
Programmers experience
(C)
Number of error
(D)
Set of user requirements
Succesive layer of design in software using but ton-up design is called :
(A)
Layer of Definement
(B)
Layer of Construction
(C)
Layer of abstraction
(D)
None of the above
Sliding window concept of software project management is :
(A)
Preperation of comprehenciable plan
(B)
Preperation of the various stages of development
(C)
Ad-hoc planning
(D)
Requirement analysis
Which of the following transonission media is used in Blue tooth Technology :
(A)
Radio links
(B)
Microwave links
(C)
VSAT Communication
(D)
Fiber - optic
Which of the following is a EDI standard ?
(A)
48.
50.
(B)
ANSI X.14
(C)
ANSI X.13
(D)
ANSI X.12
(D)
TLPP
Analysis of large database to retrive information is called :
(A)
49.
ANSI X.15
OLTP
(B)
OLAP
(C)
OLDP
The cost of the network is usually determined by :
(A)
Time complexity
(B)
Switching complexity
(C)
Circuit complexity
(D)
None of these
The mechanism with which several uses can share a medium without interference is :
(A)
Frequency modulation
(B)
Amplitude modulation
(C)
Multiplexing
(D)
None of these
-o0oD8705
www.upscportal.com
P.T.O.
Downloaded from: http://www.upscportal.com
Space For Rough Work
D8705
www.upscportal.com
S-ar putea să vă placă și
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeDe la EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeEvaluare: 4 din 5 stele4/5 (5795)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreDe la EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreEvaluare: 4 din 5 stele4/5 (1091)
- Never Split the Difference: Negotiating As If Your Life Depended On ItDe la EverandNever Split the Difference: Negotiating As If Your Life Depended On ItEvaluare: 4.5 din 5 stele4.5/5 (838)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceDe la EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceEvaluare: 4 din 5 stele4/5 (895)
- Grit: The Power of Passion and PerseveranceDe la EverandGrit: The Power of Passion and PerseveranceEvaluare: 4 din 5 stele4/5 (588)
- Shoe Dog: A Memoir by the Creator of NikeDe la EverandShoe Dog: A Memoir by the Creator of NikeEvaluare: 4.5 din 5 stele4.5/5 (537)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersDe la EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersEvaluare: 4.5 din 5 stele4.5/5 (345)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureDe la EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureEvaluare: 4.5 din 5 stele4.5/5 (474)
- Her Body and Other Parties: StoriesDe la EverandHer Body and Other Parties: StoriesEvaluare: 4 din 5 stele4/5 (821)
- The Emperor of All Maladies: A Biography of CancerDe la EverandThe Emperor of All Maladies: A Biography of CancerEvaluare: 4.5 din 5 stele4.5/5 (271)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)De la EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Evaluare: 4.5 din 5 stele4.5/5 (121)
- The Little Book of Hygge: Danish Secrets to Happy LivingDe la EverandThe Little Book of Hygge: Danish Secrets to Happy LivingEvaluare: 3.5 din 5 stele3.5/5 (400)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyDe la EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyEvaluare: 3.5 din 5 stele3.5/5 (2259)
- The Yellow House: A Memoir (2019 National Book Award Winner)De la EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Evaluare: 4 din 5 stele4/5 (98)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaDe la EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaEvaluare: 4.5 din 5 stele4.5/5 (266)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryDe la EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryEvaluare: 3.5 din 5 stele3.5/5 (231)
- Team of Rivals: The Political Genius of Abraham LincolnDe la EverandTeam of Rivals: The Political Genius of Abraham LincolnEvaluare: 4.5 din 5 stele4.5/5 (234)
- On Fire: The (Burning) Case for a Green New DealDe la EverandOn Fire: The (Burning) Case for a Green New DealEvaluare: 4 din 5 stele4/5 (74)
- The Unwinding: An Inner History of the New AmericaDe la EverandThe Unwinding: An Inner History of the New AmericaEvaluare: 4 din 5 stele4/5 (45)
- Aristotle's Model of CommunicationDocument10 paginiAristotle's Model of CommunicationJomana Macalnas100% (1)
- MWG Product 11.0, X PG-PRODUCT-1021-EnDocument941 paginiMWG Product 11.0, X PG-PRODUCT-1021-EnKuncen Server (Yurielle's M-Chan)Încă nu există evaluări
- All About Computer 1Document59 paginiAll About Computer 1Shii YaoÎncă nu există evaluări
- DSM Models and Non-Archimedean ReasoningDocument23 paginiDSM Models and Non-Archimedean ReasoningMia AmaliaÎncă nu există evaluări
- Comparative AnalysisDocument4 paginiComparative AnalysisShaina Leila Apolonio GarciaÎncă nu există evaluări
- En 2 DYSllfz 5 Q Ij WQ5 GGP 5 CBR 4 B2 V 1 T HBXZ I4 M 0 P KDocument69 paginiEn 2 DYSllfz 5 Q Ij WQ5 GGP 5 CBR 4 B2 V 1 T HBXZ I4 M 0 P KAhmad SofyanÎncă nu există evaluări
- Republic of The Philippines Division of Bohol Department of Education Region VII, Central VisayasDocument6 paginiRepublic of The Philippines Division of Bohol Department of Education Region VII, Central VisayasCecille HernandoÎncă nu există evaluări
- A Pali Grammar - Wilhelm Geiger OCRDocument129 paginiA Pali Grammar - Wilhelm Geiger OCRAnders Fernstedt82% (17)
- Booklet Vivaldiconcertos Danlaurin PDFDocument36 paginiBooklet Vivaldiconcertos Danlaurin PDFCarlos TorijaÎncă nu există evaluări
- Peer InterventionDocument4 paginiPeer Interventioniulia9gavrisÎncă nu există evaluări
- Sow Form 2Document6 paginiSow Form 2mohanaaprkashÎncă nu există evaluări
- UCanCam V9 InstructionDocument212 paginiUCanCam V9 InstructionViorel StetcoÎncă nu există evaluări
- CBSE-IX English - Chap-W1 (Descriptive Paragraph)Document8 paginiCBSE-IX English - Chap-W1 (Descriptive Paragraph)hari.savani01Încă nu există evaluări
- A Complete Guide To The Tarot Eden GrayDocument2 paginiA Complete Guide To The Tarot Eden GrayFacundo Eduardo Guaytima QuilesÎncă nu există evaluări
- Administracion de RedesDocument14 paginiAdministracion de RedesManuel Castrejon AntunezÎncă nu există evaluări
- Latest OGG ScriptDocument5 paginiLatest OGG ScriptSundar RaaviÎncă nu există evaluări
- Hacking With ReactDocument123 paginiHacking With ReactGeoRazzaÎncă nu există evaluări
- Data ProjectDocument16 paginiData ProjectamyÎncă nu există evaluări
- ICPDASDocument120 paginiICPDASPedro BortotÎncă nu există evaluări
- US Sanskrit CorrectionsDocument13 paginiUS Sanskrit CorrectionsBala HicasÎncă nu există evaluări
- Grade 8 Baseline QPDocument5 paginiGrade 8 Baseline QPKhan NurunnabiÎncă nu există evaluări
- SLK OCC Speech ContextDocument8 paginiSLK OCC Speech ContextChristian EaÎncă nu există evaluări
- Apa Format For An EssayDocument3 paginiApa Format For An Essayezkrg6k2100% (2)
- Financial Accounting - Procedure For Line Item ExtractionDocument8 paginiFinancial Accounting - Procedure For Line Item Extractionlakshmi025Încă nu există evaluări
- Guy Cook's Applied Linguistics: Chapter 3: Languages in The Contemporary World Dina BensureitiDocument29 paginiGuy Cook's Applied Linguistics: Chapter 3: Languages in The Contemporary World Dina BensureitiDina Bensreti100% (1)
- Class 6 EnglishDocument66 paginiClass 6 EnglishRahul SinghÎncă nu există evaluări
- Amdahl SolutionDocument2 paginiAmdahl SolutionGOPI CHANDÎncă nu există evaluări
- 07 Introductory Lessons in AramaicDocument134 pagini07 Introductory Lessons in AramaicTorres EdznáÎncă nu există evaluări
- BTS36 Series Hardware Description ManualDocument131 paginiBTS36 Series Hardware Description Manualmaicuongdt2Încă nu există evaluări