Documente Academic
Documente Profesional
Documente Cultură
W Wine07
Încărcat de
Ashish Kumar AgnihotriTitlu original
Drepturi de autor
Formate disponibile
Partajați acest document
Partajați sau inserați document
Vi se pare util acest document?
Este necorespunzător acest conținut?
Raportați acest documentDrepturi de autor:
Formate disponibile
W Wine07
Încărcat de
Ashish Kumar AgnihotriDrepturi de autor:
Formate disponibile
Data and Internet Security Guide
The Windows Secrets
Data and Internet Security Guide
Volume 2
Advanced tips and tools for safe computing
on and off the Web
Copyright 2014 by WindowsSecrets.com. All rights reserved.
www.WindowsSecrets.com
Page i
Data and Internet Security Guide
Table of contents:
Introduction ..............................................................................................1
A basics refresher: the WS Security Baseline .........................................2
Rebooting the Windows Secrets Security Baseline .................................................... 2
Rolling Windows back to the last known good .......................................................... 2
Reviewing the rest of the security basics .................................................................... 3
Baseline plus: A second machine for websurfing ....................................................... 4
Monitoring your system for rogue software ................................................................. 5
More tools for prevention and cleaning ....................................................................... 5
Protect your data ..................................................................................... 7
Better data and boot security for Windows PCs ......................................7
Safer alternatives to whole-disk encryption ................................................................ 8
Getting started with file and folder encryption ............................................................. 8
Step by step: Encrypting data with 7-Zip .................................................................... 9
Enabling pre-boot security passwords ...................................................................... 15
Are password managers truly safe? ......................................................17
Data-encryption alternatives to TrueCrypt .............................................19
How safe is safe enough and for what? ............................................................... 19
Which files should be encrypted and where? ........................................................... 19
BitLocker best for corporate environments ............................................................... 20
DiskCryptor: For drives and partitions....................................................................... 21
Cryptainer LE: The tool for virtual partitions ............................................................. 23
The choice: Stay with TrueCrypt or move on ............................................................ 25
Pre-encryption makes cloud-based storage safer .................................26
Why use cloud-based data storage at all? ................................................................ 26
Pre-encryption adds automatic protection ................................................................ 27
Setting up Boxcryptor, step by step .......................................................................... 28
Using Boxcryptor with OneDrive: The basics ........................................................... 33
Send email that only the recipient can read ...........................................37
Widespread third-party access to personal email ..................................................... 37
Solution 1: Send an encrypted ZIP file ..................................................................... 37
Solution 2: A plug-in, email-encryption app .............................................................. 38
Solution 3: Sendincs online mail service .................................................................. 44
Coming attractions: StartMails email system ........................................................... 45
How to reset lost passwords for Windows .............................................47
Password reset disk: Be proactive, not reactive ....................................................... 47
Windows 8: Your password is stored with Microsoft................................................. 48
www.WindowsSecrets.com
Page i
Data and Internet Security Guide
Accessing a user account via a Windows setup CD ................................................. 49
Resetting passwords without install/reset media ...................................................... 51
Court of last resort: Cracking tools............................................................................ 53
Prevent and remove malware ............................................................... 55
Two tips for removing malware ..............................................................55
Suspicious software that wont uninstall ................................................................... 55
Free tool removes malware ...................................................................................... 55
Tweaking Windows to block CryptoLocker ............................................57
Shedding some light on security-cert warnings .....................................61
Sorting out problems with Java security ................................................................... 61
Interpreting common webpage warnings .................................................................. 63
EMET 4 puts up warnings about Facebook .............................................................. 64
Hardening up security certificates in Windows ......................................................... 65
Hardened enforcement of signed code coming ........................................................ 65
Noncompliant UEFI Modules .................................................................................... 65
In the end, you have to trust your instincts ............................................................... 66
Mobile security: Apps to protect Android devices ..................................67
Android needs third-party security apps ................................................................... 67
Security suites: The absolutely must-have apps ...................................................... 68
Password management and data encryption ........................................................... 71
Apps for recovering lost or stolen phones ................................................................ 72
Virtual private network apps for Android ................................................................... 74
Apps for thoroughly sanitizing Android devices ........................................................ 75
Security tools can help keep you safe ...................................................................... 76
www.WindowsSecrets.com
Page i
Data and Internet Security Guide
Introduction
If youre truly concerned with online security and obviously you should be simply
keeping your anti-malware app and browsers updated isnt enough. Theres no such
thing as perfect security, but using some specialized apps and techniques will go most
of the way toward keeping your data and personal information completely safe.
In the Windows Secrets Data and Internet Security Guide, Volume I, we covered the
basics of safe computing. That ebook discusses how personal computers become
infected and the techniques and habits everyone needs to know to block malware,
protect sensitive personal information, and prevent data theft. It goes on to review some
basic tools for maintaining privacy.
Volume 2, takes computing security to the next level. It starts with a quick review of
security basics and then delves into advanced topics such as encryption, password
recovery, and malware removal important knowledge for anyone who wants or needs
to keep sensitive information truly secure.
The Internet can be a dangerous place. We think these security guides, based on
stories from the Windows Secrets archives, can help you make it significantly safer.
Thanks for supporting Windows Secrets!
The editors
www.WindowsSecrets.com
Page 1
Data and Internet Security Guide
A basics refresher: the WS Security Baseline
By Susan Bradley
Regular readers know that Windows Secrets discusses the importance of PC and
Internet security almost every week.
But it seems many Windows users never get the message. Here are tips for safe
computing in the year 2014. Pass them along.
Rebooting the Windows Secrets Security Baseline
In the Feb. 17, 2011, In the Wild column, Windows Secrets PC Security Baseline, we
listed the minimal steps every PC user should take to protect digital information. Back
then, it was a bit easier because smartphones were not quite as ubiquitous and the first
iPad had been released only the year before.
In that column we listed the four key elements for online security: a hardware firewall,
antivirus software, an updated browser, and up-to-date applications. To that list, add
password management. All those parts are still important. But with the evolution of
online threats, the baseline of PC security has risen a notch or two. In this updated
Windows Secrets Security Baseline, Ill review whats important today. And in a followup story, Ill discuss some advanced security options.
These days, we have a lot of threats and risks to consider. Now that most of us are
connected to the Internet 24/7, we face fewer worms and viruses spreading from system
to system, but many more zero-day attacks that come through our connections to the
Web. And to make matters more worrisome, cyber attackers are now targeting the
sources of our Web experience banks, online shopping, social networks, and many
more back-end services.
Given the many ways our digital world might be compromised, Im actually going to take
a step back from the original WS Security Baseline and start with the most basic
protection we have at hand: backing up our systems.
Rolling Windows back to the last known good
Using backups as a security tool isnt new. About 10 years ago, a Microsoft Security
program manager (now working at Amazon) wrote an article on the ways to recover
from a system breach. He argued that you couldnt recover a hacked system with
cleaning tools alone; you needed good recovery media or a trusted backup. A decade
later, that advice is still perfectly valid. To be assured you have a clean system, you
need to recover or rebuild it.
So again: Item one on any security baseline is to ensure you have a full, working backup
and that you can recover data from that backup.
Im a fan of Acronis True Image (site) and Runtimes DriveImage XML (site); both are
solid backup options, and both provide the ability to back up everything on your
computer to an external USB hard drive.
www.WindowsSecrets.com
Page 2
Data and Internet Security Guide
Reviewing the rest of the security basics
As noted, those other basic security requirements are no less important than they were
three or more years ago. Heres a summary:
Use unique passwords and keep them safe: Given all the websites and cloud
services we now use, keeping passwords is only more difficult especially because the
first rule of password security is to use a unique password for each site or account.
Keeping track of numerous passwords is tough; it would seem the two choices are either
to write them down (a dubious solution) or use password-management software.
For sensitive sites such as online banking, try changing passwords at least once every
180 days or as often as you can without driving yourself crazy. Also, select securityreset questions that cant be guessed from information you post online.
Run firewalls: Ensure that Windows built-in firewall is up and running. Also check that
your routers hardware-based firewall is active. Contrary to what some believe, the two
firewalls should not conflict with each other. And what one misses, the other will probably
catch.
A properly configured hardware firewall will protect your entire home network not just
PCs, but also other potentially vulnerable devices such as set-top boxes, tablets, and
network-attached printers and hard drives.
When Comcast recently updated my home router, I was reminded that most routers use
basically the same default sign-in credentials: i.e., admin and password or some
close approximation. Moreover, the firewalls security was set to low. Because router
settings can be a bit obtuse for the average PC user, I will cover that topic in an
upcoming article. For now, just make sure that you have a hardware firewall enabled.
Oh and change your routers default sign-in credentials if you havent done so
already!
Run anti-malware software: For many years I was content with a basic, full-time
antivirus application and an on-demand malware scanner. Those two apps were
Microsoft security Essentials and the free version of Malwarebytes Anti-Malware. But
with the threats from casual websurfing getting only worse, Ive switched to the paid, fulltime version of Malwarebytes (site) both on my home system and on others systems.
There are, obviously, many other excellent anti-malware products. Sites such as AVComparatives and AV-TEST publish regular reports of the most popular AV products.
You dont need to buy one of the big security suites unless you want defense-in-depth
and are technology-challenged.
Keep browsers up to date: Eons ago, our only browser was Netscape Navigator. And
the Net was, for the most part, a friendly place. Now its common to have three or more
browsers installed and you should. Chrome, Internet Explorer, and Firefox are the
usual choices, but you might also want Opera (site) as yet another alternative one
that might not be as big a target for cyber attacks.
www.WindowsSecrets.com
Page 3
Data and Internet Security Guide
Along with having several browsers installed, I recommend using more than one search
engine. Several, such as the awkwardly named DuckDuckGo (site), promise not to use
search-tracking to send you targeted ads.
Keep Windows and apps up to date: Windows and its associated applications might
be getting less buggy, but hackers are also getting more sophisticated. So keeping your
machine up to date is still a key element of online security.
Along with system updates, take some time to remove applications you no longer need.
Thats especially true for software that has a history of vulnerabilities. For example, if
you dont need Java, uninstall it; if you dont need Silverlight, uninstall it (and ignore
Microsofts seemingly endless offerings of Silverlight).
Also be on the lookout for updates Java and Adobe Flash Player, for example that
try to install toolbars and other free offerings. Use Secunias Personal Software
Inspector (PSI; site) to help scan for outdated and/or unpatched software. (Note: Some
overzealous security products flag PSI as malware. You can ignore the warnings.)
Set up a limited-rights account: This might be the most overlooked security tool
available to Windows users most of whom are probably running continuously in
administrator mode. Thats an opportunity for cyber attackers to take complete control of
your system. Windows 7, 8, and 8.1 make it relatively easy to work in a standard user
account and let you provide administrator credentials only when needed.
A blog post (relatively old but still valid) showcases ways to set up both administrator
and standard-user accounts. Yes, Windows User Account Control (UAC) can be
annoying, but I dont recommend disabling it. Stick with the default settings in Windows
7, 8, and 8.1.
And though we might not like Win8s Modern interface, keep in mind that Microsoft
added SmartScreen technology (more info) to the operating system itself. (Its been in IE
since Version 8.) Malware downloads that Win7 might let through stand a better chance
of being caught by Win8.
Baseline plus: A second machine for websurfing
You might suspect Im in league with computer manufacturers, but I have good reasons
for stating that the best form of Internet safely these days is to do casual Web browsing
on a second machine one dedicated to just that activity. Alternatively, dedicate a
second system just for sensitive activities such as online banking. Some PC users set
up dual-boot systems for the same purpose, but Im not a fan of that technique. Ive
seen too many patching oddities that seem to be rooted in conflicts between the two
installed operating systems.
The ideal system for casual browsing is one of the small, mobile devices such as an
Android tablet, iPad, Kindle, or if you must stick with Windows a Windows RT
device. Any of those platforms is more difficult (or less likely) to be successfully infected.
Super-geek and noted security blogger Brian Krebs recommends using a Linux boot
disk when doing online banking. Great idea, but it will defeat communications between
bank sites and any accounting software you might be using.
www.WindowsSecrets.com
Page 4
Data and Internet Security Guide
If you want additional security for online banking, I recommend installing two specialized
applications on a Windows PC:
Trusteer Rapport (site): This software works with websites to block malicious keylogger
programs that steal credentials. I reviewed the software in the March 7, 2013, On
Security article, Using Trusteer to enhance online-banking security. Its running on
several of my office machines with no issues. You might check whether your bank
supports and recommends Trusteer or some other keylogger-blocking software.
CryptoPrevent (site): CryptoLocker is still a significant threat, and this software blocks
viruses that include the CryptoLocker payload even protecting the temporary folders
that CryptoLocker loves to infect.
Monitoring your system for rogue software
In my office, I use two monitoring tools Spiceworks and EventSentry to alert me
when new software is installed on my office machines. They cover any apps Ive not
authorized, including those unwanted toolbars. Note, however, that those tools are not
recommended for consumer machines. Im still looking for monitoring tools that are
useful for personal systems.
For now, well have to stick with the old-fashioned eyeball technique. Once a month,
launch Windows Programs and Features applet and look for software you dont recall
installing. Sort the installed software by date. You should be safe uninstalling any
applications you dont recognize.
More tools for prevention and cleaning
A tool often overlooked is Microsofts Baseline Security Analyzer. MBSA 2.3 (site) is
geared more toward IT admins than consumers, but it can still be useful on personal
machines. Ill cover it in detail in an upcoming article.
A more practical tool for all Windows users is Microsofts Enhanced Mitigation
Experience Toolkit (more info). Microsoft has recommended EMET in particular for
preventing Internet Explorer zero-day attacks.
Recently, fellow Security MVP Harry Waldron helped a friend clean up his system. He
then posted his recommendations. The tools he mentions are designed to run from a
flash drive, ensuring that they get under the installed operating system. The tools are
updated regularly, so I suggest downloading them when theyre needed (assuming you
have access to a second system in order to do so). To prepare for an emergency, I
recommend keeping a blank external USB hard drive and empty flash drive of suitable
size so youll be able to move data quickly from one machine to another.
The Windows Secrets Security Baseline recap
If you want to give those with short attention spans the basics of PC security, send them
this list.
Step 1. Have a backup solution.
Step 2. Use unique passwords for each site or account.
www.WindowsSecrets.com
Page 5
Data and Internet Security Guide
Step 3. Have a hardware-based firewall in addition to the Windows firewall.
Step 4. Run and keep updated good anti-malware software, both real-time and ondemand scanning.
Step 5. Have alternative browsers and keep them all updated. Consider using alternative
search engines.
Step 6. Applications: Either patch them or remove them.
Step 7. Dont run in administrator mode; set up a standard-user account.
Step 8. Consider using a tablet-style device for recreational websurfing.
If that seems like a lot of work, consider the time and expense of getting hacked. At a
minimum, you might end up with an unwanted toolbar. On the other hand, you might
have your bank accounts cleaned out and your identity stolen. Keep in mind that cyber
thieves are constantly finding new ways to beat the system. Stay tuned for Part II of our
series on security.
www.WindowsSecrets.com
Page 6
Data and Internet Security Guide
PROTECT YOUR DATA
Better data and boot security for Windows PCs
By Fred Langa
Fundamental changes in PCs, including UEFI and Secure Boot, can interfere with
classic security techniques such as whole-disk encryption.
But a simple, free, two-step process provides extremely reliable data and system-boot
security for all Windows versions, on virtually all PC hardware.
The gold standard for local PC data and system security for years, whole-disk
encryption offers two main benefits. First, it can provide robust, virtually uncrackable
security for all the files on your hard drive. Without the correct password, anyone
snooping through your files sees only gibberish.
Second, some whole-disk encryption tools can password-protect the entire system.
Without the correct password, an unauthorized user cant boot the PC from its hard disk.
There are, however, limitations and drawbacks to encrypting an entire hard drive.
Many Vista, Win7, and Win8 PCs sold within the past decade and virtually all sold
within the past few years include some form of Unified Extensible Firmware Interface.
UEFI is essentially an enhanced replacement of the venerable BIOS. (For more on this
topic, see the Jan. 19, 2012, Top Story, Say goodbye to BIOS and hello to UEFI!)
On newer systems, UEFI can provide boot-time security to prevent malware (rootkits,
bootkits, and so forth) and other unauthorized software from meddling with the way a PC
starts up. In fact, UEFI is the foundation for Win8s Secure Boot feature, which is
enabled by default when Win8 is installed on a UEFI-equipped PC.
Some whole-disk encryption tools require low-level access to the PC early in the boot
process. These tools can fail on PCs that make use of UEFIs advanced security
features.
DiskCryptor, for example, doesnt officially support Win8. But some users have made
it work in a limited fashion on individual partitions. They installed the application as a
service on the desktop side of Win8. On the other hand, other DiskCryptor users have
lost access to all their encrypted files.
Even if these tools are eventually patched to work with UEFI and Secure Boot, theyre
still working at some level against UEFIs low-level security features. Todays systems
simply arent meant to allow third-party tools to insert themselves deeply into the boot
process.
Fortunately, you can choose better and safer ways to provide reliable data protection
and boot security on just about any PC. The tools and methods are free, and they work
without interfering with UEFI, Secure Boot, or any other existing security features or
functions.
www.WindowsSecrets.com
Page 7
Data and Internet Security Guide
Safer alternatives to whole-disk encryption
No matter how old or new your PC is, and regardless of what Windows version youre
running, you can have extremely reliable data and boot security using two free
alternatives to whole-disk encryption.
Data security: Although whole-disc encryption can be problematic, file-and-folder
encryption is rock-solid. There are many tools available, but perhaps the most popular
is the open-source 7-Zip (site) application. Its free for personal and business use, and it
can scramble any file, folder, or group of folders with essentially uncrackable 256-AES
encryption (more info). Even if a hacker gains access to your hard drive, your encrypted
files should remain completely safe, secure, and unreadable.
Note: Although this article focuses on encryption, 7-Zip also compresses files, so they
occupy less disk space. The amount of compression varies with file type, but its not
uncommon for file size to shrink by around 50 percent. Compression can be an
important added benefit if you have a small, traditional hard drive or a solid-state drive
(SSD). So 7-Zip can simultaneously encrypt your data and shrink the size of your folders
and files.
Below, Ill show you the basics of using 7-Zip to encrypt and compress files and folders
you select. (Selective file/folder encryption and compression gives you more control
than does whole-disk encryption. For example, theres little reason to encrypt or
compress music, video, and image files. More on that below.)
Boot security: Virtually every PC in use today lets you set one or more low-level, preboot passwords. One type of password protects the system as a whole; the password
must be entered before the system will boot. Many PCs also offer a separate supervisor
password to prevent unauthorized changes to the basic system settings. And some PCs
let you set a password to protect the hard disk or SSD from unauthorized access.
The passwords can be used singly or in combination, depending on how much security
you want or need. Later in this article, youll see how to access and set whatever
passwords your system offers.
Combine data and boot security, and your data is protected from almost all malicious
threats. A pre-boot password will keep hackers from accessing your system with
separate bootable media. And if a hacker gets past that barrier, encryption will prevent
access to sensitive files and folders. Whether you combine file/folder data security and
boot security or use one of the two alone, you wont run into problems with UEFI, Secure
Boot, or any other of your PCs security features.
Getting started with file and folder encryption
The first step in implementing file and folder encryption is to figure out what really needs
to be encrypted.
There are many, many files on our hard drives that simply arent all that special, unique,
or sensitive. They just dont need to be encrypted!
For example, its sort of silly to encrypt your copy of Notepad, Paint, Calculator, Solitaire,
or any of the other system files (.exe, .msc, .dll, and so forth) that came with your
www.WindowsSecrets.com
Page 8
Data and Internet Security Guide
original Windows setup. Most of Windows core operating system files are similar from
system to system, varying only by Windows version and local hardware. They typically
dont contain any sensitive information. So its wasted effort to encrypt them (as they
would be with whole-disk encryption).
Most add-on software doesnt need encryption, either. Your copy of Word, Excel, Skype,
Photoshop, or whatever is, for the most part, like any other.
That also holds true for files you acquire through public sources. Your Dead Skunk
MP3 and that downloaded National Lampoons Vacation video are likely identical to
everyone elses. Whats to be gained by encryption? Even your digital photographs
probably dont contain anything truly sensitive.
On the other hand, many of the files you create within Word, Excel, or other
applications could contain sensitive information. Those are the files that need
protection and should be encrypted!
In most cases, securing potentially sensitive information means selecting specific files
and folders. For example, you probably dont need to encrypt your Music folder, but you
almost surely want to protect Documents and its subfolders plus any other locations
that might have information you want to keep private. Consider reorganizing your
documents into sensitive and nonsensitive folders. You most likely dont need to encrypt
your collection of old family recipes.
Once youve decided what you need to encrypt, make a full system image or backup. Or
at least make separate backup copies of the files you intend to encrypt. Although fileand-folder encryption tools are usually extremely reliable, accidents and user errors can
happen. So its best to play it safe make backups!
Next, download and install the file/folder encryption tool of your choice. A quick Web
search will produce numerous options. I use 7-Zip for this article because again its
reliable, well regarded, open-source, and free for both personal and business use.
Step by step: Encrypting data with 7-Zip
If you dont have 7-Zip already installed, head over to 7-zip.org and download the
version with the correct bittedness for your PC the 64-bit 7-Zip for 64-bit systems,
and the 32-bit 7-Zip for 32-bit systems.
Select the files/folders you want to include, such as those in your Documents folder.
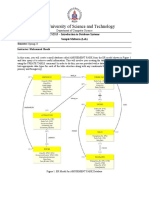
Right-click on the group of selected files/folders; youll see 7-Zip on the context menu, as
shown in Figure 1.
www.WindowsSecrets.com
Page 9
Data and Internet Security Guide
Figure 1. Once installed, 7-Zip is easily accessed by right-clicking
selected files and folders.
Click 7-Zip in the menu, and then select Add to archive as shown in Figure 2.
Figure 2. Clicking Add to archive opens 7-Zip's archive
settings.
When the Add to Archive dialog box opens (see Figure 3), enter a secure long,
complex, and hard-to-guess password where indicated.
The rest of the Add to Archive default choices are usually fine. 7-Zip will
automatically generate an archive name based on the selected folder(s), a files
name, or the selected files containing folder. The default archive format will be .7z,
www.WindowsSecrets.com
Page 10
Data and Internet Security Guide
which typically offers 210 percent better compression than the classic .zip format. I
recommend leaving the defaults alone at least until youre familiar with 7-Zip.
Click OK when youre ready.
Figure 3. At least to start, use the default archive settings for encrypting your data.
Note: I recommend using a good password manager to help generate and
remember your passwords. For more information, see the Jan. 9 Best Software
story, Why and how to use an open-source password manager, and Stepping up
to a standalone password manager in the Oct. 17, 2013, Top Story, Protect
yourself from the next big data breach.
www.WindowsSecrets.com
Page 11
Data and Internet Security Guide
Enter your password and click OK; 7-Zip will then compress and encrypt the selected
files. As a safety feature, 7-Zip creates archived copies of your files, leaving the
originals intact. In Figure 4, the files are placed in an archive called Documents.7z.
Figure 4. A new 7-Zip archive (in this example, Documents.7z) contains compressed,
encrypted copies of the selected files and folders.
Your archive is now complete!
Your next step is to test the archive to make sure that encryption and compression
worked properly. If it did and thats almost always the case you can then delete the
original files, so that only the encrypted archive remains.
www.WindowsSecrets.com
Page 12
Data and Internet Security Guide
To open an archive, simply double-click it (Documents.7z, in this example). When the
password dialog box opens (Figure 5), enter the password you gave that particular
archive. You might use different passwords for different archives. (Keep those
passwords safe! Obviously, if you lose a password, youve effectively lost the encrypted
files and/or folders.)
Figure 5. Entering the correct password opens
archived files and folders.
With the proper password entered, 7-Zip File Manager opens and displays the contents
of the archive (Figure 6). Click on any listed file or folder; it should open normally and
work just like any nonencrypted file. When you save and close an archived file, its
automatically compressed and encrypted with the archives original password.
Figure 6. 7-Zip's file manager lets you view, open, edit, and
save files.
www.WindowsSecrets.com
Page 13
Data and Internet Security Guide
Check that the archived files are accessible and saved correctly, then delete the
originals so that only the encrypted archive remains, as shown in Figure 7. (For complete
security, be sure to empty the Windows trash.)
Figure 7. With the originals deleted, your files and folders are securely
encrypted.
The 7-Zip File Manager is the key to easily using your archives. Leave it open as you
typically might the standard Windows/File Explorer then view, access, or edit any files
in the archives just as you do nonarchived files. 7-Zips File Manager also lets you
quickly add files to an archive.
That covers the bare-bones basics of using 7-Zip, but theres a lot more to the software,
including ways to extract files and folders from the archive and to add files and folders
without using the 7-Zip File Manager. For complete information on using 7-Zip, check
out its built-in Help file or see these online resources:
7-Zip support site
Video tutorials at ShowMeDo
Video tutorial at Top Windows Tutorials.com
Tutorial by expert user Grdal Ertek (autoloading video)
www.WindowsSecrets.com
Page 14
Data and Internet Security Guide
Enabling pre-boot security passwords
As mentioned above, using a pre-boot password can be an excellent security
precaution. Most current PCs have some kind of BIOS/UEFI-password option built in.
There can be multiple types of passwords, and they typically appear immediately after a
system powers on and before the operating system loads.
The number and password options and their capabilities vary from vendor to vendor. In
a moment, youll see how to determine what password options your PC offers.
Some passwords lock down the entire system; without the proper password, the system
wont boot at all either from the internal hard drive or from any bootable media! Other
passwords help to protect the hard drive from unauthorized access. And still other
passwords let you set an administrator/supervisor password to prevent unauthorized
changes to the BIOS/UEFI settings.
As Figure 8 shows, the BIOS/UEFI might offer more than one type of password.
Figure 8. A typical BIOS/UEFI lets you set one or more passwords to protect
components such as the system, settings, and/or mass-storage drives.
Using one or more of these low-level passwords can help lock your system down tight,
making it extremely secure against any unauthorized access.
Of course, make sure you remember the BIOS/UEFI passwords or you might be
unable to access your own hardware!
The various brands and models of PCs use different methods to access and change the
BIOS/UEFI-password settings. The information below is a general guide, but for specific
information for your brand and model of PC or if the following instructions dont work
for you visit your PC vendors online support site and search for BIOS/UEFI access.
Use search terms such as access BIOS, access UEFI, enter BIOS, enter UEFI, edit
BIOS, and/or edit UEFI.
BIOS/UEFI access for Win8.1 PCs (Win8.0 is similar):
Save any open files and exit all running programs.
www.WindowsSecrets.com
Page 15
Data and Internet Security Guide
Open the Charms bar, click the gear icon (Settings), and then click Change PC settings
at the bottom of the bar.
On the PC settings page, select Update and recovery.
Click Recovery and then, under Advanced startup, click Restart now. (Despite the
terminology, your PC will not immediately restart! This is normal.)
On the Choose an option screen, click Troubleshoot and then click Advanced
options.
If a UEFI Firmware Settings option appears, select it. (It might be called something
slightly different, such as Change UEFI Settings.) If no such option exists, skip the rest
of these steps.
On the UEFI Firmware Settings screen, select Restart.
Your PC will restart and run the built-in UEFI setup utility.
Explore the UEFI setup utilitys tabs and dialog boxes to find the password settings.
Theyre often found on a tab labeled Security, or something similar. (See Figure 8,
above.)
BIOS access for non-UEFI PCs
Youll find detailed information on accessing traditional BIOSes in the Jan. 9 Top Story,
The best of LangaList Plus from 2013. Skip down to the subhead, Using multiple
layers of security an update. Then look for the subsection, Protecting against
local/physical threats.
Bottom line: Easy data and system security for any PC, any Windows. In todays
era of UEFI PCs and Secure Boot, using low-level security tools such as whole-disk
encryption is just asking for trouble. But you also dont have to leave yourself vulnerable.
Take some time to investigate your systems boot-level password options. And if you
dont like 7-Zip, there are plenty of other file/folder-level encryption apps to choose from.
They work on most versions of Windows and on any PC hardware.
www.WindowsSecrets.com
Page 16
Data and Internet Security Guide
Are password managers truly safe?
By Fred Langa
Windows Secrets has often advocated the use of a good password manager for
protecting data. But some readers have questioned the wisdom of handing over
passwords to some faceless software and distant servers. Their worries are mostly
unfounded.
With any good password manager, your passwords are never out of your own, local
control. You and you alone will always have access to, and control of, your stored
passwords. Heres why:
When a good password manager generates a new password, its saved to an
encrypted file that lives only on your PC (or smartphone, or tablet). To open that file,
you make up a single, master password that only you know. The only password you
absolutely must remember is the master password.
The master password gives you immediate access to all your encrypted passwords,
whether you made them up yourself or let the password-management software generate
them. Once the correct master password is entered into the password manager, you can
view, edit, and/or delete all stored passwords.
If someone hacks or steals your PC or smartphone, all passwords stored in the
encrypted file will appear as useless gobbledygook unless, of course, the thief has
your master password (a good reason not to put the master password on a yellow Postit stuck to your PC or monitor).
Some password managers also let you store copies of your passwords in the cloud,
typically on a secure server run by the publisher of the password-management software.
(You get a private account on the server when you buy or register the software.) Better
password-management services will also sync your passwords across your digital
devices.
Your passwords are never transmitted to the cloud in the clear. They leave your PC
fully encrypted and remain encrypted on the remote server.
Whats more, your master password is never sent to or stored in the cloud which
means the publisher of the password-management software cant access your stored
passwords, either. (In other words, if you lose your master password, the publisher cant
help you recover it.)
Thus, the cloud-based copies of your password files are safe. Should hackers somehow
penetrate the publishers security and access your private account on the server, they
cant decrypt your password files without the master password. As on your PC, theyll
see only completely useless strings of characters.
Again, whether uploading or downloading your password file, the only place it can be
decrypted is on your PC or smartphone and only if you provide the correct master
password.
www.WindowsSecrets.com
Page 17
Data and Internet Security Guide
If the password-manager publisher goes out of business or your connection to the
Internet is interrupted, youll still always have access to your locally stored passwords
as long as you dont forget the master password, or the password-management system
isnt corrupted (yet another important reason to make regular backups of your PC).
Bottom line: As long as you pick good password-management software and secure it
with a strong master password, your individual passwords are effectively completely
secure from any kind of hacking local or distant.
www.WindowsSecrets.com
Page 18
Data and Internet Security Guide
Data-encryption alternatives to TrueCrypt
By Lincoln Spector
It seems as if everyone who kept sensitive files secure did it with TrueCrypt. Edward
Snowden depended on it. So did I.
But now that the popular disk-encryption app is effectively dead at least for the
foreseeable future its time to look for a replacement.
In last weeks (June 12) Top Story, The life and untimely demise of TrueCrypt, Susan
Bradley reviewed the applications history and stated, Its a mystery that we gave
TrueCrypt such an extraordinary level of trust. It had dubious legal foundations, its
developers were unknown, and its support was primarily relegated to forums that are
now missing.
In this follow-up article, Ill discuss my own approach to protecting sensitive files, and Ill
explain why I unlike Susan typically dont recommend Microsofts BitLocker. I will
recommend two file-encryption programs that might take TrueCrypts place.
How safe is safe enough and for what?
Lets use your home as an analogy. You probably keep your front door locked at least
at night and when youre away. You might have an alarm system or even bars on the
windows. But your security system most likely doesnt match those used by New Yorks
Metropolitan Museum of Art or the Getty Center in Los Angeles.
Why? Well, for one thing, you cant afford it. But mostly, it would be overkill. Few of us
have anything in our homes that would attract the sort of professional thieves who might
steal a Van Gogh.
To a large extent, the same rules apply to data. It takes a lot of time and skill to crack
encryption, and most criminals are looking for an easy score. Even the NSA, which has
the ability to crack all but the best encryption, probably wont bother. It might soak up
everyones cellphone metadata because thats relatively easy. But it reserves the hard
work for the few people of interest.
That doesnt mean you shouldnt take precautions. Going back to that house analogy,
encrypting sensitive files is like locking your front door a reasonable and generally
sufficient line of defense. (And you must ensure that unprotected bits of those files dont
remain on your hard drive.) You also need to protect the encryption key with a long,
complex password thats extremely difficult to crack and be wary of phishing scams
and other deceits that might trick you into handing over the key.
Which files should be encrypted and where?
You dont need to encrypt every file. Well assume that neither the NSA nor criminals are
really interested in your collection of cat photos or your daughters term papers.
Obviously, you do need to protect files containing bank statements, credit-card
information, and Social Security numbers basic data about your personal identity. But
you also might want to encrypt any information that you dont want others to see and
www.WindowsSecrets.com
Page 19
Data and Internet Security Guide
anyone elses personal information you might possess. The simple rule: If in doubt,
encrypt it.
Your work might dictate different encryption procedures. For example, a small
construction company might need to encrypt just a few financial and customer files,
whereas nearly every file an accountant handles probably needs encryption.
The safest place for sensitive files is on an encrypted (and fully backed-up) partition or
drive. File-by-file encryption can leave temporary, unencrypted copies on the hard drive.
But if every sector on the drive is encrypted, these temporary copies will be unreadable
as well.
Im partial to using a virtual drive/partition what TrueCrypt called a volume. This is
typically a single, often quite large, encrypted file. When you open it with the correct
password, Windows sees it as a standard drive from which you can launch files,
manage them with Windows Explorer, and so on. When youre done, you close the
volume and all files inside are once again inaccessible. Temporary and deleted files
stay within the volume, so they, too, are encrypted.
You can, of course, encrypt real partitions. In fact, you can encrypt all partitions
including C:. Booting and signing in to Windows automatically opens these encrypted,
physical partitions. But if someone boots the system from a flash drive or connects your
hard drive to another computer, nothing will be accessible.
Arguably, this is the safest type of data protection. Because your entire hard drive is
encrypted, even Windows swap and hibernation files are locked. But full-drive
encryption has its own problems. For example, you wont be able to pull files off an
unbootable system by using other boot media.
Also, with full-drive encryption, all data files are accessible whenever youre signed in to
the PC. They can be stolen by a remote cyber thief via malware or by a co-worker while
youre on a coffee break. By contrast, you have to consciously open an encrypted
volume, which can remain locked when youre in a not-so-safe environment such as
on a public Wi-Fi network.
Bottom line: Full-drive encryption makes the most sense if you work primarily and
continuously with sensitive information as in accounting. In most cases, an
encrypted partition makes more sense; its nearly as secure as full-drive encryption
and offers more flexibility. File-by-file encryption is the least secure but is worth
considering if you cant use drive/partition encryption, as discussed in the May 15 Top
Story, Better data and boot security for Windows PCs, and in a follow-up in this weeks
LangaList Plus.
BitLocker best for corporate environments
For many, Windows own BitLocker encryption tool is the obvious TrueCrypt
replacement. Susan Bradley put it at the top of her short list, and the infamous
TrueCrypt warning on the SourceForge download page provides extensive directions for
setting it up.
www.WindowsSecrets.com
Page 20
Data and Internet Security Guide
BitLocker comes with Windows 7 Ultimate and Enterprise plus Windows 8 Pro and
Enterprise. It can encrypt real and virtual partitions or the entire drive. In my view,
BitLocker has its place primarily when managed by a PC expert in an office scenario.
BitLocker is sort of set-and-forget; non-techie office workers can simply sign in and out
of Windows in the normal way without even knowing (or caring) whether their files are
encrypted.
But for personal use, BitLockers password/key system can be overly complex or
confusing. For example, when you set up BitLocker, you create an unlock password.
(You can also have a BitLocker-encrypted drive unlock automatically when users sign in
to Windows or they can use a smartcard or PIN.) But you must also create a separate
key-recovery password thats stored on the system if the PC has a Trusted Platform
Module (TPM; more info) chip, or on a flash drive if it doesnt. Setting up BitLocker on a
system without a TPM chip can take some time and admin skills.
Basically, if you dont have a newer PC and an advanced version of Windows, BitLocker
is simply not a viable option. For an individual maintaining his or her PC, its just another
layer of complication.
Here are two better data-encryption applications for personal PCs.
DiskCryptor: For drives and partitions
Like TrueCrypt, DiskCryptor (info) is free. Its also open-source, though Im not as
confident as I once was that being open-source is an advantage. (As Susan pointed out
last week, Theres even debate whether TrueCrypt qualifies as open-source.
DiskCryptor is designed to encrypt partitions. According to the DiskCryptor site,
Windows 8 isnt supported. But it seemed to work fine encrypting a separate, nonboot
partition on a fully updated Win8.1 Update system.
DiskCryptors user interface is somewhat unattractive, but its relatively easy to figure
out. The program offers industry-standard AES, Twofish, and Serpent encryptions (see
Figure 9). If youre really paranoid, you can combine them, encrypting first one way and
then another.
Figure 9. DiskCryptor lets you combine encryption
technologies for extra security.
www.WindowsSecrets.com
Page 21
Data and Internet Security Guide
A simple wizard helps you quickly encrypt any partition including C:. If you encrypt
C:, youll have to enter your DiskCryptor password before Windows will load. (If C: is
your only partition, youve effectively encrypted the entire drive. Note: As with all
current, third-party encryption apps, you cant use DiskCryptor on a Win8 systems boot
[C:] drive that has Secure Boot enabled. For more info, see Reader disagrees with
data-encryption advice in this weeks LangaList Plus [paid content].)
Although DiskCryptor doesnt support TrueCrypt-like virtual partitions, you can use a real
partition for a similar result. Use Windows Disk Management program or a third-party
partition tool to create a small, separate partition for your sensitive files. Then use
DiskCryptor to encrypt that partition (see Figure 10). The result is much like a TrueCrypt
volume, except that its a real partition.
Figure10. DiskCryptor's main menu for managing drive encryption
But using a real partition has some disadvantages. For example, the encrypted partition
is clearly visible in Windows Disk Management, though its labeled as unformatted.
www.WindowsSecrets.com
Page 22
Data and Internet Security Guide
And backups can be tricky. The only way to back up the files when the partition is closed
is with image-backup software. Using the default settings for EaseUS Todo Backup
resulted in an error message, as shown in Figure 11. After selecting the sector-by-sector
backup option, both the backup and the restore worked.
Figure 11. Backing up an encrypted partition with EaseUS default settings generated
an error message.
You can also open the partition and use a conventional file-backup program. But make
sure its one that has its own built-in encryption to secure your files.
On the other hand, backup is very simple with a virtual partition, which to Windows is
simply another (really big) file. Keep the file in a standard folder such as Documents
and itll get backed up automatically and regularly.
Cryptainer LE: The tool for virtual partitions
If, like me, you prefer a virtual partition, Cryptainer LE (also called Cypherix LE; site) is
the better option. The free version doesnt let you create a volume greater than 100MB
(see Figure12), but if youre judicious about what you encrypt, it might be enough.
And if it isnt enough, you can shell out U.S. $30 and get Cryptainer ME, which comes
with a 2.5GB-file limit. Shell out $70, and you can create terabyte-sized volumes. But if
youre going that big, you may as well encrypt the whole drive.
www.WindowsSecrets.com
Page 23
Data and Internet Security Guide
Figure 12. The free Cryptainer LE lets you set up small encrypted volumes.
Cryptainer is easy to set up and use; the buttons are big and colorful, and more
important theyre easy to understand. Tabs help you use and control multiple
volumes (see Figure 13).
Figure 13. Cryptainer LE has a simple menu system for creating and managing
encrypted volumes.
www.WindowsSecrets.com
Page 24
Data and Internet Security Guide
When you set up a volume, the free version appears to offer AES 256-bit and Blowfish
488-bit encryption but you actually get only 128-bit Blowfish. Again, for most people,
thats sufficient. Blowfish 488-bit and AES 256-bit encryption are, obviously, enabled in
the paid versions.
The choice: Stay with TrueCrypt or move on
If you dont already have TrueCrypt, either DiskCryptor or Cryptainer should do; it just
depends on how you prefer to work with encrypted files. (Or, if your encryption needs
are relatively simple, use file-by-file encryption as detailed in the May 15 Top Story.)
On the other hand, if youre already using TrueCrypt, you can probably stick with it at
least for a while. As Susan pointed out, a formal code review of TrueCrypt showed that it
does not have any back doors and still provides secure encryption that cant be easily
cracked. (Note: Theres still a downloadable version of TrueCrypt, but its read-only
i.e., you can open encrypted volumes to remove files, but you cant create new ones.)
Currently, Im still using TrueCrypt. But I dont know for how long. TrueCrypt, like many
other public encryption applications, can be cracked with some effort and the right tools.
With no updates, it might become more vulnerable over time. If a new version of
TrueCrypt doesnt rise from the ashes relatively soon, Ill seriously consider moving over
to Cryptainer LE or ME.
www.WindowsSecrets.com
Page 25
Data and Internet Security Guide
Pre-encryption makes cloud-based storage safer
By Fred Langa
I must confess: Until recently, I deeply distrusted the security of cloud-storage services
such as OneDrive, Google Drive, and Dropbox.
But now, thanks to pre-encryption software, Im comfortably using several cloud
services with no worries about the security and privacy of my files.
Most, if not all, cloud-storage services use some sort of server-based encryption to
protect user data. But, as has been widely reported and discussed, that protection is not
absolute if your cloud-storage account is hacked or your password stolen, your files
could be open to intruders.
Ensuring that the files you store online are truly safe requires encryption that you and
you alone control. Products such as Boxcryptor, which I discuss in detail below, make
it easy to pre-encrypt files before they leave your PC. Then, if a hacker manages to
breach the cloud servers own security, or if he intercepts your files while theyre being
transmitted, hell get nothing but indecipherable gibberish.
This type of encryption works just as easily in reverse. Files and folders travel from
online-storage servers to your PC under your personal encryption (on top of any
encryption the service might use). Decryption takes place only when the files are back
on your PC and under your local control.
Using your own encryption means that your data is always just as safe in the cloud as it
is on your PC.
Below, Ill show you step by step how pre-encryption software works. But first, Ill
address a couple of important points about cloud-storage services.
Why use cloud-based data storage at all?
For me, the primary benefit of cloud storage is for offsite backups. If your PC and local
backups are lost or destroyed by fire, flood, theft, or whatever, youll still have copies of
your files in the cloud.
(Keeping local copies is still important, too; some sort of disaster or outage could
prevent access to your cloud-stored files.)
Moreover, cloud-based storage can act as a sort of central server. No matter where
you are, a Web connection will provide quick and easy access to any file stored online.
There are dozens of cloud-storage services available; youre probably already using one
or more of the three mentioned above. But a search of the Web using the phrase cloud
storage service will reveal many more.
Pre-encryption works with most cloud-storage services; but for this article, I discuss
encrypting files and folders stored on Microsofts OneDrive. Heres why:
www.WindowsSecrets.com
Page 26
Data and Internet Security Guide
Microsoft is making OneDrive a central part of the Windows experience. The service is
built into Windows 8, and youre encouraged to back up at least some of your settings
and files to a OneDrive account. Likewise, Office 2013 and Office 365 save files to
OneDrive by default.
So Microsofts intentions are clear: If youre going to use Windows software, youre
going to encounter OneDrive. With that in mind, it makes sense to start with better
protection for your OneDrive data.
To follow along with the rest of this article, youll need a free OneDrive account. If youre
running Win8, its nearly certain you already have one. If youre running Vista or Win7, you
need a Microsoft account (which includes a free OneDrive account) and the OneDrive app
installed locally on your system. Start by creating the Microsoft account (site); then go to the
OneDrive site and click the Get OneDrive apps link in the lower-left corner of the window.
(Although XP users can access OneDrive via the Web, the local OneDrive app isnt
supported. However, XP users can use this article to encrypt their data on other, XPcompatible, cloud-storage services such as Google Drive [site].)
A free OneDrive account currently gives you 7GB of online storage, which is plenty to start
with. If you wish, you can add more storage space in increments, starting at 20GB for U.S.
$10 a year.
Pre-encryption adds automatic protection
No doubt some PC users are already putting encrypted files up in the cloud. You can,
for example, easily cobble together do-it-yourself encryption by using free tools such as
7-Zip (site). But thats cumbersome, requiring several manual steps before and after
every use of the encrypted files.
Pre-encryption software, on the other hand, is designed for use with cloud-storage
services. Its also transparent; as the authorized user, you save and open files just as
you do with unencrypted documents. Somewhat like file compression, the
encryption/decryption process is handled automatically on your local machine.
There are many kinds of pre-encryption software available. To see a list, simply search
the Web using the phrase cloud encryption.
For this article, Ive selected Boxcryptor (site). Its free for personal use; supports
Windows, Mac, Linux, iOS, and Android; and works with all the major cloud-storage
providers (and numerous minor ones see the list).
Like most pre-encryption apps, Boxcryptor creates a virtual drive on your computer. The
drive acts as staging area for files going to or from whatever cloud-storage service
youre using.
Any file dropped, copied, pasted, or saved into an encrypted folder within the Boxcryptor
drive is automatically encrypted (using a combination of AES-256 and RSA algorithms)
and synched to the cloud. Again, the process is transparent: you access and use your
cloud-based files via the Boxcryptor drive in the normal way. (Want the tech
details? See the Boxcryptor overview page.)
www.WindowsSecrets.com
Page 27
Data and Internet Security Guide
Setting up Boxcryptor, step by step
Boxcryptor doesnt do anything weird during installation, and the default settings should
work fine for most circumstances. Generally, you can just read the dialog boxes, accept
the default settings, and let the Boxcryptor installation run to completion. (See Figure
14.) Setup is fast and takes only a short time to finish.)
Note: If youre running Windows Professional, Enterprise, or Ultimate, the built-in
Encrypting File System (EFS) is enabled by default even if youve never used it. If
Boxcryptor detects EFS on your system, youll see a dialog box that will offer to disable
EFS, to prevent potential conflicts. Unless youre actively using EFS (or the related
BitLocker service), go ahead and let Boxcryptor disable EFS.
Boxcryptor will still run if you leave EFS enabled, but you could encounter conflicts when
EFS tries to decrypt Boxcryptor files or vice-versa.
(If you dont see the EFS dialog box, it just means that either you dont have EFS on
your system or its already disabled.)
Step 1: Download and launch Boxcryptor for Windows (site).
Figure 14. Boxcryptor for Windows is free for personal use. The
app is also available for Mac, Linux, iOS, and Android.
www.WindowsSecrets.com
Page 28
Data and Internet Security Guide
Step 2: When the setup wizard opens (see Figure 15), accept the Boxcryptor terms of
service and press Next.
Figure 15. The default settings in Boxcryptor's setup wizard
should work for virtually all cases.
Step 3: Click the Finish button when it appears. When you exit the installer program,
youll see a dialog box requesting that you reboot. Close all your files and programs, and
let your PC restart normally.
Step 4: After reboot, youll see a new Boxcryptor icon on your desktop, and a
Boxcryptor sign-in dialog box will open automatically (see Figure 16). (If it doesnt, click
the desktop Boxcryptor icon.) Click the Sign up button to create an account and private
encryption keys.
Figure 16. Click the Sign up button to create your
Boxcryptor account and private encryption keys.
www.WindowsSecrets.com
Page 29
Data and Internet Security Guide
Step 5: Enter your account information. As shown in Figure 17, the dialog box is
straightforward; just fill it in as indicated.
Use care when selecting a password. In Boxcryptor, your password is also used to
generate the encryption keys. A long, complex, hard-to-guess password will make
your Boxcryptor files as secure as possible.
If you need help generating a good password, try free online tools such as Nortons
Password Generator, GRCs Perfect Passwords, or the Secure Password Generator
or search the Web using the phrase password generator.
Figure 17. Create a unique, high-quality, hard-to-guess
password.
Step 6: Acknowledge Boxcryptors password warning. (See Figure 18.) Youre
responsible for retaining possession of the password. If you lose or forget your
password, Boxcryptor cant reset it for you! Store your password in a safe, snoopproof place.
www.WindowsSecrets.com
Page 30
Data and Internet Security Guide
(For suggestions on safe, easy ways to store all your passwords, see the Oct. 17
Top Story, Protect yourself from the next big data breach.)
Figure 18. You must acknowledge that your password cannot
be recovered or reconstructed if you lose or forget it.
Step 7: As a last setup step, select your Boxcryptor plan (Figure 19). In this
example, Ive selected the free option, which is fine for most private uses. (If you
wish, explore the other plans via the Plans and prices link.)
Figure 19. Boxcryptor offers plans for most personal
and business needs.
www.WindowsSecrets.com
Page 31
Data and Internet Security Guide
After you pick a plan, the Boxcryptor software will churn for a moment as it sets up
your account and generates your encryption keys. The sign-in dialog box will then
reappear.
Step 8: Sign in to Boxcryptor, using the username and password you created in
Step 5. Youre ready to go!
As one of its first acts, Boxcryptor will open a selection of tutorials (Figure 20). The
next section will show you the basics of using Boxcryptor. But its a good idea to
keep the tutorial handy so you can also work through the indicated lessons step by
step.
Figure 20. Boxcryptor starts you out with useful tutorials.
www.WindowsSecrets.com
Page 32
Data and Internet Security Guide
Using Boxcryptor with OneDrive: The basics
Boxcryptor is a cinch to use with OneDrive on Vista, Win7, and Win8.0. But theres a
small speed bump to overcome in Windows 8.1, because Microsoft changed OneDrives
fundamental operation in that version of Windows.
Win8.1s OneDrive now uses Smart Files, a default feature that does away with local
copies of your OneDrive files. This cuts down on local storage needs, which helps
space-constrained portable systems such as those running Windows RT (Microsoft
explanation).
Personally, I think this is a silly default setting. The vast majority of Win8.1 systems have
plenty of local storage space. Plus, the Smart Files feature creates two problems: it does
away with easy, offline access to your OneDrive files, and it creates an obstacle for apps
such as Boxcryptor which are designed to encrypt files locally before theyre sent to
OneDrive.
To allow for offline access to OneDrive files and to allow apps such as Boxcryptor to
work properly Win8.1 users need to configure OneDrive to operate the same way it
works in Vista, Win7, and Win8.0. This make offline change is easy, as described on
the Microsoft page, Getting started with OneDrive; scroll down to the Getting to files
when youre offline section.
Once thats done, all versions of Windows from Vista on will work with Boxcryptor in the
same way.
Heres how to Boxcryptor-encrypt your OneDrive files:
In File Explorer/Windows Explorer, click on the virtual Boxcryptor drive, as shown in
Figure 21. Youll see a heading for your local OneDrive files (which Boxcryptor
created automatically).
Figure 21. Here, Boxcryptor's virtual drive automatically
included a OneDrive (formerly SkyDrive) heading
www.WindowsSecrets.com
Page 33
Data and Internet Security Guide
Click on the OneDrive heading inside Boxcryptor, and youll see your local OneDrive
files. (For this how-to, I created a simple test file plaintexttestfile.txt, as you see
in Figure 22.)
Figure 22. Sample file (circled) in a Boxcryptor-encrypted
OneDrive folder.
To encrypt any file or folder, right-click its icon and select Boxcryptor/Encrypt from
the popup menu, as you see in Figure 23; Boxcryptor immediately encrypts the file
or folder and keeps it encrypted any time you dont have it open. (Any new files
dropped into an encrypted folder are automatically encrypted. File-by-file encryption
isnt needed.)
Figure 23. Three quick clicks encrypt any file or folder.
Thats all it takes!
Note: The first time you use Boxcryptor to encrypt files, you could encounter a small
Windows bug. On some systems, Windows might incorrectly assume that locally
encrypted files are managed by Windows Encrypted File System even when theyre
www.WindowsSecrets.com
Page 34
Data and Internet Security Guide
not! If this happens, a dialog box will ask you to export the local-authentication
certificates used by EFS. However, Boxcryptor doesnt use EFS and doesnt require
local-certificate export (Boxcryptor explanation).
To silence Windows needless nagging, just export the certificates anyway it should
take only a minute. On the Certificate Export Wizard, click Next and follow the prompts.
Once thats done, Windows shouldnt nag you again about exporting certificates.
The encryption process is very fast. Once its done, you can access and use (open, edit,
copy, paste, save, etc.) the encrypted files and folders within Boxcryptor just as you do
unencrypted files on your system. Encryption/decryption is totally transparent.
For example, if I click my encrypted plaintexttestfile.txt file, it opens normally in
Notepad, as shown in Figure 24.
Figure 24. My decrypted test file in Notepad
But Figure 25 shows what hackers would see if they hacked directly into my OneDrive
account and opened the same file in Notepad either without Boxcryptor entirely or
with Boxcryptor minus the correct password.
www.WindowsSecrets.com
Page 35
Data and Internet Security Guide
Figure 25. Access the file outside Boxcryptor, and it's gibberish
useless to hackers.
If this brief overview isnt sufficient to get you going, refer to Boxcryptors local and online
manuals, or work through the previously mentioned tutorials.
Encryption makes cloud storage much safer. Using Boxcryptor (or one of its
competitors) is another important tool for keeping your data safe and secure from all
prying eyes. Cloud encryption software lets you gain the benefits of cloud storage
without risking your privacy!
www.WindowsSecrets.com
Page 36
Data and Internet Security Guide
Send email that only the recipient can read
By Lincoln Spector
Worried about the U.S. government spying on you? Facebook, Google, Microsoft and
criminals could be spying on you, too.
Internet service providers and others can and do view personal email. Heres how to
securely send private information.
Widespread third-party access to personal email
Email is an open book. Between sender and recipient, messages pass through and are
stored on numerous online servers and some of those servers have eyeballs. If
youre using a free email service such as Gmail or Outlook.com, the company providing
that service almost certainly scans your mail for antivirus purposes and often to better
target advertising. (A CNNMoney story describes a Microsoft/Google spat over what
constitutes scanning.)
Moreover, the U.S. National Security Agency (NSA) not only scoops up mobile-phone
metadata but reportedly has copies of everyones email. And cyber criminals have their
own ways of snagging email in search of credit-card numbers and other bits of
information they can use to steal your identity and money.
The obvious solution to keeping your messages private is encrypting them a process
thats far from easy. The various recipients must have the ability and technical knowhow to decrypt your messages.
On the other hand, simple solutions have their own particular weaknesses. For example,
I know an accountant who emails sensitive material as password-protected PDFs. The
message accompanying the file informs the recipient that the PDFs password is the last
four digits of their Social Security number. But according to the How Secure is My
Password website, a desktop PC can hack a four-digit number in less than an eye-blink.
Here are three ways to send encrypted email that are both secure and relatively easy to
implement. Hopefully, the person youre sharing information with can handle one of
them.
Solution 1: Send an encrypted ZIP file
Nearly all PC users are familiar with .zip archive files. Significantly fewer .zip users are
aware that these files can be password-protected. Done right, its a reasonably easy and
quite secure way to pass along information.
Again, if you do it right.
First, you have to know what type of encryption you should use. The .zip format has its
own password protection, but its easily hacked. Fortunately, ZIP also supports strong
AES-256 encryption (more info), and thats the one to use.
Windows, too, has native support for zipping and unzipping files but not with AESlevel encryption. However, most third-party compression programs, including WinZip
www.WindowsSecrets.com
Page 37
Data and Internet Security Guide
(website) and the free 7-Zip (see Figure 26; website), do. Just make sure you pick the
correct encryption method whenever zipping a file.
Figure 26. 7-Zip offers strong AES-256 encryption.
Next, no encryption method is secure without a strong password. As my accountants
story makes clear, the password is often the weak link. You need a password you can
share with the recipient but that no one else can guess.
If you know the person well enough, you could send them clues preferably in a
separate email. Its the name of the dog you grew up with, followed by your first
boyfriends last name, ending in the year your ice-skating team won the championship.
(Good luck with that!)
More practically, you can simply text the recipient the password via cellphone. (Its
unlikely that anyone short of the NSA will intercept an Internet-based email and a
cellphone-based text and figure out that they go together.) Or call them up and give
them the password verbally. (But remind them its best not to leave it on a Post-it note
stuck to their monitor.)
Solution 2: A plug-in, email-encryption app
Most email users dont know that theres an open standard for encrypted email that
doesnt require sharing passwords with anybody. If the technology were integrated into
everyones mail client, sending and receiving encrypted mail would be no challenge at
all.
Why isnt it integrated into all mail clients? I suspect because email service providers
and others want to continue scanning your mail for useful information about you.
www.WindowsSecrets.com
Page 38
Data and Internet Security Guide
Based on the Pretty Good Privacy (PGP) technology, OpenPGP (site) uses publickey/private-key encryption. Each key is a long string of seemingly pointless text. The
public key only encrypts; you can safely share this with everybody. The private key only
decrypts; you dont share it with anybody.
Lets assume I want to send you some private information like the real identity of
Luke Skywalkers father. First, youd email me your public key. Using that, Id encrypt my
message and then send it to you. Even if the Galactic Empire intercepts both
components of the message the public key and the encrypted mail it still cant read
what I sent to you. But, thanks to your private key, you can.
Most mail clients dont include OpenPGP, but its relatively easy to add. For example,
the Chrome plug-in Mailvelope (Chrome Web store; Mailvelope site) gives several
Web-based mail services OpenPGP support. Ive tested it successfully with Gmail,
Yahoo, and Outlook.com. It works, and it makes an excellent choice when sending lots
of sensitive messages to a few tech-savvy folks.
But before downloading that OpenPGP plugin, take note of its limitations. For example,
it currently supports only straight text. Until that shortcoming is fixed, you cant use it to
send attached files.
You must use Mailvelope in Google Chrome; theres currently no support for Internet
Explorer, but a Firefox version is in development. (An early preview is available.)
Its also a bit complicated to set up and use. Heres how you typically do it for a Webbased email client:
Download and install the plugin; a new Mailvelope icon will appear in your browsers
toolbar.
Click the Mailvelope icon and select Options, as you see in Figure 27. In the left pane,
click Generate Key.
Figure 27. Mailvelope Options
www.WindowsSecrets.com
Page 39
Data and Internet Security Guide
Fill in the form. The passphrase should be a conventional password something you
can remember or store in a password manager and which others cant guess.
Click Submit when done, as you see in Figure 28. (If you get a Generation Error, try
again.)
Figure 28. Generate public/private encryption keys.
In the left pane, click Display Keys. If a key isnt visible, reload the page.
Figure 29. Display public key
www.WindowsSecrets.com
Page 40
Data and Internet Security Guide
Select the key and click the Export button. Select how you want to share your public key,
and then share it with anyone who might want to send you secure information.
Figure 30. Exporting the public key
The next time you compose an email, youll notice a new icon in the upper-right corner.
Well get to that shortly.
When you receive someones public key:
Copy the public key, then click the Mailvelope icon and select Options.
Click Import Keys and follow the prompts.
To send a secure message:
Open a new-message entry form in the usual way.
Click the Mailvelope icon in the upper-right corner of the messages body-text window.
www.WindowsSecrets.com
Page 41
Data and Internet Security Guide
Figure 31. Mailvelope's text-entry icon (highlighted in yellow) in Gmail
Type or paste your private information into the popup window.
Click the padlock icon in the upper-right corner.
In the resulting dialog box, select the appropriate recipient from the pull-down menu,
then click the Add button. The recipient will appear in the Encrypt for box as you see in
Figure 32. Click OK.
Figure 32. Enter recipient.
www.WindowsSecrets.com
Page 42
Data and Internet Security Guide
Click Transfer, then send the message the usual way.
To read a message:
Open the message. An icon of an envelope with a padlock will appear. Click it. (The
mouse pointer will turn into a key icon.)
Figure 33. Opening encrypted mail
Enter the password you used when generating your key. The secret message will
appear in a box.
www.WindowsSecrets.com
Page 43
Data and Internet Security Guide
Figure 34. Entering the decryption key to read the message
With a bit of practice, you should be able to secure and unencrypt your Mailvelope mail
relatively quickly.
Solution 3: Sendincs online mail service
If you need secure communications only occasionally, or if your recipient knows little
more than how to open an email or sign in to a website, try a solution that doesnt
require any special software or setups.
The Web-based service Sendinc (site) lets you simply and securely send and receive
messages and files. You sign in with your email address and a password (and yes, it
should be a strong one), enter the recipients email address, write a message, and
attach files (see Figure 35). Sendinc emails a notice to the recipient, who follows the
link, enters their own Sendinc password, and gets access to your sensitive information.
www.WindowsSecrets.com
Page 44
Data and Internet Security Guide
Figure 35. Sendinc's secure email-entry form
If the recipient doesnt have a Sendinc account, he or she will have to sign up for one to
see your message. Free accounts have limitations for instance, you cant send
messages larger than 10MB (but you can receive them). A Sendinc webpage lets you
compare the services free and paid versions.
How secure is Sendinc? According to the companys website, your message is
uploaded via SSL encryption and each message generates a unique encryption key that
Sendinc destroys after sending it to the recipient. Messages stay on Sendincs servers,
in encrypted form, for seven days (a default that can be changed with the paid version).
Youll find more details on the How Sendinc works page.
Coming attractions: StartMails email system
The preliminary information on StartMail (site) looks interesting. The service not yet
even in beta when I wrote this claims to be The worlds most private email: sort of a
Gmail with privacy.
According to a company representative, email will remain encrypted on StartMail servers
and cant be accessed by company employees. Sending secure messages between
StartMail accounts will be transparent to users; send a secure message to someone
using another service, and StartMail will find a way to forward it securely such as by
using OpenPGP.
www.WindowsSecrets.com
Page 45
Data and Internet Security Guide
StartMail wont be free, but it should be inexpensive. Currently, the company is planning
for fees of U.S. $5 to $7 per month.
Will it be worth the money? Ill tell you when it becomes available and Ive had a chance
to try it.
www.WindowsSecrets.com
Page 46
Data and Internet Security Guide
How to reset lost passwords for Windows
By Patrick Marshall
Depending on the version, there are several ways to gain access to Windows when
youve lost your password.
Vista and Windows 7 offer a little-known password-reset option; Windows 8 relies
primarily on your Microsoft account credentials.
Sadly, Ive been asked for help more than once by someone who has lost a family
member and needs access to the deceaseds computer. (Passwords are not something
you should take with you.) Less tragically, I also know many more people who have
important information stored on an old computer thats locked by a forgotten password.
Those passwords can be reset, but the technique depends on the version of Windows
youre running, the type of user account youve chosen, and whether youve taken any
steps in advance for password recovery. Ill go through each of the available options.
Password reset disk: Be proactive, not reactive
A small amount of preplanning can save you or your family a lot of passwordrecovery effort. The simplest and most certain way to recover a lost password is to
create a password-reset disc or USB drive. Built into Vista, Win7, and Win8, this option
works only with local accounts. If youre on a domain, youll have to talk to your system
administrator. With Win8, Microsoft encourages users to create an MS account during
initial setup you wont find options for creating a password-reset disk. Instead, you
can set up an online password reset with Microsoft.
Obviously, youll want to keep the reset disk in a secure location and, of course, let
your family know about it.
Assuming youre signed in to a local account, click Control Panel/User Accounts. In the
left column, select the option Create a password reset disk as shown in Figure 36.
(This option will not appear if youre attached to a domain.) Next, a wizard will ask for
your current password and the drive you want to use to store the password-reset file.
www.WindowsSecrets.com
Page 47
Data and Internet Security Guide
Figure 36. For local Vista and Win7 accounts, the Control Panel's User Accounts utility
includes an option for creating a password-reset disk.
Windows will let you use your password-reset disk when youre at the Windows sign-in
screen and your password entry fails. Click the Reset password link, and the Password
Reset Wizard will ask for the location of your password-reset file. Once youve provided
that information, the wizard will request a new password.
If you change your Windows password, you wont have to create a new password-reset
disk. You need to create the disk only once, and it will work thereafter no matter how
many times youve changed your working password. Thats all the more reason to store
the reset disk in a safe place.
Windows 8: Your password is stored with Microsoft
Yes, I know thats a scary concept. But if youve used any of Microsofts online services,
youve probably already given your MS account sign-in password to Microsoft. And you
most likely have an MS account if youre running Win8. In either case, you might also
have a 25-character account recovery code. To check, do the following.
Go to any online MS service Outlook.com, for example and sign in to your MS
account. In the upper-right corner of the window, click on your account name and select
Account settings. Next, in the panel on the left, select Security & password. Youll
have to clear a security hurdle to view the details of your account information (see
Figure 37). Specifically, youll have to give the last four digits of your phone number or a
backup email address youve set previously. Microsoft will then send you a reset code to
enter into the user-verification window.
www.WindowsSecrets.com
Page 48
Data and Internet Security Guide
Figure 37. It's not airtight security, but to retrieve a Microsoft account password, you'll
need to have access to your cell phone or email account.
This security verification will obviously complicate things if youre resetting the password
for someone else. Youll need to have access to either their email account or cellphone.
In the Protect your account window, look for the Recovery code section. If theres a
Set up link, click it to see your 25-character, account-recovery code. If youve already
set one up, the link will say Replace. In either case, youll have the option to copy or
print the code.
If youve lost your MS account credentials (or youre trying to recover someone elses),
go to an online MS service (such as outlook.com) and click the Cant access your
account? link. Youll then be prompted to select the reason you cant open your
account. Select I forgot my password, and youll be asked to enter the account youre
trying to access. Youll also be asked to enter a CAPTCHA.
Next, youll see the now-familiar screen asking whether you want a seven-digit, one-time
security code sent to a preselected email address or to your phone. If you dont have or
know either, click the I dont use these anymore link and enter the 25-character code
you established earlier.
One thing to keep in mind: Unlike the Vista/Win7 password resetdisk option, an MS
account recovery code might have changed.
Accessing a user account via a Windows setup CD
If youre using a local account but didnt prepare a password-reset disk, there are still
options. If you have a bootable Windows installation disc, you can be back in business
in no time. Keep in mind, however, that this method wont help you access encrypted
data youll still need the original password.
www.WindowsSecrets.com
Page 49
Data and Internet Security Guide
Boot the computer using the Windows CD (this might require changing the BIOS to
make the CD drive the first boot device). At the first Windows screen, select Repair your
computer (Figure 38).
Figure 38. You can reset passwords with the Repair your computer option, accessed
via a Windows installation disc.
www.WindowsSecrets.com
Page 50
Data and Internet Security Guide
Next, select the Command Prompt option (Figure 39).
Figure 39. The Windows installation disc offers an array of repair tools; choose the
Command Prompt option.
At the command prompt, type copy c:\windows\system32\sethc.exe c:\ and hit Enter.
(Youre making a copy of the Windows sticky keys executable on the local C: drive.)
Next, type copy c:\windows\system32\cmd.exe c:\windows\system32\sethc.exe and
hit Enter. (Youre making a copy of the command-prompt executable.) When asked
whether you want to overwrite the existing file, select Yes.
Reboot the computer. When the sign-in screen appears, hit the Shift key five times,
which will open an admin-level command prompt. (If a sticky-keys dialog box opens,
select Yes.)
At the command prompt, type net user {sign-in} {new password} replacing {sign-in}
with the user account youre trying to access and {new password} with a new password.
(Note: If the user name includes spaces, enclose the entire name in quotes.)
Windows should open normally.
Resetting passwords without install/reset media
For various reasons, you might not have a Windows installation disc and you might
not have known about the password-reset options. There are free utilities that let you
reset the password for an existing user account. (Again, this wont help with encrypted
files.)
www.WindowsSecrets.com
Page 51
Data and Internet Security Guide
Password-reset programs work by locating the Windows SAM file, which contains the
encrypted passwords. The catch is that the file isnt accessible while the Windows
operating system is running. So reset programs generally boot a version of Linux and do
their work from there. Taking a sort of brute-force approach, they dont attempt to
decrypt the passwords they erase them, which then allows access to the Windows
account.
The tool I use is Offline NT Password & Registry Editor (download site). And, yes:
despite the name, it works fine with current versions of Windows.
Download the ZIP-based CD image (theres also a bootable USB version), unzip it, and
then burn the ISO file to a CD.
Boot the computer from the CD; the editor will be launched within a Linux session. A
series of prompts will select the Windows partition and path to the Registry. Fortunately,
the default choices are usually correct, so its likely that you can just hit Enter
repeatedly.
Dont be thrown by the fact that the editors non-graphic interface throws a lot of
unintelligible text on the screen (see Figure 40); you dont need to understand it.
Figure 40. The interface isn't pretty, but the Offline NT Password & Registry Editor makes it
easy to reset Windows passwords.
Next, the editor asks what you want to do. Select Edit user data and password. The
editor then offers a list of installed user accounts. Enter the user account you want to
reset and then select option 1, which will clear the user password.
www.WindowsSecrets.com
Page 52
Data and Internet Security Guide
Click the Q key to leave the editor.
Reboot, and youll be able to launch the user account without a password.
Court of last resort: Cracking tools
If all else fails and especially if youre trying to access encrypted files the only way
youll get access is with the correct credentials. That means youll need to retrieve
not reset the missing password. And even with the best password crackers available,
thats not a sure thing.
Password crackers work by locating the hashed (or coded) passwords on the system
and then comparing them to translation tables called rainbow tables. If the files were
encrypted by Windows, those passwords are contained in the Windows SAM file. So
crackers, like password-resetting programs, must run under another operating system,
typically Linux.
Keep in mind that the longer and more complex the password, the less likely it is that a
password cracker will be successful.
I tested one of the most popular cracking programs Ophcrack (site) which you
burn to CD. For most users, the automatic mode is the best choice (see Figure 41). But
you can also run the cracking process manually.
Figure 41. Most users will want to use Ophcrack's automatic passwordcracking mode.
www.WindowsSecrets.com
Page 53
Data and Internet Security Guide
In my tests, the automatic mode quickly located all password hashes stored in Windows
and cracked the ones it could, as shown in Figure 42.
Figure 42. When Ophcrack is finished crunching hashes, it returns a report of all accounts'
password status.
As expected, the free version of Ophcrack was unable to crack longer and more
complex passwords in Win7 and Win8. It might do better if you pay for more detailed
cracking tables, but even then Ophcrack cant handle passwords longer than 14
characters. Still, given the simple passwords that most PC users employ, your chances
are good.
These tips point out that Windows basic security is far from foolproof. Its fine for
keeping casual intruders out of your system, but it wont stop a determined data thief.
Thats sort of a silver lining when you need to help yourself or someone else access
documents, photos, and so forth that you or they have a legitimate right to.
For more information on giving others access to your accounts when needed, see the
Sept. 15, 2011, Best Practices story, Passwords dont take them with you, and the
Jan. 7, 2012, Seattle Times article, Digital estate planning often forgotten.
www.WindowsSecrets.com
Page 54
Data and Internet Security Guide
PREVENT AND REMOVE MALWARE
Two tips for removing malware
No matter how careful we are, malware and unwanted apps still seem to crawl onto our
systems from time to time. Whether its true malware or software that hitch-hiked along
with an application you purposely installed, they can be difficult to remove. Here are
some removal techniques that might help.
Suspicious software that wont uninstall
An application that doesnt uninstall easily is often malware or at least feels like
malware. When automatic tools cant uninstall software you dont want, you can almost
always accomplish the task manually with these easy steps: delete the software from
the Registry, delete it from the hard drive, and then verify that your system is clean.
Piece of cake!
Heres that process spelled out in greater detail:
Open RegEdit and use the Find function to search the Registry for any instance of the
offending software. Delete any keys that reference that software. In this case, for
example, I suggest performing separate searches for wincleaner, oneclick,
one click, and business logic (WinCleaners publisher).
Next, use Windows/File Explorer (or the search tool of your choice) to search all hard
drives. Use the same search terms: wincleaner, oneclick, one click, and business
logic. Delete any applicable files and folders the search turns up. Note: Make sure
Explorer is set to search all locations and show all files including hidden and system
files.
Reboot.
Ensure your PC has no malware on it; use an anti-malware tool thats separate from
whatever anti-malware tool you normally use. For multiple options, see the April 11,
2013, Top Story, A dozen tools for removing almost any malware.
Reboot.
Run a good Registry cleaner, such as CCleaner (free/paid; site).
Reboot again.
Your PC should now be free of the previously uninstallable software!
Free tool removes malware
Unwanted browser extensions and toolbars can be difficult. For example,
Search.conduit is a tag-along browser toolbar/extension that typically gets installed
along with various other freeware/shareware offerings. If it finds its way onto your
system, you might want to reconsider the types of software youre downloading and
www.WindowsSecrets.com
Page 55
Data and Internet Security Guide
the places from which youre downloading them. Your current choices might be putting
you at risk!
Search.conduit can be especially difficult to get rid of. It will reinstall itself if its not
completely rooted out. It can also install itself again if you have the same browser on
multiple systems and all copies are synched via the cloud. Remove the unwanted
software from one device, and the browser-synching process brings it back from one of
the other connected devices.
Fortunately, theres an easy fix for search.conduit. The free AdwCleaner specifically
targets this type of software. AdwCleaner (see Figure 43) is available from all the major
download libraries, such as Download.com (AdwCleaner page; use the Direct Download
link).
Figure 43. The free Adwcleaner finds and removes many types of
unwanted software from PCs.
Note: If youre using any form of Web-based browser synching across multiple PCs or
mobile devices, work on only one system at a time keep the others off and inert.
This will prevent the software from resynching itself back to your cleaned devices.
Heres how to clean search.conduit from your browsers:
Run AdwCleaner; let it remove any malware it finds.
Reset all your browser settings to default (more on this in a moment).
Reboot.
Run AdwCleaner again to make sure search.conduit is truly gone.
Your browser should now be clean!
Your browsers support pages should have instructions on how to reset the browser to
its default state. It usually takes only a couple of clicks.
For example, to reset Internet Explorer, see Microsoft Support article 923737. For
Firefox, see the Mozilla support page. For Chrome, see the Google support page.
www.WindowsSecrets.com
Page 56
Data and Internet Security Guide
Tweaking Windows to block CryptoLocker
If you have Windows Professional or higher, you can tweak your systems to protect
them against CryptoLocker. Youll want to thoroughly test the impact of the settings
changes detailed below and be prepared to roll back to your original settings if
needed. (After making some of these changes, you might not be able to install or update
some applications.)
All business and Pro versions of Windows include the ability to prevent certain types of
software from launching from specific locations. CryptoLocker launches from a specific
location and in a specific way (well, for now). By implementing Windows Software
Restriction Policies rules, we can block CryptoLocker from launching its payload in your
computer.
Software Restriction Policies (more info) were first introduced in Windows XP and Server
2003. In a domain setting, you can use Group Policy to set up these restrictions or
rules; on standalone machines, you can use Local Security Policy. (Windows Home
Premium doesnt support Group or Local policies, so none of the following settings
changes is supported.)
Again, be sure you test these settings changes on a single workstation first before rolling
them out to other systems. Also, take the extra step of undoing the changes and
checking whether the test system still runs as expected. Most important: Back up all
systems before making the changes.
To make the changes, click Start/Control Panel/Administrative Tools. Click Local
Security Policy and locate Software Restriction Policies under the Security Settings
heading. Right-click it and select New Software Restriction Policies. Right-click
Additional Rules and select New Path Rule to open the new-rule dialog box shown in
Figure 44.
www.WindowsSecrets.com
Page 57
Data and Internet Security Guide
Figure 44. Creating a new path rule to block CryptoLocker
The following rules block applications such as CryptoLocker from running in the defined
locations. For example, the first set of rules applies to the specific user folder
%Appdata%, which equates to user\{yourusername}\appdata\roaming.
Enter the following sets of Path, Security Level, and Description information as separate
rules:
For Windows XP, enter the following:
Path: %AppData%\*.exe
Security Level: Disallowed
Description: Dont allow executables from AppData
and
Path: %AppData%\*\*.exe
Security Level: Disallowed
Description: Dont allow executables from AppData
www.WindowsSecrets.com
Page 58
Data and Internet Security Guide
For Windows Vista and higher, use the above settings plus the following:
Path: %localAppData%\*.exe
Security Level: Disallowed
Description: Dont allow executables from AppData
and
Path: %localAppData%\*\*.exe
Security Level: Disallowed
Description: Dont allow executables from AppData
Additional paths for blocking ZIP-file locations are described in the
bleepingcomputer.com CryptoLocker Ransomware Information Guide and FAQ. The
following will ensure the virus cant launch from embedded or attached .zip files.
Path: %Temp%\Rar*\*.exe
Security Level: Disallowed
Description: Block executables run from archive attachments opened with
WinRAR.
From archive attachments opened with 7zip:
Path: %Temp%\7z*\*.exe
Security Level: Disallowed
Description: Block executables run from archive attachments opened with 7-Zip.
From archive attachments opened with WinZip:
Path: %Temp%\wz*\*.exe
Security Level: Disallowed
Description: Block executables run from archive attachments opened with WinZip.
From archive attachments opened using Windows built-in .zip support:
Path: %Temp%\*.zip\*.exe
Security Level: Disallowed
Description: Block executables run from archive attachments opened using
Windows built-in ZIP support.
www.WindowsSecrets.com
Page 59
Data and Internet Security Guide
Figure 45 shows the Software Restrictions Policies section with newly entered rules.
Figure 45. A completed set of software restriction policies
When youre done entering new rules, reboot your system so that the changes take
effect. Again, if you discover you can no longer update some applications or install
software, you might need to undo some of these changes. Look in your application
event log or in the admin section for the specific rule thats misbehaving. (To open
the log, click Control Panel/Administrative Tools/Event Viewer; then, in the navigation
pane, click Windows Logs/Application. For more on the Event Viewer, see the Oct. 27,
2011, Top Story, What you should know about Windows Event Viewer.)
As the malware authors change their tactics, you might need to revisit the rules settings;
Ill try to post updates into the Windows Secrets Lounge whenever needed.
For even stronger CryptoLocker protection, those folks with solid IT savvy might want to
consider application whitelisting i.e., setting up a list of applications approved to run
on their workstations. All other software installations are blocked. See the National
Security Agency (yes, that NSA) document (downloaded PDF), Application whitelisting
using Software Restriction Policies.
Be aware that application whitelisting is a highly advanced tactic. Take some time to
determine all allowed applications in order to properly set up application whitelisting.
Once again, keeping your AV software up to date is not the panacea for CryptoLocker.
www.WindowsSecrets.com
Page 60
Data and Internet Security Guide
Shedding some light on security-cert warnings
By Susan Bradley
On a daily basis, we are bombarded with confusing error messages that can lead to
making bad decisions about our online security.
Whether from Java, our browsers, EMET, or some other source, heres what you should
know about the warnings.
Sorting out problems with Java security
I live in California, where the car is king a MINI Cooper, in my case. At a stop light,
Im fully aware that red means stop, green means go, and yellow means slow down (in
theory; this is California, after all). If only warnings on our computers were that clear and
simple. All too frequently, our Web browsing is interrupted with confusing security
warnings not just from websites but also from Web-enabled devices and, more
recently, Java-enabled platforms.
Many of these warnings lack any real explanation, making it difficult to understand the
security consequences of the options were offered.
For example, after the recent Java V7 Update 51 has been installed, Java apps need to
be signed with a digital security certificate. If theyre not, theyll be blocked from running.
I ran into this problem with my Western Digital My Cloud network-storage device; it
would no longer run its Java-based, mapped-drive application. Instead, I received an
error message stating: Java error: Missing required Permissions manifest attribute in
main jar. (Is that obtuse, or what?)
The workaround for the missing certificate was to place an exception in the Java control
panel. (I dont recommend following Western Digitals instructions to lower the security
settings, as noted on its help site.)
Unfortunately, where to put that exemption was at first elusive. According to the Java
instructions, its located in the Java control panel, under the Security tab (see Figure 46).
But it wasnt there. Eventually, I discovered that I had both 32-bit and 64-bit Java
installed. Removing the 64-bit version revealed the previously missing exemptions
control.
www.WindowsSecrets.com
Page 61
Data and Internet Security Guide
Figure 46. If the exemptions list doesn't show up under the Security tab,
check that you have only one version of Java installed.
Enter application exemptions with the following steps:
In Windows, click Start/Control Panel/Java and open the Java control panel.
Click the Security tab, then click Edit Site List in the lower half of the dialog box.
www.WindowsSecrets.com
Page 62
Data and Internet Security Guide
Enter the problematic sites or applications URL. In the case of the balky WD My Cloud
app, I entered the drives address, as shown in Figure 47. (The URL will, of course, be
different for any other device.)
Figure 47. To exempt Java-based sites or apps from being blocked, simply add their
URL to the exception site list.
Click OK to save your changes and exit.
The process can get more complicated for network administrators. For example, to
continue using some remote-access tools, theyll need to enter the URL for remote
servers. Tools that use self-signed certificates need to be exempted. Two examples are
HPs iLO server-management app and Dells DRAC remote-access card/app.
Interpreting common webpage warnings
Almost everyone whos gone onto the Web has at one time or another received that
annoying and often confusing error message: This page contains both secure
and nonsecure items. Fabulous. Now what do I do? you grumble. Ignore the
warning? Whats really going on?
www.WindowsSecrets.com
Page 63
Data and Internet Security Guide
A Troy Hunt blog post provides a succinct answer plus a more informative, longer
explanation. He points out that the message is not really about security; its more about
bad coding.
Webpages often pull content from more than one server. (Ads and content, for example,
often come from separate webservers.) The main part of the page is designed to
download over a secure https: connection using Secure Sockets Layer encryption. But
a component of the page is trying to make an unsecured connection. That could defeat
the security of the entire webpage.
A properly coded page uses either http: or the more secure https: throughout. (Troy
notes that this is an issue for all browsers.) A fully SSL connection ensures that all
content comes from the correct servers and that no content was inserted by an
unsecure and possibly malicious webserver.
What can you do about these confusing error messages? Not much the problem can
be fixed only by the websites coders. In most cases, if you skip past the warning, you
just wont see the content downloaded over http:.
EMET 4 puts up warnings about Facebook
If youve installed Enhanced Mitigation Experience Toolkit (EMET) Version 4, you might
have seen warnings, shown in Figure 48, about an untrusted Facebook certificate not
on Facebook but on sites that have social-networking share buttons or Like buttons.
(Anyone who has upgraded to EMET 4.1 or to the newly released EMET 5 preview
should not see these warnings.)
Figure 48. An error caused by an expired
certificate-pinning rule
The source of the warning is an EMET 4 certificate-pinning rule that expired on Dec. 31,
2013. Certificate pinning has been in Google Chrome since 2011 but was only recently
added to EMET. As noted in a Random Oracle post, Pinning addresses [the problem of
potentially bogus security certificates] by allowing a website to commit in advance to a
set of [certificate authorities] that it will do business with.
In other words, pinning sets the specific SSL certificates that a site will trust and accept.
EMET adds the ability to add expirations to SSL certificate pinning. But it never really
explains the related warning. It would be better for all users if EMET noted that its
pinning rule needed to be updated or, in this case, that we need to update to a newer
EMET version.
The situation became more complicated after it was revealed that EMET 4.1 can
potentially be bypassed by malicious hackers, as reported in a Feb. 25 PCWorld article.
www.WindowsSecrets.com
Page 64
Data and Internet Security Guide
You might consider downloading and testing EMET 5.0 (site) but only if you use
Chrome as your default browser and dont plan on watching YouTube videos.
When I tested EMET 5.0 on IE and attempted to watch various videos on YouTube, the
site crashed. I received an error message (see Figure 49) EMET detected ASR
mitigation in IEXPLORE.EXE Component: Adobe Flash Player 12.0 r0 thats
discussed in a 0xdabbad00.com post.
Figure 49. An EMET 5.0 error that crashed YouTube
Given that I was trying to watch Pharrell Williamss Happy (Official Music Video), I was
not especially happy that I needed to roll back to EMET 4.1 at least for the time
being.
Hardening up security certificates in Windows
Recently, Microsoft started pushing out updates that remove older encryption protocols.
In February, it released KB 2862973 for Windows Vista, Win7, Win8, and Windows RT
plus Windows Server 2008, 2008R2, and 2012. The update restricts the use of root
certificates with MD5 hashes (more info). You must have KB 2862966 installed before
deploying this update.
I recommend installing this update; itll increase the security of those SSL certificates
that Windows blindly trusts simply because it trusts the originating root certificate. So
far, Ive seen no side effects from either update.
Initially, I believed KB 2862973 was needed only for managed networks. But after a
closer look, I now think its best that we all tighten up the screws on SSL certificates
and ensure we remove older encryption standards to protect ourselves from spoofed
root certificates.
Hardened enforcement of signed code coming
Although we installed KB 2893294 (MS13-098) this past December, the patch wont go
into effect fully until June 10. On that date, as noted in an MS Security Research and
Defense blog post, installers are harden; application code will be considered unsigned if
its installer doesnt conform to the new verification process. After June 10, you might
need to disable this enforcement to install older, noncompliant applications.
Noncompliant UEFI Modules
Also this past December, Microsoft released KB 2871690, an update for Windows 8 and
Windows Server 2012 that revokes the digital signatures for nine private, third-party
UEFI (Unified Extensible Firmware Interface) modules that could be loaded during UEFI
Secure Boot. Secure Boot protects your system from rootkits; or, as noted in a TechNet
www.WindowsSecrets.com
Page 65
Data and Internet Security Guide
article, it helps ensure that a PC boots using only firmware trusted by the PC
manufacturer.
However, some users reported in a Microsoft Answers forum that they couldnt install
KB 2871690 without receiving an error. The patch would install only if they disabled
Secure Boot, installed the update, and then turned Secure Boot back on.
It now appears that Microsoft revised the update to fix that issue. The source of the
problem seems to be an improperly signed security certificate.
In the end, you have to trust your instincts
I spend a lot of time working with PC and network security. But even I get confused by
some of the error messages popped up by various websites. My recommendation: Go
with your gut feeling. Exit a site if you dont feel comfortable with any error messages
that might appear. Thats especially the case when new security warnings pop up with
sites youve previously visited. The safest policy is to leave the site and close down the
browser to clear it.
For example, in early January, Yahoo banner ads were infected with code that injected
Java-exploiting malware. The malicious ads were served up by Yahoos own service:
ads.yahoo.com, as reported in a ZDNet blog.
Also consider adding Web-based filtering by using such services as OpenDNS.
Changing your routers DNS entries to point to opendns.com will help block malicious
websites.
To quote Michael Conrads character in the TV series Hill Street Blues: Lets be careful
out there!
www.WindowsSecrets.com
Page 66
Data and Internet Security Guide
Mobile security: Apps to protect Android devices
By Fred Langa
There are hundreds of free and paid security apps for Android phones and tablets. But
many of those offerings are of uncertain quality.
Heres a sampling of some of the best software for keeping Android devices free of
malware, managing passwords, locking up your data, and more.
Android needs third-party security apps
If you have an Android phone or tablet, theres good news and bad news.
The good news: Youve picked the worlds best-selling mobile operating system.
Something like 70 percent of all new phones and tablets run Googles OS. Thats a
strong incentive for software developers to build cool applications for the platform.
The bad news: Androids open architecture and popularity have made it a favorite target
for malicious hackers, thieves, and other criminals.
Androids built-in security features have never been strong, and even the latest version
(4.4.4, as I write this) offers only modest safeguards for your personal data and
communications. For that reason, all Android devices need third-party security apps in
order to be safe. (Virtually no operating system, by itself, is safe from malicious
hacking.)
Fortunately, there are plenty of Android security tools to choose from. The Google Play
Store has all manner of free and commercial apps. Note, however, that some are junk
amateurish software that could cause crashes, hangs, slowdowns, or other problems.
Other tools seem to work fine until you look at them more closely. Take, for example,
some free virtual private networking (VPN) apps, which provide some Web-browsing
anonymity (especially on public Wi-Fi) by routing your data through the VPN providers
servers. If the service is free, how does the provider pay the bills for running the servers
and buying Internet bandwidth? How does the provider keep the lights lit? A cautious
person might suspect that the company is mining user data.
That said, there are many reputable companies with excellent Android security products.
Some are familiar and well-respected names you might recognize from the Windows
world, while others are relative newcomers who develop products exclusively for mobile
operating systems.
Below, Ill provide summaries of well-regarded security apps some paid, others free
in five essential categories:
Antivirus/anti-malware suites
Password management and encryption
Lost or stolen device recovery
VPNs
www.WindowsSecrets.com
Page 67
Data and Internet Security Guide
Secure file-wiping (to delete personal data when youre selling or trading in your device)
(Note: The following information applies equally to all portable Android-based devices,
including tablets. But for brevity, Ill use phone throughout the rest of the article.)
Security suites: The absolutely must-have apps
The cornerstone of Android safety is a good security suite from a reputable vendor.
Even a single, well-designed security app can provide coverage against a wide range of
attacks and dangers.
Lookout Security & Antivirus (Google Play page; publishers website) is a typical
example of a reputable suite in the security category. It offers a comprehensive selection
of tools (see Figure 50) some free and others paid. (Ill list other brands in a moment.)
Figure 50. Lookout Security & Antivirus offers basic
security features for free; additional features are in
its paid version.
Lookouts free version provides:
Anti-malware: It gives automatic, always-on protection from viruses, adware, spyware,
and other types of malware.
www.WindowsSecrets.com
Page 68
Data and Internet Security Guide
Lost/stolen phone recovery tools: A map shows you the phones location (see Figure
51), viewable via a free, private account on the Lookout website.
The Scream option sounds a loud alarm, even if the sound was turned off. The
alarm might scare a thief into abandoning the phone, but it can also help in more
mundane situations such as when you simply misplace the phone at home or the
office. The sound will lead you to the phones location.
Figure 51. Lookout can help you locate and
recover a phone, whether it's been stolen or just
lost in the sofa cushions.
Signal flare: This option saves your phones location when the battery is about to run
out. It might help you find the phone once its gone dead.
Automatic backups: Your contacts are saved to your private account on the Lookout
website. You can download the contacts to your PC or to a new or secondary device.
Multiple device support: The free account is limited to two devices.
Lookouts paid version adds:
Expanded Theft Alert features: You can have the phone send an email to your PC in
the following circumstances:
www.WindowsSecrets.com
Page 69
Data and Internet Security Guide
1. The phones unlock passcode is incorrectly entered more than three times in a
row.
2. The SIM card is removed.
3. Airplane mode is enabled or the device is turned off (two tricks thieves might
try to avoid detection), or a thief tinkers with the phones Device Administrator
mode.
Lookouts notification email includes a map of the phones location when the Theft
Alert was generated plus a theftie a photo of the person holding the phone at the
time the alert was triggered, taken automatically with the phones built-in camera.
The same Theft Alert information is posted on your private account on the Lookout
website.
Privacy Advisor: This lets you manage the permissions and personal data that each
app on the phone can access.
Remote lock and wipe: In the event the phone is stolen and not recoverable, you can
remotely lock it and erase your personal data.
Safe Browsing: This option alerts you when you visit websites known to harbor malware
or other security threats.
Photo and call-history backups: Use this tool to automatically clone photos and call
data to your private Lookout account.
Multiple device support: This lets you manage up to three devices from a single
Lookout account.
You can test-drive Lookouts paid version for up to two weeks at no cost; after that, its a
modest U.S. $3 per month or $30 per year.
Again, Lookout Security & Antivirus is just one example of a typical, comprehensive,
Android security suite. There are other suites with similar features.
For example, Avast Mobile Security & Antivirus (Google Play page; publishers site)
doesnt take thefties of would-be phone thieves, but its paid version does offer GeoFencing the phone performs a specified action (lock, siren, send location, and so
forth) if it passes outside a perimeter youve established, such as a set distance from
your table in a caf. It also offers App Lock, which lets you passcode- or gestureprotect access to specified apps.
Avast Mobile Security & Antivirus is available in both free and paid versions; after a 30day free trial, the premium edition costs $2 per month or $15 per year.
Bitdefender is another name that might be familiar to Windows users. Its Mobile
Security & Antivirus (Google Play page; publishers site) is also available in free and
paid versions. Its features are similar to Avasts, but it tries to differentiate itself with
aggressive pricing. After a two-week free trial, the paid version costs only $1 per month
or $10 per year.
www.WindowsSecrets.com
Page 70
Data and Internet Security Guide
You can download Kaspersky Internet Security (Google Play page; publishers site)
for free. You must register with Kaspersky for the paid editions 30-day free trial; its $15
per year to keep. Two advanced features are Call & Text Filter, which helps block
unwanted calls and texts, and a theftie option similar to Lookouts; it can automatically
take a photo of a would-be thief.
Again, you can find many more security suites, apps, and options by visiting the Google
Play Store and using the search string security or security suite.
Password management and data encryption
Its likely youve already been affected by one or more of the recent and massive
corporate hacking incidents such as the data thefts at Adobe, Target, eBay, and others.
One of the best ways to protect yourself against these increasingly common hacks is to
use a unique password for every site. (See the Oct. 17, 2013, Top Story, Protect
yourself from the next big data breach.)
Remembering potentially dozens of passwords sounds burdensome, especially on a
phone or tablet where typing can be difficult. But password-management software
makes it vastly easier. The software does the hard lifting for you, remembering all
passwords and storing them in a securely encrypted database.
If youre using password-management software on your PC, theres a good chance you
can find an Android equivalent. That can greatly simplify setup and use because the
software will already be familiar. It might even be able to access and use the database
of passwords on your PC, saving you from the chore of re-entering everything again.
For example, RoboForm (possibly the worlds most popular password manager) has a
free Android version (Google Play page; publishers site) that connects with an existing
desktop RoboForm Everywhere account ($10 per year). Androids built-in browser (a
version of Chrome) doesnt work with third-party password apps, so RoboForm comes
with its own mini-browser that you can use to sign in to password-protected sites. You
can also use the RoboForm app with Android editions for Dolphin or Firefox.
Similarly, there are two free Android versions of the popular, open-source, desktop
Keepass Password Safe. One is called Keepass2Android Password Safe (Google
Play page; publishers site) and is shown in Figure 52.
www.WindowsSecrets.com
Page 71
Data and Internet Security Guide
Figure 52. As with other password managers,
enter a site's password once and
Keepass2Android will then remember it for you.
The other Android version of Keepass is called KeepassDroid (Google Play page;
publishers site). Both versions operate much like the desktop version of KeePass, and
they share the same database format.
If desktop commonality isnt an issue for you, the free/donationware, open-source
Universal Password Manager (Google Play page; publishers site) might be of interest.
You can find many similar apps by using the search terms password manage and
manage password (though seemingly similar, the two searches yield slightly different
results).
Apps for recovering lost or stolen phones
As already mentioned, many of the best Android security suites (Lookout, Avast,
Bitdefender, Kaspersky, and so forth) come with robust tools that can help you find and
recover a lost or stolen phone typically by sending you a map of the phones location,
letting you wipe or lock the phone, and even snapping a photo of the thief.
www.WindowsSecrets.com
Page 72
Data and Internet Security Guide
But most versions of Android also include basic, built-in features that can reconnect you
with your phone or wipe it clean. For example, Android 4.1 and higher includes the
Device Manager app (see Figure 53) that can, when linked to your Google account,
locate your phone on a map and let you remotely ring, lock, or erase it. The specific
details are explained in the Android Device Manager support page.
Figure 53. Android's built-in Device Manager lets you locate, ring, lock, or
erase a lost phone remotely from your Google account running on another
device (shown above).
Older versions of Android 2.2 and higher allow for basic remote wiping, as
explained on the Remote Wipe a Mobile Device support page.
Those tools are better than nothing, but third-party apps such as the following can do
more for example, take photos of a would-be thief. Visit the associated websites for
full details.
www.WindowsSecrets.com
Page 73
Data and Internet Security Guide
Wheres My Droid (Google Play page; publishers site) offers basic capabilities for free
(see Figure 54) plus extended features such as remote lock for $4.
Figure 54. Where's My Droid offers good lost device
recovery features, including a GPS-based locator.
AndroidLost (Google Play page; publishers site) is completely free, though the
programs author accepts voluntary donations.
Locate My Droid (Google Play page; publishers site) also is free, with voluntary
donations accepted.
Virtual private network apps for Android
A virtual private network (VPN) connection can let your phone operate securely,
privately, and anonymously from any site even from public hotspots in coffee shops,
airports, restaurants, hotels, and so on.
A VPN uses encryption to establish a secure, private channel between your PC and the
VPN providers server. That server, in turn, then connects to whatever website or other
server you want to reach (see Wikipedias VPN article).
But you really want to trust the VPN provider, because itll potentially have access to
your unencrypted data. Most legitimate VPN services recover their costs by charging a
modest fee based on your data usage or by displaying ads as you use their service. I
think this is an important consideration, because a provider with a viable revenue stream
www.WindowsSecrets.com
Page 74
Data and Internet Security Guide
should never feel tempted to mine your data stream for usernames, passwords, creditcard numbers, and so on.
Here are some of the better-regarded Android VPN services and their associated client
software:
VyprVPN for Android (Google Play page; publishers site) three-day free trial; $7
$20 per month thereafter, depending on plan details
ExpressVPN (Google Play page; publishers site) one-day free trial; $8$13 per
month thereafter
IPVanish (Google Play page; publishers site) one-week, money-back guarantee; $5
$8 per month thereafter
Hotspot Shield: VPN Proxy WiFi (Google Play page; publishers site) free, adsupported version; ad-free Elite version, $30 per year.
Apps for thoroughly sanitizing Android devices
No, this is not dipping your phone into a glass of Lysol. When its time to sell or trade in
your phone, all recent-vintage Android-based models let you easily restore the original
factory configuration. That makes it harder but not impossible for the next user to
recover traces of your data left behind in the phones flash memory.
In fact, completely erasing flash memory is technically difficult and could require special
tools and extra steps. (For more info, see the Sept. 13, 2012, Top Story, Rethinking the
process of hard-drive sanitizing.)
If your phone uses a removable SD memory card, scrubbing it is relatively easy. The
best bet is to remove the card, connect it to your PC, and use the tools described in the
aforementioned Top Story. (Or, if you can, simply keep the SD card, possibly reusing it
in some other device you own.)
But when the flash memory is built into the phone, its harder to get at and harder to
erase. These apps can help:
www.WindowsSecrets.com
Page 75
Data and Internet Security Guide
SaniDroid (Google Play page; publishers site) $1
Figure 55. Special-purpose apps such as Sanidroid
can help remove lingering traces of personal data
from a phone you're selling or trading in.
iShredder 3 (Google Play page; publishers site) free and Pro versions ($3.50); see
site for details
Secure Wipe (Google Play page; publishers site) free
SHREDroid (Google Play page; publishers site) free (doesnt work on Motorola
devices)
File Shredder (Google Play page; publishers site) free (works only on a file-andfolder basis; reportedly, whole-phone erasure in a future paid-for version)
Security tools can help keep you safe
Mobile devices such as phones and tablets are wonderfully convenient, but they also
pose huge security risks. Not only are these devices subject to the same kind of
malware and hacking that your Windows PC must cope with, theyre also far more likely
to be lost or stolen than your desktop or laptop system.
But with one good tool from each of the categories above, your portable Android device
can be as safe and secure as current technology allows. None of these products will
dent your pocketbook, so protect yourself!
www.WindowsSecrets.com
Page 76
Data and Internet Security Guide
Subscribe to the Windows Secrets Newsletter
Insider tips, authoritative how-tos,
security best practices, and more!
Sign up now and get Windows
Secrets reported by industry veterans
The Windows Secrets Newsletter brings you essential tricks for running Windows, IE,
Firefox, Windows Update, and more twice-weekly. Choose from 3 resourcepacked membership packages.
Click here to check out what's included.
Sign up today for instant access to valuable information such as:
Tighten you Facebook privacy settings
Your next PC: Thinking beyond the desktop
Hotmail's social networking busts your privacy
Preparing XP for the long haul
10 Great "Do these first" tweaks for Windows 7
Freeware outdoes Windows' built-in tools
Avoid the security reisk of shortened URLs
Windows Live shares your Messenger contacts
Subscribe today at http://www.WindowsSecrets.com
www.WindowsSecrets.com
Page 77
S-ar putea să vă placă și
- EkashlokiraamaDocument3 paginiEkashlokiraamaAshish Kumar AgnihotriÎncă nu există evaluări
- Amir84913741 - 2016 06 27 - 19 14 02Document1 paginăAmir84913741 - 2016 06 27 - 19 14 02Ashish Kumar AgnihotriÎncă nu există evaluări
- Rigveadibhashya BhumikaDocument328 paginiRigveadibhashya Bhumikayashwant100% (1)
- Amir84913741 - 2016 06 27 - 19 14 02Document1 paginăAmir84913741 - 2016 06 27 - 19 14 02Ashish Kumar AgnihotriÎncă nu există evaluări
- AbstractDocument1 paginăAbstractAshish Kumar AgnihotriÎncă nu există evaluări
- Side Channel Attacks: Evaluator: Prof. Jean-Jacques Quisquater, Math Rizk, ConsultingDocument47 paginiSide Channel Attacks: Evaluator: Prof. Jean-Jacques Quisquater, Math Rizk, ConsultingAshish Kumar AgnihotriÎncă nu există evaluări
- The Fifth HouseDocument3 paginiThe Fifth HouseAshish Kumar AgnihotriÎncă nu există evaluări
- Dissertation HandbookDocument40 paginiDissertation HandbookAshish Kumar Agnihotri100% (1)
- Ÿ Uë Uá Êÿ - Œ U - Êÿœ, Œèl Sã - ÊÿœDocument1 paginăŸ Uë Uá Êÿ - Œ U - Êÿœ, Œèl Sã - ÊÿœAshish Kumar AgnihotriÎncă nu există evaluări
- 2010-03-30 Things To Do When You ArDocument9 pagini2010-03-30 Things To Do When You ArAshish Kumar AgnihotriÎncă nu există evaluări
- RTGS NeftDocument3 paginiRTGS NeftAshish Kumar AgnihotriÎncă nu există evaluări
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceDe la EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceEvaluare: 4 din 5 stele4/5 (895)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeDe la EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeEvaluare: 4 din 5 stele4/5 (5794)
- The Yellow House: A Memoir (2019 National Book Award Winner)De la EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Evaluare: 4 din 5 stele4/5 (98)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureDe la EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureEvaluare: 4.5 din 5 stele4.5/5 (474)
- Shoe Dog: A Memoir by the Creator of NikeDe la EverandShoe Dog: A Memoir by the Creator of NikeEvaluare: 4.5 din 5 stele4.5/5 (537)
- The Little Book of Hygge: Danish Secrets to Happy LivingDe la EverandThe Little Book of Hygge: Danish Secrets to Happy LivingEvaluare: 3.5 din 5 stele3.5/5 (399)
- On Fire: The (Burning) Case for a Green New DealDe la EverandOn Fire: The (Burning) Case for a Green New DealEvaluare: 4 din 5 stele4/5 (73)
- Never Split the Difference: Negotiating As If Your Life Depended On ItDe la EverandNever Split the Difference: Negotiating As If Your Life Depended On ItEvaluare: 4.5 din 5 stele4.5/5 (838)
- Grit: The Power of Passion and PerseveranceDe la EverandGrit: The Power of Passion and PerseveranceEvaluare: 4 din 5 stele4/5 (588)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryDe la EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryEvaluare: 3.5 din 5 stele3.5/5 (231)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaDe la EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaEvaluare: 4.5 din 5 stele4.5/5 (266)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersDe la EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersEvaluare: 4.5 din 5 stele4.5/5 (344)
- The Emperor of All Maladies: A Biography of CancerDe la EverandThe Emperor of All Maladies: A Biography of CancerEvaluare: 4.5 din 5 stele4.5/5 (271)
- Team of Rivals: The Political Genius of Abraham LincolnDe la EverandTeam of Rivals: The Political Genius of Abraham LincolnEvaluare: 4.5 din 5 stele4.5/5 (234)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreDe la EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreEvaluare: 4 din 5 stele4/5 (1090)
- The Unwinding: An Inner History of the New AmericaDe la EverandThe Unwinding: An Inner History of the New AmericaEvaluare: 4 din 5 stele4/5 (45)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyDe la EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyEvaluare: 3.5 din 5 stele3.5/5 (2259)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)De la EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Evaluare: 4.5 din 5 stele4.5/5 (120)
- Her Body and Other Parties: StoriesDe la EverandHer Body and Other Parties: StoriesEvaluare: 4 din 5 stele4/5 (821)
- Rotary InformationDocument14 paginiRotary InformationMohammad UsmanÎncă nu există evaluări
- Entrepreneurial Skills-II: in This Chapter..Document34 paginiEntrepreneurial Skills-II: in This Chapter..TECH-A -TRONICSÎncă nu există evaluări
- Soalan Sebenar Sejarah STPM Penggal 2 PDFDocument1 paginăSoalan Sebenar Sejarah STPM Penggal 2 PDFFatins FilzaÎncă nu există evaluări
- IsoMetrix Case Study OmniaDocument9 paginiIsoMetrix Case Study OmniaOvaisÎncă nu există evaluări
- NAVEEN Final Project 2Document83 paginiNAVEEN Final Project 2syed bismillahÎncă nu există evaluări
- National University: Syllabus Subject: MathematicsDocument3 paginiNational University: Syllabus Subject: MathematicsFathmaakter JuiÎncă nu există evaluări
- New 2010 York PerfectDocument9 paginiNew 2010 York Perfectbasl haymourÎncă nu există evaluări
- Re Cri Retd de JagerDocument23 paginiRe Cri Retd de JagerMaitheÎncă nu există evaluări
- No. 304 (171) 2021/PA Admn 111!: To, Centre ExcellenceDocument9 paginiNo. 304 (171) 2021/PA Admn 111!: To, Centre ExcellenceSanjeev kumarÎncă nu există evaluări
- Micro, Small and Medium Enterprises (MSME) : by Ankit Avasthi SirDocument6 paginiMicro, Small and Medium Enterprises (MSME) : by Ankit Avasthi SirMonty SharmaÎncă nu există evaluări
- IGCSE COMMERCE Chapter 10.1Document5 paginiIGCSE COMMERCE Chapter 10.1Tahmid Raihan100% (1)
- Grade 9: Tle - Ict Computer Systems Servicing Quarter 2 - Module 1 Install Network CablesDocument6 paginiGrade 9: Tle - Ict Computer Systems Servicing Quarter 2 - Module 1 Install Network CablesSharmaine Paragas FaustinoÎncă nu există evaluări
- FINANOTECH Registration Form PMP Certification Training Cohort January 2023Document21 paginiFINANOTECH Registration Form PMP Certification Training Cohort January 2023Abhi CaullychurnÎncă nu există evaluări
- All Worksheets MYSQLDocument33 paginiAll Worksheets MYSQLSample1Încă nu există evaluări
- Virtual Museums A Survey and Some IssuesDocument9 paginiVirtual Museums A Survey and Some IssuesCeaser SaidÎncă nu există evaluări
- Desktop F0ecjd0 20230613 0007Document8 paginiDesktop F0ecjd0 20230613 0007Mican HoriaÎncă nu există evaluări
- Hero Pleasure Scooter Part Catalogue Mar 2010 EditionDocument78 paginiHero Pleasure Scooter Part Catalogue Mar 2010 EditionAmanÎncă nu există evaluări
- Live Video Analytics at Scale With Approximation and Delay-ToleranceDocument17 paginiLive Video Analytics at Scale With Approximation and Delay-TolerancejsprchinaÎncă nu există evaluări
- Getting Started With PIC Microcontroller - CCS C Compiler PDFDocument19 paginiGetting Started With PIC Microcontroller - CCS C Compiler PDFNithya100% (2)
- All in One Interview Questions For All GraduatesDocument61 paginiAll in One Interview Questions For All GraduatesDebasis DuttaÎncă nu există evaluări
- Sample Midterm (Lab)Document3 paginiSample Midterm (Lab)Shahab designerÎncă nu există evaluări
- Dynapac Mini Roller - CC125Document14 paginiDynapac Mini Roller - CC125Iftequar Rizwan KhanÎncă nu există evaluări
- Gen - Importance of Welding in L & T PDFDocument30 paginiGen - Importance of Welding in L & T PDFSivaÎncă nu există evaluări
- Guia de Usuario Sokkia LinkDocument81 paginiGuia de Usuario Sokkia LinkEdwin VelasquezÎncă nu există evaluări
- Construction Planning and SchedulingDocument70 paginiConstruction Planning and SchedulingDessalegn AyenewÎncă nu există evaluări
- Pucknell Vlsi Design PDF - CompressDocument2 paginiPucknell Vlsi Design PDF - CompressKotresh HothurÎncă nu există evaluări
- Purposive Communication AssignmentDocument2 paginiPurposive Communication AssignmentJohn Warren MestiolaÎncă nu există evaluări
- An Experimental Study On Airborne Landmine DetectiDocument7 paginiAn Experimental Study On Airborne Landmine Detecticlinton ruleÎncă nu există evaluări
- Elektor Electronics 1998-10Document54 paginiElektor Electronics 1998-10Adrian_Andrei_4433Încă nu există evaluări
- New Gen Trunnion Soft Seat Ball ValveDocument7 paginiNew Gen Trunnion Soft Seat Ball ValvedirtylsuÎncă nu există evaluări