Documente Academic
Documente Profesional
Documente Cultură
A Vivacious Approach To Detect and Prevent Ddos Attack
Încărcat de
esatjournalsTitlu original
Drepturi de autor
Formate disponibile
Partajați acest document
Partajați sau inserați document
Vi se pare util acest document?
Este necorespunzător acest conținut?
Raportați acest documentDrepturi de autor:
Formate disponibile
A Vivacious Approach To Detect and Prevent Ddos Attack
Încărcat de
esatjournalsDrepturi de autor:
Formate disponibile
IJRET: International Journal of Research in Engineering and Technology
eISSN: 2319-1163 | pISSN: 2321-7308
A VIVACIOUS APPROACH TO DETECT AND PREVENT DDoS ATTACK
Kharat J.S.1, Radhakrishna Naik2
1
Student ME (CSE), 2Head, Computer Science and Engineering, MIT (E) Aurangabad, Maharashtra, India,
kharat.jyo@gmail.com, naikradhakrishna@gmail.com
Abstract
A serious problem on the Internet nowadays is Distributed Denial of Service (DDoS) attacks and this is coordinated attack performed
by hackers to immobilize a particular Computer service through manipulation of techniques those are used to provide the Services. In
this attack, normally attackers generate a huge amount of requests to victims through compromised computers. DDoS attacks are a
critical threat to the internet. Packet flooding DDoS attack is a very common way to attack a victim machine by sending large amount
of unwanted traffic. This paper proposes a threshold based approach to detect and prevent the DDoS attack before reaching the
victim end with high detection rate and low false positive rate to achieve high performance. The result obtained from various
experiments on UDP Flood attack and HTTP GET attack show the effectiveness and the efficiency of our approach.
Keywords: Denial of Service (DoS), Distributed Denial of Service (DDoS), Entropy, flooding attack.
---------------------------------------------------------------------***------------------------------------------------------------------------1. INTRODUCTION
2. OVERVIEW OF DoS AND DDoS ATTACK
Internet Operators have been observed that DDoS attacks are
increasing noticeably and individual attacks are more strong
and complicated. Furthermore, the Arbor Worldwide
Infrastructure Security Report highlighted important trends in
distributed denial of service (DDoS) attacks. Several findings
stand out, including the overall expansion of attack surface
and the escalation of attack size and frequency [1].Distributed
denial-of-service (DDoS) attacks consist of an overwhelming
quantity of packets being sent from multiple attack sites to a
victim site. These packets get there in such a high quantity that
some key resource at the victim (bandwidth, buffers, CPU
time to compute responses) is quickly exhausted. The victim
cannot attend its real work due to spending so much time in
handling the attack traffic. Thus legitimate clients are deprived
of the victims service for as long as the attack lasts.
2.1 Denial of Service (Dos) Attacks
The first large-scale appearance of distributed denial-ofservice (DDoS) attacks occurred in mid-1999 and still
researchers are struggling to devise an effective solution to the
DDoS problem. There are many commercial and research
defenses has been appeared, but none of them provide
complete security from the threat. Rather, they detect a small
range of attacks that either use malformed packets or create
severe disturbances in the network; and they handle those
attacks by non-selectively dropping a portion of the traffic
destined for the victim[1]. This strategy relieves the victim
from the high-volume attack, but also inflicts damage to
legitimate traffic that is speciously dropped.
The DoS attack generally consists of efforts to temporarily or
indefinitely interrupt or suspend services of a host connected
to the internet. The goal of a Denial of Service (DoS) attack is
to interrupt some legitimate activity, such as browsing Web
pages, email functionality or net banking. It could even
shutdown the whole Web server. To obstruct legitimate
operations is to exploit vulnerabilities on the target machine or
application, by sending specially crafted requests targeting the
given vulnerabilities. Denial-of-service effect is achieved by
sending messages to the target machine such that the
message hampers with its operation and makes it hang,
crash, reboot, or do useless work. Also some key resources of
the target machine such as bandwidth, CPU time, memory, etc
can be consumed by sending a vast number of packets. One
cannot attend to legitimate clients because the target
application, machine, or network spends all of its critical
resources on handling the attack traffic [2].
2.2 Distributed Denial-Of-Service (DDoS) Attacks
It is simply an extension of DoS attack. DoS and DDoS attack
scenario is shown in Fig-2.Making a machine or network
resources unavailable to its intended user-s is the DDoS
attempt. It generally consist of the efforts of one or more
people to temporarily or indefinitely interrupt or suspend
services of a host connected to the internet. DDoS attacks are
able to take out an entire server in a matter of minutes. To
overwhelm a service to the point where it no longer works is
the goal of any DDoS attack.
__________________________________________________________________________________________
Volume: 02 Issue: 10 | Oct-2013, Available @ http://www.ijret.org
434
IJRET: International Journal of Research in Engineering and Technology
In a DDoS attack, the incoming traffic flooding the victim
originates from many different sources potentially hundreds of
thousands or more. To saturate a target computer or device
with external communications requests, such that it cannot
respond to other legitimate traffic, or responds so slowly[3] is
the most common method of DDoS attack. In general terms,
DDoS attacks are implemented by either forcing the targeted
computers to reset, or to consume their resources so that they
can no longer provide services, or obstructing the
communication media between communicators so that they
can no longer communicate.
Attacking
machine
Attack control Mechanism
Zombie
Zombie
Zombie
Target/Victim
Machine
Target/Victim
Network
DoS Attack
DDoS Attack
Fig-1: DoS and DDoS Attack Scenario
There are many types of DDoS attacks targeting both the
network and the application layers. They could be classified
upon their impact on the targeted computing resources
(saturating bandwidth, consuming servers resources,
shattering an application) or upon the targeted resources as
well:
Attacks targeting Network Resources: UDP Floods,
ICMP Floods, IGMP Floods.
Attacks targeting Server Resources: the TCP/IP
weaknesses TCP SYN Floods, TCP RST attacks, TCP
PSH+ACK attacks but also Low and Slow attacks as
Sock stress for example and SSL-based attacks, which
detection is particularly challenging.
Attacks targeting the Application Resources: HTTP
Floods, DNS Floods and other Low and Slow attacks as
Slow HTTP GET requests (Slowloris) and Slow HTTP
POST requests (R-U-Dead-Yet).
A DDoS attack usually comprises more than three attack
vectors thus increasing the attackers chances to hit its
target and escape basic DoS mitigation solutions[4].
In general there are two types of denial of service attacks:
those that target the network layer and those that target the
application layer. The server cannot simultaneously process
other requests from other legitimate users, if an attacker
overloads the server with many requests. Examples of DDoS
attacks are discussed as follows:
eISSN: 2319-1163 | pISSN: 2321-7308
A. UDP Flood Attack
UDP Flood attack is a network layer DDoS attack. UDP is a
connectionless protocol and it does not require any connection
setup procedure to transformation. To consume the bandwidth
is the main purpose of UDP Flood type attack. In this attack,
Attacker send IP packets containing UDP datagrams with the
purpose of slowing down the victim to the point that the
victim can no longer handle valid connections.
B. HTTP GET Flood Attack
HTTP GET flood attack is an Application layer DDoS Attack.
In this, a large amount of legitimate requests(to an
application)use to send by HTTP attacker. The feature of
HTTP GET Flood attack is that it will establish a normal TCP
Connection to Servers, and constantly submit a lot of calling
requests which dramatically consume database resources. For
sample, an Http Flood attack can make hundreds of thousands
of page requests to a web server, which can wear out all of the
servers processing capability. So that the server cannot handle
the legitimate request [5]
An HTTP GET flood is as exactly as it sounds: its a massive
influx of legitimate HTTP GET requests that come from large
numbers of users. These requests mimic legitimate users are
nearly impossible for applications and even harder for
traditional security to detect. This result of this attack is
similar to the effect: server errors increasingly degraded the
performance, and resource exhaustion.
3. RELATED WORK
Distributed Denial-of-Service (DDoS) and Denial-of-Service
(DoS) are the most dreadful network threats in recent years.
Different techniques and challenges involved in anomaly
detection system [6].
Yonghua You and Zulkernine[7]introduce two distance-based
DDoS detection techniques: average distance estimation and
distance-based traffic separation. They detect attacks by
analyzing distance values and traffic rates. The distance
information of a packet can be inferred from the Time-to-Live
(TTL) value of the IP header. In the average distance
estimation DDoS detection technique, the prediction of mean
distance value is used to define normality. The prediction of
traffic arrival rates from different distances is used in the
distance-based traffic separation DDoS detection technique.
The mean absolute deviation (MAD)-based deviation model
provides the legal scope to separate the normality from the
abnormality for both the techniques. The results of the
proposed techniques show that the techniques can detect
attacks effectively.
Muhai and MingLi [8] propose a model for detecting DDoS
attacks automatically. In order to reduce the error to identify
attacks, we use discrete wavelet transform (DWT) technique.
__________________________________________________________________________________________
Volume: 02 Issue: 10 | Oct-2013, Available @ http://www.ijret.org
435
IJRET: International Journal of Research in Engineering and Technology
eISSN: 2319-1163 | pISSN: 2321-7308
Author use actual data to validate proposed model and obtain
good results in terms of tradeoff between correct detections
and false alarms. The test results shows the approach not only
can be different the sudden increasing normal traffic from
anomaly traffic, but also has a well detect ratio.
Our objective in this paper is to design an attack detection
system based on entropy and packet rate to detect DDoS
attack. We use normalized entropy which calculates the over
all probability distribution in the captured flow in our
algorithm to get more accurate result.
Sumit Kar and Bibhudatta Sahoo[9]proposed method is based
upon attack detection and recovery, and uses an entropy based
anomaly detection system to detect DDoS attack. Author
design an anomaly detection system based on entropy and
entropy rate to detect DDoS attack. They uses normalized
entropy which calculates the over all probability distribution
in the captured flow in algorithm to get more accurate result.
Detection System is based on by analyzing the change in
entropy of distribution flow header feature and behavioral
features traffic distributions. The Result shows that the attack
must be detected and blocked before reaching the victim with
high detection rate and low false alarm rate.
4. PROPOSED ENTROPY BASED DETECTION
Suratose Tritilanunt et al. [10] provide a detection mechanism
based on a technique of entropy-based input-output traffic
mode detection scheme. The experimental results demonstrate
that our approach is able to detect several kinds of denial-ofservice attacks, even small spike of such attacks. To minimize
this false positive, we introduce a technique called entropybased input-output traffic mode detection scheme. By
combining packet content observation for identifying DoS and
DDoS attacks in the system, this will help approach not only
to increase the accuracy for detecting DoS attacks, but also to
effectively discriminate legitimate users from suspicious
traffic.
Yi Zhang and Qiang Liu[11] present a real-time DDoS attack
detection and prevention system which can be deployed at the
leaf router to monitor and detect DDoS attacks. The
advantages of this system lie in its statelessness and low
computation overhead, which makes the system itself immune
to flooding attacks. A number of articles suggested entropy as
a metrics to summarizing trafficdistribution for anomaly
detection[12][13].
The authors of [9] use entropy rate to discriminate the DDoS
attack from legitimate traffic. The use of entropy for analyze
changes in traffic distribution has two benefit. i) Using
entropy for anomaly detection increases the detection
capability than volume based methods. ii) It provides
additional information to classify among different types
anomaly (worms, DoS attack. Port scanning) .We considers
two classes of distribution i) flow header features (IP address,
ports, and flow sizes) ii) behavioral features (the number of
distinct destination / source address that a host communicates
with) [14]. The anomaly detection system discussed in this
paper is based on by analyzing the change in entropy of above
two traffic distributions.
TECHNIQUE
Shannons Entropy [15] based approach is used for DDoS
attack detection. entropy is a measure of the uncertainty in a
random variable or in this case data coming over the
network. The Shannons function is a useful tool for
inspecting a similarity and distribution of traffic in the
inspection time frame. When denial-of-service attacks occur in
the observation window, the entropy of that traffic will drop
noticeably and wecan identify that situation as DoS/DDoS
attacks. The value of sample entropy lies in range [0, logn].
The entropy shows its minimum value 0 when all the items (IP
address or port) are same and its maximum value logn when
all the items are different. The entropy of a random variable X
with possible values {x1 , x2 . . xn } can be calculated as
H x =
n
i=1 P
xi logP(xi )
(1)
In our proposed DDoS detection algorithm we use entropy as
a principal matrix. We use change of entropy of traffic
distributions (IP address, port) for DDoS detection. If we are
interested in measuring the entropy of packets over unique
source or destination address then maximum value of n is 232
for ipv4address [9]. If we want to calculate entropy over
various applications port then n is the maximum number of
ports. Here p(xi ) where xi X is the probability that X takes
the value xi . Suppose we randomly observe X for a fixed time
window w, thenP xi = mi m, where mi is the frequency or
number of times we observe X taking the value xi i.e. m =
n
i=1 mi
H X =
n
i=1
mi /m log(mi /m)(2)
If we want calculate probability of any source MAC address
then,
mi = number of packets with xi as source MAC address and
m = total number of packets
Number of Packets with xi as source
P xi =
Total number of packets
Here total number of packets is the number of packets seen for
a time window T.
Normalized entropy calculates the over all probability
distribution in the captured flow for the time window T.
Normalized entropy = (H log n0 )(3)
__________________________________________________________________________________________
Volume: 02 Issue: 10 | Oct-2013, Available @ http://www.ijret.org
436
IJRET: International Journal of Research in Engineering and Technology
eISSN: 2319-1163 | pISSN: 2321-7308
Where n0 is the number of distinct xi values in the given time
window.
In a DDoS attack from the captured traffic in time window T,
the attack flow dominates the whole traffic, as a result the
normalized entropy of the traffic decreased in a detectable
manner. But it is also possible in a case of massive legitimate
network accessing. To confirm the attack we have to again
calculate the packet rate (PRt ) of suspected flow. Here flow is
packages which share the same destination address/port. In
this mechanism we have taken one assumption that the
attacker uses same function to generate attack packets at
zombies.
PRt
Total No. of packets coming from
same MAC address(Tx )
x =
(4)
Total number of packets (T)
The steps in our proposed DDoS detection algorithm are
described below.
Algorithm 1 : DDoS Detection Algorithm
1: Collect sample flows for a time window T on the
edge routers.
2:Calculate router entropy H X = ni=1 P xi log P(xi )
3: Calculate NE = (H log n0 )where, NE = normalized
router entropy.
4: If NE < (1 ), identify the suspected attack
flow.
(T )
5: Calculate the packet rate PRt x = x of the suspected
(T)
flow inthat router
6:If PRt (x) threshold(2 ), it is a DDoS attack.
Else legitimate traffics.
7: Generate alarm and Discard the attack flow.
5. EXPERIMENT AND RESULT
Section 5 provides the experiment and results of our approach
to detect distributed denial-of-service attacks. The system can
detect the attack by using an entropy detection method
because the value drops significantly from the stored profile
once the DoS/DDoS attacks occur in the system. We observe
that most DoS attacks immediately decrease the entropy of the
overall system. A prototype of the proposed system has been
implemented and evaluated on an real base system.
Experimental Setup: Fig-2 shows the experimental setup.
experiment includes 3 source, 1 intermediate routers and 1
destination node. Out of which 3 source nodes 2 nodes are
legitimate users and 1 node is attacker. The bandwidth of
legitimate traffic is set constant.
Fig-2: Experimental setup
The goal of our experiments is to assess the scalability of our
approach and the performance of the protection system.
5.1 UDP Attack:
UDP is a bandwidth depletion attack. Attacker consumes the
network bandwidth with unwanted UDP traffic so that
legitimate user cannot send packets to destination.We traced
no of packets received in every 1 second interval. Performance
metrics used is Network Utilization.
Experiment 1: UDP attack with 2 legitimate user and 1
attacker: Suppose node A3 is the attack source and node A1
and A2 are legitimate users and node D1 is the victim. All the
three users sending packets to specified destination
Experiment lasts at 6 second. We traced number of packets
received in a fixed time window T.Table-1 shows the traced
data in 6 seconds. The router entropy is calculated according
to Eq. (2), and the normalized router entropy is being
calculated using Eq. (3). Table-2 shows the normalized
entropy calculation for experiments.
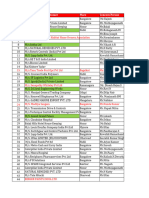
Table 1: Traced data
Times in
Second
Number of attack
packets received
0-1
1-2
2-3
3-4
4-5
5-6
80
80
699
766
700
615
Number
of
legitimate packets
received
63
65
150
125
100
80
Table-2: Normalized entropy calculations
Time in Second
Normalized Router Entropy
0-1
1-2
2-3
3-4
4-5
5-6
0.98
0.99
0.535
0.45
0.51
0.76
__________________________________________________________________________________________
Volume: 02 Issue: 10 | Oct-2013, Available @ http://www.ijret.org
437
IJRET: International Journal of Research in Engineering and Technology
Captured flow for every source is shown in Table-3 when
NE=0.535.
900
800
700
600
500
400
300
200
100
0
Destination IP
38-60-77-50b0-92
192.168.0.45
No.
of
pac
kets
70
00-1c-c0-83-b7f8
192.168.0.45
80
70-71-BC-BE11-9B
192.168.0.45
entropy
0.32
0.29
Legitimate
traffic
Attack traffic
Time in Seconds
0.23
Here router entropy = 0.29+0.32+0.23= 0.84
n0 = 3
Normalized router entropy NE = 0.84/ log2 3 = 0.535
The above data are taken practically for Edge Router. In the
above case one flow dominates the whole traffic as a result the
normalized entropy decreases. If the threshold 1 is perfect,
suppose 0.94 for the above example, it will treat flow coming
from node A3 with MAC (70-71-BC-BE-11-9B) as suspected
flow. After which the packet rate is being calculated for every
suspected flow. While the packet rates of different flows
exceed the threshold2 i.e.150 packets/second, the attack is
confirmed and attack flow is discarded. All the above
calculations are based on log 2 .
We consider 2 situations in our experiment to evaluate the
performance of our proposed algorithm. In the first situation,
we start with 2 legitimate users and 1 attacker and study how
the system performance is being degraded. In the second
situation we examine the system for 2 legitimate users and two
attackers.
Fig-3: Effect of UDP attack
Network Utilization in %
699
60
50
40
30
20
10
0
Network
Utilization
50 100 150 200 250
Packet rate
Fig-4: Threesenders with 1 attacker
The graph in Fig-4 shows the Network utilization of 4 senders
with 2 attackers. It shows the packet rate with respect to
network utilization.
The graph in Fig-3 depicts the effect of DDoS attack with 2
legitimate users and 1 attacker. It shows numbers of attack
packets as well as legitimate packets with respect totime. The
graph in Figure 4 shows the network utilization of 3senders
with 1 attacker. It shows number of packets/second with
respect to network utilization.
60
N/W Utilization in %
Node
MAC
Packet Count
Table-3: Traced Data when NE=0.535(UDP attack)
Source
with
address
eISSN: 2319-1163 | pISSN: 2321-7308
50
40
30
Network
Utilization
20
10
0
50 100 150 200 250
Packet rate
Fig-5: Foursenders with 2 attackers
__________________________________________________________________________________________
Volume: 02 Issue: 10 | Oct-2013, Available @ http://www.ijret.org
438
IJRET: International Journal of Research in Engineering and Technology
5.2 HTTP GET Flood Attack
eISSN: 2319-1163 | pISSN: 2321-7308
250
200
Packet Count
We traced no of HTTP GET request received in every 1
second interval.We have taken two examples using Fig. 2 how
the detection scheme works. Suppose node A1 is the attack
source and node A2and A3 are legitimate users and node D1 is
the victim. Based on the DDoS detection algorithm flows
coming from all the client nodes will first captured by router 1
Suppose at router 1, we have captured flows as given in Fig-6
which shows the legitimate traffic as well as attack traffic with
respect to time in a fixed time window T. The router entropy is
calculated according to Eq. (2) and the normalized router
entropy is being calculated using Eq. (3).Table-4 shows the
Normalized entropy calculations and Table-5 shows the traced
data when NE=0.81
150
Legitimate
packets
100
Attack
packets
50
0
1
0-1
1-2
2-3
3-4
4-5
0.71
0.86
0.63
0.67
0.81
The graph in Fig-7 shows the Heap utilization of 3 senders
with 1 attacker. It shows packet rate with respect to Heap
Memory utilization in %.The graph in Fig-8 shows the Heap
utilization of 4 senders with 2attacker. It shows packet rate
with respect to Heap Memory utilization.
Heap Memory in %
Normalized Router Entropy
Table-5 Traced Data when NE=0.81
Source Node
with
MAC
address
38-60-77-50b0-92
Destination
IP
No.of
request
entropy
192.168.0.45
217
0.41
00-1c-c0-83b7-f8
192.168.0.45
74
0.47
70-71-BCBE-11-9B
192.168.0.45
49
0.40
Heap
Memory
Utilization
Fig-7: three senders with 1 attacker
Heap Memory in
The above data are taken practically for Router1. In the above
case one flow dominates the whole traffic as a result the
normalized entropy decreases. If the threshold is perfect,
suppose 0.94 for the above example, it will treat flow coming
from node A3 with MAC(70-71-BC-BE-11-9B) as suspected
flow. After which the packet rate is being calculated for every
suspected flow. While the packet rates of different flows
exceed the threshold 2 i.e. 150 p/s, the attack is confirmed
and attack flow is discarded.
60
50
40
30
20
10
0
50 100 150 200 250
Packet rate
Here router entropy = 0.41+0.47+0.40= 1.28 and n0 = 3
Normalized router entropy NE = 0.84 log 2 3 = 0.811
Fig-6: Traced data
Table-4: Normalized entropy calculation
Times in Second
2
3
4
Time in Seconds
80
70
60
50
40
30
20
10
0
Heap
Memory
Utilization
50
100 150 200 250
Packet rate
Fig-8: four senders with 2 attackers
__________________________________________________________________________________________
Volume: 02 Issue: 10 | Oct-2013, Available @ http://www.ijret.org
439
IJRET: International Journal of Research in Engineering and Technology
CONCLUSIONS
In this paper we discussed different types of DDoS attacks that
could exploit network and related detection strategies and
introduces an alternative technique to detect denial-of-service
and distributed denial-of-service attacks by using packet rates
and packet address entropy-based technique. As we will take
the detection threshold 1 as0.94 then, the proposed anomaly
detection system can detect DDoS attack traffics with high
detection rate and without any false positive before reaching
the victim and taking threshold 2 as 150 p/s then, proposed
system can achieve the efficient use of Network utilization in
case of UDP attack and Heap Memory utilization in case of
HTTP Get flood attack. we plan to test our approach with
other kinds of DoS/DDoS attacks in the future work.
REFERENCES
[1].
[2].
[3].
[4].
[5].
[6].
[7].
[8].
[9].
[10].
[11].
[12].
[13].
http://blogs.ixiacom.com/ixia-blog/application-layerddos-attacks-growing.
http://www.linuxforu.com/2011/04/securing-apachepart-8-dos-ddos-attacks.
http://en.wikipedia.org/wiki/Denial-of-service_attack.
http://security.radware.com/knowledgecenter/DDoSPedia/ddos-attack/
Saman Taghavi Zargar, James Joshi, David Tipper,
Survey of Defense Mechanisms Against Distributed
Denial of Service (DDoS) Flooding Attacks,ieee
communications surveys & tutorials 2009.
P. G. Teodoro, J. D.Verdejo, G. M.Fernandez,
E.Vazquez, Anomaly-based network intrusion
detection: Techniques, systems and challenges,
computer & security, Volume 28, Issues 1-2, pp.18-28,
2008.
Yonghua You and Zulkernine,A Distributed Defense
Framework for Flooding-Based DDoS Attacks, ICC
Proceeding, 2007
Muhai Li and Ming Li, A New Approach for
Detecting DDoS Attacks Based on Wavelet
Analysis,ieeeconference, 2009.
Sumit Kar and Bibhudatta Sahoo, An Anomaly
Detection System for DDoS Attack,ijca-se 2009.
Suratose Tritilanunt et al, Entropy-based Input-Output
Traffic Mode Detection Scheme for DoS/DDoS
Attacks,2010 .
Yi Zhang and Qiang Liu, A Real-Time DDoS Attack
Detection and Prevention System Based on per-ITraffic
Behavioral Analysis,2010.
Suratose
Tritilanunt,
SuphanneeSivakorn,
ChoochernJuengjincharoen,
AusaneeSiripornpisan,
Entropy-based Input-Output Traffic Mode Detection
Scheme for DoS/DDoS Attacks, ISCIT 2010
Wonjun Lee and Squicciarini,Detection and Protection
against Distributed Denial of Service Attacks in
Accountable Grid Computing Systems,IEEEJournel
2011.
eISSN: 2319-1163 | pISSN: 2321-7308
[14]. G. Nychis, V. Sekar, D. G Andersen, H. Kim and
H.Zhang, An Empirical Evaluation of Entropy-Based
Traffic Anomaly Detection. Tech. Rep. CMU-CS-08145, Computer Science Department, Carnegie Mellon
University, 2008
[15]. Thomas M. Cover and Joy A. Thomas, Elements of
Information Theory, second edition, 2007
BIOGRAPHIES
Ms. Kharat J.S. obtained her Bachelors
Degree in Computer Science from BAMU
University during 2008 and currently pursuing
Masters Degree from the same university. She
is working in Computer Dept. of Shreeyash
Polytechnic Aurangabad as Lecturer from last 5 years. Her
research area includes Network Security.
Dr. Radhakrishna Naik is working as
professor and Head in CSE Department of MIT
(E) Aurangabad. He did his PhD in Real Time
Systems and his subjects of interest are Real
Time
systems,
Real
Time
database
management and Network security.
__________________________________________________________________________________________
Volume: 02 Issue: 10 | Oct-2013, Available @ http://www.ijret.org
440
S-ar putea să vă placă și
- Shoe Dog: A Memoir by the Creator of NikeDe la EverandShoe Dog: A Memoir by the Creator of NikeEvaluare: 4.5 din 5 stele4.5/5 (537)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeDe la EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeEvaluare: 4 din 5 stele4/5 (5794)
- PTE 3 Week Study ScheduleDocument3 paginiPTE 3 Week Study ScheduleesatjournalsÎncă nu există evaluări
- Analysis and Design of A Multi Compartment Central Cone Cement Storing Silo PDFDocument7 paginiAnalysis and Design of A Multi Compartment Central Cone Cement Storing Silo PDFesatjournalsÎncă nu există evaluări
- Analysis and Optimization of Electrodes For Improving The Performance of Ring Laser Gyro PDFDocument4 paginiAnalysis and Optimization of Electrodes For Improving The Performance of Ring Laser Gyro PDFesatjournalsÎncă nu există evaluări
- Analysis and Optimization of Sand Casting Defects With The Help of Artificial Neural Network PDFDocument6 paginiAnalysis and Optimization of Sand Casting Defects With The Help of Artificial Neural Network PDFesatjournalsÎncă nu există evaluări
- Analysis of Cylindrical Shell Structure With Varying Parameters PDFDocument6 paginiAnalysis of Cylindrical Shell Structure With Varying Parameters PDFesatjournalsÎncă nu există evaluări
- A Servey On Wireless Mesh Networking ModuleDocument5 paginiA Servey On Wireless Mesh Networking ModuleesatjournalsÎncă nu există evaluări
- A Review Paper On Smart Health Care System Using Internet of ThingsDocument5 paginiA Review Paper On Smart Health Care System Using Internet of ThingsesatjournalsÎncă nu există evaluări
- A Survey On Identification of Ranking Fraud For Mobile ApplicationsDocument6 paginiA Survey On Identification of Ranking Fraud For Mobile ApplicationsesatjournalsÎncă nu există evaluări
- A Review On Fake Biometric Detection System For Various ApplicationsDocument4 paginiA Review On Fake Biometric Detection System For Various ApplicationsesatjournalsÎncă nu există evaluări
- A Study and Survey On Various Progressive Duplicate Detection MechanismsDocument3 paginiA Study and Survey On Various Progressive Duplicate Detection MechanismsesatjournalsÎncă nu există evaluări
- A Three-Level Disposal Site Selection Criteria System For Toxic and Hazardous Wastes in The PhilippinesDocument9 paginiA Three-Level Disposal Site Selection Criteria System For Toxic and Hazardous Wastes in The PhilippinesesatjournalsÎncă nu există evaluări
- A Women Secure Mobile App For Emergency Usage (Go Safe App)Document3 paginiA Women Secure Mobile App For Emergency Usage (Go Safe App)esatjournalsÎncă nu există evaluări
- A Research On Significance of Kalman Filter-Approach As Applied in Electrical Power SystemDocument8 paginiA Research On Significance of Kalman Filter-Approach As Applied in Electrical Power SystemesatjournalsÎncă nu există evaluări
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceDe la EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceEvaluare: 4 din 5 stele4/5 (895)
- The Yellow House: A Memoir (2019 National Book Award Winner)De la EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Evaluare: 4 din 5 stele4/5 (98)
- Grit: The Power of Passion and PerseveranceDe la EverandGrit: The Power of Passion and PerseveranceEvaluare: 4 din 5 stele4/5 (588)
- The Little Book of Hygge: Danish Secrets to Happy LivingDe la EverandThe Little Book of Hygge: Danish Secrets to Happy LivingEvaluare: 3.5 din 5 stele3.5/5 (400)
- The Emperor of All Maladies: A Biography of CancerDe la EverandThe Emperor of All Maladies: A Biography of CancerEvaluare: 4.5 din 5 stele4.5/5 (271)
- Never Split the Difference: Negotiating As If Your Life Depended On ItDe la EverandNever Split the Difference: Negotiating As If Your Life Depended On ItEvaluare: 4.5 din 5 stele4.5/5 (838)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyDe la EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyEvaluare: 3.5 din 5 stele3.5/5 (2259)
- On Fire: The (Burning) Case for a Green New DealDe la EverandOn Fire: The (Burning) Case for a Green New DealEvaluare: 4 din 5 stele4/5 (74)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureDe la EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureEvaluare: 4.5 din 5 stele4.5/5 (474)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryDe la EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryEvaluare: 3.5 din 5 stele3.5/5 (231)
- Team of Rivals: The Political Genius of Abraham LincolnDe la EverandTeam of Rivals: The Political Genius of Abraham LincolnEvaluare: 4.5 din 5 stele4.5/5 (234)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaDe la EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaEvaluare: 4.5 din 5 stele4.5/5 (266)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersDe la EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersEvaluare: 4.5 din 5 stele4.5/5 (345)
- The Unwinding: An Inner History of the New AmericaDe la EverandThe Unwinding: An Inner History of the New AmericaEvaluare: 4 din 5 stele4/5 (45)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreDe la EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreEvaluare: 4 din 5 stele4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)De la EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Evaluare: 4.5 din 5 stele4.5/5 (121)
- Her Body and Other Parties: StoriesDe la EverandHer Body and Other Parties: StoriesEvaluare: 4 din 5 stele4/5 (821)
- Mode ReversionsDocument15 paginiMode ReversionsISHAANÎncă nu există evaluări
- Karcher Quotation List - 2023Document12 paginiKarcher Quotation List - 2023veereshmyb28Încă nu există evaluări
- TemplateDocument17 paginiTemplatedaveÎncă nu există evaluări
- Digital Design Course FileDocument191 paginiDigital Design Course FileCharan NethaÎncă nu există evaluări
- Procedimiento de Test & Pruebas Hidrostaticas M40339-Ppu-R10 HCL / Dosing Pumps Rev.0Document13 paginiProcedimiento de Test & Pruebas Hidrostaticas M40339-Ppu-R10 HCL / Dosing Pumps Rev.0José Angel TorrealbaÎncă nu există evaluări
- Informatics in Logistics ManagementDocument26 paginiInformatics in Logistics ManagementNazareth0% (1)
- Segmentation - Ipynb - ColaboratoryDocument8 paginiSegmentation - Ipynb - ColaboratoryManjot KaurÎncă nu există evaluări
- Turbine BladeDocument27 paginiTurbine BladesrtanandÎncă nu există evaluări
- Thrust Bearing Design GuideDocument56 paginiThrust Bearing Design Guidebladimir moraÎncă nu există evaluări
- Subject Orientation: Empowerment TechnologiesDocument10 paginiSubject Orientation: Empowerment TechnologiesJessa GuerraÎncă nu există evaluări
- Premium Protection Synthetic Motor Oils (AMO & ARO)Document2 paginiPremium Protection Synthetic Motor Oils (AMO & ARO)brian5786Încă nu există evaluări
- Manual de TallerDocument252 paginiManual de TallerEdison RodriguezÎncă nu există evaluări
- Compact FlashDocument9 paginiCompact Flashenpr87reddyÎncă nu există evaluări
- Guidelines For Hall IC SubassemblyDocument9 paginiGuidelines For Hall IC SubassemblyvkmsÎncă nu există evaluări
- Usability Engineering (Human Computer Intreraction)Document31 paginiUsability Engineering (Human Computer Intreraction)Muhammad Usama NadeemÎncă nu există evaluări
- NCP81243 Dual Output 3 & 2 Phase Controller With Single Intel Proprietary Interface For Desktop and Notebook CPU ApplicationsDocument26 paginiNCP81243 Dual Output 3 & 2 Phase Controller With Single Intel Proprietary Interface For Desktop and Notebook CPU ApplicationsAhmed Sherif CupoÎncă nu există evaluări
- Boeing Defence Australia LimitedDocument16 paginiBoeing Defence Australia LimitedMitchÎncă nu există evaluări
- Reckitt Benkiser (Case Study) For SCMDocument13 paginiReckitt Benkiser (Case Study) For SCMDiptiman GuhaÎncă nu există evaluări
- Introduction To CMOS Circuit DesignDocument20 paginiIntroduction To CMOS Circuit DesignBharathi MuniÎncă nu există evaluări
- GSM RF Interview QuestionsDocument26 paginiGSM RF Interview QuestionsmohammedelrabeiÎncă nu există evaluări
- Faqs and User Manual - Returns Offline Tool: Goods and Services Tax NetworkDocument161 paginiFaqs and User Manual - Returns Offline Tool: Goods and Services Tax NetworklathaÎncă nu există evaluări
- Z PurlinDocument2 paginiZ PurlinAddrien DanielÎncă nu există evaluări
- Marantz Product Catalogue 2010 2011Document31 paginiMarantz Product Catalogue 2010 2011O M Gee100% (1)
- Effect of Cryogenic Treatment On CompositesDocument14 paginiEffect of Cryogenic Treatment On CompositesGauthamÎncă nu există evaluări
- 334387bet777 - Everything About Bet777 CasinoDocument2 pagini334387bet777 - Everything About Bet777 Casinoz7xsdpn047Încă nu există evaluări
- Em - 1110 1 1005Document498 paginiEm - 1110 1 1005Sajid arÎncă nu există evaluări
- EAC Software SetupDocument19 paginiEAC Software SetupBinh Minh NguyenÎncă nu există evaluări
- Dissolved Gas Analysis of Transformer Oil: Mrs. Harsha Shah Insulation DivisionDocument38 paginiDissolved Gas Analysis of Transformer Oil: Mrs. Harsha Shah Insulation Divisionsjavre9390100% (1)
- Edge Wall Final-ModelDocument1 paginăEdge Wall Final-ModelAbanoub ShakerÎncă nu există evaluări
- PQ100 Data SheetDocument2 paginiPQ100 Data Sheethanif_perdanaÎncă nu există evaluări