Documente Academic
Documente Profesional
Documente Cultură
Configuration Guide - Ethernet (V100R006C01 - 02)
Încărcat de
Dimas Eliacim Aguiar CostaTitlu original
Drepturi de autor
Formate disponibile
Partajați acest document
Partajați sau inserați document
Vi se pare util acest document?
Este necorespunzător acest conținut?
Raportați acest documentDrepturi de autor:
Formate disponibile
Configuration Guide - Ethernet (V100R006C01 - 02)
Încărcat de
Dimas Eliacim Aguiar CostaDrepturi de autor:
Formate disponibile
Quidway S5700 Series Ethernet Switches
V100R006C01
Configuration Guide - Ethernet
Issue
02
Date
2011-11-21
HUAWEI TECHNOLOGIES CO., LTD.
Copyright Huawei Technologies Co., Ltd. 2011. All rights reserved.
No part of this document may be reproduced or transmitted in any form or by any means without prior written
consent of Huawei Technologies Co., Ltd.
Trademarks and Permissions
and other Huawei trademarks are trademarks of Huawei Technologies Co., Ltd.
All other trademarks and trade names mentioned in this document are the property of their respective holders.
Notice
The purchased products, services and features are stipulated by the contract made between Huawei and the
customer. All or part of the products, services and features described in this document may not be within the
purchase scope or the usage scope. Unless otherwise specified in the contract, all statements, information,
and recommendations in this document are provided "AS IS" without warranties, guarantees or representations
of any kind, either express or implied.
The information in this document is subject to change without notice. Every effort has been made in the
preparation of this document to ensure accuracy of the contents, but all statements, information, and
recommendations in this document do not constitute the warranty of any kind, express or implied.
Huawei Technologies Co., Ltd.
Address:
Huawei Industrial Base
Bantian, Longgang
Shenzhen 518129
People's Republic of China
Website:
http://www.huawei.com
Email:
support@huawei.com
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
About This Document
About This Document
Intended Audience
This document provides the basic concepts, configuration procedures, and configuration
examples in different application scenarios of the Ethernet features supported by the S5700
switch.
This document is intended for:
l
Data configuration engineers
Commissioning engineers
Network monitoring engineers
System maintenance engineers
Symbol Conventions
The symbols that may be found in this document are defined as follows.
Symbol
Description
DANGER
WARNING
CAUTION
Issue 02 (2011-11-21)
Indicates a hazard with a high level of risk, which if not
avoided, will result in death or serious injury.
Indicates a hazard with a medium or low level of risk, which
if not avoided, could result in minor or moderate injury.
Indicates a potentially hazardous situation, which if not
avoided, could result in equipment damage, data loss,
performance degradation, or unexpected results.
TIP
Indicates a tip that may help you solve a problem or save
time.
NOTE
Provides additional information to emphasize or supplement
important points of the main text.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
ii
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
About This Document
Command Conventions
The command conventions that may be found in this document are defined as follows.
Convention
Description
Boldface
The keywords of a command line are in boldface.
Italic
Command arguments are in italics.
[]
Items (keywords or arguments) in brackets [ ] are optional.
{ x | y | ... }
Optional items are grouped in braces and separated by vertical
bars. One item is selected.
[ x | y | ... ]
Optional items are grouped in brackets and separated by vertical
bars. One item is selected or no item is selected.
{ x | y | ... }*
Optional items are grouped in braces and separated by vertical
bars. A minimum of one item or a maximum of all items can be
selected.
[ x | y | ... ]*
Optional items are grouped in brackets and separated by vertical
bars. Several items or no item can be selected.
&<1-n>
The parameter before the & sign can be repeated 1 to n times.
A line starting with the # sign is comments.
Change History
Updates between document issues are cumulative. Therefore, the latest document issue contains
all updates made in previous issues.
Changes in Issue 02 (2011-11-21)
The second commercial release has the following updates:
l
Some contents are modified according to updates in the product such as features and
commands.
Changes in Issue 01 (2011-10-26)
Initial commercial release.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
iii
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
Contents
Contents
About This Document.....................................................................................................................ii
1 Ethernet Interface Configuration...............................................................................................1
1.1 Introduction to Ethernet Interfaces.....................................................................................................................2
1.2 Ethernet Interface Features Supported by the S5700.........................................................................................2
1.3 Configuring Basic Attributes of an Ethernet Interface.......................................................................................3
1.3.1 Establishing the Configuration Task.........................................................................................................3
1.3.2 (Optional) Configuring an Interface Description......................................................................................4
1.3.3 (Optional) Configuring the Cable Type on an Interface............................................................................4
1.3.4 (Optional) Setting the Duplex Mode.........................................................................................................5
1.3.5 (Optional) Setting the Interface Rate.........................................................................................................5
1.3.6 (Optional) Enabling Auto-Negotiation......................................................................................................6
1.3.7 (Optional) Switching Between Optical and Electrical Interfaces..............................................................6
1.3.8 (Optional) Configuring an Interface to Work at Layer 2 or Layer 3.........................................................7
1.3.9 Checking the Configuration.......................................................................................................................8
1.4 Configuring Advanced Attributes of an Ethernet Interface................................................................................8
1.4.1 Establishing the Configuration Task.........................................................................................................8
1.4.2 (Optional) Configuring the Loopback Function........................................................................................9
1.4.3 (Optional) Configuring a Port Group........................................................................................................9
1.4.4 (Optional) Setting the Maximum Frame Length.....................................................................................10
1.4.5 (Optional) Enabling Flow Control...........................................................................................................10
1.4.6 (Optional) Enabling Auto-Negotiation of Flow Control.........................................................................11
1.4.7 (Optional) Enabling Port Isolation..........................................................................................................11
1.4.8 (Optional) Performing a Cable Test........................................................................................................12
1.4.9 (Optional) Configuring a Loopback Test on an Interface.......................................................................13
1.4.10 Checking the Configuration...................................................................................................................13
1.5 Maintaining Ethernet Interfaces.......................................................................................................................13
1.5.1 Debugging Ethernet Interfaces................................................................................................................13
1.6 Configuration Examples...................................................................................................................................14
1.6.1 Example for Configuring Port Isolation..................................................................................................14
2 Link Aggregation Configuration..............................................................................................17
2.1 Introduction to Link Aggregation.....................................................................................................................18
2.2 Link Aggregation Supported by the S5700......................................................................................................18
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
iv
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
Contents
2.3 Configuring Link Aggregation in Manual Load Balancing Mode...................................................................19
2.3.1 Establishing the Configuration Task.......................................................................................................19
2.3.2 Configuring an Eth-Trunk Interface to Work in Manual Load Balancing Mode....................................20
2.3.3 Adding Member Interfaces to an Eth-Trunk Interface............................................................................21
2.3.4 (Optional) Configuring the Load Balancing Mode.................................................................................22
2.3.5 (Optional) Limiting the Number of Active Interfaces.............................................................................23
2.3.6 (Optional) Configuring the Load Balancing Mode for Unknown Unicast Traffic..................................24
2.3.7 Checking the Configuration.....................................................................................................................25
2.4 Configuring Link Aggregation in Static LACP Mode.....................................................................................25
2.4.1 Establishing the Configuration Task.......................................................................................................25
2.4.2 Configuring an Eth-Trunk Interface to Work in Static LACP Mode......................................................26
2.4.3 Adding Member Interfaces to an Eth-Trunk Interface............................................................................27
2.4.4 (Optional) Configuring the Load Balancing Mode.................................................................................28
2.4.5 (Optional) Limiting the Number of Active Interfaces.............................................................................29
2.4.6 (Optional) Setting the System LACP Priority.........................................................................................30
2.4.7 (Optional) Setting the LACP Priority for an Interface............................................................................31
2.4.8 (Optional) Enabling LACP Preemption and Setting the Preemption Delay...........................................31
2.4.9 (Optional) Setting the Timeout Interval for Receiving LACP Packets...................................................32
2.4.10 (Optional) Configuring the Load Balancing Mode for Unknown Unicast Traffic................................33
2.4.11 Checking the Configuration...................................................................................................................33
2.5 Configuring an E-Trunk...................................................................................................................................34
2.5.1 Establishing the Configuration Task.......................................................................................................34
2.5.2 Setting the LACP System ID and LACP Priority of an E-Trunk............................................................35
2.5.3 Creating an E-Trunk and Setting the E-Trunk Priority...........................................................................35
2.5.4 Configuring Local and Peer IP Addresses of an E-Trunk.......................................................................36
2.5.5 Binding an E-Trunk to a BFD Session....................................................................................................37
2.5.6 Adding an Eth-Trunk Interface to an E-Trunk........................................................................................37
2.5.7 (Optional) Configuring the Working Mode of an Eth-Trunk Interface in an E-Trunk...........................38
2.5.8 (Optional) Setting the Password for Encrypting Packets........................................................................39
2.5.9 (Optional) Setting the Timeout Interval of Hello Packets.......................................................................40
2.5.10 (Optional) Setting the Revertive Switching Delay................................................................................41
2.5.11 Checking the Configuration...................................................................................................................41
2.6 Maintaining Link Aggregation.........................................................................................................................42
2.6.1 Clearing LACP Packet Statistics.............................................................................................................42
2.6.2 Debugging a Link Aggregation Group....................................................................................................42
2.6.3 Monitoring the Operating Status of a Link Aggregation Group.............................................................43
2.7 Configuration Examples...................................................................................................................................43
2.7.1 Example for Configuring Link Aggregation in Manual Load Balancing Mode.....................................43
2.7.2 Example for Configuring Link Aggregation in Static LACP Mode.......................................................46
3 VLAN Configuration..................................................................................................................50
3.1 Introduction......................................................................................................................................................52
3.2 VLAN Features Supported by the S5700.........................................................................................................59
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
Contents
3.3 Dividing a LAN into VLANs...........................................................................................................................63
3.3.1 Establishing the Configuration Task.......................................................................................................63
3.3.2 Dividing a LAN into VLANs Based on Ports.........................................................................................65
3.3.3 Dividing a LAN into VLANs Based on MAC Addresses.......................................................................67
3.3.4 Dividing a LAN into VLANs Based on IP Subnets................................................................................69
3.3.5 Dividing a LAN into VLANs Based on Protocols..................................................................................70
3.3.6 Dividing a LAN into VLANs Based on Policies.....................................................................................72
3.3.7 Checking the Configuration.....................................................................................................................73
3.4 Creating a VLANIF Interface...........................................................................................................................74
3.4.1 Establishing the Configuration Task.......................................................................................................74
3.4.2 Creating a VLANIF Interface..................................................................................................................75
3.4.3 Assigning an IP Address to a VLANIF Interface....................................................................................75
3.4.4 (Optional) Setting a Delay After Which a VLANIF Interface Goes Down............................................76
3.4.5 (Optional) Setting the MTU of a VLANIF Interface...............................................................................77
3.4.6 Checking the Configuration.....................................................................................................................77
3.5 Configuring Inter-VLAN Communication.......................................................................................................78
3.5.1 Establishing the Configuration Task.......................................................................................................78
3.5.2 Configuring VLANIF Interfaces for Inter-VLAN Communication........................................................79
3.5.3 Checking the Configuration.....................................................................................................................80
3.6 Configuring VLAN Aggregation to Save IP Addresses...................................................................................80
3.6.1 Establishing the Configuration Task.......................................................................................................81
3.6.2 Creating a Sub-VLAN.............................................................................................................................82
3.6.3 Creating a Super-VLAN..........................................................................................................................83
3.6.4 Assigning an IP Address to the VLANIF Interface of a Super-VLAN...................................................83
3.6.5 (Optional) Enabling Proxy ARP on the VLANIF Interface of a Super-VLAN......................................84
3.6.6 Checking the Configuration.....................................................................................................................85
3.7 Configuring a MUX VLAN to Separate Layer 2 Traffic.................................................................................85
3.7.1 Establishing the Configuration Task.......................................................................................................85
3.7.2 Configuring a Principal VLAN for a MUX VLAN................................................................................87
3.7.3 Configuring a Group VLAN for a Subordinate VLAN...........................................................................87
3.7.4 Configuring a Separate VLAN for a Subordinate VLAN.......................................................................88
3.7.5 Enabling the MUX VLAN Function on a Port........................................................................................89
3.7.6 Checking the Configuration.....................................................................................................................89
3.8 Configuring a Voice VLAN to Transmit Voice Data.......................................................................................90
3.8.1 Establishing the Configuration Task.......................................................................................................90
3.8.2 Enabling the Voice VLAN Function.......................................................................................................92
3.8.3 Configuring an OUI for a Voice VLAN..................................................................................................92
3.8.4 (Optional) Setting an Aging Timer for a Voice VLAN...........................................................................93
3.8.5 (Optional) Configuring an 802.1p Priority and a DSCP Value for the Voice VLAN.............................94
3.8.6 (Optional) Configuring the Mode in Which Ports Are Added to a Voice VLAN...................................94
3.8.7 (Optional) Configuring the Working Mode for a Voice VLAN..............................................................95
3.8.8 (Optional) Configuring a Port to Communicate with a Voice Device of Another Vendor.....................96
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
vi
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
Contents
3.8.9 Checking the Configuration.....................................................................................................................97
3.9 Configuring an mVLAN to Implement Integrated Management.....................................................................97
3.9.1 Establishing the Configuration Task.......................................................................................................98
3.9.2 Configuring an mVLAN..........................................................................................................................98
3.9.3 Configuring a VLANIF Interface for an mVLAN..................................................................................99
3.9.4 Checking the Configuration.....................................................................................................................99
3.10 Maintaining VLAN.........................................................................................................................................99
3.10.1 Clearing the Statistics of VLAN Packets............................................................................................100
3.11 Configuration Examples...............................................................................................................................100
3.11.1 Example for Assigning VLANs Based on Ports.................................................................................100
3.11.2 Example for Assigning VLANs based on MAC Addresses................................................................103
3.11.3 Example for Assigning VLANs Based on IP Subnets........................................................................105
3.11.4 Example for Assigning VLANs Based on Protocols...........................................................................108
3.11.5 Example for Implementing Inter-VLAN Communication Using VLANIF Interfaces.......................111
3.11.6 Example for Configuring VLAN Aggregation....................................................................................114
3.11.7 Example for Configuring MUX VLAN..............................................................................................117
3.11.8 Example for Configuring a Voice VLAN in Auto Mode....................................................................120
3.11.9 Example for Configuring a Voice VLAN in Manual Mode................................................................122
4 VLAN Mapping Configuration..............................................................................................126
4.1 Introduction to VLAN Mapping.....................................................................................................................127
4.2 VLAN Mapping Features Supported by the S5700........................................................................................127
4.3 Configuring VLAN Mapping for Single-tagged Packets...............................................................................127
4.3.1 Establishing the Configuration Task.....................................................................................................127
4.3.2 Replacing a Single Tag..........................................................................................................................128
4.3.3 Checking the Configuration...................................................................................................................129
4.4 Configuring VLAN Mapping for Double-tagged Packets.............................................................................129
4.4.1 Establishing the Configuration Task.....................................................................................................129
4.4.2 Replacing the Outer VLAN Tag............................................................................................................130
4.4.3 Checking the Configuration...................................................................................................................130
4.5 Configuration Examples.................................................................................................................................131
4.5.1 Example for Configuring Single-Tag VLAN Mapping........................................................................131
4.5.2 Example for Configuring N:1 VLAN Mapping....................................................................................134
5 QinQ Configuration..................................................................................................................137
5.1 QinQ Overview...............................................................................................................................................138
5.2 QinQ Features Supported by the S5700.........................................................................................................138
5.3 Configuring QinQ on an Interface..................................................................................................................138
5.3.1 Establishing the Configuration Task.....................................................................................................138
5.3.2 Setting the Link Type of an Interface....................................................................................................139
5.3.3 Specifying the Outer VLAN ID.............................................................................................................139
5.3.4 Checking the Configuration...................................................................................................................140
5.4 Configuring Selective QinQ...........................................................................................................................140
5.4.1 Establishing the Configuration Task.....................................................................................................140
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
vii
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
Contents
5.4.2 Setting the Link Type of an Interface....................................................................................................141
5.4.3 Adding the Interface to the Stacked VLAN..........................................................................................141
5.4.4 Configuring Selective QinQ..................................................................................................................142
5.4.5 Checking the Configuration...................................................................................................................142
5.5 Configuring QinQ Stacking on a VLANIF Interface.....................................................................................143
5.5.1 Establishing the Configuration Task.....................................................................................................143
5.5.2 Configuring QinQ Stacking on a VLANIF Interface............................................................................144
5.5.3 Checking the Configuration...................................................................................................................145
5.6 Setting the Protocol Type in the Outer VLAN Tag........................................................................................145
5.6.1 Establishing the Configuration Task.....................................................................................................145
5.6.2 Configuring the Link Type of an Interface............................................................................................146
5.6.3 Setting the Protocol Type in the Outer VLAN Tag...............................................................................146
5.6.4 Checking the Configuration...................................................................................................................147
5.7 Configuration Examples.................................................................................................................................147
5.7.1 Example for Configuring QinQ on Interfaces.......................................................................................147
5.7.2 Example for Configuring Selective QinQ.............................................................................................150
5.7.3 Example for Configuring Selective QinQ with VLAN Mapping..........................................................153
5.7.4 Example for Configuring QinQ Stacking on a VLANIF Interface.......................................................156
6 GVRP Configuration................................................................................................................160
6.1 GVRP Overview.............................................................................................................................................161
6.2 GVRP Features Supported by the S5700.......................................................................................................164
6.3 Configuring GVRP.........................................................................................................................................165
6.3.1 Establishing the Configuration Task.....................................................................................................165
6.3.2 Enabling GVRP.....................................................................................................................................165
6.3.3 (Optional) Setting the Registration Mode for a GVRP Interface..........................................................166
6.3.4 (Optional) Setting the GARP Timers....................................................................................................167
6.3.5 Checking the Configuration...................................................................................................................168
6.4 Maintaining GVRP.........................................................................................................................................168
6.4.1 Clearing GARP Statistics......................................................................................................................168
6.5 Configuration Examples.................................................................................................................................169
6.5.1 Example for Configuring GVRP...........................................................................................................169
7 MAC Address Table Configuration.......................................................................................173
7.1 MAC Address Table Overview......................................................................................................................175
7.2 MAC Address Features Supported by the S5700...........................................................................................176
7.3 Configuring a Static MAC Address Entry......................................................................................................178
7.4 Configuring a Blackhole MAC Address Entry...............................................................................................179
7.5 Setting the Aging Time of Dynamic MAC Address Entries..........................................................................180
7.6 Disabling MAC Address Learning.................................................................................................................181
7.6.1 Establishing the Configuration Task.....................................................................................................181
7.6.2 Disabling MAC Address Learning on an Interface...............................................................................182
7.6.3 Disabling MAC Address Learning in a VLAN.....................................................................................183
7.6.4 Checking the Configuration...................................................................................................................183
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
viii
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
Contents
7.7 Limiting the Number of Learned MAC Addresses........................................................................................183
7.7.1 Establishing the Configuration Task.....................................................................................................184
7.7.2 Limiting the Number of MAC Addresses Learned on an Interface......................................................185
7.7.3 Limiting the Number of MAC Addresses Learned in a VLAN............................................................185
7.7.4 Checking the Configuration...................................................................................................................186
7.8 Configuring Port Security...............................................................................................................................186
7.8.1 Establishing the Configuration Task.....................................................................................................187
7.8.2 Configuring the Secure Dynamic MAC Function on an Interface........................................................187
7.8.3 Configuring the Sticky MAC Function on an Interface........................................................................189
7.8.4 Checking the Configuration...................................................................................................................190
7.9 Configuring MAC Address Anti-Flapping.....................................................................................................190
7.9.1 Establishing the Configuration Task.....................................................................................................190
7.9.2 Setting the MAC Address Learning Priority for an Interface................................................................191
7.9.3 Prohibiting MAC Address Flapping Between Interfaces with the Same Priority.................................192
7.9.4 Checking the Configuration...................................................................................................................192
7.10 Configuring MAC Address Flapping Detection...........................................................................................193
7.10.1 Establishing the Configuration Task...................................................................................................193
7.10.2 Configuring MAC Address Flapping Detection..................................................................................194
7.10.3 (Optional) Unblocking a Blocked Interface or MAC Address............................................................194
7.10.4 Checking the Configuration.................................................................................................................195
7.11 Enabling MAC Spoofing Defense................................................................................................................195
7.12 Configuring the Switch to Discard Packets with an All-Zero MAC Address..............................................196
7.13 Enabling MAC Address-triggered ARP Entry Update.................................................................................197
7.14 Enabling Port Bridge....................................................................................................................................198
7.15 Configuration Examples...............................................................................................................................199
7.15.1 Example for Configuring the MAC Address Table.............................................................................199
7.15.2 Example for Configuring MAC Address Limiting in a VLAN...........................................................202
7.15.3 Example for Configuring Port Security...............................................................................................204
7.15.4 Example for Configuring MAC Address Anti-Flapping.....................................................................206
8 STP/RSTP Configuration.........................................................................................................209
8.1 STP/RSTP Overview......................................................................................................................................210
8.1.1 STP/RSTP Overview.............................................................................................................................210
8.1.2 STP/RSTP Features Supported by the S5700........................................................................................215
8.2 Configuring Basic STP/RSTP Functions.......................................................................................................217
8.2.1 Establishing the Configuration Task.....................................................................................................217
8.2.2 Configuring the STP/RSTP Mode.........................................................................................................219
8.2.3 (Optional) Configuring Switching Device Priorities.............................................................................219
8.2.4 (Optional) Setting the Path Cost for a Port............................................................................................220
8.2.5 (Optional) Configuring Port Priorities...................................................................................................221
8.2.6 Enabling STP/RSTP..............................................................................................................................222
8.2.7 Checking the Configuration...................................................................................................................222
8.3 Configuring STP/RSTP Parameters on an Interface......................................................................................223
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
ix
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
Contents
8.3.1 Establishing the Configuration Task.....................................................................................................225
8.3.2 Setting System Parameters....................................................................................................................226
8.3.3 Setting Port Parameters.........................................................................................................................227
8.3.4 Checking the Configuration...................................................................................................................229
8.4 Configuring RSTP Protection Functions........................................................................................................229
8.4.1 Establishing the Configuration Task.....................................................................................................229
8.4.2 Configuring BPDU Protection on a Switching Device.........................................................................231
8.4.3 Configuring TC Protection on a Switching Device...............................................................................232
8.4.4 Configuring Root Protection on a Port..................................................................................................232
8.4.5 Configuring Loop Protection on a Port.................................................................................................233
8.4.6 Checking the Configuration...................................................................................................................234
8.5 Configuring STP/RSTP Interoperability Between Huawei Devices and Non-Huawei Devices....................234
8.5.1 Establishing the Configuration Task.....................................................................................................234
8.5.2 Configuring the Proposal/Agreement Mechanism................................................................................235
8.5.3 Checking the Configuration...................................................................................................................236
8.6 Maintaining STP/RSTP..................................................................................................................................236
8.6.1 Clearing STP/RSTP Statistics...............................................................................................................237
8.7 Configuration Examples.................................................................................................................................237
8.7.1 Example for Configuring Basic STP Functions....................................................................................237
8.7.2 Example for Configuring Basic RSTP Functions..................................................................................242
9 MSTP Configuration.................................................................................................................247
9.1 MSTP Overview.............................................................................................................................................249
9.1.1 MSTP Introduction................................................................................................................................249
9.1.2 MSTP Features Supported by the S5700...............................................................................................257
9.2 Configuring Basic MSTP Functions...............................................................................................................261
9.2.1 Establishing the Configuration Task.....................................................................................................261
9.2.2 Configuring the MSTP Mode................................................................................................................263
9.2.3 Configuring and Activating an MST Region........................................................................................264
9.2.4 (Optional) Setting a Priority for a Switching Device in an MSTI.........................................................265
9.2.5 (Optional) Setting a Path Cost of a Port in an MSTI.............................................................................266
9.2.6 (Optional) Setting a Port Priority in an MSTI.......................................................................................267
9.2.7 Enabling MSTP.....................................................................................................................................268
9.2.8 Checking the Configuration...................................................................................................................268
9.3 Configuring MSTP Multi-process..................................................................................................................269
9.3.1 Establishing the Configuration Task.....................................................................................................269
9.3.2 Creating an MSTP Process....................................................................................................................270
9.3.3 Adding an Interface to an MSTP Process - Access Links.....................................................................271
9.3.4 Adding an Interface to an MSTP Process - Share Link.........................................................................271
9.3.5 Configuring Priorities and Root Protection in MSTP Multi-process....................................................272
9.3.6 Configuring TC Notification in MSTP Multi-process..........................................................................272
9.3.7 Checking the Configuration...................................................................................................................273
9.4 Configuring MSTP Parameters on an Interface.............................................................................................273
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
Contents
9.4.1 Establishing the Configuration Task.....................................................................................................273
9.4.2 Configuring System Parameters............................................................................................................274
9.4.3 Configuring Port Parameters.................................................................................................................276
9.4.4 Checking the Configuration...................................................................................................................277
9.5 Configuring MSTP Protection Functions.......................................................................................................278
9.5.1 Establishing the Configuration Task.....................................................................................................278
9.5.2 Configuring BPDU Protection on a Switching Device.........................................................................280
9.5.3 Configuring TC Protection on a Switching Device...............................................................................281
9.5.4 Configuring Root Protection on an Interface........................................................................................282
9.5.5 Configuring Loop Protection on an Interface........................................................................................282
9.5.6 Configuring Share-Link Protection on a Switching Device..................................................................283
9.5.7 Checking the Configuration...................................................................................................................284
9.6 Configuring MSTP Interoperability Between Huawei Devices and Non-Huawei Devices...........................284
9.6.1 Establishing the Configuration Task.....................................................................................................284
9.6.2 Configuring a Proposal/Agreement Mechanism...................................................................................285
9.6.3 Configuring the MSTP Protocol Packet Format on an Interface...........................................................286
9.6.4 Enabling the Digest Snooping Function................................................................................................287
9.6.5 Checking the Configuration...................................................................................................................288
9.7 Maintaining MSTP.........................................................................................................................................288
9.7.1 Clearing MSTP Statistics.......................................................................................................................288
9.8 Configuration Examples.................................................................................................................................289
9.8.1 Example for Configuring Basic MSTP Functions.................................................................................289
9.8.2 Example for Configuring MSTP Multi-Process for Layer 2 Single-Access Rings and Layer 2 Multi-Access
Rings...............................................................................................................................................................296
10 SEP Configuration...................................................................................................................304
10.1 SEP Overview...............................................................................................................................................306
10.1.1 SEP Overview......................................................................................................................................306
10.1.2 SEP Features Supported by the S5700................................................................................................319
10.2 Configuring Basic SEP Functions................................................................................................................325
10.2.1 Establishing the Configuration Task...................................................................................................325
10.2.2 Configuring an SEP Segment..............................................................................................................326
10.2.3 Configuring a Control VLAN..............................................................................................................326
10.2.4 Creating a Protected Instance..............................................................................................................327
10.2.5 Adding a Layer 2 Interface to a SEP Segment and Configuring a Role for the Interface...................328
10.2.6 Checking the Configuration.................................................................................................................330
10.3 Specifying an Interface to Block..................................................................................................................330
10.3.1 Establishing the Configuration Task...................................................................................................330
10.3.2 Setting an Interface Blocking Mode....................................................................................................331
10.3.3 Configuring the Preemption Mode......................................................................................................333
10.3.4 Checking the Configuration.................................................................................................................334
10.4 Configuring SEP Multi-Instance..................................................................................................................335
10.4.1 Establishing the Configuration Task...................................................................................................335
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
xi
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
Contents
10.4.2 Configuring and Activating Mappings Between Protected Instances and VLANs.............................337
10.4.3 Checking the Configuration.................................................................................................................337
10.5 Configuring the Topology Change Notification Function...........................................................................338
10.5.1 Establishing the Configuration Task...................................................................................................338
10.5.2 Reporting Topology Changes of a Lower-Layer Network - SEP Topology Change Notification
........................................................................................................................................................................340
10.5.3 Reporting Topology Changes of a Lower-Layer Network - Enabling the Edge Devices in a SEP Segment
to Process SmartLink Flush Packets...............................................................................................................341
10.5.4 Reporting Topology Changes of an Upper-Layer Network - Configuring Association Between SEP and
CFM................................................................................................................................................................342
10.5.5 Checking the Configuration.................................................................................................................343
10.6 Maintaining SEP...........................................................................................................................................343
10.6.1 Clearing SEP Statistics........................................................................................................................343
10.6.2 Debugging SEP....................................................................................................................................343
10.7 Configuration Examples...............................................................................................................................344
10.7.1 Example for Configuring SEP on a Closed Ring Network.................................................................344
10.7.2 Example for Configuring SEP on a Multi-ring Network....................................................................350
10.7.3 Example for Configuring SEP on a Hybrid-ring Network..................................................................361
10.7.4 Example for Configuring a Hybrid SEP+RRPP Ring Network (Reporting the Topology Changes of a
Lower-Layer Network)...................................................................................................................................370
10.7.5 Example for Configuring SEP Multi-Instance on a Closed Ring Network.........................................382
11 Layer 2 Protocol Transparent Transmission Configuration............................................391
11.1 Layer 2 Protocol Transparent Transmission Overview................................................................................393
11.2 Layer 2 Protocol Transparent Transmission Features Supported by the S5700...........................................394
11.3 Configuring Interface-based Layer 2 Protocol Transparent Transmission...................................................400
11.3.1 Establishing the Configuration Task...................................................................................................400
11.3.2 (Optional) Defining Characteristics of a Layer 2 Protocol..................................................................401
11.3.3 Configuring the Transparent Transmission Mode of Layer 2 Protocol Packets.................................402
11.3.4 Enabling Layer 2 Protocol Transparent Transmission on an Interface...............................................403
11.3.5 Checking Configuration......................................................................................................................404
11.4 Configuring VLAN-based Layer 2 Protocol Transparent Transmission......................................................404
11.4.1 Establishing the Configuration Task...................................................................................................404
11.4.2 (Optional) Defining Characteristics of a Layer 2 Protocol..................................................................405
11.4.3 Configuring the Transparent Transmission Mode of Layer 2 Protocol Packets.................................405
11.4.4 Enabling VLAN-based Layer 2 Protocol Transparent Transmission on an Interface.........................406
11.4.5 Checking the Configuration.................................................................................................................407
11.5 Configuring QinQ-based Layer 2 Protocol Transparent Transmission........................................................408
11.5.1 Establishing the Configuration Task...................................................................................................408
11.5.2 (Optional) Defining Characteristics of a Layer 2 Protocol..................................................................408
11.5.3 Configuring the Transparent Transmission Mode of Layer 2 Protocol Packets.................................409
11.5.4 Enabling QinQ-based Layer 2 Transparent Transmission on an Interface..........................................410
11.5.5 Checking the Configuration.................................................................................................................411
11.6 Maintaining Layer 2 Protocol Transparent Transmission............................................................................411
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
xii
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
Contents
11.6.1 Debugging Layer 2 Protocol Transparent Transmission.....................................................................412
11.7 Configuration Examples...............................................................................................................................412
11.7.1 Example for Configuring Interface-based Layer 2 Protocol Transparent Transmission.....................412
11.7.2 Example for Configuring VLAN-based Layer 2 Protocol Transparent Transmission........................419
11.7.3 Example for Configuring QinQ-based Layer 2 Protocol Transparent Transmission..........................426
12 Loopback Detection Configuration.....................................................................................433
12.1 Loopback Detection Overview.....................................................................................................................434
12.2 Configuring Loopback Detection.................................................................................................................434
12.2.1 Establishing the Configuration Task...................................................................................................434
12.2.2 Enabling Loopback Detection.............................................................................................................436
12.2.3 Specifying VLAN IDs of Loopback Detection Packets......................................................................436
12.2.4 (Optional) Configuring an Action to Perform After a Loopback Is Detected.....................................437
12.2.5 (Optional) Setting the Interface Recovery Time After a Loop Is Removed........................................438
12.2.6 (Optional) Setting the Interval for Sending Loopback Detection Packets on an Interface.................439
12.2.7 Checking the Configuration.................................................................................................................439
12.3 Configuration Examples...............................................................................................................................439
12.3.1 Example for Configuring Loopback Detection...................................................................................439
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
xiii
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
1 Ethernet Interface Configuration
Ethernet Interface Configuration
About This Chapter
This chapter describes the basic knowledge, methods, and examples for configuring the Ethernet
interface.
1.1 Introduction to Ethernet Interfaces
This section describes the types and attributes of Ethernet interfaces.
1.2 Ethernet Interface Features Supported by the S5700
The S5700 supports the following features that you can configure for Ethernet interfaces: port
grouping, auto-negotiation, and port isolation.
1.3 Configuring Basic Attributes of an Ethernet Interface
This section describes how to configure the description, cable type, duplex mode, rate, and autonegotiation for an Ethernet interface. The section also explains how to change the interface type
(optical or electrical) of combo interfaces and configure an interface to work at Layer 2 or Layer
3.
1.4 Configuring Advanced Attributes of an Ethernet Interface
This section describes how to configure the advanced attributes of an Ethernet interface,
including loopback test, port group, maximum frame size, flow control, flow control autonegotiation, cable test, loopback test, and port isolation.
1.5 Maintaining Ethernet Interfaces
This section describes how to maintain Ethernet interfaces.
1.6 Configuration Examples
This section provides a configuration example of port isolation.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
1 Ethernet Interface Configuration
1.1 Introduction to Ethernet Interfaces
This section describes the types and attributes of Ethernet interfaces.
Ethernet is an important local area network (LAN) networking technology because it is flexible,
simple, and easy to implement.
Ethernet interfaces are classified into Ethernet electrical interfaces and optical interfaces.
Table 1-1 shows the attributes of Ethernet electrical interfaces and optical interfaces.
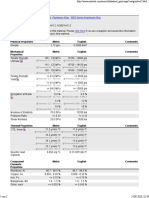
Table 1-1 Attributes of Ethernet interfaces
Interface
Type
Rate (Mbit/
s)
Auto-negotiation
Non-negotiation
Full
Duplex
Half
Duplex
Full
Duplex
Half
Duplex
Electrical
10
Yes
Yes
Yes
Yes
100
Yes
Yes
Yes
Yes
1000
Yes
No
Yes
No
100
No
No
Yes
No
1000
Yes
No
Yes
No
10000
No
No
Yes
No
Optical
If the local interface works in auto-negotiation mode, the peer interface must also work in autonegotiation mode; otherwise, packet loss occurs.
1.2 Ethernet Interface Features Supported by the S5700
The S5700 supports the following features that you can configure for Ethernet interfaces: port
grouping, auto-negotiation, and port isolation.
Port Group
A port group allows you to configure multiple interfaces at the same time. After you run a
command in the port group view, the configuration applies to all the interfaces in the group.
Auto-Negotiation
The auto-negotiation function allows interfaces on both ends of a link to select the same operating
parameters. Each interface sends its capability information to the remote end and checks the
capabilities of the remote end. After both interfaces receive capability information from each
other, they adopt the highest capability they both support to communicate with each other.
The interfaces negotiate the duplex mode, speed, and flow control parameters. After a successful
negotiation, the interfaces use the same duplex mode, speed, and flow control parameters.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
1 Ethernet Interface Configuration
Port Isolation
The port isolation function isolates Layer 2 and Layer 3 communication between ports in the
same VLAN. This function restricts packet transmission between ports flexibly, to provide a
secure and flexible network solution.
1.3 Configuring Basic Attributes of an Ethernet Interface
This section describes how to configure the description, cable type, duplex mode, rate, and autonegotiation for an Ethernet interface. The section also explains how to change the interface type
(optical or electrical) of combo interfaces and configure an interface to work at Layer 2 or Layer
3.
1.3.1 Establishing the Configuration Task
Applicable Environment
The task to configure basic attributes includes setting the following parameters:
l
Interface description. You can configure interface descriptions to facilitate interface
identification, maintenance, and configuration.
Cable type. By default, a fast Ethernet (FE) electrical interface automatically identifies the
network cable type. If the interface cannot identify the cable type, set the cable type for the
interface.
Duplex mode. By default, an FE electrical interface negotiates the duplex mode and rate
with the equipment that is directly connected to the interface. If the connected device does
not have auto-negotiation capability, set the duplex mode and rate for the FE interface so
that the interface can communicate with the connected device.
Pre-configuration Tasks
None.
Data Preparation
To configure the basic attributes of an Ethernet interface, you need the following data.
Issue 02 (2011-11-21)
No.
Data
Number of the Ethernet interface
(Optional) Description of the interface
(Optional) Cable type of the Ethernet electrical interface
(Optional) Duplex mode of the Ethernet electrical interface
(Optional) Rate of the Ethernet interface
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
1 Ethernet Interface Configuration
1.3.2 (Optional) Configuring an Interface Description
Context
Perform the following steps on the switch to configure the description of an interface.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
interface interface-type interface-number
The interface view is displayed.
Step 3 Run:
description description
A description is configured for the interface.
By default, an interface description is "HUAWEI, Quidway Series, X interface", where X
specifies the interface type and number.
----End
1.3.3 (Optional) Configuring the Cable Type on an Interface
Context
Perform the following steps on the switch to configure the cable type on an interface.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
interface interface-type interface-number
The Ethernet electrical interface view is displayed.
Step 3 Run:
mdi { across | auto | normal }
The cable type is configured for the Ethernet electrical interface.
By default, an Ethernet electrical interface automatically identifies the cable type. Use this
command when the actual cable type does not match the cable type supported by the interface.
An electrical interface can use a crossover cable or a straight-through cable. If across is specified,
the interface can only use a crossover cable. If normal is specified, the interface can only use a
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
1 Ethernet Interface Configuration
straight-through cable. If auto is specified, the interface can use either a straight-through cable
or a crossover cable.
----End
1.3.4 (Optional) Setting the Duplex Mode
Context
Perform the following steps on the switch to set the duplex mode for an Ethernet interface.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
interface interface-type interface-number
The Ethernet electrical interface view is displayed.
Step 3 Run:
undo negotiation auto
Auto-negotiation is disabled on the Ethernet electrical interface.
Step 4 Run:
duplex { full | half }
The duplex mode is set for the Ethernet electrical interface.
By default, an Ethernet electrical interface works in full-duplex mode when auto-negotiation is
disabled on the interface.
----End
1.3.5 (Optional) Setting the Interface Rate
Context
Perform the following steps on the switch to set the interface rate.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
interface interface-type interface-number
The interface view is displayed.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
1 Ethernet Interface Configuration
Step 3 Run:
undo negotiation auto
Auto-negotiation is disabled on the interface.
Step 4 Run:
speed { 10 | 100 | 1000 }
The interface rate is set.
By default, an Ethernet interface works at its maximum rate when auto-negotiation is disabled
on the interface.
----End
1.3.6 (Optional) Enabling Auto-Negotiation
Context
Perform the following steps on the switch to enable auto-negotiation on an Ethernet interface.
The local interface and remote interface must work in the same mode, that is, both or neither
work in auto-negotiation mode.
NOTE
10G optical interfaces do not support auto-negotiation.
The negotiation auto command cannot enable rate negotiation for 1000M optical interfaces. On the
S5700HI, you can use the speed auto-negotiation command to enable rate negotiation for 1000M optical
interfaces.
When the S5700SI switch connects to another device through a GE optical interface on the Interface
Subcards, configure the GE optical interface to work in non-auto negotiation mode.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
interface interface-type interface-number
The interface view is displayed.
Step 3 Run:
negotiation auto
Auto-negotiation is enabled on the interface.
By default, an interface works in auto-negotiation mode.
----End
1.3.7 (Optional) Switching Between Optical and Electrical
Interfaces
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
1 Ethernet Interface Configuration
Context
Perform the following steps on the switch to change the combo interface type.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
interface gigabitethernet interface-number
The GigabitEthernet interface view is displayed.
Step 3 Run:
combo-port { auto | copper | fiber }
The interface is changed to an optical interface or an electrical interface.
By default, a combo interface automatically selects the working mode according to the
transmission media.
----End
1.3.8 (Optional) Configuring an Interface to Work at Layer 2 or Layer
3
Context
NOTE
Only the S5700HI supports the portswitch command.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
interface interface-type interface-number
The interface view is displayed.
Step 3 Run:
portswitch
The interface is configured to work at Layer 2.
Step 4 Run:
undo portswitch
The interface is configured to work at Layer 3.
By default, an Ethernet interface works at Layer 2.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
1 Ethernet Interface Configuration
When you change an Ethernet interface from Layer 3 to Layer 2, the Layer 3 functions and
identifier are disabled on the interface, and the interface uses the MAC address of the system.
----End
1.3.9 Checking the Configuration
Procedure
Step 1 Run the display interface [ interface-type [ interface-number ] ] command to check the
description, duplex mode, and rate of an Ethernet interface.
----End
1.4 Configuring Advanced Attributes of an Ethernet
Interface
This section describes how to configure the advanced attributes of an Ethernet interface,
including loopback test, port group, maximum frame size, flow control, flow control autonegotiation, cable test, loopback test, and port isolation.
1.4.1 Establishing the Configuration Task
Applicable Environment
Advanced attributes of an Ethernet interface include:
l
Port group. The S5700 provides the interface group function, which enables you to
configure multiple interfaces at the same time.
Flow control. If the rate of traffic received on an interface is likely to exceed the interface
processing capability, and the directly connected interface supports flow control, enable
flow control on the local interface. When the rate of received traffic reaches the threshold,
the interface sends a Pause frame (in full duplex mode) or a back pressure signal (in half
duplex mode) to notify the remote interface. If the remote interface supports flow control,
it sends traffic at a lower rate so that the local interface can process received traffic.
Port isolation. The port isolation function prevents interfaces in the same VLAN from
communicating with each other. Interfaces with port isolation enabled cannot communicate
with each other. This function provides secure and flexible networking solutions for
customers.
Pre-configuration Tasks
None.
Data Preparation
To configure the advanced functions of an Ethernet interface, you need the following data.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
1 Ethernet Interface Configuration
No.
Data
Interface number
(Optional) Maximum frame length allowed on the interface
1.4.2 (Optional) Configuring the Loopback Function
Context
Perform the following steps on the switch to configure the loopback function on an Ethernet
interface.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
interface interface-type interface-number
The interface view is displayed.
Step 3 Run:
loopback internal
The loopback function is configured on the Ethernet interface.
By default, the loopback function is disabled on an Ethernet interface.
----End
1.4.3 (Optional) Configuring a Port Group
Context
Perform the following steps on the switch to configure a port group.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
port-group port-group-name
The port group view is displayed.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
1 Ethernet Interface Configuration
Step 3 Run:
group-member interface-type interface-number
An Ethernet interface is added to the port group.
----End
1.4.4 (Optional) Setting the Maximum Frame Length
Context
Perform the following steps on the switch to set the maximum frame length on an Ethernet
interface.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
interface interface-type interface-number
The Ethernet interface view is displayed.
Step 3 Run:
jumboframe enable [ value ]
The maximum frame length is set on the Ethernet interface.
By default, the maximum frame length allowed by interfaces of the S5700EI and S5700SI is
1600 bytes. The maximum frame length allowed by interfaces of the S5700HI and S5706 is
9216 bytes.
----End
1.4.5 (Optional) Enabling Flow Control
Context
To implement flow control, you must enable this function on both the local interface and peer
interface. Perform the following steps on the switch to enable flow control.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
interface interface-type interface-number
The interface view is displayed.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
10
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
1 Ethernet Interface Configuration
Step 3 Run:
flow-control
Flow control is enabled on the interface.
By default, flow control is disabled on an Ethernet interface.
----End
1.4.6 (Optional) Enabling Auto-Negotiation of Flow Control
Context
Perform the following steps on the switch to configure auto-negotiation of flow control.
GE interfaces support auto-negotiation of flow control, but FE interfaces do not.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
interface gigabitethernet interface-number
The GE interface view is displayed.
Step 3 Run:
flow-control negotiation
Auto-negotiation of flow control is enabled on the GE interface.
By default, auto-negotiation of flow control is disabled on a GE interface.
You must also configure auto-negotiation of flow control on the peer interface.
----End
1.4.7 (Optional) Enabling Port Isolation
Context
Perform the following steps on the switch to enable port isolation.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
port-isolate mode { l2 | all }
The port isolation mode is set.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
11
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
1 Ethernet Interface Configuration
By default, ports are isolated on Layer 2 but can communicate on Layer 3.
Step 3 Run:
interface interface-type interface-number
The Ethernet interface view is displayed.
Step 4 (Optional) Run:
am isolate interface-type interface-number [ to interface-number ]
The Ethernet interface is unidirectionally isolated from the specified interface.
NOTE
After interface A is unidirectionally isolated from interface B, packets sent by interface A cannot reach
interface B, whereas packets sent from interface B can reach interface A.
Step 5 Run:
port-isolate enable [ group group-id ]
Port isolation is enabled.
NOTE
Interfaces in a port isolation group are isolated from each other, and interfaces in different port isolation
groups can communicate with each other. If group-id is not specified, an interface is added to port isolation
group 1.
----End
1.4.8 (Optional) Performing a Cable Test
Context
A cable test detects faults on the cable connected to an interface. If the cable is working properly,
the test result displays the total length of the cable. If the cable cannot work properly, he test
result displays the distance between the interface and the failure point.
NOTE
l Before performing a cable test, shut down the remote interface or remove the network cable from the
remote interface. Otherwise, signals from the remote interface may make the test result inaccurate.
l Running the virtual-cable-test command affect services on the interface in a short period of time.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
interface interface-type interface-number
The interface view is displayed.
Step 3 Run:
virtual-cable-test
A cable test is performed on the interface.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
12
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
1 Ethernet Interface Configuration
NOTE
The test result is for reference only.
----End
1.4.9 (Optional) Configuring a Loopback Test on an Interface
Context
Perform the following steps on the S5700 where a loopback test needs to be performed.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
interface interface-type interface-number
The interface view is displayed.
Step 3 Run:
loopbacktest internal
A loopback test is configured on the interface.
By default, no loopback test is configured on an interface.
----End
1.4.10 Checking the Configuration
Procedure
l
Run the display port-group [ all | port-group-name ] command to check information about
a port group.
Run the display interface [ interface-type [ interface-number ] ] command to check autonegotiation capability on an Ethernet interface.
Run the display virtual-cable-test interface-type interface-number command to check the
cable test result on an Ethernet interface.
----End
1.5 Maintaining Ethernet Interfaces
This section describes how to maintain Ethernet interfaces.
1.5.1 Debugging Ethernet Interfaces
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
13
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
1 Ethernet Interface Configuration
Context
CAUTION
Debugging affects the performance of the system. Therefore, run the undo debugging all
command to disable debugging immediately after the debugging is complete.
When an Ethernet interface or Eth-Trunk fault occurs, run the following debugging command
in the user view to locate the fault.
Procedure
Step 1 Run the debugging l2if [ error | event | msg | updown ] command to enable the debugging of
link layer features.
----End
1.6 Configuration Examples
This section provides a configuration example of port isolation.
1.6.1 Example for Configuring Port Isolation
Networking Requirements
As shown in Figure 1-1, it is required that PC1 and PC2 cannot communicate with each other,
but they can communicate with PC3.
Figure 1-1 Networking diagram for port isolation configuration
Switch
GE0/0/2
GE0/0/1
GE0/0/3
PC1
PC2
PC3
10.10.10.1/24 10.10.10.2/24 10.10.10.3/24
Configuration Roadmap
The configuration roadmap is as follows:
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
14
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
1.
1 Ethernet Interface Configuration
Enable port isolation on the ports connected to PC1 and PC2 respectively to prevent PC1
and PC2 from communicating with each other.
Data Preparation
To complete the configuration, you need the following data:
l
Number of the port connected to PC1
Number of the port connected to PC2
Port isolation mode: Layer 2 isolation and Layer 3 communication (default configuration)
ID of the VLAN to which the ports connected to PC1, PC2, and PC3 belong (VLAN 1 by
default)
Port isolation group to which the ports connected to PC1 and PC2 belong (group 1 by
default)
Procedure
Step 1 Enable port isolation.
# Isolate ports on Layer 2 and allow them to communicate on Layer 3.
<Quidway> system-view
[Quidway] port-isolate mode l2
# Enable port isolation on GigabitEthernet 0/0/1.
<Quidway> system-view
[Quidway] interface gigabitethernet 0/0/1
[Quidway-GigabitEthernet0/0/1] port-isolate enable
[Quidway-GigabitEthernet0/0/1] quit
# Enable port isolation on GigabitEthernet 0/0/2.
<Quidway> system-view
[Quidway] interface gigabitethernet 0/0/2
[Quidway-GigabitEthernet0/0/2] port-isolate enable
[Quidway-GigabitEthernet0/0/2] quit
Step 2 Verify the configuration.
PC1 and PC2 cannot ping each other.
PC1 and PC3 can ping each other.
PC2 and PC3 can ping each other.
----End
Configuration Files
Configuration file of the Switch
#
sysname Quidway
#
interface GigabitEthernet0/0/1
port-isolate enable group 1
#
interface GigabitEthernet0/0/2
port-isolate enable group 1
#
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
15
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
1 Ethernet Interface Configuration
interface GigabitEthernet0/0/3
#
return
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
16
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
2 Link Aggregation Configuration
Link Aggregation Configuration
About This Chapter
This chapter describes the concepts, configuration procedures, and configuration examples of
link aggregation.
2.1 Introduction to Link Aggregation
This section describes the definition and function of link aggregation.
2.2 Link Aggregation Supported by the S5700
This S5700 supports link aggregation in manual load balancing mode and static Link
Aggregation Control Protocol (LACP) mode.
2.3 Configuring Link Aggregation in Manual Load Balancing Mode
This section describes how to configure link aggregation in manual load balancing mode.
2.4 Configuring Link Aggregation in Static LACP Mode
This section describes how to configure link aggregation in static LACP mode.
2.5 Configuring an E-Trunk
As an extension to the Link Aggregation Protocol (LACP) that implements link aggregation on
a single device, the Enhanced Trunk (E-Trunk) protocol implements link aggregation between
devices to improve link reliability between devices.
2.6 Maintaining Link Aggregation
This section describes how to clear the statistics of received and sent LACP packets, debug the
link aggregation group, and monitor the running status of the link aggregation group.
2.7 Configuration Examples
This section provides several configuration examples of link aggregation in manual load
balancing mode and static LACP mode.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
17
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
2 Link Aggregation Configuration
2.1 Introduction to Link Aggregation
This section describes the definition and function of link aggregation.
Link aggregation is a method of bundling a group of physical interfaces into a logical interface
to increase link bandwidth. It is also called load sharing group or link aggregation group. For
details, refer to IEEE802.3ad.
By setting up a link aggregation group between two devices, you can obtain higher bandwidth
and reliability. Link aggregation provides redundancy protection without the need for upgrading
the hardware.
2.2 Link Aggregation Supported by the S5700
This S5700 supports link aggregation in manual load balancing mode and static Link
Aggregation Control Protocol (LACP) mode.
Manual Load Balancing Mode
In load balancing mode, you can add member interfaces to the link aggregation group. All the
interfaces in the link aggregation group are in forwarding state. The S5700 can perform load
balancing based on destination MAC addresses, source MAC addresses, source MAC address
Exclusive-Or destination MAC address, source IP addresses, destination IP addresses, source
address Exclusive-Or destination IP address.
In manual load balancing mode, you must create an Eth-Trunk interface and add member
interfaces to the Eth-Trunk. The Link Aggregation Control Protocol (LACP) is not used in this
mode.
The manual load balancing mode is usually used when the peer device does not support LACP.
Static LACP Mode
In static LACP mode, two devices exchange LACP packets to negotiate aggregation parameters
and determine the active interfaces and inactive interfaces. In this mode, you must create an EthTrunk interface and add member interfaces to the Eth-Trunk interface. The active interfaces and
inactive interfaces are determined by LACP negotiation.
The static LACP mode is also called the M:N mode, where links implement load balancing and
redundancy at the same time. In a link aggregation group, M links are active and load balance
data traffic. N links are inactive and function as backup links. When an active link fails, the
backup link with the highest priority replaces the failed link to forward data and its status changes
to active.
In static LACP mode, some links function as backup links. In manual load balancing mode, all
member interfaces work in forwarding state to share the traffic. This is the main difference
between the two modes.
Active Interface and Inactive Interface
Active interfaces are the interfaces that are responsible for forwarding data. The interfaces that
do not forward data are called inactive interfaces. Active and inactive interfaces are classified
according to the operation modes, as follows:
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
18
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
2 Link Aggregation Configuration
Manual load balancing mode: All member interfaces are active interfaces unless a fault
occurs.
Static LACP mode: The interfaces connected to M links are active interfaces responsible
for forwarding data. The interfaces connected to N links are inactive interfaces used for
redundancy backup.
Actor and Partner
In static LACP mode, the device in the link aggregation group with a higher LACP priority is
the Actor, and the device with a lower LACP priority is the Partner.
If the two devices have the same LACP priority, the Actor is selected based on the MAC
addresses of the devices. The device with a smaller MAC address becomes the Actor.
Differentiating the Actor and the Partner keeps the active interfaces at both ends consistent. If
the devices select active interfaces according to the priorities of their own interfaces, the two
ends may have different number of the active interfaces and the active links cannot be set up.
Therefore, the Actor is determined first. The Partner selects active interfaces according to the
interface priorities on the Actor. Figure 2-1 shows the process to select active interfaces.
Figure 2-1 Determining active links in static LACP mode
SwitchA
SwitchB
Device with high
priority
SwitchA
Device with low
priority
The Actor determines
the active link
SwitchB
Active interface selected by SwitchA
Active interface selected by SwitchB
2.3 Configuring Link Aggregation in Manual Load
Balancing Mode
This section describes how to configure link aggregation in manual load balancing mode.
2.3.1 Establishing the Configuration Task
Applicable Environment
When you need to increase the bandwidth or reliability of two devices and one of the two devices
does not support LACP, create an Eth-Trunk interface in manual load balancing mode on the
two devices and add member interfaces to the Eth-Trunk interface.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
19
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
2 Link Aggregation Configuration
As shown in Figure 2-2, an Eth-Trunk is established between SwitchA and SwitchB.
Figure 2-2 Link aggregation in load balancing mode
Eth-Trunk 1
Eth-Trunk 1
Eth-Trunk
SwitchA
SwitchB
Pre-configuration Tasks
Before configuring link aggregation in manual load balancing mode, complete the following
tasks:
l
Powering on the switch
Creating an Eth-Trunk interface
Data Preparation
To configure link aggregation in manual load balancing mode, you need the following data.
No.
Data
Number of the Eth-Trunk interface in manual load balancing mode
Types and numbers of the member interfaces
2.3.2 Configuring an Eth-Trunk Interface to Work in Manual Load
Balancing Mode
Context
NOTE
Before you configure the operation mode of an Eth-Trunk interface, check whether the Eth-Trunk interface
contains member interfaces. If the Eth-Trunk contains member interfaces, you cannot change the operation
mode of the Eth-Trunk interface. To delete member interfaces from the Eth-Trunk interface, run the undo
eth-trunk command in the member interface view or run the undo trunkport interface-type interfacenumber command in the Eth-Trunk interface view.
Perform the following steps on the switch to configure an Eth-Trunk interface in manual load
balancing mode.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
20
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
2 Link Aggregation Configuration
Step 2 Run:
interface eth-trunk trunk-id
The Eth-Trunk interface view is displayed.
Step 3 Run:
mode manual load-balance
The operation mode of the Eth-Trunk interface is set to load balancing.
By default, an Eth-Trunk interface works in manual load balancing mode.
If local Eth-Trunk interface works in manual load balancing mode, the peer Eth-Trunk interface
must also work in manual load balancing mode.
----End
2.3.3 Adding Member Interfaces to an Eth-Trunk Interface
Context
Perform the following steps on the switch to add member interfaces to an Eth-Trunk interface.
Procedure
l
Configuration in the Eth-Trunk interface view
1.
Run:
system-view
The system view is displayed.
2.
Run:
interface eth-trunk trunk-id
The Eth-Trunk interface view is displayed.
3.
Run:
trunkport interface-type { interface-number1 [ to interface-number2 ] }
&<1-8>
Member interfaces are added to the Eth-Trunk.
l
Configuration in the member interface view
1.
Run:
system-view
The system view is displayed.
2.
Run:
interface interface-type interface-number
The interface view is displayed.
3.
Run:
eth-trunk trunk-id
The interface is added to the Eth-Trunk interface.
When adding an interface to an Eth-Trunk interface, pay attention to the following points:
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
21
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
2 Link Aggregation Configuration
An Eth-Trunk contains a maximum of eight member interfaces.
A member interface cannot be configured with any service or static MAC address.
When adding an interface to an Eth-Trunk interface, ensure that the interface is a hybrid
interface (default interface type).
An Eth-Trunk cannot be nested, that is, its member interfaces cannot be Eth-Trunk.
An Ethernet interface can be added to only one Eth-trunk interface. To add the Ethernet
interface to another Eth-trunk interface, delete it from the current Eth-Trunk first.
An Eth-trunk interface contains member interfaces of the same type. For example, an
FE interface and a GE interface cannot be added to the same Eth-trunk interface.
Ethernet interfaces on different LPUs can be added to the same Eth-Trunk interface.
The peer interfaces directly connected to the local Eth-Trunk member interfaces must
also be bundled into an Eth-Trunk interface; otherwise, the two ends cannot
communicate.
When the member interfaces work at different rates, the interfaces with a smaller rate
may be congested, and packets may be lost on these interfaces.
After interfaces are added to an Eth-Trunk interface, MAC addresses are learned on the
Eth-Trunk interface but not the member interfaces.
----End
2.3.4 (Optional) Configuring the Load Balancing Mode
Context
Perform the following steps on the switch to configure an Eth-Trunk interface in load balancing
mode.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
interface eth-trunk trunk-id
The Eth-Trunk interface view is displayed.
Step 3 Run:
load-balance { dst-ip | dst-mac | src-ip | src-mac | src-dst-ip | src-dst-mac }
The load balancing mode is configured for the Eth-Trunk interface.
The default load balancing mode of the S5700SI and S5700EI is src-dst-mac; the default load
balancing mode of the S5706 and S5700HI is src-dst-ip.
The S5700 supports the following load balancing modes:
l dst-ip: based on the destination IP address. In this mode, the system obtains the specified
three bits from each of the destination IP address and the TCP/UDP port number in outgoing
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
22
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
2 Link Aggregation Configuration
packets to perform the Exclusive-OR calculation, and then selects the outbound interface
from the Eth-Trunk table according to the calculation result.
l dst-mac: based on the destination MAC address. The system obtains the specified three bits
from each of the destination MAC address, VLAN ID, Ethernet type, and inbound interface
information to perform the Exclusive-OR calculation, and then selects the outbound interface
from the Eth-Trunk table according to the calculation result.
l src-ip: based on the source IP address. The system obtains the specified three bits from each
of the source IP address and the TCP or UDP port number in incoming packets to perform
the Exclusive-OR calculation, and then selects the outbound interface from the Eth-Trunk
table according to the calculation result.
l src-mac: based on the source MAC address. The system obtains the specified three bits from
each of the source MAC address, VLAN ID, Ethernet type, and inbound interface information
to perform the Exclusive-OR calculation, and then selects the outbound interface from the
Eth-Trunk table according to the calculation result.
l src-dst-ip: based on the Exclusive-OR result of the source IP address and destination IP
address. The system performs the Exclusive-OR calculation between the Exclusive-OR
results of the dip and dmac modes, and then selects the outbound interface from the EthTrunk table according to the calculation result.
l src-dst-mac: based on the Exclusive-OR result of the source MAC address and destination
MAC address. The system obtains three bits from each of the source MAC address,
destination MAC address, VLAN ID, Ethernet type, and inbound interface information to
perform the Exclusive-OR calculation, and then selects the outbound interface from the EthTrunk table according to the calculation result.
Member interfaces of an Eth-Trunk interface perform per-flow load balancing. The local end
and the remote end can use different load balancing modes. The load balancing mode on one
end does not affect load balancing on the other end.
----End
2.3.5 (Optional) Limiting the Number of Active Interfaces
Context
Perform the following steps on the switch to limit the number of active interfaces in an EthTrunk interface.
Procedure
l
Setting the maximum number of interfaces that determine bandwidth of the Eth-Trunk
interface
1.
Run:
system-view
The system view is displayed.
2.
Run:
interface eth-trunk trunk-id
The Eth-Trunk interface view is displayed.
3.
Run:
max bandwidth-affected-linknumber link-number
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
23
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
2 Link Aggregation Configuration
The maximum number of interfaces that determine bandwidth of the Eth-Trunk
interface is set.
By default, the maximum number of interfaces that determine bandwidth of an EthTrunk interface is 8.
NOTE
l The maximum number of interfaces that determine bandwidth of the Eth-Trunk interface on the
local switch can be different from that on the remote switch. If the two values are different, the
smaller one is used.
Setting the minimum number of active interfaces
1.
Run:
system-view
The system view is displayed.
2.
Run:
interface eth-trunk trunk-id
The Eth-Trunk interface view is displayed.
3.
Run:
least active-linknumber link-number
The minimum number of active interfaces is set.
By default, the minimum number of active interfaces is 1.
In manual load balancing mode, you can determine the minimum number of active
interfaces in an Eth-Trunk interface. If the number of active interfaces is smaller than the
value, the status the Eth-Trunk interface becomes Down.
NOTE
l The minimum number of active interfaces on the local switch can be different from that on the
remote switch. If the two values are different, the larger one is used.
----End
2.3.6 (Optional) Configuring the Load Balancing Mode for
Unknown Unicast Traffic
Context
Perform the following steps on the switch to configure the load balancing mode for unknown
unicast traffic.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
unknown-unicast load-balance { dmac | smac | smacxordmac }
The load balancing mode for unknown unicast traffic is configured.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
24
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
2 Link Aggregation Configuration
NOTE
Only the S5700EI supports the unknown-unicast load-balance command.
----End
2.3.7 Checking the Configuration
Procedure
l
Run the display trunkmembership eth-trunk trunk-id command to check the member
interfaces of the Eth-Trunk interface.
Run the display eth-trunk trunk-id command to check the load balancing status of the EthTrunk interface.
----End
2.4 Configuring Link Aggregation in Static LACP Mode
This section describes how to configure link aggregation in static LACP mode.
2.4.1 Establishing the Configuration Task
Applicable Environment
To increase the bandwidth and improve connection reliability, you can configure a link
aggregation group on two directly connected switches. The requirements for the link aggregation
group are:
l
The links between two devices implement redundancy backup. When a fault occurs on
some links, the backup links replace the faulty ones to maintain uninterrupted data
transmission.
The active links have the load balancing capability.
To meet these requirements, configure link aggregation in static LACP mode.
Figure 2-3 Typical networking of link aggregation in static LACP mode
Eth-Trunk 1
Eth-Trunk 1
Eth-Trunk
Active link
Standby link
SwitchB
SwitchA
Pre-configuration Tasks
Before configuring link aggregation in static LACP mode, complete the following tasks:
l
Issue 02 (2011-11-21)
Powering on the S5700
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
25
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
2 Link Aggregation Configuration
Creating an Eth-Trunk interface
Data Preparation
To configure link aggregation in static LACP mode, you need the following data.
No.
Data
Number of the Eth-Trunk interface
Types and numbers of the member interfaces
Maximum number of active interfaces
2.4.2 Configuring an Eth-Trunk Interface to Work in Static LACP
Mode
Context
NOTE
Before you configure the operation mode of an Eth-Trunk interface, check whether the Eth-Trunk interface
contains member interfaces. If the Eth-Trunk contains member interfaces, you cannot change the operation
mode of the Eth-Trunk interface. To delete member interfaces from the Eth-Trunk interface, run the undo
eth-trunk command in the member interface view or run the undo trunkport interface-type interfacenumber command in the Eth-Trunk interface view.
Perform the following steps on the switch to configure an Eth-Trunk interface in static LACP
mode.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
interface eth-trunk trunk-id
The Eth-Trunk interface view is displayed.
Step 3 Run:
bpdu enable
The Eth-Trunk member interfaces are enabled to send the received BPDUs to the CPU.
Step 4 Run:
mode lacp-static
The Eth-Trunk interface is configured to work in static LACP mode.
By default, an Eth-Trunk interface works in manual load balancing mode.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
26
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
2 Link Aggregation Configuration
If the Eth-Trunk interface works in static LACP mode, the remote Eth-Trunk interface must also
work in static LACP mode.
----End
2.4.3 Adding Member Interfaces to an Eth-Trunk Interface
Context
Perform the following steps on the switch to add member interfaces to an Eth-Trunk interface.
Procedure
l
Configuration in the Eth-Trunk interface view
1.
Run:
system-view
The system view is displayed.
2.
Run:
interface eth-trunk trunk-id
The Eth-Trunk interface view is displayed.
3.
Run:
trunkport interface-type { interface-number1 [ to interface-number2 ] }
&<1-8>
Member interfaces are added to the Eth-Trunk interface.
l
Configuration in the member interface view
1.
Run:
system-view
The system view is displayed.
2.
Run:
interface interface-type interface-number
The interface view is displayed.
3.
Run:
eth-trunk trunk-id
The interface is added to the Eth-Trunk interface.
When adding an interface to an Eth-Trunk interface, pay attention to the following points:
An Eth-Trunk contains a maximum of eight member interfaces.
A member interface cannot be configured with any service or static MAC address.
When adding an interface to an Eth-Trunk, ensure that the interface is a hybrid interface
(default interface type).
An Eth-Trunk interface cannot have other Eth-Trunk interfaces as its member interfaces.
An Ethernet interface can be added to only one Eth-Trunk interface. To add the Ethernet
interface to another Eth-Trunk interface, delete it from the current Eth-Trunk first.
An Eth-Trunk interface contains member interfaces of the same type. For example, an
FE interface and a GE interface cannot be added to the same Eth-Trunk.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
27
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
2 Link Aggregation Configuration
Ethernet interfaces on different LPUs can be added to the same Eth-Trunk interface.
The peer interfaces directly connected to the local Eth-Trunk member interfaces must
also be bundled into an Eth-Trunk interface; otherwise, the two ends cannot
communicate.
When the member interfaces work at different rates, the interfaces with a smaller rate
may be congested, and packets may be lost on these interfaces.
After interfaces are added to an Eth-Trunk interface, MAC addresses are learned on the
Eth-Trunk interface but not the member interfaces.
----End
2.4.4 (Optional) Configuring the Load Balancing Mode
Context
Perform the following steps on the S5700to configure the Eth-Trunk load balancing mode.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
interface eth-trunk trunk-id
The Eth-Trunk interface view is displayed.
Step 3 Run:
load-balance { dst-ip | dst-mac | src-ip | src-mac | src-dst-ip | src-dst-mac }
The load balancing mode is configured for the Eth-Trunk interface.
The default load balancing mode of the S5700SI and S5700EI is src-dst-mac; the default load
balancing mode of the S5706 and S5700HI is src-dst-ip.
The S5700 supports the following load balancing modes:
l dst-ip: based on the destination IP address. In this mode, the system obtains the specified
three bits from each of the destination IP address and the TCP/UDP port number in outgoing
packets to perform the Exclusive-OR calculation, and then selects the outbound interface
from the Eth-Trunk table according to the calculation result.
l dst-mac: based on the destination MAC address. The system obtains the specified three bits
from each of the destination MAC address, VLAN ID, Ethernet type, and inbound interface
information to perform the Exclusive-OR calculation, and then selects the outbound interface
from the Eth-Trunk table according to the calculation result.
l src-ip: based on the source IP address. The system obtains the specified three bits from each
of the source IP address and the TCP or UDP port number in incoming packets to perform
the Exclusive-OR calculation, and then selects the outbound interface from the Eth-Trunk
table according to the calculation result.
l src-mac: based on the source MAC address. The system obtains the specified three bits from
each of the source MAC address, VLAN ID, Ethernet type, and inbound interface information
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
28
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
2 Link Aggregation Configuration
to perform the Exclusive-OR calculation, and then selects the outbound interface from the
Eth-Trunk table according to the calculation result.
l src-dst-ip: based on the Exclusive-OR result of the source IP address and destination IP
address. The system performs the Exclusive-OR calculation between the Exclusive-OR
results of the dip and dmac modes, and then selects the outbound interface from the EthTrunk table according to the calculation result.
l src-dst-mac: based on the Exclusive-OR result of the source MAC address and destination
MAC address. The system obtains three bits from each of the source MAC address,
destination MAC address, VLAN ID, Ethernet type, and inbound interface information to
perform the Exclusive-OR calculation, and then selects the outbound interface from the EthTrunk table according to the calculation result.
Member interfaces of an Eth-Trunk interface perform per-flow load balancing. The local end
and the remote end can use different load balancing modes. The load balancing mode on one
end does not affect load balancing on the other end.
----End
2.4.5 (Optional) Limiting the Number of Active Interfaces
Context
Perform the following steps on the switch to limit the number of active interfaces.
Procedure
l
Setting the maximum number of active interfaces
1.
Run:
system-view
The system view is displayed.
2.
Run:
interface eth-trunk trunk-id
The Eth-Trunk interface view is displayed.
3.
Run:
max active-linknumber link-number
The maximum number of active interfaces is set.
By default, the maximum number of active interfaces is 8.
You can set the maximum number (M) of active interfaces for an Eth-Trunk interface in
static LACP mode. The other member interfaces function as backup.
If you do not set the maximum number, a maximum of eight interfaces in the Eth-Trunk
interface can be active.
NOTE
l The maximum number of active interfaces must be larger than or equal to the minimum number
of active interfaces.
l The maximum number of active interfaces on the local switch can be different from that on the
remote switch. If the two values are different, the smaller one is used.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
29
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
2 Link Aggregation Configuration
Setting the minimum number of active interfaces
1.
Run:
system-view
The system view is displayed.
2.
Run:
interface eth-trunk trunk-id
The Eth-Trunk interface view is displayed.
3.
Run:
least active-linknumber link-number
The minimum number of active interfaces is set.
By default, the minimum number of active interfaces is 1.
You can set the minimum number of active interfaces for an Eth-Trunk interface in static
LACP mode. If the number of active interfaces is smaller than minimum number, the status
of the Eth-Trunk interface becomes Down.
NOTE
l The minimum number of active interfaces must be smaller than or equal to the maximum number
of active interfaces.
l The minimum number of active interfaces on the local switch can be different from that on the
remote switch. If the two values are different, the larger one is used.
----End
2.4.6 (Optional) Setting the System LACP Priority
Context
The system LACP priority determines which end of an Eth-Trunk link becomes the Actor.
Perform the following steps on the switch to set the system LACP priority.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
lacp priority priority
The system LACP priority is set.
A smaller LACP priority value indicates a higher priority. By default, the system LACP priority
is 32768.
The end with a smaller priority value functions as the Actor. If the two ends have the same
priority, the end with a smaller MAC address functions as the Actor.
----End
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
30
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
2 Link Aggregation Configuration
2.4.7 (Optional) Setting the LACP Priority for an Interface
Context
In an Eth-Trunk interface, interfaces with higher LACP priorities are selected as active
interfaces. Perform the following steps on the switch to set the LACP priority for an interface.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
interface interface-type interface-number
The interface view is displayed.
Step 3 Run:
lacp priority priority
The LACP priority is set for the interface.
By default, the interface LACP priority is 32768. A smaller priority value indicates a higher
LACP priority.
----End
2.4.8 (Optional) Enabling LACP Preemption and Setting the
Preemption Delay
Context
The LACP preemption function ensures that the interface with the highest LACP priority always
functions as an active interface. For example, when the interface with the highest priority
becomes inactive due to a failure, the LACP preemption function enables the interface to become
active again after it recovers. If the LACP preemption function is disabled, the interface cannot
become an active interface again.
The LACP preemption delay is the period during which an inactive interface waits before it
becomes active.
Perform the following steps on the switch to enable LACP preemption and set the preemption
delay.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
31
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
2 Link Aggregation Configuration
interface eth-trunk trunk-id
The Eth-Trunk interface view is displayed.
Step 3 Run:
lacp preempt enable
The LACP preemption function is enabled on the Eth-Trunk interface.
By default, the LACP preemption function is disabled.
NOTE
To ensure normal running of an Eth-Trunk interface, enable or disable LACP preemption on both ends of
the Eth-Trunk interface.
Step 4 Run:
lacp preempt delay delay-time
The LACP preemption delay is set.
By default, the LACP preemption delay is 30 seconds.
----End
2.4.9 (Optional) Setting the Timeout Interval for Receiving LACP
Packets
Context
Perform the following steps on the switch to set the timeout interval for receiving LACP packets.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
interface eth-trunk trunk-id
The Eth-Trunk interface view is displayed.
Step 3 Run:
lacp timeout { fast | slow }
The timeout interval for receiving LACP protocol packets is set.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
32
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
2 Link Aggregation Configuration
NOTE
l After you run the lacp timeout command, the local end informs the peer end of the timeout interval
through LACP packets. If the fast keyword is used, the interval for sending LACP packets is 1 second.
If the slow keyword is used, the interval for sending LACP packets is 30 seconds.
l The timeout interval for receiving LACP packets is three times the interval for sending LACP packets.
In other words, when the fast keyword is used, the timeout interval for receiving LACP packets is 3
seconds. When the slow keyword is used, the timeout interval for receiving LACP packets is 90 seconds.
l You can select different keywords on the two ends. However, it is recommended that you select the
same keyword on both ends to facilitate the maintenance.
----End
2.4.10 (Optional) Configuring the Load Balancing Mode for
Unknown Unicast Traffic
Context
Perform the following steps on the switch to configure the load balancing mode for unknown
unicast traffic.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
unknown-unicast load-balance { dmac | smac | smacxordmac }
The load balancing mode for unknown unicast traffic is configured.
NOTE
Only the S5700EI supports the unknown-unicast load-balance command.
----End
2.4.11 Checking the Configuration
Procedure
l
Run the display trunkmembership eth-trunk trunk-id command to check the member
interfaces of an Eth-Trunk interface.
Run the display eth-trunk [ trunk-id [interface interface-type interface-number ] ]
command to check information about an Eth-Trunk interfaced and its member interfaces.
----End
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
33
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
2 Link Aggregation Configuration
2.5 Configuring an E-Trunk
As an extension to the Link Aggregation Protocol (LACP) that implements link aggregation on
a single device, the Enhanced Trunk (E-Trunk) protocol implements link aggregation between
devices to improve link reliability between devices.
2.5.1 Establishing the Configuration Task
Before configuring an E-Trunk, familiarize yourself with the applicable environment, complete
the pre-configuration tasks, and obtain the data required for the configuration. This will help
you complete the configuration task quickly and accurately.
Applicable Environment
As shown in Figure 2-4, E-Trunk protects the links between a CE and two PEs in a dual-homing
networking. The CE connects to each of the PEs through an Eth-Trunk in static LACP mode.
The two Eth-Trunks form an E-Trunk to implement backup of link aggregation groups between
PE1 and PE2, enhancing the network reliability.
Figure 2-4 E-Trunk networking
nk
-Tru
h
t
E
PE1
E-Trunk1
Network
CE
Eth
-Tru
nk 2
PE2
Pre-configuration Tasks
Before configuring an E-Trunk, complete the following tasks:
l
Connecting physical links between devices correctly
Configuring Eth-Trunk interfaces in static LACP mode
Data Preparation
To configure an E-Trunk, you need the following data.
Issue 02 (2011-11-21)
No.
Data
LACP system ID and priority
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
34
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
2 Link Aggregation Configuration
No.
Data
ID and priority of the E-Trunk
Interface numbers and working modes of the Eth-Trunk interfaces
Local and peer IP addresses
Encrypted password
Interval for sending hello packets and time multiplier for detecting hello packets
2.5.2 Setting the LACP System ID and LACP Priority of an E-Trunk
In an E-Trunk, the two PEs must be configured with the same LACP system ID and priority so
that the CE considers the two PEs as one device.
Context
Perform the following steps on the E-Trunk member devices.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
lacp e-trunk system-id mac-address
The LACP system ID is set for the E-Trunk.
By default, the MAC address of the Ethernet interface on the MPU is used as the LACP system
ID.
The master and backup devices in an E-Trunk must use the same LACP system ID.
Step 3 Run:
lacp e-trunk priority priority
The LACP priority of the E-Trunk member is set.
By default, the LACP priority of an E-Trunk member is 32768.
The master and backup devices in an E-Trunk must use the same LACP priority.
----End
2.5.3 Creating an E-Trunk and Setting the E-Trunk Priority
The E-Trunk priority determines whether an E-Trunk member device is the master device or the
backup device.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
35
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
2 Link Aggregation Configuration
Context
Perform the following steps on the E-Trunk member devices.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
e-trunk e-trunk-id
An E-Trunk is created, and the E-Trunk view is displayed.
If the specified E-Trunk already exists, the E-Trunk view is displayed directly.
The member devices in an E-Trunk must be configured with the same E-Trunk ID.
A maximum of 16 E-Trunks can be created on a device.
Step 3 Run:
priority priority
The E-Trunk priority is set.
The E-Trunk priority is used for master/backup negotiation between two devices. The device
with a higher priority is the master. A smaller priority value indicates a higher priority.
If the two devices have the same priority, the device with the smaller system ID is the master.
By default, the E-Trunk priority of a member device is 100.
----End
2.5.4 Configuring Local and Peer IP Addresses of an E-Trunk
E-Trunk packets are sent with the local IP address and port configured on the local device. When
you change the local or peer IP address on a device, you must change the corresponding address
on the peer device. Otherwise, LACP packets are discarded.
Context
Perform the following steps on the E-Trunk member devices of the
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
e-trunk e-trunk-id
The E-Trunk view is displayed.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
36
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
2 Link Aggregation Configuration
Step 3 Run:
peer-address peer-ip-address source-address source-ip-address
The local and peer IP addresses of the E-Trunk are configured.
The peer IP address configured on the local device must be the same as the local IP address of
the peer device. For example, an E-Trunk is set up between device A and device B. On device
A, the peer IP address is 2.2.2.2 and the local IP address is 1.1.1.1. On device B, the peer IP
address is 1.1.1.1 and the local IP address is 2.2.2.2.
----End
2.5.5 Binding an E-Trunk to a BFD Session
The local device in an E-Trunk can detect faults of the peer device when receiving LACP packets
times out. However, the fault detection is low. The Bidirectional Fast Detection (BFD) protocol
can quickly detect faults on the peer device. You can create a BFD session and bind the E-Trunk
to the BFD session to check whether the route to the peer is reachable. The E-Trunk can detect
faults reported by the BFD session and handles the faults quickly.
Perform the following steps on the E-Trunk member devices.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
e-trunk e-trunk-id
The E-Trunk view is displayed.
Step 3 Run:
e-trunk track bfd-session session-id
The E-Trunk is bound to a BFD session.
BFD sessions are used to fast detect faults of link between the two E-Trunk member devices.
NOTE
The S5700SI does not support the e-trunk track bfd-session command.
----End
2.5.6 Adding an Eth-Trunk Interface to an E-Trunk
After you configure an E-Trunk, add Eth-Trunk interfaces to the E-Trunk. Then the E-Trunk
implements backup of link aggregation groups between the two member devices to enhance
network reliability.
Context
Perform the following steps on the E-Trunk member devices.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
37
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
2 Link Aggregation Configuration
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
interface eth-trunk trunk-id
The Eth-Trunk interface view is displayed.
Only Eth-Trunk interfaces in static LACP mode can be added to an E-Trunk.
Step 3 Run:
e-trunk e-trunk-id
The Eth-Trunk interface is added to an E-Trunk.
An Eth-Trunk interface can be added to only one E-Trunk.
One two E-Trunk member devices, the IDs of the Eth-Trunk interfaces added to the E-Trunk
must be the same. For example, if you add Eth-Trunk 1 and Eth-Trunk 2 to E-Trunk 1 on device
A, you must also add Eth-Trunk 1 and Eth-Trunk 2 to E-Trunk 1 on device B.
----End
2.5.7 (Optional) Configuring the Working Mode of an Eth-Trunk
Interface in an E-Trunk
You can configure the working mode for only the Eth-Trunk interfaces that have been added to
an E-Trunk. The working mode of an Eth-Trunk interface can be automatic, forced master, or
forced backup.
Context
Perform the following steps on the member devices of the E-Trunk.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
interface eth-trunk trunk-id
The Eth-Trunk interface view is displayed.
Only Eth-Trunk interfaces in static LACP mode can be added to an E-Trunk.
Step 3 Run:
e-trunk mode { auto | force-master | force-backup }
The working mode of the Eth-Trunk interface in the E-Trunk is configured.
By default, an Eth-Trunk interface works in automatic mode in an E-Trunk.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
38
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
2 Link Aggregation Configuration
The e-trunk mode command is valid only for Eth-Trunk interface in an E-Trunk. When the EthTrunk interface is deleted from the E-Trunk, the configuration is canceled.
When the Eth-Trunk interface works in automatic mode, its master/backup status is determined
by the E-Trunk status of the local device and fault information of the peer Eth-Trunk.
l If the local E-Trunk is the master, the local Eth-Trunk interface works in master state.
l If the local E-Trunk is the backup and the peer member Eth-Trunk interface fails, the local
Eth-Trunk interface works in master state. When the local Eth-Trunk receives the message
informing that the peer Eth-Trunk interface recovers, the local Eth-Trunk interface becomes
the backup.
NOTE
If you change the interval for sending hello packets or timeout interval for waiting hello packets when the ETrunk is working, the E-Trunk status alternates between the master and the backup. Therefore, it is recommended
that you set the working mode of a member Eth-Trunk interface to forcible master/backup before changing the
hello packet sending interval or timeout. After new configurations take effect, restore the working mode to
automatic.
----End
2.5.8 (Optional) Setting the Password for Encrypting Packets
You can set a password for encryption packets transmitted on an E-Trunk to enhance system
security. The two member devices of an E-Trunk must use the same password.
Context
You can set a password in plain text or cipher text.
l
The plain text password is displayed in plain text in the configuration file.
The cipher text password is displayed as unidentifiable characters.
Perform the following steps on the E-Trunk member devices.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
e-trunk e-trunk-id
The E-Trunk view is displayed.
Step 3 Run:
security-key { simple simple-key | cipher cipher-key }
The password for encrypting packets is configured.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
39
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
2 Link Aggregation Configuration
CAUTION
If you select simple, the password is saved in plain text in the configuration file. Lower-level
users can view the configuration file to easily obtain the password, bringing a security risk.
Therefore, it is recommended that you select cipher to save the password in cipher text.
----End
2.5.9 (Optional) Setting the Timeout Interval of Hello Packets
If the backup device in an E-Trunk does not receive any hello packet from the master device
within the timeout interval, the back device becomes the master. The timeout interval is specified
in the hello packets sent from the peer device but not the timeout interval set on the local device.
Context
Perform the following steps on the E-Trunk member devices.
NOTE
If you change the interval for sending hello packets or timeout interval for waiting hello packets when the ETrunk is working, the E-Trunk status alternates between the master and the backup. Therefore, it is recommended
that you set the working mode of a member Eth-Trunk interface to forcible master/backup before changing the
hello packet sending interval or timeout. After new configurations take effect, restore the working mode to
automatic.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
e-trunk e-trunk-id
The E-Trunk view is displayed.
Step 3 Run:
timer hello hello-times
The interval for sending hello packets is set.
By default, the value of hello-times is 10. Because the unit is 100 ms, the interval for sending
hello packets is 1s.
Step 4 Run:
timer hold-on-failure multiplier multiplier
The time multiplier for detecting hello packets is set.
The peer device checks the timeout interval in the received packet to check whether the local
device times out. If the peer device is the backup and does not receive hello packets from the
local device within the timeout interval, the peer device becomes the master.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
40
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
2 Link Aggregation Configuration
Timeout interval = Interval for sending hello packets x Time multiplier. The default time
multiplier is 20. It is recommended that you set the time multiplier to at least 3.
----End
2.5.10 (Optional) Setting the Revertive Switching Delay
After the revertive switching delay is set, the local Eth-Trunk interface can become the master
again until the delay timer expires. This delays the revertive switching of service traffic to ensure
uninterrupted forwarding.
Context
If an E-Trunk works with other services, the member Eth-Trunk interface may be restored earlier
than other services after the master device recovers from a fault. If traffic is immediately switched
back to the master device, service traffic will be interrupted.
Setting the revertive switching delay prevents this problem. After the revertive switching delay
is set, the local Eth-Trunk interface becomes Up only after the delay timer times out. Then the
local device becomes the master again.
Perform the following steps on the E-Trunk member devices.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
e-trunk e-trunk-id
The E-Trunk view is displayed.
Step 3 Run:
timer revert delay delay-value
The revertive switching delay is set.
By default, the revertive switching delay is 120 seconds.
----End
2.5.11 Checking the Configuration
After configuring an E-Trunk, you can view information about the E-Trunk, including its
priority, system ID, local IP address, peer IP address, revertive switching delay, master/backup
status, and cause of status change.
Procedure
l
Run the display e-trunk e-trunk-id command to view information about the E-Trunk.
----End
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
41
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
2 Link Aggregation Configuration
2.6 Maintaining Link Aggregation
This section describes how to clear the statistics of received and sent LACP packets, debug the
link aggregation group, and monitor the running status of the link aggregation group.
2.6.1 Clearing LACP Packet Statistics
Context
CAUTION
The LACP packet statistics cannot be restored after you clear them.
Procedure
l
Run the reset lacp statistics eth-trunk [ trunk-id ] command to clear statistics about LACP
packets received and sent.
----End
2.6.2 Debugging a Link Aggregation Group
Context
CAUTION
Debugging affects the performance of the system. Therefore, run the undo debugging all
command to disable debugging immediately after the debugging is complete.
When a running fault occurs in the link aggregation group, run the following debugging
commands in the user view to check the debugging information, and locate and analyze the fault.
Procedure
l
Run the debugging trunk error command to enable the debugging of Eth-Trunk errors.
Run the debugging trunk event command to enable the debugging of Eth-Trunk events.
Run the debugging trunk lacp-pdu command to enable the debugging of LACP packets.
Run the debugging trunk lagmsg command to enable the debugging of LACP protocol
messages.
Run the debugging trunk msg command to enable the debugging of Eth-Trunk messages.
Run the debugging trunk state-machine command to enable the debugging of Eth-Trunk
status machine.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
42
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
2 Link Aggregation Configuration
Run the debugging trunk updown command to enable the debugging of Eth-Trunk Up
and Down messages.
Run the debugging trunk command to enable the debugging of Eth-Trunk messages.
----End
2.6.3 Monitoring the Operating Status of a Link Aggregation Group
Context
During daily maintenance, run the following commands in any view to check the operating status
of link aggregation groups.
Procedure
l
Run the display eth-trunk [ trunk-id [ interface interface-type interface-number ] ]
command to check the status of a link aggregation group.
Run the display lacp statistics eth-trunk [ trunk-id [ interface interface-type interfacenumber ] ] command to check the statistics about LACP packets sent and received.
Run the display trunkmembership eth-trunk trunk-id command to check the member
interfaces of an Eth-Trunk interface.
----End
2.7 Configuration Examples
This section provides several configuration examples of link aggregation in manual load
balancing mode and static LACP mode.
2.7.1 Example for Configuring Link Aggregation in Manual Load
Balancing Mode
Networking Requirements
As shown in Figure 2-5, the Switch is connected to the SwitchA through an Eth-Trunk link.
The link between the Switch and SwitchA must ensure high reliability.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
43
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
2 Link Aggregation Configuration
Figure 2-5 Link aggregation in manual load balancing mode
SwitchA
Eth-Trunk 1
Eth-Trunk
Eth-Trunk 1
GE0/0/3
GE0/0/4
Switch
GE0/0/1
VLAN 100-150
LAN Switch
GE0/0/2
VLAN 151-200
LAN Switch
Configuration Roadmap
The configuration roadmap is as follows:
1.
Create an Eth-Trunk.
2.
Add member interfaces to the Eth-Trunk.
Data Preparation
To complete the configuration, you need the following data:
l
Number of the Eth-Trunk
Types and numbers of the member interfaces in the Eth-Trunk
Procedure
Step 1 Create an Eth-Trunk.
# Create Eth-Trunk 1.
<Quidway> system-view
[Quidway] sysname Switch
[Switch] interface eth-trunk 1
[Switch-Eth-Trunk1] quit
Step 2 Add member interfaces to the Eth-Trunk.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
44
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
2 Link Aggregation Configuration
# Add GE 0/0/3 to Eth-Trunk 1.
[Switch] interface gigabitethernet 0/0/3
[Switch-GigabitEthernet0/0/3] eth-trunk 1
[Switch-GigabitEthernet0/0/3] quit
# Add GE 0/0/4 to Eth-Trunk 1.
[Switch] interface gigabitethernet 0/0/4
[Switch-GigabitEthernet0/0/4] eth-trunk 1
[Switch-GigabitEthernet0/0/4] quit
Step 3 Configure Eth-Trunk 1.
# Configure Eth-Trunk 1 to allow packets of VLANs 100 to 200 to pass through.
[Switch] interface eth-trunk 1
[Switch-Eth-Trunk1] port link-type trunk
[Switch-Eth-Trunk1] port trunk allow-pass vlan 100 to 200
[Switch-Eth-Trunk1] quit
Step 4 Verify the configuration.
Run the display trunkmembership command in any view to check whether Eth-Trunk 1 is
created and whether member interfaces are added.
[Switch] display trunkmembership eth-trunk 1
Trunk ID: 1
used status: VALID
TYPE: ethernet
Working Mode : Normal
Number Of Ports in Trunk = 2
Number Of UP Ports in Trunk = 2
operate status: up
Interface GigabitEthernet0/0/3, valid, operate up, weight=1,
Interface GigabitEthernet0/0/4, valid, operate up, weight=1,
# Display the configuration of Eth-Trunk 1.
[Switch] display eth-trunk 1
Eth-Trunk1's state information is:
WorkingMode: NORMAL
Hash arithmetic: According to SA-XOR-DA
Least Active-linknumber: 1 Max Bandwidth-affected-linknumber: 8
Operate status: up
Number Of Up Port In Trunk: 2
-------------------------------------------------------------------------------PortName
Status
Weight
GigabitEthernet0/0/3
Up
1
GigabitEthernet0/0/4
Up
1
The preceding information indicates that Eth-Trunk 1 consists of member interfaces GE 0/0/3
and GE 0/0/4. The member interfaces are both in Up state.
----End
Configuration Files
Configuration file of the Switch
#
sysname Switch
#
interface Eth-Trunk1
port link-type trunk
port trunk allow-pass vlan 100 to 200
#
interface GigabitEthernet0/0/3
eth-trunk 1
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
45
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
2 Link Aggregation Configuration
#
interface GigabitEthernet0/0/4
eth-trunk 1
#
return
2.7.2 Example for Configuring Link Aggregation in Static LACP
Mode
Networking Requirements
To improve bandwidth and connection reliability, configure a link aggregation group on two
directly connected Switches, as shown in Figure 2-6. The requirements are as follows:
l
M active links can implement load balancing.
N links between two Switches can carry out redundancy backup. When a fault occurs on
an active link, the backup link replaces the faulty link to maintain reliable data transmission.
Figure 2-6 Link aggregation in static LACP mode
Eth-Trunk 1
GE 0/0/1
GE 0/0/2
GE 0/0/3
Eth-Trunk
Eth-Trunk 1
GE 0/0/1
GE 0/0/2
GE 0/0/3
SwitchA
Active link
Backup link
SwitchB
Configuration Roadmap
The configuration roadmap is as follows:
1.
Create an Eth-Trunk interface on the Switch and configure the Eth-Trunk interface to work
in static LACP mode.
2.
Add member interfaces to the Eth-Trunk interface.
3.
Set the system priority and determine the Actor.
4.
Set the upper threshold of the active interfaces.
5.
Set the priority of the interface and determine the active link.
Data Preparation
To complete the configuration, you need the following data:
l
Number of the link aggregation group on the Switches
System priority of SwitchA
Upper threshold of active interfaces
LACP priority of the active interface
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
46
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
2 Link Aggregation Configuration
Procedure
Step 1 Create Eth-Trunk 1 and set the load balancing mode of the Eth-Trunk to static LACP mode.
# Configure SwitchA.
<Quidway> system-view
[Quidway] sysname SwitchA
[SwitchA] interface eth-trunk 1
[SwitchA-Eth-Trunk1] bpdu enable
[SwitchA-Eth-Trunk1] mode lacp-static
[SwitchA-Eth-Trunk1] quit
# Configure SwitchB.
<Quidway> system-view
[Quidway] sysname SwitchB
[SwitchB] interface eth-trunk 1
[SwitchB-Eth-Trunk1] bpdu enable
[SwitchB-Eth-Trunk1] mode lacp-static
[SwitchB-Eth-Trunk1] quit
Step 2 Add member interfaces to the Eth-Trunk.
# Configure SwitchA.
[SwitchA] interface gigabitethernet 0/0/1
[SwitchA-GigabitEthernet0/0/1] eth-trunk 1
[SwitchA-GigabitEthernet0/0/1] quit
[SwitchA] interface gigabitethernet 0/0/2
[SwitchA-GigabitEthernet0/0/2] eth-trunk 1
[SwitchA-GigabitEthernet0/0/2] quit
[SwitchA] interface gigabitethernet 0/0/3
[SwitchA-GigabitEthernet0/0/3] eth-trunk 1
[SwitchA-GigabitEthernet0/0/3] quit
# Configure SwitchB.
[SwitchB] interface gigabitethernet 0/0/1
[SwitchB-GigabitEthernet0/0/1] eth-trunk 1
[SwitchB-GigabitEthernet0/0/1] quit
[SwitchB] interface gigabitethernet 0/0/2
[SwitchB-GigabitEthernet0/0/2] eth-trunk 1
[SwitchB-GigabitEthernet0/0/2] quit
[SwitchB] interface gigabitethernet 0/0/3
[SwitchB-GigabitEthernet0/0/3] eth-trunk 1
[SwitchB-GigabitEthernet0/0/3] quit
Step 3 Set the system priority on SwitchA to 100 so that SwitchA becomes the Actor.
[SwitchA] lacp priority 100
Step 4 Set the upper threshold M of active interfaces on SwitchA to 2.
[SwitchA] interface eth-trunk 1
[SwitchA-Eth-Trunk1] max active-linknumber 2
[SwitchA-Eth-Trunk1] quit
Step 5 Set the priority of the interface and determine active links on SwitchA.
[SwitchA] interface gigabitethernet
[SwitchA-GigabitEthernet0/0/1] lacp
[SwitchA-GigabitEthernet0/0/1] quit
[SwitchA] interface gigabitethernet
[SwitchA-GigabitEthernet0/0/2] lacp
[SwitchA-GigabitEthernet0/0/2] quit
0/0/1
priority 100
0/0/2
priority 100
Step 6 Verify the configuration.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
47
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
2 Link Aggregation Configuration
# Check information about the Eth-Trunk of the Switches and check whether the negotiation is
successful on the link.
[SwitchA] display eth-trunk 1
Eth-Trunk1's state information is:
Local:
LAG ID: 1
WorkingMode: STATIC
Preempt Delay: Disabled
Hash arithmetic: According to SA-XOR-DA
System Priority: 100
System ID: 00e0-fca8-0417
Least Active-linknumber: 1 Max Active-linknumber: 2
Operate status: Up
Number Of Up Port In Trunk: 2
-----------------------------------------------------------------------------ActorPortName
Status
PortType PortPri
PortNo PortKey
PortState
Weight
GigabitEthernet0/0/1
Selected 1GE
100
6145
2865
11111100
1
GigabitEthernet0/0/2
Selected 1GE
100
6146
2865
11111100
1
GigabitEthernet0/0/3
Unselect 1GE
32768
6147
2865
11100000
1
Partner:
-----------------------------------------------------------------------------PartnerPortName
SysPri
SystemID
PortPri PortNo PortKey
PortState
GigabitEthernet0/0/1
32768 00e0-fca6-7f85 32768
6145
2609
11111100
GigabitEthernet0/0/2
32768 00e0-fca6-7f85 32768
6146
2609
11111100
GigabitEthernet0/0/3
32768 00e0-fca6-7f85 32768
6147
2609
11110000
[SwitchB] display eth-trunk 1
Eth-Trunk1's state information is:
Local:
LAG ID: 1
WorkingMode: STATIC
Preempt Delay: Disabled
Hash arithmetic: According to SA-XOR-DA
System Priority: 32768
System ID: 00e0-fca6-7f85
Least Active-linknumber: 1
Max Active-linknumber: 8
Operate status: Up
Number Of Up Port In Trunk: 2
-----------------------------------------------------------------------------ActorPortName
Status
PortType PortPri
PortNo PortKey
PortState
Weight
GigabitEthernet0/0/1 Selected 1GE
32768
6145
2609
11111100
1
GigabitEthernet0/0/2 Selected 1GE
32768
6146
2609
11111100
1
GigabitEthernet0/0/3 Unselect 1GE
32768
6147
2609
11100000
1
Partner:
-----------------------------------------------------------------------------PartnerPortName
SysPri
SystemID
PortPri PortNo PortKey
PortState
GigabitEthernet0/0/1 100
00e0-fca8-0417 100
6145
2865
11111100
GigabitEthernet0/0/2 100
00e0-fca8-0417 100
6146
2865
11111100
GigabitEthernet0/0/3 100
00e0-fca8-0417 32768
6147
2865
11110000
The preceding information shows that the system priority of SwitchA is 100, which is higher
than the system priority of SwitchB. Member interfaces GE0/0/1 and GE0/0/2 become the active
interfaces and are in Selected state. Interface GE0/0/3 is in Unselect state. M active links work
in load balancing mode and N links are the backup links.
----End
Configuration Files
l
Configuration file of SwitchA
#
sysname SwitchA
#
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
48
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
2 Link Aggregation Configuration
lacp priority 100
#
interface Eth-Trunk1
mode lacp-static
max active-linknumber 2
#
interface GigabitEthernet0/0/1
eth-trunk 1
lacp priority 100
#
interface GigabitEthernet0/0/2
eth-trunk 1
lacp priority 100
#
interface GigabitEthernet0/0/3
eth-trunk 1
#
return
Configuration file of SwitchB
#
sysname SwitchB
#
interface Eth-Trunk1
mode lacp-static
#
interface GigabitEthernet0/0/1
eth-trunk 1
#
interface GigabitEthernet0/0/2
eth-trunk 1
#
interface GigabitEthernet0/0/3
eth-trunk 1
#
return
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
49
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
VLAN Configuration
About This Chapter
Virtual Local Area Networks (VLANs) have advantages of broadcast domain isolation, security
enhancement, flexible networking, and good extensibility.
3.1 Introduction
The VLAN technology is important for forwarding on Layer 2 networks. This section describes
the background, functions, and advantages of the VLAN technology.
3.2 VLAN Features Supported by the S5700
This section describes VLAN features that the S5700 supports.
3.3 Dividing a LAN into VLANs
A LAN can be divided into several VLANs and users in each VLAN can communicate with
each other. Currently, the S5700 supports several VLAN division modes. You can choose one
of them as required.
3.4 Creating a VLANIF Interface
VLANIF interfaces are Layer 3 logical interfaces. After creating VLANIF interfaces on Layer
2 devices, you can configure Layer 3 features on these interfaces.
3.5 Configuring Inter-VLAN Communication
Configuring inter-VLAN communication allows users in different VLANs to communicate with
each other. Currently, the S5700 supports several inter-VLAN communication schemes. Choose
one of them as required.
3.6 Configuring VLAN Aggregation to Save IP Addresses
VLAN aggregation prevents the waste of IP addresses and implements inter-VLAN
communication.
3.7 Configuring a MUX VLAN to Separate Layer 2 Traffic
Configuring a MUX VLAN allows users in different VLANs to communicate with each other,
and separates users in a certain VLAN.
3.8 Configuring a Voice VLAN to Transmit Voice Data
A voice VLAN is used to transmit voice data.
3.9 Configuring an mVLAN to Implement Integrated Management
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
50
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
Configuring an mVLAN allows users to use the IP address of the VLANIF interface
corresponding to the mVLAN to log in to a management switch to manage devices attached to
the switch.
3.10 Maintaining VLAN
A command of clearing statistics helps to locate the faults in a VLAN.
3.11 Configuration Examples
This section provides VLAN configuration examples in various usage scenarios.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
51
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
3.1 Introduction
The VLAN technology is important for forwarding on Layer 2 networks. This section describes
the background, functions, and advantages of the VLAN technology.
Overview of VLAN
The Ethernet technology is for sharing communication mediums and data based on the Carrier
Sense Multiple Access/Collision Detect (CSMA/CD). If there are a large number of PCs on an
Ethernet network, collision becomes a serious problem and can lead to broadcast storms. As a
result, network performance deteriorates. This can even cause the Ethernet network to become
unavailable. Switches can be used to interconnect local area networks (LANs). Switches forward
information received by inbound ports to specified outbound ports, thereby preventing access
collision in a shared medium. If no specified outbound port is found for information received
by an inbound port, the switch will forward the information from all ports except the inbound
port. This forms a broadcast domain.
To prevent broadcast domains from being too broad and causing problems, you can divide a
network into segments. In this manner, a large broadcast domain is divided into multiple small
broadcast domains to confine the possible scope of broadcast packets. Routers can be deployed
at the network layer to separate broadcast domains, but this method has disadvantages, which
include: complex network planning, inflexible networking, and high levels of expenditure. The
Virtual Local Area Network (VLAN) technology can divide a large Layer 2 network into
broadcast domains to prevent broadcast storms and protect network security.
Definition of VLAN
The VLAN technology is used to divide a physical LAN into multiple logical broadcast domains,
each of which is called a VLAN. Each VLAN contains a group of PCs that have the same
requirements. A VLAN has the same attributes as a LAN. PCs of a VLAN can be placed on
different LAN segments. If two PCs are located on one LAN segment but belong to different
VLANs, they do not broadcast packets to each other. With VLAN, the broadcast traffic volume
is reduced; fewer devices are required; network management is simplified; and network security
is improved.
Figure 3-1 shows a typical VLAN application. Three switches are placed in different locations,
for example, different stories of an office building. The VLAN technology allows enterprises to
share LAN facilities and ensures information security for each enterprise network.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
52
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
Figure 3-1 Schematic diagram for a typical VLAN application
Router
Switch1
Switch2
Switch3
VLAN-A
VLAN-B
VLAN-C
This application shows the following VLAN advantages:
l
Broadcast domains are confined. A broadcast domain is confined to a VLAN. This saves
bandwidth and improves network processing capabilities.
Network security is enhanced. Packets from different VLANs are separately transmitted.
PCs in one VLAN cannot directly communicate with PCs in another VLAN.
Network robustness is improved. A fault in a VLAN does not affect PCs in other VLANs.
Virtual groups are set up flexibly. With the VLAN technology, PCs in different
geographical areas can be grouped together. This facilitates network construction and
maintenance.
Basic VLAN Concepts and Principles
l
802.1Q and VLAN frame format
A conventional Ethernet frame is encapsulated with the Length/Type field for an upperlayer protocol following the Destination address and Source address fields, as shown in
Figure 3-2.
Figure 3-2 Conventional Ethernet frame format
6bytes
Destination
address
6bytes
2bytes
46-1500bytes 4bytes
Source
Data
FCS
Length/Type
address
IEEE 802.1Q is an Ethernet networking standard for a specified Ethernet frame format. It
adds a 32-bit field between the Source address and the Length/Type fields of the original
frame, as shown in Figure 3-3.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
53
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
Figure 3-3 802.1Q frame format
6bytes
6bytes
4bytes
Destination Source 802.1Q
address
address
Tag
TPID
2bytes
PRI
2bytes 42-1500bytes 4bytes
Length/
Type
Data
FCS
CFI VID
3bits 1bit 12bits
Tag Protocol Identifier (TPID): a 16-bit field set to a value of 0x8100 in order to identify
the frame as an IEEE 802.1Q-tagged frame. If an 802.1Q-incapable device receives an
802.1Q frame, it will discard the frame.
Priority (PRI): a 3-bit field which indicates the frame priority. The value ranges from 0
to 7. The greater the value, the higher the priority. These values can be used to prioritize
different classes of traffic to ensure that frames with high priorities are transmitted first
when traffic is heavy.
Canonical Format Indicator (CFI): a 1-bit field. If the value of this field is 1, the MAC
address is in the non-canonical format. If the value is 0, the MAC address is in the
canonical format. CFI is used to ensure compatibility between Ethernet networks and
Token Ring networks. It is always set to zero for Ethernet switches.
VLAN Identifier (VID): a 12-bit field specifying the VLAN to which the frame belongs.
On the S5700, VLAN IDs range from 0 to 4095. The values 0 and 4095 are reserved,
and therefore VLAN IDs range from 1 to 4094.
Each frame sent by an 802.1Q-capable switch carries a VLAN ID. On a VLAN, Ethernet
frames are classified into the following types:
Tagged frames: frames with 32-bits 802.1Q tags.
Untagged frames: frames without 32-bits 802.1Q tags.
l
VLAN division methods
Table 3-1 shows VLAN division methods.
Table 3-1 VLAN division methods
VLAN
Division
Method
Definition
Port-based
VLAN division
VLANs are configured based on ports on a switch. For example, ports
1 to 4 on a switch are added to VLAN 2; ports 5 to 8 are added to
VLAN 3.
Ports on different Ethernet switches can be added to one VLAN. For
example, ports 1 to 4 on switch A and ports 3 to 6 on switch B can
be added to the same VLAN.
Each switch maintains a VLAN mapping table that records mappings
between local ports and VLANs.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
54
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
VLAN
Division
Method
Definition
MAC addressbased VLAN
division
PCs are added to VLANs based on their MAC addresses.
IP subnet-based
VLAN division
VLANs are configured based on IP addresses of PCs. PCs belonging
to one IP subnet are added to the same VLAN.
A switch maintains a VLAN mapping table that records mappings
between MAC addresses and VLANs.
A switch maintains a VLAN mapping table that records mappings
between IP subnets and VLANs.
Protocol-based
VLAN division
VLANs are configured based on the Length/Type fields in Layer 2
frames. Currently, IPv4, IPv6, IPX, or AppleTalk can be specified in
the Length/Type field of a Layer 2 frame to indicate the running
network protocol.
A switch maintains a VLAN mapping table that records mappings
between protocols and VLANs.
Policy-based
VLAN division
PCs are added to VLANs based on their MAC and IP addresses.
A switch maintains a VLAN mapping table that records mappings
between MAC addresses, IP addresses, interfaces, and VLANs.
Type of VLAN links
Figure 3-4 Schematic diagram for VLAN links
VLAN3
PC3
VLAN3
PC4
Access link
3
3
2
Trunk link
CE1
PC1
VLAN2
3
2
Trunk link
PE
2
Access link
CE2
PC2
VLAN2
As shown in Figure 3-4, there are the following types of VLAN links:
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
55
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
Access link: connects a PC to a switch. Generally, a PC does not know which VLAN
it belongs to, and PC hardware cannot distinguish frames with VLAN tags. Therefore,
PCs send and receive only untagged frames.
Trunk link: connects a switch to another switch or to a router. Data of different VLANs
are transmitted along a trunk link. The two ends of a trunk link must be able to distinguish
frames with VLAN tags. Therefore, only tagged frames are transmitted along trunk
links.
l
Port types
Table 3-2 lists VLAN port types.
Table 3-2 Port types
Port
Type
Method of
Processing
Received
Untagged Frames
Method of
Processing
Received
Tagged
Frames
Method of
Sending
Frames
Application
Access
port
Accepts an untagged
frame and adds a tag
with the default
VLAN ID to the
frame.
l Accepts a
tagged
frame if the
VLAN ID
carried in
the frame is
the same as
the default
VLAN ID.
Removes the tag
from a frame and
sends the frame.
An access port
connects a
switch to a PC
and can be
added to only
one VLAN.
l Discards a
tagged
frame if the
VLAN ID
carried in
the frame is
different
from the
default
VLAN ID.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
56
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
Port
Type
Method of
Processing
Received
Untagged Frames
Method of
Processing
Received
Tagged
Frames
Method of
Sending
Frames
Application
Trunk
port
l Adds a tag with
the default
VLAN ID to an
untagged frame
and accepts the
frame if the port
permits the
default VLAN
ID.
l Accepts a
tagged
frame if the
port permits
the VLAN
ID carried in
the frame.
l Removes the
tag from a
received
frame and
sends the
frame if the
VLAN ID
carried in the
frame is the
same as the
default
VLAN ID
and
permitted by
the port.
A trunk port
can be added to
multiple
VLANs to send
and receive
frames for these
VLANs. A
trunk port
connects a
switch to
another switch
or to a router.
l Adds a tag with
the default
VLAN ID to an
untagged frame
and discards the
frame if the port
denies the default
VLAN ID.
Hybrid
port
Issue 02 (2011-11-21)
3 VLAN Configuration
l Discards a
tagged
frame if the
port denies
the VLAN
ID carried in
the frame.
l Directly
sends a
received
frame if the
VLAN ID
carried in the
frame is
different
from the
default
VLAN ID
but permitted
by the port.
Sends a received
frame if the port
permits the
VLAN ID
carried in the
frame. A
specified
command can be
used to
determine
whether a hybrid
port sends
frames with or
without tags.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
A hybrid port
can be added to
multiple
VLANs to send
and receive
frames for these
VLANs. A
hybrid port can
connect a
switch to a PC
or connect a
network device
to another
network
device.
57
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
Port
Type
Method of
Processing
Received
Untagged Frames
Method of
Processing
Received
Tagged
Frames
Method of
Sending
Frames
Application
QinQ
port
QinQ ports are enabled with the IEEE 802.1QinQ protocol. A QinQ port adds
a tag to a single-tagged frame, and thus supports a maximum of 4094 x 4094
VLAN tags, which meets the requirement of a Networkfor the number of
VLANs.
Each access, trunk, hybrid, or QinQ port can be configured with a default VLAN, namely,
the port default VLAN ID (PVID) to specify the VLAN to which the port belongs.
The PVID of an access port indicates the VLAN to which the port belongs.
As a trunk or hybrid port can be added to multiple VLANs, the port must be configured
with PVIDs.
By default, a port is added to VLAN 1.
l
Principle for data switching in a VLAN
Use the network shown in Figure 3-4 as an example. If PC 1 in VLAN 2 intends to send
data to PC 2, the data is forwarded as follows:
1.
An access port on CE 1 receives an untagged frame from PC 1 and adds a PVID
(VLAN 2) to the frame. CE 1 searches the MAC address table for an outbound port.
Then the frame is transmitted from the outbound port.
NOTE
Assume that VLANs are configured based on MAC addresses. After an access port on CE 1
receives an untagged frame from PC 1, the port checks the VLAN mapping table for a VLAN
ID corresponding to the source MAC address, and adds a tag with the obtained VLAN ID to
the frame.
2.
After the trunk port on CE 1 and PE receives the frame, the port checks whether the
VLAN ID carried in the frame is the same as that configured on the port. If the VLAN
ID has been configured on the port, the port transparently transmits the frame to CE
2. If the VLAN ID is not configured on the port, the port discards the frame.
3.
After a trunk port on CE 2 receives the frame, the system searches the MAC address
table for an outbound port which connects CE 2 to PC 2.
4.
After the frame is sent to the access port connecting CE 2 to PC 2, the port checks that
the VLAN ID carried in the frame is the same as that configured on the port. The port
then removes the tag from the frame and sends the untagged frame to PC 2.
VLANIF interface
A VLANIF interface is a Layer 3 logical interface, which can be configured on either a
Layer 3 switch or a router.
Layer 3 switching combines routing and switching techniques to implement routing on a
switch, thus improving the overall network performance. After sending the first data flow,
a Layer 3 switch generates mappings between MAC addresses and IP addresses. To send
the same data flow, the switch directly sends the data flow at Layer 2 but not Layer 3 based
on this mapping table.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
58
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
To allow that new data flows are correctly forwarded based on the routing table, be sure
that the routing table's routing entries are correct. Therefore, VLANIF interfaces and
routing protocols must be configured on Layer 3 switches for reachable Layer 3 routes.
NOTE
Key points are summarized as follows:
l
A PC does not need to know the VLAN to which it belongs. It sends only untagged frames.
After receiving an untagged frame from a PC, a switching device determines the VLAN to which
the frame belongs. The determination is based on the configured VLAN division method such as port
information, and then the switching device processes the frame accordingly.
If the frame needs to be forwarded to another switching device, the frame must be transparently
transmitted along a trunk link. Frames transmitted along trunk links must carry VLAN tags to allow
other switching devices to properly forward the frame based on the VLAN information.
Before sending the frame to the destination PC, the switching device connected to the destination PC
removes the VLAN tag from the frame to ensure that the PC receives an untagged frame.
Generally, only tagged frames are transmitted on trunk links; only untagged frames are transmitted on
access links. In this manner, switching devices on the network can properly process VLAN information
and PCs are not concerned about VLAN information.
3.2 VLAN Features Supported by the S5700
This section describes VLAN features that the S5700 supports.
The VLAN technology helps separate broadcast domains and implement both intra-VLAN and
inter-VLAN communication.
l
AUsers in a VLAN can communicate with each other.
Users in different VLANs need to communicate with each other sometimes.
NOTE
Intra-VLAN communication and inter-VLAN communication are basic VLAN functions.
The S5700 also supports following extended VLAN functions:
VLAN aggregation: prevents the waste of IP addresses and implements inter-VLAN
communication.
MUX VLAN: provides a mechanism to isolate Layer 2 traffic between interfaces in a
VLAN.
Voice VLAN: identifies voice data packets from various packets and changes the
priority of voice data packets to improve voice data transmission quality.
Management VLAN (mVLAN): helps implement integrated management using a
remote device. A user can log in to a switch by using Telnet to access the IP address of
the VLANIF interface corresponding to the mVLAN using Telnet.
NOTE
The S5706 does not support VLAN aggregation.
VLAN Assignment
VLAN assignment is a basic VLAN configuration. Users in the same VLAN can communicate
with each other. Table 3-3 shows the VLAN assignment methods and their usage scenarios.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
59
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
Table 3-3 VLAN assignment in different usage scenarios
VLAN
Assignment
Method
Advantage
Disadvantage
Usage Scenario
Port-based
This method is the
most commonly used,
and configuration is
simple.
Configuration is not
flexible. If a port needs
to transmit frames of
another VLAN, the
port must be deleted
from the original
VLAN and added to
the new VLAN. If a
network has a large
number of traveling
users, the network
administrator must
spend more time on
maintenance.
Applicable to large-scale
networks that do not
have high security
requirements.
MAC addressbased
VLANs do not need to
be re-assigned when
users travel from one
place to another. This
VLAN assignment
method improves
security and flexibility
for terminal users.
A network
administrator must
configure MAC
addresses associated
with VLANs on the
switch. If the network
has many terminals, it
will take a long time
for the administrator to
configure the MAC
addresses.
Applicable to networks
that have many traveling
users and require high
security.
IP subnetbased
IP subnet-based and
protocol-based VLAN
assignment are both
network layer-based
VLAN assignment.
Network layer-based
VLAN assignment
greatly reduces
workload of manual
configurations and
allows users to easily
join a VLAN, move
from one VLAN to
another, or leave a
VLAN.
The switch needs to
parse the source IP
addresses of packets
and convert them into
MAC addresses. This
slows down switch
response.
Applicable to networks
that have traveling users
and require simple
management.
The switch needs to
analyze protocol
address formats and
convert between them.
This slows down
switch response.
Currently, VLANs can
be assigned based on the
AppleTalk, IPv4, IPv6,
and IPX protocols.
Protocolbased
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
60
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
VLAN
Assignment
Method
Advantage
Disadvantage
Usage Scenario
Policy-based
This method assigns
VLANs based on the
MAC and IP
addresses, or based on
the MAC address, IP
address, and interface.
Users cannot change
their MAC addresses
or IP addresses
associated with the
VLANs.
Each policy needs to
be manually
configured.
Applicable to small
networks that have strict
security requirements
and a large number of
traveling users.
Compared with other
VLAN assignment
methods, policiesbased VLAN
assignment has the
highest priority and
security.
Inter-VLAN Communication
Users in the same VLAN can communicate with each other, and users in different VLANs cannot
communicate with each other. To implement inter-VLAN communication, use the methods
listed in Table 3-4.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
61
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
Table 3-4 Inter-VLAN communication methods
Inter-VLAN
Communica
tion
Method
Advantage
Disadvantage
Usage Scenario
VLANIF
interface
Users in different
VLANs and network
segments can
communicate with
each other as long as
routes are reachable.
If multiple users on a
network belong to
different VLANs, each
VLAN requires a
VLANIF interface.
Each VLANIF interface
needs an IP address,
which increases
configuration workload
and uses a large number
of IP addresses.
This method is
applicable to small
scale networks on
which users belong to
different network
segments and IP
addresses of users are
seldom changed.
Inter-VLAN
communication can
also be implemented by
Layer 3 switches if
routes are reachable.
This method offers low
operating costs.
Use VLANIF
interfaces to
implement interVLAN communication
when a large number of
VLANs are configured
and both Layer 2 and
Layer 3 forwarding are
required.
VLAN Aggregation
To implement inter-VLAN communication, each VLANIF interface needs an IP address. When
many VLANs are deployed, a large number of IP addresses are used. VLAN aggregation helps
conserve IP addresses.
In VLAN aggregation, multiple VLANs are aggregated into a super-VLAN. The VLANs that
form the super-VLAN are called sub-VLANs.
You can create a VLANIF interface for the super-VLAN and configure an IP address for this
interface. All sub-VLANs share the same IP network segment so that fewer IP addresses are
used.
MUX VLAN
MUX VLAN isolates Layer 2 traffic between interfaces in a VLAN. For example, user interfaces
on an enterprise network can communicate with a server interface, but the user interfaces cannot
communicate with each other. MUX VLAN can be configured on this enterprise network.
In MUX VLAN implementation, VLANs are classified in to principal VLAN and subordinate
VLANs. Subordinate VLANs are classified into group VLANs and separate VLANs.
The principal VLAN can communicate with the subordinate VLANs, but the subordinate
VLANs cannot communicate with each other. Interfaces in a subordinate group VLAN can
communicate with each other, but interfaces in a subordinate separate VLAN cannot.
Inter-device MUX VLAN is implemented by configuring the same MUX VLAN on multiple
devices and configuring interfaces between the devices to allow packets of the MUX VLAN.
Implementation of inter-device MUX VLAN is the same as MUX VLAN on a single device.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
62
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
3.3 Dividing a LAN into VLANs
A LAN can be divided into several VLANs and users in each VLAN can communicate with
each other. Currently, the S5700 supports several VLAN division modes. You can choose one
of them as required.
3.3.1 Establishing the Configuration Task
Before dividing a LAN into VLANs, familiarize yourself with the applicable environment,
complete the pre-configuration tasks, and obtain the data required for the configuration. This
will help you complete the configuration task quickly and accurately.
Applicable Environment
Currently, the S5700 supports the following VLAN division modes. You can choose one of them
as required. Table 3-5 lists VLAN division modes.
Table 3-5 VLAN assignment in different usage scenarios
Issue 02 (2011-11-21)
VLAN
Assignment
Method
Advantage
Disadvantage
Usage Scenario
Port-based
This method is the
most commonly used,
and configuration is
simple.
Configuration is not
flexible. If a port needs
to transmit frames of
another VLAN, the
port must be deleted
from the original
VLAN and added to
the new VLAN. If a
network has a large
number of traveling
users, the network
administrator must
spend more time on
maintenance.
Applicable to large-scale
networks that do not
have high security
requirements.
MAC addressbased
VLANs do not need to
be re-assigned when
users travel from one
place to another. This
VLAN assignment
method improves
security and flexibility
for terminal users.
A network
administrator must
configure MAC
addresses associated
with VLANs on the
switch. If the network
has many terminals, it
will take a long time
for the administrator to
configure the MAC
addresses.
Applicable to networks
that have many traveling
users and require high
security.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
63
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
VLAN
Assignment
Method
Advantage
Disadvantage
Usage Scenario
IP subnetbased
IP subnet-based and
protocol-based VLAN
assignment are both
network layer-based
VLAN assignment.
Network layer-based
VLAN assignment
greatly reduces
workload of manual
configurations and
allows users to easily
join a VLAN, move
from one VLAN to
another, or leave a
VLAN.
The switch needs to
parse the source IP
addresses of packets
and convert them into
MAC addresses. This
slows down switch
response.
Applicable to networks
that have traveling users
and require simple
management.
The switch needs to
analyze protocol
address formats and
convert between them.
This slows down
switch response.
Currently, VLANs can
be assigned based on the
AppleTalk, IPv4, IPv6,
and IPX protocols.
This method assigns
VLANs based on the
MAC and IP
addresses, or based on
the MAC address, IP
address, and interface.
Users cannot change
their MAC addresses
or IP addresses
associated with the
VLANs.
Each policy needs to
be manually
configured.
Applicable to small
networks that have strict
security requirements
and a large number of
traveling users.
Protocolbased
Policy-based
Compared with other
VLAN assignment
methods, policiesbased VLAN
assignment has the
highest priority and
security.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
64
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
NOTE
In the case that the S5700 supports multiple VLAN division modes, the priorities of these VLAN division
modes are in descending order:
1. Policies-based VLAN division
This mode has the highest priority, but is not commonly used.
2. MAC address-based VLAN division and IP subnet-based VLAN division
By default, MAC address-based VLAN division is set as the preference. You can run commands to
change priorities of these two VLAN division modes.
3. Protocol-based VLAN division
4. Port-based VLAN division
Port-based VLAN division has the lowest priority, but is most commonly used.
Pre-configuration Tasks
Before dividing a LAN into VLANs, complete the following task:
l
Connecting ports and configuring physical parameters of the ports, ensuring that the ports
are physically Up
Data Preparation
To dividing a LAN into VLANs, you need the following data.
No.
Data
VLAN ID, number of each Ethernet port to be added to the VLAN, and (optional)
attribute of Ethernet ports
VLAN ID, MAC address mapped to the VLAN and (optional) 802.1p priority
value related to the MAC address
VLAN ID, (optional) IP subnet index, IP address mapped to the VLAN and
(optional) 802.1p priority value related to the IP address or network segment
VLAN ID, (optional) protocol template index, protocol type mapped to the
VLAN, and (optional) 802.1p priority value related to the protocol
VLAN ID, MAC address and IP address mapped to the VLAN and (optional)
number of the Ethernet port added to a VLAN based on its MAC and IP addresses
3.3.2 Dividing a LAN into VLANs Based on Ports
Dividing a LAN into VLANs based on ports is the most simple and effective VLAN division
mode.
Context
After VLANs are configured based on ports, the VLANs can process tagged and untagged frames
in the following manners:
l
Issue 02 (2011-11-21)
After receiving an untagged frame, a port adds the PVID to the frame, searches the MAC
address table for an outbound port, and sends the tagged frame from the outbound port.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
65
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
After a port receives a tagged frame, it checks the VLAN ID carried in the frame:
If the port allows frames with the specified VLAN ID to pass through, it forwards the
frame.
If the port does not allow frames with the specified VLAN ID to pass through, it discards
the frame.
The configuration roadmap is as follows:
1.
Create VLANs.
2.
Configure the port type and features.
a.
3.
Configure the port type (access, trunk, hybrid, or QinQ).
Add ports to VLANs.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
vlan vlan-id
A VLAN is created, and the VLAN view is displayed. If the specified VLAN has been created,
the VLAN view is directly displayed.
The VLAN ID ranges from 1 to 4094. If VLANs need to be created in batches, run the vlan
batch { vlan-id1 [ to vlan-id2 ] } &<1-10> command to create VLANs in batches, and then run
the vlan vlan-id command to enter the view of a specified VLAN.
Step 3 Run:
quit
The system view is displayed.
Step 4 Configure the port type and features.
1.
Run the interface interface-type interface-number command to enter the view of an
Ethernet port to be added to the VLAN.
2.
Run the port link-type { access | hybrid | trunk | dot1q-tunnel } command to configure
the port type.
By default, the port type is hybrid.
l If a Layer 2 Ethernet port is directly connected to a terminal, set the port type to access
or hybrid.
l If a Layer 2 Ethernet port is connected to another switch, the port type can be set to
access, trunk, hybrid, or QinQ.
Step 5 Add ports to the VLAN.
Run either of the following commands as needed:
l For access or QinQ ports:
Run the port default vlan vlan-id command to add a port to a specified VLAN.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
66
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
To add ports to a VLAN in batches, run the port interface-type { interface-number1 [ to
interface-number2 ] } &<1-10> command in the VLAN view.
l For trunk ports:
Run the port trunk allow-pass vlan { { vlan-id1 [ to vlan-id2 ] } &<1-10> | all }
command to add the port to specified VLANs.
(Optional) Run the port trunk pvid vlan vlan-id command to specify the default VLAN
for a trunk interface.
l For hybrid ports:
Run either of the following commands to add a port to VLANs in untagged or tagged
mode:
Run the port hybrid untagged vlan { { vlan-id1 [ to vlan-id2 ] } &<1-10> | all }
command to add a port to VLANs in untagged mode.
In untagged mode, a port removes tags from frames and then forwards the frames.
This is applicable to scenarios in which Layer 2 Ethernet ports are connected to
terminals.
Run the port hybrid tagged vlan { { vlan-id1 [ to vlan-id2 ] } &<1-10> | all }
command to add a port to VLANs in tagged mode.
In tagged mode, a port forwards frames without removing their tags. This is applicable
to scenarios in which Layer 2 Ethernet ports are connected to switches.
(Optional) Run the port hybrid pvid vlan vlan-id command to specify the default VLAN
of a hybrid interface.
By default, all ports are added to VLAN 1.
----End
3.3.3 Dividing a LAN into VLANs Based on MAC Addresses
MAC address-based VLAN division is used if user locations do not need to be concerned. This
improves security and flexibility for terminal users.
Context
VLANs configured based on MAC addresses process only untagged frames, and treat tagged
frames in the same manner as VLANs configured based on ports.
After receiving an untagged frame, a port searches for a MAC-VLAN mapping based on the
source MAC address in the frame.
l
If a mapping is found, the port forwards the frame based on the VLAN ID and priority
value in the mapping.
If no matching mapping is found, the port matches the frame with other matching rules.
The configuration roadmap is as follows:
1.
Create VLANs.
2.
Map MAC addresses to VLAN IDs.
3.
Configure the port type and features.
Issue 02 (2011-11-21)
a.
Set the port type to hybrid.
b.
Configure a port to allow frames with specified VLAN IDs to pass through.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
67
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
4.
3 VLAN Configuration
(Optional) Configure the highest priority for MAC address-based VLAN division.
NOTE
By default, MAC address-based VLAN division is set as the preference. To use IP subnet-based
VLAN division, set a higher priority for it.
5.
Enable MAC address-based VLAN division.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
vlan vlan-id
A VLAN is created, and the VLAN view is displayed. If the specified VLAN has been created,
the VLAN view is directly displayed.
The VLAN ID ranges from 1 to 4094. If VLANs need to be created in batches, run the vlan
batch { vlan-id1 [ to vlan-id2 ] } &<1-10> command to create VLANs in batches, and then run
the vlan vlan-id command to enter the view of a specified VLAN.
Step 3 Run:
mac-vlan mac-address mac-address [ mac-address-mask | mac-address-mask-length ]
[ priority priority ]
Map a MAC address to the VLAN.
l The mac-address value is in the H-H-H format. H is a hexadecimal number that contains one
to four digits, such as 00e0 and fc01. If an H contains less than four digits, 0s are padded
ahead. For example, if you specify an H as e0, it is displayed as 00e0. A MAC address cannot
be set to all 0s or all Fs.
l The optional parameter priority specifies the 802.1p priority value related to the MAC
addresses. The value ranges from 0 to 7. The greater the value, the higher the priority. The
default value is 0. After the 802.1p priority value is specified, frames with high priorities are
first forwarded when traffic is congested.
Step 4 Run:
quit
The system view is displayed.
Step 5 Configure the port type and features.
1.
Run the interface interface-type interface-number command to enter the view of the port
to be configured to allow frames with a specified VLAN ID to pass through.
2.
Run the port link-type hybrid command to set the port type to hybrid.
By default, the port type is hybrid.
3.
Run the port hybrid untagged vlan { { vlan-id1 [ to vlan-id2 ] } &<1-10> | all } command
to configure the hybrid port to allow frames with a specified VLAN ID to pass through.
Step 6 (Optional) Run the vlan precedence mac-vlan command to configure a higher priority for MAC
address-based VLAN division.
By default, MAC address-based VLAN division is set as the preference.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
68
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
Step 7 Run:
mac-vlan enable
MAC address-based VLAN division is enabled.
By default, MAC address-based VLAN division is disabled.
NOTE
MAC address-based VLAN assignment conflict with MUX VLAN. They cannot be configured on the same
interface.
----End
3.3.4 Dividing a LAN into VLANs Based on IP Subnets
IP subnet-based and protocol-based VLAN division are called network layer-based VLAN
division, which reduces manual VLAN configuration workload and allows users to easily join
a VLAN, transfer from one VLAN to another, and exit from a VLAN. IP subnet-based VLAN
division is applicable to networks that have traveling users and require simple management.
Context
VLANs configured based on IP subnets process only untagged frames. and treat tagged frames
in the same manner as VLANs configured based on ports.
After receiving untagged frames, a device determines the VLANs to which the frames belong
based on their source IP addresses before sending them to corresponding VLANs.
The configuration roadmap is as follows:
1.
Create VLANs.
2.
Associate IP subnets with VLANs to determine mappings between subnets and VLANs.
3.
Configure the port type and features.
4.
a.
Set the port type to hybrid.
b.
Configure a port to allow frames with the specified VLAN IDs to pass through.
(Optional) Set a higher priority for IP subnet-based VLAN division.
NOTE
By default, MAC address-based VLAN division is set as the preference. To use IP subnet-based
VLAN division, set a higher priority for it.
5.
Enable IP subnet-based VLAN division.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
vlan vlan-id
A VLAN is created, and the VLAN view is displayed. If the specified VLAN has been created,
the VLAN view is directly displayed.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
69
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
The VLAN ID ranges from 1 to 4094. If VLANs need to be created in batches, run the vlan
batch { vlan-id1 [ to vlan-id2 ] } &<1-10> command to create VLANs in batches, and then run
the vlan vlan-id command to enter the view of a specified VLAN.
Step 3 Run:
ip-subnet-vlan [ ip-subnet-index ] ip ip-address { mask | mask-length }
[ priority priority ]
An IP subnet is associated with the VLAN.
l The optional parameter ip-subnet-index specifies the IP subnet index. The subnet index can
be specified by a user or automatically generated by the system.
l The parameter ip-address specifies the source IP address or network address based on which
a VLAN is configured. The value is in dotted decimal notation.
l The optional parameter priority specifies the 802.1p priority value related to the VLAN
configured based on the IP address or network address. The value ranges from 0 to 7. The
greater the value, the higher the priority. The default value is 0. After the 802.1p priority
value is specified, frames with high priorities are first forwarded when traffic is congested.
Step 4 Run:
quit
The system view is displayed.
Step 5 Configure the port type and features.
1.
Run the interface interface-type interface-number command to enter the view of the port
to be configured to allow frames with the specified VLAN ID to pass through.
2.
Run the port link-type hybrid command to set the port type to hybrid.
By default, the port type is hybrid.
3.
Run the port hybrid untagged vlan { { vlan-id1 [ to vlan-id2 ] } &<1-10> | all } command
to allow frames with the specified VLAN ID to pass through.
Step 6 (Optional) Run:
vlan precedence ip-subnet-vlan
IP subnet-based VLAN division is configured with a higher priority.
By default, MAC address-based VLAN division is set as the preference.
Step 7 Run:
ip-subnet-vlan enable
IP subnet-based VLAN division is enabled.
By default, IP subnet-based VLAN division is disabled.
----End
3.3.5 Dividing a LAN into VLANs Based on Protocols
IP subnet-based and protocol-based VLAN division are called network layer-based VLAN
division, which reduces manual VLAN configuration workload and allows users to easily join
a VLAN, transfer from one VLAN to another, and exit from a VLAN.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
70
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
Context
VLANs configured based on protocols process only untagged frames. and treat tagged frames
in the same manner as VLANs configured based on ports.
After receiving an untagged frame, a port identifies the protocol template used by the frame to
determine the VLAN to which the frame belongs.
l
If the port has been added to VLANs corresponding to some protocols, and the protocol
template adopted by the frame matches one of these protocols, the port adds the
corresponding VLAN ID to the frame.
If the port has been added to VLANs corresponding to some protocols, but the protocol
template adopted by the frame does not match any one of these protocols, the port adds the
PVID to the frame.
The configuration roadmap is as follows:
1.
Create VLANs.
2.
Associate protocols with VLANs to determine mappings between protocols and VLANs.
3.
Configure the port type and features.
a.
Set the port type to hybrid.
b.
Configure a port to allow frames with the specified VLAN ID to pass through.
c.
Associate ports with VLANs.
After receiving a frame associated with a specified protocol, the system automatically
assigns the VLAN ID associated with the protocol to the frame.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
vlan vlan-id
A VLAN is created, and the VLAN view is displayed. If the specified VLAN has been created,
the VLAN view is directly displayed.
The VLAN ID ranges from 1 to 4094. If VLANs need to be created in batches, run the vlan
batch { vlan-id1 [ to vlan-id2 ] } &<1-10> command to create VLANs in batches, and then run
the vlan vlan-id command to enter the view of a specified VLAN.
Step 3 Run:
protocol-vlan [ protocol-index ] { at | ipv4 | ipv6 | ipx { ethernetii | llc | raw
| snap } | mode { ethernetii-etype etype-id1 | llc dsap dsap-id ssap ssap-id | snapetype etype-id2 } }
A protocol is associated with a VLAN and the protocol template is specified.
l The optional parameter protocol-index specifies the protocol template index.
The protocol template is determined by the protocol type and encapsulation format. A
protocol VLAN can be defined by a protocol template.
l When configuring the source and destination service access points, note the following points:
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
71
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
dsap-id and ssap-id cannot be both set to 0xaa.
dsap-id and ssap-id cannot be both set to 0xe0, which corresponds to the Logical Link
Control (LLC) encapsulation format for IPX packets.
dsap-id and ssap-id cannot be both set to 0xff, which corresponds to the RAW
encapsulation format for IPX packets.
Step 4 Configure the port type and features.
1.
Run the interface interface-type interface-number command to enter the view of the port
to be configured to allow frames with the specified VLAN ID to pass through.
2.
Run the port link-type hybrid command to set the port type to hybrid.
By default, the port type is hybrid.
3.
Run the port hybrid untagged vlan { { vlan-id1 [ to vlan-id2 ] } &<1-10> | all } command
to allow frames with the specified VLAN ID to pass through.
4.
Run:
protocol-vlan vlan vlan-id { all | protocol-index1 [ to protocol-index2 ] }
[ priority priority ]
The port is associated with the VLAN.
l The parameter vlan-id specifies the ID of a VLAN configured based on a protocol.
l The optional parameter priority specifies the 802.1p priority value related to the
protocol. The value ranges from 0 to 7. The greater the value, the higher the priority.
The default value is 0. After the 802.1p priority value is specified, frames with high
priorities are first forwarded when traffic is congested.
----End
3.3.6 Dividing a LAN into VLANs Based on Policies
VLANs configured based on policies are also called policy VLANs. Policy VLANs allow
terminals to plug and play and data for different users to be separately transmitted.
Context
A LAN can be divided into VLANs based on MAC and IP addresses or based on MAC and IP
addresses and interfaces.
To divide a LAN into VLANs based on policies, configure MAC and IP addresses of terminals
on a switch and associate pairs of MAC addresses ,IP addresses and interfaces with VLANs.
Only users matching a policy can be added to a specified VLAN. If the IP or MAC addresses
of users added to a VLAN are changed, they will exit from the VLAN.
Policy VLANs process only untagged frames. and treat tagged frames in the same manner as
VLANs configured based on ports.
After receiving an untagged frame, the device finds a VLAN matching both MAC and IP
addresses of the frame, and transmits the frame in the VLAN.
The configuration roadmap is as follows:
1.
Create VLANs.
2.
Associate pairs of MAC and IP addresses with VLANs to divide a LAN into VLANs based
on both MAC and IP addresses.
3.
Configure the port type and features.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
72
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
a.
Set the port type to hybrid.
b.
Configure a port to allow frames with specified MAC and IP addresses to pass through.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
vlan vlan-id
A VLAN is created, and the VLAN view is displayed. If the specified VLAN has been created,
the VLAN view is directly displayed.
The VLAN ID ranges from 1 to 4094. If VLANs need to be created in batches, run the vlan
batch { vlan-id1 [ to vlan-id2 ] } &<1-10> command to create VLANs in batches, and then run
the vlan vlan-id command to enter the view of a specified VLAN.
Step 3 Run:
policy-vlan mac-address mac-address ip ip-address [ interface interface-type
interface-number ] [ priority priority ]
Policy VLAN is configured.
If interface interface-type interface-number is not specified, the MAC and IP address policy
will be applied to all ports in the VLAN. If interface interface-type interface-number is
specified, the MAC and IP address policy will be applied to the specified port in the VLAN.
Before deleting a policy VLAN, run the undo policy-vlan command to disable the policy VLAN
function.
Step 4 Run:
quit
The system view is displayed.
Step 5 Configure the port type and features.
1.
Run the interface interface-type interface-number command to enter the view of the port
to be configured with a policy VLAN.
2.
Run the port link-type hybrid command to set the port type to hybrid.
By default, the port type is hybrid.
3.
Run the port hybrid untagged vlan { { vlan-id1 [ to vlan-id2 ] } &<1-10> | all } command
to allow frames with specified MAC and IP addresses to pass through.
----End
3.3.7 Checking the Configuration
After dividing a LAN into VLANs, you can view information about VLANs configured in
different modes. For example, which VLANs are classified based on ports or MAC addresses.
Prerequisite
The configurations of VLAN division are complete.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
73
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
Procedure
l
Run the display vlan [ vlan-id [ verbose ] ] command to check information about all
VLANs or a specified VLAN.
Run the display mac-vlan { mac-address { all | mac-address [ mac-address-mask | macaddress-mask-length ] } | vlan vlan-id } command to check information about VLANs
configured based on MAC addresses.
Run the display ip-subnet-vlan vlan { all | vlan-id1 [ to vlan-id2 ] } command to check
information about VLANs configured based on IP subnets.
Run the display protocol-vlan vlan { all | vlan-id1 [ to vlan-id2 ] } command to check
information about VLANs configured based on protocols.
Run the display protocol-vlan interface { all | interface-type interface-number } command
to check information about VLANs configured based on protocols associated with ports.
Run the display policy-vlan { all | vlan vlan-id } command to check information about
policy vlan.
----End
3.4 Creating a VLANIF Interface
VLANIF interfaces are Layer 3 logical interfaces. After creating VLANIF interfaces on Layer
2 devices, you can configure Layer 3 features on these interfaces.
3.4.1 Establishing the Configuration Task
Before creating a VLANIF interface, familiarize yourself with the applicable environment,
complete the pre-configuration tasks, and obtain the data required for the configuration. This
will help you complete the configuration task quickly and accurately.
Applicable Environment
Layer 3 switching combines routing and switching techniques to implement routing on a switch,
thus improving the overall network performance. After sending the first data flow, a Layer 3
switch generates mappings between MAC addresses and IP addresses. To send the same data
flow, the switch directly sends the data flow at Layer 2 but not Layer 3 based on this mapping
table.
To allow that new data flows are correctly forwarded based on the routing table, be sure that the
routing table's routing entries are correct. Therefore, VLANIF interfaces and routing protocols
must be configured on Layer 3 switches for reachable Layer 3 routes.
Pre-configuration Tasks
Before creating a VLANIF interface, complete the following task:
l
Creating a VLAN
Data Preparation
To create a VLANIF interface, you need to the following data.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
74
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
No.
Data
VLAN ID
IP address to be assigned to the VLANIF interface
(Optional) Delay after which the VLANIF interface goes Down
(Optional) MTU of the VLANIF interface
3.4.2 Creating a VLANIF Interface
Before configure Layer 3 features on a Layer 2 device, you must create a VLANIF interface on
the device.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
interface vlanif vlan-id
A VLANIF interface is created and the VLAIF interface view is displayed.
The VLAN ID specified in this command must be the ID of an existing VLAN.
NOTE
A VLANIF interface is Up only when at least one physical port added to the corresponding VLAN is Up.
----End
3.4.3 Assigning an IP Address to a VLANIF Interface
As a VLANIF interface is a Layer 3 logical interface, it can communicate with other interfaces
at the network layer only after being assigned an IP address.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
interface vlanif vlan-id
The VLANIF interface view is displayed.
The VLAN ID specified in this command must be the ID of an existing VLAN.
Step 3 Run:
ip address ip-address { mask | mask-length } [ sub ]
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
75
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
An IP address is assigned to the VLANIF interface for communication at the network layer.
----End
3.4.4 (Optional) Setting a Delay After Which a VLANIF Interface
Goes Down
Setting a delay after which a VLANIF interface goes Down prevents network flapping caused
by changes of VLANIF interface status. This function is also called VLAN damping.
Context
If a VLAN goes Down because all ports in the VLAN go Down, the system immediately reports
the VLAN Down event to the corresponding VLANIF interface, instructing the VLANIF
interface to go Down.
To prevent network flapping caused by changes of VLANIF interface status, enable VLAN
damping on the VLANIF interface. After the last Up port in a VLAN goes Down, the system
starts a delay timer and informs the corresponding VLANIF interface of the VLAN Down event
after the timer expires. If a port in the VLAN goes Up during the delay period, the VLANIF
interface remains Up.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
interface vlanif vlan-id
The VLANIF interface view is displayed.
The VLAN ID specified in this command must be the ID of an existing VLAN.
Step 3 Run:
damping time delay-time
The delay for VLAN damping is set.
The delay-time value ranges from 0 to 20, in seconds. By default, the value is 0 seconds,
indicating that VLAN damping is disabled.
----End
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
76
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
3.4.5 (Optional) Setting the MTU of a VLANIF Interface
Context
NOTE
l After changing the maximum transmission unit (MTU) by using the mtu command on a specified
interface, you need to restart the interface to make the new MTU take effect. To restart the interface,
run the shutdown command and then the undo shutdown command, or run the restart command in
the interface view.
l If you change the MTU of an interface, you need to change the MTU of the peer interface to the same
value by using the mtu command; otherwise, services may be interrupted.
l To ensure availability of Layer 3 functions, set the MTU value of the VLANIF interface to be smaller
than the maximum length of frames on the physical interface in the corresponding VLAN.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
interface vlanif vlan-id
The VLANIF interface view is displayed.
Step 3 Run:
mtu mtu
The MTU of the VLANIF interface is set.
The MTU of a VLANIF interface ranges from 128 to 9216, in bytes. The default value is 1500.
NOTE
If the MTU is too small whereas the packet size is large, the packet is probably split into many fragments.
Therefore, the packet may be discarded due to the insufficient QoS queue length. To avoid this situation,
lengthen the QoS queue accordingly.
----End
3.4.6 Checking the Configuration
After a VLANIF interface is configured for communication at the network layer, you can check
the IP address and status of a specified VLANIF interface.
Prerequisite
The configurations of a VLANIF interface are complete.
Procedure
l
Run the display interface vlanif [ vlan-id ] command to check the physical status, link
protocol status, description, and IP address of the VLANIF interface.
----End
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
77
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
3.5 Configuring Inter-VLAN Communication
Configuring inter-VLAN communication allows users in different VLANs to communicate with
each other. Currently, the S5700 supports several inter-VLAN communication schemes. Choose
one of them as required.
3.5.1 Establishing the Configuration Task
Before configuring inter-VLAN communication, familiarize yourself with the applicable
environment, complete the pre-configuration tasks, and obtain the data required for the
configuration. This will help you complete the configuration task quickly and accurately.
Applicable Environment
Currently, schemes listed in Table 3-6 are provided for inter-VLAN communication. You can
choose one of them based on the real world situation.
Table 3-6 Inter-VLAN communication methods
Inter-VLAN
Communica
tion
Method
Advantage
Disadvantage
Usage Scenario
VLANIF
interface
Users in different
VLANs and network
segments can
communicate with
each other as long as
routes are reachable.
If multiple users on a
network belong to
different VLANs, each
VLAN requires a
VLANIF interface.
Each VLANIF interface
needs an IP address,
which increases
configuration workload
and uses a large number
of IP addresses.
This method is
applicable to small
scale networks on
which users belong to
different network
segments and IP
addresses of users are
seldom changed.
Inter-VLAN
communication can
also be implemented by
Layer 3 switches if
routes are reachable.
This method offers low
operating costs.
Use VLANIF
interfaces to
implement interVLAN communication
when a large number of
VLANs are configured
and both Layer 2 and
Layer 3 forwarding are
required.
Pre-configuration Tasks
Before configuring inter-VLAN communication, complete the following task:
l
Issue 02 (2011-11-21)
Creating VLANs
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
78
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
Data Preparation
To configure inter-VLAN communication, you need the following data.
No.
Data
VLAN ID, VLANIF interface number, IP address and mask of the VLANIF
interface
3.5.2 Configuring VLANIF Interfaces for Inter-VLAN
Communication
Configuring VLANIF interfaces for inter-VLAN communication saves expenditure and helps
implement fast forwarding.
Context
VLAIF interfaces are Layer 3 logical interfaces. After being assigned IP addresses, VLANIF
interfaces are able to communicate at the network layer.
By using VLANIF interfaces to implement inter-VLAN communication, you need to configure
a VLANIF interface for each VLAN and assign an IP address to each VLANIF interface.
Figure 3-5 Networking diagram for configuring VLANIF interfaces for inter-VLAN
communication
Switch
VLANIF2
VLAN2
VLANIF3
VLAN3
NOTE
The default gateway address of each PC in a VLAN must be the IP address of the corresponding VLANIF
interface. Otherwise, inter-VLAN communication will fail.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
79
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
interface vlanif vlan-id
A VLANIF interface is created and the VLAIF interface view is displayed.
The VLAN ID specified in this command must be the ID of an existing VLAN.
NOTE
A VLANIF interface is Up only when at least one physical port added to the corresponding VLAN is Up.
Step 3 Run:
ip address ip-address { mask | mask-length } [ sub ]
An IP address is assigned to the VLANIF interface.
VLANIF interfaces must belong to different network segments.
----End
3.5.3 Checking the Configuration
After inter-VLAN communication is configured, you can check whether users in different
VLANs can communicate with each other and check information about VLANs to which users
belong.
Prerequisite
The configurations of inter-VLAN communication are complete.
Procedure
l
Run the ping [ ip ] [ -a source-ip-address | -c count | -d | -f | -h ttl-value | -i interfacetype interface-number | -m time | -n | -p pattern | -q | -r | -s packetsize | -system-time | -t
timeout | -tos tos-value | -v | -vpn-instance vpn-instance-name ] * host command to check
whether users in different VLANs can communicate with each other.
If the ping fails, you can run the following commands to locate the fault:
Run the display vlan [ vlan-id [ verbose ] ] command to check information about all
VLANs or a specified VLAN.
Run the display interface vlanif [ vlan-id ] command to check information about
VLANIF interfaces.
Before running this command, ensure that VLANIF interfaces have been configured.
----End
3.6 Configuring VLAN Aggregation to Save IP Addresses
VLAN aggregation prevents the waste of IP addresses and implements inter-VLAN
communication.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
80
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
3.6.1 Establishing the Configuration Task
Before configuring VLAN aggregation, familiarize yourself with the applicable environment,
complete the pre-configuration tasks, and obtain the data required for the configuration. This
will help you complete the configuration task quickly and accurately.
Applicable Environment
As networks expand, address resources become insufficient. VLAN aggregation is developed
to save IP addresses.
In VLAN aggregation, one super-VLAN is associated with multiple sub-VLANs. Physical ports
cannot join a super-VLAN but a VLANIF interface can be created for the super-VLAN and an
IP address can be assigned to the VLANIF interface. Physical ports can join a sub-VLAN but
no VLANIF interface can be created for the sub-VLAN. All the ports in the sub-VLAN use the
same IP address with the VLANIF interface of the super-VLAN. This saves subnet IDs, default
gateway addresses of the subnets, and directed broadcast addresses of the subnets. In addition,
different broadcast domains can use the addresses in the same subnet segment. As a result, subnet
differences are eliminated, addressing becomes flexible, and the number of idle addresses is
reduced. VLAN aggregation allows each sub-VLAN to function as a broadcast domain and
reduces the waste of IP addresses to be assigned to ordinary VLANs.
Figure 3-6 shows the typical VLAN aggregation networking.
Figure 3-6 Typical networking diagram for VLAN aggregation
PE
Super
VLAN4
CE1
CE2
Sub-VLAN 2
Sub-VLAN 3
NOTE
S5706 does not support VLAN aggregation.
Pre-configuration Tasks
Before configuring VLAN aggregation, complete the following task:
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
81
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
Connecting ports and configuring physical parameters of the ports, ensuring that the ports
are physically Up
Data Preparation
To configure VLAN aggregation, you need the following data.
No.
Data
ID of each sub-VLAN and number of each port belonging to the sub-VLAN
ID of a super-VLAN
IP address and mask of a VLANIF interface
3.6.2 Creating a Sub-VLAN
Each sub-VLAN functions as a broadcast domain.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
interface interface-type interface-number
The interface view is displayed.
Step 3 Run:
port link-type access
The link type of the interface is set to access.
Step 4 Run:
quit
Return to the system view.
Step 5 Run:
vlan vlan-id
A sub-VLAN is created and the sub-VLAN view is displayed.
Step 6 Run:
port interface-type { interface-number1 [ to interface-number2 ] } &<1-10>
A port is added to the sub-VLAN.
----End
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
82
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
3.6.3 Creating a Super-VLAN
A super-VLAN consists of several sub-VLANs. No physical port can be added to a super-VLAN,
but a VLANIF interface can be configured for the super-VLAN and an IP address can be assigned
to the VLANIF interface.
Context
NOTE
Before configuring a super-VLAN, ensure that sub-VLANs have been configured.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
vlan vlan-id
A VLAN is created, and the VLAN view is displayed.
The VLAN ID of a super-VLAN must be different from every sub-VLAN ID.
Step 3 Run:
aggregate-vlan
A super-VLAN is created.
A super-VLAN cannot contain any physical interfaces.
VLAN 1 cannot be configured as a super-VLAN.
Step 4 Run:
access-vlan { vlan-id1 [ to vlan-id2 ] } &<1-10>
A sub-VLAN is added to a super-VLAN.
Before adding sub-VLANs to a super-VLAN in batches, ensure that these sub-VLANs are not
configured with VLANIF interfaces.
----End
3.6.4 Assigning an IP Address to the VLANIF Interface of a SuperVLAN
The IP address of the VLANIF interface of a super-VLAN must contain the subnet segments
where users in sub-VLANs reside. All the sub-VLANs use the IP address of the VLANIF
interface of the super-VLAN, thus saving IP addresses.
Procedure
Step 1 Run:
system-view
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
83
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
The system view is displayed.
Step 2 Run:
interface vlanif vlan-id
A VLANIF interface is created for a super-VLAN, and the view of the VLANIF interface is
displayed.
Step 3 Run:
ip address ip-address { mask | mask-length } [ sub ]
An IP address is assigned to the VLANIF interface.
----End
3.6.5 (Optional) Enabling Proxy ARP on the VLANIF Interface of a
Super-VLAN
PCs in different sub-VLANs cannot directly communicate with each other in Layer2 network.
To allow these PCs to communicate with each other at Layer 3, enable proxy ARP on the
VLANIF interface of the super-VLAN.
Context
VLAN aggregation allows sub-VLANs to use the same subnet address, but prevents PCs in
different sub-VLANs from communicating with each other at the network layer.
PCs in ordinary VLANs can communicate with each other at the network layer by using different
gateway addresses. In VLAN aggregation, PCs in a super-VLAN use the same subnet address
and gateway address. As PCs in different sub-VLANs belong to one subnet, they communicate
with each other only at Layer 2, not Layer 3. These PCs are isolated from each other at Layer
2. Consequently, PCs in different sub-VLANs cannot communicate with each other.
Proxy ARP is required to enable PCs in a sub-VLAN to communicate with PCs in another subVLAN or PCs on other networks. After a super-VLAN and its VLANIF interface are created,
proxy ARP must be enabled to allow the super-VLAN to forward or process ARP request and
reply packets. Proxy ARP helps PCs in sub-VLANs communicate with each other at the network
layer.
NOTE
An IP address must have been assigned to the VLANIF interface corresponding to the super-VLAN.
Otherwise, proxy ARP cannot take effect.
VLAN aggregation simplifies configurations for the network where many VLANs are
configured and PCs in different VLANs need to communicate with each other.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
interface vlanif vlan-id
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
84
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
The view of the VLANIF interface of the super-VLAN is displayed.
Step 3 Run:
arp-proxy inter-sub-vlan-proxy enable
Inter-sub-VLAN proxy ARP is enabled.
----End
3.6.6 Checking the Configuration
After VLAN aggregation is configured, you can view VLAN types and information about
VLANIF interfaces, such as the physical status, link protocol status, IP address, and mask.
Prerequisite
The VLAN aggregation configurations are complete.
Procedure
l
Run the display vlan [ vlan-id [ verbose ] ] command to check VLAN information.
Run the display interface vlanif [ vlan-id ] command to check information about a specific
VLANIF interface.
----End
3.7 Configuring a MUX VLAN to Separate Layer 2 Traffic
Configuring a MUX VLAN allows users in different VLANs to communicate with each other,
and separates users in a certain VLAN.
3.7.1 Establishing the Configuration Task
Before configuring a MUX VLAN, familiarize yourself with the applicable environment,
complete the pre-configuration tasks, and obtain the data required for the configuration. This
will help you complete the configuration task quickly and accurately.
Applicable Environment
In an enterprise network, all employees of the enterprise can access the enterprise's server. It is
required that some employees be able to communicate with each other, whereas some employees
not communicate with each other.
Configuring a MUX VLAN on the switch connected to PCs helps to save VLAN ID resources,
reduce the configuration workload of the network administrator, and facilitate network
maintenance.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
85
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
Figure 3-7 Networking diagram for a MUX VLAN
Switch
Principal PORT
Group PORT
Enterprise
employee1
Separate PORT Enterprise
server
Enterprise
employee2
In the MUX VLAN shown in Figure 3-7, the principal port connects the switch to the enterprise's
server; separate ports connect the switch to employees that do not communicate with each other;
group ports connect the switch to employees that need to communicate with each other. A MUX
VLAN consists of VLANs in different types listed in Table 3-7.
Table 3-7 Components of a MUX VLAN
MUX
VLAN
VLAN
Type
Port Type
Communication Rights
Principal
VLAN
Principal port
A principal port can communicate with every
port in the MUX VLAN.
Subordinate
VLAN
Separate
VLAN
Separate port
A separate port can only communicate with
principal ports.
Each separate VLAN must be associated with
a principal VLAN.
Group
VLAN
Group port
A group port can communicate with both
principal ports and other group ports in the
same group VLAN but cannot communicate
with group ports in other group VLANs or
separate ports.
Each group VLAN must be associated with a
principal VLAN.
Pre-configuration Tasks
Before configuring a MUX VLAN, complete the following task:
l
Issue 02 (2011-11-21)
Creating VLANs
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
86
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
Data Preparation
To configure a MUX VLAN, you need the following data.
No.
Data
ID of each principal VLAN and number of each port belonging to the principal VLAN
ID of each group VLAN and number of each port belonging to the group VLAN
ID of each separate VLAN and number of each port belonging to the separate VLAN
3.7.2 Configuring a Principal VLAN for a MUX VLAN
Ports added to a principal VLAN can communicate with every port in the MUX VLAN.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
vlan vlan-id
A VLAN is created, and the VLAN view is displayed. If the specified VLAN has been created,
the VLAN view is directly displayed.
The VLAN ID ranges from 1 to 4094. If VLANs need to be created in batches, run the vlan
batch { vlan-id1 [ to vlan-id2 ] } &<1-10> command to create VLANs in batches, and then run
the vlan vlan-id command to enter the view of a specified VLAN.
Step 3 Run:
mux-vlan
The VLAN is configured as a principal VLAN.
The VLAN ID assigned to a principal VLAN can no longer be used to configure any VLANIF
interface, super-VLAN, or sub-VLAN.
----End
3.7.3 Configuring a Group VLAN for a Subordinate VLAN
A VLAN associated with a group port is called a group VLAN. Group ports in a group VLAN
can communicate with each other.
Context
In a MUX VLAN, group VLANs cannot share the same VLAN ID with a separate VLAN.
Do as follows on a switching device that requires a group VLAN:
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
87
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
vlan vlan-id
The view of a created principal VLAN is displayed.
Step 3 Run:
subordinate group vlan-id1 [ to vlan-id2 ]
A group VLAN is configured for the subordinate VLAN.
In this command, vlan-id1 and vlan-id2 specify a range of VLAN IDs. The value is an integer
ranging from 1 to 4094. The value of vlan-id2 must be greater than the value of vlan-id1.
The VLAN ID assigned to a group VLAN can be assigned to no other VLANIF interface, superVLAN, or sub-VLAN.
----End
3.7.4 Configuring a Separate VLAN for a Subordinate VLAN
A VLAN associated with separate ports is called a separate VLAN. Ports in a separate VLAN
cannot communicate with each other.
Context
Group VLANs and separate VLANs in one MUX VLAN cannot use the same VLAN ID.
Do as follows on a switching device that requires a separate VLAN:
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
vlan vlan-id
The view of a created principal VLAN is displayed.
Step 3 Run:
subordinate separate vlan-id
A separate VLAN is configured for a subordinate VLAN.
Group VLANs and separate VLANs in one MUX VLAN cannot use the same VLAN ID.
----End
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
88
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
3.7.5 Enabling the MUX VLAN Function on a Port
After the MUX VLAN function is enabled on a port, the principal VLAN and subordinate VLAN
can communicate with each other; ports in a group VLAN can communicate with each other;
ports in a separate VLAN cannot communicate with each other.
Context
Before the MUX VLAN function is enabled on a port, ensure that:
l
The port has been added to only one ordinary VLAN. If the port has been added to multiple
VLANs, the MUX VLAN function cannot be enabled on this port.
The port has been added to a principal or subordinate VLAN.
Do as follows on the switching device on which a port needs to be enabled with the MUX VLAN
function:
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
interface interface-type interface-number
The view of an Ethernet port connecting users is displayed.
Step 3 Run:
port mux-vlan enable
The MUX VLAN function is enabled.
The interface has been added only to a principal VLAN or a subordinate VLAN.
After being enabled with the MUX VLAN function, the port can no longer be configured with
VLAN mapping or VLAN stacking.
NOTE
l Disabling MAC address learning or limiting the number of learned MAC addresses on an interface
affects the MUX VLAN function on the interface.
l The MUX VLAN and port security functions cannot be enabled on the same interface.
l The MUX VLAN and MAC address authentication cannot be enabled on the same interface.
l The MUX VLAN and 802.1x authentication cannot be enabled on the same interface.
----End
3.7.6 Checking the Configuration
After a MUX VLAN is configured, you can check the principal VLAN ID, subordinate VLAN
ID, and VLAN type.
Prerequisite
The configurations of a MUX VLAN are complete.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
89
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
Procedure
Step 1 Run the display mux-vlan command to check information about the MUX VLAN.
----End
3.8 Configuring a Voice VLAN to Transmit Voice Data
A voice VLAN is used to transmit voice data.
3.8.1 Establishing the Configuration Task
Before configuring a voice VLAN, familiarize yourself with the applicable environment,
complete the pre-configuration tasks, and obtain the data required for the configuration. This
will help you complete the configuration task quickly and accurately.
Applicable Environment
Voice and non-voice data are transmitted on networks. Voice data is configured with a higher
priority than non-voice data to reduce the probability of the transmission delay and packet loss.
In most cases, an Access Control List (ACL) is configured to distinguish voice data from nonvoice data, and the Quality of Service (QoS) is used to ensure the transmission quality of voice
data.
Voice over IP (VoIP) phones are commonly used. If an ACL is configured to distinguish voice
data from non-voice data, and QoS is used to ensure the transmission quality of voice data, each
terminal needs to be configured with an ACL rule. This increases the network administrator's
workload and burdens maintenance.
The voice VLAN technique is introduced to solve the preceding problem.
After being enabled with the voice VLAN function, a device determines voice data based on
source MAC addresses of received frames, adds ports that receive voice data to a voice VLAN,
and automatically applies priority rules to ensure high priorities and good qualities of voice data.
This simplifies user configuration and facilitates management on voice data.
On the network shown in Figure 3-8, a user's High Speed Internet (HSI), VoIP, and Internet
Protocol Television (IPTV) services are connected to a switch. A voice VLAN can be configured
on the switch to implement QoS for voice data, prioritize voice data, and ensure the
communication quality.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
90
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
Figure 3-8 Networking diagram for configuring a voice VLAN
Server
Network
Voice VLAN
VLAN 10
Switch
LAN Switch2
LAN Switch1
HSI
VoIP
IPTV
HSI
VoIP
IPTV
Voice flow
Pre-configuration Tasks
Before configuring a voice VLAN, complete the following task:
l
Creating VLANs
Data Preparation
To configure a voice VLAN, you need the following data.
Issue 02 (2011-11-21)
No.
Data
Type and number of the port enabled with the voice VLAN function, voice VLAN
ID
The Organizationally Unique Identifier (OUI) address and mask of the voice VLAN
(Optional) Aging timer value of the voice VLAN
(Optional) 802.1p priority and DSCP value for the voice VLAN
(Optional) Mode in which the port is added to the voice VLAN
(Optional) Security mode of the voice VLAN
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
91
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
3.8.2 Enabling the Voice VLAN Function
After being enabled with the voice VLAN function, a device is able to identify voice data based
on source MAC addresses of received frames.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
interface interface-type interface-number
The view of a port connecting the device to users' voice devices is displayed.
Step 3 Run:
voice-vlan vlan-id enable
A voice VLAN is configured and the voice VLAN function is enabled on the port.
By default, the voice VLAN function is disabled on ports.
NOTE
l VLAN 1 cannot be configured as a voice VLAN.
l The voice VLAN and default VLAN on a port must be assigned different VLAN IDs to ensure that
every function works properly.
l Only one VLAN on a port can be configured as a voice VLAN at a time.
l If the voice VLAN configured on an interface works in automatic mode, you need to run the port linktype command to set the interface type to trunk, or hybrid.
l Before deleting a voice VLAN, run the undo voice-vlan enable command to disable the voice VLAN
function.
l The port enabled with the voice VLAN function cannot be configured with VLAN mapping, VLAN
stacking, or traffic policies.
----End
3.8.3 Configuring an OUI for a Voice VLAN
A voice VLAN-enabled port checks source MAC addresses of received frames. If the source
MAC addresses match OUIs, the frames are considered voice data.
Context
An OUI is a globally-unique identifier assigned by the Institute of Electrical and Electronics
Engineers (IEEE) to a specific equipment vendor. An OUI represents the first 24 bits of a binary
MAC address.
An OUI represents a MAC address segment that is obtained by performing the AND operation
between a 48-bit MAC address and a mask. For example, the MAC address is 1-1-1, and the
mask is FFFF-FF00-0000. The AND operation is performed between the MAC address and the
mask to obtain the OUI 0001-0000-0000. If the first 24 bits of the MAC address of a device are
the same as an OUI, a voice VLAN-enabled port considers the device as a voice device and data
from the device as voice data.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
92
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
voice-vlan mac-address
mac-address mask oui-mask [ description text ]
An OUI is configured.
l The mac-address value cannot be all 0s or a multicast or broadcast address.
l A device can be configured with a maximum of 16 OUIs. When the device is configured
with 16 OUIs, subsequent configurations will not take effect.
l When using the undo voice-vlan mac-address command to delete an OUI, specify the macaddress value in this command as the result of the AND operation by using the configured
MAC address and mask.
NOTE
When the source MAC address of a packet matches the OUI, the S5700 changes the priority of the packet
basing on the configuration of 3.8.5 (Optional) Configuring an 802.1p Priority and a DSCP Value for
the Voice VLAN to improve the transmission quality.
----End
3.8.4 (Optional) Setting an Aging Timer for a Voice VLAN
In automatic mode, a voice VLAN-enabled port learns source MAC addresses of frames from
voice devices, adds ports connecting the device to voice devices to a voice VLAN, and uses the
voice VLAN aging timer to control the number of ports in the voice VLAN.
Context
The aging timer of a voice VLAN is effective only when ports are automatically added to the
voice VLAN.
If a voice VLAN-enabled port does not receive voice data from a voice device before the aging
timer expires, the port will be automatically deleted from the voice VLAN. If the port receives
voice data from the voice device again, the port will be automatically added to the voice VLAN
and the aging timer will be reset.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
voice-vlan aging-time minutes
The aging timer is set for a voice VLAN.
The aging timer value ranges from 5 to 43200, in minutes. The default value is 1440 minutes.
----End
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
93
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
3.8.5 (Optional) Configuring an 802.1p Priority and a DSCP Value
for the Voice VLAN
Different 802.1p priorities and DiffServ Code Point (DSCP) values can be configured for
different voice VLANs, which makes voice service deployment more flexible.
Context
By default, the 802.1p priority and DSCP value for each voice VLAN are 6 and 46 respectively.
Manual configuration of the 802.1p priority and DSCP value will allow you to plan priorities
for different voice services at will.
NOTE
l The 802.1p priority is indicated by the value in the 3-bit PRI field in each 802.1Q VLAN frame. This
field determines the transmission priority for data packets when a switching device is congested.
l The DSCP value is indicated by the 6 bits in the Type of Service (ToS) field in the IPv4 packet header.
DSCP, as the signaling for DiffServ, is used for QoS guarantee on IP networks. The traffic controller
on the network gateway takes actions merely based on the information carried by the 6 bits.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
voice-vlan remark { 8021p 8021p-value | dscp dscp-value }
An 802.1p priority and a DSCP value are configured for a voice VLAN.
By default, the 802.1p priority and DSCP value for a voice VLAN are 6 and 46 respectively.
----End
3.8.6 (Optional) Configuring the Mode in Which Ports Are Added
to a Voice VLAN
On a switching device, only one VLAN on a port can be configured as a voice VLAN. Ports can
be added to the voice VLAN in either automatic or manual mode.
Context
Ports can be added to a voice VLAN in either of the following modes:
l
Automatic mode
A voice VLAN-enabled port learns source MAC addresses of frames from voice devices,
adds ports connecting the device to voice devices to a voice VLAN, and uses the voice
VLAN aging timer to control the number of ports in the voice VLAN. If a voice VLANenabled port does not receive voice data from a voice device before the aging timer expires,
the port will be automatically deleted from the voice VLAN. If the port receives voice data
from the voice device again, the port will be automatically added to the voice VLAN.
l
Issue 02 (2011-11-21)
Manual mode
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
94
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
After the voice VLAN function is enabled, ports connected to voice devices must be
manually added to a voice VLAN. Otherwise, the voice VLAN function does not take
effect.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
interface interface-type interface-number
The view of a port connecting the device to users' voice devices is displayed.
Step 3 Run:
voice-vlan mode { auto | manual }
The mode in which ports are added to a voice VLAN is configured.
By default, ports are automatically added to a voice VLAN.
l If the auto parameter is configured, ports will be automatically added to a voice VLAN.
l If the manual parameter is configured, ports will be manually added to a voice VLAN.
If trunk ports are connected to voice devices, run the port trunk allow-pass vlan
{ { vlan-id1 [ to vlan-id2 ] } &<1-10> | all } command to manually add these ports to a
voice VLAN.
If hybrid ports are connected to voice devices, do as follows as required:
Run the port hybrid untagged vlan { { vlan-id1 [ to vlan-id2 ] } &<1-10> | all }
command to manually add these ports to a voice VLAN in untagged mode.
Run the port hybrid tagged vlan { { vlan-id1 [ to vlan-id2 ] } &<1-10> | all }
command to manually add these ports to a voice VLAN in tagged mode.
NOTE
In Access ports cannot be automatically added to a voice VLAN. To add a port of the access type to the
voice VLAN, run the port link-type command to change the port type to trunk or hybrid.
----End
3.8.7 (Optional) Configuring the Working Mode for a Voice VLAN
A voice VLAN works in either security or ordinary mode to transmit merely voice data or both
voice and non-voice data.
Context
Based on the data filtering mechanism, a voice VLAN works in either security or ordinary mode:
l
Security mode
A voice VLAN-enabled inbound port transmits only frames of which the source MAC
addresses match OUIs configured on the device, discards the voice data not belong to the
current voice VLAN and the other data can be forwarded normally.
The security mode prevents a voice VLAN from being attacked by malicious data flows,
but consumes system resources to check frames.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
95
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
Ordinary mode
A voice VLAN-enabled inbound port transmits both voice and non-voice data. The port
does not compare source MAC addresses in received frames with configured OUIs,
exposing a voice VLAN to malicious attacks.
NOTE
Transmitting voice and service data at the same time in a voice VLAN is not recommended. If a voice
VLAN must transmit both voice and service data, ensure that the voice VLAN works in ordinary mode.
Table 3-8 shows how to process frames in different voice VLAN working modes.
Table 3-8 Frame processing in different voice VLAN working modes
Voice VLAN
Working Mode
Frame Processing Mode
Security mode
If the source MAC address of a frame and the OUI do not match,
the priority of the frame is not changed and the frame is prohibited
from forwarding in the voice VLAN.
Ordinary mode
If the source MAC address of a frame and the OUI do not match,
the priority of the frame is not changed and the frame is allowed to
be forwarded in the voice VLAN.
Procedure
l
Security mode
1.
Run the system-view command to enter the system view.
2.
Run the interface interface-type interface-number command to enter the view of a
port connecting the device to users' voice devices.
3.
Run the voice-vlan security enable command to configure the voice VLAN work in
security mode.
By default, a voice VLAN works in security mode.
Ordinary mode
1.
Run the system-view command to enter the system view.
2.
Run the interface interface-type interface-number command to enter the view of a
port connecting the device to users' voice devices.
3.
Run the undo voice-vlan security enable command to configure the voice VLAN
work in ordinary mode.
By default, a voice VLAN works in security mode.
----End
3.8.8 (Optional) Configuring a Port to Communicate with a Voice
Device of Another Vendor
The voice VLAN legacy function can be configured to allow Huawei datacom devices to identify
packets of proprietary protocols of other vendors.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
96
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
Context
After VoIP devices of some vendors are powered on, proprietary protocol packets but not DHCP
packets are sent to apply for IP addresses. To help Huawei datacom devices communicate with
voice devices of other vendors, you can enable the voice VLAN legacy function. This allows
Huawei devices to identify packets of proprietary protocols of other vendors.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
interface interface-type interface-number
The view of a port connecting the device to users' voice devices is displayed.
Step 3 Run:
voice-vlan legacy enable
The port is configured to communicate with a voice device of another vendor.
By default, ports on Huawei devices cannot communicate with voice devices of other vendors.
----End
3.8.9 Checking the Configuration
After a voice VLAN is configured, you can view information about the voice VLAN, including
the OUI, working mode, security mode or ordinary mode, aging timer value, the 802.1p priority
and DSCP value as well as the configuration of the port enabled with the voice VLAN function.
Prerequisite
The configurations of a voice VLAN are complete.
Procedure
l
Run the display voice-vlan [ vlan-id ] status command to check information about the
voice VLAN, including the working mode, security mode, aging timer value and the 802.1p
priority and DSCP value as well as the configuration of the port enabled with the voice
VLAN function.
Run the display voice-vlan oui command to check information about the OUI of the voice
VLAN, including the mask and description of the OUI.
----End
3.9 Configuring an mVLAN to Implement Integrated
Management
Configuring an mVLAN allows users to use the IP address of the VLANIF interface
corresponding to the mVLAN to log in to a management switch to manage devices attached to
the switch.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
97
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
3.9.1 Establishing the Configuration Task
Before configuring an mVLAN to implement integrated management, familiarize yourself with
the applicable environment, complete the pre-configuration tasks, and obtain the data required
for the configuration. This will help you complete the configuration task quickly and accurately.
Applicable Environment
An mVLAN can be configured to help a user use an NMS to manage indirectly-connected
devices.
After an mVLAN is configured, a user can use the IP address of the VLANIF interface
corresponding to the mVLAN to telnet to a management switch and manage devices attached
to the switch.
Pre-configuration Tasks
Before configuring an mVLAN, complete the following task:
l
Creating a VLAN
Data Preparation
To configure an mVLAN, you need the following data.
No.
Data
VLAN ID
3.9.2 Configuring an mVLAN
An mVLAN allows a user to use the IP address of the VLANIF interface corresponding to the
mVLAN to telnet to a management switch to manage devices attached to the switch.
Do as follows on the device that requires an mVLAN:
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
vlan vlan-id
The VLAN view is displayed.
Step 3 Run:
management-vlan
An mVLAN is configured.
Only a trunk or hybrid port can be added to an mVLAN.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
98
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
After the undo management-vlan command is used for an mVLAN, the mVLAN becomes an
ordinary VLAN, to which access, trunk, or hybrid ports can be added.
----End
3.9.3 Configuring a VLANIF Interface for an mVLAN
You need to use the IP address of the VLANIF interface corresponding to an mVLAN to telnet
to a management switch to manage attached devices.
Do as follows on the device that requires an mVLAN:
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
interface vlanif vlan-id
A VLANIF interface is created and the VLAIF interface view is displayed.
The ID of the VLANIF interface must be the ID of a configured mVLAN.
Step 3 Run:
ip address ip-address { mask | mask-length } [ sub ]
After assigning an IP address to the VLANIF interface, you can run the telnet command to log
in to a management switch to manage attached devices.
----End
3.9.4 Checking the Configuration
After an mVLAN is configured, you can check information about the mVLAN.
Prerequisite
The configurations of an mVLAN are complete.
Procedure
l
Run the display vlan command to check information about the mVLAN. The command
output shows information about the mVLAN in the line started with an asterisk sign (*).
----End
3.10 Maintaining VLAN
A command of clearing statistics helps to locate the faults in a VLAN.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
99
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
3.10.1 Clearing the Statistics of VLAN Packets
Before collecting traffic statistics in a specified time period on an interface, you need to reset
the original statistics on the interface.
Context
CAUTION
Statistics about VLAN packets cannot be restored after you clear it. So, confirm the action before
you use the command.
To clear the Statistics of VLAN Packets, run the following reset command in the user view:
Procedure
l
Run the reset vlan vlan-id statistics command to clear packets of a specified VLAN
statistics.
----End
3.11 Configuration Examples
This section provides VLAN configuration examples in various usage scenarios.
3.11.1 Example for Assigning VLANs Based on Ports
It is easy to divide a LAN into VLANs based on ports. After ports are added to different VLANs,
users in the same VLAN can directly communicate with each other, whereas users in different
VLANs cannot directly communicate with each other.
Networking Requirements
As shown in Figure 3-9, an enterprise has multiple departments. The enterprise allows
departments in charge of the same service to communicate with each other, and want to isolate
the departments in charge of different services.
The requirements are as follows:
l
Department 1 and Department 2 are isolated from Department 3 and Department 4.
Department 1 and Department 2 can communicate with each other.
Department 3 and Department 4 can communicate with each other.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
100
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
Figure 3-9 Port-based VLAN assignment
Network
GE0/0/4
GE0/0/1
GE0/0/2
Switch
GE0/0/3
Group32 Department 4
Department 1 Department 2 Department
VLAN 3
VLAN 2
VLAN 3
Configuration Roadmap
The configuration roadmap is as follows:
1.
Create VLANs and determine mappings between employees and VLANs.
2.
Configure port types to determine the device connected to each port.
3.
Add the ports connected to department 1 and department 2 to VLAN 2 and the ports
connected to department 3 and department 4 to VLAN 3 to prevent employees in department
1 or department 2 from communicating with employees in department 3 or department 4.
Data Preparation
To complete the configuration, you need the following data:
l
GE 0/0/1 and GE 0/0/2 belong to VLAN 2.
GE 0/0/3 and GE 0/0/4 belong to VLAN 3.
Procedure
Step 1 Configure the Switch.
# Create VLAN 2.
<Quidway> system-view
[Quidway] vlan 2
[Quidway-vlan2] quit
# Set the link type of GE 0/0/1 to trunk and add GE 0/0/1 to VLAN 2.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
101
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
[Quidway] interface gigabitethernet 0/0/1
[Quidway-GigabitEthernet0/0/1] port link-type trunk
[Quidway-GigabitEthernet0/0/1] port trunk allow-pass vlan 2
[Quidway-GigabitEthernet0/0/1] quit
# Set the link type of GE 0/0/2 to trunk and add GE 0/0/2 to VLAN 2.
[Quidway]interface gigabitethernet 0/0/2
[Quidway-GigabitEthernet0/0/2] port link-type trunk
[Quidway-GigabitEthernet0/0/2] port trunk allow-pass vlan 2
[Quidway-GigabitEthernet0/0/2] quit
# Create VLAN 3.
[Quidway] vlan 3
[Quidway-vlan3] quit
# Set the link type of GE 0/0/3 to trunk and add GE 0/0/3 to VLAN 3.
[Quidway] interface gigabitethernet 0/0/3
[Quidway-GigabitEthernet0/0/3] port link-type trunk
[Quidway-GigabitEthernet0/0/3] port trunk allow-pass vlan 3
[Quidway-GigabitEthernet0/0/3] quit
# Set the link type of GE 0/0/4 to trunk and add GE 0/0/4 to VLAN 3.
[Quidway] interface gigabitethernet 0/0/4
[Quidway-GigabitEthernet0/0/4] port link-type trunk
[Quidway-GigabitEthernet0/0/4] port trunk allow-pass vlan 3
[Quidway-GigabitEthernet0/0/4] quit
Step 2 Verify the configuration.
Ping any host in VLAN 3 from a host in VLAN 2. The ping operation fails. This indicates that
Department 1 and Department 2 are isolated from Department 3 and Department 4.
Ping any host in Department 2 from a host in Department 1. The ping operation is successful.
This indicates that Department 1 and Department 2 can communicate with each other.
Ping any host in Department 4 from a host in Department 3. The ping operation is successful.
This indicates that Department 3 and Department 4 can communicate with each other.
----End
Configuration Files
The following lists the configuration file of the Switch.
#
sysname Quidway
#
vlan batch 2 to 3
#
interface GigabitEthernet0/0/1
port link-type trunk
port trunk allow-pass vlan 2
#
interface GigabitEthernet0/0/2
port link-type trunk
port trunk allow-pass vlan 2
#
interface GigabitEthernet0/0/3
port link-type trunk
port trunk allow-pass vlan 3
#
interface GigabitEthernet0/0/4
port link-type trunk
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
102
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
port trunk allow-pass vlan 3
#
return
3.11.2 Example for Assigning VLANs based on MAC Addresses
MAC address-based VLAN assignment is applicable only to simple networks where network
adapters are not changed frequently.
Networking Requirements
On a company intranet, the network administrator adds the PCs in a department to the same
VLAN. To improve information security, only employees is this department are allowed to
access the intranet.
As shown in Figure 3-10, only PC1, PC2, and PC3 are allowed to access the intranet through
SwitchA and Switch.
Figure 3-10 MAC address-based VLAN assignment
Network
GE0/0/2
Switch
GE0/0/1
GE0/0/1
SwitchA
MAC:22-22-22 MAC:33-33-33 MAC:44-44-44
PC3
PC2
PC1
VLAN 10
Configuration Roadmap
The configuration roadmap is as follows:
1.
Create VLANs and determine which VLAN the PCs of employees belong to.
2.
Add Ethernet interfaces to VLANs.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
103
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3.
3 VLAN Configuration
Associate MAC addresses of PC1, PC2, and PC3 with the specified VLAN so that the
Switch can assign the VLAN to packets according to their source MAC addresses.
Data Preparation
To complete the configuration, you need the following data:
l
PVID of GE0/0/1 on the Switch: 100
Mode in which GE0/0/1 of the Switch needs to be added to VLAN 10: untagged mode
Mode in which GE0/0/2 of the Switch needs to be added to VLAN 10: tagged mode
VLAN configuration of interfaces on the SwitchA: default VLAN configuration (all
interfaces are added to VLAN 1 in untagged mode)
MAC addresses of PC1, PC2, and PC3 that need to be associated with VLAN 10
Procedure
Step 1 Configure the Switch.
# Create VLANs.
<Quidway> system-view
[Quidway] vlan batch 10 100
# Set the PVID of interfaces and add interfaces to the VLANs.
[Quidway] interface gigabitethernet
[Quidway-GigabitEthernet0/0/1] port
[Quidway-GigabitEthernet0/0/1] port
[Quidway-GigabitEthernet0/0/1] quit
[Quidway] interface gigabitethernet
[Quidway-GigabitEthernet0/0/2] port
[Quidway-GigabitEthernet0/0/2] quit
0/0/1
hybrid pvid vlan 100
hybrid untagged vlan 10
0/0/2
hybrid tagged vlan 10
# Associate MAC addresses of PC1, PC2, and PC3 with VLAN 10.
[Quidway] vlan 10
[Quidway-Vlan10] mac-vlan mac-address 22-22-22
[Quidway-Vlan10] mac-vlan mac-address 33-33-33
[Quidway-Vlan10] mac-vlan mac-address 44-44-44
[Quidway-Vlan10] quit
# Enable MAC address-based VLAN assignment on GE0/0/1.
[Quidway] interface gigabitethernet 0/0/1
[Quidway-GigabitEthernet0/0/1] mac-vlan enable
[Quidway-GigabitEthernet0/0/1] quit
Step 2 Verify the configuration.
PC1, PC2, and PC3 can access the intranet, whereas other PCs cannot access the intranet.
----End
Configuration Files
Configuration file of the Switch
#
sysname Quidway
#
vlan batch 10 100
#
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
104
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
vlan 10
mac-vlan mac-address 0022-0022-0022
mac-vlan mac-address 0033-0033-0033
mac-vlan mac-address 0044-0044-0044
#
interface GigabitEthernet0/0/1
port hybrid pvid vlan 100
port hybrid untagged vlan 10
mac-vlan enable
#
interface GigabitEthernet0/0/2
port hybrid tagged vlan 10
#
return
3.11.3 Example for Assigning VLANs Based on IP Subnets
After a LAN is divided into VLANs based on IP subnets, frames from a network segment or IP
address are transmitted in a specified VLAN. This reduces the configuration workload and
facilitates network management.
Networking Requirements
A company has multiple services, including IPTV, VoIP, and Internet access. Each service uses
a unique IP address. Packets of the same service must be transmitted in the same VLAN, and
packets of different services must be transmitted in different VLANs.
On the network shown in Figure 3-11, the Switch receives Internet, IPTV, and voice services
from users with diverse IP addresses. Packets of different services need to be transmitted in
different VLANs, and packets of each service need to be sent to a specified remote server.
Figure 3-11 IP subnet-based VLAN assignment
IPTV
server
Voice
Network
Internet
RouterB
RouterA
RouterC
GE0/0/3
GE0/0/2
GE0/0/4
Switch
GE0/0/1
192.168.1.2
Issue 02 (2011-11-21)
192.168.3.2
192.168.2.2
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
105
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
Configuration Roadmap
The configuration roadmap is as follows:
1.
Create VLANs and determine which VLAN each service belongs to.
2.
Associate IP subnets with VLANs.
The Switch assigns VLANs to frames based on their source IP addresses. When new nodes
are deployed on the network, the Switch adds each new node to a corresponding VLAN
based on the network address of the node.
3.
Configure a port to allow frames with specified VLAN IDs to pass through.
4.
Configure the highest priority for IP subnet-based VLAN assignment.
5.
Enable IP subnet-based VLAN assignment.
Data Preparation
To complete the configuration, you need the following data:
l
VLANs to which GE 0/0/1 needs to be added in untagged mode: VLAN 100, VLAN 200,
and VLAN 300
VLANs to which GE 0/0/2, GE 0/0/3, and GE 0/0/4 need to be added in tagged mode
respectively: VLAN 100, VLAN 200, and VLAN 300
Configuration data for IP subnet-based VLAN assignment, as shown in Table 3-9
Table 3-9 IP subnet-based VLAN assignment data
VLAN ID
IP Subnet
Index
Source IP
Address
Subnet Mask
802.1p Priority
100
192.168.1.2
255.255.255.0
200
192.168.2.2
255.255.255.0
300
192.168.3.2
255.255.255.0
Procedure
Step 1 Create VLANs.
# Create VLAN 100, VLAN 200, and VLAN 300 on the Switch.
<Quidway> system-view
[Quidway] vlan batch 100 200 300
Step 2 Configure interfaces.
# Set the link type of GE 0/0/1 to hybrid and add it to VLAN 100, VLAN 200, and VLAN 300.
[Quidway] interface gigabitethernet 0/0/1
[Quidway-GigabitEthernet0/0/1] port link-type hybrid
[Quidway-GigabitEthernet0/0/1] port hybrid untagged vlan 100 200 300
[Quidway-GigabitEthernet0/0/1] quit
# Add GE 0/0/2 of the Switch to VLAN 100.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
106
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
[Quidway] interface gigabitethernet 0/0/2
[Quidway-GigabitEthernet0/0/2] port link-type trunk
[Quidway-GigabitEthernet0/0/2] port trunk allow-pass vlan 100
[Quidway-GigabitEthernet0/0/2] quit
# Add GE 0/0/3 of the Switch to VLAN 200.
[Quidway] interface gigabitethernet 0/0/3
[Quidway-GigabitEthernet0/0/3] port link-type trunk
[Quidway-GigabitEthernet0/0/3] port trunk allow-pass vlan 200
[Quidway-GigabitEthernet0/0/3] quit
# Add GE 0/0/4 of the Switch to VLAN 300.
[Quidway] interface gigabitethernet 0/0/4
[Quidway-GigabitEthernet0/0/4] port link-type trunk
[Quidway-GigabitEthernet0/0/4] port trunk allow-pass vlan 300
[Quidway-GigabitEthernet0/0/4] quit
# Enable the IP subnet-based VLAN function on GE 0/0/1.
[Quidway] interface gigabitethernet 0/0/1
[Quidway-GigabitEthernet0/0/1] ip-subnet-vlan enable
[Quidway-GigabitEthernet0/0/1] quit
Step 3 Configure IP subnet-based VLAN assignment.
# Associate 192.168.1.2 to VLAN 100 and set the 802.1p priority of VLAN 100 to 2.
[Quidway] vlan 100
[Quidway-vlan100] ip-subnet-vlan 1 ip 192.168.1.2 24 priority 2
[Quidway-vlan100] quit
# Associate 192.168.2.2 to VLAN 200 and set the 802.1p priority of VLAN 200 to 3.
[Quidway] vlan 200
[Quidway-vlan200] ip-subnet-vlan 1 ip 192.168.2.2 24 priority 3
[Quidway-vlan200] quit
# Associate IP subnet 192.168.3.2 to VLAN 100 and set the 802.1p priority of VLAN 300 to 4.
[Quidway] vlan 300
[Quidway-vlan300] ip-subnet-vlan 1 ip 192.168.3.2 24 priority 4
[Quidway-vlan300] quit
Step 4 Verify the configuration.
Run the display ip-subnet-vlan vlan all command on the Switch. The following information
is displayed:
[Quidway] display ip-subnet-vlan vlan all
---------------------------------------------------------------Vlan
Index
IpAddress
SubnetMask
Priority
---------------------------------------------------------------100
1
192.168.1.2
255.255.255.0
2
200
1
192.168.2.2
255.255.255.0
3
300
1
192.168.3.2
255.255.255.0
4
---------------------------------------------------------------ip-subnet-vlan count: 3
total count: 3
----End
Configuration Files
l
Configuration file of the Switch
#
sysname Quidway
#
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
107
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
vlan batch 100 200 300
#
vlan 100
ip-subnet-vlan 1 ip 192.168.1.2 255.255.255.0 priority 2
#
vlan 200
ip-subnet-vlan 1 ip 192.168.2.2 255.255.255.0 priority 3
#
vlan 300
ip-subnet-vlan 1 ip 192.168.3.2 255.255.255.0 priority 4
#
interface GigabitEthernet0/0/1
port hybrid untagged vlan 100 200 300
ip-subnet-vlan enable
#
interface GigabitEthernet0/0/2
port link-type trunk
port trunk allow-pass vlan 100
#
interface GigabitEthernet0/0/3
port link-type trunk
port trunk allow-pass vlan 200
#
interface GigabitEthernet0/0/4
port link-type trunk
port trunk allow-pass vlan 300
#
return
3.11.4 Example for Assigning VLANs Based on Protocols
Protocol-based VLAN assignment reduces manual configuration workload and allows the
administrator to add and move network devices flexibly.
Networking Requirements
A company has multiple services, including IPTV, VoIP, and Internet access. Each service uses
a unique protocol. To facilitate network management and reduce manual VLAN configuration
workload, each service is added to a different VLAN.
As shown in Figure 3-12, the Switch receives packets of multiple services that use different
protocols. Users in VLAN 10 use IPv4 to communicate with remote users, and users in VLAN
20 use IPv6 to communicate with the servers. The Switch needs to assign VLANs to packets of
different services and transmit packets with different VLAN IDs to different servers.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
108
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
Figure 3-12 Protocol-based VLAN assignment
Voice
Network
RouterA
Internet
RouterB
GE0/0/2
GE0/0/3
Switch
GE0/0/1
IPv4
VLAN 10
IPv6
VLAN 20
Configuration Roadmap
The configuration roadmap is as follows:
1.
Create VLANs and determine which VLAN each service belongs to.
2.
Associate protocols with VLANs.
The Switch assigns VLAN IDs to framed based on the protocol or protocol suite. As long
as the protocols of user devices remain unchanged, users do not need to be added to new
VLANs when they move to other physical locations, assigned other network segments, or
their network adapters are changed.
3.
Configure a port to allow frames with specified VLAN IDs to pass through.
4.
Associate ports with VLANs.
After the Switch receives a frame of a specified protocol, it assigns the VLAN ID associated
with the protocol to the frame.
Data Preparation
To complete the configuration, you need the following data:
l
VLANs to which GE0/0/1 of the Switch needs to be added in untagged mode: VLAN 10
and VLAN 20
VLANs to which GE0/0/2 and GE0/0/3 of the Switch need to be added in tagged mode:
VLAN 10 and VLAN 20
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
109
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
Protocol associated with each VLAN
VLAN 10: IPv4
VLAN 20: IPv6
Procedure
Step 1 Create VLANs.
# Configure the Switch.
<Quidway> system-view
[Quidway] sysname Switch
[Switch] vlan batch 10 20
Step 2 Configure protocol-based VLANs.
# Associate IPv4 with VLAN 10.
[Switch] vlan 10
[Switch-vlan10] protocol-vlan ipv4
[Switch-vlan10] quit
# Associate IPv6 with VLAN 20.
[Switch] vlan 20
[Switch-vlan20] protocol-vlan ipv6
[Switch-vlan20] quit
Step 3 Associate interfaces with protocol-based VLANs.
# Associate GE0/0/1 with VLAN 10 and set the 802.1p priority of VLAN 10 to 5.
[Switch] interface gigabitethernet 0/0/1
[Switch-GigabitEthernet0/0/1] protocol-vlan vlan 10 all priority 5
# Associate GE0/0/1 with VLAN 20 and set the 802.1p priority of VLAN 20 to 6.
[Switch-GigabitEthernet0/0/1] protocol-vlan vlan 20 all priority 6
[Switch-GigabitEthernet0/0/1] quit
Step 4 Configure interfaces.
# Add GE0/0/1 to VLAN 10 and VLAN 20 so that GE0/0/1 allows packets of VLAN 10 and
VLAN 20 to pass through.
[Switch] interface gigabitethernet 0/0/1
[Switch-GigabitEthernet0/0/1] port link-type hybrid
[Switch-GigabitEthernet0/0/1] port hybrid untagged vlan 10 20
[Switch-GigabitEthernet0/0/1] quit
# Add GE0/0/2 to VLAN 10 so that GE0/0/2 allows packets of VLAN 10 to pass through.
[Switch] interface gigabitethernet 0/0/2
[Switch-GigabitEthernet0/0/2] port link-type trunk
[Switch-GigabitEthernet0/0/2] port trunk allow-pass vlan 10
[Switch-GigabitEthernet0/0/2] quit
# Add GE0/0/3 to VLAN 20 so that GE0/0/3 allows packets of VLAN 20 to pass through.
[Switch] interface gigabitethernet 0/0/3
[Switch-GigabitEthernet0/0/3] port link-type trunk
[Switch-GigabitEthernet0/0/3] port trunk allow-pass vlan 20
[Switch-GigabitEthernet0/0/3] quit
Step 5 Verify the configuration.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
110
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
After you complete the configuration, run the display protocol-vlan interface all command to
view the protocol-based VLAN assignment on GE0/0/1.
<Switch> display protocol-vlan interface all
------------------------------------------------------------------------------Interface
VLAN
Index
Protocol Type
Priority
------------------------------------------------------------------------------GigabitEthernet0/0/1
10
0
ipv4
5
GigabitEthernet0/0/1
20
0
ipv6
6
----End
Configuration Files
l
Configuration file of the Switch
#
sysname Switch
#
vlan batch 10 20
#
vlan 10
protocol-vlan 0 ipv4
vlan 20
protocol-vlan 0 ipv6
#
interface GigabitEthernet0/0/1
port hybrid untagged vlan 10 20
protocol-vlan vlan 10 0 priority 5
protocol-vlan vlan 20 0 priority 6
#
interface GigabitEthernet0/0/2
port link-type trunk
port trunk allow-pass vlan 10
#
interface GigabitEthernet0/0/3
port link-type trunk
port trunk allow-pass vlan 20
#
return
3.11.5 Example for Implementing Inter-VLAN Communication
Using VLANIF Interfaces
A Layer 3 switch can replace a router to implement communication between VLANs using
VLANIF interfaces.
Networking Requirements
Departments of an enterprise are located on different network segments and use the same
services, such as Internet access and VoIP. The departments are different VLANs, so interVLAN communication must be implemented.
As shown in Figure 3-13, Department 1 and Department 2 use the same service, but they belong
to different VLANs and network segments. Users in Department 1 and Department 2 need to
communicate with each other.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
111
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
Figure 3-13 Communication between VLANs using VLANIF interfaces
Switch
GE0/0/1
SwitchA
GE0/0/2
VLAN 10
Department1
GE0/0/1
GE0/0/3
VLAN 20
Department2
PC1
10.10.10.2/24
PC2
20.20.20.2/24
Configuration Roadmap
The configuration roadmap is as follows:
1.
Create VLANs on the switches for different departments.
2.
Add Layer 2 interfaces to the VLANs so that packets of the VLANs can pass through the
Layer 2 interfaces.
3.
On the Layer 3 switch (Switch), create VLANIF interfaces and configure IP addresses for
the VLANIF interfaces to implement Layer 3 communication.
NOTE
To implement communication between VLANs, hosts in each VLAN must use the IP address of the
corresponding VLANIF interface as the gateway address.
Data Preparation
To complete the configuration, you need the following data:
l
VLANs to which GE0/0/1 of the Switch belongs: VLAN 10 and VLAN 20
IP address of VLANIF 10 on the Switch: 10.10.10.1/24
IP address of VLANIF 20 on the Switch: 20.20.20.1/24
VLANs to which GE0/0/1of SwitchA belongs: VLAN 10 and VLAN 20
VLAN to which GE0/0/2 of SwitchA belongs: VLAN 10
VLANs to which GE0/0/3 of SwitchA belongs: VLAN 20
Procedure
Step 1 # Configure the Switch.
# Create VLANs.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
112
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
<Quidway> system-view
[Quidway] vlan batch 10 20
# Add GE0/0/1 to VLANs.
[Quidway] interface gigabitethernet 0/0/1
[Quidway-GigabitEthernet0/0/1] port link-type trunk
[Quidway-GigabitEthernet0/0/1] port trunk allow-pass vlan 10 20
[Quidway-GigabitEthernet0/0/1] quit
# Assign IP addresses to VLANIF interfaces.
[Quidway] interface vlanif 10
[Quidway-Vlanif10] ip address 10.10.10.1 24
[Quidway-Vlanif10] quit
[Quidway] interface vlanif 20
[Quidway-Vlanif20] ip address 20.20.20.1 24
[Quidway-Vlanif20] quit
Step 2 Configure SwitchA.
# Create VLANs.
<Quidway> system-view
[Quidway] vlan batch 10 20
# Add interfaces to VLANs.
[Quidway] interface gigabitethernet
[Quidway-GigabitEthernet0/0/1] port
[Quidway-GigabitEthernet0/0/1] port
[Quidway-GigabitEthernet0/0/1] quit
[Quidway] interface gigabitethernet
[Quidway-GigabitEthernet0/0/2] port
[Quidway-GigabitEthernet0/0/2] port
[Quidway-GigabitEthernet0/0/2] quit
[Quidway] interface gigabitethernet
[Quidway-GigabitEthernet0/0/2] port
[Quidway-GigabitEthernet0/0/2] port
[Quidway-GigabitEthernet0/0/3] quit
0/0/1
link-type trunk
trunk allow-pass vlan 10 20
0/0/2
link-type access
default vlan 10
0/0/3
link-type access
default vlan 20
Step 3 Verify the configuration.
On PC1 in VLAN 10, set the default gateway address to 10.10.10.1/24 (IP address of VLANIF
10).
On PC2 in VLAN 20, set the default gateway address to 20.20.20.1/24 (IP address of VLANIF
20).
When the preceding configurations are complete, PC1 and PC2 can communicate with each
other.
----End
Configuration Files
Configuration file of the Switch
#
sysname Quidway
#
vlan batch 10 20
#
interface Vlanif10
ip address 10.10.10.1 255.255.255.0
#
interface Vlanif20
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
113
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
ip address 20.20.20.1 255.255.255.0
#
interface GigabitEthernet0/0/1
port link-type trunk
port trunk allow-pass vlan 10 20
#
return
Configuration file of SwitchA
#
sysname Quidway
#
vlan batch 10 20
#
interface GigabitEthernet0/0/1
port link-type trunk
port trunk allow-pass vlan 10 20
#
interface GigabitEthernet0/0/2
port link-type access
port default vlan 10
#
interface GigabitEthernet0/0/3
port link-type access
port default vlan 20
#
return
3.11.6 Example for Configuring VLAN Aggregation
This example illustrates how to implement communication between VLANs with fewer IP
addresses.
Networking Requirements
An enterprise has multiple departments in the same network segment. To improve service
security, different departments are added to different VLANs. Employees in different
departments need to communicate with each other.
As shown in Figure 3-14, the R&D department and test department belong to different VLANs
and need to communicate with each other.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
114
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
Figure 3-14 VLAN aggregation
Switch
GE0/0/1
GE0/0/3
GE0/0/2
GE0/0/4
VLAN2
VLAN3
VLAN4
VLANIF4:100.1.1.12/24
VLAN 2
VLAN 3
Development
Department
Test
Department
Configuration Roadmap
The configuration roadmap is as follows:
1.
Add interfaces of the Switch to sub-VLANs.
2.
Add the sub-VLANs to a super-VLAN.
3.
Configure the IP address for the super-VLAN.
4.
Configure proxy ARP for the super-VLAN.
Data Preparation
To complete the configuration, you need the following data:
l
VLAN to which GE 0/0/1 and GE 0/0/2 belong: VLAN 2
VLAN to which GE 0/0/3 and GE 0/0/4 belong: VLAN 3
Super-VLAN: VLAN 4
IP address of the super-VLAN: 100.1.1.12
Procedure
Step 1 Set the interface type.
# Configure GE 0/0/1 as an access interface.
<Quidway> system-view
[Quidway] interface gigabitethernet 0/0/1
[Quidway-GigabitEthernet0/0/1] port link-type access
[Quidway-GigabitEthernet0/0/1] quit
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
115
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
# Configure GE 0/0/2 as an access interface.
<Quidway> system-view
[Quidway] interface gigabitethernet 0/0/2
[Quidway-GigabitEthernet0/0/2] port link-type access
[Quidway-GigabitEthernet0/0/2] quit
# Configure GE 0/0/3 as an access interface.
<Quidway> system-view
[Quidway] interface gigabitethernet 0/0/3
[Quidway-GigabitEthernet0/0/3] port link-type access
[Quidway-GigabitEthernet0/0/3] quit
# Configure GE 0/0/4 as an access interface.
<Quidway> system-view
[Quidway] interface gigabitethernet 0/0/4
[Quidway-GigabitEthernet0/0/4] port link-type access
[Quidway-GigabitEthernet0/0/4] quit
Step 2 Configure VLAN 2.
# Create VLAN 2.
[Quidway] vlan 2
# Add GE 0/0/1 and GE 0/0/2 to VLAN 2.
[Quidway-vlan2] port gigabitethernet 0/0/1 0/0/2
[Quidway-vlan2] quit
Step 3 Configure VLAN 3.
# Create VLAN 3.
[Quidway] vlan 3
# Add GE 0/0/3 and GE 0/0/4 to VLAN 3.
[Quidway-vlan3] port gigabitethernet 0/0/3 0/0/4
[Quidway-vlan3] quit
Step 4 Configure VLAN 4.
# Configure the super-VLAN.
[Quidway] vlan 4
[Quidway-vlan4] aggregate-vlan
[Quidway-vlan4] access-vlan 2 to 3
# Configure the VLANIF interface.
[Quidway] interface vlanif 4
[Quidway-Vlanif4] ip address 100.1.1.12 255.255.255.0
[Quidway-Vlanif4] quit
Step 5 Configure the PCs.
Configure an IP address for each PC. Ensure that the PC IP addresses are in the same network
segment as VLAN 4.
When the configuration is complete, the PCs and the Switch can ping each other, but the PCs in
VLAN 2 and the PCs in VLAN 3 cannot ping each other.
Step 6 Configure proxy ARP.
[Quidway] interface vlanif 4
[Quidway-Vlanif4] arp-proxy inter-sub-vlan-proxy enable
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
116
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
Step 7 Verify the configuration.
When the configuration is complete, the PCs in VLAN 2 and VLAN 3 can ping each other.
----End
Configuration Files
Configuration file of the Switch
#
sysname Quidway
#
vlan batch 2 to 4
#
vlan 4
aggregate-vlan
access-vlan 2 to 3
#
interface Vlanif4
ip address 100.1.1.12 255.255.255.0
arp-proxy inter-sub-vlan-proxy enable
#
interface GigabitEthernet0/0/1
port link-type access
port default vlan 2
#
interface GigabitEthernet0/0/2
port link-type access
port default vlan 2
#
interface GigabitEthernet0/0/3
port link-type access
port default vlan 3
#
interface GigabitEthernet0/0/4
port link-type access
port default vlan 3
#
return
3.11.7 Example for Configuring MUX VLAN
MUX VLAN isolates Layer 2 traffic of different interfaces in a VLAN. It allows some employees
of an enterprise to communicate with each other and isolates other employees from each other.
Networking Requirements
On an enterprise network shown in Figure 3-15, all employees can access the enterprise server.
Some employees need to communicate with each other, whereas some employees must be
isolated each other.
To meet these requirements, the administrator can add employees that need to be isolated to
different VLANs, and configure inter-VLAN communication to allow employees to access the
enterprise server. However, if the enterprise has a large number of employees, this method wastes
VLAN IDs and imposes additional configuration workload on the network administrator.
MUX VLAN can be configured on the Switch to meet the enterprise's requirements using fewer
VLAN IDs. In addition, MUX VLAN reduces the configuration workload of the network
administrator, and facilitates network maintenance.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
117
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
Figure 3-15 MUX VLAN configuration
Switch
GE0/0/1
GE0/0/2
GE0/0/3 GE0/0/4
GE0/0/5
HostB HostC
HostD HostE
HostA
VLAN3
VLAN4
VLAN2
Configuration Roadmap
The configuration roadmap is as follows:
1.
Configure the principal VLAN.
2.
Configure the group VLAN.
3.
Configure the separate VLAN.
4.
Add interfaces to the VLANs and enable the MUX VLAN function.
Data Preparation
To complete the configuration, you need the following data:
l
VLAN to which GE 0/0/1 belongs: VLAN 2
VLAN to which GE 0/0/2 and GE 0/0/3 belong: VLAN 3
VLAN to which GE 0/0/4 and GE 0/0/5 belong: VLAN 4
Procedure
Step 1 Configure the MUX VLAN.
# Create VLAN 2, VLAN 3, and VLAN 4.
<Quidway> system-view
[Quidway] vlan batch 2 3 4
[Quidway] quit
# Configure the principal VLAN, subordinate VLANs, and interfaces.
<Quidway> system-view
[Quidway] vlan 2
[Quidway-vlan2] mux-vlan
[Quidway-vlan2] subordinate group 3
[Quidway-vlan2] subordinate separate 4
[Quidway-vlan2] quit
[Quidway] interface gigabitethernet 0/0/1
[Quidway-GigabitEthernet0/0/1] port link-type access
[Quidway-GigabitEthernet0/0/1] port default vlan 2
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
118
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
[Quidway-GigabitEthernet0/0/1] port
[Quidway-GigabitEthernet0/0/1] quit
[Quidway] interface gigabitethernet
[Quidway-GigabitEthernet0/0/2] port
[Quidway-GigabitEthernet0/0/2] port
[Quidway-GigabitEthernet0/0/2] port
[Quidway-GigabitEthernet0/0/2] quit
[Quidway] interface gigabitethernet
[Quidway-GigabitEthernet0/0/3] port
[Quidway-GigabitEthernet0/0/3] port
[Quidway-GigabitEthernet0/0/3] port
[Quidway-GigabitEthernet0/0/3] quit
[Quidway] interface gigabitethernet
[Quidway-GigabitEthernet0/0/4] port
[Quidway-GigabitEthernet0/0/4] port
[Quidway-GigabitEthernet0/0/4] port
[Quidway-GigabitEthernet0/0/4] quit
[Quidway] interface gigabitethernet
[Quidway-GigabitEthernet0/0/5] port
[Quidway-GigabitEthernet0/0/5] port
[Quidway-GigabitEthernet0/0/5] port
[Quidway-GigabitEthernet0/0/5] quit
3 VLAN Configuration
mux-vlan enable
0/0/2
link-type access
default vlan 3
mux-vlan enable
0/0/3
link-type access
default vlan 3
mux-vlan enable
0/0/4
link-type access
default vlan 4
mux-vlan enable
0/0/5
link-type access
default vlan 4
mux-vlan enable
Step 2 Verify the configuration.
l Host A can ping Hosts B to E. Hosts B to E can also ping Host A.
l Host B and Host C can ping each other.
l Host D and Host E cannot ping each other.
l Host B and Host C cannot ping Host D or host E. Host D and Host E cannot ping Host B or
Host C.
----End
Configuration Files
Configuration file of the Switch
#
sysname Quidway
#
vlan batch 2 to 4
#
vlan 2
mux-vlan
subordinate group 3
subordinate separate 4
#
interface GigabitEthernet0/0/1
port link-type access
port default vlan 2
port mux-vlan enable
#
interface GigabitEthernet0/0/2
port link-type access
port default vlan 3
port mux-vlan enable
#
interface GigabitEthernet0/0/3
port link-type access
port default vlan 3
port mux-vlan enable
#
interface GigabitEthernet0/0/4
port link-type access
port default vlan 4
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
119
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
port mux-vlan enable
#
interface GigabitEthernet0/0/5
port link-type access
port default vlan 4
port mux-vlan enable
#
return
3.11.8 Example for Configuring a Voice VLAN in Auto Mode
In this example, voice traffic is transmitted within a specific VLAN (voice VLAN). If a voice
device fails or exits from the network, the interface connected to the voice device will exit from
the voice VLAN after a specified period of time.
Networking Requirements
Data flows of the high speed Internet (HSI), VoIP, and IPTV services are transmitted on a
network. Users require high quality of VoIP services; therefore, voice data flows must be
transmitted with a high priority.
As shown in Figure 3-16, after a voice VLAN is configured on the Switch, the Switch checks
whether a data flow received by GigabitEthernet0/0/1 is a voice data flow based on the source
MAC address of the flow. If the data flow is a voice data flow, the Switch changes the priority
of the flow and transmits it in the voice VLAN. If not, the Switch transmits the flow in a common
VLAN without changing the priority of the flow. GigabitEthernet0/0/1 needs to be automatically
added to or deleted from the voice VLAN.
Figure 3-16 Configuring a voice VLAN in auto mode
DHCP Server
Internet
Switch
GE0/0/1
LAN Switch
HSI
Issue 02 (2011-11-21)
VoIP
IPTV
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
120
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
Configuration Roadmap
The configuration roadmap is as follows:
1.
Create VLANs.
2.
Configure the link type and default VLAN of the interface.
3.
Enable the voice VLAN on the interface.
4.
Set the voice VLAN mode to auto.
5.
Set the OUI of the voice VLAN.
6.
Set the aging time of the voice VLAN.
7.
Set the security mode of the voice VLAN.
Data Preparation
To complete the configuration, you need the following data:
l
Voice VLAN and VLAN through which the IP phone applies for an IP address: VLAN 2
and VLAN 6
OUI and mask: 0011-2200-0000 and ffff-ff00-0000
Aging time of the voice VLAN: 100 minutes
The default VLAN of GigabitEthernet 0/0/1 is VLAN 6.
Procedure
Step 1 Create VLANs and configure the interface on the Switch.
# Create VLAN 2 and VLAN 6.
<Quidway> system-view
[Quidway] vlan batch 2 6
# Configure the link type and default VLAN of the interface.
[Quidway] interface gigabitethernet 0/0/1
[Quidway-GigabitEthernet0/0/1] port hybrid pvid vlan 6
[Quidway-GigabitEthernet0/0/1] port hybrid untagged vlan 6
[Quidway-GigabitEthernet0/0/1] quit
Step 2 Configure the voice VLAN on the Switch.
# Configure the voice VLAN on the interface.
[Quidway] interface gigabitethernet 0/0/1
[Quidway-GigabitEthernet0/0/1] voice-vlan 2 enable
# Set the voice VLAN mode to auto so that the interface can be automatically added to or deleted
from the voice VLAN.
[Quidway-GigabitEthernet0/0/1] voice-vlan mode auto
[Quidway-GigabitEthernet0/0/1] quit
# Set the OUI of the voice VLAN.
[Quidway] voice-vlan mac-address 0011-2200-0000 mask ffff-ff00-0000
# Set the aging time of the voice VLAN.
[Quidway] voice-vlan aging-time 100
# Set the working mode of the voice VLAN.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
121
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
[Quidway-GigabitEthernet0/0/1] voice-vlan security enable
Step 3 Verify the configuration.
Run the display voice-vlan oui command to check the OUI of the voice VLAN.
<Quidway> display voice-vlan oui
--------------------------------------------------OuiAddress
Mask
Description
--------------------------------------------------0011-2200-0000
ffff-ff00-0000
Run the display voice-vlan 2 status command to check the voice VLAN mode, voice VLAN
security mode, and voice VLAN aging time.
<Quidway> display voice-vlan 2 status
Voice VLAN Configurations:
--------------------------------------------------Voice VLAN ID
: 2
Voice VLAN status
: Enable
Voice VLAN aging time
: 100 (minutes)
Voice VLAN 8021p remark : 6
Voice VLAN dscp remark
: 46
---------------------------------------------------------Port Information:
----------------------------------------------------------Port
Add-Mode Security-Mode Legacy
----------------------------------------------------------GigabitEthernet0/0/1
Auto
Security
Disable
----End
Configuration Files
Configuration file of the Switch
#
sysname Quidway
#
vlan batch 2 6
#
voice-vlan aging-time 100
#
voice-vlan mac-address 0011-2200-0000 mask ffff-ff00-0000
#
interface GigabitEthernet0/0/1
port hybrid pvid vlan 6
port hybrid untagged vlan 6
voice-vlan 2 enable
#
return
3.11.9 Example for Configuring a Voice VLAN in Manual Mode
In manual voice VLAN mode, an interface with voice VLAN enabled can forward voice data
packets only after the interface is manually added to the voice VLAN.
Networking Requirements
Data flows of the high speed Internet (HSI), VoIP, and IPTV services are transmitted on a
network. Users require high quality of VoIP services; therefore, voice data flows must be
transmitted with a high priority.
As shown in Figure 3-17, after a voice VLAN is configured on the Switch, the Switch checks
whether a data flow received by GigabitEthernet0/0/1 is a voice data flow based on the source
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
122
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
MAC address of the flow. If the data flow is a voice data flow, the Switch changes the priority
of the flow and transmits it in the voice VLAN. If not, the Switch transmits the flow in a common
VLAN without changing the priority of the flow. GigabitEthernet0/0/1 needs to be manually
added to or deleted from the voice VLAN.
Figure 3-17 Configuring a voice VLAN in manual mode
DHCP Server
Internet
Switch
GE0/0/1
LAN Switch
HSI
VoIP
IPTV
Configuration Roadmap
The configuration roadmap is as follows:
1.
Create VLANs.
2.
Configure the link type and default VLAN of the interface.
3.
Enable the voice VLAN on the interface.
4.
Set the voice VLAN mode to manual.
5.
Set the OUI of the voice VLAN.
6.
Set the security mode of the voice VLAN.
7.
Add the interface to the voice VLAN.
Data Preparation
To complete the configuration, you need the following data:
l
Voice VLAN and VLAN through which the IP phone applies for an IP address: VLAN 2
and VLAN 6
OUI and mask: 0011-2200-0000 and ffff-ff00-0000
Default VLAN of GigabitEthernet 0/0/1: VLAN 6
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
123
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
Procedure
Step 1 Create VLANs and configure the interface on the Switch.
# Create VLAN 2 and VLAN 6.
<Quidway> system-view
[Quidway] vlan batch 2 6
# Configure the link type and default VLAN of the interface.
[Quidway] interface gigabitethernet 0/0/1
[Quidway-GigabitEthernet0/0/1] port hybrid pvid vlan 6
[Quidway-GigabitEthernet0/0/1] port hybrid untagged vlan 6
[Quidway-GigabitEthernet0/0/1] quit
Step 2 Configure the voice VLAN on the Switch.
# Configure the voice VLAN on the interface.
[Quidway] interface gigabitethernet 0/0/1
[Quidway-GigabitEthernet0/0/1] voice-vlan 2 enable
# Set the voice VLAN mode to manual and add the interface to the voice VLAN.
[Quidway-GigabitEthernet0/0/1] voice-vlan mode manual
[Quidway-GigabitEthernet0/0/1] port hybrid tagged vlan 2
[Quidway-GigabitEthernet0/0/1] quit
# Set the OUI of the voice VLAN.
[Quidway] voice-vlan mac-address 0011-2200-0000 mask ffff-ff00-0000
# Set the working mode of the voice VLAN.
[Quidway-GigabitEthernet0/0/1] voice-vlan security enable
Step 3 Verify the configuration.
Run the display voice-vlan oui command to check the OUI of the voice VLAN.
<Quidway> display voice-vlan oui
--------------------------------------------------OuiAddress
Mask
Description
--------------------------------------------------0011-2200-0000
ffff-ff00-0000
Run the display voice-vlan 2 status command to check voice VLAN mode, security mode, and
voice VLAN aging time.
<Quidway> display voice-vlan 2 status
Voice VLAN Configurations:
--------------------------------------------------Voice VLAN ID
: 2
Voice VLAN status
: Enable
Voice VLAN aging time
: 1440 (minutes)
Voice VLAN 8021p remark : 6
Voice VLAN dscp remark
: 46
---------------------------------------------------------Port Information:
----------------------------------------------------------Port
Add-Mode Security-Mode Legacy
----------------------------------------------------------GigabitEthernet0/0/1
Manual
Security
Disable
----End
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
124
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
3 VLAN Configuration
Configuration Files
Configuration file of the Switch
#
sysname Quidway
#
vlan batch 2 6
#
voice-vlan mac-address 0011-2200-0000 mask ffff-ff00-0000
#
interface GigabitEthernet0/0/1
port hybrid pvid vlan 6
port hybrid tagged vlan 2
port hybrid untagged vlan 6
voice-vlan 2 enable
voice-vlan mode manual
#
return
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
125
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
4 VLAN Mapping Configuration
VLAN Mapping Configuration
About This Chapter
This chapter describes the concepts and configuration procedure of VLAN mapping, and
provides configuration examples.
4.1 Introduction to VLAN Mapping
This section describes the concept of VLAN mapping.
4.2 VLAN Mapping Features Supported by the S5700
This section describes VLAN mapping modes supported by the S5700.
4.3 Configuring VLAN Mapping for Single-tagged Packets
This section describes how to replace the VLAN tag of single-tagged packets.
4.4 Configuring VLAN Mapping for Double-tagged Packets
This section describes how to replace the outer tag of both tags of double-tagged packets.
4.5 Configuration Examples
This section provides several examples of VLAN mapping configuration.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
126
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
4 VLAN Mapping Configuration
4.1 Introduction to VLAN Mapping
This section describes the concept of VLAN mapping.
VLAN Mapping is a function that maps the customer VLAN ID to the carrier VLAN ID by
replacing the inner and outer VLAN tags of data frames. VLAN mapping implements VLAN
aggregation and allows service data to be transmitted according to carriers' network plans.
4.2 VLAN Mapping Features Supported by the S5700
This section describes VLAN mapping modes supported by the S5700.
The S5700 supports the following VLAN mapping features:
l
Single-tag VLAN mapping based on the interface and VLAN
Double-tag VLAN mapping based on the interface and VLAN
Single-tag VLAN mapping based on the interface, VLAN, and 802.1p priority
NOTE
The S5700SI does not support double-tag VLAN mapping.
4.3 Configuring VLAN Mapping for Single-tagged Packets
This section describes how to replace the VLAN tag of single-tagged packets.
4.3.1 Establishing the Configuration Task
Applicable Environment
When two private networks in different VLANs communicate with each other through a public
network, the user packets may carry the C-VLAN tag when reaching the ISP network. You can
configure VLAN mapping on the edge device of the public network so that the VLANs of private
networks are separated from VLANs of the public network. This saves VLAN resources on the
public network.
Pre-configuration Tasks
Before configuring VLAN mapping, complete the following task:
l
Configuring VLANs
Data Preparation
To configure VLAN mapping, you need the following data.
Issue 02 (2011-11-21)
No.
Data
Original VLAN ID before VLAN mapping
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
127
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
No.
Data
Translated VLAN ID after VLAN mapping
4 VLAN Mapping Configuration
4.3.2 Replacing a Single Tag
Context
Perform the following steps on the switch to configure VLAN mapping for single-tagged
packets.
NOTE
l VLAN mapping can only be configured on a trunk or hybrid interface, and the interface must be added
to the VLAN specified by map-vlan in tagged mode.
l If multiple VLANs are specified in vlan, the interface needs to be added to these VLANs in tagged
mode, and the VLAN specified by map-vlan cannot be a VLAN corresponding to a VLANIF interface.
l If VLAN mapping and DHCP are configured on the same interface, the interface must be added to the
original VLANs (VLANs before mapping) in tagged mode.
l Limiting MAC address learning on an interface may affect the N:1 VLAN mapping on the interface.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
interface interface-type interface-number
The Ethernet interface view is displayed.
Step 3 Run:
port link-type trunk
The link type of the interface is set.
By default, the link type of an interface is hybrid.
Step 4 Run:
port trunk allow-pass vlan vlan-id
The interface is added to the translated VLAN (specified by map-vlan).
Step 5 Run:
qinq vlan-translation enable
VLAN translation is enabled on the interface.
Step 6 Run:
port vlan-mapping vlan vlan-id1 [ to vlan-id2 ] map-vlan vlan-id3 [ remark-8021p
8021p-value ]
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
128
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
4 VLAN Mapping Configuration
Single-tag VLAN mapping is configured on the interface.
----End
4.3.3 Checking the Configuration
Procedure
l
Run the display vlan vlan-id command to check whether the interface is added to the
translated local VLAN.
Run the display current-configuration command to check information about the VLAN
mapping of single VLAN tag on the interface.
You can obtain the following information:
The interface is added to the translated local VLAN.
The information about the VLAN mapping is correct.
----End
4.4 Configuring VLAN Mapping for Double-tagged Packets
This section describes how to replace the outer tag of both tags of double-tagged packets.
4.4.1 Establishing the Configuration Task
Applicable Environment
When two private networks in different VLANs communicate with each other through a public
network, the user packets may carry one or two VLAN tags when arriving on the public network.
You can configure VLAN mapping of double VLAN tags on the edge device of the public
network so that the VLANs of private networks and public network can be separated. This saves
VLAN resources on the public network. Compared with VLAN mapping for single-tagged
packets, this function is more flexible and supports a wider scope of services.
NOTE
The S5700SI does not support double-tag VLAN mapping.
Pre-configuration Tasks
Before configuring VLAN mapping for double-tagged packets, Create VLANs.
Data Preparation
To configure VLAN mapping for double-tagged packets, you need the following data.
Issue 02 (2011-11-21)
No.
Data
Original outer VLAN ID
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
129
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
No.
Data
Original inner VLAN ID
Translated outer VLAN ID
4 VLAN Mapping Configuration
4.4.2 Replacing the Outer VLAN Tag
Context
Perform the following steps on the switch to replace the outer VLAN tags of packets.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
interface interface-type interface-number
The interface view is displayed.
Step 3 Run:
port link-type trunk
The link type of the interface is set to trunk.
Step 4 Run:
port trunk allow-pass vlan vlan-id
The interface is added to the translated outer VLAN.
Step 5 Run:
qinq vlan-translation enable
VLAN translation is enabled on the interface.
Step 6 Run:
port vlan-mapping vlan vlan-id1 inner-vlan vlan-id2 [ to vlan-id3 ] map-vlan vlanid4 [ remark-8021p 8021p-value ]
The switch is configured to replace the outer VLAN tag of packets.
NOTE
VLAN mapping can only be configured on a trunk or hybrid interface, and the interface must be added to
the VLAN specified by map-vlan in tagged mode.
----End
4.4.3 Checking the Configuration
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
130
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
4 VLAN Mapping Configuration
Procedure
l
Run the display vlan vlan-id command to check whether the interface is added to the
translated local VLAN.
Run the display current-configuration command to check information about the mapping
of double VLAN tags on the interface.
You can obtain the following information:
The interface is added to the translated local VLAN.
The information about the VLAN mapping is correct.
----End
4.5 Configuration Examples
This section provides several examples of VLAN mapping configuration.
4.5.1 Example for Configuring Single-Tag VLAN Mapping
Networking Requirements
As shown in Figure 4-1, users in VLAN 6 need to communicate with users in VLAN 5 through
VLAN 10 on the network.
Figure 4-1 Networking diagram of single-tag VLAN mapping configurations
Network
SwitchC
GE0/0/1
VLAN10
SwitchD
GE0/0/1
SwitchA
SwitchB
GE0/0/1
VLAN6
GE0/0/2
GE0/0/3
172.16.0.1/16 172.16.0.2/16 172.16.0.3/16
Issue 02 (2011-11-21)
GE0/0/1
GE0/0/2
VLAN5
GE0/0/3
172.16.0.5/16 172.16.0.6/16 172.16.0.7/16
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
131
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
4 VLAN Mapping Configuration
Configuration Roadmap
The configuration roadmap is as follows:
1.
Create VLANs on SwitchA, SwitchB, SwitchC, and SwitchD.
2.
Add interfaces of SwitchA, SwitchB, SwitchC, and SwitchD to the corresponding VLANs.
3.
Configure single-tag VLAN mapping on GE 0/0/1 of SwitchA.
4.
Configure single-tag VLAN mapping on GE 0/0/1 of SwitchB.
Data Preparation
To complete the configuration, you need the following data:
l
VLAN to be created on SwitchA: VLAN 6
VLAN to be created on SwitchB: VLAN 5
VLAN to be created on SwitchC and SwitchD: VLAN 10
Procedure
Step 1 Create VLANs on the Switches.
# Create VLAN 6 on SwitchA.
<Quidway> system-view
[Quidway] sysname SwitchA
[SwitchA] vlan 6
# Create VLAN 5 on SwitchB.
<Quidway> system-view
[Quidway] sysname SwitchB
[SwitchB] vlan 5
# Create VLAN 10 on SwitchC.
<Quidway> system-view
[Quidway] sysname SwitchC
[SwitchC] vlan 10
# Create VLAN 10 on SwitchD.
<Quidway> system-view
[Quidway] sysname SwitchD
[SwitchD] vlan 10
Step 2 Add interfaces to VLANs.
# Add GE 0/0/2 and GE 0/0/3 of SwitchA to VLAN 6.
[SwitchA] interface gigabitethernet
[SwitchA-GigabitEthernet0/0/2] port
[SwitchA-GigabitEthernet0/0/2] port
[SwitchA-GigabitEthernet0/0/2] quit
[SwitchA] interface gigabitethernet
[SwitchA-GigabitEthernet0/0/3] port
[SwitchA-GigabitEthernet0/0/3] port
[SwitchA-GigabitEthernet0/0/3] quit
0/0/2
link-type trunk
trunk allow-pass vlan 6
0/0/3
link-type trunk
trunk allow-pass vlan 6
# Add GE 0/0/1 of SwitchA to VLAN 6.
[SwitchA] interface gigabitethernet 0/0/1
[SwitchA-GigabitEthernet0/0/1] port link-type trunk
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
132
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
4 VLAN Mapping Configuration
[SwitchA-GigabitEthernet0/0/1] port trunk allow-pass vlan 6
[SwitchA-GigabitEthernet0/0/1] quit
# Add GE 0/0/2 and GE 0/0/3 of SwitchB to VLAN 5.
[SwitchB] interface gigabitethernet
[SwitchB-GigabitEthernet0/0/2] port
[SwitchB-GigabitEthernet0/0/2] port
[SwitchB-GigabitEthernet0/0/2] quit
[SwitchB] interface gigabitethernet
[SwitchB-GigabitEthernet0/0/3] port
[SwitchB-GigabitEthernet0/0/3] port
[SwitchB-GigabitEthernet0/0/3] quit
0/0/2
link-type trunk
trunk allow-pass vlan 5
0/0/3
link-type trunk
trunk allow-pass vlan 5
# Add GE 0/0/1 of SwitchB to VLAN 5.
[SwitchB] interface gigabitethernet 0/0/1
[SwitchB-GigabitEthernet0/0/1] port link-type trunk
[SwitchB-GigabitEthernet0/0/1] port trunk allow-pass vlan 5
[SwitchB-GigabitEthernet0/0/1] quit
# Add GE 0/0/1 of SwitchC to VLAN 10.
[SwitchC] interface gigabitethernet 0/0/1
[SwitchC-GigabitEthernet0/0/1] port link-type trunk
[SwitchC-GigabitEthernet0/0/1] port trunk allow-pass vlan 10
[SwitchC-GigabitEthernet0/0/1] quit
# Add GE 0/0/1 of SwitchD to VLAN 10.
[SwitchD] interface gigabitethernet 0/0/1
[SwitchD-GigabitEthernet0/0/1] port link-type trunk
[SwitchD-GigabitEthernet0/0/1] port trunk allow-pass vlan 10
[SwitchD-GigabitEthernet0/0/1] quit
Step 3 Configure single-tag VLAN mapping on the Switches.
# Configure single-tag VLAN mapping on GE 0/0/1 of SwitchA.
[SwitchA-GigabitEthernet0/0/1] qinq vlan-translation enable
[SwitchA-GigabitEthernet0/0/1] port vlan-mapping vlan 10 map-vlan 6
# Configure single-tag VLAN mapping on GE 0/0/1 of SwitchB.
[SwitchB-GigabitEthernet0/0/1] qinq vlan-translation enable
[SwitchB-GigabitEthernet0/0/1] port vlan-mapping vlan 10 map-vlan 5
Step 4 Verify the configuration.
The hosts in VLAN 6 and the hosts in VLAN 5 can ping each other.
----End
Configuration Files
l
Configuration file of SwitchA
#
sysname SwitchA
#
vlan batch 6
#
interface GigabitEthernet0/0/1
qinq vlan-translation enable
port link-type trunk
port trunk allow-pass vlan 6
port vlan-mapping vlan 10 map-vlan 6
#
interface GigabitEthernet0/0/2
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
133
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
4 VLAN Mapping Configuration
port link-type trunk
port trunk allow-pass vlan 6
#
interface GigabitEthernet0/0/3
port link-type trunk
port trunk allow-pass vlan 6
#
return
Configuration file of SwitchB
#
sysname SwitchB
#
vlan batch 5
#
interface GigabitEthernet0/0/1
qinq vlan-translation enable
port link-type trunk
port trunk allow-pass vlan 5
port vlan-mapping vlan 10 map-vlan 5
#
interface GigabitEthernet0/0/2
port link-type trunk
port trunk allow-pass vlan 5
#
interface GigabitEthernet0/0/3
port link-type trunk
port trunk allow-pass vlan 5
#
return
Configuration file of SwitchC
#
sysname SwitchC
#
vlan batch 10
#
interface GigabitEthernet0/0/1
port link-type trunk
port trunk allow-pass vlan 10
#
return
Configuration file of SwitchD
#
sysname SwitchD
#
vlan batch 10
#
interface GigabitEthernet0/0/1
port link-type trunk
port trunk allow-pass vlan 10
#
return
4.5.2 Example for Configuring N:1 VLAN Mapping
Networking Requirements
As shown in Figure 4-2, users in VLAN 100 to VLAN 200 connect to the Internet through the
aggregate switch (Switch) of the carrier.
After user devices are powered on, they send service request packets to the switch of the carrier.
After the user devices pass the authentication, services can be used.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
134
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
4 VLAN Mapping Configuration
Figure 4-2 N:1 VLAN mapping
Internet
Switch GE0/0/1
VLAN100~200
SwitchA
SwitchC
SwitchB
SwitchD
SwitchE
Configuration Roadmap
The configuration roadmap is as follows:
1.
Configure the original and translated VLAN IDs.
2.
Add GE 0/0/1 of the Switch to the original and translated VLANs in tagged mode.
3.
Configure VLAN mapping on GE 0/0/1 of the Switch.
Data preparation
To complete the configuration, you need the following data:
l
VLANs before mapping: VLAN 100 to VLAN 200
VLAN after mapping: VLAN 10
Procedure
Step 1 Configure the Switch.
# Create VLANs.
<Quidway> system-view
[Quidway] vlan batch 10 100 to 200
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
135
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
4 VLAN Mapping Configuration
# Add related GE 0/0/1 to the VLANs.
[Quidway] interface gigabitethernet 0/0/1
[Quidway-GigabitEthernet0/0/1] port hybrid tagged vlan 10 100 to 200
# Configure VLAN mapping on GE 0/0/1.
[Quidway-GigabitEthernet0/0/1] qinq vlan-translation enable
[Quidway-GigabitEthernet0/0/1] port vlan-mapping vlan 100 to 200 map-vlan 10
[Quidway-GigabitEthernet0/0/1] quit
Step 2 Verify the configuration.
Users in VLAN 100 to VLAN 200 can connect to the Internet through the Switch.
----End
Configuration Files
l
Configuration file of the Switch
#
sysname Quidway
#
vlan batch 10 100 to 200
#
interface GigabitEthernet0/0/1
qinq vlan-translation enable
port hybrid tagged vlan 10 100 to 200
port vlan-mapping vlan 100 to 200 map-vlan 10
#
return
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
136
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
5 QinQ Configuration
QinQ Configuration
About This Chapter
This chapter describes the concepts and configuration procedure of 802.1Q-in-802.1Q (QinQ),
and provides configuration examples.
5.1 QinQ Overview
This section describes the concept of QinQ.
5.2 QinQ Features Supported by the S5700
This section describes the QinQ features that the S5700 supports.
5.3 Configuring QinQ on an Interface
This section describes how to configure the interface type, the protocol used by the outer VLAN
tag, and the interface-based QinQ.
5.4 Configuring Selective QinQ
This section describes how to configure the interface type, the outer VLAN ID, and selective
QinQ.
5.5 Configuring QinQ Stacking on a VLANIF Interface
To log in to a remote device to manage it, configure QinQ stacking on the VLANIF interface
corresponding to the management VLAN on the remote device.
5.6 Setting the Protocol Type in the Outer VLAN Tag
This section describes how to set the protocol type in the outer VLAN tag on an interface.
5.7 Configuration Examples
This section provides several configuration examples of QinQ.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
137
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
5 QinQ Configuration
5.1 QinQ Overview
This section describes the concept of QinQ.
The 802.1Q-in-802.1Q (QinQ) protocol is a Layer 2 tunneling protocol based on the IEEE
802.1Q technology. A frame transmitted on the public network has double 802.1Q tags. One is
a public tag and the other is a private tag.
The principle of QinQ is to encapsulate a private VLAN tag in a public VLAN tag; therefore, a
packet traverses the backbone network of the Internet service provider (ISP) carrying double
VLAN tags. QinQ technology provides a simpler Layer 2 VPN tunnel for users.
5.2 QinQ Features Supported by the S5700
This section describes the QinQ features that the S5700 supports.
Selective QinQ
Selective QinQ is an extension to QinQ. It allows an interface to add outer VLAN tags with
different public VLAN IDs to frames according to the private VLAN IDs of the frames. This
can differentiate various types of users.
The S5700 not only supports selective QinQ based on the interface and VLAN, but also supports
flow-based selective QinQ.
For the commands related to flow-based selective QinQ, see the Quidway S5700 Series Ethernet
Switches Command Reference - QoS.
Protocols in Outer VLAN Tags
The protocols applied to outer VLAN tags vary according to the vendors. The S5700 allows you
to set the protocol type in the outer VLAN tags so that it can work with non-Huawei devices.
5.3 Configuring QinQ on an Interface
This section describes how to configure the interface type, the protocol used by the outer VLAN
tag, and the interface-based QinQ.
5.3.1 Establishing the Configuration Task
Applicable Environment
To separate the private network from the public network and save VLAN resources, you can
configure double 802.1q tags on a QinQ interface of the S5700. The private VLAN IDs (inner
VLAN tags) are assigned to internal networks such as an enterprise intranet. The public VLAN
IDs (outer VLAN tag) are assigned external networks such as an ISP network. In this way, a
maximum of 4094 x 4094 VLAN tags are provided to transparently transmit packets from
different private networks with the same VLAN ID.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
138
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
5 QinQ Configuration
Pre-configuration Tasks
None.
Data Preparation
To configure QinQ on an interface, you need the following data.
No.
Data
Number of the QinQ interface
(Optional) Protocol type in the outer VLAN tag
Outer VLAN ID
5.3.2 Setting the Link Type of an Interface
Context
Perform the following steps on the switch to set the link type of an interface.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
interface interface-type interface-number
The interface view is displayed.
Step 3 Run:
port link-type dot1q-tunnel
The link type of the interface is set to dot1q-tunnel.
By default, the link type of an interface is hybrid.
Dot1q-tunnel interfaces do not support Layer 2 multicast.
----End
5.3.3 Specifying the Outer VLAN ID
Context
Perform the following steps on the S5700 to specify the outer VLAN ID.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
139
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
5 QinQ Configuration
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
vlan vlan-id
The VLAN is created.
Step 3 Run:
quit
Return to the system view.
Step 4 Run:
interface interface-type interface-number
The interface view is displayed.
Step 5 Run:
port default vlan vlan-id
The VLAN ID (default VLAN) in the outer VLAN tag is specified.
----End
5.3.4 Checking the Configuration
Procedure
l
Run the display current-configuration interface interface-type interface-number
command to check the QinQ configuration on the interface.
----End
5.4 Configuring Selective QinQ
This section describes how to configure the interface type, the outer VLAN ID, and selective
QinQ.
5.4.1 Establishing the Configuration Task
Applicable Environment
To enable users to communicate through the ISP network, user packets are added an outer VLAN
tag.
Pre-configuration Tasks
None
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
140
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
5 QinQ Configuration
Data Preparation
To configure selective QinQ, you need the following data.
No.
Data
Number of the interface to be configured with selective QinQ
Inner VLAN ID
Outer VLAN ID
5.4.2 Setting the Link Type of an Interface
Context
Perform the following steps on the switch to set the link type of an interface.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
interface interface-type interface-number
The interface view is displayed.
Step 3 Run:
port link-type hybrid
The link type of the interface is set to hybrid.
By default, the link type of an interface is hybrid.
----End
5.4.3 Adding the Interface to the Stacked VLAN
Context
Perform the following steps on the switch to add the interface to the stacked VLAN.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
141
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
5 QinQ Configuration
Step 2 Run:
interface interface-type interface-number
The interface view is displayed.
Step 3 Run:
port hybrid untagged vlan vlan-id
The interface is added to the stacked VLAN in untagged mode.
The stacked outer VLAN must exist on the switch, but the inner VLANs do not need to be created
on the switch.
----End
5.4.4 Configuring Selective QinQ
Context
An interface learns the MAC address from the outer VLAN tag of a QinQ packet.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
interface interface-type interface-number
The interface view is displayed.
Step 3 Run:
qinq vlan-translation enable
VLAN translation is enabled on the interface.
Step 4 Run:
port vlan-stacking vlan vlan-id1 [ to vlan-id2 ] stack-vlan vlan-id3 [
remark-8021p 8021p-value ]
Selective QinQ is configured. The meanings of the parameters are as follows:
l vlan-id1 [ to vlan-id2 ] specifies the C-VLAN IDs of packets to which you need to add an
outer VLAN tag.
l stack-vlan vlan-id3 specifies the VLAN ID in the outer VLAN tag to be added.
l [ remark-8021p 8021p-value ] specifies the internal priority in the stacked outer VLAN tag.
By default, the priority in the stacked outer VLAN tag is the same as the priority in the inner
VLAN tag.
----End
5.4.5 Checking the Configuration
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
142
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
5 QinQ Configuration
Procedure
l
Run the display current-configuration interface interface-type interface-number
command to check the selective QinQ configuration on the interface.
----End
5.5 Configuring QinQ Stacking on a VLANIF Interface
To log in to a remote device to manage it, configure QinQ stacking on the VLANIF interface
corresponding to the management VLAN on the remote device.
5.5.1 Establishing the Configuration Task
Before configuring QinQ stacking on a VLANIF interface, familiarize yourself with the
applicable environment, complete the pre-configuration tasks, and obtain the data required for
the configuration. This will help you complete the configuration task quickly and accurately.
Applicable Environment
As shown in Figure 5-1, SwitchA is connected to SwitchB through a third-party network. The
management VLAN on SwitchB is the same as the VLAN for users connected to SwitchA. The
VLAN ID provided by the carrier, however, is different from the management VLAN ID.
Figure 5-1 Networking for QinQ stacking on a VLANIF interface
IP
10
20
SwitchB
Internet
SwitchA
IP
Management VLAN 10
Interface VLANIF 10
10
user2
user1
VLAN 10
To log in to SwitchB to manage it from SwitchA, you can configure QinQ stacking on the
VLANIF interface corresponding to the management VLAN on SwitchB.
After QinQ stacking is configured, data frames are processed as follows:
l
Frames sent from SwitchA to SwitchB
The user-side interface of SwitchA, which is configured with QinQ, sends double-tagged
frames to the ISP network. The outer VLAN tag is assigned by the carrier so that the frames
can be transparently transmitted across the ISP network to SwitchB.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
143
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
5 QinQ Configuration
When SwitchB receives double-tagged frames, it compares the VLAN tags of the frames
with the VLAN tags configured on the VLANIF interface. If the outer tag of the frames is
the same as the outer tag configured on the VLANIF interface, SwitchB removes the outer
tag and sends the frames to the IP layer for processing.
l
Frames sent from SwitchB to SwitchA
When the VLANIF interface of SwitchB receives data frames, SwitchB adds a VLAN tag
to the frames according to the QinQ stacking configuration. The new outer VLAN tag is
assigned by the carrier so that the double-tagged data frames can be transparently
transmitted to SwitchA across the ISP network. SwitchA removes the outer VLAN tag of
the frames and forwards the frames to users.
Pre-configuration Tasks
Before configuring QinQ stacking on a VLANIF interface, complete the following tasks:
l
Creating VLANs
Configuring the management VLAN
Data Preparations
To configure QinQ stacking on a VLANIF interface, you need the following data.
No.
Data
VLAN IDs
5.5.2 Configuring QinQ Stacking on a VLANIF Interface
To log in to a remote device to manage it, configure QinQ stacking on the VLANIF interface
corresponding to the management VLAN on the remote device.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
interface vlanif vlan-id
The VLANIF interface corresponding to the management VLAN is created.
Before running this command, ensure that the management VLAN exists.
Step 3 Run:
qinq stacking vlan vlan-id
QinQ stacking is configured on the VLANIF interface.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
144
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
5 QinQ Configuration
NOTE
l When configuring QinQ stacking on a VLANIF interface, ensure that the VLANIF interface
corresponds to the management VLAN. VLANIF interfaces corresponding to other VLANs do not
support QinQ stacking.
l To change the configured outer VLAN tag, run the undo qinq stacking vlan command to disable QinQ
stacking, and then run the qinq stacking vlan command to configure a new outer VLAN tag.
l The qinq stacking vlan command conflicts with the icmp host-unreachable send command.
Therefore, you must run the undo icmp host-unreachable send command before using the qinq
stacking vlan command.
----End
5.5.3 Checking the Configuration
After QinQ stacking is configured on the VLANIF interface of the remote device, you can log
in to the remote device to manage the remote device from the local device.
Prerequisite
The configurations of QinQ stacking on the VLANIF interface are complete.
Procedure
Step 1 Run the display vlan [ vlan-id [ verbose ] ] command to check the management VLAN.
Step 2 Run the display this command in the VLANIF interface view to check the QinQ stacking
configuration.
----End
5.6 Setting the Protocol Type in the Outer VLAN Tag
This section describes how to set the protocol type in the outer VLAN tag on an interface.
5.6.1 Establishing the Configuration Task
Applicable Environment
To enable the S5700 to communicate with non-Huawei devices, set a protocol type that can be
identified by the peer device in the outer VLAN tag.
Pre-configuration Tasks
None.
Data Preparation
To set the protocol type in the outer VLAN tag, you need the following data.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
145
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
No.
Data
Interface number
Protocol type in the outer VLAN tag
5 QinQ Configuration
5.6.2 Configuring the Link Type of an Interface
Context
Perform the following steps on the switch to set the link type of an interface.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
interface interface-type interface-number
The interface view is displayed.
Step 3 Run:
port link-type { hybrid | trunk | access }
The link type is configured.
By default, the link type of an interface is hybrid.
----End
5.6.3 Setting the Protocol Type in the Outer VLAN Tag
Context
Perform the following steps on the switch to set the protocol type in the outer VLAN tag.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
interface interface-type interface-number
The interface view is displayed.
Step 3 Run:
qinq protocol protocol-id
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
146
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
5 QinQ Configuration
The protocol type in the outer VLAN tag is set.
The qinq protocol command cannot be used on a QinQ interface.
The qinq protocol command is used to identify incoming frames and add or change the TPID
for outgoing frames.
By default, the protocol type in the outer VLAN tag is 0x8100.
NOTE
l To implement the connectivity between the devices of different vendors, ensure that the protocol type
in the outer VLAN tag can be identified by the peer device.
l The protocol IDs set by the qinq protocol command cannot be the same as well-known protocol IDs.
Otherwise, the interface cannot distinguish packets of these protocols. For example, protocol-id cannot
be set to 0x0806, which is the ARP protocol ID.
----End
5.6.4 Checking the Configuration
Procedure
Step 1 Run the display current-configuration interface interface-type interface-number command to
check the protocol type in the outer VLAN tag set on an interface.
----End
5.7 Configuration Examples
This section provides several configuration examples of QinQ.
5.7.1 Example for Configuring QinQ on Interfaces
Networking Requirements
As shown in Figure 5-2, there are two enterprises on the network, Enterprise 1 and Enterprise
2. Enterprise 1 has two office locations, and Enterprise 2 has three office locations. The office
locations of the two enterprises access SwitchG or SwitchF of the ISP network. The network of
Enterprise 1 is divided into VLAN 1000 to VLAN 1500; the network of Enterprise 2 is divided
into VLAN 2000 to VLAN 3000. Employees in the same VLAN need to communicate with each
other through the ISP network, but the two enterprises must be isolated from each other.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
147
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
5 QinQ Configuration
Figure 5-2 Configuring QinQ on interfaces
Enterprise 2
Enterprise 2
SwitchG
GE0/0/1
GE0/0/2
GE0/0/3
GE0/0/4
SwitchF
GE0/0/3
GE0/0/1
VLAN2000
VLAN3000
VLAN2000
VLAN3000
GE0/0/2
VLAN1000 VLAN1500
Enterprise 1
VLAN2000
VLAN3000
VLAN1000
Enterprise 2
VLAN1500
Enterprise1
Configuration Roadmap
The configuration roadmap is as follows:
1.
Create VLAN 10 and VLAN 20 on SwitchF; create VLAN 20 on SwitchG.
2.
Configure GE 0/0/1, GE 0/0/2, and GE 0/0/3 of SwitchF as QinQ interfaces.
3.
Configure GE 0/0/1 and GE 0/0/2 of SwitchG as QinQ interfaces.
4.
Add GE 0/0/4 of SwitchF and GE 0/0/3 of SwitchG to VLAN 20 in tagged mode.
Data Preparation
To complete the configuration, you need the following data:
l
VLAN assigned to Enterprise 1 on the ISP network: VLAN 10
VLAN assigned to Enterprise 2 on the ISP network: VLAN 20
Procedure
Step 1 Create VLANs.
# Create VLAN 10 and VLAN 20 on SwitchF.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
148
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
5 QinQ Configuration
<Quidway> system-view
[Quidway] sysname SwitchF
[SwitchF] vlan batch 10 20
# Create VLAN 20 on SwitchG.
<Quidway> system-view
[Quidway] sysname SwitchG
[SwitchG] vlan 20
Step 2 Configure the interfaces as QinQ interfaces.
# Configure GE 0/0/1, GE 0/0/2, and GE 0/0/3 of SwitchF as QinQ interfaces. Set the VLAN
ID of the outer VLAN tag added by GE 0/0/1 and GE 0/0/3/ to VLAN 10; set the VLAN ID of
the outer VLAN tag added by GE 0/0/2 to VLAN 20.
[SwitchF] interface gigabitethernet
[SwitchF-GigabitEthernet0/0/1] port
[SwitchF-GigabitEthernet0/0/1] port
[SwitchF-GigabitEthernet0/0/1] quit
[SwitchF] interface gigabitethernet
[SwitchF-GigabitEthernet0/0/2] port
[SwitchF-GigabitEthernet0/0/2] port
[SwitchF-GigabitEthernet0/0/2] quit
[SwitchF] interface gigabitethernet
[SwitchF-GigabitEthernet0/0/3] port
[SwitchF-GigabitEthernet0/0/3] port
[SwitchF-GigabitEthernet0/0/3] quit
0/0/1
link-type dot1q-tunnel
default vlan 10
0/0/2
link-type dot1q-tunnel
default vlan 20
0/0/3
link-type dot1q-tunnel
default vlan 10
# Set GE 0/0/1 and GE 0/0/2 of SwitchG as QinQ interfaces; set the VLAN ID of the outer
VLAN tags added by GE 0/0/1 and GE 0/0/2/ to VLAN 20.
[SwitchG] interface gigabitethernet
[SwitchG-GigabitEthernet0/0/1] port
[SwitchG-GigabitEthernet0/0/1] port
[SwitchG-GigabitEthernet0/0/1] quit
[SwitchG] interface gigabitethernet
[SwitchG-GigabitEthernet0/0/2] port
[SwitchG-GigabitEthernet0/0/2] port
[SwitchG-GigabitEthernet0/0/2] quit
0/0/1
link-type dot1q-tunnel
default vlan 20
0/0/2
link-type dot1q-tunnel
default vlan 20
Step 3 Configure other interfaces.
# Add GE 0/0/4 of SwitchF to VLAN 20.
[SwitchF] interface gigabitethernet 0/0/4
[SwitchF-GigabitEthernet0/0/4] port link-type trunk
[SwitchF-GigabitEthernet0/0/4] port trunk allow-pass vlan 20
[SwitchF-GigabitEthernet0/0/4] quit
# Add GE 0/0/3 of SwitchG to VLAN 20.
[SwitchG] interface gigabitethernet 0/0/3
[SwitchG-GigabitEthernet0/0/3] port link-type trunk
[SwitchG-GigabitEthernet0/0/3] port trunk allow-pass vlan 20
[SwitchG-GigabitEthernet0/0/3] quit
Step 4 Verify the configuration.
Ping a remote host on the same VLAN in another office location of Enterprise 1 from a host of
Enterprise 1. If it can ping the remote host, hosts in different locations of Enterprise 1 can
communicate with each other.
Ping a remote host on the same VLAN in another office location of Enterprise 2 from a host of
Enterprise 2. If it can ping the remote host, hosts in different locations of Enterprise 2 can
communicate with each other.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
149
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
5 QinQ Configuration
Ping a host of Enterprise 2 from a host in any office location of Enterprise 1. If it fails to ping
the host of Enterprise 2, the two enterprises are isolated from each other.
----End
Configuration Files
l
Configuration file of SwitchF
#
sysname SwitchF
#
vlan batch 10 20
#
interface GigabitEthernet0/0/1
port link-type dot1q-tunnel
port default vlan 10
#
interface GigabitEthernet0/0/2
port link-type dot1q-tunnel
port default vlan 20
#
interface GigabitEthernet0/0/3
port link-type dot1q-tunnel
port default vlan 10
#
interface GigabitEthernet0/0/4
port link-type trunk
port trunk allow-pass vlan 20
#
return
Configuration file of SwitchG
#
sysname SwitchG
#
vlan batch 20
#
interface GigabitEthernet0/0/1
port link-type dot1q-tunnel
port default vlan 20
#
interface GigabitEthernet0/0/2
port link-type dot1q-tunnel
port default vlan 20
#
interface GigabitEthernet0/0/3
port link-type trunk
port trunk allow-pass vlan 20
#
return
5.7.2 Example for Configuring Selective QinQ
Networking Requirements
As shown in Figure 5-3, common Internet access users (using PCs) and IPTV users (using IPTV
terminals) connect to the carrier network through SwitchA and SwitchB. These users
communicate with each other through the carrier network.
Packets of PCs and IPTV terminals need to be tagged VLAN 2 and VLAN 3 when the packets
are transmitted through the carrier network.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
150
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
5 QinQ Configuration
Figure 5-3 Configuring selective QinQ
S w itc h A
S w itc h B
G E 0 /0 /2
N e tw o rk
G E 0 /0 /1
PC
IP T V
G E 0 /0 /2
G E 0 /0 /1
IP T V
PC
Configuration Roadmap
The configuration roadmap is as follows:
1.
Create VLANs on SwitchA and SwitchB.
2.
Configure types of interfaces on SwitchA and SwitchB, and add the interfaces to
corresponding VLANs.
3.
Configure selective QinQ on interfaces of SwitchA and SwitchB.
Data Preparation
To complete the configuration, you need the following data:
l
VLANs that PCs belong to: VLAN 100 to VLAN 200
VLANs that IPTV terminals belong to: VLAN 300 to VLAN 400
VLAN tag that packets of PCs carry on the carrier network: VLAN 2
VLAN tag that packets of IPTV terminals carry on the carrier network: VLAN 3
Procedure
Step 1 Create VLANs.
# On SwitchA, create VLAN 2 and VLAN 3, that is, the outer VLAN IDs added to packets on
the carrier network.
<Quidway> system-view
[Quidway] sysname SwitchA
[SwitchA] vlan batch 2 3
# On SwitchB, create VLAN 2 and VLAN 3, that is, the outer VLAN IDs added to packets on
the carrier network.
<Quidway> system-view
[Quidway] sysname SwitchB
[SwitchB] vlan batch 2 3
Step 2 Configure selective QinQ on interfaces of SwitchA and SwitchB.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
151
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
5 QinQ Configuration
# Configure GE 0/0/1 of Switch A.
[SwitchA] interface gigabitethernet
[SwitchA-GigabitEthernet0/0/1] port
[SwitchA-GigabitEthernet0/0/1] port
[SwitchA-GigabitEthernet0/0/1] qinq
[SwitchA-GigabitEthernet0/0/1] port
[SwitchA-GigabitEthernet0/0/1] port
[SwitchA-GigabitEthernet0/0/1] quit
0/0/1
link-type hybrid
hybrid untagged vlan 2 3
vlan-translation enable
vlan-stacking vlan 100 to 200 stack-vlan 2
vlan-stacking vlan 300 to 400 stack-vlan 3
# Configure GE 0/0/1 of Switch B.
[SwitchB] interface gigabitethernet
[SwitchB-GigabitEthernet0/0/1] port
[SwitchB-GigabitEthernet0/0/1] port
[SwitchB-GigabitEthernet0/0/1] qinq
[SwitchB-GigabitEthernet0/0/1] port
[SwitchB-GigabitEthernet0/0/1] port
[SwitchB-GigabitEthernet0/0/1] quit
0/0/1
link-type hybrid
hybrid untagged vlan 2 3
vlan-translation enable
vlan-stacking vlan 100 to 200 stack-vlan 2
vlan-stacking vlan 300 to 400 stack-vlan 3
Step 3 Configure other interfaces.
# Add GE 0/0/2 of Switch A to VLAN 2 and VLAN 3.
[SwitchA] interface gigabitethernet 0/0/2
[SwitchA-GigabitEthernet0/0/2] port link-type trunk
[SwitchA-GigabitEthernet0/0/2] port trunk allow-pass vlan 2 3
[SwitchA-GigabitEthernet0/0/2] quit
# Add GE 0/0/2 of Switch B to VLAN 2 and VLAN 3.
[SwitchB] interface gigabitethernet 0/0/2
[SwitchB-GigabitEthernet0/0/2] port link-type trunk
[SwitchB-GigabitEthernet0/0/2] port trunk allow-pass vlan 2 3
[SwitchB-GigabitEthernet0/0/2] quit
Step 4 Verify the configuration.
# View the configuration of each interface on SwitchA.
<SwitchA> display current-configuration interface gigabitethernet 0/0/1
#
interface GigabitEthernet0/0/1
qinq vlan-translation enable
port hybrid untagged vlan 2 to 3
port vlan-stacking vlan 100 to 200 stack-vlan 2
port vlan-stacking vlan 300 to 400 stack-vlan 3
#
return
<SwitchA> display current-configuration interface gigabitethernet 0/0/2
#
interface GigabitEthernet0/0/2
port link-type trunk
port trunk allow-pass vlan 2 to 3
#
return
# View the configuration of each interface on SwitchB.
<SwitchB> display current-configuration interface gigabitethernet 0/0/1
#
interface GigabitEthernet0/0/1
qinq vlan-translation enable
port hybrid untagged vlan 2 to 3
port vlan-stacking vlan 100 to 200 stack-vlan 2
port vlan-stacking vlan 300 to 400 stack-vlan 3
#
return
<SwitchB> display current-configuration interface gigabitethernet 0/0/2
#
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
152
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
5 QinQ Configuration
interface GigabitEthernet0/0/2
port link-type trunk
port trunk allow-pass vlan 2 to 3
#
return
If SwitchA and SwitchB are configured correctly:
l PCs can communicate with each other through the carrier network.
l IPTV terminals can communicate with each other through the carrier network.
----End
Configuration Files
Only the configuration files of the Switches are provided:
l
Configuration file of SwitchA
#
sysname SwitchA
#
vlan batch 2 to 3
#
interface GigabitEthernet0/0/1
qinq vlan-translation enable
port hybrid untagged vlan 2 to 3
port vlan-stacking vlan 100 to 200 stack-vlan 2
port vlan-stacking vlan 300 to 400 stack-vlan 3
#
interface GigabitEthernet0/0/2
port link-type trunk
port trunk allow-pass vlan 2 to 3
#
return
Configuration file of SwitchB
#
sysname SwitchB
#
vlan batch 2 to 3
#
interface GigabitEthernet0/0/1
qinq vlan-translation enable
port hybrid untagged vlan 2 to 3
port vlan-stacking vlan 100 to 200 stack-vlan 2
port vlan-stacking vlan 300 to 400 stack-vlan 3
#
interface GigabitEthernet0/0/2
port link-type trunk
port trunk allow-pass vlan 2 to 3
#
return
5.7.3 Example for Configuring Selective QinQ with VLAN
Mapping
Networking Requirements
As shown in Figure 5-4, the Internet access, IPTV, and VoIP services are provided for users
through home gateways.
The corridor switches allocate VLANs to the services as follows:
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
153
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
5 QinQ Configuration
VLANs for the Internet access service of different users: VLAN 1000 to VLAN 1100
Shared VLAN for the IPTV service: VLAN 1101
Shared VLAN for the VoIP service: VLAN 1102
Shared VLAN for home gateways: VLAN 1103
Each community switch is connected to 50 downstream corridor switches, and maps the VLAN
IDs in the Internet access service packets from the corridor switches to VLAN 101 to VLAN
150.
The aggregate switch of the carrier is connected to 50 downstream community switches, and
adds outer VLAN IDs 21 to 70 to the packets sent from the community switches.
After user devices are powered on, they send service request packets to the aggregate switch.
After the user devices are authenticated, users can use services.
Figure 5-4 Configuring selective QinQ
ME60
Internet
Aggregate switch of carrier SwitchA
GE0/0/1
Community
switch
SwitchB
GE0/0/2
GE0/0/1
Corridor
switch
Home
gateway
Configuration Roadmap
The configuration roadmap is as follows:
1.
Create VLANs on SwitchA and SwitchB.
2.
Configure VLAN mapping on SwitchB and add GE 0/0/1 and GE 0/0/2 to the VLANs.
3.
Configure selective QinQ on SwitchA and add GE 0/0/1 to VLANs.
4.
Add other downlink interfaces of SwitchA and SwitchB to the VLANs. The configurations
are similar to the configurations of their GE 0/0/1 interfaces.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
154
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
5.
5 QinQ Configuration
Configure other community switches. The configuration is similar to the configuration on
SwitchB.
Data preparation
To complete the configuration, you need the following data:
l
VLANs to which GE 0/0/1 of SwitchB is added in tagged mode: VLAN 1000 to VLAN
1100, VLAN 1101, VLAN 1102, VLAN 1103, and VLAN 101
VLANs to which GE 0/0/2 of SwitchB is added in tagged mode: VLAN 101 to VLAN 150,
VLAN 1101, VLAN 1102, and VLAN 1103
VLANs to which GE 0/0/1 of SwitchA is added in tagged mode: VLAN 1101, VLAN 1102,
and VLAN 1103
VLANs to which GE 0/0/1 of SwitchA is added in untagged mode: VLAN 21
Interface on SwitchB where VLAN mapping is configured: GE 0/0/1
Interface on SwitchA where selective QinQ is configured: GE 0/0/1
Procedure
Step 1 # Configure SwitchA.
# Create VLANs.
<Quidway> system-view
[Quidway] vlan batch 21 to 70 1101 to 1103
# Add related GE 0/0/1 to the VLANs.
[Quidway] interface gigabitethernet 0/0/1
[Quidway-GigabitEthernet0/0/1] port hybrid untagged vlan 21
[Quidway-GigabitEthernet0/0/1] port hybrid tagged vlan 1101 to 1103
[Quidway-GigabitEthernet0/0/1] quit
# Configure selective QinQ on GE 0/0/1.
[Quidway] interface gigabitethernet 0/0/1
[Quidway-GigabitEthernet0/0/1] qinq vlan-translation enable
[Quidway-GigabitEthernet0/0/1] port vlan-stacking vlan 101 to 150 stack-vlan 21
[Quidway-GigabitEthernet0/0/1] quit
Step 2 # Configure SwitchB.
# Create VLANs.
<Quidway> system-view
[Quidway] vlan batch 101 to 150 1000 to 1103
# Add GE 0/0/1 and GE 0/0/2 to the VLANs.
[Quidway] interface gigabitethernet
[Quidway-GigabitEthernet0/0/1] port
[Quidway-GigabitEthernet0/0/1] quit
[Quidway] interface gigabitethernet
[Quidway-GigabitEthernet0/0/2] port
[Quidway-GigabitEthernet0/0/2] quit
0/0/1
hybrid tagged vlan 101 1000 to 1103
0/0/2
hybrid tagged vlan 101 to 150 1101 to 1103
# Configure VLAN mapping on GE 0/0/1.
[Quidway] interface gigabitethernet 0/0/1
[Quidway-GigabitEthernet0/0/1] qinq vlan-translation enable
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
155
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
5 QinQ Configuration
[Quidway-GigabitEthernet0/0/1] port vlan-mapping vlan 1000 to 1100 map-vlan 101
[Quidway-GigabitEthernet0/0/1] quit
Step 3 Verify the configuration.
The Internet access service, IPTV service, and VoIP service can be used.
----End
Configuration Files
Configuration file of SwitchA
#
sysname Quidway
#
vlan batch 21 to 70 1101 to 1103
#
interface GigabitEthernet0/0/1
qinq vlan-translation enable
port hybrid tagged vlan 1101 to 1103
port hybrid untagged vlan 21
port vlan-stacking vlan 101 to 150 stack-vlan 21
#
return
Configuration file of SwitchB
#
sysname Quidway
#
vlan batch 101 to 150 1000 to 1103
#
interface GigabitEthernet0/0/1
qinq vlan-translation enable
port hybrid tagged vlan 101 1000 to 1103
port vlan-mapping vlan 1000 to 1100 map-vlan 101
#
interface GigabitEthernet0/0/2
port hybrid tagged vlan 101 to 150 1101 to 1103
#
return
5.7.4 Example for Configuring QinQ Stacking on a VLANIF
Interface
In this networking, the management VLAN is deployed on the remote server and the VLAN ID
of SwitchA is the same as the management VLAN ID. The VLAN ID provided by the carrier,
however, is different from the management VLAN ID. To remotely log in to the remote server
for managing VLAN services on SwitchA, you can configure VLAN stacking according to this
example.
Networking Requirements
As shown in Figure 5-5, SwitchA is connected to the remote server through the third-party
network. The management VLAN is deployed on the remote server and the VLAN ID of the
downstream user connected to SwitchA is the same as the management VLAN ID. The VLAN
ID provided by the carrier, however, is different from the management VLAN ID.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
156
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
5 QinQ Configuration
Figure 5-5 Configuring QinQ stacking on the VLANIF interface
IP
10
20
GE0/0/2
Internet
Server
GE0/0/2
SwitchA GE0/0/1
IP
10
GE0/0/2
SwitchC
GE0/0/1
user1
VLAN 10
To remotely log in to the remote server for managing VLAN services on SwitchA, you can
configure QinQ stacking on the VLANIF interface corresponding to the management VLAN on
SwitchB.
NOTE
The VLANIF interface where QinQ stacking is configured must correspond to the management VLAN.
This is because other types of VLANs do not support QinQ stacking.
Configuration Roadmap
The configuration roadmap is as follows:
1.
Configure QinQ on SwitchA.
2.
Perform the following steps on the remote server:
a.
Create VLAN 10 and configure VLAN 10 as the management VLAN.
b.
Create a VLANIF interface on VLAN 10.
c.
Configure QinQ stacking on the VLANIF interface.
Data Preparation
To complete the configuration, you need the following data:
l
Outer tag that SwitchA adds to data frames
Management VLAN ID on the remote server
Procedure
Step 1 Configure SwitchC.
# Configure GE 0/0/1 and GE 0/0/2 to allow packets from VLAN 10 to pass through.
<Quidway> system-view
[Quidway] sysname SwitchC
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
157
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
[SwitchC] vlan batch 10
[SwitchC] interface gigabitethernet
[SwitchC-GigabitEthernet0/0/1] port
[SwitchC-GigabitEthernet0/0/1] quit
[SwitchC] interface gigabitethernet
[SwitchC-GigabitEthernet0/0/2] port
[SwitchC-GigabitEthernet0/0/2] quit
5 QinQ Configuration
0/0/1
hybrid tagged vlan 10
0/0/2
hybrid tagged vlan 10
Step 2 Configure SwitchA.
# Configure QinQ so that the frames sent from SwitchA to the remote server carry double tags.
<Quidway> system-view
[Quidway] sysname SwitchA
[SwitchA] vlan batch 20
[SwitchA] interface gigabitethernet
[SwitchA-GigabitEthernet0/0/1] port
[SwitchA-GigabitEthernet0/0/1] port
[SwitchA-GigabitEthernet0/0/1] quit
[SwitchA] interface gigabitethernet
[SwitchA-GigabitEthernet0/0/2] port
[SwitchA-GigabitEthernet0/0/2] quit
0/0/1
vlan-stacking vlan 10 stack-vlan 20
hybrid untagged vlan 20
0/0/2
hybrid tagged vlan 20
Step 3 Configure the remote server.
# Configure GE 0/0/2 to allow frames from VLAN 20 to pass through.
<Quidway> system-view
[Quidway] sysname Server
[Server] vlan batch 10 20
[Server] interface gigabitethernet 0/0/2
[Server-GigabitEthernet0/0/2] port hybrid tagged vlan 20
[Server-GigabitEthernet0/0/2] quit
# Configure QinQ stacking.
[Server] vlan 10
[Server-vlan10] management-vlan
[Server-vlan10] quit
[Server] interface vlanif 10
[Server-Vlanif10] undo icmp host-unreachable send
[Server-Vlanif10] qinq stacking vlan 20
[Server-Vlanif10] ip address 10.10.10.1 24
[Server-Vlanif10] quit
[Server] interface gigabitethernet 0/0/2
[Server-GigabitEthernet0/0/2] port hybrid tagged vlan 10 20
Step 4 Verify the configuration.
You can log in to the remote server for managing VLAN services on SwitchA.
----End
Configuration Files
l
Configuration file of SwitchA
#
sysname SwitchA
#
vlan batch 20
#
interface GigabitEthernet 0/0/1
port hybrid untagged vlan 20
port vlan-stacking vlan 10 stack-vlan 20
#
interface GigabitEthernet 0/0/2
port hybrid tagged vlan 20
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
158
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
5 QinQ Configuration
#
return
Configuration file of SwitchC
#
sysname SwitchC
#
vlan batch 10
#
interface GigabitEthernet 0/0/1
port hybrid tagged vlan 10
#
interface GigabitEthernet 0/0/2
port hybrid tagged vlan 10
#
return
Configuration file of the remote server
#
sysname Server
#
vlan batch 10 20
#
vlan 10
management-vlan
#
interface Vlanif10
ip address 10.10.10.1 255.255.255.0
undo icmp host-unreachable send
qinq stacking vlan 20
#
interface GigabitEthernet 0/0/2
port hybrid tagged vlan 10 20
#
return
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
159
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
6 GVRP Configuration
GVRP Configuration
About This Chapter
This chapter describes basic GVRP concepts, GVRP configuration procedures, and concludes
with a GVRP configuration example.
6.1 GVRP Overview
This section explains the concepts of Generic Attribute Registration Protocol (GARP) and GARP
VLAN Registration Protocol (GVRP), and how they relate to each another.
6.2 GVRP Features Supported by the S5700
This section describes the GVRP features supported by the S5700.
6.3 Configuring GVRP
This section describes how to configure the GVRP function.
6.4 Maintaining GVRP
This section describes how to clear the GARP statistics.
6.5 Configuration Examples
This section provides a GVRP configuration example.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
160
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
6 GVRP Configuration
6.1 GVRP Overview
This section explains the concepts of Generic Attribute Registration Protocol (GARP) and GARP
VLAN Registration Protocol (GVRP), and how they relate to each another.
GVRP
GVRP is an application of GARP that maintains and propagates VLAN registration information
to other devices.
GARP
GARP enables member switches on a LAN to distribute, transmit, and register information such
as VLAN information and multicast addresses with one another.
GARP is not an entity on a device. GARP-compliant entities are called GARP participants.
GVRP is a GARP application. When a GARP application runs on an interface, the interface is
considered a GARP participant.
l
GARP messages
GARP members transmit VLAN registration information by exchanging GARP messages.
The three main GARP messages are Join, Leave, and LeaveAll.
Join messages: When a GARP participant expects other devices to register its attributes,
it sends Join messages to other devices. When the GARP participant receives a Join
message from another participant or is statically configured with attributes, it also sends
Join messages to other devices for the devices to register the new attributes.
Leave messages: When a GARP participant expects other devices to deregister its
attributes, it sends Leave messages to other devices. When the GARP participant
receives a Leave message from another participant or some of its attributes are statically
deregistered, it also sends Leave messages to other devices.
LeaveAll messages: When a GARP participant is enabled, the LeaveAll timer is started.
When the LeaveAll timer expires, the GARP participant sends LeaveAll messages to
request other GARP participants to deregister all the attributes of the sender. Then other
participants can re-register the attributes.
The Join, Leave, and LeaveAll messages are used to control registration and
deregistration of attributes.
Through GARP messages, all attributes that need to be registered are sent to all the
GARP-enabled devices on the same LAN.
GARP timers
The GARP timers controls the interval at which GARP messages sent. GARP defines four
timers to control the intervals for sending GARP messages.
Hold timer: When a GARP participant receives a registration message from another
participant, it does not send the registration message in a Join message to other
participants immediately. Instead, the participant starts the Hold timer. When the Hold
timer expires, the participant packs all the registration messages received within this
period in a Join message and sends the Join message to other participants. Hold timers
helps reduce bandwidth usage on the network.
Join timer: To ensure reliable transmission of Join messages, a participant can send each
Join message twice. If the participant does not receive a response after sending the Join
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
161
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
6 GVRP Configuration
message the first time, it sends the Join message again. The Join timer specifies the
interval between the two Join messages.
Leave timer: When a GARP participant expects other participants to deregister its
attribute, it sends Leave messages to other participants. When another participant
receives the Leave message, it starts the Leave timer. If the participant does not receive
any Join message before the Leave timer expires, it deregisters the attributes of the
Leave message sender.
LeaveAll timer: When a GARP participant is enabled, the LeaveAll timer is started.
When the LeaveAll timer expires, the GARP participant sends LeaveAll messages to
request other GARP participants to re-register all its attributes. Then the LeaveAll timer
restarts.
NOTE
l The GARP timers apply to all GARP participants (such as GVRP) on the same LAN.
l The Hold timer, Join timer, and Leave timer must be set individually on each interface,
whereas the LeaveAll timer is set globally and takes effect on all interfaces of a device.
l Devices on a network may have different settings for the LeaveAll timer. In this case, all the
devices use the smallest LeaveAll timer value on the network. When the LeaveAll timer of
a device expires, the device sends LeaveAll messages to other devices. After other devices
receive the LeaveAll messages, they reset their LeaveAll timers. Therefore, only the
LeavelAll timer with the smallest value takes effect even if devices have different settings
for the LeaveAll timer.
GARP operation process
Through GARP, the configuration information of a GARP member can be propagated on
the entire LAN. A GARP member may be a terminal workstation or a bridge. A GARP
member sends an attribute declaration or an attribute reclaim declaration to request other
GARP members to register or deregister its attributes. The GARP member can also register
or deregister attributes of other members when receiving attribute declarations or attribute
reclaim declarations from other members. When an interface receives an attribute
declaration, it registers the attribute. When the interface receives an attribute reclaim
declaration, the interface deregisters the attribute.
PDUs sent from a GARP participant use a multicast MAC address as the destination MAC
address. When a device receives a packet from a GARP participant, the device identifies
the packet according to the destination MAC address of the packet and sends the packet to
the corresponding GARP participant (such as GVRP).
Format of a GARP packet
Figure 6-1 shows the format of a GARP packet.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
162
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
6 GVRP Configuration
Figure 6-1 Format of a GARP packet
DA SA length DSAP SSAP Ctrl
PDU
Ethernet Frame
N
Protocol ID Message 1 Message N End Mark
1
2
Attribute Type
GARP PDU structure
Message structure
Attribute List
N
1
Attribute 1
1
Attribute List structure
Attribute N End Mark
3
Attribute Length Attribute Event Attribute Value
Attribute structure
The following table describes the fields in a GARP packet.
Issue 02 (2011-11-21)
Field
Description
Value
Protocol ID
Indicates the protocol ID.
The value is 1.
Message
Indicates the messages in
the packet. A message
consists of the Attribute
Type and Attribute List
fields.
Attribute Type
Indicates the type of an
attribute, which is defined
by the GARP application.
The value is 0x01 for
GVRP, indicating that the
attribute value is a VLAN
ID.
Attribute List
Indicates the attribute list,
which consists of multiple
attributes.
Attribute
Indicates an attribute,
which consists of the
Attribute Length, Attribute
Event, and Attribute Value
fields.
Attribute Length
Indicates the length of an
attribute.
The value ranges from 2 to
255, in bytes.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
163
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
6 GVRP Configuration
Field
Description
Value
Attribute Event
Indicates the event that an
attribute describes.
The value can be:
l 0: LeaveAll event
l 1: JoinEmpty event
l 2: JoinIn event
l 3: LeaveEmpty event
l 4: LeaveIn event
l 5: Empty event
Attribute Value
Indicates the value of an
attribute.
The value is a VLAN ID for
GVRP. This field is invalid
in a LeaveAll attribute.
End Mark
Indicates the end of a
GARP PDU.
The value is 0x00.
6.2 GVRP Features Supported by the S5700
This section describes the GVRP features supported by the S5700.
GVRP is an application of GARP. Based on the working mechanism of GARP, GVRP maintains
dynamic VLAN registration information in a device and propagates the registration information
to other devices.
After GVRP is enabled on the S5700, the S5700 can receive VLAN registration information
from other devices and dynamically update local VLAN registration information. VLAN
registration information includes which VLAN members are on the VLAN and through which
interfaces their packets can be sent to the S5700. The S5700 can also send the local VLAN
registration information to other devices. By exchanging VLAN registration information, all the
devices on the same LAN have the same VLAN information. The VLAN registration
information transmitted through GVRP contains both static local registration information that
is manually configured and the dynamic registration information from other devices.
A GVRP interface supports three registration modes:
l
Normal: In this mode, the GVRP interface can dynamically register and deregister VLANs,
and transmit dynamic VLAN registration information and static VLAN registration
information.
Fixed: In this mode, the GVRP interface is disabled from dynamically registering and
deregistering VLANs and can transmit only the static registration information. If the
registration mode of a trunk interface is set to fixed, the interface allows only the manually
configured VLANs to pass even if it is configured to allow all the VLANs to pass.
Forbidden: In this mode, the GVRP interface is disabled from dynamically registering and
deregistering VLANs and can transmit only information about VLAN 1. If the registration
mode of a trunk interface is set to forbidden, the interface allows only VLAN 1 to pass even
if it is configured to allow all the VLANs to pass.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
164
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
6 GVRP Configuration
NOTE
The S5700 supports a maximum of 4094 dynamic VLANs.
The GVRP protocol can run only in the Common and Internal Spanning Tree (CIST) instance. The interface
blocked by MSTP in the CIST instance cannot send or receive GVRP packets.
6.3 Configuring GVRP
This section describes how to configure the GVRP function.
6.3.1 Establishing the Configuration Task
Applicable Environment
On a complex Layer 2 network, GVRP enables interfaces to dynamically join or leave VLANs,
which reduces manual configuration workload.
Pre-configuration Tasks
Before configuring the GVRP function, complete the following tasks:
l
Adding the GVRP interfaces to all VLANs
Configuring the interface to send BPDUs to the CPU
Data Preparation
To configure the GVRP function, you need the following data.
No.
Data
(Optional) Registration mode of GVRP interfaces
(Optional) Values of the GARP timers
6.3.2 Enabling GVRP
Context
Perform the following steps on the S5700 to enable GVRP.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
gvrp
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
165
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
6 GVRP Configuration
GVRP is enabled globally.
Step 3 Run:
interface interface-type interface-number
The interface view is displayed.
Step 4 Run:
port link-type trunk
The link type of the interface is set to trunk.
Step 5 Run:
port trunk allow-pass vlan { { vlan-id1 [ to vlan-id2 ] }&<1-10> | all }
The interface is added to the specified VLANs.
Step 6 Run:
gvrp
GVRP is enabled on the interface.
By default, GVRP is disabled globally and on each interface.
NOTE
l Before enabling GVRP on an interface, you must enable GVRP globally.
l Before enabling GVRP on an interface, you must set the link type of the interface to trunk.
----End
6.3.3 (Optional) Setting the Registration Mode for a GVRP Interface
Context
A GVRP interface supports three registration modes:
l
Normal: In this mode, the GVRP interface can dynamically register and deregister VLANs,
and transmit dynamic VLAN registration information and static VLAN registration
information.
Fixed: In this mode, the GVRP interface is disabled from dynamically registering and
deregistering VLANs and can transmit only the static registration information. If the
registration mode of a trunk interface is set to fixed, the interface allows only the manually
configured VLANs to pass even if it is configured to allow all the VLANs to pass.
Forbidden: In this mode, the GVRP interface is disabled from dynamically registering and
deregistering VLANs and can transmit only information about VLAN 1. If the registration
mode of a trunk interface is set to forbidden, the interface allows only VLAN 1 even if it
is configured to allow all the VLANs.
Perform the following steps on the S5700 to set the registration mode for an interface.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
166
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
6 GVRP Configuration
Step 2 Run:
interface interface-type interface-number
The interface view is displayed.
Step 3 Run:
gvrp registration { fixed | forbidden | normal }
The registration mode is set for the interface.
By default, the registration type of a GVRP interface is normal.
NOTE
Before setting the registration mode for an interface, enable GVRP on the interface.
----End
6.3.4 (Optional) Setting the GARP Timers
Context
When a GARP participant is enabled, the LeaveAll timer is started. When the LeaveAll timer
expires, the GARP participant sends LeaveAll messages to request other GARP participants to
re-register all its attributes. Then the LeaveAll timer restarts.
Devices on a network may have different settings for the LeaveAll timer. In this case, all the
devices use the smallest LeaveAll timer value on the network. When the LeaveAll timer of a
device expires, the device sends LeaveAll messages to other devices. After other devices receive
the LeaveAll messages, they reset their LeaveAll timers. Therefore, only the LeavelAll timer
with the smallest value takes effect even if devices have different settings for the LeaveAll timer.
When using the garp timer command to set the GARP timers, pay attention to the following
points:
l
The undo garp timer command restores the default values of the GARP timers. If the
default value of a timer is out of the valid range, the undo garp timer command does not
take effect.
The value range of each timer changes with the values of the other timers. If a value set for
a timer is not within the allowed range, change the value of the timer that determines the
value range of this timer.
To restore the default values of all the GARP timers, restore the Hold timer to the default
value, and then sequentially restore the Join timer, Leave timer, and LeaveAll timer to the
default values.
NOTE
It is recommended that you use the following values for the GVRP timers:
l
GARP Hold timer: 100 centiseconds (1 second)
GARP Join timer: 600 centiseconds (6 seconds)
GARP Leave timer: 3000 centiseconds (30 seconds)
GARP LeaveAll timer: 12000 centiseconds (2 minutes)
When the number of dynamic VLANs increases, the lengths of the GARP timers need to be increased.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
167
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
6 GVRP Configuration
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
garp timer leaveall timer-value
The LeaveAll timer is set.
The default value of the LeaveAll timer is 1000 centiseconds (10 seconds).
Step 3 Run:
interface interface-type interface-number
The interface view is displayed.
Step 4 Run:
garp timer { hold | join | leave } timer-value
The Hold timer, Join timer, or Leave timer is set.
By default, the value of the Hold timer is 10 centiseconds, the value of the Join timer is 20
centiseconds, and the value of the Leave timer is 60 centiseconds.
----End
6.3.5 Checking the Configuration
Procedure
l
Run the display gvrp status command to view the status of global GVRP is enabled.
Run the display gvrp statistics [ interface { interface-type interface-number [ to interfacetype interface-number ] }&<1-10> ] command to view the GVRP statistics on an interface.
Run the display garp timer [ interface { interface-type interface-number [ to interfacetype interface-number ] }&<1-10> ] command to view the values of GARP timers.
----End
6.4 Maintaining GVRP
This section describes how to clear the GARP statistics.
6.4.1 Clearing GARP Statistics
Context
CAUTION
GARP statistics cannot be restored after being cleared.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
168
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
6 GVRP Configuration
Procedure
Step 1 Run the reset garp statistics [ interface { interface-type interface-number [ to interface-type
interface-number ] }&<1-10> ] command in the user view to clear GARP statistics on the
specified interfaces.
----End
6.5 Configuration Examples
This section provides a GVRP configuration example.
6.5.1 Example for Configuring GVRP
Networking Requirements
As shown in Figure 6-2, a branch of Company A communicates with the headquarters through
SwitchA and SwitchB. To simplify the configuration, you need to enable GVRP on all switches
of Company A and set the registration mode to normal on interfaces of these switches.
Company B communicates with Company A through SwitchB and SwitchC. To configure
switches of Company B to transmit packets of only VLANs of Company B, you need to enable
GVRP on all switches of Company B and set the registration mode to fixed on the interfaces
connected to switches of Company A.
Figure 6-2 Configuring GVRP
SwitchB
GE0/0/1
SwitchA
GE0/0/2
GE0/0/1SwitchC
GE0/0/1
Company A
GE0/0/2
GE0/0/2
Branch of
company A
Company A
Company A
Company B
Configuration Roadmap
The configuration roadmap is as follows:
1.
Enable GVRP globally.
2.
Set the link type of the interfaces to trunk.
3.
Enable GVRP on interfaces.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
169
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
4.
6 GVRP Configuration
Set the registration mode of interfaces.
Data Preparation
To complete the configuration, you need the following data:
l
VLANs allowed by interfaces of SwitchA, SwitchB, and SwitchC: all VLANs
Registration mode for interfaces of SwitchA and SwitchB: normal
Registration modes of GE 0/0/1 and GE 0/0/2 of SwitchC: fixed and normal respectively
VLANS of Company B on SwitchC: VLAN 101 to VLAN 200
Procedure
Step 1 Configure SwitchA.
# Enable GVRP globally.
<Quidway> system-view
[Quidway] sysname SwitchA
[SwitchA] gvrp
# Set the link type of GE 0/0/1 and GE 0/0/2 to trunk and configure the interfaces to allow all
VLANs.
[SwitchA] interface gigabitethernet
[SwitchA-GigabitEthernet0/0/1] port
[SwitchA-GigabitEthernet0/0/1] port
[SwitchA-GigabitEthernet0/0/1] quit
[SwitchA] interface gigabitethernet
[SwitchA-GigabitEthernet0/0/2] port
[SwitchA-GigabitEthernet0/0/2] port
[SwitchA-GigabitEthernet0/0/2] quit
0/0/1
link-type trunk
trunk allow-pass vlan all
0/0/2
link-type trunk
trunk allow-pass vlan all
# Enable GVRP on the interfaces and set the registration modes of the interfaces.
[SwitchA] interface gigabitethernet
[SwitchA-GigabitEthernet0/0/1] gvrp
[SwitchA-GigabitEthernet0/0/1] gvrp
[SwitchA-GigabitEthernet0/0/1] bpdu
[SwitchA-GigabitEthernet0/0/1] quit
[SwitchA] interface gigabitethernet
[SwitchA-GigabitEthernet0/0/2] gvrp
[SwitchA-GigabitEthernet0/0/2] gvrp
[SwitchA-GigabitEthernet0/0/2] bpdu
[SwitchA-GigabitEthernet0/0/2] quit
0/0/1
registration normal
enable
0/0/2
registration normal
enable
The configuration of SwitchB is similar to the configuration of SwitchA.
Step 2 Configure SwitchC.
# Create VLAN 101 to VLAN 200.
<Quidway> system-view
[Quidway] sysname SwitchC
[SwitchC] vlan batch 101 to 200
# Enable GVRP globally.
[SwitchC] gvrp
# Set the link type of GE 0/0/1 and GE 0/0/2 to trunk and configure the interfaces to allow all
VLANs.
[SwitchC] interface gigabitethernet 0/0/1
[SwitchC-GigabitEthernet0/0/1] port link-type trunk
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
170
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
[SwitchC-GigabitEthernet0/0/1] port
[SwitchC-GigabitEthernet0/0/1] quit
[SwitchC] interface gigabitethernet
[SwitchC-GigabitEthernet0/0/2] port
[SwitchC-GigabitEthernet0/0/2] port
[SwitchC-GigabitEthernet0/0/2] quit
6 GVRP Configuration
trunk allow-pass vlan all
0/0/2
link-type trunk
trunk allow-pass vlan all
# Enable GVRP on the interfaces and set the registration modes of the interfaces.
[SwitchC] interface gigabitethernet
[SwitchC-GigabitEthernet0/0/1] gvrp
[SwitchC-GigabitEthernet0/0/1] gvrp
[SwitchC-GigabitEthernet0/0/1] bpdu
[SwitchC-GigabitEthernet0/0/1] quit
[SwitchC] interface gigabitethernet
[SwitchC-GigabitEthernet0/0/2] gvrp
[SwitchC-GigabitEthernet0/0/2] gvrp
[SwitchC-GigabitEthernet0/0/2] bpdu
[SwitchC-GigabitEthernet0/0/2] quit
0/0/1
registration fixed
enable
0/0/2
registration normal
enable
Step 3 Verify the configuration.
After the configuration is complete, the branch of Company A can communicate with the
headquarters, and users of Company A in VLAN 101 to VLAN 200 can communicate with users
in Company B.
Run the display gvrp status command on SwitchA to check whether GVRP is enabled globally.
The following information is displayed:
<SwitchA> display gvrp status
GVRP is enabled
Run the display gvrp statistics command on SwitchA to view GVRP statistics on GVRP
interfaces, including the GVRP state, number of GVRP registration failures, source MAC
address of the last GVRP PDU, and registration mode.
<SwitchA> display gvrp statistics
GVRP statistics on port GigabitEthernet0/0/1
GVRP status
: Enabled
GVRP registrations failed
: 0
GVRP last PDU origin
: 0000-0000-0000
GVRP registration type
: Normal
Verify the configurations of SwitchB and SwitchC in the same way.
----End
Configuration Files
l
Configuration file of SwitchA
#
sysname SwitchA
#
gvrp
#
interface GigabitEthernet0/0/1
port link-type trunk
port trunk allow-pass vlan 2 to 4094
gvrp
#
interface GigabitEthernet0/0/2
port link-type trunk
port trunk allow-pass vlan 2 to 4094
gvrp
#
return
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
171
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
6 GVRP Configuration
Configuration file of SwitchB
#
sysname SwitchB
#
gvrp
#
interface GigabitEthernet0/0/1
port link-type trunk
port trunk allow-pass vlan 2 to 4094
gvrp
#
interface GigabitEthernet0/0/2
port link-type trunk
port trunk allow-pass vlan 2 to 4094
gvrp
#
return
Configuration file of SwitchC
#
sysname SwitchC
#
vlan batch 101 to 200
#
gvrp
#
interface GigabitEthernet0/0/1
port link-type trunk
port trunk allow-pass vlan 2 to 4094
gvrp
gvrp registration fixed
#
interface GigabitEthernet0/0/2
port link-type trunk
port trunk allow-pass vlan 2 to 4094
gvrp
#
return
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
172
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
7 MAC Address Table Configuration
MAC Address Table Configuration
About This Chapter
This chapter provides the basics for MAC address table configuration, configuration procedure,
and configuration examples.
7.1 MAC Address Table Overview
This section describes the definition of the MAC address table, how MAC address entries are
generated, and how packets are forwarded based on the MAC address table.
7.2 MAC Address Features Supported by the S5700
This section describes the MAC address features supported by the S5700 and provides usage
scenarios of the features to help you complete configuration.
7.3 Configuring a Static MAC Address Entry
A static MAC address entry specifies an outbound interface for packets destined for a specified
MAC address. Static MAC address entries protect the S5700 from MAC address attacks.
7.4 Configuring a Blackhole MAC Address Entry
You can configure a blackhole MAC address entry so that the S5700 can discard packets with
the specified source or destination MAC address.
7.5 Setting the Aging Time of Dynamic MAC Address Entries
Dynamic MAC address entries are created by the S5700 and can be aged out. Setting an
appropriate aging time prevents sharp increase of MAC address entries.
7.6 Disabling MAC Address Learning
If a fixed device is connected to an interface, you can disable MAC address learning on the
interface. This prevents other devices from accessing the interface and improves device security.
7.7 Limiting the Number of Learned MAC Addresses
This section describes how to limit the number of MAC addresses learned on an interface or in
a VLAN.
7.8 Configuring Port Security
The port security function prevents devices with untrusted MAC addresses from accessing an
interface. This function is applicable to the networks that require high access security.
7.9 Configuring MAC Address Anti-Flapping
This section describes how to prevent MAC address flapping between interfaces.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
173
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
7 MAC Address Table Configuration
7.10 Configuring MAC Address Flapping Detection
This section describes how to configure the switch to detect MAC address flapping.
7.11 Enabling MAC Spoofing Defense
MAC spoofing defense ensures that a MAC address learned on an interface will not be learned
on other interfaces, protecting the system against MAC spoofing attacks.
7.12 Configuring the Switch to Discard Packets with an All-Zero MAC Address
You can configure the switch to discard packets with an all-zero source or destination MAC
address.
7.13 Enabling MAC Address-triggered ARP Entry Update
The MAC address-triggered ARP entry update enables the switch to update the corresponding
ARP entry when the outbound interface in a MAC address entry changes.
7.14 Enabling Port Bridge
The port bridge function enables an interface to process packets in which the source and
destination MAC addresses are the same.
7.15 Configuration Examples
This section provides several examples of MAC address table configuration.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
174
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
7 MAC Address Table Configuration
7.1 MAC Address Table Overview
This section describes the definition of the MAC address table, how MAC address entries are
generated, and how packets are forwarded based on the MAC address table.
Definition
A MAC address table is maintained on theS5700. The MAC address table stores the MAC
addresses of other devices learned by the S5700, the VLAN IDs, and the outbound interfaces
that are used to send data. Before forwarding a data packet, the S5700 searches the MAC address
table based on the destination MAC address and the VLAN ID of the packet to find the outbound
interface quickly. This reduces the number of broadcast packets.
Creation of MAC Address Entries
MAC address entries can be created dynamically or manually.
l
Automatic creation: MAC address entries are learned by the system automatically. The
MAC address table needs to be updated constantly because the network topology always
changes. The automatically created MAC address entries are not always valid and have an
aging time. If an entry is not updated within the aging time, it is deleted. If the entry is
updated before its aging time expires, the aging timer is reset.
Manual creation: Automatically created MAC address entries cannot distinguish attack
packets from packets of authorized users. If a hacker sets the source MAC address of attack
packets to the MAC address of an authorized user and connects to another interface of the
S5700, the S5700 learns an incorrect MAC address entry. The packets that should be
forwarded to the authorized user are forwarded to the hacker. To improve interface security,
you can manually create MAC address entries to bind MAC addresses of authorized users
to specified interfaces. This prevents hackers from intercepting data of authorized users.
Manually created MAC address entries take precedence over automatically created MAC
address entries.
Classification of MAC Address Entries
MAC address entries are classified into the following types:
l
Dynamic MAC address entries that are learned by an interface after MAC address learning
is enabled.
Static MAC address entries that are configured manually. Static MAC address entries take
precedence over dynamic MAC address entries.
Blackhole MAC address entries that are the manually configured and used to discard data
frames with the specified source or destination MAC addresses. Blackhole MAC address
entries take precedence over dynamic MAC address entries.
Packet Forwarding Based on the MAC Address Table
The S5700 forwards packets based on the MAC address table in either of the following modes:
l
Issue 02 (2011-11-21)
Unicast mode: If the destination MAC address of a packet can be found in the MAC address
table, the S5700 forwards the packet through the outbound interface specified in the
matching entry.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
175
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
7 MAC Address Table Configuration
Broadcast mode: If a packet is a broadcast or multicast packet or its destination MAC
address cannot be found in the MAC address table, the S5700 broadcasts the packet to all
the interfaces except the inbound interface of the packet.
7.2 MAC Address Features Supported by the S5700
This section describes the MAC address features supported by the S5700 and provides usage
scenarios of the features to help you complete configuration.
You can configure the following MAC address features to improve device security and control
the number of entries in the MAC address table:
l
Create static MAC address entries for MAC addresses of fixed upstream devices or trusted
user devices to improve communication security.
Configure blackhole MAC address entries to protect the S5700 from attacks.
Set a proper aging time for dynamic MAC addresses to prevent sharp increase of dynamic
MAC address entries.
You can use the following methods to improve security or meet special requirements:
l
Disable MAC address learning. This method can be used on a network where the topology
seldom changes or forwarding paths are specified in static MAC address entries. This
method prevents users with unknown MAC addresses from accessing the network, protects
the network from MAC address attacks, and improves network security.
Limit the number of MAC addresses that can be learned. MAC address limiting protects
the S5700 from MAC address attacks on an insecure network.
Enable port security. If a network requires high security, port security can be configured
on the interfaces connected to trusted devices. The port security function prevents devices
with untrusted MAC addresses from accessing these interfaces and improves device
security.
Configure MAC address anti-flapping. MAC address flapping occurs when a MAC address
is learned on two interfaces. If an interface is connected to a trusted upstream device or
server, you can set a high MAC address learning priority for the interface. The MAC address
learned by the interface will not be overridden by an entry learned by another interface.
This protects the S5700 from MAC address attacks.
Configure MAC spoofing defense. This function ensures that a MAC address learned on
an interface will not be learned on other interfaces, protecting the system against MAC
spoofing attacks.
Configure MAC address flapping detection. This function reduces the impact of loops on
the S5700.
Discard packets with an all-zero MAC address. A faulty device may send packets with an
all-zero source or destination MAC address to the S5700. You can configure the S5700 to
discard such packets and send a trap to the network management system (NMS). You can
locate the faulty device according to the trap message.
Enable MAC address-triggered ARP entry update. This function enables the S5700 to
update the corresponding ARP entry when the outbound interface in a MAC address entry
changes.
Enable port bridge. This function enables an interface to process packets in which the source
and destination MAC addresses are the same. It can be configured on an S5700 connected
to a device without Layer 2 forwarding capability or an S5700 functioning as an access
device in a data center.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
176
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
7 MAC Address Table Configuration
NOTE
Only the S5706 and S5700HI support MAC address anti-flapping.
The S5706 and S5700HI do not support MAC spoofing defense.
Disabling MAC Address Learning
When an S5700 with MAC address learning enabled receives an Ethernet frame, it records the
source MAC address and inbound interface of the Ethernet frame in a MAC address entry. When
receiving other Ethernet frames destined for this MAC address, the S5700 forwards the frames
through the outbound interface according to the MAC address entry. The MAC address learning
function reduces broadcast packets on a network.
After MAC address learning is disabled on an interface, the S5700 does not learn source MAC
addresses of packets received by the interface.
Limiting the Number of Learned MAC Addresses
The S5700 can limit the number of MAC addresses learned on an interfaceor a VLAN. When
the number of learned MAC address entries reaches the limit, the S5700 stops learning MAC
addresses. When the S5700 receives packets with unknown source MAC addresses, it generates
an alarm to alert you if it is configured to do so. This method protects user devices and the
network from MAC address attacks.
Port Security
The port security function changes MAC addresses learned by an interface to secure dynamic
MAC addresses or sticky MAC addresses. It prevents devices with untrusted MAC addresses
from accessing an interface and improves device security.
Differences between secure dynamic MAC addresses and sticky MAC addresses are:
l
Secure dynamic MAC addresses are learned after port security is enabled and are not aged
out by default. You can set the aging time for secure dynamic MAC addresses so that they
can be aged out. Secure dynamic MAC addresses are lost after the device restarts, so the
device needs to learn the MAC addresses again.
Sticky MAC addresses are learned after the sticky MAC function is enabled. Sticky MAC
addresses are not aged out and still exist after the S5700 restarts.
MAC Address Anti-flapping
MAC address flapping occurs on a network when the network has a loop or is attacked. To
prevent MAC address flapping, you can set MAC address learning priorities for interfaces so
that MAC addresses can be learned by correct interfaces. When the same MAC address is learned
by interfaces with different priorities, the MAC address entry learned by the interface with the
highest priority overrides the MAC address entries learned by other interfaces. You can also
determine whether to allow MAC address flapping between interfaces with the same priority.
MAC Address Flapping Detection
The S5700 can detect MAC address flapping and perform a specified action, for example, block
the interface, to minimize the impact of MAC address flapping on the network. You can also
configure the S5700 to only send trap messages to the network management system when the
S5700 detects MAC address flapping.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
177
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
7 MAC Address Table Configuration
7.3 Configuring a Static MAC Address Entry
A static MAC address entry specifies an outbound interface for packets destined for a specified
MAC address. Static MAC address entries protect the S5700 from MAC address attacks.
Applicable Environment
You can configure a static MAC address entry if an interface is connected to an upstream device
or a server, as shown in Figure 7-1. Attackers may set the source MAC address of packets to
the server MAC address and send the packets to the Switch to intercept data of the server. To
protect the server and ensure communication between users and the server, you can configure a
static MAC address entry in which the destination MAC address is the server MAC address and
the outbound interface is the interface connected to the server.
Figure 7-1 Static MAC address entry configuration
Network
Server
Switch
VLAN2
LSW
PC1
VLAN4
PC2
Pre-configuration Tasks
None.
Data Preparation
To configure a static MAC address entry, you need the following data.
Issue 02 (2011-11-21)
No.
Data
Destination MAC address, destination outbound interface number, and ID of the
VLAN to which the outbound interface belongs
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
178
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
7 MAC Address Table Configuration
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
mac-address static mac-address interface-type interface-number vlan vlan-id1
A static MAC address entry is configured.
NOTE
Static MAC address entries take precedence over dynamic MAC address entries.
----End
Checking the Configuration
Run the display mac-address static [ vlan vlan-id | interface-type interface-number ] *
[ verbose ] command to view static MAC address entries.
7.4 Configuring a Blackhole MAC Address Entry
You can configure a blackhole MAC address entry so that the S5700 can discard packets with
the specified source or destination MAC address.
Applicable Environment
To protect user devices or network devices from MAC address attacks, you can configure
untrusted MAC addresses as blackhole MAC addresses. Packets with source or destination MAC
addresses matching the blackhole MAC address entries are discarded.
Pre-configuration Tasks
None.
Data Preparation
To configure a blackhole MAC address entry, you need the following data.
No.
Data
Destination or source MAC address and ID of VLAN to which the outbound interface
belongs to
Procedure
Step 1 Run:
system-view
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
179
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
7 MAC Address Table Configuration
The system view is displayed.
Step 2 Run:
mac-address blackhole mac-address [ vlan vlan-id ]
A blackhole MAC address entry is configured.
----End
Checking the Configuration
Run the display mac-address blackhole [ vlan vlan-id ] [ verbose ] command to view blackhole
MAC address entries.
7.5 Setting the Aging Time of Dynamic MAC Address
Entries
Dynamic MAC address entries are created by the S5700 and can be aged out. Setting an
appropriate aging time prevents sharp increase of MAC address entries.
Applicable Environment
Dynamic MAC address entries are learned by the S5700 from source MAC addresses of received
packets. The system starts an aging timer for each dynamic MAC address entry. If a dynamic
MAC address entry is not updated within a certain period (twice the aging time), this entry is
deleted. If the entry is updated within this period, the aging timer of this entry is reset. A shorter
aging time enables the S5700 to respond to network topology changes more quickly.
The network topology changes frequently, and the S5700 will learn many MAC addresses. After
an aging time is set for dynamic MAC address entries, the S5700 can delete unneeded MAC
address entries.
Pre-configuration Tasks
None.
Data Preparation
To set the aging time of dynamic MAC address entries, you need the following data.
No.
Data
Aging time
Procedure
Step 1 Run:
system-view
The system view is displayed.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
180
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
7 MAC Address Table Configuration
Step 2 Run:
mac-address aging-time aging-time
The aging time is set for dynamic MAC address entries.
By default, the aging time of dynamic MAC address entries is 300 seconds.
----End
Checking the Configuration
Run the display mac-address aging-time command to check the aging time of dynamic MAC
address entries.
7.6 Disabling MAC Address Learning
If a fixed device is connected to an interface, you can disable MAC address learning on the
interface. This prevents other devices from accessing the interface and improves device security.
7.6.1 Establishing the Configuration Task
Before disabling MAC address learning, familiarize yourself with the applicable environment,
complete the pre-configuration tasks, and obtain the data required for the configuration. This
will help you complete the configuration task quickly and accurately.
Applicable Environment
As shown in Figure 7-2, an interface of the Switch is connected to a server. To protect the server,
configure the server MAC address as a static MAC address, disable MAC address learning on
the interface, and configure the interface to discard the packets with unknown MAC addresses.
This configuration prevents other servers or terminals from accessing the interface and improves
network stability and security.
Figure 7-2 Disabling MAC address learning
Server
mac-address
learning disable
Switch
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
181
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
7 MAC Address Table Configuration
Pre-configuration Tasks
None.
Data Preparation
To disable MAC address learning, you need the following data.
No.
Data
Interface type and number
VLAN ID
7.6.2 Disabling MAC Address Learning on an Interface
Disabling MAC address learning on an interface can improve security of the device connected
to the interface.
Context
When an S5700 with MAC address learning enabled receives an Ethernet frame, it records the
source MAC address and inbound interface of the Ethernet frame in a MAC address entry. When
receiving other Ethernet frames destined for this MAC address, the S5700 forwards the frames
through the outbound interface according to the MAC address entry. The MAC address learning
function reduces broadcast packets on a network. After MAC address learning is disabled on an
interface, the S5700 does not learn source MAC addresses of packets received by the interface.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
interface interface-type interface-number
The interface view is displayed.
Step 3 Run:
mac-address learning disable [ action { discard | forward } ]
MAC address learning is disabled on the interface.
By default, MAC address learning is enabled on an interface.
You can configure an action for the S5700 to perform when a packet with an unknown MAC
address is received on the interface. By default, the S5700 forwards such packets based on the
MAC address table. When the action is set to discard, the S5700 searches for the source MAC
address of the packet in the MAC address table. If the source MAC address is found, the
S5700 forwards the packet according to the MAC address entry. If the source MAC address is
not found, the S5700 discards the packet.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
182
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
7 MAC Address Table Configuration
NOTE
If you set the action to forward when disabling MAC address learning, untrusted terminals can still access
the network. This action only controls the number of learned MAC address entries.
----End
7.6.3 Disabling MAC Address Learning in a VLAN
Disabling MAC address learning in a VLAN can protect users in this VLAN from MAC address
attacks.
Context
After MAC address learning is disabled in a VLAN, the S5700 checks source MAC addresses
of packets received by interfaces in the VLAN. If the source MAC address of a packet is in the
MAC address table, the S5700 forwards the packet; otherwise, the S5700 broadcasts the packet.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
vlan vlan-id
The VLAN view is displayed.
Step 3 Run:
mac-address learning disable
MAC address learning is disabled in the VLAN.
By default, MAC address learning is enabled in a VLAN.
----End
7.6.4 Checking the Configuration
After disabling MAC address learning on an interface or in a VLAN, use the following
commands to verify the configuration.
Procedure
l
Run the display current-configuration interface interface-type interface-number
command to view the current configuration of an interface.
Run the display vlan command to check the VLAN configuration.
----End
7.7 Limiting the Number of Learned MAC Addresses
This section describes how to limit the number of MAC addresses learned on an interface or in
a VLAN.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
183
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
7 MAC Address Table Configuration
7.7.1 Establishing the Configuration Task
Before limiting the number of learned MAC addresses, familiarize yourself with the applicable
environment, complete the pre-configuration tasks, and obtain the data required for the
configuration. This will help you complete the configuration task quickly and accurately.
Applicable Environment
As shown in Figure 7-3, an insecure residential network or enterprise often receives packets
with bogus MAC addresses. The capacity of a MAC address table is limited. If hackers forge a
large number of packets with different source MAC addresses and send the packets to the
Switch, the MAC address table of the Switch becomes full quickly. When the MAC address
table is full, the Switch cannot learn source MAC addresses of valid packets. A limit can be set
for the number of learned MAC addresses. When the number of learned MAC addresses reaches
the limit, the Switch stops learning MAC addresses. When the Switch receives packets with
unknown source MAC addresses, it can generate an alarm. This protects the network from MAC
address attacks.
Figure 7-3 Limiting the number of MAC addresses on an insecure network
Internet
Switch
VLAN2
MAC- Limit
VLAN2
LSW1
LSW2
VLAN2
Pre-configuration Tasks
Before limiting the number of learned MAC addresses, complete the following task:
l
Deleting the existing MAC address entries from the interface or VLAN where you want to
limit the number of learned MAC addresses
Data Preparation
To limit the number of learned MAC addresses, you need the following data.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
184
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
7 MAC Address Table Configuration
No.
Data
Maximum number of MAC addresses that can be learned on an interface or a VLAN
7.7.2 Limiting the Number of MAC Addresses Learned on an
Interface
When MAC address limiting is configured on an interface and the number of learned MAC
addresses on the interface reaches the limit, the switch stops learning MAC addresses on this
interface. When the interface receives packets with unknown source MAC addresses, the
switch can generate an alarm. This protects the network from MAC address attacks.
Context
When the number of learned MAC addresses reaches the limit, the switch forwards the packets
with new source MAC addresses but does not add the new MAC addresses to the MAC address
table.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
interface interface-type interface-number
The interface view is displayed.
Step 3 Run:
mac-limit maximum max-num
The maximum number of MAC addresses learned on the interface is set.
By default, the number of MAC addresses learned on an interface is not limited.
Step 4 Run:
mac-limit alarm { disable | enable }
The switch is configured to (or not to) send a trap to the NMS when the number of learned MAC
addresses reaches the limit.
By default, the switch sends a trap to the NMS when the number of learned MAC addresses
reaches the limit.
----End
7.7.3 Limiting the Number of MAC Addresses Learned in a VLAN
When MAC address limiting is configured in a VLAN and the number of learned MAC addresses
in the VLAN reaches the limit, the S5700 stops learning MAC addresses in this VLAN. When
the interface receives packets with unknown source MAC addresses, the switch can generate an
alarm. This protects the network from MAC address attacks.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
185
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
7 MAC Address Table Configuration
Context
When the number of learned MAC addresses reaches the limit, the switch forwards the packets
with new source MAC addresses but does not add the new MAC addresses to the MAC address
table.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
vlan vlan-id
The VLAN view is displayed.
Step 3 Run:
mac-limit maximum max-num
The maximum number of MAC addresses learned in the VLAN is set.
By default, the number of MAC addresses learned in a VLAN is not limited.
Step 4 Run:
mac-limit alarm { disable | enable }
The switch is configured to (or not to) send a trap to the NMS when the number of learned MAC
addresses reaches the limit.
By default, the switch sends a trap to the NMS when the number of learned MAC addresses
reaches the limit.
----End
7.7.4 Checking the Configuration
After completing the configuration of MAC address limiting, use the following command to
verify the configuration.
Procedure
Step 1 Run the display mac-limit [ interface-type interface-number | vlan vlan-id ] command to view
the MAC address limiting rule.
----End
7.8 Configuring Port Security
The port security function prevents devices with untrusted MAC addresses from accessing an
interface. This function is applicable to the networks that require high access security.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
186
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
7 MAC Address Table Configuration
7.8.1 Establishing the Configuration Task
The port security function changes MAC addresses learned by an interface to secure dynamic
MAC addresses or sticky MAC addresses. It prevents devices with untrusted MAC addresses
from accessing an interface and improves device security.
Applicable Environment
If a network requires high access security, you can configure port security on specified interfaces.
MAC addresses learned by these interfaces change to secure dynamic MAC addresses or sticky
MAC addresses. When the number of learned MAC addresses reaches the limit, the interface
does not learn new MAC addresses and allows only the devices with the learned MAC addresses
to communicate with the S5700. This prevents devices with untrusted MAC addresses from
accessing these interfaces, improving security of the S5700 and the network.
Pre-configuration Tasks
Before configuring port security on an interface, complete the following tasks:
l
Disabling MAC address limiting on the interface
Disabling MUX VLAN on the interface
Disabling MAC address authentication on the interface
Disabling 802.1x authentication on the interface
Disabling MAC address security for DHCP snooping on the interface
Data Preparation
To configure port security on an interface, you need the following data.
No.
Data
Secure dynamic MAC: interface type and number, limit on the number of learned
MAC addresses, action to perform when the limit is exceeded, and aging time of
secure dynamic MAC addresses
Sticky MAC: interface type and number, limit on the number of learned MAC
addresses, and action to perform when the limit is exceeded
7.8.2 Configuring the Secure Dynamic MAC Function on an
Interface
After port security is enabled on an interface, MAC addresses learned by the interface change
to secure dynamic MAC addresses. When the number of secure dynamic MAC addresses reaches
the limit, the interface does not learn new MAC addresses and allows only the devices with the
learned MAC addresses to communicate with the S5700. You can configure a protection action
for the S5700 to perform when it receives a packet with a new source MAC address.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
187
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
7 MAC Address Table Configuration
Context
By default, secure dynamic MAC addresses will not be aged out. You can set the aging time of
secure dynamic MAC addresses so that they can be aged out. Secure dynamic MAC addresses
are lost after the device restarts and the device needs to learn the MAC addresses again.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
interface interface-type interface-number
The interface view is displayed.
Step 3 Run:
port-security enable
Port security is enabled.
By default, port security is disabled on an interface.
NOTE
You can set the limit on the number of secure dynamic MAC addresses, aging time of secure dynamic
MAC addresses, and protection action only when port security is enabled.
Step 4 (Optional) Run:
port-security max-mac-num max-number
The limit on the number of secure dynamic MAC addresses is set.
By default, the limit on the number of secure dynamic MAC addresses is 1.
Step 5 (Optional) Run:
port-security protect-action { protect | restrict | shutdown }
The protection action is configured.
The default action is restrict.
l protect: discards packets with new source MAC addresses when the number of learned MAC
addresses reaches the limit.
l restrict: discards packets with new source MAC addresses and sends a trap message when
the number of learned MAC addresses exceeds the limit.
l shutdown: shuts down the interface when the number of learned MAC addresses exceeds
the limit.
Step 6 (Optional) Run:
port-security aging-time time [ type { absolute | inactivity } ]
The aging time of secure dynamic MAC addresses is set.
By default, secure dynamic MAC addresses will not be aged out.
----End
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
188
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
7 MAC Address Table Configuration
7.8.3 Configuring the Sticky MAC Function on an Interface
After the sticky MAC function is enabled on an interface, MAC addresses learned by the
interface change to sticky MAC addresses. When the number of sticky MAC addresses reaches
the limit, the interface does not learn new MAC addresses and allows only the devices with the
learned MAC addresses to communicate with the S5700. You can configure a protection action
for the S5700 to perform when it receives a packet with a new source MAC address.
Context
The sticky MAC function changes MAC addresses learned by an interface to sticky MAC
addresses. Sticky MAC addresses will not be aged out and will exist after the S5700 restarts.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
interface interface-type interface-number
The interface view is displayed.
Step 3 Run:
port-security enable
Port security is enabled.
By default, port security is disabled on an interface.
Step 4 Run:
port-security mac-address sticky
The sticky MAC function is enabled on the interface.
By default, the sticky MAC function is disabled on an interface.
Step 5 (Optional) Run:
port-security max-mac-num max-number
The limit on the number of sticky MAC addresses is set.
By default, the limit on the number of sticky MAC addresses is 1.
Step 6 (Optional) Run:
port-security protect-action { protect | restrict | shutdown }
The protection action is configured.
The default action is restrict.
l protect: discards packets with new source MAC addresses when the number of learned MAC
addresses reaches the limit.
l restrict: discards packets with new source MAC addresses and sends a trap message when
the number of learned MAC addresses exceeds the limit.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
189
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
7 MAC Address Table Configuration
l shutdown: shuts down the interface when the number of learned MAC addresses exceeds
the limit.
Step 7 (Optional) Run:
port-security mac-address sticky mac-address vlan vlan-id
A sticky MAC address entry is configured.
----End
7.8.4 Checking the Configuration
After completing the port security configuration, you can verify the configuration and view
secure dynamic MAC address entries or sticky MAC address entries.
Procedure
l
Run the display current-configuration interface interface-type interface-number
command to view the current configuration of an interface.
Run the display mac-address sticky [ vlan vlan-id | interface-type interface-number ] *
[ verbose ] command to view sticky MAC address entries.
Run the display mac-address security [ vlan vlan-id | interface-type interface-number ]
[ verbose ] command to view secure dynamic MAC address entries.
----End
7.9 Configuring MAC Address Anti-Flapping
This section describes how to prevent MAC address flapping between interfaces.
7.9.1 Establishing the Configuration Task
Before configuring MAC address anti-flapping, familiarize yourself with the applicable
environment, complete the pre-configuration tasks, and obtain the data required for the
configuration. This will help you complete the configuration task quickly and accurately.
Applicable Environment
As shown in Figure 7-4, an interface of the Switch is connected to a server. To prevent
unauthorized users from using the server MAC address to intercept data of the server, you can
set a high MAC address learning priority for the interface. When the same MAC address is
learned by the server-side interface and other interfaces, the entry learned by the server-side
interface overrides the MAC address entries learned by other interfaces. Therefore, the Switch
will not learn MAC addresses of unauthorized users and only authorized users can access the
server and use network resources.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
190
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
7 MAC Address Table Configuration
Figure 7-4 MAC address anti-flapping
MAC:11-22-33
Server
MAC:11-22-33
Switch
NOTE
The S5700SI and S5700EI do not support MAC Address Anti-flapping.
Pre-configuration Tasks
None.
Data Preparation
To configure MAC address anti-flapping, you need the following data.
No.
Data
(Optional) MAC address learning priority of each interface
7.9.2 Setting the MAC Address Learning Priority for an Interface
To prevent MAC address flapping, set different MAC address learning priorities for interfaces.
When interfaces learn the same MAC address, the MAC address entry learned by the interface
with the highest priority overrides the MAC address entries learned by the other interfaces.
Context
Setting different MAC address learning priorities for interfaces prevents MAC address flapping.
If an attacker uses the MAC address of an authorized network device to connect to the S5700
after the network device is powered off, the S5700 learns the MAC address on another interface.
If the interface connected to the network device has a higher priority than the interface connected
to the attacker, the S5700 can learn the MAC address on the correct interface after the network
device is powered on.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
191
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
7 MAC Address Table Configuration
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
interface interface-type interface-number
The interface view is displayed.
Step 3 Run:
mac-learning priority priority-id
A MAC address learning priority is set for the interface.
By default, the MAC address learning priority of an interface is 0. A larger priority value
indicates a higher MAC address learning priority.
----End
7.9.3 Prohibiting MAC Address Flapping Between Interfaces with
the Same Priority
Prohibiting MAC address flapping between interfaces with the same priority can improve
network security.
Context
When MAC address flapping between interfaces with the same priority is prohibited, these
interfaces cannot learn the same MAC addresses. If an attacker uses the MAC address of an
authorized network device to connect to the S5700 after the network device is powered off, the
S5700 learns the MAC address on another interface. After the network device is powered on,
the S5700 cannot learn the MAC address on the correct interface.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
undo mac-learning priority priority-id allow-flapping
MAC address flapping between the interfaces with a specified priority is prohibited.
By default, MAC address flapping between interfaces with the same priority is allowed.
----End
7.9.4 Checking the Configuration
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
192
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
7 MAC Address Table Configuration
Procedure
Step 1 Run the display current-configuration command to check the MAC address learning priorities
of interfaces.
----End
7.10 Configuring MAC Address Flapping Detection
This section describes how to configure the switch to detect MAC address flapping.
7.10.1 Establishing the Configuration Task
Before configuring MAC address flapping detection, familiarize yourself with the applicable
environment, complete the pre-configuration tasks, and obtain the data required for the
configuration. This will help you complete the configuration task quickly and accurately.
Applicable Environment
As shown in Figure 7-5, a loop occurs on the network, which will cause MAC address flapping.
After MAC address flapping detection is configured in a VLAN, the Switch checks all MAC
addresses in the VLAN to detect MAC address flapping.
The Switch checks whether a MAC address moves from one interface to another in the VLAN.
If MAC address flapping occurs, the Switch performs the configured action, for example,
blocking the interface to remove the loop. This function reduces MAC address flapping caused
by loops and broadcast storms. You can also configure the Switch to only send trap messages
to the NMS when it detects MAC address flapping.
Figure 7-5 MAC address flapping detection
Switch
Pre-configuration Tasks
None.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
193
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
7 MAC Address Table Configuration
Data Preparation
To configure MAC flapping detection, you need the following data.
No.
Data
ID of the VLAN where MAC address flapping needs to be configured
Blocking time for the interface where MAC address flapping occurs
Number of detection attempts before an interface is permanently blocked
7.10.2 Configuring MAC Address Flapping Detection
After MAC address flapping detection is configured in a VLAN, the S5700 checks all MAC
addresses in the VLAN to detect MAC address flapping. When MAC address flapping occurs
on an interface, the S5700 blocks the interface, blocks the MAC address, or only reports a trap
according to the configuration.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
vlan vlan-id
The VLAN view is displayed.
Step 3 Run:
loop-detect eth-loop { [ block-mac ] block-time block-time retry-times retry-times
| alarm-only }
MAC address flapping detection is configured in the VLAN.
When the S5700 detects MAC address flapping in the VLAN, it performs either of the following
actions:
l Blocks the interface or MAC address. When the block-mac keyword is used in the command,
the S5700 does not block the interface but blocks the traffic from the flapping MAC address.
l Sends a trap to the NMS.
----End
7.10.3 (Optional) Unblocking a Blocked Interface or MAC Address
After an interface or a MAC address is permanently blocked because of MAC address flapping,
the interface or MAC address can be restored only by using the reset loop-detect eth-loop
command in the corresponding VLAN view.
Context
After MAC address flapping detection is configured in a VLAN, the system checks all MAC
addresses in the VLAN to detect MAC address flapping. If MAC address flapping occurs on an
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
194
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
7 MAC Address Table Configuration
interface, the system blocks the interface. After a specified period of time, the system unblocks
the interface. If no MAC address flapping is detected within 20 seconds, the system completely
unblocks the interface and starts detection. If MAC address flapping is detected again within 20
seconds, the system blocks the interface. This process repeats for a specified number of times.
If MAC address flapping persists, the interface is permanently blocked.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
reset loop-detect eth-loop vlan vlan-id { all | interface { interface-type
interface-number } | mac-address mac-address }
The specified interface or MAC address is unblocked.
Before using the reset loop-detect eth-loop command, run the display loop-detect eth-loop
command to check which interfaces or MAC addresses are blocked.
----End
7.10.4 Checking the Configuration
After configuring MAC address flapping detection, use the following commands to verify the
configuration and view information about permanently blocked interfaces and MAC addresses.
Procedure
Step 1 Run the display loop-detect eth-loop [ vlan vlan-id ] command to check information about
MAC address flapping detection on a VLAN.
----End
7.11 Enabling MAC Spoofing Defense
MAC spoofing defense ensures that a MAC address learned on an interface will not be learned
on other interfaces, protecting the system against MAC spoofing attacks.
Applicable Environment
A user device may send bogus packets with a server's MAC address to prevent other users from
accessing the real server. To prevent such attacks, enable MAC spoofing defense on the networkside interface connected to the server so that the interface becomes a trusted interface. MAC
addresses learned by this interface will not be learned by other interfaces; therefore, the MAC
address entry of the server cannot be modified by attack packets.
NOTE
The S5706 and S5700HI do not support MAC spoofing defense.
Pre-configuration Tasks
Before configuring MAC spoofing defense, complete the following task:
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
195
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
7 MAC Address Table Configuration
Powering on the S5700 and ensuring that it functions properly
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
mac-spoofing-defend enable
Global MAC spoofing defense is enabled.
By default, global MAC spoofing defense is disabled.
Step 3 Run:
interface interface-type interface-number
The interface view is displayed.
Step 4 Run:
mac-spoofing-defend enable
MAC spoofing defense is enabled on the interface so that the interface becomes a trusted
interface.
By default, MAC spoofing defense is disabled on an interface.
----End
Checking the Configuration
Run the display current-configuration command to check the configuration of MAC spoofing
defense.
7.12 Configuring the Switch to Discard Packets with an AllZero MAC Address
You can configure the switch to discard packets with an all-zero source or destination MAC
address.
Applicable Environment
A faulty network device may send packets with an all-zero source or destination MAC address
to the switch. Configure the switch to discard such packets and send a trap to the NMS. Then
you can locate the faulty device according to the trap message.
Pre-configuration Tasks
l
Powering on the switch and ensuring that it functions properly
Data Preparation
None.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
196
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
7 MAC Address Table Configuration
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
drop illegal-mac enable
The switch is configured to discard packets with an all-zero MAC address.
By default, the switch does not discard packets with an all-zero MAC address.
Step 3 (Optional) Run:
drop illegal-mac alarm
The switch is configured to send a trap to the NMS when receiving packets with an all-zero
MAC address.
By default, the switch does not send a trap to the NMS when receiving packets with an all-zero
MAC address.
NOTE
The switch sends only one trap after receiving packets with an all-zero MAC address. To enable the
switch to send a trap again after receiving packets with an all-zero MAC address, run the drop illegal-mac
alarm command.
----End
Checking the Configuration
Run the display current-configuration command to check whether the switch is configured to
discard the packets with an all-zero MAC address.
7.13 Enabling MAC Address-triggered ARP Entry Update
The MAC address-triggered ARP entry update enables the switch to update the corresponding
ARP entry when the outbound interface in a MAC address entry changes.
Applicable Environment
Each network device uses an IP address to communicate with other devices. On an Ethernet
network, a device sends and receives Ethernet data frames based on MAC addresses. The ARP
protocol maps IP addresses to MAC addresses. When a device communicates with a device on
a different network segment, it finds the MAC address and outbound interface of a packet
according to the corresponding ARP entry.
If a user host moves from one interface to another, the host MAC address is learned by the new
interface, so the outbound interface mapping the MAC address changes. The corresponding ARP
entry, however, is not updated until the aging time expires. Before the ARP entry aging time
expires, the device sends data frames based on the original ARP entry. This causes data frame
loss. The S5700 provides the MAC address-triggered ARP entry update function to solve this
problem.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
197
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
7 MAC Address Table Configuration
Pre-configuration Tasks
None.
Data Preparation
None.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
mac-address update arp
MAC address-triggered ARP entry update is enabled.
By default, the switch does not update the corresponding ARP entry when the outbound interface
in a MAC address entry changes.
NOTE
l This command takes effect only for dynamic ARP entries. Static ARP entries are not updated when
the corresponding MAC address entries change.
l The mac-address update arp command does not take effect after ARP anti-spoofing is enabled by
using the arp anti-attack entry-check enable command.
l After the mac-address update arp command is run, the switch updates an ARP entry only if the
outbound interface in the corresponding MAC address entry changes.
----End
Checking the Configuration
Run the display current-configuration command to check whether the MAC address triggered
ARP entry update function is enabled.
7.14 Enabling Port Bridge
The port bridge function enables an interface to process packets in which the source and
destination MAC addresses are the same.
Applicable Environment
By default, an interface does not forward frames whose source and destination MAC addresses
are both learned by this interface. When the interface receives such a frame, it discards the frame
as an invalid frame. After the port bridge function is enabled on the interface, the interface
forwards such a frame if the destination MAC address of the frame is in the MAC address table.
The port bridge function is used in the following scenarios:
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
198
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
7 MAC Address Table Configuration
The S5700 connects to a device that does not support Layer 2 forwarding. When users
connected to this device communicate with each other, user packets are sent to the S5700
and forwarded by the S5700. In this scenario, the port bridge function must be enabled.
The S5700 is used as an access switch in a data center and is connected to servers. Each
server is configured with multiple virtual machines. The virtual machines need to transmit
data to each other. To improve the data transmission rate and server performance, enable
the port bridge functions on the interfaces connected to the servers so that the S5700
forwards data packets between the virtual machines.
Data Preparation
No.
Data
Interface type and number
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
interface interface-type interface-number
The interface view is displayed.
Step 3 Run:
port bridge enable
The port bridge function is enabled.
By default, the port bridge function is disabled on an interface.
----End
Checking the Configuration
Run the display current-configuration command to check whether the port bridge function is
enabled.
7.15 Configuration Examples
This section provides several examples of MAC address table configuration.
7.15.1 Example for Configuring the MAC Address Table
Networking Requirements
As shown in Figure 7-6, the MAC address of the user host PC1 is 0002-0002-0002 and the MAC
address of the user host PC2 is 0003-0003-0003. PC1 and PC2 are connected to the Switch
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
199
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
7 MAC Address Table Configuration
through the LSW. The LSW is connected to GE 0/0/1 of the Switch. Interface GE 0/0/1 belongs
to VLAN 2. The MAC address of the server is 0004-0004-0004. The server is connected to
GE 0/0/2 of the Switch. Interface GE 0/0/2 belongs to VLAN 2.
l
To prevent hackers from attacking the network with MAC addresses, add a static entry to
the MAC table of the Switch for each user host. When sending packets through GE 0/0/1,
the Switch changes the VLAN ID to VLAN 4 to which the LSW belongs. In addition, you
need to set the aging time of the dynamic entries in the MAC address table to 500 seconds.
To prevent hackers from forging the MAC address of the server and stealing user
information, configure the packet forwarding based on static MAC address entries on the
Switch.
Figure 7-6 Configuring the MAC address table
S e rve r
N e tw o rk
S w itch
M A C a d d re ss: 4 -4 -4
G E 0 /0 /2
VLAN2
G E 0 /0 /1
LSW
PC1
VLAN4
PC2
M A C a d d re ss: 2 -2 -2
M A C a d d re ss: 3 -3 -3
Configuration Roadmap
The configuration roadmap is as follows:
1.
Create a VLAN and add interfaces to the VLAN.
2.
Add static MAC address entries.
3.
Set the aging time of dynamic MAC address entries.
Data Preparation
To complete the configuration, you need the following data:
l
MAC address of PC1: 0002-0002-0002
MAC address of PC2: 0003-0003-0003
MAC address of the server: 0004-0004-0004
VLAN to which the Switch belongs: VLAN 2
Interface connecting the Switch to the LSW: GE 0/0/1
Interface connecting the Switch to the server: GE 0/0/2
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
200
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
7 MAC Address Table Configuration
VLAN ID required to be changed to when the Switch sends packets through the outbound
interface: VLAN 4
Aging time of dynamic entries in the MAC address table of the Switch: 500 seconds
Procedure
Step 1 Add static MAC address entries.
# Create VLAN 2; add GE 0/0/1 0/0/2 to VLAN 2; configure VLAN mapping on GE 0/0/1.
<Quidway> system-view
[Quidway] vlan 2
[Quidway-vlan2] quit
[Quidway] interface gigabitethernet
[Quidway-GigabitEthernet0/0/1] port
[Quidway-GigabitEthernet0/0/1] port
[Quidway-GigabitEthernet0/0/1] qinq
[Quidway-GigabitEthernet0/0/1] port
[Quidway-GigabitEthernet0/0/1] quit
[Quidway] interface gigabitethernet
[Quidway-GigabitEthernet0/0/2] port
[Quidway-GigabitEthernet0/0/2] port
[Quidway-GigabitEthernet0/0/2] quit
0/0/1
hybrid pvid vlan 2
hybrid untagged vlan 2
vlan-translation enable
vlan-mapping vlan 4 map-vlan 2
0/0/2
hybrid pvid vlan 2
hybrid untagged vlan 2
# Configure static MAC address entries.
[Quidway] mac-address static 2-2-2 gigabitethernet 0/0/1 vlan 2
[Quidway] mac-address static 3-3-3 gigabitethernet 0/0/1 vlan 2
[Quidway] mac-address static 4-4-4 gigabitethernet 0/0/2 vlan 2
Step 2 Set the aging time of dynamic MAC address entries.
[Quidway] mac-address aging-time 500
Step 3 Verify the configuration.
# Run the display mac-address static command in any view. You can check whether the static
MAC address entries are successfully added.
[Quidway] display mac-address static vlan 2
------------------------------------------------------------------------------MAC Address
VLAN/VSI
Learned-From
Type
------------------------------------------------------------------------------0002-0002-0002
2/GE0/0/1
static
0003-0003-0003
2/GE0/0/1
static
0004-0004-0004
2/GE0/0/2
static
------------------------------------------------------------------------------Total items displayed = 3
# Run the display mac-address aging-time command in any view. You can check whether the
aging time of dynamic entries is set successfully.
[Quidway] display mac-address aging-time
Aging time: 500 seconds
----End
Configuration Files
The following lists the configuration file of the Switch.
#
sysname Quidway
#
vlan batch 2
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
201
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
7 MAC Address Table Configuration
#
mac-address aging-time 500
#
interface GigabitEthernet0/0/1
port hybrid pvid vlan 2
port hybrid untagged vlan 2
qinq vlan-translation enable
port vlan-mapping vlan 4 map-vlan
#
interface GigabitEthernet0/0/2
port hybrid pvid vlan 2
port hybrid untagged vlan 2
#
mac-address static 0002-0002-0002
mac-address static 0003-0003-0003
mac-address static 0004-0004-0004
#
return
GigabitEthernet0/0/1 vlan 2
GigabitEthernet0/0/1 vlan 2
GigabitEthernet0/0/2 vlan 2
7.15.2 Example for Configuring MAC Address Limiting in a VLAN
Networking Requirements
As shown in Figure 7-7, user network 1 is connected to GE 0/0/1 on the Switch through an
LSW. User network 2 is connected to GE 0/0/2 on the Switch through another LSW. GE 0/0/1
and GE 0/0/2 belong to VLAN 2. To prevent MAC address attacks and control the number of
access users, limit the MAC address learning in VLAN 2.
Figure 7-7 Configuring MAC address limiting in a VLAN
Network
Switch
GE0/0/1
GE0/0/2
LSW
User
network 1
LSW
VLAN 2
User
network 2
Configuration Roadmap
The configuration roadmap is as follows:
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
202
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
7 MAC Address Table Configuration
1.
Create a VLAN and add interfaces to the VLAN.
2.
Configure the limitation on MAC address learning based on VLANs.
Data Preparation
To complete the configuration, you need the following data:
l
VLAN to which the interfaces belong: VLAN 2
User interfaces: GE 0/0/1 and GE 0/0/2
Maximum number of learned MAC addresses: 100
Procedure
Step 1 Configure the limitation on MAC address learning.
# Add GE 0/0/1 and GE 0/0/2 to VLAN 2.
<Quidway> system-view
[Quidway] vlan 2
[Quidway-vlan2] quit
[Quidway] interface gigabitethernet
[Quidway-GigabitEthernet0/0/1] port
[Quidway-GigabitEthernet0/0/1] port
[Quidway-GigabitEthernet0/0/1] quit
[Quidway] interface gigabitethernet
[Quidway-GigabitEthernet0/0/2] port
[Quidway-GigabitEthernet0/0/2] port
[Quidway-GigabitEthernet0/0/2] quit
0/0/1
hybrid pvid vlan 2
hybrid untagged vlan 2
0/0/2
hybrid pvid vlan 2
hybrid untagged vlan 2
# Configure the rule of limiting MAC address learning in VLAN 2: A maximum of 100 MAC
addresses can be learned; packets are still forwarded and an alarm is generated when the number
of learned MAC addresses reaches the limit, but new MAC addresses are not added to the MAC
address table.
[Quidway] vlan 2
[Quidway-vlan2] mac-limit maximum 100 alarm enable
[Quidway-vlan2] quit
Step 2 Verify the configuration.
# Run the display mac-limit command in any view. You can check whether the rule of limiting
MAC address learning is successfully configured.
<Quidway> display mac-limit
MAC Limit is enabled
Total MAC Limit rule count : 1
PORT
VLAN/VSI/SI
SLOT Maximum Rate(ms) Action Alarm
---------------------------------------------------------------------------2
100
forward enable
----End
Configuration Files
The following lists the configuration file of the Switch.
#
sysname Quidway
#
vlan batch 2
#
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
203
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
7 MAC Address Table Configuration
vlan 2
mac-limit maximum 100
#
interface GigabitEthernet0/0/1
port hybrid pvid vlan 2
port hybrid untagged vlan 2
#
interface GigabitEthernet0/0/2
port hybrid pvid vlan 2
port hybrid untagged vlan 2
#
return
7.15.3 Example for Configuring Port Security
Networking Requirements
As shown in Figure 7-8, a company wants to prevent the computers of non-employees from
accessing the company intranet to protect information security. To achieve this goal, the
company needs to enable the sticky MAC function on the interface connected to computers of
employees, and set the maximum number of MAC addresses learned by the interface to be the
same as the number of trusted computers.
Figure 7-8 Port security configuration
Internet
Switch
GE0/0/1
VLAN 10
SwitchA
PC1
PC2
PC3
Configuration Roadmap
The configuration roadmap is as follows:
1.
Create a VLAN and set the link type of the interface to trunk.
2.
Enable the port security function.
3.
Enable the sticky MAC function on the interface.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
204
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
7 MAC Address Table Configuration
4.
Configure the action to be taken when the number of learned MAC addresses exceeds the
limit.
5.
Set the maximum number of MAC addresses that can be learned by the interface.
Data Preparation
To complete the configuration, you need the following data:
l
VLAN allowed by the interface
Type and number of the interface connected to computers of employees
Action to be taken when the number of learned MAC addresses exceeds the limit
Maximum number of MAC addresses learned by the interface
Procedure
Step 1 Create a VLAN and set the link type of the interface to trunk.
<Quidway> system-view
[Quidway] vlan 10
[Quidway-vlan10] quit
[Quidway] interface gigabitethernet 0/0/1
[Quidway-GigabitEthernet0/0/1] port link-type trunk
[Quidway-GigabitEthernet0/0/1] port trunk allow-pass vlan 10
Step 2 Configure the port security function.
# Enable the port security function.
[Quidway-GigabitEthernet0/0/1] port-security enable
Enable the sticky MAC function.
[Quidway-GigabitEthernet0/0/1] port-security mac-address sticky
# Configure the action to be taken when the number of learned MAC addresses exceeds the limit.
[Quidway-GigabitEthernet0/0/1] port-security protect-action protect
# Set the maximum number of MAC addresses that can be learned by the interface.
[Quidway-GigabitEthernet0/0/1] port-security max-mac-num 4
To enable the port security function on other interfaces, repeat the preceding steps.
Step 3 Verify the configuration.
If an employee's PC is replaced by another PC, the new PC cannot access the company intranet.
----End
Configuration Files
Configuration file of the Switch
#
sysname Quidway
#
vlan batch 10
#
interface GigabitEthernet0/0/1
port link-type trunk
port trunk allow-pass vlan 10
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
205
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
port-security
port-security
port-security
port-security
#
return
7 MAC Address Table Configuration
enable
protect-action protect
mac-address sticky
max-mac-num 4
7.15.4 Example for Configuring MAC Address Anti-Flapping
The MAC address anti-flapping function protects enterprise servers or VIP customers from
attacks.
Networking Requirements
As shown in Figure 7-9, employees of an enterprise need to access the server connected to a
Switch interface. If an attacker uses the server MAC address as the source MAC address to send
packets to another interface, the server MAC address is learned on the interface. As a result,
employees cannot access the server, and important data will be intercepted by the attacker.
MAC address anti-flapping can be configured to protect the server from attacks.
Figure 7-9 MAC address anti-flapping
Server
MAC:11-22-33
GE0/0/1
VLAN 10
Switch
GE0/0/2
PC4
MAC:11-22-33
LSW
PC1
PC2
PC3
VLAN10
Configuration Roadmap
The configuration roadmap is as follows:
1.
Create a VLAN and add interfaces to the VLAN.
2.
Configure MAC address anti-flapping on the server-side interface.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
206
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
7 MAC Address Table Configuration
Data Preparation
To complete the configuration, you need the following data:
l
VLAN that the server-side and user-side interfaces belong to: VLAN 10
Server-side interface: GigabitEthernet0/0/1
User-side interface: GigabitEthernet0/0/2
MAC address learning priority of the server-side interface: 2
Procedure
Step 1 Create a VLAN and add interfaces to the VLAN.
# Add GigabitEthernet0/0/1 and GigabitEthernet0/0/2 to VLAN 10.
<Quidway> system-view
[Quidway] vlan 10
[Quidwayvlan10] quit
[Quidway] interface gigabitethernet
[Quidway-GigabitEthernet0/0/2] port
[Quidway-GigabitEthernet0/0/2] port
[Quidway-GigabitEthernet0/0/2] quit
[Quidway] interface gigabitethernet
[Quidway-GigabitEthernet0/0/1] port
[Quidway-GigabitEthernet0/0/1] port
0/0/2
link-type trunk
trunk allow-pass vlan 10
0/0/1
hybrid pvid vlan 10
hybrid untagged vlan 10
Step 2 Configure MAC anti-flapping.
# Set the MAC address learning priority of GigabitEthernet0/0/1 to 2.
[Quidway-GigabitEthernet0/0/1] mac-learning priority 2
Step 3 Verify the configuration.
# Run the display current-configuration command in any view to check whether the MAC
address learning priority of GigabitEthernet0/0/1 is set correctly.
<Quidway> display current-configuration
#
interface GigabitEthernet0/0/1
port hybrid pvid vlan 10
port hybrid untagged vlan 10
mac-learning priority 2
#
return
----End
Configuration Files
Configuration file of the Switch
#
sysname Quidway
#
vlan batch 10
#
interface GigabitEthernet0/0/1
port hybrid pvid vlan 10
port hybrid untagged vlan 10
mac-learning priority 2
#
interface GigabitEthernet0/0/2
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
207
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
7 MAC Address Table Configuration
port link-type trunk
port trunk allow-pass vlan 10
#
return
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
208
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
8 STP/RSTP Configuration
STP/RSTP Configuration
About This Chapter
The Spanning Tree Protocol (STP) trims a ring network into a loop-free tree network. It prevents
replication and circular propagation of packets, provides multiple redundant paths for Virtual
LAN (VLAN) data traffic, and enables load balancing. The Rapid Spanning Tree Protocol
(RSTP) develops rapid convergence and introduces the edge port and its protection function
based on STP.
8.1 STP/RSTP Overview
STP is a management protocol on the data link layer. It is used to block redundant links on the
Layer 2 network and trim a network into a loop-free tree. RSTP is a refinement of STP and
introduces rapid convergence of the network topology.
8.2 Configuring Basic STP/RSTP Functions
STP/RSTP is used to block redundant links on the Layer 2 network and trim a network into a
loop-free tree topology.
8.3 Configuring STP/RSTP Parameters on an Interface
A feedback mechanism is provided to confirm topology convergence. Thus, rapid convergence
is implemented for RSTP.
8.4 Configuring RSTP Protection Functions
RSTP protection functions are as follows, and you can configure one or more functions as
required.
8.5 Configuring STP/RSTP Interoperability Between Huawei Devices and Non-Huawei Devices
To supports STP/RSTP interoperability between Huawei devices and non-Huawei devices,
proper parameters are required on Huawei devices running STP/RSTP to ensure nonstop
communication.
8.6 Maintaining STP/RSTP
STP/RSTP maintenance includes resetting STP/RSTP statistics.
8.7 Configuration Examples
This section shows typical usage scenarios of STP/RSTP by describing networking
requirements, configuration roadmap, and data preparation, and provides related configuration
files.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
209
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
8 STP/RSTP Configuration
8.1 STP/RSTP Overview
STP is a management protocol on the data link layer. It is used to block redundant links on the
Layer 2 network and trim a network into a loop-free tree. RSTP is a refinement of STP and
introduces rapid convergence of the network topology.
8.1.1 STP/RSTP Overview
STP/RSTP is used to block redundant links on the Layer 2 network and trim a network into a
loop-free tree topology.
Introduction
On a complex network, loops are inevitable. With the requirement for network redundancy
backup, network designers tend to deploy multiple physical links between two devices, one of
which is the master and the others are the backup. Loops are likely or bound to occur in such a
situation.
Loops will cause broadcast storms, thereby exhausting network resources and paralyzing the
network. Loops also cause flapping of MAC address tables and thus damages MAC address
entries.
The devices running STP discover loops on the network by exchanging information with each
other and trim the ring topology into a loop-free tree topology by blocking a certain interface.
In this manner, replication and circular propagation of packets are prevented on the network. In
addition, it is prevented that the processing performance of devices is degraded when
continuously processing repeated packets.
STP, however, converges the network topology slowly. In 2001, the IEEE published document
802.1w to introduce an evolution of the Spanning Tree Protocol: Rapid Spanning Tree Protocol
(RSTP). RSTP is developed based on STP but outperforms STP.
Concepts
l
Root bridge
A tree topology must have a root. Therefore, the root bridge is introduced by STP/RSTP.
There is only one root bridge on the entire STP/RSTP-capable network. The root bridge is
the logical center but is unnecessarily the physical center of the entire network. The root
bridge may be served by another switching device along with the network topology change.
ID
There are Bridge IDs (BIDs) and port IDs (PIDs).
BID
IEEE 802.1D defines that a BID is composed of a 2-bit bridge priority and a bridge
MAC address. That is, BID (8 bits) = Bridge priority (2 bits) + Bridge MAC address (6
bits).
On the STP-capable network, the device with the smallest BID is selected as the root
bridge. The bridge priority that is allowed to be configured on a Huawei device ranges
from 0 to 61440. By default, the bridge priority is 32768.
PID
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
210
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
8 STP/RSTP Configuration
A 16-bit PID is composed of a 4-bit port priority and a 12-bit port number.
The PID is used when the designated port needs to be selected. That is, when the root
path costs and the sender BIDs of two ports are the same, the port with a smaller PID
is selected as the designated port. As shown in Figure 8-1, the root path costs and sender
BIDs of port A and port B on S2 are the same. Port A has a smaller PID, and is thus
selected as the designated port on the local segment. The port priority that can be
configured on a Huawei device ranges from 0 to 240, with the step 16. That is, the port
priority can be 0, 16, or 32. By default, the port priority is 128.
l
Path cost
A path cost is port-specific, which is used by STP/RSTP as a reference to select a link.
STP/RSTP calculates the path cost to select the robust link and blocks redundant links to
trim the network into a loop-free tree topology.
On an STP/RSTP-capable network, the accumulative cost of the path from a certain port
to the root bridge is the sum of the costs of the segment paths into which the path is separated
by the ports on the transit bridges.
Port roles
STP-capable port
Root port
The root port is the port that is nearest to the root bridge. The root port is determined
based on the path cost. Among all the ports where STP is enabled on the network
bridge, the port with the smallest root path cost is the root port. There is only one
root port on an STP-capable device, but there is no root port on the root bridge.
Designated Port
The designated port on a switching device forwards bridge protocol data units
(BPDUs) to the downstream switching device. All ports on the root bridge are
designated ports. A designated port is selected on each network segment. The device
where the designated port resides is called the designated bridge on the network
segment.
RSTP-capable port
Compared with STP, RSTP has two additional types of ports, namely, the alternate port
and backup port. More port roles are defined to simplify the knowledge and deployment
of STP.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
211
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
8 STP/RSTP Configuration
Figure 8-1 Diagram of port roles
S1
Root bridge
S2
S3
S1
Root bridge
S2
A
B
b
S3
Root port
Designated port
Alternate port
Backup port
As shown in Figure 8-1, RSTP defines four port roles: root port, designated port,
alternate port, and backup port.
The functions of the root port and designated port are the same as those defined in STP.
The description of the alternate port and backup port is as follows:
From the perspective of configuration BPDU transmission:
The alternate port is blocked after learning the configuration BPDUs sent by
other bridges.
The backup port is blocked after learning the configuration BPDUs sent by itself.
From the perspective of user traffic:
The alternate port backs up the root port and provides an alternate path from the
designated bridge to the root bridge.
The backup port backs up the designated port and provides an alternate path from
the root node to the leaf node.
After all ports are assigned roles, topology convergence is completed.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
212
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
8 STP/RSTP Configuration
Port status
STP port state
Table 8-1 shows the port status of an STP-capable port.
Table 8-1 STP port state
Port
state
Purpose
Description
Forward
ing
The port in the Forwarding state
forwards not only user traffic but
also BPDUs.
Only the root port and designated
port can enter the Forwarding state.
Learnin
g
When a port is in the Learning state,
a device creates a MAC address
table based on the received user
traffic but does not forward user
traffic.
This is a transition state, which is
designed to prevent temporary
loops.
Listenin
g
When a port is in the Listening
state, the root bridge, root port, and
designated port are to be selected.
This is a transition state.
Blockin
g
The port in the Blocking state
receives and forwards only BPDUs
but does not forward user traffic.
This is the final state of a blocked
port.
Disabled
The port in the Disabled state
forwards neither BPDUs nor user
traffic.
The port is Down.
RSTP port state
Table 8-2 shows the port status of an RSTP-capable port.
Table 8-2 RSTP port state
Port state
Description
Forwarding
A port in the Forwarding state can send and receive BPDUs as
well as forward user traffic.
Learning
This is a transition state. A port in the Learning state learns
MAC addresses from user traffic to construct a MAC address
table.
In the Learning state, the port can send and receive BPDUs, but
cannot forward user traffic.
Discarding
Issue 02 (2011-11-21)
A port in the Discarding state can only receive BPDUs.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
213
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
8 STP/RSTP Configuration
CAUTION
A Huawei datacom device is in MSTP mode by default. After a device experiences the
transition from the MSTP mode to the STP mode, an STP-capable port supports the same
port states as those supported by an MSTP-capable port, including the Forwarding,
Learning, and Discarding states. For details, see Table 8-2.
l
Three timers
Hello Timer
Sets the interval at which BPDUs are sent.
Forward Delay Timer
Sets the time spent in the Listening and Learning states.
Max Age
Sets the maximum lifetime of a BPDU on the network. When the Max Age time expires,
the connection to the root bridge fails.
Comparison between STP, RSTP, and MSTP
Table 8-3 shows the comparison between STP, RSTP, and MSTP.
Table 8-3 Comparison between STP, RSTP, and MSTP
Spanning
Tree
Protocol
Characteristics
Applicable
Environment
Precautions
STP
A loop-free tree is
generated. Thus, broadcast
storms are prevented and
redundancy is
implemented.
Irrespective of different
users or services, all
VLANs share one
spanning tree.
NOTE
RSTP
l A loop-free tree is
generated. Thus,
broadcast storms are
prevented and
redundancy is
implemented.
l A feedback mechanism
is provided to confirm
topology convergence.
Thus, rapid
convergence is
implemented.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
l If the current
switching device
supports STP and
RSTP, RSTP is
recommended.
l If the current
switching device
supports STP or
RSTP, and MSTP,
MSTP is
recommended. See
MSTP
Configuration.
214
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
8 STP/RSTP Configuration
Spanning
Tree
Protocol
Characteristics
Applicable
Environment
MSTP
l In an MSTP region, a
loop-free tree is
generated. Thus,
broadcast storms are
prevented and
redundancy is
implemented.
User or service-specific
load balancing is
required. Traffic for
different VLANs is
forwarded through
different spanning
trees, which are
independent of each
other.
l A feedback mechanism
is provided to confirm
topology convergence.
Thus, rapid
convergence is
implemented.
Precautions
l MSTP implements
load balancing among
VLANs. Traffic in
different VLANs is
transmitted along
different paths.
8.1.2 STP/RSTP Features Supported by the S5700
Before configuring STP/RSTP, familiarize yourself with the concepts of basic STP/RSTP
functions, topology convergence, STP/RSTP protection, and STP/RSTP interoperability
between Huawei devices and non-Huawei devices. This will help you complete the configuration
task quickly and accurately.
STP/RSTP is used to block redundant links on the Layer 2 network and trim a network into a
loop-free tree topology. The basic configuration roadmap of STP/RSTP is as follows:
1.
Select a switching device (functioning as a root bridge) from switching devices for each
spanning tree. You can configure the priorities of the switching devices to preferentially
select a root bridge.
2.
In each spanning tree, calculate the shortest paths from the other switching devices to the
root bridge, and select a root port for each non-root switching device. You can configure
the cost of the path from a switching device to the root bridge to preferentially select a root
port.
3.
In each spanning tree, select a designated port for each connection according to the bridge
ID, the cost of path and port IDs. If the devices have the same bridge ID and the cost of
path, You can configure the port priorities to preferentially select a designated port.
STP/RSTP also supports the following features to meet requirements of special applications and
extended functions:
l
A feedback mechanism is provided to confirm topology convergence. Thus, rapid
convergence is implemented.
RSTP provides the following protection functions, as listed in Table 8-4.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
215
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
8 STP/RSTP Configuration
Supports STP/RSTP interoperability between Huawei devices and non-Huawei devices.
Proper parameters are required on Huawei devices running STP/RSTP to ensure nonstop
communication.
Table 8-4 RSTP Protection Function
Issue 02 (2011-11-21)
Protection
Function
Scenario
Configuration Impact
BPDU
protection
An edge port changes to be
a non-edge port after
receiving a BPDU, which
triggers spanning tree
recalculation. If an attacker
keeps sending bogus
BPDUs to a switching
device, network flapping
occurs.
After BPDU protection is enabled on the
switching device, the switching device
shuts down the edge port if the edge port
receives an RST BPDU, and notifies the
NMS of the shutdown event. The attributes
of the edge port are not changed.
TC
protection
Generally, after receiving
TC BPDUs (packets for
advertising network
topology changes), a
switching device needs to
delete MAC entries and
ARP entries. Frequent
deletion operations will
exhaust CPU resources.
TC protection is used to suppress TCBPDUs. The number of times that TCBPDUs are processed by a switching
device within a given time period is
configurable. If the number of TC-BPDUs
that the switching device receives within a
given time exceeds the specified threshold,
the switching device handles TC-BPDUs
only for the specified number of times.
Excess TC-BPDUs are processed by the
switching device as a whole for once after
the timer (that is, the specified time period)
expires. This protects the switching device
from frequently deleting MAC entries and
ARP entries, thus avoiding over-burdened.
Root
protection
Due to incorrect
configurations or
malicious attacks on the
network, a root bridge may
receive BPDUs with a
higher priority.
Consequently, the
legitimate root bridge is no
longer able to serve as the
root bridge, and the
network topology is
illegitimately changed,
triggering spanning tree
recalculation. This may
transfer traffic from highspeed links to low-speed
links, causing traffic
congestion.
If a designated port is enabled with the root
protection function, the role of the port
cannot be changed. Once a designated port
that is enabled with root protection
receives RST BPDUs with a higher
priority, the port enters the Discarding state
and does not forward packets. If the port
does not receive any RST BPDUs with a
higher priority before a period (generally
two Forward Delay periods) expires, the
port automatically enters the Forwarding
state.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
216
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
8 STP/RSTP Configuration
Protection
Function
Scenario
Configuration Impact
Loop
protection
A root port or an alternate
port will age if link
congestion or a one-way
link failure occurs. After
the root port ages, a
switching device may reselect a root port
incorrectly and after the
alternate port ages, the port
enters the Forwarding
state. Loops may occur in
such a situation.
After loop protection is configured, if the
root port or alternate port does not receive
RST BPDUs from the upstream switching
device for a long time, the switching device
notifies the NMS that the port enters the
Discarding state. The blocked port remains
in the Blocked state and no longer forwards
packets. This prevents loops on the
network. The root port restores the
Forwarding state after receiving new
BPDUs.
8.2 Configuring Basic STP/RSTP Functions
STP/RSTP is used to block redundant links on the Layer 2 network and trim a network into a
loop-free tree topology.
STP/RSTP is commonly configured on a switching device to trim a ring network to a loop-free
network. STP/RSTP configurations on the switching device involve STP/RSTP working mode
configuration. If you need to interfere in the spanning tree calculation, the following methods
are available:
l
Setting a priority for a switching device: The lower the numerical value, the higher the
priority of the switching device and the more likely the switching device becomes a root
bridge; the higher the numerical value, the lower the priority of the switching device and
the less likely that the switching device becomes a root bridge.
Setting a path cost for a port: With the same calculation method, the lower the numerical
value, the smaller the cost of the path from the port to the root bridge and the more likely
the port becomes a root port; the higher the numerical value, the larger the cost of the path
from the port to the root bridge and the less likely that the port becomes a root port.
Setting a priority for a port: The lower the numerical value, the more likely the port becomes
a designated port; the higher the numerical value, the less likely that the port becomes a
designated port.
8.2.1 Establishing the Configuration Task
Before configuring basic STP/RSTP functions, familiarize yourself with the applicable
environment, complete the pre-configuration tasks, and obtain the required data. This will help
you complete the configuration task quickly and accurately.
Applicable Environment
On a complex network, loops are inevitable. With the requirement for network redundancy
backup, network designers tend to deploy multiple physical links between two devices, one of
which is the master and the others are the backup. Loops are likely or bound to occur in such a
situation.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
217
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
8 STP/RSTP Configuration
Loops will cause broadcast storms, thereby exhausting network resources and paralyzing the
network. Loops also cause flapping of MAC address tables and thus damages MAC address
entries.
STP/RSTP can be deployed on a network to eliminate loops. If a loop is detected, STP/RSTP
blocks one port to eliminate the loop.
As shown in Figure 8-2, Switch A, Switch B, Switch C, and Switch D form a ring network, and
STP/RSTP is enabled on the ring network to eliminate loops.
Figure 8-2 Diagram of a ring network
Network
Root
Bridge
SwitchA
SwitchB
SwitchC
SwitchD
PC1
PC2
Blocked port
NOTE
If the current switching device supports STP and RSTP, RSTP is recommended.
Pre-configuration Tasks
Before configuring basic STP/RSTP functions, complete the following task:
l
Connecting interfaces and setting physical parameters for the interfaces to ensure that the
physical status of the interfaces is Up
Data Preparation
To configure basic STP/RSTP functions, you need the following data.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
218
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
No.
Data
(Optional) Priority of a switching device
(Optional) Priority of a port
(Optional) Path cost of a port
8 STP/RSTP Configuration
8.2.2 Configuring the STP/RSTP Mode
Before configuring basic STP/RSTP functions, you need to configure the working mode of a
switching device to STP/RSTP. RSTP is compatible with STP.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
stp mode { stp | rstp }
The working mode of the switching device is configured as STP/RSTP.
By default, the working mode of the S5700 is MSTP.
----End
8.2.3 (Optional) Configuring Switching Device Priorities
The lower the numerical value is, the higher priority a switching device has and the more likely
the switching device will be selected as a root bridge.
Context
On an STP/RSTP-capable network, there is only one root bridge and it is the logic center of the
entire spanning tree. In root bridge selection, the switching device with high performance and
network hierarchy is generally selected as a root bridge; however, the priority of such a device
may be not that high. Thus setting a high priority for the switching device is necessary so that
the device can function as a root bridge.
Other devices with low performance and network hierarchy are not fit to be a root bridge.
Therefore, set low priorities for these devices.
CAUTION
If an S5700 is configured as the root switch or secondary root switch, the priority of the
S5700 cannot be set. If you want to set the priority of the S5700, you must disable the root switch
or secondary root switch.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
219
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
8 STP/RSTP Configuration
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
stp priority
priority
The priority of a switching device is configured.
The default priority value of a switching device is 32768.
NOTE
l To configure a switching device as a primary root bridge, you can run the stp root primary command
directly. The priority value of this switching device is 0.
l To configure a switching device as a secondary root bridge, run the stp root secondary command. The
priority value of this switching device is 4096.
A switching device cannot act as a primary root bridge and a secondary root bridge at the same time.
----End
8.2.4 (Optional) Setting the Path Cost for a Port
The STP/RSTP path cost determines root port selection. The port from which to the root port
costs the least is selected as the root port.
Context
A path cost is port-specific, which is used by STP/RSTP as a reference to select a link.
The range of the path cost value is determined by the calculation method. After the calculation
method is determined, you are recommended to set a relatively small path cost value for the port
at a high link rate.
Use the Huawei proprietory calculation method as an example. Different link rates correspond
to default path cost values of ports. For details, see Table 8-5.
Table 8-5 Mappings between link rates and path cost values
Issue 02 (2011-11-21)
Link Rate
Recommended
value
Recommended
Value Range
Value Range
10 Mbit/s
2000
200-20000
1-200000
100 Mbit/s
200
20-2000
1-200000
1 Gbit/s
20
2-200
1-200000
10 Gbit/s
2-20
1-200000
Over 10 Gbit/s
1-2
1-200000
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
220
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
8 STP/RSTP Configuration
On a network where loops occur, you are recommended to set a relatively large path cost for the
port at a low link rate. STP/RSTP puts the port with the large path cost in the Blocking state and
blocks the link where this port resides.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
stp pathcost-standard { dot1d-1998 | dot1t | legacy }
A path cost calculation method is configured.
By default, the IEEE 802.1t standard method is used to calculate the default path cost.
All switching devices on a network must use the same calculation method for path costs.
Step 3 Run:
interface interface-type interface-number
The Ethernet interface view is displayed.
Step 4 Run:
stp cost cost
A path cost is set for the port.
l When the Huawei proprietory calculation method is used, cost ranges from 1 to 200000.
l When the IEEE 802.1d standard method is used, cost ranges from 1 to 65535.
l When the IEEE 802.1t standard method is used, cost ranges from 1 to 200000000.
----End
8.2.5 (Optional) Configuring Port Priorities
The lower the numerical value, the more likely the port on a switching device becomes a
designated port; the higher the numerical value, the more likely the port is to be blocked.
Context
Whether a port on a switching device will be selected as a designated port is determined by its
priority. For details, see 8.1.1 STP/RSTP Overview.
If you expect to block a port on a switching device to eliminate loops, set the port priority value
to be larger than the default value when the devices have the same bridge ID and the cost of
path. This port will be blocked in designated port selection.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
221
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
8 STP/RSTP Configuration
Step 2 Run:
interface interface-type interface-number
The Ethernet interface view is displayed.
Step 3 Run:
stp port priority priority
The port priority is configured.
The default priority value of a port on a switching device is 128.
----End
8.2.6 Enabling STP/RSTP
After STP/RSTP is enabled, spanning trees are calculated.
Context
After STP/RSTP is enabled on a ring network, STP/RSTP immediately calculates spanning trees
on the network. Configurations on the switching device, such as the switching device priority
and port priority, will affect spanning tree calculation. Any change of the configurations may
cause network flapping. Therefore, to ensure rapid and stable spanning tree calculation, perform
basic configurations on the switching device and its ports and enable STP/RSTP.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
stp enable
STP/RSTP is enabled on the switching device.
By default, the STP/RSTP function is enabled on a S5700.
----End
8.2.7 Checking the Configuration
After basic STP/RSTP functions are configured, you can view the information such as the port
role and port status to check whether the spanning tree calculation is correctly performed.
Prerequisite
All configurations of basic STP/RSTP functions are complete.
Procedure
l
Run the display stp [ interface interface-typeinterface-number ] [ brief ] command to view
spanning-tree status and statistics.
----End
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
222
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
8 STP/RSTP Configuration
8.3 Configuring STP/RSTP Parameters on an Interface
A feedback mechanism is provided to confirm topology convergence. Thus, rapid convergence
is implemented for RSTP.
STP does not implement rapid convergence; however, STP parameters, such as the network
diameter, hello time, Max Age time, and Forward Delay time, may affect network convergence.
RSTP is a refinement of STP and implements rapid convergence. In addition to the preceding
parameters, such parameters as the type of the link where the port resides, rapid transition
mechanism, and maximum number of sent BPDUs port parameters also affect STP/RSTP
topology convergence.
For the parameters of devices running STP/RSTP, see Table 8-6.
Table 8-6 Parameters affecting the STP/RSTP topology convergence
Issue 02 (2011-11-21)
Paramete
r
Parameter
Description
Commands
Description
System
parameter
network
diameter, timer
value (Hello
Time, Forward
Delay period,
Max Age time),
and timeout
period for
waiting for
BPDUs from
the upstream (3
x hello time x
time factor)
l stp bridge-diameter
diameter
It is recommended that you
set the network diameter to
determine the timer value.
The switching device
automatically calculates
the Forward Delay period,
Hello time, and Max Age
time based on the network
diameter. Then, you can
run the stp timer-factor
factor command to set the
timeout period for waiting
for BPDUs from the
upstream (3 x hello time x
time factor).
l stp timer hello hello-time
l stp timer forward-delay
forward-delay
l stp timer max-age max-age
l stp timer-factor factor
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
223
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
8 STP/RSTP Configuration
Paramete
r
Parameter
Description
Commands
Description
Port
parameter
Link type of a
port
l stp point-to-point { auto |
force-false | force-true }
A P2P link helps
implement the rapid
convergence.
l If the port works in fullduplex mode, the link
where the port resides is
a P2P link.
l If the port works in
half-duplex mode, you
can forcibly switch the
link where the port
resides to a P2P link.
l In other cases, you can
enable the port to
automatically
determine whether to
connect to the P2P link.
Port transition
to the RSTP
mode
l stp mcheck
On a switching device
running RSTP, if an
interface is connected to a
device running STP, the
interface automatically
transitions to the STP
mode.
Enabling MCheck on the
interface is required When
the interface fail to
automatically transition to
the RSTP mode.
Maximum
number of
BPDUs sent by
the interface
within each
Hello time
Issue 02 (2011-11-21)
l stp transmit-limit packetnumber
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
If the maximum number of
BPDUs sent by the
interface within each Hello
time is set properly, the rate
at which BPDUs are sent
can be restricted, which
prevents RSTP from
consuming too many
bandwidths when network
flapping occurs.
224
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
Paramete
r
8 STP/RSTP Configuration
Parameter
Description
Commands
Description
Edge ports
l stp edged-port enable
The ports connecting to
terminals do not participate
in STP/RSTP calculation.
If a port is configured as an
edge port, the port does not
participate in STP/RSTP
calculation.
l error-down auto-recovery
cause cause-item interval
interval-value
After BPDU protection is
configured on a switching
device, an edge port is shut
down when receiving
BPDUs. The port can be
configured to
automatically go Up after a
specific delay.
8.3.1 Establishing the Configuration Task
Before configuring parameters affecting STP/RSTP rapid convergence, familiarize yourself
with the applicable environment, complete the pre-configuration tasks, and obtain the required
data. This will help you complete the configuration task quickly and accurately.
Applicable Environment
On some specific networks, RSTP parameters will affect the speed of network convergence.
Configuring proper RSTP parameters is required.
NOTE
The default configurations of the parameters described in this section help implement RSTP rapid
convergence. Therefore, the configuration process and all involved procedures described in this section
are optional. You can perform some of the configurations as required.
Pre-configuration Tasks
Before configuring STP/RSTP parameters, complete the following task:
l
Configuring basic STP/RSTP functions
Data Preparation
To configure STP/RSTP parameters, you need the following data.
Issue 02 (2011-11-21)
No.
Data
Network diameter
Hello time, forwarding delay time, maximum aging time, and timeout period for
waiting for BPDUs from the upstream (3 x hello time x time factor)
Link type of a port
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
225
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
8 STP/RSTP Configuration
No.
Data
Whether a port is enabled with rapid transition mechanism
Whether a port needs to transition to the RSTP mode
Maximum number of sent BPDUs
Whether a port needs to be configured as an edge port
Whether auto recovery needs to be configured for an edge port being shut down
Whether a port needs to clear statistics of the spanning tree
10
Whether an edge port needs to be configured as a BPDU filter
8.3.2 Setting System Parameters
STP/RSTP parameters that may affect network convergence include the network diameter, hello
time, and timeout period for waiting for BPDUs from the upstream (3 x hello time x time factor).
Therefore, STP/RSTP parameters need to be set properly to help implement rapid network
convergence.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
stp bridge-diameter diameter
The network diameter is configured.
By default, the network diameter is 7.
l RSTP uses a single spanning tree instance on the entire network, which cannot prevent the
performance from deteriorating when the network scale grows. Therefore, the network
diameter cannot be larger than 7.
l It is recommended that you run the stp bridge-diameter diameter command to set the
network diameter. Then, the switching device calculates the optimal Forward Delay period,
Hello time, and Max Age period based on the set network diameter.
Step 3 Run:
stp timer-factor factor
The timeout period for waiting for BPDUs from the upstream of a switching device is set.
By default, the timeout period of a switching device is 9 times as long as the Hello time.
Step 4 (Optional) To set the Forward Delay period, Hello time, and Max Age period, perform the
following operations:
l Run the stp timer forward-delay forward-delay command to set the Forward Delay period
for a switching device.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
226
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
8 STP/RSTP Configuration
The default Forward Delay period of a switching device is 1500, in centiseconds.
l Run the stp timer hello hello-time command to set the Hello time for a switching device.
The default Hello time of a switching device is 200, in centiseconds.
l Run the stp timer max-age max-age command to set the Max Age period for a switching
device.
The default Max Age period of a switching device is 2000, in centiseconds.
NOTE
The values of the Hello time, Forward Delay period, and Max Age period must comply with the following
formulas. Otherwise, networking flapping occurs.
l 2 (Forward Delay - 1.0 second) >= Max Age
l Max Age >= 2 (Hello Time + 1.0 second)
----End
8.3.3 Setting Port Parameters
Port parameters that may affect RSTP topology convergence include the link type and maximum
number of sent BPDUs. Proper port parameters help RSTP to implement rapid topology
convergence.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
interface interface-type interface-number
The Ethernet interface view is displayed.
Step 3 (Optional) Run:
stp point-to-point { auto | force-false | force-true }
The link type is configured for a port.
By default, a port automatically determines whether to connect to a P2P link. The P2P link
supports rapid network convergence.
l If the Ethernet port works in full-duplex mode, the port is connected to a P2P link. In this
case, force-true can be configured to implement rapid network convergence.
l If the Ethernet port works in half-duplex mode, you can configure stp point-to-point forcetrue to forcibly set the link type to P2P to implement rapid network convergence.
Step 4 Run:
stp mcheck
MCheck is enabled.
On a switching device running RSTP, if a port is connected to a device running STP, the port
automatically transitions to the STP interoperable mode.
Enabling MCheck on the port is required because the port may fail to automatically transition
to the RSTP mode in the following situations:
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
227
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
8 STP/RSTP Configuration
l The switching device running STP is shut down or moved.
l The switching device running STP transitions to the RSTP mode.
NOTE
If you run the stp mcheck command in the system view, the MCheck operation is performed on all the
interfaces.
Step 5 Run:
stp transmit-limit packet-number
The maximum number of BPDUs sent by a port within each Hello time is set.
By default, the maximum number of BPDUs that a port sends within each Hello time is 147.
Step 6 (Optional) Run:
stp edged-port enable
The port is configured as an edge port.
If a device port is connected to a terminal, you can run this command to configure the port as
an edge port.
By default, the port is a non-edge port.
Step 7 Run:
quit
Return to the system view.
Step 8 (Optional) Run:
error-down auto-recovery cause cause-item interval interval-value
The auto recovery function on an edge port is configured. That is, enable the port in the errordown state to automatically go Up, and set the delay for the transition from Down to Up.
There is no default value for the recovery time. Therefore, you must specify a delay when
configuring this command.
----End
Follow-up Procedure
When the topology of a spanning tree changes, the forwarding paths to associated VLANs are
changed. Then, ARP entries corresponding to those VLANs on the switching device need to be
updated. STP/RSTP processes ARP entries in either fast or normal mode.
l
In fast mode, ARP entries to be updated are directly deleted.
In normal mode, ARP entries to be updated are rapidly aged.
The remaining lifetime of ARP entries to be updated is set to 0. The switching device rapidly
processes these aged entries. If the number of ARP aging probe attempts is not set to 0,
ARP implements aging probe for these ARP entries.
In either fast or normal mode, MAC entries are directly deleted.
You can run the stp converge { fast | normal } command in the system view to configure the
STP/RSTP convergence mode.
By default, the STP/RSTP convergence is configured as normal.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
228
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
8 STP/RSTP Configuration
NOTE
The normal mode is recommended. If the fast mode is adopted, ARP entries will be frequently deleted,
causing the CPU usage on the MPU or LPU to reach 100%. As a result, network flapping frequently occurs.
8.3.4 Checking the Configuration
You can verify that the configurations take effect after configuring STP/RSTP parameters that
affect the topology convergence.
Prerequisite
The parameters that affect the topology convergence have been configured.
Procedure
l
Run the display stp [ interface interface-type interface-number ] [ brief ] command to
view spanning-tree status and statistics.
----End
8.4 Configuring RSTP Protection Functions
RSTP protection functions are as follows, and you can configure one or more functions as
required.
8.4.1 Establishing the Configuration Task
Before configuring RSTP protection functions, familiarize yourself with the applicable
environment, complete the pre-configuration tasks, and obtain the required data. This will help
you complete the configuration task quickly and accurately.
Applicable Environment
RSTP provides the following protection functions, as listed in Table 8-7.
Table 8-7 RSTP Protection Function
Issue 02 (2011-11-21)
Protection
Function
Scenario
Configuration Impact
BPDU
protection
An edge port changes to be a
non-edge port after
receiving a BPDU, which
triggers spanning tree
recalculation. If an attacker
keeps sending bogus BPDUs
to a switching device,
network flapping occurs.
After BPDU protection is enabled on the
switching device, the switching device shuts
down the edge port if the edge port receives
an RST BPDU, and notifies the NMS of the
shutdown event. The attributes of the edge
port are not changed.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
229
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
8 STP/RSTP Configuration
Protection
Function
Scenario
Configuration Impact
TC protection
Generally, after receiving
TC BPDUs (packets for
advertising network
topology changes), a
switching device needs to
delete MAC entries and ARP
entries. Frequent deletion
operations will exhaust CPU
resources.
TC protection is used to suppress TC-BPDUs.
The number of times that TC-BPDUs are
processed by a switching device within a
given time period is configurable. If the
number of TC-BPDUs that the switching
device receives within a given time exceeds
the specified threshold, the switching device
handles TC-BPDUs only for the specified
number of times. Excess TC-BPDUs are
processed by the switching device as a whole
for once after the timer (that is, the specified
time period) expires. This protects the
switching device from frequently deleting
MAC entries and ARP entries, thus avoiding
over-burdened.
Root
protection
Due to incorrect
configurations or malicious
attacks on the network, a
root bridge may receive
BPDUs with a higher
priority. Consequently, the
legitimate root bridge is no
longer able to serve as the
root bridge, and the network
topology is illegitimately
changed, triggering
spanning tree recalculation.
This may transfer traffic
from high-speed links to
low-speed links, causing
traffic congestion.
If a designated port is enabled with the root
protection function, the role of the port cannot
be changed. Once a designated port that is
enabled with root protection receives RST
BPDUs with a higher priority, the port enters
the Discarding state and does not forward
packets. If the port does not receive any RST
BPDUs with a higher priority before a period
(generally two Forward Delay periods)
expires, the port automatically enters the
Forwarding state.
Loop
protection
A root port or an alternate
port will age if link
congestion or a one-way link
failure occurs. After the root
port ages, a switching device
may re-select a root port
incorrectly and after the
alternate port ages, the port
enters the Forwarding state.
Loops may occur in such a
situation.
After loop protection is configured, if the root
port or alternate port does not receive RST
BPDUs from the upstream switching device
for a long time, the switching device notifies
the NMS that the port enters the Discarding
state. The blocked port remains in the
Blocked state and no longer forwards packets.
This prevents loops on the network. The root
port restores the Forwarding state after
receiving new BPDUs.
Pre-configuration Tasks
Before configuring basic RSTP functions, complete the following task:
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
230
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
8 STP/RSTP Configuration
Configuring basic RSTP functions
NOTE
Configuring an edge port on the switching device before configuring BPDU protection.
Data Preparation
To configure basic RSTP functions, you need the following data.
No.
Data
Number of the port on which root protection is to be enabled
Number of the port on which loop protection is to be enabled
8.4.2 Configuring BPDU Protection on a Switching Device
After BPDU protection is enabled on a switching device, the switching device shuts down an
edge port if the edge port receives a BPDU, and notifies the NMS of the shutdown event.
Context
Edge ports are directly connected to user terminals and normally, the edge ports will not receive
BPDUs. Some attackers may send pseudo BPDUs to attach the switching device. If the edge
ports receive the BPDUs, the switching device automatically configures the edge ports as nonedge ports and triggers new spanning tree calculation. Network flapping then occurs. BPDU
protection can be used to protect switching devices against malicious attacks.
NOTE
Do as follows on a switching device having an edge port:
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
stp bpdu-protection
BPDU protection is enabled on the switching device.
By default, BPDU protection is not enabled on the switching device.
----End
Follow-up Procedure
To allow an edge port to automatically start after being shut down, you can run the error-down
auto-recovery cause cause-item interval interval-value command to configure the auto
recovery function and set the delay on the port. After the delay expires, the port automatically
goes Up. interval interval-value ranges from 30 to 86400, in seconds. Note the following when
setting this parameter:
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
231
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
8 STP/RSTP Configuration
The smaller the interval-value is set, the sooner the edge port becomes Up, and the more
frequently the edge port alternates between Up and Down.
The larger the interval-value is set, the later the edge port becomes Up, and the longer the
service interruption lasts.
8.4.3 Configuring TC Protection on a Switching Device
After TC protection is enabled, you can set the number of times for a switching device to process
TC BPDUs within a given time. TC protection avoids frequent deletion of MAC address entries
and ARP entries, thereby protecting switching devices.
Context
An attacker may send pseudo TC BPDUs to attack switching devices. Switching devices receive
a large number of TC BPDUs in a short time and delete entries frequently, which burdens system
processing and degrades network stability.
TC protection is used to suppress TC BPDUs. The number of times that TC BPDUs are processed
by a switching device within a given time period is configurable. If the number of TC BPDUs
that the switching device receives within a given time exceeds the specified threshold, the
switching device handles TC BPDUs only for the specified number of times. Excess TC-BPDUs
are processed by the switching device as a whole for once after the specified time period expires.
This protects the switching device from frequently deleting MAC entries and ARP entries, thus
avoiding overburden.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
stp tc-protection
TC protection is enabled for a switching device.
By default, TC protection is enabled on the switching device.
Step 3 Run:
stp tc-protection threshold threshold
The threshold of the number of times the switching device handles the received TC BPDUs and
updates forwarding entries within a given time is set.
NOTE
The value of the given time is consistent with the RSTP Hello time set by using the stp timer hello hellotime command.
----End
8.4.4 Configuring Root Protection on a Port
The root protection function on a switching device protects a root bridge by preserving the role
of a designated port.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
232
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
8 STP/RSTP Configuration
Context
Due to incorrect configurations or malicious attacks on the network, a root bridge may receive
BPDUs with a higher priority. Consequently, the legitimate root bridge is no longer able to serve
as the root bridge, and the network topology is incorrectly changed, triggering spanning tree
recalculation. This also may cause the traffic that should be transmitted over high-speed links
to be transmitted over low-speed links, leading to network congestion. The root protection
function on a switching device is used to protect the root bridge by preserving the role of the
designated port.
NOTE
Root protection is configured on a designated port. Root protection takes effect only on a designated port.
Do as follows on the root bridge.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
interface interface-type interface-number
The Ethernet interface view is displayed.
Step 3 Run:
stp root-protection
Root protection is configured on the switching device.
By default, root protection is disabled.
----End
8.4.5 Configuring Loop Protection on a Port
The loop protection function suppresses the loops caused by link congestion.
Context
On a network running RSTP, a switching device maintains the root port status and status of
blocked ports by receiving BPDUs from an upstream switching device. If the switching device
cannot receive BPDUs from the upstream because of link congestion or unidirectional-link
failure, the switching device re-selects a root port. The original root port becomes a designated
port and the original blocked ports change to the Forwarding state. This may cause network
loops. To address such a problem, configure loop protection.
After loop protection is configured, if the root port or alternate port does not receive BPDUs
from the upstream switching device, the root port is blocked and the switching device notifies
the NMS that the port enters the Discarding state. The blocked port remains in the Blocked state
and no longer forwards packets. This prevents loops on the network. The root port restores the
Forwarding state after receiving new BPDUs.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
233
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
8 STP/RSTP Configuration
NOTE
An alternate port is a backup port of a root port. If a switching device has an alternate port, you need to
configure loop protection on both the root port and the alternate port.
Do as follows on a root port and an alternate port on a switching device.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
interface interface-type interface-number
The Ethernet interface view is displayed.
Step 3 Run:
stp loop-protection
Loop protection for the root port or the alternate port is configured on the switching device.
By default, loop protection is disabled.
----End
8.4.6 Checking the Configuration
After RSTP protection functions are configured, you can verify that the configurations take
effect.
Prerequisite
All configurations of RSTP protection functions are complete.
Procedure
l
Run the display stp [ interface interface-type interface-number ] [ brief ] command to
view the status of a spanning tree, including the status of protection functions on a switching
device
----End
8.5 Configuring STP/RSTP Interoperability Between
Huawei Devices and Non-Huawei Devices
To supports STP/RSTP interoperability between Huawei devices and non-Huawei devices,
proper parameters are required on Huawei devices running STP/RSTP to ensure nonstop
communication.
8.5.1 Establishing the Configuration Task
Before configuring STP/RSTP interoperability between Huawei devices and non-Huawei
devices, familiarize yourself with the applicable environment, complete the pre-configuration
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
234
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
8 STP/RSTP Configuration
tasks, and obtain the required data. This will help you complete the configuration task quickly
and accurately.
Applicable Environment
On a network running STP/RSTP, inconsistent protocol packet formats and BPDU keys may
lead to a communication failure. Configuring proper STP/RSTP parameters on Huawei devices
ensures interoperability between Huawei devices and non-Huawei devices.
Pre-configuration Tasks
Before configuring STP/RSTP interoperability between Huawei devices and non-Huawei
devices, complete the following task:
l
Configuring basic STP/RSTP functions
Data Preparation
To configure STP/RSTP interoperability between Huawei devices and non-Huawei devices, you
need the following data.
No.
Data
BPDU format
8.5.2 Configuring the Proposal/Agreement Mechanism
To enable Huawei Datacom devices to communicate with non-Huawei devices, a proper rapid
transition mechanism needs to be configured on Huawei devices based on the Proposal/
Agreement mechanism on non-Huawei devices.
Context
The rapid transition mechanism is also called the Proposal/Agreement mechanism. Switching
devices currently support the following modes:
l
Enhanced mode: The current interface counts a root port when it counts the synchronization
flag bit.
An upstream device sends a Proposal message to a downstream device, requesting rapid
status transition. After receiving the message, the downstream device sets the port
connected to the upstream device to a root port and blocks all non-edge ports.
The upstream device then sends an Agreement message to the downstream device. After
the downstream device receives the message, the root port transitions to the Forwarding
state.
The downstream device responds the Proposal message with an Agreement message.
After receiving the message, the upstream device sets the port connected to the
downstream device as a designated port. The designated port then transitions to the
Forwarding state.
Issue 02 (2011-11-21)
Common mode: The current interface ignores the root port when it counts the
synchronization flag bit.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
235
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
8 STP/RSTP Configuration
An upstream device sends a Proposal message to a downstream device, requesting rapid
status transition. After receiving the message, the downstream device sets the port
connected to the upstream device to a root port and blocks all non-edge ports. The root
port then transitions to the Forwarding state.
The downstream device responds the Proposal message with an Agreement message.
After receiving the message, the upstream device sets the port connected to the
downstream device as a designated port. The designated port then transitions to the
Forwarding state.
When Huawei datacom devices are interworking with non-Huawei devices, select either mode
depending on the Proposal/Agreement mechanisms on non-Huawei devices.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
interface interface-type interface-number
The Ethernet interface view is displayed.
Step 3 Run:
stp no-agreement-check
The common rapid transition mechanism is configured.
By default, the interface uses the enhanced rapid transition mechanism.
----End
8.5.3 Checking the Configuration
After MSTP parameters are configured for the interoperability between Huawei devices and
non-Huawei devices, you can verify that the configurations take effect.
Prerequisite
Parameters have been configured to ensure MSTP interoperability between Huawei devices and
non-Huawei devices.
Procedure
l
Run the display stp [ interface interface-type interface-number ] [ brief ] command to
view spanning-tree status.
----End
8.6 Maintaining STP/RSTP
STP/RSTP maintenance includes resetting STP/RSTP statistics.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
236
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
8 STP/RSTP Configuration
8.6.1 Clearing STP/RSTP Statistics
You can run the reset commands to reset STP/RSTP statistics to 0.
Context
CAUTION
STP/RSTP statistics cannot be restored after you clear them. Therefore, exercise caution when
using the reset commands.
After you confirm that STP/RSTP statistics need to be cleared, run the following command in
the user view.
Procedure
Step 1 Run the reset stp [ interface interface-type interface-number ] statistics command to clear
spanning-tree statistics.
----End
8.7 Configuration Examples
This section shows typical usage scenarios of STP/RSTP by describing networking
requirements, configuration roadmap, and data preparation, and provides related configuration
files.
8.7.1 Example for Configuring Basic STP Functions
This example shows how to configure basic STP functions.
Networking Requirements
Network designers tend to deploy multiple physical links between two devices (one link is the
master and the others are backups) to fulfill network redundancy requirements. Loops are bound
to occur on such types of complex networks.
Loops will cause broadcast storms, which exhaust network resources and paralyze the network.
Loops also cause MAC address flapping that damages MAC address entries.
STP can be deployed on a network to eliminate loops by blocking some ports. On the network
shown in Figure 8-3, after SwitchA, SwitchB, SwitchC, and SwitchD running STP discover
loops by exchanging information, they trim the ring topology into a loop-free tree topology by
blocking a certain port. STP prevents replication and circular propagation of packets on the
network and the release the switching devices from processing duplicate packets, improving
their processing performance.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
237
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
8 STP/RSTP Configuration
Figure 8-3 Configuring basic STP functions
Network
GE0/0/3
SwitchD
GE0/0/3
Root
GE0/0/1 GE0/0/1
Bridge
GE0/0/2 SwitchA
GE0/0/2
STP
GE0/0/3
GE0/0/3
SwitchC
GE0/0/1
SwitchB
GE0/0/1
GE0/0/2
GE0/0/2
PC1
PC2
Blocked port
Configuration Roadmap
The configuration roadmap is as follows:
1.
Configure basic STP functions, including:
a.
Configure the STP mode for the ring network.
b.
Configure primary and secondary root bridges.
c.
Set path costs for ports to block certain ports.
d.
Enable STP to eliminate loops.
NOTE
STP is not required on the interfaces connected to terminals because these interfaces do not
need to participate in STP calculation.
Data Preparation
To complete the configuration, you need the following data:
l
GEInterface number, as shown in Figure 8-3
Primary root bridge SwitchA and secondary root bridge SwitchD
Path cost of a port to be blocked (20000 is used in this example)
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
238
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
8 STP/RSTP Configuration
Procedure
Step 1 Configure basic STP functions.
1.
Configure the STP mode for the devices on the ring network.
# Configure the STP mode on SwitchA.
<Quidway> system-view
[Quidway] sysname SwitchA
[SwitchA] stp mode stp
# Configure the STP mode on SwitchB.
<Quidway> system-view
[Quidway] sysname SwitchB
[SwitchB] stp mode stp
# Configure the STP mode on SwitchC.
<Quidway> system-view
[Quidway] sysname SwitchC
[SwitchC] stp mode stp
# Configure the STP mode on SwitchD.
<Quidway> system-view
[Quidway] sysname SwitchD
[SwitchD] stp mode stp
2.
Configure primary and secondary root bridges.
# Configure SwitchA as a primary root bridge.
[SwitchA] stp root primary
# Configure SwitchD as a secondary root bridge.
[SwitchD] stp root secondary
3.
Set path costs for ports in each spanning tree to block certain ports.
NOTE
l The values of path costs depend on the path-cost calculation method. Huawei calculation method
is used in this example, and the path cost of the blocked port is set to 200000 (the highest value
in the range).
l All switching devices on a network must use the same path cost calculation method.
# Set the path cost of GE0/0/1 on SwitchC to 20000.
[SwitchC] interface gigabitethernet 0/0/1
[SwitchC-GigabitEthernet0/0/1] stp cost 20000
[SwitchC-GigabitEthernet0/0/1] quit
4.
Enable STP to eliminate loops.
l Disable STP on interfaces connected to PCs.
# Disable STP on GE 0/0/2 on SwitchB.
[SwitchB] interface gigabitethernet 0/0/2
[SwitchB-GigabitEthernet0/0/2] stp disable
[SwitchB-GigabitEthernet0/0/2] quit
# Disable STP on GE 0/0/2 on SwitchC.
[SwitchC] interface gigabitethernet 0/0/2
[SwitchC-GigabitEthernet0/0/2] stp disable
[SwitchC-GigabitEthernet0/0/2] quit
l Enable STP globally.
# Enable STP globally on SwitchA.
[SwitchA] stp enable
# Enable STP globally on SwitchB.
[SwitchB] stp enable
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
239
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
8 STP/RSTP Configuration
# Enable STP globally on SwitchC.
[SwitchC] stp enable
# Enable STP globally on SwitchD.
[SwitchD] stp enable
l Enable BPDU on all the interfaces except the interfaces connected to terminals.
# Enable BPDU on GE 0/0/1 and GE 0/0/2 on SwitchA.
[SwitchA] interface gigabitethernet
[SwitchA-GigabitEthernet0/0/1] bpdu
[SwitchA-GigabitEthernet0/0/1] quit
[SwitchA] interface gigabitethernet
[SwitchA-GigabitEthernet0/0/2] bpdu
[SwitchA-GigabitEthernet0/0/2] quit
0/0/1
enable
0/0/2
enable
# Enable BPDU on GE 0/0/1 and GE 0/0/3 on SwitchB.
[SwitchB] interface gigabitethernet
[SwitchB-GigabitEthernet0/0/1] bpdu
[SwitchB-GigabitEthernet0/0/1] quit
[SwitchB] interface gigabitethernet
[SwitchB-GigabitEthernet0/0/3] bpdu
[SwitchB-GigabitEthernet0/0/3] quit
0/0/1
enable
0/0/3
enable
# Enable BPDU on GE 0/0/1 and GE 0/0/3 on SwitchC.
[SwitchC] interface gigabitethernet
[SwitchC-GigabitEthernet0/0/1] bpdu
[SwitchC-GigabitEthernet0/0/1] quit
[SwitchC] interface gigabitethernet
[SwitchC-GigabitEthernet0/0/3] bpdu
[SwitchC-GigabitEthernet0/0/3] quit
0/0/1
enable
0/0/3
enable
# Enable BPDU on GE 0/0/1 and GE 0/0/2 on SwitchD.
[SwitchD] interface gigabitethernet
[SwitchD-GigabitEthernet0/0/1] bpdu
[SwitchD-GigabitEthernet0/0/1] quit
[SwitchD] interface gigabitethernet
[SwitchD-GigabitEthernet0/0/2] bpdu
[SwitchD-GigabitEthernet0/0/2] quit
0/0/1
enable
0/0/2
enable
Step 2 Verify the configuration.
After the previous configurations, run the following commands to verify the configuration when
the network is stable:
# Run the display stp brief command on SwitchA to view the interface status and protection
type. The displayed information is as follows:
[SwitchA] display stp brief
MSTID Port
0
GigabitEthernet0/0/1
0
GigabitEthernet0/0/2
Role
DESI
DESI
STP State
FORWARDING
FORWARDING
Protection
NONE
NONE
After SwitchA is configured as a root bridge, GE 0/0/2 and GE 0/0/1 connected to SwitchB and
SwitchD respectively are elected as designated ports in spanning tree calculation.
# Run the display stp interface gigabitethernet 0/0/1 brief command on SwitchB to view status
of GE 0/0/1. The displayed information is as follows:
[SwitchB] display stp interface gigabitethernet 0/0/1 brief
MSTID Port
Role STP State
Protection
0
GigabitEthernet0/0/1
DESI FORWARDING
NONE
GE 0/0/1 is elected as a designated port in spanning tree calculation and is in the Forwarding
state.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
240
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
8 STP/RSTP Configuration
# Run the display stp brief command on SwitchC to view the interface status and protection
type. The displayed information is as follows:
[SwitchC] display stp brief
MSTID Port
0
GigabitEthernet0/0/1
0
GigabitEthernet0/0/3
Role
ALTE
ROOT
STP State
DISCARDING
FORWARDING
Protection
NONE
NONE
GE 0/0/1 is elected as an alternate port in spanning tree calculation and is in the Discarding state.
GE 0/0/3 is elected as a root port in spanning tree calculation and is in the Forwarding state.
----End
Configuration Files
l
Configuration file of SwitchA
#
sysname
SwitchA
#
stp mode
stp
stp instance 0 root
primary
#
return
Configuration file of SwitchB
#
sysname
SwitchB
#
stp mode
stp
#
interface GigabitEthernet0/0/2
stp disable
#
return
Configuration file of SwitchC
#
sysname
SwitchC
#
stp mode
stp
#
interface GigabitEthernet0/0/1
stp instance 0 cost
20000
#
interface GigabitEthernet0/0/2
stp disable
#
return
Configuration file of SwitchD
#
sysname
SwitchD
#
stp mode
stp
stp instance 0 root
secondary
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
241
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
8 STP/RSTP Configuration
#
return
8.7.2 Example for Configuring Basic RSTP Functions
This example describes how to configure basic RSTP functions.
Networking Requirements
Network designers tend to deploy multiple physical links between two devices (one link is the
master and the others are backups) to fulfill network redundancy requirements. Loops are bound
to occur on such types of complex networks.
Loops will cause broadcast storms, which exhaust network resources and paralyze the network.
Loops also cause MAC address flapping that damages MAC address entries.
RSTP can be deployed on a network to eliminate loops by blocking some ports. On the network
shown in Figure 8-4, after SwitchA, SwitchB, SwitchC, and SwitchD running RSTP detect
loops by exchanging information, they trim the ring topology into a loop-free tree topology by
blocking a certain port. RSTP prevents replication and circular propagation of packets on the
network and the release the switching devices from processing duplicate packets, improving
their processing performance.
Figure 8-4 Configuring basic RSTP functions
Network
GE0/0/3
SwitchD
GE0/0/3
Root
GE0/0/1 GE0/0/1
Bridge
GE0/0/2 SwitchA
GE0/0/2
RSTP
GE0/0/3
GE0/0/3
SwitchC
GE0/0/1
GE0/0/2
SwitchB
GE0/0/1
GE0/0/2
PC1
PC2
Blocked port
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
242
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
8 STP/RSTP Configuration
Configuration Roadmap
The configuration roadmap is as follows:
1.
Configure basic RSTP functions, including:
a.
Configure the RSTP mode for the ring network.
b.
Configure primary and secondary root bridges.
c.
Set path costs for the ports in each MSTI to determine the port to be blocked.
d.
Enable RSTP to eliminate loops.
NOTE
RSTP is not required on the interfaces connected to terminals because these interfaces do not
need to participate in RSTP calculation.
2.
Configure RSTP protection functions, for example, root protection on a designated port of
a root bridge in each MSTI.
Data Preparation
To complete the configuration, you need the following data:
l
GE interface number, as shown in Figure 8-4
Primary root bridge SwitchA and secondary root bridge SwitchD
Path cost of the port to be blocked (20000 is used in this example)
Procedure
Step 1 Configure basic RSTP functions.
1.
Configure the RSTP mode for the devices on the ring network.
# Configure the RSTP mode on SwitchA.
<Quidway> system-view
[Quidway] sysname SwitchA
[SwitchA] stp mode rstp
# Configure the RSTP mode on SwitchB.
<Quidway> system-view
[Quidway] sysname SwitchB
[SwitchB] stp mode rstp
# Configure the RSTP mode on SwitchC.
<Quidway> system-view
[Quidway] sysname SwitchC
[SwitchC] stp mode rstp
# Configure the RSTP mode on SwitchD.
<Quidway> system-view
[Quidway] sysname SwitchD
[SwitchD] stp mode rstp
2.
Configure primary and secondary root bridges.
# Configure SwitchA as the primary root bridge.
[SwitchA] stp root primary
# Configure SwitchD as the secondary root bridge.
[SwitchD] stp root secondary
3.
Issue 02 (2011-11-21)
Set path costs for ports to block certain ports.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
243
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
8 STP/RSTP Configuration
NOTE
l The values of path costs depend on the path-cost calculation method. Huawei calculation method
is used in this example, and the path cost of the blocked port is set to 200000 (the highest value
in the range).
l All switching devices on a network must use the same path cost calculation method.
# Set the path cost of GE0/0/1 on SwitchC to 20000.
[SwitchC] interface gigabitethernet 0/0/1
[SwitchC-GigabitEthernet0/0/1] stp cost 20000
[SwitchC-GigabitEthernet0/0/1] quit
4.
Enable RSTP to eliminate loops.
l Disable RSTP on interfaces connected to PCs.
# Disable RSTP on GE 0/0/2 on SwitchB.
[SwitchB] interface gigabitethernet 0/0/2
[SwitchB-GigabitEthernet0/0/2] stp disable
[SwitchB-GigabitEthernet0/0/2] quit
# Disable RSTP on GE 0/0/2 on SwitchC.
[SwitchC] interface gigabitethernet 0/0/2
[SwitchC-GigabitEthernet0/0/2] stp disable
[SwitchC-GigabitEthernet0/0/2] quit
l Enable RSTP globally.
# Enable RSTP globally on SwitchA.
[SwitchA] stp enable
# Enable RSTP globally on SwitchB.
[SwitchB] stp enable
# Enable RSTP globally on SwitchC.
[SwitchC] stp enable
# Enable RSTP globally on SwitchD.
[SwitchD] stp enable
l Enable BPDU on all the interfaces except the interfaces connected to terminals.
# Enable BPDU on GE 0/0/1 and GE 0/0/2 on SwitchA.
[SwitchA] interface gigabitethernet
[SwitchA-GigabitEthernet0/0/1] bpdu
[SwitchA-GigabitEthernet0/0/1] quit
[SwitchA] interface gigabitethernet
[SwitchA-GigabitEthernet0/0/2] bpdu
[SwitchA-GigabitEthernet0/0/2] quit
0/0/1
enable
0/0/2
enable
# Enable BPDU on GE 0/0/1 and GE 0/0/3 on SwitchB.
[SwitchB] interface gigabitethernet
[SwitchB-GigabitEthernet0/0/1] bpdu
[SwitchB-GigabitEthernet0/0/1] quit
[SwitchB] interface gigabitethernet
[SwitchB-GigabitEthernet0/0/3] bpdu
[SwitchB-GigabitEthernet0/0/3] quit
0/0/1
enable
0/0/3
enable
# Enable BPDU on GE 0/0/1 and GE 0/0/3 on SwitchC.
[SwitchC] interface gigabitethernet
[SwitchC-GigabitEthernet0/0/1] bpdu
[SwitchC-GigabitEthernet0/0/1] quit
[SwitchC] interface gigabitethernet
[SwitchC-GigabitEthernet0/0/3] bpdu
[SwitchC-GigabitEthernet0/0/3] quit
0/0/1
enable
0/0/3
enable
# Enable BPDU on GE 0/0/1 and GE 0/0/2 on SwitchD.
[SwitchD] interface gigabitethernet 0/0/1
[SwitchD-GigabitEthernet0/0/1] bpdu enable
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
244
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
8 STP/RSTP Configuration
[SwitchD-GigabitEthernet0/0/1] quit
[SwitchD] interface gigabitethernet 0/0/2
[SwitchD-GigabitEthernet0/0/2] bpdu enable
[SwitchD-GigabitEthernet0/0/2] quit
Step 2 Configure RSTP protection functions.
# Enable root protection on GE 0/0/1 on SwitchA.
[SwitchA] interface gigabitethernet 0/0/1
[SwitchA-GigabitEthernet0/0/1] stp root-protection
[SwitchA-GigabitEthernet0/0/1] quit
# Enable root protection on GE 0/0/2 on SwitchA.
[SwitchA] interface gigabitethernet 0/0/2
[SwitchA-GigabitEthernet0/0/2] stp root-protection
[SwitchA-GigabitEthernet0/0/2] quit
Step 3 Verify the configuration.
After the previous configurations, run the following commands to verify the configuration when
the network is stable:
# Run the display stp brief command on SwitchA to view the interface status and protection
type. Information similar to the following will be displayed:
[SwitchA] display stp brief
MSTID Port
0
GigabitEthernet0/0/1
0
GigabitEthernet0/0/2
Role
DESI
DESI
STP State
FORWARDING
FORWARDING
Protection
ROOT
ROOT
After SwitchA is configured as a root bridge, GE 0/0/2 and GE 0/0/1 connected to SwitchB and
SwitchD respectively are elected as designated ports in spanning tree calculation. The root
protection function is enabled on the designated ports.
# Run the display stp interface gigabitethernet 0/0/1 brief command on SwitchB to view status
of GE 0/0/1. Information similar to the following will be displayed:
[SwitchB] display stp interface gigabitethernet 0/0/1 brief
MSTID Port
Role STP State
Protection
0
GigabitEthernet0/0/1
DESI FORWARDING
NONE
GE 0/0/1 is elected as a designated port in spanning tree calculation and is in the Forwarding
state.
# Run the display stp brief command on SwitchC to view the interface status and protection
type. Information similar to the following will be displayed:
[SwitchC] display stp brief
MSTID Port
0
GigabitEthernet0/0/1
0
GigabitEthernet0/0/3
Role
ALTE
ROOT
STP State
DISCARDING
FORWARDING
Protection
NONE
NONE
GE 0/0/1 is elected as an alternate port in spanning tree calculation and is in the Discarding state.
GE 0/0/3 is elected as a root port in spanning tree calculation and is in the Forwarding state.
----End
Configuration Files
l
Configuration file of SwitchA
#
sysname SwitchA
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
245
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
8 STP/RSTP Configuration
#
stp mode
rstp
stp instance 0 root
primary
#
interface GigabitEthernet0/0/1
stp rootprotection
#
interface GigabitEthernet0/0/2
stp rootprotection
#
return
Configuration file of SwitchB
#
sysname SwitchB
#
stp mode
rstp
#
interface GigabitEthernet0/0/2
stp disable
#
return
Configuration file of SwitchC
#
sysname SwitchC
#
stp mode
rstp
#
interface GigabitEthernet0/0/1
stp instance 0 cost
20000
#
interface GigabitEthernet0/0/2
stp disable
#
return
Configuration file of SwitchD
#
sysname SwitchD
#
stp mode
rstp
stp instance 0 root
secondary
#
return
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
246
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
9 MSTP Configuration
MSTP Configuration
About This Chapter
The Multiple Spanning Tree Protocol (MSTP) trims a ring network into a loop-free tree network.
It prevents replication and circular propagation of packets, provides multiple redundant paths
for Virtual LAN (VLAN) data traffic, and enables load balancing.
9.1 MSTP Overview
MSTP enables multiple VLANs to be grouped into a spanning-tree instance, forming a VLAN
mapping table. Each instance has a spanning-tree topology independent of other spanning-tree
instances. This architecture provides multiple forwarding paths for data traffic and enables load
balancing.
9.2 Configuring Basic MSTP Functions
MSTP based on the basic STP/RSTP function divides a switching network into multiple regions,
each of which has multiple spanning trees that are independent of each other. MSTP isolates
user traffic and service traffic, and load-balances VLAN traffic.
9.3 Configuring MSTP Multi-process
After an MSTP device binds its ports to different processes, the MSTP device performs the
MSTP calculation based on processes, and only relevant ports in each process take part in MSTP
calculation.
9.4 Configuring MSTP Parameters on an Interface
MSTP implements RSTP rapid convergence. To achieve rapid convergence, you need to
configure proper MSTP parameters.
9.5 Configuring MSTP Protection Functions
MSTP protection functions are as follows, and you can configure one or more functions as
required.
9.6 Configuring MSTP Interoperability Between Huawei Devices and Non-Huawei Devices
To enable Huawei devices to interwork with non-Huawei devices, configure proper parameters
and functions, including the BPDU format, MSTP protocol packet format, and digest snooping
function, on the Huawei devices running MSTP.
9.7 Maintaining MSTP
MSTP maintenance includes resetting MSTP statistics.
9.8 Configuration Examples
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
247
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
9 MSTP Configuration
This section provides an MSTP configuration example.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
248
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
9 MSTP Configuration
9.1 MSTP Overview
MSTP enables multiple VLANs to be grouped into a spanning-tree instance, forming a VLAN
mapping table. Each instance has a spanning-tree topology independent of other spanning-tree
instances. This architecture provides multiple forwarding paths for data traffic and enables load
balancing.
9.1.1 MSTP Introduction
The Multiple Spanning Tree Protocol (MSTP) incorporates the functions of the Spanning Tree
Protocol (STP) and Rapid Spanning Tree Protocol (RSTP), and outperforms them. It enables
rapid convergence and provides load balancing across redundant paths.
Background
STP and RSTP are used in a LAN to prevent loops. The devices running STP/RSTP discover
loops on the network by exchanging information with each other and trim the ring topology into
a loop-free tree topology by blocking a certain interface. Replication and circular propagation
of packets are thus prevented on the network and the processing performance of devices is
improved by avoiding repeated packets on the network.
STP and RSTP both have a defect: All VLANs on a LAN use one spanning tree, and thus interVLAN load balancing cannot be performed. Once a link is blocked, the link will no longer
transmit traffic, wasting bandwidth and causing a failure in forwarding certain VLAN packets.
To fix the defect of STP and RSTP, the IEEE released the 802.1s standard in 2002, defining
MSTP. MSTP compatible with STP and RSTP implements rapid convergence and provides
multiple paths to load balance VLAN traffic.
Table 9-1 shows the comparison between STP, RSTP, and MSTP.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
249
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
9 MSTP Configuration
Table 9-1 Comparison between STP, RSTP, and MSTP
Spannin
g Tree
Protocol
s
Characteristics
Application Scenarios
Precautions
STP
A loop-free tree is
generated. Thus,
broadcast storms are
prevented and
redundancy is
implemented.
Irrespective of different
users or services, all
VLANs share one
spanning tree.
NOTE
RSTP
l A loop-free tree is
generated. Thus,
broadcast storms are
prevented and
redundancy is
implemented.
l If the current
switching device
supports both STP
and RSTP, RSTP is
recommended. For
details, see STP/
RSTP
Configuration.
l A feedback
mechanism is
provided to confirm
topology
convergence. Thus,
rapid convergence is
implemented.
MSTP
l A loop-free tree or
some loop-free trees
are generated. Thus,
broadcast storms are
prevented and
redundancy is
implemented.
l A feedback
mechanism is
provided to confirm
topology
convergence. Thus,
rapid convergence is
implemented.
l If the current
switching device
supports only STP,
STP is
recommended. For
details, see STP/
RSTP
Configuration.
l If the current
switching device
supports STP or
RSTP, and MSTP,
MSTP is
recommended.
User or service-specific
load balancing is
required. Traffic for
different VLANs is
forwarded through
different spanning trees,
which are independent of
each other.
l MSTP implements
load balancing among
VLANs. Traffic in
different VLANs is
transmitted along
different paths.
Introduction
On a complex network, loops are inevitable. With the requirement for network redundancy
backup, network designers tend to deploy multiple physical links between two devices, one of
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
250
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
9 MSTP Configuration
which is the master and the others are the backup. Loops are likely or bound to occur in such a
situation.
Loops will cause broadcast storms, thereby exhausting network resources and paralyzing the
network. Loops also cause flapping of MAC address tables and thus damages MAC address
entries.
MSTP, compatible with STP and RSTP, isolates service traffic and user traffic by using multiple
instances and provides multiple paths to load balance VLAN traffic.
If MSTP is deployed in the LAN shown in Figure 9-1, MSTIs are generated, as shown in Figure
9-1.
Figure 9-1 Multiple spanning trees in an MST region
SwitchD
SwitchA
VLAN3
VLAN2
VLAN2
VLAN2
VLAN3
VLAN3
Host C
(VLAN3)
Host A
(VLAN2)
SwitchB
SwitchE
VLAN2
Host B
(VLAN2)
VLAN2
VLAN2
VLAN3
VLAN2
VLAN3
Host D
(VLAN3)
VLAN3
SwitchC
VLAN3
SwitchF
MSTI1 (root switch: SwitchD)
MSTI2 (root switch: SwitchF)
VLAN2 --> MSTI1
VLAN3 --> MSTI2
MSTI 1 uses Switch D as the root switching device to forward packets of VLAN 2.
MSTI 2 uses Switch F as the root switching device to forward packets of VLAN 3.
Devices within the same VLAN can communicate with each other and packets of different
VLANs are load-balanced along different paths.
Basic MSTP Concepts
l
MST region
An MST region contains multiple switching devices and network segments between them.
The switching devices have the following characteristics:
MSTP-enabled
Same region name
Same VLAN-to-instance mapping
Same MSTP revision number
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
251
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
9 MSTP Configuration
A LAN can comprise several MST regions that are directly or indirectly connected.
Multiple switching devices can be grouped into an MST region by using MSTP
configuration commands.
As shown in Figure 9-2, the MST region D0 contains the switching devices S1, S2, S3,
and S4, and has three MSTIs.
Figure 9-2 MST region
AP1
D0
Master Bridge
MSTI1
root switch:S3
S1
MSTI2
root switch:S2
S2
S3
S4
MSTI0 (IST)
root switch:S1
VLAN1
MSTI1
VLAN2,VLAN3 MSTI2
other VLANs MSTI0
VLAN mapping table
The VLAN mapping table is an attribute of the MST region. It describes mappings between
VLANs and MSTIs.
Figure 9-2 shows the mappings in the VLAN mapping table of the MST region D0:
VLAN 1 is mapped to MSTI 1.
VLAN 2 and VLAN 3 are mapped to MSTI 2.
Other VLANs are mapped to MSTI 0.
Regional root
Regional roots are classified into Internal Spanning Tree (IST) and MSTI regional roots.
In the region B0, C0, and D0 on the network shown in Figure 9-4, the switching devices
closest to the Common and Internal Spanning Tree (CIST) root are IST regional roots.
An MST region can contain multiple spanning trees, each called an MSTI. An MSTI
regional root is the root of the MSTI. On the network shown in Figure 9-3, each MSTI has
its own regional root.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
252
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
9 MSTP Configuration
Figure 9-3 MSTI
MST Region
VLA
N
VLAN
10&20&30
10&
20
VLAN 20&30
VLAN
10&30
VLAN
30
VLAN
20
VLAN
10&30
VLAN 10
Root
Root
MSTI
corresponding to
VLAN 10
MSTI
corresponding to
VLAN 20
MSTI Root
corresponding to
VLAN 30
MSTI links
MSTI links blocked by the protocol
MSTIs are independent of each other. An MSTI can correspond to one or more VLANs,
but a VLAN can be mapped to only one MSTI.
l
Issue 02 (2011-11-21)
CIST root
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
253
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
9 MSTP Configuration
Figure 9-4 MSTP network
A0
CIST Root
D0
Region Root
B0
Region Root
C0
Region Root
IST
CST
On the network shown in Figure 9-4, the CIST root is the root bridge of a CIST. The CIST
root is a device in A0.
l
CST
A Common Spanning Tree (CST) connects all the MST regions on a switching network.
Each MST region can be considered a node. A CST is calculated by using STP or RSTP
based on all the nodes.
As shown in Figure 9-4, the MST regions are connected to form a CST.
IST
An IST resides within an MST region.
An IST is a special MSTI with the MSTI ID of 0, called MSTI 0.
An IST is a segment of the CIST in an MST region.
As shown in Figure 9-4, the switching devices in an MST region are connected to form an
IST.
CIST
A CIST, calculated by using STP or RSTP, connects all the switching devices on a switching
network.
As shown in Figure 9-4, the ISTs and the CST form a complete spanning tree, that is, CIST.
SST
A Single Spanning Tree (SST) is formed in either of the following situations:
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
254
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
9 MSTP Configuration
A switching device running STP or RSTP belongs to only one spanning tree.
An MST region has only one switching device.
As shown in Figure 9-4, the switching device in B0 is an SST.
l
Port roles
Compared with RSTP, MSTP has two additional port types. MSTP ports can be root ports,
designated ports, alternate ports, backup ports, edge ports, master ports, and regional edge
ports.
The functions of root ports, designated ports, alternate ports, backup ports, and edge ports
have been defined in RSTP. Table 9-2 lists all port roles in MSTP.
NOTE
Except edge ports, all ports participate in MSTP calculation.
A port can play different roles in different MSTIs.
Table 9-2 Port roles
Port
Roles
Description
Root port
A root port is the non-root bridge port closest to the root bridge. Root bridges
do not have root ports.
Root ports are responsible for sending data to root bridges.
As shown in Figure 9-5, S1 is the root; CP1 is the root port on S3; BP1 is
the root port on S2; DP1 is the root port on S4.
Designat
ed port
The designated port on a switching device forwards bridge protocol data
units (BPDUs) to the downstream switching device.
As shown in Figure 9-5, AP2 and AP3 are designated ports on S1; BP2 is
a designated port on S2; CP2 is a designated port on S3.
Alternate
port
l From the perspective of sending BPDUs, an alternate port is blocked after
a BPDU sent by another switching devices is received.
l From the perspective of user traffic, an alternate port provides an
alternate path to the root bridge. This path is different than using the root
port.
As shown in Figure 9-5, BP2 and AP4 are alternate ports.
Backup
port
l From the perspective of sending BPDUs, a backup port is blocked after
a BPDU sent by itself is received.
l From the perspective of user traffic, a backup port provides a backup/
redundant path to a segment where a designated port already connects.
As shown in Figure 9-5, CP3 is a backup port.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
255
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
9 MSTP Configuration
Port
Roles
Description
Master
port
A master port is on the shortest path connecting MST regions to the CIST
root.
BPDUs of an MST region are sent to the CIST root through the master port.
Master ports are special regional edge ports, functioning as root ports on
ISTs or CISTs and master ports in instances.
As shown in Figure 9-5, S1, S2, S3, and S4 form an MST region. AP1 on
S1, being the nearest port in the region to the CIST root, is the master port.
Regional
edge port
A regional edge port is located at the edge of an MST region and connects
to another MST region or an SST.
During MSTP calculation, the roles of a regional edge port in the MSTI and
the CIST instance are the same. If the regional edge port is the master port
in the CIST instance, it is the master port in all the MSTIs in the region.
As shown in Figure 9-5, AP1, DP2, and DP3 in an MST region are directly
connected to other regions, and therefore they are all regional edge ports of
the MST region.
As shown in Figure 9-5, AP1 is a regional edge port and also a master port
in the CIST. Therefore, AP1 is the master port in every MSTI in the MST
region.
Edge
port
An edge port is located at the edge of an MST region and does not connect
to any switching device.
Generally, edge ports are directly connected to terminals.
As shown in Figure 9-5, BP3 is an edge port.
Figure 9-5 Port roles
AP1
AP4
MST Region
AP2
Root port
AP3
Designated port
S1
Root Bridge
CP1
S3
CP2
Alternate port
BP1
S2
BP2
CP3
Backup port
Regional edge port
BP3
Master port
Edge port
DP1
DP2
Issue 02 (2011-11-21)
S4
DP4
PC
DP3
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
256
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
9 MSTP Configuration
Port status
Table 9-3 lists the MSTP port status, which is the same as the RSTP port status.
Table 9-3 Port status
Port
Status
Description
Forwardi
ng
A port in the Forwarding state can send and receive BPDUs as well as
forward user traffic.
Learning
This is a transition state. A port in the Learning state learns MAC addresses
from user traffic to construct a MAC address table.
In the Learning state, the port can send and receive BPDUs, but cannot
forward user traffic.
Discardi
ng
A port in the Discarding state can only receive BPDUs.
There is no necessary link between the port status and the port role. Table 9-4 lists the
relationships between port roles and port status.
Table 9-4 Relationships between port roles and port status
Port
Status
Root Port/
Master
Port
Designate
d Port
Regional
Edge Port
Alternate
Port
Backup
Port
Forwardi
ng
Yes
Yes
Yes
No
No
Learning
Yes
Yes
Yes
No
No
Discardi
ng
Yes
Yes
Yes
Yes
Yes
Yes: The port supports this status.
No: The port does not support this status.
9.1.2 MSTP Features Supported by the S5700
Before configuring MSTP, familiarize yourself with the concepts of basic MSTP functions,
topology convergence, MSTP protection, MSTP multi-process, and MSTP interoperability
between Huawei devices and non-Huawei devices. This will help you complete the configuration
task quickly and accurately.
MSTP is used to block redundant links on the Layer 2 network and trim a network into a loopfree tree. In MSTP, multiple MSTIs can be created and VLANs are mapped into different
instances to load-balance VLAN traffic. The basic configuration roadmap of MSTP is as follows:
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
257
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
9 MSTP Configuration
1.
In a ring network, divide regions and create different instances for regions.
2.
Select a switching device functioning as a root bridge from switching devices for each
instance.
3.
In each instance, calculate the shortest paths from the other switching devices to the root
bridge, and select a root port for each non-root switching device.
4.
In each instance, select a designated port for each connection according to port IDs.
According to current networking, master ports and backup ports may be involved. For details,
see 9.1.1 MSTP Introduction.
MSTP also supports the following features to meet requirements of special applications and
extended functions:
l
Supports the Proposal/Agreement mechanism to implement rapid convergence.
Supports protection functions as listed in Table 9-5.
Supports MSTP multi-process in the scenario where MSTP and STP/RSTP are used
together. MSTP multi-process implements independent spanning tree calculation for every
access rings.
Supports MSTP interoperability between Huawei devices and non-Huawei devices. Proper
parameters are required on Huawei devices running MSTP to ensure nonstop
communication.
NOTE
The S5706 does not support MSTP multi-process.
Table 9-5 MSTP protection
Issue 02 (2011-11-21)
MSTP
Protection
Scenario
Configuration Impact
BPDU
protection
An edge port changes to be a
non-edge port after
receiving a BPDU, which
triggers spanning tree
recalculation. If an attacker
keeps sending bogus BPDUs
to a switching device,
network flapping occurs.
After BPDU protection is enabled on the
switching device, the switching device shuts
down the edge port if the edge port receives
an RST BPDU, and notifies the NMS of the
shutdown event. The attributes of the edge
port are not changed.
TC protection
Generally, after receiving
TC BPDUs (packets for
advertising network
topology changes), a
switching device needs to
delete MAC entries and ARP
entries. Frequent deletion
operations will exhaust CPU
resources.
TC protection is used to suppress TC-BPDUs.
The number of times that TC-BPDUs are
processed by a switching device within a
given time period is configurable. If the
number of TC-BPDUs that the switching
device receives within the given time exceeds
the specified threshold, the switching device
handles TC-BPDUs only for the specified
number of times. Excessive TC-BPDUs are
processed by the switching device as a whole
for once after the timeout period expires. This
protects the switching device from frequently
deleting MAC entries and ARP entries, thus
avoiding over-burden.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
258
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
9 MSTP Configuration
MSTP
Protection
Scenario
Configuration Impact
Root
protection
Due to incorrect
configurations or malicious
attacks on the network, a
root bridge may receive
BPDUs with a higher
priority. Consequently, the
legitimate root bridge is no
longer able to serve as the
root bridge, and the network
topology is illegitimately
changed, triggering
spanning tree recalculation.
This may transfer traffic
from high-speed links to
low-speed links, causing
traffic congestion.
To address this issue, the root protection
function can be configured to protect the root
bridge by preserving the role of the
designated port. With this function, when the
designated port receives RST BPDUs with a
higher priority, the port enters the Discarding
state and does not forward the BPDUs. If the
port does not receive any RST BPDUs with a
higher priority for a certain period (double the
Forward Delay), the port transitions to the
Forwarding state.
Loop
protection
A root port or an alternate
port will age if link
congestion or a one-way link
failure occurs. After the root
port ages, a switching device
may re-select a root port
incorrectly and after the
alternate port ages, the port
enters the Forwarding state.
Loops may occur in such a
situation.
The loop protection function can be used to
prevent such network loops. If the root port
or alternate port cannot receive RST BPDUs
from the upstream switching device, the root
port is blocked and the switching device
notifies the NMS that the port enters the
Discarding state. The blocked port remains in
the Blocked state and no longer forwards
packets. This prevents loops on the network.
The root port restores the Forwarding state
after new RST BPDUs are received.
Share-link
protection
In the scenario where a
switching device is dualhomed to a network, when
the share link of multiple
processes fails, loops may
occur.
Share-link protection can address such a
problem. This function forcibly changes the
working mode of the local switching device
to RSTP. Share-link protection needs to be
used together with root protection to avoid
network loops.
MSTP Multi-process
l
Background
As shown in Figure 9-6, SwitchA, SwitchB, and SwitchC are connected through Layer 2
links, and are all enabled with MSTP. The CEs on the rings support only STP/RSTP.
Multiple access rings exist and these rings access the MST region by using different
interfaces on SwitchA and SwitchB.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
259
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
9 MSTP Configuration
Figure 9-6 Networking diagram of MSTP multi-process
SwitchC
PE1
CE
PE2
SwitchB
SwitchA
CE
Ring1
Ring3
Ring2
CE
CE
Instance1:VLAN2~100
Process 1
Instance3:VLAN201~300
Process 3
CE
CE
Instance2:VLAN101~200
Process 2
On the network shown in Figure 9-6, multiple Layer 2 rings, Ring 1, Ring 2, and Ring 3
exists. STP must be enabled on these rings to prevent loops. SwitchA and SwitchB are
connected to multiple access rings and these rings are isolated from each other and do not
need intercommunication. STP then will not calculate out one spanning tree for all these
access rings. Instead, STP on each access ring calculates the trees independently.
MSTP supports multiple spanning tree instances (MSTIs) only when all devices support
MSTP and the devices are configured with the same MST region. In the networking, the
CEs connected to switching devices, however, support only STP/RSTP. According to
MSTP, switching devices consider that they are in different regions with CEs after receiving
STP/RSTP messages sent from the CEs. Therefore, only one spanning tree is calculated
for the ring formed by switching devices and CEs and the access rings are not independent
of each other.
In this case, MSTP multi-process can be used. Multiple MSTP processes can be configured
on SwitchA and SwitchB. Each MSTP process has the same function and supports MSTIs.
Each MSTP process corresponds to one access ring.
After MSTP multi-process is enabled, each MSTP process can manage some interfaces on
a device. That is, Layer 2 interfaces on the device are divided and managed by multiple
MSTP processes. Each MSTP process runs the standard MSTP.
NOTE
CEs that support MSTP can also be configured with MSTP multi-process.
After a device properly starts, there is a default MSTP process with the ID 0. MSTP configurations
in the system view and interface view both belong to this process.
Issue 02 (2011-11-21)
Share link
As shown in Figure 9-6, the link between SwitchA and SwitchB is a Layer 2 link running
MSTP. The share link between SwitchA and SwitchB is different from the links connecting
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
260
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
9 MSTP Configuration
switching devices to CEs. The ports on the share link need to participate in the calculation
for multiple access rings and MSTP processes. This allows SwitchA and SwitchB to
identify from which MST BPDUs are sent.
In addition, a port on the share link participates in the calculation for multiple MSTP
processes, and obtains different status. As a result, the port cannot determine its status.
To prevent this situation, it is defined that a port on a share link always adopts its status in
MSTP process 0 when participating in the calculation for multiple MSTP processes.
NOTE
The S5700 does not support the Per-VLAN Spanning Tree (PVST) protocol and cannot process PVST
packets. You can configure the S5700 to transparently transmit PVST packets. For details, see 11 Layer
2 Protocol Transparent Transmission Configuration.
9.2 Configuring Basic MSTP Functions
MSTP based on the basic STP/RSTP function divides a switching network into multiple regions,
each of which has multiple spanning trees that are independent of each other. MSTP isolates
user traffic and service traffic, and load-balances VLAN traffic.
MSTP is commonly configured on a switching device to trim a ring network to a loop-free
network. MSTP configurations on the switching device involve MSTP working mode
configuration and MST region configuration and activation. If you need to interfere in the
spanning tree calculation, the following methods are available:
l
Setting a priority for a switching device in an MSTI: The lower the numerical value, the
higher the priority of the switching device and the more likely the switching device becomes
a root bridge; the higher the numerical value, the lower the priority of the switching device
and the less likely that the switching device becomes a root bridge.
Setting a path cost for a port in an MSTI: With the same calculation method, the lower the
numerical value, the smaller the cost of the path from the port to the root bridge and the
more likely the port becomes a root port; the higher the numerical value, the larger the cost
of the path from the port to the root bridge and the less likely that the port becomes a root
port.
Setting a priority for a port in an MSTI: The lower the numerical value, the more likely the
port becomes a designated port; the higher the numerical value, the less likely that the port
becomes a designated port.
9.2.1 Establishing the Configuration Task
Before configuring basic MSTP functions, familiarize yourself with the applicable environment,
complete the pre-configuration tasks, and obtain the required data. This will help you complete
the configuration task quickly and accurately.
Applicable Environment
On a complex network, loops are inevitable. With the requirement for network redundancy
backup, network designers tend to deploy multiple physical links between two devices, one of
which is the master and the others are the backup. Loops are likely or bound to occur in such a
situation.
Loops will cause broadcast storms, thereby exhausting network resources and paralyzing the
network. Loops also cause flapping of MAC address tables and thus damages MAC address
entries.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
261
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
9 MSTP Configuration
MSTP can be deployed on a network to eliminate loops. If a loop is detected, MSTP blocks one
or more ports to eliminate the loop. In addition, MSTIs can be configured to load-balance VLAN
traffic.
As shown in Figure 9-7, Switches A, B, C, and D all support MSTP. It is required to create
MSTI 1 and MSTI 2, configure a root bridge for each MSTI, and set the ports to be blocked to
load-balance traffic of VLANs 1 to 10 and VLANs 11 to 20 among different paths.
Figure 9-7 Networking diagram of configuring basic MSTP functions
Network
MST Region
SwitchA
SwitchB
SwitchC
SwitchD
PC1
PC2
VLAN1~10
VLAN11~20
MSTI1
MSTI2
MSTI1:
Root Switch:SwitchA
Blocked port
MSTI2:
Root Switch:SwitchB
Blocked port
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
262
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
9 MSTP Configuration
NOTE
If the current device supports MSTP, configuring MSTP is recommended.
Pre-configuration Tasks
Before configuring basic MSTP functions, complete the following task:
l
Connecting interfaces and setting physical parameters for the interfaces to ensure that the
physical status of the interfaces is Up
Configuring VLAN features of the ports
Data Preparation
To configure basic MSTP functions, you need the following data.
No.
Data
MSTP working mode
MST region name, VLAN-to-instance mapping, and MSTP revision number
(Optional) ID of an MSTI
(Optional) Priority of a switching device in an MSTI
(Optional) Priority of a port in an MSTI
(Optional) Path cost of a port in an MSTI
9.2.2 Configuring the MSTP Mode
Before configuring basic MSTP functions, you need to configure the working mode of a
switching device to MSTP. MSTP is compatible with STP and RSTP.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
stp mode mstp
The working mode of the switching device is configured as MSTP. By default, the working
mode is MSTP.
STP and MSTP cannot recognize packets of each other but MSTP and RSTP can. If a switching
device is configured to work in MSTP mode and is connected to some switching devices running
STP, the switching device automatically transits the working mode of the interfaces connected
to the switching devices running STP to STP and other interfaces still run MSTP. This enables
devices running different spanning tree protocols to interwork with each other.
----End
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
263
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
9 MSTP Configuration
9.2.3 Configuring and Activating an MST Region
MSTP divides a switching network into multiple MST regions. After an MST region name,
VLAN-to-instance mappings, and an MSTP revision number are configured, activating the MST
region is necessary. After this step is done, MST region configuration is complete.
Context
An MST region contains multiple switching devices and network segments between them. These
switching devices are directly connected and have the same region name, same VLAN-toinstance mapping, same configuration revision number after MSTP is enabled. One switching
network can have multiple MST regions and multiple switching devices can be grouped into
one MST region by using MSTP configuration commands.
CAUTION
Two switching devices belong to the same MST region when they have the same:
l
Name of the MST region
Mapping between VLANs and MSTIs
Revision level of the MST region
Do as follows on a switching device that needs to join an MST region:
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
stp region-configuration
The MST region view is displayed.
Step 3 Run:
region-name name
The name of an MST region is configured.
By default, the MST region name is the MAC address of the management network interface on
the MPU of the switching device.
Step 4 Perform either of the following steps to configure VLAN-to-instance mappings.
l Run the instance instance-id vlan { vlan-id [ to vlan-id ] }&<1-10> command to configure
VLAN-to-instance mappings.
l Run the vlan-mapping modulo modulo command to enable VLAN-to-instance mapping
assignment based on a default algorithm.
By default, all VLANs in an MST region are mapped to MSTI 0.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
264
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
9 MSTP Configuration
NOTE
l The instance instance-id vlan { vlan-id [ to vlan-id ] }&<1-10> command is recommended because
VLAN-to-instance mapping assignments cannot meet actual mapping requirements.
l In the command, vlan-mapping modulo indicates that the formula (VLAN ID-1)%modulo+1 is used.
In the formula, (VLAN ID-1)%modulo means the remainder of (VLAN ID-1) divided by the value of
modulo. This formula is used to map a VLAN to the corresponding MSTI. The calculation result of
the formula is ID of the mapping MSTI.
Step 5 (Optional) Run:
revision-level level
The MSTP revision number is set.
By default, the MSTP revision number is 0.
If the revision number of the MST region is not 0, this step is necessary.
NOTE
The change of related MST region configurations (especially change of the VLAN mapping table) causes
the recalculation of spanning trees and the route flapping in a network. Therefore, after an MST region
name, VLAN-to-instance mappings, and an MSTP revision number is configured, activating the MST
region is necessary. You can run the check region-configuration command in the MST region view to check
whether region configurations are correct. After confirming that region configurations are correct, run the
active region-configuration command to activate MST region configurations.
Step 6 Run:
active region-configuration
MST region configurations are activated so that the configured region name, VLAN-to-instance
mappings, and revision number can take effect.
If this step is not done, the preceding configurations cannot take effect.
If you have changed MST region configurations on the switching device after MSTP starts, run
the active region-configuration command to activate the MST region so that the changed
configurations can take effect.
----End
9.2.4 (Optional) Setting a Priority for a Switching Device in an MSTI
The lower the numerical value is, the higher priority a switching device has and the more likely
the switching device will be selected as a root bridge.
Context
In an MSTI, there is only one root bridge and it is the logic center of the MSTI. In root bridge
selection, the switching device with high performance and network hierarchy is generally
selected as a root bridge; however, the priority of such a device may be not that high. Thus setting
a high priority for the switching device is necessary so that the device can function as a root
bridge.
Other devices with low performance and network hierarchy are not fit to be a root bridge.
Therefore, set low priorities for these devices.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
265
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
9 MSTP Configuration
CAUTION
If an S5700 is configured as the root switch or secondary root switch, the priority of the
S5700 cannot be set. If you want to set the priority of the S5700, you must disable the root switch
or secondary root switch.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
stp [ instance instance-id ] priority priority
A priority is set for the switching device in an MSTI.
The default priority value of the switching device is 32768.
If the instance is not designated, a priority is set for the switching device in MSTI0.
NOTE
l To configure a switching device as a primary root bridge, you can run the stp [ instance instance-id ]
root primary command directly. The priority value of this switching device is 0.
l To configure a switching device as a secondary root bridge, run the stp [ instance instance-id ] root
secondary command. The priority value of this switching device is 4096.
In an MSTI, a switching device cannot act as a primary root bridge and a secondary root bridge at the
same time.
----End
9.2.5 (Optional) Setting a Path Cost of a Port in an MSTI
The MSTP path cost determines root port selection in an MSTI. The port with the lowest path
cost to the root bridge is selected as a root port.
Context
A path cost is port-specific, which is used by MSTP as a reference to select a link.
Path costs of a port are an important basis for calculating spanning trees. If you set different path
costs for a port in different MSTIs, you can make VLAN traffic be transmitted along different
physical links and thus carry out VLAN load balancing.
On a network where loops occur, you are recommended to set a relatively large path cost for the
port at a low link rate. MSTP puts the port with the large path cost in the Blocking state and
blocks the link where this port resides.
Procedure
Step 1 Run:
system-view
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
266
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
9 MSTP Configuration
The system view is displayed.
Step 2 Run:
stp pathcost-standard { dot1d-1998 | dot1t | legacy }
A path cost calculation method is configured.
By default, the IEEE 802.1t standard method is used to calculate the default path cost.
All switching devices on a network must use the same path cost calculation method.
Step 3 Run:
interface interface-type interface-number
The Ethernet interface view is displayed.
Step 4 Run:
stp instance instance-id cost cost
A path cost is set for the port in the current MSTI.
l When the Huawei proprietory calculation method is used, cost ranges from 1 to 200000.
l When the IEEE 802.1d standard method is used, cost ranges from 1 to 65535.
l When the IEEE 802.1t standard method is used, cost ranges from 1 to 200000000.
----End
9.2.6 (Optional) Setting a Port Priority in an MSTI
The lower the numerical value, the more likely the port on a switching device becomes a
designated port; the higher the numerical value, the more likely the port is to be blocked.
Context
In spanning tree calculation, priorities of ports on switching devices in MSTIs determine
designated port selection.
If you expect to block a port on a switching device in an MSTI to eliminate loops, set the port
priority value to be larger than the default value. This port will be blocked in designated port
selection.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
interface interface-type interface-number
The Ethernet interface view is displayed.
Step 3 Run:
stp
instance instance-id port priority priority
A port priority is set in an MSTI.
By default, the port priority is 128.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
267
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
9 MSTP Configuration
The value range of the priority is from 0 to 240, with the step 16. That is, the port priority can
be 0, 16, or 32.
----End
9.2.7 Enabling MSTP
After basic MSTP functions are configured on a switching device, enabling the MSTP function
is required so that MSTP can work properly.
Context
After MSTP is enabled on a ring network, MSTP immediately calculates spanning trees on the
network. Configurations on the switching device, such as, the switching device priority and port
priority, will affect spanning tree calculation. Any change of the configurations may cause
network flapping. Therefore, to ensure rapid and stable spanning tree calculation, perform basic
configurations on the switching device and its ports and enable MSTP.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
stp enable
MSTP is enabled on the switching device.
By default, the MSTP function is enabled on a S5700.
----End
9.2.8 Checking the Configuration
After basic MSTP functions are configured, verify that the configurations take effect.
Prerequisite
All configurations of basic MSTP functions are complete.
Procedure
l
Run the display stp [ instance instance-id ][ interface { interface-type interfacenumber } ] [ brief ] command to view spanning-tree status and statistics.
Run the display stp region-configuration command to view configurations of activated
MST regions.
Run the display stp region-configuration [ digest ] command to view the digest
configurations of activated MST regions.
----End
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
268
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
9 MSTP Configuration
9.3 Configuring MSTP Multi-process
After an MSTP device binds its ports to different processes, the MSTP device performs the
MSTP calculation based on processes, and only relevant ports in each process take part in MSTP
calculation.
9.3.1 Establishing the Configuration Task
Before configuring MSTP multi-process, familiarize yourself with the applicable environment,
complete the pre-configuration tasks, and obtain the required data. This will help you complete
the configuration task quickly and accurately.
Applicable Environment
On the networking with both Layer 2 single-access rings and multi-access rings deployed,
switching devices bear both Layer 2 and Layer 3 services. To enable different rings to bear
different services, deploy MSTP multi-process. Spanning trees of different processes are
calculated independently and do not affect each other.
As shown in Figure 9-8, Switches A, B, and C are connected through Layer 2 links, and are all
enabled with MSTP. The CEs on the on rings support only STP/RSTP. Multiple access rings
exist and these rings access the MSTP region through different interfaces on Switches A and B.
Figure 9-8 Networking diagram of MSTP multi-process
SwitchC
PE1
CE
PE2
SwitchB
SwitchA
CE
Ring1
Ring3
Ring2
CE
CE
Instance1:VLAN2~100
Process 1
Instance3:VLAN201~300
Process 3
CE
CE
Instance2:VLAN101~200
Process 2
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
269
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
9 MSTP Configuration
Pre-configuration Tasks
Before configuring MSTP multi-process, complete the following task:
l
Configuring basic MSTP functions
Data Preparation
To configure MSTP multi-process, you need the following data.
No.
Data
IDs of MSTP processes
Priority of a switching device in an MSTI
9.3.2 Creating an MSTP Process
A process ID uniquely identifies an MSTP multi-process. After an MSTP device binds its ports
to different processes, the MSTP device performs the MSTP calculation based on processes, and
only relevant ports in each process take part in MSTP calculation.
Context
Do as follows on the devices connected to access rings:
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
stp process process-id
An MSTP process is created and the MSTP process view is displayed.
Step 3 Run:
stp mode mstp
A working mode is configured for the MSTP process.
The default mode is MSTP.
NOTE
l After a device starts, there is a default MSTP process with the ID 0. MSTP configurations in the system
view and interface view belong to this process. The default working mode of this process is MSTP.
l To add an interface to an MSTP process with the ID of non-zero, run the stp process command and
then the stp binding process command.
----End
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
270
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
9 MSTP Configuration
9.3.3 Adding an Interface to an MSTP Process - Access Links
The links connecting MSTP devices and access rings are called access links. After being added
to MSTP processes, interfaces on the access links can participate in MSTP calculation.
Context
Do as follows on the devices connected to access rings:
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
interface interface-type interface-number
The Ethernet interface view is displayed.
Step 3 Run:
stp binding process process-id
The current interface is added to the MSTP process.
----End
9.3.4 Adding an Interface to an MSTP Process - Share Link
The link shared by multiple access rings are called a share link. The interfaces on the share link
need to participate in MSTP calculation in multiple access rings in different MSTP processes.
After being added to MSTP processes, interfaces on the access links can participate in MSTP
calculation.
Context
Do as follows on the devices connected to access rings:
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
interface interface-type interface-number
The Ethernet interface view is displayed.
The interface specified in this command must be an interface on the share link between the
devices configured with MSTP multi-process but not the interfaces that connect an access ring
and a device.
Step 3 Run:
stp binding process process-id [ to process-id ] link-share
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
271
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
9 MSTP Configuration
The interface is added to multiple MSTP processes to complete MSTP calculation.
NOTE
For a process with share links, you must run the stp enable command globally. For an interface that is
added to the process in link-share mode, you must run the stp enable command in the interface view.
----End
9.3.5 Configuring Priorities and Root Protection in MSTP Multiprocess
You can configure priorities and root protection in MSTP multi-process to protect links over
access rings.
Context
To prevent loops over the access ring after the share links fails, configure priorities and root
protection in MSTP multi-process.
Root protection is configured on the access interface of a device with second highest priority.
l
For detailed configuration of priorities in MSTP multi-process, see 9.2.4 (Optional)
Setting a Priority for a Switching Device in an MSTI.
For detailed configuration of root protection in MSTP multi-process, see 9.5.4 Configuring
Root Protection on an Interface.
NOTE
The MSTP priority of a downstream device must be lower than that of a UPE.
9.3.6 Configuring TC Notification in MSTP Multi-process
After the TC notification function is configured for MSTP multi-process, the current MSTP
process can notify the MSTIs in other specified MSTP processes to refresh MAC address entries
and ARP entries after receiving a TC-BPDU. Nonstop services are ensured.
Context
Do as follows on the devices connected to access rings:
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
stp process process-id
The view of the created MSTP process is displayed.
Step 3 Run:
stp tc-notify process 0
TC notification is enabled in the MSTP process.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
272
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
9 MSTP Configuration
After the stp tc-notify process 0 command is run, the current MSTP process notifies the MSTIs
in MSTP process 0 to update MAC entries and ARP entries after receiving a TC-BPDU. This
prevents services from being interrupted.
----End
9.3.7 Checking the Configuration
After MSTP multi-process is configured, check whether the configurations take effect.
Prerequisite
All configurations of MSTP multi-process are complete.
Procedure
Step 1 Run the display stp [ process process-id ] [ instance instance-id ] [ interface interface-type
interface-number | slot slot-id ] [ brief ] command to view spanning-tree status and statistics.
----End
9.4 Configuring MSTP Parameters on an Interface
MSTP implements RSTP rapid convergence. To achieve rapid convergence, you need to
configure proper MSTP parameters.
9.4.1 Establishing the Configuration Task
Before configuring basic MSTP parameters, familiarize yourself with the applicable
environment, complete the pre-configuration tasks, and obtain the required data. This will help
you complete the configuration task quickly and accurately.
Applicable Environment
In some specific networks, MSTP parameters will affect the speed of network convergence.
Configuring proper MSTP parameters is required.
NOTE
The default parameters also can be used to complete MSTP rapid convergence. Therefore, the configuration
procedures and steps in this command task are all optional.
Pre-configuration Tasks
Before configuring MSTP parameters, complete the following task:
l
Configuring basic MSTP functions
Data Preparation
To configure MSTP parameters, you need the following data.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
273
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
9 MSTP Configuration
No.
Data
Network diameter
Hello time, forwarding delay time, maximum aging time, and timeout period for
waiting for BPDUs from the upstream (3 x hello time x time factor)
Maximum hop count in an MST region
Link type of a port
Whether to Rapid transition mechanism
Whether to transition to the RSTP mode
Maximum number of sent BPDUs
Whether a port needs to be configured as an edge port
Whether auto recovery needs to be configured for an edge port being shut down
10
Whether a port needs to clear statistics of the spanning tree
11
Whether an edge port needs to be configured as a BPDU filter
9.4.2 Configuring System Parameters
MSTP parameters that may affect network convergence include the network diameter, hello
time, and timeout period for waiting for BPDUs from the upstream (3 x hello time x time factor).
Configure proper MSTP parameters to implement rapid network convergence.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 (Optional) Run:
stp process process-id
The MSTP process view is displayed.
NOTE
This step is needed only when you perform configurations in an MSTP process with a non-zero ID. If you
perform configurations in the MSTP process 0, skip is step.
Step 3 Run:
stp bridge-diameter diameter
The network diameter is configured.
By default, the network diameter is 7.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
274
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
9 MSTP Configuration
l RSTP uses a single spanning tree instance on the entire network, which cannot prevent the
performance from deteriorating when the network scale grows. Therefore, the network
diameter cannot be larger than 7.
l It is recommended that you run the stp bridge-diameter diameter command to set the
network diameter. Then, the switching device calculates the optimal Forward Delay period,
Hello time, and Max Age period based on the set network diameter.
Step 4 Run:
stp timer-factor factor
The timeout period for waiting for BPDUs from the upstream of a switching device is set.
By default, the timeout period of a switching device is 9 times as long as the Hello time.
Step 5 (Optional) To set the Forward Delay period, Hello time, and Max Age period, perform the
following operations:
l Run the stp timer forward-delay forward-delay command to set the Forward Delay period
for a switching device.
The default Forward Delay period of a switching device is 1500, in centiseconds.
l Run the stp timer hello hello-time command to set the Hello time for a switching device.
The default Hello time of a switching device is 200, in centiseconds.
l Run the stp timer max-age max-age command to set the Max Age period for a switching
device.
The default Max Age period of a switching device is 2000, in centiseconds.
NOTE
The values of the Hello time, Forward Delay period, and Max Age period must comply with the following
formulas. Otherwise, networking flapping occurs.
l 2 (Forward Delay - 1.0 second) >= Max Age
l Max Age >= 2 (Hello Time + 1.0 second)
Step 6 Run:
stp max-hops hop
The maximum hop count is set for the MST region.
By default, the maximum hop count of the MST region is 20.
Step 7 Run:
stp mcheck
MCheck is enabled.
On a switching device running MSTP, if an interface is connected to a device running STP, the
interface automatically transitions to the STP mode.
Enabling MCheck on the interface is required because the interface may fail to automatically
transition to the MSTP mode in the following situations:
l The switching device running STP is shut down or moved.
l The switching device running STP transitions to the MSTP mode.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
275
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
9 MSTP Configuration
NOTE
If you run the stp mcheck command in the system view, the MCheck operation is performed on all the
interfaces.
----End
9.4.3 Configuring Port Parameters
Port parameters that may affect MSTP topology convergence include the link type and maximum
number of sent BPDUs. Configure proper port parameters to implement rapid topology
convergence.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
interface interface-type interface-number
The Ethernet interface view is displayed.
Step 3 (Optional) Run:
stp point-to-point { auto | force-false | force-true }
The link type is configured for a port.
By default, a port automatically determines whether to connect to a P2P link. The P2P link
supports rapid network convergence.
l If the Ethernet port works in full-duplex mode, the port is connected to a P2P link. In this
case, force-true can be configured to implement rapid network convergence.
l If the Ethernet port works in half-duplex mode, you can configure stp point-to-point forcetrue to forcibly set the link type to P2P to implement rapid network convergence.
Step 4 Run:
stp mcheck
MCheck is enabled.
On a switching device running MSTP, if an interface is connected to a device running STP, the
interface automatically transitions to the STP mode.
Enabling MCheck on the interface is required because the interface may fail to automatically
transition to the MSTP mode in the following situations:
l The switching device running STP is shut down or moved.
l The switching device running STP transitions to the MSTP mode.
Step 5 Run:
stp transmit-limit packet-number
The maximum number of BPDUs sent by a port within each Hello time is set.
By default, the maximum number of BPDUs that a port sends within each Hello time is 147.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
276
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
9 MSTP Configuration
Step 6 (Optional) Run:
stp edged-port enable
The port is configured as an edge port.
If a device port is connected to a terminal, you can run this command to configure the port as
an edge port.
By default, the port is a non-edge port.
Step 7 Run:
quit
Return to the system view.
Step 8 (Optional) Run:
error-down auto-recovery cause cause-item interval interval-value
The auto recovery function on an edge port is configured. That is, enable the port in the errordown state to automatically go Up, and set the delay for the transition from Down to Up.
There is no default value for the recovery time. Therefore, you must specify a delay when
configuring this command.
----End
Follow-up Procedure
When the topology of a spanning tree changes, the forwarding paths to associated VLANs are
changed. Then, ARP entries corresponding to those VLANs on the switching device need to be
updated. MSTP processes ARP entries in either fast or normal mode.
l
In fast mode, ARP entries to be updated are directly deleted.
In normal mode, ARP entries to be updated are rapidly aged.
The remaining lifetime of ARP entries to be updated is set to 0. The switching device rapidly
processes these aged entries. If the number of ARP aging probe attempts is not set to 0,
ARP implements aging probe for these ARP entries.
In either fast or normal mode, MAC entries are directly deleted.
You can run the stp converge { fast | normal } command in the system view to configure the
MSTP convergence mode.
By default, the MSTP convergence is configured as normal.
NOTE
The normal mode is recommended. If the fast mode is adopted, ARP entries will be frequently deleted,
causing the CPU usage on the MPU or LPU to reach 100%. As a result, network flapping frequently occurs.
9.4.4 Checking the Configuration
After MSTP parameters are configured, check whether the configurations take effect.
Prerequisite
The configurations of MSTP parameters are complete.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
277
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
9 MSTP Configuration
Procedure
l
Run the display stp [ instance instance-id ] [ interface { interface-type interfacenumber } ] [ brief ] command to view spanning-tree status and statistics.
----End
9.5 Configuring MSTP Protection Functions
MSTP protection functions are as follows, and you can configure one or more functions as
required.
9.5.1 Establishing the Configuration Task
Before configuring MSTP protection functions, familiarize yourself with the applicable
environment, complete the pre-configuration tasks, and obtain the required data. This will help
you complete the configuration task quickly and accurately.
Applicable Environment
MSTP provides the following protection functions, as listed in Table 9-6.
Table 9-6 MSTP protection
Issue 02 (2011-11-21)
MSTP
Protection
Scenario
Configuration Impact
BPDU
protection
An edge port changes to be a
non-edge port after
receiving a BPDU, which
triggers spanning tree
recalculation. If an attacker
keeps sending bogus BPDUs
to a switching device,
network flapping occurs.
After BPDU protection is enabled on the
switching device, the switching device shuts
down the edge port if the edge port receives
an RST BPDU, and notifies the NMS of the
shutdown event. The attributes of the edge
port are not changed.
TC protection
Generally, after receiving
TC BPDUs (packets for
advertising network
topology changes), a
switching device needs to
delete MAC entries and ARP
entries. Frequent deletion
operations will exhaust CPU
resources.
TC protection is used to suppress TC-BPDUs.
The number of times that TC-BPDUs are
processed by a switching device within a
given time period is configurable. If the
number of TC-BPDUs that the switching
device receives within the given time exceeds
the specified threshold, the switching device
handles TC-BPDUs only for the specified
number of times. Excessive TC-BPDUs are
processed by the switching device as a whole
for once after the timeout period expires. This
protects the switching device from frequently
deleting MAC entries and ARP entries, thus
avoiding over-burden.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
278
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
9 MSTP Configuration
MSTP
Protection
Scenario
Configuration Impact
Root
protection
Due to incorrect
configurations or malicious
attacks on the network, a
root bridge may receive
BPDUs with a higher
priority. Consequently, the
legitimate root bridge is no
longer able to serve as the
root bridge, and the network
topology is illegitimately
changed, triggering
spanning tree recalculation.
This may transfer traffic
from high-speed links to
low-speed links, causing
traffic congestion.
To address this issue, the root protection
function can be configured to protect the root
bridge by preserving the role of the
designated port. With this function, when the
designated port receives RST BPDUs with a
higher priority, the port enters the Discarding
state and does not forward the BPDUs. If the
port does not receive any RST BPDUs with a
higher priority for a certain period (double the
Forward Delay), the port transitions to the
Forwarding state.
Loop
protection
A root port or an alternate
port will age if link
congestion or a one-way link
failure occurs. After the root
port ages, a switching device
may re-select a root port
incorrectly and after the
alternate port ages, the port
enters the Forwarding state.
Loops may occur in such a
situation.
The loop protection function can be used to
prevent such network loops. If the root port
or alternate port cannot receive RST BPDUs
from the upstream switching device, the root
port is blocked and the switching device
notifies the NMS that the port enters the
Discarding state. The blocked port remains in
the Blocked state and no longer forwards
packets. This prevents loops on the network.
The root port restores the Forwarding state
after new RST BPDUs are received.
Share-link
protection
In the scenario where a
switching device is dualhomed to a network, when
the share link of multiple
processes fails, loops may
occur.
Share-link protection can address such a
problem. This function forcibly changes the
working mode of the local switching device
to RSTP. Share-link protection needs to be
used together with root protection to avoid
network loops.
NOTE
l After a device normally starts, there is a default MSTP process with the ID 0. MSTP configurations in
the system view and interface view both belong to this process.
l For more information about MSTP multi-process configuration, see 9.3 Configuring MSTP Multiprocess.
Pre-configuration Tasks
Before configuring MSTP protection functions on a switching device, complete the following
task:
l
Issue 02 (2011-11-21)
Configuring basic MSTP functions
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
279
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
9 MSTP Configuration
NOTE
Configuring an edge port on the switching device before configuring BPDU protection.
Data Preparation
To configure MSTP protection functions on a switching device, you need the following data.
No.
Data
Number of the port on which root protection is to be enabled
Number of the port on which loop protection is to be enabled
9.5.2 Configuring BPDU Protection on a Switching Device
After BPDU protection is enabled on a switching device, the switching device shuts down an
edge port if the edge port receives a BPDU, and notifies the NMS of the shutdown event.
Context
Edge ports are directly connected to user terminals and normally, the edge ports will not receive
BPDUs. Some attackers may send pseudo BPDUs to attach the switching device. If the edge
ports receive the BPDUs, the switching device automatically sets the edge ports as non-edge
ports and triggers new spanning tree calculation. Network flapping then occurs. BPDU
protection can be used to protect switching devices against network attacks.
NOTE
Do as follows on a switching device having an edge port:
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 (Optional) Run:
stp process process-id
The MSTP process view is displayed.
NOTE
This step is needed only when you perform configurations in an MSTP process with a non-zero ID. If you
perform configurations in the MSTP process 0, skip is step.
Step 3 Run:
stp bpdu-protection
BPDU protection is enabled on the switching device.
By default, BPDU protection is not enabled on the switching device.
----End
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
280
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
9 MSTP Configuration
9.5.3 Configuring TC Protection on a Switching Device
After TC protection is enabled, you can set the number of times for an MSTP process to process
TC-BPDUs within a given time. TC protection avoids frequent deletion of MAC address entries
and ARP entries, thereby protecting switching devices.
Context
An attacker may send pseudo TC-BPDUs to attack switching devices. Switching devices receive
a large number of TC BPDUs in a short time and delete entries frequently, which burdens system
processing and degrades network stability.
TC protection is used to suppress TC-BPDUs. The number of times that TC-BPDUs are
processed by a switching device within a given time period is configurable. If the number of
TC-BPDUs that the switching device receives within a given time exceeds the specified
threshold, the switching device handles TC-BPDUs only for the specified number of times.
Excessive TC-BPDUs are processed by the switching device as a whole for once after the timer
(that is, the specified time period) expires. This protects the switching device from frequently
deleting MAC entries and ARP entries, thus avoiding over-burdened.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 (Optional) Run:
stp process process-id
The MSTP process view is displayed.
NOTE
This step is needed only when you perform configurations in an MSTP process with a non-zero ID. If you
perform configurations in the MSTP process 0, skip is step.
Step 3 Run:
stp tc-protection
TC protection is enabled for the MSTP process.
By default, TC protection is enabled on the switching device.
Step 4 Run:
stp tc-protection threshold threshold
The threshold of the number of times the MSTP process handles the received TC-BPDUs and
updates forwarding entries within a given time is set.
NOTE
The value of the given time is consistent with the MSTP Hello time set by using the stp timer hello hellotime command.
----End
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
281
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
9 MSTP Configuration
9.5.4 Configuring Root Protection on an Interface
The root protection function on a switching device protects a root bridge by preserving the role
of a designated port.
Context
Due to incorrect configurations or malicious attacks on the network, a root bridge may receive
BPDUs with a higher priority. Consequently, the legitimate root bridge is no longer able to serve
as the root bridge, and the network topology is illegitimately changed, triggering spanning tree
recalculation. This also may cause the traffic that should be transmitted over high-speed links
to be transmitted over low-speed links, leading to network congestion. The root protection
function on a switching device is used to protect the root bridge by preserving the role of the
designated port.
NOTE
Root protection is configured on a designated port. It takes effect only when being configured on the port
that functions as a designated port on all MSTIs. If root protection is configured on other types of ports, it
does not take effect.
Do as follows on a root bridge in an MST region:
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
interface interface-type interface-number
The Ethernet interface view is displayed.
Step 3 (Optional) Run:
stp binding process process-id
The port is bound to an MSTP process.
NOTE
This step is performed only when the interface needs to be bound to an MSTP process with a non-zero ID.
If the interface belongs to process 0, skip this step.
Step 4 Run:
stp root-protection
Root protection is configured on the switching device.
By default, root protection is disabled.
----End
9.5.5 Configuring Loop Protection on an Interface
The loop protection function suppresses the loops caused by link congestion.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
282
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
9 MSTP Configuration
Context
On a network running MSTP, a switching device maintains the root port status and status of
blocked ports by receiving BPDUs from an upstream switching device. If the switching device
cannot receive BPDUs from the upstream because of link congestion or unidirectional-link
failure, the switching device re-selects a root port. The original root port becomes a designated
port and the original blocked ports change to the Forwarding state. This may cause network
loops. To address such a problem, configure loop protection.
After loop protection is configured, if the root port or alternate port does not receive BPDUs
from the upstream switching device, the root port is blocked and the switching device notifies
the NMS that the port enters the Discarding state. The blocked port remains in the Blocked state
and no longer forwards packets. This prevents loops on the network. The root port restores the
Forwarding state after receiving new BPDUs.
NOTE
An alternate port is a backup port of a root port. If a switching device has an alternate port, you need to
configure loop protection on both the root port and the alternate port.
Do as follows on a root port and an alternate port on a switching device in an MST region:
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
interface interface-type interface-number
The Ethernet interface view is displayed.
Step 3 (Optional) Run:
stp binding process process-id
The port is bound to an MSTP process.
NOTE
This step is performed only when the interface needs to be bound to an MSTP process with a non-zero ID.
If the interface belongs to process 0, skip this step.
Step 4 Run:
stp loop-protection
Loop protection for the root port is configured on the switching device.
By default, loop protection is disabled.
----End
9.5.6 Configuring Share-Link Protection on a Switching Device
The share-link protection function on a switching device helps automatically transition to the
RSTP working mode. It can also be used together with root protection to avoid network loops.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
283
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
9 MSTP Configuration
Context
Share-link protection is used in the scenario where a switching device is dual homed to a network.
When a share link fails, share-link protection forcibly changes the working mode of a local
switching device to RSTP. This function can also be used together with root protection to avoid
network loops.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
stp process process-id
The MSTP process view is displayed.
Step 3 Run:
stp link-share-protection
Share-link protection is enabled.
----End
9.5.7 Checking the Configuration
After MSTP protection functions are configured, check whether the configurations take effect.
Prerequisite
All configurations of MSTP protection functions are complete.
Procedure
l
Run the display stp [ instance instance-id ] [ interface { interface-type interfacenumber } ] [ brief ] command to view spanning-tree status and statistics.
----End
9.6 Configuring MSTP Interoperability Between Huawei
Devices and Non-Huawei Devices
To enable Huawei devices to interwork with non-Huawei devices, configure proper parameters
and functions, including the BPDU format, MSTP protocol packet format, and digest snooping
function, on the Huawei devices running MSTP.
9.6.1 Establishing the Configuration Task
Before configuring MSTP interoperability between Huawei devices and non-Huawei devices,
familiarize yourself with the applicable environment, complete the pre-configuration tasks, and
obtain the data required for the configuration. This will help you complete the configuration task
quickly and accurately.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
284
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
9 MSTP Configuration
Applicable Environment
On an MSTP network, inconsistent protocol packet formats and BPDU keys may lead to a
communication failure. Configuring proper MSTP parameters on Huawei devices ensures
interoperability between Huawei devices and non-Huawei devices.
Pre-configuration Tasks
Before configuring MSTP interoperability between Huawei devices and non-Huawei devices,
complete the following task:
l
Configuring basic MSTP functions
Data Preparation
To configure MSTP interoperability between Huawei devices and non-Huawei devices, you
need the following data.
No.
Data
BPDU format
MSTP protocol packet format
9.6.2 Configuring a Proposal/Agreement Mechanism
To enable Huawei Datacom devices to communicate with non-Huawei devices, configure a
proper rapid transition mechanism on Huawei devices according to the Proposal/Agreement
mechanism on non-Huawei devices.
Context
The rapid transition mechanism is also called the Proposal/Agreement mechanism. Switching
devices currently support the following modes:
l
Enhanced mode: The current interface counts a root port when it computes the
synchronization flag bit.
An upstream device sends a Proposal message to a downstream device, requesting rapid
status transition. After receiving the message, the downstream device sets the port
connected to the upstream device as a root port and blocks all non-edge ports.
The upstream device then sends an Agreement message to the downstream device. After
the downstream device receives the message, the root port transitions to the Forwarding
state.
The downstream device then responds to the Proposal message with an Agreement
message. After receiving the message, the upstream device sets the port connected to
the downstream device as a designated port, and the designated port transitions to the
Forwarding state.
Common mode: The current interface ignores the root port when it computes the
synchronization flag bit.
An upstream device sends a Proposal message to a downstream device, requesting rapid
status transition. After receiving the message, the downstream device sets the port
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
285
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
9 MSTP Configuration
connected to the upstream device as a root port and blocks all non-edge ports. The root
port then transitions to the Forwarding state.
The downstream device responds to the Proposal message with an Agreement message.
After receiving the message, the upstream device sets the port connected to the
downstream device as a designated port. The designated port then transitions to the
Forwarding state.
When Huawei Datacom devices are interworking with non-Huawei devices, select either mode
depending on the Proposal/Agreement mechanism on non-Huawei devices.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
interface interface-type interface-number
The Ethernet interface view is displayed.
Step 3 (Optional) Run:
stp binding process process-id
The interface is bound to an MSTP process.
NOTE
This step binds an interface to an MSTP process with a non-zero ID. If the interface belongs to process 0,
skip this step.
Step 4 Run:
stp no-agreement-check
The common rapid transition mechanism is configured.
By default, the interface uses the enhanced rapid transition mechanism.
----End
9.6.3 Configuring the MSTP Protocol Packet Format on an Interface
MSTP protocol packets can be transmitted in auto, dot1s, or legacy mode. The default mode is
auto.
Context
MSTP protocol packets have two formats: dot1s (IEEE 802.1s standard packets) and legacy
(proprietary protocol packets). The auto mode is introduced to allow an interface to automatically
use the format of MSTP protocol packets sent from the remote interface. In this manner, the two
interfaces use the same MSTP protocol packet format.
Do as follows on a switching device in an MST region:
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
286
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
9 MSTP Configuration
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
interface interface-type interface-number
The Ethernet interface view is displayed.
Step 3 (Optional) Run:
stp binding process process-id
The interface is bound to an MSTP process.
NOTE
This step binds an interface to an MSTP process with a non-zero ID. If the interface belongs to process 0,
skip this step.
Step 4 Run:
stp compliance { auto | dot1s | legacy }
The MSTP protocol packet format is configured on the interface.
The auto mode is used by default.
NOTE
If the format of MSTP packets is set to dot1s on one end and legacy on the other end, the negotiation fails.
----End
9.6.4 Enabling the Digest Snooping Function
When a Huawei device is connected to a non-Huawei device, if the region names, revision
numbers, and VLAN-to-instance mappings configured on the two devices are consistent but the
BPDU keys are different, the two devices cannot communicate. To address this problem, enable
the digest snooping function on the Huawei device.
Context
Do as follows on a switching device in an MST region:
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
interface interface-type interface-number
The Ethernet interface view is displayed.
Step 3 (Optional) Run:
stp binding process process-id
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
287
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
9 MSTP Configuration
The interface is bound to an MSTP process.
NOTE
This step binds an interface to an MSTP process with a non-zero ID. If the interface belongs to process 0,
skip this step.
Step 4 Run:
stp config-digest-snoop
The digest snooping function is enabled.
----End
9.6.5 Checking the Configuration
After MSTP parameters are configured for the interoperability between Huawei devices and
non-Huawei devices, check whether the configurations take effect.
Prerequisite
All the configurations for the interoperability between Huawei devices and non-Huawei devices
are complete.
Procedure
l
Run the display stp [ instance instance-id ] [ interface { interface-type interfacenumber } ] [ brief ] command to view spanning-tree status and statistics.
----End
9.7 Maintaining MSTP
MSTP maintenance includes resetting MSTP statistics.
9.7.1 Clearing MSTP Statistics
You can run the reset commands to reset MSTP statistics to 0.
Context
CAUTION
MSTP statistics cannot be restored after you clear them. Therefore, exercise caution when using
the reset commands.
After you confirm that MSTP statistics need to be cleared, run the following command in the
user view.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
288
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
9 MSTP Configuration
Procedure
Step 1 Run the reset stp [ interface interface-type interface-number ] statistics command to clear
spanning-tree statistics.
----End
9.8 Configuration Examples
This section provides an MSTP configuration example.
9.8.1 Example for Configuring Basic MSTP Functions
Networking Requirements
SwitchA, SwitchB, SwitchC, and SwitchD run MSTP. In this example, MSTP runs on Layer 2
interfaces of the Switches.
Figure 9-9 Networking diagram of basic MSTP configurations
SwitchA
GE0/0/2
GE0/0/2
SwitchB
GE0/0/1
GE0/0/1
GE0/0/3
GE0/0/3
SwitchC
GE0/0/1
SwitchD
GE0/0/2
GE0/0/2
GE0/0/1
Configuration Roadmap
The configuration roadmap is as follows:
1.
Add SwitchA and SwitchC to MST region RG1, and create MSTI1.
2.
Add SwitchB and SwitchD to MST region RG2, and create MSTI1.
3.
Configure SwitchA as the CIST root.
4.
In RG1, configure SwitchA as the CIST regional root and regional root of MSTI1.
Configure the root protection function on GE 0/0/2 and the GE 0/0/1 on SwitchA.
5.
In RG2, configure SwitchB as the CIST regional root and SwitchD as the regional root of
MSTI1.
6.
On SwitchC and SwitchD, connect GE 0/0/1 to a PC and configure GE 0/0/1 as an edge
port. Enable BPDU protection on SwitchC and SwitchD.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
289
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
7.
9 MSTP Configuration
Configure the Switches to calculate the path cost by using the Huawei-proprietary
algorithm.
Data Preparation
To complete the configuration, you need the following data:
l
Region that SwitchA and SwitchC belong to: RG1
Region that SwitchB and SwitchD belong to: RG2
Numbers of the GE interfaces, as shown in Figure 9-9
VLAN IDs: 1-20
Procedure
Step 1 Configure SwitchA.
# Configure the MST region on SwitchA.
<SwitchA> system-view
[SwitchA] stp region-configuration
[SwitchA-mst-region] region-name RG1
[SwitchA-mst-region] instance 1 vlan 1 to 10
# Activate the configuration of the MST region.
[SwitchA-mst-region] active region-configuration
[SwitchA-mst-region] quit
# Set the priority of SwitchA in MSTI0 to 0 to ensure that SwitchA functions as the CIST root.
[SwitchA] stp instance 0 priority 0
# Set the priority of SwitchA in MSTI1 to 1 to ensure that SwitchA functions as the regional
root of MSTI1.
[SwitchA] stp instance 1 priority 0
# Configure SwitchA to use the Huawei-proprietary algorithm to calculate the path cost.
[SwitchA] stp pathcost-standard legacy
# Create VLANs 2 to 20.
[SwitchA] vlan batch 2 to 20
# Add GE 0/0/2 to the VLANs.
[SwitchA] interface GigabitEthernet
[SwitchA-GigabitEthernet0/0/2] port
[SwitchA-GigabitEthernet0/0/2] port
[SwitchA-GigabitEthernet0/0/2] bpdu
[SwitchA-GigabitEthernet0/0/2] quit
0/0/2
link-type trunk
trunk allow-pass vlan 1 to 20
enable
# Add GE 0/0/1 to the VLANs.
[SwitchA] interface GigabitEthernet
[SwitchA-GigabitEthernet0/0/1] port
[SwitchA-GigabitEthernet0/0/1] port
[SwitchA-GigabitEthernet0/0/1] bpdu
[SwitchA-GigabitEthernet0/0/1] quit
0/0/1
link-type trunk
trunk allow-pass vlan 1 to 20
enable
# Enable root protection on the GE 0/0/1.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
290
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
9 MSTP Configuration
[SwitchA] interface GigabitEthernet 0/0/1
[SwitchA-GigabitEthernet0/0/1] stp root-protection
[SwitchA-GigabitEthernet0/0/1] quit
# Enable root protection on the GE 0/0/2.
[SwitchA] interface GigabitEthernet 0/0/2
[SwitchA-GigabitEthernet0/0/2] stp root-protection
[SwitchA-GigabitEthernet0/0/2] quit
# Enable MSTP.
[SwitchA] stp enable
Step 2 Configure SwitchB.
# Configure the MST region on SwitchB.
[SwitchB] stp region-configuration
[SwitchB-mst-region] region-name RG2
[SwitchB-mst-region] instance 1 vlan 1 to 10
# Activate the configuration of the MST region.
[SwitchB-mst-region] active region-configuration
[SwitchB-mst-region] quit
# Set the priority of SwitchB in MSTI0 to 4096 to ensure that SwitchB functions as the CIST
root.
[SwitchB] stp instance 0 priority 4096
# Configure SwitchB to use the Huawei-proprietary algorithm to calculate the path cost.
[SwitchB] stp pathcost-standard legacy
# Create VLANs 2 to 20.
[SwitchB] vlan batch 2 to 20
# Add GE 0/0/1 to the VLANs.
[SwitchB] interface GigabitEthernet
[SwitchB-GigabitEthernet0/0/1] port
[SwitchB-GigabitEthernet0/0/1] port
[SwitchB-GigabitEthernet0/0/1] bpdu
[SwitchB-GigabitEthernet0/0/1] quit
0/0/1
link-type trunk
trunk allow-pass vlan 1 to 20
enable
# Add GE 0/0/2 to the VLANs.
[SwitchB] interface GigabitEthernet
[SwitchB-GigabitEthernet0/0/2] port
[SwitchB-GigabitEthernet0/0/2] port
[SwitchB-GigabitEthernet0/0/2] bpdu
[SwitchB-GigabitEthernet0/0/2] quit
0/0/2
link-type trunk
trunk allow-pass vlan 1 to 20
enable
# Enable MSTP.
[SwitchB] stp enable
Step 3 Configure SwitchC.
# Configure the MST region on SwitchC.
[SwitchC] stp region-configuration
[SwitchC-mst-region] region-name RG1
[SwitchC-mst-region] instance 1 vlan 1 to 10
# Activate the configuration of the MST region.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
291
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
9 MSTP Configuration
[SwitchC-mst-region] active region-configuration
[SwitchC-mst-region] quit
# Configure SwitchC to use the Huawei-proprietary algorithm to calculate the path cost.
[SwitchC] stp pathcost-standard legacy
# Enable BPDU protection.
[SwitchC] stp bpdu-protection
# Create VLANs 2 to 20.
[SwitchC] vlan batch 2 to 20
# Add GE 0/0/2 to the VLANs.
[SwitchC] interface GigabitEthernet
[SwitchC-GigabitEthernet0/0/2] port
[SwitchC-GigabitEthernet0/0/2] port
[SwitchC-GigabitEthernet0/0/2] bpdu
[SwitchC-GigabitEthernet0/0/2] quit
0/0/2
link-type trunk
trunk allow-pass vlan 1 to 20
enable
# Add GE 0/0/3 to the VLANs.
[SwitchC] interface GigabitEthernet
[SwitchC-GigabitEthernet0/0/3] port
[SwitchC-GigabitEthernet0/0/3] port
[SwitchC-GigabitEthernet0/0/3] bpdu
[SwitchC-GigabitEthernet0/0/3] quit
0/0/3
link-type trunk
trunk allow-pass vlan 1 to 20
enable
# Configure GE 0/0/1 as an edge port.
[SwitchC] interface GigabitEthernet 0/0/1
[SwitchC-GigabitEthernet0/0/1] stp edged-port enable
[SwitchC-GigabitEthernet0/0/1] port hybrid pvid vlan 20
[SwitchC-GigabitEthernet0/0/1] port hybrid untagged vlan 20
[SwitchC-GigabitEthernet0/0/1] quit
# Enable MSTP.
[SwitchC] stp enable
Step 4 Configure SwitchD.
# Configure the MST region on SwitchD.
[SwitchD] stp region-configuration
[SwitchD-mst-region] region-name RG2
[SwitchD-mst-region] instance 1 vlan 1 to 10
# Activate the configuration of the MST region.
[SwitchD-mst-region] active region-configuration
[SwitchD-mst-region] quit
# Set the priority of SwitchD in MSTI1 to 0 to ensure that SwitchD functions as the regional
root of MSTI1.
[SwitchD] stp instance 1 priority 0
# Configure SwitchD to use the Huawei-proprietary algorithm to calculate the path cost.
[SwitchD] stp pathcost-standard legacy
# Enable BPDU protection.
[SwitchD] stp bpdu-protection
# Create VLANs 2 to 20.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
292
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
9 MSTP Configuration
[SwitchD] vlan batch 2 to 20
# Add GE 0/0/2 to the VLANs.
[SwitchD] interface GigabitEthernet
[SwitchD-GigabitEthernet0/0/2] port
[SwitchD-GigabitEthernet0/0/2] port
[SwitchD-GigabitEthernet0/0/2] bpdu
[SwitchD-GigabitEthernet0/0/2] quit
0/0/2
link-type trunk
trunk allow-pass vlan 1 to 20
enable
# Add GE 0/0/3 to the VLANs.
[SwitchD] interface GigabitEthernet
[SwitchD-GigabitEthernet0/0/3] port
[SwitchD-GigabitEthernet0/0/3] port
[SwitchD-GigabitEthernet0/0/3] bpdu
[SwitchD-GigabitEthernet0/0/3] quit
0/0/3
link-type trunk
trunk allow-pass vlan 1 to 20
enable
# Configure GE 0/0/1 as an edge port.
[SwitchD] interface GigabitEthernet 0/0/1
[SwitchD-GigabitEthernet0/0/1] stp edged-port enable
[SwitchD-GigabitEthernet0/0/1] port hybrid pvid vlan 10
[SwitchD-GigabitEthernet0/0/1] port hybrid untagged vlan 10
[SwitchD-GigabitEthernet0/0/1] quit
# Enable MSTP.
[SwitchD] stp enable
Step 5 Verify the configuration.
After the preceding configurations are complete and the network topology becomes stable,
perform the following operations to verify the configuration.
# Run the display stp brief command on SwitchA to view the status and protection type on the
interfaces. The displayed information is as follows:
<SwitchA> display stp brief
MSTID
Port
0
GigabitEthernet0/0/1
0
GigabitEthernet0/0/2
1
GigabitEthernet0/0/1
1
GigabitEthernet0/0/2
Role
DESI
DESI
DESI
DESI
STP State
FORWARDING
FORWARDING
FORWARDING
FORWARDING
Protection
ROOT
ROOT
ROOT
ROOT
The priority of SwitchA is the highest in the CIST; therefore, SwitchA is elected as the CIST
root and regional root of RG1. GE 0/0/2 and GE 0/0/1 of SwitchA are designated ports in the
CIST.
The priority of SwitchA in MSTI1 is the highest in RG1; therefore, SwitchA is elected as the
regional root of SwitchA. GE 0/0/2 and GE 0/0/1 of SwitchA are designated ports in MSTI1.
# Run the display stp interface brief commands on SwitchC. The displayed information is as
follows:
<SwitchC> display stp interface GigabitEthernet 0/0/3 brief
MSTID
Port
Role STP State
Protection
0
GigabitEthernet0/0/3
ROOT FORWARDING
NONE
1
GigabitEthernet0/0/3
ROOT FORWARDING
NONE
<SwitchC> display stp interface GigabitEthernet 0/0/2 brief
MSTID
Port
Role STP State
Protection
0
GigabitEthernet0/0/2
DESI FORWARDING
NONE
1
GigabitEthernet0/0/2
DESI FORWARDING
NONE
GE 0/0/3 of SwitchC is the root port in the CIST and MSTI1. GE 0/0/2 of SwitchC is a designated
port in the CIST and MSTI1.
# Run the display stp brief command on SwitchB. The displayed information is as follows:
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
293
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
<SwitchB> display stp brief
MSTID
Port
0
GigabitEthernet0/0/1
0
GigabitEthernet0/0/2
1
GigabitEthernet0/0/1
1
GigabitEthernet0/0/2
9 MSTP Configuration
Role
DESI
ROOT
ROOT
MAST
STP State
FORWARDING
FORWARDING
FORWARDING
FORWARDING
Protection
NONE
NONE
NONE
NONE
The priority of SwitchB in the CIST is lower than that of SwitchA; therefore, GE 0/0/2 of
SwitchB functions as the root port in the CIST. SwitchA and SwitchB belong to different regions;
therefore, GE 0/0/2 of SwitchB functions as the master port in MSTI1. In MSTI1, the priority
of SwitchB is lower than that of SwitchD; therefore, GE 0/0/1 of SwitchB functions as the root
port. The priority of SwitchB in the CIST is higher than that of SwitchB; therefore, GE 0/0/1 of
SwitchB functions as the designated port in the CIST.
# Run the display stp interface brief commands on SwitchD. The displayed information is as
follows:
<SwitchD> display stp interface GigabitEthernet 0/0/3 brief
MSTID
Port
Role STP State
Protection
0
GigabitEthernet0/0/3
ROOT FORWARDING
NONE
1
GigabitEthernet0/0/3
DESI FORWARDING
NONE
<SwitchD> display stp interface GigabitEthernet 0/0/2 brief
MSTID
Port
Role STP State
Protection
0
GigabitEthernet0/0/2
ALTE DISCARDING
NONE
1
GigabitEthernet0/0/2
ALTE DISCARDING
NONE
On SwitchD, GE 0/0/2 functions as the alternate port in the CIST. SwitchD and SwitchC are in
different regions; therefore, GE 0/0/2 of SwitchD also functions as the alternate port in MSTI1.
GE 0/0/3 of SwitchD is the root port in the CIST. The priority of SwitchD is higher than that of
SwitchB in MSTI1; therefore, GE 0/0/3 also functions as the designated port in MSTI1.
----End
Configuration Files
l
Configuration file of SwitchA
#
sysname SwitchA
#
vlan batch 2 to 20
#
stp instance 0 priority 0
stp instance 1 priority 0
stp pathcost-standard legacy
stp region-configuration
region-name RG1
instance 1 vlan 1 to 10
active region-configuration
#
interface GigabitEthernet0/0/1
port link-type trunk
port trunk allow-pass vlan 2 to 20
stp root-protection
#
interface GigabitEthernet0/0/2
port link-type trunk
port trunk allow-pass vlan 2 to 20
stp root-protection
#
return
Configuration file of SwitchB
#
sysname SwitchB
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
294
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
9 MSTP Configuration
#
vlan batch 2 to 20
#
stp instance 0 priority 4096
stp pathcost-standard legacy
stp region-configuration
region-name RG2
instance 1 vlan 1 to 10
active region-configuration
#
interface GigabitEthernet0/0/1
port link-type trunk
port trunk allow-pass vlan 2 to 20
#
interface GigabitEthernet0/0/2
port link-type trunk
port trunk allow-pass vlan 2 to 20
#
return
Configuration file of SwitchC
#
sysname SwitchC
#
vlan batch 2 to 20
#
stp bpdu-protection
stp pathcost-standard legacy
stp region-configuration
region-name RG1
instance 1 vlan 1 to 10
active region-configuration
#
interface GigabitEthernet0/0/1
port hybrid pvid vlan 20
port hybrid untagged vlan 20
stp edged-port enable
#
interface GigabitEthernet0/0/2
port link-type trunk
port trunk allow-pass vlan 2 to 20
#
interface GigabitEthernet0/0/3
port link-type trunk
port trunk allow-pass vlan 2 to 20
#
return
Configuration file of SwitchD
#
sysname SwitchD
#
vlan batch 2 to 20
#
stp instance 1 priority 0
stp bpdu-protection
stp pathcost-standard legacy
stp region-configuration
region-name RG2
instance 1 vlan 1 to 10
active region-configuration
#
interface GigabitEthernet0/0/1
port hybrid pvid vlan 10
port hybrid untagged vlan 10
stp edged-port enable
#
interface GigabitEthernet0/0/2
port link-type trunk
port trunk allow-pass vlan 2 to 20
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
295
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
9 MSTP Configuration
#
interface GigabitEthernet0/0/3
port link-type trunk
port trunk allow-pass vlan 2 to 20
#
Return
9.8.2 Example for Configuring MSTP Multi-Process for Layer 2
Single-Access Rings and Layer 2 Multi-Access Rings
MSTP multi-process enables different Layer 2 access rings to transmit different services.
Networking Requirements
On the network with both Layer 2 single-access rings and multi-access rings deployed, switching
devices transmit both Layer 2 and Layer 3 services. To enable different rings to transmit different
services, configure MSTP multi-process. Spanning trees of different processes are calculated
independently.
As shown in Figure 9-10, both Layer 2 single-access rings and dual-access rings are deployed
and switches A and B carry both Layer 2 and Layer 3 services. Switches A and B connected to
dual-access rings are also connected to a single-access ring.
NOTE
In the ring where MSTP multi-process is configured, you are advised not to block the interface directly
connected to the root protection-enabled designated port.
Figure 9-10 MSTP multi-process for Layer 2 single-access rings and multi-access rings
Network
SwitchC
GE0/0/5
GE0/0/5
Region name:RG1
PE1
CE
GE0/0/4
GE0/0/3
SwitchA
GE0/0/1
GE0/0/2
SwitchB
GE0/0/1
PE2
GE0/0/4
GE0/0/2
CE
GE0/0/3
CE
CE
Instance1:VLAN2~100
Process 1
Instance3:VLAN201~300
CE
CE
Process 3
Instance2:VLAN101~200
Process 2
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
296
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
9 MSTP Configuration
Configuration Roadmap
The configuration roadmap is as follows:
1.
Configure basic MSTP functions, add devices to MST regions, and create MSTIs.
NOTE
l Each ring can belong to only one region.
l Each CE can join only one ring.
2.
3.
Configure multiple MSTP processes:
a.
Create multiple MSTP processes and add interfaces to these processes.
b.
Configure a shared link.
Configure MSTP protection functions:
l Configure priorities of MSTP processes and enable root protection.
l Configure shared link protection.
4.
Configure the Layer 2 forwarding function on devices.
Data Preparation
To complete the configuration, you need the following data:
l
Name of an MST region and names of MSTIs
VLAN IDs
IDs of MSTP processes
Procedure
Step 1 Configure basic MSTP functions, add devices to an MST region, and create MSTIs.
1.
Configure MST regions and create MSTIs.
# Configure an MST region and create MSTIs on SwitchA.
<Quidway> system-view
[Quidway] sysname SwitchA
[SwitchA] stp region-configuration
[SwitchA-mst-region] region-name RG1
[SwitchA-mst-region] instance 1 vlan 2 to 100
[SwitchA-mst-region] instance 2 vlan 101 to 200
[SwitchA-mst-region] instance 3 vlan 201 to 300
[SwitchA-mst-region] active region-configuration
[SwitchA-mst-region] quit
# Configure an MST region and create MSTIs on SwitchB.
<Quidway> system-view
[Quidway] sysname SwitchB
[SwitchB] stp region-configuration
[SwitchB-mst-region] region-name RG1
[SwitchB-mst-region] instance 1 vlan 2 to 100
[SwitchB-mst-region] instance 2 vlan 101 to 200
[SwitchB-mst-region] instance 3 vlan 201 to 300
[SwitchB-mst-region] active region-configuration
[SwitchB-mst-region] quit
2.
Enable MSTP.
# Configure SwitchA.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
297
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
9 MSTP Configuration
[SwitchA] stp enable
# Configure SwitchB.
[SwitchB] stp enable
Step 2 Configure multiple MSTP processes.
1.
Create multiple MSTP processes and add interfaces to these processes.
# Create MSTP processes 1 and 2 on SwitchA.
[SwitchA] stp process 1
[SwitchA-mst-process-1] quit
[SwitchA] stp process 2
[SwitchA-mst-process-2] quit
# Create MSTP processes 2 and 3 on SwitchB.
[SwitchB] stp process 2
[SwitchB-mst-process-2] quit
[SwitchB] stp process 3
[SwitchB-mst-process-3] quit
# Add GE 0/0/3 and GE 0/0/4 on SwitchA to MSTP process 1 and GE 0/0/2 to MSTP
process 2.
[SwitchA] interface gigabitethernet 0/0/4
[SwitchA-GigabitEthernet0/0/4] bpdu enable
[SwitchA-GigabitEthernet0/0/4] stp binding process 1
[SwitchA-GigabitEthernet0/0/4] quit
[SwitchA] interface gigabitethernet 0/0/3
[SwitchA-GigabitEthernet0/0/3] bpdu enable
[SwitchA-GigabitEthernet0/0/3] stp binding process 1
[SwitchA-GigabitEthernet0/0/3] quit
[SwitchA] interface gigabitethernet 0/0/2
[SwitchA-GigabitEthernet0/0/2] bpdu enable
[SwitchA-GigabitEthernet0/0/2] stp binding process 2
[SwitchA-GigabitEthernet0/0/2] quit
# Add GE 0/0/3 and GE 0/0/4 on SwitchB to MSTP process 3 and GE 0/0/2 to MSTP
process 2.
[SwitchB] interface gigabitethernet 0/0/4
[SwitchB-GigabitEthernet0/0/4] bpdu enable
[SwitchB-GigabitEthernet0/0/4] stp binding process 3
[SwitchB-GigabitEthernet0/0/4] quit
[SwitchB] interface gigabitethernet 0/0/3
[SwitchB-GigabitEthernet0/0/3] bpdu enable
[SwitchB-GigabitEthernet0/0/3] stp binding process 3
[SwitchB-GigabitEthernet0/0/3] quit
[SwitchB] interface gigabitethernet 0/0/2
[SwitchB-GigabitEthernet0/0/2] bpdu enable
[SwitchB-GigabitEthernet0/0/2] stp binding process 2
[SwitchB-GigabitEthernet0/0/2] quit
2.
Configure a shared link.
# Configure SwitchA.
[SwitchA] interface gigabitethernet0/0/1
[SwitchA-GigabitEthernet0/0/1] bpdu enable
[SwitchA-GigabitEthernet0/0/1] stp binding process 2 link-share
[SwitchA-GigabitEthernet0/0/1] quit
# Configure SwitchB.
[SwitchB] interface gigabitethernet0/0/1
[SwitchB-GigabitEthernet0/0/1] bpdu enable
[SwitchB-GigabitEthernet0/0/1] stp binding process 2 link-share
[SwitchB-GigabitEthernet0/0/1] quit
3.
Enable the MSTP function in MSTP multi-process.
# Configure SwitchA.
[SwitchA] stp process 1
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
298
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
[SwitchA-stp-process-1]
[SwitchA-stp-process-1]
[SwitchA] stp process 2
[SwitchA-stp-process-2]
[SwitchA-stp-process-2]
9 MSTP Configuration
stp enable
quit
stp enable
quit
# Configure SwitchB.
[SwitchB] stp process 3
[SwitchB-stp-process-3]
[SwitchB-stp-process-3]
[SwitchB] stp process 2
[SwitchB-stp-process-2]
[SwitchB-stp-process-2]
stp enable
quit
stp enable
quit
Step 3 Configure MSTP protection functions.
l Configure priorities of MSTP processes and enable root protection.
# Configure SwitchA.
[SwitchA] stp process 1
[SwitchA-stp-process-1] stp instance 0 root primary
[SwitchA-stp-process-1] stp instance 1 root primary
[SwitchA-stp-process-1] quit
[SwitchA] stp process 2
[SwitchA-stp-process-2] stp instance 0 root primary
[SwitchA-stp-process-2] stp instance 2 root primary
[SwitchA-stp-process-2] quit
[SwitchA] interface gigabitethernet 0/0/2
[SwitchA-GigabitEthernet0/0/2] stp root-protection
[SwitchA-GigabitEthernet0/0/2] quit
# Configure SwitchB.
[SwitchB] stp process 3
[SwitchB-stp-process-3] stp instance 0 root primary
[SwitchB-stp-process-3] stp instance 3 root primary
[SwitchB-stp-process-3] quit
[SwitchB] stp process 2
[SwitchB-stp-process-2] stp instance 0 root secondary
[SwitchB-stp-process-2] stp instance 2 root secondary
[SwitchB-stp-process-2] quit
[SwitchB] interface gigabitethernet 0/0/2
[SwitchB-GigabitEthernet0/0/2] stp root-protection
[SwitchB-GigabitEthernet0/0/2] quit
NOTE
l In each ring, the priority of the MSTP process on the downstream CE must be lower than the priority
of the MSTP process on the switching device.
l For switches A and B on the dual-access ring, you are recommended to configure them as the
primary root bridges of different MSTIs.
l Configure shared link protection.
# Configure SwitchA.
[SwitchA] stp process 2
[SwitchA-stp-process-2] stp link-share-protection
[SwitchA-stp-process-2] quit
# Configure SwitchB.
[SwitchB] stp process 2
[SwitchB-stp-process-2] stp link-share-protection
[SwitchB-stp-process-2] quit
Step 4 Create VLANs and add interfaces to VLANs.
# Create VLANs 2 to 200 on SwitchA. Add GE 0/0/3 and GE 0/0/4 to VLANs 2 to 100, and add
GE 0/0/1 and GE 0/0/2 to VLANs 101 to 200.
[SwitchA] vlan batch 2 to 200
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
299
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
[SwitchA] interface gigabitethernet
[SwitchA-GigabitEthernet0/0/3] port
[SwitchA-GigabitEthernet0/0/3] port
[SwitchA-GigabitEthernet0/0/3] quit
[SwitchA] interface gigabitethernet
[SwitchA-GigabitEthernet0/0/4] port
[SwitchA-GigabitEthernet0/0/4] port
[SwitchA-GigabitEthernet0/0/4] quit
[SwitchA] interface gigabitethernet
[SwitchA-GigabitEthernet0/0/1] port
[SwitchA-GigabitEthernet0/0/1] port
[SwitchA-GigabitEthernet0/0/1] quit
[SwitchA] interface gigabitethernet
[SwitchA-GigabitEthernet0/0/2] port
[SwitchA-GigabitEthernet0/0/2] port
[SwitchA-GigabitEthernet0/0/2] quit
9 MSTP Configuration
0/0/3
link-type trunk
trunk allow-pass vlan 2 to 100
0/0/4
link-type trunk
trunk allow-pass vlan 2 to 100
0/0/1
link-type trunk
trunk allow-pass vlan 101 to 200
0/0/2
link-type trunk
trunk allow-pass vlan 101 to 200
# Create VLANs 101 to 300 on SwitchB. Add GE 0/0/3 and GE 0/0/4 to VLANs 201 to 300,
and add GE 0/0/1 and GE 0/0/2 to VLANs 101 to 200.
[SwitchB] vlan batch 101 to 300
[SwitchB] interface gigabitethernet
[SwitchB-GigabitEthernet0/0/3] port
[SwitchB-GigabitEthernet0/0/3] port
[SwitchB-GigabitEthernet0/0/3] quit
[SwitchB] interface gigabitethernet
[SwitchB-GigabitEthernet0/0/4] port
[SwitchB-GigabitEthernet0/0/4] port
[SwitchB-GigabitEthernet0/0/4] quit
[SwitchB] interface gigabitethernet
[SwitchB-GigabitEthernet0/0/1] port
[SwitchB-GigabitEthernet0/0/1] port
[SwitchB-GigabitEthernet0/0/1] quit
[SwitchB] interface gigabitethernet
[SwitchB-GigabitEthernet0/0/2] port
[SwitchB-GigabitEthernet0/0/2] port
[SwitchB-GigabitEthernet0/0/2] quit
0/0/3
link-type trunk
trunk allow-pass vlan 201 to 300
0/0/4
link-type trunk
trunk allow-pass vlan 201 to 300
0/0/1
link-type trunk
trunk allow-pass vlan 101 to 200
0/0/2
link-type trunk
trunk allow-pass vlan 101 to 200
Step 5 Verify the configuration.
l Run the display stp interface brief command on SwitchA.
# GE 0/0/4 is a designated port in the CIST of MSTP process 1 and in MSTI 1.
[SwitchA] display stp process 1 interface GiabitEthernet 0/0/4 brief
MSTID
Port
Role STP State
Protection
0
GigabitEthernet0/0/4
DESI FORWARDING
NONE
1
GigabitEthernet0/0/4
DESI FORWARDING
NONE
# GE 0/0/2 is a designated port in the CIST of MSTP process 2 and in MSTI 2.
[SwitchA] display stp process 2 interface giabitethernet 0/0/2 brief
MSTID
Port
Role STP State
Protection
0
GigabitEthernet0/0/2
DESI FORWARDING
ROOT
2
GigabitEthernet0/0/2
DESI FORWARDING
ROOT
l Run the display stp interface brief command on SwitchB.
# GE 0/0/4 is a designated port in the CIST of MSTP process 3 and in MSTI 3.
[SwitchB] display stp process 3 interface giabitethernet 0/0/4 brief
MSTID
Port
Role STP State
Protection
0
GigabitEthernet0/0/4
DESI FORWARDING
NONE
3
GigabitEthernet0/0/4
DESI FORWARDING
NONE
# GE 0/0/2 is a designated port in the CIST of MSTP process 2 and in MSTI 2.
[SwitchB] display stp process 2 interface giabitethernet 0/0/2 brief
MSTID
Port
Role STP State
Protection
0
GigabitEthernet0/0/2
DESI FORWARDING
ROOT
2
GigabitEthernet0/0/2
DESI FORWARDING
ROOT
----End
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
300
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
9 MSTP Configuration
Configuration Files
Only the MSTP-related configuration files are provided.
l
Configuration file of SwitchA
#
sysname
SwitchA
#
vlan batch 2 to
300
#
stp regionconfiguration
region-name
RG1
instance 1 vlan 2 to
100
instance 2 vlan 101 to
200
instance 3 vlan 201 to
300
active regionconfiguration
#
stp process
1
stp instance 0 root
primary
stp instance 1 root
primary
stp
enable
stp process
2
stp instance 0 root
primary
stp instance 2 root
primary
stp link-shareprotection
stp
enable
#
interface
GigabitEthernet0/0/1
port link-type trunk
port trunk allow-pass vlan 101 to
200
stp binding process 2 link-share
#
interface
GigabitEthernet0/0/2
port link-type trunk
port trunk allow-pass vlan 101 to
200
stp binding process
2
stp rootprotection
#
interface GigabitEthernet0/0/3
port link-type trunk
port trunk allow-pass vlan 2 to
100
stp binding process
1
#
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
301
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
9 MSTP Configuration
interface GigabitEthernet0/0/4
port link-type trunk
port trunk allow-pass vlan 2 to
100
stp binding process 1
#
return
Configuration file of SwitchB
#
sysname
SwitchB
#
vlan batch 2 to
300
#
stp regionconfiguration
region-name
RG1
instance 1 vlan 2 to
100
instance 2 vlan 101 to
200
instance 3 vlan 201 to
300
active regionconfiguration
#
stp process
2
stp instance 0 root
secondary
stp instance 2 root
secondary
stp link-shareprotection
stp
enable
stp process
3
stp instance 0 root
primary
stp instance 3 root
primary
stp
enable
#
interface GigabitEthernet0/0/1
port link-type trunk
port trunk allow-pass vlan 101 to
200
stp binding process 2 linkshare
#
interface GigabitEthernet0/0/2
port link-type trunk
port trunk allow-pass vlan 101 to
200
stp binding process
2
stp rootprotection
#
interface GigabitEthernet0/0/3
port link-type trunk
port trunk allow-pass vlan 201 to
300
stp binding process
3
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
302
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
9 MSTP Configuration
#
interface GigabitEthernet0/0/4
port link-type trunk
port trunk allow-pass vlan 201 to
300
stp binding process
3
#
return
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
303
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
10
SEP Configuration
About This Chapter
As a link layer protocol dedicated to Ethernet rings, SEP blocks redundant links on a network
to prevent logical loops.
10.1 SEP Overview
The Smart Ethernet Protection (SEP) protocol is a dedicated link layer protocol for use on
Ethernet rings. It boasts the high convergence speed, supports diverse topologies, and is able to
display the network topology on any device.
10.2 Configuring Basic SEP Functions
When there is no faulty link on a ring network running SEP, SEP can eliminate loops on the
Ethernet. When a link fault occurs on a ring network running SEP, SEP can immediately restore
the communication links between the nodes.
10.3 Specifying an Interface to Block
By default, the blocked interface is one of the last two interfaces that complete neighbor
negotiation. Sometimes, the negotiated blocked interface, however, may not be the expected
one. An interface can be selected to block as required.
10.4 Configuring SEP Multi-Instance
SEP multi-instance allows two SEP segments to be configured on a physical ring network. After
different protected instances are configured for the SEP segments and VLANs are mapped to
specified protected instances, load balancing and link backup can be implemented for service
traffic.
10.5 Configuring the Topology Change Notification Function
The function of advertising topology changes is configured on the device connecting a lowerlevel network to an upper-level network. With this function, the device can notify the remote
device of topology changes of the lower-level and upper-level networks. After being notified of
these topology changes, all the devices on the network where the remote device resides delete
associated MAC addresses and ARP entry in time and relearn the MAC address of the remote
device. This ensures nonstop traffic forwarding.
10.6 Maintaining SEP
This section describes the commands for maintaining SEP, including the commands for clearing
SEP statistics.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
304
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
10.7 Configuration Examples
This section describes the networking requirements, configuration roadmap, and data
preparation for a typical SEP application and provides the configuration examples.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
305
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
10.1 SEP Overview
The Smart Ethernet Protection (SEP) protocol is a dedicated link layer protocol for use on
Ethernet rings. It boasts the high convergence speed, supports diverse topologies, and is able to
display the network topology on any device.
10.1.1 SEP Overview
SEP supports open-ring, closed-ring, single-ring, and multi-ring topologies and meets the
requirements of various topologies for redundant protection.
Introduction
Generally, redundant links are used on an Ethernet switching network to provide link backup
and enhance network reliability. The use of redundant links, however, may produce loops,
causing broadcast storms and rendering the MAC address table unstable. As a result, the
communication quality deteriorates, and communication services may even be interrupted.
To solve the loop problem, Huawei datacom devices support the ring network protocols shown
in Table 10-1.
Table 10-1 Ring Network Protocol
Issue 02 (2011-11-21)
Ring
Network
Protocol
Advantage
Disadvantage
Deployment Scenario
STP/
RSTP/
MSTP
The Spanning Tree
Protocol (STP), Rapid
Spanning Tree Protocol
(RSTP), and MultiSpanning Tree Protocol
(MSTP) are standard
protocols for breaking
loops on Ethernet
networks. They are
mature and widely
applied. Huawei
devices running one of
them can communicate
with non-Huawei
devices.
The network
convergence time
is at the second
level, which
cannot meet the
requirements of
some real-time
services. The
convergence time
is affected by the
network topology.
They are applicable to Layer 2
networks that have a low
requirement on convergence
time.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
306
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
Issue 02 (2011-11-21)
10 SEP Configuration
Ring
Network
Protocol
Advantage
Disadvantage
Deployment Scenario
RRPP
The Rapid Ring
Protection Protocol
(RRPP) is a private
protocol of Huawei. It
features short
convergence time (less
than 50 ms) and
supports load balancing
for different types of
traffic.
l A Huawei
device running
RRPP cannot
communicate
with any nonHuawei
device.
It is applicable to single rings,
tangent rings, and intersecting
rings that have a high
requirement on the
convergence time.
l RRPP has a
high
requirement on
network
topologies.
Logical
topologies
need to be
configured for
a physical
topology, and
primary rings
and sub-rings
need to be
defined for
these logical
topologies.
Therefore,
RRPP is not
applicable to
complex
networks.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
307
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
Ring
Network
Protocol
Advantage
Disadvantage
Deployment Scenario
SEP
l SEP is a private
protocol of Huawei.
It boasts short
convergence time
(less than 50 ms).
Huawei devices
running SEP can
communicate with
non-huawei devices
running other types
of ring protocols.
l The devices on
a SEP-enabled
network must
be Huawei
datacom
devices.
It is applicable to Layer 2
networks that have a high
requirement on convergence
time.
l SEP supports
various types of
networking modes.
For example, a
network running
SEP can
communicate with a
network running
STP, RSTP, MSTP,
or RRPP. SEP
supports all
topologies and the
display of network
topologies.
l On a SEP
network, after
network
convergence, a
specified
interface is
blocked to
prevent data
traffic from
passing
through the
interface, even
if the link
where the
interface
resides is a
direct link.
The blocked
interface, therefore,
can be quickly
located. When a
fault occurs, SEP
can quickly locate
the fault, improving
network
maintainability.
l SEP supports
various policies for
specifying an
interface to block.
This allows the
implementation of
traffic load
balancing.
Definitions
The SEP protocol is a dedicated link layer protocol for use on Ethernet ring networks. A SEP
segment is the basic unit of the protocol. A SEP segment is composed of multiple interconnected
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
308
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
Layer 2 switching devices that are configured with the same SEP segment ID and control VLAN
ID.
Only two interfaces on a Layer 2 switching device can be added to the same SEP segment. In a
SEP segment, loops can be prevented by starting a protection mechanism to selectively block
certain interfaces and eliminate Ethernet redundant links. When a fault occurs on a ring network,
a device running SEP can quickly unblock the blocked interface to perform link switching. This
maintains normal communication between nodes on the ring network.
Figure 10-1 shows a typical SEP application. CE1 is connected to NPEs through a closed-ring
formed by switches. A VRRP backup group is deployed on the NPEs. Initially, the status of
NPE1 is master and the status of NPE2 is backup. When the link between NPE1 and LSW5 or
a node on the link becomes faulty (it is assumed that the link between LSW1 and LSW5 becomes
faulty), the following situations occur:
l
If SEP is not deployed on the closed-ring, CE1 still forwards traffic along the original path,
causing traffic interruption.
If SEP is deployed on the closed-ring, the blocked interface on LSW5 becomes unblocked
and enters the forwarding state. In addition, it sends Link Status Advertisements (LSAs)
to instruct other nodes on the SEP segment to refresh their LSA databases. CE1 sends traffic
along the backup link LSW5->LSW2->LSW4->LSW3->NPE1. This ensures proper traffic
transmission.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
309
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
Figure 10-1 Schematic diagram for SEP
Access
Aggregation
LSW1
CE1
LSW3
IP/MPLS
Core
LSW5
LSW4
Backup
a,SEP is not deployed on the closed-ring
Aggregation
Core
Access
LSW1
LSW3
Master
SEP
NPE1
Segment VRRP+peer BFD
NPE2
IP/MPLS
Core
LSW5
LSW2
Access
LSW4
Backup
Aggregation
LSW1
SEP
Segment
CE1
Master
NPE1
VRRP+peer BFD
NPE2
LSW2
CE1
Core
Core
LSW3
Master
NPE1
VRRP+peer BFD
NPE2
IP/MPLS
Core
LSW5
LSW2
LSW4
Backup
b,SEP is deployed on the closed-ring
Primary Edge Node
Secondary Edge Node
Block Port
Basic Concepts
Basic SEP concepts are introduced by using Figure 10-1 and Figure 10-2.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
310
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
Figure 10-2 Networking diagram for an open ring running SEP
VLAN/VPLS
VLAN/VPLS
LSW1
LSW5
SEP
Segment
SEP
Segment
LSW2
LSW5
LSW1
LSW4
LSW4
LSW2
LSW3
LSW3
CE
CE
No-Neighbor Primary Edge Node
No-Neighbor Secondary Edge Node
Primary Edge Node
Secondary Edge Node
Block Port
SEP segment
A SEP segment is the basic unit of SEP. A SEP segment is composed of multiple
interconnected Layer 2 switching devices configured with the same SEP segment ID and
the same control VLAN ID.
A SEP segment corresponds to a ring-shaped or line-shaped Ethernet topology. Each SEP
segment has a control VLAN, edge interfaces, and common interfaces.
Control VLAN
In a SEP segment, the control VLAN is used to transmit only SEP packets.
Each SEP segment must be configured with a control VLAN. After being added to a SEP
segment configured with a control VLAN, an interface is added to the control VLAN
automatically.
Different SEP segments can use the same control VLAN.
Unlike a control VLAN, a data VLAN is used to transmit data packets.
Node
A node is a Layer 2 switching device added to a SEP segment. Only two interfaces on a
node can be added to the same SEP segment.
Interface role
As defined by SEP, interfaces are classified into common interfaces and edge interfaces.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
311
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
As shown in Table 10-2, edge interfaces are further classified into primary edge interfaces,
secondary edge interfaces, no-neighbor primary edge interfaces, and no-neighbor
secondary edge interfaces.
NOTE
Normally, an edge interface and a no-neighbor edge interface belong to different SEP segments.
Table 10-2 Interface roles
Interfac
e roles
Sub-role
Description
Deployment
Scenario
Common
port
In a SEP segment, all interfaces except edge
interfaces and the blocked interface are
common interfaces.
A common interface monitors the status of
its directly connected SEP link and notifies
its neighboring interface of link status
changes in time. The neighboring interface
constantly floods the notification message to
other interfaces in the SEP segment until the
message reaches the primary edge interface.
The primary edge interface then processes
the message.
Edge
port
Primary
Edge Port
A SEP segment has only one primary edge
interface. It can either be configured or be
elected.
The primary edge interface initiates
blocked-interface preemption, terminates
packets, and sends packets about topology
changes to other networks.
Secondary
edge port
A SEP segment has only one secondary edge
interface. It can either be configured or be
elected.
Open ring
network
Closed ring
network
Multiple-ring
networking
Hybrid SEP
+RRPP ring
networking
A secondary edge interface terminates
packets, and sends topology change
notification messages to other networks.
Noneighbor
primary
edge port
The interface at the most marginal edge of a
SEP segment is a no-neighbor primary edge
interface, as shown in Figure 10-2. It is
configured by users.
Hybrid SEP
+MSTP ring
networking
A no-neighbor primary interface initiates
blocked-interface preemption, terminates
packets, and sends topology change
notification messages to other networks.
No-neighbor primary edge interfaces are
used to interconnect Huawei devices and
non-Huawei devices or devices that do not
support SEP.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
312
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
Interfac
e roles
10 SEP Configuration
Sub-role
Description
Noneighbor
secondary
edge port
A no-neighbor secondary edge interface
terminates packets and sends topology
change notification messages to other
networks.
Deployment
Scenario
No-neighbor secondary edge interfaces are
used to interconnect non-Huawei devices
and devices that do not support SEP.
Blocked interface
In a SEP segment, an interface is blocked to prevent loops.
If you do not specify the interface as a blocked interface, any interface in a SEP segment
may be blocked. Only one interface is blocked in a SEP segment that works properly.
Status of SEP-enabled interfaces
Table 10-3 shows the status of SEP-enabled interfaces in a SEP segment.
Table 10-3 Interface status
Interface
Status
Description
Forwarding
An interface in the forwarding state can forward user traffic, and receive
and send SEP packets.
Discarding
An interface in the discarding state only receives and sends SEP packets.
The interface status does not depend on the interface role. An interface may be in forwarding
or discarding state regardless of its role.
The process of breaking a loop by using SEP
1.
After a SEP segment is created, the interfaces on each node of the ring network are added
to the SEP segment, and a role is configured for each interface.
2.
The neighbor negotiation mechanism is started after the interfaces are added to the SEP
segment. One of the last two interfaces that complete neighbor negotiation becomes a
blocked interface.
3.
The blocked interface sends LSAs to instruct other nodes in the SEP segment to update
their LSA databases.
The blocked interface does not allow data packets but SEP protocol packets to pass through.
4.
After receiving the LSAs, the nodes update their LSA databases, and then determine
forwarding paths. The loop is successfully broken.
Typical SEP Topologies
l
Issue 02 (2011-11-21)
Open ring network
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
313
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
Figure 10-3 Networking diagram for an open ring running SEP
NPE2
NPE1
Core
IP/MPLS Core
Aggregation
VRRP+peer BFD
PE-AGG1
PE-AGG2
VLAN/VPLS
LSW1
LSW5
Access
SEP
Segment
LSW2
LSW4
LSW3
CE
Primary Edge Node
Secondary Edge Node
Block Port
As shown in Figure 10-3, the networking consists of the access layer, aggregation layer,
and core layer. The CE is dual-homed to the upstream Layer 2 network through LSW1 to
LSW5. LSW1 to LSW5 form an open ring network. The open ring network is deployed at
the access layer to implement Layer 2 transparent transmission of unicast and multicast
packets. SEP runs at the access layer to implement link redundancy.
On a closed ring network, an edge interface is deployed on each of the two edge devices.
l
Issue 02 (2011-11-21)
Closed ring network
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
314
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
Figure 10-4 Networking diagram for a closed ring running SEP
Core
IP/MPLS Core
NPE1
NPE2
VRRP+peer BFD
Aggregation
LSW1
LSW5
SEP
Segment
LSW2
LSW4
Access
LSW3
CE1
CE2
CE3
Primary Edge Node
Secondary Edge Node
Block Port
As shown in Figure 10-4, the CEs are dual-homed to the upstream Layer 2 network through
LSW1 to LSW5. The edge devices LSW1 and LSW5 are directly connected to each other.
LSW1 to LSW5 form a closed ring network. The closed ring network is deployed at the
aggregation layer to aggregate unicast and multicast services. SEP runs at the aggregation
layer to implement link redundancy.
On a closed ring network, two edge interfaces are deployed on one edge device.
l
Issue 02 (2011-11-21)
Multiple-ring networking
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
315
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
Figure 10-5 Networking diagram for multiple rings running SEP
Core
IP/MPLS Core
NPE1
NPE2
VRRP+peer BFD
Aggregation
LSW1
LSW5
SEP
Segment 1
LSW2
LSW4
LSW3
Access
Se
S
gm EP
en
t2
P t3
SE en
gm
Se
LSW6
LSW8
LSW12
SEP
Segment 5
SEP
Segment 4
LSW9
LSW14
LSW13
LSW7
LSW10
LSW11
Block Port
As shown in Figure 10-5, LSW1 to LSW14 form multiple rings. LSW1 to LSW5 are at
the aggregation layer, and LSW6 to LSW14 are at the access layer. Layer 2 services are
transparently transmitted at the access layer and the aggregation layer. SEP runs at the
aggregation layer and access layer to implement link redundancy. If the topology of a SEP
segment at the access layer changes, a node in the SEP segment sends a Flush-FDB packet
to instruct the other nodes in the SEP segment to refresh their MAC address forwarding
tables and ARP tables. The edge devices in the SEP segment send TC packets to notify
devices at the upper layer that the topology of the SEP segment has changed.
In multi-ring networking, topology change notification among ring networks needs to be
configured.
l
Hybrid networking
Hybrid SEP+MSTP ring networking
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
316
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
Core
Figure 10-6 Networking diagram for hybrid rings running SEP+MSTP
IP/MPLS Core
Aggregation
NPE1
NPE2
VRRP+peer BFD
PE4
PE3
MSTP
PE1
PE2
Access
Do not Support SEP
SEP
Segment
LSW1
LSW2
LSW3
No-neighbor Primary Edge Node
No-neighbor Secondary Edge Node
Block Port
As shown in Figure 10-6, LSW1 to LSW3 form a SEP segment to access an MSTP
ring. The networking is called hybrid SEP+MSTP ring networking. LSW1 to LSW3
are at the access layer to transparently transmit Layer 2 unicast and multicast packets.
SEP runs at the access layer to implement link redundancy. If the topology of the SEP
segment at the access layer changes, a node in the SEP segment sends a Flush-FDB
packet to instruct the other nodes in the SEP segment to refresh their MAC forwarding
tables and ARP tables. LSW1 and LSW2 in the SEP segment send TC packets to notify
devices at the upper-layer that the topology of the SEP segment has changed.
In hybrid SEP+MSTP ring networking, no-neighbor edge interfaces need to be deployed
on the edge devices of SEP networks, and the SEP networks need to report topology
changes to STP networks.
Hybrid SEP+RRPP ring networking
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
317
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
Core
Figure 10-7 Networking diagram for hybrid rings running SEP+RRPP
IP/MPLS Core
Aggregation
NPE1
NPE2
VRRP+peer BFD
PE4
PE3
RRPP
PE1
PE2
Access
SEP
Segment
LSW1
LSW2
LSW3
Primary Edge Node
Secondary Edge Node
Block Port
As shown in Figure 10-7, PE1, PE2 and LSW1 to LSW3 form a SEP segment to access
an RRPP ring. The networking is called hybrid SEP+RRPP ring networking. PE1, PE2
and LSW1 to LSW3 are at the access layer to transparently transmit Layer 2 unicast
and multicast packets. SEP runs at the access layer to implement link redundancy. If
the topology of the SEP segment at the access layer changes, a node in the SEP segment
sends a Flush-FDB packet to instruct the other nodes in the SEP segment to refresh their
MAC forwarding tables and ARP tables. PE1 and PE2 in the SEP segment send TC
packets to notify devices at the upper-layer that the topology of the SEP segment has
changed.
In hybrid SEP+RRPP ring networking, the SEP networks need to report topology
changes to RRPP networks on the edge devices of SEP networks.
NOTE
The basic SEP configurations in the preceding topologies are the same, except for the locations and
configurations of the primary edge interface, no-neighbor primary edge interface, secondary edge interface,
and no-neighbor secondary edge interface. For details about these interfaces, see Table 10-2.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
318
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
10.1.2 SEP Features Supported by the S5700
This section describes SEP features supported by the S5700 from the perspective of SEP
configuration logic. Familiarizing yourself with SEP configuration logic helps you complete
configuration tasks quickly and efficiently.
SEP configuration roadmap is as follows:
1.
After basic SEP functions are configured on devices, the devices start the SEP negotiation.
One of the last two interfaces that complete neighbor negotiation is blocked to eliminate
redundant links.
NOTE
When logging in to nodes on a SEP semi-ring through Telnet to configure them, note the following
points:
l VLANIF interfaces and their IP address need to be configured, because these nodes are Layer 2
devices. The VLANs to which these VLANIF interfaces correspond must be mapped to the SEP
protection instance.
l Basic SEP functions need to be configured from the node at one end of the semi-ring to the node
at the other end of the semi-ring.
2.
In some cases, however, the blocked interface obtained through the SEP calculation may
not be the one you expect to be blocked. You can specify an interface to block as needed.
3.
To implement load balancing and make efficient use of bandwidth, protected instances
need to be deployed on a network running SEP and mappings between protected instances
and VLANs need to be worked out.
4.
A SEP network usually needs to work together with another network deployed with other
features. To ensure network reliability, if the topology of either of the networks changes,
the other network must be able to detect the topology change and take measures to
implement reliable data transmission. Therefore, the topology change notification function
needs to be enabled on the network running SEP.
Specifying an Interface to Block
In general, a blocked interface is one of the last two interfaces that complete neighbor negotiation.
In some cases, however, the negotiated blocked interface may not be the one you expect to be
blocked. You specify an interface to block as needed. The designated blocking does not,
however, become effective immediately. A preemption mechanism allows a designated interface
to be blocked instead of a previously blocked interface.
l
Interface blocking mode
You can configure an interface blocking mode in order to specify the location of a blocked
interface. Table 10-4 lists interface blocking modes.
Table 10-4 Interface blocking mode
Issue 02 (2011-11-21)
Interface Blocking
Mode
Description
Specifying the interface
with the highest priority
as the blocked interface
Is applicable to a large-scale network.
After fault recovery, the interface with the highest priority in
a SEP segment is designated as the blocked interface. In this
mode, the priorities of the interfaces on the SEP segment need
to be set in advanced.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
319
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
Interface Blocking
Mode
Description
Specifying the interface
in the middle of a SEP
segment as the blocked
interface
Is applicable to a network where traffic is symmetrically
distributed.
Specifying the blocked
interface based on the
configured hop count
Is applicable to a small-scale network.
Specifying the blocked
interface based on the
device name and
interface name
Is applicable to a small-scale network.
After fault recovery, the interface in the middle of a SEP
segment is designated as the blocked interface.
After fault recovery, a specified interface can be blocked
based on the hop count. A network planner needs to be
familiar with the topology of the entire SEP segment and the
number of hops from the blocked interface to the primaryedge interface.
After fault recovery, a specified interface can be blocked
based on the device name and the interface name. A network
planner needs to be familiar with the names of devices and
interfaces on the entire SEP segment and ensures that each
device name is unique.
Preemption
After the interface blocking mode is specified, whether the specified interface will be
blocked is determined by the preemption mode. Table 10-5 lists the preemption modes.
Table 10-5 Preemption mode
Preemption
Mode
Advantage
Disadvantage
Non-preemption
mode
SEP is in the nonpreemption mode by
default.
The blocked interface is one of the last
two interfaces that complete neighbor
negotiation.
In this mode, blocking
an interface does not
disconnect any link in a
SEP segment.
Preemp
tion
mode
Issue 02 (2011-11-21)
Delaye
d
preemp
tion
Each time a fault is
rectified, the system
automatically
completes preemption
and ensures that the
specified interface is
blocked.
l Related commands need to be used to
specify the delayed preemption mode
in advance. The preemption delay
does not have a default value, and
therefore related commands must be
used to set the preemption delay.
l After delayed preemption is
configured successfully, a fault needs
to be simulated to ensure that the
specified interface is blocked.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
320
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
Preemption
Mode
Manual
preemp
tion
10 SEP Configuration
Advantage
Disadvantage
Whether the specified
interface will be
blocked can be
controlled manually.
l The manual preemption mode needs
to be specified in advance.
l After related faults are rectified and
the preemption action is taken,
manual preemption does not take
effect.
Manual preemption needs to be
configured so that the specified
interface is blocked after the next
fault is rectified. This increases the
maintenance workload.
NOTE
In preemption mode, blocking an interface temporarily disconnects a link in a SEP segment.
SEP Multi-Instance
As shown in Figure 10-8, in regular SEP networking, a physical ring network can be configured
with only one SEP segment in which only one interface can be blocked. If an interface in the
SEP segment in the complete state is blocked, all user data is transmitted only along the path
where the primary edge interface is located. The path where the secondary edge interface is
located is idle, which leads to a waste of bandwidth.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
321
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
Figure 10-8 Networking diagram for SEP multi-instance
Core
IP/MPLS Core
group 2:Master
group 1:Backup
NPE2
group 1:Master
group 2:Backup
NPE1
Access
Aggregation
VRRP+peer BFD
LSW2
LSW4
SEP
Segment1
LSW1
LSW3
VLAN 201~400
VLAN 100~200
CE1
CE2
Primary Edge Node
Secondary Edge Node
Block Port
SEP multi-instance allows two SEP segments to be configured on one physical ring network.
All devices, interface roles, and control VLANs in each SEP segment must be configured by
conforming to basic SEP configurations principles. Each SEP segment has one blocked interface.
Each blocked interface detects whether the physical ring network is complete. The blocked
interfaces in the two SEP segments are independent of each other.
A physical ring network can be configured with one or two SEP segments. Each SEP segment
needs to be configured with a protected instance and each protected instance represents a VLAN
range. The topology calculated by a SEP segment is valid only for that SEP segment.
After different protected instances are configured for SEP segments and the mapping between
protected instances and VLANs is set, a blocked interface is valid only for the VLANs protected
by the SEP segment where the blocked interface resides. Data traffic of different VLANs can
be transmitted along different paths. This implements traffic load balancing and link backup.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
322
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
Figure 10-9 Networking diagram for SEP multi-instance
Core
IP/MPLS Core
group 2:Master
group 1:Backup
NPE2
group 1:Master
group 2:Backup
NPE1
Aggregation
VRRP+peer BFD
LSW2
LSW4
SEP
Segment2
Access
P2
P1
SEP Segment1
Instance1:
VLAN 100~200
LSW1
CE1
LSW3
Instance2:
VLAN 201~400
CE2
Primary Edge Node
Secondary Edge Node
Block Port
As shown in Figure 10-9, the SEP multi-instance ring network that consists of LSW1 to LSW4
has two SEP segments. P1 is the blocked interface in SEP segment 1, and P2 is the blocked
interface in SEP segment 2.
l
Protected instance 1 is configured in SEP segment 1 to protect the data of VLAN 100 to
VLAN 200. The data is transmitted along path LSW1->LSW2->NPE1. As the blocked
interface in SEP segment 2, P2 blocks only the data of VLAN 201 to VLAN 400.
Protected instance 2 is configured in SEP segment 2 to protect the data of VLAN 201 to
VLAN 400. The data is transmitted along path LSW3->LSW4->NPE2. As the blocked
interface in SEP segment 1, P1 blocks only the data of VLAN 100 to VLAN 200.
In the case of a node or a link failure, each SEP segment calculates its own topology
independently, and the nodes in each SEP segment update their LSA databases.
SEP Topology Change Notification
Table 10-6 lists the situations in which the topology of a SEP segment changes.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
323
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
Table 10-6 SEP topology changes
SEP Topology
Change
Description
Topology
change caused
by an interface
fault
If an interface on a device in a complete SEP segment becomes faulty, the
topology of the SEP segment changes.
Topology
change caused
by a fault being
rectified and the
preemption
function taking
effect
One or more faults occur in the SEP segment. When the last fault is rectified
and the blocked interface is preempted, the topology is considered
changed.
An interface fault can be a link fault or a neighboring interface fault.
Table 10-7 list the situations in which topology changes are reported.
Table 10-7 SEP topology change notification
SEP
Topology
Change
Notification
Scenario
Description
Solution
Topology
change
notification
from a lowerlayer network
to an upperlayer network
Networking where a
SEP network is
connected to an
upper-layer network
running other
features such as
SEP, STP, RRPP
and SmartLink
l If the blocked interface in a
lower-layer SEP network is
manually changed, the topology
of the SEP segment changes.
Because the upper-layer
network cannot detect the
topology change, traffic is
interrupted.
Configure
the SEP
topology
change
notification
function.
l If an interface in a lower-layer
SEP network becomes faulty,
the topology of the SEP segment
changes but the upper-layer
network cannot detect the
change. As a result, traffic is
interrupted.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
324
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
SEP
Topology
Change
Notification
10 SEP Configuration
Scenario
Description
Solution
Networking
scenario where a
host is connected to
a SEP network by
using a SmartLink
group
During an active/standby
switchover of member interfaces in
the SmartLink group, the host sends
a SmartLink Flush packet to notify
the connected devices in the SEP
segment of the switchover.
Enable the
edge devices
in the SEP
segment to
process
SmartLink
Flush
packets.
If the connected devices in the SEP
segment cannot identify the
SmartLink Flush packet (that is, if
these connected devices in the SEP
segment cannot detect any topology
change of the lower-layer network),
traffic will be interrupted.
Topology
change
notification
from an upperlayer network
to a lower-layer
network
Networking
scenario where a
SEP network is
connected to an
upper-layer network
configured with
CFM.
If a fault occurs on the upper-layer
network, the topology of that
network changes but the lowerlayer network cannot detect the
change. As a result, traffic is
interrupted.
Configure
association
between SEP
and CFM.
10.2 Configuring Basic SEP Functions
When there is no faulty link on a ring network running SEP, SEP can eliminate loops on the
Ethernet. When a link fault occurs on a ring network running SEP, SEP can immediately restore
the communication links between the nodes.
10.2.1 Establishing the Configuration Task
Before configuring basic SEP functions, familiarize yourself with the applicable environment,
complete the pre-configuration tasks, and obtain the required data. This can help you complete
the configuration task quickly and efficiently.
Applicable Environment
Generally, redundant links are used to connect an Ethernet switching network to an upper-layer
network to provide link backup and enhance network reliability. The use of redundant links,
however, may produce loops, causing broadcast storms and rendering the MAC address table
unstable. As a result, the communication quality deteriorates, and communication services may
even be interrupted. SEP can be deployed on the ring network to block redundant links and
unblock them if a link fault occurs.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
325
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
Pre-configuration Tasks
Before configuring basic SEP functions, complete the following tasks:
l
Establishing the ring networking
Ensuring that the devices are powered on correctly and operate properly
Data Preparation
To configure basic SEP functions, you need the following data.
No.
Data
SEP segment ID
ID of the control VLAN in the SEP segment
Role of each interface added to the SEP segment
10.2.2 Configuring an SEP Segment
SEP takes an SEP segment as a basic unit. An SEP segment is composed of multiple
interconnected Layer 2 switching devices configured with the same SEP segment ID and the
same control VLAN ID.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
sep segment segment-id
An SEP segment is created and the view of the SEP segment is displayed.
Before deleting a created SEP segment, you need to check whether there is any interface added
to the SEP segment. If there is an interface added to the SEP segment, run the undo sep
segment segment-id command in the interface view to delete the interface from the SEP segment.
Otherwise, the SEP segment cannot be deleted.
----End
10.2.3 Configuring a Control VLAN
In a SEP segment, a control VLAN is used to transmit SEP packets but not service packets,
enhancing the security of SEP. Each SEP segment must be configured with a control VLAN.
After being added to a SEP segment configured with a control VLAN, an interface is added to
the control VLAN automatically.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
326
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
Context
NOTE
On a SEP network that has no-neighbor edge interfaces, a device that is not in a SEP segment cannot be
added to the control VLAN of the SEP segment. Otherwise, a loop will be caused on the network.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
sep segment segment-id
A SEP segment is created and the view of the SEP segment is displayed.
Step 3 Run:
control-vlan vlan-id
The control VLAN of the SEP segment is configured for transmitting SEP packets.
The control VLAN specified by vlan-id must be newly created and must not have been used by
RRPP or used in port trunk, default, mapping, or stacking mode.
l Different SEP segments can use the same control VLAN.
l If there is an interface added to the SEP segment, you cannot directly delete the control VLAN
of the SEP segment. To delete the control VLAN, run the undo sep segment segment-id
command in the interface view to delete the interface from the SEP segment, and then run
the undo control-vlan command to delete the control VLAN.
l If there is no interface added to the SEP segment, you can run the control-vlan vlan-id
command for multiple times. Only the latest configuration takes effect.
l After the control VLAN is created successfully, the command used to create a common
VLAN will be displayed in the configuration file.
Each SEP segment must be configured with a control VLAN. After an interface is added to
a SEP segment configured with a control VLAN, the interface will be automatically added
to the control VLAN.
If the interface type is Trunk, in the configuration file, the port trunk allow-pass vlan
command is displayed in the view of the interface added to the SEP segment.
If the interface type is Hybrid, in the configuration file, the port hybrid tagged vlan
command is displayed in the view of the interface added to the SEP segment.
----End
10.2.4 Creating a Protected Instance
Interfaces can be added to an SEP segment only after the SEP segment is configured with
protected instances.
Procedure
Step 1 Run:
system-view
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
327
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
The system view is displayed.
Step 2 Run:
sep segment segment-id
A SEP segment is created and the view of the SEP segment is displayed.
Step 3 Run:
protected-instance { all | { instance-id1 [ to instance-id2 ] &<1-10> } }
A protected instance is created in a SEP segment.
By default, no protected instance is configured in a SEP segment.
----End
10.2.5 Adding a Layer 2 Interface to a SEP Segment and Configuring
a Role for the Interface
To ensure the normal forwarding of SEP packets in a SEP segment, add Layer 2 interfaces to
the SEP segment and configure different roles for the interfaces.
Context
After an interface is added to SEP segment, the interface sets its interface role to the primary
edge interface if the interface has the right to participate in the election of the primary edge
interface. Then, the interface periodically sends a primary edge interface-election packet without
waiting for the success of neighbor negotiation.
The primary edge interface-election packet contains the role of the interface (primary edge
interface, secondary edge interface, or common interface), the bridge MAC address of the
interface, interface ID, and the status of the topology database.
Table 10-8 lists interface roles.
Table 10-8 Interface roles
Interface
roles
Sub-role
Description
Deployment
Scenario
Common
port
In a SEP segment, all interfaces except edge
interfaces and the blocked interface are
common interfaces.
A common interface monitors the status of its
directly connected SEP link and notifies its
neighboring interface of link status changes in
time. The neighboring interface constantly
floods the notification message to other
interfaces in the SEP segment until the
message reaches the primary edge interface.
The primary edge interface then processes the
message.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
328
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
Interface
roles
Sub-role
Description
Deployment
Scenario
Edge port
Primary
Edge Port
A SEP segment has only one primary edge
interface. It can either be configured or be
elected.
Open ring
network
Closed ring
network
Multiple-ring
networking
Hybrid SEP
+RRPP ring
networking
The primary edge interface initiates blockedinterface preemption, terminates packets, and
sends packets about topology changes to other
networks.
Secondary
edge port
A SEP segment has only one secondary edge
interface. It can either be configured or be
elected.
A secondary edge interface terminates packets,
and sends topology change notification
messages to other networks.
Noneighbor
primary
edge port
The interface at the most marginal edge of a
SEP segment is a no-neighbor primary edge
interface, as shown in Figure 10-2. It is
configured by users.
Hybrid SEP
+MSTP ring
networking
A no-neighbor primary interface initiates
blocked-interface preemption, terminates
packets, and sends topology change
notification messages to other networks.
No-neighbor primary edge interfaces are used
to interconnect Huawei devices and nonHuawei devices or devices that do not support
SEP.
Noneighbor
secondary
edge port
A no-neighbor secondary edge interface
terminates packets and sends topology change
notification messages to other networks.
No-neighbor secondary edge interfaces are
used to interconnect non-Huawei devices and
devices that do not support SEP.
NOTE
Normally, an edge interface and a no-neighbor edge interface belong to different SEP segments.
Before adding a Layer 2 interface to a SEP segment, ensure that STP has been disabled on the interface.
Before adding an interface to a SEP segment,configure a protected instance or a range of protected
instances .
Procedure
Step 1 Run:
system-view
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
329
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
The system view is displayed.
Step 2 Run:
interface interface-type interface-number
The view of an Ethernet interface added to the SEP segment is displayed.
Step 3 Run:
stp disable
STP is disabled on the interface.
Step 4 Run:
sep segment segment-id [ edge [ no-neighbor ] { primary | secondary } ]
The Ethernet interface is added to a specified SEP segment and a role is configured for it.
NOTE
An interface can be added to only two SEP segments.
----End
10.2.6 Checking the Configuration
After basic SEP functions are configured, you can view the information such as the names and
roles of interfaces added to an SEP segment, status of the interfaces on neighbors, and forwarding
status of the local interface.
Prerequisite
The configurations of basic SEP functions are complete.
Procedure
l
Run the display sep interface [ interface-type interface-number | segment segment-id ]
[ verbose ] command to check the information about interfaces that reside on the device
and are added to a specified SEP segment.
Run the display sep topology [ segment segment-id ] [ verbose ] command to check the
topology status of a specified SEP segment.
----End
10.3 Specifying an Interface to Block
By default, the blocked interface is one of the last two interfaces that complete neighbor
negotiation. Sometimes, the negotiated blocked interface, however, may not be the expected
one. An interface can be selected to block as required.
10.3.1 Establishing the Configuration Task
Before specifying an interface to block, familiarize yourself with the applicable environment,
complete the pre-configuration tasks, and obtain the required data. This can help you complete
the configuration task quickly and efficiently.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
330
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
Applicable Environment
In general, a blocked interface is one of the last two interfaces that complete neighbor negotiation.
In some cases, however, the negotiated blocked interface may not be the one you expect to be
blocked. You specify an interface to block as needed. The designated blocking does not,
however, become effective immediately. A preemption mechanism allows a designated interface
to be blocked instead of a previously blocked interface.
Pre-configuration Tasks
Before specifying an interface to block, complete the following task:
l
Configuring Basic SEP Functions
Data Preparation
To specify an interface to block, you need the following data.
No.
Data
Interface blocking mode
SEP preemption mode
10.3.2 Setting an Interface Blocking Mode
Each interface in a SEP segment may become a blocked interface. You can specify an interface
to block by configuring an interface blocking mode.
Context
In a SEP segment, an interface is blocked to prevent loops.
You can configure an interface blocking mode in order to specify the location of a blocked
interface. Table 10-9 lists interface blocking modes.
Table 10-9 Interface blocking mode
Issue 02 (2011-11-21)
Interface Blocking
Mode
Description
Specifying the interface
with the highest priority
as the blocked interface
Is applicable to a large-scale network.
Specifying the interface
in the middle of a SEP
segment as the blocked
interface
Is applicable to a network where traffic is symmetrically
distributed.
After fault recovery, the interface with the highest priority in a
SEP segment is designated as the blocked interface. In this mode,
the priorities of the interfaces on the SEP segment need to be set
in advanced.
After fault recovery, the interface in the middle of a SEP segment
is designated as the blocked interface.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
331
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
Interface Blocking
Mode
Description
Specifying the blocked
interface based on the
configured hop count
Is applicable to a small-scale network.
Specifying the blocked
interface based on the
device name and interface
name
Is applicable to a small-scale network.
After fault recovery, a specified interface can be blocked based
on the hop count. A network planner needs to be familiar with
the topology of the entire SEP segment and the number of hops
from the blocked interface to the primary-edge interface.
After fault recovery, a specified interface can be blocked based
on the device name and the interface name. A network planner
needs to be familiar with the names of devices and interfaces on
the entire SEP segment and ensures that each device name is
unique.
Do as follows on the device where the primary edge interface or the no-neighbor primary edge
interface is located:
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
sep segment segment-id
A SEP segment is created and the view of the SEP segment is displayed.
Step 3 Run:
block port { optimal | middle | hop hop-id | sysname sysname interface interfacetype interface-number }
An interface blocking mode is set.
By default, one of the interfaces at both ends of the last link that is set up or the last link that
recovers from a fault is blocked.
l optimal specifies the interface with the highest priority as the blocked interface.
l middle specifies the interface in the middle of the SEP segment as the blocked interface.
l hop specifies the interface that is hop-id hops away from the primary edge interface as the
blocked interface.
If hop-id is set to 1, it indicates that the blocked interface is the primary edge interface. If
hop-id is set to 2, it indicates that the blocked interface is the neighboring interface of the
primary edge interface. The hop count increases along with the number of downstream
neighbors of the primary edge interface.
l sysname+interface specifies the name of the device where the interface to be blocked
resides.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
332
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
For information on how to select an interface blocking mode, see the preceding table.
----End
Follow-up Procedure
If the interface that has the highest priority is specified to block, run the sep segment segmentid priority priority command in the view of the interface to be blocked to increase its priority.
When a fault is rectified, the specified interface will be blocked.
The default priority of an interface added to a SEP segment is 64. The priority value of an
interface is an integer ranging from 1 to 128. The greater the priority value, the higher the priority.
10.3.3 Configuring the Preemption Mode
The SEP preemption mode is classified into delay preemption and manual preemption.
Context
After the interface blocking mode is specified, whether the specified interface will be blocked
is determined by the preemption mode. Table 10-10 lists the preemption modes.
Table 10-10 Preemption mode
Preemption
Mode
Advantage
Disadvantage
Non-preemption
mode
SEP is in the nonpreemption mode by
default.
The blocked interface is one of the last two
interfaces that complete neighbor
negotiation.
In this mode, blocking an
interface does not
disconnect any link in a
SEP segment.
Preempt
ion
mode
Delayed
preempt
ion
Each time a fault is
rectified, the system
automatically completes
preemption and ensures
that the specified
interface is blocked.
l Related commands need to be used to
specify the delayed preemption mode in
advance. The preemption delay does not
have a default value, and therefore
related commands must be used to set
the preemption delay.
l After delayed preemption is configured
successfully, a fault needs to be
simulated to ensure that the specified
interface is blocked.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
333
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
Preemption
Mode
Manual
preempt
ion
10 SEP Configuration
Advantage
Disadvantage
Whether the specified
interface will be blocked
can be controlled
manually.
l The manual preemption mode needs to
be specified in advance.
l After related faults are rectified and the
preemption action is taken, manual
preemption does not take effect.
Manual preemption needs to be
configured so that the specified
interface is blocked after the next fault
is rectified. This increases the
maintenance workload.
The following conditions must be met to trigger preemption:
l
The topology of the SEP segment must be normal.
The primary edge interface or no-neighbor primary edge interface has been elected in the
SEP segment.
The function of flexibly specifying a blocked interface is enabled on the device where the
primary edge interface or no-neighbor primary edge interface resides.
Do as follows on the Layer 2 switching device where the primary edge interface or the noneighbour primary edge interface is elected.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
sep segment segment-id
A SEP segment is created and the view of the SEP segment is displayed.
Step 3 Run:
preempt { manual | delay seconds }
The preemption mode is configured on the primary edge interface.
By default, the primary edge interface is not configured with the preemption mode, that is, the
non-preemption mode is adopted.
----End
10.3.4 Checking the Configuration
After specifying an interface to block, you can view information about a specified blocked
interface.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
334
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
Prerequisite
The configurations of specifying an interface to block are complete.
Procedure
l
Run the display sep topology [ segment segment-id ] [ verbose ] command to check the
topology status of a specified SEP segment.
----End
10.4 Configuring SEP Multi-Instance
SEP multi-instance allows two SEP segments to be configured on a physical ring network. After
different protected instances are configured for the SEP segments and VLANs are mapped to
specified protected instances, load balancing and link backup can be implemented for service
traffic.
10.4.1 Establishing the Configuration Task
Before configuring SEP multi-instance, familiarize yourself with the applicable environment,
complete the pre-configuration tasks, and obtain the required data. This will help you complete
the configuration task quickly and efficiently.
Applicable Environment
in regular SEP networking, a physical ring network can be configured with only one SEP segment
in which only one interface can be blocked. If an interface in the SEP segment in the complete
state is blocked, all user data is transmitted only along the path where the primary edge interface
is located. The path where the secondary edge interface is located is idle, which leads to a waste
of bandwidth.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
335
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
Figure 10-10 Networking diagram for SEP multi-instance
Core
IP/MPLS Core
group 2:Master
group 1:Backup
NPE2
group 1:Master
group 2:Backup
NPE1
Aggregation
VRRP+peer BFD
LSW2
LSW4
SEP
Segment2
Access
P2
P1
SEP Segment1
Instance1:
VLAN 100~200
LSW1
CE1
LSW3
Instance2:
VLAN 201~400
CE2
Primary Edge Node
Secondary Edge Node
Block Port
To solve the problem of bandwidth waste and to implement traffic load balancing and link
backup, multi-instance can be deployed in the SEP network and mappings between protected
instances and user VLANs need to be set, as shown in Figure 10-10. Data traffic of different
VLANs can be transmitted along different paths.
NOTE
Currently, SEP multi-instance allows two SEP segments to be configured on a physical ring network.
Pre-configuration Tasks
Before configuring SEP multi-instance, complete the following tasks:
l
Configuring Basic SEP Functions
Specifying an Interface to Block
Data Preparation
To configure SEP multi-instance, you need the following data.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
336
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
No.
Data
ID of a protected instance in a SEP segment
ID of a VLAN mapped to a protected instance
10 SEP Configuration
10.4.2 Configuring and Activating Mappings Between Protected
Instances and VLANs
A physical ring network can be configured with one or two SEP segments. To ensure proper
traffic transmission, each SEP segment needs to be configured with a protected instance. After
mappings between protected instances and specified VLANs are configured, load balancing and
link backup can be implemented.
Context
After mappings between protected instances and VLANs are configured, the mappings need to
be activated to implement load balancing and link backup.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
stp region-configuration
The MST region view is displayed.
Step 3 Run:
instance instance-id vlan { vlan-id [ to vlan-id ] } &<1-10>
Mappings between protected instances and VLANs are configured.
The value of instance-id specified in this command must be consistent with that of instance-id
specified in the protected-instance command.
Step 4 Run:
active region-configuration
Mappings between protected instances and VLANs are activated.
After mappings between protected instances and VLANs take effect, topology changes of a SEP
segment affect only corresponding VLANs. This ensures reliable transmission of user data.
----End
10.4.3 Checking the Configuration
After configuring SEP multi-instance on a ring network, you can view the blocked interface in
each SEP segment.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
337
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
Prerequisite
The configurations of SEP multi-instance are complete.
Procedure
l
Run the display sep topology [ segment segment-id ] [ verbose ] command to check the
topology status of a specified SEP segment.
----End
10.5 Configuring the Topology Change Notification
Function
The function of advertising topology changes is configured on the device connecting a lowerlevel network to an upper-level network. With this function, the device can notify the remote
device of topology changes of the lower-level and upper-level networks. After being notified of
these topology changes, all the devices on the network where the remote device resides delete
associated MAC addresses and ARP entry in time and relearn the MAC address of the remote
device. This ensures nonstop traffic forwarding.
10.5.1 Establishing the Configuration Task
Before configuring the topology change notification function, familiarize yourself with the
applicable environment, complete the pre-configuration tasks, and obtain the required data. This
will help you complete the configuration task quickly and efficiently.
Applicable Environment
Currently, the S5700 can report topology changes in two modes, as shown in Table 10-11. You
can select a mode as needed.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
338
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
Table 10-11 SEP topology change notification
SEP
Topology
Change
Notification
Scenario
Description
Solution
Topology
change
notification
from a lowerlayer network
to an upperlayer network
Networking where a
SEP network is
connected to an
upper-layer network
running other
features such as
SEP, STP, RRPP
and SmartLink
l If the blocked interface in a
lower-layer SEP network is
manually changed, the topology
of the SEP segment changes.
Because the upper-layer
network cannot detect the
topology change, traffic is
interrupted.
Configure
the SEP
topology
change
notification
function.
l If an interface in a lower-layer
SEP network becomes faulty,
the topology of the SEP segment
changes but the upper-layer
network cannot detect the
change. As a result, traffic is
interrupted.
Networking
scenario where a
host is connected to
a SEP network by
using a SmartLink
group
During an active/standby
switchover of member interfaces in
the SmartLink group, the host sends
a SmartLink Flush packet to notify
the connected devices in the SEP
segment of the switchover.
If the connected devices in the SEP
segment cannot identify the
SmartLink Flush packet (that is, if
these connected devices in the SEP
segment cannot detect any topology
change of the lower-layer network),
traffic will be interrupted.
Topology
change
notification
from an upperlayer network
to a lower-layer
network
Networking
scenario where a
SEP network is
connected to an
upper-layer network
configured with
CFM.
If a fault occurs on the upper-layer
network, the topology of that
network changes but the lowerlayer network cannot detect the
change. As a result, traffic is
interrupted.
Enable the
edge devices
in the SEP
segment to
process
SmartLink
Flush
packets.
Configure
association
between SEP
and CFM.
Pre-configuration Tasks
Before configuring the topology change notification function, complete the following tasks:
l
Configuring Basic SEP Functions
Specifying an Interface to Block
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
339
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
Data Preparation
To configure the topology change notification function, you need the following data.
No.
Data
SEP segment ID
Mode of reporting topology changes
Names of the Maintenance Domain (MD) and the Maintenance Association (MA),
ID and type of a MEP, name of the interface on which the Maintenance association
End Point (MEP) resides, name of the interface enabled with Ethernet CFM, and name
of the interface associated with Ethernet CFM
10.5.2 Reporting Topology Changes of a Lower-Layer Network SEP Topology Change Notification
SEP runs at the access layer. To help an upper-layer network to detect whether the topology of
the network at the access layer changes, configure the SEP topology change notification function
on the device connecting the lower-layer network to the upper-layer network.
Context
If the topology of a specified SEP segment changes but the topology change is not reported to
the upper-layer network in time, the MAC address tables of the devices on the upper-layer
network retain the MAC address entries generated before the topology of the lower-layer
network changes. As a result, user traffic is interrupted. To ensure nonstop traffic forwarding,
configure the device on the lower-layer network to report topology changes to the upper-layer
network. The objects that are notified of topology changes can be specified as needed.
NOTE
Currently, topology changes of a SEP segment can be reported to other SEP segments, STP networks,
RRPP networks and SmartLink networks
After receiving a packet indicating topology changes of a lower-layer network, a device on an
upper-layer network sends TC packets locally to instruct the other devices on this network to
clear associated MAC addresses and relearn MAC addresses after the topology of the lowerlayer network changes. This ensures nonstop traffic forwarding.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
sep segment segment-id
A SEP segment is created and the view of the SEP segment is displayed.
Step 3 Run:
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
340
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
tc-notify { segment { segment-id1 [ to segment-id2 ] } &<1-10> | stp | rrpp | smartlink send-packet vlan vlan-id }
The topology change of a specified SEP segment is reported to another SEP segment or a network
running other ring protocols such as STP or RRPP.
By default, the topology change of a SEP segment is not reported.
----End
Follow-up Procedure
In the networking scenario where three or more SEP ring networks exist, when a TC notification
packet is sent through multiple links, the upper-layer network will receive it multiple times. This
reduces the efficiency for processing packets on the upper-layer network. Therefore, TC
notification packets need to be suppressed. Suppressing TC notification packets frees the upperlayer network from processing multiple duplicate packets and protects the devices in the SEP
segment against TC notification packet attacks.
Run the tc-protection interval interval-value command in the SEP-segment view to set the
interval for suppressing TC notification packets.
By default, the interval for suppressing TC notification packets is 2s, and three TC notification
packets with different source addresses are processed within 2s.
NOTE
l In the networking scenario where three or more SEP ring networks exist, this command must be run.
If this command is not run, the default interval for suppressing TC notification packets is used.
l A longer interval ensures stable SEP operating but deteriorates the convergence performance.
10.5.3 Reporting Topology Changes of a Lower-Layer Network Enabling the Edge Devices in a SEP Segment to Process SmartLink
Flush Packets
In the networking where a host is connected to a SEP network by using a SmartLink group , if
the active/standby switchover of member interfaces in the SmartLink group occurs, the host
sends SmartLink Flush packets to inform the edge devices in the SEP segment of the switchover.
Therefore, the edge devices in the SEP segment must be able to process SmartLink Flush packets.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
sep segment segment-id
A SEP segment is created and the view of the SEP segment is displayed.
Step 3 Run:
deal smart-link-flush
An edge device in a SEP segment is enabled to process SmartLink Flush packets.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
341
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
After receiving a SmartLink Flush packet, the edge device in a SEP segment floods FLUSHFDB packets to notify the other devices in the SEP segment of topology changes.
By default, no device in a SEP segment is enabled to process SmartLink Flush packets.
----End
10.5.4 Reporting Topology Changes of an Upper-Layer Network Configuring Association Between SEP and CFM
SEP runs at the access layer or aggregation layer. To help SEP networks to detect whether the
topology of an upper-layer network changes, you must configure association between SEP and
CFM on the device connecting the lower-layer network to the upper-layer network.
Context
When CFM detects a fault on the upper-layer network, the edge device notifies the OAM module
of the fault by sending a CFM packet. Then, on the edge device, the SEP status of the interface
associated with CFM changes to Down.
After the SEP status of the interface associated with CFM on the edge device is Down, an
interface on the peer device of the edge device in the SEP segment needs to send a Flush-FDB
packet to notify other nodes that the topology changes. After a device in the SEP segment
receives the Flush-FDB packet, the blocked interface on the device is unblocked and enters the
Forwarding state. Then, the interface sends a Flush-FDB packet to instruct the other nodes in
the SEP segment to refresh the MAC address forwarding table and the ARP table. Therefore,
the lower-layer network can sense the fault of the upper-layer network, and the reliable
transmission of services is ensured.
NOTE
IEEE 802.1ag defines protocols and practices for Operations, Administration and Maintenance (OAM).
IEEE 802.1ag Ethernet CFM protocols comprise three protocols that work together to help administrators
debug Ethernet networks. These protocols are continuity check, link trace and loopback protocols. CFM
provides network-level OAM and is applicable to large-scaled end-to-end networking.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
oam-mgr
The OAM management view is displayed.
Step 3 Run:
oam-bind ingress cfm md md-name ma ma-name egress sep segment segment-id interface
interface-type interface-number
Association between SEP and CFM is configured.
l md md-name: specifies a maintenance domain (MD). The total length of md-name and maname cannot be greater than 44 characters.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
342
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
l ma ma-name: specifies a maintenance association (MA). The total length of md-name and
ma-name cannot be greater than 44 characters.
l interface must have been added to the SEP segment.
----End
10.5.5 Checking the Configuration
After configuring the topology change notification function, you can view the objects that are
notified of topology changes.
Prerequisite
The configurations of the topology change notification function are complete.
Procedure
l
Run the display sep interface verbose command to check the configuration of reporting
changes in the lower-layer network topology.
Run the display this command in the OAM management view to check the configuration
of reporting changes in the upper-layer network topology.
----End
10.6 Maintaining SEP
This section describes the commands for maintaining SEP, including the commands for clearing
SEP statistics.
10.6.1 Clearing SEP Statistics
You can run the reset command to reset the SEP statistics before recollecting SEP statistics.
Context
CAUTION
SEP statistics cannot be restored after being cleared. Therefore, perform the action with caution.
Procedure
Step 1 Run the reset sep interface interface-type interface-number statistics command in the user view
to clear SEP statistics.
----End
10.6.2 Debugging SEP
When a fault occurs during the running of SEP, run the following debugging command in the
user view to display the debugging information and locate the fault.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
343
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
Context
CAUTION
Debugging affects the performance of the system. So, after debugging, run the undo debugging
all command to disable it immediately.
Procedure
Step 1 Run the debugging sep { all | common | error | machine | message | pdu [ [ epa | lsa | nbr |
preempt ] [ transmit | receive ] ] } [ segment segment-id | interface interface-type interfacenumber ] command in the user view to debug SEP.
----End
10.7 Configuration Examples
This section describes the networking requirements, configuration roadmap, and data
preparation for a typical SEP application and provides the configuration examples.
10.7.1 Example for Configuring SEP on a Closed Ring Network
In the closed ring networking, CE1 is dual homed to a Layer 2 network through multiple Layer
2 switching devices. The two edge devices connected to the upper-layer Layer 2 network are
directly connected to each other. The closed ring network is deployed at the aggregation layer
to implement Layer 2 transparent transmission of unicast and multicast packets. SEP runs at the
aggregation layer to implement link redundancy.
Networking Requirements
Generally, redundant links are used to connect an Ethernet switching network to an upper-layer
network to provide link backup and enhance network reliability. The use of redundant links,
however, may produce loops, causing broadcast storms and rendering the MAC address table
unstable. As a result, the communication quality deteriorates, and communication services may
even be interrupted. SEP can be deployed on the ring network to block redundant links and
unblock them if a link fault occurs.
As shown in Figure 10-11, Layer 2 switching devices LSW1 to LSW5 form a ring network,
which is connected to the core network. SEP runs at the aggregation layer. When the ring network
is normal, SEP blocks the redundant Ethernet links. When a link on the ring fails, SEP can
quickly restore communication between the nodes on the ring.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
344
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
Core
Figure 10-11 Networking diagram of a closed ring SEP network
IP/MPLS Core
GE0/0/3
GE0/0/2
Aggregation
LSW1
GE0/0/1
GE0/0/3
GE0/0/2
LSW5
GE0/0/1
SEP
Segment1
GE0/0/1
GE0/0/1
LSW2
LSW4
GE0/0/2
GE0/0/1
LSW3
GE0/0/2
GE0/0/2
GE0/0/3
Access
GE0/0/1
CE1
VLAN
100
Primary Edge Node
Secondary Edge Node
Block Port
Configuration Roadmap
The configuration roadmap is as follows:
1.
Issue 02 (2011-11-21)
Configure basic SEP functions.
a.
Configure SEP segment 1 on LSW1 to LSW5 and configure VLAN 10 as the control
VLAN of SEP segment 1.
b.
Add all devices on the ring to SEP segment 1, and configure the roles of GE0/0/1 and
GE0/0/3 of LSW1 in SEP segment 1.
c.
On the device where the primary edge port is located, specify that the port with the
highest priority will be blocked.
d.
Set priorities of the ports in the SEP segment.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
345
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
Set the highest priority for GE0/0/2 of LSW3 and retain the default priority of the
other ports so that GE0/0/2 of LSW3 will be blocked.
e.
2.
Configure delayed preemption on the device where the primary edge port is located.
Configure the Layer 2 forwarding function on CE1 and LSW1 to LSW5.
Data Preparation
To complete the configuration, you need the following data:
l
SEP segment ID
Control VLAN of the SEP segment
Port roles in the SEP segment
Preemption mode
Method of selecting the port to block
Priorities of the ports in the SEP segment
Procedure
Step 1 Configure basic SEP functions.
1.
Configure SEP segment 1 on LSW1 to LSW5 and configure VLAN 10 as the control VLAN
of SEP segment 1.
# Configure LSW1.
<Quidway> system-view
[Quidway] sysname LSW1
[LSW1] sep segment 1
[LSW1-sep-segment1] control-vlan 10
[LSW1-sep-segment1] protected-instance all
[LSW1-sep-segment1] quit
# Configure LSW2.
<Quidway> system-view
[Quidway] sysname LSW2
[LSW2] sep segment 1
[LSW2-sep-segment1] control-vlan 10
[LSW2-sep-segment1] protected-instance all
[LSW2-sep-segment1] quit
# Configure LSW3.
<Quidway> system-view
[Quidway] sysname LSW3
[LSW3] sep segment 1
[LSW3-sep-segment1] control-vlan 10
[LSW3-sep-segment1] protected-instance all
[LSW3-sep-segment1] quit
# Configure LSW4.
<Quidway> system-view
[Quidway] sysname LSW4
[LSW4] sep segment 1
[LSW4-sep-segment1] control-vlan 10
[LSW4-sep-segment1] protected-instance all
[LSW4-sep-segment1] quit
# Configure LSW5.
<Quidway> system-view
[Quidway] sysname LSW5
[LSW5] sep segment 1
[LSW5-sep-segment1] control-vlan 10
[LSW5-sep-segment1] protected-instance all
[LSW5-sep-segment1] quit
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
346
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
NOTE
l The control VLAN must be a VLAN that has not been created or used, but the configuration file
automatically displays the command for creating the VLAN.
l Each SEP segment must be configured with a control VLAN. After an interface is added to the
SEP segment configured with a control VLAN, the interface is added to the control VLAN
automatically. The configuration file displays port hybrid tagged vlan under this interface.
2.
Add all devices on the ring to SEP segment 1 and configure port roles on the devices.
NOTE
By default, STP is enabled on a Layer 2 interface. Before adding an interface to the SEP segment,
disable STP on the interface.
# On LSW1, configure GE0/0/1 as the primary edge port and GE0/0/3 as the secondary
edge port.
[LSW1] interface gigabitethernet 0/0/1
[LSW1-GigabitEthernet0/0/1] stp disable
[LSW1-GigabitEthernet0/0/1] sep segment 1 edge primary
[LSW1-GigabitEthernet0/0/1] quit
[LSW1] interface gigabitethernet 0/0/3
[LSW1-GigabitEthernet0/0/3] stp disable
[LSW1-GigabitEthernet0/0/3] sep segment 1 edge secondary
[LSW1-GigabitEthernet0/0/3] quit
# Configure LSW2.
[LSW2] interface gigabitethernet 0/0/1
[LSW2-GigabitEthernet0/0/1] stp disable
[LSW2-GigabitEthernet0/0/1] sep segment 1
[LSW2-GigabitEthernet0/0/1] quit
[LSW2] interface gigabitethernet 0/0/2
[LSW2-GigabitEthernet0/0/2] stp disable
[LSW2-GigabitEthernet0/0/2] sep segment 1
[LSW2-GigabitEthernet0/0/2] quit
# Configure LSW3.
[LSW3] interface gigabitethernet 0/0/1
[LSW3-GigabitEthernet0/0/1] stp disable
[LSW3-GigabitEthernet0/0/1] sep segment 1
[LSW3-GigabitEthernet0/0/1] quit
[LSW3] interface gigabitethernet 0/0/2
[LSW3-GigabitEthernet0/0/2] stp disable
[LSW3-GigabitEthernet0/0/2] sep segment 1
[LSW3-GigabitEthernet0/0/2] quit
# Configure LSW4.
[LSW4] interface gigabitethernet 0/0/1
[LSW4-GigabitEthernet0/0/1] stp disable
[LSW4-GigabitEthernet0/0/1] sep segment 1
[LSW4-GigabitEthernet0/0/1] quit
[LSW4] interface gigabitethernet 0/0/2
[LSW4-GigabitEthernet0/0/2] stp disable
[LSW4-GigabitEthernet0/0/2] sep segment 1
[LSW4-GigabitEthernet0/0/2] quit
# Configure LSW5.
[LSW5] interface gigabitethernet 0/0/1
[LSW5-GigabitEthernet0/0/1] stp disable
[LSW5-GigabitEthernet0/0/1] sep segment 1
[LSW5-GigabitEthernet0/0/1] quit
[LSW5] interface gigabitethernet 0/0/3
[LSW5-GigabitEthernet0/0/3] stp disable
[LSW5-GigabitEthernet0/0/3] sep segment 1
[LSW5-GigabitEthernet0/0/3] quit
3.
Specify a port to block.
# On LSW1 where the primary edge port is located, specify that the port with the highest
priority is blocked.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
347
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
[LSW1] sep segment 1
[LSW1-sep-segment1] block port optimal
4.
Set the priority of GE0/0/2 on LSW3.
[LSW3] interface gigabitethernet 0/0/2
[LSW3-GigabitEthernet0/0/2] sep segment 1 priority 128
[LSW3-GigabitEthernet0/0/2] quit
5.
Configure the preemption mode.
# Configure the delayed preemption mode on LSW1.
[LSW1-sep-segment1] preempt delay 30
[LSW1-sep-segment1] quit
NOTE
l You must set the preemption delay when delayed preemption is adopted because there is no
default delay time.
l After all the faulty ports recover, the edge ports no longer receive fault notification packets. If
the primary edge port does not receive any fault notification packet, it starts the delay timer.
When the delay timer expires, nodes in the SEP segment start blocked port preemption.
To implement delayed preemption in this example, you need to simulate a port fault and then
rectify the fault. For example:
Run the shutdown command on GE0/0/2 of LSW2 to simulate a port fault, and then run the
undo shutdown command on GE0/0/2 to rectify the fault.
Step 2 Configure the Layer 2 forwarding function on CE1 and LSW1 to LSW5.
For details about the configuration, see the configuration files.
Step 3 Verify the configuration.
l Run the shutdown command on GE0/0/1 of LSW3 to simulate a port fault, and then run the
display sep interface command on LSW3 to check whether GE0/0/2 of LSW3 switches from
the Discarding state to the Forwarding state.
<LSW3> display sep interface gigabitethernet 0/0/2
SEP segment 1
---------------------------------------------------------------Interface
Port Role
Neighbor Status
Port Status
---------------------------------------------------------------GE0/0/2
common
up
forwarding
----End
Configuration Files
l
Configuration file of LSW1
#
sysname LSW1
#
vlan batch 10 100 200
#
sep segment 1
control-vlan 10
block port optimal
preempt delay 30
protected-instance 0 to 48
#
interface GigabitEthernet0/0/1
port hybrid tagged vlan 10 100
stp disable
sep segment 1 edge primary
#
interface GigabitEthernet0/0/2
port hybrid pvid vlan 200
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
348
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
port hybrid tagged vlan 100
port hybrid untagged vlan 200
#
interface GigabitEthernet0/0/3
port hybrid tagged vlan 10 100 200
stp disable
sep segment 1 edge secondary
#
return
Configuration file of LSW2
#
sysname LSW2
#
vlan batch 10 100
#
sep segment 1
control-vlan 10
protected-instance 0 to 48
#
interface GigabitEthernet0/0/1
port hybrid tagged vlan 10 100
stp disable
sep segment 1
#
interface GigabitEthernet0/0/2
port hybrid tagged vlan 10 100
stp disable
sep segment 1
#
return
Configuration file of LSW3
#
sysname LSW3
#
vlan batch 10 100
#
sep segment 1
control-vlan 10
protected-instance 0 to 48
#
interface GigabitEthernet0/0/1
port hybrid tagged vlan 10 100
stp disable
sep segment 1
#
interface GigabitEthernet0/0/2
port hybrid tagged vlan 10 100
stp disable
sep segment 1
sep segment 1 priority 128
#
interface GigabitEthernet0/0/3
port hybrid tagged vlan 100
#
return
Configuration file of LSW4
#
sysname LSW4
#
vlan batch 10 100
#
sep segment 1
control-vlan 10
protected-instance 0 to 48
#
interface GigabitEthernet0/0/1
port hybrid tagged vlan 10 100
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
349
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
stp disable
sep segment 1
#
interface GigabitEthernet0/0/2
port hybrid tagged vlan 10 100
stp disable
sep segment 1
#
return
Configuration file of LSW5
#
sysname LSW5
#
vlan batch 10 100 200
#
sep segment 1
control-vlan 10
protected-instance 0 to 48
#
interface GigabitEthernet0/0/1
port hybrid tagged vlan 10 100
stp disable
sep segment 1
#
interface GigabitEthernet0/0/2
port hybrid pvid vlan 200
port hybrid tagged vlan 100
port hybrid untagged vlan 200
#
interface GigabitEthernet0/0/3
port hybrid tagged vlan 10 100 200
stp disable
sep segment 1
#
return
Configuration file of CE1
#
sysname CE1
#
vlan batch 100
#
interface GigabitEthernet0/0/1
port hybrid tagged vlan 100
#
return
10.7.2 Example for Configuring SEP on a Multi-ring Network
In multi-ring networking, multiple rings consisting of Layer 2 switching devices are deployed
at the access layer and aggregation layer. SEP runs at the access layer and aggregation layer to
implement link redundancy.
Networking Requirements
Generally, redundant links are used to connect an Ethernet switching network to an upper-layer
network to provide link backup and enhance network reliability. The use of redundant links,
however, may produce loops, causing broadcast storms and rendering the MAC address table
unstable. As a result, the communication quality deteriorates, and communication services may
even be interrupted. SEP can be deployed on the ring network to block redundant links and
unblock them if a link fault occurs.
As shown in Figure 10-12, multiple Layer 2 switching devices form ring networks at the access
layer and aggregation layer. The ring network at the aggregation layer is connected to the core
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
350
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
layer. SEP runs at the access layer and aggregation layer. When the ring network is normal, SEP
blocks the redundant Ethernet links. When a link on the ring fails, SEP can quickly restore
communication between the nodes on the ring.
Core
Figure 10-12 Networking diagram of a multi-ring SEP network
IP/MPLS Core
GE0/0/2
GE0/0/2
GE0/0/3 GE0/0/3
LSW1
Aggregation
GE0/0/1
GE0/0/1
LSW2
GE0/0/2
LSW6
GE0/0/2
GE0/0/3
LSW4
GE0/0/1
G
GE0/0/2
E0
/0 LSW3
/3
GE0/0/4
GE0/0/2
GE0/0/1
Se S
gm EP
GE0/0/2
en
t3
LSW8
GE0/0/1
GE0/0/2
GE0/0/1
GE0/0/2
LSW11
GE0/0/1
LSW9 GE0/0/1
GE0/0/1
GE0/0/2
LSW7 GE0/0/3
LSW10 GE0/0/3
GE0/0/1
GE0/0/1
CE2
VLAN
200
Issue 02 (2011-11-21)
GE0/0/1
Se S
gm EP
en
t2
GE0/0/1
Access
SEP
Segment 1
LSW5
CE1
VLAN
100
Primary Edge Node
Control VLAN 10
Secondary Edge Node
Control VLAN 20
Block Port
Control VLAN 30
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
351
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
Configuration Roadmap
The configuration roadmap is as follows:
1.
Configure basic SEP functions.
a.
Configure SEP segments 1 to 3 and configure VLAN 10, VLAN 20, and VLAN 30
as their control VLANs.
l Configure SEP segment 1 on LSW1 to LSW5 and configure VLAN 10 as the
control VLAN of SEP segment 1.
l Configure SEP segment 2 on LSW2, LSW3, and LSW6 to LSW8, and configure
VLAN 20 as the control VLAN of SEP segment 2.
l Configure SEP segment 3 on LSW3, LSW4, and LSW9 to LSW11, and configure
VLAN 30 as the control VLAN of SEP segment 3.
b.
Add devices on the rings to the SEP segments and configure port roles on the edge
devices of the SEP segments.
l On LSW1 to LSW5, add the interfaces on the ring at the access layer to SEP
segment 1. Configure the roles of GE0/0/1 and GE0/0/3 of LSW1 in SEP segment
1.
l Add GE0/0/2 of LSW2, GE0/0/1 and GE0/0/2 of LSW6 to LSW8, and GE0/0/2
of LSW3 to SEP segment 2. Configure the roles of GE0/0/2 of LSW2 and GE0/0/2
of LSW3 in SEP segment 2.
l Add GE0/0/1 of LSW3, GE0/0/1 and GE0/0/2 of LSW9 to LSW11, and GE0/0/1
of LSW4 to SEP segment 3. Configure the roles of GE0/0/1 of LSW2 and GE0/0/1
of LSW3 in SEP segment 3.
c.
Specify the port to block on the device where the primary edge port is located.
l In SEP segment 1, specify that the port with the highest priority will be blocked.
l In SEP segment 2, specify the device name and port name to block the specified
port.
l In SEP segment 3, specify that the blocked port be selected according to the
configured hop counts of ports.
d.
Configure the preemption mode on the device where the primary edge port is located.
Configure delayed preemption in SEP segment 1 and manual preemption in SEP
segment 2 and SEP segment 3.
e.
2.
Configure the topology change notification function on the edge devices between SEP
segments, namely, LSW2, LSW3, and LSW4.
Configure the Layer 2 forwarding function on CE1, CE2, and LSW1 to LSW11.
Data Preparation
To complete the configuration, you need the following data:
l
SEP segment ID
Control VLAN of the SEP segment
Port roles in the SEP segment
Preemption mode
Method of selecting the port to block
Priorities of the ports in the SEP segment
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
352
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
Procedure
Step 1 Configure basic SEP functions.
1.
Configure SEP segments 1 to 3 and configure VLAN 10, VLAN 20, and VLAN 30 as their
control VLANs, as shown in Figure 10-12.
# Configure LSW1.
<Quidway> system-view
[Quidway] sysname LSW1
[LSW1] sep segment 1
[LSW1-sep-segment1] control-vlan 10
[LSW1-sep-segment1] protected-instance all
[LSW1-sep-segment1] quit
# Configure LSW2.
<Quidway> system-view
[Quidway] sysname LSW2
[LSW2] sep segment 1
[LSW2-sep-segment1] control-vlan 10
[LSW2-sep-segment1] protected-instance all
[LSW2-sep-segment1] quit
[LSW2] sep segment 2
[LSW2-sep-segment2] control-vlan 20
[LSW2-sep-segment2] protected-instance all
[LSW2-sep-segment2] quit
# Configure LSW3.
<Quidway> system-view
[Quidway] sysname LSW3
[LSW3] sep segment 1
[LSW3-sep-segment1] control-vlan 10
[LSW3-sep-segment1] protected-instance all
[LSW3-sep-segment1] quit
[LSW3] sep segment 2
[LSW3-sep-segment2] control-vlan 20
[LSW3-sep-segment2] protected-instance all
[LSW3-sep-segment2] quit
[LSW3] sep segment 3
[LSW3-sep-segment3] control-vlan 30
[LSW3-sep-segment3] protected-instance all
[LSW3-sep-segment3] quit
# Configure LSW4.
<Quidway> system-view
[Quidway] sysname LSW4
[LSW4] sep segment 1
[LSW4-sep-segment1] control-vlan 10
[LSW4-sep-segment1] protected-instance all
[LSW4-sep-segment1] quit
[LSW4] sep segment 3
[LSW4-sep-segment3] control-vlan 30
[LSW4-sep-segment3] protected-instance all
[LSW4-sep-segment3] quit
# Configure LSW5.
<Quidway> system-view
[Quidway] sysname LSW5
[LSW5] sep segment 1
[LSW5-sep-segment1] control-vlan 10
[LSW5-sep-segment1] protected-instance all
[LSW5-sep-segment1] quit
# Configure LSW6 to LSW11.
The configurations of LSW6 to LSW11 are similar to the configurations of LSW1 to LSW5
except for the control VLANs of different SEP segments.
For details about the configuration, see the configuration files.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
353
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
NOTE
l The control VLAN must be a VLAN that has not been created or used, but the configuration file
automatically displays the command for creating the VLAN.
l Each SEP segment must be configured with a control VLAN. After an interface is added to the
SEP segment configured with a control VLAN, the interface is added to the control VLAN
automatically. The configuration file displays port hybrid tagged vlan under this interface.
2.
Add devices on the rings to the SEP segments and configure port roles according to Figure
10-12.
NOTE
By default, STP is enabled on a Layer 2 interface. Before adding an interface to the SEP segment,
disable STP on the interface.
# On LSW1, configure GE0/0/1 as the primary edge port and GE0/0/3 as the secondary
edge port.
[LSW1] interface gigabitethernet 0/0/1
[LSW1-GigabitEthernet0/0/1] stp disable
[LSW1-GigabitEthernet0/0/1] sep segment 1 edge primary
[LSW1-GigabitEthernet0/0/1] quit
[LSW1] interface gigabitethernet 0/0/3
[LSW1-GigabitEthernet0/0/3] stp disable
[LSW1-GigabitEthernet0/0/3] sep segment 1 edge secondary
[LSW1-GigabitEthernet0/0/3] quit
# Configure LSW2.
[LSW2] interface gigabitethernet 0/0/1
[LSW2-GigabitEthernet0/0/1] stp disable
[LSW2-GigabitEthernet0/0/1] sep segment 1
[LSW2-GigabitEthernet0/0/1] quit
[LSW2] interface gigabitethernet 0/0/3
[LSW2-GigabitEthernet0/0/3] stp disable
[LSW2-GigabitEthernet0/0/3] sep segment 1
[LSW2-GigabitEthernet0/0/3] quit
[LSW2] interface gigabitethernet 0/0/2
[LSW2-GigabitEthernet0/0/2] stp disable
[LSW2-GigabitEthernet0/0/2] sep segment 2 edge primary
[LSW2-GigabitEthernet0/0/2] quit
# Configure LSW3.
[LSW3] interface gigabitethernet 0/0/3
[LSW3-GigabitEthernet0/0/3] stp disable
[LSW3-GigabitEthernet0/0/3] sep segment
[LSW3-GigabitEthernet0/0/3] quit
[LSW3] interface gigabitethernet 0/0/4
[LSW3-GigabitEthernet0/0/4] stp disable
[LSW3-GigabitEthernet0/0/4] sep segment
[LSW3-GigabitEthernet0/0/4] quit
[LSW3] interface gigabitethernet 0/0/2
[LSW3-GigabitEthernet0/0/2] stp disable
[LSW3-GigabitEthernet0/0/2] sep segment
[LSW3-GigabitEthernet0/0/2] quit
[LSW3] interface gigabitethernet 0/0/1
[LSW3-GigabitEthernet0/0/1] stp disable
[LSW3-GigabitEthernet0/0/1] sep segment
[LSW3-GigabitEthernet0/0/1] quit
2 edge secondary
3 edge secondary
# Configure LSW4.
[LSW4] interface gigabitethernet 0/0/2
[LSW4-GigabitEthernet0/0/2] stp disable
[LSW4-GigabitEthernet0/0/2] sep segment 1
[LSW4-GigabitEthernet0/0/2] quit
[LSW4] interface gigabitethernet 0/0/3
[LSW4-GigabitEthernet0/0/3] stp disable
[LSW4-GigabitEthernet0/0/3] sep segment 1
[LSW4-GigabitEthernet0/0/3] quit
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
354
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
[LSW4] interface gigabitethernet 0/0/1
[LSW4-GigabitEthernet0/0/1] stp disable
[LSW4-GigabitEthernet0/0/1] sep segment 3 edge primary
[LSW4-GigabitEthernet0/0/1] quit
# Configure LSW5.
[LSW5] interface gigabitethernet 0/0/1
[LSW5-GigabitEthernet0/0/1] stp disable
[LSW5-GigabitEthernet0/0/1] sep segment 1
[LSW5-GigabitEthernet0/0/1] quit
[LSW5] interface gigabitethernet 0/0/3
[LSW5-GigabitEthernet0/0/3] stp disable
[LSW5-GigabitEthernet0/0/3] sep segment 1
[LSW5-GigabitEthernet0/0/3] quit
# Configure LSW6 to LSW11.
The configurations of LSW6 to LSW11 are similar to the configurations of LSW1 to LSW5
except for the port roles.
For details about the configuration, see the configuration files.
3.
Specify the port to block.
# On LSW1 where the primary edge port of SEP segment 1 is located, specify that the port
with the highest priority be blocked.
[LSW1] sep segment 1
[LSW1-sep-segment1] block port optimal
[LSW1-sep-segment1] quit
# On LSW3, set the priority of GE0/0/4 to 128, which is the highest priority among the
ports so that GE0/0/4 will be blocked.
[LSW3] interface gigabitethernet 0/0/4
[LSW3-GigabitEthernet0/0/4] sep segment 1 priority 128
[LSW3-GigabitEthernet0/0/4] quit
Use the default priority for the other ports in SEP segment 1.
# On LSW2 where the primary edge port of SPE segment 2 is located, specify the device
name and port name so that the specified port will be blocked.
Before specifying the port to block, you can use the display sep topology command to
view the current topology information and obtain information about all the ports in the
topology. Then you can select the device name and port name.
[LSW2] sep segment 2
[LSW2-sep-segment2] block port sysname LSW7 interface gigabitethernet 0/0/1
[LSW2-sep-segment2] quit
# On LSW4 where the primary edge port of SEP segment 3 is located, specify that the
blocked port be selected according to the configured hop counts of ports.
[LSW4] sep segment 3
[LSW4-sep-segment3] block port hop 5
[LSW4-sep-segment3] quit
NOTE
SEP sets the hop count of the primary edge port to 1 and the hop count of the secondary edge port
to 2. Hop counts of other ports increase at a step of 1 in the downstream direction of the primary port.
4.
Configure the preemption mode.
# Configure the delayed preemption mode on LSW1.
[LSW1] sep segment 1
[LSW1-sep-segment1] preempt delay 30
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
355
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
NOTE
l You must set the preemption delay when delayed preemption is adopted because there is no
default delay time.
l After all the faulty ports recover, the edge ports no longer receive fault notification packets. If
the primary edge port does not receive any fault notification packet, it starts the delay timer.
When the delay timer expires, nodes in the SEP segment start blocked port preemption.
To implement delayed preemption in this example, you need to simulate a port fault and then
rectify the fault. For example:
Run the shutdown command on GE0/0/2 of LSW2 to simulate a port fault, and then run the
undo shutdown command on GE0/0/2 to rectify the fault.
# Configure the manual preemption mode on LSW2.
[LSW2] sep segment 2
[LSW2-sep-segment2] preempt manual
# Configure the manual preemption mode on LSW4.
[LSW4] sep segment 3
[LSW4-sep-segment3] preempt manual
5.
Configure the topology change notification function.
# Configure SEP segment 2 to notify SEP segment 1 of topology changes.
# Configure LSW2.
[LSW2] sep segment 2
[LSW2-sep-segment2] tc-notify segment 1
[LSW2-sep-segment2] quit
# Configure LSW3.
[LSW3] sep segment 2
[LSW3-sep-segment2] tc-notify segment 1
[LSW3-sep-segment2] quit
# Configure SEP segment 3 to notify SEP segment 1 of topology changes.
# Configure LSW3.
[LSW3] sep segment 3
[LSW3-sep-segment3] tc-notify segment 1
[LSW3-sep-segment3] quit
# Configure LSW4.
[LSW4] sep segment 3
[LSW4-sep-segment3] tc-notify segment 1
[LSW4-sep-segment3] quit
NOTE
The topology change notification function is configured on edge devices between SEP segments so
that the upper-layer network can be notified of topology changes on the lower-layer network.
Step 2 Configure the Layer 2 forwarding function on the CEs and LSW1 to LSW11.
For details about the configuration, see the configuration files.
Step 3 Verify the configuration.
After completing the preceding configurations, do as follows to verify the configuration. LSW1
is taken as an example.
l Run the shutdown command on GE0/0/1 of LSW2 to simulate a port fault, and then run the
display sep interface command on LSW3 to check whether GE0/0/4 of LSW3 switches from
the Discarding state to the Forwarding state.
<LSW3> display sep interface gigabitethernet 0/0/4
SEP segment 1
----------------------------------------------------------------
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
356
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
Interface
Port Role
Neighbor Status
Port Status
---------------------------------------------------------------GE0/0/4
common
up
forwarding
----End
Configuration Files
l
Configuration file of LSW1
#
sysname LSW1
#
vlan batch 10 100 200 300
#
sep segment 1
control-vlan 10
block port optimal
preempt delay 30
protected-instance 0 to 48
#
interface GigabitEthernet0/0/1
port hybrid tagged vlan 10 100 200
stp disable
sep segment 1 edge primary
#
interface GigabitEthernet0/0/2
port hybrid pvid vlan 300
port hybrid tagged vlan 100 200
port hybrid untagged vlan 300
#
interface GigabitEthernet0/0/3
port hybrid tagged vlan 10 100 200 300
stp disable
sep segment 1 edge secondary
#
return
Configuration file of LSW2
#
sysname LSW2
#
vlan batch 10 20 100 200
#
sep segment 1
control-vlan 10
protected-instance 0 to 48
sep segment 2
control-vlan 20
block port sysname LSW7 interface GigabitEthernet0/0/1
tc-notify segment 1
protected-instance 0 to 48
#
interface GigabitEthernet0/0/1
port hybrid tagged vlan 10 100 200
stp disable
sep segment 1
#
interface GigabitEthernet0/0/2
port hybrid tagged vlan 20 200
stp disable
sep segment 2 edge primary
#
interface GigabitEthernet0/0/3
port hybrid tagged vlan 10 100 200
stp disable
sep segment 1
#
return
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
357
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
Configuration file of LSW3
#
sysname LSW3
#
vlan batch 10 20 30 100 200
#
sep segment 1
control-vlan 10
protected-instance 0 to 48
sep segment 2
control-vlan 20
tc-notify segment 1
protected-instance 0 to 48
sep segment 3
control-vlan 30
tc-notify segment 1
protected-instance 0 to 48
#
interface GigabitEthernet0/0/1
port hybrid tagged vlan 30 100
stp disable
sep segment 3 edge secondary
#
interface GigabitEthernet0/0/2
port hybrid tagged vlan 20 200
stp disable
sep segment 2 edge secondary
#
interface GigabitEthernet0/0/3
port hybrid tagged vlan 10 100 200
stp disable
sep segment 1
#
interface GigabitEthernet0/0/4
port hybrid tagged vlan 10 100 200
stp disable
sep segment 1
sep segment 1 priority 128
#
return
Configuration file of LSW4
#
sysname LSW4
#
vlan batch 10 30 100 200
#
sep segment 1
control-vlan 10
protected-instance 0 to 48
sep segment 2
control-vlan 30
protected-instance 0 to 48
sep segment 3
control-vlan 30
block port hop 5
tc-notify segment 1
protected-instance 0 to 48
#
interface GigabitEthernet0/0/1
port hybrid tagged vlan 30 100
stp disable
sep segment 3 edge primary
#
interface GigabitEthernet0/0/2
port hybrid tagged vlan 10 100 200
stp disable
sep segment 1
#
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
358
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
interface GigabitEthernet0/0/3
port hybrid tagged vlan 10 100 200
stp disable
sep segment 1
#
return
Configuration file of LSW5
#
sysname LSW5
#
vlan batch 10 100 200 300
#
sep segment 1
control-vlan 10
protected-instance 0 to 48
#
interface GigabitEthernet0/0/1
port hybrid tagged vlan 10 100 200
stp disable
sep segment 1
#
interface GigabitEthernet0/0/2
port hybrid pvid vlan 300
port hybrid tagged vlan 100 200
port hybrid untagged vlan 300
#
interface GigabitEthernet0/0/3
port hybrid tagged vlan 10 100 200 300
stp disable
sep segment 1
#
return
Configuration file of LSW6
#
sysname LSW6
#
vlan batch 20 200
#
sep segment 2
control-vlan 20
protected-instance 0 to 48
#
interface GigabitEthernet0/0/1
port hybrid tagged vlan 20 200
stp disable
sep segment 2
#
interface GigabitEthernet0/0/2
port hybrid tagged vlan 20 200
stp disable
sep segment 2
#
return
Configuration file of LSW7
#
sysname LSW7
#
vlan batch 20 200
#
sep segment 2
control-vlan 20
protected-instance 0 to 48
#
interface GigabitEthernet0/0/1
port hybrid tagged vlan 20 200
stp disable
sep segment 2
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
359
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
#
interface GigabitEthernet0/0/2
port hybrid tagged vlan 20 200
stp disable
sep segment 2
#
interface GigabitEthernet0/0/3
port hybrid tagged vlan 200
#
return
Configuration file of LSW8
#
sysname LSW8
#
vlan batch 20 200
#
sep segment 2
control-vlan 20
protected-instance 0 to 48
#
interface GigabitEthernet0/0/1
port hybrid tagged vlan 20 200
stp disable
sep segment 2
#
interface GigabitEthernet0/0/2
port hybrid tagged vlan 20 200
stp disable
sep segment 2
#
return
Configuration file of LSW9
#
sysname LSW9
#
vlan batch 30 100
#
sep segment 3
control-vlan 30
protected-instance 0 to 48
#
interface GigabitEthernet0/0/1
port hybrid tagged vlan 30 100
stp disable
sep segment 3
#
interface GigabitEthernet0/0/2
port hybrid tagged vlan 30 100
stp disable
sep segment 3
#
return
Configuration file of LSW10
#
sysname LSW10
#
vlan batch 30 100
#
sep segment 3
control-vlan 30
protected-instance 0 to 48
#
interface GigabitEthernet0/0/1
port hybrid tagged vlan 30 100
stp disable
sep segment 3
#
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
360
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
interface GigabitEthernet0/0/2
port hybrid tagged vlan 30 100
stp disable
sep segment 3
#
interface GigabitEthernet0/0/3
port hybrid tagged vlan 100
#
return
Configuration file of LSW11
#
sysname LSW11
#
vlan batch 30 100
#
sep segment 3
control-vlan 30
protected-instance 0 to 48
#
interface GigabitEthernet0/0/1
port hybrid tagged vlan 30 100
stp disable
sep segment 3
#
interface GigabitEthernet0/0/2
port hybrid tagged vlan 30 100
stp disable
sep segment 3
#
return
Configuration file of CE1
#
sysname CE1
#
vlan batch 100
#
interface GigabitEthernet0/0/1
port hybrid tagged vlan 100
#
return
Configuration file of CE2
#
sysname CE2
#
vlan batch 200
#
interface GigabitEthernet0/0/1
port hybrid tagged vlan 200
#
return
10.7.3 Example for Configuring SEP on a Hybrid-ring Network
In the networking of this configuration example, the two devices where the access layer and the
aggregation layer are intersected do not support SEP. You can configure SEP at the access layer
to implement redundancy protection switching and configure the function of advertising
topology changes on an edge device in a SEP segment. This helps an upper-layer network to
detect topology changes of a lower-layer network in time.
Networking Requirements
Generally, redundant links are used to connect an Ethernet switching network to an upper-layer
network to provide link backup and enhance network reliability. The use of redundant links,
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
361
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
however, may produce loops, causing broadcast storms and rendering the MAC address table
unstable. As a result, the communication quality deteriorates, and communication services may
even be interrupted. SEP can be deployed on the ring network to block redundant links and
unblock them if a link fault occurs.
NOTE
In this example, devices at the aggregation layer run the MSTP protocol.
As shown in Figure 10-13, multiple Layer 2 switching devices form a ring at the access layer,
and multiple Layer 3 devices form a ring at the aggregation layer, which is connected to the core
layer. In this case, SEP needs to run at the access layer to implement the following functions:
l
When there is no faulty link on the ring network, SEP helps to eliminate loops.
When a link fault occurs on the ring network, SEP helps to rapidly restore the
communication between nodes.
The function of advertising topology changes should be configured on an edge device in a
SEP segment. This helps an upper-layer network to detect topology changes of a lowerlayer network in time.
After receiving a message indicating topology changes of a lower-layer network, a device on an
upper-layer network sends TC packets locally to instruct the other devices to clear associated
MAC addresses and relearn MAC addresses after the topology of the lower-layer network
changes. This ensures nonstop traffic forwarding.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
362
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
Figure 10-13 Networking diagram of a hybrid-ring SEP network
Core
IP/MPLS Core
GE0/0/2
Aggregation
GE0/0/3
GE0/0/3
PE4
GE0/0/1
GE0/0/2
PE3
GE0/0/1
MSTP
PE2 GE0/0/2
PE1
GE0/0/2
GE0/0/3
Do not Support SEP
GE0/0/1
GE0/0/1
SEP
Segment1
LSW1
LSW2
GE0/0/2
GE0/0/2
GE0/0/2
Access
GE0/0/1
GE0/0/1
GE0/0/1
LSW3
GE0/0/3
GE0/0/1
CE
VLAN100
No-neighbor Primary Edge Node
No-neighbor Secondary Edge Node
Block Port(SEP)
Block Port(MSTP)
Configuration Roadmap
The configuration roadmap is as follows:
1.
Issue 02 (2011-11-21)
Configure basic SEP functions.
a.
Configure SEP segment 1 on LSW1 to LSW3 and configure VLAN 10 as the control
VLAN of SEP segment 1.
b.
Add LSW1 to LSW3 to SEP segment 1 and configure port roles on the edge devices
of the SEP segment, namely, LSW1 and LSW2.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
363
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
NOTE
PE1 and PE2 do not support the SEP protocol; therefore, the ports of LSW1 and LSW2
connected to the PEs must be no-neighbor edge ports.
2.
3.
c.
On the device where the no-neighbor primary edge port is located, specify the port in
the middle of the SEP segment as the port to block.
d.
Configure manual preemption.
e.
Configure the topology change notification function so that the upper-layer network
running MSTP can be notified of topology changes in the SEP segment.
Configure basic MSTP functions.
a.
Add PE1 to PE4 to an MST region RG1.
b.
Create VLANs on PE1 to PE4 and add interfaces on the STP ring to the VLANs.
c.
Configure PE3 as the root bridge and PE4 as the backup root bridge.
Configure the Layer 2 forwarding function on CE1 and LSW1 to LSW3.
Data Preparation
To complete the configuration, you need the following data:
l
SEP segment ID
Control VLAN of the SEP segment
Port roles in the SEP segment
Preemption mode
Method of selecting the port to block
MST region name, MSTI ID, and priorities of the PEs in the region
Procedure
Step 1 Configure basic SEP functions.
1.
Configure SEP segment 1 on LSW1 to LSW5 and configure VLAN 10 as the control VLAN
of SEP segment 1.
# Configure LSW1.
<Quidway> system-view
[Quidway] sysname LSW1
[LSW1] sep segment 1
[LSW1-sep-segment1] control-vlan 10
[LSW1-sep-segment1] protected-instance all
[LSW1-sep-segment1] quit
# Configure LSW2.
<Quidway> system-view
[Quidway] sysname LSW2
[LSW2] sep segment 1
[LSW2-sep-segment1] control-vlan 10
[LSW2-sep-segment1] protected-instance all
[LSW2-sep-segment1] quit
# Configure LSW3.
<Quidway> system-view
[Quidway] sysname LSW3
[LSW3] sep segment 1
[LSW3-sep-segment1] control-vlan 10
[LSW3-sep-segment1] protected-instance all
[LSW3-sep-segment1] quit
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
364
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
NOTE
l The control VLAN must be a VLAN that has not been created or used, but the configuration file
automatically displays the command for creating the VLAN.
l Each SEP segment must be configured with a control VLAN. After an interface is added to the
SEP segment configured with a control VLAN, the interface is added to the control VLAN
automatically. The configuration file displays port hybrid tagged vlan under this interface.
2.
Add LSW1 to LSW3 to SEP segment 1 and configure port roles.
# Configure LSW1.
[LSW1] interface gigabitethernet 0/0/1
[LSW1-GigabitEthernet0/0/1] sep segment 1 edge no-neighbor primary
[LSW1-GigabitEthernet0/0/1] quit
[LSW1] interface gigabitethernet 0/0/2
[LSW1-GigabitEthernet0/0/2] stp disable
[LSW1-GigabitEthernet0/0/2] sep segment 1
[LSW1-GigabitEthernet0/0/2] quit
# Configure LSW2.
[LSW2] interface gigabitethernet 0/0/1
[LSW2-GigabitEthernet0/0/1] sep segment 1 edge no-neighbor secondary
[LSW2-GigabitEthernet0/0/1] quit
[LSW2] interface gigabitethernet 0/0/2
[LSW2-GigabitEthernet0/0/2] stp disable
[LSW2-GigabitEthernet0/0/2] sep segment 1
[LSW2-GigabitEthernet0/0/2] quit
# Configure LSW3.
[LSW3] interface gigabitethernet 0/0/1
[LSW3-GigabitEthernet0/0/1] stp disable
[LSW3-GigabitEthernet0/0/1] sep segment 1
[LSW3-GigabitEthernet0/0/1] quit
[LSW3] interface gigabitethernet 0/0/2
[LSW3-GigabitEthernet0/0/2] stp disable
[LSW3-GigabitEthernet0/0/2] sep segment 1
[LSW3-GigabitEthernet0/0/2] quit
3.
Specify the port to block.
# On LSW1 where the no-neighbor primary edge port of SEP segment 1 is located, specify
the port in the middle of the SEP segment as the port to block.
[LSW1] sep segment 1
[LSW1-sep-segment1] block port middle
4.
Configure the preemption mode.
# Configure the manual preemption mode on LSW1.
[LSW1-sep-segment1] preempt manual
5.
Configure the topology change notification function.
# Configure SEP segment 1 to notify the MSTP network of topology changes.
# Configure LSW1.
[LSW1-sep-segment1] tc-notify stp
[LSW1-sep-segment1] quit
# Configure LSW2.
[LSW2] sep segment 1
[LSW2-sep-segment1] tc-notify stp
[LSW2-sep-segment1] quit
After completing the preceding configurations, do as follows to verify the configuration. LSW1
is taken as an example.
l Run the display sep topology command on LSW1 to view detailed topology information of
the SEP segment.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
365
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
The topology information shows that GE0/0/2 of LSW3 is in Discarding state, and the other
ports are in Forwarding state.
<LSW1> display sep topology
SEP segment 1
---------------------------------------------------------------System Name
Port Name
Port Role
Port Status
---------------------------------------------------------------LSW1
GE0/0/1
*primary
forwarding
LSW1
GE0/0/2
common
forwarding
LSW3
GE0/0/1
common
forwarding
LSW3
GE0/0/2
common
discarding
LSW2
GE0/0/1
common
forwarding
LSW2
GE0/0/2
*secondary
forwarding
Step 2 Configure basic MSTP functions.
1.
Configure an MST region
# Configure PE1.
<Quidway> system-view
[Quidway] sysname PE1
[PE1] stp region-configuration
[PE1-mst-region] region-name RG1
[PE1-mst-region] active region-configuration
[PE1-mst-region] quit
# Configure PE2.
<Quidway> system-view
[Quidway] sysname PE2
[PE2] stp region-configuration
[PE2-mst-region] region-name RG1
[PE2-mst-region] active region-configuration
[PE2-mst-region] quit
# Configure PE3.
<Quidway> system-view
[Quidway] sysname PE3
[PE3] stp region-configuration
[PE3-mst-region] region-name RG1
[PE3-mst-region] active region-configuration
[PE3-mst-region] quit
# Configure PE4.
<Quidway> system-view
[Quidway] sysname PE4
[PE4] stp region-configuration
[PE4-mst-region] region-name RG1
[PE4-mst-region] active region-configuration
[PE4-mst-region] quit
2.
Create VLANs and add interfaces to VLANs.
# On PE1, create VLAN 100 and add GE0/0/1, GE0/0/2, and GE0/0/3 to VLAN 100.
[PE1] vlan 100
[PE1-vlan100] quit
[PE1] interface gigabitethernet
[PE1-GigabitEthernet0/0/1] port
[PE1-GigabitEthernet0/0/1] quit
[PE1] interface gigabitethernet
[PE1-GigabitEthernet0/0/2] port
[PE1-GigabitEthernet0/0/2] quit
[PE1] interface gigabitethernet
[PE1-GigabitEthernet0/0/3] port
[PE1-GigabitEthernet0/0/3] quit
0/0/1
hybrid tagged vlan 100
0/0/2
hybrid tagged vlan 100
0/0/3
hybrid tagged vlan 100
# On PE2, PE3, and PE4, create VLAN 100 and add GE0/0/1, GE0/0/2, and GE0/0/3 to
VLAN 100.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
366
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
The configuration of PE2, PE3, and PE3 is similar to the configuration of PE1. For details
about the configuration, see the configuration files.
3.
Enable MSTP.
# Configure PE1.
[PE1] stp enable
# Configure PE2.
[PE2] stp enable
# Configure PE3.
[PE3] stp enable
# Configure PE4.
[PE4] stp enable
4.
Configure PE3 as the root bridge and PE4 as the backup root bridge.
# Set the priority of PE3 to 0 in MSTI0 to ensure that PE3 functions as the root bridge.
[PE3] stp instance 0 priority 0
[PE3] stp root primary
# Set the priority of PE4 to 4096 in MSTI0 to ensure that PE4 functions as the backup root
bridge.
[PE4] stp instance 0 priority 4096
[PE4] stp root secondary
After the configuration is complete, run the display stp brief command on PE2 to check whether
GE0/0/3 is blocked.
<PE4> display stp brief
MSTID Port
0
GigabitEthernet0/0/1
0
GigabitEthernet0/0/2
0
GigabitEthernet0/0/3
Role STP State
DESI FORWARDING
ROOT FORWARDING
ALTE DISCARDING
Protection
NONE
NONE
NONE
Step 3 Configure the Layer 2 forwarding function on the CE and LSW1 to LSW3.
For details about the configuration, see the configuration files.
Step 4 Verify the configuration.
After the configurations are complete and network become stable, run the following commands
to verify the configuration. LSW1 is taken as an example.
l Run the shutdown command on GE0/0/1 of LSW2 to simulate a port fault, and then run the
display sep interface command on LSW3 to check whether GE0/0/2 of LSW3 switches from
the Discarding state to the Forwarding state.
<LSW3> display sep interface gigabitethernet 0/0/2
SEP segment 1
---------------------------------------------------------------Interface
Port Role
Neighbor Status
Port Status
---------------------------------------------------------------GE0/0/2
common
up
forwarding
----End
Configuration Files
l
Configuration file of LSW1
#
sysname LSW1
#
vlan batch 10 100
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
367
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
#
sep segment 1
control-vlan 10
block port middle
tc-notify stp
protected-instance 0 to 48
#
interface GigabitEthernet0/0/1
port hybrid tagged vlan 10 100
stp disable
sep segment 1 no-neighbor edge primary
#
interface GigabitEthernet0/0/2
port hybrid tagged vlan 10 100
stp disable
sep segment 1
#
return
Configuration file of LSW2
#
sysname LSW2
#
vlan batch 10 100
#
sep segment 1
control-vlan 10
tc-notify stp
protected-instance 0 to 48
#
interface GigabitEthernet0/0/2
port hybrid tagged vlan 10 100
stp disable
sep segment 1
#
interface GigabitEthernet0/0/1
port hybrid tagged vlan 10 100
stp disable
sep segment 1 no-neighbor edge secondary
#
return
Configuration file of LSW3
#
sysname LSW3
#
vlan batch 10 100
#
sep segment 1
control-vlan 10
protected-instance 0 to 48
#
interface GigabitEthernet0/0/1
port hybrid tagged vlan 10 100
stp disable
sep segment 1
#
interface GigabitEthernet0/0/2
port hybrid tagged vlan 10 100
stp disable
sep segment 1
#
interface GigabitEthernet0/0/3
port hybrid tagged vlan vlan 100
#
return
Configuration file of PE1
#
sysname PE1
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
368
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
#
vlan batch 100
#
stp enable
#
stp region-configuration
region-name RG1
active region-configuration
#
interface GigabitEthernet0/0/1
port hybrid tagged vlan 100
#
interface GigabitEthernet0/0/2
port hybrid tagged vlan 100
#
interface GigabitEthernet0/0/3
port hybrid tagged vlan 100
#
return
Configuration file of PE2
#
sysname PE2
#
vlan batch 100
#
stp enable
#
stp region-configuration
region-name RG1
active region-configuration
#
interface GigabitEthernet0/0/1
port hybrid tagged vlan 100
#
interface GigabitEthernet0/0/2
port hybrid tagged vlan 100
#
interface GigabitEthernet0/0/3
port hybrid tagged vlan 100
#
return
Configuration file of PE3
#
sysname PE3
#
vlan batch 100 200
#
stp instance 0 root primary
stp enable
#
stp region-configuration
region-name RG1
active region-configuration
#
interface GigabitEthernet0/0/1
port hybrid tagged vlan 100
#
interface GigabitEthernet0/0/2
port hybrid tagged vlan 100 200
#
interface GigabitEthernet0/0/3
port hybrid pvid vlan 200
port hybrid tagged vlan 100
port hybrid untagged vlan 200
#
return
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
369
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
Configuration file of PE4
#
sysname PE4
#
vlan batch 100 200
#
stp instance 0 root secondary
stp enable
#
stp region-configuration
region-name RG1
active region-configuration
#
interface GigabitEthernet0/0/1
port hybrid tagged vlan 100
#
interface GigabitEthernet0/0/2
port hybrid tagged vlan 100 200
#
interface GigabitEthernet0/0/3
port hybrid pvid vlan 200
port hybrid tagged vlan 100
port hybrid untagged vlan 200
#
return
Configuration file of CE1
#
sysname CE1
#
vlan batch 100
#
interface GigabitEthernet0/0/1
port hybrid tagged vlan 100
#
return
10.7.4 Example for Configuring a Hybrid SEP+RRPP Ring Network
(Reporting the Topology Changes of a Lower-Layer Network)
In the networking of this configuration example, you can configure SEP at the access layer to
implement redundancy protection switching and configure the function of advertising topology
changes on an edge device in a SEP segment. This helps an upper-layer network to detect
topology changes of a lower-layer network in time.
Networking Requirements
Generally, redundant links are used to connect an Ethernet switching network to an upper-layer
network to provide link backup and enhance network reliability. The use of redundant links,
however, may produce loops, causing broadcast storms and rendering the MAC address table
unstable. As a result, the communication quality deteriorates, and communication services may
even be interrupted. SEP can be deployed on the ring network to block redundant links and
unblock them if a link fault occurs.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
370
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
Figure 10-14 Hybrid rings running SEP+RRPP
Network
NPE1
NPE2
GE0/0/2
Aggregation
GE0/0/3
GE0/0/3
PE4
GE0/0/1
GE0/0/2
PE3
GE0/0/1
RRPP
PE1
GE0/0/2
PE2 GE0/0/2
GE0/0/3
GE0/0/1
GE0/0/1
SEP
Segment1
LSW1
LSW2
GE0/0/2
GE0/0/2
Access
GE0/0/1
GE0/0/1
GE0/0/2
GE0/0/1
GE0/0/3LSW3
GE0/0/1
CE
VLAN100
Primary Edge Node
Secondary Edge Node
Block Port(SEP)
Block Port(RRPP)
As shown in Figure 10-14, Multiple Layer 2 switching devices at the access layer and
aggregation layer form a ring network to access the core layer. RRPP has been configured at the
aggregation layer to eliminate loops. In this case, SEP needs to run at the access layer to
implement the following functions:
l
When there is no faulty link on the ring network, SEP helps to eliminate loops.
When a link fault occurs on the ring network, SEP helps to rapidly restore the
communication between nodes.
The function of advertising topology changes should be configured on an edge device in a
SEP segment. This helps an upper-layer network to detect topology changes of a lowerlayer network in time.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
371
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
After receiving a message indicating topology changes of a lower-layer network, a device
on an upper-layer network sends TC packets locally to instruct the other devices to clear
associated MAC addresses and relearn MAC addresses after the topology of the lowerlayer network changes. This ensures nonstop traffic forwarding.
Configuration Roadmap
The configuration roadmap is as follows:
1.
2.
3.
Configure basic SEP functions.
a.
Configure the segment with the ID of 1 and the control VLAN with the ID of 10 on
PE1, PE2 and LSW1 to LSW3.
b.
Add PE1, PE2 and LSW1 to LSW3 to a SEP segment, and configure the roles of the
interfaces that reside on PE1 and PE2 and are added to SEP segment.
c.
Set an interface blocking mode on a primary edge interface to specify an interface to
block.
d.
Configure the SEP preemption mode to ensure that the user-defined blocked interface
takes effect when a fault is cleared.
e.
Configure the function of advertising the topology change of a SEP segment so that
the topology change of the local SEP segment can be advertised to the upper-layer
network where RRPP is enabled.
Configure basic RRPP functions.
a.
Add PE1 to PE4 to a rrpp domain with the ID of 1, create a control VLAN with the
ID of 5 on PE1 to PE4, and configure a protected VLAN.
b.
Configure PE1 as the master node and PE2 to PE4 as the transmit node of the major
ring, and configure the primary interface and secondary interface of the nodes.
c.
Create a VLAN on PE1 to PE4, and then add the interfaces on the RRPP ring network
to the VLAN.
Configure a VLAN on PE3 and PE4 to transmit VRRP packets and BFD packets.
Data Preparation
To complete the configuration, you need the following data:
l
SEP segment ID, control VLAN ID, roles of interfaces added to the SEP segment, interface
blocking mode, and SEP preemption mode.
RRPP domain ID, RRPP ring ID and control VLAN ID.
Procedure
Step 1 Configure basic SEP functions.
1.
Configure a SEP segment with the ID being 1 and a control VLAN with the ID being 10.
# Configure PE1.
<Quidway> system-view
[Quidway] sysname PE1
[PE1] sep segment 1
[PE1-sep-segment1] control-vlan 10
[PE1-sep-segment1] protected-instance all
[PE1-sep-segment1] quit
# Configure PE2.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
372
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
<Quidway> system-view
[Quidway] sysname PE2
[PE2] sep segment 1
[PE2-sep-segment1] control-vlan 10
[PE2-sep-segment1] protected-instance all
[PE2-sep-segment1] quit
# Configure LSW1.
<Quidway> system-view
[Quidway] sysname LSW1
[LSW1] sep segment 1
[LSW1-sep-segment1] control-vlan 10
[LSW1-sep-segment1] protected-instance all
[LSW1-sep-segment1] quit
# Configure LSW2.
<Quidway> system-view
[Quidway] sysname LSW2
[LSW2] sep segment 1
[LSW2-sep-segment1] control-vlan 10
[LSW2-sep-segment1] protected-instance all
[LSW2-sep-segment1] quit
# Configure LSW3.
<Quidway> system-view
[Quidway] sysname LSW3
[LSW3] sep segment 1
[LSW3-sep-segment1] control-vlan 10
[LSW3-sep-segment1] protected-instance all
[LSW3-sep-segment1] quit
2.
Add PE1, PE2 and LSW1 to LSW3 to Segment1 and configure roles of interfaces.
NOTE
By default, STP is enabled on an interface. Before adding an interface to a SEP segment, disable STP
on the interface.
# Configure PE1.
[PE1] interface gigabitethernet 0/0/1
[PE1-GigabitEthernet0/0/1] stp disable
[PE1-GigabitEthernet0/0/1] sep segment 1 edge primary
[PE1-GigabitEthernet0/0/1] quit
# Configure LSW1.
[LSW1] interface gigabitethernet 0/0/1
[LSW1-GigabitEthernet0/0/1] sep segment 1 edge no-neighbor primary
[LSW1-GigabitEthernet0/0/1] quit
[LSW1] interface gigabitethernet 0/0/2
[LSW1-GigabitEthernet0/0/2] stp disable
[LSW1-GigabitEthernet0/0/2] sep segment 1
[LSW1-GigabitEthernet0/0/2] quit
# Configure LSW2.
[LSW2] interface gigabitethernet 0/0/1
[LSW2-GigabitEthernet0/0/1] sep segment 1 edge no-neighbor secondary
[LSW2-GigabitEthernet0/0/1] quit
[LSW2] interface gigabitethernet 0/0/2
[LSW2-GigabitEthernet0/0/2] stp disable
[LSW2-GigabitEthernet0/0/2] sep segment 1
[LSW2-GigabitEthernet0/0/2] quit
# Configure LSW3.
[LSW3] interface gigabitethernet 0/0/1
[LSW3-GigabitEthernet0/0/1] stp disable
[LSW3-GigabitEthernet0/0/1] sep segment 1
[LSW3-GigabitEthernet0/0/1] quit
[LSW3] interface gigabitethernet 0/0/2
[LSW3-GigabitEthernet0/0/2] stp disable
[LSW3-GigabitEthernet0/0/2] sep segment 1
[LSW3-GigabitEthernet0/0/2] quit
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
373
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
# Configure PE2.
[PE2] interface gigabitethernet 0/0/1
[PE2-GigabitEthernet0/0/1] stp disable
[PE2-GigabitEthernet0/0/1] sep segment 1 edge secondary
[PE2-GigabitEthernet0/0/1] quit
After completing the preceding configurations, run the display sep topology command on
PE1 to view the topology of the SEP segment. You can see that the blocked interface is
one of the last two interfaces that complete neighbor negotiation.
[PE1] display sep topology
SEP segment 1
----------------------------------------------------------------System Name
Port Name
Port Role
Port Status
----------------------------------------------------------------PE1
GE0/0/1
primary
forwarding
LSW1
GE0/0/1
common
forwarding
LSW1
GE0/0/2
common
forwarding
LSW3
GE0/0/2
common
forwarding
LSW3
GE0/0/1
common
forwarding
LSW2
GE0/0/2
common
forwarding
LSW2
GE0/0/1
common
forwarding
PE2
GE0/0/1
secondary
discarding
3.
Set an interface blocking mode.
# In Segment1, block the interface in the middle of the SEP segment on PE1 where the
primary edge interface resides.
[PE1] sep segment 1
[PE1-sep-segment1] block port middle
4.
Set the preemption mode.
# In Segment1, set the preemption mode on PE1 where the primary edge interface resides
to manual preemption.
[PE1-sep-segment1] preempt manual
5.
Advertise SEP topology changes.
# In Segment1, advertise the topology change to RRPP.
# Configure PE1.
[PE1-sep-segment1] tc-notify rrpp
[PE1-sep-segment1] quit
# Configure PE2.
[PE2] sep segment 1
[PE2-sep-segment1] tc-notify rrpp
[PE2-sep-segment1] quit
After the preceding configurations are successful, perform the following operations to verify the
configurations. Take PE1 as an example.
l Run the display sep topology command on PE1 to view the information about the topology
of the SEP segment.
The command output shows that the forwarding status of GE 0/0/2 on LSW3 is
discarding and the forwarding status of the other interfaces is forwarding.
[PE1] display sep topology
SEP segment 1
----------------------------------------------------------------System Name
Port Name
Port Role
Port Status
----------------------------------------------------------------PE1
GE0/0/1
primary
forwarding
LSW1
GE0/0/1
common
forwarding
LSW1
GE0/0/2
common
forwarding
LSW3
GE0/0/2
common
discarding
LSW3
GE0/0/1
common
forwarding
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
374
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
LSW2
LSW2
PE2
10 SEP Configuration
GE0/0/2
GE0/0/1
GE0/0/1
common
common
secondary
forwarding
forwarding
forwarding
l Run the display sep interface verbose command on PE1 to view the detailed information
about the interfaces added to the SEP segment.
[PE1] display sep interface verbose
SEP segment 1
Control-vlan
:10
Preempt Delay Timer
:0
TC-Notify Propagate to :rrpp
---------------------------------------------------------------Interface
:GE0/0/1
Port Role
:Config = primary / Active = primary
Port Priority
:64
Port Status
:forwarding
Neighbor Status
:up
Neighbor Port
:LSW1 - GE0/0/1 (00e0-0829-7c00.0000)
NBR TLV
rx :2124
tx :2126
LSP INFO TLV
rx :2939
tx :135
LSP ACK TLV
rx :113
tx :768
PREEMPT REQ TLV
rx :0
tx :3
PREEMPT ACK TLV
rx :3
tx :0
TC Notify
rx :5
tx :3
EPA
rx :363
tx :397
Step 2 Configure basic RRPP functions.
1.
Add PE1 to PE4 to a rrpp domain with the ID of 1, create a control VLAN with the ID of
5 on PE1 to PE4, and configure a protected VLAN.
# Configure PE1.
<Quidway> system-view
[Quidway] sysname PE1
[PE1] rrpp domain 1
[PE1-rrpp-domain-region1] control-vlan 100
[PE1-rrpp-domain-region1] protected-vlan reference-instance all
# Configure PE2.
<Quidway> system-view
[Quidway] sysname PE2
[PE2] rrpp domain 1
[PE2-rrpp-domain-region1] control-vlan 100
[PE2-rrpp-domain-region1] protected-vlan reference-instance all
# Configure PE3.
<Quidway> system-view
[Quidway] sysname PE3
[PE3] rrpp domain 1
[PE3-rrpp-domain-region1] control-vlan 100
[PE3-rrpp-domain-region1] protected-vlan reference-instance all
# Configure PE4.
<Quidway> system-view
[Quidway] sysname PE4
[PE4] rrpp domain 1
[PE4-rrpp-domain-region1] control-vlan 100
[PE4-rrpp-domain-region1] protected-vlan reference-instance all
2.
Create a VLAN and add interfaces on the ring network to the VLAN.
# Create VLAN 100 on PE1, and then add GE 0/0/1, GE 0/0/2, and GE 0/0/3 to VLAN
100.
[PE1] vlan 100
[PE1-vlan100] quit
[PE1] interface gigabitethernet 0/0/1
[PE1-GigabitEthernet0/0/1] stp disable
[PE1-GigabitEthernet0/0/1] port link-type trunk
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
375
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
[PE1-GigabitEthernet0/0/1] port trunk allow-pass vlan 100
[PE1-GigabitEthernet0/0/1] quit
[PE1] interface gigabitethernet 0/0/2
[PE1-GigabitEthernet0/0/2] stp disable
[PE1-GigabitEthernet0/0/2] port link-type trunk
[PE1-GigabitEthernet0/0/2] port trunk allow-pass vlan 100
[PE1-GigabitEthernet0/0/2] quit
[PE1] interface gigabitethernet 0/0/3
[PE1-GigabitEthernet0/0/3] stp disable
[PE1-GigabitEthernet0/0/3] port link-type trunk
[PE1-GigabitEthernet0/0/3] port trunk allow-pass vlan 100
[PE1-GigabitEthernet0/0/3] quit
# Create VLAN 100 on PE2, and then add GE 0/0/1, GE 0/0/2, and GE 0/0/3 to VLAN
100.
[PE2] vlan 100
[PE2-vlan100] quit
[PE2] interface gigabitethernet 0/0/1
[PE2-GigabitEthernet0/0/1] stp disable
[PE2-GigabitEthernet0/0/1] port link-type trunk
[PE2-GigabitEthernet0/0/1] port trunk allow-pass vlan 100
[PE2-GigabitEthernet0/0/1] quit
[PE2] interface gigabitethernet 0/0/2
[PE2-GigabitEthernet0/0/2] stp disable
[PE2-GigabitEthernet0/0/2] port link-type trunk
[PE2-GigabitEthernet0/0/2] port trunk allow-pass vlan 100
[PE2-GigabitEthernet0/0/2] quit
[PE2] interface gigabitethernet 0/0/3
[PE2-GigabitEthernet0/0/3] stp disable
[PE2-GigabitEthernet0/0/3] port link-type trunk
[PE2-GigabitEthernet0/0/3] port trunk allow-pass vlan 100
[PE2-GigabitEthernet0/0/3] quit
# Create VLAN 100 on PE3, and then add GE 0/0/1 and GE 0/0/2 to VLAN 100.
[PE3] vlan 100
[PE3-vlan100] quit
[PE3] interface gigabitethernet 0/0/1
[PE3-GigabitEthernet0/0/1] stp disable
[PE3-GigabitEthernet0/0/1] port link-type trunk
[PE3-GigabitEthernet0/0/1] port trunk allow-pass vlan 100
[PE3-GigabitEthernet0/0/1] quit
[PE3] interface gigabitethernet 0/0/2
[PE3-GigabitEthernet0/0/2] stp disable
[PE3-GigabitEthernet0/0/2] port link-type trunk
[PE3-GigabitEthernet0/0/2] port trunk allow-pass vlan 100
[PE3-GigabitEthernet0/0/2] quit
# Create VLAN 100 on PE4, and then add GE 0/0/1 and GE 0/0/2 to VLAN 100.
[PE4] vlan 100
[PE4-vlan100] quit
[PE4] interface gigabitethernet 0/0/1
[PE4-GigabitEthernet0/0/1] stp disable
[PE4-GigabitEthernet0/0/1] port link-type trunk
[PE4-GigabitEthernet0/0/1] port trunk allow-pass vlan 100
[PE4-GigabitEthernet0/0/1] quit
[PE4] interface gigabitethernet 0/0/2
[PE4-GigabitEthernet0/0/2] stp disable
[PE4-GigabitEthernet0/0/2] port link-type trunk
[PE4-GigabitEthernet0/0/2] port trunk allow-pass vlan 100
[PE4-GigabitEthernet0/0/2] quit
3.
Configure PE1 as the master node and PE2 to PE4 as the transmit node of the major ring,
and configure the primary interface and secondary interface of the nodes.
# Configure PE1.
[PE1] rrpp domain 1
[PE1-rrpp-domain-region1] ring 1 node-mode master primary-port
gigabitEthernet0/0/2 secondary-port gigabitEthernet0/0/3 level 0
[PE1-rrpp-domain-region1] ring 1 enable
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
376
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
# Configure PE2.
[PE2] rrpp domain 1
[PE2-rrpp-domain-region1] ring 1 node-mode transit primary-port
gigabitEthernet0/0/2 secondary-port gigabitEthernet0/0/3 level 0
[PE2-rrpp-domain-region1] ring 1 enable
# Configure PE3.
[PE3] rrpp domain 1
[PE3-rrpp-domain-region1] ring 1 node-mode transit primary-port
gigabitEthernet0/0/1 secondary-port gigabitEthernet0/0/2 level 0
[PE3-rrpp-domain-region1] ring 1 enable
# Configure PE4.
[PE4] rrpp domain 1
[PE4-rrpp-domain-region1] ring 1 node-mode transit primary-port
gigabitEthernet0/0/1 secondary-port gigabitEthernet0/0/2 level 0
[PE4-rrpp-domain-region1] ring 1 enable
4.
Enable RRPP.
# Configure PE1.
[PE1] rrpp enable
# Configure PE2.
[PE2] rrpp enable
# Configure PE3.
[PE3] rrpp enable
# Configure PE4.
[PE4] rrpp enable
After completing the preceding configurations, run the display rrpp brief or display rrpp
verbose domain command on PE1 to check the RRPP configuration.
[PE1] display rrpp brief
Abbreviations for Switch Node Mode :
M - Master , T - Transit , E - Edge , A - Assistant-Edge
RRPP Protocol Status: Enable
RRPP Working Mode: HW
RRPP Linkup Delay Timer: 0 sec (0 sec default)
Number of RRPP Domains: 1
Domain Index
: 1
Control VLAN
: major 5
sub 6
Protected VLAN : Reference Instance 1
Hello Timer
: 1 sec(default is 1 sec) Fail Timer : 6 sec(default is 6 sec)
Ring Ring
Node Primary/Common
Secondary/Edge
Is
ID
Level Mode Port
Port
Enabled
---------------------------------------------------------------------------1
0
M
GigabitEthernet0/0/2
GigabitEthernet0/0/3
Yes
You can view that RRPP is enabled on PE1. In domain 1, VLAN 5 is the major control VLAN,
VLAN 6 is the sub-control VLAN, Instance1 is the protected VLAN, and PE1 is the master node
in major ring 1 with the primary interface and secondary interface respectively as
GigabitEthernet 0/0/2 and GigabitEthernet 0/0/3.
[PE1] display rrpp verbose domain 1
Domain Index
: 1
Control VLAN
: major 5
sub 6
Protected VLAN : Reference Instance 1
Hello Timer
: 1 sec(default is 1 sec)
RRPP
Ring
Node
Ring
Issue 02 (2011-11-21)
Ring
Level
Mode
State
:
:
:
:
Fail Timer : 6 sec(default is 6 sec)
1
0
Master
Complete
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
377
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
Is Enabled
: Enable
Primary port
: GigabitEthernet0/0/2
Secondary port : GigabitEthernet0/0/3
10 SEP Configuration
Is Active: Yes
Port status: UP
Port status: BLOCKED
You can view that in domain 1, VLAN 5 is the major control VLAN, VLAN 6 is the sub-control
VLAN, Instance1 is the protected VLAN, and PE1 is the master node in major ring 1 with the
primary interface and secondary interface respectively as GigabitEthernet 0/0/2 and
GigabitEthernet 0/0/3, and the node status is Complete.
Step 3 Configure the Layer 2 forwarding function on the CE, LSW1 to LSW3 and PE1 to PE4.
For the configuration details, see configuration files in this example.
Step 4 Verify the configuration.
After the previous configurations, run the following commands to verify the configuration when
the network is stable. Take LSW1 as an example.
l Run the shutdown command on GE 0/0/1 on LSW2 to simulate an interface fault, and then
run the display sep interface command on LSW3 to check whether the status of GE 0/0/2
changes from blocked to forwarding.
[LSW3] display sep interface gigabitethernet 0/0/2
SEP segment 1
---------------------------------------------------------------Interface
Port Role
Neighbor Status
Port Status
---------------------------------------------------------------GE0/0/2
common
up
forwarding
----End
Configuration Files
l
Configuration file of LSW1
#
sysname LSW1
#
vlan batch 10 100
#
sep segment 1
control-vlan 10
protected-instance 0 to 48
#
interface GigabitEthernet0/0/1
port link-type trunk
port trunk allow-pass vlan 10 100
stp disable
sep segment 1
#
interface GigabitEthernet0/0/2
port link-type trunk
port trunk allow-pass vlan 10 100
stp disable
sep segment 1
#
return
Configuration file of LSW2
#
sysname LSW2
#
vlan batch 10 100
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
378
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
#
sep segment 1
control-vlan 10
protected-instance 0 to 48
#
interface GigabitEthernet0/0/2
port link-type trunk
port trunk allow-pass vlan 10 100
stp disable
sep segment 1
#
interface GigabitEthernet0/0/1
port link-type trunk
port trunk allow-pass vlan 10 100
stp disable
sep segment 1
#
return
Configuration file of LSW3
#
sysname LSW3
#
vlan batch 10 100
#
sep segment 1
control-vlan 10
protected-instance 0 to 48
#
interface GigabitEthernet0/0/1
port link-type trunk
port trunk allow-pass vlan 10 100
stp disable
sep segment 1
#
interface GigabitEthernet0/0/2
port link-type trunk
port trunk allow-pass vlan 10 100
stp disable
sep segment 1
#
interface GigabitEthernet0/0/3
port link-type trunk
port trunk allow-pass vlan 100
#
return
Configuration file of PE1
#
sysname PE1
#
vlan batch 5 to 6 100
#
rrpp enable
#
stp region-configuration
instance 1 vlan 5 to 6 100
active region-configuration
#
rrpp domain 1
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
379
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
control-vlan 5
protected-vlan reference-instance 1
ring 1 node-mode master primary-port GigabitEthernet 0/0/2 secondary-port
GigabitEthernet 0/0/3 level 0
ring 1 enable
#
sep segment 1
control-vlan 10
block port middle
tc-notify rrpp
protected-instance 0 to 48
#
interface GigabitEthernet0/0/1
port link-type trunk
port trunk allow-pass vlan 100
stp disable
sep segment 1 edge primary
#
interface GigabitEthernet0/0/2
port link-type trunk
port trunk allow-pass vlan 5 to 6 100
stp disable
#
interface GigabitEthernet0/0/3
port link-type trunk
port trunk allow-pass vlan 5 to 6 100
stp disable
#
return
Configuration file of PE2
#
sysname PE2
#
vlan batch 5 to 6 100
#
rrpp enable
#
stp region-configuration
instance 1 vlan 5 to 6 100
active region-configuration
#
rrpp domain 1
control-vlan 5
protected-vlan reference-instance 1
ring 1 node-mode transit primary-port GigabitEthernet 0/0/2 secondary-port
GigabitEthernet 0/0/3 level 0
ring 1 enable
#
sep segment 1
control-vlan 10
tc-notify rrpp
protected-instance 0 to 48
#
interface GigabitEthernet0/0/1
port link-type trunk
port trunk allow-pass vlan 100
stp disable
sep segment 1 edge secondary
#
interface GigabitEthernet0/0/2
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
380
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
port link-type trunk
port trunk allow-pass vlan 5 to 6 100
stp disable
#
interface GigabitEthernet0/0/3
port link-type trunk
port trunk allow-pass vlan 5 to 6 100
stp disable
#
return
Configuration file of PE3
#
sysname PE3
#
vlan batch 5 to 6 100 200
#
rrpp enable
#
stp region-configuration
instance 1 vlan 5 to 6 100
active region-configuration
#
rrpp domain 1
control-vlan 5
protected-vlan reference-instance 1
ring 1 node-mode transit primary-port GigabitEthernet 0/0/1 secondary-port
GigabitEthernet 0/0/2 level 0
ring 1 enable
#
interface GigabitEthernet0/0/1
port link-type trunk
port trunk allow-pass vlan 100
stp disable
#
interface GigabitEthernet0/0/2
port link-type trunk
port trunk allow-pass vlan 5 to 6 100 200
stp disable
#
interface GigabitEthernet0/0/3
port default vlan 200
port trunk allow-pass vlan 5 to 6 100
#
return
Configuration file of PE4
#
sysname PE4
#
vlan batch 5 to 6 100 200
#
rrpp enable
#
stp region-configuration
instance 1 vlan 5 to 6 100
active region-configuration
#
rrpp domain 1
control-vlan 5
protected-vlan reference-instance 1
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
381
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
ring 1 node-mode transit primary-port GigabitEthernet 0/0/1 secondary-port
GigabitEthernet 0/0/2 level 0
ring 1 enable
#
interface GigabitEthernet0/0/1
port link-type trunk
port trunk allow-pass vlan 100
stp disable
#
interface GigabitEthernet0/0/2
port link-type trunk
port trunk allow-pass vlan 5 to 6 100 200
stp disable
#
interface GigabitEthernet0/0/3
port default vlan 200
port trunk allow-pass vlan 5 to 6 100
#
return
Configuration file of CE1
#
sysname CE1
#
vlan batch 100
#
interface GigabitEthernet0/0/1
port link-type trunk
port trunk allow-pass vlan 100
#
return
10.7.5 Example for Configuring SEP Multi-Instance on a Closed
Ring Network
On a closed ring network, two SEP segments are configured to process different VLAN services,
implement load balancing, and provide link backup.
Networking Requirements
In common SEP networking, a physical ring can be configured with only one SEP segment in
which only one interface can be blocked. If an interface in the SEP segment in the complete state
is blocked, all user data is transmitted only along the path where the primary edge interface is
located. The path where the secondary edge interface is located is idle, which leads to a waste
of bandwidth.
To solve the problem of bandwidth waste and to implement traffic load balancing, Huawei
develops SEP multi-instance.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
382
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
Figure 10-15 SEP multi-instance on a closed ring network
IP/MPLS Core
Core
NPE1
GE0/0/2
3
0/0/
GE
NPE2
GE0
/0
/3
GE0/0/2
Aggregation
LSW1
GE0/0/1
GE0/0/1
LSW2
GE0/0/3
LSW4
GE0/0/1
P2
P1
GE
0/0
/2
2
0/0/
GE
GE0/0/3
GE0/0/1
Access
GE0/0/1
LSW3
GE0/0/1
CE1
Instance1:
VLAN 100~300
CE2
Instance2:
VLAN 301~500
SEP Segment1
SEP Segment2
Primary Edge Node
Secondary Edge Node
Block Port
As shown in Figure 10-15, a ring network comprising Layer 2 switches LSW1 to LSW5 is
connected to a core network. SEP runs at the aggregation layer. SEP multi-instance is configured
on LSW1 to LSW4. This allows two SEP segments to solve the problem of bandwidth waste,
implement load balancing, and provide link backup.
Configuration Roadmap
The configuration roadmap is as follows:
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
383
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
1.
10 SEP Configuration
Create two SEP segments and one control VLAN on LSW1 to LSW4.
Different SEP segments can use the same control VLAN.
2.
Configure SEP protected instances, and set mappings between SEP protected instances and
user VLANs to ensure that topology changes affect only corresponding VLANs.
3.
Add all the devices on the ring network to the SEP segments, and configure GE 0/0/1 as
the primary edge interface and GE 0/0/3 as the secondary edge interface on LSW1.
4.
Enable the function of specifying an interface to block on the device where the primary
edge interface resides.
5.
Configure the SEP preemption mode to ensure that the specified blocked interface takes
effect when a fault is rectified.
6.
Configure the Layer 2 forwarding function on CE1, CE2, and LSW1 to LSW4.
Data Preparation
To complete the configuration, you need the following data:
l
ID of each SEP segment
ID of a control VLAN
role of each interface added to each SEP segment
mode of blocking an interface
preemption mode
ID of each SEP protection instance
Procedure
Step 1 Configure basic SEP functions.
l Configure a SEP segment with the ID of 1 and a control VLAN with the ID of 10.
# Configure LSW1.
<Quidway> system-view
[Quidway] sysname LSW1
[LSW1] sep segment 1
[LSW1-sep-segment1] control-vlan 10
[LSW1-sep-segment1] quit
# Configure LSW2.
<Quidway> system-view
[Quidway] sysname LSW2
[LSW2] sep segment1
[LSW2-sep-segment1] control-vlan 10
[LSW2-sep-segment1] quit
# Configure LSW3.
<Quidway> system-view
[Quidway] sysname LSW3
[LSW3] sep segment 1
[LSW3-sep-segment1] control-vlan 10
[LSW3-sep-segment1] quit
# Configure LSW4.
<Quidway> system-view
[Quidway] sysname LSW4
[LSW4] sep segment 1
[LSW4-sep-segment1] control-vlan 10
[LSW4-sep-segment1] quit
l Configure a SEP segment with the ID of 2 and a control VLAN with the ID of 10.
# Configure LSW1.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
384
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
[LSW1] sep segment 2
[LSW1-sep-segment2] control-vlan 10
[LSW1-sep-segment2] quit
# Configure LSW2.
[LSW2] sep segment2
[LSW2-sep-segment2] control-vlan 10
[LSW2-sep-segment2] quit
# Configure LSW3.
[LSW3] sep segment 2
[LSW3-sep-segment2] control-vlan 10
[LSW3-sep-segment2] quit
# Configure LSW4.
[LSW4] sep segment 2
[LSW4-sep-segment2] control-vlan 10
[LSW4-sep-segment2] quit
NOTE
l The control VLAN must be a new one.
l The command used to create a common VLAN is automatically displayed in a configuration file.
l Each SEP segment must be configured with a control VLAN. After being added to a SEP segment
configured with a control VLAN, an interface is added to the control VLAN automatically.
Step 2 Configure SEP protected instances, and then configure mappings between SEP protected
instances and user VLANs.
# Configure LSW1.
[LSW1] vlan batch 100 to 500
[LSW1] sep segment 1
[LSW1-sep-segment1] protected-instance 1
[LSW1-sep-segment1] quit
[LSW1] sep segment 2
[LSW1-sep-segment2] protected-instance 2
[LSW1-sep-segment2] quit
[LSW1] stp region-configuration
[LSW1-mst-region] instance 1 vlan 100 to 300
[LSW1-mst-region] instance 2 vlan 301 to 500
[LSW1-mst-region] active region-configuration
[LSW1-mst-region] quit
The configurations of LSW2 to LSW4 are similar to those of LSW1, and are not provided here.
For details, see configuration files in this configuration example.
Step 3 Add all the devices on the ring network to the SEP segments and configure interface roles.
NOTE
By default, STP is enabled on a Layer 2 interface. Before adding an interface to a SEP segment, disable
STP on the interface.
# On LSW1, configure GE 0/0/1 as the primary edge interface and GE 0/0/3 as the secondary
edge interface.
[LSW1] interface gigabitethernet 0/0/1
[LSW1-GigabitEthernet0/0/1] stp disable
[LSW1-GigabitEthernet0/0/1] sep segment
[LSW1-GigabitEthernet0/0/1] sep segment
[LSW1-GigabitEthernet0/0/1] quit
[LSW1] interface gigabitethernet 0/0/3
[LSW1-GigabitEthernet0/0/3] stp disable
[LSW1-GigabitEthernet0/0/3] sep segment
[LSW1-GigabitEthernet0/0/3] sep segment
[LSW1-GigabitEthernet0/0/3] quit
1 edge primary
2 edge primary
1 edge secondary
2 edge secondary
# Configure LSW2.
[LSW2] interface gigabitethernet 0/0/1
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
385
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
[LSW2-GigabitEthernet0/0/1] stp disable
[LSW2-GigabitEthernet0/0/1] sep segment
[LSW2-GigabitEthernet0/0/1] sep segment
[LSW2-GigabitEthernet0/0/1] quit
[LSW2] interface gigabitethernet 0/0/2
[LSW2-GigabitEthernet0/0/2] stp disable
[LSW2-GigabitEthernet0/0/2] sep segment
[LSW2-GigabitEthernet0/0/2] sep segment
[LSW2-GigabitEthernet0/0/2] quit
10 SEP Configuration
1
2
1
2
# Configure LSW3.
[LSW3] interface gigabitethernet 0/0/1
[LSW3-GigabitEthernet0/0/1] stp disable
[LSW3-GigabitEthernet0/0/1] sep segment
[LSW3-GigabitEthernet0/0/1] sep segment
[LSW3-GigabitEthernet0/0/1] quit
[LSW3] interface gigabitethernet 0/0/2
[LSW3-GigabitEthernet0/0/2] stp disable
[LSW3-GigabitEthernet0/0/2] sep segment
[LSW3-GigabitEthernet0/0/2] sep segment
[LSW3-GigabitEthernet0/0/2] quit
1
2
1
2
# Configure LSW4.
[LSW4] interface gigabitethernet 0/0/1
[LSW4-GigabitEthernet0/0/1] stp disable
[LSW4-GigabitEthernet0/0/1] sep segment
[LSW4-GigabitEthernet0/0/1] sep segment
[LSW4-GigabitEthernet0/0/1] quit
[LSW4] interface gigabitethernet 0/0/3
[LSW4-GigabitEthernet0/0/3] stp disable
[LSW4-GigabitEthernet0/0/3] sep segment
[LSW4-GigabitEthernet0/0/3] sep segment
[LSW4-GigabitEthernet0/0/3] quit
1
2
1
2
After completing the preceding configurations, run the display sep topology command on
LSW1 to view the topology of each SEP segment. You can see that the blocked interface is one
of the last two interfaces that complete neighbor negotiation.
[LSW1] display sep topology
SEP segment 1
----------------------------------------------------------------System Name
Port Name
Port Role
Port Status
----------------------------------------------------------------LSW1
GE0/0/1
primary
forwarding
LSW2
GE0/0/1
common
forwarding
LSW2
GE0/0/2
common
forwarding
LSW3
GE0/0/2
common
forwarding
LSW3
GE0/0/1
common
forwarding
LSW4
GE0/0/1
common
forwarding
LSW4
GE0/0/3
common
forwarding
LSW1
GE0/0/3
secondary
discarding
SEP segment 2
----------------------------------------------------------------System Name
Port Name
Port Role
Port Status
----------------------------------------------------------------LSW1
GE0/0/1
primary
forwarding
LSW2
GE0/0/1
common
forwarding
LSW2
GE0/0/2
common
forwarding
LSW3
GE0/0/2
common
forwarding
LSW3
GE0/0/1
common
forwarding
LSW4
GE0/0/1
common
forwarding
LSW4
GE0/0/3
common
forwarding
LSW1
GE0/0/3
secondary
discarding
Step 4 Specify an interface to block.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
386
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
# Configure delayed preemption and the mode of blocking an interface to be based on the device
name and interface name on LSW1 where the primary edge interface is located.
[LSW1] sep segment 1
[LSW1-sep-segment1] block port sysname LSW3 interface gigabitethernet 0/0/1
[LSW1-sep-segment1] preempt delay 15
[LSW1-sep-segment1] quit
[LSW1] sep segment 2
[LSW1-sep-segment2] block port sysname LSW2 interface gigabitethernet 0/0/1
[LSW1-sep-segment2] preempt delay 15
[LSW1-sep-segment2] quit
NOTE
l In this configuration example, an interface fault needs to be simulated and then rectified to implement
delayed preemption. To ensure that delayed preemption takes effect on the two SEP segments, simulate
an interface fault in the two SEP segment. For example:
l In SEP segment 1, run the shutdown command on GE 0/0/1 of LSW2 to simulate an interface
fault. Then, run the undo shutdown command on GE 0/0/1 to simulate interface fault recovery.
l In SEP segment 2, run the shutdown command on GE 0/0/1 of LSW3 to simulate an interface
fault. Then, run the undo shutdown command on GE 0/0/1 to simulate interface fault recovery.
After completing the preceding operations, view SEP topologies. Use the display on LSW1 as
an example.
Run the display sep topology command on LSW1. You can view information about the topology
of each SEP segment.
[LSW1] display sep topology
SEP segment 1
----------------------------------------------------------------System Name
Port Name
Port Role
Port Status
----------------------------------------------------------------LSW1
GE0/0/1
primary
forwarding
LSW2
GE0/0/1
common
forwarding
LSW2
GE0/0/2
common
forwarding
LSW3
GE0/0/2
common
forwarding
LSW3
GE0/0/1
common
discarding
LSW4
GE0/0/1
common
forwarding
LSW4
GE0/0/3
common
forwarding
LSW1
GE0/0/3
secondary
forwarding
SEP segment 2
----------------------------------------------------------------System Name
Port Name
Port Role
Port Status
----------------------------------------------------------------LSW1
GE0/0/1
primary
forwarding
LSW2
GE0/0/1
common
discarding
LSW2
GE0/0/2
common
forwarding
LSW3
GE0/0/2
common
forwarding
LSW3
GE0/0/1
common
forwarding
LSW4
GE0/0/1
common
forwarding
LSW4
GE0/0/3
common
forwarding
LSW1
GE0/0/3
secondary
forwarding
From the preceding command output, you can see:
l On LSW3 in SEP segment 1, GE 0/0/1 is in the discarding state, and the other interfaces are
in the forwarding state.
l On LSW2 in SEP segment 2, GE 0/0/1 is in the discarding state, and the other interfaces are
in the forwarding state.
Step 5 Configure the Layer 2 forwarding function on CE1, CE2, and LSW1 to LSW4.
The configuration details are not provided here. For details, see configuration files in this
example.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
387
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
Step 6 Verify the configuration.
Simulate a fault, and then check whether the status of the blocked interface changes from blocked
to forwarding.
Run the shutdown command on GE 0/0/1 of LSW2 to simulate an interface fault.
Run the display sep interface command on LSW3 to check whether the status of GE0/0/1 in
SEP segment 1 changes from blocked to forwarding.
[LSW3] display sep interface gigabitethernet 0/0/1
SEP segment 1
---------------------------------------------------------------Interface
Port Role
Neighbor Status
Port Status
---------------------------------------------------------------GE0/0/1
common
up
forwarding
SEP segment 2
---------------------------------------------------------------Interface
Port Role
Neighbor Status
Port Status
---------------------------------------------------------------GE0/0/1
common
up
forwarding
The preceding command output shows that the status of GE 0/0/1 changes from blocked to
forwarding and the forwarding path change in SEP segment 1 does not affect the forwarding
path in SEP segment 2.
----End
Configuration Files
l
Configuration file of LSW1
#
sysname LSW1
#
vlan batch 10 100 to 500
#
stp region-configuration
instance 1 vlan 100 to 300
instance 2 vlan 301 to 500
active region-configuration
#
sep segment 1
control-vlan 10
block port sysname LSW3 interface
preempt delay 15
protected-instance 1
sep segment 2
control-vlan 10
block port sysname LSW2 interface
preempt delay 15
protected-instance 2
#
interface GigabitEthernet0/0/1
port link-type trunk
port trunk allow-pass vlan 10 100
stp disable
sep segment 1 edge primary
sep segment 2 edge primary
#
interface GigabitEthernet0/0/3
port link-type trunk
port trunk allow-pass vlan 10 100
stp disable
sep segment 1 edge secondary
sep segment 2 edge secondary
Issue 02 (2011-11-21)
GigabitEthernet0/0/1
GigabitEthernet0/0/1
to 500
to 500
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
388
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
#
return
Configuration file of LSW2
#
sysname LSW2
#
vlan batch 10 100 to 500
#
stp region-configuration
instance 1 vlan 100 to 300
instance 2 vlan 301 to 500
active region-configuration
#
sep segment 1
control-vlan 10
protected-instance 1
sep segment 2
control-vlan 10
protected-instance 2
#
interface GigabitEthernet0/0/1
port link-type trunk
port trunk allow-pass vlan 10 100 to 500
stp disable
sep segment 1
sep segment 2
#
interface GigabitEthernet0/0/2
port link-type trunk
port trunk allow-pass vlan 10 100 to 500
stp disable
sep segment 1
sep segment 2
#
interface GigabitEthernet0/0/3
port link-type trunk
port trunk allow-pass vlan 100 to 300
#
return
Configuration file of LSW3
#
sysname LSW3
#
vlan batch 10 100 to 500
#
stp region-configuration
instance 1 vlan 100 to 300
instance 2 vlan 301 to 500
active region-configuration
#
sep segment 1
control-vlan 10
protected-instance 1
sep segment 2
control-vlan 10
protected-instance 2
#
interface GigabitEthernet0/0/1
port link-type trunk
port trunk allow-pass vlan 10 100 to 500
stp disable
sep segment 1
sep segment 2
#
interface GigabitEthernet0/0/2
port link-type trunk
port trunk allow-pass vlan 10 100 to 500
stp disable
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
389
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
10 SEP Configuration
sep segment 1
sep segment 2
#
interface GigabitEthernet0/0/3
port link-type trunk
port trunk allow-pass vlan 301 to 500
#
return
Configuration file of LSW4
#
sysname LSW4
#
vlan batch 10 60 100 to 500
#
stp region-configuration
instance 1 vlan 100 to 300
instance 2 vlan 301 to 500
active region-configuration
#
sep segment 1
control-vlan 10
protected-instance 1
sep segment 2
control-vlan 10
protected-instance 2
#
interface GigabitEthernet0/0/1
port link-type trunk
port trunk allow-pass vlan 10 100 to 500
stp disable
sep segment 1
sep segment 2
#
interface GigabitEthernet0/0/3
port link-type trunk
port trunk allow-pass vlan 10 100 to 500
stp disable
sep segment 1
sep segment 2
#
return
Configuration file of CE1
#
sysname CE1
#
vlan batch 100 to 300
#
interface GigabitEthernet0/0/1
port link-type trunk
port trunk allow-pass vlan 100 to 300
#
return
Configuration file of CE2
#
sysname CE2
#
vlan batch 301 to 500
#
interface GigabitEthernet0/0/1
port link-type trunk
port trunk allow-pass vlan 301 to 500
#
return
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
390
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
11
11 Layer 2 Protocol Transparent Transmission Configuration
Layer 2 Protocol Transparent
Transmission Configuration
About This Chapter
This chapter describes the concept, configuration procedure, and configuration examples of
Layer 2 protocol transparent transmission.
11.1 Layer 2 Protocol Transparent Transmission Overview
This section describes the concepts of Layer 2 protocol transparent transmission.
11.2 Layer 2 Protocol Transparent Transmission Features Supported by the S5700
This section describes the Layer 2 protocol transparent transmission features supported by the
S5700.
11.3 Configuring Interface-based Layer 2 Protocol Transparent Transmission
When each interface of a backbone device is connected to only one user network and Layer 2
protocol packets sent from the user network do not need VLAN tags, configure interface-based
Layer 2 protocol transparent transmission on the interface connected to the user network. This
configuration allows Layer 2 protocol packets to be transparently transmitted on the backbone
network.
11.4 Configuring VLAN-based Layer 2 Protocol Transparent Transmission
When each interface of a backbone device is connected to multiple user networks and Layer 2
protocol packets sent from user networks contain VLAN tags, configure VLAN-based Layer 2
protocol transparent transmission. This configuration allows Layer 2 protocol packets to be
transparently transmitted on the backbone network.
11.5 Configuring QinQ-based Layer 2 Protocol Transparent Transmission
When each interface of backbone devices is connected to multiple user networks and Layer 2
protocol packets sent from user network contain VLAN tags, you can configure QinQ-based
Layer 2 protocol transparent transmission. This configuration allows Layer 2 protocol packets
to be transparently transmitted on the backbone network and reduces VLAN IDs that the carrier
uses.
11.6 Maintaining Layer 2 Protocol Transparent Transmission
This section describes how to debug Layer 2 protocol transparent transmission.
11.7 Configuration Examples
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
391
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
11 Layer 2 Protocol Transparent Transmission Configuration
This section provides examples for configuring interface, VLAN, and QinQ based Layer 2
protocol transparent transmission.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
392
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
11 Layer 2 Protocol Transparent Transmission Configuration
11.1 Layer 2 Protocol Transparent Transmission Overview
This section describes the concepts of Layer 2 protocol transparent transmission.
Background
In certain network environments, packets of Layer 2 protocols such as MSTP, HGMP, and LACP
need to be transmitted between user networks across the backbone network to complete protocol
calculation.
As shown in Figure 11-1, user network 1 and user network 2 run Layer 2 protocols, for example,
MSTP. Layer 2 protocol packets of user network 1 must traverse the backbone network to reach
user network 2 so that the spanning tree can be calculated. Packets of a Layer 2 protocol usually
use the same destination MAC address. For example, MSTP packets are BPDUs that use 0180C200-0000 as the destination MAC address. Therefore, when the BPDUs reach a PE on the
backbone network, the PE cannot identify whether the BPDUs are sent from a user network or
the backbone network. As a result, the PE sends the BPDUs to the CPU for spanning tree
calculation.
When this occurs, the spanning tree is calculated between the devices of user network 1 and
PE1, and the devices of user network 2 are not involved in the calculation. Therefore, BPDUs
of user network 1 cannot be sent to user network 2 through the backbone network.
Figure 11-1 Transparent transmission of Layer 2 protocol packets on an ISP network
ISP
network
PE1
PE2
CE1
CE2
User
network1
User
network2
Layer 2 protocol transparent transmission allows BPDUs from user networks to traverse the
backbone network.
To transparently transmit Layer 2 protocol packets on the backbone network, the following
requirements must be met:
l
Issue 02 (2011-11-21)
Each site on a user network can receive Layer 2 protocol packets from other sites.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
393
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
11 Layer 2 Protocol Transparent Transmission Configuration
Layer 2 protocol packets sent from a user network are not processed by CPUs of devices
on the backbone network.
Layer 2 protocol packets of different user networks are separated from each other.
A Layer 2 protocol packet is transparently transmitted as follows:
l
A user-side device on the backbone network replaces the multicast destination MAC
address of Layer 2 protocol packets with a specified multicast MAC address.
Devices on the backbone network determine whether to add an outer VLAN tag to the
packet according to the transparent transmission mode.
The egress device on the backbone network restores the original multicast destination MAC
address of the packet according to the mappings between multicast destination MAC
addresses and Layer 2 protocols. The egress device also determines whether to remove the
outer VLAN tag, and then forwards the packet to the user network.
11.2 Layer 2 Protocol Transparent Transmission Features
Supported by the S5700
This section describes the Layer 2 protocol transparent transmission features supported by the
S5700.
Based on application scenarios, the S5700 supports the following Layer 2 protocol transparent
transmission features:
l
Interface-based Layer 2 protocol transparent transmission
VLAN-based Layer 2 protocol transparent transmission
QinQ-based Layer 2 protocol transparent transmission
The S5700 can transparently transmit packets of the following Layer 2 protocols:
l
Spanning Tree Protocol (STP)
Link Aggregation Control Protocol (LACP)
Ethernet Operation, Administration, and Maintenance 802.3ah (EOAM3ah)
Link Layer Discovery Protocol (LLDP)
Generic VLAN Registration Protocol (GVRP)
Generic Multicast Registration Protocol (GMRP)
HUAWEI Group Management Protocol (HGMP)
VLAN Trunking Protocol (VTP)
Unidirectional Link Detection (UDLD)
Port Aggregation Protocol (PAGP)
Cisco Discovery Protocol (CDP)
Per VLAN Spanning Tree Plus (PVST+)
Shared Spanning Tree Protocol (SSTP)
Dynamic Trunking Protocol (DTP)
User-defined protocols
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
394
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
11 Layer 2 Protocol Transparent Transmission Configuration
Interface-based Layer 2 Protocol Transparent Transmission
Figure 11-2 Interface-based Layer 2 protocol transparent transmission
Port based
VLAN 200
Port based
VLAN 200
LAN-B
MSTP
LAN-B
MSTP
ISP Network
PE1
Port based
VLAN 300
LAN-A
MSTP
PE2
BPDU Tunnel 200
BPDU Tunnel 300
Port based
VLAN 300
PE3
LAN-A
MSTP
Port based
VLAN 200
LAN-B
MSTP
As shown in Figure 11-2, each interface of a PE is connected to one user network. The user
networks connected to the same PE belong to different LANs, namely, LAN-A and LAN-B.
BPDUs sent from user networks are not tagged, but the PE needs to identify the LAN that each
BPDU belongs to. BPDUs of a user network on LAN-A must be forwarded to other user networks
on LAN-A, but cannot be forwarded to user networks on LAN-B. In addition, BPDUs cannot
be processed by network devices of the ISP.
The following methods can be used to meet the preceding requirements:
l
Issue 02 (2011-11-21)
Replace the default multicast MAC address of Layer 2 protocol packets that can be
identified by PEs on the backbone network with another multicast MAC address.
1.
Configure all PEs as providers. Then the multicast destination MAC address of
BPDUs sent from the backbone network is changed from 01-80-C2-00-00-00 to
01-80-C2-00-00-08.
2.
Configure all devices on user networks as customers. Then the multicast destination
MAC address of BPDUs sent from user networks is 01-80-C2-00-00-00.
3.
On PEs, add the interfaces connected to the same user network to the same VLAN.
Then PEs add VLAN tags to received BPDUs according to default VLANs of the
interfaces.
4.
PEs (providers) do not consider these packets as Layer 2 protocol BPDUs and do not
send them to the CPU. Instead, PEs select a Layer 2 tunnel to forward the packets
according to the default VLANs of interfaces.
5.
Internal nodes on the backbone network forward the packets across the backbone
network as common Layer 2 packets.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
395
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
6.
11 Layer 2 Protocol Transparent Transmission Configuration
The egress device on the backbone network forwards the packets to user networks
without modifying the packets.
NOTE
l This method is applicable only to STP, RSTP, and MSTP. To configure a device as the provider,
run the bpdu-tunnel stp bridge role provider command.
l The S5700HI and S5706 do not support this method.
Replace the original multicast MAC address of Layer 2 protocol packets from user networks
with a specified multicast MAC address.
NOTE
This method is applicable to all Layer 2 protocols.
Issue 02 (2011-11-21)
1.
PEs identify the type (such as STP) of the Layer 2 protocol packets sent from user
networks and tag the packets with corresponding VLAN IDs according to default
VLANs of interfaces.
2.
PEs replace the standard multicast destination MAC address of Layer 2 protocol
packets with a specified multicast MAC address according to the mappings between
multicast destination MAC addresses and Layer 2 protocols.
3.
Internal nodes on the backbone network forward the packets across the backbone
network as common Layer 2 packets.
4.
The egress device of the backbone network restores the original destination MAC
address of the packets according to the mappings between multicast destination MAC
addresses and Layer 2 protocols, and then forwards the packets to user networks.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
396
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
11 Layer 2 Protocol Transparent Transmission Configuration
VLAN-based Layer 2 Protocol Transparent Transmission
Figure 11-3 VLAN-based Layer 2 protocol transparent transmission
LAN-B
MSTP
LAN-B
MSTP
CE-VLAN 100
CE-VLAN 100
PE 1
ISP Network
PE 2
BPDU Tunnel
CE-VLAN 200
Trunk
100-200
Trunk
100-200
PE 3
CE-VLAN 200
CE-VLAN 100
LAN-A
MSTP
LAN-A
MSTP
LAN-B
MSTP
A PE generally functions as an aggregation device. As shown in Figure 11-3, the aggregation
interface on PE1 can receive BPDUs from LAN-A and LAN-B. To differentiate BPDUs from
the two LANs, BPDUs sent from CEs to PEs must have VLAN tags. In Figure 11-3, packets
sent from LAN-A contain VLAN 200 and packets sent from LAN-B contain VLAN 100.
Packets of certain Layer 2 protocols such as STP, RSTP, and MSTP are untagged. When
receiving Layer 2 protocol packets with VLAN tags, PEs consider the packets invalid and discard
them. In this case, you can configure VLAN-based Layer 2 protocol transparent transmission
on PEs so that Layer 2 protocol packets can traverse the backbone network through Layer 2
tunnels.
Similar to interface-based Layer 2 protocol transparent transmission, you can use either of the
following methods to implement VLAN-based Layer 2 protocol transparent transmission:
l
Issue 02 (2011-11-21)
Replace the default multicast MAC address of the Layer 2 protocol that can be identified
by PEs with another multicast MAC address.
1.
Configure all PEs as providers. Then the multicast destination MAC address of
BPDUs sent from the backbone network is changed from 01-80-C2-00-00-00 to
01-80-C2-00-00-08.
2.
Configure all devices on user networks as customers. Then the multicast destination
MAC address of BPDUs sent from user networks is 01-80-C2-00-00-00.
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
397
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
11 Layer 2 Protocol Transparent Transmission Configuration
3.
Configure devices on user networks to send Layer 2 protocol packets with the specified
VLAN IDs to the backbone network.
4.
Enable PEs to identify Layer 2 protocol packets with the specified VLAN IDs and
allow these packets to pass.
5.
PEs (providers) do not consider these packets as Layer 2 protocol BPDUs and do not
send them to the CPU. Instead, PEs select a Layer 2 tunnel to forward the packets
according to the default VLANs of interfaces.
6.
Internal nodes on the backbone network forward the packets across the backbone
network as common Layer 2 packets.
7.
The egress device on the backbone network forwards the packets to user networks
without modifying the packets.
NOTE
l This method is applicable only to STP, RSTP, and MSTP. To configure a device as the provider,
run the bpdu-tunnel stp bridge role provider command.
l The S5700HI and S5706 do not support this method.
Replace the original multicast MAC address of Layer 2 protocol packets from user networks
with a specified multicast MAC address.
NOTE
This method is applicable to all Layer 2 protocols.
1.
Configure devices on user networks to send Layer 2 protocol packets with the specified
VLAN IDs to the backbone network.
2.
Enable PEs to identify Layer 2 protocol packets with the specified VLAN IDs and
allow these packets to pass.
3.
PEs replace the standard multicast destination MAC address of Layer 2 protocol
packets with a specified multicast MAC address according to the mappings between
multicast destination MAC addresses and Layer 2 protocols.
4.
Internal nodes on the backbone network forward the packets across the backbone
network as common Layer 2 packets.
5.
The egress device of the backbone network restores the original destination MAC
address of the packets according to the mappings between multicast destination MAC
addresses and Layer 2 protocols, and then forwards the packets to user networks.
QinQ-based Layer 2 Protocol Transparent Transmission
The QinQ protocol is a Layer 2 tunneling protocol based on IEEE 802.1Q. The QinQ technology
adds another 802.1Q tag to a packet so that services on a private VLAN can be transparently
transmitted to the public network. A packet transmitted on the backbone network is called a
QinQ packet because it has two 802.1Q tags (a public tag and a private tag), that is, 802.1Qin-802.1Q.
Figure 11-4 shows the format of a QinQ packet. Compared with an 802.1Q packet, a QinQ
packet contains an additional tag following the source address (SA) field. This tag is called an
outer tag or a public tag and contains the VLAN ID of the public network. The inner tag is known
as the private tag and contains the VLAN ID of the private network.
NOTE
The QinQ function configured on a Layer 2 interface is called VLAN stacking.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
398
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
11 Layer 2 Protocol Transparent Transmission Configuration
Figure 11-4 802.1Q encapsulation and QinQ encapsulation
802.1Q Encapsulation
DA
SA
ETYPE TAG LEN/ETYPE
DATA
FCS
6 Bytes 6 Bytes 2 Bytes 2 Bytes 2 Bytes 46 Byte~1500 Bytes 4 Bytes
QinQ
Encapsulation
DA
SA ETYPE TAG ETYPE TAG LEN/ETYPE
DATA
FCS
6 Bytes 6 Bytes 2 Bytes 2 Bytes 2 Bytes 2 Bytes 2 Bytes
46 Byte~1500 Bytes 4 Bytes
0x8100
Priority
CFI VLAN ID
When a large number of user networks are connected to the backbone network, considerable
number of VLAN IDs are required on the ISP network if packets are transparently transmitted
based on VLANs. To reduce the number of VLANs required, BPDUs can be forwarded in QinQ
mode on the backbone network.
Figure 11-5 QinQ-based Layer 2 protocol transparent transmission
LAN-B
MSTP
LAN-B
MSTP
PE-VLAN20:CE-VLAN 100~199
PE 1
CE-VLAN 100
ISP Network
PE 2
BPDU Tunnel
CE-VLAN 100
BPDU Tunnel
CE-VLAN 200
CE-VLAN 200
PE-VLAN30:CE-VLAN 200~299
LAN-A
MSTP
LAN-A
MSTP
As shown in Figure 11-5, QinQ-based Layer 2 protocol transparent transmission is configured
on aggregation interfaces of PEs. Packets from different user networks are encapsulated in
different outer VLAN tags. QinQ-based Layer 2 protocol transparent transmission is
implemented as follows:
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
399
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
11 Layer 2 Protocol Transparent Transmission Configuration
1.
Configure devices on user networks to send Layer 2 protocol packets with the specified
VLAN IDs to the backbone network.
2.
Enable Layer 2 protocol transparent transmission and QinQ on interfaces of the ingress
device on the backbone network.
3.
Configure PEs to add different outer VLAN tags (public VLAN IDs) to packets according
to customer VLAN IDs.
4.
PEs select different Layer 2 tunnels according to outer VLAN tags of packets. Then the
Layer 2 protocol packets are forwarded by internal nodes on the backbone network as
common Layer 2 packets.
5.
Enable Layer 2 protocol transparent transmission and QinQ on interfaces of the egress
device on the backbone network.
6.
The egress device removes outer VLAN tags of the packets and forwards the packets to
user networks according to customer VLAN IDs.
As shown in Figure 11-5, PEs add outer VLAN 20 to Layer 2 protocol packets of VLANs 100
to 199, and add outer VLAN 30 to Layer 2 protocol packets of VLANs 200 to 299. The PEs
then forward the packets to other devices on the backbone network. In this way, Layer 2 protocol
packets of different user networks are transparently transmitted on the backbone network, and
carrier uses fewer VLAN IDs.
11.3 Configuring Interface-based Layer 2 Protocol
Transparent Transmission
When each interface of a backbone device is connected to only one user network and Layer 2
protocol packets sent from the user network do not need VLAN tags, configure interface-based
Layer 2 protocol transparent transmission on the interface connected to the user network. This
configuration allows Layer 2 protocol packets to be transparently transmitted on the backbone
network.
11.3.1 Establishing the Configuration Task
Applicable Environment
When each interface of a backbone device is connected to only one user network and Layer 2
protocol packets sent from the user network do not need VLAN tags, configure interface-based
Layer 2 protocol transparent transmission on the interface connected to the user network. This
configuration enables Layer 2 protocol packets to be transmitted between user networks through
different Layer 2 tunnels on the backbone network for Layer 2 protocol calculation.
Pre-configuration Tasks
Before configuring interface-based Layer 2 protocol transparent transmission, complete the
following tasks:
l
Connecting interfaces correctly
Configuring VLANs on Layer 2 interfaces
Using the bpdu enable command to enable the interfaces to send BPDUs to the CPU
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
400
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
11 Layer 2 Protocol Transparent Transmission Configuration
Data Preparation
To configure interface-based Layer 2 protocol transparent transmission, you need the following
data.
No.
Data
Name of the user-defined protocol
Destination MAC address of Layer 2 protocol packets and multicast MAC address
that replaces the destination MAC address
Names of the user-side interfaces on PEs and their default VLANs
11.3.2 (Optional) Defining Characteristics of a Layer 2 Protocol
Context
When non-standard Layer 2 protocol packets with a specified multicast destination address need
to be transparently transmitted on the backbone network, you can define characteristics of the
Layer 2 protocol.
Perform the following steps on PEs.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
l2protocol-tunnel user-defined-protocol protocol-name protocol-mac protocol-mac
[ encape-type { { ethernetii | snap } protocol-type protocol-type | llc dsap dsapvalue ssap ssap-value } ] group-mac { group-mac | default-group-mac }
The characteristics of the Layer 2 protocol are defined, including the protocol name, Ethernet
encapsulation format and destination MAC address of Layer 2 protocol packets, and MAC
address that replaces the destination MAC address.
Do not use the following multicast MAC addresses to replace the destination MAC address of
Layer 2 protocol packets:
l Destination MAC addresses of BPDUs: 0180-C200-0000 to 0180-C200-002F
l Destination MAC address of Smart Link packets: 010F-E200-0004
l Special multicast MAC addresses: 0100-0CCC-CCCC and 0100-0CCC-CCCD
l Common multicast MAC addresses that have been used on the device
----End
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
401
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
11 Layer 2 Protocol Transparent Transmission Configuration
11.3.3 Configuring the Transparent Transmission Mode of Layer 2
Protocol Packets
Context
To implement transparent transmission of Layer 2 protocol packets, replace the default multicast
MAC address of the Layer 2 protocol that can be identified by PEs with another multicast MAC
address or replace the original multicast destination MAC address of Layer 2 protocol packets
from user networks with a specified multicast MAC address.
Use either of the following methods on PEs according to the Layer 2 protocol type and the
required transparent transmission mode.
Procedure
l
Replace the default multicast MAC address of the Layer 2 protocol that can be identified
by PEs with another multicast MAC address.
1.
Run:
system-view
The system view is displayed.
2.
Run:
bpdu-tunnel stp bridge role provider
The PE is configured as a provider.
NOTE
l This method is applicable only to STP, RSTP, and MSTP.
l The S5700HI and S5706 do not support this method.
Replace the original multicast MAC address of Layer 2 protocol packets from user networks
with a specified multicast MAC address.
1.
Run:
system-view
The system view is displayed.
2.
Run:
l2protocol-tunnel protocol-type group-mac group-mac
The original multicast destination MAC address of Layer 2 protocol packets is
replaced with a specified multicast MAC address.
NOTE
This method is applicable to all Layer 2 protocols.
When configuring Layer 2 protocol transparent transmission, do not use the following multicast
MAC addresses to replace the destination MAC address of Layer 2 protocol packets:
l Destination MAC addresses of BPDUs: 0180-C200-0000 to 0180-C200-002F
l Destination MAC address of Smart Link packets: 010F-E200-0004
l Special multicast MAC addresses: 0100-0CCC-CCCC and 0100-0CCC-CCCD
l Common multicast MAC addresses that have been used on the device
----End
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
402
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
11 Layer 2 Protocol Transparent Transmission Configuration
11.3.4 Enabling Layer 2 Protocol Transparent Transmission on an
Interface
Context
Perform the following steps on PEs when you need to add an outer VLAN tag to Layer 2 protocol
packets.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
interface interface-type interface-number
The user-side interface view is displayed.
Step 3 Run:
port hybrid pvid vlan vlan-id
The default VLAN of the interface is configured.
Step 4 Run:
port hybrid untagged vlan vlan-id
The interface is added to the default VLAN in untagged mode.
Step 5 Run:
port hybrid tagged vlan { { vlan-id1 [ to vlan-id2 ] } &<1-10> | all }
The interface is added to the specified VLANs in tagged mode.
NOTE
The range of VLAN IDs specified in this step must include VLAN IDs of Layer 2 protocol packets from
user networks.
Step 6 Run:
l2protocol-tunnel { all | protocol-type | user-defined-protocol protocol-name }
enable
Layer 2 protocol transparent transmission is enabled on the interface.
NOTE
l For details on how to add an interface to VLANs, see "VLAN Configuration."
l Before specifying a user-defined protocol in the l2protocol-tunnel command, run the l2protocoltunnel user-defined-protocol command to define characteristic information about the Layer 2
protocol. STP packets have a default MAC address to replace the original destination MAC address.
For packets of other Layer 2 protocols, configure a global MAC address to replace the destination MAC
address. For details, see l2protocol-tunnel group-mac.
l The l2protocol-tunnel and l2protocol-tunnel vlan commands cannot specify the same protocol type
on the same interface; otherwise, the configurations conflict.
----End
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
403
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
11 Layer 2 Protocol Transparent Transmission Configuration
11.3.5 Checking Configuration
Context
Configuration of interface-based Layer 2 protocol transparent transmission is complete.
Procedure
l
Run the display l2protocol-tunnel group-mac { all | protocol-type | user-definedprotocol protocol-name } command to check information about transparent transmission
of specified or all Layer 2 protocol packets.
----End
11.4 Configuring VLAN-based Layer 2 Protocol Transparent
Transmission
When each interface of a backbone device is connected to multiple user networks and Layer 2
protocol packets sent from user networks contain VLAN tags, configure VLAN-based Layer 2
protocol transparent transmission. This configuration allows Layer 2 protocol packets to be
transparently transmitted on the backbone network.
11.4.1 Establishing the Configuration Task
Applicable Environment
When each interface of a backbone device is connected to multiple user networks and Layer 2
protocol packets sent from user networks contain VLAN tags, configure VLAN-based Layer 2
protocol transparent transmission. This configuration enables Layer 2 protocol packets to be
transmitted between user networks through different Layer 2 tunnels on the backbone network
for Layer 2 protocol calculation.
Pre-configuration Tasks
Before configuring VLAN-based Layer 2 protocol transparent transmission, complete the
following tasks:
l
Connecting interfaces correctly
Using the bpdu enable command to enable interfaces to send BPDUs to the CPU
Data Preparation
To configure VLAN-based Layer 2 protocol transparent transmission, you need the following
data.
Issue 02 (2011-11-21)
No.
Data
Name of the user-defined protocol
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
404
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
11 Layer 2 Protocol Transparent Transmission Configuration
No.
Data
Destination MAC address of Layer 2 protocol packets and multicast MAC address
that replaces the destination MAC address
Names of user-side interfaces on PEs and VLANs allowed by user-side interfaces
11.4.2 (Optional) Defining Characteristics of a Layer 2 Protocol
Context
When non-standard Layer 2 protocol packets with a specified multicast destination address need
to be transparently transmitted on the backbone network, you can define characteristics of the
Layer 2 protocol.
Perform the following steps on PEs.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
l2protocol-tunnel user-defined-protocol protocol-name protocol-mac protocol-mac
[ encape-type { { ethernetii | snap } protocol-type protocol-type | llc dsap dsapvalue ssap ssap-value } ] group-mac { group-mac | default-group-mac }
The characteristics of the Layer 2 protocol are defined, including the protocol name, Ethernet
encapsulation format and destination MAC address of Layer 2 protocol packets, and MAC
address that replaces the destination MAC address.
Do not use the following multicast MAC addresses to replace the destination MAC address of
Layer 2 protocol packets:
l Destination MAC addresses of BPDUs: 0180-C200-0000 to 0180-C200-002F
l Destination MAC address of Smart Link packets: 010F-E200-0004
l Special multicast MAC addresses: 0100-0CCC-CCCC and 0100-0CCC-CCCD
l Common multicast MAC addresses that have been used on the device
----End
11.4.3 Configuring the Transparent Transmission Mode of Layer 2
Protocol Packets
Context
To implement transparent transmission of Layer 2 protocol packets, replace the default multicast
MAC address of the Layer 2 protocol that can be identified by PEs with another multicast MAC
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
405
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
11 Layer 2 Protocol Transparent Transmission Configuration
address or replace the original multicast destination MAC address of Layer 2 protocol packets
from user networks with a specified multicast MAC address.
Use either of the following methods on PEs according to the Layer 2 protocol type and the
required transparent transmission mode.
Procedure
l
Replace the default multicast MAC address of the Layer 2 protocol that can be identified
by PEs with another multicast MAC address.
1.
Run:
system-view
The system view is displayed.
2.
Run:
bpdu-tunnel stp bridge role provider
The PE is configured as a provider.
NOTE
l This method is applicable only to STP, RSTP, and MSTP.
l The S5700HI and S5706 do not support this method.
Replace the original multicast MAC address of Layer 2 protocol packets from user networks
with a specified multicast MAC address.
1.
Run:
system-view
The system view is displayed.
2.
Run:
l2protocol-tunnel protocol-type group-mac group-mac
The original multicast destination MAC address of Layer 2 protocol packets is
replaced with a specified multicast MAC address.
NOTE
This method is applicable to all Layer 2 protocols.
When configuring Layer 2 protocol transparent transmission, do not use the following multicast
MAC addresses to replace the destination MAC address of Layer 2 protocol packets:
l Destination MAC addresses of BPDUs: 0180-C200-0000 to 0180-C200-002F
l Destination MAC address of Smart Link packets: 010F-E200-0004
l Special multicast MAC addresses: 0100-0CCC-CCCC and 0100-0CCC-CCCD
l Common multicast MAC addresses that have been used on the device
----End
11.4.4 Enabling VLAN-based Layer 2 Protocol Transparent
Transmission on an Interface
Context
Perform the following steps on PEs according to the type of Layer 2 protocol packets to be
transparently transmitted.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
406
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
11 Layer 2 Protocol Transparent Transmission Configuration
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
interface interface-type interface-number
The user-side interface view is displayed.
Step 3 Run:
port hybrid tagged vlan { { vlan-id1 [ to vlan-id2 ] } &<1-10> | all }
The interface is added to the specified VLANs in tagged mode.
NOTE
The range of VLAN IDs specified in this step must include VLAN IDs of Layer 2 protocol packets from
user networks.
Step 4 Run:
l2protocol-tunnel { all | protocol-type | user-defined-protocol protocol-name }
{ vlan low-id [ to high-id ] } &<1-10>
VLAN-based Layer 2 protocol transparent transmission is enabled on the interface.
NOTE
l For details on how to add an interface to VLANs in tagged mode, see the VLAN configuration in the
S5700 Configuration Guide- Ethernet.
l Before specifying a user-defined protocol in the l2protocol-tunnel vlan command, run the l2protocoltunnel user-defined-protocol command to define characteristic information about the Layer 2
protocol. STP packets have a default MAC address to replace the original destination MAC address.
For packets of other Layer 2 protocols, configure a global MAC address to replace the destination MAC
address. For details, see l2protocol-tunnel group-mac.
l The l2protocol-tunnel vlan and l2protocol-tunnel commands cannot specify the same protocol type
on the same interface; otherwise, the configurations conflict.
----End
11.4.5 Checking the Configuration
Context
Configurations of Layer 2 protocol transparent transmission are complete.
Procedure
l
Run the display l2protocol-tunnel group-mac { all | protocol-type | user-definedprotocol protocol-name } command to check information about transparent transmission
of specified or all Layer 2 protocol packets.
----End
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
407
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
11 Layer 2 Protocol Transparent Transmission Configuration
11.5 Configuring QinQ-based Layer 2 Protocol Transparent
Transmission
When each interface of backbone devices is connected to multiple user networks and Layer 2
protocol packets sent from user network contain VLAN tags, you can configure QinQ-based
Layer 2 protocol transparent transmission. This configuration allows Layer 2 protocol packets
to be transparently transmitted on the backbone network and reduces VLAN IDs that the carrier
uses.
11.5.1 Establishing the Configuration Task
Applicable Environment
When each interface of backbone devices is connected to multiple user networks and Layer 2
protocol packets sent from user networks contain VLAN tags, you can configure QinQ-based
Layer 2 protocol transparent transmission to help the carrier conserve VLAN IDs. In this way,
devices on the backbone network select tunnels for Layer 2 protocol packets according to outer
VLAN IDs so that Layer 2 protocol packets of different VLANs are transmitted across the
backbone network through different tunnels.
Pre-configuration Tasks
Before configuring QinQ-based Layer 2 protocol transparent transmission, complete the
following tasks:
l
Connecting interfaces correctly
Using the bpdu enable command to enable interfaces to send BPDUs to the CPU
Data Preparation
To configure QinQ-based Layer 2 protocol transparent transmission, you need the following
data.
No.
Data
Name of the user-defined protocol
Destination MAC address and group MAC address of Layer 2 protocol packets
Names of user-side interfaces on PEs, default VLAN IDs, and VLANs allowed by
user-side interfaces
Outer VLAN IDs added to Layer 2 protocol packets
11.5.2 (Optional) Defining Characteristics of a Layer 2 Protocol
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
408
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
11 Layer 2 Protocol Transparent Transmission Configuration
Context
When non-standard Layer 2 protocol packets with a specified multicast destination address need
to be transparently transmitted on the backbone network, you can define characteristics of the
Layer 2 protocol.
Perform the following steps on PEs.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
l2protocol-tunnel user-defined-protocol protocol-name protocol-mac protocol-mac
[ encape-type { { ethernetii | snap } protocol-type protocol-type | llc dsap dsapvalue ssap ssap-value } ] group-mac { group-mac | default-group-mac }
The characteristics of the Layer 2 protocol are defined, including the protocol name, Ethernet
encapsulation format and destination MAC address of Layer 2 protocol packets, and MAC
address that replaces the destination MAC address.
Do not use the following multicast MAC addresses to replace the destination MAC address of
Layer 2 protocol packets:
l Destination MAC addresses of BPDUs: 0180-C200-0000 to 0180-C200-002F
l Destination MAC address of Smart Link packets: 010F-E200-0004
l Special multicast MAC addresses: 0100-0CCC-CCCC and 0100-0CCC-CCCD
l Common multicast MAC addresses that have been used on the device
----End
11.5.3 Configuring the Transparent Transmission Mode of Layer 2
Protocol Packets
Context
To implement transparent transmission of Layer 2 protocol packets, replace the default multicast
MAC address of the Layer 2 protocol that can be identified by PEs with another multicast MAC
address or replace the original multicast destination MAC address of Layer 2 protocol packets
from user networks with a specified multicast MAC address.
Use either of the following methods on PEs according to the Layer 2 protocol type and the
required transparent transmission mode.
Procedure
l
Replace the default multicast MAC address of the Layer 2 protocol that can be identified
by PEs with another multicast MAC address.
1.
Run:
system-view
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
409
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
11 Layer 2 Protocol Transparent Transmission Configuration
The system view is displayed.
2.
Run:
bpdu-tunnel stp bridge role provider
The PE is configured as a provider.
NOTE
l This method is applicable only to STP, RSTP, and MSTP.
l The S5700HI and S5706 do not support this method.
Replace the original multicast MAC address of Layer 2 protocol packets from user networks
with a specified multicast MAC address.
1.
Run:
system-view
The system view is displayed.
2.
Run:
l2protocol-tunnel protocol-type group-mac group-mac
The original multicast destination MAC address of Layer 2 protocol packets is
replaced with a specified multicast MAC address.
NOTE
When configuring Layer 2 protocol transparent transmission, do not use the following multicast
MAC addresses to replace the destination MAC address of Layer 2 protocol packets:
l Destination MAC addresses of BPDUs: 0180-C200-0000 to 0180-C200-002F
l Destination MAC address of Smart Link packets: 010F-E200-0004
l Special multicast MAC addresses: 0100-0CCC-CCCC and 0100-0CCC-CCCD
l Common multicast MAC addresses that have been used on the device
----End
11.5.4 Enabling QinQ-based Layer 2 Transparent Transmission on
an Interface
Context
Perform the following steps on PEs according to the type of Layer 2 protocol packets to be
transparently transmitted.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
interface interface-type interface-number
The user-side interface view is displayed.
Step 3 Run:
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
410
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
11 Layer 2 Protocol Transparent Transmission Configuration
port hybrid untagged vlan { { vlan-id1 [ to vlan-id2 ] } &<1-10> | all }
The interface is added to the specified VLANs in untagged mode.
Step 4 Run:
qinq vlan-translation enable
VLAN translation is enabled on the interface.
Step 5 Run:
port vlan-stacking vlan vlan-id1 [ to vlan-id2 ] stack-vlan vlan-id3
The interface is configured to add an outer VLAN tag to the Layer 2 protocol packets.
Step 6 Run:
l2protocol-tunnel { all | protocol-type | user-defined-protocol protocol-name }
{ vlan low-id [ to high-id ] } &<1-10>
VLAN-based Layer 2 protocol transparent transmission is enabled on the interface.
NOTE
l The outer VLAN tag (vlan-id3) specified in step 5 must be included in the VLAN range specified in
step 6.
l For details on how to add an interface to VLANs in untagged mode, see the VLAN configuration in
the S5700 Configuration Guide- Ethernet.
l Before specifying a user-defined protocol in the l2protocol-tunnel vlan command, run the l2protocoltunnel user-defined-protocol command to define characteristic information about the Layer 2
protocol. STP packets have a default MAC address to replace the original destination MAC address.
For packets of other Layer 2 protocols, configure a global MAC address to replace the destination MAC
address. For details, see l2protocol-tunnel group-mac.
l The l2protocol-tunnel vlan and l2protocol-tunnel commands cannot specify the same protocol type
on the same interface; otherwise, the configurations conflict.
----End
11.5.5 Checking the Configuration
Context
Configurations of Layer 2 protocol transparent transmission are complete.
Procedure
l
Run the display l2protocol-tunnel group-mac { all | protocol-type | user-definedprotocol protocol-name } command to check information about transparent transmission
of specified or all Layer 2 protocol packets.
----End
11.6 Maintaining Layer 2 Protocol Transparent
Transmission
This section describes how to debug Layer 2 protocol transparent transmission.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
411
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
11 Layer 2 Protocol Transparent Transmission Configuration
11.6.1 Debugging Layer 2 Protocol Transparent Transmission
Context
CAUTION
Debugging affects the performance of the system. Therefore, run the undo debugging all
command to disable debugging immediately after the debugging is complete.
When a fault occurs during Layer 2 protocol transparent transmission, run the following
debugging command in the user view to locate the fault.
Procedure
l
Run the debugging l2protocol-tunnel [ msg | error | event ] command in the user view
to enable Layer 2 protocol transparent transmission.
----End
11.7 Configuration Examples
This section provides examples for configuring interface, VLAN, and QinQ based Layer 2
protocol transparent transmission.
11.7.1 Example for Configuring Interface-based Layer 2 Protocol
Transparent Transmission
Networking Requirements
As shown in Figure 11-6, CEs on user networks communicate with each other through PEs and
STP runs on user networks; therefore, STP packets sent from CEs must be transmitted through
the backbone network between PEs. Each PE interface is connected to only one CE and receives
STP packets from the CE. In this scenario, configure interface-based Layer 2 protocol transparent
transmission.
In this example, PEs on the backbone network transparently transmit STP packets sent from CEs
by replacing the original multicast destination MAC address of STP packets with a specified
MAC address. By default, the destination MAC address of STP packets is 0180-C200-0000.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
412
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
11 Layer 2 Protocol Transparent Transmission Configuration
Figure 11-6 Networking of interface-based Layer 2 protocol transparent transmission
VLAN100
VLAN100
CE1
CE2
GE 0/0/1
PE1
GE 0/0/1
GE 0/0/1
PE2
GE 0/0/1
GE 0/0/3
GE 0/0/2
GE0/0/3
GE0/0/1
GE 0/0/2
GE 0/0/1
CE3
CE4
VLAN200
VLAN200
Configuration Roadmap
The configuration roadmap is as follows:
1.
Configure STP on CEs.
2.
Add user-side interfaces of PEs to the specified VLANs.
3.
Configure interface-based Layer 2 protocol transparent transmission on PEs.
4.
Configure network-side interfaces of PEs to allow packets of VLAN 100 and VLAN 200
to pass.
Data Preparation
To complete the configuration, you need the following data:
l
IDs of VLANs that user-side interfaces of PEs belong to
IDs of VLANs allowed by network-side interfaces of PEs
Procedure
Step 1 Enable STP on CEs and PEs.
# Configure CE1.
<Quidway> system-view
[Quidway] sysname CE1
[CE1] vlan 100
[CE1-vlan100] quit
[CE1] stp enable
[CE1] interface gigabitethernet 0/0/1
[CE1-GigabitEthernet0/0/1] port hybrid pvid vlan 100
[CE1-GigabitEthernet0/0/1] port hybrid untagged vlan 100
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
413
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
11 Layer 2 Protocol Transparent Transmission Configuration
[CE1-GigabitEthernet0/0/1] bpdu enable
# Configure CE2.
<Quidway> system-view
[Quidway] sysname CE2
[CE2] vlan 100
[CE2-vlan100] quit
[CE2] stp enable
[CE2] interface gigabitethernet
[CE2-GigabitEthernet0/0/1] port
[CE2-GigabitEthernet0/0/1] port
[CE2-GigabitEthernet0/0/1] bpdu
0/0/1
hybrid pvid vlan 100
hybrid untagged vlan 100
enable
# Configure CE3.
<Quidway> system-view
[Quidway] sysname CE3
[CE3] vlan 200
[CE3-vlan200] quit
[CE3] stp enable
[CE3] interface gigabitethernet
[CE3-GigabitEthernet0/0/1] port
[CE3-GigabitEthernet0/0/1] port
[CE3-GigabitEthernet0/0/1] bpdu
0/0/1
hybrid pvid vlan 200
hybrid untagged vlan 200
enable
# Configure CE4.
<Quidway> system-view
[Quidway] sysname CE4
[CE4] vlan 200
[CE4-vlan200] quit
[CE4] stp enable
[CE4] interface gigabitethernet
[CE4-GigabitEthernet0/0/1] port
[CE4-GigabitEthernet0/0/1] port
[CE4-GigabitEthernet0/0/1] bpdu
0/0/1
hybrid pvid vlan 200
hybrid untagged vlan 200
enable
# Configure PE1.
<Quidway> system-view
[Quidway] sysname PE1
[PE1]
# Configure PE2.
<Quidway> system-view
[Quidway] sysname PE2
[PE2]
Step 2 On PE1 and PE2, add GE 0/0/1 to VLAN 100, add GE 0/0/2 to VLAN 200, and enable Layer 2
protocol transparent transmission.
# Configure PE1.
[PE1] vlan 100
[PE1-vlan100] quit
[PE1] interface GigabitEthernet 0/0/1
[PE1-GigabitEthernet0/0/1] port hybrid pvid vlan 100
[PE1-GigabitEthernet0/0/1] port hybrid untagged vlan 100
[PE1-GigabitEthernet0/0/1] l2protocol-tunnel stp enable
[PE1-GigabitEthernet0/0/1] bpdu enable
[PE1-GigabitEthernet0/0/1] quit
[PE1] vlan 200
[PE1-vlan200] quit
[PE1] interface GigabitEthernet 0/0/2
[PE1-GigabitEthernet0/0/2] port hybrid pvid vlan 200
[PE1-GigabitEthernet0/0/2] port hybrid untagged vlan 200
[PE1-GigabitEthernet0/0/2] l2protocol-tunnel stp enable
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
414
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
11 Layer 2 Protocol Transparent Transmission Configuration
[PE1-GigabitEthernet0/0/2] bpdu enable
[PE1-GigabitEthernet0/0/2] quit
# Configure PE2.
[PE2] vlan 100
[PE2-vlan100] quit
[PE2] interface GigabitEthernet 0/0/1
[PE2-GigabitEthernet0/0/1] port hybrid pvid vlan 100
[PE2-GigabitEthernet0/0/1] port hybrid untagged vlan 100
[PE2-GigabitEthernet0/0/1] l2protocol-tunnel stp enable
[PE2-GigabitEthernet0/0/1] bpdu enable
[PE2-GigabitEthernet0/0/1] quit
[PE2] vlan 200
[PE2-vlan200] quit
[PE2] interface GigabitEthernet 0/0/2
[PE2-GigabitEthernet0/0/2] port hybrid pvid vlan 200
[PE2-GigabitEthernet0/0/2] port hybrid untagged vlan 200
[PE2-GigabitEthernet0/0/2] l2protocol-tunnel stp enable
[PE2-GigabitEthernet0/0/2] bpdu enable
[PE2-GigabitEthernet0/0/2] quit
Step 3 Configure PEs to replace the destination MAC address of STP packets received from CEs.
# Configure PE1.
[PE1] l2protocol-tunnel stp group-mac 0100-5e00-0011
# Configure PE2.
[PE2] l2protocol-tunnel stp group-mac 0100-5e00-0011
Step 4 On PE1 and PE2, configure network-side interface GE 0/0/3 to allow packets of VLAN 100 and
VLAN 200 to pass.
# Configure PE1.
[PE1] interface gigabitethernet 0/0/3
[PE1-GigabitEthernet0/0/3] port hybrid tagged vlan 100 200
[PE1-GigabitEthernet0/0/3] quit
# Configure PE2.
[PE2] interface gigabitethernet 0/0/3
[PE2-GigabitEthernet0/0/3] port hybrid tagged vlan 100 200
[PE2-GigabitEthernet0/0/3] quit
Step 5 Verify the configuration.
After the configuration is complete, run the display l2protocol-tunnel group-mac command
to view the protocol type or name, original destination MAC address, new destination MAC
address, and priority of Layer 2 protocol packets to be transparently transmitted.
The output on PE1 is used as an example:
<PE1> display l2protocol-tunnel group-mac stp
Protocol
EncapeType ProtocolType Protocol-MAC
Group-MAC
Pri
----------------------------------------------------------------------------stp
llc
dsap 0x42
0180-c200-0000 0100-5e00-0011 0
ssap 0x42
Run the display stp command on CE1 and CE2 to view the root in the MST region. The command
output shows that a spanning tree is calculated between CE1 and CE2. GE 0/0/1 of CE1 is a root
port, and CE 0/0/1 of CE2 is a designated port.
<CE1> display stp
-------[CIST Global Info] [Mode MSTP] ------CIST Bridge
:32768.00e0-fc9f-3257
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
415
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
11 Layer 2 Protocol Transparent Transmission Configuration
Bridge Times
:Hello 2s MaxAge 20s FwDly 15s MaxHop 20
CIST Root/ERPC
:32768.00e0-fc9a-4315 / 199999
CIST RegRoot/IRPC
:32768.00e0-fc9f-3257 / 0
CIST RootPortId
:128.82
BPDU-Protection
:disabled
TC or TCN received :6
TC count per hello :6
STP Converge Mode
:Normal
Time since last TC received :0 days 2h:24m:36s
----[Port1(GigabitEthernet0/0/1)] [FORWARDING] ---Port Protocol
:enabled
Port Role
:Root Port
Port Priority
:128
Port Cost(Dot1T )
:Config=auto / Active=200000000
Desg. Bridge/Port
:32768.00e0-fc9a-4315 / 128.82
Port Edged
:Config=disabled / Active=disabled
Point-to-point
:Config=auto / Active=true
Transit Limit
:147 packets/hello-time
Protection Type
:None
Port Stp Mode
:MSTP
Port Protocol Type :Config=auto / Active= dot1s
BPDU Encapsulation :Config=stp / Active=stp
PortTimes
:Hello 2s MaxAge 20s FwDly 15s RemHop 20
TC or TCN send
:0
TC or TCN received :0
BPDU Sent
:6
TCN: 0, Config: 0, RST: 0, MST: 6
BPDU Received
:4351
TCN: 0, Config: 0, RST: 0, MST: 4351
<CE2> display stp
-------[CIST Global Info] [Mode MSTP] ------CIST Bridge
:32768.00e0-fc9a-4315
Bridge Times
:Hello 2s MaxAge 20s FwDly 15s MaxHop 20
CIST Root/ERPC
:32768.00e0-fc9a-4315 / 0
CIST RegRoot/IRPC
:32768.00e0-fc9a-4315 / 0
CIST RootPortId
:0.0
BPDU-Protection
:disabled
TC or TCN received :3
TC count per hello :3
STP Converge Mode
:Normal
Time since last TC received :0 days 2h:26m:42s
----[Port1(GigabitEthernet0/0/1)] [FORWARDING] ---Port Protocol
:enabled
Port Role
:Designated Port
Port Priority
:128
Port Cost(Dot1T )
:Config=auto / Active=200000000
Desg. Bridge/Port
:32768.00e0-fc9a-4315 / 128.82
Port Edged
:Config=disabled / Active=disabled
Point-to-point
:Config=auto / Active=true
Transit Limit
:147 packets/hello-time
Protection Type
:None
Port Stp Mode
:MSTP
Port Protocol Type :Config=auto / Active= dot1s
BPDU Encapsulation :Config=stp / Active=stp
PortTimes
:Hello 2s MaxAge 20s FwDly 15s RemHop 20
TC or TCN send
:0
TC or TCN received :0
BPDU Sent
:4534
TCN: 0, Config: 0, RST: 0, MST: 4534
BPDU Received
:6
TCN: 0, Config: 0, RST: 0, MST: 6
Run the display stp command on CE3 and CE4 to view the root in the MST region. The command
output shows that a spanning tree is calculated between CE3 and CE4. GE 0/0/1 of CE3 is a root
port, and CE 0/0/1 of CE4 is a designated port.
<CE3> display stp
-------[CIST Global Info][Mode MSTP]------CIST Bridge
:32768.000b-0967-58a0
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
416
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
11 Layer 2 Protocol Transparent Transmission Configuration
Bridge Times
:Hello 2s MaxAge 20s FwDly 15s MaxHop 20
CIST Root/ERPC
:32768.000b-0952-f13e / 199999
CIST RegRoot/IRPC
:32768.000b-0967-58a0 / 0
CIST RootPortId
:128.82
BPDU-Protection
:disabled
TC or TCN received :0
TC count per hello :0
STP Converge Mode
:Normal
Time since last TC received :0 days 10h:54m:37s
----[Port1(GigabitEthernet0/0/1)][FORWARDING]---Port Protocol
:enabled
Port Role
:Root Port
Port Priority
:128
Port Cost(Dot1T )
:Config=auto / Active=200000000
Desg. Bridge/Port
:32768.000b-0952-f13e / 128.82
Port Edged
:Config=disabled / Active=disabled
Point-to-point
:Config=auto / Active=true
Transit Limit
:147 packets/hello-time
Protection Type
:None
Port Stp Mode
:MSTP
Port Protocol Type :Config=auto / Active= dot1s
BPDU Encapsulation :Config=stp / Active=stp
PortTimes
:Hello 2s MaxAge 20s FwDly 15s RemHop 20
TC or TCN send
:0
TC or TCN received :0
BPDU Sent
:114
TCN: 0, Config: 0, RST: 0, MST: 114
BPDU Received
:885
TCN: 0, Config: 0, RST: 0, MST: 885
<CE4> display stp
-------[CIST Global Info][Mode MSTP]------CIST Bridge
:32768.000b-0952-f13e
Bridge Times
:Hello 2s MaxAge 20s FwDly 15s MaxHop 20
CIST Root/ERPC
:32768.000b-0952-f13e / 0
CIST RegRoot/IRPC
:32768.000b-0952-f13e / 0
CIST RootPortId
:0.0
BPDU-Protection
:disabled
TC or TCN received :4
TC count per hello :4
STP Converge Mode
:Normal
Time since last TC received :0 days 8h:59m:18s
----[Port1(GigabitEthernet0/0/1)][FORWARDING]---Port Protocol
:enabled
Port Role
:Designated Port
Port Priority
:128
Port Cost(Dot1T )
:Config=auto / Active=200000000
Desg. Bridge/Port
:32768.000b-0952-f13e / 128.82
Port Edged
:Config=disabled / Active=disabled
Point-to-point
:Config=auto / Active=true
Transit Limit
:147 packets/hello-time
Protection Type
:None
Port Stp Mode
:MSTP
Port Protocol Type :Config=auto / Active= dot1s
BPDU Encapsulation :Config=stp / Active=stp
PortTimes
:Hello 2s MaxAge 20s FwDly 15s RemHop 20
TC or TCN send
:0
TC or TCN received :0
BPDU Sent
:1834
TCN: 0, Config: 0, RST: 0, MST: 1834
BPDU Received
:1
TCN: 0, Config: 0, RST: 0, MST: 1
----End
Configuration Files
l
Configuration file of CE1
#
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
417
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
11 Layer 2 Protocol Transparent Transmission Configuration
sysname CE1
#
vlan batch 100
#
interface GigabitEthernet0/0/1
port hybrid pvid vlan 100
port hybrid untagged vlan 100
#
return
Configuration file of CE2
#
sysname CE2
#
vlan batch 100
#
interface GigabitEthernet0/0/1
port hybrid pvid vlan 100
port hybrid untagged vlan 100
#
return
Configuration file of CE3
#
sysname CE3
#
vlan batch 200
#
interface GigabitEthernet0/0/1
port hybrid pvid vlan 200
port hybrid untagged vlan 200
#
return
Configuration file of CE4
#
sysname CE4
#
vlan batch 200
#
interface GigabitEthernet0/0/1
port hybrid pvid vlan 200
port hybrid untagged vlan 200
#
return
Configuration file of PE1
#
sysname PE1
#
vlan batch 100 200
#
l2protocol-tunnel stp group-mac 0100-5e00-0011
#
interface GigabitEthernet0/0/1
port hybrid pvid vlan 100
port hybrid untagged vlan 100
l2protocol-tunnel stp enable
#
interface GigabitEthernet0/0/2
port hybrid pvid vlan 200
port hybrid untagged vlan 200
l2protocol-tunnel stp enable
#
interface GigabitEthernet0/0/3
port hybrid tagged vlan 100 200
#
return
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
418
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
11 Layer 2 Protocol Transparent Transmission Configuration
Configuration file of PE2
#
sysname PE2
#
vlan batch 100 200
#
l2protocol-tunnel stp group-mac 0100-5e00-0011
#
interface GigabitEthernet0/0/1
port hybrid pvid vlan 100
port hybrid untagged vlan 100
l2protocol-tunnel stp enable
#
interface GigabitEthernet0/0/2
port hybrid pvid vlan 200
port hybrid untagged vlan 200
l2protocol-tunnel stp enable
#
interface GigabitEthernet0/0/3
port hybrid tagged vlan 100 200
#
return
11.7.2 Example for Configuring VLAN-based Layer 2 Protocol
Transparent Transmission
Networking Requirements
As shown in Figure 11-7, CEs on user networks communicate with each other through PEs and
STP runs on user networks; therefore, STP packets sent from CEs must be transmitted through
the backbone network between PEs. Each PE interface is an aggregation interface. PEs identify
STP packets from different user networks according to VLAN tags of STP packets. In this
scenario, configure VLAN-based Layer 2 protocol transparent transmission to ensure that:
l
All the devices in VLAN 100 participate in the calculation of a spanning tree.
All the devices in VLAN 200 participate in the calculation of a spanning tree.
In this example, PEs transparently transmit STP packets sent from user networks by replacing
the original multicast destination MAC address of STP packets with a specified multicast MAC
address. By default, the destination MAC address of STP packets is 0180-C200-0000.
Figure 11-7 Networking of VLAN-based Layer 2 protocol transparent transmission
PE1
PE2
GE0/0/1
GE0/0/1
GE0/0/1
GE0/0/2
GE0/0/3
GE0/0/2
GE0/0/1
GE0/0/1
CE1
CE3
VLAN 100
Issue 02 (2011-11-21)
GE0/0/2
VLAN 200
GE0/0/1
CE2
VLAN 100
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
GE0/0/3
GE0/0/1
CE4
VLAN 200
419
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
11 Layer 2 Protocol Transparent Transmission Configuration
Configuration Roadmap
The configuration roadmap is as follows:
1.
Enable STP on the CEs.
2.
Configure CEs to send STP packets with specified VLAN tags to PEs.
3.
Configure VLAN-based Layer 2 protocol transparent transmission on PEs.
4.
Configure network-side interfaces of PEs to allow packets of VLAN 100 and VLAN 200
to pass.
5.
Configure the Layer 2 forwarding function on the P device so that packets sent from PEs
can be transmitted on the backbone network.
Data Preparation
To complete the configuration, you need the following data:
l
VLAN tags in STP packets sent from CEs to PEs
IDs of the VLANs that interfaces of PEs and CEs belong to
Procedure
Step 1 Enable STP on CEs and PEs.
# Configure CE1.
[CE1] stp enable
# Configure CE2.
[CE2] stp enable
# Configure CE3.
[CE3] stp enable
# Configure CE4.
[CE4] stp enable
Step 2 Configure CE1 and CE2 to send STP packets with VLAN tag 100 to PEs and configure CE3
and CE4 to send STP packets with VLAN tag 200 to PEs.
# Configure CE1.
[CE1] vlan 100
[CE1-vlan100] quit
[CE1] interface gigabitethernet 0/0/1
[CE1-GigabitEthernet0/0/1] port hybrid tagged vlan 100
[CE1-GigabitEthernet0/0/1] stp bpdu vlan 100
[CE1-GigabitEthernet0/0/1] bpdu enable
# Configure CE2.
[CE2] vlan 100
[CE2-vlan100] quit
[CE2] interface gigabitethernet 0/0/1
[CE2-GigabitEthernet0/0/1] port hybrid tagged vlan 100
[CE2-GigabitEthernet0/0/1] stp bpdu vlan 100
[CE2-GigabitEthernet0/0/1] bpdu enable
# Configure CE3.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
420
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
11 Layer 2 Protocol Transparent Transmission Configuration
[CE3] vlan 200
[CE3-vlan200] quit
[CE3] interface gigabitethernet 0/0/1
[CE3-GigabitEthernet0/0/1] port hybrid tagged vlan 200
[CE3-GigabitEthernet0/0/1] stp bpdu vlan 200
[CE3-GigabitEthernet0/0/1] bpdu enable
# Configure CE4.
[CE4] vlan 200
[CE4-vlan200] quit
[CE4] interface gigabitethernet 0/0/1
[CE4-GigabitEthernet0/0/1] port hybrid tagged vlan 200
[CE4-GigabitEthernet0/0/1] stp bpdu vlan 200
[CE4-GigabitEthernet0/0/1] bpdu enable
Step 3 Configure PE interfaces to transparently transmit STP packets of CEs to the P device.
# Configure PE1.
[PE1] vlan 100
[PE1-vlan100] quit
[PE1] vlan 200
[PE1-vlan200] quit
[PE1] interface gigabitethernet 0/0/1
[PE1-GigabitEthernet0/0/1] port hybrid tagged vlan 100 200
[PE1-GigabitEthernet0/0/1] quit
[PE1] interface gigabitethernet 0/0/2
[PE1-GigabitEthernet0/0/2] port hybrid tagged vlan 100
[PE1-GigabitEthernet0/0/2] l2protocol-tunnel stp vlan 100
[PE1-GigabitEthernet0/0/2] bpdu enable
[PE1-GigabitEthernet0/0/2] quit
[PE1] interface gigabitethernet 0/0/3
[PE1-GigabitEthernet0/0/3] port hybrid tagged vlan 200
[PE1-GigabitEthernet0/0/3] l2protocol-tunnel stp vlan 200
[PE1-GigabitEthernet0/0/3] bpdu enable
[PE1-GigabitEthernet0/0/3] quit
# Configure PE2.
[PE2] vlan 100
[PE2-vlan100] quit
[PE2] vlan 200
[PE2-vlan200] quit
[PE2] interface gigabitethernet 0/0/1
[PE2-GigabitEthernet0/0/1] port hybrid tagged vlan 100 200
[PE2-GigabitEthernet0/0/1] quit
[PE2] interface gigabitethernet 0/0/2
[PE2-GigabitEthernet0/0/2] port hybrid tagged vlan 100
[PE2-GigabitEthernet0/0/2] l2protocol-tunnel stp vlan 100
[PE2-GigabitEthernet0/0/2] bpdu enable
[PE2-GigabitEthernet0/0/2] quit
[PE2] interface gigabitethernet 0/0/3
[PE2-GigabitEthernet0/0/3] port hybrid tagged vlan 200
[PE2-GigabitEthernet0/0/3] l2protocol-tunnel stp vlan 200
[PE2-GigabitEthernet0/0/3] bpdu enable
[PE2-GigabitEthernet0/0/3] quit
Step 4 Configure PEs to replace the destination MAC address of STP packets received from CEs.
# Configure PE1.
[PE1] l2protocol-tunnel stp group-mac 0100-5e00-0011
# Configure PE2.
[PE2] l2protocol-tunnel stp group-mac 0100-5e00-0011
Step 5 Configure the Layer 2 forwarding function on the P device and configure it to allow packets of
VLAN 100 and VLAN 200 to pass.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
421
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
[P] vlan 100
[P-vlan100] quit
[P] vlan 200
[P-vlan200] quit
[P] interface gigabitethernet
[P-GigabitEthernet0/0/1] port
[P-GigabitEthernet0/0/1] quit
[P] interface gigabitethernet
[P-GigabitEthernet0/0/2] port
[P-GigabitEthernet0/0/2] quit
11 Layer 2 Protocol Transparent Transmission Configuration
0/0/1
hybrid tagged vlan 100 200
0/0/2
hybrid tagged vlan 100 200
Step 6 Verify the configuration.
After the configuration is complete, run the display l2protocol-tunnel group-mac command.
You can view the protocol type or name, original destination MAC address, new destination
MAC address, and priority of Layer 2 protocol packets to be transparently transmitted.
Take the output on PE1 as an example.
<PE1> display l2protocol-tunnel group-mac stp
Protocol
EncapeType ProtocolType Protocol-MAC
Group-MAC
Pri
----------------------------------------------------------------------------stp
llc
dsap 0x42
0180-c200-0000 0100-5e00-0011 0
ssap 0x42
Run the display stp command on CE1 and CE2 to view the root in the MST region. The command
output shows that a spanning tree is calculated between CE1 and CE2. GE 0/0/1 of CE1 is a root
port, and CE 0/0/1 of CE2 is a designated port.
<CE1> display stp
-------[CIST Global Info][Mode MSTP]------CIST Bridge
:32768.000b-09f0-1b91
Bridge Times
:Hello 2s MaxAge 20s FwDly 15s MaxHop 20
CIST Root/ERPC
:32768.000b-09d4-b66c / 199999
CIST RegRoot/IRPC
:32768.000b-09f0-1b91 / 0
CIST RootPortId
:128.82
BPDU-Protection
:disabled
TC or TCN received :2
TC count per hello :2
STP Converge Mode
:Normal
Time since last TC received :0 days 3h:53m:43s
----[Port17(GigabitEthernet0/0/1)][FORWARDING]---Port Protocol
:enabled
Port Role
:Root Port
Port Priority
:128
Port Cost(Dot1T )
:Config=auto / Active=200000000
Desg. Bridge/Port
:32768.000b-09d4-b66c / 128.82
Port Edged
:Config=disabled / Active=disabled
Point-to-point
:Config=auto / Active=true
Transit Limit
:147 packets/hello-time
Protection Type
:None
Port Stp Mode
:MSTP
Port Protocol Type :Config=auto / Active= dot1s
BPDU Encapsulation :Config=stp / Active=stp
PortTimes
:Hello 2s MaxAge 20s FwDly 15s RemHop 20
TC or TCN send
:0
TC or TCN received :0
BPDU Sent
:237
TCN: 0, Config: 0, RST: 0, MST: 237
BPDU Received
:9607
TCN: 0, Config: 0, RST: 0, MST: 9607
<CE2> display stp
-------[CIST Global Info][Mode MSTP]------CIST Bridge
:32768.000b-09d4-b66c
Bridge Times
:Hello 2s MaxAge 20s FwDly 15s MaxHop 20
CIST Root/ERPC
:32768.000b-09d4-b66c / 0
CIST RegRoot/IRPC
:32768.000b-09d4-b66c / 0
CIST RootPortId
:0.0
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
422
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
11 Layer 2 Protocol Transparent Transmission Configuration
BPDU-Protection
:disabled
TC or TCN received :1
TC count per hello :1
STP Converge Mode
:Normal
Time since last TC received :0 days 5h:29m:6s
----[Port17(GigabitEthernet0/0/1)][FORWARDING]---Port Protocol
:enabled
Port Role
:Designated Port
Port Priority
:128
Port Cost(Dot1T )
:Config=auto / Active=200000000
Desg. Bridge/Port
:32768.000b-09d4-b66c / 128.82
Port Edged
:Config=disabled / Active=disabled
Point-to-point
:Config=auto / Active=true
Transit Limit
:147 packets/hello-time
Protection Type
:None
Port Stp Mode
:MSTP
Port Protocol Type :Config=auto / Active= dot1s
BPDU Encapsulation :Config=stp / Active=stp
PortTimes
:Hello 2s MaxAge 20s FwDly 15s RemHop 20
TC or TCN send
:0
TC or TCN received :0
BPDU Sent
:7095
TCN: 0, Config: 0, RST: 0, MST: 7095
BPDU Received
:2
TCN: 0, Config: 0, RST: 0, MST: 2
Run the display stp command on CE3 and CE4 to view the root in the MST region. The command
output shows that a spanning tree is calculated between CE3 and CE4. GE 0/0/1 of CE3 is a root
port, and CE 0/0/1 of CE4 is a designated port.
<CE3> display stp
-------[CIST Global Info][Mode MSTP]------CIST Bridge
:32768.00e0-fc9f-3257
Bridge Times
:Hello 2s MaxAge 20s FwDly 15s MaxHop 20
CIST Root/ERPC
:32768.00e0-fc9a-4315 / 199999
CIST RegRoot/IRPC
:32768.00e0-fc9f-3257 / 0
CIST RootPortId
:128.82
BPDU-Protection
:disabled
TC or TCN received :4
TC count per hello :4
STP Converge Mode
:Normal
Time since last TC received :0 days 3h:57m:0s
----[Port17(GigabitEthernet0/0/1)][FORWARDING]---Port Protocol
:enabled
Port Role
:Root Port
Port Priority
:128
Port Cost(Dot1T )
:Config=auto / Active=200000000
Desg. Bridge/Port
:32768.00e0-fc9a-4315 / 128.82
Port Edged
:Config=disabled / Active=disabled
Point-to-point
:Config=auto / Active=true
Transit Limit
:147 packets/hello-time
Protection Type
:None
Port Stp Mode
:MSTP
Port Protocol Type :Config=auto / Active= dot1s
BPDU Encapsulation :Config=stp / Active=stp
PortTimes
:Hello 2s MaxAge 20s FwDly 15s RemHop 20
TC or TCN send
:0
TC or TCN received :0
BPDU Sent
:238
TCN: 0, Config: 0, RST: 0, MST: 238
BPDU Received
:9745
TCN: 0, Config: 0, RST: 0, MST: 9745
<CE4> display stp
-------[CIST Global Info][Mode MSTP]------CIST Bridge
:32768.00e0-fc9a-4315
Bridge Times
:Hello 2s MaxAge 20s FwDly 15s MaxHop 20
CIST Root/ERPC
:32768.00e0-fc9a-4315 / 0
CIST RegRoot/IRPC
:32768.00e0-fc9a-4315 / 0
CIST RootPortId
:0.0
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
423
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
11 Layer 2 Protocol Transparent Transmission Configuration
BPDU-Protection
:disabled
TC or TCN received :2
TC count per hello :2
STP Converge Mode
:Normal
Time since last TC received :0 days 5h:33m:17s
----[Port17(GigabitEthernet0/0/1)][FORWARDING]---Port Protocol
:enabled
Port Role
:Designated Port
Port Priority
:128
Port Cost(Dot1T )
:Config=auto / Active=200000000
Desg. Bridge/Port
:32768.00e0-fc9a-4315 / 128.82
Port Edged
:Config=disabled / Active=disabled
Point-to-point
:Config=auto / Active=true
Transit Limit
:147 packets/hello-time
Protection Type
:None
Port Stp Mode
:MSTP
Port Protocol Type :Config=auto / Active= dot1s
BPDU Encapsulation :Config=stp / Active=stp
PortTimes
:Hello 2s MaxAge 20s FwDly 15s RemHop 20
TC or TCN send
:0
TC or TCN received :0
BPDU Sent
:7171
TCN: 0, Config: 0, RST: 0, MST: 7171
BPDU Received
:2
TCN: 0, Config: 0, RST: 0, MST: 2
----End
Configuration Files
l
Configuration file of CE1
#
sysname CE1
#
vlan batch 100
#
interface GigabitEthernet0/0/1
port hybrid tagged vlan 100
stp bpdu vlan 100
#
return
Configuration file of CE2
#
sysname CE2
#
vlan batch 100
#
interface GigabitEthernet0/0/1
port hybrid tagged vlan 100
stp bpdu vlan 100
#
return
Configuration file of CE3
#
sysname CE3
#
vlan batch 200
#
interface GigabitEthernet0/0/1
port hybrid tagged vlan 200
stp bpdu vlan 200
#
return
Configuration file of CE4
#
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
424
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
11 Layer 2 Protocol Transparent Transmission Configuration
sysname CE4
#
vlan batch 200
#
interface GigabitEthernet0/0/1
port hybrid tagged vlan 200
stp bpdu vlan 200
#
Return
Configuration file of PE1
#
sysname PE1
#
vlan batch 100 200
#
l2protocol-tunnel stp group-mac 0100-5e00-0011
#
interface GigabitEthernet0/0/1
port hybrid tagged vlan 100 200
#
interface GigabitEthernet0/0/2
port hybrid tagged vlan 100
l2protocol-tunnel stp vlan 100
#
interface GigabitEthernet0/0/3
port hybrid tagged vlan 200
l2protocol-tunnel stp vlan 200
#
return
Configuration file of P
#
sysname P
#
vlan batch 100 200
#
interface GigabitEthernet0/0/1
port hybrid tagged vlan 100 200
#
interface GigabitEthernet0/0/2
port hybrid tagged vlan 100 200
#
return
Configuration file of PE2
#
sysname PE2
#
vlan batch 100 200
#
l2protocol-tunnel stp group-mac 0100-5e00-0011
#
interface GigabitEthernet0/0/1
port hybrid tagged vlan 100 200
#
interface GigabitEthernet0/0/2
port hybrid tagged vlan 100
l2protocol-tunnel stp vlan 100
#
interface GigabitEthernet0/0/3
port hybrid tagged vlan 200
l2protocol-tunnel stp vlan 200
#
return
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
425
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
11 Layer 2 Protocol Transparent Transmission Configuration
11.7.3 Example for Configuring QinQ-based Layer 2 Protocol
Transparent Transmission
Networking Requirements
As shown in Figure 11-8, CEs on user networks communicate with each other through PEs.
STP runs on user networks. CE1 and CE2 send STP packets with VLAN tag 100 to PEs; CE3
and CE4 send STP packets with VLAN tag 200 to PEs. In this scenario, configure QinQ-based
Layer 2 protocol transparent transmission to ensure that:
l
All the devices in VLAN 100 participate in the calculation of a spanning tree.
All the devices in VLAN 200 participate in the calculation of a spanning tree.
To save VLAN IDs on the public network, configure VLAN stacking on PEs to add outer VLAN
tag 10 to STP packets with VLAN tag 100 and VLAN tag 200. Then STP packets contain double
tags and are transparently transmitted on the backbone network.
In this example, PEs transparently transmit STP packets sent from user networks by replacing
the original multicast destination MAC address of STP packets with a specified multicast MAC
address. By default, the destination MAC address of STP packets is 0180-C200-0000.
Figure 11-8 Networking of QinQ-based Layer 2 protocol transparent transmission
VLAN100
VLAN100
GE0/0/1
GE0/0/2
CE1
PE1
CE3
GE0/0/2
GE0/0/1
CE2
PE2
GE0/0/1
GE0/0/3
GE0/0/1
CE4
GE0/0/3
GE0/0/1
VLAN200
GE0/0/1
VLAN200
Configuration Roadmap
The configuration roadmap is as follows:
1.
Enable STP on the CEs.
2.
Configure CEs to send STP packets with specified VLAN tags to PEs.
3.
Configure VLAN-based Layer 2 protocol transparent transmission on PEs.
4.
Configure QinQ (VLAN stacking) on PEs so that PEs add outer VLAN tag 10 to STP
packets sent from CEs.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
426
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
11 Layer 2 Protocol Transparent Transmission Configuration
Data Preparation
To complete the configuration, you need the following data:
l
VLAN tags in STP packets sent from CEs to PEs
Outer VLAN tag that PEs add to STP packets
IDs of the VLANs that interfaces of PEs and CEs belong to
Procedure
Step 1 Enable STP on CEs and PEs.
# Configure CE1.
[CE1] stp enable
# Configure CE2.
[CE2] stp enable
# Configure CE3.
[CE3] stp enable
# Configure CE4.
[CE4] stp enable
Step 2 Configure CE1 and CE2 to send STP packets with VLAN tag 100 to PEs and configure CE3
and CE4 to send STP packets with VLAN tag 200 to PEs.
# Configure CE1.
[CE1] vlan 100
[CE1-vlan100] quit
[CE1] interface gigabitethernet 0/0/1
[CE1-GigabitEthernet0/0/1] port hybrid tagged vlan 100
[CE1-GigabitEthernet0/0/1] stp bpdu vlan 100
[CE1-GigabitEthernet0/0/1] bpdu enable
[CE1-GigabitEthernet0/0/1] quit
# Configure CE2.
[CE2] vlan 100
[CE2-vlan100] quit
[CE2] interface gigabitethernet 0/0/1
[CE2-GigabitEthernet0/0/1] port hybrid tagged vlan 100
[CE2-GigabitEthernet0/0/1] stp bpdu vlan 100
[CE2-GigabitEthernet0/0/1] bpdu enable
[CE2-GigabitEthernet0/0/1] quit
# Configure CE3.
[CE3] vlan 200
[CE3-vlan200] quit
[CE3] interface gigabitethernet 0/0/1
[CE3-GigabitEthernet0/0/1] port hybrid tagged vlan 200
[CE3-GigabitEthernet0/0/1] stp bpdu vlan 200
[CE3-GigabitEthernet0/0/1] bpdu enable
[CE3-GigabitEthernet0/0/1] quit
# Configure CE4.
[CE4] vlan 200
[CE4-vlan200] quit
[CE4] interface gigabitethernet 0/0/1
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
427
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
[CE4-GigabitEthernet0/0/1]
[CE4-GigabitEthernet0/0/1]
[CE4-GigabitEthernet0/0/1]
[CE4-GigabitEthernet0/0/1]
11 Layer 2 Protocol Transparent Transmission Configuration
port hybrid tagged vlan 200
stp bpdu vlan 200
bpdu enable
quit
Step 3 Configure QinQ-based transparent transmission on PEs so that PEs add outer VLAN tag 10 to
STP packets with VLAN tag 100 and VLAN tag 200.
# Configure PE1.
[PE1] vlan 10
[PE1-Vlan10] quit
[PE1] interface gigabitethernet 0/0/1
[PE1-GigabitEthernet0/0/1] port hybrid tagged vlan 10
[PE1-GigabitEthernet0/0/1] quit
[PE1] interface gigabitethernet 0/0/2
[PE1-GigabitEthernet0/0/2] qinq vlan-translation enable
[PE1-GigabitEthernet0/0/2] port hybrid untagged vlan 10
[PE1-GigabitEthernet0/0/2] port vlan-stacking vlan 100 stack-vlan 10
[PE1-GigabitEthernet0/0/2] l2protocol-tunnel stp vlan 10
[PE1-GigabitEthernet0/0/2] bpdu enable
[PE1-GigabitEthernet0/0/2] quit
[PE1] interface gigabitethernet 0/0/3
[PE1-GigabitEthernet0/0/3] qinq vlan-translation enable
[PE1-GigabitEthernet0/0/3] port hybrid untagged vlan 10
[PE1-GigabitEthernet0/0/3] port vlan-stacking vlan 200 stack-vlan 10
[PE1-GigabitEthernet0/0/3] l2protocol-tunnel stp vlan 10
[PE1-GigabitEthernet0/0/3] bpdu enable
[PE1-GigabitEthernet0/0/3] quit
# Configure PE2.
[PE2] vlan 10
[PE2-Vlan10] quit
[PE2] interface gigabitethernet 0/0/1
[PE2-GigabitEthernet0/0/1] port hybrid tagged vlan 10
[PE2-GigabitEthernet0/0/1] quit
[PE2] interface gigabitethernet 0/0/2
[PE2-GigabitEthernet0/0/2] qinq vlan-translation enable
[PE2-GigabitEthernet0/0/2] port hybrid untagged vlan 10
[PE2-GigabitEthernet0/0/2] port vlan-stacking vlan 100 stack-vlan 10
[PE2-GigabitEthernet0/0/2] l2protocol-tunnel stp vlan 10
[PE2-GigabitEthernet0/0/2] bpdu enable
[PE2-GigabitEthernet0/0/2] quit
[PE2] interface gigabitethernet 0/0/3
[PE2-GigabitEthernet0/0/3] qinq vlan-translation enable
[PE2-GigabitEthernet0/0/3] port hybrid untagged vlan 10
[PE2-GigabitEthernet0/0/3] port vlan-stacking vlan 200 stack-vlan 10
[PE2-GigabitEthernet0/0/3] l2protocol-tunnel stp vlan 10
[PE2-GigabitEthernet0/0/3] bpdu enable
[PE2-GigabitEthernet0/0/3] quit
Step 4 Configure PEs to replace the destination MAC address of STP packets received from CEs.
# Configure PE1.
[PE1] l2protocol-tunnel stp group-mac 0100-5e00-0011
# Configure PE2.
[PE2] l2protocol-tunnel stp group-mac 0100-5e00-0011
Step 5 Verify the configuration.
After the configuration is complete, run the display l2protocol-tunnel group-mac command.
You can view the protocol type or name, original destination MAC address, new destination
MAC address, and priority of Layer 2 protocol packets to be transparently transmitted.
Take the output on PE1 as an example.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
428
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
11 Layer 2 Protocol Transparent Transmission Configuration
<PE1> display l2protocol-tunnel group-mac stp
Protocol
EncapeType ProtocolType Protocol-MAC
Group-MAC
Pri
----------------------------------------------------------------------------stp
llc
dsap 0x42
0180-c200-0000 0100-5e00-0011 0
ssap 0x42
Run the display stp command on CE1 and CE2 to view the root in the MST region. The command
output shows that a spanning tree is calculated between CE1 and CE2. GE 0/0/1 of CE1 is a root
port, and CE 0/0/1 of CE2 is a designated port.
<CE1> display stp
-------[CIST Global Info][Mode MSTP]------CIST Bridge
:32768.000b-09f0-1b91
Bridge Times
:Hello 2s MaxAge 20s FwDly 15s MaxHop 20
CIST Root/ERPC
:32768.000b-09d4-b66c / 199999
CIST RegRoot/IRPC
:32768.000b-09f0-1b91 / 0
CIST RootPortId
:128.82
BPDU-Protection
:disabled
TC or TCN received :2
TC count per hello :2
STP Converge Mode
:Normal
Time since last TC received :0 days 3h:53m:43s
----[Port17(GigabitEthernet0/0/1)][FORWARDING]---Port Protocol
:enabled
Port Role
:Root Port
Port Priority
:128
Port Cost(Dot1T )
:Config=auto / Active=200000000
Desg. Bridge/Port
:32768.000b-09d4-b66c / 128.82
Port Edged
:Config=disabled / Active=disabled
Point-to-point
:Config=auto / Active=true
Transit Limit
:147 packets/hello-time
Protection Type
:None
Port Stp Mode
:MSTP
Port Protocol Type :Config=auto / Active= dot1s
BPDU Encapsulation :Config=stp / Active=stp
PortTimes
:Hello 2s MaxAge 20s FwDly 15s RemHop 20
TC or TCN send
:0
TC or TCN received :0
BPDU Sent
:237
TCN: 0, Config: 0, RST: 0, MST: 237
BPDU Received
:9607
TCN: 0, Config: 0, RST: 0, MST: 9607
<CE2> display stp
-------[CIST Global Info][Mode MSTP]------CIST Bridge
:32768.000b-09d4-b66c
Bridge Times
:Hello 2s MaxAge 20s FwDly 15s MaxHop 20
CIST Root/ERPC
:32768.000b-09d4-b66c / 0
CIST RegRoot/IRPC
:32768.000b-09d4-b66c / 0
CIST RootPortId
:0.0
BPDU-Protection
:disabled
TC or TCN received :1
TC count per hello :1
STP Converge Mode
:Normal
Time since last TC received :0 days 5h:29m:6s
----[Port17(GigabitEthernet0/0/1)][FORWARDING]---Port Protocol
:enabled
Port Role
:Designated Port
Port Priority
:128
Port Cost(Dot1T )
:Config=auto / Active=200000000
Desg. Bridge/Port
:32768.000b-09d4-b66c / 128.82
Port Edged
:Config=disabled / Active=disabled
Point-to-point
:Config=auto / Active=true
Transit Limit
:147 packets/hello-time
Protection Type
:None
Port Stp Mode
:MSTP
Port Protocol Type :Config=auto / Active= dot1s
BPDU Encapsulation :Config=stp / Active=stp
PortTimes
:Hello 2s MaxAge 20s FwDly 15s RemHop 20
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
429
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
11 Layer 2 Protocol Transparent Transmission Configuration
TC or TCN send
:0
TC or TCN received :0
BPDU Sent
:7095
TCN: 0, Config: 0, RST: 0, MST: 7095
BPDU Received
:2
TCN: 0, Config: 0, RST: 0, MST: 2
Run the display stp command on CE3 and CE4 to view the root in the MST region. The command
output shows that a spanning tree is calculated between CE3 and CE4. GE 0/0/1 of CE3 is a root
port, and CE 0/0/1 of CE4 is a designated port.
<CE3> display stp
-------[CIST Global Info][Mode MSTP]------CIST Bridge
:32768.00e0-fc9f-3257
Bridge Times
:Hello 2s MaxAge 20s FwDly 15s MaxHop 20
CIST Root/ERPC
:32768.00e0-fc9a-4315 / 199999
CIST RegRoot/IRPC
:32768.00e0-fc9f-3257 / 0
CIST RootPortId
:128.82
BPDU-Protection
:disabled
TC or TCN received :4
TC count per hello :4
STP Converge Mode
:Normal
Time since last TC received :0 days 3h:57m:0s
----[Port17(GigabitEthernet0/0/1)][FORWARDING]---Port Protocol
:enabled
Port Role
:Root Port
Port Priority
:128
Port Cost(Dot1T )
:Config=auto / Active=200000000
Desg. Bridge/Port
:32768.00e0-fc9a-4315 / 128.82
Port Edged
:Config=disabled / Active=disabled
Point-to-point
:Config=auto / Active=true
Transit Limit
:147 packets/hello-time
Protection Type
:None
Port Stp Mode
:MSTP
Port Protocol Type :Config=auto / Active= dot1s
BPDU Encapsulation :Config=stp / Active=stp
PortTimes
:Hello 2s MaxAge 20s FwDly 15s RemHop 20
TC or TCN send
:0
TC or TCN received :0
BPDU Sent
:238
TCN: 0, Config: 0, RST: 0, MST: 238
BPDU Received
:9745
TCN: 0, Config: 0, RST: 0, MST: 9745
<CE4> display stp
-------[CIST Global Info][Mode MSTP]------CIST Bridge
:32768.00e0-fc9a-4315
Bridge Times
:Hello 2s MaxAge 20s FwDly 15s MaxHop 20
CIST Root/ERPC
:32768.00e0-fc9a-4315 / 0
CIST RegRoot/IRPC
:32768.00e0-fc9a-4315 / 0
CIST RootPortId
:0.0
BPDU-Protection
:disabled
TC or TCN received :2
TC count per hello :2
STP Converge Mode
:Normal
Time since last TC received :0 days 5h:33m:17s
----[Port17(GigabitEthernet0/0/1)][FORWARDING]---Port Protocol
:enabled
Port Role
:Designated Port
Port Priority
:128
Port Cost(Dot1T )
:Config=auto / Active=200000000
Desg. Bridge/Port
:32768.00e0-fc9a-4315 / 128.82
Port Edged
:Config=disabled / Active=disabled
Point-to-point
:Config=auto / Active=true
Transit Limit
:147 packets/hello-time
Protection Type
:None
Port Stp Mode
:MSTP
Port Protocol Type :Config=auto / Active= dot1s
BPDU Encapsulation :Config=stp / Active=stp
PortTimes
:Hello 2s MaxAge 20s FwDly 15s RemHop 20
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
430
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
11 Layer 2 Protocol Transparent Transmission Configuration
TC or TCN send
:0
TC or TCN received :0
BPDU Sent
:7171
TCN: 0, Config: 0, RST: 0, MST: 7171
BPDU Received
:2
TCN: 0, Config: 0, RST: 0, MST: 2
Run the display vlan command on PEs to view the QinQ configuration.
Take the output on PE1 as an example.
<PE1> display vlan 10 verbose
* : Management-VLAN
--------------------VLAN ID
: 10
VLAN Type
: Common
Description : VLAN 0010
Status
: Enable
Broadcast
: Enable
MAC Learning : Enable
Statistics
: Disable
Property
: Default
VLAN State
: Up
---------------Tagged
Port: GigabitEthernet0/0/1
---------------QinQ-stack
Port: GigabitEthernet0/0/2
GigabitEthernet0/0/3
----End
Configuration Files
l
Configuration file of CE1
#
sysname CE1
#
vlan batch 100
#
interface GigabitEthernet0/0/1
port hybrid tagged vlan 100
stp bpdu vlan 100
#
return
Configuration file of CE2
#
sysname CE2
#
vlan batch 100
#
interface GigabitEthernet0/0/1
port hybrid tagged vlan 100
stp bpdu vlan 100
#
return
Configuration file of CE3
#
sysname CE3
#
vlan batch 200
#
interface GigabitEthernet0/0/1
port hybrid tagged vlan 200
stp bpdu vlan 200
#
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
431
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
11 Layer 2 Protocol Transparent Transmission Configuration
return
Configuration file of CE4
#
sysname CE4
#
vlan batch 200
#
interface GigabitEthernet0/0/1
port hybrid tagged vlan 200
stp bpdu vlan 200
#
return
Configuration file of PE1
#
sysname PE1
#
vlan batch 10
#
l2protocol-tunnel stp group-mac 0100-5e00-0011
#
interface GigabitEthernet0/0/1
port hybrid tagged vlan 10
#
interface GigabitEthernet0/0/2
qinq vlan-translation enable
port hybrid untagged vlan 10
port vlan-stacking vlan 100 stack-vlan 10
l2protocol-tunnel stp vlan 10
#
interface GigabitEthernet0/0/3
qinq vlan-translation enable
port hybrid untagged vlan 10
port vlan-stacking vlan 200 stack-vlan 10
l2protocol-tunnel stp vlan 10
#
return
Configuration file of PE2
#
sysname PE2
#
vlan batch 10
#
l2protocol-tunnel stp group-mac 0100-5e00-0011
#
interface GigabitEthernet0/0/1
port hybrid tagged vlan 10
#
interface GigabitEthernet0/0/2
qinq vlan-translation enable
port hybrid untagged vlan 10
port vlan-stacking vlan 100 stack-vlan 10
l2protocol-tunnel stp vlan 10
#
interface GigabitEthernet0/0/3
qinq vlan-translation enable
port hybrid untagged vlan 10
port vlan-stacking vlan 200 stack-vlan 10
l2protocol-tunnel stp vlan 10
#
return
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
432
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
12
12 Loopback Detection Configuration
Loopback Detection Configuration
About This Chapter
This chapter describes the concept and configuration of loopback detection and provides
configuration examples.
12.1 Loopback Detection Overview
This section describes the concept of loopback detection.
12.2 Configuring Loopback Detection
This section describes how to configure the loopback detection function.
12.3 Configuration Examples
This section provides a loopback detection configuration example.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
433
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
12 Loopback Detection Configuration
12.1 Loopback Detection Overview
This section describes the concept of loopback detection.
When a loop occurs on a network, broadcast, multicast, and unknown unicast packets are
repeatedly transmitted on the network. This wastes network resources or even causes service
interruption on the entire network. To protect the network, certain actions should be taken on
the interface where the loop occurs, and the administrator need to check the network connection
and configuration to solve the problem soon. Therefore, a mechanism is required on a Layer 2
network to detect loops and notify the administrator.
Loopback detection is such a mechanism. It sends detection packets from an interface at intervals
and checks whether the packets are sent back to the interface. When this occurs, there is a
loopback on the interface. When detecting a loopback, the system sends a trap to the network
management system to notify the administrator. The system also blocks the interface, disables
MAC address learning on the interface, or shuts down the interface to minimize the impact on
the network.
12.2 Configuring Loopback Detection
This section describes how to configure the loopback detection function.
12.2.1 Establishing the Configuration Task
Before configuring loopback detection, familiarize yourself with the applicable environment,
complete the pre-configuration tasks, and obtain the data required for the configuration. This
will help you complete the configuration task quickly and accurately.
Applicable Environment
Figure 12-1 and Figure 12-2 show the application of loopback detection.
A loopback occurs on an interface usually because optical fibers are connected incorrectly, the
optical modem fails, or the interface is damaged by high voltage. As shown in Figure 12-1, a
cable is incorrectly connected on the device connected to the Switch. As a result, packets sent
from an interface of the Switch are sent back to the interface. This may cause traffic forwarding
errors or MAC address flapping on the same interface.
Figure 12-1 Loopback detection application 1
Switch
TX
Issue 02 (2011-11-21)
RX
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
434
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
12 Loopback Detection Configuration
As shown in Figure 12-2, loops may occur on the network connected to a Switch interface.
When a loop occurs, packets sent from the interface are sent back to this interface.
Figure 12-2 Loopback detection application 2
Switch
You can configure loopback detection on the interface in the preceding scenarios. When a
loopback is detected on the interface, the Switch performs certain actions, for example, blocks
the interface. Only users connected to this interface are affected, and other users can still
communicate. When the Switch detects that the loopback has been removed, it recovers
communication on the interface.
NOTE
l Loopback detection cannot prevent loops on the entire network. It only detects loops on a single node.
l A large number of packets are sent during loopback detection, occupying CPU resources; therefore,
disable loopback detection if it is not required.
Pre-configuration Tasks
Before configuring loopback detection, complete the following task:
l
Connecting interfaces and setting physical parameters for the interfaces to ensure that the
physical layer status of the interfaces is Up
Data Preparation
To configure loopback detection, you need the following data.
Issue 02 (2011-11-21)
No.
Data
Interface number
VLAN IDs in detection packets
(Optional) Action performed when a loopback is detected
(Optional) Interface recovery time after a loop is detected
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
435
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
12 Loopback Detection Configuration
No.
Data
(Optional) Loopback detection interval for sending detection packets
12.2.2 Enabling Loopback Detection
An interface sends detection packets to detect loopbacks only after loopback detection is enabled
on the interface.
Context
You can enable loopback detection on all interfaces at one time in the system view or enable it
on a single interface in the interface view.
Procedure
l
Enabling loopback detection on all interfaces
1.
Run:
system-view
The system view is displayed.
2.
Run:
loopback-detect enable
Loopback detection is enabled on all interfaces.
By default, loopback detection is disabled on an interface.
TIP
You can use this method to simplify configuration when most interfaces need to perform
loopback detection.
Enabling loopback detection on a single interface
1.
Run:
system-view
The system view is displayed.
2.
Run:
interface interface-type interface-number
The interface view is displayed.
3.
Run:
loopback-detect enable
Loopback detection is enabled on the interface.
NOTE
Loopback detection cannot be configured on an Eth-Trunk or its member interfaces.
----End
12.2.3 Specifying VLAN IDs of Loopback Detection Packets
You can specify one or more VLAN IDs for loopback detection packets.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
436
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
12 Loopback Detection Configuration
Context
By default, the system sends untagged detection packets after loopback detection is enabled on
interface. If the interface has been added to a VLAN in tagged mode, the untagged detection
packets are discarded on the link, and the interface cannot receive loopback packets. To solve
the problem, you can configure the VLAN ID for detection packets.
After VLAN IDs are specified, the interface sends an untagged detection packet and multiple
detection packets with the specified VLAN tags. Each interface can send detection packets with
a maximum of eight VLAN IDs.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
interface interface-type interface-number
The interface view is displayed.
Step 3 Run:
loopback-detect packet vlan vlan-id
A VLAN ID is specified for loopback detection packets.
By default, detection packets do not have a VLAN ID. You can specify a maximum of eight
VLAN IDs for loopback detection packets.
NOTE
Before running the loopback-detect packet vlan vlan-id command, ensure that:
l The specified VLAN exists.
l The interface has been added to the specified VLAN in tagged mode.
----End
12.2.4 (Optional) Configuring an Action to Perform After a
Loopback Is Detected
When a loopback is detected on an interface, the system sets the interface status to loopback and
sends a trap, blocks the interface, disables MAC address learning on the interface, or shuts down
the interface as configured.
Context
After loopback detection is enabled on an interface, the interface periodically sends detection
packets and checks whether loopback packets are received. You can configure the Switch to
take an action to minimize impact on the system and the entire network when a loopback is
detected.
Procedure
Step 1 Run:
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
437
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
12 Loopback Detection Configuration
system-view
The system view is displayed.
Step 2 Run:
interface interface-type interface-number
The interface view is displayed.
Step 3 Run:
loopback-detect action { block | nolearn | shutdown | trap }
The action that will be performed after a loopback is detected on the interface is configured.
The default action is block.
When a loopback is detected on an interface, the system performs any of the following actions:
l block: blocks the interface. After the interface is blocked, it is isolated from other interfaces
and does not forward received data packets to other interfaces.
l nolearn: disables MAC address learning on the interface. When a loopback is detected on
the interface, the interface stops learning MAC addresses.
l shutdown: shuts down the interface.
l trap: only sends a trap.
----End
12.2.5 (Optional) Setting the Interface Recovery Time After a Loop
Is Removed
Context
Perform the following steps on the S5700 that needs to perform loopback detection.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
interface interface-type interface-number
The interface view is displayed.
Step 3 Run:
loopback-detect recovery-time recovery-time
The interface recovery time after a loop is removed is set.
The default recovery time is three times the loopback detection interval.
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
438
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
12 Loopback Detection Configuration
NOTE
l It is recommended that the recovery time be at least three times the interval for sending loopback
detection packets. If the interval for sending loopback detection packets is very short, set the recovery
time to be at least 10 seconds longer than the interval.
l An interface cannot recover automatically after it is shut down. You must manually recover the interface
by using the undo shutdown command.
----End
12.2.6 (Optional) Setting the Interval for Sending Loopback
Detection Packets on an Interface
Context
An interface sends loopback detection packets at intervals to check whether a loopback exists
or whether the existing loopback has been removed.
Procedure
Step 1 Run:
system-view
The system view is displayed.
Step 2 Run:
loopback-detect packet-interval packet-interval-time
The interval for sending loopback detection packets is set.
By default, the interval for sending loopback detection packets is 5s.
----End
12.2.7 Checking the Configuration
Procedure
l
Run the display loopback-detect command to check the loopback detection configuration
and status of loopback detection enabled interfaces.
----End
12.3 Configuration Examples
This section provides a loopback detection configuration example.
12.3.1 Example for Configuring Loopback Detection
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
439
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
12 Loopback Detection Configuration
Networking Requirements
As shown in Figure 12-3, if there is a loop on the network connected to GE 0/0/1, broadcast
storms will occur on the Switch or even the entire network. To detect loops on the network
quickly, you can enable loopback detection on this interface.
Figure 12-3 Loopback detection network diagram
Switch
GE0/0/1
Configuration Roadmap
The configuration roadmap is as follows:
1.
Enable loopback detection on the interface.
2.
Specify the VLAN ID of loopback detection packets.
3.
Configure loopback detection parameters.
Data Preparation
To complete the configuration, you need the following data:
l
Interface where loopback detection needs to be enabled: GE 0/0/1
Interval for sending loopback detection packets: 10s
VLAN ID of loopback detection packets: 100
Interface recovery time: 30s
Procedure
Step 1 Enable loopback detection on the interface.
<Quidway> system-view
[Quidway] interface gigabitethernet 0/0/1
[Quidway-GigabitEthernet0/0/1] loopback-detect enable
[Quidway-GigabitEthernet0/0/1] quit
Step 2 Specify the VLAN ID of loopback detection packets.
[Quidway] vlan 100
[Quidway-vlan100] quit
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
440
Quidway S5700 Series Ethernet Switches
Configuration Guide - Ethernet
12 Loopback Detection Configuration
[Quidway] interface gigabitethernet 0/0/1
[Quidway-GigabitEthernet0/0/1] port hybrid tagged vlan 100
[Quidway-GigabitEthernet0/0/1] loopback-detect packet vlan 100
Step 3 Configure loopback detection parameters.
# Configure the system to block the interface when a loopback is detected.
[Quidway-GigabitEthernet0/0/1] loopback-detect action block
# Set the interface recovery time after a loopback is removed.
[Quidway-GigabitEthernet0/0/1] loopback-detect recovery-time 30
[Quidway-GigabitEthernet0/0/1] quit
# Set the interval for sending loopback detection packets.
[Quidway] loopback-detect packet-interval 10
Step 4 Verify the configuration.
When a loop occurs on the network connected to GigabitEthernet 0/0/1, the interface is blocked.
The interface will recover 30s after the loop is removed.
----End
Configuration Files
Configuration file of the Switch
#
sysname Quidway
#
vlan batch 100
#
loopback-detect packet-interval 10
#
interface GigabitEthernet0/0/1
port hybrid tagged vlan 100
loopback-detect enable
loopback-detect recovery-time 30
loopback-detect packet vlan 100
#
return
Issue 02 (2011-11-21)
Huawei Proprietary and Confidential
Copyright Huawei Technologies Co., Ltd.
441
S-ar putea să vă placă și
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryDe la EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryEvaluare: 3.5 din 5 stele3.5/5 (231)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)De la EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Evaluare: 4.5 din 5 stele4.5/5 (121)
- Grit: The Power of Passion and PerseveranceDe la EverandGrit: The Power of Passion and PerseveranceEvaluare: 4 din 5 stele4/5 (588)
- Never Split the Difference: Negotiating As If Your Life Depended On ItDe la EverandNever Split the Difference: Negotiating As If Your Life Depended On ItEvaluare: 4.5 din 5 stele4.5/5 (838)
- The Little Book of Hygge: Danish Secrets to Happy LivingDe la EverandThe Little Book of Hygge: Danish Secrets to Happy LivingEvaluare: 3.5 din 5 stele3.5/5 (400)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaDe la EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaEvaluare: 4.5 din 5 stele4.5/5 (266)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeDe la EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeEvaluare: 4 din 5 stele4/5 (5794)
- Her Body and Other Parties: StoriesDe la EverandHer Body and Other Parties: StoriesEvaluare: 4 din 5 stele4/5 (821)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreDe la EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreEvaluare: 4 din 5 stele4/5 (1090)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyDe la EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyEvaluare: 3.5 din 5 stele3.5/5 (2259)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersDe la EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersEvaluare: 4.5 din 5 stele4.5/5 (345)
- Shoe Dog: A Memoir by the Creator of NikeDe la EverandShoe Dog: A Memoir by the Creator of NikeEvaluare: 4.5 din 5 stele4.5/5 (537)
- The Emperor of All Maladies: A Biography of CancerDe la EverandThe Emperor of All Maladies: A Biography of CancerEvaluare: 4.5 din 5 stele4.5/5 (271)
- Team of Rivals: The Political Genius of Abraham LincolnDe la EverandTeam of Rivals: The Political Genius of Abraham LincolnEvaluare: 4.5 din 5 stele4.5/5 (234)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceDe la EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceEvaluare: 4 din 5 stele4/5 (895)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureDe la EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureEvaluare: 4.5 din 5 stele4.5/5 (474)
- On Fire: The (Burning) Case for a Green New DealDe la EverandOn Fire: The (Burning) Case for a Green New DealEvaluare: 4 din 5 stele4/5 (74)
- The Yellow House: A Memoir (2019 National Book Award Winner)De la EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Evaluare: 4 din 5 stele4/5 (98)
- The Unwinding: An Inner History of the New AmericaDe la EverandThe Unwinding: An Inner History of the New AmericaEvaluare: 4 din 5 stele4/5 (45)
- General Diesel Engine Diagnostic Guide PDFDocument3 paginiGeneral Diesel Engine Diagnostic Guide PDFan0th3r_0n3Încă nu există evaluări
- HSBC in A Nut ShellDocument190 paginiHSBC in A Nut Shelllanpham19842003Încă nu există evaluări
- American AccentDocument40 paginiAmerican AccentTimir Naha67% (3)
- Oracle FND User APIsDocument4 paginiOracle FND User APIsBick KyyÎncă nu există evaluări
- 450i User ManualDocument54 pagini450i User ManualThượng Lê Văn0% (2)
- Familiarization With Apparatus and Equipment Used in Testing of MaterialsDocument5 paginiFamiliarization With Apparatus and Equipment Used in Testing of MaterialsEmanoAce33% (6)
- TAB Procedures From An Engineering FirmDocument18 paginiTAB Procedures From An Engineering Firmtestuser180Încă nu există evaluări
- Catalogo AWSDocument46 paginiCatalogo AWScesarÎncă nu există evaluări
- 5 Star Hotels in Portugal Leads 1Document9 pagini5 Star Hotels in Portugal Leads 1Zahed IqbalÎncă nu există evaluări
- FIRE FIGHTING ROBOT (Mini Project)Document21 paginiFIRE FIGHTING ROBOT (Mini Project)Hisham Kunjumuhammed100% (2)
- Basic Vibration Analysis Training-1Document193 paginiBasic Vibration Analysis Training-1Sanjeevi Kumar SpÎncă nu există evaluări
- Sourcing Decisions in A Supply Chain: Powerpoint Presentation To Accompany Powerpoint Presentation To AccompanyDocument58 paginiSourcing Decisions in A Supply Chain: Powerpoint Presentation To Accompany Powerpoint Presentation To AccompanyAlaa Al HarbiÎncă nu există evaluări
- Audit On ERP Implementation UN PWCDocument28 paginiAudit On ERP Implementation UN PWCSamina InkandellaÎncă nu există evaluări
- Load Data Sheet: ImperialDocument3 paginiLoad Data Sheet: ImperialLaurean Cub BlankÎncă nu există evaluări
- Recommended Practices For Developing An Industrial Control Systems Cybersecurity Incident Response CapabilityDocument49 paginiRecommended Practices For Developing An Industrial Control Systems Cybersecurity Incident Response CapabilityJohn DavisonÎncă nu există evaluări
- PLT Lecture NotesDocument5 paginiPLT Lecture NotesRamzi AbdochÎncă nu există evaluări
- JAZEL Resume-2-1-2-1-3-1Document2 paginiJAZEL Resume-2-1-2-1-3-1GirlieJoyGayoÎncă nu există evaluări
- CLAT 2014 Previous Year Question Paper Answer KeyDocument41 paginiCLAT 2014 Previous Year Question Paper Answer Keyakhil SrinadhuÎncă nu există evaluări
- SILABO 29-MT247-Sensors-and-Signal-ConditioningDocument2 paginiSILABO 29-MT247-Sensors-and-Signal-ConditioningDiego CastilloÎncă nu există evaluări
- Specialty Arc Fusion Splicer: FSM-100 SeriesDocument193 paginiSpecialty Arc Fusion Splicer: FSM-100 SeriesSFTB SoundsFromTheBirdsÎncă nu există evaluări
- Aluminum 3003-H112: Metal Nonferrous Metal Aluminum Alloy 3000 Series Aluminum AlloyDocument2 paginiAluminum 3003-H112: Metal Nonferrous Metal Aluminum Alloy 3000 Series Aluminum AlloyJoachim MausolfÎncă nu există evaluări
- Course Specifications: Fire Investigation and Failure Analysis (E901313)Document2 paginiCourse Specifications: Fire Investigation and Failure Analysis (E901313)danateoÎncă nu există evaluări
- BSCSE at UIUDocument110 paginiBSCSE at UIUshamir mahmudÎncă nu există evaluări
- Selvan CVDocument4 paginiSelvan CVsuman_civilÎncă nu există evaluări
- Assignment - 2: Fundamentals of Management Science For Built EnvironmentDocument23 paginiAssignment - 2: Fundamentals of Management Science For Built EnvironmentVarma LakkamrajuÎncă nu există evaluări
- MOTOR INSURANCE - Two Wheeler Liability Only SCHEDULEDocument1 paginăMOTOR INSURANCE - Two Wheeler Liability Only SCHEDULESuhail V VÎncă nu există evaluări
- CS321 Computer ArchitectureDocument160 paginiCS321 Computer ArchitectureAnurag kumarÎncă nu există evaluări
- A Novel Adoption of LSTM in Customer Touchpoint Prediction Problems Presentation 1Document73 paginiA Novel Adoption of LSTM in Customer Touchpoint Prediction Problems Presentation 1Os MÎncă nu există evaluări
- CV Ovais MushtaqDocument4 paginiCV Ovais MushtaqiftiniaziÎncă nu există evaluări
- 4 Bar LinkDocument4 pagini4 Bar LinkConstance Lynn'da GÎncă nu există evaluări