Documente Academic
Documente Profesional
Documente Cultură
Cryptography Teacher Guide Brian Veitch
Încărcat de
Aung KentDrepturi de autor
Formate disponibile
Partajați acest document
Partajați sau inserați document
Vi se pare util acest document?
Este necorespunzător acest conținut?
Raportați acest documentDrepturi de autor:
Formate disponibile
Cryptography Teacher Guide Brian Veitch
Încărcat de
Aung KentDrepturi de autor:
Formate disponibile
Introduction to Cryptography
Brian Veitch
July 2, 2013
Contents
1 Introduction
1.1 Alice, Bob, and Eve . . . . . . . . . . .
1.2 Basic Terminology . . . . . . . . . . .
1.3 Brief History of Cryptography . . . . .
1.4 Kerckhoffs Principles of Cryptographic
.
.
.
.
3
3
4
4
11
2 Substitution Cipher
2.1 Caesar Cipher Activity . . . . . . . . . . . . . . . . . . . . . . . . .
2.2 Keyword Cipher Activity . . . . . . . . . . . . . . . . . . . . . . . .
2.3 Vigenere Cipher Activity . . . . . . . . . . . . . . . . . . . . . . . .
13
13
17
20
3 Transposition
3.1 Easy Example . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .
3.2 Railfence Cipher . . . . . . . . . . . . . . . . . . . . . . . . . . . .
3.3 Transposition Activity . . . . . . . . . . . . . . . . . . . . . . . . .
22
22
22
23
4 Modular Arithmetic
4.1 Examples of Congruences . . . . .
4.2 Arithmetic with Congruences . . .
4.3 Multipication Tables . . . . . . . .
4.4 Finding the Inverse . . . . . . . . .
4.5 Solving Equations (mod n) . . . . .
4.6 The Extended Euclidean Algorithm
24
26
27
27
29
32
34
.
.
.
.
.
.
.
.
.
.
.
.
. . . . .
. . . . .
. . . . .
Secuity
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
CONTENTS
5 Diffie-Hellman Key Exhange
5.1 What is it? . . . . . . . . . . . . . . . .
5.2 The Algorithm . . . . . . . . . . . . . .
5.3 Example of a Key Exhange . . . . . . .
5.4 Why is Cracking this Exchange Difficult
5.5 Key Exhange Activity . . . . . . . . . .
.
.
.
.
.
37
37
37
38
39
40
.
.
.
.
.
.
.
42
42
42
45
46
50
52
53
7 Using RSA for Authentication
7.1 Algorithm . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .
7.2 Authentication Activity . . . . . . . . . . . . . . . . . . . . . . . .
54
54
56
8 Important Information
8.1 Caesar Shift Wheel . . .
8.2 Letter Frequency Tables
8.3 Vigeneres Table . . . . .
8.4 ASCII Table . . . . . . .
8.5 Useful Websites . . . . .
57
57
58
59
60
60
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
6 RSA Encryption
6.1 Introduction . . . . . . . . . . . . . . . . . . .
6.2 Example of RSA Encryption . . . . . . . . . .
6.3 RSA Algorithm . . . . . . . . . . . . . . . . .
6.4 Using The Extended Euclidean Algorithm . .
6.5 ASCII Table . . . . . . . . . . . . . . . . . . .
6.6 Cracking RSA by finding the private key d. .
6.7 Your turn to crack an RSA encrypted message
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
1 INTRODUCTION
Introduction
You dont have to be an expert in cryptogrphy to appreciate the field.
Cryptography is all around us. We use it to store senstive data, send secret
messages, send financial information over the internet, hide messages from
parents, etc. The methods we will cover in this paper can be easily picked up
with some knowledge of basic arithmetic and some modular algebra.
There are two basic types of encryption: substitution and transposition. We will
cover the basics of each with some easy examples. Since this is an introduction,
the techniques will be easier. After reading a section, try to improve on the
method by coming up with your own versions.
1.1
Alice, Bob, and Eve
Suppose Alice wants to send Bob a message. She doesnt want Eve to intercept it
and read it, so she decides to disguise it. Heres a diagram that outlines the
whats happening.
Your hope is that Eve doesnt know how to figure out your message or alter it in
some way.
1 INTRODUCTION
1.2
Basic Terminology
1. Plaintext - this is the original message to be sent. It can letters, numbers,
characters, symbols, etc.
2. Encryption - disgusing the plaintext using some method. These methods
usually have a key or algorithm to generate the ciphertext.
3. Ciphertext - the result of the encryption. It can be letters, numbers,
characters, etc., but unreadable.
4. Decryption - the process of undoing the encryption. You should get the
original plaintext when finished.
5. Key - something that is used to encrypt the message. Think of it as a
password that disguises and un-disguises your message.
6. Keyspace - the set of all possible keys. For example, a four digit lock has
10000 possible keys. (0000, 0001, 0002, ..., 9998, 9999)
7. Cryptography - the science of the enciphering and deciphering of messages in
secret code or cipher. Also referred to as cryptology.
8. Cryptosystem - a system for encrypting information.
9. Cryptanalysis - the science (and art) of recovering information from ciphers
without knowledge of the key.
1.3
Brief History of Cryptography
Cryptography is an ancient science. The term comes from the Greek language
meaning the study of hidden or secret writing. Ever since there were multiple
tribes (or countries), we needed a way to communicate to one another without
the other tribe (country) understanding it. Today its vital to communicatations,
authentication, sending sensative data over the internet, purchasing items from
1 INTRODUCTION
eBay, Amazon, and more.
One of the earliest examples of cryptography was in Egypt around 2000 B.C.
where they used hieroglyphics to decorate their tombs. Even though they werent
trying to completely hide the meaning, it still wasnt easy to interpret.
The Greek writer Polybius used a 5x5 or a 6x6 (with out alphabet) to disguise
the message. Below is an example of how it would work,
If you wanted to write the message SAVE ME, it would be disguised as
S-A-V-E-M-E
41-11-44-15-31-15
Another Greek tool for disguising a message was called the Scytale. It is a tool
used to perform a transposition cipher, consisting of a cylinder with a strip of
parchment wound around it on which is written a message. In other words, it was
a way to rearrange the letters.
You would wrap a long thin parchment around a rod. You then write your
message across the rod, SEND HELP!
1 INTRODUCTION
When you unwrap the parchment the letters appear rearranged. To understand
the message, the receiver would need a rod of the same size.
Julius Caesar used his own way of disguising messages to send to his military. We
know call it the Caesar Cipher. If he had anything important to send, he would
write out his message and then replace each letter of his message with another
letter down the alphabet. So A = D, B = E, C = F, D = G, etc. When it needed
to be read, the receiver of the message would reverse this process, changing D
back to A, E back to B, F back to C. We will go over this method in great detail
in the next chapter. The tool we will use will look something like this,
1 INTRODUCTION
This method is a form of substitution, where you replace one letter for another.
Over the years, the substitution method evolved. In this next chapter, we discuss
the Keyword Cipher, which is another form of substitution.
The Vigenere cipher was a substitution cipher where each letter of the message
used its own caesar shift. This means the first letter might be shifted by 3 letters,
the second letter of the message could be shifted by 5 letters, the third letter by
3, the fourth letter by 5, the fifth letter by 3, and so on. This particular pattern
would be two Caesar shifts with 3 and 5. For 300 years it was believed to be
indecipherable. It can now be broken by determining the number of different
caesar shifts and then do a frequency analysis on the letters that use the same
Caesar shift.
To give you an idea, suppose your keyword is DOG and you want to disguise
the message HELP ME, you use the Vigenere Table below to determine the
ciphertext.
1 INTRODUCTION
Message: H E L P M E
Keyword: D O G D O G
Cipher:
K S R S A K
Why was this cipher so strong? Consider the ciphertext. There are two Ks but
each corresonds to a different letter in the plaintext. One K decrypts back to H
while the other K decrypts to E.
In 1917 U.S. Army Major Joseph Mauborgne developed a technique known as the
One-Time Pad. It works the same way as a Vigenere Cipher. The only
1 INTRODUCTION
difference is the keyword is a random string of letters that is the same length as
the message. That way the keyword never repeats which makes frequency
analysis useless. If this method is done correctly, it is the only provably
unbreakable encryption algorithm.
Heres an example. Suppose the ciphertext is KNEXYLTCOW. Now suppose
you used two different one-time pad keys, AFTMRDARKF and
DJWMRDARKF. Lets see what happens. Use the Vigenere Table to convert
back to plaintext.
Cipher:
K N E X Y L T C O W
Key:
D J W M R D A R K F
Plaintext: H E I L H I T L E R
Cipher:
K N E X Y L T C O W
Key:
A F T M R D A R K F
Plaintext: K I L L H I T L E R
This means you can make the plaintext say anything you want. But there are two
main weaknessess to this method.
1. Making sure the key is random and of sufficient length.
2. Distributing the keys. How is the receiver suppose to know which key to use?
One way to accompish the distribution of keys is to have an agreed upon book.
Each day the random key starts with the first letter of a page in that book. Keep
reading the letters from the page until its the same length as the message.
Another interesting use of crytography was to send messages through newspapers.
Before the telegraph, people needed to send messages through the mail. Postage
could be expensive, plus someone could intercept the letter. Newspapers traveled
freely and without charge. So someone could publish an article in the newspaper
and put a dot above the letter that was part of the plaintext. For example,
1 INTRODUCTION
10
to
announce
I am
excited
the wedding of my brother. He is back from
his journey overseas and is looking forward to a new life with his beautiful bride.
Excluding is, which would have two dots, the letters with dots above them spell
attack
World War II
The Germans adopted the use of a family of electro-mechanical encryption
devices invented by the German engineer Arthur Scherbuis. They became known
as the Enigma Machines, and were extremely effective during the war.
The details about how the Engima machine works is a bit complicated. The
Enigma looks roughly like a typewriter.
Heres an excerpt from www.bbc.co.uk/history/tpics/enigma
Enigma allowed an operator to type in a message, then scramble it by
using three to five notched wheels, which displayed different letters of
the alphabet. The receiver needed to know the exact settings of these
rotors in order to reconstitute the coded text. Over the years the basic
machines became more complicated as German code experts added
plugs with electronic circuits.
When a key was pressed, a set of electrical contacts in the disks would complete a
circuit lighting up the ciphertext letter. The disks would rotate after each letter is
pressed providing a different encryption.
In 1932, Polish cryptologists broke the Enigma by reverse engineering the
machine. As Germany added more complexity to their machine, the initial
1 INTRODUCTION
11
decryption techniques became unsuccessful. Poland presented their initial
decryption technqiues to the British military intelligence. The cryptanalysts at
Bletchley Park used this information to greatly increase their success of
decrypting Enigma.
Modern Era
In 1972, the U.S. identified a need for a government-wide data encryption
standard. They went with the encryption technique designed by cryptographers
from IBM. It became known as DES. AES, the advanced encrpytion standard
replaced DES in 2001.
In 1977, the RSA algorithm was presented by its creators Ron Rivest, Adi
Shamir, and Leonard Adleman from MIT. With many of the classical
cryptosystems, the key used to encrypt a message was also used to decrypt the
message. Suppose 300 people send financial information to a bank. Each person
could encrypt it and have the bank decrypt it. This would, however, require the
bank to know 300 separate keys. Not only is it inefficient, how would the bank
know each persons key?
RSA is called public key encrpytion (asymmetric key encription). To encrypt a
message, someone uses a public key known to everyone to encrypt their data.
Only the receiver of the message knows the private key to decipher the message.
This means 300 people can send their personal info using the banks public key to
encrypt it. Only the bank can decrypt it with their private key. We will discuss
more of RSA later on.
Now this was only a taste of the more famous works in cryptography. More
information can be found through reserach in your libraries or online.
1.4
Kerckhoff s Principles of Cryptographic Secuity
You might think that the power behind an encryption technique is keeping the
technique secret. This is not true. Kerckhoffs principles (some of them) state
1. The system must be practically indecipherable. In other words, if the data
can be deciphered, it must take a very long time.
1 INTRODUCTION
12
2. The system must not be secret. If you encrypted a message using Caesars
cipher, then your evesdropper Eve must also know that.
3. Any evesdroppers or attackers must be able to get their hands on the
ciphertext.
4. The security of the system should depend solely on the secrecy of the key.
To summarize, a good cryptosystem is one where everyone knows what it is and
how it works, everyone can get their hands on the ciphertext, and its strength lies
in the secrecy of the key.
2 SUBSTITUTION CIPHER
13
Substitution Cipher
2.1
Caesar Cipher Activity
With a Caesar Cipher, you replace each letter in a message with a letter along
the alphabet. A Caesar cipher shifts the alphabet and is therefore also called a
shift cipher. The key is the number of letters you shift. The Caesar Cipher is
named after Julius Caesar, who is said to have used it to send messages to his
generals over 2,000 years ago.
You should have a pdf of a Caesar Shift Wheel. Follow the directions to create
the wheel.
Example: Key: Shift 3
Message: M A T H E Q U A L S M O N E Y
Cipher: P D W K H T X D O V P R Q H B
1. Use a key shift of 7, encrypt the following message:
Message: W E L C O M E T O M A T H C A M P
Cipher:
2. Use a key shift of 13, encrypt the following message:
Message: B O W L I N G T O U R N A M E N T T O N I G H T
Cipher:
2 SUBSTITUTION CIPHER
14
3. Use a key shift of 20, encrypt the following message:
Message: T H E S E C R E T P A S S W O R D I S B O O G E R
Cipher:
4. A KEY SPACE is the set of all possible keys. What is the size of the KEY
SPACE for the shift cipher?
2 SUBSTITUTION CIPHER
15
To decrypt a shift cipher, you just reverse the shift. If you shifted RIGHT 3,
then to decrypt the message we shift LEFT 3.
Example: Key shift: -3
Cipher:
PDWK HTXDOV PRQHB
Plaintext : M A T H E Q U A L S M O N E Y
1. Use a key shift of 4, decrypt the following ciphertext:
Ciphertext: G S H I R E Q I: K S S R M I W
Plaintext:
2. Choose your own key shift. Encrypt your name and high school grade level
Plaintext:
Ciphertext:
3. Pass your ciphertext to your neighbor. DO NOT TELL THEM YOUR KEY.
Have your neighbor decrypt your message.
4. Go to
http://www.brianveitch.com/cryptography/caesar_friendly.php. Use
this page to figure out the answer to this riddle. What did the one eye say to
the other?
Ciphertext: TWLOWWF
QGM
Plaintext:
Ciphertext: KGEWLZAFY KEWDDK!
Plaintext:
SFV EW
2 SUBSTITUTION CIPHER
5. Why cant you tell an egg a joke? Key = 23
Ciphertext: FQ JFDEQ ZOXZH RM.
Plaintext:
6. Now that you got a chance to play around with the shift cipher, can you
think of any weaknesses in this encryption technique?
16
2 SUBSTITUTION CIPHER
2.2
17
Keyword Cipher Activity
With a Keyword Shift, you place a word underneath the original alphabet. The
Keyletter is the letter where you start your keyword. In this example below, the
keyword is KINGDOM and the keyletter is G
Starting after the letter M, you fill in the rest of the alphabet. If the letter was
already used in the keyword, then you skip it. Also, your keyword cannot have
repeated letters.
Example: With the keyword: KINGDOM and keyletter M
Message: G R A V I T Y I S
Cipher:
KFUPNJS
A D O W N E R!
N H U X B Q A Y F!
1. Use the keyword: BACON, keyletter: C
2 SUBSTITUTION CIPHER
Message:
18
CRYPTO IS COOL
Ciphertext:
2. Use the keyword: BACON, keyletter A to decrypt the following ciphertext.
Ciphertext: T R Y S T B P J G L E H N J J M T M B T R N N
Plaintext:
3. Go to http://www.brianveitch.com/cryptography/keyword.php. Use
this page to decrypt the following statement.
Keyword: THUNDERCLAP, Keyletter: E
ZPAJ SPK NWJT DJ ONTA SPKGT JTQJDAU WAZ CSDAU PA SPKG
XWYR ONTA SPKG BNPAT ZTYDZTI JP XT W ADAEW, ICDBI
JNGPKUN SPKG HDAUTGI, WAZ WJJWYRI SPKG HWYT!
2 SUBSTITUTION CIPHER
19
4. The following are quotes from famous movies. Each quote has been
encrypted with the same keyword and keyletter. Your job is to decrypt them
and determine its origin. Identify the keyword and keyletter.
Use the letter frequency calculator at
http://www.brianveitch.com/cryptography/relative_frequency.php to
help determine the plaintext.
WSC ZE RCVMTD, IV VEFVC M ISCOR FYMF ZD VEFZCVOK SGC
SIE.
TMK FYV WSCPV NV IZFY KSG.
FYVCVD ES AOMPV OZUV YSTV.
KSG PMEF YMEROV FYV FCGFY!
KSGCV XSEEM EVVR M NZXXVC NSMF.
YVCVD QSYEEK!
TK ACVPZSGD.
KSGC TSFYVC IMD M YMTDFVC MER KSGC WMFYVC DTVOF SW
VORVCNVCCZVD.
Z DYMOO PMOO YZT DBGZDYK. MER YV DYMOO NV TZEV. MER
YV DYMOO NV TK DBGZDYK.
FYVKHV RSEV DFGRZVD, KSG UESI. DZJFK AVCPVEF SW FYV
FZTV, ZF ISCUD VHVCK FZTV.
CMK, EVJF FZTV DSTVSEV MDUD KSG ZW KSGCV M XSR, KSG
DMK KVD!
2 SUBSTITUTION CIPHER
2.3
20
Vigenere Cipher Activity
The Vigenre Cipher is a method of encrypting alphabetic text by using a series
of different Caesar ciphers based on the letters of a keyword. Instead of shifting
every letter of your plaintext by C = 2, each letter of the plaintext will have a
different shift.
Though the cipher is easy to understand and implement, for three
centuries it resisted all attempts to break it; this earned it the
description le chiffre indchiffrable (French for the indecipherable
cipher) (wikipedia).
Each letter of the alphabet represents a shift. For example, A = 0 (no shift), B =
1 (shift 1 to the right), C = 2 (shift 2 to the right), D = 3 (shift 3 to the right), E
= 4 (shift 4 to the right), ...
If the keyword is BED, it means you shift the first letter of your cipher by B =
1, the second letter of the cipher by E = 4, third letter by D = 3. Repeat this
pattern. The keyword BED converts to the numeric key 143. Consider the
following example.
You can use your Caesar Shift Wheel to do this. Since you will have to keep
changing the shift for each letter, the wheel will help you do it quickly.
Example: Using the keyword: NEMO, encrypt the following message.
NEMO =
(corresponding numeric key)
2 SUBSTITUTION CIPHER
21
Example: Using the keyword: CRYPTO, encrypt the following message.
CRYPTO =
(corresponding numeric key)
Decrypting the Ciphertext
Decrypting a Vigenere message requires you to reverse the shift from the
keyword. You would line up your ciphertext with the numeric key and reverse the
shift, just like you reversed the shift with the Caesar Cipher.
Example: Using the keyword: AVENGERS, decrypt the following message.
Decryping by hand can be tedious. Go to
http://www.brianveitch.com/cryptography/vigenere.php. This allows you
to encrypt a message with the Vigenere keyword and also decrypt messages very
quickly.
3 TRANSPOSITION
22
Transposition
There are two basic ways of encrypting a message. One way is through some sort
of substitution, which was covered in the previous section. The other way is
through transposition. Transposition ciphers are formed by changing the
normal position of the letters that make up the message.
3.1
Easy Example
A common transposition can be simply writing out the letters of a word
backwards.
ATTACK AT DAWN
translates into
KCATTA TA NWAD
You could also read the entire message right to left, which would encrypt to
NWAD TA KCATTA
3.2
Railfence Cipher
Suppose you have the message STOP THE ATTACK WE ARE
OUTNUMBERED
1. Write the message vertical. You must choose how many letters you go down.
When you reach the bottom of the column, you start the next column.
Some examples,
(a) Vertical: 5
S
T
O
P
T
H
E
A
T
T
A
C
K
W
E
A
R
E
O
U
T
N
U
M
B
E
R
E
D
3 TRANSPOSITION
23
(b) Vertical: 2
S O T E T A K E R O T U B R D
T P H A T C W A E U N M E E
2. Next, you would write out the message from left to right like you were
reading a book. The cipher text would be
(a) Vertical 5 by Horizontal 6:
SHAATE TECRNR OAKEUE PTWOMD TTEUB
or (without spaces)
SHAATETECRNROAKEUEPTWOMDTTEUB
(b) Vertical 2 by Horizontal 15:
SOTETAKEROTUBRD TPHATCWAEUNMEE
or (without spaces)
SOTETAKEROTUBRDTPHATCWAEUNMEE
3. You can keep changing the vertical length to get a new cipher for the exact
same message. You just need to agree upon a length with the receiver
beforehand.
4. To decrypt this message, youll need the vertical and horizontal length. Its
possible to do it without, but it will take a lot of trial and error.
3.3
Transposition Activity
Choose a vertical length and encrypt a message. Give your encrypted message to
your partner. Try to decipher your partners message without knowledge of the
vertical and horizontal length. After 5 minutes, if you have not deciphered the
message, have your partner tell you the vertical and horizontal lengths.
4 MODULAR ARITHMETIC
24
Modular Arithmetic
Clock Example
What if we kept counting after 12 oclock? Where would 13 oclock be? Turn the
time back into our normal 12 hour time.
The 24 hour clock face:
13 =
oclock
17 =
oclock
23 =
oclock
24 =
oclock
4 MODULAR ARITHMETIC
25
With modular arithmetic, we would use the following notation,
13 1 (mod 12)
17 5 (mod 12)
23 11 (mod 12)
24 0 (mod 12)
Formal Definition of a b (mod n)
means congruent
a is congruent to b mod n if b a is a integer multiple of n
Thats great for a math class, but a bit confusing for your first exposure to mod.
Another way to look at it is,
Informal Definition of a b (mod n)
b is the remainder when you divide a by n
Examples:
13 12 = 1 R 1
17 12 = 1 R 5
23 12 = 1 R 11
24 12 = 2 R 0
4 MODULAR ARITHMETIC
26
So when we talk about (mod n), we really only care about the remainder when
you divide by n. Your answer must be a number between
0 and n 1
4.1
Examples of Congruences
1. 27
(mod 12) - answer must be between 0 and 11
2. 145
(mod 12)
3. 214
(mod 12)
4. 28
(mod 5) - answer must be between 0 and 4
5. 16
(mod 3)
6. 1563
7. 10625
8. 783
(mod 27)
(mod 101) - answer must be between 0 and 100
(mod 27)
If the number is negative, you must add multiples of n until you get a
number between 0 and n
3 5 (mod 8) because -3 + 8 = 5
28 4 (mod 8) because -28 + 8 + 8 + 8 + 8 = 4
9. 8
(mod 12)
10. 15
(mod 4)
11. 126
12. 54
(mod 18)
(mod 13)
4 MODULAR ARITHMETIC
27
We can do addition, subtraction, multipication, and exponentiation exactly the
same way. Give them a try,
4.2
Arithmetic with Congruences
1. 11 + 4
2. 23 17
3. 16 2
4. 4 8
5. 16 3
6. 154 + 27
(mod 12)
(mod 12)
(mod 12)
(mod 5)
(mod 3)
(mod 27)
7. 24
(mod 27)
8. 36
(mod 13)
9. 73 1
10. 94
4.3
(mod 7)
(mod 5)
Multipication Tables
Suppose you multiply each number (mod 5) with another number from (mod 5).
We can create a table to keep track of the results.
* mod 5 0 1 2 3 4
0
0 0 0 0 0
1
0 1 2 3 4
2
0 2 4 1 3
3
0 3 1 4 2
4
0 4 3 2 1
Notice how 2 3 1 (mod 5). This will be important very soon.
4 MODULAR ARITHMETIC
28
Example:
Now you try creating a multiplication table for (mod 4), (mod 7) and (mod 11).
* mod 4
* mod 7
* mod 11
4 MODULAR ARITHMETIC
29
Division is very different. What is 4/3 (mod 7)?
Division like this doesnt make sense. When we added, subtracted, and multiplied
we still got an integer. We then divided that integer by n. But 4/3 is not an
integer!
You might recall that 4/3 is the same thing as 4
if we want to compute 4/3 we need to do,
1
1
And is the inverse of 3. So,
3
3
4/3 = 4 31
So whats the inverse of 3 (mod 7)? Recall that the inverse of 3 is a number than
when you multiply it to 3 you get 1.
3x=1
Lets look at an example.
4.4
Finding the Inverse
1. 31 (mod 7)
We need to solve
3x 1 (mod 7)
There are three ways we can do this. Lets first do it by trial and error,
3 1 3 (mod 7)
3 2 6 (mod 7)
3 3 9 2 (mod 7)
3 4 12 5 (mod 7)
3 5 15 1 (mod 7)
4 MODULAR ARITHMETIC
30
From the multiplication table, you should have
3 5 1 (mod 7)
So if an inverse exists, you can find it from the multiplication table. The
third way will be covered in the section The Extended Euclidean
Algorithm.
So when we are in (mod 7), 31 is 5 (mod 7).
So 4/3 (mod 7) can be calculated as
4 31 4 5 = 20 6 (mod 7)
2. 31 (mod 4)
3. 71 (mod 11)
4 MODULAR ARITHMETIC
31
Please note that some inverses and divisions do not exist. For example, 21
(mod 4) did not exist. Therefore, you cannot divide by 2 in (mod 4).
However, every number (except 0) in (mod 7) and (mod 11) did have
inverses. There is a reason for this. Take some time to think about it. Try
creating a multipication table for (mod 12) and see what happens.
* mod 12
Example: Find
11
(mod 12)
5
4 MODULAR ARITHMETIC
4.5
32
Solving Equations (mod n)
How did we solve an equation like 3x = 5 from basic algebra? We divided both
sides by 3.
3x = 5
3x 5
=
3
3
x=
5
3
So how would we solve the equation
3x 5 (mod 11)
Instead of dividing both sides by 3 (we dont do division like this in (mod n)), we
multiply both sides by the inverse of 3, 31 .
3x 5 (mod 11)
31 3x 31 5 (mod 11)
x 31 5 (mod 11)
So whats 31 (mod 11)?
From the multiplication table, 31 4 (mod 11) since 3 4 1 (mod 11).
Therefore, our solution to 3x 5 (mod 11) is
x 31 5 (mod 11)
x 4 5 (mod 11)
4 MODULAR ARITHMETIC
33
x 9 mod 11
Now lets verify.
3 9 = 27 5 (mod 11)
Your turn.
1. 5x 7 (mod 12)
2. 7x 9 (mod 12)
3. x2 1 (mod 12) - use the multiplication table for (mod 12)
4 MODULAR ARITHMETIC
4.6
34
The Extended Euclidean Algorithm
A very useful tool to use when trying to find the inverse of a number (mod n) is
called the Extended Euclidean Algorithm. As you probably figured out by now, a
number will have an inverse (mod n) as long as that number is relativly prime to
n.
This method requires the division algorithm on the left hand side, and a recursive
formula on the right. Please follow the example below.
We need the recursive formula: pi = pi2 pi1 qi2 where p0 = 0 and p1 = 1.
When you move onto the next step, you use ai = bi1 and bi = ri1
3 d 1 (mod 20)
ai =
pi = pi2 pi1 qi2
qi bi + ri
Step 0: 20 = (6) 3 + 2
p0 = 0
Step 1:
3 = (1) 2 + 1
p1 = 1
Step 2:
2 = (2) 1 + 0
p2 = p0 p1 q0 = 0 1(6) = 6
p3 = p1 p2 q1 = 1 (6) 1 = 7
Therefore, the solution to 3 d 1 (mod 20) is d = 7 (mod 20).
This means 31 7 (mod 20)
Heres another example:
7 d 1 (mod 40)
Remember, ai = bi1 and bi = ri1
4 MODULAR ARITHMETIC
ai =
35
qi bi + ri
pi = pi2 pi1 qi2
Step 0: 40 = (5) 7 + 5
p0 = 0
Step 1:
7 = (1) 5 + 2
p1 = 1
Step 2:
5 = (2) 2 + 1
p2 = p0 p1 q0 = 0 1(5) = 5
Step 3:
2 = (2) 1 + 0
p3 = p1 p2 q1 = 1 (5)(1) = 6
p4 = p2 p3 q2 = 5 6 2 = 17
Therefore, the solution to 7 d 1 (mod 40) is
d = 17 23 (mod 40)
Just to check,
7 23 = 161 1 (mod 40)
Therefore, 71 23 (mod 40).
Your turn! Find 91 (mod 16) by solving the following equation.
9 d 1 (mod 16)
Youll find a table on the next page to complete the Extended Euclidean
Algorithm.
4 MODULAR ARITHMETIC
ai
36
= qi bi + ri
pi = pi2 pi1 qi2
Step 0:
Step 1:
Step 2:
Step 3:
Step 4:
Step 5:
Your inverse is the last pi value in the table. Make sure its (mod n).
The inverse of 91 (mod 16) is
91
(mod 16)
Use the website http://www.brianveitch.com/cryptography/modinverse.php
to confirm the inverse.
5 DIFFIE-HELLMAN KEY EXHANGE
37
Diffie-Hellman Key Exhange
5.1
What is it?
Suppose Alice sends Bob an encrypted message using the Vigenere Cipher. Bob
and Alice need to also agree upon the key, otherwise Bob would have to decipher
Alices message the hard way. If Eve, our evesdropper, is aware of the key then
she can decipher all of Alices messages to Bob. Diffie-Hellman Key
Exchange allows the sender, Alice, and the receiver, Bob, to come up with a key
with public information. The upside to this method is Eve, our evesdropper, is
aware of the exchange the whole time but will have a difficult time cracking it
and finding the secret key. Heres how it works.
5.2
The Algorithm
1. Alice and Bob agree, publicly, on a prime number P , and another number N ,
where N < P . Everyone, including Eve, will know these two numbers.
2. Alice chooses her own personal (private) number A. She does not tell anyone
this number. This number should be relatively prime to N .
3. Bob chooses his own personal (private) number B. He does not tell anyone
this number. This number should be relatively prime to N .
4. Alice calculates the number
S = N A (mod P )
and sends this number S to Bob.
5. Bob calculates
R = N B (mod P )
and sends this number R to Alice.
6. So now Bob and Alice have two numbers. Eve, who is watching this
exchange, is fully aware of the numbers S and R. But since she doesnt know
A and B, she doesnt know how Alice and Bob calculated the R and S.
5 DIFFIE-HELLMAN KEY EXHANGE
7. Alice takes the number she received from Bob and calculates
C = RA (mod P )
and Bob takes the number he received from Alice and calculates
C = S B (mod P )
8. C is their shared key. Since the last step is done in private, Eve does not
know C.
5.3
Example of a Key Exhange
Alice wants to send the message ATTACK AT DAWN to Bob. Before
encrypting it with the Vigenere Cipher, her and Bob need to agree upon the
keyword (in numeric form). Alice calls Bob, with Eve evesdropping on this
conversation, and come up with a public key
P = 983 and N = 20
Youll probably want to use the exponentiation calculator at
http://www.brianveitch.com/cryptography/modexp.php
1. Alice chooses the number A = 7 and Bob chooses the number B = 9.
Remember, these must be relatively prime to N = 20.
2. Alice calculates
S = 207 = 1280000000 312 (mod 983)
and sends this number to Bob.
3. Bob calculates
R = 209 = 512000000000 942 (mod 983)
and sends this number to Alice.
38
5 DIFFIE-HELLMAN KEY EXHANGE
39
4. Alice takes 942 (mod 983) and raises it to her number A = 7.
9427 101 (mod 983)
5. Bob takes 312 (mod 983) and raises it to his number B = 9.
3129 101 (mod 983)
6. So Alice encrypts the message ATTACK AT DAWN with the Vigenere
numeric key 101, or its equivalent alphabetic key BAB. The cipher text is
5.4
Why is Cracking this Exchange Difficult
In the previous example, here is all the information Eve has during this key
exchange.
P = 983, N = 20, , S = 312, and R = 942
In order for Eve, our evesdropper, to determine the keyword, she needs to solve
the following equations
312 20A (mod 983)
or
942 20B (mod 983)
This is difficult to do, especially when P and N are extremely large. Our example,
they arent large. But even for us, our best bet is probably trial and error. We
would try to plug in all the values (mod 983) for A and B and see which work.
5 DIFFIE-HELLMAN KEY EXHANGE
5.5
40
Key Exhange Activity
Get in groups of 3. One of you will be Alice, another will be Bob, and the third
will be Alice. In this activity, Alice and Bob will come up with their Vigenere
Cipher key right in front of Eve.
1. Alice writes a message. It doesnt matter how long since you will be using
the online Vigenere Cipher. You want to send this message to Bob. Do not
show this message to anyone.
2. Alice and Bob now speak to each other publicly. Eve is there listening and
taking notes. Alice and Bob agree on two numbers. Choose a prime number
P and another number N less than P . You may use the website
http://www.brianveitch.com/cryptography/prime_generator to
generate the prime number.
P =
and N =
3. Alice and Bob choose their private number. If youre Alice write it below
A=
and calculate
NA
(mod P)
If you are Bob, write it below
B=
and calculate
NB
(mod P)
4. Alice and Bob exchange numbers. Eve receives these numbers as well.
5. Alice and Bob finish the calculations to come with the key. Alice uses the
Vigenere Cipher at
http://www.brianveitch.com/cryptography/vigenere.php to create the
ciphertext.
5 DIFFIE-HELLMAN KEY EXHANGE
6. Alice sends the message to Bob for him to decipher.
7. Eve should write down the equations she must solve in order to calculate
their private key. She may try to crack it by using trial and error.
Change positions and redo this until everyone gets a chance to be Alice.
41
6 RSA ENCRYPTION
6
6.1
42
RSA Encryption
Introduction
I can think of two uses for RSA encryption that should make sense to us. In the
last chapter, we discussed a key exhange. This is a method for Alice and Bob to
commuicate publicly to create a secret key. If done correctly, Eve should have a
very hard time figuring this key out.
RSA encryption can also be used to send the key. Its very similar to the
Diffie-Hellman Key Exhange. RSA is called public key encryption (or
asymmetric-key encryption). It means that there is a public key to encrypt the
data and a secret key (only the receiver of the message knows) that will decrypt
the data. So Alice chooses the keyword for the Vigenere Cipher. She uses the
public key to encrypt her keyword and sends the ciphertext to Bob. Bob uses his
secret key, known only to him, to decrypt it. With the keyword now agreed upon,
Alice can use a different method to encrypt the data and send it to Bob.
Another use of RSA encryption is called Authentication. Suppose Bob recevies
a message, supposedly from Alice. How does he actually know this message is
from Alice? Its possible Eve intercepted the message and created her own to
send to Bob.
6.2
Example of RSA Encryption
Lets do an example using RSA. Public key is (e, n) = (3, 33)
Message: A T T A C K N O W
First, lets convert the letters to numbers using A = 0, B = 1, C = 2, D = 3, ...,
X = 23, Y = 24, Z = 25. Later on we will convert letters to their ASCII number.
Message:
ATTACK NOW
Pre-Cipher: 0 19 19 0 2 10 13 14 22
e = 3 is called the encryption key. Raise each number in the pre-cipher to e = 3,
(mod 33).
6 RSA ENCRYPTION
43
A:
T:
T:
A:
C:
K:
N:
O:
W:
03 0 (mod 33)
193 = 6859 28 (mod 33)
193 = 6859 28 (mod 33)
03 0 (mod 33)
23 8 (mod 33)
103 = 1000 10 (mod 33)
133 = 2197 19 (mod 33)
143 = 2744 5 (mod 33)
223 = 10648 22 (mod 33)
Message: A T T A C K N O W
Cipher:
0 28 28 0 8 10 19 5 22
Everyone has access to the public key. Only the receiver of the encrypted data
has the private key. This is called asymmetric key encryption. It means there is
one key to encrypt and a completely different key to decrypt.
The private key for our example is d = 7. Lets see what happens when we raise
our ciphertext numbers to the power of d = 7.
07 0
287 19
287 19
07 0
87 2
107 10
197 13
57 14
227 22
(mod
(mod
(mod
(mod
(mod
(mod
(mod
(mod
(mod
33)
33)
33)
33)
33)
33)
33)
33)
33)
6 RSA ENCRYPTION
44
We get back the original set of numbers
Plaintext: 0 19 19 0 2 10 13 14 22
Message:
ATTACK NOW
Suppose you want to send the number M . The ciphertext is
C M 3 (mod 33)
To decrypt the ciphertext, you compute
M C 7 (mod 33)
So to encrypt a number, we raised it to the 3rd power. To undo it, we raise it to
the 7th power. The question now is how do you come up with the private key
d = 7?
Warning:
Notice the same letter encrypted to the same number. Those numbers carry the
same statistical information as the Ceasar method. Once I figure out T = 28, I
can replace all 28s with T. This is no good to us. So lets go back to
Message: A T T A C K N O W
Cipher:
0 19 19 0 2 10 13 14 22
Instead of enrypting 0, 19, 19, 0, 2, 10, 13, 14, and 22, we can regroup the
numbers. One example would be,
01, 91, 90, 21, 01, 31, 42, 2
6 RSA ENCRYPTION
45
The problem is our modulus is 33, which is too small (since we have numbers
larger than 33 - 91, 90, 42) We need to choose a larger modulus and figure out a
new public and private key. Lets figure out how to do this now.
6.3
RSA Algorithm
Suppose Alice wants to send Bob a message. She uses Bobs public key (e, n).
Lets see how Bob came up with his public/private key by coming up with our
own public and private key.
1. Bob chooses two large primes. Call them p and q. He must keep these
secret!
Now you choose two primes (preferably between 10 and 20).
p=
q=
2. He then computes n = p q. This is part of the public key.
n=
3. Bob computes (n) = (p 1) (q 1)
(n) =
4. Bob chooses an integer e, 1 < e < (n) where e does not share any factors
with (n). This is called copime (or relatively prime).
Example: 8 and 15 are coprime because they share no factors.
Example: 9 and 24 are NOT coprime because they share a common factor 3.
6 RSA ENCRYPTION
46
e=
5. Bob now has his public key (e, n). Your public key is
(e, n) = (
6. Bob then computes his private key d. To find d, you must solve the following
equation
e d 1 (mod n)
Your equation is
d 1 (mod
Lets go over how Bob found d to the following equation. Then follow the
pattern. This may take a few tries to get right.
6.4
Using The Extended Euclidean Algorithm
We need the recursive formula: pi = pi2 pi1 qi2 where p0 = 0 and p1 = 1.
When you move onto the next step, you use ai = bi1 and bi = ri1
3 d 1 (mod 20)
6 RSA ENCRYPTION
ai =
47
qi bi + ri
pi = pi2 pi1 qi2
Step 0: 20 = (6) 3 + 2
p0 = 0
Step 1:
3 = (1) 2 + 1
p1 = 1
Step 2:
2 = (2) 1 + 0
p2 = p0 p1 q0 = 0 1(6) = 6
p3 = p1 p2 q1 = 1 (6) 1 = 7
Therefore, the solution to 3 d 1 (mod 20) is d = 7 (mod 20). This is how
Bob got his private key.
To view another example, please check out the Extended Euclidean
Algorithm section in Modular Arithmetic.
Your turn!
d 1 (mod
ai
Step 0:
Step 1:
Step 2:
Step 3:
Step 4:
Step 5:
= qi bi + ri
pi = pi2 pi1 qi2
6 RSA ENCRYPTION
48
Your d is the last pi value in the table. Make sure its (mod n).
Your private key is
d=
Use the website http://www.brianveitch.com/cryptography/modinverse.php
to confirm the inverse.
Example: Use your public key to encrypt the following. First, convert the letters
to numbers.
Message:
M A T H
Pre-Cipher:
E Q U A L S
M O N E Y
To encrypt each number N into the cipher C
C N e (mod n)
Use my expontentiation calculator at
http://www.brianveitch.com/cryptography/modexp.php
6 RSA ENCRYPTION
M:
A:
T:
H:
E:
Q:
U:
A:
L:
S:
M:
O:
N:
E:
Y:
49
(mod
(mod
(mod
(mod
(mod
(mod
(mod
(mod
(mod
(mod
(mod
(mod
(mod
(mod
(mod
)
)
)
)
)
)
)
)
)
)
)
)
)
)
)
To practice RSA encryption, work with a partner. Write a short message (no
more than 20 letters) and encrypt it using your partners public key. Do not tell
your partner your plaintext message. Give them only the ciphertext.
Your partner then decrypts the ciphertext using his or her private key to reveal
your message. Remember, to decrypt the message do the following
N C d (mod n)
Using the website
http://www.brianveitch.com/cryptography/generate_rsa_keys.php,
genereate your own public and private key.
Exchange public keys with your partner. Use your partners public key to encrypt
a word (at most 7 letters). Have your partner decrypt the word. Since the
modular exponentiation will be large, use the following websites to help
6 RSA ENCRYPTION
50
http://www.brianveitch.com/cryptography/modexp.php
and
http://www.brianveitch.com/cryptography/modinverse.php
How do we make this harder to crack?
Let me return to our previous example of encrypting
ATTACK NOW
Use the ASCII table provided below to convert every character (including the
space, periods, etc.) into its correponding ASCII number.
6.5
ASCII Table
6 RSA ENCRYPTION
51
After converting the characters to their corresponding ASCII numbers, we get the
following,
Message:
Plaintext: 65 84 84 65 67 75 32 78 79 87
Lets use the public key (e = 709, n = 923). To make this harder to crack, we
regroup the numbers into blocks of 3. There is nothing special about the size of
the block. You just have to make sure the numbers youre encrypting are less
than n = 923.
658|484|656|775|327|879|87
Since the numbers will get large, use the calculator at
http://www.brianveitch.com/cryptography/modexp.php
658709
484709
656709
775709
327709
879709
87709
(mod
(mod
(mod
(mod
(mod
(mod
(mod
923)
923)
923)
923)
923)
923)
923)
Therefore, the message
ATTACK NOW
encrypts to
697 419 188 541 288 333 854
6 RSA ENCRYPTION
52
Suppose youre Eve and you come across this encrypted message. You know the
method used and you know Bobs public key (709, 923). How do we crack it?
6.6
Cracking RSA by finding the private key d.
To decrypt the ciphertext, we need the private key d. So lets try to crack it.
1. Factor n = 923 into two prime numbers p and q.
n=
2. Calculte (n) = (p 1) (q 1)
(923) =
3. Now solve the equation using the Extended Euclidean Algorithm.
709 d 1 (mod 840)
qi
Step 0:
Step 1:
Step 2:
Step 3:
Step 4:
Step 5:
Step 6:
pi = pi2 pi1 qi2
6 RSA ENCRYPTION
53
Good! You now have the private key d =
Use http://www.brianveitch.com/cryptography/modexp.php to complete
the exponentiation. Raise each block of the ciphertext by the power of d.
(mod 923)
(mod 923)
(mod 923)
(mod 923
(mod 923)
(mod 923)
(mod 923)
4. After decrypting the numbers, you should have
658 484 656 775 327 879 87
5. Regroup the numbers back into blocks of 2 (starting from the left)
6. Finally rewrite the ASCII number back into its characters.
6.7
Your turn to crack an RSA encrypted message
You are Eve and you intercept a message sent from Alice to Bob. It was
encrypted using Bobs public key (n = 1224825487, e = 1118107197).
The ciphertext is
71218284 237148343 889555017 473479370 649324334 6660643 260396109
637251342 924334351 935096349 271621588 366934580 271621588 576453518
423052470 618017834 332813753 397822860
7 USING RSA FOR AUTHENTICATION
54
To crack the code, find the private key d. Follow the method we used to crack the
RSA example from before. Start by factoring n.
You can decrypt it using the private key d using the website
http://www.brianveitch.com/cryptography/modexp.php. If youre doing it by
hand, the original block size (before encryption) was 4.
or the website http://www.brianveitch.com/cryptography/rsa.php. Use a
block size of 2 on this website.
There you go. This is the general idea behind the RSA encryption. Now before
we finish with our RSA introduction, Id like to show you the size of a typical
modulus n.
16152174667064029642647365822885998430666314431815268152405470907824573
65903662972483772980826569393306732864932303362619914669385966910731129
68626710792148904239628873374506302653492009810626437582587089465395941
37549600473991849827667633423824146549803003658606392990236819200423317
2032080188726965600617167
Can you see why trying to factor n to crack RSA is hard? Even if you can factor
it, you still need to find the private key d.
Using RSA for Authentication
7.1
Algorithm
As noted earlier, how does Bob actually know the message is sent from Alice.
Heres what she does.
1. Alice pubicly announces her RSA public key, say (n = 2263, e = 917).
2. She converts her name to ASCII numbers: 65 76 73 67 69. She then encrypts
her name with her private key d = 1133. Remember that only Alice knows
the private key. You may need the calculator at
http://www.brianveitch.com/cryptography/modexp.php
7 USING RSA FOR AUTHENTICATION
651133
761133
731133
671133
691133
55
228 (mod 2263)
1630 (mod 2263)
1314 (mod 2263)
645 (mod 2263)
1405 (mod 2263)
3. She sends her encrypted name along with the encrypted message meant for
Bob.
ALICE Encrypted: 228 1630 1314 645 1405
4. Bob receives two ciphers. One is Alices encrypted name. The other is the
actual encrypted message. Bob decrypts her message, but isnt convinced it
was sent from Alice.
5. Bob uses Alices public key, which is accessible by everyone, to decrypt the
name.
228917
1630917
1314917
645917
1405917
65
76
73
67
69
(mod
(mod
(mod
(mod
(mod
2263)
2263)
2263)
2263)
2263)
65 76 73 67 69 ALICE
6. Since Alice sent her name by encrypting it with her private key, no one can
fake this. The only way Eve can fake her name is by encrypting ALICE
with her private key. And the only way Eve can do that is by cracking her
RSA public key.
7 USING RSA FOR AUTHENTICATION
7.2
56
Authentication Activity
1. Get in groups of 3. One person is Alice, another is Bob, and the third is
Alice.
2. Alice needs to generate a public key. She also needs her find her private key.
She can do this by hand or use the RSA Key Generator at
http://www.brianveitch.com/cryptography/generate_rsa_keys. Alice
will create a message and encrypt it. She may use any method she wants.
3. Eve will create her own message (something that may contradict Alices
message).
Example:
(a) Alice may encrypt the message ATTACK AT DAWN using the Caesar
Cipher.
(b) Eve may encrypt DO NOT ATTACK AT DAWN using the Caesar
Cipher.
4. Using Alices public key, she encrypts her name by using her private key.
5. Eve will also encrypt Alices name, but she must guess on the private key.
6. Both Alice and Eve send Bob their messages with the encrypted name.
7. Bob decrypts both message. Not sure which message came from Alice, use
Alices public key to decrypt the names.
8. Unless Eve guessed correctly on Alices private key, Alices encrypted name
should decrypt back to Alice and Eves should decrypt to jibberish.
8 IMPORTANT INFORMATION
8
8.1
Important Information
Caesar Shift Wheel
57
8 IMPORTANT INFORMATION
8.2
Letter Frequency Tables
58
8 IMPORTANT INFORMATION
8.3
Vigeneres Table
59
8 IMPORTANT INFORMATION
8.4
ASCII Table
8.5
Useful Websites
Random Substitution Generator
http://www.brianveitch.com/cryptography/sub_shift.php
Easier Caesar Cipher
http://www.brianveitch.com/cryptography/caesar_friendly.php
Caesar Cipher
http://www.brianveitch.com/cryptography/caesar.php
Keyword Substitution Cipher
http://www.brianveitch.com/cryptography/keyword.php
60
8 IMPORTANT INFORMATION
Vigenere Ciphere
http://www.brianveitch.com/cryptography/vigenere.php
Letter Frequency
http://www.brianveitch.com/cryptography/relative_frequency.php
Modular Exponentiation
http://www.brianveitch.com/cryptography/modexp.php
Modular Inverse
http://www.brianveitch.com/cryptography/modinverse.php
String to ASCII
http://www.brianveitch.com/cryptography/string_to_number.php
ASCII to String
http://www.brianveitch.com/cryptography/number_to_string.php
Easier RSA - No Blocking Before Encrypting
http://www.brianveitch.com/cryptography/rsa_easy.php
RSA - Blocking Before Encrypting
http://www.brianveitch.com/cryptography/rsa.php
Generate RSA Public and Private Keys
http://www.brianveitch.com/cryptography/generate_rsa_keys.php
Generate Prime Numbers
http://www.brianveitch.com/cryptography/generate_primes.php
61
S-ar putea să vă placă și
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeDe la EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeEvaluare: 4 din 5 stele4/5 (5794)
- Shoe Dog: A Memoir by the Creator of NikeDe la EverandShoe Dog: A Memoir by the Creator of NikeEvaluare: 4.5 din 5 stele4.5/5 (537)
- The Yellow House: A Memoir (2019 National Book Award Winner)De la EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Evaluare: 4 din 5 stele4/5 (98)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceDe la EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceEvaluare: 4 din 5 stele4/5 (895)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersDe la EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersEvaluare: 4.5 din 5 stele4.5/5 (344)
- The Little Book of Hygge: Danish Secrets to Happy LivingDe la EverandThe Little Book of Hygge: Danish Secrets to Happy LivingEvaluare: 3.5 din 5 stele3.5/5 (399)
- Grit: The Power of Passion and PerseveranceDe la EverandGrit: The Power of Passion and PerseveranceEvaluare: 4 din 5 stele4/5 (588)
- The Emperor of All Maladies: A Biography of CancerDe la EverandThe Emperor of All Maladies: A Biography of CancerEvaluare: 4.5 din 5 stele4.5/5 (271)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaDe la EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaEvaluare: 4.5 din 5 stele4.5/5 (266)
- Never Split the Difference: Negotiating As If Your Life Depended On ItDe la EverandNever Split the Difference: Negotiating As If Your Life Depended On ItEvaluare: 4.5 din 5 stele4.5/5 (838)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryDe la EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryEvaluare: 3.5 din 5 stele3.5/5 (231)
- On Fire: The (Burning) Case for a Green New DealDe la EverandOn Fire: The (Burning) Case for a Green New DealEvaluare: 4 din 5 stele4/5 (73)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureDe la EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureEvaluare: 4.5 din 5 stele4.5/5 (474)
- Team of Rivals: The Political Genius of Abraham LincolnDe la EverandTeam of Rivals: The Political Genius of Abraham LincolnEvaluare: 4.5 din 5 stele4.5/5 (234)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyDe la EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyEvaluare: 3.5 din 5 stele3.5/5 (2259)
- The Unwinding: An Inner History of the New AmericaDe la EverandThe Unwinding: An Inner History of the New AmericaEvaluare: 4 din 5 stele4/5 (45)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreDe la EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreEvaluare: 4 din 5 stele4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)De la EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Evaluare: 4.5 din 5 stele4.5/5 (120)
- Her Body and Other Parties: StoriesDe la EverandHer Body and Other Parties: StoriesEvaluare: 4 din 5 stele4/5 (821)
- Interurban RMC Rail Bus ManualDocument4 paginiInterurban RMC Rail Bus ManualSteven GardnerÎncă nu există evaluări
- Banana ChipsDocument5 paginiBanana Chipsbikram limbuÎncă nu există evaluări
- PetroMod 1NEWDocument20 paginiPetroMod 1NEWAbdalrhman MuhammadÎncă nu există evaluări
- Open IVDocument84 paginiOpen IVSokr AbdoÎncă nu există evaluări
- 2016 GME Steel ProductsDocument16 pagini2016 GME Steel ProductsMarco Dos Santos NevesÎncă nu există evaluări
- Geopolymer Reinforced With Bamboo For Sustainable Construction MaterialsDocument7 paginiGeopolymer Reinforced With Bamboo For Sustainable Construction MaterialsSamyuktha SridharÎncă nu există evaluări
- CPAR Summary - WK 144Document6 paginiCPAR Summary - WK 144NagarajÎncă nu există evaluări
- Activity3 3 1utilitesDocument2 paginiActivity3 3 1utilitesapi-302096056Încă nu există evaluări
- PICP Manual 3rd Edition PDFDocument62 paginiPICP Manual 3rd Edition PDFanmolÎncă nu există evaluări
- Harsh SukhramaniDocument6 paginiHarsh SukhramaniHarsh SukhramaniÎncă nu există evaluări
- New Concept in AC Power TheoryDocument8 paginiNew Concept in AC Power TheoryGabor PeterÎncă nu există evaluări
- WAHLER Imagebroschuere SERIE enDocument16 paginiWAHLER Imagebroschuere SERIE ensagarpatel337Încă nu există evaluări
- VAV CablingDocument2 paginiVAV Cablingsripriya01Încă nu există evaluări
- VCS Commands Ease Coverage Efforts - Speed Simulation PDFDocument6 paginiVCS Commands Ease Coverage Efforts - Speed Simulation PDFAnonymous k2nUzQgO6HÎncă nu există evaluări
- MESCO News January 2016Document4 paginiMESCO News January 2016GoriZakirSalimÎncă nu există evaluări
- Ijesrt: Modelling and Simulation of Solar Photovoltaic Array For Battery Charging Application Using Matlab-SimulinkDocument5 paginiIjesrt: Modelling and Simulation of Solar Photovoltaic Array For Battery Charging Application Using Matlab-Simulinksrinureddy2014Încă nu există evaluări
- Patriot MissileDocument19 paginiPatriot MissileBogdan Claudiu HututuiÎncă nu există evaluări
- Cat Fines Presentation SlidesDocument48 paginiCat Fines Presentation SlidescaptkcÎncă nu există evaluări
- Cks 180 Ton MIGAS BaruDocument46 paginiCks 180 Ton MIGAS BaruHario PramuditoÎncă nu există evaluări
- Shower CatalogueDocument36 paginiShower CataloguekavyaÎncă nu există evaluări
- Drying Kinetics and Characteristic Drying Curve of Lightly Salted Sardine (Sardinella Aurita)Document8 paginiDrying Kinetics and Characteristic Drying Curve of Lightly Salted Sardine (Sardinella Aurita)Nguyen Thu HaÎncă nu există evaluări
- Ohlins Tool Manual 2017Document46 paginiOhlins Tool Manual 2017Pier o.f.r.Încă nu există evaluări
- WoodwardDocument5 paginiWoodwardMuhammad UsmanÎncă nu există evaluări
- Bridge Inspection ManualDocument539 paginiBridge Inspection ManualماقوريÎncă nu există evaluări
- Topic 05 All Possible QuestionsDocument9 paginiTopic 05 All Possible QuestionsMaxamed Cabdi KariimÎncă nu există evaluări
- Hot Pumps & Thermal ExpansionDocument3 paginiHot Pumps & Thermal ExpansionMahmoud Al Homran100% (1)
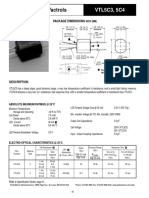
- Low Cost Axial Vactrols: VTL5C3, 5C4Document2 paginiLow Cost Axial Vactrols: VTL5C3, 5C4sillyÎncă nu există evaluări
- GFM Lab ReportDocument102 paginiGFM Lab ReportÁlvaroDeLaGarza100% (1)
- G1 - PPT - Design and Simulation of Microstrip Patch Antenna For Wireless ApplicationsDocument18 paginiG1 - PPT - Design and Simulation of Microstrip Patch Antenna For Wireless Applicationspooja yadav100% (1)