Documente Academic
Documente Profesional
Documente Cultură
Fortigate 200D Quick Start Guide
Încărcat de
miloymorales7274Drepturi de autor
Formate disponibile
Partajați acest document
Partajați sau inserați document
Vi se pare util acest document?
Este necorespunzător acest conținut?
Raportați acest documentDrepturi de autor:
Formate disponibile
Fortigate 200D Quick Start Guide
Încărcat de
miloymorales7274Drepturi de autor:
Formate disponibile
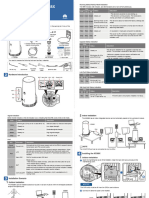
FortiGate-200 LED Indicators
LED State Description FortiGate-200
Power Green The FortiGate unit is powered on.
Off The FortiGate unit is powered off.
Status Flashing green The FortiGate unit is starting up.
POWER STATUS INTERNAL EXTERNAL DMZ
CONSOLE INTERNAL EXTERNAL DMZ
Green The FortiGate unit is running normally.
Off The FortiGate unit is powered off.
QuickStart Guide
Internal External Green The correct cable is in use, and the
DMZ connected equipment has power.
(front and back) Flashing green (front) Network activity at this interface.
Flashing Amber (back)
Copyright 2004 Fortinet Incorporated. All rights reserved.
Off No link established. Trademarks
Products mentioned in this document are trademarks or registered trademarks of their respective holders.
Factory default settings Regulatory Compliance
FCC Class A Part 15 CSA/CUS
NAT/Route mode Transparent mode 03 November 2004
Internal interface 192.168.1.99 Management IP 10.10.10.1
For technical support please visit http://www.fortinet.com.
External interface 192.168.100.99 Administrative account settings
DMZ interface 10.10.10.1 User name admin
Password (none) 01-28005-0034-20041103
1 Checking the package contents Check that the package contents are complete.
Front
Ethernet Cables:
Orange - Crossover
Grey - Straight-through
Connector Type Speed Protocol Description
POWER STATUS INTERNAL EXTERNAL DMZ
CONSOLE INTERNAL EXTERNAL DMZ
Null-Modem Cable
Internal RJ-45 10/100Base_T Ethernet Connection to the internal network. (RS-232)
Power Status Internal, External, RS-232 Serial Internal External DMZ
External RJ-45 10/100Base_T Ethernet Connection to the Internet. LED LED DMZ Interface LEDs Connection Interface Interface Interface
Power Cable
Optional connection to a DMZ network, or other Back
DMZ RJ-45 10/100Base_T Ethernet FortiGate-200 units for high availability (HA). For details,
see the Documentation CD-ROM. Rack-Mount Brackets
RS-232 Optional connection to the management computer.
CONSOLE DB-9 9600 bps
FortiGate-200
serial Provides access to the command line interface (CLI). Removable Power Power USER MANUAL POWER STATUS INTERNAL EXTERNAL DMZ
CONSOLE INTERNAL EXTERNAL DMZ
Hard Drive Switch Connection QuickStart Guide
Copyright 2003 Fortinet Incorporated. All rights reserved.
Trademarks
Products mentioned in this document are trademarks.
Documentation
2 Connecting the FortiGate-200
Place the unit on a stable surface or mount it in a 19-inch rack. It
Connect the FortiGate-200 unit to power outlets and to the internal and external networks.
Optional null modem cable connects to serial port on management computer
Power cable connects to power outlet
requires 1.5 inches clearance (3.75 cm) on each side to allow for
cooling. POWER STATUS INTERNAL EXTERNAL DMZ
CONSOLE INTERNAL EXTERNAL DMZ
Make sure the power switch on the back of the unit is turned off before or
connecting the power and network cables. Optional straight-through Ethernet cable connects to DMZ network
Straight-through Ethernet cable connects to Internet (public switch, router or modem)
Crossover Ethernet cable connects to management computer on internal network
Straight-through Ethernet cable connects to LAN or switch on internal network
3
NAT/Route mode
Planning the configuration
In NAT/Route mode, the FortiGate-200 is visible to the networks that it is connected to.
Before configuring the FortiGate-200, you need to plan how to integrate the unit into your
network. Your configuration plan is dependent upon the operating mode that you select: NAT/
Route mode (the default) or Transparent mode.
Transparent mode
In Transparent mode, the FortiGate-200 is invisible to the network. All of its interfaces
All of its interfaces are on different subnets. You must configure the internal and are on the same subnet. You only have to configure a management IP address so that
external interfaces with IP addresses. Optionally, you can also configure the DMZ you can make configuration changes.
interface. You would typically use the FortiGate-200 in Transparent mode on a private network
You would typically use NAT/Route mode when the FortiGate-200 is deployed as a behind an existing firewall or behind a router. In its default Transparent mode
gateway between private and public networks. In its default NAT/Route mode configuration, the unit functions as a firewall. By default, the unit has a single firewall
configuration, the unit functions as a firewall. Firewall policies control communications policy that allows users on the internal network segment to connect to the external
through the FortiGate-200 unit. network segment. No other traffic is possible until you have configured more policies.
Internal network FortiGate-200 Unit
Gateway to
in Transparent mode
192.168.1.3
FortiGate-200 Unit Internal
public network
204.23.1.5 10.10.10.2 Internal network
in NAT/Route mode 192.168.1.99 POWER STATUS INTERNAL EXTERNAL DMZ
CONSOLE INTERNAL EXTERNAL DMZ
Internet
External 10.10.10.3
Route mode policies External
204.23.1.5 (firewall, router) 10.10.10.1 Internal
POWER STATUS INTERNAL EXTERNAL DMZ
controlling traffic between
Internet
CONSOLE INTERNAL EXTERNAL DMZ
internal networks. Management IP
DMZ DMZ network Transparent mode policies
10.10.10.1 controlling traffic between
NAT mode policies controlling internal and external networks
traffic between internal and
external networks. 10.10.10.2
You can connect up to three network segments to the FortiGate-200 unit to control
traffic between these network segments.
In NAT/Route mode, firewall policies can operate in NAT mode or in Route mode. In
NAT mode, the FortiGate-200 performs network address translation before IP packets
are sent to the destination network. In route mode, no translation takes place. By
default, the unit has a single NAT mode policy that allows users on the internal network
to securely access and download content from the Internet. No other traffic is possible
until you have configured more policies.
Refer to the Documentation CD-ROM for information on how to control traffic, and how to configure HA, antivirus protection, Web content filtering, Spam filtering, intrusion
prevention (IPS), and virtual private networking (VPN).
4 Choosing a configuration tool
Web-based manager and Setup
Choose among two different tools to configure the FortiGate-200.
Command Line Interface (CLI)
Wizard The CLI is a full-featured management tool.
Using the Setup Wizard you can add basic settings Use it to configure the administrator password, the
by stepping through the wizard pages and filling in interface addresses, the default gateway address, and
the information required. the DNS server addresses. To configure advanced
settings, see the Documentation CD-ROM.
The FortiGate web-based manager is an easy to use
management tool. Use it to configure the Requirements:
administrator password, interface addresses, the The RJ-45-serial connection between the FortiGate-200
default gateway address, and the DNS server and management computer.
addresses.
A terminal emulation application (HyperTerminal for Windows) on the management
Requirements: computer.
Ethernet connection between the FortiGate-200 and a management computer.
Internet Explorer version 6.0 or higher on the management computer.
5 Collecting information
NAT/Route mode
Use these tables to record your FortiGate-200 configuration.
Transparent mode
IP: ____.____.____.____ IP: ____.____.____.____
Internal Interface: Management IP:
Netmask: ____.____.____.____ Netmask: ____.____.____.____
IP: ____.____.____.____
External Interface: The management IP address and netmask must be valid for the network from which
Netmask: ____.____.____.____ you will manage the FortiGate-200.
IP: ____.____.____.____ General settings
DMZ Interface
Netmask: ____.____.____.____ Administrator password:
The internal interface IP address and netmask must be valid for the internal network. Default Gateway: ____.____.____.____
Network Settings: Primary DNS Server: ____.____.____.____
Secondary DNS Server: ____.____.____.____
A default gateway is required for the FortiGate unit to route connections to the Internet.
6 Configuring the FortiGate-200
Web-based manager
1. Connect the FortiGate-200 internal interface to a management computer Ethernet interface.
Use a cross-over Ethernet cable to connect the devices directly. Use straight-through Ethernet
cables to connect the devices through a hub or switch.
2. Configure the management computer to be on the same subnet as the internal interface of the FortiGate-200. To do this,
change the IP address of the management computer to 192.168.1.2 and the netmask to 255.255.255.0.
and Setup Wizard 3. To access the FortiGate web-based manager, start Internet Explorer and browse to https://192.168.1.99 (remember to
include the s in https://).
4. Type admin in the Name field and select Login.
NAT/Route mode Transparent mode
To configure the FortiGate-200 using the Setup Wizard, select the To switch from NAT/route mode to transparent mode
Easy Setup Wizard button and follow the prompts. Select the 1. Go to System > Status, select Change beside Operation Mode, and select OK.
To change the administrator password Easy Setup Wizard 2. Change the IP address of the management computer to 10.10.10.2 and use
1. Go to System > Admin > Administrators. Internet Explorer to browse to https://10.10.10.1.
2. Select Change Password for the admin administrator and enter a new password. To configure the FortiGate-200 using the Setup Wizard, select the Easy Setup Wizard
button and follow the prompts.
To configure interfaces
To change the administrator password
1. Go to System > Network > Interface.
1. Go to System > Admin > Administrators.
2. Select the edit icon for each interface to configure.
2. Select Change Password for the admin administrator and enter a new password.
3. Set the addressing mode for the interface. (see the online help for information.)
For manual addressing, enter the IP address and netmask for the interface. To configure the management interface
For DHCP addressing, select DHCP and any required settings. 1. Go to System > Network > Management.
For PPPoE addressing, select PPPoE, and enter the username and password 2. Enter the Management IP address and netmask that you recorded above.
and any other required settings. 3. Select administrative access options if required and select OK.
To configure the Primary and Secondary DNS server IP addresses To configure the Primary and Secondary DNS server IP addresses
1. Go to System > Network > DNS, enter the Primary and Secondary DNS IP 1. Go to System > Network > DNS, enter the Primary and Secondary DNS IP
addresses that you recorded above and select Apply. addresses that you recorded above and select Apply.
To configure a Default Gateway To configure a Default Gateway
1. Go to Router > Static and select Edit icon for the static route. 1. Go to System > Network > Management.
2. Set Gateway to the Default Gateway IP address that you recorded above and select 2. Set Default Gateway to the Default Gateway IP address that you recorded above
OK. and select OK.
Note: If you change the internal interface IP address (NAT/Route mode) or management IP address (Transparent mode), you must use this address to reconnect to the web-based manager and Setup Wizard.
You might also have to change the IP address of the management computer to be on the same subnet as the new IP address.
Using the 1. Use the serial cable to connect the FortiGate Console port to the management computer serial port.
2. Start a terminal emulation program (HyperTerminal) on the management computer. Use these settings:
Command Line Interface Baud Rate (bps) 9600, Data bits 8, Parity None, Stop bits 1, and Flow Control None.
3. At the Login: prompt, type admin and press Enter twice (no password required).
NAT/Route mode Transparent mode
1. Configure the FortiGate-200 internal interface. 1. Change from NAT/Route mode to Transparent mode.
config system interface config system global
edit internal set opmode transparent
set mode static end
set ip <intf_ip> <netmask_ip>
end 2. Wait a moment and then log in again at the prompt.
2. Repeat to configure each interface, for example, to configure the external interface. 3. Configure the Management IP address.
config system interface config system manageip
edit external set ip <mng_ip> <netmask>
... end
3. Configure the primary and secondary DNS server IP addresses. Configure the DNS server IP address.
config system dns config system dns
set primary <dns-server_ip> set primary <dns-server_ip>
set secondary <dns-server_ip> set secondary <dns-server_ip>
end end
4. Configure the default gateway. 4. Configure the default route.
config router static config router static
edit 1 edit 1
set gateway <gateway_ip> set gateway <gateway_ip>
end end
Restarting the FortiGate-200 To restart the unit, go to System > Maintenance > CLI: execute reboot
ShutDown and select Reboot.
Should you mistakenly change a network setting and cannot connect to the unit, reboot
the unit and try again or to set the unit back to factory defaults and start over again. To reset the unit, go to System > Maintenance > CLI: execute factoryreset
Shutdown and select Reset to factory default.
7 Completing the configuration
Congratulations!
Technical support
Fortinet Technical Support Web site: http://support.fortinet.com
Fortinet email support:
You have finished configuring the basic settings. Your network is now protected amer_support@fortinet.com For customers in the United States, Canada, Mexico, Latin
from Internet-based threats. To explore the full range of configuration options, see America and South America.
the online help or the Documentation CD-ROM.
apac_support@fortinet.com For customers in Japan, Korea, China, Hong Kong,
Singapore, Malaysia, all other Asian countries, and Australia.
eu_support@fortinet.com For customers in the United Kingdom, Scandinavia,
Mainland Europe, Africa, and the Middle East.
S-ar putea să vă placă și
- Verizon Internet Gateway Arc Xci55ax User GuideDocument167 paginiVerizon Internet Gateway Arc Xci55ax User GuideJordan OxleyÎncă nu există evaluări
- Fortiwifi 81CM QuickstartDocument2 paginiFortiwifi 81CM QuickstartgroverramiroÎncă nu există evaluări
- Fortigate 80C QuickstartDocument2 paginiFortigate 80C QuickstartZbrda ZdolaÎncă nu există evaluări
- FortiGate-100A Quick Start GuideDocument2 paginiFortiGate-100A Quick Start GuiderobotsallaÎncă nu există evaluări
- Package Contents: Quickstart GuideDocument2 paginiPackage Contents: Quickstart GuideFedericoÎncă nu există evaluări
- FortiGate LED SpecsDocument4 paginiFortiGate LED SpecsrajeshÎncă nu există evaluări
- FW-60B QuickStart GuideDocument2 paginiFW-60B QuickStart GuideSteve FisherÎncă nu există evaluări
- Package Contents: Quickstart GuideDocument2 paginiPackage Contents: Quickstart GuideBayu AlamÎncă nu există evaluări
- Quickstart Guide: Fortigate 3500F SeriesDocument9 paginiQuickstart Guide: Fortigate 3500F Seriesxserver managerÎncă nu există evaluări
- FG 200F QSGDocument15 paginiFG 200F QSGHadi SleemÎncă nu există evaluări
- Power Status HA Alarm Left LED Ports 1 To 10Document2 paginiPower Status HA Alarm Left LED Ports 1 To 10crushhim100% (2)
- FortiSwitch 108F Series QSGDocument15 paginiFortiSwitch 108F Series QSGfelomino.bacquianoÎncă nu există evaluări
- FortiAP 831F QSGDocument9 paginiFortiAP 831F QSGmateequllah9809Încă nu există evaluări
- 5G Outdoor CPE N5368X Quick Start GuideDocument5 pagini5G Outdoor CPE N5368X Quick Start GuidenviscaqÎncă nu există evaluări
- Users Manual 3326997Document24 paginiUsers Manual 3326997Andrzej GomulaÎncă nu există evaluări
- FortiGate 50B - QuickStart - Guide - 01 30003 0361 20070419Document2 paginiFortiGate 50B - QuickStart - Guide - 01 30003 0361 20070419Ludving Coy ArévaloÎncă nu există evaluări
- Fortinet Fortigate 60Document2 paginiFortinet Fortigate 60Davor Mendizabal TapiaÎncă nu există evaluări
- WISI Mux SpecificationDocument4 paginiWISI Mux Specificationnobagi8890Încă nu există evaluări
- FG 80f QSG SeriesDocument19 paginiFG 80f QSG SeriesviabibÎncă nu există evaluări
- Windows Agent 4.1 Enhancements: Fortisiem 6.2.0Document6 paginiWindows Agent 4.1 Enhancements: Fortisiem 6.2.0Pierina FernandezÎncă nu există evaluări
- Quick Guide For GT41: GT41 IP Processing ModuleDocument4 paginiQuick Guide For GT41: GT41 IP Processing Modulelunalo marcÎncă nu există evaluări
- Lab 2: Security Fabric: Do Not Reprint © FortinetDocument27 paginiLab 2: Security Fabric: Do Not Reprint © FortinetCarlos MuñozÎncă nu există evaluări
- OptimDocument2 paginiOptimSteveÎncă nu există evaluări
- FortiSwitch 448E Series QSGDocument15 paginiFortiSwitch 448E Series QSGmohammad alalamiÎncă nu există evaluări
- EAP225 outdoorIGDocument2 paginiEAP225 outdoorIGAlejandróò MarinÎncă nu există evaluări
- Redundant Architecture (Expert) - Fortinet CookbookDocument14 paginiRedundant Architecture (Expert) - Fortinet Cookbooksam_azly100% (1)
- 1265.D.01.0015 - 1 G-ULTRA Q Guide - SAONLY - 14052021 - AP - WebDocument2 pagini1265.D.01.0015 - 1 G-ULTRA Q Guide - SAONLY - 14052021 - AP - WebMaria Coetzee CoetzeeÎncă nu există evaluări
- GT26 Quick GuidDocument4 paginiGT26 Quick GuidHubert Chang EscalanteÎncă nu există evaluări
- Fortigate 200B Quickstart PDFDocument2 paginiFortigate 200B Quickstart PDFAmit PatilÎncă nu există evaluări
- Fortigate 620B QuickstartDocument2 paginiFortigate 620B QuickstartSandy JosephÎncă nu există evaluări
- Quickstart Guide: Fortigate/FortiwifiDocument17 paginiQuickstart Guide: Fortigate/Fortiwifim0nsysÎncă nu există evaluări
- FortiGate 300D SupplementDocument12 paginiFortiGate 300D SupplementCristian AmezquitaÎncă nu există evaluări
- Enterprise FW 05-Central ManagementDocument34 paginiEnterprise FW 05-Central ManagementMarcos Vinicios Santos CorrêaÎncă nu există evaluări
- GEH-6421System Manual For Mark VIDocument342 paginiGEH-6421System Manual For Mark VIjorge lopezÎncă nu există evaluări
- Fortigate 60C: Quickstart GuideDocument24 paginiFortigate 60C: Quickstart Guideqwerty12999Încă nu există evaluări
- GPM - June 2019Document15 paginiGPM - June 2019Yogender YadavÎncă nu există evaluări
- GPM - June 2019Document15 paginiGPM - June 2019Yogender YadavÎncă nu există evaluări
- FortiSwitch Secure Access SeriesDocument16 paginiFortiSwitch Secure Access SeriesSiva NanthamÎncă nu există evaluări
- 05 C1 SD1 Config Ha LabDocument18 pagini05 C1 SD1 Config Ha LabPaul SjobergÎncă nu există evaluări
- Fortinet ProductsDocument1 paginăFortinet ProductsFnDÎncă nu există evaluări
- Barracuda NG Firewall F100 / F101Document4 paginiBarracuda NG Firewall F100 / F101adiclÎncă nu există evaluări
- FortiSwitch Secure Access SeriesDocument13 paginiFortiSwitch Secure Access SeriesAlexandro LaurentÎncă nu există evaluări
- Fortigate 20C: Quickstart GuideDocument14 paginiFortigate 20C: Quickstart GuideIrving LunaÎncă nu există evaluări
- Us 16 150W QSGDocument24 paginiUs 16 150W QSGSzigyarto MihaiÎncă nu există evaluări
- FortiSwitch Data Center SeriesDocument8 paginiFortiSwitch Data Center SeriesDuško PetrovićÎncă nu există evaluări
- Microwave-bc-En-zxmw Nr8250 v1.00 Commissioning GuideDocument105 paginiMicrowave-bc-En-zxmw Nr8250 v1.00 Commissioning GuideOmingo Kingi100% (1)
- Rackmount Accessory Model: CKG2-RMDocument17 paginiRackmount Accessory Model: CKG2-RMGeorge ClooneyÎncă nu există evaluări
- Ingate Siparator Getting Starting Guide PDFDocument88 paginiIngate Siparator Getting Starting Guide PDFguesieroÎncă nu există evaluări
- Redundant ArchitectureDocument12 paginiRedundant ArchitecturemedjdoubmayaÎncă nu există evaluări
- ATN905Document18 paginiATN905Ahmed SharafÎncă nu există evaluări
- FortiGate 500DDocument12 paginiFortiGate 500DDavyAvicenneÎncă nu există evaluări
- Fortinet Fortigate and Nozomi Networks Guardian: Deployment GuideDocument11 paginiFortinet Fortigate and Nozomi Networks Guardian: Deployment GuideCom DigfulÎncă nu există evaluări
- Integriti - Nemtek Integration GuideDocument8 paginiIntegriti - Nemtek Integration GuideShahid MehboobÎncă nu există evaluări
- Jimi JC400 AI-Powered Video Telematics Solutions 20200507Document34 paginiJimi JC400 AI-Powered Video Telematics Solutions 20200507kyczq8wbzbÎncă nu există evaluări
- Datasheet IES-2042PA v1.1Document3 paginiDatasheet IES-2042PA v1.1oring2012Încă nu există evaluări
- Linksys SRW224G4Document3 paginiLinksys SRW224G4outlaw666hrÎncă nu există evaluări
- Comp Eng 5 Sem TCP Ip and Internet 3446 Summer 2019Document2 paginiComp Eng 5 Sem TCP Ip and Internet 3446 Summer 2019VaishÎncă nu există evaluări
- Concepts of Web BrowserDocument31 paginiConcepts of Web BrowserNeha DhadveÎncă nu există evaluări
- CCNPv6 ROUTE Lab6-1 BGP Config InstructorDocument15 paginiCCNPv6 ROUTE Lab6-1 BGP Config InstructorMiguel Andres Castañeda OrtegaÎncă nu există evaluări
- 01 - MTCNA v5.4 - ALLDocument334 pagini01 - MTCNA v5.4 - ALLIqbal Wahyu Septian 24TKJÎncă nu există evaluări
- Value Added Course - 2020-21 BatchDocument2 paginiValue Added Course - 2020-21 BatchSUPRIYA PRAJAPATIÎncă nu există evaluări
- KSMDSMDDocument279 paginiKSMDSMDandry adamÎncă nu există evaluări
- TCP IP - IP Protocol Suite PDFDocument62 paginiTCP IP - IP Protocol Suite PDFMustafa Al HassanÎncă nu există evaluări
- IPsec VPN TroubleshootingDocument8 paginiIPsec VPN TroubleshootingmipingoÎncă nu există evaluări
- 7750 SR OS MPLS Guide 10.0.R1Document5 pagini7750 SR OS MPLS Guide 10.0.R1Dennis PhillipsÎncă nu există evaluări
- NIOS Configuration Class: Course SummaryDocument2 paginiNIOS Configuration Class: Course SummaryforeverbikasÎncă nu există evaluări
- Guia de Usuario Routers Tp-link-WR840N (EU) - V5 - UGDocument120 paginiGuia de Usuario Routers Tp-link-WR840N (EU) - V5 - UGsebas_qsryÎncă nu există evaluări
- CCNP Class Notes (Ospf)Document20 paginiCCNP Class Notes (Ospf)Bashri MabyouÎncă nu există evaluări
- v6.3.1 Releasenotes v3.0Document66 paginiv6.3.1 Releasenotes v3.0Dale DiduloÎncă nu există evaluări
- CLI Command HierarchyDocument6 paginiCLI Command HierarchyddiixxyyÎncă nu există evaluări
- Asr9k Mpls Config GuideDocument280 paginiAsr9k Mpls Config GuideMaulik ShethÎncă nu există evaluări
- IOS Series AP - Event LogDocument1 paginăIOS Series AP - Event LogkumaÎncă nu există evaluări
- Chap 06Document17 paginiChap 06Anand Kumar SumanÎncă nu există evaluări
- New York University Computer Science Department Courant Institute of Mathematical SciencesDocument11 paginiNew York University Computer Science Department Courant Institute of Mathematical SciencesNusrat UllahÎncă nu există evaluări
- ONVIF Profile Feature Overview v2.5: Function Lists Use The Following AbbreviationsDocument7 paginiONVIF Profile Feature Overview v2.5: Function Lists Use The Following AbbreviationsHai Dang DaoÎncă nu există evaluări
- Lab Manual For Computer Communication & Networks: (LAB-11) (Configuration of Inter Virtual LAN's)Document16 paginiLab Manual For Computer Communication & Networks: (LAB-11) (Configuration of Inter Virtual LAN's)Přîñçè Abdullah SohailÎncă nu există evaluări
- The NGN Carrier Ethernet SystemDocument52 paginiThe NGN Carrier Ethernet SystemjuharieÎncă nu există evaluări
- User Guide: AC1000 Dual-Band Wi-Fi RouterDocument46 paginiUser Guide: AC1000 Dual-Band Wi-Fi RouterHector Fabio Gonzalez AlvarezÎncă nu există evaluări
- F5 GTM Course ContentDocument4 paginiF5 GTM Course ContentTanveer AkhtarÎncă nu există evaluări
- Computer Networks MCQ QuestionsDocument8 paginiComputer Networks MCQ QuestionsRez HabloÎncă nu există evaluări
- Homework 4 SolutionDocument9 paginiHomework 4 SolutionMohamed AlserÎncă nu există evaluări
- M1000 Pro ModemDocument4 paginiM1000 Pro ModemJuan Francisco Vera AbarcaÎncă nu există evaluări
- 04 TP NT1 MidtermsDocument2 pagini04 TP NT1 MidtermsFranco Danemark Benedicto0% (1)
- Call-Forward B2buaDocument4 paginiCall-Forward B2buaDenisa PriftiÎncă nu există evaluări
- M.C.I.T.P L1 Interview QuestionsDocument7 paginiM.C.I.T.P L1 Interview QuestionsShaik Ashwaq JavedÎncă nu există evaluări