Documente Academic
Documente Profesional
Documente Cultură
Cryptography or Cryptology (From: - Logia
Încărcat de
Demo DesignerTitlu original
Drepturi de autor
Formate disponibile
Partajați acest document
Partajați sau inserați document
Vi se pare util acest document?
Este necorespunzător acest conținut?
Raportați acest documentDrepturi de autor:
Formate disponibile
Cryptography or Cryptology (From: - Logia
Încărcat de
Demo DesignerDrepturi de autor:
Formate disponibile
Cryptography or cryptology (from Greek krypts, "hidden, secret";
and graphein, "writing", or - -logia, "study", respectively[1]) is the practice and study
of techniques for secure communication in the presence of third parties called adversaries.[2]More
generally, cryptography is about constructing and analyzing protocols that prevent third parties or
the public from reading private messages;[3] various aspects in information security such as
data confidentiality, data integrity, authentication, and non-repudiation[4] are central to modern
cryptography. Modern cryptography exists at the intersection of the disciplines
of mathematics, computer science, and electrical engineering. Applications of cryptography
include military communications, electronic commerce, ATM cards, and computer passwords.
Cryptography prior to the modern age was effectively synonymous with encryption, the
conversion of information from a readable state to apparent nonsense. The originator of an
encrypted message (Alice) shared the decoding technique needed to recover the original
information only with intended recipients (Bob), thereby precluding unwanted persons (Eve) from
doing the same. The cryptography literature often uses Alice ("A") for the sender, Bob ("B") for
the intended recipient, and Eve ("eavesdropper") for the adversary.[5] Since the development
of rotor cipher machines in World War I and the advent of computers in World War II, the
methods used to carry out cryptology have become increasingly complex and its application
more widespread.
Modern cryptography is heavily based on mathematical theory and computer science practice;
cryptographic algorithms are designed around computational hardness assumptions, making
such algorithms hard to break in practice by any adversary. It is theoretically possible to break
such a system, but it is infeasible to do so by any known practical means. These schemes are
therefore termed computationally secure; theoretical advances, e.g., improvements in integer
factorization algorithms, and faster computing technology require these solutions to be
continually adapted. There exist information-theoretically secure schemes that provably cannot
be broken even with unlimited computing poweran example is the one-time padbut these
schemes are more difficult to implement than the best theoretically breakable but computationally
secure mechanisms.
The growth of cryptographic technology has raised a number of legal issues in the information
age. Cryptography's potential for use as a tool for espionage and sedition has led many
governments to classify it as a weapon and to limit or even prohibit its use and export. [6] In some
jurisdictions where the use of cryptography is legal, laws permit investigators to compel the
disclosure of encryption keys for documents relevant to an investigation. [7][8] Cryptography also
plays a major role in digital rights management and copyright infringement of digital media.[9]
S-ar putea să vă placă și
- Cryptography or Cryptology (From: - LogiaDocument1 paginăCryptography or Cryptology (From: - LogiaShubhendu KushwahÎncă nu există evaluări
- Cryptography: Modern Computing and Data SecurityDocument5 paginiCryptography: Modern Computing and Data Security19 Kunal DasÎncă nu există evaluări
- A Review Paper On CryptographyDocument5 paginiA Review Paper On CryptographycikechukwujohnÎncă nu există evaluări
- " - ), Literally Means 'Covered Writing' (4), and Is The Authors Are With The University ofDocument9 pagini" - ), Literally Means 'Covered Writing' (4), and Is The Authors Are With The University ofSuriya NamachiÎncă nu există evaluări
- Cryptography, or Cryptology (From: - LogiaDocument1 paginăCryptography, or Cryptology (From: - LogiaAAAAÎncă nu există evaluări
- CryptographyDocument3 paginiCryptographyR x41x4aÎncă nu există evaluări
- Topic: Cryptology: History of CryptographyDocument24 paginiTopic: Cryptology: History of CryptographyAziz Ur RehmanÎncă nu există evaluări
- Cryptography ReportDocument6 paginiCryptography ReportSakthiSriÎncă nu există evaluări
- Cryptography or Cryptology (From: - LogiaDocument1 paginăCryptography or Cryptology (From: - Logiarosev15Încă nu există evaluări
- CRYPTOGRAPHICDocument2 paginiCRYPTOGRAPHICAsok KumarÎncă nu există evaluări
- 3630-Article Text-6635-1-10-20180104Document5 pagini3630-Article Text-6635-1-10-20180104Anonymous uGow9p7y8Încă nu există evaluări
- Paper 74-Prudently Secure Information Theoretic LSBDocument21 paginiPaper 74-Prudently Secure Information Theoretic LSBCaius Paul Landon BetkouÎncă nu există evaluări
- Cryptography Term PaperDocument4 paginiCryptography Term PaperAngelica AngelesÎncă nu există evaluări
- LESSON 6 - CryptographyDocument12 paginiLESSON 6 - CryptographyKIBEÎncă nu există evaluări
- CRYPTOGRAPHY: A Node To The Future 1Document7 paginiCRYPTOGRAPHY: A Node To The Future 1L E MooreÎncă nu există evaluări
- Cryptographic Algorithms and Current TrendsDocument13 paginiCryptographic Algorithms and Current TrendsvignanarajÎncă nu există evaluări
- Paper of CryptographyDocument3 paginiPaper of CryptographySuinÎncă nu există evaluări
- Cryptography: Presented byDocument11 paginiCryptography: Presented byapi-19799369Încă nu există evaluări
- 20MCA1527 - Cryptography A Mechanism For Network Security A Survey - Research ArticleDocument7 pagini20MCA1527 - Cryptography A Mechanism For Network Security A Survey - Research ArticleRonak ChawlaÎncă nu există evaluări
- Cryptography (Encryption & Decryption) SynopsisDocument5 paginiCryptography (Encryption & Decryption) SynopsishhÎncă nu există evaluări
- Index: 3.1 Private Key Algorithm 3.2 Public Key Algorithm 3.3 Hash FunctionsDocument11 paginiIndex: 3.1 Private Key Algorithm 3.2 Public Key Algorithm 3.3 Hash FunctionsYogesh YadavÎncă nu există evaluări
- Title - The Intriguing World of Cryptography - Unraveling The Secrets of Secure CommunicationDocument2 paginiTitle - The Intriguing World of Cryptography - Unraveling The Secrets of Secure Communicationhaseeb.hussainy14Încă nu există evaluări
- Chapter Four Security Techniques Origin of CryptographyDocument33 paginiChapter Four Security Techniques Origin of CryptographyGetnete degemuÎncă nu există evaluări
- Submitted By: A.Irfana Cse-First Year Deepthi Cse-First YearDocument14 paginiSubmitted By: A.Irfana Cse-First Year Deepthi Cse-First YearNiranjan ChandarrajÎncă nu există evaluări
- A Review Paper On Cryptography: June 2019Document7 paginiA Review Paper On Cryptography: June 2019Raynaldy Mahdi PutraÎncă nu există evaluări
- Assignment Title:: Proposed Cryptographic ProtocolsDocument13 paginiAssignment Title:: Proposed Cryptographic Protocolsco1ossusÎncă nu există evaluări
- En CryptDocument2 paginiEn CryptV Iv Ek ParekhÎncă nu există evaluări
- What Is Cryptography - Definition FromDocument2 paginiWhat Is Cryptography - Definition FromGirgio Moratti CullenÎncă nu există evaluări
- New Comparative Study Between DES, 3DES and AES Within Nine FactorsDocument6 paginiNew Comparative Study Between DES, 3DES and AES Within Nine FactorsKashish GuptaÎncă nu există evaluări
- Cryptographic Technique For Communication SystemDocument9 paginiCryptographic Technique For Communication SystemIJRASETPublicationsÎncă nu există evaluări
- Cryptography and Network SecurityDocument18 paginiCryptography and Network Securitykarishma vaidyaÎncă nu există evaluări
- DocumentDocument2 paginiDocumentKristi NureÎncă nu există evaluări
- EncryptationDocument4 paginiEncryptationjuanÎncă nu există evaluări
- Cryptography Prior To The Modern Age Was Effectively Synonymous WithDocument3 paginiCryptography Prior To The Modern Age Was Effectively Synonymous Withanmathew00Încă nu există evaluări
- An Overview of Modern CryptographyDocument7 paginiAn Overview of Modern CryptographyTI Journals PublishingÎncă nu există evaluări
- 8 SubmissionDocument5 pagini8 Submissionsharwari solapurÎncă nu există evaluări
- How To Get To Level 2 in A Tough Crowd To Learn Crowd ControlDocument1 paginăHow To Get To Level 2 in A Tough Crowd To Learn Crowd Controlpokin73091Încă nu există evaluări
- Multilevel Cryptography Technique Using Graceful CodesDocument5 paginiMultilevel Cryptography Technique Using Graceful CodesAnthony LiangÎncă nu există evaluări
- CryptographyDocument20 paginiCryptographyArfath PashaÎncă nu există evaluări
- Assignment - Criminal Uses of Cryptography and LawDocument25 paginiAssignment - Criminal Uses of Cryptography and LawrhythmofkrishnaÎncă nu există evaluări
- CryptographyDocument19 paginiCryptographySrilekha RajakumaranÎncă nu există evaluări
- Research PaperDocument5 paginiResearch Paperlomir76956Încă nu există evaluări
- ON Cryptography: BY: Deepak Krishna 08/ ME/08 Mechanical Fiem, KolkataDocument14 paginiON Cryptography: BY: Deepak Krishna 08/ ME/08 Mechanical Fiem, KolkataEmanuel MaričićÎncă nu există evaluări
- Overview of Cryptography: SSRN Electronic Journal January 2011Document10 paginiOverview of Cryptography: SSRN Electronic Journal January 2011EbubeÎncă nu există evaluări
- Introduction To CryptographyDocument31 paginiIntroduction To CryptographyzaikoryuÎncă nu există evaluări
- Cryptography ReportDocument16 paginiCryptography ReportGRACEÎncă nu există evaluări
- Analysis of Cryptography in Information TechnologyDocument6 paginiAnalysis of Cryptography in Information Technologypia potatoeÎncă nu există evaluări
- A Seminar ReportDocument39 paginiA Seminar ReportNutan BhorÎncă nu există evaluări
- A Seminar ReportDocument39 paginiA Seminar ReportDivyaswaroop Srivastav100% (1)
- CryptographyDocument6 paginiCryptographyManoj WankhedeÎncă nu există evaluări
- Chapter Seven Data Security and Integrity Under This Chapter We Will Discuss Fundamentals of Secure NetworksDocument23 paginiChapter Seven Data Security and Integrity Under This Chapter We Will Discuss Fundamentals of Secure NetworksGetnete degemuÎncă nu există evaluări
- Cryptography Full ReportDocument9 paginiCryptography Full ReportSushant SharmaÎncă nu există evaluări
- CSE Cryptography ReportDocument21 paginiCSE Cryptography ReportOtunuya Chukwudi Henry EngrÎncă nu există evaluări
- Final RSA DocumentationDocument125 paginiFinal RSA DocumentationKishore PinnintiÎncă nu există evaluări
- CryptographyDocument20 paginiCryptographySrilekha RajakumaranÎncă nu există evaluări
- Cryptography ResearchDocument7 paginiCryptography ResearchShikha MishraÎncă nu există evaluări
- CryptographyDocument1 paginăCryptographyVishal MadanÎncă nu există evaluări
- The Basics of Cryptography: Encryption and DecryptionDocument5 paginiThe Basics of Cryptography: Encryption and DecryptionAngelyn BlanquiscoÎncă nu există evaluări
- Cryptology for Beginners #1 Guide for Security, Encryption, Crypto, Algorithms and PythonDe la EverandCryptology for Beginners #1 Guide for Security, Encryption, Crypto, Algorithms and PythonÎncă nu există evaluări
- Pro Cryptography and Cryptanalysis: Creating Advanced Algorithms with C# and .NETDe la EverandPro Cryptography and Cryptanalysis: Creating Advanced Algorithms with C# and .NETÎncă nu există evaluări
- HelloDocument1 paginăHelloDemo DesignerÎncă nu există evaluări
- Abc 123Document4 paginiAbc 123Demo DesignerÎncă nu există evaluări
- Business Balance Sheet TemplateDocument4 paginiBusiness Balance Sheet TemplateDemo DesignerÎncă nu există evaluări
- SA FY15 Q4 Year Finstatement PDFDocument38 paginiSA FY15 Q4 Year Finstatement PDFDemo DesignerÎncă nu există evaluări
- Hello!, My Name Is Ajit Pal Singh. I Am A StudentDocument1 paginăHello!, My Name Is Ajit Pal Singh. I Am A StudentDemo DesignerÎncă nu există evaluări
- DemoDocument8 paginiDemoDemo DesignerÎncă nu există evaluări
- Write A Program To Study Various Shell Scripting Commands.: Practical - 5 AIMDocument1 paginăWrite A Program To Study Various Shell Scripting Commands.: Practical - 5 AIMDemo DesignerÎncă nu există evaluări
- List of State Code PDFDocument1 paginăList of State Code PDFDemo DesignerÎncă nu există evaluări
- Revised Schedule of Academic Calendar of UG PG Courses 2017-18Document2 paginiRevised Schedule of Academic Calendar of UG PG Courses 2017-18Demo DesignerÎncă nu există evaluări
- Page 3Document1 paginăPage 3Demo DesignerÎncă nu există evaluări
- TF 00002110Document1 paginăTF 00002110PratapareddyBogoluÎncă nu există evaluări
- Demo FileDocument1 paginăDemo FileDemo DesignerÎncă nu există evaluări
- Create An Instant Messaging App Using Google Cloud Messaging (GCM)Document5 paginiCreate An Instant Messaging App Using Google Cloud Messaging (GCM)Demo DesignerÎncă nu există evaluări
- Scribd: Hello - Docx Doesn't Appear To Substantial. Please Upload Another DocumentDocument3 paginiScribd: Hello - Docx Doesn't Appear To Substantial. Please Upload Another DocumentDemo DesignerÎncă nu există evaluări
- Demo File 3Document1 paginăDemo File 3Demo DesignerÎncă nu există evaluări
- Hello This My First Document For ScribdDocument1 paginăHello This My First Document For ScribdDemo DesignerÎncă nu există evaluări
- WordDocument1 paginăWordDemo DesignerÎncă nu există evaluări
- Wifi Seminar ReportDocument26 paginiWifi Seminar ReportDemo DesignerÎncă nu există evaluări
- Hello This My First DocumentDocument1 paginăHello This My First DocumentDemo DesignerÎncă nu există evaluări
- Document OdtDocument1 paginăDocument OdtDemo DesignerÎncă nu există evaluări
- Demo File 1Document1 paginăDemo File 1Demo DesignerÎncă nu există evaluări
- Demo FileDocument1 paginăDemo FileDemo DesignerÎncă nu există evaluări
- Demo File 2Document1 paginăDemo File 2Demo DesignerÎncă nu există evaluări
- Cruz, Dave Garcia PSSGDocument2 paginiCruz, Dave Garcia PSSGAnafer BautistaÎncă nu există evaluări
- Atp 3-55-12Document62 paginiAtp 3-55-12condorblack2001Încă nu există evaluări
- Romeo SpyDocument247 paginiRomeo SpyOdiseo100% (1)
- Effect of Cyber Crime in Legal PracticeDocument2 paginiEffect of Cyber Crime in Legal PracticeTwain JonesÎncă nu există evaluări
- Edward SnowdenDocument45 paginiEdward SnowdenTanmmay100% (4)
- Exploring Criminal Justice 3rd Edition Ebook PDFDocument61 paginiExploring Criminal Justice 3rd Edition Ebook PDFdorothy.carr400100% (44)
- World CheckDocument13 paginiWorld CheckAlex koÎncă nu există evaluări
- Afpam36 2241Document500 paginiAfpam36 2241ericjamezÎncă nu există evaluări
- Combat Commit Cut Petty Prevention Rate Violent WaveDocument2 paginiCombat Commit Cut Petty Prevention Rate Violent WaveÁgnes JassóÎncă nu există evaluări
- Advanced Kriegspiel Theory by Mike SheflerDocument7 paginiAdvanced Kriegspiel Theory by Mike Sheflerratao123Încă nu există evaluări
- From Kutch To Taskent - Speech - SOAS 26 11 13Document9 paginiFrom Kutch To Taskent - Speech - SOAS 26 11 13Saeed AbdulRahim100% (1)
- Springfield Police Sergeant PromotionsDocument3 paginiSpringfield Police Sergeant PromotionsPatrick JohnsonÎncă nu există evaluări
- Research and Analysis Wing (R&AW) : Anusa Dhān Aur Viśle A Vi GDocument20 paginiResearch and Analysis Wing (R&AW) : Anusa Dhān Aur Viśle A Vi GAryaman GuptaÎncă nu există evaluări
- Police Intelligence and Secret ServiceDocument17 paginiPolice Intelligence and Secret ServiceJoshua D None-NoneÎncă nu există evaluări
- Cybercrime: Fraud and Financial CrimesDocument4 paginiCybercrime: Fraud and Financial CrimeshardikÎncă nu există evaluări
- Field Manual 100-5 - OperationsDocument164 paginiField Manual 100-5 - OperationsDave Whitefeather100% (1)
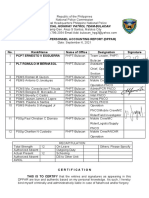
- Provincial Highway Patrol Team-Bulacan: Daily PNP Personnel Accounting Report (Dppar)Document2 paginiProvincial Highway Patrol Team-Bulacan: Daily PNP Personnel Accounting Report (Dppar)Andrew SalamatÎncă nu există evaluări
- Mugisha - The Way Forward in SomaliaDocument8 paginiMugisha - The Way Forward in SomaliaMatthew MachowskiÎncă nu există evaluări
- Rachit PriyadarshiDocument39 paginiRachit PriyadarshiRachitPriyadarshiÎncă nu există evaluări
- Lifestyle Polygraph Security Clearance Sexual MisconductDocument21 paginiLifestyle Polygraph Security Clearance Sexual Misconductapi-3931606Încă nu există evaluări
- Law EnforcementDocument4 paginiLaw Enforcementapi-76789393Încă nu există evaluări
- WarfareDocument102 paginiWarfareHammad Rao100% (2)
- BENGHAZI - Transcript of One The Record Special Report Operation Zero FootprintDocument8 paginiBENGHAZI - Transcript of One The Record Special Report Operation Zero FootprintBigMamaTEAÎncă nu există evaluări
- ESentire Managed Detection and ResponseDocument2 paginiESentire Managed Detection and ResponseasdÎncă nu există evaluări
- OSP Cybersecurity AuditDocument22 paginiOSP Cybersecurity AuditMark FurmanÎncă nu există evaluări
- United States Modern Penology Approach Correction Prison System and Rehabilitation ProgramsDocument51 paginiUnited States Modern Penology Approach Correction Prison System and Rehabilitation ProgramsLesson Plan ni Teacher GÎncă nu există evaluări
- Lea4 M3Document4 paginiLea4 M3Jhav BaguioÎncă nu există evaluări
- Atp 8 (D) Vol I VRS.1 Doctrine For Amphibious PDFDocument190 paginiAtp 8 (D) Vol I VRS.1 Doctrine For Amphibious PDFTelmo Reis73% (11)
- JW V DOJ HRC Emails Production 32 02046Document277 paginiJW V DOJ HRC Emails Production 32 02046Ronald RonÎncă nu există evaluări
- Basics of International Humanitarian LawDocument3 paginiBasics of International Humanitarian Lawbjwoo6Încă nu există evaluări