Documente Academic
Documente Profesional
Documente Cultură
ESM Siemt
Încărcat de
kkbkDescriere originală:
Titlu original
Drepturi de autor
Formate disponibile
Partajați acest document
Partajați sau inserați document
Vi se pare util acest document?
Este necorespunzător acest conținut?
Raportați acest documentDrepturi de autor:
Formate disponibile
ESM Siemt
Încărcat de
kkbkDrepturi de autor:
Formate disponibile
Certification Guide
Intel Security Certified
Product Specialist
Security Information Event Management (SIEM)
Why Get Intel Security Certified?
As technology and security threats continue to evolve, organizations are looking for
employees with the most up-to-date certifications on the most current techniques and Highlights
technologies. In a well cited IDC White Paper, over 70% of IT Managers surveyed felt This guide has been
developed as a resource for
certifications are valuable for their team and were worth the time and money to maintain.
your preparation to take
Becoming Intel Security certified distinguishes you from other security professionals and the Intel Security Certified
helps validate that you have mastery of the critical skills covered by the certification exams. Product Specialist SIEM
Earning a certification also your commitment to continued learning and professional growth. Exam (MA0-104). The
following information is
About Intel Security Certification Program provided:
About the Intel Security
Currently, Intel offers two industry-recognized certifications as part of our Intel Security
Certification Program
Certification Program: Intel Security Certified Product Specialist and Intel Security Certified Exam details
Security Professional. Suggested resources for exam
The Intel Security Certified Product Specialist certifications are designed for candidates who preparation
administer a specific McAfee product or suite of products, and have one to three years of Knowledge domain topics
Sample exam items
experience with that product or product suite. This certification level allows candidates to
demonstrate knowledge in the following key product areas:
Installation
Configuration
Management
Basic architecture and troubleshooting
The Intel Security Certified Security Professional certifications are designed for security
practitioners, penetration testers, auditors, consultants, administrators with one to three
years of experience. This certification level allows candidates to demonstrate knowledge in
the following high-level assessment areas:
Profiling and inventorying
Vulnerability identification
Vulnerability exploitation
Expanding influence
About This Guide
This guide is intended to help prepare you for the Intel Security Certified Security Professional
Security Information Event Management (SIEM) exam. For more information about other
certification exams or about the Intel Security Certification program go to www.mcafee.com and
select For Enterprise, Services, and then Education Services.
Certification Guide
Intel Security Certified Product Specialist Security Information Event Management (SIEM)
This exam validates that the successful candidate has the knowledge and skills necessary to successfully install, configure,
and manage a McAfee SIEM solution. It is intended for security professionals with one to three years of experience using
McAfee SIEM products and associated technologies.
Exam Details
Associated exam: MA0-104
Associated Training: McAfee SIEM Administration 101 (4 days), McAfee SIEM Administration 201 (4 days)
Number of Questions: 70
Exam Duration: 140 Minutes
Passing Score: 62%
Exam Price: $150 USD (Exam prices are subject to change. Please visit the following link for exact pricing:
http://www.pearsonvue.com/intel/index.asp
Exam Preparation
Suggested preparation for this exam is:
4 Days McAfee SIEM Administration 101 training (https://mcafee.netexam.com/catalog.html)
4 Days McAfee SIEM Administration 201 course (www. mcafee.com/us/services/product-training/index.aspx)
Minimum of one year using McAfee SIEM
Knowledge domains (see later in the guide)
Sample questions (see later in the guide)
Certificate Registration
Intel Security has partnered with Pearson VUE, the global leader in computer-based testing, to administer our certification
program. Pearson VUE makes the certification process easy from start to finish. With over 5,000 global locations, you can
conveniently test your knowledge and become Intel Security Certified.
To register for an exam, go to: http://www.pearsonvue.com/intel/index.asp
Exam Duration
The Intel Security Certification Program has built in time to include the following actions during an exam challenge at each
testing facility:
Time to answer exam questions
Time to review instructions and provide comments after completion
Intel Security reserves the right to change the exam content and time requirements at any time. The most accurate means of
obtaining this information is to contact the exam delivery provider on the day of your exam challenge. A notification appears
on your screen before the exam begins that shows the maximum time allowed for answering the questions in that exam.
Certification Transcripts
Individuals who have passed an Intel Security certification exam are granted access to the Intel Security Certification Program
Candidate site. On the site, you will find:
Your official Intel Security Certification Program transcript and access to the transcript sharing tool
The ability to download custom certification logos
Additional information and offers for Intel-certified individuals
Your contact preferences and profile
News and promotions
Certification Guide
McAfee SIEM Administration (4 days)
Although formal training is not required prior to the exam, the McAfee SIEM Administration 101 (4 days) and/or the McAfee SIEM
Administration 201 course is recommended.
The McAfee SIEM Administration 101 course provides in-depth training on how to set up and administer McAfee Security
Information and Event Management (SIEM) solution. Using both lectures and practical lab exercises, the course shows you
how to effectively implement the SIEM solution in a complex enterprise environment.
The McAfee SIEM Administration 201 course uses guided demonstrations and independent lab environments to configure
and use McAfee SIEM appliances to resolve security challenges typically found in an enterprise environment.
To register for either or both of these courses, go to: https://mcafee.netexam.com/catalog.html
Practical (Hands-on) Experience
A minimum of one year of experience using McAfee SIEM and associated technologies. Recommended hands-on activities
include but are not limited to:
Solution Planning
Installation/upgrade
Configuration
Management
Troubleshooting
Technical ServicePortal
The Technical ServicePortal provides a single point of access to valuable tools and resources, such as:
Documentation
Security bulletins
Technical articles
Product downloads
Tools
To access the ServicePortal, go to: https://support.mcafee.com
Expert Center Community
The Expert Center is a community for McAfee product users. Here you will find valuable information for your McAfee products,
such as
Instructional videos and whitepapers
Discussion feeds for experts and other users
Guidelines to establish baselines, and to harden your IT environment
Ways to expedite monitoring, response, and remediation processes
To access the Expert Center, go to: https://community.mcafee.com/community/business/expertcenter
Certification Guide
Exam Knowledge Domains System testing procedures Architecture and
Proactive Protection Scan Integration Best Practices
Networking policy Level of security required
Networking technology Network password Security monitoring
theory, principles and procedures
practices Problem isolation tools/
Company security policies practices
Data networking standards
Device usage policies
and Security Foundation
Change control procedures
protocols Computer viruses, spyware,
Product specific maintenance
LAN and WAN technologies and malware, spam
procedures
Network administration Network threat prevention
Incident response
Network and routing technologies
procedures
protocols Firewall technologies and
Role specific escalation
Baseline conditions intrusion prevention
procedures
Perimeter security Heuristic-based protection
Corporate security controls
Internal network security Authentication
Corporate security strategy
Basic infrastructure Vulnerabilities and
Device access control
remediation techniques
Sniffing/network monitoring
Architect and Malware incidents
TCP/IP and NAT/PAT Integration/Best Practices Internal and external threats
Systems Level of security required and attacks
Client/server technology Problem isolation/tools Security protocols
Group policy overview and required Cryptography
security templates Industry security standard Network security policies and
Web permissions and Security Foundation access control
authorization Common threats and
Firewall
Redundancy/fault tolerance/ vulnerabilities
high availability Computer viruses, spyware,
and malware, spam Operation and
Drive encryption
Network threat prevention Administration
System administration
technologies Password management
Virtual environments
Spyware protection Network and support
Processors (CPUs) technologies management tools and
Baseline conditions Firewall technologies and procedures
System access and intrusion prevention Patch management
navigation Heuristic-based protection Security alerts, front-line
Multi-server environments Authentication analysis and escalation
Operating systems Vulnerabilities and Intrusion detection systems
Applications remediation techniques Monitoring tools
Malware incidents Problem determination
Databases
Internal threats and attacks Incident and issue
Redundancy
External threats and attacks categorization
Web protocols
Security protocols Basic product functions
Baseline conditions
Cryptography Product policy configuration
Policies and Procedures Network security policies Product report generation
Permissions, delegation, and Network access control Version controls
auditing
Common threats and Detailed product functions
Policies governing user vulnerabilities Protected materials
access
Role permissions
Certification Guide
Sample Exam Items
The following exam items are provided for review. These items are similar in style and content to those referenced in the Intel
Security Certified Product Specialist SIEM exam. The answers are provided after the questions.
1. Which feature is accessed via the Receiver Properties?
A Alarms
B Data Source Profiles
C Watchlists
D Asset Management
2. Default Event Aggregation occurs on which of the following fields?
A Signature ID
B Username
C Destination Port
D Source Port
3. Which of the following components make up the functional SIEM stack?
A Data Processing
B Correlation
C Mitigation
D Policy Updating
4. Which of the following statements are NOT true concerning Global Threat Intelligence (GTI) Watchlists?
A They are comprised of third-party threat advisories.
B They are comprised of Watchlists containing suspicious and malicious IP addresses
C They are used as a scoring source
D They are licensed from McAfee
5. ELM storage pools require what percentage of allocated space for mirroring overhead?
A Firewall Rule
B Firewall Group
C Firewall Options
D Firewall Catalogs
6. Specific event and network flow statistics were gathered from a network over a specific 12 hour period.
Firewall produced 450,000 total events
Unix Servers produced 62,000 total events
Web Applications produced 1,200,500 total events
Routers produced 150,000,000 total flows
With these statistics in mind, what is the total EPS for the network?
A 3,511
B 3,472
C 3,500
D 3,510
7. Which of the following time zones is the default setting for the McAfee Enterprise Security Manager (ESM) system clock?
A International Date Line West
B Eastern Standard Time
C Greenwich Mean Time
D Geo-Location
Certification Guide
8. While investigating malware, an analyst can narrow the search quickly by using which of the following watchlists in the
McAfee SIEM?
A Botnet Control Channel
B Malware Detections
C GTI Suspicious and Malicious
D Passive DNS Malware Domain
9. Which of the following statements about Child Data Sources is NOT true?
A They will have VIPS, policy and Agent rights
B They will be displayed on the Receiver Properties > Data Sources table
C They will appear on the System Navigation tree
D They do not count towards the total number of data sources
10. Which of the following appliances contains an event database?
A ESM
B ADM
C ELM
D DEM
Answer Key
1. B
2. A
3. B
4. A
5. C
6. A
7. C
8. C
9. D
10. A
Intel Security
2821 Mission College Boulevard
Santa Clara, CA 95054
888 847 8766
www.intelsecurity.com
S-ar putea să vă placă și
- 2021 Professional CertificationsDocument4 pagini2021 Professional CertificationsjainithishÎncă nu există evaluări
- Cisco Challenges To Check Point (IAS 2) by Kyla Claire Liberato and Michelle Alfaro MacahisDocument3 paginiCisco Challenges To Check Point (IAS 2) by Kyla Claire Liberato and Michelle Alfaro MacahisMichelle Alfaro MacahisÎncă nu există evaluări
- CCNP and CCIE Security Core SCOR 350-701 Official Cert Guide - Omar SantosDocument9 paginiCCNP and CCIE Security Core SCOR 350-701 Official Cert Guide - Omar Santostemirocu50% (4)
- CompTIA Security Cert Prep PlanDocument6 paginiCompTIA Security Cert Prep Planyoseph mezemerÎncă nu există evaluări
- Sam Security CertificationsDocument12 paginiSam Security CertificationspkjmesraÎncă nu există evaluări
- Endpoint Security Essentials Study Guide-PandaDocument117 paginiEndpoint Security Essentials Study Guide-PandaRahul BhosaleÎncă nu există evaluări
- CompTIA Security+ 601 Certification - UpdatedDocument7 paginiCompTIA Security+ 601 Certification - UpdatedKishanÎncă nu există evaluări
- Higher Certificate in Information Systems (Cyber Security) 2Document2 paginiHigher Certificate in Information Systems (Cyber Security) 2obarodreamsbigÎncă nu există evaluări
- Comptia Security Plus Bootcamp IntlDocument12 paginiComptia Security Plus Bootcamp IntlHammad Bhatti100% (1)
- Cloud Tech Associate Advanced SecurityDocument163 paginiCloud Tech Associate Advanced SecurityJuntos PodCastÎncă nu există evaluări
- Cyber Security Expert - Masters - SimplilearnDocument23 paginiCyber Security Expert - Masters - SimplilearnKopparapu MukeshÎncă nu există evaluări
- Cyber Expert - Masters V3Document23 paginiCyber Expert - Masters V3John JosephÎncă nu există evaluări
- Microsoft SecurityDocument201 paginiMicrosoft SecurityShishir YadavÎncă nu există evaluări
- Fortinet Recommended Security Best Practices v1.2Document23 paginiFortinet Recommended Security Best Practices v1.2arcanerkÎncă nu există evaluări
- Microsoft Security Best PracticesDocument265 paginiMicrosoft Security Best PracticesahmedÎncă nu există evaluări
- Cisco Software Support For Security: January 2021Document8 paginiCisco Software Support For Security: January 2021Foxy EdenÎncă nu există evaluări
- CSCU FlyerDocument1 paginăCSCU FlyerKiran KumarÎncă nu există evaluări
- 2.2.1 - SIS - Design, Analysis and Justification (EC50) - ISADocument2 pagini2.2.1 - SIS - Design, Analysis and Justification (EC50) - ISARoberto CarrascoÎncă nu există evaluări
- Achilles Practices Certification From Ge Digital DatasheetDocument3 paginiAchilles Practices Certification From Ge Digital DatasheetFacundo ArlistanÎncă nu există evaluări
- CompTIA CASP+ CAS-004 Exam Guide: A-Z of Advanced Cybersecurity Concepts, Mock Exams, Real-world Scenarios with Expert Tips (English Edition)De la EverandCompTIA CASP+ CAS-004 Exam Guide: A-Z of Advanced Cybersecurity Concepts, Mock Exams, Real-world Scenarios with Expert Tips (English Edition)Încă nu există evaluări
- Understanding CertificationsDocument4 paginiUnderstanding CertificationsShehzad HaleemÎncă nu există evaluări
- CompTIA Security+ SY0-501 - Marks4Sure - MansoorDocument4 paginiCompTIA Security+ SY0-501 - Marks4Sure - MansoorMansoor AhmedÎncă nu există evaluări
- NSE2 Course DescriptionDocument2 paginiNSE2 Course DescriptionTASONA DOKO JOCELYN TANGUYÎncă nu există evaluări
- Cyber Security: Master's ProgramDocument25 paginiCyber Security: Master's ProgramKishore.v Kishore.VÎncă nu există evaluări
- Simplilearn Cyber Security Expert MastersDocument23 paginiSimplilearn Cyber Security Expert MastersNadeem MsÎncă nu există evaluări
- Infrastructure TracksDocument8 paginiInfrastructure Tracksabdlwhapahmed12Încă nu există evaluări
- Ccie Security at A Glance PDFDocument2 paginiCcie Security at A Glance PDFjaaniÎncă nu există evaluări
- New Microsoft Word DocumentDocument2 paginiNew Microsoft Word Documentcharles mainaÎncă nu există evaluări
- Comptia It Security ToolkitDocument14 paginiComptia It Security ToolkitHash TechÎncă nu există evaluări
- Functional SafetyDocument1 paginăFunctional SafetyravisankarÎncă nu există evaluări
- BrochureDocument6 paginiBrochureSamuel Bamgboye kobomojeÎncă nu există evaluări
- Administrator Study GuideDocument20 paginiAdministrator Study GuidesachinkoenigÎncă nu există evaluări
- Information Sheet - Certification Programs in The Information Security FieldDocument9 paginiInformation Sheet - Certification Programs in The Information Security FieldWala LangÎncă nu există evaluări
- BTEC Assignment Brief: (For NQF Only)Document3 paginiBTEC Assignment Brief: (For NQF Only)JwsÎncă nu există evaluări
- Training or Certification???Document26 paginiTraining or Certification???Ahmed Ali KhanÎncă nu există evaluări
- LABSIM For Security Pro Fact SheetDocument3 paginiLABSIM For Security Pro Fact Sheetirshaad010% (1)
- Security, Privacy and Compliance: Training 2020Document46 paginiSecurity, Privacy and Compliance: Training 2020Ingrid CardenasÎncă nu există evaluări
- CISSP SyallabusDocument10 paginiCISSP SyallabusAbi BobbyÎncă nu există evaluări
- Functional Safety Certified Professional - Level 1 in Accordance With IEC 61508 IEC 61511 UnaccreditedDocument1 paginăFunctional Safety Certified Professional - Level 1 in Accordance With IEC 61508 IEC 61511 UnaccreditedSyed AhmedÎncă nu există evaluări
- Brochure ECSADocument4 paginiBrochure ECSAjuniÎncă nu există evaluări
- Ec Council Certified Security Analyst Ecsa v8Document5 paginiEc Council Certified Security Analyst Ecsa v8fazli3036Încă nu există evaluări
- Bug Bounty CourseDocument10 paginiBug Bounty Coursess1391161Încă nu există evaluări
- Analyst IT Security Sample ResumeDocument3 paginiAnalyst IT Security Sample ResumeSoumya RoutÎncă nu există evaluări
- Study Guide: Check Point Security AdministrationDocument20 paginiStudy Guide: Check Point Security Administrationchakki100% (1)
- EC-Council Certified Security Analyst (ECSA)Document21 paginiEC-Council Certified Security Analyst (ECSA)touqeerÎncă nu există evaluări
- Technical Introduction To Cybersecurity 1.0 Course DescriptionDocument2 paginiTechnical Introduction To Cybersecurity 1.0 Course DescriptionluciaanopjÎncă nu există evaluări
- ISP-Sample Exam En-V1.0Document10 paginiISP-Sample Exam En-V1.0Hailu TegenawÎncă nu există evaluări
- Trainingfacts: Fs 132 - Functional Safety Engineer (Tüv Rheinland)Document1 paginăTrainingfacts: Fs 132 - Functional Safety Engineer (Tüv Rheinland)faisal84inÎncă nu există evaluări
- CCNSP V3.0el Module 1Document33 paginiCCNSP V3.0el Module 1erinb10102Încă nu există evaluări
- TMAO-Trend Micro Apex OneDocument6 paginiTMAO-Trend Micro Apex OneRonaldo SadangÎncă nu există evaluări
- Comptia-Security-Sy0-401 Exam Objectives PDFDocument19 paginiComptia-Security-Sy0-401 Exam Objectives PDFergkÎncă nu există evaluări
- Security Program and PoliciesDocument22 paginiSecurity Program and PoliciesdangermanÎncă nu există evaluări
- Sec OView DSheetDocument3 paginiSec OView DSheetRoger JeríÎncă nu există evaluări
- 2.2.2 - SIS - Design, Analysis, and Justification (EC50E - Online Version) - ISADocument3 pagini2.2.2 - SIS - Design, Analysis, and Justification (EC50E - Online Version) - ISARoberto Carrasco0% (1)
- Secure Configuration StandardDocument3 paginiSecure Configuration StandardMagda FakhryÎncă nu există evaluări
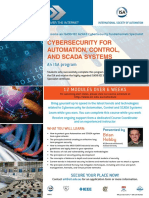
- Cybersecurity For Automation, Control, and Scada Systems: An Isa ProgramDocument3 paginiCybersecurity For Automation, Control, and Scada Systems: An Isa ProgrambariÎncă nu există evaluări
- Cyber Security and Threat ModelingDocument6 paginiCyber Security and Threat ModelingGirish AralikattiÎncă nu există evaluări
- Ccie Security at A GlanceDocument2 paginiCcie Security at A GlanceAbdul Rahaman GaffarÎncă nu există evaluări
- CISABrochureDocument5 paginiCISABrochuresiddharth.dubeyÎncă nu există evaluări
- SSL VPN : Understanding, evaluating and planning secure, web-based remote accessDe la EverandSSL VPN : Understanding, evaluating and planning secure, web-based remote accessÎncă nu există evaluări
- Xvision AHD DVR Manual V1 PDFDocument58 paginiXvision AHD DVR Manual V1 PDFAndy Wisnu WardanaÎncă nu există evaluări
- E BusinessDocument196 paginiE BusinessNikola JovovicÎncă nu există evaluări
- Ccms Administrators GuideDocument584 paginiCcms Administrators GuideMohammed MuzafferuddinÎncă nu există evaluări
- Crsimulator: A Discrete Simulation Model For Cognitive Radio Ad Hoc Networks in Omnet ++Document8 paginiCrsimulator: A Discrete Simulation Model For Cognitive Radio Ad Hoc Networks in Omnet ++VijayKumar LokanadamÎncă nu există evaluări
- Solidworks Workgroup PDM InstallationDocument7 paginiSolidworks Workgroup PDM InstallationmecanicajcÎncă nu există evaluări
- Leverage Iam and Idp To Provide Zero Trust Access To Corporate Applications enDocument6 paginiLeverage Iam and Idp To Provide Zero Trust Access To Corporate Applications enMighty TextÎncă nu există evaluări
- Ccna IndustrialDocument36 paginiCcna IndustrialSuperhypoÎncă nu există evaluări
- Dev - Is There A Net Energy Saving by The Use of Task Offloading in Mobile Devices?Document10 paginiDev - Is There A Net Energy Saving by The Use of Task Offloading in Mobile Devices?ISSSTNetworkÎncă nu există evaluări
- FWSM 4.1 - Config GuideDocument742 paginiFWSM 4.1 - Config GuideAerel BornÎncă nu există evaluări
- Passive Optical LAN-State of The MarketDocument30 paginiPassive Optical LAN-State of The MarketGustavo MoriceÎncă nu există evaluări
- RN-131 Eval GuideDocument46 paginiRN-131 Eval Guidemorcov19Încă nu există evaluări
- EN FANOX MANUAL SILG FeederGenerator ProtectionRelays R107Document204 paginiEN FANOX MANUAL SILG FeederGenerator ProtectionRelays R107Zhivko TerzievÎncă nu există evaluări
- 300-208 SISAS v17 Nov 2018 PDFDocument179 pagini300-208 SISAS v17 Nov 2018 PDFJohann Crisostomo ChoqueÎncă nu există evaluări
- Our SCADA BSD Using ZigbeeDocument24 paginiOur SCADA BSD Using ZigbeePankaj SarodeÎncă nu există evaluări
- ZXWM M920 Product DescriptionDocument138 paginiZXWM M920 Product Descriptionxiway100% (1)
- Unit 15 Transport Network DesignDocument47 paginiUnit 15 Transport Network Designronica100% (1)
- Manal Lantastic DOSDocument66 paginiManal Lantastic DOSfzatt100% (1)
- ACE3600 ManualDocument164 paginiACE3600 ManualAlexander Marcos TeixeiraÎncă nu există evaluări
- Data Center OverviewDocument8 paginiData Center OverviewMTU650100% (2)
- Sungrow Data Logger 1000 - 1000B Usert ManualDocument120 paginiSungrow Data Logger 1000 - 1000B Usert ManualJoão TeixeiraÎncă nu există evaluări
- 11 Frame RelayDocument6 pagini11 Frame RelayChis LebroÎncă nu există evaluări
- M Tech Syllabus Without LabsDocument53 paginiM Tech Syllabus Without LabsRajesh KannaÎncă nu există evaluări
- Exampdf: Higher Quality, Better Service!Document8 paginiExampdf: Higher Quality, Better Service!Marcio KatanÎncă nu există evaluări
- EIS Installation Checklist For The ORACLE® Database Appliance (ODA) X8-2S & X8-2MDocument47 paginiEIS Installation Checklist For The ORACLE® Database Appliance (ODA) X8-2S & X8-2MHieu Tran100% (2)
- X300 Network Export HostDocument18 paginiX300 Network Export Hosthoan leÎncă nu există evaluări
- Huawei CX912 Switch Module V100R001C10 White Paper 04Document38 paginiHuawei CX912 Switch Module V100R001C10 White Paper 04atluis82Încă nu există evaluări
- Optical Network Security Technical Analysis of Fiber Tapping MecDocument6 paginiOptical Network Security Technical Analysis of Fiber Tapping MecSteven MuñozÎncă nu există evaluări
- 9.1 Cyber LawDocument178 pagini9.1 Cyber LawVikasÎncă nu există evaluări
- Xenta 511Document86 paginiXenta 511Lucky Karunia Setyawan PratamaÎncă nu există evaluări
- Cryptography and Security Services - Mechanisms and ApplicationsDocument489 paginiCryptography and Security Services - Mechanisms and ApplicationsAlexandru100% (3)