Documente Academic
Documente Profesional
Documente Cultură
Trend Report SD WAN Trends 161110
Încărcat de
Pichai Ng-arnpairojhDrepturi de autor
Formate disponibile
Partajați acest document
Partajați sau inserați document
Vi se pare util acest document?
Este necorespunzător acest conținut?
Raportați acest documentDrepturi de autor:
Formate disponibile
Trend Report SD WAN Trends 161110
Încărcat de
Pichai Ng-arnpairojhDrepturi de autor:
Formate disponibile
Innovation Research Team
Trend Report
11/10/2016
SD-WAN Trends
Reshaping the WAN, the Remote Office,
WAN Management and WAN Security
Disclaimer This document has been prepared solely for Trace3's internal research purposes without any
commitment or responsibility on our part. Trace3 accepts no liability for any direct or consequential loss arising
from the transmission of this information to third parties. This report is current at the date of writing only and
Trace3 will not be responsible for informing of any future changes in circumstances which may affect the accuracy
of the information contained in this report. Trace3 does not offer or hold itself out as offering any advice relating to
investment, future performance or market acceptance.
2016 Trace3, Inc. All Rights Reserved
SD-WAN Trends
Reshaping the WAN, the Remote Office, WAN Management and WAN
Security
Executive Summary
As the SD-WAN market continues to gain momentum, so do questions on how best to select, design and deploy a
solution. A barrage of new features is being introduced that improve network traffic patterns across any medium, while
decreasing the time and labor needed to deploy, manage and secure the enterprise WAN. These developments have
widespread implications not only on IT operations, but are also reshaping the larger business landscape in general.
Report Scope
This trend report looks at how today's solutions are reshaping traditional WANs and was conducted from the customer's
point of view, gathering feedback from actual users, field engineers, published material and direct product
demonstrations. It analyzes each solution's ability to deliver the 26 use cases found to be most critical to customer
purchasing decisions [8]. These use cases can be categorized into four groups based upon how the solution reshapes:
The Remote/Branch Office
WAN Management
WAN Security
The WAN Itself
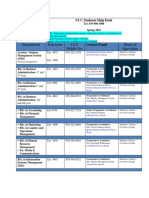
This study selected six of the leading SD-WAN solutions on the market today and the accompanying comparison matrix
presents each product's capabilities to support these key use cases. This report also makes predictions of future trending
and recommendations based on these predictions. This report does not delve into remote office onsite networking issues
such as ROBO wireless solutions.
A special note on Cisco's WAN solutions: No discussion on SD-WAN would be complete without a section on the WAN
market leader, Cisco. Their IWAN suite is a transport-independent design, intelligent path control, application
optimization, and secure encrypted communications between branch locations [7]. IWAN provides a highly configurable
series of networking components (e.g. DMVPN, LAN/WAN/DMVPN routing schemes, PFR traffic classifications and
policies, Frontend VRF and WAAS) from which to build complex network topologies requiring substantial manual
customization. They also offer APIC-EM for lighter weight implementations. As such, IWAN and its components fall
outside the primary evaluation feature set and will not be explored within the scope of this report. Cisco also recently
introduced Meraki MX for a more turnkey solution, but due to its newness to the market it is not covered in this report. For
organizations looking to implement bespoke WAN configurations, it is recommended that the Cisco suite be considered.
Did You Know...
SD-WAN is expected to grow at a CAGR of 90% through 2020, with global annual revenues reaching $6 billion. [1]
By the end of 2019, 30% of enterprises will use SD-WAN products in all their branches, up from <1% today. [2]
SD-WAN is on 90% of companies' road maps. [3]
Redundant telecommunications links connecting remote sites date back to the 1970's, with X.25 links used for remote
mainframe terminal access.
The term SD-WAN started showing up in networking publications as early as 2014. [4]
2016 Trace3, Inc. All Rights Reserved 2
SD-WAN Trends
Reshaping the WAN, the Remote Office, WAN Management and WAN
Security
Trends
Overview - The SD-WAN Landscape
As today's enterprises increase their adoption of cloud
applications, growing mobility and wider distribution of
talent and assets, the traditional model for Wide Area
Networking (WAN) becomes steadily more costly and
exponentially more complex. SD-WAN solutions have
emerged to reduce both WAN costs and complexity,
allowing the business to be more agile, secure and easier
to manage by introducing table stake features such as:
Offering a lightweight replacement for WAN Routers
Supporting multiple connection types (e.g., MPLS,
Broadband, LTE)
Providing secure VPNs
Some of today's SD-WAN solutions also provide advanced "nice-to-have" features such as:
Remote office/branch office (ROBO) device reduction or elimination
Service chaining or service insertion (e.g., integration with Zscaler)
Cost-based/quality-based/performance-based connection selection
Traffic steering
Typically, these features are provided by an appliance installed at each remote location that is managed and configured
by a secure centralized cloud-based management console that sets access, routing and configuration policies for the
entire enterprise WAN across all media types. For this study, six leading SD-WAN products were selected based on
feature set and market presence; CloudGenix, Riverbed SteelConnect, Talari, Velocloud, Versa and Viptela. Of course,
there are many other companies including 128 Technology, Aryaka, Bigleaf, Cato Networks, Citrix, Cradelpoint, Ecessa,
Elfig, Fatpipe, Glue Networks, Mushroom Networks, Nuage Networks, Silver Peak and Sonus Networks who offer
solutions in the SD-WAN market and adjacent, but related, WAN spaces such as WAN security, WAN Optimization and
Hybrid WAN. However, due to the constraints of this study, are not covered here.
Reshaping the Remote Office
Branch office network solutions are increasingly complex
and inflexible, as well as costly to deploy and manage. In
addition, it is equally complex and difficult to obtain
visibility into application performance across the hybrid
WAN and to ensure applications receive appropriate
prioritization and are forwarded over an appropriate WAN
path.
One of the complexities involved with installation of
remote or branch offices connectivity is the requirement
for a bevy of remote networking devices. This typically
requires an IT engineer to physically travel to the remote
site to install and configure all the devices. Many SD-WAN solutions seek to solve this problem with plug and play
appliances that can be easily connected at the remote site by local untrained staff, after which the device automatically
configures itself; a practice commonly dubbed Zero Touch Install.
Traditionally networked remote offices typically include a plethora of network devices such as firewalls, routers and
switches, each of which requires periodic configuration, maintenance and tech refreshing. Many of today's SD-WAN
solutions pack a stack of functionality into their appliances, allowing for the removal of many remote network devices and
2016 Trace3, Inc. All Rights Reserved 3
SD-WAN Trends
Reshaping the WAN, the Remote Office, WAN Management and WAN
Security
the avoidance of periodically putting an engineer on a plane. Although many SD-WAN solutions can replace numerous
remote devices, they typically dont have more advanced features built in like Next Generation Firewalls, Intrusion
Prevention Systems or Anti-Malware. This can be remedied through a technique called service chaining or service
insertion in which the SD-WAN appliance provides a virtual space that can host other advanced feature applications in
their own VMs. Many of the SD-WAN vendors in this study have already established partnerships with various vendors to
provide these advanced features out of the box.
Customers consistently request that an SD-WAN delivers six key features for their remote offices:
Zero-Touch Install - Remote devices only require a local untrained staff member to connect power and network(s) to
complete a branch install.
Remote Device Elimination - The solution provides enough capability to eliminate other remote devices such as
routers and firewalls.
Service Chaining/Insertion - The solution provides a mechanism to chain or insert other services.
Automated IP Address Discovery - The solution can detect a DHCP server, address itself and update the address
table without human intervention.
Brown-Out Resiliency - The solution can maintain connectivity in the event of a transient drop in voltage.
MOS Scoring - The solution collects metrics that measure changes or degradation in the quality of video and voice
connections.
Edge Device - Describes the remote office deployment form factor
Reshaping the WAN Management
Today's SD-WAN solutions are also reshaping the way
network teams monitor and manage WAN traffic,
connectivity, access and performance by transforming
functions from command line configuration, point-to-point
access rules and manual monitoring into a more nimble,
adaptable and resilient platform. SD-WAN management
solutions are typically built with four key characteristics:
Cloud-based Management Platform - the solution
manages WAN operations from secure cloud
management consoles, making them accessible and
controllable from anywhere and allowing availability of
management functions even in the event of a loss
of connectivity to, or from, the data center.
Application Awareness - The solution is aware of what applications reside where, what connectivity they require and
what access should be granted to its users or dependent systems and allows network operators to easily adjust priority
across the network to any application.
Centralized Policy Engine - Instead of relying on a myriad of manual point-to-point configuration rules spread across a
wide range of devices and locations, the solution uses its application awareness and roles-based policy engine to
configure complex access topologies with only a handful of policies written with business-intelligible terms.
Analytics & Reporting - The solution can collect key metrics, performance analytics and give visibility to both network
operations teams and security analysts as needed. The solutions application awareness also allows operators to gather
voluminous data for real-time and historical reporting eliminating the need for packet capture tools or other complex and
time consuming traffic monitors.
API Exposure - The solution exposes a RESTful API allowing it to integrate with other existing operations, network or
security monitoring and management platforms giving operations staff a "single pane of glass". It is important to note
many incumbent and traditional WAN solutions have difficulties exposing their APIs to other monitoring and management
platforms.
Export to SIEM - Describes the capability to natively export logs to a Security Information Event Management (SIEM)
tool.
2016 Trace3, Inc. All Rights Reserved 4
SD-WAN Trends
Reshaping the WAN, the Remote Office, WAN Management and WAN
Security
Reshaping WAN Security
Security is of paramount importance in every IT setting. In
the early days of SD-WAN, security was a noted
weakness and prohibited many organizations from
adoption. However, SD-WAN solutions have steadily
added both fundamental and advanced security features
and now integrate with technologies like Zscaler and other
service chaining alternatives to provide an unprecedented
suite of security layering options.
Although not as robust as a dedicated security appliance,
most of today's SD-WAN platforms are delivered with
enough out of the box security features for widespread
use. Most solutions provide end to end encrypted tunnels on top of basic firewall capabilities and many can incorporate a
host of third party security tools.
SD-WAN solutions also help to dispel the common misconception that MPLS is completely secure while every other
medium is rife with risk. However MPLS, at its core, is also a shared medium and subject to some of the same security
concerns as networking over another media. Nonetheless, many enterprises are still worried about leakage of highly
sensitive data and employ a hybrid strategy of MPLS plus another less expensive alternative and use SD-WAN to
segregate sensitive traffic to MPLS in normal operations.
Customers consistently request SD-WAN solutions deliver four key security features:
Built-in FW Capabilities - The solution provides basic firewall rule functionality.
Built-in IPS Capabilities - The solution provides a basic Intrusion Prevention System functionality.
AES-128 Encryption - The solution provides the Advanced Encryption Standard supporting 128 key length.
AES-256 Encryption - The solution provides the Advanced Encryption Standard supporting 256 key length.
FIPS 140-2 Certified - U.S. Government computer security standard used to accredit cryptographic modules.
Reshaping the WAN
Gone are the days of traditional WAN topologies where a
hub and spoke architecture satisfies even the most
advanced shops. Today, both branch offices and data
centers increasingly use cloud-based applications,
participate in video conferences, conduct online video
training and require direct access from branch to branch.
A simple point-to-point link between offices is no longer
adequate.
Utilizing software to define and manage the WAN provides
on-demand switching decisions in response to real-time
changes in traffic demands, priority, connection quality,
cost and available bandwidth. This agility is something that traditional WAN routers, routing algorithms and manual
configuration have not been, and will not be, able to accomplish.
Customers consistently request this new WAN topology deliver six key features:
MPLS Replacement - Solution allows for the replacement of one or more MPLS point-to-point connections to and
between remote offices.
Centralized Configuration - The solution makes WAN configuration changes from a centralized management console
instead of on each remote device.
2016 Trace3, Inc. All Rights Reserved 5
SD-WAN Trends
Reshaping the WAN, the Remote Office, WAN Management and WAN
Security
Hosts Own POPs - The vendor owns a series of geographically dispersed Points of Presence (POPs) to increase
performance/quality by using local cloud connections.
Multiple Connection Types - Solution supports the use of many different media types such as LTE, MPLS or
Broadband.
Traffic Steering - The solution can steer traffic to the most optimal locations, functions or devices based on
configurable policies.
Support Legacy WAN Interfaces - The solution supports integration with older WAN interfaces such as E1/T1.
OpEx/CapEx - The solution is licensed as Operational Expenses (OpEx) and/or Capital Expenses (CapEx).
SD-WAN is also changed by the WAN fabric provided by
large carriers and telcos. At some point, most telcos have
attempted to build their own SD-WAN solutions, primarily
by layering functionality on top of Cisco iWAN.
Although there are still a few DIY stalwarts, the vast
majority of carriers are abandoning internal development
efforts and opting to partner with other companies covered
in this report. [5] The most popular partnering choice
today is clearly Velocloud, who has inked agreements with
AT&T, Deutcshe Telekom, Sprint, EarthLink, Vonage and
MetTel. Not to be left out of the party, Versa Networks has
signed with CenturyLink/Level3 and Viptela has partnered with Verizon. Other agreements are also certainly in the works.
2016 Trace3, Inc. All Rights Reserved 6
SD-WAN Trends
Reshaping the WAN, the Remote Office, WAN Management and WAN
Security
Trace3's Take
Predictions
1. As is common in rapidly growing markets, the SD-WAN market will continue to expand both in the spend and the
number of players. Trace3 expects most, if not all, CDN, WAN Security, WAN optimization, WAN monitoring and other
WAN related technology companies will develop and deploy their own SD-WAN solutions in the coming year. Although it
is unlikely these latecomers will be able to generate much traction against today's established players, they will provide
the kindling for an inevitable consolidation phase as networking incumbents, CDNs and larger telecommunications firms
acquire many of the players in the SD-WAN space. Undoubtedly a few of today's SD-WAN leaders will remain
independent, but it is too early to make bets on which ones will hold out.
2. Network service providers are taking advantage of emerging SD-WAN technologies to provide the MPLS alternatives
their customers demand. It is inevitable all carriers will need an SD-WAN solution and it is unlikely they will be able to
develop internal solutions that can compare in cost, features or agility of the products already on the market. As such,
Trace3 sees and expects to continue to see carriers abandon their own internal SD-WAN development projects and form
partnerships with the SD-WAN providers already on the market. The economics of the larger telecommunications
companies will also compel them to acquire SD-WAN product vendors.
3. SD-WAN killed the Optimization Star? In the past, technologies like traffic shaping, packet prioritization and other WAN
optimization solutions have been developed to overcome the runaway cost of MPLS connectivity as bandwidth demands
skyrocket. SD-WAN products are also targeting this very pain point and developing features to obviate this need for WAN
optimization or deliver these features "out of the box". However, Trace3 does not predict that SD-WAN solutions will
replace the need for WAN optimization, but they will certainly change the perception of WAN optimization as an advanced
standalone product into a table stake feature of a larger WAN platform. Some WAN optimization vendors, like Riverbed,
recognize this and are attempting to get ahead of this trend by developing and acquiring SD-WAN solutions and
integrating their optimization solution into a new larger SD-WAN platform - a tricky proposition to be sure, but Trace3
expects this trend to continue.
4. Looking longer term, Trace3 expects to see SD-WAN solutions continue to evolve into more of an on-demand
connectivity model much like other consumer products on the market today.
2016 Trace3, Inc. All Rights Reserved 7
SD-WAN Trends
Reshaping the WAN, the Remote Office, WAN Management and WAN
Security
Recommendations
1. Although the SD-WAN space is evolving rapidly, waiting for the calm in the storm is illusory. If you have a business
need for an SD-WAN solution, the benefits of immediate implementation will outweigh waiting for a plateau in product
offerings.
2. MPLS replacement should not be the sole driver for transitioning from a traditional WAN topology to an SD-WAN
implementation. Although the cost savings from MPLS replace can be compelling, in the long-term savings in the remote
office infrastructure, centralized management and security efficiency will approach MPLS savings.
3. Professional services costs are often overlooked when pricing SD-WAN solutions, which can hide the true TCO of a
solution requiring manual configuration as opposed to those that provide "out-of-the-box" implementation.
4. Failing to solidify your WAN underlay before rolling out an SD-WAN solution can become a showstopper during
deployment. A full WAN assessment and remediation is highly recommended.
5. Traditional WAN solutions are typically architected so that all remote internet bound traffic runs over the WAN back to
the corporate data center and out to the internet - a technique commonly dubbed 'data center backhauling'. Today's WAN
must handle an increasing amount of uncompressible, un-deduplicatable, and prioritized communications such as voice
and video, and so, the option to send this traffic directly from the remote site to the Internet is a very compelling
alternative to backhauling. Therefore, quantifying the amount of backhaul elimination is critical.
6. Conversely, while backhaul elimination is a boon for network simplification, it can present a larger attack surface that
must be protected. Many advanced security tools are housed in the corporate data center. Thus, it may make sense from
a security operations, management and cost perspective to have internet bound traffic flow back through the data center.
A close evaluation of corporate security policies and restrictions can help determine if backhaul elimination is desirable or
even possible.
7. There are three recommended methods to secure the Internet-connected branch office:
a). Service chaining additional security appliance features. However, if these virtual appliances do not incorporate a
strong central management strategy, this can be costly and arduous to manage.
b). Service insertion of cloud-based security features. This removes the need for an appliance to be managed in the
branch by providing centralized management.
c). Integration of a hybrid approach. This provides a combination of virtual appliances and cloud-based solutions in
which the onsite SD-WAN appliance provides local services but is managed by a central cloud-based solution service.
8. Finally, an SD-WAN solution should be viewed as a component of an overall WAN ecosystem that also includes WAN
Optimization, WAN Security, Analytics, Networking Infrastructure and even other IT operations use cases like DR, backup
and restore and copy data management.
2016 Trace3, Inc. All Rights Reserved 8
SD-WAN Trends
Reshaping the WAN, the Remote Office, WAN Management and WAN
Security
Appendix
Featured Use Cases
Software Defined WAN
New Hotness: VeloCloud, CloudGenix
Software-defined WAN (SD-WAN) is an approach to designing and deploying an enterprise wide area network (WAN)
that uses software-defined networking (SDN) to determine the most effective way to route traffic to remote locations.
Sources
1 IDC - IDC Forecasts Strong Growth for Software-Defined WAN As Enterprises Seek to Optimize Their Cloud
Strategies 2016
2 Gartner Market Guide for Software Defined WAN 2015
3 Forrester The Future of The WAN is Software-Defined 2016
4 Network Computing Software-Defined WAN: A Primer 2014
5 Fierce Telecom - Level 3: We dont want to release a me-too SD-WAN product 2016
6 - QOS Consulting - Debunking Common SD-WAN Misconceptions - 2016
7 - Cisco - Intelligent WAN Technology Design Guide - 2016
8 - Open Networking Users Group - SD-WAN Working Group - 2016
2016 Trace3, Inc. All Rights Reserved 9
SD-WAN Trends
Reshaping the WAN, the Remote Office, WAN Management and WAN
Security
Overview - The SD-WAN Landscape
Reshaping the Remote Office
2016 Trace3, Inc. All Rights Reserved 10
SD-WAN Trends
Reshaping the WAN, the Remote Office, WAN Management and WAN
Security
Reshaping the WAN Management
Reshaping WAN Security
Reshaping the WAN
2016 Trace3, Inc. All Rights Reserved 11
SD-WAN Trends
Reshaping the WAN, the Remote Office, WAN Management and WAN
Security
(end of report)
2016 Trace3, Inc. All Rights Reserved 12
S-ar putea să vă placă și
- Active Directory TrainingDocument124 paginiActive Directory TrainingPichai Ng-arnpairojh100% (1)
- Introduction To PythonDocument64 paginiIntroduction To PythonPichai Ng-arnpairojhÎncă nu există evaluări
- MX Deep DiveDocument36 paginiMX Deep DivePichai Ng-arnpairojhÎncă nu există evaluări
- Card Acceptance GuideDocument46 paginiCard Acceptance GuideJózsef PataiÎncă nu există evaluări
- Juniper Networks VMX OverviewDocument16 paginiJuniper Networks VMX OverviewPichai Ng-arnpairojhÎncă nu există evaluări
- Cisco Sdwan Design GuideDocument102 paginiCisco Sdwan Design GuideSheik ShareefÎncă nu există evaluări
- (23d4ead4 83ce 4aab 8acb 487dfcdc6d1a) Telstra SD WAN Guide FinalDocument46 pagini(23d4ead4 83ce 4aab 8acb 487dfcdc6d1a) Telstra SD WAN Guide FinaldheevettiÎncă nu există evaluări
- Capstone ProjectDocument59 paginiCapstone ProjectBhavika Goyal100% (1)
- Cisco Meraki Cloud Managed Solution - CLLE PDFDocument30 paginiCisco Meraki Cloud Managed Solution - CLLE PDFPichai Ng-arnpairojhÎncă nu există evaluări
- Meraki Solution OverviewDocument32 paginiMeraki Solution OverviewPichai Ng-arnpairojh100% (1)
- Chapter 1 For Thesis Arduino FinalDocument13 paginiChapter 1 For Thesis Arduino FinalCrash Zerocool50% (2)
- Ebook Network Leaders Guide To SD WAN - 2019 PDFDocument17 paginiEbook Network Leaders Guide To SD WAN - 2019 PDFITUMELENGÎncă nu există evaluări
- VeloCloud Lab Hol 2140 91 Ism - PDF - enDocument19 paginiVeloCloud Lab Hol 2140 91 Ism - PDF - enpaulo_an7381Încă nu există evaluări
- Fortinet Secure-Sdwan-7.0-Concept-GuideDocument19 paginiFortinet Secure-Sdwan-7.0-Concept-GuideSayed Ashraf Husaini KaziÎncă nu există evaluări
- SD-WAN Explained: The Ultimate Guide To SD-WAN ArchitectureDocument25 paginiSD-WAN Explained: The Ultimate Guide To SD-WAN ArchitecturehogadÎncă nu există evaluări
- SD WAN Three Use Cases For TransformingDocument8 paginiSD WAN Three Use Cases For TransformingduartefrancoÎncă nu există evaluări
- SD WAN Architecture 1621768797Document10 paginiSD WAN Architecture 1621768797Shakeel AminÎncă nu există evaluări
- SD WanDocument4 paginiSD WanFernala Sejmen-BanjacÎncă nu există evaluări
- Gartner Market Guide For SD WanDocument23 paginiGartner Market Guide For SD WanedyÎncă nu există evaluări
- Riverbed SD-WAN: Ricky Lin, CCIE#7469, MBA Deputy CTODocument26 paginiRiverbed SD-WAN: Ricky Lin, CCIE#7469, MBA Deputy CTOjmbrhnÎncă nu există evaluări
- Cisco Sdwan Design GuideDocument102 paginiCisco Sdwan Design GuideJohn TsigkrisÎncă nu există evaluări
- Cisco SD-WAN Design GuideDocument103 paginiCisco SD-WAN Design GuideMohmed IbrahimÎncă nu există evaluări
- Cisco Sdwan Design GuideDocument102 paginiCisco Sdwan Design GuideChien DauÎncă nu există evaluări
- Advance WLANDocument156 paginiAdvance WLANPichai Ng-arnpairojhÎncă nu există evaluări
- SD Wan PresoDocument19 paginiSD Wan PresoK KhaleelÎncă nu există evaluări
- Introduction To Cisco SD-WAN (Viptela) - IP With EaseDocument3 paginiIntroduction To Cisco SD-WAN (Viptela) - IP With EasemvsnkraoÎncă nu există evaluări
- SASE Vs SD WAN Beyond SecurityDocument11 paginiSASE Vs SD WAN Beyond SecurityEve AthanasekouÎncă nu există evaluări
- Python DigsilentDocument16 paginiPython DigsilentSunil MåüřÿäÎncă nu există evaluări
- Cisco Meraki Product Launch Q1 2017Document40 paginiCisco Meraki Product Launch Q1 2017Pichai Ng-arnpairojhÎncă nu există evaluări
- ExtremeXOS 22.1 RelNotesDocument68 paginiExtremeXOS 22.1 RelNotesMoises ReznikÎncă nu există evaluări
- SD Wan 1592482748Document6 paginiSD Wan 1592482748Florick Le MahamatÎncă nu există evaluări
- Sd-Wan For Enterprises: Vmware Special EditionDocument5 paginiSd-Wan For Enterprises: Vmware Special EditionEduardo SoberanisÎncă nu există evaluări
- AAG - Key SD WAN Use CasesDocument3 paginiAAG - Key SD WAN Use Caseshcm daukhiÎncă nu există evaluări
- Annamacharya Institute of Technology: Basics of Cloud ComputingDocument18 paginiAnnamacharya Institute of Technology: Basics of Cloud ComputingAbhinavreddy BÎncă nu există evaluări
- Automating SD-WAN Branch Configuration With HCLTech TIS Powered by Aruba Edge ConnectDocument12 paginiAutomating SD-WAN Branch Configuration With HCLTech TIS Powered by Aruba Edge Connect39.Anandadeep Bala XII S4Încă nu există evaluări
- Sd-Wan Overview: Vmware Special EditionDocument6 paginiSd-Wan Overview: Vmware Special EditionEduardo SoberanisÎncă nu există evaluări
- SD WanDocument32 paginiSD WanAbdalrawoof AlsherifÎncă nu există evaluări
- Unleashing The Power of SD-WANDocument3 paginiUnleashing The Power of SD-WANSaqib AfzalÎncă nu există evaluări
- SD-WAN Demystified: Empowering Your Network for SuccessDe la EverandSD-WAN Demystified: Empowering Your Network for SuccessÎncă nu există evaluări
- Chapter 5Document16 paginiChapter 5Hina SaeedÎncă nu există evaluări
- Software Defined Wide Area Network: Puja A. Dhakulkar, Pranjali S. Dubey, Ankita A. Gaikwad, Sneha P. DhokaneDocument6 paginiSoftware Defined Wide Area Network: Puja A. Dhakulkar, Pranjali S. Dubey, Ankita A. Gaikwad, Sneha P. DhokanekamalgaihreÎncă nu există evaluări
- SO SDBranchDocument5 paginiSO SDBranchhcm daukhiÎncă nu există evaluări
- Juniper - Five Must Haves For Next Gen SD WAN SolutionsDocument7 paginiJuniper - Five Must Haves For Next Gen SD WAN SolutionsJÎncă nu există evaluări
- Fortinet 1 4JLJ8BNDocument6 paginiFortinet 1 4JLJ8BNkentmultanÎncă nu există evaluări
- Whitepaper Go MainstreamDocument12 paginiWhitepaper Go Mainstream张裴Încă nu există evaluări
- Vmware SD Wan by Velocloud Overview - 551681Document5 paginiVmware SD Wan by Velocloud Overview - 551681Eduardo SoberanisÎncă nu există evaluări
- Finding The Best SD-WAN Solution For Your Enterprise: Guide For Evaluating SD-WAN ProductsDocument7 paginiFinding The Best SD-WAN Solution For Your Enterprise: Guide For Evaluating SD-WAN Productseleazar_lostÎncă nu există evaluări
- Nss Labs Security Controls in The Us EnterpriseDocument16 paginiNss Labs Security Controls in The Us EnterpriseYoel ArmasÎncă nu există evaluări
- Virtualized Network Services: Transcend Connectivity and Empower IT With SD-WAN 2.0Document9 paginiVirtualized Network Services: Transcend Connectivity and Empower IT With SD-WAN 2.0Barry ZhuÎncă nu există evaluări
- Untangle Whitepaper Securing The Distributed Enterprise With SD WanDocument3 paginiUntangle Whitepaper Securing The Distributed Enterprise With SD WanRajeev AroraÎncă nu există evaluări
- The Cios Guide To Sd-Wan: Building The Case For A Faster, Better, and Cheaper NetworkDocument22 paginiThe Cios Guide To Sd-Wan: Building The Case For A Faster, Better, and Cheaper NetworktangolauÎncă nu există evaluări
- 2022 SD-WAN GuideDocument38 pagini2022 SD-WAN Guidejaysa0Încă nu există evaluări
- 04wp SD Wan - Solutions EkinopsDocument8 pagini04wp SD Wan - Solutions EkinopsTransmission NOCÎncă nu există evaluări
- Nokia Nuage Networks Secure SDWAN EbookDocument14 paginiNokia Nuage Networks Secure SDWAN EbookBarry ZhuÎncă nu există evaluări
- Vmware SD WanDocument16 paginiVmware SD Wan张裴Încă nu există evaluări
- Eight Questions To Ask When Considering An SD Wan WPDocument9 paginiEight Questions To Ask When Considering An SD Wan WPAlphonseÎncă nu există evaluări
- Design WAN For Cloud BrochureDocument5 paginiDesign WAN For Cloud BrochurefghghjyeeÎncă nu există evaluări
- How Service Providers Can Optimize Managed SD WAN and SD Branch Delivery and ManagementDocument15 paginiHow Service Providers Can Optimize Managed SD WAN and SD Branch Delivery and ManagementEdiz İşlerÎncă nu există evaluări
- Huawei SD-WAN Solution DatasheetDocument6 paginiHuawei SD-WAN Solution DatasheetEduardo SoberanisÎncă nu există evaluări
- Sdwan 712 Edge Platform Spec Ds 1020Document16 paginiSdwan 712 Edge Platform Spec Ds 1020juharieÎncă nu există evaluări
- NB 06 Idc Business Value SD Wan Analyst RPT Cte enDocument13 paginiNB 06 Idc Business Value SD Wan Analyst RPT Cte enSou EuÎncă nu există evaluări
- Sdwan 712 Edge Platform Spec Ds 1020Document17 paginiSdwan 712 Edge Platform Spec Ds 1020Cesar Campos LimaÎncă nu există evaluări
- Fortinet Secure SdwanDocument8 paginiFortinet Secure SdwanpepeÎncă nu există evaluări
- Sdwan 712 Edge Platform Spec Ds 1020Document17 paginiSdwan 712 Edge Platform Spec Ds 1020Jonny TekÎncă nu există evaluări
- Versa Secure SD WanDocument4 paginiVersa Secure SD WanAziz NugrohoÎncă nu există evaluări
- Huawei SD-WAN Solution DatasheetDocument9 paginiHuawei SD-WAN Solution Datasheetkareem saleemÎncă nu există evaluări
- Sdwan 712 Edge Platform Spec Ds 0320Document14 paginiSdwan 712 Edge Platform Spec Ds 0320Sumit Chanda100% (1)
- Cisco SDWAN Case StudyDocument4 paginiCisco SDWAN Case Studysm.ccde2024Încă nu există evaluări
- Infra Planning SdwanDocument1 paginăInfra Planning SdwanMarj SyÎncă nu există evaluări
- Cisco SMB NB 06 SD Wan Sol Overview Cte en PDFDocument7 paginiCisco SMB NB 06 SD Wan Sol Overview Cte en PDFRakesh KumarÎncă nu există evaluări
- IO158822à - Apcelaà - à - 2447917 - EGuide1 - à - 2.2.2023 - ACDocument9 paginiIO158822à - Apcelaà - à - 2447917 - EGuide1 - à - 2.2.2023 - ACadminakÎncă nu există evaluări
- Secure SD-WAN Customer Success StoriesDocument22 paginiSecure SD-WAN Customer Success Storiesjc.ovandoÎncă nu există evaluări
- Future of Sd-Wan: Vmware Special EditionDocument4 paginiFuture of Sd-Wan: Vmware Special EditionEduardo SoberanisÎncă nu există evaluări
- Juniper SRX Quickstart-12.1r3Document455 paginiJuniper SRX Quickstart-12.1r3Pichai Ng-arnpairojhÎncă nu există evaluări
- Juniper SRX Quickstart-12.1r3Document455 paginiJuniper SRX Quickstart-12.1r3Pichai Ng-arnpairojhÎncă nu există evaluări
- Juniper IDP OverviewDocument55 paginiJuniper IDP OverviewPichai Ng-arnpairojhÎncă nu există evaluări
- Juniper Lab1 BGP Exercise BGP Peering PDFDocument16 paginiJuniper Lab1 BGP Exercise BGP Peering PDFPichai Ng-arnpairojhÎncă nu există evaluări
- Meraki Powered Services BellDocument30 paginiMeraki Powered Services BellPichai Ng-arnpairojhÎncă nu există evaluări
- RsyslogDocument329 paginiRsyslogPichai Ng-arnpairojhÎncă nu există evaluări
- Skype For Business and Exchange Deployment Planning Services Datasheet PDFDocument2 paginiSkype For Business and Exchange Deployment Planning Services Datasheet PDFPichai Ng-arnpairojhÎncă nu există evaluări
- Cisco Meraki Cloud NetworkingDocument30 paginiCisco Meraki Cloud NetworkingPichai Ng-arnpairojhÎncă nu există evaluări
- Windows Server 2008 Active DirectoryDocument151 paginiWindows Server 2008 Active DirectoryPichai Ng-arnpairojhÎncă nu există evaluări
- Configuring Log SourcesDocument70 paginiConfiguring Log SourcesPichai Ng-arnpairojhÎncă nu există evaluări
- Localhost - Localdomain PerformanceDocument2 paginiLocalhost - Localdomain PerformancePichai Ng-arnpairojhÎncă nu există evaluări
- 2015 VERNA Ebrochure 1519269571059Document14 pagini2015 VERNA Ebrochure 1519269571059Jazzi SehrawatÎncă nu există evaluări
- Smart Site Management Unit SCC800 Datasheet (Overseas Version)Document2 paginiSmart Site Management Unit SCC800 Datasheet (Overseas Version)Ahmad Putra100% (1)
- Intellectual Property Office of The PhilippinesDocument2 paginiIntellectual Property Office of The Philippinesmiggy13Încă nu există evaluări
- Basic Education Enrollment Form - 2018Document4 paginiBasic Education Enrollment Form - 2018Dwight Kayce VizcarraÎncă nu există evaluări
- Aadhaar Failures: A Tragedy of ErrorsDocument11 paginiAadhaar Failures: A Tragedy of ErrorsSneha GuptaÎncă nu există evaluări
- Doxographi Graeci DielsDocument883 paginiDoxographi Graeci DielsFlorin FilimonÎncă nu există evaluări
- T8 B19 Miles Kara HQ FAA 3 of 3 FDR - FAA WOC Staffing On 911Document5 paginiT8 B19 Miles Kara HQ FAA 3 of 3 FDR - FAA WOC Staffing On 9119/11 Document ArchiveÎncă nu există evaluări
- Dynamic Tiering Option Administration Guide enDocument112 paginiDynamic Tiering Option Administration Guide ensridharÎncă nu există evaluări
- Booking Confirmation On IRCTC, Train: 12101, 08-Dec-2017, SL, LTT - HWHDocument2 paginiBooking Confirmation On IRCTC, Train: 12101, 08-Dec-2017, SL, LTT - HWHShubhrajit MaitraÎncă nu există evaluări
- Giovanna Harbor ResumeDocument1 paginăGiovanna Harbor Resumegch5043Încă nu există evaluări
- NPM GuideDocument92 paginiNPM Guidebelalr84Încă nu există evaluări
- Fee ReciptDocument1 paginăFee Reciptrohitkumar60483Încă nu există evaluări
- Instructor: DR - Maaz Bin Ahmad. 0333-5264960: Maaz@pafkiet - Edu.pkDocument54 paginiInstructor: DR - Maaz Bin Ahmad. 0333-5264960: Maaz@pafkiet - Edu.pkSubhan50Încă nu există evaluări
- PCI DSS Policies and ProceduresDocument38 paginiPCI DSS Policies and Proceduresjustforfun2009Încă nu există evaluări
- UCC Students Help Desk Phone NumbersDocument4 paginiUCC Students Help Desk Phone NumbersRicardo HoustonÎncă nu există evaluări
- Accord SLD FormatDocument3 paginiAccord SLD FormatMishkat Immaculate100% (1)
- KeyDocument4 paginiKeyQuocduy LieuÎncă nu există evaluări
- Digital Envelopes and Digital SignaturesDocument5 paginiDigital Envelopes and Digital SignaturesThamolwan Chumni0% (1)
- Genie Superlift SOP 003Document27 paginiGenie Superlift SOP 003Mauricio SantanaÎncă nu există evaluări
- Computers in Human Behavior: Lyn E. Pleger, Katharina Guirguis, Alexander MertesDocument17 paginiComputers in Human Behavior: Lyn E. Pleger, Katharina Guirguis, Alexander MertesMhdRahulÎncă nu există evaluări
- Sentry A3810Document7 paginiSentry A3810Darkcastle2012Încă nu există evaluări
- Artificial Passenger: (AS P D B C S)Document17 paginiArtificial Passenger: (AS P D B C S)gaganpk100% (1)
- FortinetDocument21 paginiFortinet0neboxÎncă nu există evaluări
- Non Disclosure AgreementDocument3 paginiNon Disclosure AgreementtessÎncă nu există evaluări
- El Moqaddam Riffimohamed, 05oct1340tangier, TNGDocument3 paginiEl Moqaddam Riffimohamed, 05oct1340tangier, TNGTarik ThomasÎncă nu există evaluări