Documente Academic
Documente Profesional
Documente Cultură
Lecture3 PDF
Încărcat de
me_bastiTitlu original
Drepturi de autor
Formate disponibile
Partajați acest document
Partajați sau inserați document
Vi se pare util acest document?
Este necorespunzător acest conținut?
Raportați acest documentDrepturi de autor:
Formate disponibile
Lecture3 PDF
Încărcat de
me_bastiDrepturi de autor:
Formate disponibile
Security and Cooperation
in Wireless Networks
http://secowinet.epfl.ch/
Chapter 1: The security of existing
wireless networks
cellular networks:
- GSM;
- UMTS;
WiFi LANs;
Bluetooth;
© 2007 Levente Buttyán and Jean-Pierre Hubaux
Why is security more of a concern in wireless?
no inherent physical protection
– physical connections between devices are replaced by logical associations
– sending and receiving messages do not need physical access to the network
infrastructure (cables, hubs, routers, etc.)
broadcast communications
– wireless usually means radio, which has a broadcast nature
– transmissions can be overheard by anyone in range
– anyone can generate transmissions,
• which will be received by other devices in range
• which will interfere with other nearby transmissions and may prevent their correct
reception (jamming)
eavesdropping is easy
injecting bogus messages into the network is easy
replaying previously recorded messages is easy
illegitimate access to the network and its services is easy
denial of service is easily achieved by jamming
Security and Cooperation in Wireless Networks
2/60
Chapter 1: The security of existing wireless networks
Wireless communication security requirements
confidentiality
– messages sent over wireless links must be encrypted
authenticity
– origin of messages received over wireless links must be verified
replay detection
– freshness of messages received over wireless links must be checked
integrity
– modifying messages on-the-fly (during radio transmission) is not so easy, but
possible …
– integrity of messages received over wireless links must be verified
access control
– access to the network services should be provided only to legitimate entities
– access control should be permanent
• it is not enough to check the legitimacy of an entity only when it joins the network
and its logical associations are established, because logical associations can be
hijacked
protection against jamming
Security and Cooperation in Wireless Networks
3/60
Chapter 1: The security of existing wireless networks
Chapter outline
1.3.1 Cellular networks
1.3.2 WiFi LANs
1.3.3 Bluetooth
Security and Cooperation in Wireless Networks
4/60
Chapter 1: The security of existing wireless networks
GSM Security
main security requirement
– subscriber authentication (for the sake of billing)
• challenge-response protocol
• long-term secret key shared between the subscriber and the home
network operator
• supports roaming without revealing long-term key to the visited networks
other security services provided by GSM
– confidentiality of communications and signaling over the wireless
interface
• encryption key shared between the subscriber and the visited network is
established with the help of the home network as part of the subscriber
authentication protocol
– protection of the subscriber’s identity from eavesdroppers on the
wireless interface
• usage of short-term temporary identifiers
Security and Cooperation in Wireless Networks 1.3.1 Cellular networks
GSM security
5/60
Chapter 1: The security of existing wireless networks
The SIM card (Subscriber Identity Module)
Must be tamper-resistant
Protected by a PIN code (checked locally by the SIM)
Is removable from the terminal
Contains all data specific to the end user which have to
reside in the Mobile Station:
– IMSI: International Mobile Subscriber Identity (permanent user’s
identity)
– PIN
– TMSI (Temporary Mobile Subscriber Identity)
– Ki : User’s secret key
– Kc : Ciphering key
– List of the last call attempts
– List of preferred operators
– Supplementary service data (abbreviated dialing, last short messages
received,...)
Security and Cooperation in Wireless Networks 1.3.1 Cellular networks
GSM security
6/60
Chapter 1: The security of existing wireless networks
Cryptographic algorithms of GSM
Random number User’s secret key
R Ki
A3 A8
R S Kc Triplet
Authentication A5 Ciphering algorithm
Kc: ciphering key
S : signed result
A3: subscriber authentication (operator-dependent algorithm)
A5: ciphering/deciphering (standardized algorithm)
A8: cipher generation (operator-dependent algorithm)
Security and Cooperation in Wireless Networks 1.3.1 Cellular networks
GSM security
7/60
Chapter 1: The security of existing wireless networks
Authentication principle of GSM
Mobile Station Visited network Home network
Ki R
IMSI/TMSI
IMSI (or TMSI)
IMSI A8 A3
Kc S
Triplets (Kc, R, S)
Triplets
Authenticate (R)
Ki R
A8 A3
Kc S’ Auth-ack(S’)
S=S’?
Security and Cooperation in Wireless Networks 1.3.1 Cellular networks
GSM security
8/60
Chapter 1: The security of existing wireless networks
Ciphering in GSM
Kc FRAME NUMBER Kc FRAME NUMBER
A5 A5
CIPHERING CIPHERING
SEQUENCE SEQUENCE
PLAINTEXT CIPHERTEXT PLAINTEXT
SEQUENCE ! SEQUENCE ! SEQUENCE
Sender Receiver
(Mobile Station or Network) (Network or Mobile Station)
Security and Cooperation in Wireless Networks 1.3.1 Cellular networks
GSM security
9/60
Chapter 1: The security of existing wireless networks
Conclusion on GSM security
Focused on the protection of the air interface
No protection on the wired part of the network (neither for
privacy nor for confidentiality)
The visited network has access to all data (except the secret
key of the end user)
Generally robust, but a few successful attacks have been
reported:
– faked base stations
– cloning of the SIM card
Security and Cooperation in Wireless Networks 1.3.1 Cellular networks
GSM security
10/60
Chapter 1: The security of existing wireless networks
3GPP Security Principles (1/2)
Reuse of 2nd generation security principles (GSM):
– Removable hardware security module
• In GSM: SIM card
• In 3GPP: USIM (User Services Identity Module)
– Radio interface encryption
– Limited trust in the Visited Network
– Protection of the identity of the end user (especially on the radio
interface)
Correction of the following weaknesses of the previous
generation:
– Possible attacks from a faked base station
– Cipher keys and authentication data transmitted in clear between and
within networks
– Encryption not used in some networks open to fraud
– Data integrity not provided
– …
Security and Cooperation in Wireless Networks 1.3.1 Cellular networks
UMTS security
11/60
Chapter 1: The security of existing wireless networks
3GPP Security Principles (2/2)
New security features
– New kind of service providers (content providers, HLR only service
providers,…)
– Increased control for the user over their service profile
– Enhanced resistance to active attacks
– Increased importance of non-voice services
– …
Security and Cooperation in Wireless Networks 1.3.1 Cellular networks
UMTS security
12/60
Chapter 1: The security of existing wireless networks
Authentication in 3GPP
Mobile Station Visited Network Home Environment
Sequence number (SQN) RAND(i)
K: User’s Generation of
secret key cryptographic material
User authentication request IMSI/TMSI Authentication vectors
K
RAND(i ) || AUTN (i )
Verify AUTN(i)
Compute RES(i)
User authentication response RES(i)
Compare RES(i)
K
and XRES(i)
Compute CK(i) Select CK(i)
and IK(i) and IK(i)
Security and Cooperation in Wireless Networks 1.3.1 Cellular networks
UMTS security
13/60
Chapter 1: The security of existing wireless networks
Generation of the authentication vectors
Generate SQN
Generate RAND
AMF
f1 f2 f3 f4 f5
MAC (Message XRES CK IK AK
Authentication (Expected (Cipher (Integrity (Anonymity
Code) Result) Key) Key) Key)
AUTN := ( SQN ! ACK ) || AMF || MAC AMF: Authentication and Key Management Field
AUTN: Authentication Token
AV := RAND || XRES || CK || IK || AUTN
AV: Authentication Vector
Security and Cooperation in Wireless Networks 1.3.1 Cellular networks
UMTS security
14/60
Chapter 1: The security of existing wireless networks
User Authentication Function in the USIM
RAND AUTN
SQN ! AK AMF MAC
f5
AK !
SQN
K
f1 f2 f3 f4
XMAC RES CK IK
(Expected MAC) (Result) (Cipher (Integrity
Key) Key)
• Verify MAC = XMAC
• Verify that SQN is in the correct range
USIM: User Services Identity Module
Security and Cooperation in Wireless Networks 1.3.1 Cellular networks
UMTS security
15/60
Chapter 1: The security of existing wireless networks
More about the authentication and key generation
In addition to f1, f2, f3, f4 and f5, two more functions are
defined: f1* and f5*, used in case the authentication
procedure gets desynchronized (detected by the range of
SQN).
f1, f1*, f2, f3, f4, f5 and f5* are operator-specific
However, 3GPP provides a detailed example of algorithm set,
called MILENAGE
MILENAGE is based on the Rijndael block cipher
In MILENAGE, the generation of all seven functions f1…f5* is
based on the Rijndael algorithm
Security and Cooperation in Wireless Networks 1.3.1 Cellular networks
UMTS security
16/60
Chapter 1: The security of existing wireless networks
Authentication and key generation functions f1…f5*
RAND
OP EK OPc
SQN||AMF OPc
EK
OPc OPc OPc OPc OPc
rotate rotate rotate rotate rotate
by r1 by r2 by r3 by r4 by r5
c1 c2 c3 c4 c5
EK EK EK EK EK
OPc OPc OPc OPc OPc
f1 f1* f5 f2 f3 f4 f5*
OP: operator-specific parameter
r1,…, r5: fixed rotation constants EK : Rijndael block cipher with
c1,…, c5: fixed addition constants 128 bits text input and 128 bits key
Security and Cooperation in Wireless Networks 1.3.1 Cellular networks
UMTS security
17/60
Chapter 1: The security of existing wireless networks
Signalling integrity protection method
SIGNALLING MESSAGE SIGNALLING MESSAGE
FRESH FRESH
COUNT-I DIRECTION COUNT-I DIRECTION
IK f9 IK f9
MAC-I XMAC-I
Sender Receiver
(Mobile Station or (Radio Network Controller
Radio Network Controller) or Mobile Station)
FRESH: random input
Security and Cooperation in Wireless Networks 1.3.1 Cellular networks
UMTS security
18/60
Chapter 1: The security of existing wireless networks
Ciphering method
BEARER LENGTH BEARER LENGTH
COUNT-C DIRECTION COUNT-C DIRECTION
CK f8 CK f8
KEYSTREAM KEYSTREAM
BLOCK BLOCK
PLAINTEXT CIPHERTEXT PLAINTEXT
BLOCK ! BLOCK
! BLOCK
Sender Receiver
(Mobile Station or (Radio Network Controller
Radio Network Controller) or Mobile Station)
BEARER: radio bearer identifier
COUNT-C: ciphering sequence counter
Security and Cooperation in Wireless Networks 1.3.1 Cellular networks
UMTS security
19/60
Chapter 1: The security of existing wireless networks
The keystream generator f8
COUNT || BEARER || DIRECTION || 0…0
KM: Key Modifier
KS: Keystream
CK KM KASUMI
Register
BLKCNT=0 BLKCNT=1 BLKCNT=2 BLKCNT=BLOCKS-1
CK KASUMI CK KASUMI CK KASUMI CK KASUMI
KS[0]…KS[63] KS[64]…KS[127] KS[128]…KS[191]
Security and Cooperation in Wireless Networks 1.3.1 Cellular networks
UMTS security
20/60
Chapter 1: The security of existing wireless networks
KLi, KOi , KIi : subkeys used at ith round
Details of Kasumi S7, S9: S-boxes
L0 R0
32 64 32 32 16
16 16 9 7
KL1 KO1 , KI1 FIi1 KOi,1
S9
FL1 FO1 KIi,1 Zero-extend
KO2 , KI2 KL2
FO2 FL2
S7
FIi2 KOi,2 truncate
KL3 KO3 , KI3 KIi,j,2
KIi,2
FL3 FO3 KIi,j,1
KO4, KI4 KL4
FO4 FL4 S9
FIi3 KOi,3
Zero-extend
KIi,3
KL5 KO5 , KI5
FL5 FO5
S7
truncate
KO6 , KI6 KL6
FO6 FL6
KL7 KO7 , KI7 Fig. 2 : FO Function Fig. 3 : FI Function
FL7 FO7
32
16 16
KO8 , KI8 KL8 KLi,1
FO8 FL8 <<<
KLi,2 Bitwise AND operation
L8 C R8 <<< Bitwise OR operation
<<< One bit left rotation
Fig. 4 : FL Function
Fig. 1 : KASUMI
Security and Cooperation in Wireless Networks 1.3.1 Cellular networks
UMTS security
21/60
Chapter 1: The security of existing wireless networks
Conclusion on 3GPP security
Some improvement with respect to 2nd generation
– Cryptographic algorithms are published
– Integrity of the signalling messages is protected
Quite conservative solution
Privacy/anonymity of the user not completely protected
2nd/3rd generation interoperation will be complicated and
might open security breaches
Security and Cooperation in Wireless Networks 1.3.1 Cellular networks
UMTS security
22/60
Chapter 1: The security of existing wireless networks
Chapter outline
1.3.1 Cellular networks
1.3.2 WiFi LANs
1.3.3 Bluetooth
Security and Cooperation in Wireless Networks
23/60
Chapter 1: The security of existing wireless networks
Introduction to WiFi
“connected” scanning on
each channel
STA
association request
association response
AP
beacon
- MAC header
- timestamp
- beacon interval
- capability info
- SSID (network name)
- supported data rates
- radio parameters
- power slave flags
Security and Cooperation in Wireless Networks
1.3.2 WiFi LANs 24/60
Chapter 1: The security of existing wireless networks
Introduction to WiFi
Internet
AP
Security and Cooperation in Wireless Networks
1.3.2 WiFi LANs 25/60
Chapter 1: The security of existing wireless networks
WEP – Wired Equivalent Privacy
part of the IEEE 802.11 specification
goal
– make the WiFi network at least as secure as a wired LAN (that has
no particular protection mechanisms)
– WEP was never intended to achieve strong security
services
– access control to the network
– message confidentiality
– message integrity
Security and Cooperation in Wireless Networks 1.3.2 WiFi LANs
Wired Equivalent Privacy (WEP)
26/60
Chapter 1: The security of existing wireless networks
WEP – Access control
before association, the STA needs to authenticate itself to
the AP
authentication is based on a simple challenge-response
protocol:
STA AP: authenticate request
AP STA: authenticate challenge (r) // r is 128 bits long
STA AP: authenticate response (eK(r))
AP STA: authenticate success/failure
once authenticated, the STA can send an association
request, and the AP will respond with an association
response
if authentication fails, no association is possible
Security and Cooperation in Wireless Networks 1.3.2 WiFi LANs
Wired Equivalent Privacy (WEP)
27/60
Chapter 1: The security of existing wireless networks
WEP – Message confidentiality and integrity
WEP encryption is based on RC4 (a stream cipher developed in 1987 by
Ron Rivest for RSA Data Security, Inc.)
– operation:
• for each message to be sent:
– RC4 is initialized with the shared secret (between STA and AP)
– RC4 produces a pseudo-random byte sequence (key stream)
– this pseudo-random byte sequence is XORed to the message
• reception is analogous
– it is essential that each message is encrypted with a different key stream
• the RC4 generator is initialized with the shared secret and an IV (initial value)
together
– shared secret is the same for each message
– 24-bit IV changes for every message
WEP integrity protection is based on an encrypted CRC value
– operation:
• ICV (integrity check value) is computed and appended to the message
• the message and the ICV are encrypted together
Security and Cooperation in Wireless Networks 1.3.2 WiFi LANs
Wired Equivalent Privacy (WEP)
28/60
Chapter 1: The security of existing wireless networks
WEP – Message confidentiality and integrity
message + ICV
K
IV secret key RC4
encode
IV message + ICV
decode
K
IV secret key RC4
K: pseudo-random sequence message + ICV
Security and Cooperation in Wireless Networks 1.3.2 WiFi LANs
Wired Equivalent Privacy (WEP)
29/60
Chapter 1: The security of existing wireless networks
WEP – Keys
two kinds of keys are allowed by the standard
– default key (also called shared key, group key, multicast key, broadcast key,
key)
– key mapping keys (also called individual key, per-station key, unique key)
id:X | key:abc default key id:X | key:def key mapping key
id:Y | key:abc id:Y | key:ghi
id:Z | key:abc id:Z | key:jkl
key:abc id:X | key:def
id:Y | key:ghi
id:Z | key:jkl
in practice, often only default keys are supported
– the default key is manually installed in every STA and the AP
– each STA uses the same shared secret key in principle, STAs can decrypt
each other’s messages
Security and Cooperation in Wireless Networks 1.3.2 WiFi LANs
Wired Equivalent Privacy (WEP)
30/60
Chapter 1: The security of existing wireless networks
WEP – Management of default keys
the default key is a group key, and group keys need to be
changed when a member leaves the group
– e.g., when someone leaves the company and shouldn’t have access
to the network anymore
it is practically impossible to change the default key in every
device simultaneously
hence, WEP supports multiple default keys to help the
smooth change of keys
– one of the keys is called the active key
– the active key is used to encrypt messages
– any key can be used to decrypt messages
– the message header contains a key ID that allows the receiver to find
out which key should be used to decrypt the message
Security and Cooperation in Wireless Networks 1.3.2 WiFi LANs
Wired Equivalent Privacy (WEP)
31/60
Chapter 1: The security of existing wireless networks
WEP – The key change process
Œ
time
abc* abc* * active key
--- ---
abc* abc* abc
--- def def*
--- abc
def* def*
--- ---
def* def*
Security and Cooperation in Wireless Networks 1.3.2 WiFi LANs
Wired Equivalent Privacy (WEP)
32/60
Chapter 1: The security of existing wireless networks
WEP flaws – Authentication and access control
authentication is one-way only
– AP is not authenticated to STA
– STA is at risk to associate to a rogue AP
the same shared secret key is used for authentication and
encryption
– weaknesses in any of the two protocols can be used to break the key
no session key is established during authentication
– access control is not continuous
– once a STA has authenticated and associated to the AP, an attacker
send messages using the MAC address of STA
– correctly encrypted messages cannot be produced by the attacker,
but replay of STA messages is still possible
STA can be impersonated
– … next slide
Security and Cooperation in Wireless Networks 1.3.2 WiFi LANs
Wired Equivalent Privacy (WEP)
33/60
Chapter 1: The security of existing wireless networks
WEP flaws – Authentication and access control
recall that authentication is based on a challenge-response
protocol:
…
AP STA: r
STA AP: IV | r ⊕ K
…
where K is a 128 bit RC4 output on IV and the shared secret
an attacker can compute r ⊕ (r ⊕ K) = K
then it can use K to impersonate STA later:
…
AP attacker: r’
attacker AP: IV | r’ ⊕ K
…
Security and Cooperation in Wireless Networks 1.3.2 WiFi LANs
Wired Equivalent Privacy (WEP)
34/60
Chapter 1: The security of existing wireless networks
WEP flaws – Integrity and replay protection
There’s no replay protection at all
– IV is not mandated to be incremented after each message
The attacker can manipulate messages despite the ICV
mechanism and encryption
– CRC is a linear function wrt to XOR:
CRC(X ⊕ Y) = CRC(X) ⊕ CRC(Y)
- attacker observes (M | CRC(M)) ⊕ K where K is the RC4 output
- for any ΔM, the attacker can compute CRC(ΔM)
- hence, the attacker can compute:
((M | CRC(M)) ⊕ K) ⊕ (ΔM | CRC(ΔM)) =
((M ⊕ ΔM) | (CRC(M) ⊕ CRC(ΔM))) ⊕ K =
((M ⊕ ΔM) | CRC(M ⊕ ΔM)) ⊕ K
Security and Cooperation in Wireless Networks 1.3.2 WiFi LANs
Wired Equivalent Privacy (WEP)
35/60
Chapter 1: The security of existing wireless networks
WEP flaws – Confidentiality
IV reuse
– IV space is too small
• IV size is only 24 bits there are 16,777,216 possible IVs
• after around 17 million messages, IVs are reused
• a busy AP at 11 Mbps is capable for transmitting 700 packets per second IV
space is used up in around 7 hours
– in many implementations IVs are initialized with 0 on startup
• if several devices are switched on nearly at the same time, they all use the same
sequence of IVs
• if they all use the same default key (which is the common case), then IV collisions
are readily available to an attacker
weak RC4 keys
– for some seed values (called weak keys), the beginning of the RC4 output is
not really random
– if a weak key is used, then the first few bytes of the output reveals a lot of
information about the key breaking the key is made easier
– for this reason, crypto experts suggest to always throw away the first 256
bytes of the RC4 output, but WEP doesn’t do that
– due to the use of IVs, eventually a weak key will be used, and the attacker
will know that, because the IV is sent in clear
WEP encryption can be broken by capturing a few million messages !!!
Security and Cooperation in Wireless Networks 1.3.2 WiFi LANs
Wired Equivalent Privacy (WEP)
36/60
Chapter 1: The security of existing wireless networks
WEP – Lessons learnt
1. Engineering security protocols is difficult
– One can combine otherwise strong building blocks in a wrong way and obtain
an insecure system at the end
• Example 1:
– stream ciphers alone are OK
– challenge-response protocols for entity authentication are OK
– but they shouldn’t be combined
• Example 2:
– encrypting a message digest to obtain an ICV is a good principle
– but it doesn’t work if the message digest function is linear wrt to the encryption function
– Don’t do it alone (unless you are a security expert)
• functional properties can be tested, but security is a non-functional property it
is extremely difficult to tell if a system is secure or not
– Using an expert in the design phase pays out (fixing the system after
deployment will be much more expensive)
• experts will not guarantee that your system is 100% secure
• but at least they know many pitfalls
• they know the details of crypto algorithms
2. Avoid the use of WEP (as much as possible)
Security and Cooperation in Wireless Networks 1.3.2 WiFi LANs
Wired Equivalent Privacy (WEP)
37/60
Chapter 1: The security of existing wireless networks
Overview of 802.11i
After the collapse of WEP, IEEE started to develop a new
security architecture 802.11i
Main novelties in 802.11i wrt to WEP
– access control model is based on 802.1X
– flexible authentication framework (based on EAP – Extensible
Authentication Protocol)
– authentication can be based on strong protocols (e.g., TLS –
Transport Layer Security)
– authentication process results in a shared session key (which
prevents session hijacking)
– different functions (encryption, integrity) use different keys derived
from the session key using a one-way function
– integrity protection is improved
– encryption function is improved
Security and Cooperation in Wireless Networks 1.3.2 WiFi LANs
IEEE 802.11i
38/60
Chapter 1: The security of existing wireless networks
Overview of 802.11i
802.11i defines the concept of RSN (Robust Security Network)
– integrity protection and encryption is based on AES (and not on RC4
anymore)
– nice solution, but needs new hardware cannot be adopted immediately
802.11i also defines an optional protocol called TKIP (Temporal Key
Integrity Protocol)
– integrity protection is based on Michael (we will skip the details of that)
– encryption is based on RC4, but WEP’s problems have been avoided
– ugly solution, but runs on old hardware (after software upgrade)
Industrial names
– TKIP WPA (WiFi Protected Access)
– RSN/AES WPA2
Security and Cooperation in Wireless Networks 1.3.2 WiFi LANs
IEEE 802.11i
39/60
Chapter 1: The security of existing wireless networks
802.1X authentication model
supplicant sys authenticator system auth server sys
supplicant services authenticator authentication
server
controls
port
LAN
the supplicant requests access to the services (wants to connect to the
network)
the authenticator controls access to the services (controls the state of a
port)
the authentication server authorizes access to the services
– the supplicant authenticates itself to the authentication server
– if the authentication is successful, the authentication server instructs the
authenticator to switch the port on
– the authentication server informs the supplicant that access is allowed
Security and Cooperation in Wireless Networks 1.3.2 WiFi LANs
IEEE 802.11i
40/60
Chapter 1: The security of existing wireless networks
Mapping the 802.1X model to WiFi
supplicant mobile device (STA)
authenticator access point (AP)
authentication server server application running on the AP
or on a dedicated machine
port logical state implemented in software in the AP
one more thing is added to the basic 802.1X model in
802.11i:
– successful authentication results not only in switching the port on, but
also in a session key between the mobile device and the
authentication server
– the session key is sent to the AP in a secure way
• this assumes a shared key between the AP and the auth server
• this key is usually set up manually
Security and Cooperation in Wireless Networks 1.3.2 WiFi LANs
IEEE 802.11i
41/60
Chapter 1: The security of existing wireless networks
Protocols – EAP, EAPOL, and RADIUS
EAP (Extensible Authentication Protocol) [RFC 3748]
– carrier protocol designed to transport the messages of “real” authentication
protocols (e.g., TLS)
– very simple, four types of messages:
• EAP request – carries messages from the supplicant to the authentication server
• EAP response – carries messages from the authentication server to the supplicant
• EAP success – signals successful authentication
• EAP failure – signals authentication failure
– authenticator doesn’t understand what is inside the EAP messages, it
recognizes only EAP success and failure
EAPOL (EAP over LAN) [802.1X]
– used to encapsulate EAP messages into LAN protocols (e.g., Ethernet)
– EAPOL is used to carry EAP messages between the STA and the AP
RADIUS (Remote Access Dial-In User Service) [RFC 2865-2869, RFC
2548]
– used to carry EAP messages between the AP and the auth server
– MS-MPPE-Recv-Key attribute is used to transport the session key from the
auth server to the AP
– RADIUS is mandated by WPA and optional for RSN
Security and Cooperation in Wireless Networks 1.3.2 WiFi LANs
IEEE 802.11i 42/60
Chapter 1: The security of existing wireless networks
EAP in action
STA encapsulated in EAPOL AP auth server
EAPOL-Start
EAP Request (Identity) encapsulated in RADIUS
EAP Response (Identity) EAP Response (Identity)
EAP Request 1 EAP Request 1
embedded auth. protocol
EAP Response 1 EAP Response 1
...
...
EAP Request n EAP Request n
EAP Response n EAP Response n
EAP Success
EAP Success
Security and Cooperation in Wireless Networks 1.3.2 WiFi LANs
IEEE 802.11i
43/60
Chapter 1: The security of existing wireless networks
Protocols – LEAP, EAP-TLS, PEAP, EAP-SIM
LEAP (Light EAP)
– developed by Cisco
– similar to MS-CHAP extended with session key transport
EAP-TLS (TLS over EAP)
– only the TLS Handshake Protocol is used
– server and client authentication, generation of master secret
– TLS maser secret becomes the session key
– mandated by WPA, optional in RSN
PEAP (Protected EAP)
– phase 1: TLS Handshake without client authentication
– phase 2: client authentication protected by the secure channel established in phase 1
EAP-SIM
– extended GSM authentication in WiFi context
– protocol (simplified) :
STA AP: EAP res ID ( IMSI / pseudonym )
STA AP: EAP res ( nonce )
AP: [gets two auth triplets from the mobile operator’s AuC]
AP STA: EAP req ( 2*RAND | MIC2*Kc | {new pseudonym}2*Kc )
STA AP: EAP res ( 2*SRES )
AP STA: EAP success
Security and Cooperation in Wireless Networks 1.3.2 WiFi LANs
IEEE 802.11i
44/60
Chapter 1: The security of existing wireless networks
Summary of the protocol architecture
TLS (RFC 2246)
EAP-TLS (RFC 2716)
EAP (RFC 3748)
EAPOL (802.1X) EAP over RADIUS (RFC 3579)
802.11 RADIUS (RFC 2865)
TCP/IP
802.3 or else
mobile device AP auth server
Security and Cooperation in Wireless Networks 1.3.2 WiFi LANs
IEEE 802.11i
45/60
Chapter 1: The security of existing wireless networks
Key hierarchies
802.1X authentication random generation
in AP
PMK (pairwise master key) GMK (group master key)
key derivation key derivation
in STA and AP in AP
PTK (pairwise transient keys): GTK (group transient keys):
- key encryption key - group encryption key
- key integrity key - group integrity key
protection
- data encryption key
- data integrity key transport
to every STA
(128 bits each)
protection
protection
unicast message trans. broadcast messages trans.
between STA and AP from AP to STAs
Security and Cooperation in Wireless Networks 1.3.2 WiFi LANs
IEEE 802.11i
46/60
Chapter 1: The security of existing wireless networks
Four-way handshake
objective:
– prove that AP also knows the PMK (result of authentication)
– exchange random values to be used in the generation of PTK
protocol:
AP : generate ANonce
AP STA : ANonce | KeyReplayCtr
STA : generate SNonce and compute PTK
STA AP : SNonce | KeyReplayCtr | MICKIK
AP : compute PTK, generate GTK, and verify MIC
AP STA : ANonce | KeyReplayCtr+1 | {GTK}KEK | MICKIK
STA : verify MIC and install keys
STA AP : KeyReplayCtr+1 | MICKIK
AP : verify MIC and install keys
MICKIK : Message Integrity Code (computed by the mobile device using the key-integrity key)
KeyReplayCtr: used to prevent replay attacks
Security and Cooperation in Wireless Networks 1.3.2 WiFi LANs
IEEE 802.11i
47/60
Chapter 1: The security of existing wireless networks
PTK and GTK computation
for TKIP
PRF-512( PMK,
“Pairwise key expansion”,
MAC1 | MAC2 | Nonce1 | Nonce2 ) =
= KEK | KIK | DEK | DIK
PRF-256( GMK,
“Group key expansion”,
MAC | GNonce ) =
= GEK | GIK
for AES-CCMP
PRF-384( PMK,
“Pairwise key expansion”,
MAC1 | MAC2 | Nonce1 | Nonce2 ) =
= KEK | KIK | DE&IK
PRF-128( GMK,
“Group key expansion”,
MAC | GNonce ) =
= GE&IK
Security and Cooperation in Wireless Networks 1.3.2 WiFi LANs
IEEE 802.11i
48/60
Chapter 1: The security of existing wireless networks
TKIP
runs on old hardware (supporting RC4), but …
WEP weaknesses are corrected
– new message integrity protection mechanism called Michael
• MIC value is added at SDU level before fragmentation into PDUs
• implemented in the device driver (in software)
– use IV as replay counter
– increase IV length to 48 bits in order to prevent IV reuse
– per-packet keys to prevent attacks based on weak keys
Security and Cooperation in Wireless Networks 1.3.2 WiFi LANs
IEEE 802.11i
49/60
Chapter 1: The security of existing wireless networks
TKIP – Generating RC4 keys
48 bits
IV data encryption key from PTK
upper lower
128 bits
32 bits 16 bits
key mix
(phase 1) MAC address
key mix
(phase 2)
dummy byte
IV d IV per-packet key RC4 seed value
3x8 = 24 bits 104 bit
Security and Cooperation in Wireless Networks 1.3.2 WiFi LANs
IEEE 802.11i
50/60
Chapter 1: The security of existing wireless networks
AES-CCMP
CCMP means CTR mode and CBC-MAC
– integrity protection is based on CBC-MAC (using AES)
– encryption is based on CTR mode (using AES)
CBC-MAC
– CBC-MAC is computed over the MAC header, CCMP header, and the MPDU (fragmented
data)
– mutable fields are set to zero
– input is padded with zeros if length is not multiple of 128 (bits)
– CBC-MAC initial block:
• flag (8)
• priority (8)
• source address (48)
• packet number (48)
• data length (16)
– final 128-bit block of CBC encryption is truncated to (upper) 64 bits to get the CBC-
MAC value
CTR mode encryption
– MPDU and CBC-MAC value is encrypted, MAC and CCMP headers are not
– format of the counter is similar to the CBC-MAC initial block
• “data length” is replaced by “counter”
• counter is initialized with 1 and incremented after each encrypted block
Security and Cooperation in Wireless Networks 1.3.2 WiFi LANs
IEEE 802.11i
51/60
Chapter 1: The security of existing wireless networks
Summary on WiFi security
security has always been considered important for WiFi
early solution was based on WEP
– seriously flawed
– not recommended to use
the new security standard for WiFi is 802.11i
– access control model is based on 802.1X
– flexible authentication based on EAP and upper layer authentication
protocols (e.g., TLS, GSM authentication)
– improved key management
– TKIP
• uses RC4 runs on old hardware
• corrects WEP’s flaws
• mandatory in WPA, optional in RSN (WPA2)
– AES-CCMP
• uses AES in CCMP mode (CTR mode and CBC-MAC)
• needs new hardware that supports AES
Security and Cooperation in Wireless Networks 1.3.2 WiFi LANs
IEEE 802.11i
52/60
Chapter 1: The security of existing wireless networks
Chapter outline
1.3.1 Cellular networks
1.3.2 WiFi LANs
1.3.3 Bluetooth
Security and Cooperation in Wireless Networks
53/60
Chapter 1: The security of existing wireless networks
Bluetooth
Short-range communications, master-slave principle
Eavesdropping is difficult:
– Frequency hopping
– Communication is over a few meters only
Security issues:
– Authentication of the devices to each other
– Confidential channel
based on secret link key
Security and Cooperation in Wireless Networks 1.3.3 Bluetooth 54/60
Chapter 1: The security of existing wireless networks
Bluetooth
When two devices communicate for the first time:
– Set up the temporary initialization key.
Security and Cooperation in Wireless Networks 1.3.3 Bluetooth 55/60
Chapter 1: The security of existing wireless networks
Bluetooth
Setting up the link key:
Security and Cooperation in Wireless Networks 1.3.3 Bluetooth 56/60
Chapter 1: The security of existing wireless networks
Bluetooth
The authentication protocol:
Security and Cooperation in Wireless Networks 1.3.3 Bluetooth 57/60
Chapter 1: The security of existing wireless networks
Bluetooth
Generation of the encryption key and the key stream:
Security and Cooperation in Wireless Networks 1.3.3 Bluetooth 58/60
Chapter 1: The security of existing wireless networks
Weaknesses
The strength of the whole system is based on the strength of
the PIN:
– PIN: 4-digit number, easy to try all 10000 possible values.
– PIN can be cracked off-line.
– many devices use the default PIN.
For memory-constrained devices: the link key = the long-
term unit key of the device.
Fixed and unique device addresses: privacy problem.
Weaknesses in the E0 stream cipher.
Security and Cooperation in Wireless Networks 1.3.3 Bluetooth 59/60
Chapter 1: The security of existing wireless networks
Conclusion
Security issues of wireless networks:
– wireless channel: easy to eavesdrop on, jam, overuse
– Users: usually mobile
Classical requirements:
– authentication, confidentiality, integrity, availability
Location privacy: unique to mobile networks.
Mobile devices:
– Limited resources
– Lack of physical protection
roaming of users across different networks
Security and Cooperation in Wireless Networks
60/60
Chapter 1: The security of existing wireless networks
S-ar putea să vă placă și
- The Yellow House: A Memoir (2019 National Book Award Winner)De la EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Evaluare: 4 din 5 stele4/5 (98)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeDe la EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeEvaluare: 4 din 5 stele4/5 (5795)
- Shoe Dog: A Memoir by the Creator of NikeDe la EverandShoe Dog: A Memoir by the Creator of NikeEvaluare: 4.5 din 5 stele4.5/5 (537)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureDe la EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureEvaluare: 4.5 din 5 stele4.5/5 (474)
- Grit: The Power of Passion and PerseveranceDe la EverandGrit: The Power of Passion and PerseveranceEvaluare: 4 din 5 stele4/5 (588)
- On Fire: The (Burning) Case for a Green New DealDe la EverandOn Fire: The (Burning) Case for a Green New DealEvaluare: 4 din 5 stele4/5 (74)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryDe la EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryEvaluare: 3.5 din 5 stele3.5/5 (231)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceDe la EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceEvaluare: 4 din 5 stele4/5 (895)
- Never Split the Difference: Negotiating As If Your Life Depended On ItDe la EverandNever Split the Difference: Negotiating As If Your Life Depended On ItEvaluare: 4.5 din 5 stele4.5/5 (838)
- The Little Book of Hygge: Danish Secrets to Happy LivingDe la EverandThe Little Book of Hygge: Danish Secrets to Happy LivingEvaluare: 3.5 din 5 stele3.5/5 (400)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersDe la EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersEvaluare: 4.5 din 5 stele4.5/5 (345)
- The Unwinding: An Inner History of the New AmericaDe la EverandThe Unwinding: An Inner History of the New AmericaEvaluare: 4 din 5 stele4/5 (45)
- Team of Rivals: The Political Genius of Abraham LincolnDe la EverandTeam of Rivals: The Political Genius of Abraham LincolnEvaluare: 4.5 din 5 stele4.5/5 (234)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyDe la EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyEvaluare: 3.5 din 5 stele3.5/5 (2259)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaDe la EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaEvaluare: 4.5 din 5 stele4.5/5 (266)
- The Emperor of All Maladies: A Biography of CancerDe la EverandThe Emperor of All Maladies: A Biography of CancerEvaluare: 4.5 din 5 stele4.5/5 (271)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreDe la EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreEvaluare: 4 din 5 stele4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)De la EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Evaluare: 4.5 din 5 stele4.5/5 (121)
- Her Body and Other Parties: StoriesDe la EverandHer Body and Other Parties: StoriesEvaluare: 4 din 5 stele4/5 (821)
- Openssl Commands To Convert Certificate FormatDocument3 paginiOpenssl Commands To Convert Certificate FormatrajeshÎncă nu există evaluări
- CRY303c PE Solution Spring22Document2 paginiCRY303c PE Solution Spring22Dao Manh Cong (K16HL)Încă nu există evaluări
- Block Chain SetDocument9 paginiBlock Chain Setakshay BaleshgolÎncă nu există evaluări
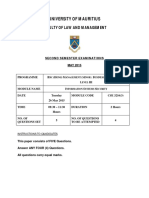
- University of Mauritius: Faculty of Law and ManagementDocument3 paginiUniversity of Mauritius: Faculty of Law and ManagementDeep ShiÎncă nu există evaluări
- Chapter 2lecture02Document52 paginiChapter 2lecture02Tomas AgonaferÎncă nu există evaluări
- Unit3 CryptographyDocument87 paginiUnit3 CryptographyRαndσm thíngsÎncă nu există evaluări
- Computer Network Security: P.S.Dhekne BarcDocument41 paginiComputer Network Security: P.S.Dhekne BarcAnil BatraÎncă nu există evaluări
- Principles of Information SecurityDocument23 paginiPrinciples of Information SecurityDinesh R RdxÎncă nu există evaluări
- Get VPN ConceptsDocument3 paginiGet VPN ConceptsAnsan Sport KeralaÎncă nu există evaluări
- Ayan Roy (Cryptography - & - Network - Security)Document8 paginiAyan Roy (Cryptography - & - Network - Security)ayan royÎncă nu există evaluări
- OPC Unified Architecture Specification Part 2 - Security Model Version 1.00Document30 paginiOPC Unified Architecture Specification Part 2 - Security Model Version 1.00Sandra BravoÎncă nu există evaluări
- Software Requirement SpecificationDocument8 paginiSoftware Requirement SpecificationPrashant TodkarÎncă nu există evaluări
- Solving Section I PDFDocument10 paginiSolving Section I PDFMehdi WalkerÎncă nu există evaluări
- CNS QBDocument10 paginiCNS QBঅচেনাআবিরÎncă nu există evaluări
- Data Encryption StandardDocument15 paginiData Encryption Standardabcdas kaÎncă nu există evaluări
- Ebook Cissp Passport 2 Full Chapter PDFDocument67 paginiEbook Cissp Passport 2 Full Chapter PDFgerald.loesch285100% (27)
- Seminar Report RSADocument45 paginiSeminar Report RSAcharchit99Încă nu există evaluări
- CS409 Cryptography and Network Security, December 2018 PDFDocument2 paginiCS409 Cryptography and Network Security, December 2018 PDFReshma SindhuÎncă nu există evaluări
- Audio EncryptionDocument11 paginiAudio EncryptionMainak PaulÎncă nu există evaluări
- DartDocument3 paginiDartAndrei StefanÎncă nu există evaluări
- Creptography: Student Name: Student IDDocument6 paginiCreptography: Student Name: Student IDManal FaluojiÎncă nu există evaluări
- Cryptography With Python TutorialDocument83 paginiCryptography With Python TutorialSunendran Shanmuganathan100% (1)
- AadhaarDocument1 paginăAadhaarsahil sukhsainiÎncă nu există evaluări
- Chapter 17 SlidesDocument19 paginiChapter 17 SlidesLipsa SahooÎncă nu există evaluări
- Green Book 7edDocument198 paginiGreen Book 7edAjith UtilityÎncă nu există evaluări
- (Slides) Authenticated Encryption GCM - CCMDocument48 pagini(Slides) Authenticated Encryption GCM - CCMProject Symphony Collection100% (1)
- Applied Cryptography and Network SecurityDocument715 paginiApplied Cryptography and Network SecurityzxarisÎncă nu există evaluări
- AdvantagesDocument1 paginăAdvantagesRushad WankadiaÎncă nu există evaluări
- An Efficient AES and Blowfish Based Video Data EncryptionDocument6 paginiAn Efficient AES and Blowfish Based Video Data EncryptionKrishnamoorthy KumarÎncă nu există evaluări
- Course: Cryptography Code: CS-21123 Branch: M.Tech - IS 1 SemesterDocument28 paginiCourse: Cryptography Code: CS-21123 Branch: M.Tech - IS 1 SemesterManish BarlaÎncă nu există evaluări