Documente Academic
Documente Profesional
Documente Cultură
Lesson 1493761882
Încărcat de
santhi saranya0 evaluări0% au considerat acest document util (0 voturi)
23 vizualizări1 paginăThis document outlines a lesson plan for a computer security course taught over 4 modules across 14 weeks. The plan covers topics such as types of threats and vulnerabilities, encryption standards, program and operating system security, database security, network security, and administrative security practices. Specific techniques covered include substitution ciphers, transposition ciphers, DES, AES, RSA, user authentication, firewalls, and intrusion detection systems. The plan aims to teach students the meaning and goals of computer security, as well as technical and policy-based approaches to protecting computer systems and data.
Descriere originală:
Lesson 1493761882
Drepturi de autor
© © All Rights Reserved
Formate disponibile
PDF, TXT sau citiți online pe Scribd
Partajați acest document
Partajați sau inserați document
Vi se pare util acest document?
Este necorespunzător acest conținut?
Raportați acest documentThis document outlines a lesson plan for a computer security course taught over 4 modules across 14 weeks. The plan covers topics such as types of threats and vulnerabilities, encryption standards, program and operating system security, database security, network security, and administrative security practices. Specific techniques covered include substitution ciphers, transposition ciphers, DES, AES, RSA, user authentication, firewalls, and intrusion detection systems. The plan aims to teach students the meaning and goals of computer security, as well as technical and policy-based approaches to protecting computer systems and data.
Drepturi de autor:
© All Rights Reserved
Formate disponibile
Descărcați ca PDF, TXT sau citiți online pe Scribd
0 evaluări0% au considerat acest document util (0 voturi)
23 vizualizări1 paginăLesson 1493761882
Încărcat de
santhi saranyaThis document outlines a lesson plan for a computer security course taught over 4 modules across 14 weeks. The plan covers topics such as types of threats and vulnerabilities, encryption standards, program and operating system security, database security, network security, and administrative security practices. Specific techniques covered include substitution ciphers, transposition ciphers, DES, AES, RSA, user authentication, firewalls, and intrusion detection systems. The plan aims to teach students the meaning and goals of computer security, as well as technical and policy-based approaches to protecting computer systems and data.
Drepturi de autor:
© All Rights Reserved
Formate disponibile
Descărcați ca PDF, TXT sau citiți online pe Scribd
Sunteți pe pagina 1din 1
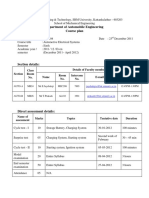
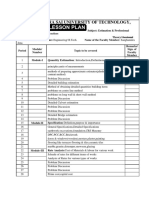
Lesson Teaching Plan
Subject: Computer Security Branch: MCA
Semester: 5th Faculty Name: Sucheta Panda
Module Topic No. of Classes
1. Meaning of Computer Security, Security Problem 1
2. Kinds of Vulnerability, Threats 1
3. Types of Threats, Method, Opportunity and Motive 1
I 4. Security goal and Computer Criminal 1
5. Ethical and Legal Issues 1
6. Cryptanalysis, Cryptology, Plain text, Cipher text 1
7. Substitution cipher, Examples additive cipher, mono-alphabetic cipher 2
8. Transposition cipher, Rail-fence Cipher, Hill Cipher 1
9. Data Encryption Standard, Design issues, Security in DES, Double and 2
Triple DES, Weakness in DES
10. AES Encryption Standard, Design issues, Difference between AES 2
and DES
11. Public and private key encryption, Uses of encryption 1
12. RSA algorithm for encryption 1
1. Program Security, Secure Programs 1
2. Non-malicious Program Errors, Viruses 1
3. Other malicious codes, Targeted Malicious code 1
4. Controls against program Threats 1
5. Protection, General-purpose Operating System protected objects 1
6. Methods of protection memory 1
II 7. Addmens Protection, File Protection mechanisms 2
8. User Authentication, Designing Trusted O.S. 1
9. Security Policies, models of security 1
10. Trusted O.S. design 1
11. Assurance in trusted O.S. 1
12. Implementation examples 1
1. Database Security, Security requirements 1
2. Reliability and Integrity 1
3. Sensitive data, Inference 1
III 4. Multilevel database 1
5. Proposals for multilevel security 1
6. Security in Network 1
7. Network Security controls, Firewalls 2
8. Intrusion Detection systems 1
9. Secure E-mail 1
10. Threats in network 1
1. Administering Security 1
2. Security Planning 1
3. Risk Analysis 1
IV 4. Organizational Security policies 1
5. Physical Security 1
6. Legal Privacy and Ethical Issues in Computer security 1
7. Protecting program and data 1
S-ar putea să vă placă și
- Computer Security Lecture Plan MCA-505: Unit Topic Hours RequiredDocument2 paginiComputer Security Lecture Plan MCA-505: Unit Topic Hours RequiredAnonymous nDBwyakhÎncă nu există evaluări
- Jntuh College of Engineering Hyderabad Dept of Computer Science and EngineeringDocument4 paginiJntuh College of Engineering Hyderabad Dept of Computer Science and EngineeringsidÎncă nu există evaluări
- System SecurityDocument4 paginiSystem SecurityTanishka MayekarÎncă nu există evaluări
- Internship Weekly ReportDocument6 paginiInternship Weekly Reportmrharshilpatel8802Încă nu există evaluări
- Cyber Security LectureDocument2 paginiCyber Security LectureSayan MajumderÎncă nu există evaluări
- W.E.F Academic Year 2012-13 G' SchemeDocument5 paginiW.E.F Academic Year 2012-13 G' SchemeSanket bhosaleÎncă nu există evaluări
- CNCS2004-Cybersecurity SyllabusDocument3 paginiCNCS2004-Cybersecurity SyllabusZoyaÎncă nu există evaluări
- William Stallings - Cryptography and Network Security - Chap1 (2022)Document23 paginiWilliam Stallings - Cryptography and Network Security - Chap1 (2022)muhammad moazzamÎncă nu există evaluări
- Notes For Cyber Information Security NotesDocument191 paginiNotes For Cyber Information Security Notesmohd mursleenÎncă nu există evaluări
- Course OutlineDocument3 paginiCourse OutlineFasiledesÎncă nu există evaluări
- CCISO Certified Chief Information Security Officer All-In-One Exam GuideDocument862 paginiCCISO Certified Chief Information Security Officer All-In-One Exam Guideamin jahromi100% (1)
- Information Security: Dr. Pranita UpadhyayaDocument35 paginiInformation Security: Dr. Pranita UpadhyayaMANOJÎncă nu există evaluări
- Is Scouse Outline VFDocument4 paginiIs Scouse Outline VFMuller MuleyÎncă nu există evaluări
- Cyber Security: Professional Diploma inDocument5 paginiCyber Security: Professional Diploma inAnshpreet SinghÎncă nu există evaluări
- Contact Information:: Security Blue Team Blue Team Level 1 Certification Syllabus v1Document8 paginiContact Information:: Security Blue Team Blue Team Level 1 Certification Syllabus v1HelloÎncă nu există evaluări
- Cciso Certified Chief Information Security Officer All in One Exam Guide Steve Bennett Full ChapterDocument67 paginiCciso Certified Chief Information Security Officer All in One Exam Guide Steve Bennett Full Chapterwanda.dahl659100% (3)
- CSCU Exam Blueprint v1 PDFDocument3 paginiCSCU Exam Blueprint v1 PDFIT EXPERT BDÎncă nu există evaluări
- IT 513 Course OutlineDocument4 paginiIT 513 Course OutlineWaleed HussainÎncă nu există evaluări
- B.Tech. Computer: Uka Tarsadia UniversityDocument6 paginiB.Tech. Computer: Uka Tarsadia UniversityPatelÎncă nu există evaluări
- CSCU Exam Blueprint v3Document3 paginiCSCU Exam Blueprint v3tanifahniatiÎncă nu există evaluări
- Information SecurityDocument205 paginiInformation SecurityM.I.M KRUPHAÎncă nu există evaluări
- Information Security NotesDocument217 paginiInformation Security NotesAbhinav Dixit100% (6)
- UNIT - I & II - 3R-Cryptography-Lectures - 2021-22 - VSMDocument133 paginiUNIT - I & II - 3R-Cryptography-Lectures - 2021-22 - VSMpubgÎncă nu există evaluări
- Cryptography and Network SecurityDocument2 paginiCryptography and Network SecurityVishwa Pratap SinghÎncă nu există evaluări
- UT Dallas Syllabus For cs6324.001 05f Taught by Hsingmean Sha (Edsha)Document3 paginiUT Dallas Syllabus For cs6324.001 05f Taught by Hsingmean Sha (Edsha)UT Dallas Provost's Technology GroupÎncă nu există evaluări
- It SpacDocument18 paginiIt Spacshiva kumarÎncă nu există evaluări
- Course Plan Information SecurityDocument7 paginiCourse Plan Information SecurityMalik KashifÎncă nu există evaluări
- Cybersecurity TermDocument2 paginiCybersecurity TermVishal PatilÎncă nu există evaluări
- 1 - Monitoring and Diagnosing Networks TerminologyDocument17 pagini1 - Monitoring and Diagnosing Networks TerminologyAntonio SodréÎncă nu există evaluări
- Unit 1 Information Security Concerns: Structure 1.1 1.2 1.3Document20 paginiUnit 1 Information Security Concerns: Structure 1.1 1.2 1.3Mr. MANTRAÎncă nu există evaluări
- CTIA Exam Blueprint v1Document13 paginiCTIA Exam Blueprint v1AlbertÎncă nu există evaluări
- App inDocument1 paginăApp inAamir AkhtarÎncă nu există evaluări
- 12 December 2010 - E-Commerce Security Challenges and SolutionsDocument50 pagini12 December 2010 - E-Commerce Security Challenges and Solutionstalals90Încă nu există evaluări
- Intro Week 2Document11 paginiIntro Week 2Gopi Krishna PittuÎncă nu există evaluări
- Week 2 Intro HijackingDocument56 paginiWeek 2 Intro Hijackingyasmin karaÎncă nu există evaluări
- Week 1 Lecture 1 Information SecurityDocument28 paginiWeek 1 Lecture 1 Information SecurityZulkifl HasanÎncă nu există evaluări
- DNN DPCS Webinar (4) Security 101Document12 paginiDNN DPCS Webinar (4) Security 101Chen MichaelÎncă nu există evaluări
- Add Structure and Credibility To Your Security Portfolio With CIS Controls v8 Cybersecurity FrameworkDocument55 paginiAdd Structure and Credibility To Your Security Portfolio With CIS Controls v8 Cybersecurity FrameworkLâm Hữu TiếnÎncă nu există evaluări
- Ebook Computer and Information Security Handbook PDF Full Chapter PDFDocument77 paginiEbook Computer and Information Security Handbook PDF Full Chapter PDFclara.hem799100% (26)
- Syllabus For Diploma in Cyber SecurityDocument4 paginiSyllabus For Diploma in Cyber SecurityppghoshinÎncă nu există evaluări
- Security Concept - Chapter 6Document20 paginiSecurity Concept - Chapter 6Muhammad AyAzÎncă nu există evaluări
- Cryptography and System SecurityDocument3 paginiCryptography and System SecurityNirishÎncă nu există evaluări
- Ite4001 Network-And-Information-security Eth 1.1 47 Ite4001Document2 paginiIte4001 Network-And-Information-security Eth 1.1 47 Ite4001Vivek GopalshettyÎncă nu există evaluări
- Ite4001 Network-And-Information-security Eth 1.1 47 Ite4001Document2 paginiIte4001 Network-And-Information-security Eth 1.1 47 Ite4001Prateek AgarwalÎncă nu există evaluări
- Unit 1Document18 paginiUnit 1shikshj9Încă nu există evaluări
- Computer SecurityDocument519 paginiComputer SecurityGyan RanjanÎncă nu există evaluări
- Computer and Information Security Handbook John R Vacca Full ChapterDocument67 paginiComputer and Information Security Handbook John R Vacca Full Chapterstacy.merlette128100% (4)
- Information AssuranceDocument7 paginiInformation Assurancelols14029Încă nu există evaluări
- Professional Elective: Cryptography & Network SecurityDocument2 paginiProfessional Elective: Cryptography & Network SecurityDinesh RathiÎncă nu există evaluări
- Cybersecurity Professional Training PDFDocument2 paginiCybersecurity Professional Training PDFTester MaheÎncă nu există evaluări
- Week 6 - WatermarkDocument146 paginiWeek 6 - Watermarkshailesh karthikÎncă nu există evaluări
- Internet Security E-BookDocument128 paginiInternet Security E-BookMONIKA R PSGRKCWÎncă nu există evaluări
- Exam Questions Computer Systems Information SecurityDocument1 paginăExam Questions Computer Systems Information SecurityAbbas ElouzeirÎncă nu există evaluări
- Layers of Cyber Security FinalDocument9 paginiLayers of Cyber Security FinalSyed SalmanÎncă nu există evaluări
- IT502 - Information SecurityDocument3 paginiIT502 - Information SecurityNader AzalÎncă nu există evaluări
- Strawman IASDocument12 paginiStrawman IASwallofkleinÎncă nu există evaluări
- Instructional Resoure #1 PDFDocument48 paginiInstructional Resoure #1 PDFRex YMÎncă nu există evaluări
- Security for Small Computer Systems: A Practical Guide for UsersDe la EverandSecurity for Small Computer Systems: A Practical Guide for UsersTricia SaddingtonÎncă nu există evaluări
- Computer and Information Security HandbookDe la EverandComputer and Information Security HandbookEvaluare: 2.5 din 5 stele2.5/5 (4)
- Mastering Cyber Security A Comprehensive Guide: cyber security, #2De la EverandMastering Cyber Security A Comprehensive Guide: cyber security, #2Încă nu există evaluări
- Btech Vi Sem 15ce347eDocument2 paginiBtech Vi Sem 15ce347esanthi saranyaÎncă nu există evaluări
- BT1001 Biology For Engineers1Document3 paginiBT1001 Biology For Engineers1santhi saranyaÎncă nu există evaluări
- Course Code: CH1106 Course Title: Introduction To Biochemical Principles Semester: Course Time: Jan - MayDocument4 paginiCourse Code: CH1106 Course Title: Introduction To Biochemical Principles Semester: Course Time: Jan - Maysanthi saranyaÎncă nu există evaluări
- Introduction To Biochemical Principles 2013 2014Document4 paginiIntroduction To Biochemical Principles 2013 2014santhi saranyaÎncă nu există evaluări
- Btech VI Sem 15ce347e PDFDocument3 paginiBtech VI Sem 15ce347e PDFsanthi saranyaÎncă nu există evaluări
- Department of Automobile Engineering Course PlanDocument4 paginiDepartment of Automobile Engineering Course Plansanthi saranyaÎncă nu există evaluări
- BT1001 Biology For Engineers PDFDocument2 paginiBT1001 Biology For Engineers PDFsanthi saranyaÎncă nu există evaluări
- Ar 15201 Building Materials Ii (3-0-0-0) CR-03Document3 paginiAr 15201 Building Materials Ii (3-0-0-0) CR-03santhi saranyaÎncă nu există evaluări
- BT1001 Biology For Engineers 2 PDFDocument2 paginiBT1001 Biology For Engineers 2 PDFsanthi saranyaÎncă nu există evaluări
- Department of Automobile Engineering Course PlanDocument4 paginiDepartment of Automobile Engineering Course Plansanthi saranyaÎncă nu există evaluări
- Department of Automobile Engineering Course PlanDocument4 paginiDepartment of Automobile Engineering Course Plansanthi saranyaÎncă nu există evaluări
- Veer Surendra Sai University of Technology, Burla: Lesson PlanDocument2 paginiVeer Surendra Sai University of Technology, Burla: Lesson Plansanthi saranyaÎncă nu există evaluări
- Veer Surendra Sai University of Technology, Burla: Lesson PlanDocument2 paginiVeer Surendra Sai University of Technology, Burla: Lesson Plansanthi saranyaÎncă nu există evaluări
- Veer Surendra Sai University of Technology, Burla: Lesson PlanDocument1 paginăVeer Surendra Sai University of Technology, Burla: Lesson Plansanthi saranyaÎncă nu există evaluări
- Lesson1499214383 PDFDocument2 paginiLesson1499214383 PDFsanthi saranyaÎncă nu există evaluări
- Ar 15203 History of Architecture I (3-0-0-0) CR-03Document2 paginiAr 15203 History of Architecture I (3-0-0-0) CR-03santhi saranyaÎncă nu există evaluări
- Veer Surendra Sai University of Technology, Burla: Lesson PlanDocument2 paginiVeer Surendra Sai University of Technology, Burla: Lesson Plansanthi saranyaÎncă nu există evaluări
- Veer Surendra Sai University of Technology, Burla Lesson PlanDocument2 paginiVeer Surendra Sai University of Technology, Burla Lesson Plansanthi saranyaÎncă nu există evaluări
- Veer Surendra Sai University of Technology, Burla Lesson PlanDocument1 paginăVeer Surendra Sai University of Technology, Burla Lesson Plansanthi saranyaÎncă nu există evaluări
- Veer Surendra Sai University of Technology, Burla Lesson PlanDocument1 paginăVeer Surendra Sai University of Technology, Burla Lesson Plansanthi saranyaÎncă nu există evaluări
- Lesson Plan: Veer Surendra Sai University of Technology, BurlaDocument2 paginiLesson Plan: Veer Surendra Sai University of Technology, Burlasanthi saranyaÎncă nu există evaluări
- Lesson Plan: Veer Surendra Sai University of Technology, BurlaDocument2 paginiLesson Plan: Veer Surendra Sai University of Technology, Burlasanthi saranyaÎncă nu există evaluări
- Veer Surendra Sai University of Technology, Burla Lesson PlanDocument1 paginăVeer Surendra Sai University of Technology, Burla Lesson Plansanthi saranyaÎncă nu există evaluări
- Veer Surendra Sai University of Technology, Burla Lesson PlanDocument2 paginiVeer Surendra Sai University of Technology, Burla Lesson Plansanthi saranyaÎncă nu există evaluări
- Veer Surendra Sai University of Technology, Burla Lesson PlanDocument2 paginiVeer Surendra Sai University of Technology, Burla Lesson Plansanthi saranyaÎncă nu există evaluări
- Veer Surendra Sai University of Technology, Burla Lesson PlanDocument1 paginăVeer Surendra Sai University of Technology, Burla Lesson Plansanthi saranyaÎncă nu există evaluări
- Veer Surendra Sai University of Technology, Burla Lesson PlanDocument1 paginăVeer Surendra Sai University of Technology, Burla Lesson Plansanthi saranyaÎncă nu există evaluări
- Veer Surendra Sai University of Technology, Burla Lesson PlanDocument1 paginăVeer Surendra Sai University of Technology, Burla Lesson Plansanthi saranyaÎncă nu există evaluări
- Veer Surendra Sai University of Technology, Burla Lesson PlanDocument1 paginăVeer Surendra Sai University of Technology, Burla Lesson Plansanthi saranyaÎncă nu există evaluări
- Veer Surendra Sai University of Technology, Burla: Quantity Estimation: Introduction, Definitions & Terms UsedDocument2 paginiVeer Surendra Sai University of Technology, Burla: Quantity Estimation: Introduction, Definitions & Terms Usedsanthi saranyaÎncă nu există evaluări
- JetpackCompose NavigationDocument58 paginiJetpackCompose NavigationMarijan JurešićÎncă nu există evaluări
- 01 00 Stud PDFDocument320 pagini01 00 Stud PDFflotudÎncă nu există evaluări
- Title of The Project: Help DeskDocument4 paginiTitle of The Project: Help DeskSriram SridharÎncă nu există evaluări
- How To Integrate Visual Paradigm With Netbeans: InstallationDocument14 paginiHow To Integrate Visual Paradigm With Netbeans: InstallationNguyễn Cửu HưngÎncă nu există evaluări
- APPLICATIONS OF IOT in SMART WearablesDocument6 paginiAPPLICATIONS OF IOT in SMART WearablesLegendÎncă nu există evaluări
- Risk Management Roles and ResponsibilitiesDocument2 paginiRisk Management Roles and ResponsibilitiesOmnia HassanÎncă nu există evaluări
- Databases Integration With ARCGISDocument12 paginiDatabases Integration With ARCGISHatem HelmyÎncă nu există evaluări
- câu hỏi ôn tập - đềDocument16 paginicâu hỏi ôn tập - đề21110294Încă nu există evaluări
- MTATT2017c4 PDFDocument340 paginiMTATT2017c4 PDFjoelbravobritoÎncă nu există evaluări
- PrashantGirase ResumeDocument3 paginiPrashantGirase Resumevyom saxenaÎncă nu există evaluări
- Comparing Leading Cloud Service ProvidersDocument2 paginiComparing Leading Cloud Service Providersharshaks116Încă nu există evaluări
- Win InetDocument207 paginiWin InetAndreiRaduPoleacuÎncă nu există evaluări
- AZ 900 Ver9Document159 paginiAZ 900 Ver9praveen kumarÎncă nu există evaluări
- UntitledDocument4 paginiUntitledsamÎncă nu există evaluări
- Practical Guide To Securing Work From Anywhere Using Microsoft 365 Business PremiumDocument28 paginiPractical Guide To Securing Work From Anywhere Using Microsoft 365 Business PremiumPedro Palmeira RochaÎncă nu există evaluări
- Operations Transformation: Key For A Consistent Customer Experience in Next-Generation NetworksDocument17 paginiOperations Transformation: Key For A Consistent Customer Experience in Next-Generation NetworksM AhmedÎncă nu există evaluări
- TCP2201 Object Oriented Analysis and Design SESSION 3 2017/18 Group AssignmentDocument3 paginiTCP2201 Object Oriented Analysis and Design SESSION 3 2017/18 Group AssignmentTvyan RaajÎncă nu există evaluări
- Zero Trust Security: Gowdhaman JothilingamDocument19 paginiZero Trust Security: Gowdhaman JothilingamImran ChowdhuryÎncă nu există evaluări
- Case Study On Bay Networks IncDocument2 paginiCase Study On Bay Networks IncAbhishekKaushik100% (3)
- YouTube Data Analysis Using HadoopDocument64 paginiYouTube Data Analysis Using HadoopG JhaÎncă nu există evaluări
- SAM Entity Administrator Letter Template3 International No Banking InfoDocument3 paginiSAM Entity Administrator Letter Template3 International No Banking InfoNEHEMIA MANUCDUCÎncă nu există evaluări
- Best Digital Marketing Company in ChennaiDocument12 paginiBest Digital Marketing Company in ChennaiIbrah FathimaÎncă nu există evaluări
- NOREA Privacy Control Framework v1.0Document68 paginiNOREA Privacy Control Framework v1.0saf100% (1)
- Expert Coaching CatalogDocument30 paginiExpert Coaching Catalogsmart rajÎncă nu există evaluări
- Azure - Unit 4Document13 paginiAzure - Unit 4210303124128Încă nu există evaluări
- User Manual For: Online Application Process in Swami Vivekananda Merit Cum Means Scholarship (V3.0)Document28 paginiUser Manual For: Online Application Process in Swami Vivekananda Merit Cum Means Scholarship (V3.0)sujit patraÎncă nu există evaluări
- RMAN ExerciseDocument4 paginiRMAN Exercisemuddasani1986Încă nu există evaluări
- SQL - Guided PracticeDocument11 paginiSQL - Guided PracticeSanjay Raaj100% (1)
- Chapter VDocument125 paginiChapter VEugene San LorenzoÎncă nu există evaluări
- RailwaysDocument39 paginiRailwaysAnagha AvinashÎncă nu există evaluări