Documente Academic
Documente Profesional
Documente Cultură
Issap Mindmap
Încărcat de
deewanandTitlu original
Drepturi de autor
Formate disponibile
Partajați acest document
Partajați sau inserați document
Vi se pare util acest document?
Este necorespunzător acest conținut?
Raportați acest documentDrepturi de autor:
Formate disponibile
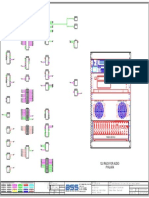
Issap Mindmap
Încărcat de
deewanandDrepturi de autor:
Formate disponibile
Risk Theory
Risk Analysis
Attack by email
Attack by Deception
Hoaxes
Hackers
Web Page Attacks
Attack of the Worms
IRC and P2P
Subject - WHO?
Viruses
Object - WHAT?
Asset and Data Valuation Attack Vectors Write Permission Problem -
Rights (Subject -> the right to create user) - HOW?
give permissions to write
Context and Data Value
Permissions (Subject R/W/X) - HOW? anything, i.e. virus
Corporate vs Departmental Access Control Concepts Access Control List - RWX
Business Legal and Regulatory
Access Control on OSI model
Requirements Read Permission Problem -
TOE
Domain 4 - ACL List subject reads file and create a
Requirements ACL Repository copy of this file with its
EAL Product Assurance Evaluation Criteria Analysis and ownership
CC Assurance Security Standards Mandatory Access control (Labels)
ISO 27000 series 20/02 : 28/02 Limit access to essential objects
Cap ab ility Maturity Mod el 7 workday(s)
Label data
(SEI-CMM)
DAC Implementation Strategie s Filter information
Concept of Layered Architecture
Policy
PCI DSS
Monitoring
Architectural Solutio n
Architecture Frameworks Configuration files
Discretionary Access Control - DAC Windows registry
Department of Defence DoDAF
(Object Owner decides) | evaluates ACL
The Zachman Framework Services
ISO 7 498 series Data
System Security Engineering
Methodology CACLS tool (execute problem) Set all to READ ONLY
Design Validation Block removable media
Certification Access Control Mechanisms Solutions HIDS
Peer Reviews Software integrity inventories
Documentation Monitor execution
RBAC (roles)
Natural
ORCON (contest of the originator is required)
Industry
Risk Analysis DRM (Digital - cryptographic)
Neighbours Non-Discretionary Access Control (more DAC than MAC)
UCON (usage controlled / frequency of access)
Business Impact Analysis
Rule-based (Firewalls / VPNs) |
Data stored in electronic Form
evaluates activity
Remote Replication and Off-site journaling
Least Functionality
Selecting Recovery Strategy
ISSAP
Domain 5 - BCP and DR
Backup Strateg ies Least Privilege (no limitations)
01/03 : 11/03
Implementing Recovery Strateg y 7 workday(s) Separation of Duties
Documenting the Plan
AAA
The Human Factor
Cost-Benefit Analysis Single Sign-On
Logistics
Plan Maintenance
Proxy Access Control
Gatekeeper
Access Control Server
TACACS
Voice Communication Domain 6 - Centralized Access Control RADIUS
Network Architectu r e Telecommunications and
Protocols EAP
Network Design Considerations Network Security
12/03 : 19/03 KERBEROS
6 workday(s)
SESAME
Design Considerations
Domain 1 - Access Architecture
Control Systems
and Methodology
23/01 : 31/01 Distributed | Shared database | Robust | Scalable
7 workday(s) De-centralized Access Control
Design Considerations
Trusted Computing Base
Federated Access Control Design Considerations
Directories and Access Control Design Considerations
Identity Management
Who?What?Where?When?Effec t ?
Accounting
Authorized | Monitored | Validated
Access Control Administration
P2P
Access Control Ad ministration
and Management Concepts Views | Triggers | Stored Procedures
Database Access
Inherent Rights
Change of Privilege Levels
Role based
Groups
Task based
Dual Control
Location
Topology
Subnet
Geo consideration
Physical and Logical
Device types Network based
Third Party Software
Strength and Weaknesses of
Authentication Tools
Badges
Magnetic Strips
Granted Rig hts Token based Authentication Tools
Proximity Cards
Common Issues
Performance
Biometric Authenticatio n Implementation
Common Issues
Authentication Design Validation
Architecture Effectiveness Assurance
Testing Strategies
Testing Objectives
Testing Paradigms
Repeatability
Methodology
Developing Test Procedures
Risk-Based Consideration s
Applications of Cryptography
Message Encryption
Secure IP Communication (IPSEC)
Remote Access
Wireless Communication
Other types of Secure Communication
Identification and Authenticatio n
Storage Encryption
Code Signing
Principles
Symmetric
Block Cipher
Stream Cipher
Methods of Cryptography
Asymmetric
Hash and MAC
Digital Signatures
Key Types
Strength and Key Size
Key Life Cycle
Key Creation
Key Distribution
Key Management Key Storage
Key Update
Domain 2 - Cryptography
Key Revocation
01/02 : 11/02
7 workday(s)
Key Escrow
Backup and Recovery
Key Distribution
Certificates and Key Storage
PKI Registration
Certificate Issuance
Public Key Infrastructure Trust Models
Certificate Chains
Certificate Revocation
Cross Certification
Review of Cryptanalytic Attacks
Design Validation
Risk-Based Cryp tog rap h ic
Architecture
NSA-FIPS-19 7
NSA-FIPS-14 0
Standards
NIST CAVP
NIST CMVP
Cryp tog rap h ic Comp lian ce
PCI DSS
Industry- specific Standards HIPAA
EU Data Protection Act
Roadway Design
Parking
Traffic Monitoring
Open Area Parking
Loading Docks
Infrared Sensors
Microwave
Coaxial Strain-Sensitive Ca b l e
Taut-Wire Systems
Unauthorized access Surveillance Devices Time Domain Reflectometry Systems
CCTV
DVR
Video Content Analysis
Physical Security Risks Guard Force
Card Types
Domain 3 - Physical Security Badge Equipment
11/02 : 19/02 Access Control Systems
7 workday(s) Biometrics
Access control Head-End
Low Profile
Location Hazard
Threat Assessment
Facility Risk Site Planning
Restricted Work Areas
Entrances and Exits
Mobile Devices
Evacuation Drills
Protection Plan Incident Response
Penetration Tests
Design Validation Access Control Violation Monitorin g
ISSAP_map_0113.mmap - 29/01/2013 - Mindjet
S-ar putea să vă placă și
- CCSP Certification Exam OutlineDocument14 paginiCCSP Certification Exam OutlineironmanÎncă nu există evaluări
- ISC - Actualtests.cissp ISSAP.v2015!03!13.by - Adella.237qDocument68 paginiISC - Actualtests.cissp ISSAP.v2015!03!13.by - Adella.237qdeewanandÎncă nu există evaluări
- CCSKdemo PDFDocument16 paginiCCSKdemo PDFBharath ScoÎncă nu există evaluări
- ISSAP EbbokDocument32 paginiISSAP EbbokAntwan BellÎncă nu există evaluări
- CCSK QBDocument25 paginiCCSK QBJorge J. Trujillo RamirezÎncă nu există evaluări
- Unified Threat Detection For AWS Cloud and Containers - CSADocument23 paginiUnified Threat Detection For AWS Cloud and Containers - CSAjelen_againÎncă nu există evaluări
- Cissp-Issap: The Ultimate Guide To TheDocument13 paginiCissp-Issap: The Ultimate Guide To TheFedericoÎncă nu există evaluări
- Issap CibDocument34 paginiIssap CibCoffee GeeÎncă nu există evaluări
- 2021 Cloud Security Report FINALDocument20 pagini2021 Cloud Security Report FINALHabomÎncă nu există evaluări
- Advanced Whiteboard Hacking - Aka Hands-On Threat Modelling: Training Course 30 & 31 of OctoberDocument6 paginiAdvanced Whiteboard Hacking - Aka Hands-On Threat Modelling: Training Course 30 & 31 of OctoberJustin SuthÎncă nu există evaluări
- SANS CISO Scorecard v1.2Document1 paginăSANS CISO Scorecard v1.2Shun KamÎncă nu există evaluări
- CCSKStudy Guide 1Document35 paginiCCSKStudy Guide 1deals4kbÎncă nu există evaluări
- W102 Sabsa Risk Management: Part One - The Meaning of RiskDocument17 paginiW102 Sabsa Risk Management: Part One - The Meaning of Risklalou4Încă nu există evaluări
- Multi-Factor Authentication With ISEDocument4 paginiMulti-Factor Authentication With ISERakesh BadayaÎncă nu există evaluări
- (CISM) Course 1Document137 pagini(CISM) Course 1GAL MORÎncă nu există evaluări
- SABSA IntroductionDocument51 paginiSABSA Introductionbobwillmore100% (1)
- Cissp: The 8 Domains of CISSPDocument52 paginiCissp: The 8 Domains of CISSPLacky KrishnanÎncă nu există evaluări
- CyberSecurity Short Course - Week 3Document46 paginiCyberSecurity Short Course - Week 3tapera_mangeziÎncă nu există evaluări
- UltimateGuideCCSP 2018Document13 paginiUltimateGuideCCSP 2018Manish JoshiÎncă nu există evaluări
- CompTIA Security Test 1Document7 paginiCompTIA Security Test 1annÎncă nu există evaluări
- CCSPDocument4 paginiCCSPlovedeep30Încă nu există evaluări
- CCSK Study GuideDocument37 paginiCCSK Study Guidedeals4kbÎncă nu există evaluări
- NIST Security Reference Architecture 2013.05.15 v1.0Document204 paginiNIST Security Reference Architecture 2013.05.15 v1.0Mariori TrIdiaÎncă nu există evaluări
- Security: The Great Cloud Inhibitor: Brought To You by andDocument4 paginiSecurity: The Great Cloud Inhibitor: Brought To You by anddeals4kbÎncă nu există evaluări
- CISSP Test TemplateDocument37 paginiCISSP Test TemplateRichard WilliamsÎncă nu există evaluări
- SABSA White PaperDocument25 paginiSABSA White PaperMunyaradzi PasinawakoÎncă nu există evaluări
- CCSK sample questionsDocument17 paginiCCSK sample questionsCristian Ezequiel Ibiri0% (1)
- Test 2015 CSSLPDocument158 paginiTest 2015 CSSLPAnonymous prxufEbSÎncă nu există evaluări
- Network SegmentationDocument9 paginiNetwork SegmentationJose Luis GomezÎncă nu există evaluări
- AlgoSec Firewall Analyzer DatasheetDocument2 paginiAlgoSec Firewall Analyzer DatasheetGaston AcevedoÎncă nu există evaluări
- Best Practices For MITRE ATTCK MappingDocument20 paginiBest Practices For MITRE ATTCK MappingEduardo BezerraÎncă nu există evaluări
- SABSA MATRIX ASSETS BUSINESS DECISIONS CONTEXTDocument1 paginăSABSA MATRIX ASSETS BUSINESS DECISIONS CONTEXTEli_HuxÎncă nu există evaluări
- Ec-Council Testinises 312-50v11 Exam Question 2021-Jun-26 by Bartholomew 131q VceDocument18 paginiEc-Council Testinises 312-50v11 Exam Question 2021-Jun-26 by Bartholomew 131q VceYazid BenjamaâÎncă nu există evaluări
- Security Threat and AWS Modeling Project LectureDocument11 paginiSecurity Threat and AWS Modeling Project LectureNopeÎncă nu există evaluări
- Web Application FirewallDocument15 paginiWeb Application FirewallYuvijoeÎncă nu există evaluări
- Key Tables, Charts and Flows For SSCP - CISSPDocument45 paginiKey Tables, Charts and Flows For SSCP - CISSPKevin HuangÎncă nu există evaluări
- Questions: Strong Cloud GovernanceDocument4 paginiQuestions: Strong Cloud GovernanceBrayanÎncă nu există evaluări
- CISSP Skillset OverviewDocument66 paginiCISSP Skillset OverviewicvÎncă nu există evaluări
- CCSKDocument10 paginiCCSKtimelineinfosec1100% (1)
- CISSP - New NotesDocument92 paginiCISSP - New NotesbabuÎncă nu există evaluări
- CCSP Cloud SlidesDocument133 paginiCCSP Cloud Slidesbobwillmore100% (3)
- CCSK notes-MGDocument23 paginiCCSK notes-MGN Sai Avinash100% (1)
- Notes - Ludgenstein - ISC2 Certified Cloud Security Professional (CCSP) - Module 6Document9 paginiNotes - Ludgenstein - ISC2 Certified Cloud Security Professional (CCSP) - Module 6Samir JhaÎncă nu există evaluări
- Continuous Security MonitoringDocument14 paginiContinuous Security Monitoringtavillo1980100% (1)
- ACSC Cyber Incident Response Plan Guidance - A4Document56 paginiACSC Cyber Incident Response Plan Guidance - A4Elena VaciagoÎncă nu există evaluări
- ICSI - CNSS Certified Network Security SpecialistDocument262 paginiICSI - CNSS Certified Network Security Specialistnahid01Încă nu există evaluări
- GIAC CertificationsDocument13 paginiGIAC CertificationsYemi ShowunmiÎncă nu există evaluări
- Application Security Posture Management: Secure Cloud-Native Applications at ScaleDocument27 paginiApplication Security Posture Management: Secure Cloud-Native Applications at ScaleVlad VikernesÎncă nu există evaluări
- CCSK PrepDocument3 paginiCCSK PrepAmr SaidÎncă nu există evaluări
- Cortex XDRDocument6 paginiCortex XDRStacy Marie100% (1)
- Security Orchestration, Automation and Response (SOAR) CapabilitiesDocument17 paginiSecurity Orchestration, Automation and Response (SOAR) CapabilitiesBaatar SukhbaatarÎncă nu există evaluări
- Cism Exam GuideDocument364 paginiCism Exam GuideNyengeterai Mafarachisi100% (1)
- CISSP Exam Study GuideDocument93 paginiCISSP Exam Study Guidedaniel arturo muñoz cordovaÎncă nu există evaluări
- CISSP Session 04Document93 paginiCISSP Session 04wfelicescÎncă nu există evaluări
- MITRE ATT&CK in Amazon Web Services (AWS) :: A Defender's Cheat SheetDocument12 paginiMITRE ATT&CK in Amazon Web Services (AWS) :: A Defender's Cheat SheetKaran OjhaÎncă nu există evaluări
- Secrets Management A Complete Guide - 2019 EditionDe la EverandSecrets Management A Complete Guide - 2019 EditionÎncă nu există evaluări
- Cloud Security Strategy A Complete Guide - 2021 EditionDe la EverandCloud Security Strategy A Complete Guide - 2021 EditionÎncă nu există evaluări
- Cloud Security Compliance A Complete Guide - 2021 EditionDe la EverandCloud Security Compliance A Complete Guide - 2021 EditionÎncă nu există evaluări
- ISO 27001 Documents and Records GuideDocument4 paginiISO 27001 Documents and Records Guidedeewanand60% (5)
- CISSPDocument4 paginiCISSPdeewanandÎncă nu există evaluări
- AES Example - Input (128 bit key and messageDocument17 paginiAES Example - Input (128 bit key and messageVikas PsÎncă nu există evaluări
- Reasons To Become CISSP Certified: Keith A. Watson, CISSP CeriasDocument17 paginiReasons To Become CISSP Certified: Keith A. Watson, CISSP CeriasdeewanandÎncă nu există evaluări
- WP CISSPQuestions PDFDocument7 paginiWP CISSPQuestions PDFAlex DcostaÎncă nu există evaluări
- Cissp TocDocument4 paginiCissp TocVijay ShuklaÎncă nu există evaluări
- Cryptographic Attacks Flash CardsDocument9 paginiCryptographic Attacks Flash CardsdeewanandÎncă nu există evaluări
- WP-Encryption Steps Checklist 060830Document19 paginiWP-Encryption Steps Checklist 060830deewanandÎncă nu există evaluări
- CISSP 2015 Acronyms PDFDocument1 paginăCISSP 2015 Acronyms PDFdeewanandÎncă nu există evaluări
- The Ultimate Network Security ChecklistDocument13 paginiThe Ultimate Network Security ChecklistdeewanandÎncă nu există evaluări
- ISO 27001 Documentation Requirements ListDocument2 paginiISO 27001 Documentation Requirements ListdeewanandÎncă nu există evaluări
- Aaaaaaaaaaaaaaaaaaaa V Qa CCF (Document1 paginăAaaaaaaaaaaaaaaaaaaa V Qa CCF (deewanandÎncă nu există evaluări
- ISO IEC 27001 2013 Translated Into Plain EnglishDocument10 paginiISO IEC 27001 2013 Translated Into Plain Englishdeewanand0% (1)
- Writing Effective Learning Objectives: Digital Education StrategiesDocument4 paginiWriting Effective Learning Objectives: Digital Education Strategieszaruba78Încă nu există evaluări
- ISO 27002 Control Category Changes SummaryDocument8 paginiISO 27002 Control Category Changes SummarybzanajÎncă nu există evaluări
- Writing tools quick referenceDocument1 paginăWriting tools quick referenceNathan BudzinskiÎncă nu există evaluări
- My Gram NotesDocument1 paginăMy Gram NotesdeewanandÎncă nu există evaluări
- 7 QC ToolsDocument1 pagină7 QC ToolsRashid HussainÎncă nu există evaluări
- Using CAATs For Audit of BanksDocument4 paginiUsing CAATs For Audit of BanksRama Komenk DhaniÎncă nu există evaluări
- ArcSight Express - Technical PresentationDocument37 paginiArcSight Express - Technical PresentationdeewanandÎncă nu există evaluări
- QRadar SIEM Product Overview PresentationDocument32 paginiQRadar SIEM Product Overview Presentationdeewanand0% (1)
- 9BMC BPWP Itil Cobit 06Document16 pagini9BMC BPWP Itil Cobit 06Agus PramonoÎncă nu există evaluări
- RTI Manual TeluguDocument212 paginiRTI Manual Telugunmsusarla999Încă nu există evaluări
- MS Telugu Style GuideDocument60 paginiMS Telugu Style Guidedeewanand0% (1)
- Two-Stage-Based Polyphase Structures For Arbitrary-Integer Sampling Rate ConversionDocument5 paginiTwo-Stage-Based Polyphase Structures For Arbitrary-Integer Sampling Rate ConversionAnju BalaÎncă nu există evaluări
- Question & Answers: Certified in Cybersecurity (CC)Document6 paginiQuestion & Answers: Certified in Cybersecurity (CC)ArifÎncă nu există evaluări
- Max target UL interference parameter for E-DCH schedulingDocument3 paginiMax target UL interference parameter for E-DCH schedulingClive MangwiroÎncă nu există evaluări
- A Novel Authentication and Key Agreement Scheme For Internet ofDocument14 paginiA Novel Authentication and Key Agreement Scheme For Internet ofMSAMHOURIÎncă nu există evaluări
- Lithium Reference LetterDocument4 paginiLithium Reference LetterNguyen Ho LongÎncă nu există evaluări
- DNS Behavior With Mediatrix GatewaysDocument10 paginiDNS Behavior With Mediatrix GatewaysSteggosÎncă nu există evaluări
- Drive Test Analysis 1Document16 paginiDrive Test Analysis 1Shashank PrajapatiÎncă nu există evaluări
- Log Units and ApplicationsDocument29 paginiLog Units and ApplicationsShailly KhannaÎncă nu există evaluări
- TFIX-1: Turbine IP66 IEC Ex Intercom Atex Active Noise Cancelling IP Over 2-WireDocument3 paginiTFIX-1: Turbine IP66 IEC Ex Intercom Atex Active Noise Cancelling IP Over 2-WireEhsan RohaniÎncă nu există evaluări
- Lab No. Coverage Experiments: CN-LAB/socket-programming-slides PDFDocument3 paginiLab No. Coverage Experiments: CN-LAB/socket-programming-slides PDFTushar SrivastavaÎncă nu există evaluări
- EMERGENCY PROCEDURES FOR AIRCRAFTDocument24 paginiEMERGENCY PROCEDURES FOR AIRCRAFTdhatasofkaÎncă nu există evaluări
- Week 3 ActivitiesDocument2 paginiWeek 3 ActivitiesDanny MannoÎncă nu există evaluări
- Anti PubgDocument5 paginiAnti PubgQuy HuyÎncă nu există evaluări
- Cisco 642-436 Practice Exam QuestionsDocument150 paginiCisco 642-436 Practice Exam QuestionsTeresia BrownÎncă nu există evaluări
- Implementers Guide: Report Concerning Space Data System StandardsDocument108 paginiImplementers Guide: Report Concerning Space Data System StandardsDwij PatelÎncă nu există evaluări
- 1734UserManual Um011 en PDocument156 pagini1734UserManual Um011 en Pclebeson_pontalÎncă nu există evaluări
- Variable Length Subnet Masking (VLSM) : Samiul Haque SumanDocument12 paginiVariable Length Subnet Masking (VLSM) : Samiul Haque Sumanসামিউল সুমনÎncă nu există evaluări
- PWM Motor Control with dsPIC and MPLABDocument11 paginiPWM Motor Control with dsPIC and MPLABArkendu MitraÎncă nu există evaluări
- EIA-485 Overview: 1 The EIA-485 Interface StandardDocument6 paginiEIA-485 Overview: 1 The EIA-485 Interface StandardAbdelkader ChahmiÎncă nu există evaluări
- Huong Dan Su Dung TRILOGI - LAp Trinh PLC Va DK LogicDocument188 paginiHuong Dan Su Dung TRILOGI - LAp Trinh PLC Va DK LogicNgô Đình NhânÎncă nu există evaluări
- Job Sheet Networking OkDocument4 paginiJob Sheet Networking Okshedrey bargayoÎncă nu există evaluări
- 12U Rack For Audio Pyalara: Genelec 8010ap Genelec 8010apDocument1 pagină12U Rack For Audio Pyalara: Genelec 8010ap Genelec 8010apOsama YaseenÎncă nu există evaluări
- Data Center Infrastructure Checklist: ServicesDocument4 paginiData Center Infrastructure Checklist: Servicessugeng wahyudiÎncă nu există evaluări
- NDB SPI-IIan GPS Phase IdentificationDocument2 paginiNDB SPI-IIan GPS Phase IdentificationAnonymous OuY6oAMggxÎncă nu există evaluări
- Analog To Digital Conversion (A/D) : Engr. Francis B. MalitDocument66 paginiAnalog To Digital Conversion (A/D) : Engr. Francis B. MalitJuliene ArganaÎncă nu există evaluări
- Jupiter ht1100Document80 paginiJupiter ht1100asepÎncă nu există evaluări
- MN Opc 76Document150 paginiMN Opc 76VanaÎncă nu există evaluări
- Release Notes - QualiPoc Android 13.1.1Document19 paginiRelease Notes - QualiPoc Android 13.1.1riichy1980Încă nu există evaluări
- Test Report M77PEUDocument31 paginiTest Report M77PEUtimmylau23Încă nu există evaluări
- 1st Review Report - Smart Distribution SystemDocument54 pagini1st Review Report - Smart Distribution SystemretechÎncă nu există evaluări