Documente Academic
Documente Profesional
Documente Cultură
Lecture2-Risk Identification PDF
Încărcat de
Kalpana Aryal0 evaluări0% au considerat acest document util (0 voturi)
74 vizualizări39 paginiidentification of project risks
Drepturi de autor
© © All Rights Reserved
Formate disponibile
PDF, TXT sau citiți online pe Scribd
Partajați acest document
Partajați sau inserați document
Vi se pare util acest document?
Este necorespunzător acest conținut?
Raportați acest documentidentification of project risks
Drepturi de autor:
© All Rights Reserved
Formate disponibile
Descărcați ca PDF, TXT sau citiți online pe Scribd
0 evaluări0% au considerat acest document util (0 voturi)
74 vizualizări39 paginiLecture2-Risk Identification PDF
Încărcat de
Kalpana Aryalidentification of project risks
Drepturi de autor:
© All Rights Reserved
Formate disponibile
Descărcați ca PDF, TXT sau citiți online pe Scribd
Sunteți pe pagina 1din 39
CC7178
Cyber Security Management
Lecture 2
Risk Identification and Risk
Assessment
CC7178 Cyber Security Management
Learning Objectives
• To define risk management and its role in
the organization
• To use risk management techniques
identifying and prioritizing risk factors for
information assets
• To assess risk based on the likelihood of
adverse events and the effects on information
assets when events occur
• To document the results of risk identification
CC7178 Cyber Security Management Slide 2
Introduction
• Information security departments are created
primarily to manage IT risk
• Managing risk is one of the key
responsibilities of every manager within the
organization
• In any well-developed risk management
program, two formal processes are at work:
– Risk Identification and Assessment
– Risk Control
CC7178 Cyber Security Management Slide 3
Risk Management
• If you know the enemy and know yourself,
you need not fear the result of a hundred
battles
• If you know yourself but not the enemy, for
every victory gained you will also suffer a
defeat
• If you know neither the enemy nor
yourself, you will succumb in every battle
544–496 BC, The Art of War -- Sun Tzu
CC7178 Cyber Security Management Slide 4
Knowing Yourselves
• Identifying, examining, and understanding the
information and how it is processed, stored, and
transmitted.
• Armed with this knowledge, initiate an in-depth
risk management program.
• Risk management is a process of creating the
safeguards and controls which are not installed-
and-forgot.
• Risk management is devised and implemented in
your organization.
CC7178 Cyber Security Management Slide 5
Knowing the Enemy
• Identifying, examining, and understanding the
threats facing the organization’s information
assets
• Managers must be prepared to fully identify
those threats that pose risks to the organization
and the security of its information assets.
• Risk management is the process:
– assessing the risks to an organization’s information
assets
– determining how those risks can be controlled or
mitigated.
CC7178 Cyber Security Management Slide 6
Risk Identification
• Risk identification begins with the process
of self-examination.
• Managers identify the organization’s
information assets, classify them into useful
groups, and prioritize them by their overall
importance.
CC7178 Cyber Security Management Slide 7
Creating an Inventory of
Information Assets
• Identify information assets, including
– people
– Procedures
– data and information
– Software
– Hardware
– networking elements
• This step should be done without pre-judging the
value of each asset (values will be assigned later in
the process).
CC7178 Cyber Security Management Slide 8
Organizational Assets Used in Systems
CC7178 Cyber Security Management Slide 9
Attributes for People, Procedures,
and Data Assets
• People
– Position name/number/ID
– Supervisor name/number/ID
– Security clearance level
– Special skills
• Procedures
– Description
– Intended purpose
– Software/hardware/networking elements to which it is
tied
– Location where it is stored for reference
– Location where it is stored for update purposes
CC7178 Cyber Security Management Slide 10
Attributes for People, Procedures,
and Data Assets (cont.)
• Data
– Classification
– Owner/creator/manager
– Size of data structure
– Data structure used
– Online or offline
– Location
– Backup procedures
CC7178 Cyber Security Management Slide 11
Attributes for Software, Hardware,
and Network Assets
• Consider the following list of potential attributes:
– Name
– IP address
– MAC address
– Asset type
– Serial number
– Manufacturer name
– Manufacturer’s model or part number
– Software version or update revision
– Physical location
– Logical location
– Controlling entity
CC7178 Cyber Security Management Slide 12
Classifying and Categorizing Assets
• Once the initial inventory is assembled,
determine whether its asset categories are
meaningful.
• Inventory should also reflect sensitivity and
security priority assigned to each information
asset.
• A classification scheme categorizes these
information assets based on their sensitivity and
security needs.
CC7178 Cyber Security Management Slide 13
Classifying and Categorizing Assets
(cont.)
• Each of these categories designates the level
of protection needed for a particular
information asset.
• Some asset types, such as personnel, may
require an alternative classification scheme
that would identify the clearance needed to
use the asset type.
• Classification categories must be
comprehensive and mutually exclusive.
CC7178 Cyber Security Management Slide 14
Assessing Values for Information
Assets
• As each information asset is identified, categorized, and
classified, assign a relative value.
• Relative values are comparative judgments made to ensure
that the most valuable information assets are given the highest
priority, for example:
– Which information asset is the most critical to the success
of the organization?
– Which information asset generates the most revenue?
– Which information asset generates the highest
profitability?
– Which information asset is the most expensive to
replace?
– Which information asset is the most expensive to protect?
– Which information asset’s loss or compromise would be the
most embarrassing or cause the greatest liability?
CC7178 Cyber Security Management Slide 15
Sample Asset Classification Worksheet
CC7178 Cyber Security Management Slide 16
Listing Assets in Order of
Importance
• The final step in the risk identification
process is to list the assets in order of
importance.
• This goal can be achieved by using a
weighted factor analysis worksheet.
CC7178 Cyber Security Management Slide 17
Weighted Factor Analysis Worksheet
CC7178 Cyber Security Management Slide 18
Threat Identification
• Any organization typically faces a wide variety of
threats.
• If you assume that every threat can and will
attack every information asset, then the project
scope becomes too complex.
• To make the process less cumbersome, each
step in the threat identification and vulnerability
identification process is managed separately and
then coordinated at the end.
CC7178 Cyber Security Management Slide 19
Identify and Prioritize
Threats and Threat Agents
• Each threat presents an unique challenge to
information security and must be handled with
specific controls that directly address the particular
threat and the threat agent’s attack strategy.
• Before threats can be assessed in the risk
identification process, however, each threat must
be further examined to determine its potential to
affect the targeted information asset .
• In general, this process is referred to as a threat
assessment.
CC7178 Cyber Security Management Slide 20
Threats to Information Security
CC7178 Cyber Security Management Slide 21
Weighted
Ranks of
Threats to
Information
Security
CC7178 Cyber Security Management Slide 22
Weighted Ranking of Threat-Driven Expenditures
CC7178 Cyber Security Management Slide 23
Vulnerability Assessment
• Once you have identified the information assets of the
organization and documented some threat assessment
criteria, you can begin to review every information asset for
each threat.
• This review leads to the creation of a list of vulnerabilities
that remain potential risks to the organization.
• Vulnerabilities are specific avenues that threat agents can
exploit to attack an information asset.
• At the end of the risk identification process, a list of assets
and their vulnerabilities has been developed.
• This list serves as the starting point for the next step in the
risk management process: risk assessment.
CC7178 Cyber Security Management Slide 24
Vulnera-
bility
Assess-
ment of
a DMZ
Router
CC7178 Cyber Security Management Slide 25
The Threats-Vulnerabilities-Assets
(TVA) Worksheet
• At the end of the risk identification process, a list
of assets and their vulnerabilities has been
developed.
• Another list prioritizes threats facing the
organization based on the weighted table
discussed earlier.
• These two lists can be combined into a single
worksheet.
CC7178 Cyber Security Management Slide 26
Sample TVA Spreadsheet
CC7178 Cyber Security Management Slide 27
Introduction to Risk Assessment
• The goal at this point is to create a method
to evaluate the relative risk of each listed
vulnerability.
Risk = (The likelihood of the occurrence of a
vulnerability) * (The value of the information
asset) - (The percentage of risk mitigated by
current controls)+ (The uncertainty of current
knowledge of the vulnerability)
CC7178 Cyber Security Management Slide 28
Risk Identification Estimate Factors
Risk is
The likelihood of the occurrence of a vulnerability
Multiplied by
The value of the information asset
Minus
The percentage of risk mitigated by current
controls
Plus
The uncertainty of current knowledge of the
vulnerability
CC7178 Cyber Security Management Slide 29
The Likelihood and Value
• Likelihood is the overall rating—often a
numerical value on a defined scale (such as 0.1
– 1.0)—of the probability that a specific
vulnerability will be exploited.
• Using the information documented during the
risk identification process, you can assign
weighted scores based on the value of each
information asset, i.e. 1-100, low-med-high, etc.
CC7178 Cyber Security Management Slide 30
Percentage of Risk
Mitigated by Current Controls
• If a vulnerability is fully managed by an
existing control, it can be set aside.
• If it is partially controlled, estimate what
percentage of the vulnerability has been
controlled.
CC7178 Cyber Security Management Slide 31
Uncertainty
• It is not possible to know everything about
every vulnerability.
• The degree to which a current control can
reduce risk is also subject to estimation
error.
• Uncertainty is an estimate made by the
manager using judgment and experience.
CC7178 Cyber Security Management Slide 32
Risk Determination Example
• Asset A has a value of 50 and one vulnerability,
which has a likelihood of 1.0 with no current
controls. Your assumptions and data are 90%
accurate.
• Asset B has a value of 100 and has two
vulnerabilities: vulnerability #2 has a likelihood of
0.5 with a current control that addresses 50% of
its risk; vulnerability # 3 has a likelihood of 0.1 with
no current controls. Your assumptions and data
are 80% accurate.
CC7178 Cyber Security Management Slide 33
Risk Determination Example (cont.)
• The resulting ranked list of risk ratings for
the three vulnerabilities is as follows:
– Asset A: Vulnerability 1 rated as 55 = (50 × 1.0) – 0% +
10%
– Asset B: Vulnerability 2 rated as 35 = (100 × 0.5) – 50% +
20%
– Asset B: Vulnerability 3 rated as 12 = (100 × 0.1) – 0 % +
20%
CC7178 Cyber Security Management Slide 34
Identifying Possible Controls
• Three general categories of controls
exist:
– Policies
– Programs
– Technical controls
CC7178 Cyber Security Management Slide 35
Documenting the Results
of Risk Assessment
• The goal of the risk management process so far has
been to identify information assets and their
vulnerabilities and to rank them according to the need
for protection.
• In preparing the list, a wealth of factual information
about the assets and the threats they face is collected.
• Also, information about the controls that are already in
place is collected.
• The final summarized document is the ranked
vulnerability risk worksheet.
CC7178 Cyber Security Management Slide 36
Table 7-6
Ranked
Vulnerability
Risk
Worksheet
CC7178 Cyber Security Management Slide 37
Risk Identification & Assessment
Deliverables
CC7178 Cyber Security Management Slide 38
Summary
• Introduction
• Risk Management
– Risk Identification and Risk Assessment
• Inventory of information assets
• Threat identification
• Vulnerability assessment
• Risk assessment
– Risk Control (next week’s topic)
• Documenting the Results of Risk Assessment
CC7178 Cyber Security Management Slide 39
S-ar putea să vă placă și
- Network Design in The Supply ChainDocument14 paginiNetwork Design in The Supply ChainPrasad GantiÎncă nu există evaluări
- The Business CaseDocument21 paginiThe Business CaseStojan BozhinovÎncă nu există evaluări
- Determining Sales Forecasts: © 2011 John Wiley & Sons Edition Dopson, Hayes, & MillerDocument40 paginiDetermining Sales Forecasts: © 2011 John Wiley & Sons Edition Dopson, Hayes, & MillerMary Christ TabasÎncă nu există evaluări
- Entrepmall GuidelinesDocument4 paginiEntrepmall GuidelinesMac b IBANEZÎncă nu există evaluări
- Remote Deposit Capture Project Part 1: Project Integration ManagementDocument7 paginiRemote Deposit Capture Project Part 1: Project Integration ManagementManasa KarumuriÎncă nu există evaluări
- Hilton Hotel Reservation SampleDocument2 paginiHilton Hotel Reservation SampleAlan Dean Valencia LalogÎncă nu există evaluări
- Washing Machine ManualDocument44 paginiWashing Machine ManualAngel Angeleye100% (1)
- Assignment of PurchasingDocument6 paginiAssignment of PurchasingMuhammad Khalid Mushtaq MayoÎncă nu există evaluări
- Chapter 2Document28 paginiChapter 2Kul Bunna100% (1)
- 8th Annual National Secondary Students' Council Leaders' Conference SpeechDocument2 pagini8th Annual National Secondary Students' Council Leaders' Conference SpeechBenjamin mwanikiÎncă nu există evaluări
- Chapter 7 - Report - PPTDocument40 paginiChapter 7 - Report - PPTRose AnnÎncă nu există evaluări
- Lecture 1 - Understanding The Supply ChainDocument27 paginiLecture 1 - Understanding The Supply ChainNhi Nguyễn Thị NgânÎncă nu există evaluări
- Garnett Jackson MK STUDY CASEDocument1 paginăGarnett Jackson MK STUDY CASEazkaÎncă nu există evaluări
- Intro To MiceDocument33 paginiIntro To MiceCRISTINE AGUILARÎncă nu există evaluări
- Activity in Professional Ethics MIDTERMDocument10 paginiActivity in Professional Ethics MIDTERMAr Jay JuanÎncă nu există evaluări
- 7 Investigator Lab Xid-10984456 2Document32 pagini7 Investigator Lab Xid-10984456 2Zoey TanÎncă nu există evaluări
- OSINTRODocument25 paginiOSINTROlovishsindhwaniÎncă nu există evaluări
- Geclif - Midterm Examination (Bsma 1c - Zion R. Desamero)Document2 paginiGeclif - Midterm Examination (Bsma 1c - Zion R. Desamero)Zion EliÎncă nu există evaluări
- 3) FA Lec 2 Accounting Equation Mon 20Document13 pagini3) FA Lec 2 Accounting Equation Mon 20Yashvi Patel0% (1)
- F.O. CBC FinalDocument6 paginiF.O. CBC FinalAmy Amper Pelenio-LofrancoÎncă nu există evaluări
- AI and CybersecurityDocument92 paginiAI and Cybersecurityerdevendrasoni2022Încă nu există evaluări
- Chapter 11 Lodging, Planning and Design QuestionsDocument5 paginiChapter 11 Lodging, Planning and Design QuestionsAbhishek AgarwalÎncă nu există evaluări
- Professional Ethics and ResponsibilitiesDocument26 paginiProfessional Ethics and Responsibilitiessamas7480Încă nu există evaluări
- CMO 53, S. 2006Document42 paginiCMO 53, S. 2006Jeffrey ErazoÎncă nu există evaluări
- Hapter 19: © 2008 Prentice Hall Business Publishing Accounting Information Systems, 11/e Romney/SteinbartDocument159 paginiHapter 19: © 2008 Prentice Hall Business Publishing Accounting Information Systems, 11/e Romney/Steinbartp12400Încă nu există evaluări
- Cri Lecture Obe 2 Theories of InnovationDocument26 paginiCri Lecture Obe 2 Theories of InnovationDiana Rose100% (1)
- Discrete Structures FundamentalsDocument2 paginiDiscrete Structures FundamentalsMausam Pokhrel100% (1)
- Introduction To Logistics Management Module 4Document19 paginiIntroduction To Logistics Management Module 4Kyle SikorskyÎncă nu există evaluări
- Digital Evidence in The Courtroom: A Guide For Law Enforcement and ProsecutorsDocument81 paginiDigital Evidence in The Courtroom: A Guide For Law Enforcement and ProsecutorsManuel PuentesÎncă nu există evaluări
- Guide To Computer Forensics and Investigations Fifth EditionDocument58 paginiGuide To Computer Forensics and Investigations Fifth EditionAnonymous TyFkSRuÎncă nu există evaluări
- Chapter 4 MPTH MidtermDocument6 paginiChapter 4 MPTH MidtermLiaa Angelique BaranganÎncă nu există evaluări
- Computer Graphics - AnimationDocument6 paginiComputer Graphics - AnimationknightIndustriesÎncă nu există evaluări
- Foundations of Information Systems in BusinessDocument56 paginiFoundations of Information Systems in BusinessYasir HasnainÎncă nu există evaluări
- SCM PrelimDocument15 paginiSCM PrelimRegina IldefonsoÎncă nu există evaluări
- PPT ch09Document47 paginiPPT ch09bikasÎncă nu există evaluări
- Euthenics Prelims CoverageDocument14 paginiEuthenics Prelims CoverageDarlene De PazÎncă nu există evaluări
- SCM 1-18 PPTDocument801 paginiSCM 1-18 PPTMr Boda Saikiran IPEÎncă nu există evaluări
- Prototype Types and ClassificationsDocument18 paginiPrototype Types and Classificationss_coolbugÎncă nu există evaluări
- Designing Supply Chain NetworksDocument10 paginiDesigning Supply Chain NetworksDulmi RathnasekaraÎncă nu există evaluări
- Syllabus E-Commerce in TourismDocument4 paginiSyllabus E-Commerce in TourismBabu GeorgeÎncă nu există evaluări
- Guide To Computer Forensics and InvestigationsDocument39 paginiGuide To Computer Forensics and InvestigationsYukta JaiswalÎncă nu există evaluări
- Bachelor of Science in Nutrition and Diatetics 2Document4 paginiBachelor of Science in Nutrition and Diatetics 2Denice Tamayo De GuzmanÎncă nu există evaluări
- Information Assurance and Security (SDisaster Recovery and Business Continuity Plan Module 7)Document4 paginiInformation Assurance and Security (SDisaster Recovery and Business Continuity Plan Module 7)Marneil Allen SanchezÎncă nu există evaluări
- Property Management System (PMS)Document20 paginiProperty Management System (PMS)Rv TejadaÎncă nu există evaluări
- Lec13 Report WritingDocument33 paginiLec13 Report WritingQomindawoÎncă nu există evaluări
- Tourism Chapter 5 - by Group 4Document28 paginiTourism Chapter 5 - by Group 4Desi TriherawatiÎncă nu există evaluări
- Security, Privacy, and Ethical Issues in Information SystemsDocument16 paginiSecurity, Privacy, and Ethical Issues in Information SystemsAntonyÎncă nu există evaluări
- Hotel Reservation Systems Case StudyDocument6 paginiHotel Reservation Systems Case StudyJay-r CabayanÎncă nu există evaluări
- CNB4313-Tutorial 1-Solution-220211 - 113016Document4 paginiCNB4313-Tutorial 1-Solution-220211 - 113016Raguwaran SamayyahÎncă nu există evaluări
- Working Capital Management and The Profitability of Corporate Organizations in NigeriaDocument18 paginiWorking Capital Management and The Profitability of Corporate Organizations in NigeriaSolomon Reuben IrmiyaÎncă nu există evaluări
- Quality Service Midterm ReviewerDocument19 paginiQuality Service Midterm ReviewerAngela Denise DizonÎncă nu există evaluări
- Article III Bill of RightsDocument22 paginiArticle III Bill of RightsFrances Ann Teves100% (1)
- Supply Chain Management Lecture 2Document38 paginiSupply Chain Management Lecture 2Amit Abhijit DasÎncă nu există evaluări
- Configure Computer Systems NC II - Configuring Systems & NetworksDocument51 paginiConfigure Computer Systems NC II - Configuring Systems & NetworksAnnabelle Reyes SucgangÎncă nu există evaluări
- Lesson 1 The Hotel IndustryDocument17 paginiLesson 1 The Hotel IndustryReinaÎncă nu există evaluări
- UNIT II Probability TheoryDocument84 paginiUNIT II Probability TheoryaymanÎncă nu există evaluări
- Expert Testimony Guide for Computer Forensics InvestigationsDocument45 paginiExpert Testimony Guide for Computer Forensics InvestigationsGURLEEN KAURÎncă nu există evaluări
- Risk Mgt SecurityDocument70 paginiRisk Mgt Securityupdeshroy816Încă nu există evaluări
- Lecture 4 (UCI 403) Risk Assesment and ControlDocument41 paginiLecture 4 (UCI 403) Risk Assesment and Controlbenard jangayaÎncă nu există evaluări
- Unit 2 Part-IiDocument59 paginiUnit 2 Part-IirohithatimsiÎncă nu există evaluări
- Hazmat Test (2014)Document2 paginiHazmat Test (2014)Wodro100% (1)
- Disaster Laws in Pakistan - Nadeem Ahmed AbroDocument50 paginiDisaster Laws in Pakistan - Nadeem Ahmed Abroamirbashir24Încă nu există evaluări
- OSHA 1910.144 - Safety Color Code For Marking Physical HazardsDocument1 paginăOSHA 1910.144 - Safety Color Code For Marking Physical HazardsHarold GillÎncă nu există evaluări
- Tag ScaffoldingDocument17 paginiTag ScaffoldingHendri AnurÎncă nu există evaluări
- Fall Protection Risk AssessmentDocument3 paginiFall Protection Risk Assessmentsimone0% (1)
- Explosives Manufacturing and Processing Guideline To Safety TrainingDocument16 paginiExplosives Manufacturing and Processing Guideline To Safety TrainingCuesta AndresÎncă nu există evaluări
- Oil and Gas Summary SyllabusDocument5 paginiOil and Gas Summary Syllabusnedian1982100% (1)
- What Is NIOSH?: National Institute For Occupational Safety and Health (NIOSH)Document3 paginiWhat Is NIOSH?: National Institute For Occupational Safety and Health (NIOSH)haliza amirahÎncă nu există evaluări
- Region I Schools DRRR Activity SheetsDocument2 paginiRegion I Schools DRRR Activity SheetsMina Caragan Carreon100% (1)
- 1 - Project HSE Plan - IMC-1 ProjectDocument95 pagini1 - Project HSE Plan - IMC-1 ProjectJamalYousufÎncă nu există evaluări
- GDN 227Document31 paginiGDN 227Vasant Kumar Varma100% (2)
- Regulations (Standards - 29 CFR) - Occupational Safety and Health AdministrationDocument15 paginiRegulations (Standards - 29 CFR) - Occupational Safety and Health Administrationaliyildizx17730Încă nu există evaluări
- Hot Work Procedure, WHSPRO-010 CMDocument3 paginiHot Work Procedure, WHSPRO-010 CMmyo lwinÎncă nu există evaluări
- Alantoina Msds (1) .PHP - Msdsid 9922829Document5 paginiAlantoina Msds (1) .PHP - Msdsid 9922829xavier castilloÎncă nu există evaluări
- HSE Policy PDFDocument10 paginiHSE Policy PDFgiovadiÎncă nu există evaluări
- Abraj HSE PolicyDocument1 paginăAbraj HSE PolicyShahid AlamÎncă nu există evaluări
- SiteSpecificSafetyPlan MasterDocument37 paginiSiteSpecificSafetyPlan MasterCris VilceanuÎncă nu există evaluări
- Click Here To Download Nebosh Igc Course Details (Nebosh) PDFDocument2 paginiClick Here To Download Nebosh Igc Course Details (Nebosh) PDFWahyu Sunday75% (4)
- HIRARC For CONSTRUCTIONDocument12 paginiHIRARC For CONSTRUCTIONpalanitharan95% (59)
- Plant Floor Safety Fall EditionDocument54 paginiPlant Floor Safety Fall EditionPravivVivpraÎncă nu există evaluări
- SITXWHS003 Assessment 2 Project AnswersDocument30 paginiSITXWHS003 Assessment 2 Project AnswersArmughan Bukhari62% (13)
- Example Workplace Health Safety Inspection FormDocument4 paginiExample Workplace Health Safety Inspection Formbadar13Încă nu există evaluări
- Hva B3Document1 paginăHva B3aldhilaÎncă nu există evaluări
- 65-HACCP Certification Scheme June 2012Document64 pagini65-HACCP Certification Scheme June 2012Osman AitaÎncă nu există evaluări
- Course Electrical Installation and Maintenance NC Ii Unit of Competency Participate in Workplace CommunicationDocument5 paginiCourse Electrical Installation and Maintenance NC Ii Unit of Competency Participate in Workplace Communicationrowell ramosÎncă nu există evaluări
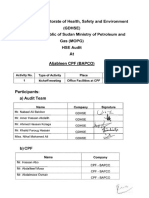
- Audit Report at BAPCO and ORCDocument16 paginiAudit Report at BAPCO and ORCNabiel AliÎncă nu există evaluări
- Haccp CateringDocument12 paginiHaccp CateringDeparted MoonÎncă nu există evaluări
- Safety AlertDocument1 paginăSafety Alertjithin shankarÎncă nu există evaluări
- Health Safety Wellbeing InductionDocument46 paginiHealth Safety Wellbeing InductionNada GhloomÎncă nu există evaluări
- Functional Safety With Iec62061 and Iso13849Document1 paginăFunctional Safety With Iec62061 and Iso13849최재호0% (1)