Documente Academic
Documente Profesional
Documente Cultură
Number (I) Max (Number (0), Number (1),, Number (N - 1) ) +1 J 0 J N J++) (Number (J) ! 0) &&
Încărcat de
Vishal Mittal0 evaluări0% au considerat acest document util (0 voturi)
45 vizualizări3 paginiTitlu original
compre_IIsem_2005.pdf
Drepturi de autor
© © All Rights Reserved
Formate disponibile
PDF, TXT sau citiți online pe Scribd
Partajați acest document
Partajați sau inserați document
Vi se pare util acest document?
Este necorespunzător acest conținut?
Raportați acest documentDrepturi de autor:
© All Rights Reserved
Formate disponibile
Descărcați ca PDF, TXT sau citiți online pe Scribd
0 evaluări0% au considerat acest document util (0 voturi)
45 vizualizări3 paginiNumber (I) Max (Number (0), Number (1),, Number (N - 1) ) +1 J 0 J N J++) (Number (J) ! 0) &&
Încărcat de
Vishal MittalDrepturi de autor:
© All Rights Reserved
Formate disponibile
Descărcați ca PDF, TXT sau citiți online pe Scribd
Sunteți pe pagina 1din 3
BIRLA INSTITUTE OF TECHNOLOGY & SCIENCE, PILANI
First Semester 2005-2005
Course Title : OPERATING SYSTEMS Course No IS C362
Component : Comprehensive Exam Closed Book Component
Weightage : 30% Max Marks: 90 Date: 03/05/2005
Note: Attempt all the Questions. Start each answer from a fresh page.
Question #1 CPU scheduling (18 Marks)
In the following scenario compare results in terms of Average waiting time,
Average turn around time, and CPU utilization between SJF, SRTF, Preemptive priority,
and Non preemptive priority scheduling. (The lesser the priority value the more the
priority)
Process CPU Burst T.CPU burst Priority Arrival Time I/O time
P1 5 9 3 0 3
P2 7 7 2 1 0
P3 6 11 4 3 2
P4 3 7 6 6 7
Question #2 Process, Thread And Concurrency (18 Marks)
(Question #2A) (6 Marks)
Below describes Bakery algorithm. Mention a scenario where this implementation
of Bakery algorithm will fail. Rewrite the Bakery algorithm to overcome this flaw.
Do {
number[i] = max(number[0], number[1], …, number [n – 1])+1;
for ( j = 0 ; j < n ; j++ ) {
while ( number[j] != 0) &&
( number [ j , j ] ) < ( number [ i , i ] ) ;
}
CRITICAL SECTION
number[i] = 0 ;
REMAINDER SECTION
} while(1) ;
(Question #2B) (5 Marks)
Suppose you try to implement semaphores as follows (call this version 1):
P: V:
disable interrupts disable interrupts
while (s <= 0) s=s+1
; /* do nothing */ enable interrupts
s=s–1
enable interrupts
Now suppose you try to implement semaphores by replacing the “; /*do nothing
*/” in the definition of P with “{disable interrupts; enable interrupts}”(call this version2).
(1) What problem does version 1 have that is fixed by version 2? (2M)
(2) What problems do both of these implementations share? (3M)
(Question #2C) (3 Marks)
Suppose we have N processes, which use 2 critical regions, which are protected
using semaphores. You can assume that the critical regions are independent of each other,
the processes implement the critical region protocol correctly and that there is no
starvation. What is the maximum number of suspended processes?
(Question #2D) (4 Marks)
Consider the interprocess-communication scheme where mailboxes are used.
Suppose a process P wants to wait for two messages, one from mailbox A and one from
mailbox B. What sequence of send and receive should it execute? (Remember send is not
blocking but receive is blocking. Also, it should be noted that P does not know whether A
will have the message before B or vice-versa)
Question #3 Memory Management (31 Marks)
(Question #3A) (10 Marks)
A system uses TLB (Mt), Cache (Mc), Primary memory (Mp) and Disk as the
secondary memory (Ms). The time to access Mt is 5nS, time to access Mc is 5nS, time to
access Mp is 70nS and the time to access and process Ms (including page in, page out
and page table update) is 5mS. If a probability of TLB hit is 0.9 (Mc contain all the
information what Mt points to) and residual probability of the data being in Mp is 0.95
and the residual probability of data being in Ms is 1.00. Assume that the memory
hierarchy is checked in the order Mt Mp Ms, what is the expected access time for a byte
instruction. (3+3+4)
(Question #3B) (2 Marks)
_________ and ___________ kinds of pages in a process’ virtual address space
are usually protected as “Read Only”.
(Question #3C) (11 Marks)
Suppose we have a computer system with a 44-bit virtual address, page size of
16K, and 4 bytes per page table entry.
1) How many pages are in the virtual address space? (2M)
2) Suppose we use N-level paging and arrange for all page tables to fit into a single page
frame. How will the bits of address be divided up? (3M)
3) Suppose we have a 4 Gbyte program such that the entire program and all necessary
page tables (using N-level paging as in part b) are in memory. How much memory (in
page frames) is used by the program, including its page tables? (6M)
(Question #3D) (8 Marks)
Suppose we have an average of one page fault every 20,000,000 instructions, a
normal instruction takes 2 nanoseconds, and a page fault causes the instruction to take an
additional 10 milliseconds. What is the average instruction time, taking page faults into
account? Redo the calculation assuming that a normal instruction takes 1 nanoseconds
instead of 2 nanoseconds.
Question #4 File Systems (23 Marks)
(Question #4A) (4 Marks)
On a Unix file system, how many disk read operations are required to read the
first block of the file "/home/unix/isc362/os/copre.pdf"? Assume that the master block is
in memory, but nothing else. Also assume that all directories are one block in size.
(Question #4B) (10 Marks)
(2 Marks for every right answer, -1 mark for wrong answer & 0 marks if not attempting)
1. Is it possible to implement a file system inside of a file stored in another file
system? (Yes / No)
2. Is it possible to have two file systems on a single physical disk drive? (Yes / No)
3. Is it possible to have a file system that spans two physical disk drives? (Yes / No)
4. Is it possible to have a file that is not in a file system? (Yes / No)
5. The mount operation allows you to graft the directory tree from one file system
onto the directory tree of another file system. Does this mean that a file can span
both file systems? (Yes / No)
(Question #4C) (4 Marks)
Consider a file of size 262144 bytes (2 ^18 bytes). Assume that this file is stored
on a disk where the block size is 256 bytes and a block address is 16 bits. Furthermore
the content of this file is such that the first logical block consists of just the character ‘a’
(256 times). The logical block in the middle of the file consists of just the character ‘b’
and the last logical block consists of character ‘c’. The rest of the data in the file is all
zeros.
Suppose this file is stored using linked allocation. How many blocks on the disk will be
used by this file.
(Question #4D) (5 Marks)
There exist a file named “compre.c” in prithvi server. The ls –l command gives
following details about the file
-rw–r--r-- 1 OS staff 1002 April 24 15:40 compre.c
We created the following hard link and symbolic link on May 2 10:10.
The commands we executed on May 2 are
ln compre.c hl1
ln compre.c hl2
ln –s compre.c sl1
What will be the output of the following ls commands if I am executing it after
the above commands?
1. ls –l compre.c (1Mark)
2. ls –l hl2 (2Marks)
3. ls –l sl1 (2Marks)
S-ar putea să vă placă și
- Operating Systems INT2206 20 (2019-2020) : UetotsDocument6 paginiOperating Systems INT2206 20 (2019-2020) : Uetots20021408 Lê Thị Cẩm NhungÎncă nu există evaluări
- Cegep Vanier College Department of Computer Science Assignment #6: Max MarksDocument2 paginiCegep Vanier College Department of Computer Science Assignment #6: Max MarksJocelyn Moreno0% (1)
- EXT4 FilesystemDocument4 paginiEXT4 FilesystemNeha KarayilÎncă nu există evaluări
- Question #1 (9 Marks) : Operating Systems (CS C372) Comprehensive Exam RegularDocument4 paginiQuestion #1 (9 Marks) : Operating Systems (CS C372) Comprehensive Exam RegularVishal MittalÎncă nu există evaluări
- Open Book ComponentDocument3 paginiOpen Book ComponentVishal MittalÎncă nu există evaluări
- hệ điều hànhDocument18 paginihệ điều hànhfranklampardnumber8Încă nu există evaluări
- Midterm Fall2012SolutionsDocument6 paginiMidterm Fall2012SolutionsanjugaduÎncă nu există evaluări
- Qualcomm QnsDocument9 paginiQualcomm QnsPrincy MurugesanÎncă nu există evaluări
- EXAMDec2012 SolutionDocument8 paginiEXAMDec2012 Solutionخالد ناهض نايف نجمÎncă nu există evaluări
- Ractice Roblems O S: I D P: Perating Ystems Nternals and Esign Rinciples S EDocument28 paginiRactice Roblems O S: I D P: Perating Ystems Nternals and Esign Rinciples S EHamza Asim Ghazi100% (1)
- Mca C106Document2 paginiMca C106akhilchaudhary712Încă nu există evaluări
- Compre IIsem 2003-04 SolDocument6 paginiCompre IIsem 2003-04 SolmorigasakiÎncă nu există evaluări
- Final Exam Fall 2020 PDFDocument4 paginiFinal Exam Fall 2020 PDFRatul BiswasÎncă nu există evaluări
- Exam #1 For Computer Networks SOLUTIONSDocument4 paginiExam #1 For Computer Networks SOLUTIONS87bbÎncă nu există evaluări
- Com-Sci 111 Eyolfson mt1 Fall20 Id186Document9 paginiCom-Sci 111 Eyolfson mt1 Fall20 Id186mikeÎncă nu există evaluări
- OS Midterm SolutionDocument4 paginiOS Midterm SolutionRofaelEmil100% (2)
- Cse 312 - Os End Term - 17 Nov 2021 FinalDocument2 paginiCse 312 - Os End Term - 17 Nov 2021 FinalHussain KaideÎncă nu există evaluări
- Devi Balika Revision PaperDocument16 paginiDevi Balika Revision PaperDahanyakage WickramathungaÎncă nu există evaluări
- Midterm I Solutions: Problem Possible ScoreDocument20 paginiMidterm I Solutions: Problem Possible ScoreAlfin AbdullahÎncă nu există evaluări
- Birla Institute of Technology & Science, Pilani Comprehensive ExaminationDocument6 paginiBirla Institute of Technology & Science, Pilani Comprehensive ExaminationVishal MittalÎncă nu există evaluări
- Compre Regular Final Answer KeyDocument7 paginiCompre Regular Final Answer KeyManisha JaiswalÎncă nu există evaluări
- Open Book ComponentDocument2 paginiOpen Book ComponentVishal MittalÎncă nu există evaluări
- Midterm 369 10s AnsDocument8 paginiMidterm 369 10s Anstarsonis134Încă nu există evaluări
- Midterm Exam Solutions and Grading GuidelinesDocument8 paginiMidterm Exam Solutions and Grading GuidelinesrakeshguptaÎncă nu există evaluări
- CSE473/Spring 2008 - 1st Midterm ExamDocument6 paginiCSE473/Spring 2008 - 1st Midterm ExamsatyendrainÎncă nu există evaluări
- CENG400-Final-Fall 2014Document11 paginiCENG400-Final-Fall 2014Mohamad IssaÎncă nu există evaluări
- Ops611s - Operating Systems - 2ND Opp - July 2022Document8 paginiOps611s - Operating Systems - 2ND Opp - July 2022Gerald KufangaÎncă nu există evaluări
- Interview QnsDocument5 paginiInterview Qnssaikirannani277Încă nu există evaluări
- CS311 ExamDocument16 paginiCS311 ExamTetzÎncă nu există evaluări
- CS609 - Final Term Papers Fall 2012Document16 paginiCS609 - Final Term Papers Fall 2012dopvisionÎncă nu există evaluări
- Final AOS SPR 2018Document2 paginiFinal AOS SPR 2018Tabish KhalidÎncă nu există evaluări
- Programming Assignment 2: Priority Queues and Disjoint SetsDocument11 paginiProgramming Assignment 2: Priority Queues and Disjoint SetsAnanya KallankudluÎncă nu există evaluări
- Programming Assignment 2: Priority Queues and Disjoint SetsDocument11 paginiProgramming Assignment 2: Priority Queues and Disjoint SetsDaniel SerranoÎncă nu există evaluări
- Past Paper Question StudentDocument5 paginiPast Paper Question StudentminedeathpcÎncă nu există evaluări
- OC Lec QuizzesDocument12 paginiOC Lec QuizzesScrabler7381Încă nu există evaluări
- 1 Written Part (30pts) : CS 340 Assignment 1 Total: 100pts + 10pts (Bonus)Document4 pagini1 Written Part (30pts) : CS 340 Assignment 1 Total: 100pts + 10pts (Bonus)jenl chaklasiyaÎncă nu există evaluări
- Question BankDocument5 paginiQuestion Bank20IT019 ROHIT SÎncă nu există evaluări
- Tutorial 03 With Answers ProcessDocument4 paginiTutorial 03 With Answers Processphi nguyenÎncă nu există evaluări
- Csci 4630 TestDocument14 paginiCsci 4630 Testbunty1836Încă nu există evaluări
- Asn HS07Document6 paginiAsn HS07saravanan_nallusamyÎncă nu există evaluări
- Operating Systems: Assignment Sheet 1Document2 paginiOperating Systems: Assignment Sheet 1MathumathiAÎncă nu există evaluări
- Operating System (Minor) (Csmi-301) DR B R Ambedkar National Institute of Technology, Jalandhar Solve All The QuestionsDocument6 paginiOperating System (Minor) (Csmi-301) DR B R Ambedkar National Institute of Technology, Jalandhar Solve All The QuestionsDamanpreet SinghÎncă nu există evaluări
- Quiz QuestionsDocument2 paginiQuiz QuestionsAditya DusiÎncă nu există evaluări
- Os + DsDocument12 paginiOs + DsAniket AggarwalÎncă nu există evaluări
- OS Assignment-1 - 22-23Document12 paginiOS Assignment-1 - 22-23Sreenidhi SaluguÎncă nu există evaluări
- Midterm Exam #2 Solutions: Your Name: Sid: Circle The Letters of Your CS162 Login (1 Per Line) : TA Name / SectionDocument12 paginiMidterm Exam #2 Solutions: Your Name: Sid: Circle The Letters of Your CS162 Login (1 Per Line) : TA Name / SectionIshan JawaÎncă nu există evaluări
- Model Papers IV Sem Comp SciDocument6 paginiModel Papers IV Sem Comp ScidebasiskamilaÎncă nu există evaluări
- Final Examination: This Is A Closed Book, Closed Notes, No Calculator ExamDocument10 paginiFinal Examination: This Is A Closed Book, Closed Notes, No Calculator Exambunty daÎncă nu există evaluări
- IT 241 Assignment-1Document5 paginiIT 241 Assignment-1TAHER AL-NEMERÎncă nu există evaluări
- M. Sc. Tech. Indus. MathsDocument135 paginiM. Sc. Tech. Indus. MathsrapsjadeÎncă nu există evaluări
- Assignment Os NewDocument4 paginiAssignment Os NewSupriya KumarÎncă nu există evaluări
- Os QuizDocument5 paginiOs QuizHem RameshÎncă nu există evaluări
- Implementation of Symbol TableDocument31 paginiImplementation of Symbol TableBhanu SharmaÎncă nu există evaluări
- DR B R Ambedkar National Institute of Technology, Jalandhar CSPC-303, Operating Systems End Semester Examination, November/December 2021Document4 paginiDR B R Ambedkar National Institute of Technology, Jalandhar CSPC-303, Operating Systems End Semester Examination, November/December 2021AagdsÎncă nu există evaluări
- CU-2022 B.Sc. (General) Computer Science Semester-4 Paper-CC4-GE4 QPDocument2 paginiCU-2022 B.Sc. (General) Computer Science Semester-4 Paper-CC4-GE4 QPgozombie43Încă nu există evaluări
- IT1020 - Introduction To Computer SystemsDocument6 paginiIT1020 - Introduction To Computer SystemsgepoveÎncă nu există evaluări
- Instructions:: Q1. Answer The Following Questions: (Marks 10)Document3 paginiInstructions:: Q1. Answer The Following Questions: (Marks 10)Zoha MobinÎncă nu există evaluări
- Lab 4 Process (Cont) Course: Operating Systems: Thanh Le-Hai Hoang Email: Thanhhoang@hcmut - Edu.vnDocument9 paginiLab 4 Process (Cont) Course: Operating Systems: Thanh Le-Hai Hoang Email: Thanhhoang@hcmut - Edu.vnAnh NguyễnÎncă nu există evaluări
- OS Question - Process Scheduling and Memory ManagementDocument4 paginiOS Question - Process Scheduling and Memory ManagementMohamad FirdausÎncă nu există evaluări
- Write A COBOL Program For Matrix AdditionDocument7 paginiWrite A COBOL Program For Matrix AdditionNani ChowdaryÎncă nu există evaluări
- Good Habits for Great Coding: Improving Programming Skills with Examples in PythonDe la EverandGood Habits for Great Coding: Improving Programming Skills with Examples in PythonÎncă nu există evaluări
- Computer ArchitectureDocument30 paginiComputer ArchitectureNAMAN DEEP SRIVASTAVAÎncă nu există evaluări
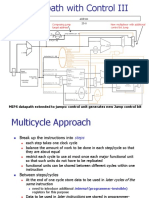
- Lect6 Multi Cycle DatapathDocument22 paginiLect6 Multi Cycle DatapathVishal MittalÎncă nu există evaluări
- Instructions: Language of The MachineDocument47 paginiInstructions: Language of The MachineVishal MittalÎncă nu există evaluări
- Lect7 Multi Cycle ControlDocument46 paginiLect7 Multi Cycle ControlVishal MittalÎncă nu există evaluări
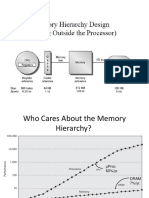
- Lect11 Cache BasicsDocument22 paginiLect11 Cache BasicsVishal MittalÎncă nu există evaluări
- Lect 1Document54 paginiLect 1Vishal MittalÎncă nu există evaluări
- Lect3 PDFDocument64 paginiLect3 PDFShivam KhandelwalÎncă nu există evaluări
- 13) Ilp1 PDFDocument85 pagini13) Ilp1 PDFAnoushka SaraswatÎncă nu există evaluări
- How Many New Processes Are Created by Fork Calls?: CS C372/IS C362 - Operating SystemDocument3 paginiHow Many New Processes Are Created by Fork Calls?: CS C372/IS C362 - Operating SystemVishal MittalÎncă nu există evaluări
- Lect5 Single Cycle ControlDocument29 paginiLect5 Single Cycle ControlVishal MittalÎncă nu există evaluări
- Revisiting Hazards: Data Hazards Control Hazards HardwareDocument45 paginiRevisiting Hazards: Data Hazards Control Hazards HardwareVishal MittalÎncă nu există evaluări
- Lect8 Pipelined DP ControlDocument59 paginiLect8 Pipelined DP ControlVishal MittalÎncă nu există evaluări
- Branch PredictionDocument41 paginiBranch PredictionSHASHANK DWIVEDIÎncă nu există evaluări
- Lect12 CacheDocument39 paginiLect12 CacheVishal MittalÎncă nu există evaluări
- Cache 2Document24 paginiCache 2Aditya GargÎncă nu există evaluări
- OS Quiz Solutions PDFDocument4 paginiOS Quiz Solutions PDFVishal MittalÎncă nu există evaluări
- 1st Sem 03-04 (Compre Quiz) PDFDocument8 pagini1st Sem 03-04 (Compre Quiz) PDFVishal MittalÎncă nu există evaluări
- Open Book ComponentDocument2 paginiOpen Book ComponentVishal MittalÎncă nu există evaluări
- CS C372/IS C362 - Operating System: Birla Institute of Technology & Science, Pilani QUIZ 2 - Closed BookDocument2 paginiCS C372/IS C362 - Operating System: Birla Institute of Technology & Science, Pilani QUIZ 2 - Closed BookVishal MittalÎncă nu există evaluări
- Open Book ComponentDocument2 paginiOpen Book ComponentVishal MittalÎncă nu există evaluări
- CS C372/IS C362 - Operating System: Birla Institute of Technology & Science, Pilani QUIZ 3 - Closed BookDocument2 paginiCS C372/IS C362 - Operating System: Birla Institute of Technology & Science, Pilani QUIZ 3 - Closed BookVishal MittalÎncă nu există evaluări
- CS C372/IS C362 - Operating System: Birla Institute of Technology & Science, Pilani Test 1 - Closed BookDocument2 paginiCS C372/IS C362 - Operating System: Birla Institute of Technology & Science, Pilani Test 1 - Closed BookVishal MittalÎncă nu există evaluări
- 1st Sem 03-04 (Compre Quiz) PDFDocument8 pagini1st Sem 03-04 (Compre Quiz) PDFVishal MittalÎncă nu există evaluări
- Os1 First 2013-14 PDFDocument2 paginiOs1 First 2013-14 PDFVishal MittalÎncă nu există evaluări
- Birla Institute of Technology & Science, Pilani Comprehensive ExaminationDocument6 paginiBirla Institute of Technology & Science, Pilani Comprehensive ExaminationVishal MittalÎncă nu există evaluări
- Compre IIsem 2003-04 SolDocument6 paginiCompre IIsem 2003-04 SolmorigasakiÎncă nu există evaluări
- Test1 Makeup - 2004 - IIsem - Makeup - Sol PDFDocument3 paginiTest1 Makeup - 2004 - IIsem - Makeup - Sol PDFVishal MittalÎncă nu există evaluări
- Linux CommandsDocument6 paginiLinux CommandsYellankiÎncă nu există evaluări
- Issues in SapDocument7 paginiIssues in Sapsaibalaji2kÎncă nu există evaluări
- ToolsDocument9 paginiToolswenijo4171Încă nu există evaluări
- Birla Institute of Technology & Science, Pilani Course Handout Part A: Content DesignDocument8 paginiBirla Institute of Technology & Science, Pilani Course Handout Part A: Content DesignAman BhargavaÎncă nu există evaluări
- BC670 PDFDocument225 paginiBC670 PDFMailin1981Încă nu există evaluări
- DLM8000 GuideDocument14 paginiDLM8000 GuideKiran HareendranÎncă nu există evaluări
- VXVM Interview QuestionsDocument18 paginiVXVM Interview Questionssankar0202100% (3)
- Epm BackupDocument58 paginiEpm BackupdmdunlapÎncă nu există evaluări
- VNX5600 Storage ConfigurationDocument8 paginiVNX5600 Storage ConfigurationTestiesÎncă nu există evaluări
- HCIP StorageDocument291 paginiHCIP StorageDendiÎncă nu există evaluări
- FILESTREAM Storage in SQL Server 2008Document22 paginiFILESTREAM Storage in SQL Server 2008bc2255Încă nu există evaluări
- Unix CommandDocument3 paginiUnix Commandgeo2928Încă nu există evaluări
- 21CS44Document4 pagini21CS44Edu techÎncă nu există evaluări
- Aix Interview QustDocument21 paginiAix Interview QustMaddyGangs100% (2)
- Modernization of TV Samsung LE32C530 F1W - Restoring - BRICK - 100.org - Ua - Programmer's BlogDocument18 paginiModernization of TV Samsung LE32C530 F1W - Restoring - BRICK - 100.org - Ua - Programmer's BlogsopteaÎncă nu există evaluări
- Input Output Intermediate and Look Up FilesDocument12 paginiInput Output Intermediate and Look Up FilesSreenivas Yadav50% (2)
- Using Sap Netweaver With The Oracle Exadata Database MachineDocument20 paginiUsing Sap Netweaver With The Oracle Exadata Database Machineraghav8055Încă nu există evaluări
- Using WinHex and MHDD To Fix and Restore Original 20GB HDDDocument7 paginiUsing WinHex and MHDD To Fix and Restore Original 20GB HDDÁtila Pohl GuimarãesÎncă nu există evaluări
- TroubleshootingDocument35 paginiTroubleshootingyoorin_chayoo7610Încă nu există evaluări
- FOR508 Extra Applis PDFDocument14 paginiFOR508 Extra Applis PDFPhu Cong LeÎncă nu există evaluări
- 8 Logical Disk Manager (LDM) PDFDocument18 pagini8 Logical Disk Manager (LDM) PDFDarmoni LaishramÎncă nu există evaluări
- Oracle Examquestions 1z0-083 v2020-04-14 by William 46qDocument27 paginiOracle Examquestions 1z0-083 v2020-04-14 by William 46qtusharnemadeÎncă nu există evaluări
- Creating A Partition On Windows 8Document7 paginiCreating A Partition On Windows 8Angah LanzÎncă nu există evaluări
- Fat File System. Fat32 Fat16 Fat12Document2 paginiFat File System. Fat32 Fat16 Fat12sadiqabdul297Încă nu există evaluări
- Dell FluidFS Architecture For System PerformanceDocument14 paginiDell FluidFS Architecture For System PerformanceLenin Kumar100% (1)
- OCI 2023 Architect Associate 1Z0 1072 23Document89 paginiOCI 2023 Architect Associate 1Z0 1072 23saw andrewÎncă nu există evaluări
- 3 - Forensic Acquisition and Analysis of VMware Virtual Machine ArtifactsDocument5 pagini3 - Forensic Acquisition and Analysis of VMware Virtual Machine ArtifactsberrezegÎncă nu există evaluări
- SS1 Data Processing Lesson Note Second TermDocument16 paginiSS1 Data Processing Lesson Note Second TermOLUWATAYO OLUWASEUNÎncă nu există evaluări
- 0llcomputer Applications CBSE 9th Answer PDFDocument94 pagini0llcomputer Applications CBSE 9th Answer PDFGopi JampaniÎncă nu există evaluări