Documente Academic
Documente Profesional
Documente Cultură
Aws Solution Architect Associate Demo
Încărcat de
navin_netTitlu original
Drepturi de autor
Formate disponibile
Partajați acest document
Partajați sau inserați document
Vi se pare util acest document?
Este necorespunzător acest conținut?
Raportați acest documentDrepturi de autor:
Formate disponibile
Aws Solution Architect Associate Demo
Încărcat de
navin_netDrepturi de autor:
Formate disponibile
https://www.pass4lead.com/aws-solution-architect-associate.
html
2019 Latest pass4lead AWS-SOLUTION-ARCHITECT-ASSOCIATE PDF and
VCE dumps Download
AWS-SOLUTION-ARCHITECT-
ASSOCIATEQ&As
AWS Certified Solutions Architect - Associate
Pass Amazon AWS-SOLUTION-ARCHITECT-
ASSOCIATE Exam with 100% Guarantee
Free Download Real Questions & Answers PDF and VCE file from:
https://www.pass4lead.com/aws-solution-architect-associate.html
100% Passing Guarantee
100% Money Back Assurance
Following Questions and Answers are all new published by Amazon
Official Exam Center
AWS-SOLUTION-ARCHITECT-ASSOCIATE PDF Dumps | AWS-SOLUTION-ARCHITECT-ASSOCIATE 1Exam
/ 21
Questions | AWS-SOLUTION-ARCHITECT-ASSOCIATE Braindumps
https://www.pass4lead.com/aws-solution-architect-associate.html
2019 Latest pass4lead AWS-SOLUTION-ARCHITECT-ASSOCIATE PDF and
VCE dumps Download
AWS-SOLUTION-ARCHITECT-ASSOCIATE PDF Dumps | AWS-SOLUTION-ARCHITECT-ASSOCIATE 2Exam
/ 21
Questions | AWS-SOLUTION-ARCHITECT-ASSOCIATE Braindumps
https://www.pass4lead.com/aws-solution-architect-associate.html
2019 Latest pass4lead AWS-SOLUTION-ARCHITECT-ASSOCIATE PDF and
VCE dumps Download
QUESTION 1
A Solutions Architect is designing a web application. The web and application tiers need to access the Internet, but they
cannot be accessed from the Internet. Which of the following steps is required?
A. Attach an Elastic IP address to each Amazon EC2 instance and add a route from the private subnet to the public
subnet.
B. Launch a NAT gateway in the public subnet and add a route to it from the private subnet.
C. Launch Amazon EC2 instances in the public subnet and change the security group to allow outbound traffic on port
80.
D. Launch a NAT gateway in the private subnet and deploy a NAT instance in the private subnet.
Correct Answer: B
QUESTION 2
A workload in an Amazon VPC consists of a single web server launched from a custom AMI. Session state is stored in a
database. How should the Solutions Architect modify this workload to be both highly available and scalable?
A. Create a launch configuration with a desired capacity of two web servers across multiple Availability Zones. Create
an Auto Scaling group with the AMI ID of the web server image. Use Amazon Route 53 latency-based routing to
balance traffic across the Auto Scaling group.
B. Create a launch configuration with the AMI ID of the web server image. Create an Auto Scaling group using the newly-
created launch configuration, and a desired capacity of two web servers across multiple regions. Use an Application
Load Balancer (ALB) to balance traffic across the Auto Scaling group.
C. Create a launch configuration with the AMI ID of the web server image. Create an Auto Scaling group using the
newly-created launch configuration, and a desired capacity of two web servers across multiple Availability Zones. Use
an ALB to balance traffic across the Auto Scaling group.
D. Create a launch configuration with the AMI ID of the web server image. Create an Auto Scaling group using the
newly-created launch configuration, and a desired capacity of two web servers across multiple Availability Zones. Use
Amazon Route 53 weighted routing to balance traffic across the Auto Scaling group.
Correct Answer: A
QUESTION 3
An organization (account ID 123412341234) has configured the IAM policy to allow the user to modify his credentials.
What will the below mentioned statement allow the user to perform? { "Version": "2012-10-I7",
"Statement": [{
"Effect": "A||ow",
"Action": [
AWS-SOLUTION-ARCHITECT-ASSOCIATE PDF Dumps | AWS-SOLUTION-ARCHITECT-ASSOCIATE 3Exam
/ 21
Questions | AWS-SOLUTION-ARCHITECT-ASSOCIATE Braindumps
https://www.pass4lead.com/aws-solution-architect-associate.html
2019 Latest pass4lead AWS-SOLUTION-ARCHITECT-ASSOCIATE PDF and
VCE dumps Download
"iam:AddUserToGroup",
"iam:RemoveUserFromGroup",
"iam:GetGroup"
]!
"Resource": "arn:aws:iam:: I23412341234:group/TestingGroup" }I
A. Allow the IAM user to update the membership of the group called TestingGroup
B. The IAM policy will throw an error due to an invalid resource name
C. The IAM policy will allow the user to subscribe to any IAM group
D. Allow the IAM user to delete the TestingGroup
Correct Answer: A
AWS Identity and Access Management is a web service which allows organizations to manage users and user
permissions for various AWS services. If the organization (account ID 123412341234) wants their users to manage
their
subscription to the groups, they should create a relevant policy for that. The below mentioned policy allows the
respective IAM user to update the membership of the group called MarketingGroup.
"Version": "2012-10-I7",
"Statement": [{
"Effect": "A||ow",
"Action": [
"iam:AddUserToGroup",
"iam:RemoveUserFromGroup",
"iam:GetGroup"
]!
"Resource": "arn:aws:iam:: 123412341234:group/ TestingGroup " }I
Reference:
http://docs.aws.amazon.com/IAM/latest/UserGuide/CredentiaIs-Permissions-examples.htm|#creds-po|ici es-credentials
QUESTION 4
A company plans to migrate a website to AWS to use a serverless architecture. The website contains both static and
dynamic content and is accessed by users across the world. The website should maintain sessions for returning users
AWS-SOLUTION-ARCHITECT-ASSOCIATE PDF Dumps | AWS-SOLUTION-ARCHITECT-ASSOCIATE 4Exam
/ 21
Questions | AWS-SOLUTION-ARCHITECT-ASSOCIATE Braindumps
https://www.pass4lead.com/aws-solution-architect-associate.html
2019 Latest pass4lead AWS-SOLUTION-ARCHITECT-ASSOCIATE PDF and
VCE dumps Download
to improve the user experience.
Which service should a Solutions Architect use for a cost-efficient solution with the LOWEST latency?
A. Amazon S3, AWS Lambda, Amazon API Gateway, and Amazon DynamoDB
B. Amazon CloudFront, AWS Lambda, API Gateway, and Amazon RDS
C. Amazon CloudFront, Elastic Load Balancing, Amazon EC2, and Amazon RDS
D. Amazon S3, Amazon CloudFront, AWS Lambda, Amazon API Gateway, and Amazon DynamoDB.
Correct Answer: C
QUESTION 5
A Solutions Architect is designing a shared file system for a company. Multiple users will be accessing it at any given
time. Different teams will have their own directories, and the company wants to secure files so that users can access
only files owned by their team.
How should the Solutions Architect design this?
A. Use Amazon EFS and control permissions by using file-level permissions.
B. Use Amazon S3 and control permissions by using ACLs.
C. Use Amazon EFS and control permissions by using security groups.
D. Use AWS Storage Gateway and control permissions by using AWS Identity and Access Management (IAM)
Correct Answer: D
Reference: https://docs.aws.amazon.com/IAM/latest/UserGuide/id_credentials_access-keys.html
QUESTION 6
A web company is looking to implement an external payment service into their highly available application deployed in a
VPC. Their application EC2 instances are behind a public lacing ELB Auto scaling is used to add additional instances
as
traffic increases under normal load the application runs
2 instances in the Auto Scaling group but at peak it can scale 3x in size. The application instances need to communicate
with the payment service over the Internet which requires whitelisting of all public IP addresses used to communicate
with it. A maximum of 4 whitelisting IP addresses is allowed at a time and can be added through an API.
How should they architect their solution?
A. Route payment requests through two NAT instances setup for High Availability and whitelist the Elastic IP addresses
attached to the MAT instances.
B. Whitelist the VPC Internet Gateway Public IP and route payment requests through the Internet Gateway.
AWS-SOLUTION-ARCHITECT-ASSOCIATE PDF Dumps | AWS-SOLUTION-ARCHITECT-ASSOCIATE 5Exam
/ 21
Questions | AWS-SOLUTION-ARCHITECT-ASSOCIATE Braindumps
https://www.pass4lead.com/aws-solution-architect-associate.html
2019 Latest pass4lead AWS-SOLUTION-ARCHITECT-ASSOCIATE PDF and
VCE dumps Download
C. Whitelist the ELB IP addresses and route payment requests from the Application servers through the ELB.
D. Automatically assign public IP addresses to the application instances in the Auto Scaling group and run a script on
boot that adds each instances public IP address to the payment validation whitelist API.
Correct Answer: A
B is incorrect as you do not have insight into the public ip associated with a VPC Internet Gateways.
C is incorrect as ELB receives a public DNS name.
D would exceed the maximum of 4 whitelisting IP addresses.
QUESTION 7
Your company currently has a 2-tier web application running in an on-premises data center. You have experienced
several infrastructure failures in the past two months resulting in significant financial losses. Your CIO is strongly
agreeing to
move the application to AWS. While working on achieving buy-in from the other company executives, he asks you to
develop a disaster recovery plan to help improve Business continuity in the short term. He specifies a target Recovery
Time
Objective (RTO) of 4 hours and a Recovery Point Objective (RPO) of 1 hour or less. He also asks you to implement the
solution within 2 weeks. Your database is 200GB in size and you have a 20Mbps Internet connection.
How would you do this while minimizing costs?
A. Create an EBS backed private AMI which includes a fresh install of your application. Develop a CloudFormation
template which includes your AMI and the required EC2, AutoScaling, and ELB resources to support deploying the
application across Multiple- Availability-Zones. Asynchronously replicate transactions from your on-premises database
to a database instance in AWS across a secure VPN connection.
B. Deploy your application on EC2 instances within an Auto Scaling group across multiple availability zones.
Asynchronously replicate transactions from your on-premises database to a database instance in AWS across a secure
VPN connection.
C. Create an EBS backed private AMI which includes a fresh install of your application. Setup a script in your data
center to backup the local database every 1 hour and to encrypt and copy the resulting file to an S3 bucket using multi-
part upload.
D. Install your application on a compute-optimized EC2 instance capable of supporting the application\\'s average load.
Synchronously replicate transactions from your on-premises database to a database instance in AWS across a secure
Direct Connect connection.
Correct Answer: A
Overview of Creating Amazon EBS-Backed AMIs First, launch an instance from an AMI that\\'s similar to the AMI that
you\\'d like to create. You can connect to your instance and customize it. When the instance is configured correctly,
ensure data integrity by stopping the instance before you create an AMI, then create the image. When you create an
Amazon EBS-backed AMI, we automatically register it for you. Amazon EC2 powers down the instance before creating
the AMI to ensure that everything on the instance is stopped and in a consistent state during the creation process. If
you\\'re confident that your instance is in a consistent state appropriate for AMI creation, you can tell Amazon EC2 not to
power down and reboot the instance. Some file systems, such as XFS, can freeze and unfreeze activity, making it safe
to create the image without rebooting the instance. During the AMI-creation process, Amazon EC2 creates snapshots of
AWS-SOLUTION-ARCHITECT-ASSOCIATE PDF Dumps | AWS-SOLUTION-ARCHITECT-ASSOCIATE 6Exam
/ 21
Questions | AWS-SOLUTION-ARCHITECT-ASSOCIATE Braindumps
https://www.pass4lead.com/aws-solution-architect-associate.html
2019 Latest pass4lead AWS-SOLUTION-ARCHITECT-ASSOCIATE PDF and
VCE dumps Download
your instance\\'s root volume and any other EBS volumes attached to your instance. If any volumes attached to the
instance are encrypted, the new AMI only launches successfully on instances that support Amazon EBS encryption. For
more information, see Amazon EBS Encryption. Depending on the size of the volumes, it can take several minutes for
the AMI-creation process to complete (sometimes up to 24 hours). You may find it more efficient to create snapshots of
your volumes prior to creating your AMI. This way, only small, incremental snapshots need to be created when the AMI
is created, and the process completes more quickly (the total time for snapshot creation remains the same). For more
information, see Creating an Amazon EBS Snapshot. After the process completes, you have a new AMI and snapshot
created from the root volume of the instance. When you launch an instance using the new AMI, we create a new EBS
volume for its root volume using the snapshot. Both the AMI and the snapshot incur charges to your account until you
delete them. For more information, see Deregistering Your AMI. If you add instance-store volumes or EBS volumes to
your instance in addition to the root device volume, the block device mapping for the new AMI contains information for
these volumes, and the block device mappings for instances that you launch from the new AMI automatically contain
information for these volumes. The instance-store volumes specified in the block device mapping for the new instance
are new and don\\'t contain any data from the instance store volumes of the instance you used to create the AMI. The
data on EBS volumes persists. For more information, see Block Device Mapping.
QUESTION 8
A Solutions Architect is designing network architecture for an application that has compliance requirements. The
application will be hosted on Amazon EC2 instances in a private subnet and will be using Amazon S3 for storing data.
The compliance requirements mandate that the data cannot traverse the public Internet.
What is the MOST secure way to satisfy this requirement?
A. Use a NAT Instance.
B. Use a NAT Gateway.
C. Use a VPC endpoint.
D. Use a Virtual Private Gateway.
Correct Answer: C
Reference: https://aws.amazon.com/blogs/aws/new-vpc-endpoint-for-amazon-s3/
QUESTION 9
A retail company has sensors placed in its physical retail stores. The sensors send messages over HTTP when
customers interact with in-store product displays. A Solutions Architect needs to implement a system for processing
those sensor messages; the results must be available for the Data Analysis team.
Which architecture should be used to meet these requirements?
A. Implement an Amazon API Gateway to server as the HTTP endpoint. Have the API Gateway trigger an AWS Lambda
function to process the messages, and save the results to an Amazon DynamoDB table.
B. Create an Amazon EC2 instance to server as the HTTP endpoint and to process the messages. Save the results to
Amazon S3 for the Data Analysis team to download.
C. Use Amazon Route 53 to direct incoming sensor messages to a Lambda function to process the message and save
the results to a Amazon DynamoDB table.
AWS-SOLUTION-ARCHITECT-ASSOCIATE PDF Dumps | AWS-SOLUTION-ARCHITECT-ASSOCIATE 7Exam
/ 21
Questions | AWS-SOLUTION-ARCHITECT-ASSOCIATE Braindumps
https://www.pass4lead.com/aws-solution-architect-associate.html
2019 Latest pass4lead AWS-SOLUTION-ARCHITECT-ASSOCIATE PDF and
VCE dumps Download
D. Use AWS Direct Connect to connect sensors to DynamoDB so that data can be written directly to a DynamoDB table
where it can be accessed by the Data Analysis team.
Correct Answer: A
QUESTION 10
You\\'re running an application on-premises due to its dependency on non-x86 hardware and want to use AWS for data
backup. Your backup application is only able to write to POSIX-compatible block- based storage. You have 140TB of
data and would like to mount it as a single folder on your file server Users must be able to access portions of this data
while the backups are taking place. What backup solution would be most appropriate for this use case?
A. Use Storage Gateway and configure it to use Gateway Cached volumes.
B. Configure your backup software to use S3 as the target for your data backups.
C. Configure your backup software to use Glacier as the target for your data backups.
D. Use Storage Gateway and configure it to use Gateway Stored volumes.
Correct Answer: D
Data is hosted on the On-premise server as well. The requirement for 140TB is for file server On- Premise more to
confuse and not in AWS. Just need a backup solution hence stored instead of cached volumes.
QUESTION 11
A Solutions Architect is designing a solution for a media company that will stream large amounts of data from an
Amazon EC2 instance. The data streams are typically large and sequential, and must be able to support up to 500
MB/s.
Which storage type will meet the performance requirements of this application?
A. EBS Provisioned IOPS SSD
B. EBS General Purpose SSD
C. EBS Cold HDD
D. EBS Throughput Optimized HDD
Correct Answer: D
QUESTION 12
An application currently stores objects in Amazon S3-Standard. The application accesses new objects frequently for one
week. After one week, they are accessed occasionally for analysis batch jobs. A Solutions Architect has been asked to
reduce storage costs for the application while allowing immediate access for batch jobs.
How can costs be reduced without reducing data durability?
AWS-SOLUTION-ARCHITECT-ASSOCIATE PDF Dumps | AWS-SOLUTION-ARCHITECT-ASSOCIATE 8Exam
/ 21
Questions | AWS-SOLUTION-ARCHITECT-ASSOCIATE Braindumps
https://www.pass4lead.com/aws-solution-architect-associate.html
2019 Latest pass4lead AWS-SOLUTION-ARCHITECT-ASSOCIATE PDF and
VCE dumps Download
A. Create a lifecycle policy that moves Amazon S3 data to Amazon S3 One Zone-Infrequent Access storage after 7
days. After 30 days, move the data to Amazon Glacier.
B. Keep the data on Amazon S3, and create a lifecycle policy to move S3 data to Amazon Glacier after 7 days.
C. Move all Amazon S3 data to S3 Standard-Infrequent Access storage, and create a lifecycle policy to move the data
to Amazon Glacier after 7 days.
D. Keep the data on Amazon S3, then create a lifecycle policy to move the data to S3 Standard-Infrequent Access
storage after 7 days.
Correct Answer: A
Reference: https://aws.amazon.com/blogs/aws/new-automatic-cost-optimization-for-amazon-s3-via-intelligent-tiering/
QUESTION 13
A Solutions Architect is designing an application that is expected to have millions of users. The Architect needs options
to store session data. Which option is the MOST performant?
A. Amazon ElastiCache
B. Amazon RDS
C. Amazon S3
D. Amazon EFS
Correct Answer: B
QUESTION 14
A company has a popular multi-player mobile game hosted in its on-premises datacenter. The current infrastructure can
no longer keep up with demand and the company is considering a move to the cloud. Which solution should a Solutions
Architect recommend as the MOST scalable and cost-effective solution to meet these needs?
A. Amazon EC2 and an Application Load Balancer
B. Amazon S3 and Amazon CloudFront
C. Amazon EC2 and Amazon Elastic Transcoder
D. AWS Lambda and Amazon API Gateway
Correct Answer: B
QUESTION 15
An application stores data in an Amazon RDS PostgreSQL Multi-AZ database instance. The ratio of read requests to
write requests is about 2 to 1. Recent increases in traffic are causing very high latency. How can this problem be
corrected?
AWS-SOLUTION-ARCHITECT-ASSOCIATE PDF Dumps | AWS-SOLUTION-ARCHITECT-ASSOCIATE 9Exam
/ 21
Questions | AWS-SOLUTION-ARCHITECT-ASSOCIATE Braindumps
https://www.pass4lead.com/aws-solution-architect-associate.html
2019 Latest pass4lead AWS-SOLUTION-ARCHITECT-ASSOCIATE PDF and
VCE dumps Download
A. Create a similar RDS PostgreSQL instance and direct all traffic to it.
B. Use the secondary instance of the Multiple Availability Zone for read traffic only.
C. Create a read replica and send half of all traffic to it.
D. Create a read replica and send all read traffic to it.
Correct Answer: D
Reference: https://docs.aws.amazon.com/AmazonRDS/latest/UserGuide/Concepts.MultiAZ.html
QUESTION 16
You are designing an SSUTLS solution that requires HTTPS clients to be authenticated by the Web server using client
certificate authentication. The solution must be resilient. Which of the following options would you consider for
configuring the web server infrastructure? (Choose two.)
A. Configure ELB with TCP listeners on TCP/4d3. And place the Web servers behind it.
B. Configure your Web servers with EIPS Place the Web servers in a Route53 Record Set and configure health checks
against all Web servers.
C. Configure ELB with HTTPS listeners, and place the Web servers behind it.
D. Configure your web servers as the origins for a CloudFront distribution. Use custom SSL certificates on your
CloudFront distribution.
Correct Answer: AB
This question is regarding "two-way" SSL authentication.
Currently, ELBs cannot support authentication for the client side SSL/TLS cert required for two-way SSL authentication
to succeed. Therefore, you only have two options:
A. Configure the ELB with a TCP/443 listener. This is effectively TLS "pass through" mode, where the TLS connection
does not terminate on the ELB, it is passed through and decrypted on the back-end servers. This will cause quite a bit
of
CPU overhead on the back-end instances, due to the lack of TLS offload that cannot happen on the ELB, so an auto-
scaling group which monitors the web server CPU metrics would be essential here. (Not that you probably wouldn\\'t
have it
anyway, just saying!) B. Don\\'t use an ELB. Just have the web servers act as the endpoint for the traffic, and let
Route53 DNS serve in the place of the ELB by load balancing client DNS queries across the web servers.
C and D are not options here, since neither are supported by AWS.
QUESTION 17
You are designing a data leak prevention solution for your VPC environment. You want your VPC Instances to be able
to access software depots and distributions on the Internet for product updates. The depots and distributions are
AWS-SOLUTION-ARCHITECT-ASSOCIATE PDF Dumps | AWS-SOLUTION-ARCHITECT-ASSOCIATE10
Exam
/ 21
Questions | AWS-SOLUTION-ARCHITECT-ASSOCIATE Braindumps
https://www.pass4lead.com/aws-solution-architect-associate.html
2019 Latest pass4lead AWS-SOLUTION-ARCHITECT-ASSOCIATE PDF and
VCE dumps Download
accessible via third party CONs by their URLs. You want to explicitly deny any other outbound connections from your
VPC instances to hosts on the Internet.
Which of the following options would you consider?
A. Configure a web proxy server in your VPC and enforce URL-based rules for outbound access Remove default
routes.
B. Implement security groups and configure outbound rules to only permit traffic to software depots.
C. Move all your instances into private VPC subnets remove default routes from all routing tables and add specific
routes to the software depots and distributions only.
D. Implement network access control lists to all specific destinations, with an Implicit deny as a rule.
Correct Answer: A
Organizations usually implement proxy solutions to provide URL and web content filtering, IDS/IPS, data loss
prevention, monitoring, and advanced threat protection. https://d0.awsstatic.com/aws-
answers/Controlling_VPC_Egress_Traffic.pdf
QUESTION 18
You have deployed a three-tier web application in a VPC with a CIOR block of 10 0 0 0/28. You initially deploy two web
servers, two application servers, two database servers and one NAT instance tor a total of seven EC2 instances. The
web. Application and database servers are deployed across two availability zones (AZs). You also deploy an ELB in
front of the two web servers, and use Route53 for DNS Web (raffle gradually increases in the first few days following
the
deployment, so you attempt to double the number of instances in each tier of the application to handle the new load
unfortunately some of these new instances fail to launch.
Which of the following could De the root caused? (Choose two.)
A. AWS reserves the first and the last private IP address in each subnet\\'s CIDR block so you do not have enough
addresses left to launch all of the new EC2 instances
B. The Internet Gateway (IGW) of your VPC has scaled-up, adding more instances to handle the traffic spike, reducing
the number of available private IP addresses for new instance launches
C. The ELB has scaled-up, adding more instances to handle the traffic spike, reducing the number of available private
IP addresses for new instance launches
D. AWS reserves one IP address in each subnet\\'s CIDR block for Route53 so you do not have enough addresses left
to launch all of the new EC2 instances
E. AWS reserves the first four and the last IP address in each subnet\\'s CIDR block so you do not have enough
addresses left to launch all of the new EC2 instances
Correct Answer: CE
http://docs.aws.amazon.com/AmazonVPC/latest/UserGuide/VPC_Subnets.html
AWS-SOLUTION-ARCHITECT-ASSOCIATE PDF Dumps | AWS-SOLUTION-ARCHITECT-ASSOCIATE11
Exam
/ 21
Questions | AWS-SOLUTION-ARCHITECT-ASSOCIATE Braindumps
https://www.pass4lead.com/aws-solution-architect-associate.html
2019 Latest pass4lead AWS-SOLUTION-ARCHITECT-ASSOCIATE PDF and
VCE dumps Download
QUESTION 19
A Solutions Architect is designing a multi-tier application consisting of an Application Load Balancer, an Amazon RDS
database instance, and an Auto Scaling group on Amazon EC2 instances. Each tier is in a separate subnet. There are
some EC2 instances in the subnet that belong to another application. The RDS database instance should accept traffic
only from the EC2 instances in the Auto Scaling group.
What should be done to meet these requirements?
A. Configure the inbound network ACLs on the database subnet to accept traffic from the IP addresses of the EC2
instances only.
B. Configure the inbound rules on the security group associated with the RDS database instance. Set the source to the
security group associated with instances in the Auto Scaling group.
C. Configure the outbound rules on the security group associated with the Auto Scaling group. Set the destination to the
security group associated with the RDS database instance.
D. Configure the inbound network ACLs on the database subnet to accept traffic only from the CIDR range of the subnet
used by the Auto Scaling group.
Correct Answer: C
QUESTION 20
Can a \\'user\\' be associated with multiple AWS accounts?
A. No
B. Yes
Correct Answer: A
AWS-SOLUTION-ARCHITECT-ASSOCIATE PDF Dumps | AWS-SOLUTION-ARCHITECT-ASSOCIATE12
Exam
/ 21
Questions | AWS-SOLUTION-ARCHITECT-ASSOCIATE Braindumps
https://www.pass4lead.com/aws-solution-architect-associate.html
2019 Latest pass4lead AWS-SOLUTION-ARCHITECT-ASSOCIATE PDF and
VCE dumps Download
QUESTION 21
IAM provides several policy templates you can use to automatically assign permissions to the groups you create. The
_____ policy template gives the Admins group permission to access all account resources, except your AWS account
information
A. Read Only Access
B. Power User Access
C. AWS Cloud Formation Read Only Access
D. Administrator Access
Correct Answer: B
AWS managed policies are designed to provide permissions for many common use cases. For example, there are AWS
managed policies that define typical permissions for administrators (all access), for power users (all access except IAM),
and for other various levels of access to AWS services. AWS managed policies make it easier for you to assign
appropriate permissions to users, groups, and roles than if you had to write the policies yourself. http://
docs.aws.amazon.com/IAM/latest/UserGuide/ access_policies_managed-vs-inline.html
QUESTION 22
An application launched on Amazon EC2 instances needs to publish personally identifiable information (PII) about
customers using Amazon SNS. The application is launched in private subnets within an Amazon VPC. Which is the
MOST secure way to allow the application to access service endpoints in the same region?
A. Use an internet gateway.
B. Use AWS PrivateLink.
C. Use a NAT gateway.
D. Use a proxy instance.
Correct Answer: B
QUESTION 23
A company wants to run a static website served through Amazon CloudFront.
What is an advantage of storing the website content in an S3 bucket instead of an EBS volume?
A. S3 buckets are replicated globally, allowing for large scalability. EBS volumes are replicated only within a region.
B. S3 is an origin for CloudFront. EBS volumes would need EC2 instances behind an Elastic Load Balancing load
balancer to be an origin.
C. S3 buckets can be encrypted, allowing for secure storage of the web files. EBS volumes cannot be encrypted.
D. S3 buckets support object-level read throttling, preventing abuse. EBS volumes do not provide object-level throttling.
AWS-SOLUTION-ARCHITECT-ASSOCIATE PDF Dumps | AWS-SOLUTION-ARCHITECT-ASSOCIATE13
Exam
/ 21
Questions | AWS-SOLUTION-ARCHITECT-ASSOCIATE Braindumps
https://www.pass4lead.com/aws-solution-architect-associate.html
2019 Latest pass4lead AWS-SOLUTION-ARCHITECT-ASSOCIATE PDF and
VCE dumps Download
Correct Answer: B
QUESTION 24
An AWS customer is deploying an application mat is composed of an AutoScaling group of EC2 Instances.
The customers\\' security policy requires that every outbound connection from these instances to any other service
within the customers Virtual Private Cloud must be authenticated using a unique x 509 certificate that contains the
specific
instance-id.
In addition, an x 509 certificates must Designed by the customer\\'s Key management service in order to be trusted for
authentication.
Which of the following configurations will support these requirements?
A. Configure an IAM Role that grants access to an Amazon S3 object containing a signed certificate and configure me
Auto Scaling group to launch instances with this role Have the instances bootstrap get the certificate from Amazon S3
upon first boot.
B. Embed a certificate into the Amazon Machine Image that is used by the Auto Scaling group Have the launched
instances generate a certificate signature request with the instance\\'s assigned instance- id to the Key management
service for signature.
C. Configure the Auto Scaling group to send an SNS notification of the launch of a new instance to the trusted key
management service. Have the Key management service generate a signed certificate and send it directly to the newly
launched instance.
D. Configure the launched instances to generate a new certificate upon first boot Have the Key management service
poll the AutoScaling group for associated instances and send new instances a certificate signature (hat contains the
specific instance-id.
Correct Answer: A
http://jayendrapatil.com/tag/iam/
QUESTION 25
A Solutions Architect needs to design a centralized logging solution for a group of web applications running on Amazon
EC2 instances. The solution requires minimal development effort due to budget constraints. Which of the following
should the Architect recommend?
A. Create a crontab job script in each instance to push the logs regularly to Amazon S3.
B. Install and configure Amazon CloudWatch Logs agent in the Amazon EC2 instances.
C. Enable Amazon CloudWatch Events in the AWS Management Console.
D. Enable AWS CloudTrail to map all API calls invoked by the applications.
Correct Answer: B
AWS-SOLUTION-ARCHITECT-ASSOCIATE PDF Dumps | AWS-SOLUTION-ARCHITECT-ASSOCIATE14
Exam
/ 21
Questions | AWS-SOLUTION-ARCHITECT-ASSOCIATE Braindumps
https://www.pass4lead.com/aws-solution-architect-associate.html
2019 Latest pass4lead AWS-SOLUTION-ARCHITECT-ASSOCIATE PDF and
VCE dumps Download
QUESTION 26
A client has set up an Auto Scaling group associated with a load balancer. The client has noticed that instances
launched by the Auto Scaling group are reported unhealthy as the result of an Elastic Load Balancing (ELB) health
check, but these unhealthy instances are not being terminated.
What can a Solutions Architect do to ensure that the instances marked unhealthy will be terminated and replaced?
A. Increase the value for the health check interval set on the ELB load balancer.
B. Change the thresholds set on the Auto Scaling group health check.
C. Change the health check type to ELB for the Auto Scaling group.
D. Change the health check set on the ELB load balancer to use TCP rather than HTTP checks.
Correct Answer: C
Reference: http://docs.aws.amazon.com/AutoScaling/latest/DeveloperGuide/as-add-elb-healthcheck.html
QUESTION 27
A customer has a 10 GB AWS Direct Connect connection to an AWS region where they have a web application hosted
on Amazon Elastic Computer Cloud (EC2). The application has dependencies on an on-premises mainframe database
that uses a BASE (Basic Available. Sort stale Eventual consistency) rather than an ACID (Atomicity. Consistency
isolation. Durability) consistency model. The application is exhibiting undesirable behavior because the database is not
able to handle the volume of writes. How can you reduce the load on your on-premises database resources in the most
cost-effective way?
A. Use an Amazon Elastic Map Reduce (EMR) S3DistCp as a synchronization mechanism between the on-premises
database and a Hadoop cluster on AWS.
B. Modify the application to write to an Amazon SQS queue and develop a worker process to flush the queue to the on-
premises database.
C. Modify the application to use DynamoDB to feed an EMR cluster which uses a map function to write to the on-
premises database.
D. Provision an RDS read-replica database on AWS to handle the writes and synchronize the two databases using Data
Pipeline.
Correct Answer: B
QUESTION 28
A Solutions Architect must design a storage solution for incoming billing reports in CSV format. The data does not need
to be scanned frequently and is discarded after 30 days. Which service will be MOST cost-effective in meeting these
requirements?
AWS-SOLUTION-ARCHITECT-ASSOCIATE PDF Dumps | AWS-SOLUTION-ARCHITECT-ASSOCIATE15
Exam
/ 21
Questions | AWS-SOLUTION-ARCHITECT-ASSOCIATE Braindumps
https://www.pass4lead.com/aws-solution-architect-associate.html
2019 Latest pass4lead AWS-SOLUTION-ARCHITECT-ASSOCIATE PDF and
VCE dumps Download
A. Import the logs into an RDS MySQL instance.
B. Use AWS Data Pipeline to import the logs into a DynamoDB table.
C. Write the files to an S3 bucket and use Amazon Athena to query the data.
D. Import the logs to an Amazon Redshift cluster
Correct Answer: C
QUESTION 29
A Solutions Architect is designing solution with AWS Lambda where different environments require different database
passwords. What should the Architect do to accomplish this in a secure and scalable way?
A. Create a Lambda function for each individual environment.
B. Use Amazon DynamoDB to store environmental variables.
C. Use encrypted AWS Lambda environmental variables.
D. Implement a dedicated Lambda function for distributing variables.
Correct Answer: C
QUESTION 30
A company plans to deploy a new application in AWS that reads and writes information to a database. The company
wants to deploy the application in two different AWS Regions in an active-active configuration. The databases need to
replicate to keep information in sync.
What should be used to meet these requirements?
A. Amazon Athena with Amazon S3 cross-region replication
B. AWS Database Migration Service with change data capture
C. Amazon DynamoDB with global tables
D. Amazon RDS for PostgreSQL with a cross-region Read Replica
Correct Answer: D
QUESTION 31
A customer has a production application that frequently overwrites and deletes data, the application requires the most
up-to-date version of the data every time it is requested. Which storage should a Solutions Architect recommend to bet
accommodate this use case?
A. Amazon S3
AWS-SOLUTION-ARCHITECT-ASSOCIATE PDF Dumps | AWS-SOLUTION-ARCHITECT-ASSOCIATE16
Exam
/ 21
Questions | AWS-SOLUTION-ARCHITECT-ASSOCIATE Braindumps
https://www.pass4lead.com/aws-solution-architect-associate.html
2019 Latest pass4lead AWS-SOLUTION-ARCHITECT-ASSOCIATE PDF and
VCE dumps Download
B. Amazon RDS
C. Amazon RedShift
D. AWS Storage Gateway
Correct Answer: A
QUESTION 32
An organization runs an online media site, hosted on-premises. An employee posted a product review that contained
videos and pictures. The review went viral and the organization needs to handle the resulting spike in website traffic.
What action would provide an immediate solution?
A. Redesign the website to use Amazon API Gateway, and use AWS Lambda to deliver content.
B. Add server instances using Amazon EC2 and use Amazon Route 53 with a failover routing policy.
C. Serve the images and videos via an Amazon CloudFront distribution created using the news site as the origin.
D. Use Amazon ElasticCache for Redis for caching and reducing the load requests from the origin.
Correct Answer: C
QUESTION 33
A Solutions Architect is designing a solution that includes a managed VPN connection. To monitor whether the VPN
connection is up or down, the Architect should use:
A. an external service to ping the VPN endpoint from outside the VPC.
B. AWS CloudTrail to monitor the endpoint.
C. the CloudWatch TunnelState Metric.
D. an AWS Lambda function that parses the VPN connection logs.
Correct Answer: C
Reference: https://docs.aws.amazon.com/AmazonVPC/latest/UserGuide/monitoring-cloudwatch-vpn.html
QUESTION 34
A company is creating a web application that will run on an Amazon EC2 instance. The application on the instance
needs access to an Amazon DynamoDB table for storage. What should be done to meet these requirements?
A. Create another AWS account root user with permissions to the DynamoDB table.
B. Create an IAM role and assign the role to the EC2 instance with permissions to the DynamoDB table.
C. Create an identity provider and assign the identity provider to the EC2 instance with permissions to the DynamoDB
AWS-SOLUTION-ARCHITECT-ASSOCIATE PDF Dumps | AWS-SOLUTION-ARCHITECT-ASSOCIATE17
Exam
/ 21
Questions | AWS-SOLUTION-ARCHITECT-ASSOCIATE Braindumps
https://www.pass4lead.com/aws-solution-architect-associate.html
2019 Latest pass4lead AWS-SOLUTION-ARCHITECT-ASSOCIATE PDF and
VCE dumps Download
table.
D. Create identity federation with permissions to the DynamoDB table.
Correct Answer: B
QUESTION 35
Which of the following statements is true of IAM?
A. If you are configuring MFA for a user who will use a smartphone to generate an OTP, you must have the smartphone
available in order to finish the wizard.
B. If you are configuring MFA for a user who will use a smartphone to generate an OTP, the smartphone is not required
in order to finish the wizard.
C. If you are configuring MFA for a user who will use a smartphone to generate an OTP, you can finish the wizard on
any device and later use the smartphone for authentication.
D. None of these are correct.
Correct Answer: A
MFA can be used either with a specific MFA-enabled device or by installing an application on a smartphone. If a user
chooses to use her smartphone, physical access to the device is required in order to complete the configuration wizard.
http://docs.aws.amazon.com/IAM/latest/UserGuide/GenerateMFAConfig.html
QUESTION 36
A company hosts a popular web application. The web application connects to a database running in a private VPC
subnet. The web servers must be accessible only to customers on an SSL connection. The RDS MySQL database
server must be accessible only from the web servers.
How should the Architect design a solution to meet the requirements without impacting running applications?
A. Create a network ACL on the web server\\'s subnet, and allow HTTPS inbound and MySQL outbound. Place both
database and web servers on the same subnet.
B. Open an HTTPS port on the security group for web servers and set the source to 0.0.0.0/0. Open the MySQL port on
the database security group and attach it to the MySQL instance. Set the source to Web Server Security Group.
C. Create a network ACL on the web server\\'s subnet, and allow HTTPS inbound, and specify the source as 0.0.0.0/0.
Create a network ACL on a database subnet, allow MySQL port inbound for web servers, and deny all outbound traffic.
D. Open the MySQL port on the security group for web servers and set the source to 0.0.0.0/0. Open the HTTPS port on
the database security group and attach it to the MySQL instance. Set the source to Web Server Security Group.
Correct Answer: B
QUESTION 37
AWS-SOLUTION-ARCHITECT-ASSOCIATE PDF Dumps | AWS-SOLUTION-ARCHITECT-ASSOCIATE18
Exam
/ 21
Questions | AWS-SOLUTION-ARCHITECT-ASSOCIATE Braindumps
https://www.pass4lead.com/aws-solution-architect-associate.html
2019 Latest pass4lead AWS-SOLUTION-ARCHITECT-ASSOCIATE PDF and
VCE dumps Download
A large media site has multiple applications in Amazon ECS. A Solutions Architect needs to use content metadata and
route traffic to specific services. What is the MOST efficient method to perform this task?
A. Use an AWS Classic Load Balancer with a host-based routing option to route traffic to the correct service.
B. Use the AWS CLI to update Amazon Route 53 hosted zone to route traffic as services get updated.
C. Use an AWS Application Load Balancer with host-based routing option to route traffic to the correct service.
D. Use Amazon CloudFront to manage and route traffic to the correct service.
Correct Answer: A
QUESTION 38
A company has a website running on Amazon EC2. The application DNS name points to an Elastic IP address
associated with the EC2 instance. In the event of an attack on the website coming from a specific IP address, the
company wants a way to block the offending IP address.
Which tool or service should a Solutions Architect recommend to block the IP address?
A. Security groups
B. Network ACL
C. AWS WAF
D. AWS Shield
Correct Answer: C
QUESTION 39
A Solutions Architect must design a solution that encrypts data in Amazon S3. Corporate policy mandates encryption
keys be generated and managed on premises. Which solution should the Architect use to meet the security
requirements?
A. AWS CloudHSM
B. SSE-KMS: Server-side encryption with AWS KMS managed keys
C. SSE-S3: Server-side encryption with Amazon-managed master key
D. SSE-C: Server-side encryption with customer-provided encryption keys
Correct Answer: B
QUESTION 40
For each DB Instance class, what is the maximum size of associated storage capacity?
AWS-SOLUTION-ARCHITECT-ASSOCIATE PDF Dumps | AWS-SOLUTION-ARCHITECT-ASSOCIATE19
Exam
/ 21
Questions | AWS-SOLUTION-ARCHITECT-ASSOCIATE Braindumps
https://www.pass4lead.com/aws-solution-architect-associate.html
2019 Latest pass4lead AWS-SOLUTION-ARCHITECT-ASSOCIATE PDF and
VCE dumps Download
A. 5GB
B. 1TB
C. 6TB
D. 500GB
Correct Answer: C
"You can now create MySQL, PostgreSQL, and Oracle RDS database instances with up to 6TB of storage and SQL
Server RDS database instances with up to 4TB of storage when using the Provisioned IOPS and General Purpose
(SSD) storage types. Existing MySQL, PostgreSQL, and Oracle RDS database instances can be scaled to these new
database storage limits without any downtime."
AWS-SOLUTION- AWS-SOLUTION- AWS-SOLUTION-
ARCHITECT-ASSOCIATE ARCHITECT-ASSOCIATE ARCHITECT-ASSOCIATE
PDF Dumps Exam Questions Braindumps
AWS-SOLUTION-ARCHITECT-ASSOCIATE PDF Dumps | AWS-SOLUTION-ARCHITECT-ASSOCIATE20
Exam
/ 21
Questions | AWS-SOLUTION-ARCHITECT-ASSOCIATE Braindumps
https://www.pass4lead.com/aws-solution-architect-associate.html
2019 Latest pass4lead AWS-SOLUTION-ARCHITECT-ASSOCIATE PDF and
VCE dumps Download
To Read the Whole Q&As, please purchase the Complete Version from Our website.
Try our product !
100% Guaranteed Success
100% Money Back Guarantee
365 Days Free Update
Instant Download After Purchase
24x7 Customer Support
Average 99.9% Success Rate
More than 800,000 Satisfied Customers Worldwide
Multi-Platform capabilities - Windows, Mac, Android, iPhone, iPod, iPad, Kindle
We provide exam PDF and VCE of Cisco, Microsoft, IBM, CompTIA, Oracle and other IT Certifications.
You can view Vendor list of All Certification Exams offered:
https://www.pass4lead.com/allproducts
Need Help
Please provide as much detail as possible so we can best assist you.
To update a previously submitted ticket:
Any charges made through this site will appear as Global Simulators Limited.
All trademarks are the property of their respective owners.
Copyright © pass4lead, All Rights Reserved.
AWS-SOLUTION-ARCHITECT-ASSOCIATE PDF Dumps | AWS-SOLUTION-ARCHITECT-ASSOCIATE21
Exam
/ 21
Questions | AWS-SOLUTION-ARCHITECT-ASSOCIATE Braindumps
Powered by TCPDF (www.tcpdf.org)
S-ar putea să vă placă și
- AWS Solutions Architect Certification Case Based Practice Questions Latest Edition 2023De la EverandAWS Solutions Architect Certification Case Based Practice Questions Latest Edition 2023Încă nu există evaluări
- Sample Que Ans1Document194 paginiSample Que Ans1Sid DeshmukhÎncă nu există evaluări
- Website: Vce To PDF Converter: Facebook: Twitter:: Saa-C02.Vceplus - Premium.Exam.65QDocument22 paginiWebsite: Vce To PDF Converter: Facebook: Twitter:: Saa-C02.Vceplus - Premium.Exam.65Qharyati rasyidÎncă nu există evaluări
- AWS Solution Architect Certification Exam Practice Paper 2019De la EverandAWS Solution Architect Certification Exam Practice Paper 2019Evaluare: 3.5 din 5 stele3.5/5 (3)
- Amazon Web Services Prep4sure Saa-C02 Vce Download 2021-Jun-23 by Michell 277q VceDocument17 paginiAmazon Web Services Prep4sure Saa-C02 Vce Download 2021-Jun-23 by Michell 277q VcePushan GhoshÎncă nu există evaluări
- Exam Questions AWS-Solution-Architect-AssociateDocument6 paginiExam Questions AWS-Solution-Architect-AssociatetestÎncă nu există evaluări
- Exam Questions SAA-C02Document7 paginiExam Questions SAA-C02debjeettoniÎncă nu există evaluări
- AWS Solution Architect Associate Exam DumpsDocument9 paginiAWS Solution Architect Associate Exam DumpsSanjay Suryadevra0% (2)
- Aws Certified Solutions Architect Associate TrainingDocument21 paginiAws Certified Solutions Architect Associate TrainingCloud Sarainfo50% (2)
- Free AWS Solutions Architect Practice Test Questions - Exam Prep - SimplilearnDocument24 paginiFree AWS Solutions Architect Practice Test Questions - Exam Prep - SimplilearnRavish MalhotraÎncă nu există evaluări
- AWS Solution Architect CertificationDocument6 paginiAWS Solution Architect Certificationpappupass200467% (12)
- Practice Test 6Document50 paginiPractice Test 6AVINASHÎncă nu există evaluări
- AWS Solutions AssociateDocument7 paginiAWS Solutions AssociateAnonymous aeT7bvQÎncă nu există evaluări
- AWS Certified Solutions Architect Associate Practice Test 2Document134 paginiAWS Certified Solutions Architect Associate Practice Test 2AbhishekÎncă nu există evaluări
- AWS Certified Solutions Architect Associate Exam Guide BETADocument3 paginiAWS Certified Solutions Architect Associate Exam Guide BETAmp.rathanÎncă nu există evaluări
- Amazon - Pass4sure - Aws Solution Architect Associate - Sample.question.2021 May 30.by - Nathan.248q.vceDocument45 paginiAmazon - Pass4sure - Aws Solution Architect Associate - Sample.question.2021 May 30.by - Nathan.248q.vcePavan Kumar Sresty100% (1)
- Click To Edit Master Title Style AWS Certified Solutions Architect Crash Course V2Document136 paginiClick To Edit Master Title Style AWS Certified Solutions Architect Crash Course V2yugandhar_ch100% (2)
- Amazon AWS Certified Solutions Architect Associate PDFDocument369 paginiAmazon AWS Certified Solutions Architect Associate PDFAkrem Zitouni100% (1)
- Amazon - Pass4sures - Aws Certified Solutions Architect AssociateDocument69 paginiAmazon - Pass4sures - Aws Certified Solutions Architect Associateshai100% (3)
- AWS Solutions Architect Lesson 0Document13 paginiAWS Solutions Architect Lesson 0Selvaganapathy DuraiswamyÎncă nu există evaluări
- The Ultimate AWS Solutions Architect Certification Guide PDFDocument8 paginiThe Ultimate AWS Solutions Architect Certification Guide PDFSaddam MullaÎncă nu există evaluări
- Whizlabs Practice Test IDocument56 paginiWhizlabs Practice Test IdebashishÎncă nu există evaluări
- Cloud ArchitectDocument8 paginiCloud ArchitectSubhadip Ghosh0% (1)
- AWS Solutions Architect Professional Questions AnswersDocument7 paginiAWS Solutions Architect Professional Questions AnswersExamsure975% (4)
- AWS Solution ArchitectDocument115 paginiAWS Solution ArchitectNeerajroy G67% (3)
- Amazon Lead2pass AWS-Solution-Architect-Associate Actual Test V2019-Jun-03 by Devin 328q VceDocument43 paginiAmazon Lead2pass AWS-Solution-Architect-Associate Actual Test V2019-Jun-03 by Devin 328q VceJayakrishna Injeti100% (2)
- Sanford N. AWS Certified Solutions Architect Associate (SAA-C02) 2021Document378 paginiSanford N. AWS Certified Solutions Architect Associate (SAA-C02) 2021Edgar Alfonso Godoy López100% (1)
- AWS Certified Solutions Architect Official - AWS Certified Solutions ArchitectDocument16 paginiAWS Certified Solutions Architect Official - AWS Certified Solutions Architecthowardchoi11% (19)
- Pass Amazon AWS Certified Solutions Architect - Associate Certification Exam in First Attempt Guaranteed!Document5 paginiPass Amazon AWS Certified Solutions Architect - Associate Certification Exam in First Attempt Guaranteed!Jan Rey AltivoÎncă nu există evaluări
- AWS Solution ArchitectDocument5 paginiAWS Solution ArchitectArunkumar Palathumpattu50% (4)
- AWS Solution Architect Associate Certification (SAA-C02) & Q/ADocument5 paginiAWS Solution Architect Associate Certification (SAA-C02) & Q/AJasiekÎncă nu există evaluări
- Aws Solution Architect Preparation GuideDocument201 paginiAws Solution Architect Preparation GuideSaisandeep K M100% (2)
- Skipped: Practice Exam 2 - ResultsDocument42 paginiSkipped: Practice Exam 2 - ResultsAkash PaulÎncă nu există evaluări
- AWS Certified Solutions Architect Professional Blueprint PDFDocument37 paginiAWS Certified Solutions Architect Professional Blueprint PDFrajinikvÎncă nu există evaluări
- 30091Document12 pagini30091hemanth-07100% (1)
- Aws OverviewDocument36 paginiAws OverviewDebabrata BiswasÎncă nu există evaluări
- AWS ArchitectDocument72 paginiAWS ArchitectRonald Quevedo100% (1)
- AWS CSAA Practice-Questions DCT V08-Ambu0dDocument411 paginiAWS CSAA Practice-Questions DCT V08-Ambu0dMihai Eminescu100% (10)
- Aws TestDocument122 paginiAws TestNguyễn CươngÎncă nu există evaluări
- ExamTestSAA PDFDocument289 paginiExamTestSAA PDFPham Xuan Ngoc0% (2)
- AWS Certified Solutions Architect - Associate Exam Dumps With PDF and VCE Download (1-50)Document11 paginiAWS Certified Solutions Architect - Associate Exam Dumps With PDF and VCE Download (1-50)Jatin Kumar69% (16)
- Products Whizcard Saa c02!26!23Document132 paginiProducts Whizcard Saa c02!26!23HARSHAD BAJPAIÎncă nu există evaluări
- AWS Certified Solutions Architect - Associate Dumps PrepawayDocument100 paginiAWS Certified Solutions Architect - Associate Dumps PrepawayNaimat Ali86% (7)
- Aws 25Document37 paginiAws 25kdr akm100% (1)
- 7 Ways To Reduce AWS CostDocument4 pagini7 Ways To Reduce AWS CostProyectos de AutorÎncă nu există evaluări
- AWS Course Content MindQfghfgDocument8 paginiAWS Course Content MindQfghfgSaidi Reddy100% (1)
- Amazon: Exam Questions AWS-Solution-Architect-AssociateDocument29 paginiAmazon: Exam Questions AWS-Solution-Architect-AssociatePritam Jena100% (1)
- AWS Solutions Architect Certification TrainingDocument13 paginiAWS Solutions Architect Certification TrainingAbdullaHanèèfaÎncă nu există evaluări
- AWS Technical Essentials CourseDocument2 paginiAWS Technical Essentials Coursepriya_psalmsÎncă nu există evaluări
- L01c CloudFoundations 01 Cloud ConceptsDocument45 paginiL01c CloudFoundations 01 Cloud ConceptsJan jan1100% (1)
- AWS Certified Cloud Practitioner 1 PDFDocument11 paginiAWS Certified Cloud Practitioner 1 PDFAbhisek PaulÎncă nu există evaluări
- 341 - AWS Certified Solutions Architect-PDF - 1572386609 PDFDocument266 pagini341 - AWS Certified Solutions Architect-PDF - 1572386609 PDFFarhan PatelÎncă nu există evaluări
- AWS Arch Refnotes PDFDocument369 paginiAWS Arch Refnotes PDFnbharat9Încă nu există evaluări
- Exam: SAA-C02 Name: AWS Certified Solutions Architect - Associate V9.01 118 Q&As Official WebsiteDocument6 paginiExam: SAA-C02 Name: AWS Certified Solutions Architect - Associate V9.01 118 Q&As Official WebsiteAnkur67% (3)
- Aws CloudDocument11 paginiAws CloudredmiÎncă nu există evaluări
- Architecting On AWS 5 - LabDocument61 paginiArchitecting On AWS 5 - LabSrinivasanÎncă nu există evaluări
- AWS Certified Developer Associate Updated June 2018 Exam GuideDocument3 paginiAWS Certified Developer Associate Updated June 2018 Exam GuideDivyaÎncă nu există evaluări
- Hackettjoe - Amazon-AWS-SAA-C02 - My Study Material and Notes For Taking The AWS SAA-C02 ExamDocument64 paginiHackettjoe - Amazon-AWS-SAA-C02 - My Study Material and Notes For Taking The AWS SAA-C02 ExamsamalparthaÎncă nu există evaluări
- AWS Certified Architect QuestionsDocument36 paginiAWS Certified Architect QuestionsBaburaj Vp100% (1)
- Red Hat Enterprise Linux 6: 6.10 Release NotesDocument30 paginiRed Hat Enterprise Linux 6: 6.10 Release Notesnavin_netÎncă nu există evaluări
- OflDocument2 paginiOflnavin_netÎncă nu există evaluări
- Input - DC 12-15V: 5V / 9V Output XL4015 Module Buck ConverterDocument1 paginăInput - DC 12-15V: 5V / 9V Output XL4015 Module Buck Converternavin_netÎncă nu există evaluări
- PF - 13070 - PF - 11079 - Annexure 1 - Day Care Procedures 1Document4 paginiPF - 13070 - PF - 11079 - Annexure 1 - Day Care Procedures 1navin_netÎncă nu există evaluări
- Schematic 12V UPS+V5.0 2021-09-02 BackupDocument1 paginăSchematic 12V UPS+V5.0 2021-09-02 Backupnavin_netÎncă nu există evaluări
- DIY Mini UPS For WiFi Router V50Document77 paginiDIY Mini UPS For WiFi Router V50navin_netÎncă nu există evaluări
- The World's Open Source Leader - Red Hat PDFDocument9 paginiThe World's Open Source Leader - Red Hat PDFnavin_netÎncă nu există evaluări
- Mysql Dba QuestionsDocument1 paginăMysql Dba Questionsnavin_netÎncă nu există evaluări
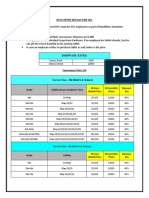
- BYJU's Offer DetailsDocument4 paginiBYJU's Offer Detailsnavin_netÎncă nu există evaluări
- Java Programming On LinuxDocument732 paginiJava Programming On Linuxapi-3839016100% (1)
- Mysql Dba QaDocument4 paginiMysql Dba Qanavin_netÎncă nu există evaluări
- (November-2019) Braindump2go New AWS-Certified-Solutions-Architect-Associate PDF Dumps Free Share PDFDocument5 pagini(November-2019) Braindump2go New AWS-Certified-Solutions-Architect-Associate PDF Dumps Free Share PDFnavin_netÎncă nu există evaluări
- Dell Latitude 5420/E5420/E5420m Owner's Manual: Regulatory Model P15F Regulatory Type P15F001Document176 paginiDell Latitude 5420/E5420/E5420m Owner's Manual: Regulatory Model P15F Regulatory Type P15F001navin_netÎncă nu există evaluări
- 2014 11 20 Tomcat Load Balancing and ClusteringDocument95 pagini2014 11 20 Tomcat Load Balancing and Clusteringnavin_netÎncă nu există evaluări
- Nginx Config AppDocument1 paginăNginx Config Appnavin_netÎncă nu există evaluări
- The Ultimate Veritas Cluster Server (VCS) Interview Questions PDFDocument21 paginiThe Ultimate Veritas Cluster Server (VCS) Interview Questions PDFnavin_netÎncă nu există evaluări
- Selecting The Network Connection Type For A Virtual Machine PDFDocument1 paginăSelecting The Network Connection Type For A Virtual Machine PDFnavin_netÎncă nu există evaluări
- Appserver InstallDocument2 paginiAppserver Installnavin_netÎncă nu există evaluări
- Uwsgi Config WebsiteDocument1 paginăUwsgi Config Websitenavin_netÎncă nu există evaluări
- PayU Technical Integration Document v11.6Document25 paginiPayU Technical Integration Document v11.6navin_netÎncă nu există evaluări
- Uwsgi Config AppDocument1 paginăUwsgi Config Appnavin_netÎncă nu există evaluări
- (November-2019) Braindump2go New AWS-Certified-Solutions-Architect-Associate Dumps VCE Free Share PDFDocument5 pagini(November-2019) Braindump2go New AWS-Certified-Solutions-Architect-Associate Dumps VCE Free Share PDFnavin_netÎncă nu există evaluări
- (November-2019) Braindump2go New AWS-Certified-Solutions-Architect-Associate Dumps With VCE and PDF Free Share PDFDocument5 pagini(November-2019) Braindump2go New AWS-Certified-Solutions-Architect-Associate Dumps With VCE and PDF Free Share PDFnavin_netÎncă nu există evaluări
- Network Diagram: Rockstand Corporate Office New Delhi, India IDC Data Center Mumbai,, IndiaDocument1 paginăNetwork Diagram: Rockstand Corporate Office New Delhi, India IDC Data Center Mumbai,, Indianavin_netÎncă nu există evaluări
- Nginx Config WebsiteDocument1 paginăNginx Config Websitenavin_netÎncă nu există evaluări
- (November-2019) Braindump2go New AWS-Certified-Solutions-Architect-Associate Dumps PDF Free Share PDFDocument5 pagini(November-2019) Braindump2go New AWS-Certified-Solutions-Architect-Associate Dumps PDF Free Share PDFnavin_netÎncă nu există evaluări
- (November-2019) Braindump2go New AWS-Certified-Solutions-Architect-Associate VCE Dumps Free Share PDFDocument5 pagini(November-2019) Braindump2go New AWS-Certified-Solutions-Architect-Associate VCE Dumps Free Share PDFnavin_net100% (1)
- Saa c01Document7 paginiSaa c01navin_netÎncă nu există evaluări
- Grep Awk SedDocument9 paginiGrep Awk SedvishnuselvaÎncă nu există evaluări
- GCP VPN Tunnel LabDocument3 paginiGCP VPN Tunnel Labnavin_netÎncă nu există evaluări
- VCAP NV QuestionsDocument17 paginiVCAP NV QuestionsShinji OnoÎncă nu există evaluări
- VX LAN@nettrainDocument59 paginiVX LAN@nettrainNiayesh ShafieÎncă nu există evaluări
- OCI Professional 2023Document43 paginiOCI Professional 2023Natnael KoraÎncă nu există evaluări
- Fortigate Cookbook 506 ExpandedDocument399 paginiFortigate Cookbook 506 Expandedsat74Încă nu există evaluări
- TestDocument4 paginiTestSoru-Dara JemivakyÎncă nu există evaluări
- Post TestDocument2 paginiPost TestBenito AbrasaldoÎncă nu există evaluări
- Introduction To Public CloudDocument26 paginiIntroduction To Public CloudMayra Katherine Durand GutiérrezÎncă nu există evaluări
- PA120604 - 0201 - ICOM Control PA-HPM Application - Manual ICOM Control PA-HPM Application PDFDocument20 paginiPA120604 - 0201 - ICOM Control PA-HPM Application - Manual ICOM Control PA-HPM Application PDFbata88100% (1)
- KX NS500Document60 paginiKX NS500Michael Piaca Gonzales100% (1)
- Package Contents: Quickstart GuideDocument2 paginiPackage Contents: Quickstart GuideJudyrey P. MediavilloÎncă nu există evaluări
- Network LayerDocument73 paginiNetwork LayerchandruuncleÎncă nu există evaluări
- Banks Oalm T CnaDocument48 paginiBanks Oalm T CnaJulianto TaekÎncă nu există evaluări
- Th6D ABB Ethernet Interface: Translation of The Original Technical InformationDocument25 paginiTh6D ABB Ethernet Interface: Translation of The Original Technical InformationMihail AvramovÎncă nu există evaluări
- Assignment Subnetting Exercises Spring 2012Document2 paginiAssignment Subnetting Exercises Spring 2012Ansa MalikÎncă nu există evaluări
- PaperCut MF - Ricoh Embedded ManualDocument53 paginiPaperCut MF - Ricoh Embedded ManualDerick Ho Chin FaiÎncă nu există evaluări
- Refer To The Exhibit. What Cabling Fault Does The Exhibit Represent?Document31 paginiRefer To The Exhibit. What Cabling Fault Does The Exhibit Represent?András SzűcsÎncă nu există evaluări
- SE V100 Station Explorer II Rev 130Document254 paginiSE V100 Station Explorer II Rev 130mato3848Încă nu există evaluări
- Manual OpenHPCDocument52 paginiManual OpenHPCOemar BakrieÎncă nu există evaluări
- A Fazer 9.4.2.8 Packet Tracer - Skills Integration Challenge Instructions PDFDocument2 paginiA Fazer 9.4.2.8 Packet Tracer - Skills Integration Challenge Instructions PDFEder MonteiroÎncă nu există evaluări
- Software Installation Manual For Ovation 1.8 OS180 - 10: January 2007Document123 paginiSoftware Installation Manual For Ovation 1.8 OS180 - 10: January 2007evbaruÎncă nu există evaluări
- Clase 3. IPv6 AddressingDocument99 paginiClase 3. IPv6 AddressingRomario Garcia SantanaÎncă nu există evaluări
- ALCOMA ALxxF Class Carrier Radio DescriptionDocument91 paginiALCOMA ALxxF Class Carrier Radio DescriptionTaha TounsiÎncă nu există evaluări
- ZeroTier - IOTstackDocument35 paginiZeroTier - IOTstackAlvaro CardosoÎncă nu există evaluări
- A10 5.2.1-P6 AvcsDocument60 paginiA10 5.2.1-P6 AvcsThịnh Nguyễn XuânÎncă nu există evaluări
- Rafal Lukawiecki Strategic Consultant Project Botticelli LTDDocument52 paginiRafal Lukawiecki Strategic Consultant Project Botticelli LTDPham TrungÎncă nu există evaluări
- Kali Linux Tools CatalogDocument76 paginiKali Linux Tools CatalogStephen HilliardÎncă nu există evaluări
- IP Addressing and SubbnettingDocument45 paginiIP Addressing and SubbnettingAhsan KhanÎncă nu există evaluări
- Control LEDs Through A Web Page With An ArduinoDocument13 paginiControl LEDs Through A Web Page With An Arduinokangazzam1984Încă nu există evaluări
- 01 HCNA-Cloud V2.0 Lab GuideDocument179 pagini01 HCNA-Cloud V2.0 Lab GuideMicael CelestinoÎncă nu există evaluări
- Lesson Plan Labsim For Networkpro 20120425CB54845B66A0Document129 paginiLesson Plan Labsim For Networkpro 20120425CB54845B66A0chris665Încă nu există evaluări
- The Dark Net: Inside the Digital UnderworldDe la EverandThe Dark Net: Inside the Digital UnderworldEvaluare: 3.5 din 5 stele3.5/5 (104)
- Defensive Cyber Mastery: Expert Strategies for Unbeatable Personal and Business SecurityDe la EverandDefensive Cyber Mastery: Expert Strategies for Unbeatable Personal and Business SecurityEvaluare: 5 din 5 stele5/5 (1)
- The Digital Marketing Handbook: A Step-By-Step Guide to Creating Websites That SellDe la EverandThe Digital Marketing Handbook: A Step-By-Step Guide to Creating Websites That SellEvaluare: 5 din 5 stele5/5 (6)
- How to Do Nothing: Resisting the Attention EconomyDe la EverandHow to Do Nothing: Resisting the Attention EconomyEvaluare: 4 din 5 stele4/5 (421)
- More Porn - Faster!: 50 Tips & Tools for Faster and More Efficient Porn BrowsingDe la EverandMore Porn - Faster!: 50 Tips & Tools for Faster and More Efficient Porn BrowsingEvaluare: 3.5 din 5 stele3.5/5 (23)
- The Wires of War: Technology and the Global Struggle for PowerDe la EverandThe Wires of War: Technology and the Global Struggle for PowerEvaluare: 4 din 5 stele4/5 (34)
- The Internet Con: How to Seize the Means of ComputationDe la EverandThe Internet Con: How to Seize the Means of ComputationEvaluare: 5 din 5 stele5/5 (6)
- CISM Certified Information Security Manager Study GuideDe la EverandCISM Certified Information Security Manager Study GuideÎncă nu există evaluări
- Branding: What You Need to Know About Building a Personal Brand and Growing Your Small Business Using Social Media Marketing and Offline Guerrilla TacticsDe la EverandBranding: What You Need to Know About Building a Personal Brand and Growing Your Small Business Using Social Media Marketing and Offline Guerrilla TacticsEvaluare: 5 din 5 stele5/5 (32)
- React.js Design Patterns: Learn how to build scalable React apps with ease (English Edition)De la EverandReact.js Design Patterns: Learn how to build scalable React apps with ease (English Edition)Încă nu există evaluări
- So You Want to Start a Podcast: Finding Your Voice, Telling Your Story, and Building a Community That Will ListenDe la EverandSo You Want to Start a Podcast: Finding Your Voice, Telling Your Story, and Building a Community That Will ListenEvaluare: 3.5 din 5 stele3.5/5 (24)
- Grokking Algorithms: An illustrated guide for programmers and other curious peopleDe la EverandGrokking Algorithms: An illustrated guide for programmers and other curious peopleEvaluare: 4 din 5 stele4/5 (16)
- Practical Industrial Cybersecurity: ICS, Industry 4.0, and IIoTDe la EverandPractical Industrial Cybersecurity: ICS, Industry 4.0, and IIoTÎncă nu există evaluări
- Evaluation of Some Websites that Offer Virtual Phone Numbers for SMS Reception and Websites to Obtain Virtual Debit/Credit Cards for Online Accounts VerificationsDe la EverandEvaluation of Some Websites that Offer Virtual Phone Numbers for SMS Reception and Websites to Obtain Virtual Debit/Credit Cards for Online Accounts VerificationsEvaluare: 5 din 5 stele5/5 (1)
- An Internet in Your Head: A New Paradigm for How the Brain WorksDe la EverandAn Internet in Your Head: A New Paradigm for How the Brain WorksÎncă nu există evaluări
- Python for Beginners: The 1 Day Crash Course For Python Programming In The Real WorldDe la EverandPython for Beginners: The 1 Day Crash Course For Python Programming In The Real WorldÎncă nu există evaluări
- How to Start a Blog with WordPress: Beginner's Guide to Make Money by Writing OnlineDe la EverandHow to Start a Blog with WordPress: Beginner's Guide to Make Money by Writing OnlineEvaluare: 3.5 din 5 stele3.5/5 (2)
- Web Copy That Sells: The Revolutionary Formula for Creating Killer Copy That Grabs Their Attention and Compels Them to BuyDe la EverandWeb Copy That Sells: The Revolutionary Formula for Creating Killer Copy That Grabs Their Attention and Compels Them to BuyEvaluare: 4 din 5 stele4/5 (13)
- Articulating Design Decisions: Communicate with Stakeholders, Keep Your Sanity, and Deliver the Best User ExperienceDe la EverandArticulating Design Decisions: Communicate with Stakeholders, Keep Your Sanity, and Deliver the Best User ExperienceEvaluare: 4 din 5 stele4/5 (19)
- HTML5 and CSS3 Masterclass: In-depth Web Design Training with Geolocation, the HTML5 Canvas, 2D and 3D CSS Transformations, Flexbox, CSS Grid, and More (English Edition)De la EverandHTML5 and CSS3 Masterclass: In-depth Web Design Training with Geolocation, the HTML5 Canvas, 2D and 3D CSS Transformations, Flexbox, CSS Grid, and More (English Edition)Încă nu există evaluări
- Kill All Normies: Online Culture Wars From 4Chan And Tumblr To Trump And The Alt-RightDe la EverandKill All Normies: Online Culture Wars From 4Chan And Tumblr To Trump And The Alt-RightEvaluare: 3.5 din 5 stele3.5/5 (240)