Documente Academic
Documente Profesional
Documente Cultură
900.81018V01 AE Pra 2of2
Încărcat de
Anonymous GmpXIPTitlu original
Drepturi de autor
Formate disponibile
Partajați acest document
Partajați sau inserați document
Vi se pare util acest document?
Este necorespunzător acest conținut?
Raportați acest documentDrepturi de autor:
Formate disponibile
900.81018V01 AE Pra 2of2
Încărcat de
Anonymous GmpXIPDrepturi de autor:
Formate disponibile
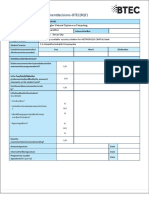
Skills Assessment
Criteria
Unit code, name and release number
ICTNWK305 Install and manage network protocols (R1)
ICTNWK421 Install, configure and test network security (R1)
ICTNWK511 Manage network security (R1)
Qualification/Course code, name and release number
900-81018V01 Statement of Attainment CCNA Cybersecurity Operations
Student details
Student number
Student name
Assessment Declaration
This assessment is my original work and no part of it has been copied from any other
source except where due acknowledgement is made.
No part of this assessment has been written for me by any other person except
where such collaboration has been authorised by the assessor concerned.
I understand that plagiarism is the presentation of the work, idea or creation of
another person as though it is your own. Plagiarism occurs when the origin of the
material used is not appropriately cited. No part of this assessment is plagiarised.
Student signature and Date
Document title: Unit Code_AE_Sk_1of2_20181015 Page 1 of 9
Resource ID: STUDENT NAME:
Version: 1.0
Date created: 3 July 2018
Date modified: 26/11/2019
For queries, please contact:
SkillsPoint
Location
© 2019 TAFE NSW, Sydney
RTO Provider Number 90003 | CRICOS Provider Code: 00591E
This assessment can be found in the: Learning Bank
The contents in this document is copyright © TAFE NSW 2019, and should not be reproduced without the
permission of the TAFE NSW. Information contained in this document is correct at time of printing: 26
November 2019. For current information please refer to our website or your teacher as appropriate.
Document title: Unit Code_AE_Sk_1of2_20181015 Page 2 of 9
Resource ID: STUDENT NAME:
Assessment instructions
Table 1 Assessment instructions
Assessment details Instructions
Assessment overview The objective of this assessment is to assess your skills as would be
required to perform the tasks within a cyber operations centre.
Assessment Event 2 of 3
number
Instructions for this This is a skills based assessment and will be assessing you on your
assessment ability to demonstrate skills required in the unit.
This assessment has four parts:
1. Gathering basic information
2. Learn about the exploits
3. Determining the source of the malware
4. Analyse details of the exploit
5. Assessment Feedback
Submission instructions On completion of this assessment, you are required to upload it for
marking.
Ensure you have written your name at the bottom of each page of this
assessment.
It is important that you keep a copy of all electronic and hardcopy
assessments submitted to TAFE and complete the assessment
declaration when submitting the assessment.
What do I need to do to To successfully complete this assessment the student will be available
achieve a satisfactory at the arranged time to complete all the assessment criteria as outlined
result? in the assessment instructions.
All parts of the observable task must be performed to a satisfactory
level as indicated in the criteria section of the Observation Checklist.
All questions must be answered correctly to be deemed satisfactory in
this assessment task; however, Assessors may ask questions to clarify
understanding.
Document title: Unit Code_AE_Sk_1of2_20181015 Page 3 of 9
Resource ID: STUDENT NAME:
Assessment details Instructions
What do I need? securityOnion-sba.ova:
https://share.tafensw.edu.au/share/file/bb68d6e7-ca36-4fb6-9c89-
40021fa39bb7/1/SecurityOnion_%5BSBA%5D.ova
workstation.ova
Available for download from Cisco
Due date/time To be advised by instructor
allowed/venue
This can be completed off campus
Assessment feedback, Appeals are addressed in accordance with Every Students Guide to
review or appeals Assessment.
Skills Assessment
Introduction
Working as the security analyst for ACME Inc., you notice a number of events on the SGUIL
dashboard. Your task is to analyze these events, learn more about them, and decide if they
indicate malicious activity.
You will have access to Google to learn more about the events. Security Onion is the only VM with
Internet access in the Cybersecurity Operations virtual environment.
The tasks below are designed to provide some guidance through the analysis process.
You will practice and be assessed on the following skills:
o Evaluating Snort/SGUIL events.
o Using SGUIL as a pivot to launch ELSA, Bro and Wireshark for further event inspection.
o Using Google search as a tool to obtain intelligence on a potential exploit.
Content for this assessment was obtained from http://www.malware-traffic-analysis.net/ and is
used with permission. We are grateful for the use of this material.
Addressing Table
The following addresses are preconfigured on the network devices. Addresses are provided for
reference purposes.
Device Interface Network/Address Description
eth0 192.168.0.1/24 Interface connected to the Internal Network
Security Onion VM Interface connected to the External
eth2 209.165.201.21/24 Networks/Internet
Part 1: Gathering Basic Information
a. Log into Security Onion VM using with the username analyst and password cyberops.
b. Open a terminal window. Enter the sudo service nsm status command to verify that all the
services and sensors are ready.
Document title: Unit Code_AE_Sk_1of2_20181015 Page 4 of 9
Resource ID: STUDENT NAME:
c. When the nsm service is ready, log into SGUIL with the username analyst and password
cyberops. Click Select All to monitor all the networks. Click Start SQUIL to continue.
d. In the SGUIL window, identify the group of events that are associated with exploit(s). This
group of events are related to a single multi-part exploit.
How many events were generated by the entire exploit? Include screenshot.
___________________________________________________________________________
___________________________________________________________________________
e. According to SGUIL, when did the exploit begin? When did it end? Approximately how long
did it take? Include screenshot.
___________________________________________________________________________
___________________________________________________________________________
f. What is the IP address of the internal computer involved in the events? Include screenshot.
________________________________________________________________
g. What is the MAC address of the internal computer involved in the events? How did you find it?
Include screenshot
___________________________________________________________________________
___________________________________________________________________________
___________________________________________________________________________
h. What are some of the signature IDs of the rules that fire when the exploit occurs? Where are
the Signature IDs from? Include screenshot.
___________________________________________________________________________
___________________________________________________________________________
___________________________________________________________________________
___________________________________________________________________________
i. Do the events look suspicious to you? Does it seem like the internal computer was infected or
compromised? Explain.
___________________________________________________________________________
___________________________________________________________________________
___________________________________________________________________________
j. What is the operating system running on the internal computer in question? Use screenshot of
tool used.
_______________________________________________________________________
Part 2: Learn About the Exploit
a. According to Snort, what is the exploit kit (EK) in use? Include screenshot
___________________________________________________________________________
___________________________________________________________________________
Document title: Unit Code_AE_Sk_1of2_20181015 Page 5 of 9
Resource ID: STUDENT NAME:
b. What is an exploit kit?
___________________________________________________________________________
___________________________________________________________________________
___________________________________________________________________________
___________________________________________________________________________
___________________________________________________________________________
c. Do a quick Google search on ‘Angler EK’ to learn a little about the fundamentals the exploit kit.
Summarize your findings and record them here.
___________________________________________________________________________
___________________________________________________________________________
___________________________________________________________________________
___________________________________________________________________________
___________________________________________________________________________
___________________________________________________________________________
d. How does this exploit fit the definition on an exploit kit? Give examples from the events you
see in SGUIL. Provide at least one screenshot.
___________________________________________________________________________
___________________________________________________________________________
___________________________________________________________________________
___________________________________________________________________________
___________________________________________________________________________
e. What are the major stages in exploit kits?
___________________________________________________________________________
___________________________________________________________________________
___________________________________________________________________________
___________________________________________________________________________
Part 3: Determining the Source of the Malware
a. In the context of the events displayed by SGUIL for this exploit, record below the IP addresses
involved.
b. The first new event displayed by SGUIL contains the message “ET Policy Outdated Flash
Version M1”. The event refers to which host? What does that event imply? Include screenshot
___________________________________________________________________________
___________________________________________________________________________
___________________________________________________________________________
___________________________________________________________________________
___________________________________________________________________________
___________________________________________________________________________
c. According to SGUIL, what is the IP address of the host that appears to have delivered the
exploit? Include screenshot
Document title: Unit Code_AE_Sk_1of2_20181015 Page 6 of 9
Resource ID: STUDENT NAME:
___________________________________________________________________________
___________________________________________________________________________
___________________________________________________________________________
___________________________________________________________________________
d. Pivoting from SGUIL, open the transcript of the transaction. What is the domain name
associated with the IP address of the host that appears to have delivered the exploit? Include
screenshot
___________________________________________________________________________
___________________________________________________________________________
e. This exploit kit typically targets vulnerabilities in which three software applications?
___________________________________________________________________________
___________________________________________________________________________
___________________________________________________________________________
___________________________________________________________________________
___________________________________________________________________________
f. Based on the SGUIL events, what vulnerability seems to have been used by the exploit kit?
___________________________________________________________________________________
g. What is the most common file type that is related to that vulnerable software?
___________________________________________________________________________________
h. Use ELSA to gather more evidence to support the hypothesis that the host you identified
above delivered the malware. Launch ELSA and list all hosts that downloaded the type of file
listed above. Remember to adjust the timeframe accordingly.
Were you able to find more evidence? If so, record your findings here. Include screenshot
___________________________________________________________________________
___________________________________________________________________________
___________________________________________________________________________
___________________________________________________________________________
___________________________________________________________________________
___________________________________________________________________________
i. At this point you should know, with quite some level of certainty, whether the site listed in Part
3b and Part 3c delivered the malware. Record your conclusions below.
___________________________________________________________________________
___________________________________________________________________________
___________________________________________________________________________
___________________________________________________________________________
___________________________________________________________________________
___________________________________________________________________________
Document title: Unit Code_AE_Sk_1of2_20181015 Page 7 of 9
Resource ID: STUDENT NAME:
Part 4: Analyze Details of the Exploit
a. Exploit kits often rely on a landing page used to scan the victim’s system for vulnerabilities and
exfiltrate a list of them. Use ELSA to determine if the exploit kit in question used a landing
page. If so, what is the URL and IP address of it? What is the evidence? Include screenshots
Hint: The first two SGUIL events contain many clues.
___________________________________________________________________________
___________________________________________________________________________
___________________________________________________________________________
___________________________________________________________________________
___________________________________________________________________________
___________________________________________________________________________
___________________________________________________________________________
b. What is the domain name that delivered the exploit kit and malware payload?
_____________________________________________________________________
_____________________________________________________________________
____________________________________________________________________
c. What is the IP address that delivered the exploit kit and malware payload? Include screenshot
___________________________________________________________________________________
___________________________________________________________________________________
___________________________________________________________________________________
___________________________________________________________________________________
d. Pivoting from events in SGUIL, launch Wireshark and export the files from the captured
packets as was done in a previous lab. What files or programs are you able to successfully
export? Include screenshot
___________________________________________________________________________
___________________________________________________________________________
___________________________________________________________________________
Document title: Unit Code_AE_Sk_1of2_20181015 Page 8 of 9
Resource ID: STUDENT NAME:
Part 5: Assessment Feedback
NOTE: This section must have the assessor signature and student signature to complete the feedback.
Assessment outcome
☐ Satisfactory
☐ Unsatisfactory
Assessor Feedback
☐ Was the assessment event successfully completed?
☐ If no, was the resubmission/re-assessment successfully completed?
☐ Was reasonable adjustment in place for this assessment event?
If yes, ensure it is detailed on the assessment document.
Comments:
Assessor name, signature and date:
Student acknowledgement of assessment outcome
Would you like to make any comments about this assessment?
Student name, signature and date
NOTE: Make sure you have written your name at the bottom of each page of your
submission before attaching the cover sheet and submitting to your assessor for marking.
Document title: Unit Code_AE_Sk_1of2_20181015 Page 9 of 9
Resource ID: STUDENT NAME:
S-ar putea să vă placă și
- Security Yohan PDFDocument71 paginiSecurity Yohan PDFCool MarttÎncă nu există evaluări
- Internal Verification of Assessment Decisions - BTEC (RQF) : Higher NationalsDocument54 paginiInternal Verification of Assessment Decisions - BTEC (RQF) : Higher Nationalsrivindu ranasinghe100% (2)
- Security AssaignmentDocument55 paginiSecurity Assaignmentkaruna niluÎncă nu există evaluări
- 203-1540467331035-Unit 5 Security 2018.07.03Document13 pagini203-1540467331035-Unit 5 Security 2018.07.03SajithÎncă nu există evaluări
- Security AssignmentDocument114 paginiSecurity AssignmentLenovo LegionÎncă nu există evaluări
- 50 SecurityDocument43 pagini50 SecurityMohamed SahlÎncă nu există evaluări
- Software Engineering Unit 3Document103 paginiSoftware Engineering Unit 3navaneethÎncă nu există evaluări
- Web Application Security Audit ReportDocument23 paginiWeb Application Security Audit ReportWieslaw KrawczynskiÎncă nu există evaluări
- NIC Asia Bank Network Security ReportDocument47 paginiNIC Asia Bank Network Security ReportFahad AhmadÎncă nu există evaluări
- Apply Quality StandardsDocument39 paginiApply Quality StandardsEric Manrique Talamisan100% (2)
- Internal Verification of Assessment Decisions - BTEC (RQF) : Higher NationalsDocument33 paginiInternal Verification of Assessment Decisions - BTEC (RQF) : Higher NationalsU & Me100% (2)
- Competency-Based Learning Materials: Computer Systems Servicing NC IiDocument79 paginiCompetency-Based Learning Materials: Computer Systems Servicing NC IiNereo ReoliquioÎncă nu există evaluări
- Providing a Security Solution for METROPOLIS CAPITAL BankDocument52 paginiProviding a Security Solution for METROPOLIS CAPITAL BankHasantha Indrajith100% (2)
- History of Computing - WikipediaDocument51 paginiHistory of Computing - Wikipediaعلی رضاÎncă nu există evaluări
- Vba Codes ExcelDocument46 paginiVba Codes ExcelKen Matsuda100% (1)
- The Machine As Seen at The End of The Mechanical Age 1968Document222 paginiThe Machine As Seen at The End of The Mechanical Age 1968Manuel Bogalheiro100% (2)
- CL CyberAware AE Sk2of2Document38 paginiCL CyberAware AE Sk2of2ultigodlinkÎncă nu există evaluări
- Manage Network and Data Integrity Assessment GuideDocument6 paginiManage Network and Data Integrity Assessment Guideascending0neÎncă nu există evaluări
- Ictnwk503 Ae KN 1of2Document9 paginiIctnwk503 Ae KN 1of2Ashutosh MaharajÎncă nu există evaluări
- CyberOps Skills AssessmentDocument6 paginiCyberOps Skills AssessmentJosias Silva PereiraÎncă nu există evaluări
- CL AdvServer AE Pro 2of2Document44 paginiCL AdvServer AE Pro 2of2Ashutosh MaharajÎncă nu există evaluări
- Internal Verification of Assessment Decisions - BTEC (RQF) : Higher NationalsDocument14 paginiInternal Verification of Assessment Decisions - BTEC (RQF) : Higher NationalsmahdiÎncă nu există evaluări
- MM234Document96 paginiMM234thiwankaamila75Încă nu există evaluări
- Skills Assessment 2: CriteriaDocument36 paginiSkills Assessment 2: Criteriaaarav singhÎncă nu există evaluări
- 1155-1619623492920-Security Reworded 2021Document34 pagini1155-1619623492920-Security Reworded 2021Cool MarttÎncă nu există evaluări
- 20158K Unit11 Pef 20180815Document12 pagini20158K Unit11 Pef 20180815Tarek OsamaÎncă nu există evaluări
- Test Cases For Amazon Prime Video: Micro Project ReportDocument15 paginiTest Cases For Amazon Prime Video: Micro Project ReportVasant ShitoleÎncă nu există evaluări
- VU21993 AE SK 4of5Document16 paginiVU21993 AE SK 4of5Nawjesh KhanÎncă nu există evaluări
- Student Declaration: I Declare That The Work Submitted Is MyDocument9 paginiStudent Declaration: I Declare That The Work Submitted Is Mytilak adhikariÎncă nu există evaluări
- Tata Cara Skill Based Assessment (Sba) : Huruf Berwarna BiruDocument5 paginiTata Cara Skill Based Assessment (Sba) : Huruf Berwarna BirumirroringÎncă nu există evaluări
- Winter 2019_CS Assignment QP - FinalDocument7 paginiWinter 2019_CS Assignment QP - FinalTafseer DeedarÎncă nu există evaluări
- 788-1601897459456-Unit 05 - Security - 2020Document14 pagini788-1601897459456-Unit 05 - Security - 2020Career and EducationÎncă nu există evaluări
- Unit 03Document30 paginiUnit 03Shareen Prem DSouzaÎncă nu există evaluări
- OS Programming Password ManagerDocument7 paginiOS Programming Password ManagerTauha NadeemÎncă nu există evaluări
- Skills Assessment 2Document29 paginiSkills Assessment 2aarav singhÎncă nu există evaluări
- Virtualisation 1-3: Application and Data Defense TasksDocument7 paginiVirtualisation 1-3: Application and Data Defense TasksS ChaudhuriÎncă nu există evaluări
- Remote Assessments-FAQ-Documentation - v2Document16 paginiRemote Assessments-FAQ-Documentation - v2Romeo SamÎncă nu există evaluări
- CBLM For ChsDocument124 paginiCBLM For ChsANTONIO A. SANTOSÎncă nu există evaluări
- Plantilla Reporte eCPPTv2 v2Document14 paginiPlantilla Reporte eCPPTv2 v2HardWiseÎncă nu există evaluări
- BSBMGT407 Student Assessment Booklet CB V2.0 (Restricted)Document36 paginiBSBMGT407 Student Assessment Booklet CB V2.0 (Restricted)Jenny YipÎncă nu există evaluări
- BSBMGT407 Student Assessment Booklet CB V2.0 (Restricted)Document34 paginiBSBMGT407 Student Assessment Booklet CB V2.0 (Restricted)Jenny YipÎncă nu există evaluări
- BSBMGT407 Student Assessment Booklet CB V2.0 (Restricted)Document41 paginiBSBMGT407 Student Assessment Booklet CB V2.0 (Restricted)Jenny YipÎncă nu există evaluări
- Tutorial 14Document5 paginiTutorial 14Nissita PdlÎncă nu există evaluări
- Aui3701 2021 ExamDocument9 paginiAui3701 2021 ExamtinyikodiscussÎncă nu există evaluări
- Trainee Training Report OJT Competencies - How Yu Yang CN Comments 2Document14 paginiTrainee Training Report OJT Competencies - How Yu Yang CN Comments 2Ashok KmarÎncă nu există evaluări
- Ictict418 Ae KN 1of2Document13 paginiIctict418 Ae KN 1of2Ashutosh MaharajÎncă nu există evaluări
- 5exp Akhila ResumeDocument5 pagini5exp Akhila ResumeAkhila ChinniÎncă nu există evaluări
- Ictpmg501 Ae Pro 2of3Document26 paginiIctpmg501 Ae Pro 2of3Ashutosh MaharajÎncă nu există evaluări
- 03 L4DC Computer Systems CSYS Sample QPDocument7 pagini03 L4DC Computer Systems CSYS Sample QPEi Mon HtunÎncă nu există evaluări
- Unit - 05 - Security AssignmentDocument96 paginiUnit - 05 - Security AssignmentsachinÎncă nu există evaluări
- Unit - 05 - SecurityDocument13 paginiUnit - 05 - SecuritycmlunoufgroupÎncă nu există evaluări
- Ilovepdf Merged (7) MergedDocument139 paginiIlovepdf Merged (7) MergeddiplomadosthaÎncă nu există evaluări
- Ste SwaDocument14 paginiSte Swakamblepiyush426Încă nu există evaluări
- Azure Sentinel Workshop: Partner Overview DeckDocument17 paginiAzure Sentinel Workshop: Partner Overview Decklfi91509 zslszÎncă nu există evaluări
- #1 Penetration Testing Internship ReportDocument18 pagini#1 Penetration Testing Internship ReportI Don't KnowÎncă nu există evaluări
- Unit 17 - Network SecurityDocument12 paginiUnit 17 - Network SecuritychaÎncă nu există evaluări
- Female Assignment ExampleDocument143 paginiFemale Assignment ExampleHarry potterÎncă nu există evaluări
- Report For Cse 343 LpuDocument25 paginiReport For Cse 343 LpuShoaib AkhterÎncă nu există evaluări
- Chapter One and Chapter TwoDocument13 paginiChapter One and Chapter TwoKaftanle channelÎncă nu există evaluări
- Career Objective: GraduationDocument5 paginiCareer Objective: GraduationAkshay BmÎncă nu există evaluări
- Unit: Computer Systems Assignment Title: Practical Portfolio December 2015 - Sample AssignmentDocument7 paginiUnit: Computer Systems Assignment Title: Practical Portfolio December 2015 - Sample AssignmentBright Harrison MwaleÎncă nu există evaluări
- Summer Training Report: Maharaja Surajmal Institute of TechnologyDocument35 paginiSummer Training Report: Maharaja Surajmal Institute of TechnologyHarsh JhaÎncă nu există evaluări
- Industry Internship Summary Report Web Page Automation Using SeleniumDocument28 paginiIndustry Internship Summary Report Web Page Automation Using SeleniumKANIKA RAIÎncă nu există evaluări
- Baxter Business Excellence ModelDocument34 paginiBaxter Business Excellence ModelKAMAL BEHLÎncă nu există evaluări
- Low Voltage Alternator - 4 Pole: 1100 To 1640 kVA - 50 HZ / 1250 To 2000 kVA - 60 HZ Electrical and Mechanical DataDocument12 paginiLow Voltage Alternator - 4 Pole: 1100 To 1640 kVA - 50 HZ / 1250 To 2000 kVA - 60 HZ Electrical and Mechanical DataBart VyveyÎncă nu există evaluări
- Unit 3 Working With XML Introduction To XMLDocument41 paginiUnit 3 Working With XML Introduction To XMLAishwaryaÎncă nu există evaluări
- ABAP ObjectsDocument3 paginiABAP ObjectsvenkatÎncă nu există evaluări
- Uci 401 AssignmentDocument15 paginiUci 401 Assignmentevans kiplimoÎncă nu există evaluări
- MS For Maintenance of CCTV SystemDocument15 paginiMS For Maintenance of CCTV Systemsheb_khaleelÎncă nu există evaluări
- Budgeting and Financing Substation: SubstationsDocument2 paginiBudgeting and Financing Substation: SubstationsManuel Henríquez SantanaÎncă nu există evaluări
- SEM Workshop Presentation 3Document28 paginiSEM Workshop Presentation 3felixkern1991Încă nu există evaluări
- TD100 VDM Installation ManualDocument25 paginiTD100 VDM Installation ManualSumit KumarÎncă nu există evaluări
- 6 1 1 Procedures Recording Qualitative DataDocument2 pagini6 1 1 Procedures Recording Qualitative DataRhenmar Morales GalvezÎncă nu există evaluări
- JM JTManualDocument23 paginiJM JTManualcuongÎncă nu există evaluări
- Agenda Scheduling Principles and Tools - Chet Holmes PDFDocument72 paginiAgenda Scheduling Principles and Tools - Chet Holmes PDFSH LCÎncă nu există evaluări
- Design of Engine Cylinder Block : M NareshDocument4 paginiDesign of Engine Cylinder Block : M NareshMudavath NareshÎncă nu există evaluări
- ECE 124 Week 7 ReviewDocument55 paginiECE 124 Week 7 Reviewjahnavi thotaÎncă nu există evaluări
- Permintaan Harga Alat LaboratoriumDocument34 paginiPermintaan Harga Alat Laboratorium197011014 Fahri Agung Nugraha S /CÎncă nu există evaluări
- Bandpass Project PDFDocument13 paginiBandpass Project PDFarjun aluÎncă nu există evaluări
- p328.07x - Vogue Wireless Charging Speaker 2Document28 paginip328.07x - Vogue Wireless Charging Speaker 2Georgie SÎncă nu există evaluări
- A7800 PDFDocument9 paginiA7800 PDFkarkonÎncă nu există evaluări
- Bank of Baroda BankingApplicationDocument45 paginiBank of Baroda BankingApplicationprateekÎncă nu există evaluări
- Pa3X Factory ResetDocument12 paginiPa3X Factory ResetAnonymous qz5pEMh44Încă nu există evaluări
- The Antennagate Crisis ManagementDocument7 paginiThe Antennagate Crisis ManagementMenghui DaiÎncă nu există evaluări
- Elec Grs Pumps 203seriesDocument5 paginiElec Grs Pumps 203serieschand_yelÎncă nu există evaluări
- Communication Physics PDFDocument2 paginiCommunication Physics PDFJulie33% (3)
- ST 252Document2 paginiST 252jamesyuÎncă nu există evaluări
- Denver Ac-5000w Mk2 - EnglishDocument2 paginiDenver Ac-5000w Mk2 - EnglishPrva CetaÎncă nu există evaluări
- Nid Automotive Mechtronics Curriculum and Course SpecificationsDocument220 paginiNid Automotive Mechtronics Curriculum and Course SpecificationsSamuel KwaghterÎncă nu există evaluări