Documente Academic
Documente Profesional
Documente Cultură
BCACloud Technology and Information Security Management 2016
Încărcat de
Riya AbrahamDescriere originală:
Drepturi de autor
Formate disponibile
Partajați acest document
Partajați sau inserați document
Vi se pare util acest document?
Este necorespunzător acest conținut?
Raportați acest documentDrepturi de autor:
Formate disponibile
BCACloud Technology and Information Security Management 2016
Încărcat de
Riya AbrahamDrepturi de autor:
Formate disponibile
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
BACHELOR OF COMPUTER APPLICATIONS [Specialization in Cloud Technology and
Information Security]
Preamble
The Computer Department of St. Teresa’s College is proposed to start a new course on Dual
Specialization in Cloud Technology and Information Security Management. As St.Teresa’s
College is granted academic autonomy in the year 2014, hence it has the privilege of
restructuring the syllabus. Keeping an eye on the industry and to modernize the curriculum, the
Board of Studies members of the Department of Computer Applications, St.Teresas College, has
initiated an industry collaboration to impart Bachelor of Computer Applications (dual
specialization) programme in Cloud Technology and Information Security Management.
The main objective of this program is to inculcate among the students, the technical as well as
the theoretical knowledge about the computers and its various applications in different fields.
This program is designed in such a way that students can have a detailed knowledge of subjects
as well as the knowledge of IT related applications. Throughout this program the students will go
through the IT scenario, its scope, career and the essentials of the IT world.
This unique course provides dual career options for the students in the latest and fast growing
technology sectors of Cloud Technology and Information Security.
The syllabus aims to focus on enabling the students to familiarize with the new technologies, and
at the same time enhance and strengthen the fundamental knowledge in Computer Applications,
Mathematics, and Statistics.
[Curriculum Design – 2015] Page 1
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Graduate Attributes
The Bachelor of Computer Applications (dual specialization) programme will equip the students
with the necessary knowledge and skills for the existing and emerging challenges that a career in
computing and software technology will entail. In addition it prepares graduates to show high
quality of independent thought, flexibility and maturity based on a sound technical knowledge of
the field.
Bachelor of Computer Applications (Dual Specialization) programme, which will enable the
student to embark on a successful career in the area of Cloud Technology and Information
Security Management.
On completion of the Bachelor of Computer Applications in Cloud Technology and Information
Security Management course students should be able to,
Use a range of programming languages and tools to develop computer programs and
systems that are effective solutions to problems.
Be able to understand, design, and analyze precise specifications of algorithms,
procedures, and interaction behavior.
Be able to apply mathematics, logic, and statistics to the design, development, and
analysis of software systems.
Be equipped with a range of fundamental principles of Computer Science that will
provide the basis for future learning and enable them to adapt to the constant rapid
development of the field.
Be able to gain experience of working in teams to build software systems.
Students will be able to gain a strong ground in basic discipline of study
Students will be able to learn the practical implementation , as the learning of the
practical subjects will happen in laboratories or on the field ,
The student will be able to have an insight to the situations in the existing
field/market/industries because of the project work.
[Curriculum Design – 2015] Page 2
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Programme Objective
This unique course provides dual career options for the students in the fast growing technology
sectors of Cloud Technology and Information Security. In addition to all the mandatory subjects
of a traditional BCA, this specialized course offers in-depth practical know-how of the current
trend Technology – Cloud and Information Security. These sectors have the potential to grow
exponentially and they provide challenging job opportModuleies for young professionals with
the right skill sets.
On the Cloud Technology front, the course will provide students with the fundamental
knowledge of all aspects of Cloud Technology. The course focuses on Virtualization
Technology, Cloud Technology, Datacenters, Networking and Operating Systems. On the
Information Security front, this course equips the students with the concepts and the technical
skills in Information Security. The focus of the course is on the models, tools and techniques for
enforcement of Security Policies, with emphasis on Cryptography, Ethical Hacking, Computer
Forensics and Virtualization and Cloud Security.
At the end of first year (1st and 2nd Semester), the learner will be able to:
Understand the basic concepts and working of a Computer, the types of languages used,
the organization and architecture of the components in a Computer, and the working of
operating system.
Discuss the features and functions of Linux Operating System
Understand the concepts behind programming in C and C++, and develop simple to
complex programs.
Compare the different types of data structures and develop programs to search and sort
for elements.
At the end of second year (3rd and 4th Semester), the learner will be able to:
Understand software development and the concepts behind Java programming, and
develop simple to complex programs.
Discuss how to provide protection for information, how to manage data using a database,
how to perform ethical hacking and explain the different concepts in computer networks.
Discuss fundamentals of cloud computing
[Curriculum Design – 2015] Page 3
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Understand the concept of virtualization and different products for doing the same
At the end of third year (5th and 6th Semester), the learner will be able to:
Understand various security concepts needed for virtualization and cloud, how to manage
risks and information security
Discuss about how to provide security for mobile and wireless technology and understand
computer forensics and investigation concepts
Understand how the different IT services can be provided with the help of Windows
Azure
Discuss the administration of Linux server and understand how to configure and
administer different services
Career Opportunities for Cloud Technology Professionals
Global Scenario
Combined Market of Private and Public Cloud Services - $11 Billion in 2012
Poised to grow to $ 65 to 85$ Billion in 2015
- McKinsey Analysis: Winning in the SMB Cloud: Charting a Path to Success
Growth and Forecast
There are currently about 50 million enterprise users of Cloud Office Systems which
represent only 8 percent of overall office system users, excluding China and India.
Predicts that a major shift toward cloud office systems will begin by the first half of 2015
and reach 33 % penetration by 2017.
- Gartner Report
Worldwide spending on public IT cloud services will be more than $40 billion in
2014
Expected to approach $100 billion in 2016.
[Curriculum Design – 2015] Page 4
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Over the 2012–2016 forecast period, public IT cloud services will enjoy a compound
annual growth rate (CAGR) of 26.4%, five times that of the IT industry overall
- IDC research
Jobs and Opportunities - Global
Cloud Computing to Create 14 Million New Jobs by 2015.
By 2015, business revenues from IT innovation enabled by the cloud could reach US$1.1
trillion a year.
Indian Scenario
Market Size - India
The public cloud services market in India is forecast to grow 36 percent in 2014 to total $443
million, up from $326 million in 2013, according to Gartner, Inc. Infrastructure as a service
(IaaS), including cloud computing, storage and print services, continues as the fastest-growing
segment of the market in India, growing 22.7 percent in 2013 to $43.1 million, and it is expected
to grow 39.6 percent in 2014 to $60.2 million. Infrastructure as a service (IaaS), including cloud
compute, storage and print services continued as the fastest-growing segment of the market,
growing 42.4 percent in 2012 to $6.1 billion and expected to grow 47.3 percent in 2013 to $9
billion.
Jobs and Opportunities - India
India will create over 2 million jobs in Cloud sector, predicts a study commissioned by Microsoft
and conducted by International Data Corporation (IDC).
[Curriculum Design – 2015] Page 5
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Career Progression Path - Cloud Technology
Industry Entry level (0-1 yrs Mid Level (3-5 yrs exp.) Advanced level (5 yrs
exp.) plus exp.)
Cloud Architect Cloud Consultant
Cloud Engineer Sr. Cloud Engineer Manager Cloud
Manager Cloud Technology
Technology
Job Role Datacenter Technician Datacenter Engineer Datacenter Manager
Remote Desktop Cloud Provisioning Datacenter Manager
Engineer Engineer
Cloud Security Security Engineer Manager Cloud Security
Specialist
Job Opportunity for Cyber Security in various departments of different sectors:
Corporate (Information Security, Compliance, IT&IS Audit, Software Development etc.)
Banking, Finance and Insurance Sector (IT and Data Security, E-Commerce and Net-
banking Security, Compliance, Information Risk Management, IT&IS Audit etc.)
Defense and Police (R&D, Investigation and Forensics, IT Infrastructure Security etc.)
Governance (E-Governance, Public Key Infrastructure Management, Forensic Science
Labs etc.)
Legal Department (Cyber Forensics Consultants, Cyber Law Expert, Expert witness etc.)
Cyber Fraud Consultants / Management (Ethical Hacker, Penetration Testers, Cyber
Fraud Detectives)
Career Progression Path – Information Security
Industry Entry level (0-1 yrs Mid Level (3-5 yrs exp.) Advanced level (5 yrs
exp.) plus exp.)
Executive Information Sr. Information Security Chief Information
Security Officer Security Officer
Malware Analyst Sr. Malware Analyst Manager Anti Virus
Development
Datacenter Technician Datacenter Engineer Datacenter Manager
Job Role Junior Penetration Penetration Tester Ethical Hacker
Tester
Database Manager – IT Network and Database Datacenter Security
Security Manager - IT Security Engineer
Junior Cyber Forensic Cyber Forensic Analyst Cyber Forensic
Analyst Investigator
[Curriculum Design – 2015] Page 6
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Structure of Bachelors Program in Computer Application - Cloud Computing
& Information Security Management
The B.C.A in Cloud Technology and Information Security Management includes,
a. Common Courses
b. Core Courses
c. Choice Based Core Courses
d. Complementary Courses
e. Open Courses
f. Project.
No course shall carry more than 4 credits. The student shall select any Choice based core course
offered by the department which offers the core courses, depending on the availability of
teachers and infrastructure facilities, in the institution. Open course shall be offered in any
subject and the student shall have the option to do courses offered by other departments.
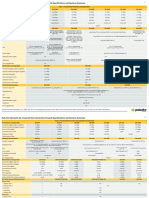
Scheme of Courses
S.No Category No. of Papers Credits
1 Common Courses 2 10
2 Core Courses 16 48
3 Choice Based Core Courses 3 12
4 Complementary Courses 17 42
5 Open Courses 1 04
6 Project 1 04
Grand Total 40 120
Open Course
All students are expected to do the open course in fifth semester. The students can opt
from the courses offered by any discipline other than their own core discipline.
The Department of Computer Applications is offering two open courses “Security
Threats and Trends “, “ Cryptography Fundamentals” with 4 credits. This course is for
other Department Students.
[Curriculum Design – 2015] Page 7
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Choice Based Core Course
The Department of Computer Applications is offering six choice based core courses;
Fundamentals of ITIL
Semester 3
Software Engineering
Cloud Web Services
Semester 4
Fundamentals of Data Center
Database Security Fundamentals
Hacktivism, Cyberwarfare and Cyber terrorism Semester 5
Among which three can be selected by the students. Departments have the freedom to change
current papers /choose other papers if found relevant. But changes should not affect number of
teaching hours of each department
Project
All students are to do a project. This project can be done individually or as a group of 2
students. The projects are to be identified during the 5th semester of the programme with
the help of the supervising teacher. The project evaluation will be carried out in the sixth
semester.
[Curriculum Design – 2015] Page 8
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Detailed Distribution of Courses for Bachelor in Computer Applications – Cloud
Technology and Information Security Management
Total
Semester
No.of Hrs./Se Total Marks
Course Title of the m Exam
Hrs/W Credits Duration
Code Course eek SA FA
1
CA1C01TB Basics of 4-0-0 04
72 3 20 80
Statistics
CA1C02TB Computer
fundamentals & 4-0-0 03 72 3 20 80
organization
CA1C03TB Programming in 4-0-0 03
72 3 20 80
C
CA1C04TB Introduction to 4-0-0 03
72 3 20 80
Linux
Learning Labs
Programming in 0-0-2 01 36 80
CA1C01PB 3 20
C – Lab
CA1C02PB Linux Lab 0-0-2 01 36 3 20 80
2 CA2C05TB Fundamentals of 3 80
4-0-0 03 72 20
mathematics
CA2C06TB Operating system 4-0-0 04 72 3 20 80
CA2C07TB OOPS with C++ 4-0-0 03 72 3 20 80
CA2C08TB Data structures 4-0-0 03 3 80
72 20
using C
English BCA201
Learning labs
CA2C03PB OOPS with C++ 0-0-2 01 3 80
36 20
Lab
CA2C04PB Data structures 0-0-2 01 3 80
36 20
using C - lab
[Curriculum Design – 2015] Page 9
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Exam
Semester
Course Title of the Duratio
No. of Total
Hrs/week
Credits Hrs./Sem n Sessionals Total
Code Course
3 Information
CA3B01TB security 4-0-0 04 90 20 80
3
fundamentals
Choice Based
CA3B02TB/
Core Courses 4-0-0 04 72 3 20 80
CA3B03TB
-1
CA3C09TB RDBMS 4-0-0 03 72 3 20 80
Computer
CA3C10TB 4-0-0 04 72 20 80
networks 3
Programming
CA3C11TB 4-0-0 03 72 20 80
in Java 3
Learning labs
CA3C05PB RDBMS – lab 0-0-2 01 36 3 20 80
Programming
CA3C06PB 0-0-3 01 36 3 20 80
in Java – lab
4 Core Courses
Basics of
Server
CA4B04TB 4-0-0 04 72 3 20 80
Operating
System
Specialization -1 Information Security Management Services
Ethical
CA4B05TB Hacking 03 72 3 20 80
4-0-0
Fundamentals
CA4B06TB Choice Based
/ Core Course - 04 72 3 20 80
4-0-0
CA4B07TB II
Specialization - 2 Cloud Technology
Introduction
CA4B08TB to Cloud 03 72 3 20 80
4-0-0
Technology
Principles of
CA4B09TB 4-0-0 04 72 3 20 80
Virtualization
Learning Labs
Ethical
CA4B07PB Hacking - 01 54 3 20 80
0-0-3
Lab
Introduction
to Cloud
CA4B08PB 01 36 3 20 80
Technology- 0-0-2
Lab
[Curriculum Design – 2015] Page 10
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
5 CA5B10TB Computer
Forensics and 4-0-0 03 72 3 20 80
Investigation
CA5B11TB Virtualization
and Cloud 4-0-0 04 72 3 20 80
Security
CA5B12TB IT
Governance,
Risk, &
4-0-0 04 72 3 20 80
Information
Security
Management
Specialization - 2 Cloud Technology
Linux
CA5B13TB Administratio 4-0-0 03 72 3 20 80
n
CA5D01TB/
Open Course 4-0-0 04 72 3 20 80
CA5D02TB
Learning Labs
CA5B09PB Computer
Forensics and
0-0-3 01 54 3 20 80
Investigation
- lab
CA5B10PB Linux
administratio 0-0-2 01 36 3 20 80
n- Lab
6 Specialization -1 Information Security Management Services
CA6B14TB Mobile,
Wireless and
4-0-0 72 3 80
VOIP 04 20
Security
Choice Based
CA6B15TB/
Core Course - 4-0-0 04 72 3 20 80
CA6B16TB
III
Specialization - 2 Cloud Technology
CA6B17TB Introduction
to Windows 4-0-0 72 3 80
04 20
Azure
CA6B18TB Disaster
recovery and
Business 4-0-0 04 72 3 20 80
continuity
management
CA6B19PB Project 0-0-9 4 162 3 20 80
[Curriculum Design – 2015] Page 11
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Choice Based Core Course –I Subjects:-
1. Fundamentals of ITIL
2. Software engineering
Choice Based Core Course -II
1. Cloud Web Services
2. Fundamentals of Datacenter
Choice Based Core Course - III –
1. Database Security Fundamentals
2. Hacktivism, Cyberwarfare and Cyberterrorism
List of Open Course subjects -
1. Security Threats and Trends
2. Cryptography Fundamentals
[Curriculum Design – 2015] Page 12
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Credit details – Coursewise
S. Category Semester Course Name of the Subject Credits
No Code
1 Common English – I Communication Skills in
05
English (BCA 101)
2 Complementary CA1C01TB 04
Basics of Statistics
3 Complementary Semester 1 CA1C02TB
Computer fundamentals & organization 03
4 Complementary CA1C03TB 03
Programming in C
5 Complementary CA1C01PB
Programming in C - Lab 01
6 Complementary CA2C05TB
Fundamentals of mathematics 03
7 Complementary CA2C06TB 04
Operating system
8 Complementary CA2C07TB 03
OOPS with C++
Semester 2
9 Complementary CA2C08TB 03
Data structures using C
10 Complementary CA2C03PB 01
OOPS with C++ Lab
11 Complementary CA2C04PB 01
Data structures using C - lab
12 Common CA2A02TB English – II Critical Thinking, 05
Academic Writing & Presentation
(BCA 201)
13 Complementary Semester CA3C11TB 03
Programming in Java
3
14 Complementary CA3C06PB 01
Programming in Java – Lab
15 Complementary Semester CA1C04TB 03
Introduction to Linux
1
16 Complementary CA1C02PB 01
Linux Lab
17 Complementary CA3C09TB 03
RDBMS
18 Complementary CA3C10TB 04
Computer Networks
Semester 3
19 Complementary CA3C05PB 01
RDBMS – lab
CA3B02TB Fundamentals of ITIL
Choice Based
20
Core-I 04
CA3B03TB Software Engineering
[Curriculum Design – 2015] Page 13
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
21 Core CA3B01TB Information security fundamentals 04
22 Core CA4B04TB Basics of Server Operating System 04
23 Core CA4B05TB 03
Ethical Hacking Fundamentals
24 CA4B06TB Cloud Web Services
Choice Based
Core-II
Semester 4 CA4B07TB
Fundamentals of Datacenter
04
25 Core CA4B08TB
Introduction to Cloud Technology
03
26 Core CA4B09TB
Principles of Virtualization 04
27 Core CA4B07PB
Ethical Hacking - Lab 01
28 Core CA4B08PB
Introduction to Cloud Technology- Lab 01
29 Core CA5B10TB
Computer Forensics and Investigation 03
30 Core CA5B11TB
Virtualization and Cloud Security 04
Semester 5
31 Core CA5B12TB IT Governance, Risk, & Information
04
Security Management
32 Core CA5B13TB Linux Administration 03
33 Core CA5B09PB Computer Forensics and Investigation -
01
lab
34 Core CA5B10PB
Linux administration- Lab 01
35 Core CA6B14TB
Mobile, Wireless and VOIP Security
04
CA6B15TB Database Security Fundamentals
Choice Based
36 CA6B16TB
Core - III Hacktivism, Cyberwarfare and 04
Semester 6
Cyberterrorism
37 Core CA6B17TB
Introduction to Windows Azure
04
38 Core CA6B18TB Disaster recovery and Business
04
continuity management
39 Core
Project 04
40 CA5D01TB Security Threats and Trends
Open Semester
04
5 CA5D02TB Cryptography Fundamentals
[Curriculum Design – 2015] Page 14
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Examination System
The evaluation of each course shall contain two parts – Sessional Assessment and Final
Assessment. The sessional and final assessments shall be made using a Mark – based grading
system based on a 7 point scale. Overall sessional : Final ratio will be maintained as 20:80.
Sessional Assessment
The Sessional evaluation is to be done by continuous assessment of the following
components. The components of the evaluation for theory and practical and its
weights are as below:
1. Distribution of Sessional Marks
a. For theory courses:
a. Attendance - 5 marks
b. Assignment - 5 marks
c. Test Paper - 10marks
Total 20 Marks.
b. For Practical
a. Attendance - 3 marks
b. Record - 5 marks
c. Test Paper - 10 marks
d. Lab Involvement - 2 marks
Total 20 Marks
2. Attendance Evaluation
A student should have a minimum of 75% attendance. Those who do not have the
minimum requirement of attendance will not be allowed to appear for the final
examinations.
Distribution of marks for evaluation
90% - 100% - 5 marks
85% - 89% - 4 marks
80% - 84% - 3 marks
75% - 79% - 2 marks
[Curriculum Design – 2015] Page 15
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
3. Assignment/Seminar/Viva
i. 1st to 5th Semesters - Assignment / Seminar
ii. 6th Semester - Seminar Only
4. Test Paper
i. Average mark of two sessional examinations shall be taken.
Final Examination
The Final examination of all semesters shall be conducted by the institution on the close
of each semester. For re-appearance/improvement, students may appear along with the
next batch.
Pattern of Questions:
Questions shall be set to assess knowledge acquired, application of knowledge in
life situations, critical evaluation of knowledge and the ability to synthesize
knowledge. The question setter shall ensure that questions covering all skills are
set. He/She shall also submit a detailed scheme of evaluation along with the
question paper.
A question paper shall be a judicious mix of very short answer type, short answer
type, short essay type/Problem solving type and long essay type questions.
Courses such as common courses, open course and elective course do not contain
practical courses. The pattern of questions for these courses without practical are
listed below:
a. Each question paper has four parts A, B, C and D.
b. Part A contains 6 questions of 1 mark each all of which the candidate has to
answer.
c. Part B contains 10 short answer type questions spanning the entire syllabus
and the candidate has to answer 7 questions. Each question carries 2 marks.
d. Part C contains 8 problem type questions/short essays spanning the entire
syllabus and the candidate has to answer 5 questions. Each question carries 6
marks. But for Open Courses, Part C contains short essay type questions only.
e. Part D contains 4 essay type questions spanning the entire syllabus ad the
candidate has to answer 2 questions. Each question carries 15 marks.
[Curriculum Design – 2015] Page 16
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
f. The total mark for courses is 80.
Practical Examinations
The practical examinations for the core and complementary courses are to be conducted
at the end of every semester by the institution. The external examiner shall be selected by
the institution. The score sheet should be sent to the Controller of Examinations soon
after the evaluation.
A minimum of 16 experiments should be done in a practical course and a candidate
submitting a certified record with a minimum of 8 experiments alone is eligible for
appearing for the practical examinations.
Evaluation:
Practical Examinations
The scheme of evaluation of the practical examination shall be decided by the Board of
Examiners.
Student Strength for Practical Examination:
There shall be at least one teacher to supervise a batch of not more than 15 students in
each laboratory session.
Pattern of Questions
The Practical examination consists of 2 Compulsory Questions. The student has to
design algorithm and develop a software program to solve the given problem.
Question 1 Question 2
Algorithm 10 -
Program 10 15
Output 10 20
Viva 10 marks
Record 5 marks
Total 80 Marks
Project Evaluation
All Students have to begin working on the project in the FIFTH semester and must
submit it in the SIXTH semester.
[Curriculum Design – 2015] Page 17
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
The ratio of Sessional to Final Component of the project is 2:3. The mark distribution for
assessment of the various components is shown below:
Sessional Evaluation
For Project
Attendance - 5
Review 1 - 5
Review II - 5
Viva - 5
Record - 10
Presentation - 10
Total - 40 Marks
Final Evaluation
For Project
Stages Components Marks
Interim Report 1 Attendance/Interim Report/Viva 5
Interim Report 2 Attendance/IR 2/Viva/Project Updates 10
Interim Report 3 Attendance/IR 3/Viva/Paper Presentation 15
Final Report Attendance/Final Report/Viva/Demonstration 30
Total 60
Computation of CCPA
Grade and Grade Points is given teach course based on the percentage of marks obtained as
follows:
Percentage of Marks Grade Grade Point
90 and above A+ - 10
80 – 89 A - Excellent
Outstanding 9
70 – 79 B – Very Good 8
60 – 69 C - Good 7
50 – 59 D - Satisfactory 6
40 - 49 E - Adequate 5
Below 40 F - Failure 4
Note: Decimal are to be rounded off to the next whole number.
Credit Point and Credit Point Average
Credit Point (CP) of a course is calculated using the formula
[Curriculum Design – 2015] Page 18
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
CP = C × GP, where C=Credit ; GP = Grade Point.
Semester Credit Point Average (SCPA) of a semester / Programme is calculated using the
formula
SCPA = Total Credit Points(TCP) / Total Credits(TC)
Grades for the different semesters/programme are given based on the corresponding SCPA as
shown below :
CPA Grade
Above 9 A+ - Outstanding
Above 8, but below or equal to 9 A - Excellent
Above 7, but below or equal to 8 B – Very Good
Above 6, but below or equal to 7 C - Good
Above 5, but below or equal to 6 D - Satisfactory
Above 4, but below or equal to 5 E - Adequate
4 or below F - Failure
Cumulative Credit Point Average for the Program is calculated as follows:
Where TCP1 …….., TCP6 are the the Total Credit Points in each semester and TC1………..TC6
are the Total Credits in each semester.
Note: A separate minimum of 30% marks each for Sessionals and Finals (for both theory and
practical) and an aggregate minimum of 40% is required for the pass of a course. For pass in a
programme, a separate minimum of Grade E is required for all the individual courses. If a
candidate secures F Grade for any one of the courses offered in a Semester/Programme only F
grade will be awarded for that Semester/Programme until he/she improves this to E grade or
above within the permitted period. Candidate who secures E grade and above will be eligible for
higher studies.
[Curriculum Design – 2015] Page 19
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
SYLLABI
OF
CORE COURSES
[Curriculum Design – 2015] Page 20
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Course Code : CA3B01TB
Name of the course - INFORMATION SECURITY FUNDAMENTALS
Duration: One semester
Semester : III
Total Lecture Hours: 72
Aim of the course
To enable starters to know the fundamentals of Information Security, Need of Information
Security, Business needs, Threats, Attacks. And also to get familiarize with Risk
Management, Risk Mitigation, Risk Control and also to know the Network Infrastructure
security, Monitoring Network, Physical & Network Security.
Course Overview and Context
The Module initially covers the Introduction part of Information Security like how it emerges
first, the essential principles and concepts that are crucial with the components. And it also
says about the Access and Balancing the Information Security. It deals also with the
execution, SDLC and the organizational professionals in security.
The Module highlights the Business needs, Threats, Attacks and explains how these are
violating the system.
Finally, the Module covers the Risk Management to Identify & Access Risk related on the
probability of occurrence and its impact, the basic Risk Assessment, Risk Mitigation,
Strategy and the list of controls. It deals along Network Infrastructure Security to secure the
Device based, Media based and with the monitoring of Network, Firewall, IDS and IPS,
hardening of applications and at last it says about the Physical & Network Security.
Syllabus Content
Module – 1 : Know the Basics about the Information Security
Introduction to Information Security
[Curriculum Design – 2015] Page 21
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Definition of Information Security, Evolution of Information Security; Basics
Principles of Information Security; Critical Concepts of Information Security;
Components of the Information System; Balancing Information Security and Access;
implement IT Security, The system Development Life cycle, Security professional in
the organization.
Module – 2 : Gain Skills on the Need of Information Security
The Need for IT Security
Business Needs-Protecting the functionality, Enabling the safe operations, Protecting
the data, safe guarding the technology assets; Threats-compromises to Intellectual
property, deliberate software attacks, Espionage and trespass, sabotage and
vandalism; Attacks-Malicious Codes, Back Doors, Denial of Service and Distributed
Denial of Service, Spoofing, sniffing, Spam, Social Engineering.
Module – 3: Identify how the Risk Management Performs
Risk Management
Definition of risk management, risk identification, and risk control, Identifying and
Accessing Risk, Assessing risk based on probability of occurrence and likely impact,
the fundamental aspects of documenting risk via the process of risk assessment, the
various risk mitigation strategy options, the categories that can be used to classify
controls.
Module – 4 : Know the detailed descriptions on Network Infrastructure Security and
Control
Network Infrastructure Security and Connectivity
Understanding Infrastructure Security- Device Based Security, Media-Based Security,
Monitoring and Diagnosing; Monitoring Network- Firewall, Intrusion Detection
System, Intrusion Prevention system; OS and Network Hardening, Application
[Curriculum Design – 2015] Page 22
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Hardening; Physical and Network Security- Policies, Standards and Guidelines.
Competencies of the course
On a successful completion of this Module the learner will:
C1. Understand the Basics of Information Security
C2. Gain skills on the Needs of IT Security
C3. Identify how the Risk Management performs
C4. Know the detailed descriptions on Network Infrastructure Security and Control.
Learning Resources
o Principles of Information Security- Fourth Edition, Michael E. Whitman, Herbert J.
Mattord
o Information Security Risk Analysis - Thomas R. Peltier, Third Edition, Pub:
Auerbach, 20
o Operating System Concepts, 8th Edition by Abraham Silberschatz, Peter B. Galvin,
Greg Gagne, Pub: John Wiley & sons, Inc., 2009.
o Information security: Principles and Practice - Mark Stamp, 2nd Edition, Pub: John
Wiley & Sons, Inc., 20
Question Paper – Blue Print
Information Security Fundamentals
Blue Print - Question Paper
Part A Part B Part C
Module (6/6) (7/10) (6/8) Part D (2/4)
* 1 Mark 2 Marks (5 Marks) (15 Marks)
1 1 2 1 1
2 1 2 2 1
3 2 3 2 1
4 2 3 3 1
[Curriculum Design – 2015] Page 23
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Course Code : CA4B04TB
Name of the Course: BASICS OF SERVER OPERATING SYSTEM
Duration: One Semester
Total Lecture Hours: 72
Aim of the course: To educate the students about the Basics of a Sever operating system
using Windows server 2008.
Course Overview and Context:
In totality it is a vast subject and the horizon spreads wide. This course covers “Windows
Server 2008” installation and configuration of network and network services.
Syllabus Content:
Module 1: Installing and Configuring Windows Server 2008
History of Server OS, Introduction to windows server 2003 & 2008, Overview of Windows
Server 2008, Installing Windows Server 2008, Managing Server Roles and Features,
Configuring and Managing Windows Server 2008 Server Core, Choosing a Deployment
Technology, Deploying Windows Server 2008, Introduction and Creation of Users accounts
Module 2: Configuring Networking and Network Services
Configuring IPv6 Addressing, Migrating from IPv4 to IPv6, DHCP and DNS Enhancements
in Windows Server 2008, Configuring zones, Configuring DNS server settings, Configuring
zone transfer and Replication, Configuring and Managing Windows Firewall with Advanced
Security.
Module 3: Configuring and Managing Active Directory Domain Services
Active Directory Enhancements in Windows Server 2008 and 2008 R2, Installing and
Configuring Domain Controllers, Configuring Read-Only Domain Controllers, Configuring
Fine-Grained Password Policies, Sites and Global Catalog, Managing Active Directory
Objects with Windows PowerShell, Active Directory Database Management, Replication
[Curriculum Design – 2015] Page 24
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
between the Domain Controllers.
Module 4: Managing Group Policy in Active Directory Domain Services
Group Policy Enhancements in Windows Server 2008, Managing Security with Group
Policy, Managing Clients with Group Policy Preferences, Server Management in Windows
Server 2008: Managing Windows Server with Server Manager, Managing Server Updates by
Using WSUS, Managing Backup and Restore by Using Windows Server Backup, Managing
Event Logs and Auditing, Performance and Resource Management.
Competencies of the course:
C1. How to install “windows server 2008”
C2. Configuring different types of server
C3. Learning about deployment technology
C4. Configuring network and networking services
C5. Installation of Active Directory
Learning Resources
70-642:Windows Server 2008 Network Infrastructure Configuration (MOC) from
John Wiley & Sons, 2009
Windows Server 2008: the definitive guide By Jonathan Hassell, O’Reilly, 2008
MCTS: Windows Server 2008 Network Infrastructure Configuration Study
Guide By William Panek, T lor Wentworth, James, O’Reilly, 2011
Question Paper – Blue Print
Basics of Server Operating System
Blue Print - Question Paper
Part A Part B Part C
Module (6/6) (7/10) (6/8) Part D (2/4)
* 1 Mark 2 Marks (5 Marks) (15 Marks)
1 1 2 1 1
2 1 2 2 1
3 2 3 2 1
4 2 3 3 1
[Curriculum Design – 2015] Page 25
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Course Code : CA4B05TB
Name of the course: ETHICAL HACKING FUNDAMENTALS
Duration: One Semester
Total Lecture Hours: 72
Aim of the course
To enable learner to make better understand the Ethical Hacking concepts and various phases
of Hacking along with the objective of providing an in-depth knowledge on Web Application
vulnerabilities and exploitation techniques. To make him familiarize with the wide range of
attacks in a Networking environment and to enable him/her to prepare a well defined
vulnerability reporting procedure along with the remediation techniques.
Course Overview and Context
The Module Primarily covers the Ethical Hacking methodology and its different stages which
include the Foot printing, Scanning, Enumeration and System Hacking techniques and a
broad knowledge about white box and black box testing.
The Module describes a wide range of attacks that can cause adverse negative effects on IT
systems that include Denial of service, Session Hijacking and severe vulnerabilities that can
be seen in Web Applications. The Module also covers Hacking attacks caused in other
Operating System environment like Linux and the secret techniques to Evade Firewalls.
The Module not only captures valuable information on vulnerabilities and threats but also
covers an effective way of report making methodology that can helps the top level
management to take immediate decisions on mitigating the threats.
Syllabus Content
Module 1: Introduction to Ethical Hacking
Hacking Methodology, Process of Malicious Hacking, Footprinting and Scanning:
Footprinting, Scanning. Enumeration: Enumeration. System Hacking and Trojans: System
[Curriculum Design – 2015] Page 26
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Hacking, Trojans and Black Box Vs White Box Techniques
Module 2: Hacking Methodology
Denial of Service, Sniffers, Session Hijacking and Hacking Web Servers: Session Hijacking,
Hacking Web Servers. Web Application Vulnerabilities and Web Techniques Based
Password Cracking: Web Application Vulnerabilities, Web Based Password Cracking
Techniques
Module 3: Web and Network Hacking
SQL Injection, Hacking Wireless Networking, Viruses, Worms and Physical Security:
Viruses and Worms, Physical Security. Linux Hacking: Linux Hacking. Evading IDS and
Firewalls: Evading IDS and Firewalls
Module 4: Report writing & Mitigation
Introduction to Report Writing & Mitigation, requirements for low level reporting & high
level reporting of Penetration testing results, Demonstration of vulnerabilities and Mitigation
of issues identified including tracking
Competencies of the course
C1. Understand the Ethical Hacking Methodology and Phases
C2. Demonstrate the Attacks and Vulnerabilities in Web Application servers
C3. Demonstrate Attacks against Linux environment
C4. Understand the Reporting Procedure and control suggestion for mitigation
[Curriculum Design – 2015] Page 27
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Learning Resources
o Hacking Exposed 7th Edition, by Stuart McClure, Joel Scambray, George Kurtz –
McGraw Hill- 2010
o Basic of Hacking and Penetration – Patrick Engerbrestson 2010
Certified Ethical Hacker All-in-One – Matt Walker 2011
Question Paper – Blue Print
Ethical Hacking Fundamentals
Blue Print - Question Paper
Part A Part B Part C
Module (6/6) (7/10) (6/8) Part D (2/4)
* 1 Mark 2 Marks (5 Marks) (15 Marks)
1 1 2 1 1
2 1 2 2 1
3 2 3 2 1
4 2 3 3 1
[Curriculum Design – 2015] Page 28
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Course Code : CA4B08TB
Name of the Course: INTRODUCTION TO CLOUD TECHNOLOGY
Duration: One Semester
Total Lecture Hours: 72
Aim of the course: To educate the students about the cloud technology and different aspects
of the same.
Course Overview and Context:
This course covers cloud technology in a whole. This covers the delivery models , risks and
the methodology of cot management and the selection of the services offered by the Service
provider.
Syllabus Content:
Module 1: Introduction
Introduction to Cloud Computing, History and Evolution of Cloud Computing, Types of
clouds, Private Public and hybrid clouds, Cloud Computing architecture, Cloud computing
infrastructure, Merits of Cloud computing, , Cloud computing delivery models and services
(IaaS, PaaS, SaaS), obstacles for cloud technology, Cloud vulnerabilities, Cloud challenges,
Practical applications of cloud computing.
Module 2: Cloud Computing Companies and Migrating to Cloud
Web-based business services, Delivering Business Processes from the Cloud: Business
process examples, Broad Approaches to Migrating into the Cloud, The Seven-Step Model of
Migration into a Cloud, Efficient Steps for migrating to cloud., Risks: Measuring and
assessment of risks, Company concerns Risk Mitigation methodology for Cloud computing,
Case Studies
Module 3: Cloud Cost Management and Selection of Cloud Provider
Assessing the Cloud: software Evaluation, System Testing, Seasonal or peak loading, Cost
cutting and cost-benefit analysis, Selecting the right scalable application. Considerations for
[Curriculum Design – 2015] Page 29
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
selecting cloud solution. Understanding Best Practices used in selection of Cloud service and
providers, Clouding the Standards and Best Practices Issue: Interoperability, Portability,
Integration, Security, Standards Organizations and Groups associated with Cloud Computing,
Commercial and Business Consideration
Module 4: Governance in the Cloud
Industry Standards Organizations and Groups associated with Cloud Computing, Need for IT
governance in cloud computing, Cloud Governance Solution: Access Controls, Financial
Controls, Key Management and Encryption, Logging and Auditing, API integration. Legal
Issues: Data Privacy and Security Issues, Cloud Contracting models, Jurisdictional Issues
Raised by Virtualization and Data Location, Legal issues in Commercial and Business
Considerations
Module -5 ten cloud do and do not’s.
Don’t be reactive,do consider the cloud a financial issue, don’t go alone, do think about your
architecture, don’t neglect governance, don’t forget about business purpose, do make security
the centerpiece of your strategy, don’t apply the cloud to everything, don’t forget about
Service Management, do start with a pilot project.
Competencies of the course:
C1. Awareness about the different types of Cloud
C2. Awareness about the different cloud services
C3. Cost Management while using the cloud services
C4. Governance of the cloud services
C5. List of Do’s and Do not’s
[Curriculum Design – 2015] Page 30
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Learning Resources
Cloud Computing: Principles and Paradigms, Rajkumar Buyya, James Broberg,
Andrzej M. Goscinski,, John Wiley and Sons Publications, 2011
Brief Guide to Cloud Computing, Christopher Barnett, Constable & Robinson
Limited, 2010
Handbook on Cloud Computing, Borivoje Furht, Armando Escalante,
Springer, 2010
Question Paper – Blue Print
Introduction to Cloud Technology
Blue Print - Question Paper
Part A Part B Part C
Module (6/6) (7/10) (6/8) Part D (2/4)
* 1 Mark 2 Marks (5 Marks) (15 Marks)
1 1 2 1 1
2 1 2 2 1
3 2 3 2 1
4 2 3 3 1
[Curriculum Design – 2015] Page 31
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Course Code : CA4B09TB
Name of the Course: PRINCIPLES OF VIRTUALIZATION
Duration: One Semester
Semester : 4
Total Lecture Hours: 72
Aim of the course:
To enable learners to understand Virtualization, planning for a virtual implementation and
also prepare for different vendor technologies available in the field of Virtualization.
Course Overview and Context:
Virtualization is the single most effective way to reduce IT expenses while boosting
efficiency and agility in organizations.
This Module explores the implementation and usage of VMWare Virtualization, its
installation process and the working of Windows Server Hyper V
Syllabus Content:
Module 1: Basics of Virtualization
Understanding Virtualization, Need of Virtualization and Virtualization Technologies: Server
Virtualization, Storage Virtualization, I/O Virtualization, Network Virtualization, Client
Virtualization, Application virtualization, Desktop virtualization, Understanding
Virtualization Uses: Studying Server Consolidation, Development and Test Environments ,
Helping with Disaster Recovery
Module 2: Deploying and Managing an Enterprise Desktop Virtualization Environment
[Curriculum Design – 2015] Page 32
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
configure the BIOS to support hardware virtualization; Install and configure
Windows Virtual PC: installing Windows Virtual PC on various platforms (32-bit, 64-bit),
creating and managing virtual hard disks, configuring virtual machine resources including
network resources, preparing host machines; create, deploy, and maintain images
Module 3: Deploying and Managing a Presentation Virtualization Environment
Prepare and manage remote applications: configuring application sharing, package
applications for deployment by using RemoteApp, installing and configuring the RD Session
Host Role Service on the server. Access published applications: configuring Remote Desktop
Web Access, configuring role-based application provisioning, configuring Remote Desktop
client connections. Configure client settings to access virtualized desktops: configuring client
settings,
Module 4: Understanding Virtualization Software
List of virtualization Software available . Vmware- introduction to Vsphere, ESXi, VCenter
Server and Vsphere client. Creating Virtual Machine.. Introduction to HYPER-V role.
Create Virtual Machines. Create Hyper-v virtual networking, Use virtual Machine Snapshots.
Monitor the performance of a Hyper-v server, Citrix XENDesktop fundamentals.
Competencies of the course:
C1. Understand Virtualization
C2. Understand and Implement VMware Virtualization
C3. Install VMware Components
C4. Understand and Configure Window server 2008 Hyper V
[Curriculum Design – 2015] Page 33
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Learning Resources
Virtualization: a beginner's guide - Danielle Ruest, Nelson Ruest , McGraw-Hill Prof
Med, 2010
Windows Server 2008 Hyper-V: Insiders Guide to Microsoft's Hypervisor By John
Kelbley, Mike Sterling, Allen Stewart, Sybex; 1 edition (April 20, 2009
Virtualization for Dummies - Bernard Golden, For Dummies; 1 edition (December 5,
2007)
Mastering Microsoft Virtualization - Tim Cerling, Jeffrey Buller, Jeffrey L. Buller, Sybex; 1
edition (December 21, 2009)
Question Paper – Blue Print
Principles of Virtualization
Blue Print - Question Paper
Part A Part B Part C
Module (6/6) (7/10) (6/8) Part D (2/4)
* 1 Mark 2 Marks (5 Marks) (15 Marks)
1 1 2 1 1
2 1 2 2 1
3 2 3 2 1
4 2 3 3 1
[Curriculum Design – 2015] Page 34
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Course Code : CA4B07PB
Name of the course: ETHICAL HACKING – LAB
Duration: One Semester
Semester : 4
Aim of the course:
To enable learners to identify the Ethical Hacking tools and to make learners gain knowledge
on how to handle those tools for cracking & Hacking of system, applications. The learners in
this lab session can gain how to be secure from unauthorized access.
Course Overview and Context:
The learners in this lab session will use all the tools and techniques practically with the
sessions like Passive Reconnaissance using “who is” and online tools, the Active
Reconnaissance using “Sam pad” and web site details, Full Scan, Half Open Scan and Stealth
scan using “nmap”, UDP and Ping Scanning using “Advance LAN Scanner” and
“Superscan”, Packet crafting using “Packet creator” tools.
In this lab the learners also have the practical’s like Exploiting NetBIOS vulnerability,
Password Revelation from browsers and social networking application, Creating and
Analyzing spoofed emails, Creating and Analyzing Trojans
Syllabus Content:
Module 1:
Understand about the Passive Reconnaissance using “Who is” and Online tools and to
understand about the Active Reconnaissance using “Sam pad” and web site details
Module 2 :
Understand about the Full Scan, Half Open Scan and Stealth scan using “nmap” , and to
understand about the UDP and Ping Scanning using “Advance LAN Scanner” and
“Superscan”
[Curriculum Design – 2015] Page 35
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Module 3 :
To gain knowledge on Packet crafting using “Packet creator” tools and to gain
exposure on Exploiting NetBIOS vulnerability
Module 4 :
To gain knowledge on Password Revelation from browsers and social networking
application and exposure on OS password cracking, creating and analyzing spoofed
emails and gain knowledge on Creating and Analyzing Trojans
Competencies of the course:
On successful completion of this lab a learner will:
C1. Explore the knowledge on Passive Reconnaissance using “Who is” and Online tools
C2. Understand about the Active Reconnaissance using “Sam pad” and web site details
C3. Understand about the Full Scan, Half Open Scan and Stealth scan using “nmap”
C4. Understand about the UDP and Ping Scanning using “Advance LAN Scanner” and
“Superscan”
C5. To gain knowledge on Packet crafting using “Packet creator” tools
C6. Gain exposure on Exploiting NetBIOS vulnerability
C7. To gain knowledge on Password Revelation from browsers and social networking
application
C8. Gain exposure on Creating and Analyzing spoofed emails
C9. To gain knowledge on Creating and Analyzing Trojans
[Curriculum Design – 2015] Page 36
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
C10. Gain exposure on OS password cracking
Learning Resources
o Hacking Exposed 7th Edition, by Stuart McClure, Joel Scambray, George Kurtz –
McGraw Hill- 2010
o Basic of Hacking and Penetration – Patrick Engerbrestson 2010
o Certified Ethical Hacker All-in-One – Matt Walker 2011
[Curriculum Design – 2015] Page 37
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Course Code : CA4B08PB
Name of the Course: INTRODUCTION TO CLOUD TECHNOLOGY - LAB
Duration: One Semester
Semester 4
Aim of the course:
To provide the students with real life experience of the cloud.
Course Overview and Context:
This Laboratory course covers the different aspects of cloud services
Syllabus Content:
Module 1 :
Study the basic cloud architecture and represent it using a case study. Enlist Major
difference between SAAS PAAS & Iaas also submit a research done on various
companies in cloud business and the corresponding services provided by them , tag them
under SAAS , Paas & Iaas.
Module 2 :
Study and present a report on Jolly cloud.
Present a report on obstacles and vulnerabilities in cloud computing on generic level
Present a report on Amazon cloud services.
Present a report on Microsoft cloud services.
Present a report on cost management on cloud
Module 3:
Enlist and explain legal issues involved in the cloud with the help of a case study
And explain the process of migrating to cloud with a case study.
Module 4 :
Present a report on google cloud and cloud services.
[Curriculum Design – 2015] Page 38
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Competencies of the course:
C1. Will get to know about SAAS
C2. Will get to Know about PAAS
C3. Will be familiarized with Amazon Cloud Services
C4. Will be familiarized with Microsoft Cloud services
Learning Resources
Cloud Computing: Principles and Paradigms, Rajkumar Buyya, James Broberg,
Andrzej M. Goscinski,, John Wiley and Sons Publications, 2011
Brief Guide to Cloud Computing, Christopher Barnett, Constable & Robinson
Limited, 2010
Handbook on Cloud Computing, Borivoje Furht, Armando Escalante, Springer, 2010
[Curriculum Design – 2015] Page 39
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Course Code : CA5B10TB
Name of the course: COMPUTER FORENSICS AND INVESTIGATION
Duration: One Semester
Semester : 5
Total Lecture Hours: 72
Aim of the course
To enable the learner to perceive overall about the computer Forensics, how the Storage
Devices & Data Recovery Processes, deep explanation about Forensics techniques and it also
gives you the Basics of Cyber Law.
Course Overview and Context
The Module concentrates on the essentials of computer Forensics, how Cyber Crime forms
and the First Responder procedures like Technical Staff, Non-Technical Staff, Forensics
Expert and Computer Investigation Procedure.
The Module also deals with Storage Devices and the Data Recovery Medium. It also explains
about the Forensics techniques like Windows, Linux, Mobile, Stegnography and the
application password cracking methods like Brute-Force, Dictionary Attack, Rainbow Attack
and the Tracking process of E-mails with various header types such ad SMTP, POP3 &
IMAP.
The Module give a brief notes to know about the Cyber Law like major characteristics of IT
Act 2008, Corporate Espionage, Evidence handling procedures & Chain of custody.
Syllabus Content
Module 1 :
Understand the Importance of Computer Forensics.
Computer Forensics
Introduction to Computer Forensics, Forms of Cyber Crime, First Responder
[Curriculum Design – 2015] Page 40
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Procedure- Non-technical staff, Technical Staff, Forensics Expert and Computer
Investigation procedure
Module 2 :
Learn to identify and trace Passwords, E-mail using Forensics Tools.
Storage Devices & Data Recover Method
Storage Devices- Magnetic Medium, Non-magnetic medium and Optical Medium.
Working of Storage devices-Platter, Head assembly, spindle motor. Data Acquisition,
Data deletion and data recovery method and techniques
Module 3:
Acquire skills to perform how Data works on Storage Devices & the Recovery
Devices.
Forensics Techniques
Windows forensic, Linux Forensics, Mobile Forensics, Stegnography, Application
Password cracking-Brute force, Dictionary attack, Rainbow attack. Email Tacking –
Header option of SMTP, POP3, IMAP
Module 4 :
Gain Knowledge about Cyber Laws.
Cyber Law
Corporate espionage, Evidence handling procedure, Chain of custody, Main features
of Indian IT Act 2008 (Amendment)
Competencies of the course
On successful completion of this Module a learner will:
C1. Understand the Importance of Computer Forensics.
C2. Learn to identify and trace Passwords, E-mail using Forensics Tools
C3. Acquire skills to perform how Data works on Storage Devices & the Recovery Devices.
C4. Gain Knowledge about Cyber Laws
[Curriculum Design – 2015] Page 41
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Learning Resources
o Hacking Exposed Computer Forensics – Aaron Philipp, David Cowen, Chris Davis,
Pub: McGraw Hill-2009
o Guide to Computer Forensics and Investigations – 3rd Edition –B. Nelson, et al, -
Cengage, 2010 BBS
Question Paper – Blue Print
Computer Forensics and Investigation
Blue Print - Question Paper
Part A Part B Part C
Module (6/6) (7/10) (6/8) Part D (2/4)
* 1 Mark 2 Marks (5 Marks) (15 Marks)
1 1 2 1 1
2 1 2 2 1
3 2 3 2 1
4 2 3 3 1
[Curriculum Design – 2015] Page 42
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Course Code : CA5B11TB
Name of the course - VIRTUALIZATION AND CLOUD SECURITY
Duration: One semester
Semester : 5
Total Lecture Hours: 72
Aim of the course
The main goal of this Module is to give a special knowledge on Virtualization & Cloud
computing concepts; also from this you can gain knowledge on cloud security, cloud trust
protocols & transparency. It also talks about the cloud control matrix and the top cloud
threats.
Course Overview and Context
The Module gives you the knowledge about the Virtualization & Cloud Computing Concepts
like private cloud vs. public cloud, IAAS, PAAS & SAAS concepts, it says about the
Virtualization security concerns like Hypervisor security, Platform security, security
communication, security between guest instance & hosts, guests.
The Module concentrates on Cloud Security like Complete Certificate of Cloud Security
Knowledge (CCSK). It also deals with the cloud Trust protocols and transparency with their
concepts, security, privacy and compliance aspects of cloud.
The Module finally tries to give out the cloud control matrix and top cloud threats,
architecture of cloud initiative and Security as a Service.
Syllabus Content
Module 1:
To understand about the Virtualization & Cloud
Introduction to Virtualization & Cloud
Virtualization and Cloud computing concepts, Private cloud Vs Public cloud, IAAS,
[Curriculum Design – 2015] Page 43
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
PAAS & SAAS concepts, Virtualization security concerns, Hypervisor Security,
Host/Platform Security, Security communications, Security between Guest instances,
Security between Hosts and Guests
Module 2 :
To get knowledge on cloud security
Cloud Security
Cloud Security vulnerabilities and mitigating controls, Cloud Trust Protocol, Cloud
Controls Matrix. Complete Certificate of Cloud Security Knowledge (CCSK)
Module 3 :
Gain exposure about cloud trust protocol & transparency
Cloud Trust Protocol & Transparency
Introduction to Cloud Trust Protocol & Transparency, Cloud Trust Protocol and
Transparency, Transparency as a Service, Concepts, Security, Privacy & Compliance
aspects of cloud
Module 4 :
To get knowledge about how to control cloud matrix and the top cloud threats
Cloud Controls Matrix &Top Cloud Threats
Introduction to Cloud Controls Matrix & Top Cloud Threats, Cloud Controls Matrix,
Trusted Cloud Initiative architecture and reference model, requirements of Security as
a Service model and Top Security threats to the cloud model
Competencies of the course
On successful completion of this Module a learner will
C1. To understand about the Virtualization & Cloud
C2. To get knowledge on cloud security
C3. Gain exposure about cloud trust protocol & transparency
C4. To get knowledge about how to control cloud matrix and the top cloud threats
[Curriculum Design – 2015] Page 44
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Learning Resources
o Visible Ops Private Cloud – Andi Mann, Kurt Miline and Jeanne Morain, IT Process
Institute, Inc.; first edition (April 8, 20 )
o Cloud Computing Explained – John Rhoton 2009
Question Paper – Blue Print
Blue Print - Question Paper
Module
* Part A Part B Part C Part D
1 1 3 2 1
2 1 2 2 1
3 2 2 2 1
4 2 3 2 1
5
[Curriculum Design – 2015] Page 45
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Course Code : CA5B12TB
Name of the Course: IT GOVERNANCE, RISK, & INFORMATION SECURITY
MANAGEMENT
Duration: One Semester
Semester 5
Total Lecture Hours: 72
Aim of the course
To enable learners to understand the overview of IT Governance. To familiarize with the
Information Systems & Strategies, Risk Management Program and also the Information
Security Management.
Course Overview and Context
The Module primarily covers the Introduction, Concepts, Role of Governance in Information
Security, Best Practices on Role of IT Strategy Committee, Standard IT Balancing Scorecard,
Val-IT framework of ISACA. The Module also deals with the Role of Strategies planning for
IT, Role of Steering Committee and their policies with procedures. The Module covers the
development of whole Risk Management Program & Process with Risk Analysis methods
and about ISACA.
The Module also explains the Introduction to Information Security management,
Performance Optimization, IT Security-roles & responsibilities, Segregation of Duty,
Frameworks like COBIT.
Syllabus Content
Module 1 :
Acquire knowledge about IT Governance & ISACA
IT Governance
Introduction & Concepts, Role of Governance in Information Security, Best Practices
for IT Governance Role of IT Strategy Committee, Standard IT Balanced Scorecard.
[Curriculum Design – 2015] Page 46
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Val-IT framework of ISACA
Module 2 :
Gain Exposure on Information Security Strategies
Information Systems Strategy
Role of Strategic Planning for IT, Role of Steering committee, Policies and
Procedures
Module 3 :
Understand the Importance of Risk management Program & Risk IT Framework of
ISACA
Risk Management Program
Develop a Risk Management Program. Risk Management Process, Risk Analysis
methods, Risk-IT Framework of ISACA
Module 4 :
Better understand the Information Security management & COBIT
Information Security Management
Introduction, Performance Optimization, IT Security roles & responsibilities,
Segregation of Duties, Description of COBIT and other Frameworks
Competencies of the course
On successful completion of this Module a learner will:
C1. Acquire Knowledge about IT and IS Governance
C2. Gain Exposure on Risk management and Risk –IT framework
C3. Understand the Importance Roles and segregation of Duties
C4. Get introduced to COBIT framework and VAL-IT of ISACA
[Curriculum Design – 2015] Page 47
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Learning Resources
o IT Governance – Peter Weill and Jeanne Ross, Pub: Harvard Business Review Press;
1 edition (June 1, 2004)
o Managing Risk and Information Security – Malcolm Harkins, Pub: Apress; 1 edition
(December 17, 20 )
o Information Security Risk Analysis – Thomas R.Peltier
Question Paper – Blue Print
IT Governance , RISK & Information Security Mgmt
Blue Print - Question Paper
Part A Part B Part C
Module (6/6) (7/10) (6/8) Part D (2/4)
* 1 Mark 2 Marks (5 Marks) (15 Marks)
1 1 2 1 1
2 1 2 2 1
3 2 3 2 1
4 2 3 3 1
[Curriculum Design – 2015] Page 48
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Course Code : CA5B13TB
Name of the Course: LINUX ADMINISTRATION
Duration: One Semester
Semester : 5
Total Lecture Hours: 72
Aim of the course:
To enable the learners to attain the skills required to manage and administer systems and
servers using Linux Operating System. The operating system used for this Module is Red Hat
Enterprise Linux (RHEL)
Course Overview and Context:
RHEL is a high performing operating system that is a long term and predictable operating
platform. With the flexibility to deploy on physical hardware, as a virtual host, as a virtual
guest or in the cloud, Red Hat Enterprise Linux is the ideal foundation for next-generation
datacenters. The fresh system administrators need to have a strong functional knowledge of
RHEL in any current IT work environment. The Module explores the security and network
access controls in Linux, organizing network system and File System, Securing Data and
Account Management
Syllabus Content:
Module 1: Fundamentals of Linux:
Development of Linux, Linux Distributions. Structure of Linux Operating System, Logging
In and General Orientation, The X Window System, KDE, GNOME. Navigating the File
Systems, Managing Files, File Permission and Access, Shell Basics, Shell Advanced
Features, File Name Generation. Common Unix commands
Module 2: Administration of Linux OS:
Installing Linux, Configuring Disk Devices, Creating and Managing File Systems, File
[Curriculum Design – 2015] Page 49
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
System Backup, Kickstart Installation, Linux Boot Loaders, Linux Kernel Management,
Managing User Accounts, Understanding File Listing, Ownership and Permission, Managing
Software using RPM, Connecting to Network, Linux Network Services, Setting up a Printer
Module 3: Input and Output Redirection:
Input Redirection, Output Redirection, Error Redirection, Filter, Pipes. Networking in
Linux: Network Connectivity, IP address, Accessing Remote system, Transferring files, and
Internet configuration. Process Control: Identifying Process, Managing Process, Background
Processing, Putting jobs in Background. Offline File Storage: Storing files to Media Booting
process and User
Module 4: Linux Basic networking and naming service:
Introduction to Networking, Networking, Internet Network Services, Dynamic DNS,
Electronic Messaging, Apache , NIS and Network File Sharing: NIS, Network File Sharing,
SAMBA. Security: Defining System Security Policies, System Authentication Services and
Security, Securing Services, Securing Data and Communication
Module 5 : The Unix File System
Inodes - Structure of a regular file – Directories - Conversion of a path name to an inode -
Super block - Inode assignment to a new file - Allocation of disk blocks. System calls for the
file System: Open – Read - Write - Lseek – Close - File creation - Creation of special files -
Changing directory and root - changing owner and mode – stat and fstat - pipes - Dup -
Mounting and Un mounting file systems - Link and Un link.
Competencies of the course:
C1. Understand the fundamentals of Linux
C2. Understand the administration of the OS like backup , user administration
C3. Implement Network System, NFS, SAMBA and Web Services in Redhat Linux
C4. Knowledge of file system
[Curriculum Design – 2015] Page 50
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Learning Resources
Linux Bible By: Christopher Negus- Wiley Publishing, Inc, 2010
Redhat Linux Networking and System Admin By: Terry Collings and Kurt Wall-M&T
Books, 2009
UNIX and Linux System Administration Handbook (4th Edition), Evi Nemeth, Garth
Snyder, Trent R. Hein, Ben Whaley, Prentice Hall; 4th edition (July 24, 2010)
Linux Administration A Beginners Guide 6/E, Wale Soyinka, McGraw-Hill Osborne
Media; 6 edition (February 21, 2012)
Question Paper – Blue Print
Linux Administration
Blue Print - Question Paper
Part A Part B Part C
Module (6/6) (7/10) (6/8) Part D (2/4)
* 1 Mark 2 Marks (5 Marks) (15 Marks)
1 1 2 1 1
2 1 2 2 1
3 2 3 2 1
4 2 3 3 1
[Curriculum Design – 2015] Page 51
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Course Code : CA5B10TB
Name of the course: COMPUTER FORENSICS AND INVESTIGATION - LAB
Duration: One semester
Semester : 5
Aim of the course:
To enable learners to identify the electronic evidence using Forensics tools, examining,
analyzing, data recovery techniques for the USB devices.
Course Overview and Context:
In this lab the learners can perform practical work by physical collection of electronic device
using forensic standards, re-building PCs in order to access the storage media securely, boot
sequence and Power On Self Test mode analysis, examination of File systems of windows,
linux, Mac.
The learners can also analyze network data sniffing, password and encryption process,
internet forensics and malware process, data recovery process for hard drive, data recovery
process for pen drive and CD.
Syllabus Content:
Module 1 : Understand the Physical Collection of electronic evidence using forensic
standards and to gain knowledge about the Dismantling and re-building PCs in order
to access the storage media safely
Module 2 :To know about Boot sequence and Power On Self Test mode analysis
and to understand about the Examination of File systems of Windows, Linux and Mac
Module 3 : To gain knowledge about the Analysing Word processing and Graphic file
format and to understand the basic Network data sniffing and analysing
Module 4: To know about the Password and encryption techniques and get enough
skills how to perform Internet forensic and Malware analysis
Module 5 :To know on how Data recovery techniques for hard drive and attain skills
of how to execute Data recovery techniques for Pen drive and CD
[Curriculum Design – 2015] Page 52
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Competencies of the course:
On successful completion of this lab a learner will:
o Understand the Physical Collection of electronic evidence using forensic standards
o Gain knowledge about the Dismantling and re-building PCs in order to access the
storage media safely
o To know about Boot sequence and Power On Self Test mode analysis
o To understand about the Examination of File systems of Windows, Linux and Mac
o Gain knowledge about the Analyzing Word processing and Graphic file format
o To understand the basic Network data sniffing and analyzing
o To know about the Password and encryption techniques
o Get enough skills how to perform Internet forensic and Malware analysis
o To know on how Data recovery techniques for hard drive
o Attain skills of how to execute Data recovery techniques for Pen drive and CD
Learning Resources
o Hacking Exposed Computer Forensics – Aaron Philipp, David Cowen, Chris Davis,
Pub: McGraw Hill-2009
o Guide to Computer Forensics and Investigations – 3rd Edition –B. Nelson, et al, -
Cengage, 2010 BBS
[Curriculum Design – 2015] Page 53
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Course Code : CA4B07PB
Name of the Course: LINUX ADMINISTRATION - LAB
Duration: One Semester
Total Lecture Hours: 36
Aim of the course: To provide the students hands on experience in real time.
Course Overview and Context: This course covers the administration and configuration of
the Linux Operating System.
Syllabus Content:
1) Configure the following tasks & verify it. (Hint - use grep/cut/tr/sed)
a) List the lines containing "/sbin/nologin" from the /etc/passwd file.
b) List only lines of output from ps, which lists running processes that contain the string
"init".
c) Display the list of GIDs from /etc/passwd file.
d) Alter all the letters that starts from range "a-f" to "A-F" in /etc/passwd file.
2) Create an alias named eth0:0 using below credentials in RHEL 5 and verify it.
(a) IP ADRESS = 172.16.0.1 (b) 255.255.0.0
(c) Default Gateway = 172.16.0.254 (d) DNS 1 = 4.2.2.1
3) Configure password policy for user john with below arguments in RHEL 5. After
configuration verify the policy applied.
(a) Minimum password age = 4 days
(b) Maximum password age = 15 days
(c) Inactive days = 2 days
[Curriculum Design – 2015] Page 54
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
(d) Account Expiration date = 6 months from today
4) Configure the following tasks:
(a) Add user accounts to your system: Joshua, alex, dax, bryan, zak, ed and manager.
Assign each user this password: 123@iMs.
(b) Add the groups to your system: sales with GID: 1000, HR with GID: 1100 and web
with GID: 1200.
(c) Add Joshua and alex to the sales group, dax and bryan to the HR group, zak and ed to
the web group and add manager to all of these groups.
(d) Login with each user & verify using id command that they are in the appropriate
groups.
5) Use ACL to accomplish these tasks:
(a) Create groups named Admin and Web.
(b) Create users named John and Jimmy.
(c) Create a new directory named /depts/tech/. Change the permission so that root is the
owner and Admin is the group owner.
(d) Use ACL to give full permission for /depts/tech/ to the Web group.
(e) Allow John read/execute but not write permission on the /depts/tech/ directory.
(f) Allow Jimmy full permission on the /depts/tech/ directory.
6) You are tasked with finding all SUID & SGID files under the / directories.
7) Configure your system that boots to run level 3 by default. Configure X server using
command in run level 3.
[Curriculum Design – 2015] Page 55
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
8) Devise a ps command that does the following. (Hint: sort/ps/top)
(a) List all processes.
(b) For each process, prints the information which displays the percentage of CPU usage,
the process ID & name of the command that created it.
(c) The output is sorted by the %cpu value from highest to lowest
9) Explain the suid, sgid & sticky bit permission with example
10) Customize the Bash prompt as per given tasks (Hint - PS1)
(a) Display the current value of primary prompt string.
(b) Changes prompt to print a static string "ITIMS -'".
(c) Restore the original prompt.
(d) Insert the bash history prompt special character "\!" between the hostname and dollar-
sign.
11) Configure given tasks for package management: (Hint: use rpm command)
(a) Check whether ftp package is installed or not.
(b) If it is not installed, install it & verify it.
(c) Display the configuration files available through this package.
(d) Be sure that ftp service must be enabled at startup.
12) Use rpm queries to answer the following questions.
(a) What files are in the "initscripts" package?
[Curriculum Design – 2015] Page 56
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
(b) Which installed packages have "gnome" in their names?
(c) Which RPM provides /etc/inittab?
13) Prepare a cron job that take the backup of /home at 5:00pm on every Saturday.
14) Change your system date to 1:00pm March 1990.
15) Copy /etc/fstab file to /tmp directory as newfstab file. The user owner is Jack and
group owner is admin. Give full permission to user owner and read, write permission to
group owner. No permission to others.
16) Configure your system such that SELinux must be in enforcing mode and firewall is
enables and ssh service is not allowed through your firewall.
17) Configure ftp server such that anonymous can download and upload the data to ftp
server. Deny users John and Carel to access the ftp server. Note that your ftp server must be
accessible in your private network only. It can't be accessible in another network.
18) Create a RAID level 1 on /dev/md0 device by creating two equal partitions of 100MB
size and mount it on /data. The RAID device must be mounted at the time of system startup.
19) Configure LVM in volume group named volgrp by creating 2 partitions of 100MB
size and mount it on /exam directory. The initial size of LVM is approximately 40MB and
after extending the size of LVM is 80MB.
21) Configure the DHCP server such that your DHCP server will able to provide IP
configuration to 65 systems in your network.
22) Configure the station as NFS server such that /share directory is shared & only
accessible in your network. This NFS share should be automatically mounted on remote
client using autofs. On remote client system, NFS share should be mounted on /data/share
directory.
23) Configure stationx.example.com for quota such that when user neo type
dd if=/dev/zero of=/quota/somefile bs=1024 count=30, he succeed. When he type
dd if=/dev/zero of=/quota/somefile bs=1024 count=70 he fails.
[Curriculum Design – 2015] Page 57
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Competencies of the course:
C1. Will be familiarized with the various type of desktops
C2. Will be familiarized with the commands
C3. Will be knowing with user management
C4. Will be configuring storage
C5. Configure the DHCP server
Learning Resources
Linux Bible By: Christopher Negus- Wiley Publishing, Inc, 2010
Redhat Linux Networking and System Admin By: Terry Collings and Kurt Wall-M&T
Books, 2009
UNIX and Linux System Administration Handbook (4th Edition), Evi Nemeth, Garth
Snyder, Trent R. Hein, Ben Whaley, Prentice Hall; 4th edition (July 24, 2010)
Linux Administration A Beginners Guide 6/E, Wale Soyinka, McGraw-Hill Osborne
Media; 6 edition (February 21, 2012)
[Curriculum Design – 2015] Page 58
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Course Code : CA6B14TB
Name of the course: MOBILE, WIRELESS AND VOIP SECURITY
Duration: One semester
Semester : 6
Total Lecture Hours: 72
Aim of the course
The main aim of this Module is to provide the introduction to Mobile Communications, how
to secure the Wireless protocols & VoIP protocols and its vulnerabilities. It also gives detail
descriptions over Mobile Forensics & how to extract data from it.
Course Overview and Context
The Module concentrates on the basis of Mobile & Telecommunication Protocols along
vulnerabilities to get knowledge and how on managerial, technical, procedural controls of
Mobile & Telecommunication Vulnerabilities.
The Module also explains about managerial, technical & procedural controls to address
Wireless Vulnerabilities, VoIP Vulnerabilities.
The Module covers Mobile Forensics process having Seizure and the data extraction types
like physical, logical and manual along external & internal memory, storage, analysis using
tool & techniques.
Syllabus Content
Module 1 : Understand about the Mobile Communication
Introduction to Mobile communication
Mobile & Telecommunication protocols and their vulnerabilities, Gain knowledge of
managerial, technical and procedural controls to address Mobile &
Telecommunication vulnerabilities
Module 2 : Understand about the Wireless Security
[Curriculum Design – 2015] Page 59
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Wireless Security
Wireless protocols and their vulnerabilities, Gain knowledge of managerial, technical
and procedural controls to address Wireless vulnerabilities
Module 3 : Understand about the VoIP Security
Voice over Internet Protocol (VOIP) Security
VOIP concepts, protocols and vulnerabilities, Gain knowledge of managerial,
technical and procedural controls to address VOIP vulnerabilities
Module 4 : Learn to identify Mobile Forensics & to handle how to extract data
Mobile Forensics & Data Extraction
Mobile forensics process including seizure, data acquisition types like Physical,
Logical, Manual, External & Internal memory, storage, analysis using tools &
techniques
Competencies of the course
On successful completion of this Module, the learner will
C1. Understand about the Mobile Communication
C2. Understand about the Wireless Security
C3. Understand about the VoIP Security
C4. Learn to identify Mobile Forensics & to handle how to extract data
Learning Resources
o Computer security handbook, Seymour Bosworth, Michel E. Kabay
o Securing wireless LANs: a practical guide for network managers, Gilbert Held
o Mobile telecommunications protocols for data networks by Anna Hać
[Curriculum Design – 2015] Page 60
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Question Paper – Blue Print
Mobile, Wireless & VOIP security
Blue Print - Question Paper
Part B Part C
Part A (7/10) (6/8)
Modul (6/6) 2 (5 Part D (2/4)
e* 1 Mark Marks Marks) (15 Marks)
1 1 2 1 1
2 1 2 2 1
3 2 3 2 1
4 2 3 3 1
[Curriculum Design – 2015] Page 61
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Course Code : CA6B17TB
Name of the Course: INTRODUCTION TO WINDOWS AZURE
Duration: One Semester
Semester : 6
Total Lecture Hours: 72
Aim of the course: To introduce the course to the students as a first time information to
ensure that the students are aware of the mostly used features.
Course Overview and Context: The course seeks to cover the holistic perspective of
Windows Azure on infrastructure perspective. How this service can be used by different
services.
Syllabus Content:
Module 1 : Introduction
Introduction to MS. Azure, Virtual Machines: Creating Virtual Machines, Difference
Between Basic and Standard VMs,Logging in to a VM and Working, Attaching an empty
Hard Disk to VM, Hosting a Website in VM , Configuring End Points, Scaling up and Down,
Creating a custom Image from VM,Creating a VM from a custom Image, Shut down VM
without Getting Billed,VM Pricing
Module 2 Managing Infrastructure in Azure
Managing Infrastructure in Azure: Azure Virtual Networks, Highly Available Azure Virtual
Machines ,Virtual Machine Configuration Management, Customizing Azure Virtual Machine
Networking. Load Balancing: Creating Cloud Services, Adding Virtual Machines to a
Cluster, Configuring Load Balancer.
Module 3 Windows Azure
Azure Storage: What is a Storage Account,Advantages, Tables, blobs, queues and drives,
Azure Appfabric: Connectivity and Access control Automation: Introduction Windows
[Curriculum Design – 2015] Page 62
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Power Shell ,Creation of Runbooks, Uploading a Shell Script, Authoring a Shell Script, ,
Module 4 SQL Azure
SQL Azure: Creating a SQL Server, Creating a SQL DB, Creating Tables, Adding Data to
the Tables, View Connection Strings, Security Configurations, Migrating on premise DB to
SQL Azure.
Module 5 Websites
Websites: Creating a Website, Setting deployment credentials, Choosing a platform, Setting
up Default page for website, Scaling ,Auto Scaling by Time, Auto Scaling by Metric,
Difference between Free, Shared, Basic and Standard websites, Creating a website using
Visual studio
Competencies of the course:
C1. Get acquainted with the Microsoft Azure
C2. Learn how to create a virtual machine
C3. Acquire knowledge about virtual networking in Azure
C4. Learn how to create locad balancer, clusters etc
C5. How to use SQL in Azure
C6. How to create and manage website in Azure
Learning Resources
Windows Azure Step By step by Roberto Brunetti
Cloud Computing Bible, Barrie Sosinsky, Wiley-India, 2010
Cloud Computing: Principles and Paradigms, Editors: Rajkumar Buyya,
James Broberg, Andrzej M. Goscinski, Wiley, 2011
[Curriculum Design – 2015] Page 63
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Question Paper – Blue Print
Introduction to Windows Azure
Blue Print - Question Paper
Part A Part B Part C
Module (6/6) (7/10) (6/8) Part D (2/4)
* 1 Mark 2 Marks (5 Marks) (15 Marks)
1 1 2 1 1
2 1 2 2 1
3 2 3 2 1
4 2 3 3 1
[Curriculum Design – 2015] Page 64
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Course Code : CA6B18TB
Name of the Course: DISASTER RECOVERY AND BUSINESS CONTINUITY
MANAGEMENT
Duration: One Semester
Semester : 6
Total Lecture Hours: 72
Aim of the course:
To enable learner to familiarize with the concept and importance of Business Continuity
Planning for an Organization and to make aware of the recovery strategies on the event of
Service Disruption, Testing and Maintenance also the training methodology to educate the
user community.
Course Overview and Context:
Primarily the Module covers the importance of having a Business Continuity Planning,
Disaster recovery planning for Organization and emphasizes the Standard practices proposed
by the NIST SP 800-34 Emergency Action Plan for recovery.
The Module gives a broad coverage on the different phases of BCP that consist of Project
Management and Initiation, Business Impact Analysis, Recovery Strategies, Planning
Development and Implementation.
The Module emphasizes the various methods of Technical Data Recovery procedures that can
be immediately taken on the event of a Service Disruption and also allocating the roles and
responsibilities for Various Key personnel.
The Module also gives importance to the Testing, Maintenance and Training process. A wide
variety of testing process that involves full interruption, walk through, Check listing,
Simulation and Parallel are explained in detail.
Syllabus Content:
Module 1 : Realize the Importance of BCP and DRP
[Curriculum Design – 2015] Page 65
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Introduction to Business Continuity Planning (BCP), Business Resumption Plan (BRP) or
Disaster Recovery Plan (DRP), Common terminologies used in BCP and DRP, NIST SP800-
34 Emergency Action plan which includes the phases of Recover/Resume, Protect and
Sustain, Causes of Disasters
Module 2 : Acquire knowledge on Creation and implementation of BCP
BCP objectives. Information Protection Environment. Security Technology and Tools. Steps
involved in creating a BCP, Phase 1: Project Management and Initiation. Phase 2: Business
Impact Analysis. Phase 3: Recovery Strategies, Phase 4: Plan Development and
Implementation
Module 3 : Gain Knowledge on Technical Data Recovery
Business Recovery strategies. Facility and Supply Recovery strategies. User Recovery
strategies. Technical Recovery strategies, Data Recovery strategies, Activation Phase- Major
Disaster or Disruption, Intermediate Disaster or Disruption, Minor Disaster, Activating
BC/DR Teams, Developing Triggers, Transition Trigger. Defining BC/DR Team and Key
Personnel, Defining Tasks, Assigning Resources, Communication Plan
Module 4 :Recognize the necessity to Test and Maintain a BCP
Testing, maintenance, awareness & training mechanisms. Different types of tests including
structured walk-through, checklist test, simulation, parallel test and full interruption test.
Steps required to maintain a BCP. Requirements for BCP awareness and training Visit a
business organization of your choice and prepare a Business Continuity Plan for the same
using the learning from this course
Competencies of the course:
C1. Realize the Importance of BCP and DRP
C2. Acquire knowledge on Creation and implementation of BCP
C3. Gain Knowledge on Technical Data Recovery
C4. Recognize the necessity to Test and Maintain a BCP
[Curriculum Design – 2015] Page 66
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Learning Resources
Business Continuity and Disaster Recovery Planning – Susan Snedaker, Pub:
Syngress, 2007
Crisis Management Mastering Skills – Harvard Business School, 2004
Disaster Recovery Planning: Preparing – Jon William Toigo, 3rd Edition, 2012
Question Paper – Blue Print
Disaster recovery and Business Continuity Management
Blue Print - Question Paper
Part A Part B Part C
Module (6/6) (7/10) (6/8) Part D (2/4)
* 1 Mark 2 Marks (5 Marks) (15 Marks)
1 1 2 1 1
2 1 2 2 1
3 2 3 2 1
4 2 3 3 1
[Curriculum Design – 2015] Page 67
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
SYLLABI
OF
CHOICE BASED CORE COURSES
[Curriculum Design – 2015] Page 68
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Course Code : CA3B01TB
Name of the Course: FUNDAMENTALS OF ITIL
Duration: One Semester
Semester : 3
Total Lecture Hours: 72
Aim of the course: All organizations have Mission Vision goals and objectives. IT services
play a major role in accomplishing the same. Foundation of IT Service management is Based
on ITIL and it is widely accepted as a framework. Aim of the course is to provide with a
exposure of the same.
Course Overview and Context: In this course students will be provided with the details of
the Service lifecycle and its components.
Syllabus Content:
Module 1: ITIL Overview and Service Strategy
ITIL History, Components of the ITIL Library, IT Service Management, Organizing for IT
Service Management, Technology and Architecture, Overview of HPSM and OTRS as
service management tool, Service Strategy: Service Strategy Lifecycle Stage, Service
Portfolio Management, the Demand Management Process, the IT Financial Management
Process, Introduction to ISO 20000 Standards
Module 2: Service Design
Service Design Lifecycle Stage, The Service Catalog Management Process, The Service
Level Management Process, The Availability Management Process, The Capacity
Management Process, The Information Security, Management Process, The IT Service
Continuity, Management Process, The Supplier Management Process
Module 3: Service Transition
Service Transition Lifecycle Stage, the Change Management Process, the Release and
[Curriculum Design – 2015] Page 69
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Deployment Management Process, the Service Asset and Configuration Management
Process, Knowledge Management
Module 4: Service Operation, Continual Service Improvement
Service Operation Functions : Service Operation Lifecycle Stage, The Service Desk
Function, The Technical Management Function, The Application Management Function, The
IT Operations Management Function Service Operation Processes :The Event Management
Process, The Incident Management Process, The Request Fulfillment Process, The Access
Management Process, The Problem Management Process,
Module 5: Continual Service Improvement
Continual Service Improvement principles - CSI and organizational change, Ownership,
Role definitions , External and internal drivers , Service Level Management , The Deming
Cycle, Service measurement ,Knowledge Management, Benchmarks , Governance
,Frameworks, models, standards and quality systems Continual Service Improvement
processes : 7step improvement process, Service reporting, Service management, return on in
investment for CSI, business questions for CSI, Service level management
Competencies of the course:
C1. Introduction to ITIL
C2. Understand Service Strategy
C3. Discuss Service Design
C4. Familiarize Service Operation
C5. Evaluate Continual Service improvement
Learning Resources
Introduction to ITIL, Jan van Bon Stationery Office Books, The Stationery Office,
2010
HP operation Manual from HP, 2010
A Guide to Service Desk Concepts Donna Knapp From Cengage Learning, 2010
[Curriculum Design – 2015] Page 70
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
The Shortcut Guide to Virtualization and Service Automation, Greg Shield Real-time
Publishers, 2008
Service automation and dynamic provisioning techniques in IP/MPLS environments -
Christian Jacquenet, Gilles Bourdon, Mohamed Boucadair John Wiley and Sons,
2008
Question Paper – Blue Print
ITIL
Blue Print - Question Paper
Part B
Part A (6/6) (7/10) Part C (6/8) Part D (2/4)
Module * 1 Mark 2 Marks (5 Marks) (15 Marks)
1 1 2 1 1
2 1 2 2 1
3 2 3 2 1
4 2 3 3 1
[Curriculum Design – 2015] Page 71
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Course Code : CA3B03T
Name of the Course: SOFTWARE ENGINEERING
Duration: One Semester
Semester : 3
Total Lecture Hours: 72
Aim of the course:
The aim of this course is to enable the learner to understand the different processes that are
followed in developing a software.
Course Overview and Context:
Software can be defined as ‘computer instructions or data’ The term ‘Software Engineering’
is applied to the study and application of engineering for the purpose of design, development
and maintenance of software. In general, it is the set of rules and procedures to be followed
while developing computer software. Software Engineering is all about the right practices
and approach towards computer programming; hence everyone is of the opinion that it must
be considered as an engineering segment rather than art or craft.
This course deals with the different software development lifecycle models, and software
testing. It also deals with software project management concepts like different models,
planning, scheduling, etc.
Syllabus Content:
MODULE I: SOFTWARE PRODUCT AND PROCESS
Introduction – S/W Engineering Paradigm – Verification – Validation – Life Cycle Models –
System Engineering – Computer Based System – Business Process Engineering, Overview –
Product Engineering Overview.
MODULE II: SOFTWARE REQUIREMENTS
Functional and Non-Functional – Software Document – Requirement Engineering Process –
Feasibility Studies – Software Prototyping – Prototyping in the Software Process – Data –
[Curriculum Design – 2015] Page 72
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Functional and Behavioral Models – Structured Analysis and Data Dictionary.
MODULE III: ANALYSIS, DESIGN CONCEPTS AND PRINCIPLES
Systems Engineering - Analysis Concepts - Design Process And Concepts – Modular Design
– Design Heuristic – Architectural Design – Data Design – User Interface Design – Real
Time Software Design – System Design – Real Time Executives – Data Acquisition System
– Monitoring And Control System.
MODULE IV: TESTING
Taxonomy Of Software Testing – Types Of S/W Test – Black Box Testing – Testing
Boundary Conditions – Structural Testing – Test Coverage Criteria Based On Data Flow
Mechanisms – Regression Testing – Module Testing – Integration Testing – Validation
Testing – System Testing And Debugging – Software Implementation Techniques
MODULE V: SOFTWARE PROJECT MANAGEMENT
Measures And Measurements – ZIPF’s Law – Software Cost Estimation – Function Point
Models – COCOMO Model – Delphi Method – Scheduling – Earned Value Analysis – Error
Tracking – Software Configuration Management – Program Evolution Dynamics – Software
Maintenance – Project Planning – Project Scheduling– Risk Management – CASE Tools
Competencies of the course:
C1: Understand the different attributes of a good software
C2: Recognize how to overcome the key challenges and rules to be followed in various
phases of software development
C3: Understand different models followed during SDLC along with examples
C4: Understand the different phases of SDLC
C5: Understand the different types of software testing
C6: Compare the different types of software testing
C7: Understand the different cost estimation models
C8: Recognize the different project planning and scheduling techniques
C9: Understand how to develop an error free software and analyze which SDLC model to
[Curriculum Design – 2015] Page 73
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
select
C10: Recognize risk management in software project management
Learning Resources
Roger S. Pressman, “Software Engineering – A practitioner’s Approach”, Sixth
Edition, McGraw-Hill International Edition, 2005
Ian Sommerville, “Software engineering”, Seventh Edition, Pearson Education Asia,
2007
Question Paper – Blue Print
Software engineering
Blue Print - Question Paper
Module
* Part A Part B Part C Part D
1 1 2 1 0
2 1 2 2 1
3 2 2 2 1
4 1 2 2 1
5 1 2 1 1
[Curriculum Design – 2015] Page 74
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Course Code : CA4B06TB
Name of the Course: CLOUD WEB SERVICES
Duration: One Semester
Semester : 4
Total Lecture Hours: 72
Aim of the course: Is to educate the students about the web service via the AMAZON WEB
service product.
Course Overview and Context:
This course covers the Amazon Web Service in detail about the networking, storage and
And security aspect of the most popular Product
Syllabus Content:
Module 1: Introduction to AWS and Management Console
Definition of Cloud Computing, IAAS PAAS & SAAS, Private & Public Cloud, AWS
Business hierarchy, The AWS Infrastructure, AWS Strategy, AWS Ecosystem, AWS
Benefits, AWS Competitors.AWS Management Console: Setting up AWS Account,
Accessing AWS Services, S3 Bucket, Case Studies.
Module 2: AWS Storage, Elasticity and AWS Networking
Amazon Storage, S3 Storage Basics, Managing Voluminous Information with EBS, Glacier
Storage Service, AWS Networking: Networking Basics, VLAN Basics, Basics of AWS
VLANs, AWS Network IP Addressing and Mapping. Case Studies
Module 3: AWS Security and Services
Boundaries of Cloud, Security, AWS Security Groups, Security groups for Application
Partitioning – Concept, Amazon Virtual Private Cloud.AWS Services: Cloud Front,
Relational Database Service, AWS Service Integration, AWS Platform Services: Cloud
Search, Simple Queue Service, Simple Notification Service, Simple Email Services, Simple
[Curriculum Design – 2015] Page 75
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Workflow Service, AWS Management Services: Managing AWS Applications, Monitoring
with Cloud watch, Auto-Scaling in AWS, AWS Cloud Formation, Case Studies
Module 4: AWS and Applications on Cloud & AWS Costs
Salient Features of AWS, Cloud Application Designing Principles, AWS Costing,
Advantages of Cost Utilization Tracking, working Principles, Managing AWS Costs, Case
Studies.
Competencies of the course:
C1. Knowledge about the different types of cloud service
C2. Knowledge about the different types of cloud
C3. Storage Service provided by the product
C4. Features of Cloud application
Learning Resources
Cloud Computing: Principles and Paradigms, Rajkumar Buyya, James Broberg, Andrzej
M. Goscinski,, John Wiley and Sons Publications, 2011
Brief Guide to Cloud Computing, Christopher Barnett, Constable & Robinson Limited,
2010
Amazon Web Services for Dummies, Bernald Golden, John Wiley & Sons, 2013
Question Paper – Blue Print
Cloud Web Services
Blue Print - Question Paper
Module
* Part A Part B Part C Part D
1 1 3 2 1
2 1 2 2 1
3 2 2 2 1
4 2 3 2 1
[Curriculum Design – 2015] Page 76
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Course Code : CA4B07TB
Name of the Course: FUNDAMENTALS OF DATACENTER
Duration: One Semester
Semester : 4
Total Lecture Hours: 72
Aim of the course: Is to provide the students the knowledge about data center and its
requirements and the features.
Course Overview and Context: This course is designed to deliver the relevant knowledge
about Data Center including the design in detail wit introduction to server Farm and role of
Data Center in Disaster recovery and Business continuity management.
Syllabus Content:
Module 1: Overview of Data Centers
Data Centers Defined, Data Center Goals, Data Center Facilities, Roles of Data Centers in the
Enterprise, Roles of Data Centers in the Service Provider Environment, , Application
Architecture Models. The Client/Server Model and Its Evolution, The n-Tier Model, Multitier
Architecture Application Environment, Data Center Architecture.
Module 2: Data Center Requirements
Data Center Prerequisites, Required Physical Area for Equipment and Unoccupied Space,
Required Power to Run All the Devices, Required Cooling and HVAC, Required Weight,
Required Network Bandwidth, Budget Constraints, Selecting a Geographic Location, Safe
from Natural Hazards, Safe from Man-Made Disasters, Availability of Local Technical
Talent, Abundant and Inexpensive Utilities Such as Power and Water, Selecting an Existing
Building (Retrofitting), tier standard
[Curriculum Design – 2015] Page 77
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Module 3: Data Center Design
Characteristics of an Outstanding Design, Guidelines for Planning a Data Center, Data Center
Structures, No-Raised or Raised Floor, Aisles, Ramp, Compulsory Local Building Codes,
Raised Floor Design and Deployment, Plenum, Floor Tiles, Equipment Weight and Tile
Strength, Electrical Wireways, Cable Trays, Design and Plan against Vandalism,
Module 4: Introduction to Server Farms
Types of server farms and data centre, internet server farm, intranet server farm, extranet
server farm , internet data center, corporate data center, software defined data center, data
center topologies, Aggregation Layer, Access Layer, Front-End Segment, Application
Segment, Back-End Segment, Storage Layer, Data Center Transport Layer, Data Center
Services, IP Infrastructure Services, Application Services, Security Services, Storage
Services.
Module 5: Business Continuity and Disaster Recovery fundamentals
Business continuance infrastructure services, the need for redundancy,, Information
availability , BC terminology , BC planning life cycle , BC technology solutions , backup and
recovery considerations , backup technologies , Uses of local replicas , Local replication
technologies , Restore and restart considerations , Modes of remote replications , remote
replication technologies .
Competencies of the course:
C1. Overview of the Data Center
C2. Requirements of Data Centers
C3. Concepts of Design of the Data Centers
C4. Knowledge about Server Farms
C5. Role of Data Center in Business Continuity and Disaster Recovery Management
[Curriculum Design – 2015] Page 78
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Learning Resources
IP Storage Networking by : Gary Oreinstein, Addison Wesley Professional, 2006
Question Paper – Blue Print
Fundamentals of DATA CENTER
Blue Print - Question Paper
Module * Part A Part B Part C Part D
1 1 2 1 0
2 1 2 2 1
3 2 2 2 1
4 1 2 2 1
5 1 2 1 1
[Curriculum Design – 2015] Page 79
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Course Code :CA6B15TB
Name of the course: DATABASE SECURITY FUNDAMENTALS
Duration: One Semester
Semester : 6
Total Lecture Hours: 72
Aim of the course:
To enable learner to familiarize with the Enterprise Database and Data Warehousing
environment with advantages and its growing importance in Organization’s Business
environment. With this in mind it helps the learner to understand the criticality of the
database resource thereby to provide an idea to enable protective measures through server
hardening.
Course Overview and Context:
The Module provides the Background idea about the Broad structure of Database and Data
warehousing environment and also it explains the methodology to design a database and
advantages of Database management system. By explaining the irreplaceable functionality
and feature that a DBMS can offer to an IT system, the learner will understand the criticality
of the resource.
The Module explains the Basic security measures available in the different Database
management software Products like ORACLE and SQL and also explains the implementation
of access control mechanism using Data Control Language.
The Module also covers the importance of integrity in building databases and how it can be
achieved. There is an in depth coverage of SQL injection attacks and countermeasure and a
detailed procedure on securing a database server by removing unwanted services. Finally it
makes the learner to understand the step by step Data warehousing process and Vulnerability
management procedure to maintain a secure Database management system.
[Curriculum Design – 2015] Page 80
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Syllabus Content:
Module 1 : Describe the importance of Database and protective measures for ORACLE
and SQL
The Database and Data Warehousing Environment, DBMS Architecture:
Introduction to Database & DBMS Architecture, Hierarchical Database Management
Systems, Network Database Management Systems, Relational Database Management
Systems, Object-Oriented Database Management Systems, End-User Database Management
Systems, Spreadsheets, Hardening the Database Environment, Basic Security measures in
Oracle and SQL.
Module 2 :Demonstrate Different types of SQL injection attacks and Countermeasures
Database Interface Languages:
Introduction to Database Interface Languages, Concepts of Database Interface Languages,
Database Integrity, Triggers and Event, Configuring the Server auditing, SQL Injection,
Prevention of SQL Injection, Open Connectivity Database and Object Linking and
Embedding.
Module 3 : Evaluate the importance of Database security in the Internet architecture
Accessing Databases through the Internet:
Introduction to Accessing Databases through the Internet, Concept of Accessing Databases
through the Internet, the three tier approach, securing a Web server and a Database server,
Remove Unnecessary Services if not needed to the business operation, Remote access,
Development and Security testing, monitoring the events.
Module 4 : Understand the vulnerability management process for Enterprise DB
security
Data Warehousing:
Introduction to Data Warehousing concepts, the concept of Data Warehousing, Metadata and
Online Analytical Processing (OLAP)Data mining, Database Vulnerabilities and threats,
Vulnerability Scanners, Monitoring and Base lining, Patch management, Procedure for Patch
[Curriculum Design – 2015] Page 81
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
management.
Competencies of the course:
On successful completion of this Module, the learner will:
C1. Describe the importance of Database and protective measures for ORACLE and SQL
C2. Demonstrate Different types of SQL injection attacks and Countermeasures
C3. Evaluate the importance of Database security in the Internet architecture
C4. Understand the vulnerability management process in Database security.
Learning Resources
o Database security by Silvana Castano, 2nd Edition, Pub: Addison-Wesley
Professional , 2008
o Handbook of database security: applications and trends Michael Gertz, SushilJajodia
2008
o Implementing database security and auditing: a guide for DBAs, ...Ron Ben-Natan
2009
Question Paper – Blue Print
Database Security Fundamentals
Blue Print - Question Paper
Module
* Part A Part B Part C Part D
1 1 2 2 1
2 2 2 2 1
3 1 3 2 1
4 2 3 2 1
5
[Curriculum Design – 2015] Page 82
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Course Code : CA6B16TB
Name of the course: HACKTIVISM, CYBERWARFARE AND CYBERTERRORISM
Duration: One semester
Semester : 6
Total Lecture Hours: 72
Aim of the course:
To enable learners to understand about the essentials of Hacktivism, Cyber warfare, Cyber
terrorism. The learners can also know about the current trends in Hacktivism and also the
nature of cyber warfare and finally about the Defensive measures.
Course Overview and Context:
The Module explains the introduction, impact of Hacktivism, cyber warfare, cyber terrorism
etc., the types & economic impact of information warfare.
The learners come to know about the current trends in hacktivism having wiki leaks,
anonymous, lulz movements and political nature of Hacktivism how the players involved in
it. Current trends and defensive strategies for private companies ruining those.
The Module specifies the 5 types of modern warfare including cyber warfare, nature, CAN,
CNE and how they both deploy, new cyber warfare models, current trends, cyber terrorism
and finally the recent incidents.
Learners finally know about the defense in Depth and real life samples like network defense
and the nefarious attacks of network and defense tools.
Syllabus Content:
Module 1 : To know about the Introduction of Hacktivism, Cyber warfare & cyber
terrorism.
Introduction to Hacktivism, Cyber warfare and Cyber
[Curriculum Design – 2015] Page 83
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
terrorism
Define Hacktivism, Define Cyber warfare, Define Cyber terrorism, Impact of
hacktivism, cyber warfare and cyber terrorism to society and business. Types of
Information warfare strategies and activities, Economic Impact of Information
warfare
Module 2 : Gain knowledge about the current trends in Hacktivism
Current Trends in Hacktivism
Current trends in hacktivism including wiki leaks, anonymous and lulz movements,
Political natures of Hacktivism, Players involved in hacktivism and discuss the recent
incidents, Countermeasures to protect against such incidents. Defensive strategies for
Private Companies, Surviving Offensive Ruinous and Containment
Module 3 : To understand about the nature of Cyber warfare.
Nature of Cyber warfare
5 types of modern warfare including cyber warfare, Strategic nature of cyber warfare,
Computer Network Attack (CNA) and Computer Network Exploitation (CNE), How
to deploy CNA and CNE assets within a strategic context in support of obtaining a
kinetic goal, Review historic attacks and learn new cyber warfare models that can be
used to analyze a state-sponsored attack, Current trends in Cyber warfare and Cyber
terrorism including the players and groups involved, Analyze the resent incidents of
Cyber warfare and Cyber terrorism
Module 4 :Learn to identify the Defensive measures.
Defensive measures
Defense in Depth and real life examples of how to apply it to network defense. Why
information assurance of computer equipment is critical to defend the network from
nefarious attacks. Use Defense tools
Competencies of the course:
[Curriculum Design – 2015] Page 84
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
On successful completion of this Module, the learner will be able to
C1. To know about the Introduction of Hacktivism, Cyber warfare & cyber terrorism.
C2. Gain knowledge about the current trends in Hacktivism
C3. To understand about the nature of Cyber warfare.
C4. Learn to identify the Defensive measures
Learning Resources
o Information Warfare – How to survive Cyber attacks – Michael Erbschloe,
Osborne/McGraw Hill, 2008
o Cyber security – From Luxury to Necessity by Balaji Srimoolanathan, Pub:
Frost & Sullivan, 2011
o Information Warfare and Security (Addison Wesley, 1998) Dorothy E Denning
o Cyberterrorism – The Jihadi Cyber terror Threat – By Dorothy E Denning – Naval
Postgraduate school, 2009
Blue Print of the Question Paper
Hacktivism, Cyberware and Cyberterrorism
Blue Print - Question Paper
Module
* Part A Part B Part C Part D
1 1 2 2 1
2 2 2 2 1
3 1 3 2 1
4 2 3 2 1
5
[Curriculum Design – 2015] Page 85
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
SYLLABI
OF
COMPLEMENTARY COURSES
[Curriculum Design – 2015] Page 86
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Course Code : CA1C01TB
Name of the Course: BASIC STATISTICS
Duration: One Semester
Semester : 1
Total Lecture Hours: 72
Aim of the course: Is to provide the relevant knowledge to the students to introduce the
basic concepts in Statistics and to develop data reduction techniques.
Course Overview and Context: This course covers the basics of statistics. The idea is to
provide the students with the basic understanding of the subject.
Syllabus Content:
Module I
Introduction to Statistics, Population and Sample, Collection of Data, Various methods of
data collection, Census and Sampling Methods of Sampling – Simple Random Sampling–
stratified sampling – systematic sampling (Method only), Types of data – quantitative,
qualitative, Classification and Tabulation, Frequency Table, Diagrammatic representation –
Bar diagram, pie diagram; pictogram and cartogram.
Module II
Measures of Central Tendency – Mean; Median; Mode; Geometric Mean; Harmonic Mean
and Properties, Partition values- Quartiles, Deciles, Percentiles, Absolute and Relative
measures of Dispersion – Range, Quartile Deviation, Box Plot, Mean Deviation, Standard
Deviation, Coefficient of Variation.
Graphical representation – histogram; frequency polygon; frequency curve; ogives and stem
and leaf chart.
Module III
Raw Moments, Central Moments, Inter Relationships (First Four Moments), Skewness –
Measures – Pearson’s, Bowley’s and Moment Measure; Kurtosis- Measures of Kurtosis –
[Curriculum Design – 2015] Page 87
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Moment Measure, Measure based on partition values.
Module IV
Index Numbers – definition, Simple Index Numbers; Weighted Index Numbers – Laspeyer’s
Paasche’s and Fisher’s Index Numbers, Test of Index Numbers, Construction of Index
Numbers, Cost of Living Index Numbers – Family Budget Method, Aggregate Expenditure
Method.
Competencies of the course:
C1. Understand data collection method
C2. Understand sampling method
C3. Analyze different types of DATA
C4. Determining Central tendency
C5. Understand index numbers
Learning Resources
S.P. Gupta: Statistical Methods (Sultan Chand & Sons Delhi).
S.C. Gupta and V.K. Kapoor: Fundamentals of Mathematical Statistics, Sultan Chand
and Sons.
B.L. Agarwal: Basic Statistics, New Age International (P) Ltd.
Parimal Mukhopadhya: Mathematical Statistics, New Central Book Agency (P) Ltd,
Calcutta
Murthy M.N.: Sampling theory and Methods, Statistical Publishing Society, Calcutta.
[Curriculum Design – 2015] Page 88
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Question Paper – Blue Print
Modules 1Mark 2Marks 5 Marks 15 Marks
6/6 7/10 5/8 2/4
Module I 1 2 2 --
Module II 2 3 2 2
Module III 2 3 2 1
Module IV 1 2 2 1
Model Question Paper
First Semester
Complementary Course
ST1CT01B – BASIC STATISTICS
Time: 3 hours Max.: 80 marks
Use of Scientific calculators and Statistical tables are permitted.
Part A (Short Answer Questions)
Answer all questions.
Each question carries 1 mark.
1. Define Simple random sampling
2. Define Mean deviation.
3. What is the Geometric mean of 16 and 25?
4. Give any 2 measures of Skewness.
5. The first two moments of a distribution about X = 4 are 1 and 4. Find the mean and
variance.
6. What is commodity reversal test ?
(6x1=6 marks)
[Curriculum Design – 2015] Page 89
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Part B (Brief Answer Questions)
Answer any seven questions.
Each question carries 2 marks.
7. Give the sources of secondary data.
8. Distinguish between Census and sample survey.
9. Find the standard deviation of the numbers 7,9,16,24,26
10. Prove that the sum of deviations of observations from its A.M is zero.
11. What is the difference between a Bar diagram and a Histogram.
12. What is Kurtosis? Give the measure of Kurtosis in common use.
13. What is Sheppard’s correction? What will be the correction for first four central
moments?
14. Define Raw and Central moments.
15. If ∑Pk = 360, ∑Po= 300 find the simple aggregate Index number.
16. Examine whether Laspeyer’s Index number satisfies Factor reversal test.
(7x2 = 14 marks)
Part C (Short Essay Questions)
Answer any five questions.
Each question carries 6 marks.
17. Draw an ogive for the following data and hence find Median.
C. I: 25-40 40-55 55-70 70-85 85-100
F: 7 13 21 12 9
18. What are the parts of a table?
19. Explain Box Plot
20. Find Mean, Median and using the Empirical relation find Mode.
X: 4 8 12 16 20 24
F: 2 7 15 11 9 6
21. Establish the relation between Raw and Central moments.
[Curriculum Design – 2015] Page 90
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
22. For a distribution the Mean is 10, Variance is 16, β1 = 1 , β2 = 4, Obtain the first four
moments about 0
23. Explain the various steps involved in the Construction of an Index Number.
24. What are the limitations of an Index Number?
(5x6 = 30 marks)
Part D (Essay Questions)
Answer any two questions.
Each question carries 15 marks.
25. (a) What is an Ogive ? Explain how the Ogive can be used to find out the Median and
Quartiles?
(b) Explain Stem and Leaf Chart.
26. An Analysis of monthly wages paid to workers in two firms A and B belonging to the
same Industry, gives the following results.
Firm A Firm B
No. Of wage earners 550 650
Average monthly wages 50 45
Variance of the distribution of wages 90 120
(a) Which firm A or B pays out larger amount as monthly wages?
(b) In which firm A or B is there greater variability in Individual wages ?
(c) What are the measures of average and Standard deviation of monthly wages of
all the workers in the two firms taken together ?
27. Calculate Laspeyer’s , Paasche’s and hence Fisher’s Index numbers for the following
data.
Price(Rs per Module) Quantity (Kg)
Commodity Base year Current year Base year Current year
A 20 30 12 18
[Curriculum Design – 2015] Page 91
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
B 30 42 10 14
C 22 34 6 10
D 18 28 8 12
28. (a) Show that β2 > 1 for a Disrete distribution.
(b) Calculate Pearson’s Coefficient of Skewness for the following distribution
Variable 0-5 5-10 10-15 15 – 20 20 – 25 25 -30 30-35
Frequency 3 5 9 15 21 10 7
(2x15 = 30 marks)
[Curriculum Design – 2015] Page 92
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Course Code : CA1C02TB
Name of the Course: COMPUTER FUNDAMENTALS & ORGANIZATION
Duration: One Semester
Semester : 1
Total Lecture Hours: 72
Aim of the course:
To enable learners to understand the basics of computer organization, gain functional
knowledge of the hardware used in computers and the basic knowledge of digital
fundamentals, Microsoft office tools and networking
Course Overview and Context:
The knowledge of how a computer works is very important for any IT learner. This will build
a basic understanding for learning core topics like networking, operating systems, etc.. The
functional knowledge of a computer's working and its main building components are
paramount. The computers of today may come with a variety of features, but the basic
working principles will remain the same.
In this course, the learners will explore the fundamentals of organization of a computer and
the principles and building Modules, i.e., its hardware. Also, the learners will be introduced to
digital fundamentals, the different Microsoft Office tools and basic networking.
Syllabus Content:
Module 1: General Features of a Computer
General features of a computer, Generation of computers, Personal computer, workstation,
mainframe computer and super computers. Computer applications – data processing,
information processing, commercial, office automation, industry and engineering, healthcare,
education, graphics and multimedia.
Module 2: Computer Organization
Computer organization, central processing Module, computer memory – primary memory and
[Curriculum Design – 2015] Page 93
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
secondary memory. Secondary storage devices – Magnetic and optical media. Input and
output Modules. OMR, OCR, MICR, scanner, mouse, modem.
Module 3: Computer Hardware and Software
Computer hardware and software. Machine language and high level language. Application
software, computer program, operating system. Computer virus, antivirus and computer
security. Elements of MS DOS and Windows OS. Computer arithmetic, Binary, octal and
hexadecimal number systems. Algorithm and flowcharts, illustrations, elements of a database
and its applications. Basic Gates(Demorgans theorems, duality theorem,
NOR,NAND,XOR,XNOR gates), Boolean expressions and logic diagrams, Types of Boolean
expressions
Module 4: MS Office
Word processing and electronic spread sheet. An overview of MSWORD, MSEXCEL and
MSPOWERPOINT
Module 5: Introduction to Networking
Network of computers. Types of networks, LAN, Intranet and Internet. Internet applications.
World wide web, E-mail, browsing and searching, search engines, multimedia applications.
Competencies of the course:
C1: Understand the Organization of Computers
C2: Understand the PC Hardware Components
C3: Compare the different generations and features of computers
C4: Distinguish between computer hardware and software
C5: Identify different threats that violates computer security
C6: Recognise the different logical gates and their applications
C7: Identify how to create precise documents and PowerPoint presentations using Microsoft
Office tools
[Curriculum Design – 2015] Page 94
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
C8: Understand the different types of networks
C9: Identify various internet applications
C10: Identify and list out the functionalities and features of different components of a
computer.
Learning Resources
Hamacher, Computer Organization McGrawhill
Rajaraman, V (1999): Fundamentals of Computers, Prentice Hall India
Alexis Leon and Mathews Leon (1999) : Fundamentals of information Technology,
Leon Techworld Pub.
Jain, S K (1999) : Information Technology “O” level made simple, BPB Pub
Jain V K (2000) “O” Level Personal Computer software, BPB Pub.
Alexis Leon: Computers for everyone. Vikas, UBS
Anil Madaan : Illustrated Computer Encyclopedia. Dreamland Pub
Sinha. Computer Fundamentals BPB Pub.
Question Paper – Blue Print
Computer Fundamentals and Organization
Blue Print - Question Paper
Module
* Part A Part B Part C Part D
1 1 2 1 1
2 1 2 2 1
3 2 2 2 1
4 1 2 1 0
5 1 2 2 1
[Curriculum Design – 2015] Page 95
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Model Question Paper
Second Semester
CA1C02TB - COMPUTER FUNDAMENTALS AND ORGANIZATION
Time : 3Hrs. Total Marks: 80
PART A: (Answer all the questions. Each question carries 1 mark.)
1. What is Scale of Integration?
2. ……………………. is the expansion of OCR.
3. Name two different types of hardware devices.
4. Define flowchart.
5. Write shortcut commands for copy and paste.
6. What is Point-to-Point transmission?
PART B: (Answer any 7 of the following questions. Each question carries 2 marks.)
7. What is a Computer?
8. List out the characteristics of a microcomputer.
9. Give a note on ALU?
10. What is virtual memory?
11. Define an algorithm with a simple example.
12. Convert the binary whole number 110010 to its corresponding decimal number.
13. List any four characteristics of ‘Microsoft Office 2013’.
14. Explain how to apply a theme in ‘Microsoft PowerPoint’?
15. Expand CAN and PAN and briefly explain them.
16. How will you configure the addresses in the Internet?
PART C: (Answer any 5 of the following questions. Each question carries 6 marks.)
17. Explain the overview of a computer system.
18. Explain in detail, the instruction steps to execute CPU cycle.
19. What is RAID? Explain the RAID Levels.
20. Write a short note on Machine language with an example.
21. Briefly explain about ‘Interpreters’ and ‘Assemblers’.
22. Explain the ‘Security’ feature in MS-Office.
23. Write a short note on search engines.
24. Explain DNS with example.
PART D: (Answer any 2 of the following questions. Each question carries 15 marks.)
25. Discuss the generations of computer with suitable examples.
26. Explain the memory Hierarchy.
[Curriculum Design – 2015] Page 96
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
27. What are Basic Gates? Explain with truth tables.
28. Explain different types of Networks along with their advantages and disadvantages.
Course Code : CA1C03TB
Name of the Course: PROGRAMMING IN C
Duration: One Semester
Semester : 1
Total Lecture Hours: 72
Aim of the course:
To provide learners with an understanding of the different principles of programming with
the language C. It will also enable them to design and implement procedural programming
concepts.
Course Overview and Context:
Even with the introduction of several high level languages and frameworks, the development
of procedural codes is important in several commercial app developments. The object
oriented platforms and event driven systems use procedural languages for coding integral
command content. C is an important procedural language and was developed initially to write
the UNIX operating system. UNIX operating system, C compiler and all UNIX application
programs are written in C. C is popular because, it is easy to learn, produces efficient
programs, can handle low-level activities, and can be compiled on a variety of platforms.
This course focuses on all the basic concepts, syntax and constructs of the C language. For
learners, who are new to programming, this course can be considered as the starting point
before taking up any other programming oriented courses.
Syllabus Content:
Module 1: Overview of Programming:
Introduction to computer based problem solving, Program design and implementation issues-
Flowcharts & Algorithms, Top down design & stepwise refinement, Programming
environment – Machine language, assembly language, high level languages, Assemblers,
[Curriculum Design – 2015] Page 97
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Compilers, Interpreters
Module 2: Fundamentals of C programming:
Overview of C, Data Types, Constants & Variables, Operators & Expressions, Control
constructs-if then, for, while, Arrays- single & multidimensional arrays, Functions-
fundamentals – general form, function arguments, return value, Basic I/O-formatted and
Unformatted I/O, Advanced features- Type modifiers and storage class specifiers for data
types, Bit operators, ? operator, &operator, * operator, Type casting, type conversion.
Module 3: Advanced programming techniques:
Control constructs- Do while, Switch statement, break and continue, exit() function, go to and
label, Scope rules- Local & global variables, scope rules of functions, Functions-parameter
passing, call by value and call by reference, calling functions with arrays, argc and argv,
recursion- basic concepts, ex-towers of Hanoi
Module 4: Dynamic data structures in C:
Pointers- The & and * operator, pointer expression, assignments, arithmetic, comparison,
malloc vs calloc, arrays of pointers, pointers to pointers, initializing pointers, pointers to
functions, function retuning pointers, Structures- Basics, declaring, referencing structure
elements, array of structures, passing structures to functions, structure pointers, arrays and
structures within structures, Unions – Declaration, uses, enumerated data-types, typedef
Module 5: Additional features:
File Handling – The file pointer, file accessing functions, fopen, fclose, puc, getc, fprintf, C
Preprocessor- #define, #include, #undef, Conditional compilation directives, C standard
library and header files: Header files, string functions, mathematical functions, Date and
Time functions
Competencies of the course:
C1: Understand the features and characteristics of C language
C2: Discuss the basic elements of C, its features and characteristics, create algorithms and
[Curriculum Design – 2015] Page 98
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
flowcharts
C3: Understand the working of different control flow statements, looping structures, etc.
C4: Recognise the use of different data types, operators and expressions.
C5: Understand the features and uses of arrays
C6: Understand the syntax of functions
C7: Discuss about recursion, iteration and different ways to pass arguments
C8: Understand how to implement functions, unions and structures for different
programming assignments
C9: Understand pointers and function arguments
C10: Understand how to create files and manipulate them
Learning Resources
Programming in ANSI C by Balaguruswamy, 3rd Edition, 2005, Tata McGraw Hill
Let us C by Yashwant Kanetkar, 6th Edition, PBP Publication
The C programming Language by Richie and Kenninghan, 2004, BPB Publication
Question Paper - Blue Print
Programming in C
Blue Print - Question Paper
Module
* Part A Part B Part C Part D
1 1 2 1 0
2 1 2 2 1
3 1 2 1 1
4 2 2 2 1
5 1 2 2 1
[Curriculum Design – 2015] Page 99
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Model Question Paper
First Semster - CA1C03TB - PROGRAMMING IN C
Time : 3 Hrs. Total Marks: 80
PART A: (Answer all the questions. Each question carries 1 mark.)
1. _____________ and ________________ are two features of ‘C’ Language.
2. What are the data types in ‘C’ programming?
3. Write the syntax of switch statement.
4. What is a ‘*’ in pointer?
5. What is a ‘typedef’ in ‘C’ programming?
6. Define #include.
PART B: (Answer any 7 of the following questions. Each question carries 2 marks.)
7. What is an Algorithm?
8. Define ‘Compiler’ and ‘Interpreter’.
9. What is character set in C?
10. Explain the different types of arrays.
11. Write a program to print ‘Hello C Programming’.
12. What are local and global variables in ‘C’ programming?
13. Define structures in ‘C’ programming.
14. What do you mean by ‘Call by value’?
15. What are the preprocessors?
16. Define File pointer.
PART C: (Answer any 5 of the following questions. Each question carries 6 marks.)
17. Write a flowchart and algorithm to simulate a calculator.
18. Explain the Machine language and High-level language.
19. What are operators in ‘C’ programming? Explain.
20. State the differences between ‘while’ and ‘do while’ loop with example?
21. Write a ‘C’ function to find the largest number among three numbers.
22. Write down a program to use structure within union, and display the contents of structure
elements.
23. Mention instruction codes to print details of 50 students using structures in ‘C’ programming.
24. Write a ‘C’ program to read the content of file using ‘fgets’.
PART D: (Answer any 2 of the following questions. Each question carries 15 marks.)
25. Write a program to find transpose of a given square matrix.
26. Write down the algorithm and program to print ‘Fibonacci’ series using recursion.
27. What is DMA? Explain DMA with example.
28. Explain the string and mathematical functions in detail with examples.
[Curriculum Design – 2015] Page 100
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Course Code : CA1C04TB
Name of the Course: INTRODUCTION TO LINUX
Duration: One Semester
Semester : 1
Total Lecture Hours: 72
Aim of the course:
To enable the learners to have a hands on practical exposure to the Linux Red Hat Enterprise
and make them prepared for the RHCE Certification.
Course Overview and Context:
The Course provides an overview of the Linux Operating System, geared toward new users
as an exploration tour and getting started guide. This Module provides examples to help the
learners get a better understanding of the linux system. The Module also provides the
guidelines for the learners to take up vendor certifications.
The Module explores the basics of Linux, the underlying management of the Linux operating
system and its network configuration. The complete system services of Linux is explained
along with the troubleshooting.
Syllabus Content:
Module 1: Linux Introduction
Introduction to Multi user System, History of UNIX, Features & Benefits, Versions of UNIX,
Features of UNIX File System,, Commonly Used Commands like who, pwd, cd, mkdir, rm,
rmdir, ls, mv, ln, chmod, cp, grep, sed, awk ,tr, yacc etc. getting Started (Login/Logout) .
Creating and viewing files using cat, file comparisons, View files, disk related commands,
checking disk free spaces.
Exploring Linux Flavors
Introduction to various Linux flavors. , Debian and rpm packages, Vendors providing
DEBIAN & RPM distribution & Features. Ubuntu. History, Versions, Installation, Features,
[Curriculum Design – 2015] Page 101
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Ubuntu one. Fedora: History, Versions, Installation, Features.
Module-2: The File System
Inodes - Structure of a regular file – Directories - Conversion of a path name to an inode -
Super block - Inode assignment to a new file - Allocation of disk blocks. System calls for the
file System: Open – Read - Write - Lseek – Close - File creation - Creation of special files -
Changing directory and root - changing owner and mode – stat and fstat - pipes - Dup -
Mounting and Un mounting file systems - Link and Un link.
Module 3: Process Management
The Structure of Processes: Process States and Transitions - Layout of system memory -
Context of a process. Process Control: Process Creation – Signals – Process Termination –
Invoking other programs – PID & PPID – Shell on a Shell.
Module 4: VI editor
Vi Editor: Introduction to Text Processing, Command & edit Mode, Invoking vi, deleting &
inserting Line, Deleting & Replacing Character, Searching for Strings, Yanking, Running
Shell Command Macros, Set Window, Set Auto Indent, Set No. Communicating with Other
Users: who, mail, wall, send, mesg, ftp.
Module 5: System Administration
Common administrative tasks, identifying administrative files configuration and log files,
Role of system administrator, Managing user accounts-adding & deleting users, changing
permissions and ownerships, Creating and managing groups, modifying group attributes,
Temporary disabling of user’s accounts, creating and mounting file system, checking and
monitoring system performance - file security & Permissions, becoming super user using su.
Getting system information with uname, host name, disk partitions & sizes, users, kernel,
installing and removing packages with rpm command.
[Curriculum Design – 2015] Page 102
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Competencies of the course:
C1. Gathering awareness of the history of UNIX
C2. Familiarize with different flavor of Linux
C3. Understand the File System
C4. Learn the VI editor
C5. Gathering knowledge about System Administration
Learning Resources
The Design of Unix Operating System, Maurice J. Bach, Pearson Education, 2010
Advance UNIX, a Programmer’s Guide, S. Prata, BPB Publications, and New Delhi,
2011
Unix Concepts and Applications, Sumitabh Das, 2010
The UNIX Programming Environment, B.W. Kernighan & R. Pike, Prentice Hall of
India. 2009
Guide to UNIX Using LINUX, Jack Dent Tony Gaddis, Vikas/ Thomson Pub. House
Pvt. Ltd. 2010
Question Paper – Blue Print
Introduction to Linux
Blue Print - Question Paper
Module
* Part A Part B Part C Part D
1 1 2 2 1
2 2 2 2 1
3 1 2 1 1
4 1 2 1 0
5 1 2 2 1
[Curriculum Design – 2015] Page 103
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Model Question Paper
First Semester
CA1C04TB - INTRODUCTION TO LINUX
Time: 3 Hrs. Total Marks: 80
PART A: (Answer all the questions. Each question carries 1 mark.)
1. ______________ is the command to create a file in Linux.
2. List out four flavors of Linux.
3. What is Lseek?
4. Define a Process.
5. List out two modes of vi editor.
6. _______________ is the syntax of a command to install a package using rpm.
PART B: (Answer any 7 of the following questions. Each question carries 2 marks.)
7. Define 'grep' command.
8. Explain 'chmod' command.
9. What is 'inode'?
10. Define link and unlink.
11. Explain PID and PPID.
12. What is pipe?
13. Write the syntax of search and replace command in vi editor.
14. Write the syntax of "wall" and "who" command.
15. Define kernel.
16. List out four roles of system administration.
PART C: (Answer any 5 of the following questions. Each question carries 6 marks.)
17. Explain any five system calls in Linux.
18. Describe the concept of hard link and soft link.
19. Explain the structure of file system in Linux.
20. Explain mounting and unmounting process in detail.
21. Write short notes on daemon process and background process.
22. Explain about yanking.
23. Write down the parameters of uname.
24. Explain the rpm package and its management process.
PART D: (Answer any 2 of the following questions. Each question carries 15 marks.)
25. Discuss various distributions of Linux.
26. Explain the /(root) file system with a neat diagram.
27. Describe process states and transitions with the help of a diagram.
28. Discuss the concept of managing groups and modifying group attributes.
[Curriculum Design – 2015] Page 104
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Course Code : CA1C01PB
Name of the Course: PROGRAMMING IN C - LAB
Duration: One Semester
Semester : 1
Total Lecture Hours: 36
Aim of the course:
To provide learners skills to implement the different principles of programming with the
language C.
Course Overview and Context:
C is popular because, it is easy to learn, produces efficient programs, can handle low-level
activities, and can be compiled on a variety of platforms.
This course focuses on all the basic concepts, syntax and constructs of the C language. For
learners, who are new to programming, this course can be considered as the starting point
before taking up any other programming oriented courses. The learner will be implementing
the concepts explained here to create simple to complex programs.
Syllabus Content:
List of Programs
1 Printing the reverse of an integer.
2 Printing the odd and even series of N numbers.
3 Get a string and convert the lowercase to uppercase and vice--versa using getchar() and
putchar().
4 Input a string and find the number of each of the vowels appear in the string.
5 Accept N words and make it as a sentence by inserting blank spaces and a full stop at the
end.
6 Printing the reverse of a string.
7 Searching an element in an array using pointers.
8 Checking whether the given matrix is an identity matrix or not.
[Curriculum Design – 2015] Page 105
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
9 Finding the first N terms of Fibonacci series.
10 Declare 3 pointer variables to store a character, a character string and an integer
respectively. Input values into these variables. Display the address and the contents of
each variable.
11 Define a structure with three members and display the same.
12 Declare a union with three members of type integer, char, string and illustrate the use of
union.
13 Recursive program to find the factorial of an integer.
14 Finding the maximum of 4 numbers by defining a macro for the maximum of two
numbers.
15 Arranging N numbers in ascending and in descending order using bubble sort.
16 Addition and subtraction of two matrices.
17 Multiplication of two matrices.
18 Converting a hexadecimal number into its binary equivalent.
19 Check whether the given string is a palindrome or not.
20 Demonstration of bitwise operations.
21 Applying binary search to a set of N numbers by using a function.
22 Create a sequential file with three fields: empno, empname, empbasic. Print all the details
in a neat format by adding 500 to their basic salar
Competencies of the course:
C1: Implement the different concepts to develop simple to complex programs using C
language
Learning Resources
Programming in ANSI C by Balaguruswamy, 3rd Edition, 2005, Tata McGraw Hill
Let us C by Yashwant Kanetkar, 6th Edition, PBP Publication
The C programming Language by Richie and Kenninghan, 2004, BPB Publication
Evaluation: Sample Problems
Two samples of questions with model answers to them are given below:
[Curriculum Design – 2015] Page 106
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
T11: Write a program to print the prime numbers from 1 to n.
Ans:
Problem description:
A number which is only divisible by one and itself is called a prime number.
E.g.: 2, 3, 5, 7
Variables description:
n Is the number input by the user which tells us the range upto which the prime numbers must
be printed.
i, j Are numbers which are used as counters in the loop
Algorithm:
Step 1: Start
Step 2: Read the number n
Step 3: Initialize the counter variable i=1
Step 4: If i<=n go to step 5 ELSE go to step 10
Step 5: Initialize j=1
Step 6: If j<=1 follow the steps below ELSE go to step 7
i) If i%j==0 increment c by 1
ii) Increment j by 1
iii) Go to Step 6
Step 7: if c== 2 then print the value of i
[Curriculum Design – 2015] Page 107
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Step 8: Increment value of i by 1
Step 9: Go to step 4
Step 10: Stop
Program:
#include<stdio.h>
#include<conio.h>
void main() {
int n,i,fact,j;
clrscr();
printf("enter the number:");
scanf("%d",&n);
for(i=1;i<=n;i++) {
fact=0;
//this loop will check a no to be prime or not.
for(j=1;j<=i;j++) {
if(i%j==0)
fact++;
if(fact==2)
printf("\n %d",i);
[Curriculum Design – 2015] Page 108
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
getch( );
Output:
Enter the number : 5
235
Enter the number : 10
2357
Enter the number : 12
2 3 5 7 11
T12: Write a program to add two numbers
Ans: #include<stdio.h>
int main()
int a, b, c;
printf("Enter two numbers to add\n");
scanf("%d%d",&a,&b);
c = a + b;
printf("Sum of entered numbers = %d\n",c);
return 0;
[Curriculum Design – 2015] Page 109
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Course Code : CA1C02PB
Name of the Course: LINUX - LAB
Duration: One Semester
Semester : 1
Total Lecture Hours: 36
Aim of the course:
To familiarize the students with the Linux Operating System
Course Overview and Context:
This course covers the Linux operating system from a user perspective
Syllabus Content:
1. Execute 25 basic commands of UNIX.
2. Basics of functionality and modes of VI Editor.
3. WAP that accepts user name and reports if user is logged in.
4. WAP which displays the following menu and executes the option selected by user:
1. ls 2. Pwd 3. ls –l 4. ps –fe
5. WAP to print 10 9 8 7 6 5 4 3 2 1 .
6. WAP that replaces all “*.txt” file names with “*.txt.old” in the current.
7. WAP that echoes itself to stdout, but backwards.
8. WAP that takes a filename as input and checks if it is executable, if not make it executable.
9. WAP to take string as command line argument and reverse it.
10. 1. Create a data file called employee in the format given below:
a. EmpCode Character
[Curriculum Design – 2015] Page 110
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
b. EmpName Character
c. Grade Character
d. Years of experience Numeric
e. Basic Pay Numeric
$vi employee
A001 ARJUN E1 01 12000.00
A006 Anand E1 01 12450.00
A010 Rajesh E2 03 14500.00
A002 Mohan E2 02 13000.00
A005 John E2 01 14500.00
A009 Denial SmithE2 04 17500.00
A004 Williams E1 01 12000.00
Perform the following functions on the file:
a. Sort the file on EmpCode.
b. Sort the file on
(i) Decreasing order of basic pay
(ii) Increasing order of years of experience.
c. Display the number of employees whose details are included in the file.
d. Display all records with ‘smith’ a part of employee name.
[Curriculum Design – 2015] Page 111
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
e. Display all records with EmpName starting with ‘B’.
f. Display the records on Employees whose grade is E2 and have work experience of 2 to 5
years.
g. Store in ‘file 1’ the names of all employees whose basic pay is between 10000 and 15000.
h. Display records of all employees who are not in grade E2.
Competencies of the course:
C1. Familiarized with the basic commands
C2. Learn about the “VI” Editor
C3. Creating data file and work with the same
C4. Gain knowledge and WAP
Learning Resources
The Design of Unix Operating System, Maurice J. Bach, Pearson Education, 2010
Advance UNIX, a Programmer’s Guide, S. Prata, BPB Publications, and New Delhi,
2011
Unix Concepts and Applications, Sumitabh Das, 2010
The UNIX Programming Environment, B.W. Kernighan & R. Pike, Prentice Hall of
India. 2009
Guide to UNIX Using LINUX, Jack Dent Tony Gaddis, Vikas/ Thomson Pub. House Pvt.
Ltd. 2010
Evaluation: Sample Problems
Two samples of questions with model answers to them are given below:
TI1: Name 5 basic Linux commands
Ans.
1. Ls
2. Ps
[Curriculum Design – 2015] Page 112
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
3. Date
4. Cat
5. man
TI2: Name 5 vi editor commands
Ans.
h move left (backspace)
j move down
k move up
l move right (spacebar)
[return] move to the beginning of the next line
[Curriculum Design – 2015] Page 113
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Course Code : CA2C05TB
Name of the Course: Mathematics – Matrices, Calculas and Lapilas transformers
Semester : 2
Duration : One Semester
MATRICES , CALCULUS AND LAPLACE TRANSFORMS (BCA 102)
Aim
The aim of this course is to provide an in-depth understanding of operations on matrices, limits,
differential equations and associated concepts.
Course Overview and Context :
This course promotes the methods and benefits of mathematical thoughts and logical
understandings. So as to use the concepts in computer applications
This course mainly focuses on study of first order differential equation , partial differential
equation, Laplace transforms , limit of functions, matrices etc. The learners will obtain problem
solving skills and logical perspectives through this course
Syllabus Content
MODULE I :
Matrices (17 hrs) A quick review of the fundamental concepts, Rank of a Matrix, Non-Singular and
Singular matrices, Elementary Transformations, Inverse of a Non-Singular Matrix, Canonical form,
Normal form. Systems of Linear equations: Homogeneous and Non Homogeneous Equations,
Characteristic equation of a matrix. (Relevant sections of Text 1). (proof of all the theorems are to be
excluded.)
MODULE I I :
Differential Calculus: (20hrs) A quick review of limits of function, rules for finding limits, extensions of
limit concepts, derivative of a function, differentiation rules, chain rule, rate of change and simple
applications of the rules. Extreme values of a function Rolle’s Theorem, Mean Value Theorem. (Sections
1.1, 1.2, 1.3, 2.1, 2.2, 2.3 , 3.1, 3.2 of Text 2)
[Curriculum Design – 2015] Page 114
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
MODULE III :
Partial Differential Equations (15 hrs) Introduction, formulation of Partial Differential Equation by
elimination of arbitrary constants and by elimination of arbitrary function. Solution of first order
equations using Lagrange’s method. (relevant sections of Text 3)
MODULE IV :
Laplace Transforms (20 hrs) 125 Definitions- transforms of elementary functions, properties of Laplace
transforms, inverse transforms- convolution theorem (no proof). (relevant sections of Text
Competencies of the course:
C1 : Familiarize with different operations on matrices
C2 : Understand the limits of functions.
C3 : Understand differential equation and partial differential equation
C4 :Familiarize with Laplace transforms
Learning Resources :
S.K . Stein – Calculus and analytic Geometry , (McGraw Hill )
. Zubair Khan, Shadab Ahmad Khan - Mathematics – 1 and Mathematics – II ( Ane Books )
Shanti Narayan - Matrices (S. Chand & Company)
N.P.Bali, Dr.N.Ch.Narayana Iyengar-Engineering mathematics – L
Matrices, Frank Ayres JR Schaum's Outline Series, TMH Edition
Thomas and Finney - Calculus and analytical geometry (Addison-Wesley )
Dr. B. S. Grewal – Higher Engineering Mathematics
[Curriculum Design – 2015] Page 115
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Question Paper Blue Print
Blue Print - Question Paper
Module
* Part A Part B Part C Part D
1 2 2 2 1
2 2 3 2 1
3 1 3 2 1
4 1 2 2 0
[Curriculum Design – 2015] Page 116
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Course Code : CA2C06TB
Name of the Course: OPERATING SYSTEM
Duration: One Semester
Semester : 2
Total Lecture Hours: 72
Aim of the course:
The aim of this course is to develop learners’ understanding in the fundamentals of operating
system and its working.
Course Overview and Context:
An operating system (OS) is a collection of software that manages computer hardware
resources. They will be providing common services for computer programs. The operating
system is the vital component of the system software in a computer system. it is the
intermediary between users and computer hardware. It controls the allocation of resources
and services like memory, processor, device, data, etc. Operating systems are now available
not only for computers and laptops, but also for small handheld devices like Smart phones,
tablets, etc. Operating system examples are – Windows XP, 7, 8, server; LINUX, UNIX,
Android, iOS, etc.
This course focuses on the basic concepts of operating system, the internal working, etc. This
course deals with memory management, disk management, file systems, deadlock avoidance
and prevention, etc.
Syllabus Content:
Module 1 – Introduction to Operating System
Introduction, Objectives and Functions of OS, Evolution of OS, OS Structures, OS
Components, OS Services, System calls, System programs, Virtual Machines.
Module 2 – Process Management
Processes: Process concept, Process scheduling, Co-operating processes, Operations on
[Curriculum Design – 2015] Page 117
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
processes, Inter process communication, Communication in client-server systems.
Threads: Introduction to Threads, Single and Multi-threaded processes and its benefits, User
and Kernel threads, Multithreading models, Threading issues.
CPU Scheduling: Basic concepts, Scheduling criteria, Scheduling Algorithms, Multiple
Processor Scheduling, Real-time Scheduling, Algorithm Evaluation, Process Scheduling
Models.
Process Synchronization: Mutual Exclusion, Critical – section problem, Synchronization
hardware, Semaphores, Classic problems of synchronization, Critical Regions, Monitors, OS
Synchronization, Atomic Transactions
Deadlocks: System Model, Deadlock characterization, Methods for handling Deadlocks,
Deadlock prevention, Deadlock Avoidance, Deadlock Detection, Recovery from Deadlock.
Module 3: Storage Management
Memory Management: Logical and physical Address Space, Swapping, Contiguous Memory
Allocation, Paging, Segmentation with Paging.
Virtual Management: Demand paging, Process creation, Page Replacement Algorithms,
Allocation of Frames, Thrashing, Operating System Examples, Page size and other
considerations, Demand segmentation
File-System Interface: File concept, Access Methods, Directory structure, File- system
Mounting, File sharing, Protection and consistency semantics
File-System Implementation: File-System structure, File-System Implementations, Directory
Implementation, Allocation Methods, Free-space Management, Efficiency and Performance,
Recovery
Disk Management: Disk Structure, Disk Scheduling, Disk Management, Swap-Space
Management, Disk Attachment, stable-storage Implementation
[Curriculum Design – 2015] Page 118
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Module 4: Protection and Security
Protection: Goals of Protection, Domain of Protection, Access Matrix, Implementation of
Acess Matrix, Revocation of Access Rights, Capability- Based Systems, Language – Based
Protection
Security: Security Problem, User Authentication, One – Time Password, Program Threats,
System Threats, Cryptography, Computer – Security Classifications.
Competencies of the course:
C1: Understand processes and inter-process communication
C2: Elucidate CPU scheduling methods and analyze the working of semaphores, monitors
and message passing
C3: Discuss about multiprogramming
C4: Evaluate memory management with bit maps and linked lists
C5: Interpret paging technology and different page replacement algorithms
C6: Discuss directories and principles of I/O hardware
C7: Understand disk scheduling and I/O buffering
C8: Analyze deadlocks and recognize how to avoid/prevent them
C9: Understand different protection mechanisms available for use
C10: Recognize and discuss the different security problems that can be encountered.
Learning Resources
Tanenbaum, Operation System Concepts, 2nd Edition, Pearson Education.
Silberschatz / Galvin / Gagne, Operating System,6th Edition,WSE (WILEY Publication)
Andrew S. Tanenbaum, “Modern Operating Systems”, Prentice Hall
Garry Nutt, “Operating Systems – A Modern perspective ”, Third Edition, Pearson
Education
Bach, M.J., “Design of UNIX Operating System”, Prentice Hall
Charles Crowley, “Operating systems – A Design Oriented Approach”, Tata McGrawhill,
[Curriculum Design – 2015] Page 119
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
1997
Michel Palmer “Guide o Operating Systems”, Vikas Thomson Learning Publishing,
NewDelhi
Milan Milonkovic, Operating System Concepts and design, II Edition, McGraw Hill
1992.
William Stallings, Operating System, 4th Edition, Pearson Education.
H.M.Deitel, Operating systems, 2nd Edition ,Pearson Education
Nutt: Operating Systems, 3/e Pearson Education 2004
D.M.Dhamdhere, “Operating Systems”, 2nd Edition, Tata McGraw-Hill
Question Paper – Blue Print
Operating System
Blue Print - Question Paper
Module
* Part A Part B Part C Part D
1 1 2 2 1
2 2 3 2 1
3 2 3 2 1
4 1 2 2 1
[Curriculum Design – 2015] Page 120
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Model Question Paper
Second Semester - CA2C06TB - OPERATING SYSTEM
Time : 3Hrs. Total Marks: 80
PART A: (Answer all the questions. Each question carries 1 mark.)
29. __________ and ________________ are two system services of operating system.
30. Define processes and threads.
31. Define turnaround time and waiting time.
32. What is swapping?
33. What do you understand by virtual memory?
34. What are program threats?
PART B: (Answer any 7 of the following questions. Each question carries 2 marks.)
1. What are system calls? Give two examples.
2. List out four system components.
3. What are short term schedulers?
4. What are semaphores?
5. Give the name of four necessary conditions for deadlocks.
6. Explain logical and physical address space?
7. Define paging.
8. Write down four attributes of a file.
9. Define contiguous allocation.
10. What is language-based system?
PART C: (Answer any 5 of the following questions. Each question carries 6 marks.)
29. Discuss the operating system structure.
30. What are virtual machines? Explain with example.
31. With the help of an example, explain Round Robin algorithm for CPU scheduling.
32. Explain Banker's algorithm with suitable example.
33. Describe Demand Paging with a neat diagram.
34. Compare Scan scheduling and C-Scan scheduling algorithm for disk scheduling.
35. Discuss the principles of Protection.
36. Explain Domain Structure with the help of suitable examples.
PART D: (Answer any 2 of the following questions. Each question carries 15 marks.)
29. Discuss evolution of operating system.
30. Explain Page Replacement algorithm with example.
31. What is a deadlock? Explain the methods that can be used for deadlock detection and recovery.
32. Discuss strengths&weakness of implementing the access matrix associated with domains.
[Curriculum Design – 2015] Page 121
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Course Code : CA2C07TB
Name of the Course: OOPS WITH C++
Duration: One Semester
Semester : 2
Total Lecture Hours: 72
Aim of the course:
The aim of this course is to introduce object oriented programming using the programming
language - C++.
Course Overview and Context:
C++ is an object oriented, middle-level programming language. It runs on a variety of
operating systems. C++ is an extension of C with a major addition of the class construct
feature. C++ is a versatile language for handling very large programs; it is suitable for
virtually any programming task including development of editors, compilers, databases,
communication systems and any complex real life applications systems.
This course focuses on providing an introduction to object oriented programming concepts,
C++ syntax, classes, functions, operators, errors and exceptions, file manipulation etc.
Syllabus Content:
Module 1: Introduction
Evolution of programming methodologies-Procedure oriented versus Object Oriented
Programming-characteristics of OOP, Basics of OOP, Merits and Demerits of OOP.
Data Types: Different data types, operators and expressions in C++, Keywords in C++.
Input and Output: Comparison of stido.h and iostream.h, cin and cout.
Decision and loop:
Conditional statement - if-else statement, nested if-else statement, switch, break, continue,
[Curriculum Design – 2015] Page 122
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
and goto statements, Looping statements- for loop, while loop, Do-while loop.
Arrays, String and Structures : fundamentals-Single dimensional, multi-dimensional
arrays, fundamentals of strings, different methods to accept strings, different string
manipulations, array of strings, Basics of structures-declaring and defining structure-
Accessing structure members, array of structures, Unions difference between structures and
Unions, Enumerated data types-declaration and their usage.
Module 2:
Class: Definition-defining the class, defining data members and member functions, Access
specifier-private, public, protected, objects as function arguments, returning objects from the
function, scope resolution operator, member function defined outside the class, difference
between class and structure, array as class member data, Array of objects.
Functions in C++ :
Function definition, function declaration, Built-in functions, user defined functions, calling
the function, passing parameter-actual and formal, different methods of calling the function
call by value, call by reference using reference as parameter and pointer as parameter,
overload function-different types of arguments-different number of arguments, inline
function, default argument, storage classes-automatic, external, static, register.
Constructor and Destructor: Constructors-constructor with argument, constructor without
arguments, constructor with default arguments, Dynamic constructor, constructor
overloading, copy constructor, destructors, Manipulating private data members.
Module 3:
Operator overloading:
Defining operator overloading, overloading unary operator, overloading binary operator,
manipulation of string using overloaded operator, rules for overloading operator. Data
conversion: conversion between Basic types, conversion between objects & Basic types,
[Curriculum Design – 2015] Page 123
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
conversion between objects of different classes.
Inheritance:
Base Class & derived class, defining derived classes, protected access specifier, public
inheritance and private inheritance-member accessibility, constructors and destructors in
derived classes, Level of inheritance-single inheritance, multiple inheritance, multi-level
inheritance, hierarchical inheritance, hybrid inheritance.
Module 4:
Pointer:
Pointer declaration and Access, Pointer to void, pointer and arrays, pointer constant and
pointer variable, pointer and functions, pointer, call by pointer arrays, array of pointers to
string, printer sort, memory management-new and delete, pointer to object-referencing
members using pointers, self containing class, this pointer, returning values using this pointer
Virtual function:
Normal member functions accessed with pointers, virtual member function access, late
binding, pure virtual function, abstract class, virtual base class
Friend functions and static function:
Purpose, defining friend functions, friend classes, static function, accessing static function
numbering positive objects.
Module 5:
Templates and Exception Handling: Introduction to templates, class templates, function
templates, Member function templates, Template arguments, Exception handling.
Console IO Operator :
C++ stream and C++ stream classes, unformatted I/O operators, formatted I/O operators-
[Curriculum Design – 2015] Page 124
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
manipulators-user defined manipulators.
Files : Class for file stream operators, opening and closing a file, file nodes, writing an
object to disk, reading an object from disk, binary versus character files, I/O with multiple
object, stream class, file pointer-specifying the position, specifying the object, tellg()
function, seekg() function. Command line arguments.
Competencies of the course:
C1: Understand the object oriented programming concepts
C2: Recognize the features and characteristics of the C++ programming language
C3: Understand the concept of classes, functions, variables and operators
C4: Discuss the functions and importance of constructors and destructors
C5: Understand how to implement operator overloading
C6: Recognise the different types of inheritance and polymorphism and understand how to
implement them.
C7: Understand the functions of pointers
C8: Discuss the different types of exceptions and errors that can occur in a C++ program and
understand how to handle them.
C9: Understand the use and purpose of virtual function, friend function, static function, etc.
C10: Understand how to implement files and manipulate them
Learning Resources
E. Balaguruswamy: Object Oriented Programming with C++, Tata McGraw Hill.
Publications
Let us C++ by Yeshwanth Kanetkar
Strousstrup: The C++ Programming Language, Pearson Edition, 3rd Edition
Lafore Robert: Object Oriented Programming in Turbo C++, Galgotia Publications
Lippman: C++ Primer, 3/e Pearson Education
C++ completer reference by Herbert Schildt, Tata McGraw Hill Publications.
[Curriculum Design – 2015] Page 125
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Question Paper – Blue Print
OOPs with C++
Blue Print - Question Paper
Module
* Part A Part B Part C Part D
1 1 2 1 0
2 1 2 2 1
3 2 2 2 1
4 1 2 1 1
5 1 2 2 1
Model Question Paper
Second Semester Examination
CA2C07TB - OOPS with C++
Time 3 Hrs Total Marks: 80
PART A: (Answer all the questions. Each question carries 1 mark.)
35. _______________ is the library which is responsible for I/O function in C++.
36. What is the name of “: :” ?
37. What do you call when one class is adopting the other class’s operations?
38. What does a pointer variable hold?
39. What is a file pointer?
40. What is an instance of class?
PART B: (Answer any 7 of the following questions. Each question carries 2 marks.)
41. Define data types in C++.
42. Name any two differences between union and structure.
43. Define private access specifier.
44. Explain constructor.
45. Define operator overloading.
46. What is a pointer array?
47. What do you mean by a function?
48. Define class templates.
49. Define formatted I/O.
50. Explain command line arguments.
[Curriculum Design – 2015] Page 126
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
PART C: (Answer any 5 of the following questions. Each question carries 6 marks.)
51. What are the different looping constructs in C++. Give examples.
52. Explain about default and parameterized constructor with example.
53. Define copy constructor and explain constructor overloading.
54. Explain the different types of data conversions.
55. Explain in detail about different levels of inheritance.
56. Write a short note on virtual function.
57. Explain friend function with an example.
58. Write a short note on exception handling in C++.
PART D: (Answer any 2 of the following questions. Each question carries 15 marks.)
59. Write a note on the following:
a. Built-in function
b. User-defined function
c. Different methods of calling a function
60. Discuss the following with example:
d. Unary operator overloading
e. Binary operator overloading
61. Explain the following with example:
f. Call by pointer array
g. Array of pointer
62. Write a C++ program to demonstrate file I/O operations.
*******************************
[Curriculum Design – 2015] Page 127
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Subject Code : CA2C08TB
Name of the Course: DATA STRUCTURES USING C
Duration: One Semester
Semester : 2
Total Lecture Hours: 72
Aim of the course:
The aim of this course is to make the learners understand the different structures that can be
used to store data in the memory, how to manipulate the storage of data, how to sort and
search for a data, etc.
Course Overview and Context:
Data is needed by the computer to perform different operations. These operations can be
logical or arithmetic. Data can be numbers, alphabets, symbols, etc. When the quantity of
data increases, then storing them becomes the biggest concern for every system. A program
or an operation will work efficiently if the data is easily accessible and stored safely. This is
where you use data structures. Data structures helps in storing data in a well-organized
manner in the memory. You will be able to perform a series of operations like storing,
retrieving, sorting, searching, etc on a data structure.
This course covers the basics of data structure and dynamic memory allocation. It deals with
operations like sorting, searching, retrieving, etc. Operations on data structures like stacks,
queues, linked lists, trees, arrays, and graphs are covered here.
Syllabus Content:
Module 1: Introduction to Data structures
Definition, Classification of data structures: primitive and non primitive, Elementary data
organization, Time and space complexity of an algorithm (Examples), String processing.
Definition of dynamic memory allocation, Accessing the address of a variable, Declaring and
initializing pointers, Accessing a variable through its pointer, Meaning of static and dynamic
memory allocation, Memory allocation functions: malloc(), calloc(), free() and realloc().
[Curriculum Design – 2015] Page 128
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Recursion in C (advantages), Writing Recursive programs – Binomial coefficient, Fibonacci,
GCD.
Module 2: Searching and sorting
Basic Search Techniques: Sequential search: Iterative and Recursive methods, Binary
search: Iterative and Recursive methods, Comparison between sequential and binary search.
Sort: General background and definition, Bubble sort, Selection sort, Insertion sort, Merge
sort, Quick sort
Module 3: Stack and Queue
Stack – Definition, Array representation of stack, Operations on stack: Infix, prefix and
postfix notations, Conversion of an arithmetic expression from Infix to postfix, Applications
of stacks. Queue - Definition, Array representation of queue, Types of queue: Simple queue,
Circular queue, Double ended queue (deque) , Priority queue , Operations on all types of
Queues
Module 4: Linked List
Definition, Components of linked list, Representation of linked list, Advantages and
Disadvantages of linked list. Types of linked list: Singly linked list, doubly linked list,
Circular linked list, Operations on singly linked list: creation, insertion, deletion, search and
display.
Module 5: Tree Graphs and their Applications:
Definition : Tree, Binary tree, Complete binary tree, Binary search tree, Heap Tree
terminology: Root, Node, Degree of a node and tree, Terminal nodes, Non-terminal nodes,
Siblings, Level, Edge, Path, depth, Parent node, ancestors of a node. Binary tree: Array
representation of tree, Creation of binary tree. Traversal of Binary Tree: Preorder, Inorder and
postorder. Graphs, Application of Graphs, Depth First search, Breadth First search.
[Curriculum Design – 2015] Page 129
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Competencies of the course:
C1: Understand the basic data structures and their classifications
C2: Analyze how to allocate memory dynamically
C3: Understand the advantages of recursive functions
C4: Understand and compare different searching techniques
C5: Understand and compare different sorting algorithms
C6: Identify the uses of stack data structure and understand their implementation
C7: Identify the uses of queue data structure and understand their implementation
C8: Compare the different types of linked lists and understand the operations that can be
performed on a linked list
C9: Understand the different operations that can be conducted on a tree data structure.
C10: Understand how to implement the graph data structure.
Learning Resources
Tanenbaum, Data Structures Using C. Pearson Education, 200
Lipschutz: Schaum’s outline series Data structures Tata McGraw-Hill
Kamthane: Introduction to Data Structures in C. Pearson Education 2005.
Weiss, Data Structures and Algorithm Analysis in C, II Edition, Pearson Education,
2001
Robert Kruse Data Structures and program designing using ‘C’
Trembley and Sorenson Data Structures
E. Balaguruswamy Programming in ANSI C.
Bandyopadhyay, Data Structures Using C Pearson Education, 1999
Hanumanthappa M., Practical approach to Data Structures, Laxmi Publications, Fire
Wall media 2006
Langsam, Ausenstein Maoshe & M. Tanenbaum Aaron Data Structures using C and
C++ Pearson Education
[Curriculum Design – 2015] Page 130
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Question Paper – Blue Print
Data Structures using C
Blue Print - Question Paper
Module * Part A Part B Part C Part D
1 1 2 2 1
2 1 2 2 1
3 1 2 1 1
4 1 2 1 1
5 2 2 2 1
Model Question Paper
Second Semester
CA2C08TB - DATA STRUCTURES USING C
Time 3 Hrs. Total Marks: 80
PART A: (Answer all the questions. Each question carries 1 mark.)
1. ______________ is a non-primitive data type.
2. ________________ is a dynamic memory allocation function.
3. Process of calling function again and again by itself is known as ________________
4. Process of finding any one element in a list is called ________________
5. Name any one sorting technique.
6. Write a prefix expression.
PART B: (Answer any 7 of the following questions. Each question carries 2 marks.)
7. Define primitive data types with example.
8. Define time and space complexity
9. What is the use of free () function?
10. Explain the use of realloc() function?
11. Define binomial coefficient.
12. Write a recursive function for Fibonacci series
13. Define iterative search.
14. Define recursive search.
15. What do you mean by the term sorting?
16. Define stack.
PART C: (Answer any 5 of the following questions. Each question carries 6 marks.)
17. Write a short note on dynamic memory allocation and its functions.
18. Explain the disadvantage of static memory allocation. Mention the steps for accessing a variable
through its pointer.
[Curriculum Design – 2015] Page 131
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
19. Explain the advantages and disadvantages of recursion. Write an algorithm for finding the GCD
of a number using recursion.
20. Explain binary search using an example.
21. Explain insertion sort using an example.
22. Write a short note on infix, prefix and postfix notations.
23. Explain queue and its operation with examples.
24. Give a note on tree data structure. Explain binary tree.
PART D: (Answer any 2 of the following questions. Each question carries 15 marks.)
25. What is a stack? Explain the different operations that can be done on a stack with example.
26. Explain the different operations on a queue. Write the algorithm for each operation.
27. Discuss linked list and types of linked list. Explain the advantage and disadvantages of them.
28. Explain binary search tree. Write the algorithm for searching for an element in the binary search
tree.
*******************************
[Curriculum Design – 2015] Page 132
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Subject Code : CA2C03PB
Name of the Course: OOPS WITH C++ - LAB
Duration: One Semester
Semester 2
Total Lecture Hours: 36
Aim of the course:
The aim of this course is to introduce object oriented programming using the programming
language - C++ and implement these concepts to develop simple to complex programs.
Course Overview and Context:
C++ is an object oriented, middle-level programming language. It runs on a variety of
operating systems. C++ is an extension of C with a major addition of the class construct
feature. C++ is a versatile language for handling very large programs; it is suitable for
virtually any programming task including development of editors, compilers, databases,
communication systems and any complex real life applications systems.
This course focuses on providing an introduction to object oriented programming concepts,
C++ syntax, classes, functions, operators, errors and exceptions, file manipulation etc.
Syllabus Content:
List of Programs
1. Number of vowels and number of characters in a string.
2. Write a function called zeros maller () that is passed with two introduce arguments by
reference and set the smaller of the number to zero. Write a man() program to access this
function.
3. Demonstration of array of object.
4. Using this pointer to return a value ( return by reference).
5. Pointer sort.
6. Demonstration of virtual function.
7. Demonstration of static function.
[Curriculum Design – 2015] Page 133
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
8. Accessing a particular record in a student's file.
9. Using different methods to write programs to implement function overloading with default
arguments for the following problems :
a) To find whether a given number is prime.
b) To find the factorial of a number
10. Write a program to create a database for a bank account contains Name, Account no,
Account type, Balance, Including the following a) Constructors b) destructors call)
default constructors d) input and output function ; input and output for people using
different methods.
11. Create a class to hold information of a husband and another for the wife. Using friend
functions give the total salary of the family.
12. Write a program to overload the following operators (any 3)
a) Binary operator '+' to concatenate 2 strings
b) Relational operator '<' to find whether one data is less than the other
c) Unary operator '++' to find the next date of a given date.
13. Create a base class for a stack and implement push and pop operation. Include a derived
class to check for stack criteria such as a) stack empty b)stack full c) stack overflow d)
stack underflow.
14. Create a database using concepts of files for a student including the following fields :
Student- name, Student's Reg No, Student's Attendance (overall % of attendance); and
enter data for students and output the same in proper format.
15. Using operator overloading concept implement arithmetic manipulation on two complex
[Curriculum Design – 2015] Page 134
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
numbers.
Competencies of the course:
C1: Implement the different concepts in C++ to create simple to complex programs
Evaluation: Sample Problems
Two samples of questions with model answers to them are given below:
T11: Write a program to add two numbers
Ans:
#include <iostream>
using namespace std;
int main()
int a, b, c;
cout << "Enter two numbers to add\n";
cin >> a >> b;
c = a + b;
cout <<"Sum of entered numbers = " << c << endl;
return 0;
T12: Write a program to print 10 numbers
[Curriculum Design – 2015] Page 135
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Ans:
#include<iostream.h>
#include<conio.h>
void main()
{
clrscr();
int i,j,count=1,b=0;
cout<<"First Ten Prime Numbers are\n\n"<<"2";
for(i=3;i>0;++i)
{
for(j=2;j<=i;++j)
{
if(i%j==0)
b=1;
break;
}
if(b==0)
{
cout<<"\n"<<i;
count++;
}
b=0;
if(count==10)
break;
}
getch();
}
[Curriculum Design – 2015] Page 136
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Subject Code : CA2C04PB
Name of the Course: DATA STRUCTURES USING C - LAB
Duration: One Semester
Semester 2
Total Lecture Hours: 36
Aim of the course:
The aim of this course is to make the learners implement the different structures that can be
used to store data in the memory, how to manipulate the storage of data, how to sort and
search for a data, etc.
Course Overview and Context:
Data is needed by the computer to perform different operations. These operations can be
logical or arithmetic. Data can be numbers, alphabets, symbols, etc. When the quantity of
data increases, then storing them becomes the biggest concern for every system. A program
or an operation will work efficiently if the data is easily accessible and stored safely. This is
where you use data structures. Data structures helps in storing data in a well-organized
manner in the memory. You will be able to perform a series of operations like storing,
retrieving, sorting, searching, etc on a data structure.
This course covers the implementation of data structure and dynamic memory allocation
using C language.
Syllabus Content:
List of Programs
1. Use a recursive function to find GCD of two numbers.
2. Use a recursive function to find the Fibonacci series.
3. Use pointers to find the length of a string and to concatenate two strings.
4. Use pointers to copy a string and to extract a substring from a given a string.
5. Use a recursive function for the towers of Hanoi with three discs.
[Curriculum Design – 2015] Page 137
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
6. Insert an integer into a given position in an array.
7. Deleting an integer from an array.
8. Write a program to create a linked list and to display it.
9. Write a program to sort N numbers using insertion sort.
10. Write a program to sort N numbers using selection sort.
1. Inserting a node into a singly linked list.
2. Deleting a node from a singly linked list.
3. Pointer implementation of stacks.
4. Pointer implementation of queues.
5. Creating a binary search tree and traversing it using in order, preorder and post order.
6. Sort N numbers using merge sort.
Competencies of the course:
C1: Implement data structures, dynamic allocation, sorting, searching, etc using C language
Learning Resources
Tenenbaum, Data Structures Using C. Pearson Education, 200
Lipschutz: Schaum’s outline series Data structures Tata McGraw-Hill
Kamthane: Introduction to Data Structures in C. Pearson Education 2005.
Weiss, Data Structures and Algorithm Analysis in C, II Edition, Pearson Education,
2001
Robert Kruse Data Structures and program designing using ‘C’
Trembley and Sorenson Data Structures
E. Balaguruswamy Programming in ANSI C.
Bandyopadhyay, Data Structures Using C Pearson Education, 1999
Hanumanthappa M., Practical approach to Data Structures, Laxmi Publications, Fire
Wall media 2006
[Curriculum Design – 2015] Page 138
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Langsam, Ausenstein Maoshe & M. Tanenbaum Aaron Data Structures using C and
C++ Pearson Education
Evaluation: Sample Problems
Two samples of questions with model answers to them are given below:
T11: Use a recursive function to find GCD of two numbers.
Ans:
Problem description:
Using a recursive function, you will have to calculate the greatest common divisor of two
numbers. The GCD of two non-zero integers is the largest positive integer which can divide the
two integers without having a remainder. e.g. GCD of 12 and 8 is 4.
Algorithm:
Step 1: Enter the two numbers
Step 2: Read the numbers into two variables, say, num1 and num2
Step 3: Call the recursive function to calculate the GCD
Code Snippet:
int findgcd(int x,int y){
while(x!=y){
if(x>y)
return findgcd(x-y,y);
else
return findgcd(x,y-x);
[Curriculum Design – 2015] Page 139
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
return x;
T12: To print the Fibonacci series from 1 to n
Ans:
Problem description:
A Fibonacci series is defined as follows
The first term in the sequence is 0
The second term in the sequence is 1
The subsequent terms are found by adding the preceding two terms in the sequence.So,
the first 5 members of the Fibonacci series will be:
First = 0
Second = 1
Third = First + Second = 1
Fourth = Second + Third = 2
Fifth = Third + Fourth = 3
Thus, the formula for the series will be:
Let t1, t2… tn be terms in the Fibonacci sequence
t1=0, t2=1
tn = tn – 2 + tn – 1, where n>2
Variables description
a first term in the sequence
b second term in the sequence
[Curriculum Design – 2015] Page 140
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
c Is a number which stores and outputs every next member of the series
n Is the number which stores the number of members of the series to be printed
Algorithm:
Step 1: Start
Step 2: Initialize the variables a=0, b=1
Step 3: Read the number n
Step 4: if n== 1 print the value of ‘a’ and go to step 7 ELSE goto step 5
Step 5: if n== 2 print the value of ‘a’, ‘b’ and go to step 7 ELSE print ‘a’, ‘b’ and go to step 6
Step 6: Initialize i=3
i) if i<= n follow the steps below ELSE goto step 7
Add the values of a and b and store in c (c=a+b)
Print the value of ‘c’
Assign the value a=b
Assign the value b=c
Increment the value of ‘i’ using for loop
goto step 6(i)
Step 7: Stop
Program:
#include<stdio.h>
void main() {
[Curriculum Design – 2015] Page 141
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
int a,b,c,n,i;
clrscr();
printf("enter n value");
scanf("%d",&n);
a=0;
b=1;
if(n==1)
printf("%d",a);
else
if(n==2)
printf("%d%d", a, b);
else {
printf("%d%d", a, b);
for(i=2;i<n;i++) { //1 = 2, because loop will run for 2 times less in series as the
first two terms were printed in advance
c=a+b;
printf("%d",c);
a=b;
b=c;
getch();
[Curriculum Design – 2015] Page 142
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Output:
1. Enter n value : 5
01123
2. Enter n value : 7
0112358
3. Enter n value : -6
01
[Curriculum Design – 2015] Page 143
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Subject Code : CA3C09TB
Name of the Course: RDBMS
Duration: One Semester
Semester : 3
Total Lecture Hours: 72
Aim of the course:
The aim of this course is to give learners an understanding of the concepts and issues related
to databases and database design as well as the practical skills to translate that understanding
into the design and creation of complex databases.
Course Overview and Context:
Databases play an integral part in commercial domains. Users will be able to store, model and
retrieve data. Development of secure databases is an important task when it comes to
computing. Database Management Systems (DBMS) provide the systems, tools and
interfaces by which the organization can manage their information and use it to assist in the
effective running of the organization.
This course explores database architecture, database management system and the use of
databases in an organizational context. Database design techniques are investigated and
successful learners will be able to apply theoretical understanding to design, create and
document a database system.
Syllabus Content:
MODULE I : INTRODUCTION
Purpose of Database System -– Views of data – Data Models – Database Languages ––
Database System Architecture – Database users and Administrator – Entity– Relationship
model (E-R model ) – E-R Diagrams -- Introduction to relational databases
[Curriculum Design – 2015] Page 144
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
MODULE II : RELATIONAL MODEL
The relational Model – The catalog- Types– Keys - Relational Algebra – Domain Relational
Calculus – Tuple Relational Calculus - Fundamental operations – Additional Operations-
SQL fundamentals
Oracle data types, Data Constraints, Column level & table Level Constraints, working with
Tables.
Defining different constraints on the table, Defining Integrity Constraints in the ALTER
TABLE Command, Select Command, Logical Operator, Range Searching, Pattern Matching,
Oracle Function, Grouping data from Tables in SQL, Manipulation Data in SQL.
Joining Multiple Tables (Equi Joins), Joining a Table to itself (self Joins), Sub queries Union,
intersect & Minus Clause, Creating view, Renaming the Column of a view, Granting
Permissions, - Updating, Selection, Destroying view Creating Indexes, Creating and
managing User
Integrity – Triggers - Security – Advanced SQL features –Embedded SQL– Dynamic SQL-
Missing Information– Views – Introduction to Distributed Databases and Client/Server
Databases
MODULE III : DATABASE DESIGN
Functional Dependencies – Non-loss Decomposition – Functional Dependencies – First,
Second, Third Normal Forms, Dependency Preservation – Boyce/Codd Normal Form-Multi-
valued Dependencies and Fourth Normal Form – Join Dependencies and Fifth Normal Form
MODULE IV : TRANSACTIONS
Transaction Concepts - Transaction Recovery – ACID Properties – System Recovery –
Media Recovery – Two Phase Commit - Save Points – SQL Facilities for recovery –
Concurrency – Need for Concurrency – Locking Protocols – Two Phase Locking – Intent
Locking – Deadlock- Serializability – Recovery Isolation Levels – SQL Facilities for
Concurrency.
[Curriculum Design – 2015] Page 145
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Competencies of the course:
C1: Analyze the issues and applications of databases within an organization
C2: Understand the features and advantages of DBMS and RDBMS
C3: Analyze the database developmental methodology, entity-relationship modelling and
normalization
C4: Understand different queries that can be used on a database
C5: Analyze different normal forms and recognize how to optimize the database
C6: Understand Join operations
C7: Understand different transaction protocols
C8: Recognize how to avoid deadlock
C9: Understand different types of databases
C10: Recognize how to normalize a database applying different normal forms
Learning Resources
Abraham Silberschatz, Henry F. Korth, S. Sudharshan, “Database System Concepts”,
Fifth Edition, Tata McGraw Hill, 2006
Ramez Elmasri, Shamkant B. Navathe, “Fundamentals of Database Systems”, Fourth
Edition, Pearson/Addision Wesley, 2007.
Avison D and Fitzgerald G – Information Systems Development: Methodologies,
Techniques and Tools, McGraw Hill Higher Publishing Company, 2006
Connolly T and Begg C – Database Systems: A Practical Approach to Design,
Implementation and Management, Addison Wesley, 2004
[Curriculum Design – 2015] Page 146
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Howe D – Data Analysis for Database Design, Butterworth-Heinemann Ltd, 2001
Raghu Ramakrishnan, “Database Management Systems”, Third Edition, McGraw
Hill, 2003.
Chao L – Database Development and Management, CRC Press, 2006
Kroenke D – Database Concepts, 2nd Edition, Prentice Hall, 2004
Ritchie C – Relational Database Principles, Thomson Learning, 2002
Blue Print - Question Paper
RDBMS
Module
* Part A Part B Part C Part D
1 1 2 1 1
2 1 2 2 1
3 2 3 2 1
4 2 3 3 1
[Curriculum Design – 2015] Page 147
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Code : CA3C10TB
Name of the Course: COMPUTER NETWORKS
Duration: One Semester
Semester : 3
Total Lecture Hours: 72
Aim of the course:
To enable learners to understand computer networking concepts, how they work, how they
operate and the protocols, standards and the models associated with networking technology
and their troubleshooting mechanisms.
Course Overview and Context:
It is important for networking professionals to have a sound grounding in the basics of
networking and with the networking technology being developed thick and fast, the
professionals need to be updated of them at all times. The focus of this Module is providing a
background to the basics of networking and its underlying principles.
The learners taking this Module will explore the fundamentals of networking, the principle
and purpose behind layered models, devices used in networks and their wireless connectivity
and the ways to troubleshoot network related issues. The Module underpins the principles of
networking and enables the learners to work towards taking up vendor certifications in the
networking domain.
Syllabus Content:
Module 1: Networking Fundamentals
Basics of Network & Networking, Advantages of Networking, Types of Networks, Network
Terms- Host, Workstations, Server, Client, Node, Types of Network Architecture- Peer-to-
Peer & Client/Server, Workgroup Vs. Domain. Network Topologies, Types of Topologies,
Logical and physical topologies, selecting the Right Topology, Types of Transmission Media,
[Curriculum Design – 2015] Page 148
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Communication Modes, Wiring Standards and Cabling- straight through cable, crossover
cable, rollover cable, media connectors (Fiber optic, Coaxial, and TP etc.) Introduction of
OSI model, Seven layers of OSI model, Functions of the seven layers, Introduction of TCP/IP
Model, TCP, UDP, IP, ICMP, ARP/RARP, Comparison between OSI model & TCP/IP
model. Overview of Ethernet Addresses
Module 2: Basics of Network Devices
Network Devices- NIC- functions of NIC, installing NIC, Hub, Switch, Bridge, Router,
Gateways, And Other Networking Devices, Repeater, CSU/DSU, and modem, Data Link
Layer: Ethernet, Ethernet standards, Ethernet Components, Point-to-Point Protocol (PPP
),PPP standards, Address Resolution Protocol, Message format, transactions, Wireless
Networking: Wireless Technology, Benefits of Wireless Technology, Types of Wireless
Networks: Ad-hoc mode, Infrastructure mode, Wireless network Components: Wireless
Access Points, Wireless NICs, wireless LAN standards: IEEE 802. a, IEEE 802. b, IEEE
802. g, wireless LAN modulation techniques, wireless security Protocols: WEP,WPA,
802.1X, Installing a wireless LAN
Module 3: Basics of Network, Transport and Application Layers
Network Layer: Internet Protocol (IP ), IP standards, versions, functions, IPv4 addressing,
IPv4 address Classes, IPv4 address types, Subnet Mask, Default Gateway, Public & Private
IP Address, methods of assigning IP address, IPv6 address, types, assignment, Data
encapsulation, The IPv4 Datagram Format, The IPv6 Datagram Format, Internet Control
Message Protocol (ICMP ), ICMPv4, ICMPv6, Internet Group Management Protocol (IGMP
),Introduction to Routing and Switching concepts, Transport Layer: Transmission Control
Protocol(TCP), User Datagram Protocol (UDP), Overview of Ports & Sockets, Application
Layer: DHCP, DNS, HTTP/HTTPS, FTP, TFTP, SFTP, Telnet, Email: SMTP, POP3/IMAP,
NTP
[Curriculum Design – 2015] Page 149
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Module 4: WAN Technology
What Is a WAN?, WAN Switching, WAN Switching techniques Circuit Switching, Packet
Switching etc., Connecting to the Internet : PSTN, ISDN, DSL, CATV, Satellite-Based
Services, Last Mile Fiber, Cellular Technologies, Connecting LANs : Leased Lines,
SONET/SDH, Packet Switching, Remote Access: Dial-up Remote Access, Virtual Private
Networking, SSL VPN, Remote Terminal Emulation, Network security: Authentication and
Authorization, Tunneling and Encryption Protocols, IPSec, SSL and TLS, Firewall, Other
Security Appliances, Security Threats
Module 5: Network Operating Systems and Troubleshooting Network
Network Operating Systems: Microsoft Operating Systems, Novell NetWare, UNIX and
Linux Operating Systems, Macintosh Networking, Trouble Shooting Networks: Command-
Line interface Tools, Network and Internet Troubleshooting, Basic Network Troubleshooting
: Troubleshooting Model, identify the affected area, probable cause, implement a solution,
test the result, recognize the potential effects of the solution, document the solution, Using
Network Utilities: ping, traceroute, tracert, ipconfig, arp, nslookup, netstat, nbtstat, Hardware
trouble shooting tools, system monitoring tools
Competencies of the course:
C1. Understand the fundamentals of networks
C2. Understand and recall the OSI model and IP Addressing
C3. Recall the various network devices and their wireless networking
C4. Understand and apply the network troubleshooting methods
Learning Resources
1. TCP/IP Network Administration , 3rd EditionBy Craig Hunt- O’Reilly Publisher
2. Computer and Communication Networks By Nader F.Mir - Prentice Hall Publisher
[Curriculum Design – 2015] Page 150
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Question Paper – Blue Print
Computer Networks
Blue Print - Question Paper
Module
* Part A Part B Part C Part D
1 1 2 1 1
2 1 2 2 1
3 2 2 2 0
4 1 2 2 1
5 1 2 1 1
[Curriculum Design – 2015] Page 151
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Subject Code : CA3C11TB
Name of the Course: PROGRAMMING in JAVA
Duration: One Semester
Semester : 3
Total Lecture Hours: 72
Aim of the course:
The aim of this course is to provide learners with an understanding of the object oriented
concepts which helps in the field of programming, management of data, etc. and of Java
programming which helps to explore the object oriented nature of the language and the multi-
platform versatility offered by it.
Course Overview and Context:
Object oriented programming is the most proven technique for developing reliable programs.
It helps in increased productivity, reusability of code, decrease in the development time, and
reduces cost of production to an extent. The cost of maintaining such systems have also
considerably decreased. There are many languages which used the object oriented concepts
and techniques. Some of them are C++, Java, Smalltalk, Objective-C, etc.
Java is a purely object oriented language. Systems/applications created using java
programming language reduces the need for developing and maintain complex and space
consuming applications. Java has a lot of advantages of being simple, robust, platform
independent, etc. Nowadays java is also found in the mobile phones.
This course focuses on the concepts of object oriented programming language and the
different constructs for creating applications in java.
Syllabus Content:
Module 1 – Introduction
History, Overview of Java, Object Oriented Programming, A simple Programme, Two
control statements - if statement, for loop, using Blocks of codes, Lexical issues - White
space, identifiers, Literals, comments, separators, Java Key words. Data types: Integers,
[Curriculum Design – 2015] Page 152
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Floating point, characters, Boolean, A closer look at Literals, Variables, Type conversion and
casting, Automatic type promotion in Expressions Arrays.
Operators:
Arithmetic operators, The Bit wise operators, Relational Operators, Boolean Logical
operators, Assignment Operator, Operator Precedence. Control Statements: Selection
Statements - if, Switch: Iteration Statements - While, Do-while, for Nested loops, Jump
statements.
Module 2 – Classes:
Class Fundamentals, Declaring objects, Assigning object reference variables, Methods,
constructors, “this” keyword, finalize ( ) method A stack class, Over loading methods, using
objects as parameters, Argument passing, Returning objects, Recursion, Access control,
Introducing final, understanding static, Introducing Nested and Inner classes, Using
command line arguments.
Inheritance: Inheritance basics, Using super, method overriding, Dynamic method Dispatch,
using abstract classes, using final with Inheritance.
Module 3 – Packages:
Definition, Access protection importing packages, Interfaces: Definition implementing
interfaces.
Exception Handling: Fundamental, Exception types, Using try and catch, Multiple catch
clauses, Nested try Statements, throw, throws, finally, Java’s Built - in exception, using
Exceptions.
Module 4- Multithreaded Programming:
The Java thread model, The main thread, Creating a thread, Creating multiple thread,
Creating a thread, Creating multiple threads, Using isalive() and Join(), Thread - Priorities,
Synchronization, Inter thread communication, suspending, resuming and stopping threads,
[Curriculum Design – 2015] Page 153
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
using multi threading. 1/0 basics, Reading control input, writing control output, Reading and
Writing files, Applet Fundamentals, the AWT package,AWT Event handling concepts The
transient and volatile modifiers, using instance of using assert.
Module 5 – JAVA Database Connectivity (JDBC) :
Database connectivity: JDBC architecture, JDBC Drivers, the JDBC API: loading a driver,
connecting to a database, Creating and executing JDBC statements, Handling SQL
exceptions, Accessing result sets: Types of result sets, Methods of result set interface. An
example JDBC application to query a database.
Competencies of the course:
C1: Discuss the basic characteristics of object oriented programming
C2: Evaluate and discuss the different object oriented concepts
C3: Discuss the principles, characteristics and features of programming in Java
C4: Understand the different data types, data structures and loops to create solutions in java
for assignments
C5: Recognise the different java packages and their functions, collections framework, etc.
C6: Design and implement the I/O and networking operations, exceptions and exception
handling, etc.
C7: Understand the different user interface components
C8: Identify the uses and features of multithreaded programming
C9: Identify the different drivers used for JDBC connectivity
C10: Explain database manipulation using JDBC connectivity
[Curriculum Design – 2015] Page 154
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Learning Resources
Java Complete Reference by Herbert Schildt
Programming with Java by Balaguruswamy
SAMS teach yourself Java – 2: 3rd Edition by Rogers Cedenhead and Leura Lemay Pub.
Pearson Education.
Bloch J – Effective Java, Second Edition, Prentice Hall, 2008
Goetz B – Java Concurrency in Practice, Addison Wesley, 2006
Niemeyer P – Learning Java, Third Edition, O’Reilly, 2005
Question Paper – Blue Print
Programming in JAVA
Blue Print - Question Paper
Module
* Part A Part B Part C Part D
1 1 2 1 1
2 1 2 2 1
3 2 2 2 1
4 1 2 2 1
5 1 2 1 0
[Curriculum Design – 2015] Page 155
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Course Code : CA3C05PB
Name of the Course: RDBMS - LAB
Duration: One Semester
Semester 3
Total Lecture Hours: 36
Aim of the course:
The aim of this course is to enable learners to develop databases and query them using SQL
Course Overview and Context:
Databases play an integral part in commercial domains. Users will be able to store, model and
retrieve data. Development of secure databases is an important task when it comes to
computing. Database Management Systems (DBMS) provide the systems, tools and
interfaces by which the organization can manage their information and use it to assist in the
effective running of the organization. This course allows users to implement databases.
Competencies of the course:
C1: Implement databases and query them using SQL
Learning Resources
Abraham Silberschatz, Henry F. Korth, S. Sudharshan, “Database System Concepts”,
Fifth Edition, Tata McGraw Hill, 2006
Ramez Elmasri, Shamkant B. Navathe, “Fundamentals of Database Systems”, Fourth
Edition, Pearson/Addision Wesley, 2007.
Avison D and Fitzgerald G – Information Systems Development: Methodologies,
Techniques and Tools, McGraw Hill Higher Publishing Company, 2006
Connolly T and Begg C – Database Systems: A Practical Approach to Design,
Implementation and Management, Addison Wesley, 2004
Howe D – Data Analysis for Database Design, Butterworth-Heinemann Ltd, 2001
Raghu Ramakrishnan, “Database Management Systems”, Third Edition, McGraw
[Curriculum Design – 2015] Page 156
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Hill, 2003.
Chao L – Database Development and Management, CRC Press, 2006
Kroenke D – Database Concepts, 2nd Edition, Prentice Hall, 2004
Ritchie C – Relational Database Principles, Thomson Learning, 2002
[Curriculum Design – 2015] Page 157
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Course Code : CA3C06PB
Name of the Course: PROGRAMMING in JAVA - LAB
Duration: One Semester
Semester 3
Total Lecture Hours: 54
Aim of the course:
The aim of this course is to enable learners to implement different object oriented concepts
using Java language
Course Overview and Context:
Object oriented programming is the most proven technique for developing reliable programs.
It helps in increased productivity, reusability of code, decrease in the development time, and
reduces cost of production to an extent. The cost of maintaining such systems have also
considerably decreased. There are many languages which used the object oriented concepts
and techniques. Some of them are C++, Java, Smalltalk, Objective-C, etc.
Java is a purely object oriented language. Systems/applications created using java
programming language reduces the need for developing and maintain complex and space
consuming applications. Java has a lot of advantages of being simple, robust, platform
independent, etc. Nowadays java is also found in the mobile phones.
This course focuses on implementing simple to complex programs using Java
Syllabus Content:
List of Programs
Part A
1. Write a program to check whether two strings are equal or not.
2. Write a program to display reverse string.
3. Write a program to find the sum of digits of a given number.
4. Write a program to display a multiplication table.
[Curriculum Design – 2015] Page 158
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
5. Write a program to display all prime numbers between 1 to 1t000.
6. Write a program to insert element in existing array.
7. Write a program to sort existing array.
8. Write a program to create object for Tree Set and Stack and use all methods.
9. Write a program to check all math class functions.
10. Write a program to execute any Windows 95 application (Like notepad, calculator
etc)
11. Write a program to find out total memory, free memory and free memory after
executing garbage Collector (gc).
Part B
12. Write a program to copy a file to another file using Java to package classes. Get
the file names at run time and if the target file is existed then ask confirmation to overwrite
and take necessary actions.
13. Write a program to get file name at runtime and display number f lines and words
in that file.
14. Write a program to list files in the current working directory depending upon a
given pattern.
15. Create a textfield that allows only numeric value and in specified length.
16. Create a Frame with 2 labels, at runtime display x and y command-ordinate of
mouse pointer in the labels.
Competencies of the course:
C1: Implement simple to complex programs using Java language
[Curriculum Design – 2015] Page 159
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Learning Resources
Java Complete Reference by Herbert Schildt
Programming with Java by Balaguruswamy
SAMS teach yourself Java – 2: 3rd Edition by Rogers Cedenhead and Leura Lemay Pub.
Pearson Education.
Bloch J – Effective Java, Second Edition, Prentice Hall, 2008
Goetz B – Java Concurrency in Practice, Addison Wesley, 2006
Niemeyer P – Learning Java, Third Edition, O’Reilly, 2005
[Curriculum Design – 2015] Page 160
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
SYLLABI
OF
OPEN COURSES
[Curriculum Design – 2015] Page 161
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Course Code : CA5D01TB
Name of the course: SECURITY THREATS AND TRENDS
Duration: One semester
Semester : 5
Total Lecture Hours: 72
Aim of the course
To enable learners to understand the Introduction for viruses, worms, malware, botnets,
trojans, rootkits and also the cyber warfare introduction to advanced persistent threats &
information warfare.
Course Overview and Context
The Module provides you to know about the introduction, concepts, various types, technical,
managerial and procedurals controls to address viruses, worms, malwares, botnets, trojans,
rootkits.
This Module also gives you the knowledge about advanced persistent threats, information
warfare same as the before topics like working methods, security implications, managerial,
technical, procedural controls to address these threats.
Syllabus Content
Module 1 : Understand about the viruses & worms
Viruses & Worms
Introduction to Viruses &Worms, the concept of how Viruses & Worms work, the
various types of Viruses &Worms, the infection vectors of Viruses &Worms,
managerial, technical & procedural controls to address Viruses & Worms
Module 2 : Understand about the malware & botnets
Malware & Botnets
Introduction to Malware & Botnets, the concept of how Malware, Trojans & Botnets
[Curriculum Design – 2015] Page 162
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
work, the concept of Honeynets and Honeypots, Managerial, technical& procedural
controls to address Malware, Trojans & Botnets
Module 3 : Understand about the trojans & rootkits
Trojans & Rootkits
Introduction to Remote Access Trojans & Rootkits, concepts, their working methods ,
their security implications and the managerial , technical and procedural controls to
address RATs
Module 4 : Learn to identify the advanced persistent threats & threat warfare
Cyber Warfare
Introduction to Advanced Persistent Threats &Information Warfare, concepts, their
working methods, their security implications and the managerial, technical and
procedural controls to address these threats
Competencies of the course
On successful completion of this Module, the learner will be able to
C1. Understand about the viruses & worms
C2. Understand about the malware & botnets
C3. Understand about the trojans & rootkits
C4. Learn to identify the advanced persistent threats & threat warfare
Learning Resources
o Information warfare: corporate attack and defense in a digital world, William
Hutchinson, Matt Warren, Pub: Butterworth-Heinemann (April 3, 2001)
o Information security: protecting the global enterprise, Donald L. Pipkin, Pub: Prentice
Hall; 1 edition (May 22, 2000)
o Intrusion detection: an introduction to Internet surveillance, Edward G. Amoroso,
Pub: intrusion Net Books; 1 edition (February 15, 1999)
[Curriculum Design – 2015] Page 163
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Question Paper – Blue Print
Security Threats and Trends
Blue Print - Question Paper
Module
* Part A Part B Part C Part D
1 1 2 1 1
2 2 3 3 1
3 2 3 2 1
4 1 2 2 1
[Curriculum Design – 2015] Page 164
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
Course Code : CA5D02TB
Name of the course: CRYPTOGRAPHY FUNDAMENTALS
Duration: One semester
Semester : 5
Total Lecture Hours: 72
Aim of the course
To enable learner to familiarize with the basics of encryption and decryption techniques in
cryptography also giving him a broad picture of an idea related to the key management and
distribution features along with the objective of providing a strong understanding on the
implementation of Cryptographic functions.
Course Overview and Context
Primarily our Module throws light on the three building blocks of Information Security viz.,
Confidentiality, Integrity and Availability and explains how the concept of cryptography and
its practices will enable the organizational business to protect confidentiality and Integrity of
data. In order to know the nuances of cryptographic technology the Module focuses on the
different types of hash and Crypto/Hash Algorithms such as (DES, RSA, SHA, MD5,
HMAC, DSA) that will help the Organization to choose an appropriate solution based on the
Business and Regulatory requirements.
The Module emphasizes the need of understanding the Key management and the technology
used to implement for achieving a well defined encryption and decryption policy. It also
covers the underlying vulnerabilities in today’s widely used cryptographic functions and the
precautionary measures while using the function. Conclusively, The Module helps the learner
to understand the importance of Certifying Authority, Public Key Infrastructure and the
System requirements for implementing Cryptographic functions.
Syllabus Content
Module 1: Introduction to Cryptography
[Curriculum Design – 2015] Page 165
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
The Confidentiality, Integrity & Availability (CIA) Triad, Cryptographic concepts,
methodologies &practices, Symmetric& Asymmetric cryptography, public& private keys,
Cryptographic algorithms and uses, Construction& use of Digital signatures
Module 2: Types of Algorithms
The basic functionality of hash/crypto algorithms (DES, RSA, SHA, MD5, HMAC, DSA)
and effects on key length concepts in Elliptical Curve Cryptography & Quantum
Cryptography
Module 3: Key Management
The basic functions involved in key management including creation, distribution,
verification, revocation and destruction, storage, recovery and life span and how these
functions affect cryptographic integrity
Module 4: Application of Cryptography
Major key distribution methods and algorithms including Kerberos, ISAKMP etc.,
Vulnerabilities to cryptographic functions, the Use and functions of Certifying Authorities
(CAs),Public Key Infrastructure (PKI) and System architecture requirements for
implementing cryptographic functions.
Competencies of the course
On successful completion of this Module a learner will:
C1. Understand the methodology, Practices and uses in Cryptography
C2. Describe the Various Hash/Crypto Algorithms
C3. Understand the Key management Principles
C4. Analyze the importance of PKI and Certificate Authority
Learning Resources
o Cryptography: An Introduction by V. V. I Ashchenko, Pub: American Mathematical
Society - 2002
o Cryptanalytic attacks on RSA – by Song Y. Yan 2005
[Curriculum Design – 2015] Page 166
Bachelor in Computer Applications – Cloud Technology and Information Security ,
St. Teresa’s College (Autonomous), Ernakulam
o Official (ISC)2 Guide to the CISSP CBK, Second Edition - Harold F. Tipton 2005
o Cryptography demystified –by John E. Hershey 2000
.
Question Paper – Blue Print
Cryptography Fundamentals
Blue Print - Question Paper
Module
* Part A Part B Part C Part D
1 1 2 1 1
2 2 3 3 1
3 2 3 2 1
4 1 2 2 1
[Curriculum Design – 2015] Page 167
S-ar putea să vă placă și
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceDe la EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceEvaluare: 4 din 5 stele4/5 (895)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeDe la EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeEvaluare: 4 din 5 stele4/5 (5794)
- Shoe Dog: A Memoir by the Creator of NikeDe la EverandShoe Dog: A Memoir by the Creator of NikeEvaluare: 4.5 din 5 stele4.5/5 (537)
- Grit: The Power of Passion and PerseveranceDe la EverandGrit: The Power of Passion and PerseveranceEvaluare: 4 din 5 stele4/5 (588)
- The Yellow House: A Memoir (2019 National Book Award Winner)De la EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Evaluare: 4 din 5 stele4/5 (98)
- The Little Book of Hygge: Danish Secrets to Happy LivingDe la EverandThe Little Book of Hygge: Danish Secrets to Happy LivingEvaluare: 3.5 din 5 stele3.5/5 (400)
- Never Split the Difference: Negotiating As If Your Life Depended On ItDe la EverandNever Split the Difference: Negotiating As If Your Life Depended On ItEvaluare: 4.5 din 5 stele4.5/5 (838)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureDe la EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureEvaluare: 4.5 din 5 stele4.5/5 (474)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryDe la EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryEvaluare: 3.5 din 5 stele3.5/5 (231)
- The Emperor of All Maladies: A Biography of CancerDe la EverandThe Emperor of All Maladies: A Biography of CancerEvaluare: 4.5 din 5 stele4.5/5 (271)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaDe la EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaEvaluare: 4.5 din 5 stele4.5/5 (266)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersDe la EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersEvaluare: 4.5 din 5 stele4.5/5 (345)
- On Fire: The (Burning) Case for a Green New DealDe la EverandOn Fire: The (Burning) Case for a Green New DealEvaluare: 4 din 5 stele4/5 (74)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyDe la EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyEvaluare: 3.5 din 5 stele3.5/5 (2259)
- Team of Rivals: The Political Genius of Abraham LincolnDe la EverandTeam of Rivals: The Political Genius of Abraham LincolnEvaluare: 4.5 din 5 stele4.5/5 (234)
- The Unwinding: An Inner History of the New AmericaDe la EverandThe Unwinding: An Inner History of the New AmericaEvaluare: 4 din 5 stele4/5 (45)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreDe la EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreEvaluare: 4 din 5 stele4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)De la EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Evaluare: 4.5 din 5 stele4.5/5 (121)
- Her Body and Other Parties: StoriesDe la EverandHer Body and Other Parties: StoriesEvaluare: 4 din 5 stele4/5 (821)
- FTLG gr001 - en eDocument111 paginiFTLG gr001 - en eIkhtiander IkhtianderÎncă nu există evaluări
- User Manual Panasonic TCP42G25Document76 paginiUser Manual Panasonic TCP42G25John LingleyÎncă nu există evaluări
- Cloud Computing Notes Btech Csvtu 6th SemDocument14 paginiCloud Computing Notes Btech Csvtu 6th SemPari BhandarkarÎncă nu există evaluări
- Cybersecurity in The Electricity Sector Managing Critical Infrastructure by Rafal LeszczynaDocument221 paginiCybersecurity in The Electricity Sector Managing Critical Infrastructure by Rafal LeszczynavictorÎncă nu există evaluări
- 18-Computer Science SyllabusDocument5 pagini18-Computer Science Syllabusmani_bushanÎncă nu există evaluări
- Introducing BACnetDocument70 paginiIntroducing BACnethourÎncă nu există evaluări
- Module 10 Globalization and Human DevelopmentDocument6 paginiModule 10 Globalization and Human DevelopmentLive LoveÎncă nu există evaluări
- TCP/IP Tutorial: The IP Address and ClassesDocument11 paginiTCP/IP Tutorial: The IP Address and ClassesRajesh JainÎncă nu există evaluări
- Seminar Report On Gigabit NetworkingDocument23 paginiSeminar Report On Gigabit Networkingnjpatel9Încă nu există evaluări
- BR 6324NL Manual BookDocument161 paginiBR 6324NL Manual BookAshutosh PandeyÎncă nu există evaluări
- Smart Agriculture Wireless Sensor Routing Protocol and Node Location Algorithm Based On Internet of Things TechnologyDocument7 paginiSmart Agriculture Wireless Sensor Routing Protocol and Node Location Algorithm Based On Internet of Things TechnologySowmmiya UthayakumarÎncă nu există evaluări
- Wlan Introduction & Advantages & Disadvantages & TopologiesDocument6 paginiWlan Introduction & Advantages & Disadvantages & TopologiesHari Krishna Konda100% (1)
- User Guide PG5 EDocument224 paginiUser Guide PG5 EMarcio MifaroÎncă nu există evaluări
- IT Essentials (ITE v6.0) Practice Final Exam AnswersDocument16 paginiIT Essentials (ITE v6.0) Practice Final Exam AnswersG JagadishÎncă nu există evaluări
- Quality of Service For VoipDocument146 paginiQuality of Service For VoipKoushik KashyapÎncă nu există evaluări
- Communication InterfaceDocument36 paginiCommunication InterfaceAsante WilliamÎncă nu există evaluări
- SAMS Wireless Lans PDFDocument360 paginiSAMS Wireless Lans PDFJose AngelÎncă nu există evaluări
- InfoSec AwarenessDocument51 paginiInfoSec AwarenessGonçalo Almeida TeixeiraÎncă nu există evaluări
- Trends, Networks, and Critical Thinking in The 21 Century: Improving Human Life Using ICTDocument13 paginiTrends, Networks, and Critical Thinking in The 21 Century: Improving Human Life Using ICTariel agosÎncă nu există evaluări
- The Study and Implementation of Mobile GPS Navigation System Based On Google MapsDocument4 paginiThe Study and Implementation of Mobile GPS Navigation System Based On Google MapsNoraniah Abd AzizÎncă nu există evaluări
- NIST SURF Orientation ManualDocument54 paginiNIST SURF Orientation ManualDannyÎncă nu există evaluări
- Palo Alto Networks Product Summary SpecsheetDocument3 paginiPalo Alto Networks Product Summary SpecsheetJackkyz RockkerzÎncă nu există evaluări
- Security Handbook: Network-Enabled Devices, AOS v7.xDocument39 paginiSecurity Handbook: Network-Enabled Devices, AOS v7.xM Aulia RahmanÎncă nu există evaluări
- It Security PDFDocument289 paginiIt Security PDFAntony AÎncă nu există evaluări
- 5th Sem SyllabusDocument5 pagini5th Sem SyllabusAnkit SinghÎncă nu există evaluări
- TK103 User Manual PDFDocument11 paginiTK103 User Manual PDFAbaca ChannelÎncă nu există evaluări
- Huawei SingleRAN IP Migration SolutionDocument24 paginiHuawei SingleRAN IP Migration SolutionHazem Maher100% (1)
- Ip Telephony & NGN: IrisetDocument74 paginiIp Telephony & NGN: IrisetPankaj kumarÎncă nu există evaluări
- Self-Assessment Guide: Rev - No.00-03/01/17Document4 paginiSelf-Assessment Guide: Rev - No.00-03/01/17Kindly LegarteÎncă nu există evaluări
- 5 8 18Document3 pagini5 8 18Holy Wayne 'Trinity' ChuaÎncă nu există evaluări