Documente Academic
Documente Profesional
Documente Cultură
Zero Trust Approach
Încărcat de
andymtkwongDrepturi de autor
Formate disponibile
Partajați acest document
Partajați sau inserați document
Vi se pare util acest document?
Este necorespunzător acest conținut?
Raportați acest documentDrepturi de autor:
Formate disponibile
Zero Trust Approach
Încărcat de
andymtkwongDrepturi de autor:
Formate disponibile
GETTING STARTED WITH
A ZERO TRUST APPROACH
TO NETWORK SECURITY
The continued, high frequency of successful cyberattacks against
today’s enterprises has made it abundantly clear that traditional,
perimeter-centric security strategies are no longer effective. The
failure of resulting architectures is a product not only of the outdated
assumption that everything on the inside of an organization’s n etwork
can be trusted but also the inability of legacy countermeasures to
provide adequate visibility, control and p rotection of application traffic
transiting associated network boundaries.
First introduced by Forrester Research, Zero Trust is an alternative
security model that addresses the shortcomings of failing p erimeter-
centric strategies by removing the assumption of trust from the
equation. With Zero Trust, essential security capabilities are deployed in
a way that provides policy enforcement and protection for all users,
devices, applications, data resources and the communications traffic
between them, regardless of location.
Palo Alto Networks | Zero Trust Approach
Executive Summary
This paper discusses the need for and details of a Zero Trust approach to network security. It also itemizes
the essential criteria and capabilities required of a Zero Trust solution, explains how the Palo Alto Networks®
Next-Generation Security Platform delivers on these requirements, and provides guidance on how to
progressively migrate to a Zero Trust design.
Benefits available to organizations that employ Palo Alto Networks solutions to implement a Zero Trust
network include:
• Dramatically improved effectiveness in mitigating data loss via visibility and safe enablement
of applications, and detection and prevention of advanced threats.
• Greater efficiency for achieving compliance with security and privacy mandates.
• Increased ability to securely enable transformative IT initiatives—such as user mobility and
infrastructure virtualization.
• Substantially reduced total cost of ownership (TCO) for IT security.
The Traditional Approach to Network Security is Failing
The Verizon 2016 Data Breach Investigations Report says “No locale, industry or organization is bulletproof
when it comes to the compromise of data.”1
Given the extent to which today’s organizations continue to rely on perimeter-centric strategies, this finding
should come as no surprise. The simple truth of the matter is that perimeter-based approaches to security are
no longer effective.
Misplaced Trust
The primary issue with a perimeter-centric security strategy where countermeasures are deployed at a handful
of well-defined ingress/egress points to the network is that it relies on the assumption that everything on
the internal network can be trusted. However, this assumption is no longer a safe one to make, given modern
business conditions and computing environments where:
• Remote employees, mobile users, and cloud computing solutions blur the distinction between
“internal” and “external.”
• Wireless technologies, the proliferation of partner connections, and the need to support guest
users introduce countless additional pathways into the network.
• Branch offices may be located in untrusted “countries of interest.”
• Insiders, whether intentionally malicious or just careless, may present a very real security threat.
Such strategies also fail to account for:
• The potential for sophisticated cyberthreats to penetrate perimeter defenses—in which case
they would then have free rein over the internal network.
• Scenarios where malicious users are able to gain access to the internal network and sensitive
resources by using the stolen credentials of trusted users.
• The reality that internal networks are rarely homogeneous but instead include pockets of users
and resources with inherently different levels of trust/sensitivity, which should ideally be sepa-
rated in any event (e.g., R&D and financial systems vs. print/file servers).
Palo Alto Networks | Zero Trust Approach 2
Inadequate Capabilities
It is important to realize that a broken trust model is not the only item responsible for the diminishing
effectiveness of perimeter-centric approaches to network security. Another contributing factor is that legacy
devices and technologies commonly used to build network perimeters let too much unwanted traffic through.
Typical shortcomings in this regard include the inability to:
• Definitively distinguish good applications from bad ones (which leads to overly permissive
access control settings).
• Adequately account for encrypted application traffic.
• Accurately identify and control users (regardless of where they’re located or what devices
they’re using).
• Filter allowed traffic not only for known application-borne threats but also unknown ones.
The net result is that merely re-architecting one’s defenses in a way that delivers pervasive internal trust
boundaries will not be sufficient. Care must be taken to also ensure that the devices and technologies used to
implement these boundaries actually provide the visibility, control and threat inspection capabilities needed to
securely enable essential business applications while still thwarting modern malware, targeted attacks, and the
unauthorized exfiltration of sensitive business data.
The Zero Trust Model – Providing Effective Security for Modern Networks
A promising alternative model for IT security, Zero Trust is intended to remedy the deficiencies with perimeter-
centric strategies and the legacy devices and technologies used to implement them. It does this by promoting
“never trust, always verify” as its guiding principle. This differs substantially from conventional security models
which operate on the basis of “trust but verify.”
In particular, with Zero Trust there is no default trust for any entity—including users, devices, applications and
packets—regardless of what it is and its location on or relative to the corporate network. In addition, verifying that
authorized entities are always doing only what they’re allowed to do is no longer optional; it’s now mandatory.
The implications for these two changes are, respectively:
a. The need to establish trust boundaries that effectively compartmentalize different segments of the internal
computing environment. The general idea is to move security functionality closer to the different pockets
of resources that require protection. This way it can always be enforced regardless of the point of origin of
associated communications traffic.
b. The need for trust boundaries to do more than just initial authorization and access control enforcement.
To “always verify” also requires ongoing monitoring and inspection of associated communications traffic for
subversive activities (i.e., threats).
The core Zero Trust principle and derivative implications are further reflected and refined in the three concepts
that define the operational objectives of a Zero Trust implementation.2
Concept #1: Ensure that all resources are accessed securely regardless of location. This suggests not only
the need for multiple trust boundaries but also increased use of secure access for communication to/from
resources, even when sessions are confined to the “internal” network. It also means ensuring that only devices
with the right status and settings (e.g., ones that are managed by corporate IT, have an approved VPN client and
proper passcodes, and are not running malware) are allowed access to the network.
Concept #2: Adopt a least-privileged strategy and strictly enforce access control. The goal in this case is to
absolutely minimize allowed access to resources as a means to reduce the pathways available for malware and
attackers to gain unauthorized access—and subsequently to spread laterally and/or exfiltrate sensitive data.
Concept #3: Inspect and log all traffic. This reiterates the need to “always verify” while also making it clear
that adequate protection requires more than just strict enforcement of access control. Close and continuous
attention must also be paid to exactly what is happening in “allowed” applications, and the only way to do this is
to inspect the content for threats.
Palo Alto Networks | Zero Trust Approach 3
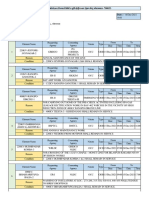
Zero Trust Conceptual Architecture
To help understand what Zero Trust looks like in practice, a conceptual architecture is shown in Figure 1.
The main components include the Zero Trust segmentation platform, trust zones and associated management
infrastructure.
PCI
Application
V Zone
SeMrie-
s Web
Application
V
CAMPUS
ZONE
SeMrie-
Zone
s
Employee
Application
V
SeM
Zone
Zero Trust rie-
Segmentation s
Platform
WIRELESS
ZONE
MANAGEMENT
ZONE
B2B
ZONE
Figure 1: Zero Trust Conceptual Architecture
Zero Trust Segmentation Platform. Referred to as a network segmentation gateway by Forrester® Research,2
the Zero Trust segmentation platform is the component used to define internal trust boundaries. In other
words, it is what provides the majority of the security functionality needed to deliver on the Zero Trust
operational objectives—including the ability to enable secure network access, granularly control traffic flow
to/from resources, and continuously monitor allowed sessions for signs of threat activity. Although Figure 1
depicts the Zero Trust segmentation platform as a single component in a single physical location, in practice—
due to performance, scalability and physical limitations—an effective implementation is more likely to entail
multiple instances distributed throughout an organization’s network. In addition, the solution is designated as
a “platform” not only to reflect that it is an aggregation of multiple distinct (and potentially distributed) security
technologies, but also that they operate as a holistic threat protection framework to reduce the attack surface
and correlate information about threats that are found.
Trust Zones. Referred to as a “micro core and perimeter” (MCAP) by Forrester Research,2 a trust zone is a
distinct pocket of infrastructure where the member resources not only operate at the same trust level but also
share similar functionality. Sharing functionality, such as protocols and types of transactions, is imperative,
in fact, because this is what is needed to actually minimize the number of allowed pathways into and out
of a given zone and, in turn, minimize the potential for malicious insiders and other types of threats to gain
unauthorized access to sensitive resources.
Example trust zones shown in Figure 1 include the user (or campus) zone, a wireless zone for guest access, a
cardholder data zone, database and application zones for multi-tier services, and a zone for public-facing web
applications.
It is important to note, too, that a trust zone is not intended to be a “pocket of trust” where systems (and
therefore threats) within the zone are able to communicate freely/directly with each other. For a full Zero Trust
implementation, the network would be configured to ensure that ALL communications traffic—including that
between devices in the same zone—is intermediated by the corresponding Zero Trust segmentation platform.
Palo Alto Networks | Zero Trust Approach 4
Management Infrastructure. Centralized management capabilities are crucial to enabling efficient
administration and ongoing monitoring, particularly for implementations involving multiple, distributed Zero
Trust segmentation platforms. In addition, a data acquisition network provides a convenient way to supplement
the native monitoring and analysis capabilities for a Zero Trust segmentation platform. By forwarding all session
logs to a data acquisition network, this data can then be processed by any number of out-of-band analysis
tools and technologies intended, for example, to further enhance network visibility, detect unknown threats, or
support compliance reporting.
Implementing Zero Trust with Palo Alto Networks
Because the heart of any Zero Trust network security architecture is the Zero Trust segmentation platform, it is
imperative that organizations choose the right solution. Accordingly, this section identifies a set of key criteria
and capabilities for IT security managers and architects to consider when making a selection. In each case, a
brief synopsis is also provided of how the Palo Alto Networks Next-Generation Security Platform meets the
corresponding requirements.
Comprehensive Security Functionality
The Palo Alto Networks platform supports:
• Secure access. GlobalProtect™ network security client for endpoints delivers consistent, secure IPsec and
SSL VPN connectivity for all employees, partners, customers and guests wherever they’re located (e.g.,
at remote/branch offices, on the local network, or over the Internet). Policies to determine which users
and devices can access sensitive applications and data can be defined based on application, user, content,
device and device state.
• Inspection of ALL traffic. App-ID™ technology accurately identifies and classifies all traffic, regardless of
ports and protocols, evasive tactics such as port hopping, or encryption. This eliminates methods that mal-
ware may use to hide from detection and provides complete context into applications, associated content
and threats.
• Least privileges access control. The combination of App-ID, User-ID™ and Content-ID™ delivers a positive
control model that allows organizations to control interactions with resources based on an extensive range
of business-relevant attributes, including the specific application and individual functions being used, user
and group identity, and the specific types or pieces of data being accessed (e.g., credit card or Social Security
numbers). Compared to alternative solutions, which let too much traffic through because they’re limited to
port and protocol level classification, the result is truly granular access control that safely enables the right
applications for the right sets of users while
automatically eliminating unwanted, unau-
thorized and potentially harmful traffic from
Least Privileges … or Just Least Effective?
gaining access to the network. (see “Least
Privileges … or Just Least Effective?” below). Legacy security gateways and other devices that
rely on stateful inspection technology are actually
• Advanced threat protection. A combination incapable of enforcing a least-privileged policy
of anti-virus/malware, intrusion prevention, (i.e., where only what’s needed to support this
and advanced threat prevention technologies business is allowed to pass). The issue with these
(Content-ID and WildFire™), provide compre- devices is that their classification engines only un-
hensive protection against both known and derstand IP addresses, ports and protocols—and,
unknown threats, including threats on mobile therefore, can’t distinguish the specific applica-
devices. In addition, support for a closed-loop, tions that reside behind/within these low-level
highly integrated defense ensures that inline “wrappers.” With a stateful inspection device, for
enforcement devices and other components example, a rule permitting traffic using the HTTP
in the threat protection framework are auto- protocol on TCP port 80 would allow the passage
matically updated with the findings from Wild- of not only a legitimate e-commerce application
Fire and other sources of threat intelligence. but potentially numerous other web applications
and utilities as well, such as those used for
Coverage for All IT Domains webmail, social networking, and countless other
The Palo Alto Networks Zero Trust offering purposes. The net result is that such devices are,
includes an extensive portfolio of virtual and in fact, poor candidates for implementing a Zero
hardware appliances that enables trust boundaries Trust security model.
to consistently and cost-effectively be established
Palo Alto Networks | Zero Trust Approach 5
throughout an organization’s entire network, including in remote/ branch offices, for mobile users, at the
Internet perimeter, in the cloud, at the ingress to the data center and for individual enclaves wherever they
might exist.
High-Performance Design
By definition, a Zero Trust platform aggregates numerous security and networking capabilities. However, it
must also be capable of delivering all of these features without becoming a performance bottleneck. The
Palo Alto Networks solution achieves this objective first and foremost by utilizing a single-pass software
architecture.
Processing requirements and latency are minimized as, unlike with other solutions, there is no need for traffic
streams to be processed
multiple times (e.g., once for each security function). In addition, Palo Alto Networks hardware appliances
feature separate control and data planes, plus function-specific, parallel processing hardware engines (i.e.,
custom chips) for core packet processing, acceleration of standard security functions, and dedicated content
scanning. At the high end, the result is 200 Gbps of Zero Trust throughput, with unmatched visibility and
control of applications, users, and content.
Flexible, non-disruptive deployment. Ideally, it should be possible to implement a Zero Trust approach in
a way that requires no modification to the existing network and is completely transparent to one’s users.
Opportunities to take advantage of major network overhauls are rare, and disrupting operations is not a good
career choice. Thus, IT security managers will need to make do as best they can, typically by converting to
Zero Trust on the fly. The Palo Alto Networks Next-Generation Security Platform supports this requirement in
numerous ways. For example:
• Virtual wire mode enables transparent, Layer 1 insertion into the network and does not require any con-
figuration changes to surrounding or adjacent network devices. All next-generation security technologies
are supported in this mode.
• A single hardware appliance can support multiple different connection modes (Layer 1, Layer 2 or Layer 3),
thereby maximizing its ability to accommodate trust zones with different needs.
• Support for a broad range of networking technologies (e.g., L2/L3 switching, dynamic routing, 802.1Q
VLANS, trunked ports and traffic shaping) guarantees the ability to integrate into practically any environment.
• Multiple management domains (see Figure 1) can be accommodated by taking advantage of a virtual
systems capability that enables separate, isolated Zero Trust virtual instances on a physical appliance.
Virtual systems allow you to segment the administration of all policies (security, NAT, QoS, etc.) as well as
all reporting and visibility functions.
Centralized management. As discussed, the basis for this requirement is the need to be able to efficiently
administer multiple, distributed Zero Trust segmentation platforms. In this case, the core need is met by Palo
Alto Networks Panorama™ network security management, an optional centralized management offering.
However, that is only the beginning of the management capabilities that Palo Alto Networks makes available
to simplify the task of implementing and maintaining a Zero Trust security model. Other notable features
include:
• A unified policy model and interface that avoids having to flip between multiple screens and/or consoles
to view and configure access control and inspection rules.
• A hierarchical policy and administration model that accommodates a combination of both global and local
rules and configuration settings.
• Advanced, graphical visualization tools for better understanding what applications and users are doing on
your network at any given point in time.
• A comprehensive REST-based API that enables quick-and-easy integration with third-party management,
automation and orchestration tools—for example, to ensure protection for newly provisioned or relocated
virtualized applications.
• Integral reporting and logging, with real-time filtering for rapid forensic investigation into every session
traversing the network.
Palo Alto Networks | Zero Trust Approach 6
A Progressive Approach for Implementing Zero Trust
In terms of moving forward with a Zero Trust redesign, it is important for IT security managers and architects
to realize that it’s not necessary to instigate or wait for the next comprehensive overhaul of their organization’s
network and security infrastructure. Indeed, one of the great advantages of a Zero Trust architecture featuring
Palo Alto Networks Zero Trust segmentation platform is that it is conducive to progressive implementation.
To get started, IT security teams can take advantage of the virtual wire feature to non-disruptively deploy Palo
Alto Networks devices at one or more locations within the enterprise computing environment. Configured in
listen-only mode, these units could then be used to obtain a detailed picture of transaction flows throughout
the network, including where, when and to what extent specific users are using specific applications and
data resources. Armed with these details, the security team would then be in an excellent position to: (a)
incrementally deploy devices in appropriate locations to establish internal trust boundaries for identified trust
zones, and (b) incrementally configure the appropriate enforcement and inspection policies to effectively
put each trust boundary “online.” Advantages of a progressive approach, such as this, include minimizing the
potential impact on IT operations and being able to spread the required investment and work effort over time.
For those security teams that already have a good understanding of the transaction flows in their environment,
an alternate approach is to map out trust zones and begin to establish corresponding trust boundaries based
on relative risk and/or the sensitivity of the data involved. A logical starting point in this case is to begin by
identifying well-defined pockets of users and systems involving high concentrations of sensitive data—such
as the 4Ps: payment card industry (PCI) or other financial data; personal healthcare information (PHI); other
personally identifiable information (PII); and intellectual property (IP). From there, it then makes sense to
consider progressively establishing trust zones/boundaries for other segments of the computing environment
based on their relative degree of risk. For example:
• IT management systems/networks (where administrators often hold the proverbial “keys to the kingdom”
and a successful attack could lead to compromise of the entire network).
• Partner resources and connections (B2B).
• High-profile, customer-facing resources and connections (B2C).
• Branch offices in “countries of interest” (followed by all other branch offices).
• Guest access networks (both wireless and wired).
• Campus networks.
Adopting Zero Trust principles and concepts at major access points to the internet also makes sense. Doing so,
however, will probably require replacing or augmenting entrenched, legacy security devices with a Zero Trust
segmentation platform to obtain all of the requisite capabilities.
Benefits of Adopting Zero Trust Principles and Practices
There are several technical and business advantages associated with using the Palo Alto Networks platform to
achieve a Zero Trust security architecture. These include being able to:
• Incrementally and non-disruptively make the transition to a Zero Trust model.
• Obtain unparalleled situational awareness of enterprise computing activity, legitimate and otherwise.
• Fully implement all Zero Trust principles and concepts, including strict enforcement of a least-privileged
access control policy (which is essential to reducing the attack surface).
• Dramatically enhance the organization’s security posture and ability to prevent the exfiltration of sensitive data.
• Simplify achieving and maintaining compliance with applicable standards and regulations (by using highly
effective trust boundaries to segment off sensitive resources).
• Securely enable and easily adapt to accommodate business-driven IT initiatives—such as user mobility,
social networking, infrastructure virtualization and cloud computing.
• Reduce the total cost of ownership by using a single consolidated security platform across the entire com-
puting environment, instead of a disparate collection of disconnected point products.
Palo Alto Networks | Zero Trust Approach 7
Conclusion
Perimeter-centric security strategies continue to be sorely challenged by not only increasingly sophisticated
cyberthreats but also major changes to the technology and business landscape—such as user mobility, hyper
interconnectivity and globalization. These factors invalidate the assumption that everything “on the inside” can
be trusted. The bottom line is that such strategies—along with the legacy technologies used to implement
them—are, for the most part, no longer effective.
Organizations looking to substantially improve their defensive posture against modern cyberthreats and more
reliably prevent the exfiltration of sensitive data should consider migrating to a Zero Trust security architecture.
An alternative model for IT security, Zero Trust eliminates the faulty assumption of trust and rectifies the
shortcomings of traditional perimeter-centric architectures by promoting the use of a Zero Trust segmentation
platform to establish secure “trust boundaries” throughout a computing environment and, in general, in closer
proximity to sensitive resources.
Because the Zero Trust segmentation platform is the foundation of any Zero Trust initiative, the importance of
selecting the right solution cannot be overstated. In this regard, Palo Alto Networks Next-Generation Security
Platform represents an ideal candidate—one that combines unparalleled visibility, control, and threat protection
capabilities with comprehensive coverage for all IT domains, from the data center and internet gateway to
branch offices, mobile users and even the cloud.
1 Verizon 2016 Data Breach Investigations Report
2 No More Chewy Centers: The Zero Trust Model Of Information Security, Forrester Research, March 23, 2016
4401 Great America Parkway © 2016 Palo Alto Networks, Inc. Palo Alto Networks is a
Santa Clara, CA 95054 registered trademark of Palo Alto Networks. A list of our
Main: +1.408.753.4000 trademarks can be found at http://www.paloaltonetworks.
Sales: +1.866.320.4788 com/company/trademarks.html. All other marks mentioned
Support: +1.866.898.9087 herein may be trademarks of their respective companies.
zero-trust-approach-wp-081616
www.paloaltonetworks.com
S-ar putea să vă placă și
- The Yellow House: A Memoir (2019 National Book Award Winner)De la EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Evaluare: 4 din 5 stele4/5 (98)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceDe la EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceEvaluare: 4 din 5 stele4/5 (895)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeDe la EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeEvaluare: 4 din 5 stele4/5 (5794)
- The Little Book of Hygge: Danish Secrets to Happy LivingDe la EverandThe Little Book of Hygge: Danish Secrets to Happy LivingEvaluare: 3.5 din 5 stele3.5/5 (399)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaDe la EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaEvaluare: 4.5 din 5 stele4.5/5 (266)
- Shoe Dog: A Memoir by the Creator of NikeDe la EverandShoe Dog: A Memoir by the Creator of NikeEvaluare: 4.5 din 5 stele4.5/5 (537)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureDe la EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureEvaluare: 4.5 din 5 stele4.5/5 (474)
- Never Split the Difference: Negotiating As If Your Life Depended On ItDe la EverandNever Split the Difference: Negotiating As If Your Life Depended On ItEvaluare: 4.5 din 5 stele4.5/5 (838)
- Grit: The Power of Passion and PerseveranceDe la EverandGrit: The Power of Passion and PerseveranceEvaluare: 4 din 5 stele4/5 (588)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryDe la EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryEvaluare: 3.5 din 5 stele3.5/5 (231)
- The Emperor of All Maladies: A Biography of CancerDe la EverandThe Emperor of All Maladies: A Biography of CancerEvaluare: 4.5 din 5 stele4.5/5 (271)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyDe la EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyEvaluare: 3.5 din 5 stele3.5/5 (2259)
- On Fire: The (Burning) Case for a Green New DealDe la EverandOn Fire: The (Burning) Case for a Green New DealEvaluare: 4 din 5 stele4/5 (73)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersDe la EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersEvaluare: 4.5 din 5 stele4.5/5 (344)
- Team of Rivals: The Political Genius of Abraham LincolnDe la EverandTeam of Rivals: The Political Genius of Abraham LincolnEvaluare: 4.5 din 5 stele4.5/5 (234)
- The Unwinding: An Inner History of the New AmericaDe la EverandThe Unwinding: An Inner History of the New AmericaEvaluare: 4 din 5 stele4/5 (45)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreDe la EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreEvaluare: 4 din 5 stele4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)De la EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Evaluare: 4.5 din 5 stele4.5/5 (121)
- Her Body and Other Parties: StoriesDe la EverandHer Body and Other Parties: StoriesEvaluare: 4 din 5 stele4/5 (821)
- Resume: Sankarapu Sirisha Contact No: 9989988095 Email-Id: Career ObjectiveDocument3 paginiResume: Sankarapu Sirisha Contact No: 9989988095 Email-Id: Career Objectivesankarapu sirishaÎncă nu există evaluări
- Omron G8P 114P FD US DC12 DatasheetDocument6 paginiOmron G8P 114P FD US DC12 DatasheetCorretaje ResidencialÎncă nu există evaluări
- How To Execute Linux Command by ABAP ProgramDocument3 paginiHow To Execute Linux Command by ABAP ProgramEEEÎncă nu există evaluări
- Crafting Wearables - Blending Technology With Fashion (PDFDrive)Document229 paginiCrafting Wearables - Blending Technology With Fashion (PDFDrive)gopika100% (2)
- Internet of ThingsDocument243 paginiInternet of ThingsWallie BillingsleyÎncă nu există evaluări
- Internet of Things For Smart Healthcare: Technologies, Challenges, and OpportunitiesDocument24 paginiInternet of Things For Smart Healthcare: Technologies, Challenges, and OpportunitiesSriharsha SarmaÎncă nu există evaluări
- Technology in The Construction IndustryDocument5 paginiTechnology in The Construction IndustryGiancarlo GonzagaÎncă nu există evaluări
- Commercializing Process TechnologiesDocument11 paginiCommercializing Process TechnologiesBramJanssen76Încă nu există evaluări
- LAB3.2 - Connecting Windows Host Over iSCSI With MPIODocument13 paginiLAB3.2 - Connecting Windows Host Over iSCSI With MPIOwendy yohanesÎncă nu există evaluări
- Risk Assessment - ElectricalDocument6 paginiRisk Assessment - ElectricalFawaaz KhurwolahÎncă nu există evaluări
- MLT526Rev 11-02Document662 paginiMLT526Rev 11-02Razvan Mitru100% (2)
- GRT8 M Instruction ManualDocument2 paginiGRT8 M Instruction ManualJosé Antonio Vega SimónÎncă nu există evaluări
- DSE8610 MKII Installation Instructions PDFDocument2 paginiDSE8610 MKII Installation Instructions PDFManuel Ortiz Galán100% (1)
- 12 TriesDocument10 pagini12 TriesNikhil 20528Încă nu există evaluări
- Presented By:: Kemal Muhammet Akkaya Sr. Instrument Engineer Humod M. Al-Shammari Maintenance SuperintendentDocument54 paginiPresented By:: Kemal Muhammet Akkaya Sr. Instrument Engineer Humod M. Al-Shammari Maintenance Superintendentmaria neneng bulakÎncă nu există evaluări
- Interactive Schematic: This Document Is Best Viewed at A Screen Resolution of 1024 X 768Document17 paginiInteractive Schematic: This Document Is Best Viewed at A Screen Resolution of 1024 X 768vvvÎncă nu există evaluări
- Opa 396Document31 paginiOpa 396renatoÎncă nu există evaluări
- EMDocument24 paginiEMYi-Ting YehÎncă nu există evaluări
- Tide Power Products50HzDocument22 paginiTide Power Products50HzmaherÎncă nu există evaluări
- Catalog AP Merit Installer V4Document264 paginiCatalog AP Merit Installer V4BillÎncă nu există evaluări
- WPS, PQR, WPQDocument2 paginiWPS, PQR, WPQESL100% (1)
- OM Course OutlineDocument2 paginiOM Course OutlineSeid KassawÎncă nu există evaluări
- Student User Manual v8 1 PDFDocument23 paginiStudent User Manual v8 1 PDFdaliaÎncă nu există evaluări
- Big Data Analytics in Supply Chain Management Between 2010 and 2016Document12 paginiBig Data Analytics in Supply Chain Management Between 2010 and 2016Kuldeep LambaÎncă nu există evaluări
- Approach of Image Processing in Diagnosis and Medication of Fungal Infections in Pet AnimalsDocument15 paginiApproach of Image Processing in Diagnosis and Medication of Fungal Infections in Pet AnimalsJohn SnowÎncă nu există evaluări
- Forage Compactor 7700: Part of The FC7000 Series of Hay PressesDocument4 paginiForage Compactor 7700: Part of The FC7000 Series of Hay PressesAbimelec TaipeÎncă nu există evaluări
- Er Shutdown For 15.12.21 Rev1Document8 paginiEr Shutdown For 15.12.21 Rev1Gitesh PatelÎncă nu există evaluări
- 4804 4Document11 pagini4804 4abhaybhosaleÎncă nu există evaluări
- Duralife CeDocument2 paginiDuralife CeVade ilustreÎncă nu există evaluări
- Asphalt and Asphalt Mixtures PPT2023Document53 paginiAsphalt and Asphalt Mixtures PPT2023Brian ReyesÎncă nu există evaluări