Documente Academic
Documente Profesional
Documente Cultură
A Comparative Study of The Big Five ISMS
Încărcat de
Jeya Shree Arunjunai RajTitlu original
Drepturi de autor
Formate disponibile
Partajați acest document
Partajați sau inserați document
Vi se pare util acest document?
Este necorespunzător acest conținut?
Raportați acest documentDrepturi de autor:
Formate disponibile
A Comparative Study of The Big Five ISMS
Încărcat de
Jeya Shree Arunjunai RajDrepturi de autor:
Formate disponibile
See discussions, stats, and author profiles for this publication at: https://www.researchgate.
net/publication/228444915
Information Security Management System Standards: A Comparative Study of
the Big Five
Article · January 2011
CITATIONS READS
82 5,926
3 authors:
Heru Susanto Mohammad Nabil Almunawar
Indonesian Institute of Sciences Universiti Brunei Darussalam
82 PUBLICATIONS 282 CITATIONS 103 PUBLICATIONS 909 CITATIONS
SEE PROFILE SEE PROFILE
Yong Chee Tuan
YES
9 PUBLICATIONS 151 CITATIONS
SEE PROFILE
Some of the authors of this publication are also working on these related projects:
Big Data Technology for Health Innovation View project
All content following this page was uploaded by Heru Susanto on 23 May 2014.
The user has requested enhancement of the downloaded file.
International Journal of Electrical & Computer Sciences IJECS-IJENS Vol: 11 No: 05 23
Information Security Management System Standards:
A Comparative Study of the Big Five
Heru Susanto12, Mohammad Nabil Almunawar1 and Yong Chee Tuan1
1 2
FBEPS, University of Brunei The Indonesian Institute of Sciences
Information System Group Information Security & IT Governance Research Group
susanto.net@gmail.com & 10h0103@ubd.edu.bn heru.susanto@lipi.go.id
Abstract. -- It cannot be denied that nowadays information is a
very important asset for any modern organization. Therefore
protecting its security is very important and becoming a top
priority for many organizations. Unfortunately there is no
single formula that can guarantee 100% of information security.
Therefore there is a need for a set of benchmarks or standards
to ensure the best security practices are adopted and an
adequate level of security is attained. In this paper, authors
introduce various information security standards briefly and
then provide a comparative study for major information
security standards, namely ISO27001, BS 7799, PCIDSS, ITIL
and COBIT. The study will provide a picture of the
position and specialization of each standard, adoption by
countries and their usability levels.
Keywords– ISO27001, BS7799, PCIDSS, ITIL, COBIT, ISMS,
Figure 1. Activities of unidentified user as potential attack and threat to
Information Security, PDCA organization
I. INTRODUCTION Since information security has a very important role in
supporting the activities of the organization, we need a standard
Information is the lifeblood of organizations, a vital
or benchmark which regulates governance over information
business asset in today’s Information Technology (IT) -enabled
security. Several private and government organizations
world. Access to high-quality, complete, accurate and up-to-
developed standards bodies whose function is to setup
date information is vital in supporting managerial decision-
benchmarks, standards and in some cases, legal regulations on
making process that leads to sound decisions. Thus, securing
information security to ensure that an adequate level of security
information system resources is extremely important to ensure
is preserved, to ensure resources used in the right way, and to
that the resources are well protected. Information security is not
ensure the best security practices adopted in an organization.
just a simple matter of having usernames and passwords [5].
There are several standards for IT Governance which leads to
Regulations and various privacy / data protection policy impose
information security such as PRINCE2, OPM3, CMMI,
a raft of obligations to organizations [6]. Meanwhile viruses,
P-CMM, PMMM, ISO27001, BS7799, PCIDSS, COSO, SOA,
worms, hackers, phishers and social engineers threaten
ITIL and COBIT.
organizations on all sides. Hackers or sometimes we call edit by
However, some of these standards are not well adopted by
unidentified user is likely to cause huge losses for an
the organizations, with a variety of reasons. In this paper we
organization [figure 1], such as by theft of customer data, spy
will discuss the big five of ISMS standards, widely used
on business strategy, for the benefit of competitors [7]. It is
standards for information security. The big five are ISO27001,
imperative for organizations to use an information security
BS 7799, PCIDSS, ITIL and COBIT. This comparative study
management system (ISMS) to effectively manage their
conducted to determine their respective strengths, focus, main
information assets. ISMS is basically consist of sets of policies
components and their adoption based on ISMS.
put place by an organization to define, construct, develop and
maintain security of their computer based on hardware and II. ISMS STANDARDS
software resources. These policies dictate the way in which
computer resources can be used. This section we give an overview of the big five ISMS
standards; ISO27001, BS7799, PCIDSS, ITIL and COBIT. The
overview includes profile and methodology used in each
113505-6969 IJECS-IJENS © October 2011 IJENS
IJENS
International Journal of Electrical & Computer Sciences IJECS-IJENS Vol: 11 No: 05 24
standard in implementing ISMS for organizations. These security management." The second part of BS7799 was first
overviews will help readers easily understand functions, published by BSI in 1999, known as BS 7799 Part 2, titled
behaviors and position of each on the big figure and whole "Information Security Management Systems - Specification with
ISMS’s strategies. guidance for use", BS 7799-2 focused on how to implement
ISMS, referring to the information security management
structure and controls identified in BS 7799-2, which later
II.1. ISO27001
became ISO 27001. The 2002 version of BS 7799-2 introduced
the Plan-Do-Check-Act (PDCA) (Deming quality assurance
ISO, founded on February 23, 1947, promulgates worldwide
model) [figure 3], aligning it with quality standards such as ISO
proprietary industrial and commercial standards, has
9000. BS 7799 Part 2 was adopted by ISO as ISO 27001 in
headquarters in Geneva, Switzerland [8]. It has 163 national
November 2005 [16].
members out of the 203 total countries in the world [figure 2].
The international standard of ISO 27001 specifies the
requirements for establishing, implementing, operating,
monitoring, reviewing, maintaining and improving a
documented ISMS within an organization [25].
Figure 3. PDCA Model on BS 7799
II.3. PCIDSS
The Payment Card Industry Data Security Standard
(PCIDSS) is a worldwide information security standard defined
by the Payment Card Industry Security Standards Council. The
standard was created to help industry organizations processes
card payments and to prevent credit card fraud through
increased controls around data and its exposure to compromise.
The standard applies to all organizations that hold, process, or
Figure 2. Map of members of ISO (by IchwanPalongengi) exchange cardholder information from any card branded with
the logo of one of the card brands [20], [figure 4].
It designed to ensure the selection of adequate and
proportionate security controls to protect information assets.
This standard is usually applicable to all types of organizations,
either private or public organizations. The standard introduces
a cyclic model known as the “Plan-Do-Check-Act” (PDCA)
model [1], aims to establish, implement, monitor and
improve the effectiveness of an organization’s ISMS [2].
II.2. BS 7799
BS 7799 was a standard originally published by British
Standard Institution (BSI) Group in 1995. It was written by the
United Kingdom Government's Department of Trade and Figure 4. Transaction security models of PCIDSS
Industry (DTI), and consisted of several parts [13], [16]. The
first part, containing the best practices for ISMS, was revised in Validation of compliance can be performed either internally
1998, which was eventually adopted by ISO as ISO17799, or externally, depending on the volume of card transactions, but
"Information Technology - Code of practice for information regardless of the size of the organization, compliance must be
113505-6969 IJECS-IJENS © October 2011 IJENS
IJENS
International Journal of Electrical & Computer Sciences IJECS-IJENS Vol: 11 No: 05 25
assessed annually. Organizations handling large volumes of the IT Governance Institute (ITGI) in 1996 [9]. They believe
transactions must have their compliance assessed by an that it is a set of practices (framework) for IT management.
independent assessor called by Qualified Security Assessor COBIT is an IT governance framework and supporting toolset
(QSA) [21], while companies handling smaller volumes have that allows managers to bridge the gap between control
the option of demonstrating compliance via a Self-Assessment requirements, technical issues, business risks, and security
Questionnaire (SAQ). issues. COBIT has five IT Governance areas of concentration
[12], [23]:
II.4. ITIL
• Strategic alignment focuses on ensuring the linkage of
business and IT plans; defining, maintaining and validating
The Information Technology Infrastructure Library (ITIL)
the IT value proposition; and aligning IT operations with
concept emerged in the 1980s, when the British government
enterprise operations.
determined that the level of IT service quality provided to them
was not sufficient [19]. ITIL is a set of concepts and practices • Value delivery is about executing the value proposition
for Information Technology Services Management (ITSM), throughout the delivery cycle, ensuring that IT delivers the
Information Technology (IT) development and IT operations, promised benefits against the strategy, concentrating on
which has parts focus on security. optimizing costs and proving the intrinsic value of IT.
• Resource management is about the optimal investment
and the proper management of critical IT resources:
applications, information, infrastructure and people.
• Risk managementis a clear understanding of the
enterprise’s appetite for risk, understanding of compliance
requirements, and transparency into the organization.
• Performance measurement tracks and monitors strategy
implementation, project completion, resource usage,
process performance and service delivery, for example,
balanced scorecards that translate strategy into action to
achieve goals measurable beyond conventional accounting.
III. FEATURES
Figure 5. The ITIL components Alfantookh2009 [2], defined 11 essential control, called by
11EC, that should be implemented by an organization, as
The ITIL originated as a collection of books, each covering requirements and compliance of the information security
a specific practice within IT Service Management, was built criteria by the standard body of ISMS [2], [6] due to these
around a process-model based view of controlling and features as basis of parameters and benchmarks for fulfillment
managing operations often credited to W. Edwards Deming and of information security which is most comprehensively cover
his plan-do-check-act (PDCA) cycle [4], as IT Services all aspects must be owned, these 11EC are [8], [24]:
Management Standards and Best Practices [18] contains of 8
main components[figure 5], they are: Service Support, Service 1. Information Security Policy: how an institution expresses
Delivery, ICT Infrastructure Management, Security its intent with emphasized to information security, means
Management, Application Management, Software Asset by which an institution's governing body expresses its
Management, Planning to Implement Service Management, intent to secure information, gives direction to
Small-Scale Implementation. management and staff and informs the other stakeholders
of the primacy of efforts.
II.5. COBIT
2. Communications and Operations Management: defined
The Control Objectives for Information and related
policy on security in the organization, in reducing security
Technology (COBIT) is a certification created by ISACA and
113505-6969 IJECS-IJENS © October 2011 IJENS
IJENS
International Journal of Electrical & Computer Sciences IJECS-IJENS Vol: 11 No: 05 26
risk and ensuring correct computing, including operational
procedures, controls, and well-defined responsibilities. 11. Compliance: these issues necessarily are divided into two
areas; the first area involves compliance with the myriad
3. Access Control: is a system which enables an authority to laws, regulations or even contractual requirements which
control access to areas and resources in a given physical are part of the fabric ofevery institution. The second area is
facility or computer-based information system. compliance with information security policies, standards
and processes.
4. Information System Acquisition, Development and
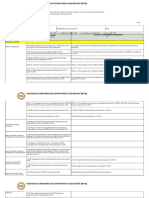
Maintenance: an integrated process that defines Table 1 below we showed up head to head comparisons on
boundaries and technical information systems, beginning the big five ISMS standards deal with 11EC of information
with the acquisition, and development and the last is the security.
maintenance of information systems.
5. Organization of Information Security: is a structure ISO BS PCIDSS ITIL COBIT
owned by an organization in implementing information 27001 7799 V2.0 V4.0 V4.1
1. Information
security, consists of; management commitment to
Security Policy
√ √ √ √ √
information security, information security co-ordination,
authorization process for information processing facilities. Communications
Two major directions: internal organization, and external 2. and Operations √ √ √ ● √
parties. Management
3. Access Control √ √ √ √ √
6. Asset Management: is based on the idea that it is
important to identify, track, classify, and assign ownership
Information
for the most important assets to ensure they are adequately
Systems
protected. 4. Acquisition, √ √ √ ● √
Development and
7. Information Security Incident Management: is a program Maintenance
that prepares for incidents. From a management
perspective, it involves identification of resources needed Organization of
5. Information √ √ √ √ √
for incident handling. Good incident management will also
help with the prevention of future incidents. Security
6. Asset
8. Business Continuity Management: to ensure continuity of Management
√ √ √ √ √
operations under abnormal conditions. Plans promote the Information
readiness of institutions for rapid recovery in the face of 7. Security Incident √ ● √ √ √
adverse events or conditions, minimize the impact of such Management
circumstances, and provide means to facilitate functioning
during and after emergencies. Business
8. Continuity √ √ √ √ √
Management
9. Human Resources Security: to ensure that all employees
(including contractors and user of sensitive data) are Human
9. Resources √ √ √ ● √
qualified for and understand their roles and responsibilities
of their job duties and that access is removed once Security
employment is terminated. Physical and
10. Environmental √ √ √ ● √
10. Physical and Environmental Security: to measures taken Security
to protect systems, buildings, and related supporting
11. Compliance √ √ √ √ √
infrastructure against threats associated with their physical
environment, buildings and rooms that house information
and information technology systems must be afforded
Tabel 1. Features of Big Five of ISMS Standard
appropriate protection to avoid damage or unauthorized
access to information and systems.
113505-6969 IJECS-IJENS © October 2011 IJENS
IJENS
International Journal of Electrical & Computer Sciences IJECS-IJENS Vol: 11 No: 05 27
IV. COMPARISONSOF THEBIG FIVE
Profile of each standard is presented here to provide a general overview and summaryof the relevant standard on their respective
positions which is currently most widely used worldwide [table 2].
ISO 27001 BS 7799 PCIDSS ITIL COBIT
ISO is a non- is an IT governance
ITIL is the abbreviation for
governmental framework and supporting
the guideline IT
organization that forms a is a worldwide information toolset that allows
BS Standards is the UK's Infrastructure Library,
bridge between the public security standard defined managers to bridge the
National Standards Body developed by CCTA, now
and private sectors. On the by the Payment Card gap between control
(NSB) and was the world's the OGC (Office
one hand, many of its Industry Security requirements, technical
first. BS Standards works of Governance Commerce)
member institutes are part Standards Council. The issues and business risks.
with manufacturing and in Norwich (England)
of the governmental standard was created to COBIT enables clear
Profile of service industries, developed on behalf of the
structure of their countries, help industry organizations policy development and
Standards businesses, governments British government. The
or are mandated by their that process card payments good practice for IT
and consumers to facilitate main focus of
government; also other prevent credit card fraud control throughout
the production of British, the development was on
members have their roots through increased controls organizations. COBIT
European and mutual best practices for
uniquely in the private around data and its emphasizes regulatory
international standards all British government
sector, having been set up exposure to compromise compliance, helps
[13] data centers to ensure
by national partnerships of [20] organizations to increase
comparable services
industry associations the value attained from IT
[19]
[8] [9]
VisaCard, MasterCard, The Central Computer and
United Kingdom American Express, Telecommunications Information Systems Audit
delegates from 25 Government's Department Discover Information and Agency (CCTA), now and Control Association
Initiated by countries of Trade and Industry Compliance, and the called the Office of (ISACA) and the IT
[8] (DTI) JCBData Security Government Commerce Governance Institute
[13] Program (OGC)– UK (ITGI)–USA
[20] [19] [9],[14]
Launched
February 23, 1947 1995 15 December 2004 1980s 1996
on
18,500 International 6 main components on 8 main components + 6 main components on
Standards & 27,000 active standards
Standards standard 5 components version 3 standard
Components [13],[16]
[8],[15],[17] [20],[21] [10],[18], [19] [10],[22],[23]
Certified Information
Systems Auditor™
(CISA®)
Certified Information
Security Manager®
Certificate Certificate of Certificate of Certificate of PCI-DSS Certificate of ITIL (CISM®)
Name ISO 27000 Series BS 7799: 1-2 Compliance Compliance Certified in the
Governance of Enterprise
IT® (CGEIT® )
Certified in Risk and
Information Systems
Control TM (CRISCTM)
Information and Data
Transaction Security on
Scope Information Security Information Security Service Management IT Governance
debit, credit, prepaid,
e-purse, ATM, and POS
163 national members out 110 national members out 125 countries out of the
Usability of the 203 total countries of the 203 total countries 203 total countries in the 50 international chapters 160 countries
in the world in the world world
Tabel 2. Profile of Big Five of ISMS Standards
113505-6969 IJECS-IJENS © October 2011 IJENS
IJENS
International Journal of Electrical & Computer Sciences IJECS-IJENS Vol: 11 No: 05 28
Substantively numbers of active standard on BS is 50% more
than the standard that is owned by ISO, and also more than
PCIDSS, ITIL and COBIT, but other reason that leads
organization not implemented BS, tend to preferred ISO,
PCIDSS, COBIT is due in some part BS using benchmarks
Europe or commonly known as BSEN (British Standard Europe
Norm) [13], inauspiciously it would confuse stakeholders,
which one is better, BS or BSEN, local or regional, such as
pouring the same water in two glasses of different shapes.
Stakeholders prefer a more flexible standard, more focus and
have not two different terms for the same issues; thus, ISO,
PCIDSS, COBIT become more consideration as best choice.
Figure 6. Country as initiator of standard
Nowadays, it is very important for a standard, accepted and
recognized as global benchmarking tools, marked by number of
county which initiated for establishment of an organization deal
with [figure 6]. ISO (25 countries) BS (1 country) PCIDSS
(1 country), ITIL (1 country), and COBIT (1 country).
[Figure7] ISO's most widely used in globally by163 countries,
compared with BS (110), PCIDSS (125), ITIL (50) and COBIT
(160). Indication descript us that ISO is more easily
implemented, stakeholders (clients, suppliers, customers and
management) is easier to recognize, also it has appropriate
platform in an organization deal with, than four others security
standards.
Figure 8. Position of each standard
The main focus on information security, ISO27001 and BS7799
have similar characteristics, since ISO27001 adopted from
BS7799, with improvements and additions emphasized on the
strength of ISMS from various aspects, while the three others
also focus on IT governance and Project Management
[figure 8].
Figure 7. Usability level of standards
113505-6969 IJECS-IJENS © October 2011 IJENS
IJENS
International Journal of Electrical & Computer Sciences IJECS-IJENS Vol: 11 No: 05 29
V. CONCLUSION REMARKS [6] Heru Susanto & Fahad bin Muhaya. Multimedia Information Security
Architecture. @ IEEE. 2010.
Each standard playing its own role and position in [7] Heru Susanto, Mohammad Nabil Almunawar & Yong Chee Tuan.
I-SolFramework View on ISO 27001. Information Security Management
implementing ISMS, several standards such as ISO 27001 and System: Refinement Integrated Solution’s Six Domains. Journal of
BS 7799 focusing on information security management system Computer, Asian Transaction. July 2011.
as main domain and their focus on, while PCIDSS focus on [8] ISO History and Definition. www.iso.org
information security relating to business transactions and smart [9] IT Governance Institute. COBIT 4.1 Excerpts. 2007. Rolling Meadows,
IL 60008 USA
card, then ITIL and COBIT focuses on information security and [10] IT Governance Institute. Mapping of ITIL v3 with COBIT 4.1. 2008.
its relation with the Project management and IT Governance Rolling Meadows, IL 60008 USA
[figure 8]. Refers to the usability of standards in global, [11] The Government of the Hong Kong. An Overview of Information
indicated that ISO (27001) leading than four other standards Security Standards. 2008. Hongkong.
[12] Overview on COBIT.
especially on ISMS, therefore it described us the standard is http://www.benchmarklearning.com/COMMUNITIES/ITIL/cobit.aspx
more easily implemented and well recognized by stakeholders [13] Overview on British Standard. http://www.bsigroup.com/en/Standards-
(top management, staff, suppliers, customers/clients, and-Publications/About-BSI-British-Standards/
regulators). We can analogous ISO (27001) is like a global [14] http://www.isaca.org/KnowledgeCenter/COBIT/Pages/Overview.aspx
[15] http://www.iso.org/iso/about/discover-iso_isos-name.htm
language in standards and benchmarking on ISMS, such as [16] http://www.isms-guide.blogspot.com/2007/11/key-components-of-
English as an international language, with level of usability and standard-bs-7799-iso.html
trust reach more than 80% of the world [figure 2]. [17] http://www.iso.org/iso/about.htm
[18] http://www.itil.org/en/vomkennen/itil/ueberblick/index.php
[19] http://www.itil-
officialsite.com/faq.aspx?category=General+FAQs&btnSubmit=Open
VI. RECOMMENDATION AND FUTURE RESEARCH [20] https://www.pcisecuritystandards.org/security_standards/index.php
[21] http://www.retrievernpc.com/cms/pci-compliance/certificate-of-pci-dss-
As the international language of standards and recognized compliance/
globally, authors recommend further research in refinement of [22] http://technet.microsoft.com/en-us/library/ff758651.aspx
ISO (27001). Purposed of refinement is to make more easily [23] http://searchsecurity.techtarget.com/feature/Introduction-to-COBIT-for-
understood, implemented, and easily measured in an SOX-compliance
[24] https://wiki.internet2.edu/confluence/display/itsg2/
organization by stakeholders. Refinement expected translating Human+Resources+Security+(ISO+8)
and interpreting high level language of terms, technical nature [25] http:// wikipedia.org/wiki/ISO
and details on the subject of ISMS assessments to Heru Susanto is a researcher at The Indonesian Institute of Sciences,
understandable human being parlance. Information Security & IT Governance Research Group, also was working at
Prince Muqrin Chair for Information Security Technologies, Information Security
Research Group, King Saud University. He received BSc in Computer Science
from Bogor Agriculture University, in 1999 and MSc in Computer Science
VII. ACKNOWLEDGMENT from King Saud University, nowadays he as PhD Candidate in Information
System from the University of Brunei Darussalam. Heru has published many
This paper is one part of the big research which topic of papers in refereed journals as well as international conferences.
framework for refinement information security management Mohammad Nabil Almunawar is a senior lecturer at Faculty of Business,
system as tools of integrated solutions. This research is Economics and Policy Studies, University of Brunei Darussalam. He received
master Degree (MSc Computer Science) from the Department of Computer
supported by FBEPS University of Brunei Darussalam (UBD), Science, University of Western Ontario, Canada in 1991 and PhD from the
The Indonesian Institute of Sciences and Prince Muqrin Chair University of New South Wales (School of Computer Science and Engineering,
(PMC) for IT Security, King Saud University (KSU). UNSW) in 1997. Dr Nabil has published many papers in refereed journals as
well as international conferences. He has many years teaching experiences in
the area computer and information systems. He was a respected consultant in
VIII. REFERENCES developing information systems for United Nations (WHO) projects, Central
Bank of Indonesia and some private companies. His overall research interest is
[1] Alan Calder and Setve Watkins. IT Governance – A Manager’s Guide to application of IT in Management and Electronic Commerce. He is also
Data Security and ISO 27001 and ISO 27002 interested in object-oriented technology, databases and multimedia retrieval.
[2] Abdulkader Alfantookh. An Approach for the Assessment of The Yong Chee Tuan is a senior lecturer at Faculty of Business, Economics and
Application of ISO 27001 Essential Information Security Controls. Policy Studies, University of Brunei Darussalam, has more than 20 years of
Computer Sciences, King Saud University. 2009 experience in IT, HRD, e-gov, environmental management and project
[3] Basie von Solms. 2005. Information Security Governance: COBIT or management. He received PhD in Computer Science from University of Leeds,
ISO 17799 or both? Computer&Security Journal. Elsevier.Science Direct UK, in 1994. He was involved in the drafting of the two APEC SME Business
[4] Basie von Solms. 2005. Information Security Governance – Compliance Forums Recommendations held in Brunei and Shanghai. He sat in the E-gov
Management vs Operational Management. Computer & Security Journal. Strategic, Policy and Coordinating Group from 2003-2007. He is the vice-chair
Elsevier, Science Direct of the Asia Oceanic Software Park Alliance. He has been appointed as the
[5] Basie von Solms & Rossouw von Solms. 2004. The 10 deadly sins of regular judge of the APICTA since 2001. He is the country representative in the
Information Security Management. Computer & Security 23(2004) 371- UNDP Digital Review Publications.
376. Elsevier Science Ltd.
113505-6969 IJECS-IJENS © October 2011 IJENS
IJENS
View publication stats
S-ar putea să vă placă și
- Information Security Management Standards - Compliance, Governance and Risk ManagementDocument9 paginiInformation Security Management Standards - Compliance, Governance and Risk ManagementbaekjungÎncă nu există evaluări
- Integration of ITIL V3 ISO 20000 and ISODocument18 paginiIntegration of ITIL V3 ISO 20000 and ISOmisjarw9600Încă nu există evaluări
- ISO27001 Information Security Management ArticleDocument6 paginiISO27001 Information Security Management Articletran duy tanÎncă nu există evaluări
- An Integrated System Theory for Information Security ManagementDocument6 paginiAn Integrated System Theory for Information Security ManagementmunierÎncă nu există evaluări
- Security by Compliance? A Study of Insider Threat Implications For Nigerian BanksDocument12 paginiSecurity by Compliance? A Study of Insider Threat Implications For Nigerian BanksakogoandrewÎncă nu există evaluări
- Can A Single Security Framework Address Information Security Risks AdequatelyDocument9 paginiCan A Single Security Framework Address Information Security Risks AdequatelybaekjungÎncă nu există evaluări
- A Balanced Information Security Maturity Model Based On ISO/IEC 27001:2013 and O-ISM3Document7 paginiA Balanced Information Security Maturity Model Based On ISO/IEC 27001:2013 and O-ISM3International Journal of Innovative Science and Research TechnologyÎncă nu există evaluări
- Seinio Tweulongelwa Ndeiluka - 2126922Document13 paginiSeinio Tweulongelwa Ndeiluka - 2126922Tate Ngeekepo Kemwiifaneni NdeilukaÎncă nu există evaluări
- Module 1 - IASDocument28 paginiModule 1 - IASKirito ZachariasÎncă nu există evaluări
- Information Security Management SystemDocument5 paginiInformation Security Management SystemMuhammad babarÎncă nu există evaluări
- ITSEAG - Secure Your Information CIODocument15 paginiITSEAG - Secure Your Information CIOEvan Chronixx TomlixÎncă nu există evaluări
- Information System Audit A Study For SecDocument4 paginiInformation System Audit A Study For SecDODY BUDI CAHYADIÎncă nu există evaluări
- Enterprise Cybersecurity PlanDocument14 paginiEnterprise Cybersecurity PlanIan Ndiba Mwangi100% (1)
- COBIT V S. ISO 27001Document3 paginiCOBIT V S. ISO 27001clu5t3r0% (1)
- Sustainability 14 01269Document20 paginiSustainability 14 01269Tugas SekolahÎncă nu există evaluări
- Jicce-18-39 Journal Q3 SOftware ISMS Nungky A CDocument10 paginiJicce-18-39 Journal Q3 SOftware ISMS Nungky A CNungky ChandraÎncă nu există evaluări
- 2009 - Encouraging Information Security Behaviors in Organizations Role of Penalties, Pressures and Perceived EffectivenessDocument12 pagini2009 - Encouraging Information Security Behaviors in Organizations Role of Penalties, Pressures and Perceived EffectivenessTomÎncă nu există evaluări
- An Approach To Information Security Management: Anene L. Nnolim, Annette L. SteenkampDocument9 paginiAn Approach To Information Security Management: Anene L. Nnolim, Annette L. SteenkampJaved IqbalÎncă nu există evaluări
- MIS Term Paper... EWU - BD - Niloy546Document46 paginiMIS Term Paper... EWU - BD - Niloy546niloyÎncă nu există evaluări
- Assessing Information Security CultureDocument12 paginiAssessing Information Security CultureTomÎncă nu există evaluări
- Final Work Miss Jennita AppanahDocument6 paginiFinal Work Miss Jennita AppanahVarun MohunahÎncă nu există evaluări
- Has_your_organization_compliance_with_ISMS_A_case_Document24 paginiHas_your_organization_compliance_with_ISMS_A_case_iqbalÎncă nu există evaluări
- Information Security Policies: A Review of Challenges and in Uencing FactorsDocument8 paginiInformation Security Policies: A Review of Challenges and in Uencing FactorsBruno S ZanellaÎncă nu există evaluări
- Model Design of Information Security Governance Assessment With Collaborative Integration of Cobit 5 and ItilDocument6 paginiModel Design of Information Security Governance Assessment With Collaborative Integration of Cobit 5 and ItilEduardo RosalesÎncă nu există evaluări
- Accountability For Information Security Roles and Responsibilities Part 1 - Joa - Eng - 1019Document10 paginiAccountability For Information Security Roles and Responsibilities Part 1 - Joa - Eng - 1019Koyel BanerjeeÎncă nu există evaluări
- Security DocumentationDocument14 paginiSecurity DocumentationGowtham ManivelÎncă nu există evaluări
- Implementing An ISMS Participant Guide V1.1Document164 paginiImplementing An ISMS Participant Guide V1.1William Anderson100% (3)
- ISMF-whitepaper 2018Document7 paginiISMF-whitepaper 2018Katyy VerdezotoÎncă nu există evaluări
- Paper1 - Evaluation and Comparison of COBIT, ITIL and ISO 27k1 - 2 Standards Within The Framework of Information SecurityDocument4 paginiPaper1 - Evaluation and Comparison of COBIT, ITIL and ISO 27k1 - 2 Standards Within The Framework of Information SecuritypmdrnoraÎncă nu există evaluări
- Security Leader Insights for Information Protection: Lessons and Strategies from Leading Security ProfessionalsDe la EverandSecurity Leader Insights for Information Protection: Lessons and Strategies from Leading Security ProfessionalsBob FahyÎncă nu există evaluări
- Antivirus Control PolicyDocument10 paginiAntivirus Control PolicyjanÎncă nu există evaluări
- Pakistani Bank InfoSec Risk AssessmentDocument12 paginiPakistani Bank InfoSec Risk AssessmentNaji HalabiÎncă nu există evaluări
- Information Technology and Cyber SecurityDocument250 paginiInformation Technology and Cyber Securitycn8q8nvnd5Încă nu există evaluări
- Iso 27001 DissertationDocument7 paginiIso 27001 DissertationWriteMyPapersSingapore100% (1)
- Wireless Network Makes Information Access Much EasierDocument3 paginiWireless Network Makes Information Access Much Easierapi-6929342Încă nu există evaluări
- Chapter 1 - Discussion NotesDocument5 paginiChapter 1 - Discussion NotesBlessed AramayÎncă nu există evaluări
- Cyber Security FrameworksDocument107 paginiCyber Security Frameworksraghunandhan.cvÎncă nu există evaluări
- RohitDocument75 paginiRohitRobin PalanÎncă nu există evaluări
- Five pillars network securityDocument11 paginiFive pillars network securityClarancè AnthònyÎncă nu există evaluări
- A Short Literature Review in Information Systems Security Management ApproachesDocument5 paginiA Short Literature Review in Information Systems Security Management ApproachesgvzftaamÎncă nu există evaluări
- AUDCIS Information SecurityDocument21 paginiAUDCIS Information SecurityBea GarciaÎncă nu există evaluări
- Information Security Baselines: Kevin J. FitzgeraldDocument5 paginiInformation Security Baselines: Kevin J. FitzgeraldFarrel Haggi Tuzahra RamadhaniÎncă nu există evaluări
- IAM Healthscope ReportDocument6 paginiIAM Healthscope Reporteinstein kavitaÎncă nu există evaluări
- 1 PB61Document8 pagini1 PB61alexÎncă nu există evaluări
- Understanding Comprehensive Database Security: Technical White PaperDocument36 paginiUnderstanding Comprehensive Database Security: Technical White PapertemptigerÎncă nu există evaluări
- Comparing ISO/IEC 27001 and IT Baseline Protection (IT-GrundschutzDocument3 paginiComparing ISO/IEC 27001 and IT Baseline Protection (IT-GrundschutzXenosÎncă nu există evaluări
- Reaserch Paper On EA SecurityDocument4 paginiReaserch Paper On EA Securityrachna rathoreÎncă nu există evaluări
- ISO/IEC 27001 and IT Baseline Protection (IT-Grundschutz) : Amgad Mahmoud, Felix Schmidt, Gerd SiebertDocument3 paginiISO/IEC 27001 and IT Baseline Protection (IT-Grundschutz) : Amgad Mahmoud, Felix Schmidt, Gerd SiebertXenosÎncă nu există evaluări
- A Security Audit Framework To Manage Information SDocument5 paginiA Security Audit Framework To Manage Information SAditi KashetwarÎncă nu există evaluări
- IsmsDocument5 paginiIsmsNaveen ShenoiÎncă nu există evaluări
- ICTCYS606 Student Assessment Tasks and Project PortfolioDocument29 paginiICTCYS606 Student Assessment Tasks and Project Portfolioakashpandet6Încă nu există evaluări
- How Does IS Fit in Governance FrameworkDocument2 paginiHow Does IS Fit in Governance FrameworkFernando Sánchez OlveraÎncă nu există evaluări
- IT Security Architecture & Leadership, 24 - 27 November 2013 Dubai UAEDocument4 paginiIT Security Architecture & Leadership, 24 - 27 November 2013 Dubai UAE360 BSIÎncă nu există evaluări
- Administrative Security and Machine Learning RulesDocument20 paginiAdministrative Security and Machine Learning RulesKennedy Gitonga ArithiÎncă nu există evaluări
- COBIT5 and InfoSec PresentationDocument48 paginiCOBIT5 and InfoSec Presentationud budiÎncă nu există evaluări
- Security Management - EditedDocument9 paginiSecurity Management - EditedIsaack ChirchirÎncă nu există evaluări
- FCNS PDFDocument132 paginiFCNS PDFAri GunawanÎncă nu există evaluări
- CSP 13 Block 03Document84 paginiCSP 13 Block 03Sri DeviÎncă nu există evaluări
- Information Security Policy Development and Implementation: The What, How and WhoDocument16 paginiInformation Security Policy Development and Implementation: The What, How and WhoHenrique GuapoÎncă nu există evaluări
- Information Security Gap Analysis Based On ISO 27001: 2013 Standard: A Case Study of The Yemeni Academy For Graduate Studies, Sana'a, YemenDocument11 paginiInformation Security Gap Analysis Based On ISO 27001: 2013 Standard: A Case Study of The Yemeni Academy For Graduate Studies, Sana'a, YemenJeya Shree Arunjunai RajÎncă nu există evaluări
- Iaas Journey To The Cloud 3097328 PDFDocument14 paginiIaas Journey To The Cloud 3097328 PDFJeya Shree Arunjunai RajÎncă nu există evaluări
- Information Security Gap Analysis Based On ISO 27001: 2013 Standard: A Case Study of The Yemeni Academy For Graduate Studies, Sana'a, YemenDocument11 paginiInformation Security Gap Analysis Based On ISO 27001: 2013 Standard: A Case Study of The Yemeni Academy For Graduate Studies, Sana'a, YemenJeya Shree Arunjunai RajÎncă nu există evaluări
- Information Security Gap Analysis Based On ISO 27001: 2013 Standard: A Case Study of The Yemeni Academy For Graduate Studies, Sana'a, YemenDocument11 paginiInformation Security Gap Analysis Based On ISO 27001: 2013 Standard: A Case Study of The Yemeni Academy For Graduate Studies, Sana'a, YemenJeya Shree Arunjunai RajÎncă nu există evaluări
- Fulltext01 PDFDocument74 paginiFulltext01 PDFJeya Shree Arunjunai RajÎncă nu există evaluări
- 13 Effective Security Controls For ISO 27001 ComplianceDocument20 pagini13 Effective Security Controls For ISO 27001 CompliancemahyarxÎncă nu există evaluări
- Collaborative Process Development Using Semantic M PDFDocument11 paginiCollaborative Process Development Using Semantic M PDFJeya Shree Arunjunai RajÎncă nu există evaluări
- IsoDocument66 paginiIsoEdwin PariÎncă nu există evaluări
- ISO 27001:2013 Statement of ApplicabilityDocument21 paginiISO 27001:2013 Statement of Applicabilityketanms70% (10)
- Master Thesis: University of PiraeusDocument47 paginiMaster Thesis: University of PiraeusJeya Shree Arunjunai RajÎncă nu există evaluări
- Guide To ISO 27001: UAE Case Study: July 2012Document20 paginiGuide To ISO 27001: UAE Case Study: July 2012Jeya Shree Arunjunai RajÎncă nu există evaluări
- Context-Aware Identity Management Framework: November 2018Document41 paginiContext-Aware Identity Management Framework: November 2018Jeya Shree Arunjunai RajÎncă nu există evaluări
- Banking-Financial Services Networks PDFDocument1 paginăBanking-Financial Services Networks PDFJeya Shree Arunjunai RajÎncă nu există evaluări
- ISO 27001 Statement of ApplicabilityDocument4 paginiISO 27001 Statement of ApplicabilitydaddyfooksÎncă nu există evaluări
- Access ManagementDocument20 paginiAccess ManagementJeya Shree Arunjunai RajÎncă nu există evaluări
- ISO 27001 Annex A.9 - Access Control PDFDocument12 paginiISO 27001 Annex A.9 - Access Control PDFJeya Shree Arunjunai Raj0% (1)
- Suggesting The Best Information Security Management System For Palestinian E-GovernmentDocument74 paginiSuggesting The Best Information Security Management System For Palestinian E-GovernmentJeya Shree Arunjunai RajÎncă nu există evaluări
- Business Case For An ISMS Whitepaper PDFDocument54 paginiBusiness Case For An ISMS Whitepaper PDFJeya Shree Arunjunai RajÎncă nu există evaluări
- How The ISO 27001 Revision Affects Your Risk Management ProcessDocument9 paginiHow The ISO 27001 Revision Affects Your Risk Management ProcessJeya Shree Arunjunai RajÎncă nu există evaluări
- ISMSDocument11 paginiISMSAnil AppayannaÎncă nu există evaluări
- Identity Management Systems: A Comparative Analysis: January 2018Document17 paginiIdentity Management Systems: A Comparative Analysis: January 2018Jeya Shree Arunjunai RajÎncă nu există evaluări
- chp:10.1007/978 3 319 26961 0 - 9 PDFDocument20 paginichp:10.1007/978 3 319 26961 0 - 9 PDFJeya Shree Arunjunai RajÎncă nu există evaluări
- Developing An Information Security Management System: Karjalainen, MikaDocument36 paginiDeveloping An Information Security Management System: Karjalainen, MikaJeya Shree Arunjunai RajÎncă nu există evaluări
- ISO 27001 ChecklistDocument32 paginiISO 27001 ChecklistVishal Vasu100% (4)
- ISO 15693-2 Radio Frequency PowerDocument16 paginiISO 15693-2 Radio Frequency PowerJeya Shree Arunjunai Raj100% (1)
- ISO 15693-1 Physical CharacteristicsDocument11 paginiISO 15693-1 Physical CharacteristicsJeya Shree Arunjunai RajÎncă nu există evaluări
- 2 PDFDocument10 pagini2 PDFJeya Shree Arunjunai RajÎncă nu există evaluări
- 2 PDFDocument10 pagini2 PDFJeya Shree Arunjunai RajÎncă nu există evaluări
- Java CourseguideDocument203 paginiJava CourseguideRishi gameingÎncă nu există evaluări
- Java CourseguideDocument203 paginiJava CourseguideRishi gameingÎncă nu există evaluări
- ISO Certification in JordanDocument16 paginiISO Certification in JordanZoya AbdulÎncă nu există evaluări
- Business Law Assignment Questions (Class E) - January 2024 IntakeDocument5 paginiBusiness Law Assignment Questions (Class E) - January 2024 Intakewtote404Încă nu există evaluări
- Welder Job Clearance Card for Ali QurbanDocument43 paginiWelder Job Clearance Card for Ali QurbanDhanush NairÎncă nu există evaluări
- IPCR Performance ReviewDocument32 paginiIPCR Performance ReviewDILG DipaculaoÎncă nu există evaluări
- Organistion StructureDocument67 paginiOrganistion Structureali hansiÎncă nu există evaluări
- Islamic Banks and Investment FinancingDocument29 paginiIslamic Banks and Investment FinancingAhmad FananiÎncă nu există evaluări
- The Waldorf Hilton Hotel Job Offered Contract LetterDocument3 paginiThe Waldorf Hilton Hotel Job Offered Contract LetterHIsham Ali100% (2)
- Blue Danube Si Green HydrobenDocument11 paginiBlue Danube Si Green HydrobenDiana AchimescuÎncă nu există evaluări
- Auditing IDocument58 paginiAuditing IBereket DesalegnÎncă nu există evaluări
- Create Invoice correction requestDocument7 paginiCreate Invoice correction requestdeepali ahireÎncă nu există evaluări
- Strategic Management MainDocument20 paginiStrategic Management MainAdityaÎncă nu există evaluări
- Business DirectoryDocument4 paginiBusiness DirectoryRegunathan PadmanathanÎncă nu există evaluări
- Uploads - Notes - Btech - 4sem - It - DBMS FRONT PAGE LAB MANUALDocument3 paginiUploads - Notes - Btech - 4sem - It - DBMS FRONT PAGE LAB MANUALKushÎncă nu există evaluări
- Architectural Record 2024-01Document124 paginiArchitectural Record 2024-01ricardoÎncă nu există evaluări
- 42-Electric Arc FurnacesDocument11 pagini42-Electric Arc Furnacessureshkumar908Încă nu există evaluări
- CHAPTER-1 Thesis GuideDocument19 paginiCHAPTER-1 Thesis GuideChristian Dior TirazonaÎncă nu există evaluări
- Daily Field Report FormDocument1 paginăDaily Field Report FormImran AmamiÎncă nu există evaluări
- Understanding Entrepreneurial Motivation TheoriesDocument31 paginiUnderstanding Entrepreneurial Motivation TheoriesCid AreÎncă nu există evaluări
- Qdoc - Tips - Kunci Jawaban Supply Chain Management Presales SpeDocument19 paginiQdoc - Tips - Kunci Jawaban Supply Chain Management Presales SpeEyuÎncă nu există evaluări
- Sdoc 02 10 SiDocument5 paginiSdoc 02 10 Siمحي الدين محمدÎncă nu există evaluări
- Income Statement 2014 2015: 3. Net Revenue 5. Gross ProfitDocument71 paginiIncome Statement 2014 2015: 3. Net Revenue 5. Gross ProfitThu ThuÎncă nu există evaluări
- Digital Marketing Freelance OpportunitiesDocument1 paginăDigital Marketing Freelance OpportunitiesSandeep JainÎncă nu există evaluări
- COPC Inc Overview PresentationDocument43 paginiCOPC Inc Overview Presentationpradip_sinha86% (7)
- Shahriar Zaman - MID ECO 1Document5 paginiShahriar Zaman - MID ECO 1Shahriar Zaman AsifÎncă nu există evaluări
- Chapter 6 Instructor - Managing A Global BusinessDocument22 paginiChapter 6 Instructor - Managing A Global BusinessYusuf ÇubukÎncă nu există evaluări
- Productivity, Efficiency and Economic Growth in Asia PacificDocument335 paginiProductivity, Efficiency and Economic Growth in Asia PacificZainudin Mohamed100% (1)
- E-Governance Challenges and Prospects in IndiaDocument13 paginiE-Governance Challenges and Prospects in Indiaakhil negiÎncă nu există evaluări
- Inside the Black Box: Role of CEO Compensation Peer GroupsDocument14 paginiInside the Black Box: Role of CEO Compensation Peer GroupsneckitoÎncă nu există evaluări
- RBI DataDocument86 paginiRBI DatarumiÎncă nu există evaluări
- CARP Outline For ClassmatesDocument3 paginiCARP Outline For ClassmatesAudreyÎncă nu există evaluări