Documente Academic
Documente Profesional
Documente Cultură
The Most Advanced Course On Web Application Penetration Testing
Încărcat de
ricardo bolivarrDescriere originală:
Titlu original
Drepturi de autor
Formate disponibile
Partajați acest document
Partajați sau inserați document
Vi se pare util acest document?
Este necorespunzător acest conținut?
Raportați acest documentDrepturi de autor:
Formate disponibile
The Most Advanced Course On Web Application Penetration Testing
Încărcat de
ricardo bolivarrDrepturi de autor:
Formate disponibile
WEB APPLICATION
PENETRATION TESTING EXTREME
VERSION 2
The most advanced course on web application penetration testing
INTRODUCTION
COURSE DESCRIPTION
Web Application Penetration Testing eXtreme is a practical online course on the
most advanced web application penetration testing techniques.
This training course is tied to Hera Lab, where students will access a number of
laboratories for each learning module.
PRE-REQUISITES
WAPTX is an advanced course that requires the following pre-requisites:
• Deep understanding of HTML, HTTP, Server-side languages, XML, JavaScript.
• Good understanding and practical proficiency of XSS, XSRF, SQLi, and basic
HTML5 attacks.
• Ability to read and understand PHP code will help, although not mandatory.
• Basic development skills required.
The eLearnSecurity WAPT course provides most of the above pre-requisites.
WHO SHOULD TAKE THIS COURSE?
The WAPTX course is primarily geared towards:
• Penetration Testers
• Web Developers
• IT Security professionals with a technical background
HOW AM I GOING TO LEARN THIS?
eLearnSecurity courses are very interactive, addictive, and presents content in such
a way that it appeals to all learning styles. WAPTX comes with practical lessons and
videos, so do not expect the outdated way of learning by just reading pages of
theoretical methodologies. During this training course, you will have several guided
labs that will provide you with relevant and hands-on practical application
experience.
Course Home Page: www.elearnsecurity.com/waptx
CONTENTS
WILL I GET A CERTIFICATE?
Once you satisfy the requirements of the final practical
certification test, you will be awarded an “eLearnSecurity Web
Penetration Tester eXtreme” certificate and will hold the
eWPTX certification.
ORGANIZATION OF CONTENTS
The WAPTX is a follow up of the WAPT course but at an “extreme” level. This course
brings students into a new world of advanced exploitation techniques using real-
world scenarios – all served with challenging and extremely hands-on laboratories in
which to put the covered techniques into practice.
• Module 1: Encoding and Filtering
• Module 2: Evasion Basic
• Module 3: Cross-Site Scripting
• Module 4: XSS Filter Evasion and WAF Bypassing
• Module 5: Cross-Site Request Forgery
• Module 6: HTML 5
• Module 7: SQL Injections
• Module 8: SQLi Filter Evasion and WAF Bypassing
• Module 9: XML Attacks
• Module 10: Attacking Serialization
• Module 11: Server Side Attacks
• Module 12: Attacking Crypto
• Module 13: Attacking Authentication & SSO
• Module 14: Pentesting APIs & Cloud Applications
• Module 15: Attacking LDAP-based Implementations
Course Home Page: www.elearnsecurity.com/waptx
WAPTX
MODULE 1: ENCODING AND FILTERING
The first module of this course is not just another module on encoding. It provides
some esoteric encoding skills that will be helpful during the rest of the course.
Understanding what kind of data encoding is used and how it works is fundamental
and ensures that the tests are performed as intended, which is why this module starts
with the basic concept of data encoding.
The Encoding and Filtering module is about filtering basics, starting from a brief
introduction on how to deal with regular expression, to understanding how to detect,
fingerprint, and evade web application firewalls. We conclude by analyzing the most
common client-side defensive mechanism.
1. ENCODING AND FILTERING
1.1 Data Encoding Basics
1.1.1 Dissecting Encoding Types
1.1.1.1 URL Encoding
1.1.1.2 HTML Encoding
1.1.1.2.1 Document Character Encoding
1.1.1.2.2 Character References
1.1.1.3 Base (36|64) Encoding
1.1.1.3.1 Base 36
1.1.1.3.2 Base 64
1.1.1.4 Unicode Encoding
1.1.2 Multiple (De|En)codings
1.2 Filtering Basics
1.2.1 Regular Expressions
1.2.1.1 Metacharacters
1.2.1.2 Shorthand Character Classes
1.2.1.3 Non-printing Characters
1.2.1.4 Unicode
1.2.2 Web Application Firewall
1.2.2.1 Simple Rules to Bypass WAFs
1.2.2.2 WAF Detection and Fingerprinting
1.2.3 Client-side Filters
1.2.3.1 Browser Add-ons
1.2.3.2 Native Browser Filters
Course Home Page: www.elearnsecurity.com/waptx
WAPTX
MODULE 2: EVASION BASICS
The Evasion Basics module provides advanced coverage of most modern filter
evasion techniques using different client-side and server-side languages. To ensure
that you have a complete understanding of filters and encoding, the main evasion
techniques that start from Base64 and lesser-known URI obfuscation techniques and
concludes with JavaScript and PHP obfuscation techniques are introduced.
2. EVASION BASICS
2.1 Base64 Encoding Evasion
2.1.1 Cookie Stealer
2.2 URI Obfuscation Techniques
2.2.1 URL Shortening
2.2.1.1 Bitly.com Short Link Info
2.2.1.2 Other Services Short Link Info
2.2.1.3 cURL Link Resolver
2.2.2. URL Hostname Obfuscation
2.2.2.1 URL Authority Obfuscation
2.3 JavaScript Obfuscation Techniques
2.3.1 JavaScript Encoding – Non-Alphanumeric
2.3.1.1 String Casting
2.3.1.2 Booleans
2.3.1.3 Numbers
2.3.1.4 String
2.3.1.4.1 Generate ‘alert’ String
2.3.1.5 JJencode
2.3.1.6 AAencode
2.3.17 JSFuck
2.3.2 JavaScript Compressing
2.3.2.1 Minifying
2.3.2.2 Packing
2.4 PHP Obfuscation Techniques
2.4.1 Basic Language Reference
2.4.1.1 Type Juggling
2.4.1.2 Numerical Data Types
2.4.1.3 String Data Types
2.4.1.4 Array Data Types
2.4.1.5 Variable Variables
2.4.2 Non-alphanumeric Code
2.4.2.1 Strings Generation
2.4.2.2 Hackvector.co.uk
Course Home Page: www.elearnsecurity.com/waptx
WAPTX
MODULE 3: CROSS-SITE SCRIPTING
Module three is entirely dedicated to cross-site scripting attacks. It starts with a brief
recap of the different types of XSS and then introduces advanced attacking
techniques and exotic XSS vectors. This module also covers how to use the most
advanced tools available and exploit any XSS.
3. CROSS-SITE SCRIPTING
3.1 Introduction
3.2 Cross-Site Scripting
3.2.1 Reflected XSS
3.2.2 Persistent XSS
3.2.3 DOM XSS
3.2.4 Universal XSS
3.3 XSS Attacks
3.3.1 Cookie Grabbing
3.3.1.1 Script Injection
3.3.1.2 Cookie Recording & Logging
3.3.1.3 Netcat Example
3.3.1.4 Bypassing HTTPOnly Flag
3.3.1.4.1 Cross-site Tracing (XST)
3.3.1.4.2 CVE: 2012-0053
3.3.1.4.3 BeEF’s Tunneling Proxy
3.3.2 Defacements
3.3.2.1 Virtual Defacement
3.3.2.2 Persistent Defacement
3.3.3 Phishing
3.3.3.1 Cloning a Website
3.3.3.2 Choosing a Domain Name
3.3.4 Keylogging
3.3.4.1 JavaScript Example
3.3.4.2 Keylogging with Metasploit
3.3.4.3 Keylogging with BeEF
3.3.5 Network Attacks
3.3.5.1 IP Detection
3.3.5.2 Subnet Detection
3.3.5.3 Ping Sweeping
3.3.5.4 Port Scanning
Simple Port Scanner
HTML5 Alternatives
Course Home Page: www.elearnsecurity.com/waptx
WAPTX
MODULE 3: CROSS-SITE SCRIPTING (cont.)
3.3.6 Self-XSS
3.3.6.1 Browsers Based on Chromium
3.3.6.2 Browsers Based on Chromium / Bypasses
3.3.6.3 Browsers Based on Mozilla Firefox
3.3.6.4 Browsers Based on Mozilla Firefox / Bypasses
3.3.6.5 Browsers’ Security Measures
3.3.6.6 Browsers Add-ons
3.3.6.7 JavaScript Console Limitations
3.4 Exotic XSS Vectors
3.4.1 Mutation-based XSS
3.4.1.1 mXSS Examples
3.4.1.2 mXSS Multiple Mutations
Course Home Page: www.elearnsecurity.com/waptx
WAPTX
MODULE 4: XSS FILTER EVASION AND WAF BYPASSING
In this module, the student will learn about advanced filter evasion and WAF
bypassing techniques. Starting from simple blacklisting filters, the student will go
through different mechanisms to bypass common input sanitization techniques,
browser filters, and much more. The student will not only find a number of well-
known vectors but will also understand how to find new ones. At the end of this
module, the student will be able to recognize the presence of WAF’s and filters and
implement effective bypassing techniques.
4. XSS FILTER EVASION AND WAF BYPASSING
4.1 Introduction
4.2 Bypassing Blacklisting Filters
4.2.1 Injecting Script Code
4.2.1.1 Bypassing Weak <script> Tag Banning
4.2.1.2 ModSecurity > Script Tag Based XSS Vectors Rule
4.2.1.3 Beyond <script> Tag…Using HTML Attributes
4.2.1.4 Beyond <script> Tag…Using HTML Events
4.2.2 Keyword Based Filter
4.2.2.1 Character Escaping
4.2.2.1.1 Unicode
4.2.2.1.2 Decimal, Octal, Hexadecimal
4.2.2.2 Constructing Strings
4.2.2.3 Execution Sinks
4.2.2.4 Pseudo-protocols
4.2.2.4.1 Data
4.2.2.4.2 Vbscript
4.3 Bypassing Sanitization
4.3.1 String Manipulations
4.3.1.1 Removing HTML Tags
4.3.1.2 Escaping Quotes
4.3.1.3 Escape Parentheses
4.4 Bypassing Browser Filters
4.4.1 (Un)Filtered Scenarios - Injecting Inside HTML Tag
4.4.2 (Un)Filtered Scenarios - Injecting Inside HTML Tag Attributes
4.4.3 (Un)Filtered Scenarios - Injecting Inside SCRIPT Tag
4.4.4 (Un)Filtered Scenarios - Injecting Inside Event Attributes
4.4.5 (Un)Filtered Scenarios - DOM Based
Course Home Page: www.elearnsecurity.com/waptx
WAPTX
MODULE 5: CROSS-SITE REQUEST FORGERY
This module is entirely dedicated to Cross-Site Request Forgery attacks. It starts
from a brief recap about this vulnerability and then introduces the main Attack
Techniques and Vectors in order to later introduce how to Exploit Weak Anti-CSRF
Measures and to conclude Advanced Exploitation techniques.
5. CROSS-SITE REQUEST FORGERY
5.1 CSRF: Recap & More
5.1.1 Vulnerable Scenario
5.2 Attack Vectors
5.2.1 Force Browsing with GET
5.2.1.1 Example > Change Email Address
5.2.2 Post Requests
5.2.2.1 Auto-submitting from > v1
5.2.2.2 Auto-submitting form > v2
5.3 Exploiting Weak Anti-CSRF Measures
5.3.1 Using Post-only Requests
5.3.2 Multi-Step Transactions
5.3.3 Checking Referer Header
5.3.4 Predictable Anti-CSRF Token
5.3.5 Unverified Anti-CSRF Token
5.3.6 Secret Cookies
5.4 Advanced CSRF Exploitation
5.4.1 Bypassing CSRF defenses with XSS
5.4.1.1 Bypassing Header Checks
5.4.1.2 Bypassing Anti-CSRF Token
5.4.1.2.1 1> Request a Valid Form with a Valid Token
5.4.1.2.2 2 > Extract the Valid Token from the Source Code
5.4.1.2.3 3 > Forge the Form with the Stolen Token
5.4.2 Bypassing Anti-CSRF Token Brute Forcing
Course Home Page: www.elearnsecurity.com/waptx
WAPTX
MODULE 6: HTML5
Module six is entirely dedicated to HTML5 and its attack vectors. It starts with a
recap of this language, analyzing the main features to focus our security research, and
then dives deep into the main exploitation techniques and attack scenarios. Once the
security concerns related to HTML5 features are analyzed, the student will learn
about the most common security mechanisms developers use. These are critical in
understanding how to leverage even more sophisticated attacks.
The module concludes with an analysis of the UI redressing attacks and an overview
of related attack vectors introduced with HTML5.
6. HTML5
6.1 HTML5: Recap & More
6.1.1 Introduction
6.1.2 Semantics
6.1.2.1 Form Elements
6.1.2.2 Media Elements
6.1.2.3 Semantic/Structural Elements
6.1.2.4 Attributes
6.1.3 Offline & Storage
6.1.3.1 Web Storage > Attack Scenario
6.1.3.1.1 Session Hijacking
6.1.3.2 Offline Web Application > Attack Scenario
6.1.4 Device Access
6.1.4.1 Geolocation > Attack Scenario
6.1.4.2 Fullscreen Mode > Attack Scenario
6.1.4.2.1 Phishing
6.1.5 Performance, Integration & Connectivity
6.1.5.1 Attack Scenarios
6.2 Exploiting HTML5
6.2.1 CORS Attack Scenario
6.2.1.1 Universal Allow
6.2.1.1.1 Allow by Wildcard Value*
6.2.1.1.2 Allow by Server-Side
6.2.1.2 Weak Access Control
6.2.1.2.1 Check Origin Example
6.2.1.3 Intranet Scanning
6.2.1.3.1 JS-Recon
Course Home Page: www.elearnsecurity.com/waptx
WAPTX
MODULE 6: HTML5 (cont.)
6.2.1.4 Remote Web Shell
6.2.1.4.1 The Shell of the Future
6.2.2 Storage Attack Scenarios
6.2.2.1 Web Storage
6.2.2.1.1 Session Hijacking
6.2.2.1.2 Cross-directory Attacks
6.2.2.1.3 User Tracking and Confidential Data Disclosure
6.2.2.2 IndexedDB
6.2.2.2.1 IndexedDB vs. WebSQL Database
6.2.3 Web Messaging Attack Scenarios
6.2.3.1 DOM XSS
6.2.3.2 Origin Issue
6.2.4 Web Sockets Attack Scenarios
6.2.4.1 Data Validation
6.2.4.2 MiTM
6.2.4.3 Remote Shell
6.2.4.4 Network Reconnaissance
6.2.5 Web Workers Attack Scenarios
6.2.5.1 Browser-Based Botnet
6.2.5.2 Distributed Password Cracking
6.2.5.3 WebWorkers + CORS - DDoS Attacks
6.3 HTML5 Security Measures
6.3.1 Security Headers: X-XSS-Protection
6.3.2 Security Headers: X-Frame-Options
6.3.3 Security Headers: Strict-Transport-Security
6.3.4 Security Headers: X-Content-Type-Options
6.3.5 Security Headers: Content Security Policy
6.4 UI Redressing: The x-Jacking Art
6.4.1 ClickJacking
6.4.1.1 ClickJacking Example
6.4.2 LikeJacking
6.4.3 StrokeJacking
6.4.3.1 StrokeJacking Example – Show Me the Hidden Picture
6.4.4 New Attack Vectors in HTML5
6.4.4.1 Drag-and-Drop
6.4.4.1.1 Text Field Injection
6.4.4.1.2 Content Extraction
Course Home Page: www.elearnsecurity.com/waptx
WAPTX
MODULE 7: SQL INJECTIONS
This module is entirely dedicated to SQL injection attacks, which recaps the main
classification of exploitation techniques and then introduces advanced attack
techniques on different DBMS’s.
7. SQL INJECTIONS
7.1 SQL Injection: Introduction, Recap & More
7.1.1 Introduction
7.1.2 Recap & More
7.2 Exploiting SQLi
7.2.1 Techniques Classification
7.2.1.1 Inband Attacks
7.2.1.2 Out-of-Band Attacks
7.2.1.3 Inference Attacks
7.2.2 Gathering Information from the Environment
7.2.2.1 Identify the DBMS
7.2.2.1.1 Error Codes Analysis
7.2.2.1.2 Error Codes Analysis > MySQL
7.2.2.1.3 Error Codes Analysis > MSSQL Server
7.2.2.1.4 Error Codes Analysis > Oracle
7.2.2.1.5 Banner Grabbing
7.2.2.1.6 Educated Guessing
7.2.2.1.7 Educated Guessing > String Concatenation
7.2.2.1.8 Educated Guessing > Numeric Functions
7.2.2.1.9 Educated Guessing > SQL Dialect
7.2.2.2 Enumerating the DBMS Content
7.2.2.2.1 Databases > MySQL
7.2.2.2.2 Databases > MSSQL
7.2.2.2.3 Databases > Oracle
7.2.2.2.4 Databases > Tables & Columns
7.2.2.2.5 Databases > Users and Privileges
7.3 Advanced SQLi Exploitation
7.3.1 Out-of-Band Exploitation
7.3.1.1 Alternative OOB Channels
7.3.1.2 OOB via HTTP
7.3.1.2.1 Oracle URL_HTTP Package
7.3.1.2.2 Oracle HTTPURITYPE Package
Course Home Page: www.elearnsecurity.com/waptx
WAPTX
MODULE 7: SQL Injections (cont.)
7.3.1.3 OOB via DNS
7.3.1.3.1 DNS Exfiltration Flow
7.3.1.3.2 Provoking DNS Requests
• MySQL (win)
• MSSQL
• Oracle
7.3.2 Exploiting Second-Order SQL Injection
7.3.2.1 First-order Example
7.3.2.2 Second-order Example
7.3.2.3 Security Considerations
7.3.2.4 Automation Considerations
Course Home Page: www.elearnsecurity.com/waptx
WAPTX
MODULE 8: SQLi FILTER EVASION AND WAF BYPASSING
In this advanced module, the student will learn about advanced filter evasion and
WAF bypassing techniques. These foundational skills will be necessary to understand
and master further techniques. By the end of this module, the student will be able to
recognize the presence of WAF’s and filters and implement effective bypassing
techniques.
8. SQLi FILTER EVASION AND WAF BYPASSING
8.1 Introduction
8.2 DBMS Gadgets
8.2.1 Comments
8.2.2 Functions and Operators
8.2.3 Intermediary Characters
8.2.4 Constants and Variables
8.2.5 Strings
8.2.6 Integers
8.2.7 MySQL Type Conversion
8.3 Bypassing Keywords Filters
8.3.1 Case changing
8.3.2 Using Intermediary Characters
8.3.3 Using Alternative Techniques
8.3.4 Circumventing by Encoding
8.3.5 Replaced Keywords
8.4 Bypassing Functions Filters
8.4.1 Building Strings
8.4.2 Brute-force Strings
8.4.3 Building Substring
Course Home Page: www.elearnsecurity.com/waptx
WAPTX
MODULE 9: XML ATTACKS
Module nine is entirely dedicated to XML attacks, which starts with a recap of this
language and then dives into the most modern attacks, such as XML Tag Injection,
XXE, XEE, and XPath Injection. For each of them, basic and advanced exploitation
techniques are analyzed. By the end of this module, the student will be able to pentest
complex applications using XML.
9. XML ATTACKS
9.1 XML Attacks: Introduction, Recap & More
9.1.1 Introduction
9.1.2 XML Attacks: Recap & More
9.1.2.1 XML Document with Internal DTD
9.1.2.2 XML Document with External DTD
9.1.2.3 Entities
9.2 XML Tag Injection
9.2.1 Testing XML Injection - Single/Double Quotes
9.2.2 Testing XML Injection - Ampersand
9.2.3 Testing XML Injection - Angular parentheses
9.2.4 Testing XML Injection - XSS with CDATA
9.3 XML eXternal Entity
9.3.1 Taxonomy
9.3.1.1 External Entities: Private vs. Public
9.3.2 XML eXternal Entity
9.3.2.1 Resource Inclusion
9.3.2.2 Resource Inclusion – Improved
• Invalid resource to extract
• CDATA Escape Using Parameter Entities
• php://I/O Stream
9.3.3 Bypassing Access Control
9.3.4 Out-Of-Band Data Retrieval
• OOB via HTTP
• OOB via HTTP using XXEServe
9.4 XML Entity Expansion
9.4.1 Recursive Entity Expansion
9.4.1.1 Billion Laugh Attack
9.4.2 Generic Entity Expansion
9.4.2.1 Quadratic Blowup Attack
9.4.3 Remote Entity Expansion
Course Home Page: www.elearnsecurity.com/waptx
WAPTX
MODULE 9: XML ATTACKS (cont.)
9.5 XPath Injection
9.5.1 XPath Recap
9.5.1.1 XPath 1.0 vs 2.0
• New Operations and Expressions on Sequences
o Function on Strings
o FOR Operator
o Conditional Expression
o Regular Expression
o Assemble/Disassemble Strings
o Data Types
9.5.2 Advanced XPath Exploitation
9.5.2.1 Blind Exploitation
• Error Based
• Boolean Based
9.5.2.2 OOB Exploitation
• HTTP Channel
• DNS Channel
Course Home Page: www.elearnsecurity.com/waptx
WAPTX
MODULE 10: ATTACKING SERIALIZATION
In this module, you will learn about serialization and deserialization in Java, PHP,
and .NET. We also present untypical serialization that you may come across during
web application penetration testing. By the end of the module, you should have a
better understanding of serialization mechanisms and how to find/exploit untrusted
deserialization in common web technologies.
10. ATTACKING SERIALIZATION
10.1 What is Serialization?
10.2 Serialization in Java
10.2.1 Creating Serialized Objects
10.2.2 Deserializing Data
10.2.3 Insecure Deserialization Conditions
10.2.3.1 Properties and Reflection
10.2.4 Gadgets
10.2.5 Introduction to Ysoserial
10.2.5.1 Additions to Ysoserial
10.2.6 Brute-force Attack with Ysoserial
10.2.7 Exploring Ysoserial
10.2.8 Exploiting Java Deserialization
10.2.8.1 Deciphering Serialized Data
10.2.8.2 Injecting Serialized Payload
10.2.9 Analysis of URLDNS Payload
10.2.9.1 Arbitrary DNS Resolution Exploit
10.2.10 Troubleshooting Ysoserial
10.2.11 Spotting Java Serialized Objects
10.2.12 Recommended Reading
10.3 Serialization in PHP
10.4 .NET Serialization
10.4.1 .NET Serialization Types
10.4.2 .NET Serialization Example
10.4.3 Spotting .NET Serialized Data
10.4.4 VIEWSTATE
10.5 Other Serialization
Course Home Page: www.elearnsecurity.com/waptx
WAPTX
MODULE 11: SERVER-SIDE ATTACKS
In this module, you will come to understand how user-supplied input can sometimes
be insecurely handled by back-end logic, as well as learn how to find and exploit
server-side bugs. Specifically, during this module, you will learn how Server-Side
Request Forgery, Server Side Include, Edge Side Include, Server Side Template
Injection, and Expression Language Injection attacks work. Attacking XSLT engines
is also covered. Note that the abovementioned attacks can have quite an impact on
the overall security of an application since they can lead to not only sensitive
information leakage but remote code execution as well.
11. SERVER-SIDE ATTACKS
11.1 Server-Side Infrastructure
11.1.1 Understanding Modern Infrastructure
11.1.2 Abusing Intermediate Devices
11.2 Server-Side Request Forgery
11.2.1 SSRF Attack
11.2.2 When SSRF is a Feature
11.2.3 Blind SSRF Exploitation
11.2.3.1 Abusing URL Structure
11.2.4 SSRF Example
11.2.4.1 Forcing Authentication
11.2.4.2 Changing Protocol
11.2.4.3 Attacking SSRF on Windows
11.2.4.4 Other SSRF Scenarios
11.2.4.5 Time-based SSRF
11.2.4.6 Extending SSRF
11.3 Server-Side Include
11.3.1 SSI Expressions
11.3.2 SSI Example
11.3.3 Edge Side Includes
11.3.4 ESI Expressions
11.3.4.1 ESI Detection
11.3.4.2 ESI Exploitation
11.4 Language Evaluation
11.4.1 Template Engines
11.4.2 Detecting Template Injection
11.4.3 Confirming Template Injection
11.4.4 Exploiting Template Injection
Course Home Page: www.elearnsecurity.com/waptx
WAPTX
MODULE 11: SERVER-SIDE ATTACKS (cont.)
11.4 Language Evaluation (cont.)
11.4.5 Expression Language
11.4.5.1 Expression Language Example
11.4.5.2 Talking to EL Parser
11.4.5.3 Playing with Classes
11.4.5.4 EL Code Execution
11.4.5.5 Extending EL Exploitation
11.4.5.6 References
11.5 Attacking XSLT Engines
11.5.1 XSLT Purpose
11.5.2 XSLT Example
11.5.2.1 XSLT Usage
11.5.3 Experimenting with XSLT Parser
11.5.3.1 XSLT Engine Detection
11.5.3.2 XSLT Documentation
11.5.3.3 XSLT File Read
11.5.3.4 XSLT SSRF
11.5.3.5 Extending XSLT Attacks
Course Home Page: www.elearnsecurity.com/waptx
WAPTX
MODULE 12: ATTACKING CRYPTO
This module will focus on identifying and attacking flawed or poorly constructed
crypto implementations. Attacks such as Known Plaintext, Padding Oracle, Hash
Length Extension, and Authorization bypass via .NET machine key will be covered.
12. ATTACKING CRYPTO
12.1 Encryption Fundamentals
12.1.1 Cryptography
12.1.2 Key Encryption Terms
12.1.2.1 Encryption
12.1.2.2 Ciphers
12.1.2.3 Electronic Code Book (ECB)
12.1.2.4 Cipher Block Chaining (CBC)
12.1.2.5 Padding
12.1.3 Attacks Against Crypto
12.2 Insecure Password Reset
12.2.1 Known Plaintext Attack Scenario
12.2.2 Exploitation
12.3 Padding Oracle Attack
12.3.1 What is a Padding Oracle?
12.3.2 Padding Oracle Attack Scenario
12.4 Hash Length Extension Attack
12.4.1 Hash Length Extension Attack Fundamentals
12.4.2 Hash Length Extension Attack Scenario
12.5 Leveraging machineKey
12.5.1 The Importance of machineKey
12.5.2 Leveraging a Leaked machineKey for RCE
12.6 Subverting HMAC in Node.js
12.6.1 Subverting HMAC in Node.js Scenario
Course Home Page: www.elearnsecurity.com/waptx
WAPTX
MODULE 13: ATTACKING AUTHENTICATION & SSO
In module thirteen, you will have the opportunity to study advanced attacks against
various Authentication and Single Sign On implementations. Before covering the
attacks, you will dive into each implementation’s internals, security shortcomings,
and common misconfigurations. SAML, OAuth, JWT, and others will be covered.
13. ATTACKING AUTHENTICATION & SSO
13.1 Authentication in Web Apps
13.2 Attacking JWT
13.2.1 JSON Web Tokens (JWT)
13.2.2 JWT Security Facts
13.2.3 JWT Attack Scenario 1
13.2.4 JWT Attack Scenario 2
13.2.5 JWT Attack Scenario 3
13.3 Attacking OAuth
13.3.1 OAuth
13.3.2 Common OAuth Attacks
13.3.3 OAuth Attack Scenario 2
13.3.4 OAuth Attack Scenario 3
13.3.5 OAuth Attack Scenario 4
13.4 Attacking SAML
13.4.1 Security Assertion Markup Language (SAML)
13.4.2 SAML Security Considerations
13.4.3 SAML Attack Scenario
13.5 Bypassing 2FA
13.5.1 2FA Bypasses
13.5.2 2FA Bypass Scenario 1
13.5.3 2FA Bypass Scenario 2
Course Home Page: www.elearnsecurity.com/waptx
WAPTX
MODULE 14: PENTESTING APIS & CLOUD APPLICATIONS
APIs can be found in any IT aspect nowadays, from web and mobile applications all
the way to IOT solutions and the cloud. It is of paramount importance for a
penetration tester to be able to perform a thorough penetration test against an API.
This module will cover in detail the most effective attacking tactics against APIs and
Cloud-powered applications.
14. PENTESTING APIS & CLOUD APPLICATIONS
14.1 Introduction to APIs
14.2 API Testing and Attacking
14.3 API Access Control
14.4 Resource Sharing
14.5 Attacking Cloud Based Applications
14.5.1 Microservices
14.5.2 Serverless Applications
14.5.3 Details of Serverless Architecture
14.5.3.1 Serverless Application Example
14.5.4 S3 Buckets
14.5.5 Tool: s3recon
14.5.6 S3 AWS Signed URLs
14.5.6.1 Creating Signed URLs
14.5.6.2 Signed Cookies
14.5.7 Serverless Event Injection
14.5.7.1 Serverless Event Injection Scenario
14.5.7.2 Serverless Event Injection 2
14.5.8 GraphQL APIs
14.5.9Function as a Service
Course Home Page: www.elearnsecurity.com/waptx
WAPTX
MODULE 15: ATTACKING LDAP-BASED
IMPLEMENTATIONS
For numerous reasons, a web application can make use of LDAP (query objects from
a directory database, authentication, management, etc.). In this module, you will
learn how to exploit vulnerable LDAP-based implementations. Specifically, you will
learn all about LDAP basics, LDAP injections, and LDAP manipulation/poisoning.
15. ATTACKING LDAP-BASED IMPLEMENTATIONS
15.1 What is LDAP?
15.1.1 Directory Database Structure
15.1.1.1 LDIF Format
15.2 LDAP Syntax
15.2.1 LDAP Implementations
15.3 Abusing LDAP
15.3.1 LDAP Over TCP
15.3.2 LDAP Vulnerabilities
15.3.3 LDAP Injection
15.3.3.1 Blind LDAP Injection
15.3.4 LDAP Python Implementation
15.3.4.1 Implementing LDAP Server
15.3.4.2 Implementing LDAP Client
15.3.5 Blind LDAP Injection Example
Course Home Page: www.elearnsecurity.com/waptx
We are eLearnSecurity.
Based in Santa Clara, California, with offices in Pisa, Italy, and Dubai, UAE, Caendra
Inc. is a trusted source of IT security skills for IT professionals and corporations of all
sizes. Caendra Inc. is the Silicon Valley-based company behind the eLearnSecurity
brand.
eLearnSecurity has proven to be a leading innovator in the field of practical security
training, with best of breed virtualization technology, in-house projects such as
Coliseum Web Application Security Framework and Hera Network Security Lab,
which has changed the way students learn and practice new skills.
Contact details:
www.elearnsecurity.com
contactus@elearnsecurity.com
S-ar putea să vă placă și
- Syllabus WAPTXDocument14 paginiSyllabus WAPTXAkiNiHandiongÎncă nu există evaluări
- Syllabus: Penetration Testing Course - Professional Version 4.0Document35 paginiSyllabus: Penetration Testing Course - Professional Version 4.0jeandelcarpioÎncă nu există evaluări
- Syllabus WAPTXDocument15 paginiSyllabus WAPTXramax01Încă nu există evaluări
- Advanced Web Attacks and Exploitation: Offensive SecurityDocument9 paginiAdvanced Web Attacks and Exploitation: Offensive SecurityMinh TanÎncă nu există evaluări
- eWPT Review - MiaulezDocument4 paginieWPT Review - MiaulezSamÎncă nu există evaluări
- eWPT Review - Anon Tuttu VenusDocument4 paginieWPT Review - Anon Tuttu VenusSamÎncă nu există evaluări
- MASPT at A GlanceDocument14 paginiMASPT at A Glancefrogman1001Încă nu există evaluări
- WindowsattacksDocument78 paginiWindowsattacksblufakesionÎncă nu există evaluări
- AV or EDR BypassDocument33 paginiAV or EDR BypassUtshav RoyÎncă nu există evaluări
- Sqlmap Manual PDFDocument46 paginiSqlmap Manual PDFJavier Guzman100% (2)
- ELearnSecurity EWPTX Notes Basic by JoasDocument311 paginiELearnSecurity EWPTX Notes Basic by JoasYves-boris N'choÎncă nu există evaluări
- AD Penetration Testing + Red Team TacticsDocument10 paginiAD Penetration Testing + Red Team TacticsMohamed Garba MoussaÎncă nu există evaluări
- eLearnSecurity eWPT Notes @offensive01 @library - SecDocument370 paginieLearnSecurity eWPT Notes @offensive01 @library - SecKaiser CastÎncă nu există evaluări
- GIAC Certified Penetration Tester The Ultimate Step-By-Step GuideDe la EverandGIAC Certified Penetration Tester The Ultimate Step-By-Step GuideÎncă nu există evaluări
- Offensive Security: Penetration Test Report For Internal Lab and ExamDocument12 paginiOffensive Security: Penetration Test Report For Internal Lab and Examnobuyuki100% (1)
- PEN-200 Lab ReportDocument8 paginiPEN-200 Lab ReportSilver UchihaÎncă nu există evaluări
- New Text DocumentDocument2 paginiNew Text DocumentJohnÎncă nu există evaluări
- OSCP Offensive Security Certified Professional Practice Tests With Answers To Pass the OSCP Ethical Hacking Certification ExamDe la EverandOSCP Offensive Security Certified Professional Practice Tests With Answers To Pass the OSCP Ethical Hacking Certification ExamÎncă nu există evaluări
- Report Crowdstrike 2023 Threat Hunting ReportDocument54 paginiReport Crowdstrike 2023 Threat Hunting ReportJan SullanoÎncă nu există evaluări
- Java Deserialization Vulnerabilites The Forgotten Bug Class Redacted v1Document57 paginiJava Deserialization Vulnerabilites The Forgotten Bug Class Redacted v120dominic100% (1)
- Book of Tips by Aditya Shende PDFDocument23 paginiBook of Tips by Aditya Shende PDFvenomÎncă nu există evaluări
- Advanced XSSDocument8 paginiAdvanced XSSWilliam CaceresÎncă nu există evaluări
- Penetration Testing Professional: The World's Premier Online Penetration Testing CourseDocument55 paginiPenetration Testing Professional: The World's Premier Online Penetration Testing CourseMehmet Emin OzmenÎncă nu există evaluări
- Oswe Notes Basic by Joas 1648716052Document233 paginiOswe Notes Basic by Joas 1648716052jjjabriyel jabriÎncă nu există evaluări
- Brute XSS Cheat Sheet SampleDocument17 paginiBrute XSS Cheat Sheet Samplejohn doe0% (1)
- Cyber Threat Hunting A Complete Guide - 2019 EditionDe la EverandCyber Threat Hunting A Complete Guide - 2019 EditionÎncă nu există evaluări
- Category Sub-Category Status: Pre-Scan AnalysisDocument53 paginiCategory Sub-Category Status: Pre-Scan AnalysisVusraÎncă nu există evaluări
- © 2020 Caendra Inc. - Hera For PTX - Red-Teaming Active Directory Lab #2 (Els - Bank)Document49 pagini© 2020 Caendra Inc. - Hera For PTX - Red-Teaming Active Directory Lab #2 (Els - Bank)Saw GyiÎncă nu există evaluări
- Phishing and Malicious Javascript: John MitchellDocument40 paginiPhishing and Malicious Javascript: John Mitchellvschauhan100% (3)
- ELearnSecurity ECPPT Notes ExamDocument157 paginiELearnSecurity ECPPT Notes ExamAngel CabralesÎncă nu există evaluări
- Syllabus THPv1Document10 paginiSyllabus THPv1alexÎncă nu există evaluări
- Mimikatz and MetasploitDocument23 paginiMimikatz and MetasploithihackthisÎncă nu există evaluări
- ELearnSecurity Mobile Application Penetration TestingDocument210 paginiELearnSecurity Mobile Application Penetration TestingPiyush RautÎncă nu există evaluări
- Burpsuite Essential Content 2Document6 paginiBurpsuite Essential Content 2Aaron PreyÎncă nu există evaluări
- OWASP Top 10 Web Security VulnerabilitiesDocument74 paginiOWASP Top 10 Web Security VulnerabilitiesAbraham FidouÎncă nu există evaluări
- ELearnSecurity Mobile Application Penetration TestingDocument223 paginiELearnSecurity Mobile Application Penetration TestingMichael MichaelÎncă nu există evaluări
- Red-Teaming Active Directory Lab #3 (ELS - CORP) (Attack Path 1)Document24 paginiRed-Teaming Active Directory Lab #3 (ELS - CORP) (Attack Path 1)Saw GyiÎncă nu există evaluări
- Web Application Penetration Testing Report of Juice ShopDocument15 paginiWeb Application Penetration Testing Report of Juice ShopPavan Reddy50% (2)
- Ethical HackingDocument12 paginiEthical Hackingmani3686Încă nu există evaluări
- Advanced Skills For Network Penetration TestersDocument4 paginiAdvanced Skills For Network Penetration TestersJPChan50% (2)
- Report For Foophones: by Utkarsh MunraDocument37 paginiReport For Foophones: by Utkarsh Munrasuraj fbÎncă nu există evaluări
- Malware Sandboxing PDFDocument19 paginiMalware Sandboxing PDFImagekingÎncă nu există evaluări
- 4 ZN2018 WV - BugBounty Automation PDFDocument49 pagini4 ZN2018 WV - BugBounty Automation PDFtest twoÎncă nu există evaluări
- How To Use Hacking LabDocument54 paginiHow To Use Hacking LabAnurag RanjanÎncă nu există evaluări
- Nessus-Nmap Lab: IST 451 - Network SecurityDocument6 paginiNessus-Nmap Lab: IST 451 - Network SecurityCool AamanÎncă nu există evaluări
- Adavanced Postgre SQL InjectionDocument15 paginiAdavanced Postgre SQL InjectionFelipe CostaÎncă nu există evaluări
- OSCP Methodology NotesDocument41 paginiOSCP Methodology NotesGaétan NG100% (1)
- Training OSCPDocument6 paginiTraining OSCPAlvaro354Încă nu există evaluări
- Python-Nmap - Nmap From PythonDocument7 paginiPython-Nmap - Nmap From PythonpedrodotnetÎncă nu există evaluări
- Penetration Test ReportDocument39 paginiPenetration Test Reportaymen MrabetÎncă nu există evaluări
- OSWE Exam ReportDocument33 paginiOSWE Exam ReportRaspberryÎncă nu există evaluări
- 110 Attacking SerializationDocument165 pagini110 Attacking SerializationAlvaro Andrade SejasÎncă nu există evaluări
- Els PTPDocument59 paginiEls PTPKaiser CastÎncă nu există evaluări
- Applications of Ethical HackingDocument3 paginiApplications of Ethical HackingRaka Adhitama100% (1)
- WEP Crack Using Aircrack-Ng by Arunabh DasDocument146 paginiWEP Crack Using Aircrack-Ng by Arunabh DasArunabh DasÎncă nu există evaluări
- Windows XP Privilege Escalation ExploitDocument3 paginiWindows XP Privilege Escalation Exploitgauth92Încă nu există evaluări
- U HalliburtonDocument3 paginiU Halliburtonanas soufÎncă nu există evaluări
- Arba Minch University Institute of Technology Faculty of Computing & Software EngineeringDocument65 paginiArba Minch University Institute of Technology Faculty of Computing & Software Engineeringjemu mamedÎncă nu există evaluări
- Response LTR 13 330 VielmettiDocument2 paginiResponse LTR 13 330 VielmettiAnn Arbor Government DocumentsÎncă nu există evaluări
- Class Participation 9 E7-18: Last Name - First Name - IDDocument2 paginiClass Participation 9 E7-18: Last Name - First Name - IDaj singhÎncă nu există evaluări
- MBA-CM - ME - Lecture 16 Market Structure AnalysisDocument11 paginiMBA-CM - ME - Lecture 16 Market Structure Analysisrohan_solomonÎncă nu există evaluări
- HDMI CABLES PERFORMANCE EVALUATION & TESTING REPORT #1 - 50FT 15M+ LENGTH CABLES v3 SMLDocument11 paginiHDMI CABLES PERFORMANCE EVALUATION & TESTING REPORT #1 - 50FT 15M+ LENGTH CABLES v3 SMLxojerax814Încă nu există evaluări
- SS 671Document9 paginiSS 671OwÎncă nu există evaluări
- UnderstandingcpucoresDocument5 paginiUnderstandingcpucoresAbdul NabiÎncă nu există evaluări
- Blanko Permohonan VettingDocument1 paginăBlanko Permohonan VettingTommyÎncă nu există evaluări
- Boeing 247 NotesDocument5 paginiBoeing 247 Notesalbloi100% (1)
- About FW TaylorDocument9 paginiAbout FW TaylorGayaz SkÎncă nu există evaluări
- VMC Ballscrew 32mm Horizontal Plane ReplacementDocument11 paginiVMC Ballscrew 32mm Horizontal Plane ReplacementMarlon GeronimoÎncă nu există evaluări
- Comprehensive Drug Abuse Prevention and Control Act of 1970Document2 paginiComprehensive Drug Abuse Prevention and Control Act of 1970Bryan AbestaÎncă nu există evaluări
- ADocument2 paginiAẄâQâŗÂlïÎncă nu există evaluări
- MAYA1010 EnglishDocument30 paginiMAYA1010 EnglishjailsondelimaÎncă nu există evaluări
- Position PaperDocument9 paginiPosition PaperRoel PalmairaÎncă nu există evaluări
- Siemens Power Engineering Guide 7E 223Document1 paginăSiemens Power Engineering Guide 7E 223mydearteacherÎncă nu există evaluări
- Ranking - Best Multivitamins in 2018Document7 paginiRanking - Best Multivitamins in 2018JosephVillanuevaÎncă nu există evaluări
- Measurement System AnalysisDocument42 paginiMeasurement System Analysisazadsingh1Încă nu există evaluări
- L-2 Steel SectionsDocument23 paginiL-2 Steel SectionsRukhsar JoueÎncă nu există evaluări
- July2020 Month Transaction Summary PDFDocument4 paginiJuly2020 Month Transaction Summary PDFJason GaskillÎncă nu există evaluări
- Samsung UDC and UEC Series Video Wall DisplaysDocument12 paginiSamsung UDC and UEC Series Video Wall DisplaysWebAntics.com Online Shopping StoreÎncă nu există evaluări
- 0601 FortecstarDocument3 pagini0601 FortecstarAlexander WieseÎncă nu există evaluări
- Role of SpeakerDocument11 paginiRole of SpeakerSnehil AnandÎncă nu există evaluări
- Corr Shield NT 4292Document9 paginiCorr Shield NT 4292Donatas BertasiusÎncă nu există evaluări
- Gabuyer Oct13Document72 paginiGabuyer Oct13William Rios0% (1)
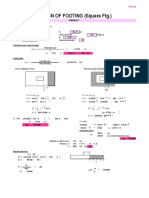
- Design of Footing (Square FTG.) : M Say, L 3.75Document2 paginiDesign of Footing (Square FTG.) : M Say, L 3.75victoriaÎncă nu există evaluări
- Address All Ifrs 17 Calculations Across The Organization W Ith A Unified PlatformDocument4 paginiAddress All Ifrs 17 Calculations Across The Organization W Ith A Unified Platformthe sulistyoÎncă nu există evaluări
- OD426741449627129100Document1 paginăOD426741449627129100SethuÎncă nu există evaluări
- E-Booklet Tacompact Board 2021Document6 paginiE-Booklet Tacompact Board 2021embenÎncă nu există evaluări