Documente Academic
Documente Profesional
Documente Cultură
Smartxweb Synopsis 03
Încărcat de
Sreenath Menon KDescriere originală:
Drepturi de autor
Formate disponibile
Partajați acest document
Partajați sau inserați document
Vi se pare util acest document?
Este necorespunzător acest conținut?
Raportați acest documentDrepturi de autor:
Formate disponibile
Smartxweb Synopsis 03
Încărcat de
Sreenath Menon KDrepturi de autor:
Formate disponibile
Smartx web
SMARTX WEB
SREELAKSHMI.K.S
Smartx web
Introduction and Objectives of the project
Smart X Web (Remote PC Management through Web) is software that allows users to access their systems from remote locations. When you are in the office or on a business trip, sometimes you may need to do something on your home computer for example, view your electricity bill or read your email. Sometimes you may get sick and won't be able to leave your apartment, however the deadline is close and you need to finish the project, or die trying. Driving through the city to get access to your work PC when you have a high fever is not a really good idea. In system controlling we can connect one system to another system and can control that system through this system. Our software provides an easy interface to access the remote PC anywhere in the world through internet without losing any of the privileges they get while they are in front of the remote PC. Users can logon to our website and reach out their PC. Our software also ensures high security and speed. Smart X Web, as we call it, is software that allows users to access devices connected to their systems from remote locations. The process starts when the different users, who need the facility, get registered through our website and download the application program for the said facility. Once the software is installed on the home pc then the user can access the devices connected to the system from any location using our website through the Internet. Lets elaborate the various steps present in this process. User Registration: A simple registration form is provided to the user wherein he can enter his name, address, contact number, email id, login id and password. After filling up the proper information, the user gets successfully registered for the application software. Login and Authentication: The user is authenticated for his login name and password, which was provided to him during the registration process. If the user fails to give his proper login id or password, an error message is displayed to him indicating that the login id does not exist. If the login is successful then the user is able to perform the following functions: Software Download: The user has this option for downloading the software to the particular system that he is using. Once the system is installed in that system, say the Home PC, and then the devices connected to that system can be accessed easily using our website. Access Devices: This is perhaps the purpose of Smart X Web. Accessing the various devices connected to the Home PC is the feature that is being implemented here. Every user will have a particular Access code to be entered for getting access to this feature. If the Access code entered is
SREELAKSHMI.K.S
Smartx web
wrong then the user gets automatically logged out. Once the correct Access Code is entered the user can access the device he wants. Logout: The user can sign out of the login area any time using this function. The System architecture has to be designed keeping all these functions in mind. We can see that the system consists of mainly the following three parts: (i) Server: It is a part of Internet, which is a host or website. It consists of the user login and
locating the Home PC for the corresponding users. (ii) Home PC: Home PC is the PC, which can be controlled by the developed software. It is the PC,
which will be controlled using a remote user. It may a PC located at home or office, which will be part of Internet. (iii) Remote PC: It is the PC in the Internet from which user access the devices on the home PC. It
is a dynamic one.
AIM:
A project for system control, device control, file and information transfer, and scanning of remote system using a website.
Tools, Software and Hardware Requirements: Tools:
Asp.net MS SQL server 2000
Hardware Requirements:
Processor Speed Base Memory : : : Pentium III or above. 1.4 GHz. 128MB RAM.
SREELAKSHMI.K.S
Smartx web
Hard Disk Drive Key Board Display Type
: : :
40 GB. 107 Keys VGA/EGA
Server System. Internet Connection. Home PC Devices like printer, mike, and webcam. Machine Details. Hardware for device controlling circuit IC DM74LS244 ,C LM7805 ,Relay, Transformer, Transistors, Capacitor, Diodes, Resistors, Circuit board.
Software Requirements:
Platform Development tool Web server Database Front end Programming language : : : : : : Windows Visual studio 2008 IIS(Internet information service) MS SQL Server ASP.NET C#
Data Flow Diagram
Level 0
Request Request Remote PC Response
Smart Xweb
Request Response HomePC
SREELAKSHMI.K.S
Smartx web
Level 1 View user Retrieve userdetails Retrieve Delete user userid option1 User Managemen t User is admin User Enter user details Downloading Managing homepc Software download Uploading Downloading System Managemen t Download client software HomePC User Registratio n option2 option3 Set Password User_reg Store user
Change passwor d
SREELAKSHMI.K.S
Smartx web
Level 2 Perform Authentication User Authenticatio n ID, password Failure Success Verify user User_reg
User
Option 1 store new password User_reg Change passwor d option 1 Brows e Select Directory Listing Director y option 2
Home
option3
System Managem ent
Software Downloa Download client d software Homepc A
Delete/ Download/ Rename files
R retrieve files
SREELAKSHMI.K.S
Smartx web
option 7 Option 2 Option 3 File upload Comman d Execution on
A option 6 option 5 option 4 Device Management Web cam Fetch stream video Proces s listing Turn off HomePC
Fetch files
Fetch and execute command Uploading
View desktop Uploading Retrieve Command Remotepc
Listing process Select processi d Killing process kill process
View image Remotepc Retrieve desktop retrieve files Homepc retrieve image retrieve process
SREELAKSHMI.K.S
Smartx web
Class Diagram
USER REGISTER String Username String Password Boolean addUserDetails()
CLIENT SOFTWARE String URL String cmd String output
String getURL(String) String get Command(String) String cmdExecution(String) String RMI Update(String)
FIS FileInputStream fin
FOS FileInputStream fos Void write (byte[]) Void close( );
byte[] read( ) Boolean isFile( ) boolean isDirecting()
SREELAKSHMI.K.S
Smartx web
VERIFICATION String Username String Password Boolean authentication (String, String)
COMMAND IDENTIFIER FileInputStream fin FileOutputStream fos
Boolean isDeviceConnected( ) Boolean isFTP( ) String getDeviceName() File[] listRoot() Void storeCommand()
* * * FILE INPUT STREAM Fetch Directory COMMAND EXECUTION String directory String Read Device config( ) boolean isDeviceConnected (String) int checkDeviceStatus (String) Boolean commandExecutio n(String)
File f File[] is Files( ) boolean isFile( ) boolean isDirectory( )
byte[] Read( ) FileInputStream fin boolean isFile( ) boolean isDirecting()
FILE OUTPUT STREAM FileOutputStream fos Void write (byte[]) Void close( );
SREELAKSHMI.K.S
Smartx web
Basic modules The software is mainly divided into two modules Administrator module User module
Administrator module Initiator is powerful user who can perform the following functions: User module Login into the server by entering the user name and password. Once he logged into the system, he can access files and external devices (webcam, printer) from HomePC. System Management After logging in, the user can perform many functions on his home PC through the remote PC. In system Management we can connect one system to another system and can control that system through this system. System Management includes various functions: Browsing File upload Command Execution Process Management Desktop viewing Device Management Turn Off HomePC Browsing In Browsing user can view any directories in his HomePC.The user has the option to delete, update, rename his files. view users Delete users
10
SREELAKSHMI.K.S
Smartx web
File Upload In file transfer the clients can transfer files to RemotePC. It also prints the message for successful completion. The user is authenticated for his login name and password, which was provided to him during the registration process. If the user fails to give his proper login id or password, an error message is displayed to him indicating that the login id does not exist. Command Execution Command execution means we can execute commands remotely. For example if we type command cmd then it will be executed in that remote system. Process Management We can control the process of that system. We can manage the processes running on that system. For example we can kill a process running on that system. It is also possible to spawn a new process in that system. We can also list all the processes running on the system. Desktop Viewing In this we can view the desktop of the remote system. It displays the screen of another computer (via Internet or network) on your own screen. Device Management Device controlling means we can control the devices connected to the system, for example we can use the mouse and keyboard. Also we can use other devices connected to that computer like webcam. User Interface Design Input Design Input design is the process of converting user originated inputs to a computer based format. Input data are collected and organized into a group of similar data. Inaccurate input data is the most common cause of data processing errors. Effective input design minimizes errors made by data entry operators. The goal of designing input data is to make entry as easy, logical and free from errors as possible. In addition to the original form considerations such as collecting only required data, grouping similar or related data, input design requires consideration of the needs of the data entry operator
11
SREELAKSHMI.K.S
Smartx web
The first thing to be noted in the input design is the type of data and the medium through which data can be entered into the system. All data are entered through the keyboard. The user is also allowed to use the mouse to select different options. Different errors that may occur while entering data, like non-numeric data in a numeric field, are controlled in the input design. Output Design:Computer output is the important and direct source of information to the user. Efficient, intelligible output design should improve the systems relationships with the user and helps in decision making. They also provide a permanent hard copy of these results for later consultation. Output design is the process that involves designing necessary inputs that are to be given to the users according to their requirements. The first step in output design is to determine what information is to be presented to the user. Here the output data is the various reports generated. The second step is to decide whether to display or print the output. In the system provisions is given to display, print or store the output on the disk. As a final step the data are arranged in an accessible format. The arrangement of information on display or printed document is termed as layout.
In order to the whole system we divide it into 3 modules:
1. User Authentication 2. Upload 3. Download 1.User Authentication Module A user is allowed to enter the system if and only if the administrator allows him to do so. After the administrator allows him to enter the system he has to undergo his own validation where he has to enter his own Username and Password Which are sent as encrypted text to the server where his validation is done. If valid he may access the features of our application. 2. Upload Module
12
SREELAKSHMI.K.S
Smartx web
In this module we upload the file to a specified location in the server. We has an upload interface which gets the source location and sent to the destination. 3. Download Module In this module we specify the source location in the server and the specified location to save that file in the client side. 4.2 Data Design:4.2.1Schema Design:The database may be defined as an organized collection of related information. The organized information serves as a base from which further recognizing can be retrieved desired information or processing the data. The most important aspect of building an application system is the design of tables. In our present project the database consists of following table. The table structure shown below: The database consists of 1 table.
Table 1:user_reg Primary key:userid Fieldname Fname Lname Address Userid Pass Email Passwordhint Ans Type varchar(50) varchar(50) varchar(50) varchar(50) varchar(50) varchar(50) varchar(50) varchar(50) Null Key
Primary key
4.2.2Data Integrity and Constraints:In this project the data security, data validation checking methods are applied using a password authentication. All the data, which is entered by the user and the administrator, will be validated. Users should enter their user name and password for the requesting access. Only the administrator can add, delete or modify the users. This single point control ensures better security.
13
SREELAKSHMI.K.S
Smartx web
Procedural Design Procedural design mainly concentrates on procedures in the project. The pseudo code =helps to identify each task of each procedure
Operational structure
Administrator module Initiator is powerful user who can perform the following functions: view users Delete users
Only administrator can add, delete or modify the users. User module Login into the server by entering the user name and password. Once he logged into the system, he can access files and external devices (webcam, printer) from HomePC. The user is authenticated for his login name and password, which was provided to him during the registration process. If the user fails to give his proper login id and password, an error message is displayed to him Indicating that the login id doesnot exist. User Authentication Module A user is allowed to enter the system if and only if the administrator allows him to do so. After the administrator allows him to enter the system he has to undergo his own validation where he has to enter his own Username and Password Which are sent as encrypted text to the server where his validation is done. If valid he may access the features of our application. Upload Module In this module we upload the file to a specified location in the server. We has an upload interface which gets the source location and sent to the destination. Download Module
14
SREELAKSHMI.K.S
Smartx web
In this module we specify the source location in the server and the specified location to save that file in the client side.
System Testing
Testing is the process of executing a program with the intent of finding errors. Testing is a destructive process. The money invested in the development of tests pays off if enough errors are found which would have been more costly if they would have been detected much later. Tests allow proofing the presence of faults but not the correctness of a program. Examining a program to see if it does not do what it is supposed to do is only half of the battle. The other half is seeing whether the program does what it is not supposed to do. Avoid throw away test cases unless the program is truly a throw-away program. Do not plan a testing effort under the tacit assumption that no errors will be found. The probability of the existence of more errors in a section of a program is proportional to the number of errors already found in that section. System testing is actually a series of different tests whose primary purpose is to fully exercise the computer based system. Although each test has a different purpose, all work to verify that all system elements have been properly integrated and perform allocated functions. The test case design methods applied are White box testing Black box testing Black box testing It is a testing with out knowledge of the internal workings of the item being tested. For example, when black box testing is applied to software engineering, the tester would only know the legal inputs and what the expected outputs should be, but not how the program actually arrives at those outputs. It is because of this that black box testing can be considered testing with respect to the specifications, no other knowledge of the program is necessary. White box testing It is a performed based on the knowledge of how the system is implemented. White box testing includes analyzing data flow, control flow, information flow, coding practices, and exception and error handling within the system, to test the intended and unintended software behaviour. White box testing can be performed to validate whether code implementation follows intended design, to validate implemented security functionality, and to uncover exploitable vulnerabilities.
15
SREELAKSHMI.K.S
Smartx web
White box testing requires access to the source code. Though white box testing can be performed any time in the life cycle after the code is developed, it is a good practice to perform white box testing during the unit testing phase. White box testing requires knowing what makes software secure or insecure.The first step in white box testing is to comprehend and analyze source code, so knowing what makes software secure is a fundamental requirement. Second, to create tests that exploit software, a tester must think like an attacker. Third, to perform testing effectively, testers need to know the different tools and techniques available for white box testing. The three requirements do not work in isolation, but together. Testing Methodologies The following are the testing methodologies: Unit testing Integration testing User acceptance testing Output testing Validation testing
Report generation
Remote PC Management through web, Smart X Web is developed for clients to get ready and easy means of access to devices. The site is mainly developed for a user to make use of online registration. A better Graphical User Interface for both Client Side and Server side is managed. Remote PC Management through web, Smart X Web is very useful in the modern world, where the number of users is growing by leaps and bound. The advantages of this system are: Software to be run in only one PC Works with dynamic IP address Remote device access. Easy and secure File Transfers. User Friendly Easy Signup
16
SREELAKSHMI.K.S
Smartx web
Future Scope and Enhancement of the Project
Smart documents can provide contextual help during the preparation of complicated documents, enabling information sharing across systems and applications. Smart documents can communicate with Web services. If the Web service provides non-sensitive data, there is no need for securing the communication between the smart document and the Web service, but if the Web service provides sensitive and confidential data, security is a must.Smart X Web is software that allows users to access devices connected to their systems from remote locations. Web is necessary in this project. Home pc should be active. Home PC is the personal computer, which is owned by the user. Remote PC is the PC from where the user login for selecting and using a device in the Home PC. For this he uses the http protocol. Server is the master controller of the entire software. It consists of controlling Application level program and it gets the requests from the users of the Remote PC. In this particular project we shall be focusing mainly on the access of web cams connected on the Home .A web server has to be setup. The web server contains the web pages to be displayed in the web site. The software is installed on the home pc then the user can access the devices connected to the system from any location using our website through the Internet. Web is necessary in this software. We would like to make the following enhancements to the project in future Increasing demand for remote pc access Video Streaming facility can be included Alerts can be included Higher level of authentication such as thumb impression can be Mouse controlling should be included implemented
Limitation of the system
The main limitations of our project SMART XW EB
17
SREELAKSHMI.K.S
Smartx web
Internet facility needed Home PC should be active Webcam is required
18
SREELAKSHMI.K.S
S-ar putea să vă placă și
- 3931 - Shape Flakiness Index & Elongation Index - SoilDocument3 pagini3931 - Shape Flakiness Index & Elongation Index - SoilSreenath Menon KÎncă nu există evaluări
- LATEST - Methods For Liquid Limit, Plastic Limit, and Plasticity Index of SoilsDocument11 paginiLATEST - Methods For Liquid Limit, Plastic Limit, and Plasticity Index of SoilsSreenath Menon KÎncă nu există evaluări
- Standard Test Method For Particle-Size Distribution (Gradation) of Soils Using Sieve AnalysisDocument3 paginiStandard Test Method For Particle-Size Distribution (Gradation) of Soils Using Sieve AnalysisSreenath Menon KÎncă nu există evaluări
- Sieve Analysis of Soil (BS)Document2 paginiSieve Analysis of Soil (BS)Sreenath Menon KÎncă nu există evaluări
- Water Absorption of Concrete BS 1881-122: ConcreDocument4 paginiWater Absorption of Concrete BS 1881-122: ConcreSreenath Menon KÎncă nu există evaluări
- Water Absorption of Concrete BS 1881-122: ConcreDocument4 paginiWater Absorption of Concrete BS 1881-122: ConcreSreenath Menon KÎncă nu există evaluări
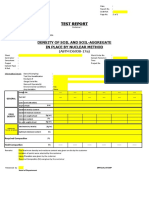
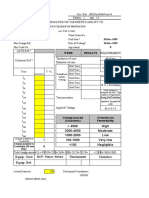
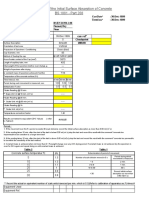
- Density of Soil and Soil-Aggregate in Place by Nuclear Method (Astm)Document2 paginiDensity of Soil and Soil-Aggregate in Place by Nuclear Method (Astm)Sreenath Menon KÎncă nu există evaluări
- 0 Material Safety Data Sheet: Sodium Diphenylamine Sulphonate MSDSDocument5 pagini0 Material Safety Data Sheet: Sodium Diphenylamine Sulphonate MSDSSreenath Menon KÎncă nu există evaluări
- Chloride Migration Test: NORDTEST METHOD (NT BUILD 492 Approved 1999-11)Document8 paginiChloride Migration Test: NORDTEST METHOD (NT BUILD 492 Approved 1999-11)Sreenath Menon K100% (1)
- Items Results: 4000 High 2000-4000 Moderate 1000-2000 Low 100-1000 Very Low 0 100 NegligibleDocument5 paginiItems Results: 4000 High 2000-4000 Moderate 1000-2000 Low 100-1000 Very Low 0 100 NegligibleSreenath Menon KÎncă nu există evaluări
- Determination of The Initial Surface Absorption of Concrete BS 1881 - Part 208Document8 paginiDetermination of The Initial Surface Absorption of Concrete BS 1881 - Part 208Sreenath Menon KÎncă nu există evaluări
- Items Results: 4000 High 2000-4000 Moderate 1000-2000 Low 100-1000 Very Low 0 100 NegligibleDocument4 paginiItems Results: 4000 High 2000-4000 Moderate 1000-2000 Low 100-1000 Very Low 0 100 NegligibleSreenath Menon KÎncă nu există evaluări
- Water Permeability of ConcreteDocument4 paginiWater Permeability of ConcreteSreenath Menon KÎncă nu există evaluări
- Research - Lab Fine Chem Industries: Certificate of AnalysisDocument1 paginăResearch - Lab Fine Chem Industries: Certificate of AnalysisSreenath Menon KÎncă nu există evaluări
- SOIL - 749742-749744 JP (Asbestos, Magnesium Pending) PDFDocument3 paginiSOIL - 749742-749744 JP (Asbestos, Magnesium Pending) PDFSreenath Menon KÎncă nu există evaluări
- Sreenath K Menon: Technical SkillsDocument2 paginiSreenath K Menon: Technical SkillsSreenath Menon KÎncă nu există evaluări
- Nitrate PDFDocument10 paginiNitrate PDFUmi NazaliaÎncă nu există evaluări
- Evaluation of AASHTO T 324 Hamburg - PDFDocument26 paginiEvaluation of AASHTO T 324 Hamburg - PDFnishant100% (1)
- Radiation Protection ManualDocument65 paginiRadiation Protection ManualSreenath Menon KÎncă nu există evaluări
- Account Opening FormDocument12 paginiAccount Opening FormSreenath Menon KÎncă nu există evaluări
- Evaluation of AASHTO T 324 Hamburg - PDFDocument26 paginiEvaluation of AASHTO T 324 Hamburg - PDFnishant100% (1)
- Evaluationof AASHTOT324 HamburgDocument31 paginiEvaluationof AASHTOT324 HamburgSreenath Menon KÎncă nu există evaluări
- Bill No. 35: Ecological Site Works For The Offshore Fishery PackageDocument5 paginiBill No. 35: Ecological Site Works For The Offshore Fishery PackageSreenath Menon KÎncă nu există evaluări
- IGC3 - Exam TemplateDocument11 paginiIGC3 - Exam TemplateSreenath Menon KÎncă nu există evaluări
- Live OS With File ManagerDocument11 paginiLive OS With File ManagerSreenath Menon KÎncă nu există evaluări
- Environmental Sampling Method StatementDocument10 paginiEnvironmental Sampling Method StatementSreenath Menon KÎncă nu există evaluări
- Hardness Conversion ChartDocument1 paginăHardness Conversion ChartIrwan NugrahaÎncă nu există evaluări
- Sodium and Softening of Bitumen 2Document1 paginăSodium and Softening of Bitumen 2Sreenath Menon KÎncă nu există evaluări
- Cyberoam Installation Guide PDFDocument27 paginiCyberoam Installation Guide PDFSreenath Menon KÎncă nu există evaluări
- CompressiveMachinePhotsand DetailsDocument11 paginiCompressiveMachinePhotsand DetailsSreenath Menon KÎncă nu există evaluări
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeDe la EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeEvaluare: 4 din 5 stele4/5 (5794)
- The Yellow House: A Memoir (2019 National Book Award Winner)De la EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Evaluare: 4 din 5 stele4/5 (98)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryDe la EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryEvaluare: 3.5 din 5 stele3.5/5 (231)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceDe la EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceEvaluare: 4 din 5 stele4/5 (895)
- The Little Book of Hygge: Danish Secrets to Happy LivingDe la EverandThe Little Book of Hygge: Danish Secrets to Happy LivingEvaluare: 3.5 din 5 stele3.5/5 (400)
- Shoe Dog: A Memoir by the Creator of NikeDe la EverandShoe Dog: A Memoir by the Creator of NikeEvaluare: 4.5 din 5 stele4.5/5 (537)
- Never Split the Difference: Negotiating As If Your Life Depended On ItDe la EverandNever Split the Difference: Negotiating As If Your Life Depended On ItEvaluare: 4.5 din 5 stele4.5/5 (838)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureDe la EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureEvaluare: 4.5 din 5 stele4.5/5 (474)
- Grit: The Power of Passion and PerseveranceDe la EverandGrit: The Power of Passion and PerseveranceEvaluare: 4 din 5 stele4/5 (588)
- The Emperor of All Maladies: A Biography of CancerDe la EverandThe Emperor of All Maladies: A Biography of CancerEvaluare: 4.5 din 5 stele4.5/5 (271)
- On Fire: The (Burning) Case for a Green New DealDe la EverandOn Fire: The (Burning) Case for a Green New DealEvaluare: 4 din 5 stele4/5 (74)
- Team of Rivals: The Political Genius of Abraham LincolnDe la EverandTeam of Rivals: The Political Genius of Abraham LincolnEvaluare: 4.5 din 5 stele4.5/5 (234)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaDe la EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaEvaluare: 4.5 din 5 stele4.5/5 (266)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersDe la EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersEvaluare: 4.5 din 5 stele4.5/5 (344)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyDe la EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyEvaluare: 3.5 din 5 stele3.5/5 (2259)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreDe la EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreEvaluare: 4 din 5 stele4/5 (1090)
- The Unwinding: An Inner History of the New AmericaDe la EverandThe Unwinding: An Inner History of the New AmericaEvaluare: 4 din 5 stele4/5 (45)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)De la EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Evaluare: 4.5 din 5 stele4.5/5 (121)
- Her Body and Other Parties: StoriesDe la EverandHer Body and Other Parties: StoriesEvaluare: 4 din 5 stele4/5 (821)
- Taopix Online Installation Guide 2015r2.1 21 August 2015Document92 paginiTaopix Online Installation Guide 2015r2.1 21 August 2015Fernando CarneiroÎncă nu există evaluări
- Mohsin DocumentationDocument96 paginiMohsin Documentationch.shahzad juttÎncă nu există evaluări
- Test CasesDocument4 paginiTest Casesdeex arnoldÎncă nu există evaluări
- Information Logging Standard PDFDocument4 paginiInformation Logging Standard PDFNZÎncă nu există evaluări
- WCDMA Performance ManagementDocument112 paginiWCDMA Performance ManagementANTENEH GE100% (1)
- CmelocalDocument42 paginiCmelocalMatthew ShawÎncă nu există evaluări
- Registering For ADP Portal - 2023Document8 paginiRegistering For ADP Portal - 2023negrapujolsÎncă nu există evaluări
- Hospital Management SystemDocument4 paginiHospital Management SystemAnu KumarÎncă nu există evaluări
- LDCE For He Promotion To SDE Grade Under 33 Perc Quota To Be Held On 15-02-15 - Notification 13-11-14Document8 paginiLDCE For He Promotion To SDE Grade Under 33 Perc Quota To Be Held On 15-02-15 - Notification 13-11-14KaranGargÎncă nu există evaluări
- Furuno CBT InstructionsDocument2 paginiFuruno CBT InstructionsRakesh Kumar0% (1)
- Symantec Vip Integration Guide For Palo Alto Networks Globalprotect VPNDocument21 paginiSymantec Vip Integration Guide For Palo Alto Networks Globalprotect VPNecardoneÎncă nu există evaluări
- Configuracion Hikvision Con NASDocument19 paginiConfiguracion Hikvision Con NASHidalgo FrancoÎncă nu există evaluări
- CMPG224 SRS Group..1Document17 paginiCMPG224 SRS Group..1Smangaliso ClementÎncă nu există evaluări
- Canto White Paper - Building A Better DAMDocument7 paginiCanto White Paper - Building A Better DAMRicardo Espinosa ReoÎncă nu există evaluări
- Apex Weblogic ConfigurationDocument33 paginiApex Weblogic ConfigurationBirendra PadhiÎncă nu există evaluări
- Books4u: Fast Track Shopping Software SystemDocument18 paginiBooks4u: Fast Track Shopping Software SystemRrr320Încă nu există evaluări
- UniFi Controller V5 UG PDFDocument158 paginiUniFi Controller V5 UG PDFTinin MgÎncă nu există evaluări
- DatAdvantage 6.0 Report OverviewDocument10 paginiDatAdvantage 6.0 Report OverviewDineshÎncă nu există evaluări
- E Book - Dos and Don'ts For UI DesignDocument55 paginiE Book - Dos and Don'ts For UI DesignJonathan60% (5)
- Privileged Access Management As A Service For Dummies Cyberark Special EditionDocument65 paginiPrivileged Access Management As A Service For Dummies Cyberark Special EditionAnkit100% (1)
- Bank Management System-ShitalDocument35 paginiBank Management System-ShitalDhruti GadhiyaÎncă nu există evaluări
- P23 - Holocaust Inventory SystemDocument30 paginiP23 - Holocaust Inventory SystemTajudeen TajuÎncă nu există evaluări
- IGL 7.2.1 Database Setup and Management GuideDocument35 paginiIGL 7.2.1 Database Setup and Management GuideVitor Stachetti de FreitasÎncă nu există evaluări
- E116818-1672849200036-232679-1184-1620009562546-Unit 28 - Prototyping - Reworded 2021Document67 paginiE116818-1672849200036-232679-1184-1620009562546-Unit 28 - Prototyping - Reworded 2021ravindupanduwawala321Încă nu există evaluări
- SS7G41 Migration Guide Issue01Document16 paginiSS7G41 Migration Guide Issue01CatalinÎncă nu există evaluări
- Passing Unix Linux Audit With Power BrokerDocument11 paginiPassing Unix Linux Audit With Power Brokerjngure100% (2)
- License Administration WorkbenchDocument15 paginiLicense Administration WorkbenchVishlashak KapoorÎncă nu există evaluări
- #100003 - Login IssueDocument3 pagini#100003 - Login IssueluckybuildingÎncă nu există evaluări
- 2) VRP Basic ConfigurationDocument37 pagini2) VRP Basic ConfigurationAngel ClavelÎncă nu există evaluări
- How To Create A APEX Workspace in Oracle 11g XE - MacLochlainns WeblogDocument5 paginiHow To Create A APEX Workspace in Oracle 11g XE - MacLochlainns WeblogAlberto Moreno LópezÎncă nu există evaluări