Documente Academic
Documente Profesional
Documente Cultură
Data Reliability and Security For SCADA Systems-Rev F
Încărcat de
api-3766362Titlu original
Drepturi de autor
Formate disponibile
Partajați acest document
Partajați sau inserați document
Vi se pare util acest document?
Este necorespunzător acest conținut?
Raportați acest documentDrepturi de autor:
Formate disponibile
Data Reliability and Security For SCADA Systems-Rev F
Încărcat de
api-3766362Drepturi de autor:
Formate disponibile
Reliable and Secure Data Communications for SCADA Systems
CIGRE 2005 Conference Cuernavaca, Mexico.
Author: Dan Ehrenreich, Motorola Inc.
Overview
Supervisory Control and Data Acquisition (SCADA) solutions provide a base for operation of Distribution Management
Systems (DMS) and Distribution Automation (DA). SCADA provides means for computerized handling of remote
installations, minimizing the number and length of outages, reducing the cost of maintenance and achieving safer control
of substations. System parameters shown on the SCADA screens must present reliable and precise information reflecting
the infrastructure condition. Equivalently to that, commands sent to remote sites by the SCADA operator must be
promptly executed and the back indication information sent to the control center computer should be reliable as well.
Modern SCADA systems allow seamless network communication from any Remote Terminal Units (RTUs) to any
RTU and from any RTU to the SCADA computer via the Front End processor (FEP), IP Gateway, OPC Server, etc.
While implementing a DMS/DA system solution, electric utilities must pay special attention to issues, which are unique
for data communications1). Therefore SCADA system engineers must also have high level of applicable
communication expertise to assure that the telemetry functions will properly operate.
Implementation of SCADA solutions requires use of secure communications in order to avoid fraud related events to
take place. Control systems can be vulnerable to variety of attacks, examples of which have already occurred.
Successful attacks on control systems could have devastating consequences, such as endangering public health and
safety; damaging the environment; or causing a loss of production, generation or distribution of public utilities 10).
Among the commonly cited SCADA security threats are the following 12):
a) Interception of Messages - Illegal “listening “ and recording of data transactions among remote sites and the
control center is a relatively simple/ easy to implement action.
b) Fabrication of Messages - Initiated creating of forged messages intended to execute specific (risky) functions at
remote sites or making the control center to “believe” that some event happened.
c) Replay of Messages – Simply implemented by delayed resending of intercepted “true” messages from the
control center to remote site or vice versa, in order to “confuse” the site receiving the message.
d) Corrupted Message - Resending of intercepted messages after the content of the original message was
intentionally “altered” to other values or presenting a “not true” condition.
Implementing high level of data security across the network achieved by encryption, use of password and authentication
methods (as outlined in this paper), may result in major operating and cost benefits for the utility as they can add more
operating functions to their system without being worried about SCADA related frauds 8).
Data Communication
Electric utility experts have learned over years that SCADA plays an important part in providing means for upgrading
their operating productivity. To achieve these goals one must implement a system, which is based on high quality
communications. Among the popular communication media used in SCADA systems are fiber-optic links, telephone
and leased lines, VHF/UHF conventional radio including the 800 MHz trunked radio, analog and digital wireless
networks, digital infrastructure operating over Internet Protocol (IP) 7), UHF and 900 Mhz Multiple Address Systems
(MAS), microwave, satellite, etc. 3).
When designing wireless communication links between field-installed RTUs and the control center, the system
integrator must a special attention has to be paid to selecting the right data communication protocol, which in a properly
designed system is carefully chosen for the specific media 5).
CIGRE 2005, Cuernavaca Mexico 1 of 6 D2-118
The International Systems Organization (ISO) and Open Systems Interconnection (OSI) defined data communication
the seven-layer protocol stack, which become the industry standard also for SCADA. The key advantages of this
method are that each layer handles a dedicated set of functions and that changes in those functions have no effect on
functions executed in other layers. Figure 1 below briefly outlines this concept.
End user applicati on process
Application Layer * Includes all transactions related to SCADA system operation
Presentation Layer Provides means for p rotocol conversion, encryption/decryption
Session Layer Provides means for mu ltip le entities to exchange data simu ltaneously
Transport Layer Handles data frag menting and confirming end to end data integrity
Network Layer Provides redundancies and routing of messages via network links
Link Layer * Provides means to establish, maintain and terminate connections
Physical Layer * Defines the physical and electrical interface to the network
Data communication network * Included in the three layer protocol
Figure 1. Description of the ISO/OSI Protocol Stack
Networked Communications
In a complex system, one may have to utilize a combination of several media types, accordingly selected for all
segments of the network. As shown in Figure 2 below, some RTUs are configured to serve as a data communication
node for routing commands to and from other RTUs. Using the seven-layer protocol (Figure 1 above), upon receiving a
set of frames the related RTU detects whether those frames were addressed to that site or were intended for another
RTU or the FEP. RTUs, which are acting as Store and Forward (S&F) repeaters or as communication nodes, will
forward the received frames to their final destination (or the next intermediate node). Once the data transaction among
the sites is done and a complete error-free message reaches its designated site, that RTU will send an "end-to-end"
acknowledgement to the source (RTU or FEP, or vice versa) confirming the integrity of the received message.
Note: Most of widely used three-layer protocols, (such as the IEC 60870-5-101 or DNP 3.0) do not have the Network
Layer and therefore RTUs cannot be utilized as a communication node.
Printer Primary
MCC
RTU & Data
Local Ethernet Comm. Node
IP
Main
Line Gateway
ToolBox
Based IP Wireline Comm.
Remote Ethernet Backup
Prime Link Link
Secondary RTU & Data
TS RTU & Data
MCC Comm. Node
(SLIP) Comm. S&F
Backup
Prime Link Link
Remote Wireline
ToolBox Comm.
RTU & Data
Comm.
Node
RTU & Data
Prime Link Comm. Node
Fig.2 Network Communications in a SCADA/DMS System
CIGRE 2005, Cuernavaca Mexico 2 of 6 D2-118
Data Reliability
Use of robust and efficient error handling solutions are especially important for wireless SCADA systems, which
operate in "Report-by-Event" rather than "Polling" mode. Here several RTUs may simultaneously detect the same fault,
which occurred along the power grid or in the substation. In such case, all RTUs (which “saw” the same event) initiate
an unsolicited message (Report by Event) to the FEP (directly or via communication nodes) and as a result of that some
frames might "collide" over the wireless channel and get “damaged”.
To avoid loss of messages, the selected SCADA protocol must include a reliable error handling mechanism, specifically
optimized for the type of communications media used by the system. When dealing with wireless data networks the
following error handling mechanisms are typically implemented:
a) Forward Error Correction (known as FEC) method is often used for mobile wireless communications. Here the
FEC code is packed along with the data and it adds a large overhead to the message. Upon receiving the message, the
data equipment at the destination site is capable of detecting as well as correcting the error.
Note: This principle works well subject to two conditions; a) the initial Bit Error Rate (BER) level is very low b) failure
to correct the digital string must not lead to a critical/dangerous event. Another problem might rise should the correction
code itself be damaged. Consequently, one may consider using the FEC method only for non-critical applications such
as: wireless fax, paging, voice, and image-communication but not for SCADA communications.
b) Error handling by Frame Retry Mechanism is a more robust process compared to the FEC method. Here, all
data frames sent from one RTU (or a data node) to another RTU, or from an RTU to the FEP, (or vice versa) are being
checked for errors. This process generates a confirmation message that refers to all received healthy frames. Upon
receipt of a "partial confirmation", (indicating that some frames were detected as “incomplete”) the message source site
will resend only the faulty (not confirmed) frames. Consequently the receiving site will test again the integrity of the
resent frames and reconfirm receipt of the complete message. Having such an advanced option embedded in the
communication process provides an even higher level of data reliability, as messages may reach their destination in
spite of temporary or permanent link malfunction
Note: If part of the network or a specific RTU (serving as a communication node) fails and it cannot communicate with
the designated site, the entire message will not be confirmed. In such case, the sending RTU may re-route the related
frames (or the entire message) via a pre-defined backup link or via alternative data nodes..
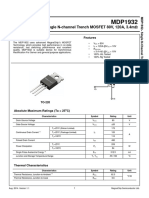
Data Security Considerations
Utilities and SCADA operators are today more concerned about fraud and hackers, which may attack the operation of
their system; therefore secure data communications plays an important role. What is missing from current cyber security
products and services? SCADA intelligence. The current solutions do not identify attacks on SCADA protocols or
security events in SCADA application logs. This is a major gap, since there are inherent security vulnerabilities in
protocols and legacy applications that were designed before SCADA cyber security was an issue 12). Figure 3 bellow
shows some of data security concerns and how are they rated.
Implementati on
Specific Concern How Severe Difficulty
Record and Ret ransmit L H E D
Change of Co mmand L H E D
Access to RTUs L H E D
Access to MCC L H E D
Viruses and Codes L H E D
L- Low H-High E-Easy D-Difficu lt
Figure 3. SCADA communication concerns
CIGRE 2005, Cuernavaca Mexico 3 of 6 D2-118
These concerns are especially valid for critical SCADA systems (such as remote control of pole mounted switchgears
and substations), which require wireless communication over wide geographical area. A solution to reduce the risk of
fraud is provided using three possible security protection measures as per the following:
a) Password protection is the most basic means for upgrading communication security, and it also helps avoiding
not intended cross communication via RTUs belonging to two not related SCADA systems. Here, each message is
equipped with a password code, which eliminate such event.
Note: While dealing with data security on the control center level, usually there are multiple password levels; operator
level, administrator level and programmer level and other security measures. These methods for upgrading the control
center security and are not covered in this paper. More information can be found in a paper presented by during the
Distributech 2005 11).
b) Data Encryption is the next level SCADA protection and its purpose is to minimize the possibility that
someone may "listen" to the communication channel and monitor the system operation via transmitted messages and
commands. For example, SCADA systems may utilize Tiny Encryption Algorithm (TEA), Data Encryption Standard
(DES), Triple DES, Advanced Encryption Standard (AES), etc. Using these solutions, the encryption is implemented on
the "frame" level, and therefore the seven-layer protocol concept is especially suitable for implementing frame-based
encryption (see Fig. 1 above). Correct receipt and processing of the received message requires use of a particular "key",
stored in the RTU, which in highly critical systems is periodically replaced /changed.
Note: Integration of enhanced encryption methods for SCADA systems is also in line with the strategy of Homeland
Security Advanced Research Projects Agency (HSARPA) under topic FY04.1-008: Advanced Secure SCADA and
Related Distributed Control Systems.
Over recent years the industry started promoting introduction of a future standard for SCADA encryption. This initiative
started as a workgroup at the Gas Technology Institute and it was designated as AGA 12. The fist step of this work (Part
1) is now completed and is known as “Cryptographic protection of SCADA communications: Background, policies and
test plan. The current AGA 12 document is now available on the web http://gtiservices.org/security/index.shtml and its
main objectives are the following 13):
• Save SCADA owners time & money
• Be comprehensive for SCADA
• Recommend Secure practices
• Uses NIST (National Institute of Standards and Technology) approved crypto algorithm
• Easier to implement than “role your own”
Following the introduction of AGA 12 Part 1, there are additional parts on the way, defined as Part 2, 3 and 4.
c) Authentication is even a higher-level security measure implemented for SCADA protection. The principle of
this method is to limit the time validity of the transmitted message (time measured from message transmission). Of
course the authentication method requires that the data protocol will support transmission of time stamped messages as
well as support network-wide time synchronization. The time synchronization process must be encrypted as well.
Note: The widely used SCADA protocols such as DNP 3.0 and IEC 60870-5-101 are currently not supporting
authentication. The standard MODBUS protocol is even weaker from this point of view, as it does not support precise
(milliseconds range) transmission of time stamped messages. (A degraded accuracy time stamp reporting can be
achieved by adding time as part of the application layer).
Figure 3 bellow outlines an example for a partially secured SCADA system using the time-based authentication. Here
the system includes RTUs linked to unauthenticated segment, and some RTUs linked to the authenticated (red frame)
part of the network. As shown, several RTUs are acting as the Synchronized Server (SS) provide precise time reference
to the Synchronized Client (SC) marked RTUs, while some other RTUs perform both SS and SC functions. A separate
port in the RTU may provide interface to the unauthenticated part of the network.
Encryption and Authentication methods are completely different processes aimed to increase the security of a SCADA
system. Upon preference, both methods can be combined in the same system. They may simultaneously operate without
interrupting each the other, thus further boosting the SCADA system security. Transmission of authenticated messages
via an encrypted network will make it practically impossible for anyone to intrude the SCADA system and cause a fraud
by retransmission of a (true) message, which was earlier illegally intercepted and recorded.
CIGRE 2005, Cuernavaca Mexico 4 of 6 D2-118
Legend
Printer SCADA
Central Unauthenticated Link
IP Network
Authenticated Link
IP SC Synchronized Client
Gateway (Authenticated Link)
SS Synchronizing Server
(Line 1) RS-232
SC/SS Client/Server
(Unauthenticated IP Link) SC/SS SC
SS RS-232
(Authenticated
Link)
Authenticated
Radio sub-network Dial
SC
(Authenticated RF Link) (Unauthenticated
RS-485 PSTN Link)
(Authenticated Link)
SC
SC SC/SS
SC SC
Figure 3. Authenticated Data System
Note: Transmission of encrypted data messages is in some countries subject to government regulation, and utility
operators shall consider obtaining permission prior investing into implementation of such system.
Summary and Conclusions
The advanced features offered by using the ISO/OSI compatible seven-layer protocol produce enhanced data reliability
and enhanced data security. These subjects were specifically highlighted in this paper since SCADA engineers, who are
lacking the necessary expertise in data communications, might overlook the importance of selecting the optimal media
and a suitable data protocol.
Another major advantages of the seven-layer concept are that modifications in the system architecture will not affect
SCADA application or operation of other functions defined within their designated layers. This concept allows
integrating multiple media in a network, flexible changes of network structure, upgrading the communication network
with encryption and authentication, etc. Furthermore, it allows implementation of system diagnostics, remote
calibration, smart RTU decisions based on imported data from other RTUs, update of programs via the network,
download and upload of new operating parameters, etc.
Note: While some widely used three-layer protocols (DNP 3.0 or IEC 60870-5-101) may perform similar system
processes achieved via their application layer programming, in the seven-layer type ISO/OSI protocol these functions
are "built-in" within the respective layers.
Consequently, the integration of a wireless SCADA system with the seven-layer communication protocol generates
major operating and cost benefits to the customer and more than justifies the investment.
@@@@@@@@@
About the Author:
Dan Ehrenreich is the Marketing Manager for SCADA Business Development in Motorola, and among his tasks are
introduction of MOSCAD based solutions for Electricity and Oil and Gas automation systems, establishment of
alliances with business partners and market studies. Dan has a Bachelor degree in Electronics Engineering from the
University of Ben Gurion in Israel. He has been with Motorola since 1991, and he also provides sales support for
Motorola SCADA solutions to Central and Latin America customers.
--------------------------------------------------------------------------------------------------------------------------------------
For more information on Motorola MOSCAD Solutions refer to our web site: http://www.moscad-systems.com.
Dan can be contacted via email: dan.ehrenreich@motorola.com
CIGRE 2005, Cuernavaca Mexico 5 of 6 D2-118
References:
1. Implementation of Intelligent Data Communications in DA Systems, John Grothman, Dan Ehrenreich,
DA/DSM'93, Palm Springs, January 1993
2. Cost Benefits resulting from use of Integrated Communications for Distribution Automation, Dan Ehrenreich,
Shlomo Liberman, DA/DSM'95 Asia, and Singapore 1995.
3. Operating benefits achieved by use of advanced communications Protocols for DA/DSM systems, Dan
Ehrenreich, Dr. Salomon Serfaty, DA/DSM Europe, Vienna 1996.
4. Dual RF channels improve grid operations, Dan Ehrenreich, Utility Automation Europe, Vol. 1, No.1 Summer
1996
5. Integration of RF communications for Distribution Automation with Dual Redundancy, Dan Ehrenreich,
Samuel Katar, DA/DSM 97 Asia, Singapore 1997.
6. Data Communications for Oil and Gas SCADA Systems. Dan Ehrenreich, Shlomo Liberman, PETROMIN
magazine October 1999.
7. Wireless IP Networks Serve Distribution Automation Systems, Dan Ehrenreich, Utility Automation Magazine,
August 2000
8. Data Reliability and Data Security Considerations for SCADA Systems Dan Ehrenreich Presented at
ENTELEC April 2004, San Antonio, Texas
9. Data Communications Reliability of Wireless SCADA Systems, Dan Ehrenreich World Pipelines Magazine,
February 2004
10. Critical Infrastructure protection; Challenges in Securing Control Systems. GAO Highlights, Gao-04-140
Testimony October 1, 2003
11. Intrusion Detection and Security Monitoring of SCADA Networks; Dale Peterson, Distributech Conference
San Diego USA, January 2005
12. Cyber Security Tools for SCADA, John Tengdin, OPUS publishing, Distributech conference (DNP 3 user
group meeting) San Diego USA, January 2005
CIGRE 2005, Cuernavaca Mexico 6 of 6 D2-118
S-ar putea să vă placă și
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)De la EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Evaluare: 4.5 din 5 stele4.5/5 (121)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryDe la EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryEvaluare: 3.5 din 5 stele3.5/5 (231)
- Grit: The Power of Passion and PerseveranceDe la EverandGrit: The Power of Passion and PerseveranceEvaluare: 4 din 5 stele4/5 (588)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaDe la EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaEvaluare: 4.5 din 5 stele4.5/5 (266)
- Never Split the Difference: Negotiating As If Your Life Depended On ItDe la EverandNever Split the Difference: Negotiating As If Your Life Depended On ItEvaluare: 4.5 din 5 stele4.5/5 (838)
- The Emperor of All Maladies: A Biography of CancerDe la EverandThe Emperor of All Maladies: A Biography of CancerEvaluare: 4.5 din 5 stele4.5/5 (271)
- The Little Book of Hygge: Danish Secrets to Happy LivingDe la EverandThe Little Book of Hygge: Danish Secrets to Happy LivingEvaluare: 3.5 din 5 stele3.5/5 (400)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeDe la EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeEvaluare: 4 din 5 stele4/5 (5794)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyDe la EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyEvaluare: 3.5 din 5 stele3.5/5 (2259)
- Shoe Dog: A Memoir by the Creator of NikeDe la EverandShoe Dog: A Memoir by the Creator of NikeEvaluare: 4.5 din 5 stele4.5/5 (537)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreDe la EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreEvaluare: 4 din 5 stele4/5 (1090)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersDe la EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersEvaluare: 4.5 din 5 stele4.5/5 (344)
- Team of Rivals: The Political Genius of Abraham LincolnDe la EverandTeam of Rivals: The Political Genius of Abraham LincolnEvaluare: 4.5 din 5 stele4.5/5 (234)
- Her Body and Other Parties: StoriesDe la EverandHer Body and Other Parties: StoriesEvaluare: 4 din 5 stele4/5 (821)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceDe la EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceEvaluare: 4 din 5 stele4/5 (895)
- The Unwinding: An Inner History of the New AmericaDe la EverandThe Unwinding: An Inner History of the New AmericaEvaluare: 4 din 5 stele4/5 (45)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureDe la EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureEvaluare: 4.5 din 5 stele4.5/5 (474)
- On Fire: The (Burning) Case for a Green New DealDe la EverandOn Fire: The (Burning) Case for a Green New DealEvaluare: 4 din 5 stele4/5 (74)
- The Yellow House: A Memoir (2019 National Book Award Winner)De la EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Evaluare: 4 din 5 stele4/5 (98)
- Connection & Operation of RS-232 Option For BF250 Mark 8 ControlDocument17 paginiConnection & Operation of RS-232 Option For BF250 Mark 8 Controlnigh_tmareÎncă nu există evaluări
- RAN KPI IntroductionDocument41 paginiRAN KPI IntroductiongbhatngarÎncă nu există evaluări
- How Can SCADA Systems Optimally Operate Over GPRS Networks (F)Document5 paginiHow Can SCADA Systems Optimally Operate Over GPRS Networks (F)api-3766362Încă nu există evaluări
- Distribution Automation AppDocument10 paginiDistribution Automation Appapi-3766362Încă nu există evaluări
- Lacpec FinalBDocument5 paginiLacpec FinalBapi-3766362Încă nu există evaluări
- Entelec 2004 Published PaperDocument9 paginiEntelec 2004 Published Paperapi-3766362Încă nu există evaluări
- Wireless Data Communication For SCADA Systems-GDocument5 paginiWireless Data Communication For SCADA Systems-Gapi-3766362Încă nu există evaluări
- Operating Benefits Achieved With SCADA For Water Distribution-FDocument6 paginiOperating Benefits Achieved With SCADA For Water Distribution-Fapi-3766362Încă nu există evaluări
- User Manual For ItronSL7000 Electricity Metering Modem v2 60 En-1Document16 paginiUser Manual For ItronSL7000 Electricity Metering Modem v2 60 En-1Santiago MuñozÎncă nu există evaluări
- Module 1 It Application Tools in Business - CompressDocument38 paginiModule 1 It Application Tools in Business - CompressJames Ryan AlzonaÎncă nu există evaluări
- EE 201 - HW 1 Solutions W2007Document11 paginiEE 201 - HW 1 Solutions W2007mrm3zaÎncă nu există evaluări
- Notice Installation Vulca Voice EngDocument38 paginiNotice Installation Vulca Voice EngJessica MathisÎncă nu există evaluări
- Transistor Circuit NotesDocument15 paginiTransistor Circuit NotesKim KeatÎncă nu există evaluări
- Chapter 1Document25 paginiChapter 1TalemaÎncă nu există evaluări
- Product Highlights: 28PW6302 28PW6322Document18 paginiProduct Highlights: 28PW6302 28PW6322VoowooÎncă nu există evaluări
- S-Parameter Characterisation of Coaxial To Microstrip TransitionDocument4 paginiS-Parameter Characterisation of Coaxial To Microstrip TransitionjrosouzaÎncă nu există evaluări
- Yamaha Rx-V473 Htr-4065 SMDocument134 paginiYamaha Rx-V473 Htr-4065 SMТатьяна Михайловна0% (1)
- Philips Price List Brochure - Final - Revised - 19-8-20Document10 paginiPhilips Price List Brochure - Final - Revised - 19-8-20vickey kumarÎncă nu există evaluări
- User's Manual: FX - 4DA Analog Output BlockDocument6 paginiUser's Manual: FX - 4DA Analog Output BlockTrần Thanh TiếnÎncă nu există evaluări
- Motorola S10-HD Bluetooth Headphones Manual (EN)Document22 paginiMotorola S10-HD Bluetooth Headphones Manual (EN)Jeff0% (2)
- 2sa1306 - 2sa1306a - 2sa1306bDocument3 pagini2sa1306 - 2sa1306a - 2sa1306bisaiasvaÎncă nu există evaluări
- ARM Instruction SetDocument3 paginiARM Instruction SetnhungdieubatchotÎncă nu există evaluări
- CDMA Vs GSMDocument5 paginiCDMA Vs GSMEbenezer AnnanÎncă nu există evaluări
- Intersil 82c54 - 5Document22 paginiIntersil 82c54 - 5anjanbsÎncă nu există evaluări
- MDP1932 MagnaChipDocument6 paginiMDP1932 MagnaChipVanderMucioÎncă nu există evaluări
- Huawei 3g Counters and Kpis PDFDocument4 paginiHuawei 3g Counters and Kpis PDFsatya vara prasad ballaÎncă nu există evaluări
- AntenaDocument4 paginiAntenaMarcos MontesÎncă nu există evaluări
- IndraDrive Planning ManualDocument310 paginiIndraDrive Planning ManualAaron HerreraÎncă nu există evaluări
- Measurements and Instrumentation (ELE 3202)Document4 paginiMeasurements and Instrumentation (ELE 3202)JithinÎncă nu există evaluări
- Samsung Galaxy J1 Ace Neo (SM-J111F) Service ManualDocument81 paginiSamsung Galaxy J1 Ace Neo (SM-J111F) Service ManualLeonias Adrian100% (1)
- CM700V 32DC AmplifierDocument1 paginăCM700V 32DC AmplifierGapWirelessÎncă nu există evaluări
- Motor ProtectionDocument4 paginiMotor ProtectionadhyarthaÎncă nu există evaluări
- XR2000 IP-PBX Data Sheet: FeaturesDocument3 paginiXR2000 IP-PBX Data Sheet: FeaturesC3RE4LÎncă nu există evaluări
- Foxess 10,5K G10500 220VDocument2 paginiFoxess 10,5K G10500 220Valex reisÎncă nu există evaluări
- IC Dao Đ NG L6599at, 16 PinDocument32 paginiIC Dao Đ NG L6599at, 16 PinchieutimhueÎncă nu există evaluări
- User Manual OpenStage 60-80 HFA HP3000-HP5000Document214 paginiUser Manual OpenStage 60-80 HFA HP3000-HP5000imarestiÎncă nu există evaluări