Documente Academic
Documente Profesional
Documente Cultură
Netflow Basics and Deployment Strategies
Încărcat de
SasiKumar PetchiappanDescriere originală:
Titlu original
Drepturi de autor
Formate disponibile
Partajați acest document
Partajați sau inserați document
Vi se pare util acest document?
Este necorespunzător acest conținut?
Raportați acest documentDrepturi de autor:
Formate disponibile
Netflow Basics and Deployment Strategies
Încărcat de
SasiKumar PetchiappanDrepturi de autor:
Formate disponibile
Networking Fundamentals
Part of the SolarWinds IT Management Educational Series
VoluME 3
NetFlow Basics and Deployment Strategies
This paper examines NetFlow technology and implementation considerations. As part of the Network Fundamentals series, it is intended to provide an introduction to traffic flow analysis and guidelines for implementation.
Networking Fundamentals Volume 3, NetFlow Basics and Deployment Strategies
Page 2
Table of Contents
The Need for Flow Analysis . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3 How does NetFlow Work? . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3 The NetFlow Cache. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3 The NetFlow Exporter . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4 The NetFlow Collector . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 6 Deployment Strategies. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 8 Deployment Planning and Mapping . . . . . . . . . . . . . . . . . . 8 Deployment Planning . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 9 Review . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 9 Related SolarWinds Products . . . . . . . . . . . . . . . . . . . . . . . . . . . 10 About SolarWinds . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 11 About the Author. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 11
Copyright 19952010 SolarWinds. All rights reserved worldwide. No part of this document may be reproduced by any means nor modified, decompiled, disassembled, published or distributed, in whole or in part, or translated to any electronic medium or other means without the written consent of SolarWinds. All right, title and interest in and to the software and documentation are and shall remain the exclusive property of SolarWinds and its licensors. SolarWinds Orion, SolarWinds Cirrus, and SolarWinds Toolset are trademarks of SolarWinds and SolarWinds.net and the SolarWinds logo are registered trademarks of SolarWinds All other trademarks contained in this document and in the Software are the property of their respective owners. SOLARWINDS DISCLAIMS ALL WARRANTIES, CONDITIONS OR OTHER TERMS, EXPRESS OR IMPLIED, STATUTORY OR OTHERWISE, ON SOFTWARE AND DOCUMENTATION FURNISHED HEREUNDER INCLUDING WITHOUT LIMITATION THE WARRANTIES OF DESIGN, MERCHANTABILITY OR FITNESS FOR A PARTICULAR PURPOSE AND NONINFRINGEMENT. IN NO EVENT SHALL SOLARWINDS, ITS SUPPLIERS OR ITS LICENSORS BE LIABLE FOR ANY DAMAGES, WHETHER ARISING IN TORT, CONTRACT OR ANY OTHER LEGAL THEORY EVEN IF SOLARWINDS HAS BEEN ADVISED OF THE POSSIBILITY OF SUCH DAMAGES. Document Revised: Oct 1, 2010
Networking Fundamentals Volume 3, NetFlow Basics and Deployment Strategies
Page 3
The Need for Flow Analysis
In general, Network Management Systems (NMS) perform a couple of basic functions: they tell you when something has failed and they tell you when something is overloaded. Most of the features of an NMS revolve around providing this information in different formats such as reports, alerts, Syslog viewers, trap viewers, et cetera. They answer the questions what happened and when. But when the issue is performance based, there is very little information to answer the why questions, especially with a saturated WAN link, one of the most common performance issues. As a Network Management Engineer, one will eventually get the call Users in site X are complaining the network is slow. Using an NMS, you might find that the link between site X and the headquarters is saturated. You could have received a couple of text messages or pages from the NMS telling you when the link became saturated. The problem is you dont know why the link is saturated. If you could see what type of traffic is using the link, you could see what is causing it. That is what NetFlow, and other related flow analysis protocols do, they capture information about the nature of the flows. Before NetFlow was around, there were some very cumbersome ways to do this, such as placing Y cables on WAN connections allowing a special protocol analyzer appliance to be connected when a link showed unusual behavior. This was expensive, required extra hardware and the results were hard to decipher. A new technology called RMON came about where a protocol analyzing agent was embedded in network equipment. The problem with RMON was that it only applied to LAN connections and bandwidth issues happen much more frequently on the WAN. RMON2 was an improvement as it added fields for network and application layer monitoring as well as support for WAN technologies. Cisco then launched NetFlow and being that Cisco has such a great share of the internetworking equipment market, NetFlow fairly quickly became the defacto standard. With an NMS and Netflow deployed, you are able to see what a link has became saturated, when the time the problem began and why the nature of the traffic on the link. Well see why I call it the nature of the traffic in the next section. For the purpose of this paper, Ill focus on NetFlow, but Ill also point out the differences and similarities with other flow monitoring technologies as appropriate.
How does NetFlow Work?
The term NetFlow is often used interchangeably between the three major components of NetFlow technology: 1. The NetFlow cache 2. The NetFlow exporter on the router or switch 3. The NetFlow collector used to analyze the flow information. The NetFlow cache is the active monitoring of traffic and only exists on a NetFlow enabled device. The NetFlow exporter involves sending completed flow information from the device to a NetFlow collector, such as Orion NetFlow Traffic Analyzer. Here is what the whole thing looks like graphically in a much simplified environment (see Figure 1). Figure 1.
Heres what is happening step-wise: Users in the remote office are accessing the information from the corporate servers and the Internet. In NetFlow terminology, the machines participating in a flow are known as endpoints. As the users data flows into R2s WAN interface, the NetFlow ingress cache is making records about the flows and saving them in R2s memory. As flows expire (well cover how that happens later) R2s NetFlow exporter sends the expired flow information to the NetFlow collector. The NetFlow collector stores and presents information about user flows. This might seem simple a first glance but there is a lot going on to make all this work. To best understand all the moving pieces well examine the NetFlow cache first, and then look at the exporter and collector.
The NetFlow Cache
Everything in NetFlow begins with the flow cache. The cache has a couple of basic jobs to do: Interrogate data headers and either mark it as a new flow or add to part of an existing flow. Keep track of flow timers and other factors and when a flow is considered complete, send it to the exporter (if one exists) and delete the flow information off of the device. This process is known as flow aging. The NetFlow cache only keeps information on current or non-expired flows. This brings up an excellent question: what constitutes a flow and how does a flow expire? NetFlow v5 is the most common version in use so well take a look at the v5 flow format. As data enters the NetFlow enabled interface, the IP header is examined and flows are defined as having values that match the following 7 key fields uniquely:
Networking Fundamentals Volume 3, NetFlow Basics and Deployment Strategies
Source IP address. Destination IP address. Source port number. Destination port number Layer 3 protocol type ToS byte value The IfIndex number, also called the logical interface number When a packet enters the NetFlow enabled interface and all seven of these key fields match an existing flow, it is not considered a new flow but part of the existing flow. If any part of the seven key fields doesnt exactly match an existing flow, it is then a new flow and a new flow record is created. Consider the below table (Table 1) of active flows in a cache. Notice that these are all unique, as none of them duplicate any of the other Table 1.
Key Field Source IP Destination IP Source port Destination Port Protocol ToS IfIndex Flow 1 10.10.1.1 10.10.2.55 21 21 17 184 1 Flow 2 10.10.1.1 10.1.23.1 8080 8080 6 184 1 Flow 3 10.10.2.1 10.10.2.253 21 21 17 184 1 Flow 4 10.10.3.35 10.10.2.23 443 1122 6 184 1
Page 4
Note that some of these non-key fields come from the new packet and some are achieved by flow cache calculations, for example the flow start and finish times. This information cannot be derived from a field in the packet but is a function of the cache marking the time the first packet is seen in a flow and the time the flow expired. Lets take a look at the NetFlow cache on R2s WAN interface using the show ip cache verbose flow command (see Figure 2). Figure 2.
Seeing as this is an introduction to NetFlow, I wont go into each field in detail but notice there are four sections to the flow cache display: Packet size distribution. Cache statistics and status. Protocol distribution. Active flow records. The cache output can be a valuable realtime trouble shooting tool. The problem is that the output is not presented in the most readable of formats and the data tends to move quickly, as it is realtime. One thing you dont see in the flow information is any of the payload data, the application information the user or device is sending. NetFlow never looks into the payload, so it cant determine anything past layer 4 information. Therefore the information NetFlow gathers tells us about the type or nature of the traffic as interpreted from the IP header. Using the default settings in NetFlow, all IP packets are interrogated and recorded. There are settings available to use a sampling algorithm but this is rarely implemented. S-flow uses sampled flow collection by either statistical random sampling or by timer-based sampling, depending on the configuration applied.
in all seven key fields. Now consider a new IP packet enters the NetFlow interface with the following fields: Source IP = 10.10.2.1 Destination IP = 10.10.2.253 Source port = 21 Destination port = 21 Protocol = 17 ToS = 184 IfIndex = 1 Because all seven key fields match Flow 3 exactly, a new flow record is not created and information in this packet header is added to the Flow 3 record. But what information is added to flow 3 if all the fields match? The matching fields above are the key fields. NetFlow v5 records also contain non-key fields. These non-key fields are stored in the flow record and these counters are updated when packets of an existing flow are detected. The non-key fields include: Bytes Packets Output interface IfIndex Flow start and finish time Next hop IP Network masks TCP flags Source and destination BGP AS numbers
The NetFlow Data Exporter (NDE)
NetFlow devices have a limited amount of memory to store flow information, so at some point the device has to make room for new flows. This is where flow aging and exporting comes into play. The NetFlow-enabled device keeps track of several factors regarding the flows and the status of the cache itself. Here are the factors the device uses to age flows and either delete them or export to a collector then delete. These are listed in order of precedence. Cache maximum size is reached. A TCP connection has been terminated by a RST (reset) or FIN (finish) flag in the flow. An active flow timer or inactive flow timer limit is reached.
Networking Fundamentals Volume 3, NetFlow Basics and Deployment Strategies
The NetFlow cache size is configurable on most Cisco routers up to 524,288 entries. Each entry uses a minimum of 64 bytes of memory. Once the cache maximum size is reached the device exports using rules to lower the cache count as quickly as possible. This process will export flows when none of the other mentioned export triggers have been reached. By definition, when an RST or FIN flag are set in a TCP connection the connection is closed. The Netflow device will export any flow when one of these flags is detected within the flow. The last in order of precedence are the flow timers. The active flow timer tracks the first packet of all flows and exports the flow data, if it is still active after 30 minutes (default setting) of active flow time. The inactive flow timer marks the time the last packet in a flow was added. If a new packet in an existing flow is detected, the timer is reset. If no new packets in a flow are detected within 15 seconds (also default) of the last packet, the flow data is exported. So, the router is examining flow keys for each packet received, updating active flows or starting a new flow record, keeping a start timer on every flow and updating the active timer on each packet in a flow. Keep in mind that what has been described here is the NetFlow v5 export format. Lets take a look at a section of the network diagram we saw earlier (see Figure 3). Here well focus on the NetFlow cache and exporter on R2 as well as the exported flows going to the collector. Figure 3. Figure 5.
Page 5
the telnet session. The source of the packet capture is the interface on the NetFlow router sending flows to our protocol analyzer. The show ip flow interface command shows us that the FastEthernet0/0 is configured to collect only inbound (ingress) flows while the FastEthernet0/1 interface is configured to collect inbound and outbound flows. The exporter groups multiple flow records as Protocol Data Units (PDUs) together to reduce the total protocol overhead of exporting. The exporter will place up to 30 PDUs in a single export. This is seen above as each export packet has 30 flows. Here is the lower protocol section with the Cisco NetFlow/IPFIX layer expanded. (see Figure 6). Figure 6.
We saw an active NetFlow cache in the previous section. Now, well look at an exporter configuration and examine some packets sent from the exporter. Here is the configuration of our exporter (see Figure 4): Figure 4. In Figures XX we see the individual flows represented as PDUs and with further expansion below, we can see the information in a single flow record (see Figure 7). Figure 7.
And here is the resulting export as capture by a protocol analyzer at the second IP address of the Exporting flows to line. (see Figure 5). What we are seeing in the packet capture is the raw data as it comes into a NetFlow collector. Note that the destination IP address in the packet capture is the second IP address listed in the Exporting flows to line of
Networking Fundamentals Volume 3, NetFlow Basics and Deployment Strategies
Notice that the seven key fields (Source and destination IP and ports, protocol, ToS, and input interface index number) are present (they define a flow!). The rest are all non-key information. Remember our goal with NetFlow is to determine who and what is using the bandwidth. Examining the above capture we see that the who is the machine at the source IP address, 10.199.5.21, which could be resolved to a machine name with DNS. The what is given in the source port line and the protocol line, port 161(SNMP) over protocol 17 (UDP). Given that there are 54 packets in this flow in less than 9 seconds we can deduce that this is most likely automated SNMP requests or some mad typing skills! This is only one out of thirty flow records in this capture containing 29 exports over about a 15 second period. This is a whole lot of information in a short period of time certainly more than a human could consume and understand in such a short amount of time. This is where the NetFlow Collector comes in. Before we look at the collector, it is worth pointing out that other versions of NetFlow can use other timers and export mechanisms. Here is a brief description of the other NetFlow versions: V1 AKA the router killer. It is still out there on very old equipment. V2 to V4 Development versions only, not released. V6 Created to meet a single customers needs but no longer supported. (There must be some good stories behind that one!) V7 Catalyst-specific export V8 Allows for the router to preprocess flow information before sending to the collector thus reducing the export traffic. This version is designed for very high throughput Service Provider devices and is not widely used. Unless the NetFlow data is being used for accounting, sampling in preferred. V9 Quickly becoming the new standard. Using flow templates, v9 implements flexibility into the definitions of key and non-key fields in a flow. This means that when a new definition of a flow or a new set of key or non-key fields is needed, it is not necessary to create a new NetFlow version. Flexible NetFlow! V10 IETF standard based flow analysis IP Flow Information Export or IPFIX. This standard is based on the NetFlow v9 export format.
Page 6
The NetFlow Collector
The collector has three main tasks, very similar to an NMS but using different data gathering methods. These are: Receive the flows as they are sent from exporters. Store and aggregate the data. Present the data. In section 2 we saw a capture of 29 v5 exports, each carrying 30 flow records in about 15 seconds. This equates to a flow rate of 58 flows per seconds (fps), which is considered low. On a mid-sized network we might have 50 or so flow exporters. Assuming the same flow rate from each we now have 2900 fps. Flow rates in large networks are measured in tens of thousands of flows per second. Flow rates vary constantly depending on the number of active user connections detected by the cache. The collector listens on a port (UDP 2055 in our example) for flows from multiple sources. The collector aggregates information received from the exporters, depending on the time frame requested by the user, using key and non-key fields similar to those used in the cache. So, flows can be aggregated twice, once by the cache and once by the collector. Below is a flow chart showing the interactions of the three NetFlow core functions, the cache, exporter and collector. (see Figure 8). Figure 8. Netflow Core Functions
Networking Fundamentals Volume 3, NetFlow Basics and Deployment Strategies
Now well take a look at some sample output from my favorite collector, SolarWinds Orion Netflow Traffic Analyzer (NTA). (see Figure 9). Figure 9.
Page 7
Top N Domains (using DNS and/or NetBIOS resolution of the endpoint IP addresses). Top N IP Address Groups Top N Receivers Top N ToS Search by Application Collector Status NetFlow Events Figure 11. Summary Level View
In the above NTA screen we see two resources, one for the Endpoint Details for the Orion NPM/NTA (10.110.66.98) and one for the Top 25 conversations involving the Orion NPM/NTA endpoint. These are conversations between 10.110.66.98 and other endpoints over the last 15 minutes, as indicated in the figure. Notice the endpoint at 10.199.5.1 is listed in the top 25 conversations. This is the collectors presentation of one of the conversation in the NetFlow cache. Separate flows exported to this collector have been stored and aggregated so we can examine these flows when we need to, rather than only as they happen. This shows us that over the last 15 minutes there has been an aggregated flow conversation containing 16 KB of data and represents 4.67% of the observed traffic. Below are the individual flow records found by drilling down on the highlighted conversation aggregate from 10.199.5.1 above. (see Figure 10). Figure 10.
Node Level View and Interface Level Views (see Figure 12) Here the same types of resources are available but the data is restricted to all exports from a single node rather than network wide. Similarly, the interface level view shows only flow data from a specific interface. Figure 12. Node Level View and Interface Level Views
The above screen shots show the flows specifically from the exporter and cache we examined in sections 2 and 3. The collector also has the ability to aggregate flow data to show flow analysis for the whole network, individual nodes and interfaces. Below are examples of each of these. Summary Level View (see Figure 11) This shows us a breakdown of the types of traffic seen at the network or summary level. Here there is only one source (exporter) but this level will aggregate data from all sources this collector is listening to. There are more graphs and tables than can be shown on a single screen shot. Other items that can be seen at the summary level include:
Networking Fundamentals Volume 3, NetFlow Basics and Deployment Strategies
Interface View with Flow Direction Options (see Figure 13) One important difference between node level information and interface level information is that at the interface level we are able to specify the directionality of the data we wish to see, as shown above. Figure 13. Interface View with Flow Direction Options
Page 8
Deployment Strategies
NetFlow is a very powerful tool. When it is applied with careful planning, this powerful tool works for you, yielding useful data and requiring a minimal investment. The flip side of that is that if NetFlow is implemented without careful planning it can overwhelm the collector with redundant data and consume valuable resources on the routers and switches. This has the effect of burying the data you need to find under tons of data you probably dont need. In this section, Ill focus on planning deployment and understanding the impact of the choices made in the process.
Deployment Planning and Mapping
The first step in deployment is to get a good understanding of what you want to achieve and then map out what points in the network require flow export to support those goals. It is critical in this phase to examine each goal, determine what questions each goal will answer and prioritize the goals using this information. The result of this process might look something like this: (see Table 2). Table 2.
Goal Understand WAN bandwidth utilization/Control recurring WAN cost. What question does this answer? Why is a circuit experiencing high utilization? How much of the WAN utilization is unnecessary traffic? Is the bandwidth being consumed mostly by a few users? Which applications are consuming the most bandwidth? Are there alternatives to buying more bandwidth? What is the network being used for? Who uses it the most? Are inappropriate sites being accessed? Who uses the most Internet bandwidth and what are they doing? Are there traffic types that need to be controlled? Are security measures working to control access? Priority 1
Understand overall network traffic Understand Internet usage to control costs, detect attacks and possible legal issues. Locate specific traffic types to detect security issues.
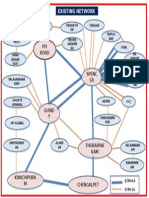
The goals should speak to business needs as much as possible, not be too technically detailed, and they should not be overly-broad. Goals like Monitor all traffic on all ports or Find the top talkers are technically possible to achieve but dont speak to a specific business needs. These might also work against other high priority goals such as Understand overall network traffic as implementing too many exporters will skew the true picture of the network and burden the collector and the devices exporting flows. Once the goals are agreed on, the proper placement of exporters to support those goals should be determined. This can best be done using a network map where upon nots can be added to indicate where the goals are being addressed and highlight the locations of exporters. Using our network drawing from section 2 here is what this might look like: (see Figure 13 on following page).
Networking Fundamentals Volume 3, NetFlow Basics and Deployment Strategies
Figure 13.
Page 9
Review
NetFlow consists of: The NetFlow cache tracking flows on the device detecting flows The NetFlow exporter on the same device The NetFlow collector A v5 flow is defined by seven key fields: Source IP address. Destination IP addresses. Source port number. Destination port number Layer 3 protocol type ToS byte value The IfIndex number also called the logical interface number As the cache receives packets with all seven key fields matching an existing flow record, the cache updates the bytes and packets counts to the existing flow record. The cache ages flows by tracking: TCP flags Active and inactive flow timers Maximum flow cache size Once any of the flow aging criteria are met the cache sends the flow information to the exporter and eliminates the record. The exporter sends flow data to the collector which listens passively for flow data on a specified UDP port. Exporters can be configured for ingress traffic and/or egress interface traffic. Collectors collect, store, and present flow data. Careful consideration of business level goals should be part of the deployment planning. Mass implementation of exporters on all or most interfaces is not recommended. I hope this has been helpful and Ill see you on thwack!
This network is very much a simplified version of what you are probably working with, but the basics still apply. I have decided to deploy only two bidirectional exporters one on the WAN port to R1 and one in the Internet access port. This has the benefit of only requiring configuration changes on R2 so the other network devices will be unaffected by the deployment. Also in this simple network all the data I need to see to achieve my goals can be met with just two exporters. This same idea can be used on a network of any size - it would just require a more in-depth analysis where exporters need to be placed to meet the goals. It would be possible to meet our goals above by exporting from all interfaces on all devices but there are some issues to consider while planning a deployment.
Deployment Planning
NetFlow will add about 4 to 20 percent CPU utilization on the exporting device. The exact amount depends on the active flows in the cache which can only be determined by implementing the exporter. Export of ingress and egress has no significant CPU impact. NetFlow export traffic will represent about 1.5% to 3% of the total traffic seen by an exporter. If the exporters are added to all interfaces the duplicated export data could become significant, especially if the network aggregates several exporters traffic into a WAN link. This would be the case if I had decided to collect on all ports in the above network. All the exports from the R1 WAN interface back to the user ports would send to the collector over the single WAN link to R2. NetFlow uses memory on the exporting device as a function of the flows in the cache. Implementing flow exporters from many devices requires a lot of time initially and will require occasional troubleshooting and maintenance. This could prove to be very time consuming. With these points in mind, you should check the system memory and CPU before implementing exporters. Also keep in mind that NetFlow is like counting cars on a highway. You could send five people out to count cars, one each mile for five miles but this could be done by just one person. All of the above factors should be used to create a deployment plan. A good plan should include a phased implementation with deployment to meet the top priority goals first and add exporters until all goals are met, keeping track on the exporting devices resources, traffic, and collector resources as you go.
Networking Fundamentals Volume 3, NetFlow Basics and Deployment Strategies
Page 10
Related SolarWinds Products
SolarWinds Solutions for NetFlow Monitoring Now that youve got a solid understanding of NetFlow technology, we wanted to introduce a couple great solutions to help you begin using NetFlow on your network.
orion NetFlow Traffic Analyzer (orion NTA)
Orion NetFlow Traffic Analyzer allows you to quantify exactly how your network is being used, by whom, and for what purpose. And with the new CBQoS monitoring you can be sure that the policies youve set give your mission-critical traffic the highest level of priority. Orion NTAs NetFlow monitoring makes it easy to get a comprehensive view of your network traffic, find the bottlenecks, and shut down the bandwidth hogs. Quickly and easily identifies which users, applications, and protocols are consuming the most network bandwidth and highlights the IP addresses of the top talkers on the network Monitors network traffic by capturing flow data from network devices, including Cisco NetFlow v5 or v9, Juniper J-Flow, IPFIX, and sFlow Performs Class-Based Quality of Service (CBQoS) monitoring to ensure that your traffic prioritization policies are effective Provides a comprehensive, customizable view of network traffic on a single page Enables you to quickly drill into traffic on specific network elements, using multiple views to get the perspective youre looking for Generates network traffic reports with just a few clicks Monitors Quality of Service (QoS) metrics Facilitates investigation of fault, performance, and configuration issues thanks to complete integration with Orion NPM and Orion NCM Get more info on Orion NetFlow Traffic Analyzer here. Orion NetFlow Traffic Analyzer Live Demo Orion NetFlow Traffic Analyzer 30-Day Trial Download
SolarWinds Real-Time NetFlow Analyzer Free Tool
Real-time NetFlow Analyzer displays inbound and outbound traffic separately for granular analysis that makes problem diagnosis quick and easy. Even better, you can view the historical NetFlow data broken out by application, conversation, domain, endpoint, and protocol. That way you know exactly how your bandwidth is being used and by whom. Put an end to complaints about the network being slow! With Real-time NetFlow Analyzer, youll get the visibility into NetFlow data that youve been waiting for. This free tool will allow you to: Investigate, troubleshoot, and quickly remediate network slowdowns Easily identify which users, devices, and applications are consuming the most bandwidth Isolate inbound and outbound traffic by conversation, application, domain, endpoint, and protocol Personalize NetFlow data displays to view traffic by specified time periods (up to 60 minutes) and by traffic type Customize refresh rates and display units for NetFlow traffic SolarWinds Real-time NetFlow Analyzer supports NetFlow Version 5 and records up to 60 minutes of NetFlow data.
Networking Fundamentals Volume 3, NetFlow Basics and Deployment Strategies
Page 11
About SolarWinds
SolarWinds is rewriting the rules for how companies manage their networks. Guided by a global community of network engineers, SolarWinds develops simple and powerful software for managing networks, small or large. Our company culture is defined by passion for innovation and a philosophy that network management can be simplified for every environment. SolarWinds products are used by more than one million network engineers to manage IT environments ranging from ten to tens of thousands of network devices. Comprised of fault and performance management products, configuration and compliance products, and tools for engineers, the SolarWinds product family is trusted by organizations around the globe to design, build, maintain, and troubleshoot complex network environments. SolarWinds is headquartered in Austin, Texas, with sales and product development offices around the world. Join our online community of experts at thwack.com!
About the Author
Andy McBride is a Technical Specialist for SolarWinds focusing on making knowledge of networking and network management accessible to customers and prospects of all levels. The Networking Fundamentals series is specifically written for an audience with limited prior exposure to these technologies. Andys technical background includes seven years at International Network Services (INS) as a Network Engineer and Managing Consultant, three years as a Novell Certified Instructor and five years as a Network Performance Products Manager with BT-Infonet. Prior to entering technology, Andy worked in aerospace on projects such as the SR-71, F-117, F-22, L-1011, F-18 and the space shuttle main engine. Andy has a degree in Chemistry but was wise enough to never work in that field. Andy invites you to follow him on Twitter, @McBrideA, and can be contacted on Thwack, McBrideA.
S-ar putea să vă placă și
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeDe la EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeEvaluare: 4 din 5 stele4/5 (5794)
- Shoe Dog: A Memoir by the Creator of NikeDe la EverandShoe Dog: A Memoir by the Creator of NikeEvaluare: 4.5 din 5 stele4.5/5 (537)
- Slot Information Report - 07!15!2015!19!28-07Document2 paginiSlot Information Report - 07!15!2015!19!28-07SasiKumar PetchiappanÎncă nu există evaluări
- Steps For PF Amount Transfer (New) ..............Document5 paginiSteps For PF Amount Transfer (New) ..............SasiKumar PetchiappanÎncă nu există evaluări
- Work Permit (Ra Puram) - 28-Nov - 2013Document1 paginăWork Permit (Ra Puram) - 28-Nov - 2013SasiKumar PetchiappanÎncă nu există evaluări
- User Manual 5 PDFDocument518 paginiUser Manual 5 PDFSasiKumar PetchiappanÎncă nu există evaluări
- Existing NetworkDocument1 paginăExisting NetworkSasiKumar PetchiappanÎncă nu există evaluări
- Grade 3 MathsDocument3 paginiGrade 3 MathsSasiKumar PetchiappanÎncă nu există evaluări
- A R Collage of Engineering and TechnologyDocument1 paginăA R Collage of Engineering and TechnologySasiKumar PetchiappanÎncă nu există evaluări
- Chapter-4: 4.1 Matrix MaterialsDocument17 paginiChapter-4: 4.1 Matrix MaterialsSasiKumar PetchiappanÎncă nu există evaluări
- Slot Information Report - 07!15!2015!19!28-07Document2 paginiSlot Information Report - 07!15!2015!19!28-07SasiKumar PetchiappanÎncă nu există evaluări
- Institution Paper Presentation Contests: S.No Name of The Program Duration of The Program Resource Person(s)Document34 paginiInstitution Paper Presentation Contests: S.No Name of The Program Duration of The Program Resource Person(s)SasiKumar PetchiappanÎncă nu există evaluări
- Front Pagels and BonofideDocument2 paginiFront Pagels and BonofideSasiKumar PetchiappanÎncă nu există evaluări
- Iat-2 EgDocument1 paginăIat-2 EgSasiKumar PetchiappanÎncă nu există evaluări
- Chapter-5: 5.1 Fabrication Techniques of Composite MaterialsDocument6 paginiChapter-5: 5.1 Fabrication Techniques of Composite MaterialsSasiKumar PetchiappanÎncă nu există evaluări
- Content Materials1Document40 paginiContent Materials1SasiKumar PetchiappanÎncă nu există evaluări
- Ieee Electronics 2013 - 2014Document49 paginiIeee Electronics 2013 - 2014SasiKumar PetchiappanÎncă nu există evaluări
- Theory of Machines12Document1 paginăTheory of Machines12SasiKumar PetchiappanÎncă nu există evaluări
- SalmanDocument2 paginiSalmanSasiKumar PetchiappanÎncă nu există evaluări
- Electrical Based Titles 2009-2010Document2 paginiElectrical Based Titles 2009-2010Siva SankarÎncă nu există evaluări
- Design Fundamentals, Methods and Material Selection 9Document1 paginăDesign Fundamentals, Methods and Material Selection 9SasiKumar PetchiappanÎncă nu există evaluări
- Quality ConceptDocument2 paginiQuality ConceptSasiKumar PetchiappanÎncă nu există evaluări
- 405 M.E. Computer Science and EngineeringDocument68 pagini405 M.E. Computer Science and EngineeringThanuambikaÎncă nu există evaluări
- Food and OilDocument11 paginiFood and OilSasiKumar PetchiappanÎncă nu există evaluări
- Centre For Research Anna University:: Chennai 600025 Enrolment Form/ Registration Renewal FormDocument1 paginăCentre For Research Anna University:: Chennai 600025 Enrolment Form/ Registration Renewal FormruthshaÎncă nu există evaluări
- Question Bank: Ee 1403 - Design of Electrical ApparatusDocument11 paginiQuestion Bank: Ee 1403 - Design of Electrical ApparatussuriyasureshÎncă nu există evaluări
- 2K Factor PDFDocument6 pagini2K Factor PDFvmgobinathÎncă nu există evaluări
- Time Table For EngDocument1 paginăTime Table For EngSasiKumar PetchiappanÎncă nu există evaluări
- Muhammad NijasDocument2 paginiMuhammad NijasSasiKumar PetchiappanÎncă nu există evaluări
- Rainwater Harvesting Basic ComponentsDocument3 paginiRainwater Harvesting Basic ComponentsSasiKumar PetchiappanÎncă nu există evaluări
- Write The Procedure To Compile and Install Linux Kernel From SourceDocument1 paginăWrite The Procedure To Compile and Install Linux Kernel From SourceSasiKumar PetchiappanÎncă nu există evaluări
- Line Chart 3Document2 paginiLine Chart 3SasiKumar PetchiappanÎncă nu există evaluări
- The Yellow House: A Memoir (2019 National Book Award Winner)De la EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Evaluare: 4 din 5 stele4/5 (98)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceDe la EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceEvaluare: 4 din 5 stele4/5 (895)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersDe la EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersEvaluare: 4.5 din 5 stele4.5/5 (344)
- The Little Book of Hygge: Danish Secrets to Happy LivingDe la EverandThe Little Book of Hygge: Danish Secrets to Happy LivingEvaluare: 3.5 din 5 stele3.5/5 (399)
- Grit: The Power of Passion and PerseveranceDe la EverandGrit: The Power of Passion and PerseveranceEvaluare: 4 din 5 stele4/5 (588)
- The Emperor of All Maladies: A Biography of CancerDe la EverandThe Emperor of All Maladies: A Biography of CancerEvaluare: 4.5 din 5 stele4.5/5 (271)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaDe la EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaEvaluare: 4.5 din 5 stele4.5/5 (266)
- Never Split the Difference: Negotiating As If Your Life Depended On ItDe la EverandNever Split the Difference: Negotiating As If Your Life Depended On ItEvaluare: 4.5 din 5 stele4.5/5 (838)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryDe la EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryEvaluare: 3.5 din 5 stele3.5/5 (231)
- On Fire: The (Burning) Case for a Green New DealDe la EverandOn Fire: The (Burning) Case for a Green New DealEvaluare: 4 din 5 stele4/5 (73)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureDe la EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureEvaluare: 4.5 din 5 stele4.5/5 (474)
- Team of Rivals: The Political Genius of Abraham LincolnDe la EverandTeam of Rivals: The Political Genius of Abraham LincolnEvaluare: 4.5 din 5 stele4.5/5 (234)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyDe la EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyEvaluare: 3.5 din 5 stele3.5/5 (2259)
- The Unwinding: An Inner History of the New AmericaDe la EverandThe Unwinding: An Inner History of the New AmericaEvaluare: 4 din 5 stele4/5 (45)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreDe la EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreEvaluare: 4 din 5 stele4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)De la EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Evaluare: 4.5 din 5 stele4.5/5 (120)
- Her Body and Other Parties: StoriesDe la EverandHer Body and Other Parties: StoriesEvaluare: 4 din 5 stele4/5 (821)
- On The Linguistic Turn in Philosophy - Stenlund2002 PDFDocument40 paginiOn The Linguistic Turn in Philosophy - Stenlund2002 PDFPablo BarbosaÎncă nu există evaluări
- Xavier High SchoolDocument1 paginăXavier High SchoolHelen BennettÎncă nu există evaluări
- Lesson 73 Creating Problems Involving The Volume of A Rectangular PrismDocument17 paginiLesson 73 Creating Problems Involving The Volume of A Rectangular PrismJessy James CardinalÎncă nu există evaluări
- Project Report On ICICI BankDocument106 paginiProject Report On ICICI BankRohan MishraÎncă nu există evaluări
- SQ1 Mogas95Document1 paginăSQ1 Mogas95Basant Kumar SaxenaÎncă nu există evaluări
- Employer'S Virtual Pag-Ibig Enrollment Form: Address and Contact DetailsDocument2 paginiEmployer'S Virtual Pag-Ibig Enrollment Form: Address and Contact DetailstheffÎncă nu există evaluări
- Hydraulics Experiment No 1 Specific Gravity of LiquidsDocument3 paginiHydraulics Experiment No 1 Specific Gravity of LiquidsIpan DibaynÎncă nu există evaluări
- Berrinba East State School OSHC Final ITO For Schools Final 2016Document24 paginiBerrinba East State School OSHC Final ITO For Schools Final 2016hieuntx93Încă nu există evaluări
- CrisisDocument13 paginiCrisisAngel Gaddi LarenaÎncă nu există evaluări
- Feuerhahn Funeral Bullet 17 March 2015Document12 paginiFeuerhahn Funeral Bullet 17 March 2015brandy99Încă nu există evaluări
- StatisticsAllTopicsDocument315 paginiStatisticsAllTopicsHoda HosnyÎncă nu există evaluări
- Economies of Scale in European Manufacturing Revisited: July 2001Document31 paginiEconomies of Scale in European Manufacturing Revisited: July 2001vladut_stan_5Încă nu există evaluări
- CAPE Env. Science 2012 U1 P2Document9 paginiCAPE Env. Science 2012 U1 P2Christina FrancisÎncă nu există evaluări
- Togaf Open Group Business ScenarioDocument40 paginiTogaf Open Group Business Scenariohmh97Încă nu există evaluări
- Conductivity MeterDocument59 paginiConductivity MeterMuhammad AzeemÎncă nu există evaluări
- Flabbergasted! - Core RulebookDocument160 paginiFlabbergasted! - Core RulebookRobert RichesonÎncă nu există evaluări
- Syllabus Biomekanika Kerja 2012 1Document2 paginiSyllabus Biomekanika Kerja 2012 1Lukman HakimÎncă nu există evaluări
- MSC in Healthcare Management (Top-Up) Degree From ARU - Delivered Online by LSBR, UKDocument19 paginiMSC in Healthcare Management (Top-Up) Degree From ARU - Delivered Online by LSBR, UKLSBRÎncă nu există evaluări
- Trenching Shoring SafetyDocument29 paginiTrenching Shoring SafetyMullapudi Satish KumarÎncă nu există evaluări
- QTP Common FunctionsDocument55 paginiQTP Common FunctionsAnkur TiwariÎncă nu există evaluări
- Ruahsur Vangin Basket-Ball Court Lungrem ChimDocument4 paginiRuahsur Vangin Basket-Ball Court Lungrem ChimchanmariansÎncă nu există evaluări
- Pronouns Workshop SENADocument7 paginiPronouns Workshop SENAPaula Rodríguez PérezÎncă nu există evaluări
- SULTANS OF SWING - Dire Straits (Impresión)Document1 paginăSULTANS OF SWING - Dire Straits (Impresión)fabio.mattos.tkd100% (1)
- Industrial Visit Report Part 2Document41 paginiIndustrial Visit Report Part 2Navratan JagnadeÎncă nu există evaluări
- Entrep Bazaar Rating SheetDocument7 paginiEntrep Bazaar Rating SheetJupiter WhitesideÎncă nu există evaluări
- Multi Grade-ReportDocument19 paginiMulti Grade-Reportjoy pamorÎncă nu există evaluări
- Narcissist's False Self vs. True Self - Soul-Snatching - English (Auto-Generated)Document6 paginiNarcissist's False Self vs. True Self - Soul-Snatching - English (Auto-Generated)Vanessa KanuÎncă nu există evaluări
- Bootstrap DatepickerDocument31 paginiBootstrap DatepickerdandczdczÎncă nu există evaluări
- Borer (2013) Advanced Exercise Endocrinology PDFDocument272 paginiBorer (2013) Advanced Exercise Endocrinology PDFNicolás Bastarrica100% (1)
- LiverDocument6 paginiLiverMiguel Cuevas DolotÎncă nu există evaluări