Documente Academic
Documente Profesional
Documente Cultură
Digitel NRX 5122 VPN Gateway & GreenBow IPsec VPN Software Configuration
Încărcat de
greenbowDrepturi de autor
Formate disponibile
Partajați acest document
Partajați sau inserați document
Vi se pare util acest document?
Este necorespunzător acest conținut?
Raportați acest documentDrepturi de autor:
Formate disponibile
Digitel NRX 5122 VPN Gateway & GreenBow IPsec VPN Software Configuration
Încărcat de
greenbowDrepturi de autor:
Formate disponibile
TheGreenBow IPSec VPN Client Configuration Guide
Digitel NRX 5122
WebSite: Contact: http://www.thegreenbow.com support@thegreenbow.com Configuration Guide written by: Writer: Suport Technical Company: www.digitel.com.br
IPSec VPN Router Configuration
Property of TheGreenBow Sistech SA - 2001-2012
1/17
Doc.Ref Doc.version VPN version
tgbvpn_ug-digitel-nrx-5122-en
Feb 2012
5.x
Table of contents
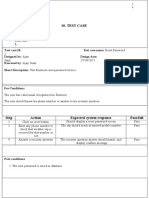
1 1.1 1.2 1.3 1.4 1.5 2 3 4 Introduction .................................................................................................................................................... 3 Goal of this document ............................................................................................................................... 3 VPN Network topology .............................................................................................................................. 3 Digitel NRX 5122 Restrictions ................................................................................................................... 3 Digitel NRX 5122 VPN Gateway .............................................................................................................. 3 Digitel NRX 5122 VPN Gateway product info .......................................................................................... 4 Digitel NRX 5122 VPN configuration............................................................................................................. 5 Digitel NRX 5122 VPN configuration options ................................................................................................ 7 TheGreenBow IPSec VPN Client configuration ............................................................................................10 4.1 VPN Client Phase 1 (IKE) Configuration ................................................................................................. 10 4.2 VPN Client Phase 2 (IPSec) Configuration ............................................................................................. 11 4.3 Open IPSec VPN tunnels........................................................................................................................ 11 5.1 6 Tools in case of trouble.................................................................................................................................12 A good network analyser: Wireshark....................................................................................................... 12
VPN IPSec Troubleshooting .........................................................................................................................13 6.1 PAYLOAD MALFORMED error (wrong Phase 1 [SA]) .................................................................... 13 6.2 INVALID COOKIE error..................................................................................................................... 13 6.3 no keystate error ............................................................................................................................... 13 6.4 received remote ID other than expected error................................................................................... 13 6.5 NO PROPOSAL CHOSEN error ....................................................................................................... 14 6.6 INVALID ID INFORMATION error ..................................................................................................... 14 6.7 I clicked on Open tunnel, but nothing happens..................................................................................... 14 6.8 The VPN tunnel is up but I cant ping ! .................................................................................................... 14 Contacts........................................................................................................................................................16
IPSec VPN Router Configuration
Property of TheGreenBow Sistech SA - 2001-2012
2/17
Doc.Ref Doc.version VPN version
tgbvpn_ug-digitel-nrx-5122-en
Feb 2012
5.x
1 Introduction
1.1 Goal of this document
This configuration guide describes how to configure TheGreenBow IPSec VPN Client software with a Digitel NRX 5122 VPN router to establish VPN connections for remote access to corporate network
1.2 VPN Network topology
In our VPN network example (diagram hereafter), we will connect TheGreenBow IPSec VPN Client software to the LAN behind the Digitel NRX 5122 router. The VPN client is connected to the Internet with a DSL connection or through a LAN. All the addresses in this document are given for example purpose.
IPSecVPNClient asseenonLAN
mygateway.dyndns.org
192.168.1.1
Internet IPSecVPNClient (Remote)
192.168.1.78
DigitelNRX 5122
192.168.1.3
1.3 Digitel NRX 5122 Restrictions
Depending on the topology to be used may need some changes to the configuration script Digitel NRX 5122. In this case you should contact the Digitel via e-mail suporte@digitel.com.br .
1.4 Digitel NRX 5122 VPN Gateway
Our tests and VPN configuration have been conducted with Digitel NRX 5122 firmware release 79309e.
IPSec VPN Router Configuration
Property of TheGreenBow Sistech SA - 2001-2012
3/17
Doc.Ref Doc.version VPN version
tgbvpn_ug-digitel-nrx-5122-en
Feb 2012
5.x
1.5 Digitel NRX 5122 VPN Gateway product info
It is critical that users find all necessary information about Digitel NRX 5122 VPN Gateway. All product info, User Guide and knowledge base for the Digitel NRX 5122 VPN Gateway can be found on the Digitel NRX 5122 website: www.digitel.com.br/pt/produtos/produto.asp?idLinha=11&idCat=36&Id=38 NRX 5122 Product page NRX 5122FAQ/Knowledge Base http://www.digitel.com.br/pt/produtos/produto.asp?IdLinha=11&Id Cat=36&Id=38 suporte@digitel.com.br
IPSec VPN Router Configuration
Property of TheGreenBow Sistech SA - 2001-2012
4/17
Doc.Ref Doc.version VPN version
tgbvpn_ug-digitel-nrx-5122-en
Feb 2012
5.x
2 Digitel NRX 5122 VPN configuration
This section describes how to build an IPSec VPN configuration with your Digitel NRX 5122 VPN router. Once connected to your Digitel NRX 5122 VPN gateway, you must select Security and VPN tabs.
SET LAN LAN0 MODE AUTO SET LAN LAN0 IP 192.168.1.254 MASK 255.255.255.0 SET LAN LAN0 UP
SET LAN LAN1 MODE AUTO SET LAN LAN1 IP 192.168.30.15 MASK 255.255.255.0 SET LAN LAN1 UP
SET ROUTES DEFAULT GW1 192.168.30.1 COST1 1 SET ROUTES UP
SET IPSEC FRAGICMP TRUE NATT TRUE MTU 1412 TYPE DEFAULTROUTE SET IPSEC CHANNEL0 NAME Teste MODE TUNNEL
SET IPSEC CHANNEL0 AUTO ADD DPDACTION RESTART DPDDELAY 120 DPDTIMEOUT 120 SET IPSEC CHANNEL0 LEFT ADDRESSTYPE DEFAULTROUTE SET IPSEC CHANNEL0 LEFT SUBNET TRUE NET 192.168.1.0 MASK 255.255.255.0 SET IPSEC CHANNEL0 RIGHT ADDRESSTYPE ANY SET IPSEC CHANNEL0 RIGHT SUBNET FALSE SET IPSEC CHANNEL0 KEY AUTH ESP AUTHBY SECRET PASS digitel SET IPSEC CHANNEL0 KEY ISAKMP 24H RETRIES 0 KEYLIFE 1H SET IPSEC CHANNEL0 IKE0 ALG 3DES HASH MD5 DH 2 SET IPSEC CHANNEL0 ESP0 ALG 3DES HASH MD5 SET IPSEC UP
Where:
SET LAN LAN0 MODE AUTO Sets LAN0 for autonegotiation. SET LAN LAN0 IP 192.168.1.254 MASK 255.255.255.0 Set IP address of the interface LAN0. In this case is Local Network. SET LAN LAN1 MODE AUTO Set LAN1, that is interface of internet access, for autonegotiation. SET LAN LAN1 IP 192.168.30.15 MASK 255.255.255.0
IPSec VPN Router Configuration Property of TheGreenBow Sistech SA - 2001-2012 5/17
Doc.Ref Doc.version VPN version
tgbvpn_ug-digitel-nrx-5122-en
Feb 2012
5.x
Set interface LAN1 IP address. SET ROUTES DEFAULT GW1 192.168.30.1 COST1 1 Set router default route.
IPSec VPN Router Configuration
Property of TheGreenBow Sistech SA - 2001-2012
6/17
Doc.Ref Doc.version VPN version
tgbvpn_ug-digitel-nrx-5122-en
Feb 2012
5.x
3 Digitel NRX 5122 VPN configuration options
FRAGICMP: This option allows the fragmentation of packets. Accepts TRUE or FALSE. HIDETOS: Provides a copy of the TOS field value and forwards it to the packet. Accepts TRUE or FALSE. UNIQUEIDS: Enables the replacement of all IDs of former connections with a new one. Accepts TRUE or FALSE. NATT: Enables the option of NAT Traversal. Accepts TRUE or FALSE. MTU: Sets the value of MTU. Accepts a value between 64 and 16 260. TYPE: Sets the type of connection. Accepts INTERFACE or DEFAULTROUTE. UP: Enable the settings. DOWN: Disable the settings. PURGE: Clears the settings. CHANNELn: For the channel configuration, the following parameters are available: NAME: Sets the name for the channel. DPDACTION: Sets what action should be taken after the tunnel is considered dead: NONE, CLEAR, HOLD, and RESTART. DPDDELAY: Set a value in seconds for the delay between Dead Peer Detection (RFS 3706) and KEEPALIVES for a given connection, the default is 30 seconds. If DPDTIMEOUT is configured, but the DPDDELAY is not, then the DPDDELAY is configured in its default pattern DPDTIMEOUT: Set a value in seconds, that IPSEC will be on hold without any traffic before considering the connection closed. The default is 120 seconds. AGGRESSIVE: Enables aggressive way. Accepts TRUE or FALSE. LEFT: Sets the local side of the tunnel. To configure this option, the following parameters are available: o ADDRESSTYPE: Accepts the following options for configuration: ANY, USER, DEFAULTROUTE, OPPORTUNISTIC, BINDED (this option can only be selected if TYPE is set as INTERFACE). o ADDRESS: This option can only be adjusted if ADDRESSTYPE is set as USER. Accepts an IP address for the interface. o SUBNET: This option accepts TRUE (true) or FALSE (false). o Enables the configuration of a subnet. o NET: This option can only be configured if SUBNET is enabled as TRUE. Configures an IP address for the subnet. o MASK: This option can only be configured if SUBNET is enabled as TRUE. Sets an IP address for the subnet mask. o USEGATEWAY: Enables the configuration of a gateway. This option accepts either TRUE or FALSE. o ID: Defines a string for authentication. o GATEWAY: For this option to be configured, USEGATEWAY must be enabled as TRUE. Configures the gateway IP address.
IPSec VPN Router Configuration
Property of TheGreenBow Sistech SA - 2001-2012
7/17
Doc.Ref Doc.version VPN version
tgbvpn_ug-digitel-nrx-5122-en
Feb 2012
5.x
o SOURCEIP: Set an IP address, which will be used when transmitting a packet to the other side of the tunnel. Example:
NRX> SET IPSEC CHANNEL0 LEFT ADDRESSTYPE USER ADDRESS 172.16.1.2 SUBNET TRUE NET 192.168.10.0 MASK 255.255.255.0 USEGATEWAY TRUE ID user@fqdn.com GATEWAY 10.10.10.5 SOURCEIP 192.168.255.0
RIGHT: Defines the network from the remote side. To accomplish the setting of this option, the same parameters of the option LEFT are available. KEY: Sets the key exchange. To achieve this configuration, the following configuration parameters are available: o AUTH: Select the type of authentication, ESP or AH. o AUTHBY: Select the authentication method, SECRET or RSB. o PASS: This option can only be adjusted if AUTHBY is configured as SECRET. Set the password for authentication. o BITS: This option can only be adjusted if AUTHBY is configured as RSA. BITS number for the key. o PEERPUBLICKEY: This option can only be adjusted if AUTHBY is configured as RSA. Accepts a set of characters referring to remote public key. o GENERATEKEY: This option can only be adjusted if AUTHBY is configured as RSA. Sets key generation. o LOCALSIDE: This option can only be set if AUTHBY is configured as RSA. Determines which side will be local in the tunnel, if LEFT or RIGHT. o NEGRESTART: Sets the times for restart of connection attempt. To accomplish the setting of this option, the following parameters are available: TIME: Sets the time. Accepts an integer value. MARGIN: Sets the margin. Accepts an integer value between 0 and 100.
o KEYLIFE: Sets the lifetime of the key. Accepts the following syntax: <integer value> <unity>, being H hours, M minutes and S seconds. o ISAKMP: Sets the lifetime of the channel before the renegotiation. Accepts the following syntax: <integer value> <unity>, being H hours, M minutes and S seconds. o RETRIES: Sets the number of retries for authentication. Accepts an integer value. o PERFECTFORWARD: Enables the use of PFS protocol (Perfect Forward Secrecy). This option accepts either TRUE or FALSE. AUTO: Sets which operation should be done automatically by ISPEC. To accomplish the setting of this option, the following parameters are available: START, ADD or ROUTE. COMPRESS: Accepts TRUE (true) or false (false). MODE: Sets the type of connection TUNNEL or TRANSPORT. PURGE: Clears the settings for the option CHANNELn. IKEn: (Internet Key Exchange) encryption and authentication algorithm that is used in the connection. To configure this option, the following configuration parameters are available: o ALG: Sets the encryption algorithm to be used. Accepted one of the options: DES, 3DES, AES, AES256 or NULL.
IPSec VPN Router Configuration Property of TheGreenBow Sistech SA - 2001-2012 8/17
Doc.Ref Doc.version VPN version
tgbvpn_ug-digitel-nrx-5122-en
Feb 2012
5.x
o HASH: Sets the hash algorithm to be used. Accepts one of the options: MD5, SHA1 or SHA256. o DH: Configure DiffieHellman group. Accept values: 2, 5, 14, 15, 16, 17 or 18. o PURGE: Clears the settings that were adjusted in IKEn. ESPn: Configuration of authentication and encryption algorithm that will be used in the connection. To accomplish the setting of this option, the following parameters are available: o ALG: Sets the encryption algorithm to be used. Accepted one of the options DES, 3DES, AES, AES256 or NULL. o HASH: Sets the hash algorithm MD5, SHA1 or SHA256. o PURGE: Clears the settings for the ESP option. IPSECn: This option can only be adjusted if TYPE is set as INTERFACE. To accomplish the setting of this option, the following parameters are available: INTERFACE: Defines which interface will be used by IPSEC. PURGE: This option clears the setting for IPSECn.
IPSec VPN Router Configuration
Property of TheGreenBow Sistech SA - 2001-2012
9/17
Doc.Ref Doc.version VPN version
tgbvpn_ug-digitel-nrx-5122-en
Feb 2012
5.x
4 TheGreenBow IPSec VPN Client configuration
This section describes the required configuration to connect to a Digitel NRX 5122 VPN router via VPN connections. To download the latest release of TheGreenBow IPSec VPN Client software, please go to http://www.thegreenbow.com/vpn_down.html.
4.1 VPN Client Phase 1 (IKE) Configuration
TheremoteVPN GatewayIPaddressis eitheranexplicitIP addressoraDNSName
digitel
Phase 1 configuration
You may use either Preshared key, Certificates, USB Tokens, OTP Token (One Time Password) or X-Auth combined with RADIUS Server for User Authentication with the Digitel NRX 5122 router. This configuration is one example of what can be accomplished in term of User Authentication. You may want to refer to either the Digitel NRX 5122 router user guide or TheGreenBow IPSec VPN Client software User Guide for more details on User Authentication options.
IPSec VPN Router Configuration
Property of TheGreenBow Sistech SA - 2001-2012
10/17
Doc.Ref Doc.version VPN version
tgbvpn_ug-digitel-nrx-5122-en
Feb 2012
5.x
4.2 VPN Client Phase 2 (IPSec) Configuration
VPNClientVirtualIP address
EntertheIPaddress (andsubnetmask) oftheremoteLAN.
Phase 2 Configuration
4.3 Open IPSec VPN tunnels
Once both Digitel NRX 5122 router and TheGreenBow IPSec VPN Client software have been configured accordingly, you are ready to open VPN tunnels. First make sure you enable your firewall with IPSec traffic. 1. Click on "Save & Apply" to take into account all modifications we've made on your VPN Client configuration 2. Click on "Open Tunnel", or generate traffic that will automatically open a secure IPSec VPN Tunnel (e.g. ping, IE browser) 3. Select "Connections" to see opened VPN Tunnels 4. Select "Console" if you want to access to the IPSec VPN logs and adjust filters to display less IPSec messaging. The following example shows a successful connection between TheGreenBow IPSec VPN Client and a Digitel NRX 5122 VPN router.
IPSec VPN Router Configuration
Property of TheGreenBow Sistech SA - 2001-2012
11/17
Doc.Ref Doc.version VPN version
tgbvpn_ug-digitel-nrx-5122-en
Feb 2012
5.x
5 Tools in case of trouble
Configuring an IPSec VPN tunnel can be a hard task. One missing parameter can prevent a VPN connection from being established. Some tools are available to find source of troubles during a VPN establishment.
5.1 A good network analyser: Wireshark
Wireshark is a free software that can be used for packet and traffic analysis. It shows IP or TCP packets received on a network card. This tool is available on website http://www.wireshark.org. It can be used to follow protocol exchange between two devices. For installation and use details, read its specific documentation (http://www.wireshark.org/docs/).
IPSec VPN Router Configuration
Property of TheGreenBow Sistech SA - 2001-2012
12/17
Doc.Ref Doc.version VPN version
tgbvpn_ug-digitel-nrx-5122-en
Feb 2012
5.x
6 VPN IPSec Troubleshooting
6.1 PAYLOAD MALFORMED error (wrong Phase 1 [SA])
114920 Default (SA CNXVPN1-P1) SEND phase 1 Main Mode [SA][VID] 114920 Default (SA CNXVPN1-P1) RECV phase 1 Main Mode [NOTIFY] 114920 Default exchange_run: exchange_validate failed 114920 Default dropped message from 195.100.205.114 port 500 due to notification type PAYLOAD_MALFORMED 114920 Default SEND Informational [NOTIFY] with PAYLOAD_MALFORMED error
If you have an PAYLOAD MALFORMED error you might have a wrong Phase 1 [SA], check if the encryption algorithms are the same on each side of the VPN tunnel.
6.2 INVALID COOKIE error
115933 Default message_recv: invalid cookie(s) 5918ca0c2634288f 7364e3e486e49105 115933 Default dropped message from 195.100.205.114 port 500 due to notification type INVALID_COOKIE 115933 Default SEND Informational [NOTIFY] with INVALID_COOKIE error
If you have an INVALID COOKIE error, it means that one of the endpoint is using a SA that is no more in use. Reset the VPN connection on each side.
6.3 no keystate error
115315 115317 115317 115319 115319 115319 Default Default Default Default Default Default (SA CNXVPN1-P1) SEND phase 1 Main Mode [SA][VID] (SA CNXVPN1-P1) RECV phase 1 Main Mode [SA][VID] (SA CNXVPN1-P1) SEND phase 1 Main Mode [KEY][NONCE] (SA CNXVPN1-P1) RECV phase 1 Main Mode [KEY][NONCE] (SA CNXVPN1-P1) SEND phase 1 Main Mode [ID][HASH][NOTIFY] ipsec_get_keystate: no keystate in ISAKMP SA 00B57C50
Check if the preshared key is correct or if the local ID is correct (see Advanced button). You should have more information in the remote endpoint logs.
6.4 received remote ID other than expected error
120348 Default (SA CNXVPN1-P1) SEND phase 1 Main 120349 Default (SA CNXVPN1-P1) RECV phase 1 Main 120349 Default (SA CNXVPN1-P1) SEND phase 1 Main 120351 Default (SA CNXVPN1-P1) RECV phase 1 Main 120351 Default (SA CNXVPN1-P1) SEND phase 1 Main 120351 Default (SA CNXVPN1-P1) RECV phase 1 Main 120351 Default ike_phase_1_recv_ID: received support@thegreenbow.fr Mode [SA][VID] Mode [SA][VID] Mode [KEY][NONCE] Mode [KEY][NONCE] Mode [ID][HASH][NOTIFY] Mode [ID][HASH][NOTIFY] remote ID other than
expected
The Remote ID value (see Advanced Button) does not match what the remote endpoint is expected.
IPSec VPN Router Configuration
Property of TheGreenBow Sistech SA - 2001-2012
13/17
Doc.Ref Doc.version VPN version
tgbvpn_ug-digitel-nrx-5122-en
Feb 2012
5.x
6.5 NO PROPOSAL CHOSEN error
115911 Default (SA CNXVPN1-P1) SEND phase 1 Main Mode [SA][VID] 115913 Default (SA CNXVPN1-P1) RECV phase 1 Main Mode [SA][VID] 115913 Default (SA CNXVPN1-P1) SEND phase 1 Main Mode [KEY][NONCE] 115915 Default (SA CNXVPN1-P1) RECV phase 1 Main Mode [KEY][NONCE] 115915 Default (SA CNXVPN1-P1) SEND phase 1 Main Mode [ID][HASH][NOTIFY] 115915 Default (SA CNXVPN1-P1) RECV phase 1 Main Mode [ID][HASH][NOTIFY] 115915 Default phase 1 done: initiator id c364cd70: 195.100.205.112, responder id c364cd72: 195.100.205.114, src: 195.100.205.112 dst: 195.100.205.114 115915 Default (SA CNXVPN1-CNXVPN1-P2) SEND phase 2 Quick Mode [SA][KEY][ID][HASH][NONCE] 115915 Default RECV Informational [HASH][NOTIFY] with NO_PROPOSAL_CHOSEN error 115915 Default RECV Informational [HASH][DEL] 115915 Default CNXVPN1-P1 deleted
If you have an NO PROPOSAL CHOSEN error, check that the Phase 2 encryption algorithms are the same on each side of the VPN Tunnel. Check Phase 1 algorithms if you have this:
115911 Default (SA CNXVPN1-P1) SEND phase 1 Main Mode [SA][VID] 115911 Default RECV Informational [NOTIFY] with NO_PROPOSAL_CHOSEN error
6.6 INVALID ID INFORMATION error
122623 Default (SA CNXVPN1-P1) SEND phase 1 Main Mode [SA][VID] 122625 Default (SA CNXVPN1-P1) RECV phase 1 Main Mode [SA][VID] 122625 Default (SA CNXVPN1-P1) SEND phase 1 Main Mode [KEY][NONCE] 122626 Default (SA CNXVPN1-P1) RECV phase 1 Main Mode [KEY][NONCE] 122626 Default (SA CNXVPN1-P1) SEND phase 1 Main Mode [ID][HASH][NOTIFY] 122626 Default (SA CNXVPN1-P1) RECV phase 1 Main Mode [ID][HASH][NOTIFY] 122626 Default phase 1 done: initiator id c364cd70: 195.100.205.112, responder id c364cd72: 195.100.205.114, src: 195.100.205.112 dst: 195.100.205.114 122626 Default (SA CNXVPN1-CNXVPN1-P2) SEND phase 2 Quick Mode [SA][KEY][ID][HASH][NONCE] 122626 Default RECV Informational [HASH][NOTIFY] with INVALID_ID_INFORMATION error 122626 Default RECV Informational [HASH][DEL] 122626 Default CNXVPN1-P1 deleted
If you have an INVALID ID INFORMATION error, check if Phase 2 ID (local address and network address) is correct and match what is expected by the remote endpoint. Check also ID type (Subnet address and Single address). If network mask is not check, you are using a IPV4_ADDR type (and not a IPV4_SUBNET type).
6.7 I clicked on Open tunnel, but nothing happens.
Read logs of each VPN tunnel endpoint. IKE requests can be dropped by firewalls. An IPSec Client uses UDP port 500 and protocol ESP (protocol 50).
6.8 The VPN tunnel is up but I cant ping !
If the VPN tunnel is up, but you still cannot ping the remote LAN, here are a few guidelines: Check Phase 2 settings: VPN Client address and Remote LAN address. Usually, VPN Client IP address should not belong to the remote LAN subnet Once VPN tunnel is up, packets are sent with ESP protocol. This protocol can be blocked by firewall. Check that every device between the client and the VPN server does accept ESP Check your VPN server logs. Packets can be dropped by one of its firewall rules.
IPSec VPN Router Configuration Property of TheGreenBow Sistech SA - 2001-2012 14/17
Doc.Ref Doc.version VPN version
tgbvpn_ug-digitel-nrx-5122-en
Feb 2012
5.x
Check your ISP support ESP If you still cannot ping, follow ICMP traffic on VPN server LAN interface and on LAN computer interface (with Wireshark for example). You will have an indication that encryption works. Check the default gateway value in VPN Server LAN. A target on your remote LAN can receive pings but does not answer because there is a no Default gateway setting. You cannot access to the computers in the LAN by their name. You must specify their IP address inside the LAN. We recommend you to install Wireshark (http://www.wireshark.org) on one of your target computer. You can check that your pings arrive inside the LAN.
IPSec VPN Router Configuration
Property of TheGreenBow Sistech SA - 2001-2012
15/17
Doc.Ref Doc.version VPN version
tgbvpn_ug-digitel-nrx-5122-en
Feb 2012
5.x
7 Contacts
News and updates on TheGreenBow web site: http://www.thegreenbow.com Technical support by email at support@thegreenbow.com Sales contacts by email at sales@thegreenbow.com
News and updates on Digitel web site: http://www.digitel.com.br Technical support by email at: suporte@digitel.com.br Sales contacts by email at: vendas_digitel@digitel.com.br
IPSec VPN Router Configuration
Property of TheGreenBow Sistech SA - 2001-2012
16/17
Secure, Strong, Simple.
TheGreenBow Security Software
S-ar putea să vă placă și
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeDe la EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeEvaluare: 4 din 5 stele4/5 (5794)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreDe la EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreEvaluare: 4 din 5 stele4/5 (1090)
- Never Split the Difference: Negotiating As If Your Life Depended On ItDe la EverandNever Split the Difference: Negotiating As If Your Life Depended On ItEvaluare: 4.5 din 5 stele4.5/5 (838)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceDe la EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceEvaluare: 4 din 5 stele4/5 (894)
- Grit: The Power of Passion and PerseveranceDe la EverandGrit: The Power of Passion and PerseveranceEvaluare: 4 din 5 stele4/5 (587)
- Shoe Dog: A Memoir by the Creator of NikeDe la EverandShoe Dog: A Memoir by the Creator of NikeEvaluare: 4.5 din 5 stele4.5/5 (537)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureDe la EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureEvaluare: 4.5 din 5 stele4.5/5 (474)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersDe la EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersEvaluare: 4.5 din 5 stele4.5/5 (344)
- Her Body and Other Parties: StoriesDe la EverandHer Body and Other Parties: StoriesEvaluare: 4 din 5 stele4/5 (821)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)De la EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Evaluare: 4.5 din 5 stele4.5/5 (119)
- The Emperor of All Maladies: A Biography of CancerDe la EverandThe Emperor of All Maladies: A Biography of CancerEvaluare: 4.5 din 5 stele4.5/5 (271)
- The Little Book of Hygge: Danish Secrets to Happy LivingDe la EverandThe Little Book of Hygge: Danish Secrets to Happy LivingEvaluare: 3.5 din 5 stele3.5/5 (399)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyDe la EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyEvaluare: 3.5 din 5 stele3.5/5 (2219)
- The Yellow House: A Memoir (2019 National Book Award Winner)De la EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Evaluare: 4 din 5 stele4/5 (98)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaDe la EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaEvaluare: 4.5 din 5 stele4.5/5 (265)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryDe la EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryEvaluare: 3.5 din 5 stele3.5/5 (231)
- Team of Rivals: The Political Genius of Abraham LincolnDe la EverandTeam of Rivals: The Political Genius of Abraham LincolnEvaluare: 4.5 din 5 stele4.5/5 (234)
- On Fire: The (Burning) Case for a Green New DealDe la EverandOn Fire: The (Burning) Case for a Green New DealEvaluare: 4 din 5 stele4/5 (73)
- The Unwinding: An Inner History of the New AmericaDe la EverandThe Unwinding: An Inner History of the New AmericaEvaluare: 4 din 5 stele4/5 (45)
- How To Configure VPN Remote Access With D-Link Netdefend DFL-800 and WinRadius Radius ServerDocument23 paginiHow To Configure VPN Remote Access With D-Link Netdefend DFL-800 and WinRadius Radius Servergreenbow100% (5)
- Information Security PracticalDocument21 paginiInformation Security PracticalDeepak Kumar Rajak67% (6)
- Free Proxy Lists - HTTP Proxy Servers (IP Address, Port)Document2 paginiFree Proxy Lists - HTTP Proxy Servers (IP Address, Port)mojiee25% (8)
- Vyatta VPN Router W/ Certificate & GreenBow IPsec VPN Software ConfigurationDocument15 paginiVyatta VPN Router W/ Certificate & GreenBow IPsec VPN Software ConfigurationgreenbowÎncă nu există evaluări
- Cisco RV120W Wireless VPN Firewall & GreenBow IPSec VPN Client Software ConfigurationDocument17 paginiCisco RV120W Wireless VPN Firewall & GreenBow IPSec VPN Client Software ConfigurationgreenbowÎncă nu există evaluări
- Cisco RV220-W VPN Router & GreenBow IPsec VPN Software ConfigurationDocument16 paginiCisco RV220-W VPN Router & GreenBow IPsec VPN Software ConfigurationgreenbowÎncă nu există evaluări
- Watchguard XTM 33 VPN Router & GreenBow IPsec VPN Software ConfigurationDocument17 paginiWatchguard XTM 33 VPN Router & GreenBow IPsec VPN Software ConfigurationgreenbowÎncă nu există evaluări
- Allied Telesis AT-AR700 VPN Gateway With Radius Server & GreenBow IPSec VPN Client Software ConfigurationDocument22 paginiAllied Telesis AT-AR700 VPN Gateway With Radius Server & GreenBow IPSec VPN Client Software ConfigurationgreenbowÎncă nu există evaluări
- Fortinet FortiGate 60B & GreenBow IPSec VPN Client Software ConfigurationDocument14 paginiFortinet FortiGate 60B & GreenBow IPSec VPN Client Software ConfigurationgreenbowÎncă nu există evaluări
- NetGear FVS336G VPN Gateway & GreenBow IPsec VPN Software ConfigurationDocument16 paginiNetGear FVS336G VPN Gateway & GreenBow IPsec VPN Software ConfigurationgreenbowÎncă nu există evaluări
- Vyatta VPN Router W/ PreSharedKey & GreenBow IPsec VPN Software ConfigurationDocument14 paginiVyatta VPN Router W/ PreSharedKey & GreenBow IPsec VPN Software ConfigurationgreenbowÎncă nu există evaluări
- Huawei Secoway SVN2260 VPN Gateway & GreenBow IPsec VPN Software ConfigurationDocument14 paginiHuawei Secoway SVN2260 VPN Gateway & GreenBow IPsec VPN Software ConfigurationgreenbowÎncă nu există evaluări
- Juniper SRX Series & GreenBow IPSec VPN Client Software Configuration (English)Document13 paginiJuniper SRX Series & GreenBow IPSec VPN Client Software Configuration (English)greenbowÎncă nu există evaluări
- Astaro Security Gateway & GreenBow IPSec VPN Client Software ConfigurationDocument15 paginiAstaro Security Gateway & GreenBow IPSec VPN Client Software ConfigurationgreenbowÎncă nu există evaluări
- Mcafee Snapgear SG300 VPN Gateway & GreenBow IPSec VPN Client Software ConfigurationDocument13 paginiMcafee Snapgear SG300 VPN Gateway & GreenBow IPSec VPN Client Software ConfigurationgreenbowÎncă nu există evaluări
- Juniper Netscreen NS 5GT Series & GreenBow IPSec VPN Client Software ConfigurationDocument14 paginiJuniper Netscreen NS 5GT Series & GreenBow IPSec VPN Client Software ConfigurationgreenbowÎncă nu există evaluări
- Hillstone SA Firewall Series & GreenBow IPSec VPN Client Software Configuration (English)Document15 paginiHillstone SA Firewall Series & GreenBow IPSec VPN Client Software Configuration (English)greenbowÎncă nu există evaluări
- Watchguard Firebox X Edge E-Series & GreenBow IPSec VPN Client Software Configuration (English)Document18 paginiWatchguard Firebox X Edge E-Series & GreenBow IPSec VPN Client Software Configuration (English)greenbowÎncă nu există evaluări
- TheGreenBow VPN Client Software - Deployment GuideDocument20 paginiTheGreenBow VPN Client Software - Deployment GuidegreenbowÎncă nu există evaluări
- Allied Telesis AT-AR700 VPN Gateway & GreenBow IPSec VPN Client Software ConfigurationDocument19 paginiAllied Telesis AT-AR700 VPN Gateway & GreenBow IPSec VPN Client Software ConfigurationgreenbowÎncă nu există evaluări
- Digi ConnectPort WAN VPN Cellular Gateway & GreenBow IPSec VPN Client Software ConfigurationDocument14 paginiDigi ConnectPort WAN VPN Cellular Gateway & GreenBow IPSec VPN Client Software ConfigurationgreenbowÎncă nu există evaluări
- LinkTrust Firewall/UTM X3-X5 VPN Router & GreenBow IPSec VPN Client Software ConfigurationDocument15 paginiLinkTrust Firewall/UTM X3-X5 VPN Router & GreenBow IPSec VPN Client Software ConfigurationgreenbowÎncă nu există evaluări
- Cisco SA 500 VPN Security Appliance & GreenBow IPSec VPN Client Software Configuration (English)Document14 paginiCisco SA 500 VPN Security Appliance & GreenBow IPSec VPN Client Software Configuration (English)greenbowÎncă nu există evaluări
- Opengear VPN Gateway & GreenBow IPSec VPN Client Software ConfigurationDocument14 paginiOpengear VPN Gateway & GreenBow IPSec VPN Client Software ConfigurationgreenbowÎncă nu există evaluări
- Digital China DCFW 1800E-UTM VPN Router & GreenBow IPSec VPN Client Software ConfigurationDocument15 paginiDigital China DCFW 1800E-UTM VPN Router & GreenBow IPSec VPN Client Software ConfigurationgreenbowÎncă nu există evaluări
- Zyxell ZyWALL USG 1000 VPN Router & GreenBow IPSec VPN Client Software ConfigurationDocument16 paginiZyxell ZyWALL USG 1000 VPN Router & GreenBow IPSec VPN Client Software ConfigurationgreenbowÎncă nu există evaluări
- Pfsense VPN Router & GreenBow IPSec VPN Client Software ConfigurationDocument14 paginiPfsense VPN Router & GreenBow IPSec VPN Client Software ConfigurationgreenbowÎncă nu există evaluări
- D-Link Wireless VPN Router DI 824-VUP & GreenBow IPSec VPN Client Software ConfigurationDocument14 paginiD-Link Wireless VPN Router DI 824-VUP & GreenBow IPSec VPN Client Software Configurationgreenbow100% (1)
- D-Link Broadband VPN Router DIR 130 & GreenBow IPSec VPN Client Software ConfigurationDocument13 paginiD-Link Broadband VPN Router DIR 130 & GreenBow IPSec VPN Client Software Configurationgreenbow100% (1)
- D-Link Netdefend IPS Firewall DFL 800 & GreenBow IPSec VPN Client Software ConfigurationDocument14 paginiD-Link Netdefend IPS Firewall DFL 800 & GreenBow IPSec VPN Client Software Configurationgreenbow100% (2)
- Cyber Tech Radar 2022 Brochure PDF en v5 WEBDocument20 paginiCyber Tech Radar 2022 Brochure PDF en v5 WEBdolamthienÎncă nu există evaluări
- The Need For Cyber Resilient Enterprise Distributed Ledger Risk Management FrameworkDocument9 paginiThe Need For Cyber Resilient Enterprise Distributed Ledger Risk Management FrameworkKrishna Prasad SatamrajuÎncă nu există evaluări
- TEST CASES FOR PINTERESTDocument6 paginiTEST CASES FOR PINTERESTSahil SinghÎncă nu există evaluări
- AWS Auditing Security Checklist PDFDocument28 paginiAWS Auditing Security Checklist PDFmaynord_arguelloÎncă nu există evaluări
- A GUIDE TO CYBER SECURITY Careed DevelopmentDocument2 paginiA GUIDE TO CYBER SECURITY Careed DevelopmentSoluciones en Blockchain100% (1)
- Introduction To Ethical Hacking Author Kanav JindalDocument12 paginiIntroduction To Ethical Hacking Author Kanav JindalabhayÎncă nu există evaluări
- IncompatibleDocument30 paginiIncompatibleCristia RiveraÎncă nu există evaluări
- 5 TH UNIT MCQSDocument15 pagini5 TH UNIT MCQSFazal QureshiÎncă nu există evaluări
- SB Database Security InsightsDocument5 paginiSB Database Security Insightslakbabi1035Încă nu există evaluări
- Online Shopping and Transactions ExplainedDocument2 paginiOnline Shopping and Transactions ExplainedNitin Lal ChandaniÎncă nu există evaluări
- AWS IAM Notes: Users, Groups, Roles and Policy DocumentsDocument7 paginiAWS IAM Notes: Users, Groups, Roles and Policy DocumentsVeena AgaramÎncă nu există evaluări
- Mobile Worms and VirusesDocument39 paginiMobile Worms and VirusesPuspala ManojkumarÎncă nu există evaluări
- Abusing Functions For Bug Bounty PDFDocument10 paginiAbusing Functions For Bug Bounty PDFbig brosÎncă nu există evaluări
- Course 1 ReadingDocument35 paginiCourse 1 Readingedu.yoyo20Încă nu există evaluări
- STEGANOGRAPHY and VISUAL CRYPTOGRAPHY FODocument5 paginiSTEGANOGRAPHY and VISUAL CRYPTOGRAPHY FODuraiyarasan MÎncă nu există evaluări
- The Secure Shell (SSH) Protocol ArchitectureDocument18 paginiThe Secure Shell (SSH) Protocol ArchitectureicsulescuÎncă nu există evaluări
- Cyber Security Assignment 2018Document8 paginiCyber Security Assignment 2018varsha guptaÎncă nu există evaluări
- Wpa Wpa2Document21 paginiWpa Wpa2G Siva Prakash ReddyÎncă nu există evaluări
- WiFi Hacking Mind MapDocument1 paginăWiFi Hacking Mind Mapakunbuat yutubÎncă nu există evaluări
- ESET KEYs SEPTEMBERDocument4 paginiESET KEYs SEPTEMBERBAR BITTERSÎncă nu există evaluări
- RE-Generator Password Reset and Account Unlock ManualDocument11 paginiRE-Generator Password Reset and Account Unlock ManualSachinShelkeÎncă nu există evaluări
- LPT BrochureDocument15 paginiLPT BrochureJoker JrÎncă nu există evaluări
- Veteran Led Cyber Security Company Anti-Virus PolicyDocument5 paginiVeteran Led Cyber Security Company Anti-Virus PolicyLuis ContrerasÎncă nu există evaluări
- Online Safety and Security PPTDocument17 paginiOnline Safety and Security PPTJEMNA PITOGOÎncă nu există evaluări
- FortiOS 7.2 Exam DescriptionDocument3 paginiFortiOS 7.2 Exam DescriptionJorge DanielÎncă nu există evaluări
- Guia Do TryHackmeDocument3 paginiGuia Do TryHackme2hwvvbz5s2Încă nu există evaluări
- Grid Stream Solution OverviewDocument11 paginiGrid Stream Solution OverviewMed Amine TAHIRIÎncă nu există evaluări
- CEH v10 Module 13 Hacking Web Servers PDFDocument25 paginiCEH v10 Module 13 Hacking Web Servers PDFDavid AmanÎncă nu există evaluări