Documente Academic
Documente Profesional
Documente Cultură
Weak Keys in DES
Încărcat de
vanand20032004Descriere originală:
Drepturi de autor
Formate disponibile
Partajați acest document
Partajați sau inserați document
Vi se pare util acest document?
Este necorespunzător acest conținut?
Raportați acest documentDrepturi de autor:
Formate disponibile
Weak Keys in DES
Încărcat de
vanand20032004Drepturi de autor:
Formate disponibile
Weak keys in DES
The block cipher DES has a few specific keys termed "weak keys" and "semi-weak keys". These are keys that cause the encryption mode of DES to act identically to the decryption mode of DES (albeit potentially that of a different key). In operation, the secret 56-bit key is broken up into 16 subkeys according to the DES key schedule; one subkey is used in each of the sixteen DES rounds. DES weak keys produce sixteen identical subkeys. This occurs when the key bits are:[1]
Alternating ones + zeros (0x0101010101010101) Alternating 'F' + 'E' (0xFEFEFEFEFEFEFEFE) '0xE0E0E0E0F1F1F1F1' '0x1F1F1F1F0E0E0E0E'
If an implementation does not consider the parity bits, the corresponding keys with the inverted parity bits may also work as weak keys:
all zeros (0x0000000000000000) all ones (0xFFFFFFFFFFFFFFFF) '0xE1E1E1E1F0F0F0F0' '0x1E1E1E1E0F0F0F0F'
Using weak keys, the outcome of the Permuted Choice 1 (PC1) in the DES key schedule leads to round keys being either all zeros, all ones or alternating zero-one patterns. Since all the subkeys are identical, and DES is a Feistel network, the encryption function is self-inverting; that is, encrypting twice produces the original plaintext. DES also has semi-weak keys, which only produce two different subkeys, each used eight times in the algorithm: This means they come in pairs K1 and K2, and they have the property that:
where EK(M) is the encryption algorithm encrypting message M with key K. There are six semiweak key pairs:
0x011F011F010E010E and 0x1F011F010E010E01 0x01E001E001F101F1 and 0xE001E001F101F101 0x01FE01FE01FE01FE and 0xFE01FE01FE01FE01 0x1FE01FE00EF10EF1 and 0xE01FE01FF10EF10E 0x1FFE1FFE0EFE0EFE and 0xFE1FFE1FFE0EFE0E 0xE0FEE0FEF1FEF1FE and 0xFEE0FEE0FEF1FEF1
There are also 48 possibly weak keys that produce only four distinct subkeys (instead of 16). They can be found in [2] These weak and semiweak keys are not considered "fatal flaws" of DES. There are 256 (7.21 1016, about 72 quadrillion) possible keys for DES, of which four are weak and twelve are semiweak. This is such a tiny fraction of the possible keyspace that users do not need to worry. If they so desire, they can check for weak or semiweak keys when the keys are generated. They are very few, and easy to recognize. Note, however, that DES is not recommended for general use since all keys can be brute-forced in about a day for a onetime hardware cost on the order of some new cards.
[edit] List of algorithms with weak keys
RC4. RC4's weak initialization vectors allow an attacker to mount a knownplaintext attack and have been widely used to compromise the security of WEP.[3] IDEA. IDEA's weak keys are identifiable in a chosen-plaintext attack. They make the relationship between the XOR sum of plaintext bits and ciphertext bits predictable. There is no list of these keys, but they can be identified by their "structure". Data Encryption Standard Blowfish. Blowfish's weak keys produce bad S-boxes, since Blowfish's S-boxes are key-dependent. There is a chosen plaintext attack against a reduced-round variant of Blowfish that is made easier by the use of weak keys. This is not a concern for full 16-round Blowfish. This list is incomplete; you can help by expanding it.
[edit] No weak keys as a design goal
The goal of having a 'flat' keyspace (i.e., all keys equally strong) is always a cipher design goal. As in the case of DES, sometimes a small number of weak keys is acceptable, provided that they are all identified or identifiable. An algorithm that has unknown weak keys does not inspire much trust[citation needed]. The two main countermeasures against inadvertently using a weak key:
Checking generated keys against a list of known weak keys, or building rejection of weak keys into the key scheduling. When the number of weak keys is known to be very small (in comparison to the size of the keyspace), generating a key uniformly at random ensures that the probability of it being weak is a (known) very small number.
A large number of weak keys is a serious flaw in any cipher design, since there will then be a (perhaps too) large chance that a randomly generated one will be a weak one,
compromising the security of messages encrypted under it. It will also take longer to check randomly generated keys for weakness in such cases, which will tempt shortcuts in interest of 'efficiency'. However, weak keys are much more often a problem where the adversary has some control over what keys are used, such as when a block cipher is used in a mode of operation intended to construct a secure cryptographic hash function (e.g. Davies-Meyer).
[edit]
S-ar putea să vă placă și
- Digraph SH Pack 2Document10 paginiDigraph SH Pack 2Elvis AungÎncă nu există evaluări
- Icse Class 1 Maths Sample Paper Model 1 PDFDocument3 paginiIcse Class 1 Maths Sample Paper Model 1 PDFAshish DasÎncă nu există evaluări
- Tektronix 576 Curve Tracer Operation and Service ManualDocument251 paginiTektronix 576 Curve Tracer Operation and Service Manualmunnizza64100% (3)
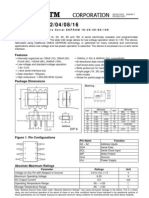
- FOR EEPROM DOCUMENTDocument9 paginiFOR EEPROM DOCUMENTIram Loya ValladaresÎncă nu există evaluări
- 2-Wire Serial EEPROM: FeaturesDocument23 pagini2-Wire Serial EEPROM: FeaturesgillupilluÎncă nu există evaluări
- Q1 TLE 9-11 Computer Systems Servicing NC II Mod5Document24 paginiQ1 TLE 9-11 Computer Systems Servicing NC II Mod5John Alfred EbordaÎncă nu există evaluări
- DTC P0135 Oxyge (A/F) Sensor Heater Circuit (Bank 1 Sensor 1)Document3 paginiDTC P0135 Oxyge (A/F) Sensor Heater Circuit (Bank 1 Sensor 1)Erln LimaÎncă nu există evaluări
- FaultMemoryList VIN7-B914278 PDFDocument2 paginiFaultMemoryList VIN7-B914278 PDFZakaria ElÎncă nu există evaluări
- Opel Simtec56.XDocument9 paginiOpel Simtec56.Xsimox_softÎncă nu există evaluări
- A Report On Industrial Work ExperienceDocument20 paginiA Report On Industrial Work ExperienceAgusiobo Anthony ChukwudiÎncă nu există evaluări
- The Secrets of DDos AttacksDocument9 paginiThe Secrets of DDos AttacksAdam Siemion100% (1)
- Corsa D EPSDocument1 paginăCorsa D EPScork_ie100% (1)
- RX 400h Personalized SettingsDocument8 paginiRX 400h Personalized SettingsSavin CristiÎncă nu există evaluări
- CIRCUIT DIAGRAMSDocument89 paginiCIRCUIT DIAGRAMSSean OsborneÎncă nu există evaluări
- EMU BLACK ECU pin functions referenceDocument4 paginiEMU BLACK ECU pin functions referenceadrianÎncă nu există evaluări
- Boost Drupal Performance by Rumen YordanovDocument40 paginiBoost Drupal Performance by Rumen YordanovsegmentsÎncă nu există evaluări
- BMW EWS2, EWS3.2 EMULATOR使用说明Document4 paginiBMW EWS2, EWS3.2 EMULATOR使用说明Manuel SuarezÎncă nu există evaluări
- How To Calculate The Score of Your Cambridge English ExamDocument15 paginiHow To Calculate The Score of Your Cambridge English ExamSameh IbrahimÎncă nu există evaluări
- LTE Site Solutions OverviewDocument94 paginiLTE Site Solutions OverviewArghyaPodderÎncă nu există evaluări
- PDS - Ingenuity - Core - 128Document20 paginiPDS - Ingenuity - Core - 128CeoĐứcTrườngÎncă nu există evaluări
- Saw Filter (Siemens)Document350 paginiSaw Filter (Siemens)Luiz059100% (1)
- Land Surveyor CV TemplateDocument3 paginiLand Surveyor CV TemplateAlexandra Zahan67% (3)
- Service Manual: LC-32A33T LC-37A33TDocument38 paginiService Manual: LC-32A33T LC-37A33TSetiawan Abdul RochimÎncă nu există evaluări
- ECM I/O Signals Diagnostic GuideDocument5 paginiECM I/O Signals Diagnostic Guideazkaz1Încă nu există evaluări
- Schrader Automotive Equipment SupplierDocument24 paginiSchrader Automotive Equipment SupplierPiotr ProkulskiÎncă nu există evaluări
- 01-15 Check DTC Memory and Erase DTC Memory PDFDocument52 pagini01-15 Check DTC Memory and Erase DTC Memory PDFmefisto06cÎncă nu există evaluări
- How To Reset An Acer BIOS Password PDFDocument5 paginiHow To Reset An Acer BIOS Password PDFrahul2222222Încă nu există evaluări
- DTC C1554/23 Power Supply Relay Failure DTC C1555/25 Motor Relay Welding FailureDocument3 paginiDTC C1554/23 Power Supply Relay Failure DTC C1555/25 Motor Relay Welding FailureOswaldo Sierra100% (1)
- PAL MaintenanceDocument4 paginiPAL MaintenanceLucas PrimaniÎncă nu există evaluări
- ADAS Description enDocument10 paginiADAS Description enIonut-alexandru IordacheÎncă nu există evaluări
- What are TPX1 TPX2,TPX3 and TPX4 cloning chips and their differences from transpondersDocument3 paginiWhat are TPX1 TPX2,TPX3 and TPX4 cloning chips and their differences from transpondersLuix TiradoÎncă nu există evaluări
- VgrsDocument6 paginiVgrsAnon JansabÎncă nu există evaluări
- Typical LED SymbolDocument4 paginiTypical LED Symbolthy thy thyÎncă nu există evaluări
- Techstream Part 1Document21 paginiTechstream Part 1Diegophd FernandezÎncă nu există evaluări
- 1zr-Fae Engine Mechanical Service DataDocument10 pagini1zr-Fae Engine Mechanical Service DataMarzena SynoradzkaÎncă nu există evaluări
- Acer Aspire 3 A315-22 NB8607 Rev1.0Document55 paginiAcer Aspire 3 A315-22 NB8607 Rev1.0Carlos Yuvini Hernandez100% (1)
- Technical Service BULLETINDocument328 paginiTechnical Service BULLETINCarlos E. FuentesÎncă nu există evaluări
- Removing and Installing Mechatronic Unit For Dual Clutch Gearbox - J743Document93 paginiRemoving and Installing Mechatronic Unit For Dual Clutch Gearbox - J743Sandro CozaciucÎncă nu există evaluări
- Greddy E Manage Instalcion en MitsubishiDocument11 paginiGreddy E Manage Instalcion en MitsubishiFelipe Cortes0% (1)
- 1 - Overview of CTC and PALs 10-23-11Document30 pagini1 - Overview of CTC and PALs 10-23-11Khoa Nam NguyenÎncă nu există evaluări
- DWM C ™ S - H C O P D S Ops2: Opeland EMI Ermetic Ompressors IL Ressure Ifferential WitchDocument5 paginiDWM C ™ S - H C O P D S Ops2: Opeland EMI Ermetic Ompressors IL Ressure Ifferential WitchMuhammadAmmarÎncă nu există evaluări
- Alfa Romeo 145 146 Useful SpecificationsDocument3 paginiAlfa Romeo 145 146 Useful SpecificationseephantomÎncă nu există evaluări
- Hybrid Battery Control: HV Battery: Charging 2010 My Ls600h (11:2009 - )Document15 paginiHybrid Battery Control: HV Battery: Charging 2010 My Ls600h (11:2009 - )Duc TruongÎncă nu există evaluări
- 32d05 Control of ECTDocument12 pagini32d05 Control of ECTMelvin MhdsÎncă nu există evaluări
- Overall Electrical Wiring DiagramDocument1 paginăOverall Electrical Wiring Diagramallaucaamor100% (1)
- 6502 Instruction Set ReferenceDocument5 pagini6502 Instruction Set ReferenceYann Van OsselaerÎncă nu există evaluări
- CIRCUIT DIAGRAMDocument40 paginiCIRCUIT DIAGRAMYannick de WalqueÎncă nu există evaluări
- 4MATIC Automatic four-wheel drive controlDocument6 pagini4MATIC Automatic four-wheel drive controlAnonymous qz5pEMh44Încă nu există evaluări
- Buk9222 55aDocument13 paginiBuk9222 55aAnthony AndreyÎncă nu există evaluări
- Esp 8.1Document5 paginiEsp 8.1Stanila CatalinÎncă nu există evaluări
- Dme 1.1 1.3Document7 paginiDme 1.1 1.3Minas HarutyunyanÎncă nu există evaluări
- BMW E23 24 28 OdogearDocument9 paginiBMW E23 24 28 OdogearporkfaceÎncă nu există evaluări
- Mx5 95 1 of 3 EngineDocument90 paginiMx5 95 1 of 3 EngineJennifer Faith EvansÎncă nu există evaluări
- Omegas Plus: Software ManualDocument40 paginiOmegas Plus: Software ManualВіктор ЛялькаÎncă nu există evaluări
- Mitchell Plus 5.9 Manual de Instalacion SoftwareDocument51 paginiMitchell Plus 5.9 Manual de Instalacion SoftwareSergio OrozÎncă nu există evaluări
- Foxwell NT301 OBD OBD2 Engine Universal Car Code Reader Scanner Diagnostic ToolDocument3 paginiFoxwell NT301 OBD OBD2 Engine Universal Car Code Reader Scanner Diagnostic ToolD JocelynÎncă nu există evaluări
- Almera N16 TechDocument4 paginiAlmera N16 TechSpiros FousasÎncă nu există evaluări
- ReadmeDocument1 paginăReadmeNicholas HarmonÎncă nu există evaluări
- Panasonic DB2S311 DatasheetDocument70 paginiPanasonic DB2S311 DatasheetKenan Qu100% (1)
- CD40 USB Pin Code ExtractingDocument2 paginiCD40 USB Pin Code Extractingkamaleon doradoÎncă nu există evaluări
- DSM Ecu Extended Map GuideDocument4 paginiDSM Ecu Extended Map GuideJohn MongielloÎncă nu există evaluări
- Volvo 850 ODB A1 Automatic Transmission DiagnosticDocument9 paginiVolvo 850 ODB A1 Automatic Transmission DiagnosticBartłomiej KilianÎncă nu există evaluări
- 2008-11-14 003029 Es Code CheckDocument6 pagini2008-11-14 003029 Es Code CheckRaysian K. SetoÎncă nu există evaluări
- Installation Instructions 30-5130Document8 paginiInstallation Instructions 30-5130alexcus1539Încă nu există evaluări
- P.Kay ECU CodesDocument8 paginiP.Kay ECU Codesadgjl123456100% (1)
- Glow Plug DriverDocument2 paginiGlow Plug DrivercooldamageÎncă nu există evaluări
- Des Analysis: Handled By: Ms. Divya BDocument19 paginiDes Analysis: Handled By: Ms. Divya BJithin VijayanÎncă nu există evaluări
- The Basic Structure of DES Describe The Details of Building Elements of DES Describe The Round Keys Generation Process To Analyze DES Mode of Encryption in Modern Symmetric Key CiphersDocument52 paginiThe Basic Structure of DES Describe The Details of Building Elements of DES Describe The Round Keys Generation Process To Analyze DES Mode of Encryption in Modern Symmetric Key CiphersSatyanarayana VollalaÎncă nu există evaluări
- OpenSSL DES APIDocument12 paginiOpenSSL DES APIFinnbarr P. MurphyÎncă nu există evaluări
- New Passitexams Cisco210-250 Dumps PDF - Understanding Cisco Cybersecurity FundamentalsDocument10 paginiNew Passitexams Cisco210-250 Dumps PDF - Understanding Cisco Cybersecurity FundamentalsMaria J. AndersonÎncă nu există evaluări
- Script For PPT SIHDocument3 paginiScript For PPT SIHjainanuj7923Încă nu există evaluări
- CC-S4C-S4D-S4E Manual (EN) CNCDocument40 paginiCC-S4C-S4D-S4E Manual (EN) CNCHakan GökbudakÎncă nu există evaluări
- Ds Whitehat DastDocument4 paginiDs Whitehat DastNguyễn LinhÎncă nu există evaluări
- Flutter SMD ClassNotesDocument20 paginiFlutter SMD ClassNoteslava bhaiÎncă nu există evaluări
- PoorvDocument46 paginiPoorvkrishna kantÎncă nu există evaluări
- 1aws Cost-ManagementDocument14 pagini1aws Cost-ManagementJohann LeeÎncă nu există evaluări
- Villanueva T3a Lab3Document5 paginiVillanueva T3a Lab3Miggy VillanuevaÎncă nu există evaluări
- Senior PHP DeveloperDocument2 paginiSenior PHP DeveloperPockie MenÎncă nu există evaluări
- Answer KeyDocument5 paginiAnswer Keyana maria csalinasÎncă nu există evaluări
- Arduino Interrupciones ManualesDocument7 paginiArduino Interrupciones Manualesleonar3177Încă nu există evaluări
- Creating A Database For Joomla PDFDocument3 paginiCreating A Database For Joomla PDFAngelo BolañosÎncă nu există evaluări
- MOSS Scheduling Simulator User Guide: PurposeDocument7 paginiMOSS Scheduling Simulator User Guide: PurposeKhushboo AgrawalÎncă nu există evaluări
- Lecture Notes For EE-226 Circuit Analysis-II: Dr. Ghulam MustafaDocument14 paginiLecture Notes For EE-226 Circuit Analysis-II: Dr. Ghulam MustafaOsama AsgharÎncă nu există evaluări
- Agile Artifact NOT Referred in ProjectDocument28 paginiAgile Artifact NOT Referred in ProjectGEO MERINÎncă nu există evaluări
- Ejemplo CV en InglesDocument1 paginăEjemplo CV en Inglesgomezmendezpablo5Încă nu există evaluări
- Excel Function Dictionary © 1998 - 2000 Peter NoneleyDocument206 paginiExcel Function Dictionary © 1998 - 2000 Peter NoneleynooverakÎncă nu există evaluări
- Las550h BPHLLLK Mfl69400864 SimDocument2 paginiLas550h BPHLLLK Mfl69400864 Simhenrique caracasÎncă nu există evaluări
- HP Scanjet Flow 8500 Fn2 Scanjet Flow n9120 Fn2 Troubleshooting ManualDocument136 paginiHP Scanjet Flow 8500 Fn2 Scanjet Flow n9120 Fn2 Troubleshooting ManualbellobevaÎncă nu există evaluări
- Solutions Manual To Accompany Miller Freunds Probability and Statistics For Engineers 8th Edition 0321640772Document23 paginiSolutions Manual To Accompany Miller Freunds Probability and Statistics For Engineers 8th Edition 0321640772paulsuarezearojnmgyiÎncă nu există evaluări
- Data DictionaryDocument5 paginiData DictionaryEric P. PobleteÎncă nu există evaluări