Documente Academic
Documente Profesional
Documente Cultură
BWP Oracle Database Firewall 257258
Încărcat de
yoonzhDescriere originală:
Titlu original
Drepturi de autor
Formate disponibile
Partajați acest document
Partajați sau inserați document
Vi se pare util acest document?
Este necorespunzător acest conținut?
Raportați acest documentDrepturi de autor:
Formate disponibile
BWP Oracle Database Firewall 257258
Încărcat de
yoonzhDrepturi de autor:
Formate disponibile
An Oracle White Paper January 2011
Oracle Database Firewall
Oracle Database Firewall
Introduction ......................................................................................... 1 Oracle Database Firewall Overview .................................................... 2 Oracle Database Firewall .................................................................... 2 White List for Positive Security Enforcement .................................. 3 Black List for Negative Security Enforcement ................................. 4 Exception List Security Enforcement .............................................. 4 Host-Based Monitors ....................................................................... 4 Oracle Database Firewall Management Server .................................. 5 Policy Management ......................................................................... 5 Reporting ......................................................................................... 5 User Role Auditing .......................................................................... 6 Stored Procedure Auditing .............................................................. 6 Integration with F5 BIG IP ASM ...................................................... 7 Integration with ArcSight ................................................................. 7 Conclusion .......................................................................................... 7
Oracle Database Firewall
Introduction
While there will continue to be much publicized cases of lost or stolen laptops containing personally identifiable information (PII), attempts to steal large amounts of information through attacks on servers is becoming increasingly common. In fact the recently published 2010 Data Breach Investigations Report published by the Verizon Risk Team showed that 98% of data breached came from servers1. Launching successful attacks on larger repositories can result in a more lucrative payday for the perpetrator and it goes without saying that application environments, data warehouses and database in general are becoming larger and more critical to business operations and thus pose a tempting target. While it is true that organized crime has become a major player in data breaches, insiders still account for a substantial number of data breaches. The 2010 Data Breach Investigations Report also noted that privilege misuse and hacking were the most common ways breaches occurred and frequently leveraged lost or stolen credentials and application SQL Injection vulnerabilities to gain unauthorized access. Securing data on servers requires multiple layers of protection spanning both technical and administrative functions. Without question simple preventive measures such as disabling unused accounts and prohibiting shared administrative accounts go a long way toward raising the security bar. In addition, solutions such as encryption and privileged user controls inside the database play an important part in securing applications. Those solutions, however, do not monitor the SQL sent to the database over the trusted connection path. Oracle Database Firewall enables perimeter security controls, providing a first line of defense around Oracle and non-Oracle databases.
2010 Data Breach Investigations Report (Verizon Business)
Oracle Database Firewall
Oracle Database Firewall Overview
Oracle Database Firewall is an active, real-time database firewall solution that provides white list, black list and exception list policies, intelligent and accurate alerts, and monitoring with very low management and administrative costs. Oracle Database Firewall is independent of the database configuration and operation. This independent boundary of protective shielding helps reduce the risk of data loss and helps organizations manage an ever changing landscape of regulations.
Figure 1 - Oracle Database Firewall
Unlike traditional SQL firewalls that relied on identifying out-of-policy SQL using strategies such as regular expressions, string matching, and schema comparison, Oracle Database Firewall delivers intelligent database firewall security, enabling policies to be set and adapted quickly and accurately. Organizations can choose to deploy Oracle Database Firewall in blocking mode as a database policy enforcement system to protect their database assets, or to just monitor database activity for supplemental auditing and compliance purposes. Oracle Database Firewall monitors data access, enforces access policies, highlights anomalies and helps protect against network based attacks originating from outside or inside. Attacks based on SQL injection can be blocked by comparing SQL against the approved white list of application SQL. Oracle Database Firewall is unique and offers organizations a first line of defense, protecting databases from threats and helping meet regulatory compliance requirement.
Oracle Database Firewall
Oracle Database Firewall is installed on the network either on a bridge or a span port and monitors every SQL transaction request. SQL statements are processed using powerful grammar-based analysis engine that decomposes and categorizes the SQL. In addition to purely looking at the SQL statement, policies can evaluate factors such as IP address, time, and program name.
Oracle Database Firewall
Figure 2 - Oracle Database Firewall Deployment Topology
A single Oracle Database Firewall can monitor and protect many databases at once. Oracle Database Firewall can be deployed in multiple scenarios:
In-line network blocking mode and out-of-band passive network monitoring. In-line means that the SQL traffic is passed through the Oracle Database Firewall and inspected before it is forwarded to the database or blocked. Out-of-band means that the SQL traffic is copied to Oracle Database Firewall while at the same time the SQL is sent directly to the database usually by mean of a span port. These can be used simultaneously for different databases. Heterogeneous, multi-database, enforcement. For example, one device can support Oracle 8i, Oracle Database 10g and Oracle Database 11g databases simultaneously, as well as SQL Server and Sybase databases. Combined deployments. In-line and/or out-of-band Oracle Database Firewall deployment can be combined with a local server-side, monitor-only agent for local connections.
Oracle Database Firewall can be deployed a high availability configuration. It is recommended that two firewalls be deployed so that SQL monitoring is not interrupted.
White List for Positive Security Enforcement
Oracle Database Firewall enforces zero-defect database security policies using a white list security model. The white list policy is a set of approved SQL statements that can be sent to the database. Oracle Database Firewall compares SQL traffic with the approved white list and then based upon the policy, it chooses to block, substitute or alert on the SQL statement. The Oracle Database Firewall baseline can be configured to block all out-of-policy events. This can be implemented as
Block the SQL statement Modify the request using SQL statement substitution Alert on all out of policy SQL statements, in addition to blocking or in lieu of
Oracle Database Firewall
In many cases, the best solution is to apply statement substitution. Statement substitution provides a means of making Oracle Database Firewall transparent to detection by hackers and is more transparent to the existing application. In simple terms statement substitution is the process of taking an out-of-policy statement and changing it for a new statement that will not return any data.
TABLE 1. EXAMPLES OF ORACLE DATABASE FIREWALL SQL STATEMENT SUBSTITUTION
ORIGINAL STATEMENT (FRAUDULENT)
SUBSTITUTED STATEMENT
DATABASE RESPONSE (RESULT)
SELECT * FROM tbl_users;
SELECT * FROM tbl_users WHERE 'a' = 'b';
No record found.
DROP TABLE tbl_accounts; UPDATE tbl_accounts SET accounts = '123' WHER user = 'Fred';
SELECT * FROM aaabbbccc; SELECT DUAL SET 'Fred';
Error. Error.
Table not known. Incorrect Syntax.
Black List for Negative Security Enforcement
In addition to the white list, positive security enforcement model, Oracle Database Firewall also supports a black list model that enables policies to specify blocking of specific SQL statements. As with white list policies, black list policies can be configured to allow specific statements based on factors such as IP address, time of day and program.
Exception List Security Enforcement
Exception lists policies supplement white list and black list policies by allowing specific policies to be created for specific activities. For example, exception list policies could be used to enable a remote administrator to diagnose a particular application performance issue.
Host-Based Monitors
Oracle Database Firewall also provides very lightweight host-based monitors or agents that monitor databases. The host monitor sends the information to the Oracle Database Firewall for monitoring, logging and alerting purposes. The characteristics and operation of the Oracle Database Firewall monitors are listed in the Table 1.
TABLE 2. CHARACTERISTICS AND OPERATION OF ORACLE DATABASE FIREWALL MONITORS
MONITOR TYPE
OPERATION METHODS
Remote Monitor
Software monitor (agent) installed on the host operating system. Agent monitors specified network traffic bound for one or many database schemas or catalogs. Captures SQL transactions and sends back traffic to the Oracle Database Firewall for real-time alerting, post-event compliance, and monitoring reports. A Remote Monitor is used when the Oracle Database Firewall cannot be deployed in front of the database host to capture incoming SQL.
Oracle Database Firewall
Local Monitor
Additional tables are installed into the monitored databases to capture SQL traffic that originates from sources that have direct access to the database, such as console users or batch jobs that run on the database server. The Oracle Database Firewall collects the data by querying the database at regular intervals, and then uses the data in the same manner as statements originating from database clients. Depending on the design of the policy, the statements may be logged and/or produce alerts.
Figure 3 - Oracle Database Firewall Local Monitor
Oracle Database Firewall Management Server
The Oracle Database Firewall Management Server centrally manages Oracle Database Firewall policies, consolidates data from the Oracle Database Firewalls, stores database activity data, and provides dozens of out-of-the-box reports.
Policy Management
Oracle Database Firewall delivers simple and easy to use policy management tools that build upon the powerful strengths of the SQL grammar-based analysis approach. Oracle Database Firewall can define a white list of approved SQL language for a given database and define a positive security model. Oracle Database Firewall policy management groups queries together that have the same effect on the database. Oracle Database Firewall allows factors such as IP addresses, client programs, and time of day to be associated with SQL. When the Oracle Database Firewall policy management uses factors on the network, fine-grained and powerful policies can be built to determine when, where, and how changes in a production environment occur.
Reporting
Oracle Database Firewall ships with dozens of predefined reports that can be used for Sarbanes-Oxley (SOX), Payment Card Industry Data Security Standard (PCI DSS), Health Insurance Portability and Accountability Act (HIPAA), Gramm-Leach-Bliley Act (GBLA) and other privacy and compliance regulations. Oracle Database Firewall records all available details about events and makes all of the
Orac Database Firewall cle
event attributes avail lable for detail or led summ reporting. Oracle Datab Firewall mary base reports can be customized and new reports w added. Reports can be scheduled a . and custom mized to includ summary in de nformation such a totals, averag percentage top 10, and as ges, es, bottom 10. Summar information can operate m ry n on par rameters that in nclude number strings, and rs, d dates a can referen pre-defined statistical, and nce arithm metic, or even u user-defined op perations. All rep ports can be sc cheduled to run at n predef fined intervals or on an ad-ho basis. All oc schedu reports ca be emailed t address lists uled an to or to p public folders i email system like in ms Micros exchange or IBM Louts notes. soft Report formats are P PDF or native Excel.
Use Role Audit er ting
Orac Database Firewall User R Auditing (U cle F Role URA) allows c customers to au and appro changes to udit ove user roles in the da atabases on a specified databa server. Ora Database F ase acle Firewall conne to the ects datab server at scheduled intervals and deter base s rmines which c changes or add ditions (if any) have been made to view: e
Ch hanges made to database role and privilege o es es When the chang were detected W ges Ch hanges are pen nding approval
Usin the administ ng tration console it is also poss e sible to monito changes and examine a history of or previ ious approvals s.
Stor Procedu Auditing red ure
Orac Database Firewall Stored Procedure Au (SPA) prov cle F udit vides auditing f functions to de etermine the contents and states of stored pro s ocedures on eac protected d ch database. The SPA functionality connects to th database serv and retriev information about stored procedures. A stored proc he ver ves n d cedure audit revea the followin data on each stored proce als ng h edure:
Fu qualified na and owne ully ame er
Oracle Database Firewall
Type of stored procedure, date created, last modified, details of any modification Action of stored procedure (DML, DCL, DDL, DML etc.) Threat rating based on key SQL grammar such as SYSTEM, UPDATE, etc.
With SPA, any changes to the stored procedures are detected and the actual change is highlighted in precise detail and automated reports can be scheduled for distribution to interested parties.
Integration with F5 BIG IP ASM
Oracle Database Firewall integrates with F5 BIG-IP Application Security Manager using a plug-in connector. The combination of Oracle Database Firewall and F5 BIG-IP Application Security Manager enables security and monitoring for both applications and databases within an enterprise. If you are also using the BIG-IP ASM interface, and an attack originates from the internet, Database Firewall provides the actual IP address and application user of the attacking Web client. This feature enables you to pinpoint the source of the internet-based attack. You can configure the integration by using the Database Firewall Administration Console.
Integration with ArcSight
The ArcSight Security Information Event Management (SIEM) system is a centralized system for logging, analyzing, and managing log messages from different sources. ArcSight SIEM enables Oracle Database Firewall to provide full details of security alerts or other selected event types, including the message text, priority and IP address of any attacker.
Conclusion
Securing data on servers requires multiple layers of protection spanning both technical and administrative functions. Oracle Database Firewall delivers intelligent database firewall security, enabling policies to be set based on SQL grammar-based analysis approach. Oracle Database Firewall validates application SQL against white list, black list and exception list policies, and to prevent SQL injection from reaching the database to begin with. Oracle Database Firewall provides dozens of outof-the-box reports that assist with a wide range of privacy and compliance regulations, including SOX, HIPAA and PCI. Flexible deployment options include inline blocking and out-of-band passive monitoring of network SQL traffic. Oracle Database Firewall enables perimeter security controls, which strengthen database security by providing a first line of defense against threats originating from both outside and inside the organization.
Oracle Database Firewall January 2011 Oracle Corporation World Headquarters 500 Oracle Parkway Redwood Shores, CA 94065 U.S.A. Worldwide Inquiries: Phone: +1.650.506.7000 Fax: +1.650.506.7200 oracle.com
Copyright 2011, Oracle and/or its affiliates. All rights reserved. This document is provided for information purposes only and the contents hereof are subject to change without notice. This document is not warranted to be error-free, nor subject to any other warranties or conditions, whether expressed orally or implied in law, including implied warranties and conditions of merchantability or fitness for a particular purpose. We specifically disclaim any liability with respect to this document and no contractual obligations are formed either directly or indirectly by this document. This document may not be reproduced or transmitted in any form or by any means, electronic or mechanical, for any purpose, without our prior written permission. Oracle and Java are registered trademarks of Oracle and/or its affiliates. Other names may be trademarks of their respective owners. AMD, Opteron, the AMD logo, and the AMD Opteron logo are trademarks or registered trademarks of Advanced Micro Devices. Intel and Intel Xeon are trademarks or registered trademarks of Intel Corporation. All SPARC trademarks are used under license and are trademarks or registered trademarks of SPARC International, Inc. UNIX is a registered trademark licensed through X/Open Company, Ltd. 0410
S-ar putea să vă placă și
- Oracle Quick Guides: Part 4 - Oracle Administration: Security and PrivilegeDe la EverandOracle Quick Guides: Part 4 - Oracle Administration: Security and PrivilegeÎncă nu există evaluări
- Oracle Database Firewall FAQDocument11 paginiOracle Database Firewall FAQanhditimemVNAÎncă nu există evaluări
- Securing SQL Server: Protecting Your Database from AttackersDe la EverandSecuring SQL Server: Protecting Your Database from AttackersÎncă nu există evaluări
- DB Firewall LabsDocument58 paginiDB Firewall Labsnt29Încă nu există evaluări
- Concise Oracle Database For People Who Has No TimeDe la EverandConcise Oracle Database For People Who Has No TimeÎncă nu există evaluări
- DB Vault 11gR2Document10 paginiDB Vault 11gR2Pradeep NpÎncă nu există evaluări
- ORACLE PL/SQL Interview Questions You'll Most Likely Be AskedDe la EverandORACLE PL/SQL Interview Questions You'll Most Likely Be AskedEvaluare: 5 din 5 stele5/5 (1)
- Ds Security Audit Vault Firewall 1883353 PDFDocument2 paginiDs Security Audit Vault Firewall 1883353 PDFAngie StumpfÎncă nu există evaluări
- Oracle Database Administration Interview Questions You'll Most Likely Be Asked: Job Interview Questions SeriesDe la EverandOracle Database Administration Interview Questions You'll Most Likely Be Asked: Job Interview Questions SeriesEvaluare: 5 din 5 stele5/5 (1)
- 405-2 - Kobal AVDF 12.1Document31 pagini405-2 - Kobal AVDF 12.1NguyenÎncă nu există evaluări
- AZURE AZ 500 STUDY GUIDE-2: Microsoft Certified Associate Azure Security Engineer: Exam-AZ 500De la EverandAZURE AZ 500 STUDY GUIDE-2: Microsoft Certified Associate Azure Security Engineer: Exam-AZ 500Încă nu există evaluări
- Ows Technology Guide WP 1864954Document25 paginiOws Technology Guide WP 1864954Ishtiaq KhanÎncă nu există evaluări
- WP-Hacking and Protecting Oracle Database VaultDocument24 paginiWP-Hacking and Protecting Oracle Database Vaultmohsen.bÎncă nu există evaluări
- Best Practices For Installing, Configuring and Deploying Oracle Database Vault Release 10.2.0.4 in An SAP EnvironmentDocument56 paginiBest Practices For Installing, Configuring and Deploying Oracle Database Vault Release 10.2.0.4 in An SAP EnvironmentRogério Pereira FalconeÎncă nu există evaluări
- Oracle Audit Vault and Database FirewallDocument16 paginiOracle Audit Vault and Database FirewallRofiq AhmedÎncă nu există evaluări
- Oracle Database 11 Product Family: An Oracle White Paper June 2012Document19 paginiOracle Database 11 Product Family: An Oracle White Paper June 2012Aliasger BharmalÎncă nu există evaluări
- Owp Avdf12 1 Sizing Best Practices v7Document13 paginiOwp Avdf12 1 Sizing Best Practices v7rongbazÎncă nu există evaluări
- Database Vault 2010 03Document44 paginiDatabase Vault 2010 03Nitya PradeepÎncă nu există evaluări
- High Availability With Oracle Database 11g Release 2: An Oracle White Paper September 2009Document32 paginiHigh Availability With Oracle Database 11g Release 2: An Oracle White Paper September 2009barisyukselÎncă nu există evaluări
- Oracle 11g Audit Vault DatasheetDocument2 paginiOracle 11g Audit Vault Datasheetcarles_perezÎncă nu există evaluări
- Exadata Security OverviewDocument2 paginiExadata Security OverviewjimmytoanÎncă nu există evaluări
- Case Study Oracle Audit Vault ImplementationDocument7 paginiCase Study Oracle Audit Vault ImplementationArjuMohamedÎncă nu există evaluări
- SWOT Analysis of The Oracle Standard and MS-SQLDocument6 paginiSWOT Analysis of The Oracle Standard and MS-SQLalexanderjohn271Încă nu există evaluări
- All About Oracle Auditing - Updated For 12C! A White Paper February 2015Document18 paginiAll About Oracle Auditing - Updated For 12C! A White Paper February 2015nt29Încă nu există evaluări
- Backend Sec ApplicationDocument183 paginiBackend Sec ApplicationKhusal PhogatÎncă nu există evaluări
- Audit Vault Firewall Faq 1958255Document9 paginiAudit Vault Firewall Faq 1958255tareqfrakÎncă nu există evaluări
- Oracle Autonomous Database Technical Overview PDFDocument28 paginiOracle Autonomous Database Technical Overview PDFMohammad Mizanur Rahman NayanÎncă nu există evaluări
- Setting Up Oracle 11g Data Guard For SAP CustomersDocument60 paginiSetting Up Oracle 11g Data Guard For SAP CustomersUdit SharmaÎncă nu există evaluări
- U SRRCHKLST Oracle10 V8R1-6Document35 paginiU SRRCHKLST Oracle10 V8R1-6jooonzÎncă nu există evaluări
- Audit Vault Firewall FAQDocument9 paginiAudit Vault Firewall FAQPraveenÎncă nu există evaluări
- Maa WP 11gr1 Activedataguard 1 128199Document41 paginiMaa WP 11gr1 Activedataguard 1 128199madhusribÎncă nu există evaluări
- Security Audit VaultDocument9 paginiSecurity Audit Vaultmrstranger1981Încă nu există evaluări
- D72591GC10 1001 UsDocument3 paginiD72591GC10 1001 Ustrungquan710Încă nu există evaluări
- Product Overview: What Is Oracle Database Vault?Document6 paginiProduct Overview: What Is Oracle Database Vault?Amani SaddohÎncă nu există evaluări
- OracleDocument66 paginiOracleAnusha SrsÎncă nu există evaluări
- Oracle Audit Vault - Data SheetDocument2 paginiOracle Audit Vault - Data SheetHot MaleÎncă nu există evaluări
- Security and Compliance With Oracle Database 12: An Oracle White Paper June 2013Document16 paginiSecurity and Compliance With Oracle Database 12: An Oracle White Paper June 2013Duarte RetratoÎncă nu există evaluări
- Corruption Bestpractices 12c 2141348Document17 paginiCorruption Bestpractices 12c 2141348Dhan DhanÎncă nu există evaluări
- Integrigy Guide To Oracle Audit VaultDocument20 paginiIntegrigy Guide To Oracle Audit VaultlemadanielÎncă nu există evaluări
- Active Data Guard Hands On LabDocument50 paginiActive Data Guard Hands On LabprasadramalaÎncă nu există evaluări
- Oracle Database 11g High Availability: An Oracle White Paper June 2007Document27 paginiOracle Database 11g High Availability: An Oracle White Paper June 2007Ganesh SinghÎncă nu există evaluări
- Azure SQL Database ArchitectureDocument7 paginiAzure SQL Database ArchitectureVirgil GlavanÎncă nu există evaluări
- Auditing the Oracle DatabaseDocument8 paginiAuditing the Oracle DatabaseahamedshihabÎncă nu există evaluări
- Oracle Database Lifecycle Management PackDocument4 paginiOracle Database Lifecycle Management PackmdalaminÎncă nu există evaluări
- Cloud Ent Hosting Del Policies 1881438Document18 paginiCloud Ent Hosting Del Policies 1881438Anil RawatÎncă nu există evaluări
- Oracle 11gdb ProductsDocument18 paginiOracle 11gdb Productsjey011Încă nu există evaluări
- Maa WP Gctomaa 134568Document53 paginiMaa WP Gctomaa 134568MigueladepazÎncă nu există evaluări
- Integrigy Intro To SQL Injection AttacksDocument24 paginiIntegrigy Intro To SQL Injection Attackskervin_dominguezÎncă nu există evaluări
- Oracle® SL500/SL3000/SL8500 Security GuideDocument12 paginiOracle® SL500/SL3000/SL8500 Security GuideAvl SubbaraoÎncă nu există evaluări
- Oracle Database 12c Product Family: Oracle White Paper June 2013Document21 paginiOracle Database 12c Product Family: Oracle White Paper June 2013mauroÎncă nu există evaluări
- Oracle Database Security OverviewDocument20 paginiOracle Database Security Overviewvipinsharma237440Încă nu există evaluări
- Starting up and shutting down Oracle database instancesDocument9 paginiStarting up and shutting down Oracle database instancesambica badanaÎncă nu există evaluări
- Ds Security Database Vault 11gr2 128162Document2 paginiDs Security Database Vault 11gr2 128162Vijay KumarÎncă nu există evaluări
- D86587GC10 378219 PTBDocument4 paginiD86587GC10 378219 PTBRicardo Kucharski ArnoudÎncă nu există evaluări
- Oracle Consulting & Advanced Customer Services Security PracticesDocument4 paginiOracle Consulting & Advanced Customer Services Security Practicessaracaro13Încă nu există evaluări
- Data Guard 11gDocument450 paginiData Guard 11gXuan Sinh PhamÎncă nu există evaluări
- Oracle Data Guard 11g Data Protection and Availability For Oracle DatabaseDocument22 paginiOracle Data Guard 11g Data Protection and Availability For Oracle DatabasesouksomdyÎncă nu există evaluări
- Operating System: COPE/Technical Test/Interview/Database Questions & AnswersDocument25 paginiOperating System: COPE/Technical Test/Interview/Database Questions & AnswersVasu DevanÎncă nu există evaluări
- 11g High AvailabilityDocument27 pagini11g High Availabilitydkr_mlrÎncă nu există evaluări
- Database Security PDFDocument10 paginiDatabase Security PDFshabuzmushfiqueÎncă nu există evaluări
- Dell Unity Storage With Oracle DatabasesDocument97 paginiDell Unity Storage With Oracle DatabasesMarck VergunstÎncă nu există evaluări
- The Role of Big Data and Predictive Analytics in RetailingDocument17 paginiThe Role of Big Data and Predictive Analytics in RetailingRiktesh SrivastavaÎncă nu există evaluări
- Code MSGDocument186 paginiCode MSGricardoweberÎncă nu există evaluări
- Assignment 3Document4 paginiAssignment 3Dark RebelÎncă nu există evaluări
- Computer Science - Paper 1 - Mock 1Document10 paginiComputer Science - Paper 1 - Mock 1uththaramala calderaÎncă nu există evaluări
- Oceanspace VTL3500Document2 paginiOceanspace VTL3500Utopia MediaÎncă nu există evaluări
- Research Paper On Content Management SystemDocument8 paginiResearch Paper On Content Management Systemgw2cgcd9100% (1)
- NestleDocument56 paginiNestleManoj Kumar BÎncă nu există evaluări
- 16261a0589 (Kota Saigoutham) PDFDocument52 pagini16261a0589 (Kota Saigoutham) PDFKota SaigouthamÎncă nu există evaluări
- Python code to create empty tuple and combine elementsDocument2 paginiPython code to create empty tuple and combine elementsJaskirat Thukral100% (1)
- Significant of Mathematics Laboratory Activities For Teaching and LearningDocument7 paginiSignificant of Mathematics Laboratory Activities For Teaching and LearningresearchparksÎncă nu există evaluări
- Response Codes: Origem Do Documento: Adabas 6 - Programming Reference Data (ADA - 510 - 131)Document14 paginiResponse Codes: Origem Do Documento: Adabas 6 - Programming Reference Data (ADA - 510 - 131)Jose RochaÎncă nu există evaluări
- Service Manual: SR130 SR200 SR150 SR220 SR175 SR250 SV185 SV250 SV300Document51 paginiService Manual: SR130 SR200 SR150 SR220 SR175 SR250 SV185 SV250 SV300Sergey67% (3)
- Obstacles To Embedding Geometallurgy Decision-Making Into Operations and How To Increase Maturity of This Critical CapabilityDocument2 paginiObstacles To Embedding Geometallurgy Decision-Making Into Operations and How To Increase Maturity of This Critical CapabilitysikujuaÎncă nu există evaluări
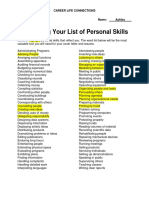
- Personal SkillsDocument1 paginăPersonal Skillsapi-371057922Încă nu există evaluări
- SR TagsDocument10 paginiSR TagsOzkhar FrEzeroÎncă nu există evaluări
- SQL DELETE and UPDATE LabDocument7 paginiSQL DELETE and UPDATE LabRheny BondocÎncă nu există evaluări
- L 02 Consumer ResearchDocument43 paginiL 02 Consumer ResearchANCHAL SINGHÎncă nu există evaluări
- IS34MW01G084/164 IS35MW01G084/164: 1Gb SLC-4b ECCDocument65 paginiIS34MW01G084/164 IS35MW01G084/164: 1Gb SLC-4b ECCdiegooliveiraEEÎncă nu există evaluări
- TreeView Control inDocument4 paginiTreeView Control inSaku RaÎncă nu există evaluări
- Data Types and Database ConceptsDocument111 paginiData Types and Database Conceptsshamanth br100% (1)
- 12 Dimensions Quality DataDocument2 pagini12 Dimensions Quality DatamtttusharÎncă nu există evaluări
- Unit 2: Data Collection and RepresentationDocument26 paginiUnit 2: Data Collection and RepresentationHeman SetiaÎncă nu există evaluări
- Ainley, J & Pratt, D (2001) Introducing A Special Issue On Constructing Meanings From Data Educational Studies in MathematicsDocument14 paginiAinley, J & Pratt, D (2001) Introducing A Special Issue On Constructing Meanings From Data Educational Studies in MathematicsRicardo NarváezÎncă nu există evaluări
- Chapter 7 HWK SolutionsDocument3 paginiChapter 7 HWK SolutionsDestiny Mae B. CarreonÎncă nu există evaluări
- Manage Disks Flexibly with LVMDocument10 paginiManage Disks Flexibly with LVMredelektraÎncă nu există evaluări
- SQL ExampleDocument11 paginiSQL ExampleAravind RadhakrishnanÎncă nu există evaluări
- Sip Research Proposal On TradingDocument8 paginiSip Research Proposal On TradingRovers ShetphalhadheÎncă nu există evaluări
- Optical Data Capture: Optical Mark Recognition (OMR)Document17 paginiOptical Data Capture: Optical Mark Recognition (OMR)Dinesh GodhaniÎncă nu există evaluări
- Circular - Extent ValidationDocument2 paginiCircular - Extent ValidationKiranmai NallapuÎncă nu există evaluări
- Defensive Cyber Mastery: Expert Strategies for Unbeatable Personal and Business SecurityDe la EverandDefensive Cyber Mastery: Expert Strategies for Unbeatable Personal and Business SecurityEvaluare: 5 din 5 stele5/5 (1)
- Dark Data: Why What You Don’t Know MattersDe la EverandDark Data: Why What You Don’t Know MattersEvaluare: 4.5 din 5 stele4.5/5 (3)
- CEH Certified Ethical Hacker Practice Exams, Third EditionDe la EverandCEH Certified Ethical Hacker Practice Exams, Third EditionÎncă nu există evaluări
- Hackers & Painters: Big Ideas from the Computer AgeDe la EverandHackers & Painters: Big Ideas from the Computer AgeEvaluare: 4.5 din 5 stele4.5/5 (5)
- IAPP CIPM Certified Information Privacy Manager Study GuideDe la EverandIAPP CIPM Certified Information Privacy Manager Study GuideÎncă nu există evaluări
- Blockchain Basics: A Non-Technical Introduction in 25 StepsDe la EverandBlockchain Basics: A Non-Technical Introduction in 25 StepsEvaluare: 4.5 din 5 stele4.5/5 (24)
- CISM Certified Information Security Manager Study GuideDe la EverandCISM Certified Information Security Manager Study GuideÎncă nu există evaluări
- Concise Oracle Database For People Who Has No TimeDe la EverandConcise Oracle Database For People Who Has No TimeÎncă nu există evaluări
- The Internet Con: How to Seize the Means of ComputationDe la EverandThe Internet Con: How to Seize the Means of ComputationEvaluare: 5 din 5 stele5/5 (6)
- Facing Cyber Threats Head On: Protecting Yourself and Your BusinessDe la EverandFacing Cyber Threats Head On: Protecting Yourself and Your BusinessEvaluare: 4.5 din 5 stele4.5/5 (27)
- Agile Metrics in Action: How to measure and improve team performanceDe la EverandAgile Metrics in Action: How to measure and improve team performanceÎncă nu există evaluări
- Monitored: Business and Surveillance in a Time of Big DataDe la EverandMonitored: Business and Surveillance in a Time of Big DataEvaluare: 4 din 5 stele4/5 (1)
- COBOL Basic Training Using VSAM, IMS and DB2De la EverandCOBOL Basic Training Using VSAM, IMS and DB2Evaluare: 5 din 5 stele5/5 (2)
- Microsoft Access Guide to Success: From Fundamentals to Mastery in Crafting Databases, Optimizing Tasks, & Making Unparalleled Impressions [III EDITION]De la EverandMicrosoft Access Guide to Success: From Fundamentals to Mastery in Crafting Databases, Optimizing Tasks, & Making Unparalleled Impressions [III EDITION]Evaluare: 5 din 5 stele5/5 (8)
- ITIL 4: Digital and IT strategy: Reference and study guideDe la EverandITIL 4: Digital and IT strategy: Reference and study guideEvaluare: 5 din 5 stele5/5 (1)
- GDPR-standard data protection staff training: What employees & associates need to know by Dr Paweł MielniczekDe la EverandGDPR-standard data protection staff training: What employees & associates need to know by Dr Paweł MielniczekÎncă nu există evaluări
- ITIL 4: Create, Deliver and Support: Reference and study guideDe la EverandITIL 4: Create, Deliver and Support: Reference and study guideÎncă nu există evaluări
- Darknet: Into the Deepest Mysteries of the InternetDe la EverandDarknet: Into the Deepest Mysteries of the InternetÎncă nu există evaluări
- Apple Card and Apple Pay: A Ridiculously Simple Guide to Mobile PaymentsDe la EverandApple Card and Apple Pay: A Ridiculously Simple Guide to Mobile PaymentsÎncă nu există evaluări
- Mastering PostgreSQL: A Comprehensive Guide for DevelopersDe la EverandMastering PostgreSQL: A Comprehensive Guide for DevelopersÎncă nu există evaluări
- OSCP Offensive Security Certified Professional Practice Tests With Answers To Pass the OSCP Ethical Hacking Certification ExamDe la EverandOSCP Offensive Security Certified Professional Practice Tests With Answers To Pass the OSCP Ethical Hacking Certification ExamÎncă nu există evaluări
- Business Intelligence Strategy and Big Data Analytics: A General Management PerspectiveDe la EverandBusiness Intelligence Strategy and Big Data Analytics: A General Management PerspectiveEvaluare: 5 din 5 stele5/5 (5)








































































































![Microsoft Access Guide to Success: From Fundamentals to Mastery in Crafting Databases, Optimizing Tasks, & Making Unparalleled Impressions [III EDITION]](https://imgv2-1-f.scribdassets.com/img/word_document/610686937/149x198/9ccfa6158e/1713743787?v=1)












