Documente Academic
Documente Profesional
Documente Cultură
Spread Spectrum
Încărcat de
aamirdalviDescriere originală:
Drepturi de autor
Formate disponibile
Partajați acest document
Partajați sau inserați document
Vi se pare util acest document?
Este necorespunzător acest conținut?
Raportați acest documentDrepturi de autor:
Formate disponibile
Spread Spectrum
Încărcat de
aamirdalviDrepturi de autor:
Formate disponibile
Spread Spectrum
Introduction to Spread Spectrum
Problems such as capacity limits, propagation
effects, synchronization occur with wireless
systems
Spread spectrum modulation spreads out the
modulated signal bandwidth so it is much
greater than the message bandwidth
Independent code spreads signal at transmitter
and despreads signal at receiver
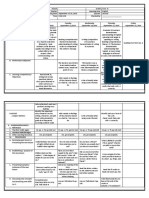
Multiplexing in 4 dimensions
space (s
i
)
time (t)
frequency (f)
code (c)
Goal: multiple use
of a shared medium
Important: guard spaces needed!
s
2
s
3
s
1
Multiplexing
f
t
c
k
2
k
3
k
4
k
5
k
6
k
1
f
t
c
f
t
c
channels k
i
Separation of spectrum into smaller frequency bands
Channel gets band of the spectrum for the whole time
Advantages:
no dynamic coordination needed
works also for analog signals
Disadvantages:
waste of bandwidth
if traffic distributed unevenly
inflexible
guard spaces
Frequency multiplex
k
3
k
4
k
5
k
6
f
t
c
f
t
c
k
2
k
3
k
4
k
5
k
6
k
1
Time multiplex
Channel gets the whole spectrum for a certain
amount of time
Advantages:
only one carrier in the
medium at any time
throughput high even
for many users
Disadvantages:
precise
synchronization
necessary
f
Time and frequency multiplex
A channel gets a certain frequency band for a
certain amount of time (e.g. GSM)
Advantages:
better protection against tapping
protection against frequency
selective interference
higher data rates compared to
code multiplex
Precise coordination
required
t
c
k
2
k
3
k
4
k
5
k
6
k
1
Code multiplex
Each channel has unique code
All channels use same spectrum at same time
Advantages:
bandwidth efficient
no coordination and synchronization
good protection against interference
Disadvantages:
lower user data rates
more complex signal regeneration
Implemented using spread spectrum technology
k
2
k
3
k
4
k
5
k
6
k
1
f
t
c
Spread Spectrum Technology
Problem of radio transmission: frequency dependent
fading can wipe out narrow band signals for duration
of the interference
Solution: spread the narrow band signal into a broad
band signal using a special code
detection at
receiver
interference
spread
signal
signal
spread
interference
f
f
power
power
Spread Spectrum Technology
Side effects:
coexistence of several signals without dynamic
coordination
tap-proof
Alternatives: Direct Sequence (DS/SS), Frequency
Hopping (FH/SS)
Spread spectrum increases BW of message signal
by a factor N, Processing Gain
10
Processing Gain 10log
ss ss
B B
N
B B
| |
= =
|
\ .
Effects of spreading and
interference
P
f
i)
P
f
ii)
sender
P
f
iii)
P
f
iv)
receiver
f
v)
user signal
broadband interference
narrowband interference
P
Spreading and frequency
selective fading
frequency
channel
quality
1
2
3
4
5 6
Narrowband
signal
guard space
2
2
2
2
2
frequency
channel
quality
1
spread
spectrum
narrowband
channels
spread spectrum
channels
DSSS (Direct Sequence Spread Spectrum) I
XOR the signal with pseudonoise (PN) sequence (chipping
sequence)
Advantages
reduces frequency selective
fading
in cellular networks
base stations can use the
same frequency range
several base stations can
detect and recover the signal
But, needs precise power control
user data
chipping
sequence
resulting
signal
0 1
0 1 1 0 1 0 1 0 1 0 0 1 1 1
XOR
0 1 1 0 0 1 0 1 1 0 1 0 0 1
=
T
b
T
c
user data
m(t)
chipping
sequence, c(t)
X
DSSS (Direct Sequence Spread Spectrum) II
modulator
radio
carrier
Spread spectrum
Signal y(t)=m(t)c(t)
transmit
signal
transmitter
demodulator
received
signal
radio
carrier
X
Chipping sequence,
c(t)
receiver
integrator
products
decision
data
sampled
sums
correlator
DS/SS Comments III
Pseudonoise(PN) sequence chosen so
that its autocorrelation is very narrow =>
PSD is very wide
Concentrated around t < T
c
Cross-correlation between two users codes is
very small
DS/SS Comments IV
Secure and Jamming Resistant
Both receiver and transmitter must know c(t)
Since PSD is low, hard to tell if signal present
Since wide response, tough to jam everything
Multiple access
If c
i
(t) is orthogonal to c
j
(t), then users do not interfere
Near/Far problem
Users must be received with the same power
FH/SS (Frequency Hopping
Spread Spectrum) I
Discrete changes of carrier frequency
sequence of frequency changes determined via PN sequence
Two versions
Fast Hopping: several frequencies per user bit (FFH)
Slow Hopping: several user bits per frequency (SFH)
Advantages
frequency selective fading and interference limited to short period
uses only small portion of spectrum at any time
Disadvantages
not as robust as DS/SS
simpler to detect
FHSS (Frequency Hopping
Spread Spectrum) II
user data
slow
hopping
(3 bits/hop)
fast
hopping
(3 hops/bit)
0 1
T
b
0 1 1 t
f
f
1
f
2
f
3
t
T
d
f
f
1
f
2
f
3
t
T
d
T
b
: bit period T
d
: dwell time
FHSS (Frequency Hopping Spread Spectrum) III
modulator
user data
hopping
sequence
modulator
narrowband
signal
Spread transmit
signal
transmitter
received
signal
receiver
demodulator
data
frequency
synthesizer
hopping
sequence
demodulator
frequency
synthesizer
Applications of Spread
Spectrum
Cell phones
IS-95 (DS/SS)
GSM
Global Positioning System (GPS)
Wireless LANs
802.11b
Performance of DS/SS Systems
Pseudonoise (PN) codes
Spread signal at the transmitter
Despread signal at the receiver
Ideal PN sequences should be
Orthogonal (no interference)
Random (security)
Autocorrelation similar to white noise (high at
t=0 and low for t not equal 0)
PN Sequence Generation
Codes are periodic and generated by a shift register and
XOR
Maximum-length (ML) shift register sequences, m-stage
shift register, length: n = 2
m
1 bits
R(t)
-1/n
T
c
t >
-nT
c
nT
c
+
Output
Generating PN Sequences
Take m=2 =>L=3
c
n
=[1,1,0,1,1,0, . . .],
usually written as
bipolar c
n
=[1,1,-1,1,1,-1,
. . .]
m Stages connected
to modulo-2 adder
2 1,2
3 1,3
4 1,4
5 1,4
6 1,6
8 1,5,6,7
+
Output
( )
s s
=
=
=
=
+
1 1 / 1
0 1
1
1
L m L
m
c c
L
m R
L
n
m n n c
Problems with m-sequences
Cross-correlations with other m-
sequences generated by different input
sequences can be quite high
Easy to guess connection setup in 2m
samples so not too secure
In practice, Gold codes or Kasami
sequences which combine the output of
m-sequences are used.
Detecting DS/SS PSK Signals
X
Bipolar, NRZ
m(t)
PN
sequence, c(t)
X
sqrt(2)cos (e
c
t + u)
Spread spectrum
Signal y(t)=m(t)c(t)
transmit
signal
transmitter
X
received
signal
X
c(t)
receiver
integrator
z(t)
decision
data
sqrt(2)cos (e
c
t + u)
LPF
w(t)
x(t)
Optimum Detection of DS/SS PSK
Recall, bipolar signaling (PSK) and white noise
give the optimum error probability
Not effected by spreading
Wideband noise not affected by spreading
Narrowband noise reduced by spreading
2
b
b
E
P Q
| |
=
|
|
\ .
Signal Spectra
Effective noise power is channel noise
power plus jamming (NB) signal power
divided by N
10
Processing Gain 10log
ss ss b
c
B B T
N
B B T
| |
= = =
|
\ .
T
b
T
c
Multiple Access Performance
Assume K users in the same frequency
band,
Interested in user 1, other users interfere
4
1
3
5
2
6
Signal Model
Interested in signal 1, but we also get
signals from other K-1 users:
At receiver,
( ) ( ) ( ) ( ) ( )
( ) ( ) ( )
2 cos
2 cos
k k k k k c k k
k k k k c k k k c k
x t m t c t t
m t c t t
t t e t u
t t e | | u e t
= +
= + =
( ) ( ) ( )
1
2
K
k
k
x t x t x t
=
= +
Interfering Signal
After mixing and despreading (assume t
1
=0)
After LPF
After the integrator-sampler
( ) ( ) ( ) ( ) ( ) ( )
1 1
2 cos cos
k k k k k c k c
z t m t c t c t t t t t e | e u = + +
( ) ( ) ( ) ( ) ( )
1 1
cos
k k k k k k
w t m t c t c t t t | u =
( ) ( ) ( ) ( )
1 1
0
cos
b
T
k k k k k k
I m t c t c t dt | u t t =
}
At Receiver
m(t) =+/-1 (PSK), bit duration Tb
Interfering signal may change amplitude at tk
At User 1:
Ideally, spreading codes are Orthogonal:
( ) ( ) ( ) ( ) ( )
1 1 1 0 1
0
cos
k b
k
T
k k k k k k
I b c t c t dt b c t c t dt
t
t
| u t t
(
= +
(
} }
( ) ( ) ( )
1 1 1 1
0
b
T
I m t c t c t dt =
}
( ) ( ) ( ) ( )
1 1 1
0 0
0
b b
T T
k k
c t c t dt A c t c t dt t = =
} }
Multiple Access Interference (MAI)
If the users are assumed to be equal power interferers,
can be analyzed using the central limit theorem (sum of
IID RVs)
( )
1
1 3 2
b
b
P Q
K N E
(
(
=
(
+
Example of Performance
Degradation
N=8 N=32
Near/Far Problem (I)
Performance estimates derived using assumption that all
users have same power level
Reverse link (mobile to base) makes this unrealistic
since mobiles are moving
Adjust power levels constantly to keep equal
1
k
Near/Far Problem (II)
K interferers, one strong interfering signal
dominates performance
Can result in capacity losses of 10-30%
( )
1
( ) (1) (1)
2
1
3 2
b
K
k
b b b
k
P Q
E E N E
=
(
(
=
(
(
+
Multipath Propagation
RAKE Receiver
Received signal sampled at the rate 1/Ts> 2/Tc for detection and
synchronization
Fed to all M RAKE fingers. Interpolation/decimation unit provides a
data stream on chiprate 1/Tc
Correlation with the complex conjugate of the spreading sequence
and weighted (maximum-ratio criterion)summation over one symbol
RAKE Receiver
RAKE Receiver has to estimate:
Multipath delays
Phase of multipath components
Amplitude of multipath components
Number of multipath components
Main challenge is receiver synchronization in
fading channels
S-ar putea să vă placă și
- Shoe Dog: A Memoir by the Creator of NikeDe la EverandShoe Dog: A Memoir by the Creator of NikeEvaluare: 4.5 din 5 stele4.5/5 (537)
- Chapter 01 - Probability Distribution - ProbabilityDocument3 paginiChapter 01 - Probability Distribution - ProbabilityaamirdalviÎncă nu există evaluări
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeDe la EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeEvaluare: 4 din 5 stele4/5 (5794)
- EC136 Walmart - Jemmy PadillaDocument6 paginiEC136 Walmart - Jemmy PadillaaamirdalviÎncă nu există evaluări
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceDe la EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceEvaluare: 4 din 5 stele4/5 (895)
- Referneces WCMDocument2 paginiReferneces WCMaamirdalviÎncă nu există evaluări
- The Yellow House: A Memoir (2019 National Book Award Winner)De la EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Evaluare: 4 din 5 stele4/5 (98)
- Mutala-e-Quran Karim Ka Muntakhab Nissab Part 1Document517 paginiMutala-e-Quran Karim Ka Muntakhab Nissab Part 1aamirdalviÎncă nu există evaluări
- Grit: The Power of Passion and PerseveranceDe la EverandGrit: The Power of Passion and PerseveranceEvaluare: 4 din 5 stele4/5 (588)
- Consumer Buying Process & Organizational Buying BehaviorDocument48 paginiConsumer Buying Process & Organizational Buying BehavioraamirdalviÎncă nu există evaluări
- The Little Book of Hygge: Danish Secrets to Happy LivingDe la EverandThe Little Book of Hygge: Danish Secrets to Happy LivingEvaluare: 3.5 din 5 stele3.5/5 (400)
- Effective Personal SellingDocument18 paginiEffective Personal SellingaamirdalviÎncă nu există evaluări
- The Emperor of All Maladies: A Biography of CancerDe la EverandThe Emperor of All Maladies: A Biography of CancerEvaluare: 4.5 din 5 stele4.5/5 (271)
- Introduction To Public Relations - ApunteakDocument15 paginiIntroduction To Public Relations - ApunteakTeresa Perez de Lucia BurgosÎncă nu există evaluări
- Never Split the Difference: Negotiating As If Your Life Depended On ItDe la EverandNever Split the Difference: Negotiating As If Your Life Depended On ItEvaluare: 4.5 din 5 stele4.5/5 (838)
- Using Sender Verification For Identifying Spoof Mail SPF, DKIM, DMARC, Exchange and Exchange Online Part 8#9Document28 paginiUsing Sender Verification For Identifying Spoof Mail SPF, DKIM, DMARC, Exchange and Exchange Online Part 8#9Eyal DoronÎncă nu există evaluări
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyDe la EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyEvaluare: 3.5 din 5 stele3.5/5 (2259)
- Business Plan Proposal IN Applied EconomicsDocument3 paginiBusiness Plan Proposal IN Applied EconomicsTsunayoshi SawadaÎncă nu există evaluări
- On Fire: The (Burning) Case for a Green New DealDe la EverandOn Fire: The (Burning) Case for a Green New DealEvaluare: 4 din 5 stele4/5 (74)
- Immaculata Lesson Plan Alyssa Brooks Subject: Writing - Expressive Writing Grade: Second I. ObjectivesDocument2 paginiImmaculata Lesson Plan Alyssa Brooks Subject: Writing - Expressive Writing Grade: Second I. Objectivesapi-272548014Încă nu există evaluări
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureDe la EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureEvaluare: 4.5 din 5 stele4.5/5 (474)
- BanegasetalManuscriptCSE (Revision) PDFDocument25 paginiBanegasetalManuscriptCSE (Revision) PDFDarío Luis BanegasÎncă nu există evaluări
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryDe la EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryEvaluare: 3.5 din 5 stele3.5/5 (231)
- Students' Attitude of Collaborative Learning and Satisfaction Towards On Online Study RoomDocument5 paginiStudents' Attitude of Collaborative Learning and Satisfaction Towards On Online Study RoomChristopher RegidorÎncă nu există evaluări
- Team of Rivals: The Political Genius of Abraham LincolnDe la EverandTeam of Rivals: The Political Genius of Abraham LincolnEvaluare: 4.5 din 5 stele4.5/5 (234)
- Ielts Mock Test 2021 June Writing Practice Test 1 394632Document8 paginiIelts Mock Test 2021 June Writing Practice Test 1 394632sreya hossainÎncă nu există evaluări
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaDe la EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaEvaluare: 4.5 din 5 stele4.5/5 (266)
- Chapter 11 - HRM784 - Communicating Change - Compatibility ModeDocument19 paginiChapter 11 - HRM784 - Communicating Change - Compatibility ModeNooria YaqubÎncă nu există evaluări
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersDe la EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersEvaluare: 4.5 din 5 stele4.5/5 (345)
- Power and PragmaticsDocument6 paginiPower and PragmaticsAlexandra Mironescu100% (2)
- Hs Lesson PlanDocument2 paginiHs Lesson Planapi-374880895Încă nu există evaluări
- The Unwinding: An Inner History of the New AmericaDe la EverandThe Unwinding: An Inner History of the New AmericaEvaluare: 4 din 5 stele4/5 (45)
- Mobile Softphone StepByStep PDFDocument68 paginiMobile Softphone StepByStep PDFMIQUEL FRONTERAÎncă nu există evaluări
- IMO Resolution A.954 (23) Proper Use of VHFDocument7 paginiIMO Resolution A.954 (23) Proper Use of VHFmiticaffÎncă nu există evaluări
- Monday September 12,2016 Tuesday September 13,2016 Wednesday September 14,2016 Thursday September 15, 2016 Friday September 16, 2016Document4 paginiMonday September 12,2016 Tuesday September 13,2016 Wednesday September 14,2016 Thursday September 15, 2016 Friday September 16, 2016Florecita CabañogÎncă nu există evaluări
- Media and Information LiteracyDocument195 paginiMedia and Information LiteracyCasey Dee Dalan AranasÎncă nu există evaluări
- DLL EntreDocument3 paginiDLL EntreRodolfo Pomida100% (2)
- Cucmconfig InterfaceDocument6 paginiCucmconfig InterfaceRa YuthÎncă nu există evaluări
- Socialbakers Analytics User GuideDocument84 paginiSocialbakers Analytics User GuideThe dudeÎncă nu există evaluări
- Robert The Rose Horse Lesson 1Document2 paginiRobert The Rose Horse Lesson 1api-5090379920% (1)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreDe la EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreEvaluare: 4 din 5 stele4/5 (1090)
- Differences Between Addie Model and Assure ModelDocument3 paginiDifferences Between Addie Model and Assure ModelRaafah Azkia AR86% (7)
- English To Urdu Dictionary - Complete List of English Words With Meaning Starting With - A - PDFDocument2 paginiEnglish To Urdu Dictionary - Complete List of English Words With Meaning Starting With - A - PDFKhudadad MalikÎncă nu există evaluări
- Lesson Plan - ScratchDocument6 paginiLesson Plan - Scratchapi-664477615Încă nu există evaluări
- Linguistics, Volume 42, Supplement 1, 2010, pp.147-157Document17 paginiLinguistics, Volume 42, Supplement 1, 2010, pp.147-157Mahfoodh AljubouryÎncă nu există evaluări
- IITH Thesis Template v2Document16 paginiIITH Thesis Template v2Sreenivasa Reddy Paidala50% (2)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)De la EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Evaluare: 4.5 din 5 stele4.5/5 (121)
- Programmed # B.Ed. (1.5) Course Name: Educational Technology Course Code: 8619 Submitted By: Saba Mushtaq Roll # CA629922Document16 paginiProgrammed # B.Ed. (1.5) Course Name: Educational Technology Course Code: 8619 Submitted By: Saba Mushtaq Roll # CA629922Malik XufyanÎncă nu există evaluări
- HCNA-HNTD V2.1 Intermediate Training MaterialsDocument362 paginiHCNA-HNTD V2.1 Intermediate Training MaterialsAyas H. Abd100% (2)
- Bryan Ye, Year 9 IPT, MR Simmonds, 2011 Communications Assessment TaskDocument28 paginiBryan Ye, Year 9 IPT, MR Simmonds, 2011 Communications Assessment TaskKevin ShenÎncă nu există evaluări
- RoamingDocument2 paginiRoamingIppolito GregoÎncă nu există evaluări
- Learning To Learn (Dummy Notes)Document2 paginiLearning To Learn (Dummy Notes)Goutham SunderÎncă nu există evaluări
- 국제 통용 한국어 표준 교육과정 - 영어 요약본Document6 pagini국제 통용 한국어 표준 교육과정 - 영어 요약본Julie AnneÎncă nu există evaluări
- Library Orientation Quiz SLOSDocument3 paginiLibrary Orientation Quiz SLOScarrrÎncă nu există evaluări
- Her Body and Other Parties: StoriesDe la EverandHer Body and Other Parties: StoriesEvaluare: 4 din 5 stele4/5 (821)