Documente Academic
Documente Profesional
Documente Cultură
Lecture-2-Different Types of Devices Used To Create A Computer Network
Încărcat de
RicHArd0 evaluări0% au considerat acest document util (0 voturi)
18 vizualizări19 pagininetworking 2
Titlu original
lecture-2-Different types of devices used to create a computer network
Drepturi de autor
© © All Rights Reserved
Formate disponibile
PPTX, PDF, TXT sau citiți online pe Scribd
Partajați acest document
Partajați sau inserați document
Vi se pare util acest document?
Este necorespunzător acest conținut?
Raportați acest documentnetworking 2
Drepturi de autor:
© All Rights Reserved
Formate disponibile
Descărcați ca PPTX, PDF, TXT sau citiți online pe Scribd
0 evaluări0% au considerat acest document util (0 voturi)
18 vizualizări19 paginiLecture-2-Different Types of Devices Used To Create A Computer Network
Încărcat de
RicHArdnetworking 2
Drepturi de autor:
© All Rights Reserved
Formate disponibile
Descărcați ca PPTX, PDF, TXT sau citiți online pe Scribd
Sunteți pe pagina 1din 19
Different types of
devices used to create a
computer network
Client is the term used to mention a workstation, a normal
desktop computer, or a laptop which an end user uses to
perform his normal duties in the office. The term client
computer is used to refer any device which participate in the
Client network.
Workstation is the term used for a high-end type computer
which has much more memory and processing power than a
Workstation normal desktop computer. Workstation computers are used
Computer for computing tasks which require more memory and
processing power than normal computing. Examples are
video rendering, 2D CAD drafting, 3D CAD drafting, heavy
image editing etc.
A server is a high configuration special computer, which
serves resources to clients. A typical computer network uses
different types of servers. Examples of servers used in a
network are file server, print server, database server, mail
Server
server, web server, DNS server, DHCP server, video streaming
server etc. Servers normally run continuously 24/7. An
unexpected shutdown of a server may cause entire operation
of the business down.
Network media is used to connect different devices in a
network together. Commonly used network media in wired
Network
networks are copper twisted pair cables. Optical fiber cables
Media
are also used to connect different devices in wired networks.
Wireless networks use electromagnetic waves to connect
different devices together.
Network
media (cable)
A hub (Ethernet hub) is a network connectivity device used to
connect clients during the early days of computer networking. A
network hub receives traffic from a device in the port where the
device is connected. Ethernet hub then forwards the received
traffic out to all its other ports. As a result, all the clients in the
Network Hub
network receive the traffic which is a burden to other clients
which are not the intended recipient. This nature of operation of
Ethernet hubs can cause large amount of unnecessary traffic in
the network. Hubs are out from the computer networking
industry and not even available in the market to purchase.
Network hub
A layer 2 switch is another type of connectivity device widely used
these days. Layer 2 switches operate at
Layer 2 of OSI reference model. A network switch has the capability
to learn which devices are connected to its ports. Switches learn
Network about connected devices by using a unique device address called as
Switch Media Access Control (MAC) address or Layer 2 address. Using
Media Access Control (MAC) address or Layer 2 addresses, a Layer 2
switch can forward the packet only to the intended recipient, not to
every device in the network. A network switch is commonly used to
connect the devices inside a OSI Layer 3 network segment.
Network
switch
Access Points (AP) are used in wireless networks. Access
Points (AP) are used to connect wirelessly connected devices
Access Points
to wired network. Typically Access Points (AP) is a separate
device, but it can be a function of router also.
Access Points
A router is another type of network connectivity device.
Routers operate at Layer 3 of OSI reference model. A router is
used to forward and receive traffic between different Layer 3
network segments. Routers depend on
Router IP addresses (also called as Layer 3 address) to forward traffic
from one network to another network. That means, switches
are used to connect devices inside a Layer 3 network segment
but routers are used to connect different Layer 3 network
segments together.
Cisco Router
A firewall is a network security device which is used to prevent
unauthorized traffic. Firewall can inspect, control, police and if
required block network traffic. Firewall can be a software, a
Firewall
hardware device or a software running on a special hardware
device. Typically, firewalls are used to prevent unauthorized
access to private networks from the users of internet.
Firewall
An intrusion prevention system (IPS) another network
security device which is used to detect and prevent network
threats. Intrusion prevention systems (IPS) can be connected
Intrusion
inline within your network and it can continuously monitor
Prevention
your network for any network threats. These devices can
Systems (IPS)
identify traffic patterns of different network threats. Intrusion
Prevention Systems (IPS) can report any threat to the
network administrator or it can proactively shut the line, if a
threat is identified.
Intrusion
Prevention
Systems (IPS)
S-ar putea să vă placă și
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeDe la EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeEvaluare: 4 din 5 stele4/5 (5794)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreDe la EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreEvaluare: 4 din 5 stele4/5 (1090)
- Never Split the Difference: Negotiating As If Your Life Depended On ItDe la EverandNever Split the Difference: Negotiating As If Your Life Depended On ItEvaluare: 4.5 din 5 stele4.5/5 (838)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceDe la EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceEvaluare: 4 din 5 stele4/5 (895)
- Grit: The Power of Passion and PerseveranceDe la EverandGrit: The Power of Passion and PerseveranceEvaluare: 4 din 5 stele4/5 (588)
- Shoe Dog: A Memoir by the Creator of NikeDe la EverandShoe Dog: A Memoir by the Creator of NikeEvaluare: 4.5 din 5 stele4.5/5 (537)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersDe la EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersEvaluare: 4.5 din 5 stele4.5/5 (345)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureDe la EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureEvaluare: 4.5 din 5 stele4.5/5 (474)
- Her Body and Other Parties: StoriesDe la EverandHer Body and Other Parties: StoriesEvaluare: 4 din 5 stele4/5 (821)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)De la EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Evaluare: 4.5 din 5 stele4.5/5 (121)
- The Emperor of All Maladies: A Biography of CancerDe la EverandThe Emperor of All Maladies: A Biography of CancerEvaluare: 4.5 din 5 stele4.5/5 (271)
- The Little Book of Hygge: Danish Secrets to Happy LivingDe la EverandThe Little Book of Hygge: Danish Secrets to Happy LivingEvaluare: 3.5 din 5 stele3.5/5 (400)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyDe la EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyEvaluare: 3.5 din 5 stele3.5/5 (2259)
- Dahua HTTP API v2.63Document301 paginiDahua HTTP API v2.63Wizzbit gxs100% (1)
- The Yellow House: A Memoir (2019 National Book Award Winner)De la EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Evaluare: 4 din 5 stele4/5 (98)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaDe la EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaEvaluare: 4.5 din 5 stele4.5/5 (266)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryDe la EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryEvaluare: 3.5 din 5 stele3.5/5 (231)
- Team of Rivals: The Political Genius of Abraham LincolnDe la EverandTeam of Rivals: The Political Genius of Abraham LincolnEvaluare: 4.5 din 5 stele4.5/5 (234)
- On Fire: The (Burning) Case for a Green New DealDe la EverandOn Fire: The (Burning) Case for a Green New DealEvaluare: 4 din 5 stele4/5 (74)
- The Unwinding: An Inner History of the New AmericaDe la EverandThe Unwinding: An Inner History of the New AmericaEvaluare: 4 din 5 stele4/5 (45)
- Grade 9 Ict Q1 W56Document8 paginiGrade 9 Ict Q1 W56RicHArdÎncă nu există evaluări
- Grade 10 Ict Q4 W78Document7 paginiGrade 10 Ict Q4 W78RicHArdÎncă nu există evaluări
- Grade 10 Ict Q4 W56Document6 paginiGrade 10 Ict Q4 W56RicHArdÎncă nu există evaluări
- Information Produced by The DBMS Are Classified Into Thre1Document9 paginiInformation Produced by The DBMS Are Classified Into Thre1RicHArdÎncă nu există evaluări
- Coding Systems For Text-Based Data: Ascii and EbcdicDocument3 paginiCoding Systems For Text-Based Data: Ascii and EbcdicRicHArdÎncă nu există evaluări
- Creating SolutionDocument26 paginiCreating SolutionRicHArdÎncă nu există evaluări
- LECTURE - ICT As Platform For Change - Empowerment TechnologiesDocument8 paginiLECTURE - ICT As Platform For Change - Empowerment TechnologiesRicHArdÎncă nu există evaluări
- CC 104 - C+ + OperatorsDocument13 paginiCC 104 - C+ + OperatorsRicHArdÎncă nu există evaluări
- Computer 10-Software DevelopmentDocument18 paginiComputer 10-Software DevelopmentRicHArdÎncă nu există evaluări
- CC 104 Lesson5Document10 paginiCC 104 Lesson5RicHArdÎncă nu există evaluări
- LP in Health AppraisalDocument1 paginăLP in Health AppraisalRicHArdÎncă nu există evaluări
- Uses For Computer Networks: What Is A Network?Document3 paginiUses For Computer Networks: What Is A Network?RicHArdÎncă nu există evaluări
- Basic Principles of Graphics and Layout: LessonDocument3 paginiBasic Principles of Graphics and Layout: LessonRicHArdÎncă nu există evaluări
- Understanding Urls and Ip Addresses: Web Browsing ComponentsDocument3 paginiUnderstanding Urls and Ip Addresses: Web Browsing ComponentsRicHArdÎncă nu există evaluări
- Types of Operating SystemsDocument39 paginiTypes of Operating SystemsRicHArdÎncă nu există evaluări
- PT Lesson l8Document7 paginiPT Lesson l8RicHArdÎncă nu există evaluări
- Understandi NG CpusDocument44 paginiUnderstandi NG CpusRicHArdÎncă nu există evaluări
- Ensure Healthy Lives and Promote Well-Being For All at All AgesDocument1 paginăEnsure Healthy Lives and Promote Well-Being For All at All AgesRicHArdÎncă nu există evaluări
- What Is A System Administr Ator?Document45 paginiWhat Is A System Administr Ator?RicHArdÎncă nu există evaluări
- Oop C#Document18 paginiOop C#RicHArdÎncă nu există evaluări
- A Vulnerable Program: Format Specifiers Format Specifier Specifier CharacterDocument4 paginiA Vulnerable Program: Format Specifiers Format Specifier Specifier CharacterRicHArdÎncă nu există evaluări
- Introductio NTO Computers AND Programmin GDocument20 paginiIntroductio NTO Computers AND Programmin GRicHArdÎncă nu există evaluări
- Internet, Intranet and ExtranetDocument9 paginiInternet, Intranet and ExtranetRicHArdÎncă nu există evaluări
- Ms-101-Introduction To Venn DiagramsDocument24 paginiMs-101-Introduction To Venn DiagramsRicHArdÎncă nu există evaluări
- Ms-101-Introduction To Size of Sets and Power SetsDocument29 paginiMs-101-Introduction To Size of Sets and Power SetsRicHArdÎncă nu există evaluări
- Ms-101-Introduction To Set EqualityDocument27 paginiMs-101-Introduction To Set EqualityRicHArdÎncă nu există evaluări
- SA Lesson102Document16 paginiSA Lesson102RicHArdÎncă nu există evaluări
- Lecture-3-Client and ServerDocument14 paginiLecture-3-Client and ServerRicHArdÎncă nu există evaluări
- Operating Systems: - Chapter 1Document6 paginiOperating Systems: - Chapter 1Hazem MohamedÎncă nu există evaluări
- The Generative Pre-Trained Transformer: GPT-3Document1 paginăThe Generative Pre-Trained Transformer: GPT-3xiaokunzhengÎncă nu există evaluări
- 0-Manual Testing UpdatedDocument40 pagini0-Manual Testing UpdatedDinesh Kumar ReddyÎncă nu există evaluări
- QR Code RRL (International)Document4 paginiQR Code RRL (International)Jamie Faith AlingigÎncă nu există evaluări
- PeckShield Audit BentoBox v1.0Document29 paginiPeckShield Audit BentoBox v1.0NameÎncă nu există evaluări
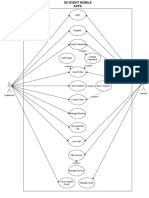
- GoEvent - UML Diagram UpdateDocument6 paginiGoEvent - UML Diagram UpdateJames Nicholas SuharjonoÎncă nu există evaluări
- Variable Speed Drives: Motors - Automation - Energy - Transmission & Distribution - CoatingsDocument28 paginiVariable Speed Drives: Motors - Automation - Energy - Transmission & Distribution - Coatingsesee57Încă nu există evaluări
- Pertemuan 6 - Tabview Part 2Document13 paginiPertemuan 6 - Tabview Part 251rojÎncă nu există evaluări
- PIC16F62X: FLASH-Based 8-Bit CMOS MicrocontrollersDocument114 paginiPIC16F62X: FLASH-Based 8-Bit CMOS MicrocontrollersJames HamiltonÎncă nu există evaluări
- Doing Bayesian Data Analysis With JASP: Darrell A. WorthyDocument76 paginiDoing Bayesian Data Analysis With JASP: Darrell A. WorthyHakan KarşılarÎncă nu există evaluări
- Using EHLLAPI in C# - CodeProjectDocument6 paginiUsing EHLLAPI in C# - CodeProjectAngel SaezÎncă nu există evaluări
- RP Prism Adyen 1 14 7Document34 paginiRP Prism Adyen 1 14 7danil.pereiraa223Încă nu există evaluări
- SEN2022 - Chapter 1Document15 paginiSEN2022 - Chapter 1ramaÎncă nu există evaluări
- Information Security: Submitted To: Submitted byDocument27 paginiInformation Security: Submitted To: Submitted byAaaÎncă nu există evaluări
- WWW Google Com Amp S Stotranidhi Com Sri Surya Namaskara ManDocument4 paginiWWW Google Com Amp S Stotranidhi Com Sri Surya Namaskara Mankrishna bhargavÎncă nu există evaluări
- Athenanet Technical Requirements: Spring 2022 Release EditionDocument8 paginiAthenanet Technical Requirements: Spring 2022 Release EditionCnu RÎncă nu există evaluări
- DIVAR IP 6000 R2 Technical Service Note enUS 22866053259Document4 paginiDIVAR IP 6000 R2 Technical Service Note enUS 22866053259Vương NhânÎncă nu există evaluări
- Stock Transport Order (STO) Process in SAPDocument27 paginiStock Transport Order (STO) Process in SAPPrateek Mohapatra100% (1)
- IT324 Database AdministrationDocument2 paginiIT324 Database Administrationاحمد قايدÎncă nu există evaluări
- Short Notes On Signals & Systems by Sujal SirDocument282 paginiShort Notes On Signals & Systems by Sujal SirHarshit SharmaÎncă nu există evaluări
- Intro. To Malware Analysis - 20313Document22 paginiIntro. To Malware Analysis - 20313Hamza ArifÎncă nu există evaluări
- A Beginner's Guide To Large Language Mo-Ebook-Part1Document25 paginiA Beginner's Guide To Large Language Mo-Ebook-Part1John O'MearaÎncă nu există evaluări
- GES 501 - Instrument Calibration Ver 4Document31 paginiGES 501 - Instrument Calibration Ver 4muhammad nomanÎncă nu există evaluări
- Inter and Intra Substation Communications: Requirements and SolutionsDocument8 paginiInter and Intra Substation Communications: Requirements and SolutionsEbrahim ArzaniÎncă nu există evaluări
- Online Medicine Order SystemDocument58 paginiOnline Medicine Order SystemHarpreet SinghÎncă nu există evaluări
- Chapter 1 IntroductionDocument40 paginiChapter 1 IntroductionHeng PhinÎncă nu există evaluări
- RSA Authentication Manager 8.5 Patch 1 ReadmeDocument9 paginiRSA Authentication Manager 8.5 Patch 1 ReadmeELias ELÎncă nu există evaluări
- Tle Ict: Quarter 4 - Module 6: Electronic SpreadsheetDocument17 paginiTle Ict: Quarter 4 - Module 6: Electronic SpreadsheetCilena DomenicinaÎncă nu există evaluări
- Information Hiding in Text Steganography A Different Approach-2019Document4 paginiInformation Hiding in Text Steganography A Different Approach-2019rawansalwan nÎncă nu există evaluări