DocumentAndysah Putera Utama Siahaan - Rabin-Karp Elaboration in Comparing Pattern Based on Hash Dataîncărcat de
DocumentAndysah Putera Utama Siahaan - Rabin-Karp Elaboration in Comparing Pattern Based on Hash Dataîncărcat de Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentComposite Performance Index for Student Admissionîncărcat de
DocumentComposite Performance Index for Student Admissionîncărcat de Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentSolly Aryza - Novelty Stability Of Electrical System Single Machine Based Runge Kutta Orde 4 Method.pdfîncărcat de
DocumentSolly Aryza - Novelty Stability Of Electrical System Single Machine Based Runge Kutta Orde 4 Method.pdfîncărcat de Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentMesran - Implementation of Complex Proportional Assessment Method in the Selection of Mango Seeds.pdfîncărcat de
DocumentMesran - Implementation of Complex Proportional Assessment Method in the Selection of Mango Seeds.pdfîncărcat de Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentMasdin Saragih - Violations of Cybercrime and the Strength of Jurisdiction in Indonesia.pdfîncărcat de
DocumentMasdin Saragih - Violations of Cybercrime and the Strength of Jurisdiction in Indonesia.pdfîncărcat de Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentExpert System of Catfish Disease Determinant Using Certainty Factor Methodîncărcat de
DocumentExpert System of Catfish Disease Determinant Using Certainty Factor Methodîncărcat de Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentFuzzification of College Adviser Proficiency Based on Specific Knowledgeîncărcat de
DocumentFuzzification of College Adviser Proficiency Based on Specific Knowledgeîncărcat de Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentWLAN Penetration Examination of the University of Pembangunan Panca Budiîncărcat de
DocumentWLAN Penetration Examination of the University of Pembangunan Panca Budiîncărcat de Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentVernam Conjugated Manipulation of Bit-Plane Complexity Segmentationîncărcat de
DocumentVernam Conjugated Manipulation of Bit-Plane Complexity Segmentationîncărcat de Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentThree-Pass Protocol Implementation on Caesar Cipher in Classic Cryptographyîncărcat de
DocumentThree-Pass Protocol Implementation on Caesar Cipher in Classic Cryptographyîncărcat de Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentThree-Pass Protocol Concept in Hill Cipher Encryption Technique Ver 2încărcat de
DocumentThree-Pass Protocol Concept in Hill Cipher Encryption Technique Ver 2încărcat de Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentThe Analysis of Average Waiting Time in Managing Concurrent Processîncărcat de
DocumentThe Analysis of Average Waiting Time in Managing Concurrent Processîncărcat de Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentHuffman Text Compression Techniqueîncărcat de
DocumentHuffman Text Compression Techniqueîncărcat de Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentRC4 Technique in Visual Cryptography RGB Image Encryptionîncărcat de
DocumentRC4 Technique in Visual Cryptography RGB Image Encryptionîncărcat de Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentRail Fence Cryptography in Securing Informationîncărcat de
DocumentRail Fence Cryptography in Securing Informationîncărcat de Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentProfile Matching in Solving Rank Problemîncărcat de
DocumentProfile Matching in Solving Rank Problemîncărcat de Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentOptimasi Penjadwalan Mata Kuliah Dengan Algoritma Genetikaîncărcat de
DocumentOptimasi Penjadwalan Mata Kuliah Dengan Algoritma Genetikaîncărcat de Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentNoise-Like Region Security Improvisation in BPCS Steganographyîncărcat de
DocumentNoise-Like Region Security Improvisation in BPCS Steganographyîncărcat de Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentKlasifikasi Data Minuman Wine Menggunakan Algoritma K-Nearest Neighborîncărcat de
DocumentKlasifikasi Data Minuman Wine Menggunakan Algoritma K-Nearest Neighborîncărcat de Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentFactorization Hack of RSA Secret Numbersîncărcat de
DocumentFactorization Hack of RSA Secret Numbersîncărcat de Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentDynamic Key Matrix of Hill Cipher Using Genetic Algorithm Ver 3încărcat de
DocumentDynamic Key Matrix of Hill Cipher Using Genetic Algorithm Ver 3încărcat de Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentDining Philosophers Theory and Concept in Operating System Schedulingîncărcat de
DocumentDining Philosophers Theory and Concept in Operating System Schedulingîncărcat de Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentDetermination of Thesis Preceptor and Examiner Based on Specification of Teaching Using Fuzzy Logicîncărcat de
DocumentDetermination of Thesis Preceptor and Examiner Based on Specification of Teaching Using Fuzzy Logicîncărcat de Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentAdler-32 Integrity Validation in 24bit Color Imageîncărcat de
DocumentAdler-32 Integrity Validation in 24bit Color Imageîncărcat de Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentComparison Between WEKA and Salford System in Data Mining Softwareîncărcat de
DocumentComparison Between WEKA and Salford System in Data Mining Softwareîncărcat de Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentA Fingerprint Pattern Approach to Hill Cipher Implementationîncărcat de
DocumentA Fingerprint Pattern Approach to Hill Cipher Implementationîncărcat de Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentRC4 Technique in Visual Cryptography RGB Image Encryptionîncărcat de
DocumentRC4 Technique in Visual Cryptography RGB Image Encryptionîncărcat de Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentDetermination of Thesis Preceptor and Examiner Based on Specification of Teaching Using Fuzzy Logicîncărcat de
DocumentDetermination of Thesis Preceptor and Examiner Based on Specification of Teaching Using Fuzzy Logicîncărcat de Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentPlaying Guitar A Beginner’s Guideîncărcat de
DocumentPlaying Guitar A Beginner’s Guideîncărcat de Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentBasic 4 Androidîncărcat de
DocumentBasic 4 Androidîncărcat de Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentData Visual Basicîncărcat de
DocumentData Visual Basicîncărcat de Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentWhat is Name? And What is its Function?încărcat de
DocumentWhat is Name? And What is its Function?încărcat de Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentRBGîncărcat de
DocumentRBGîncărcat de Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentJazz Bass Book Notationîncărcat de
DocumentJazz Bass Book Notationîncărcat de Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentMatriksîncărcat de
DocumentMatriksîncărcat de Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentPinaoîncărcat de
DocumentPinaoîncărcat de Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentLatihanîncărcat de
DocumentLatihanîncărcat de Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentPENDAHULUANîncărcat de
DocumentPENDAHULUANîncărcat de Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentDining Philosophers Problemîncărcat de
DocumentDining Philosophers Problemîncărcat de Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentDining Philosophers Problemîncărcat de
DocumentDining Philosophers Problemîncărcat de Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentAuthentication Text Sourceîncărcat de
DocumentAuthentication Text Sourceîncărcat de Andysah Putra Utama Siahaan
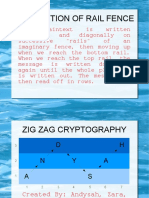
Andysah Putra Utama Siahaan DocumentZig Zag Cryptographyîncărcat de
DocumentZig Zag Cryptographyîncărcat de Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentThe Weakness of Wireless Networksîncărcat de
DocumentThe Weakness of Wireless Networksîncărcat de Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentVarious Patterns of Data Mining Techniquesîncărcat de
DocumentVarious Patterns of Data Mining Techniquesîncărcat de Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentShortest Way Huffman Text Compressionîncărcat de
DocumentShortest Way Huffman Text Compressionîncărcat de Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentGreen Computing Pada Teknologi Virtualisasiîncărcat de
DocumentGreen Computing Pada Teknologi Virtualisasiîncărcat de Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentKompresi Huffmanîncărcat de
DocumentKompresi Huffmanîncărcat de Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentThe Weakness of Wireless Networksîncărcat de
DocumentThe Weakness of Wireless Networksîncărcat de Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan DocumentMicrosoft Word 2010încărcat de
DocumentMicrosoft Word 2010încărcat de Andysah Putra Utama Siahaan
Andysah Putra Utama Siahaan
Documente Academic
Documente Profesional
Documente Cultură