DocumentUSTelecom-CSDE-2021-Botnet-Reportîncărcat de
DocumentUSTelecom-CSDE-2021-Botnet-Reportîncărcat de strokenfilled
strokenfilled Documentitu-botnet-mitigation-toolkit-backgroundîncărcat de
Documentitu-botnet-mitigation-toolkit-backgroundîncărcat de strokenfilled
strokenfilled DocumentBotnet Road Map 112918 for posting_1încărcat de
DocumentBotnet Road Map 112918 for posting_1încărcat de strokenfilled
strokenfilled DocumentA Framework for a Vulnerability Disclosure Program for Online Systemsîncărcat de
DocumentA Framework for a Vulnerability Disclosure Program for Online Systemsîncărcat de strokenfilled
strokenfilled DocumentDetecting Ransomware w Unified Securityîncărcat de
DocumentDetecting Ransomware w Unified Securityîncărcat de strokenfilled
strokenfilled DocumentLogger Course Outlineîncărcat de
DocumentLogger Course Outlineîncărcat de strokenfilled
strokenfilled Documentissue1_webrootîncărcat de
Documentissue1_webrootîncărcat de strokenfilled
strokenfilled DocumentCybersecuritystrategy Enîncărcat de
DocumentCybersecuritystrategy Enîncărcat de strokenfilled
strokenfilled DocumentTsung - Manualîncărcat de
DocumentTsung - Manualîncărcat de strokenfilled
strokenfilled DocumentITSS_01încărcat de
DocumentITSS_01încărcat de strokenfilled
strokenfilled DocumentIt Security Policyîncărcat de
DocumentIt Security Policyîncărcat de strokenfilled
strokenfilled DocumentData Standardîncărcat de
DocumentData Standardîncărcat de strokenfilled
strokenfilled Documentiso_roles_respon_guide.pdfîncărcat de
Documentiso_roles_respon_guide.pdfîncărcat de strokenfilled
strokenfilled DocumentInformation Technology Account Management Policy.pdfîncărcat de
DocumentInformation Technology Account Management Policy.pdfîncărcat de strokenfilled
strokenfilled DocumentUser Account Creation, Modification, And Deletionîncărcat de
DocumentUser Account Creation, Modification, And Deletionîncărcat de strokenfilled
strokenfilled DocumentUser Accountsîncărcat de
DocumentUser Accountsîncărcat de strokenfilled
strokenfilled DocumentuseAccPolîncărcat de
DocumentuseAccPolîncărcat de strokenfilled
strokenfilled DocumentSample SLA Templates.pdfîncărcat de
DocumentSample SLA Templates.pdfîncărcat de strokenfilled
strokenfilled DocumentBook-Tech.docîncărcat de
DocumentBook-Tech.docîncărcat de strokenfilled
strokenfilled DocumentBlockchain Programming in CSharp.pdfîncărcat de
DocumentBlockchain Programming in CSharp.pdfîncărcat de strokenfilled
strokenfilled DocumentSubnet Calculatorîncărcat de
DocumentSubnet Calculatorîncărcat de strokenfilled
strokenfilled DocumentENISA Secure Software Engineering Initiativesîncărcat de
DocumentENISA Secure Software Engineering Initiativesîncărcat de strokenfilled
strokenfilled DocumentZlib-AutomatedSecurityAssessmentîncărcat de
DocumentZlib-AutomatedSecurityAssessmentîncărcat de strokenfilled
strokenfilled DocumentIntegrating EJBCA and OpenSSOîncărcat de
DocumentIntegrating EJBCA and OpenSSOîncărcat de strokenfilled
strokenfilled DocumentInstalling EJBCA on JBoss and CentOS 6_ How to Install EJBCA 6.1.1 on JBoss 7.1încărcat de
DocumentInstalling EJBCA on JBoss and CentOS 6_ How to Install EJBCA 6.1.1 on JBoss 7.1încărcat de strokenfilled
strokenfilled DocumentRSA Leakageîncărcat de
DocumentRSA Leakageîncărcat de strokenfilled
strokenfilled Document20160111061923-Buletin SDPPI Postel Edisi 9încărcat de
Document20160111061923-Buletin SDPPI Postel Edisi 9încărcat de strokenfilled
strokenfilled DocumentConfigure SMIME on WorxMail for IOSîncărcat de
DocumentConfigure SMIME on WorxMail for IOSîncărcat de strokenfilled
strokenfilled Documentuc-web-report-final-for-dc.pdfîncărcat de
Documentuc-web-report-final-for-dc.pdfîncărcat de strokenfilled
strokenfilled DocumentUnmasking the Five Eyesîncărcat de
DocumentUnmasking the Five Eyesîncărcat de strokenfilled
strokenfilled DocumentForensic Analysis of the ChatSecure Instant Messaging Application on Android Smartphones.pdfîncărcat de
DocumentForensic Analysis of the ChatSecure Instant Messaging Application on Android Smartphones.pdfîncărcat de strokenfilled
strokenfilled DocumentLive Memory Forensics on Android With Volatilityîncărcat de
DocumentLive Memory Forensics on Android With Volatilityîncărcat de strokenfilled
strokenfilled DocumentForensic Analysis of the ChatSecure Instant Messaging Application on Android Smartphonesîncărcat de
DocumentForensic Analysis of the ChatSecure Instant Messaging Application on Android Smartphonesîncărcat de strokenfilled
strokenfilled DocumentDraftNationalCybersecurityWorkforceFrameworkV2.xlsxîncărcat de
DocumentDraftNationalCybersecurityWorkforceFrameworkV2.xlsxîncărcat de strokenfilled
strokenfilled DocumentAutomated Analysis and Deobfuscation of Android Apps & Malware.pdfîncărcat de
DocumentAutomated Analysis and Deobfuscation of Android Apps & Malware.pdfîncărcat de strokenfilled
strokenfilled DocumentAutomated Analysis and Deobfuscation of Android Apps & Malwareîncărcat de
DocumentAutomated Analysis and Deobfuscation of Android Apps & Malwareîncărcat de strokenfilled
strokenfilled Documentdsouza-fortify-07.pdfîncărcat de
Documentdsouza-fortify-07.pdfîncărcat de strokenfilled
strokenfilled DocumentDraftNationalCybersecurityWorkforceFrameworkV2.xlsxîncărcat de
DocumentDraftNationalCybersecurityWorkforceFrameworkV2.xlsxîncărcat de strokenfilled
strokenfilled DocumentCyberWar-AOCO-2014încărcat de
DocumentCyberWar-AOCO-2014încărcat de strokenfilled
strokenfilled DocumentData-In-Use Leakages From Android Memory - Test and Analysisîncărcat de
DocumentData-In-Use Leakages From Android Memory - Test and Analysisîncărcat de strokenfilled
strokenfilled DocumentIncident Report Sampleîncărcat de
DocumentIncident Report Sampleîncărcat de strokenfilled
strokenfilled DocumentICS-CERT Monitor April-June2013 0încărcat de
DocumentICS-CERT Monitor April-June2013 0încărcat de strokenfilled
strokenfilled DocumentGlobal Cyber Security Outlookîncărcat de
DocumentGlobal Cyber Security Outlookîncărcat de strokenfilled
strokenfilled DocumentMONDAY CS 1 7 Nick Galletto Michael Juergensîncărcat de
DocumentMONDAY CS 1 7 Nick Galletto Michael Juergensîncărcat de strokenfilled
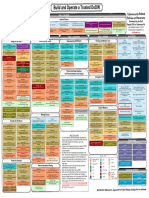
strokenfilled DocumentIa Policychartîncărcat de
DocumentIa Policychartîncărcat de strokenfilled
strokenfilled DocumentHashim Cybersecurity Malaysia June 09încărcat de
DocumentHashim Cybersecurity Malaysia June 09încărcat de strokenfilled
strokenfilled DocumentNational Cybersecîncărcat de
DocumentNational Cybersecîncărcat de strokenfilled
strokenfilled DocumentMix Columnsîncărcat de
DocumentMix Columnsîncărcat de strokenfilled
strokenfilled DocumentAESbyExampleîncărcat de
DocumentAESbyExampleîncărcat de strokenfilled
strokenfilled
Documente Academic
Documente Profesional
Documente Cultură